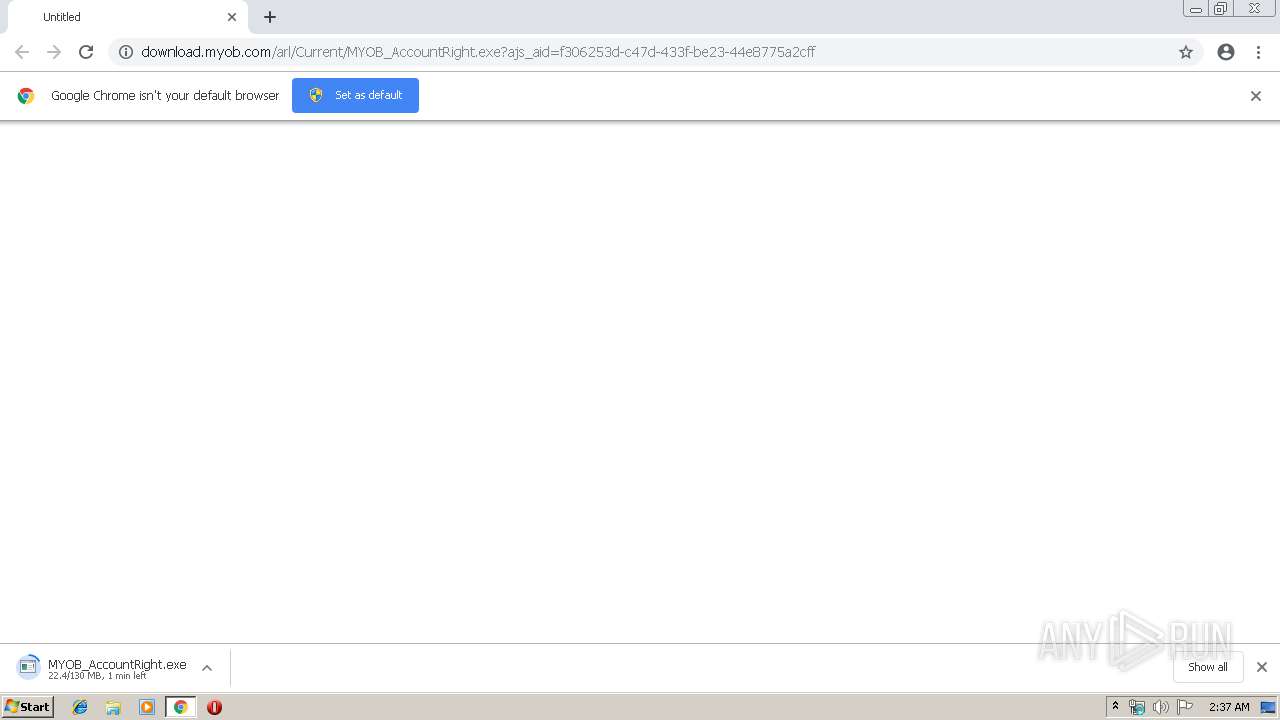
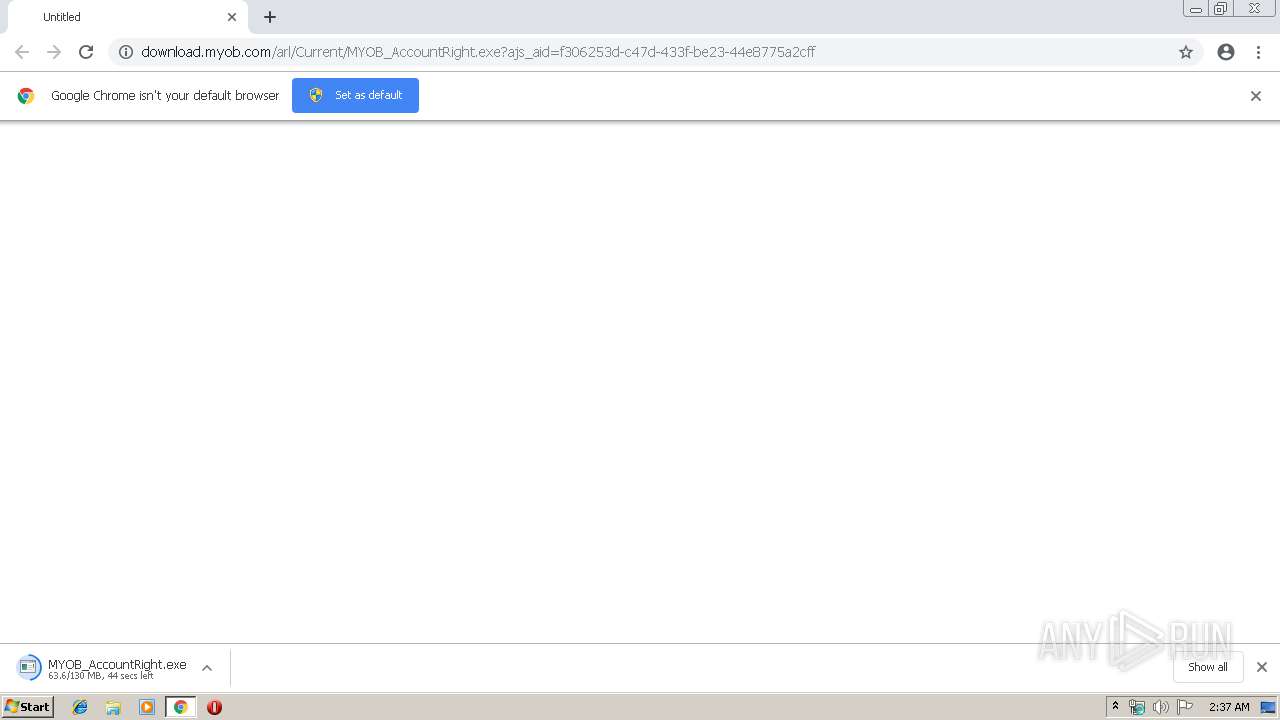
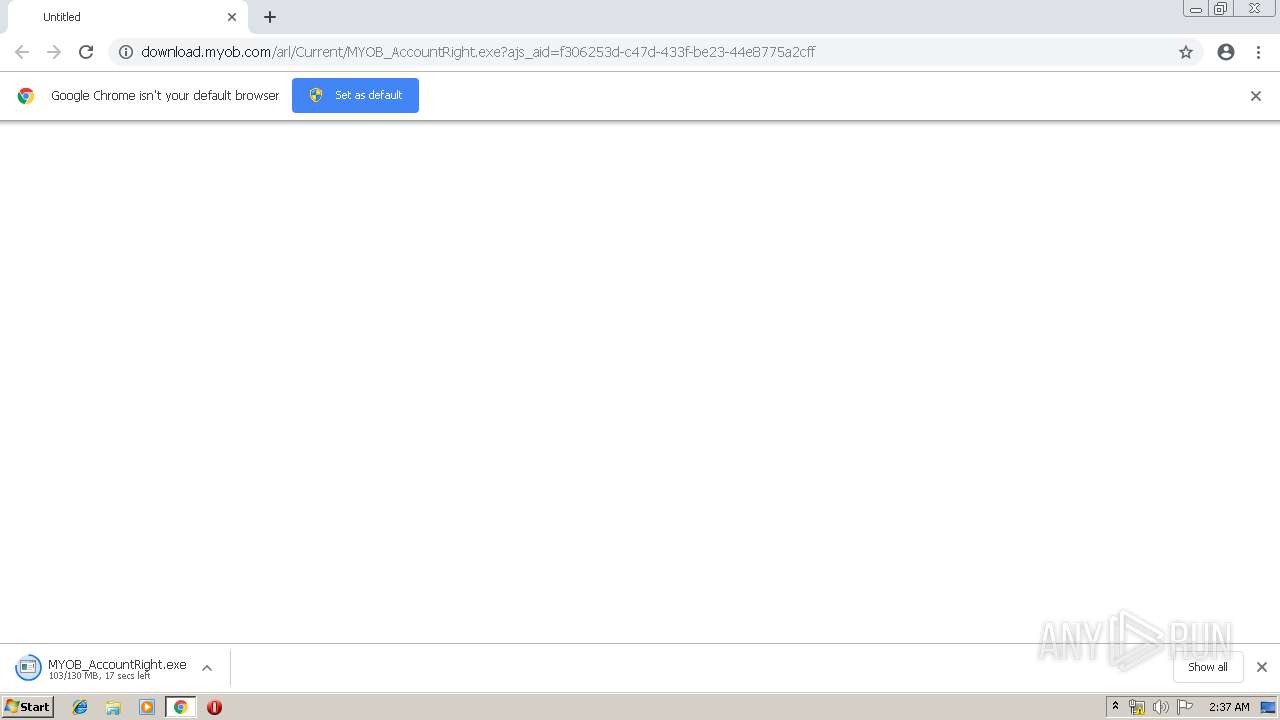
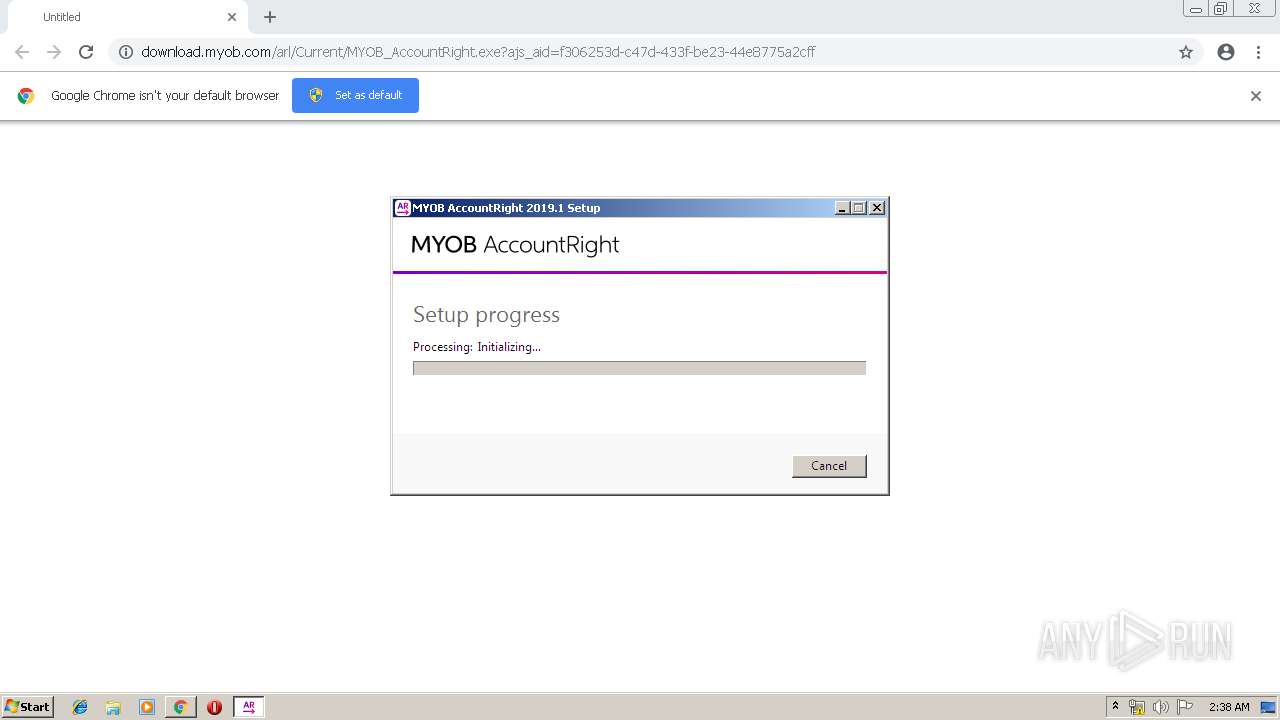
| URL: | http://download.myob.com/arl/Current/MYOB_AccountRight.exe?ajs_aid=f306253d-c47d-433f-be23-44e8775a2cff |
| Full analysis: | https://app.any.run/tasks/760fa0c4-df72-4e8e-b934-d08277a17392 |
| Verdict: | Malicious activity |
| Analysis date: | March 22, 2019, 02:36:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 3B073A03FE47057528EA7ED59D7A1C6B |
| SHA1: | 2B5CCF48CDDADB99BD4B05294575CCC39346B74F |
| SHA256: | AE460F8C40F7A47599E08C6779B740D6450C9463F6883686E4D7C7622DBC7FD9 |
| SSDEEP: | 3:N1KaKElsiZyXeR/n+SLRBtwvMBY8XQW+G0oUimH0:Ca5si4+/+4Tt89HW50Xi80 |
MALICIOUS
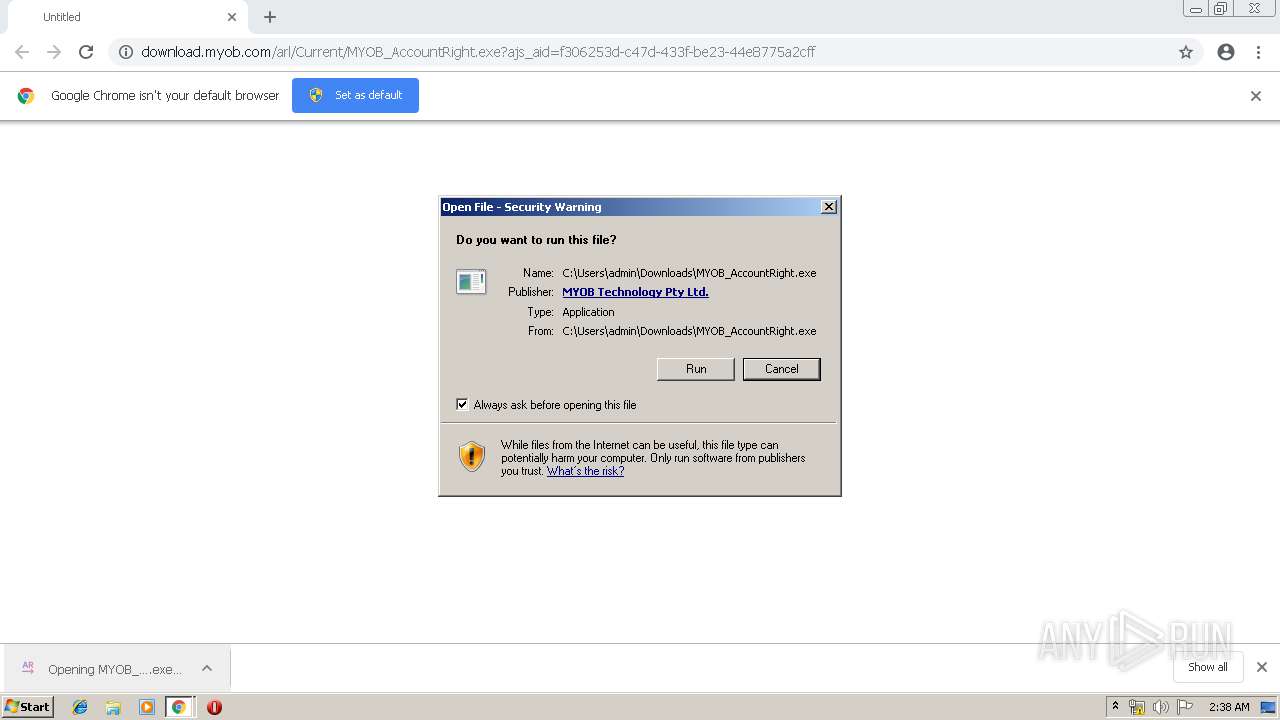
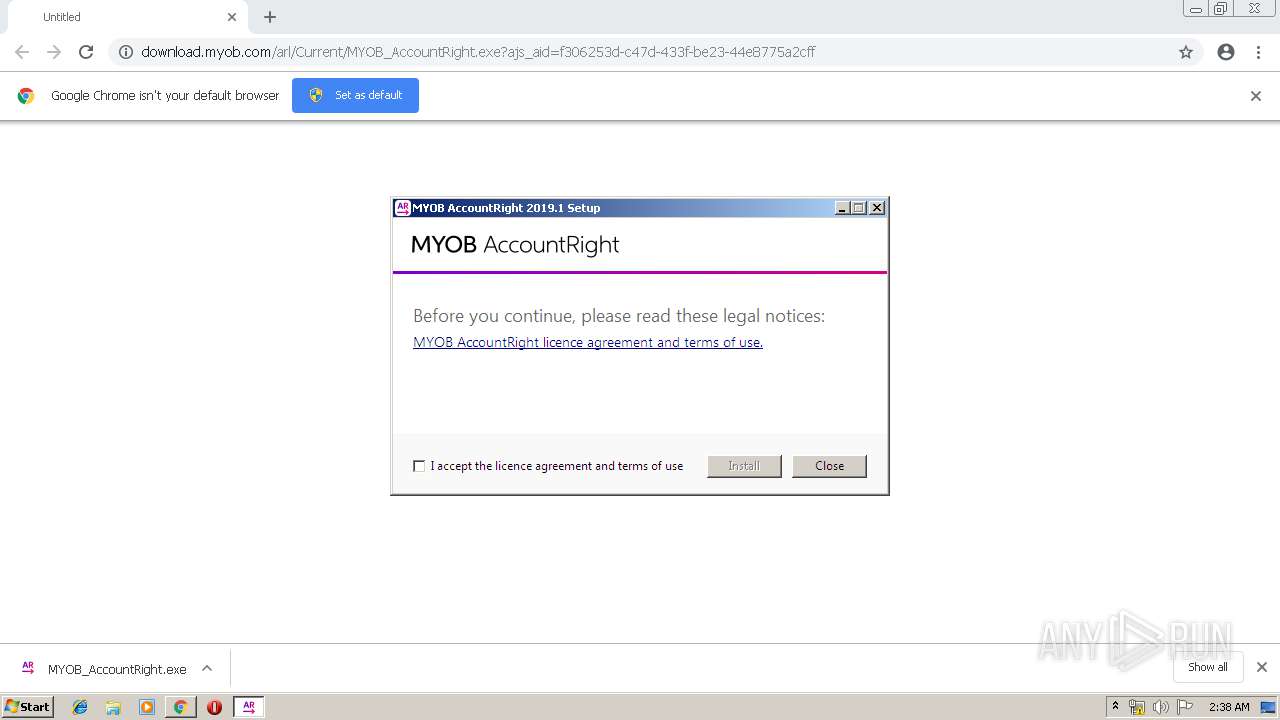
Application was dropped or rewritten from another process
- MYOB_AccountRight.exe (PID: 3712)
- MYOB_AccountRight.exe (PID: 1352)
- MYOB AccountRight Setup 2019.1.exe (PID: 3984)
- Setup.exe (PID: 1824)
- NDP462-KB3151802-Web.exe (PID: 2516)
- SetupUtility.exe (PID: 3836)
- ServiceModelReg.exe (PID: 2652)
- aspnet_regiis.exe (PID: 2332)
- SetupUtility.exe (PID: 2668)
Loads dropped or rewritten executable
- MYOB_AccountRight.exe (PID: 1352)
- Setup.exe (PID: 1824)
- SearchFilterHost.exe (PID: 2568)
Changes the autorun value in the registry
- MYOB_AccountRight.exe (PID: 1352)
Changes settings of System certificates
- Setup.exe (PID: 1824)
SUSPICIOUS
Executable content was dropped or overwritten
- MYOB_AccountRight.exe (PID: 1352)
- chrome.exe (PID: 3452)
- MYOB_AccountRight.exe (PID: 3712)
- MYOB AccountRight Setup 2019.1.exe (PID: 3984)
- NDP462-KB3151802-Web.exe (PID: 2516)
- TMPFDFA.tmp.exe (PID: 2244)
- Setup.exe (PID: 1824)
- msiexec.exe (PID: 3644)
Starts itself from another location
- MYOB_AccountRight.exe (PID: 1352)
Searches for installed software
- MYOB AccountRight Setup 2019.1.exe (PID: 3984)
Creates a software uninstall entry
- MYOB_AccountRight.exe (PID: 1352)
Adds / modifies Windows certificates
- Setup.exe (PID: 1824)
Creates COM task schedule object
- msiexec.exe (PID: 3644)
- aspnet_regiis.exe (PID: 2332)
Removes files from Windows directory
- lodctr.exe (PID: 1880)
- aspnet_regiis.exe (PID: 2332)
- msiexec.exe (PID: 3644)
Creates files in the Windows directory
- aspnet_regiis.exe (PID: 2332)
- lodctr.exe (PID: 1880)
- msiexec.exe (PID: 3644)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3452)
Changes the autorun value in the registry
- msiexec.exe (PID: 3644)
INFO
Application launched itself
- chrome.exe (PID: 3452)
- msiexec.exe (PID: 3644)
Low-level read access rights to disk partition
- vssvc.exe (PID: 1924)
Changes settings of System certificates
- DrvInst.exe (PID: 3800)
Adds / modifies Windows certificates
- DrvInst.exe (PID: 3800)
Dropped object may contain Bitcoin addresses
- msiexec.exe (PID: 3644)
- Setup.exe (PID: 1824)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 756)
- MsiExec.exe (PID: 2268)
- msiexec.exe (PID: 3644)
Creates or modifies windows services
- msiexec.exe (PID: 3644)
Creates a software uninstall entry
- msiexec.exe (PID: 3644)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
92
Monitored processes
46
Malicious processes
9
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 752 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\regtlibv12.exe" "C:\Windows\Microsoft.NET\Framework\v4.0.30319\Microsoft.JScript.tlb" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\regtlibv12.exe | — | MsiExec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: RegTLib Exit code: 0 Version: 14.6.1590.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 756 | C:\Windows\system32\MsiExec.exe -Embedding 43B627AAD9F396DCDF345F91A1C203A7 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1064 | "C:\Windows\system32\wbem\mofcomp.exe" "C:\Windows\Microsoft.NET\Framework\v4.0.30319\MOF\ServiceModel35.mof" | C:\Windows\system32\wbem\mofcomp.exe | — | MsiExec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: The Managed Object Format (MOF) Compiler Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,12260693615696510672,6953377029294146589,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=7485541946474434963 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7485541946474434963 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3992 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1172 | mofcomp C:\Windows\Microsoft.NET\Framework\v4.0.30319\aspnet.mof | C:\Windows\system32\wbem\mofcomp.exe | — | aspnet_regiis.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: The Managed Object Format (MOF) Compiler Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1352 | "C:\Users\admin\AppData\Local\Temp\{56306D14-A6DD-4D50-B8A0-C6C6618330CE}\.cr\MYOB_AccountRight.exe" -burn.clean.room="C:\Users\admin\Downloads\MYOB_AccountRight.exe" -burn.filehandle.attached=148 -burn.filehandle.self=156 | C:\Users\admin\AppData\Local\Temp\{56306D14-A6DD-4D50-B8A0-C6C6618330CE}\.cr\MYOB_AccountRight.exe | MYOB_AccountRight.exe | ||||||||||||
User: admin Company: MYOB Technology Pty. Ltd. Integrity Level: MEDIUM Description: MYOB AccountRight 2019.1 Exit code: 0 Version: 2019.1.0 Modules
| |||||||||||||||
| 1672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fa30f18,0x6fa30f28,0x6fa30f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1700 | um C:\Windows\Microsoft.NET\Framework\v4.0.30319\Microsoft.Windows.ApplicationServer.Applications.45.man | C:\Windows\system32\wevtutil.exe | — | ServiceModelReg.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Eventing Command Line Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1728 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\regtlibv12.exe" "C:\Windows\Microsoft.NET\Framework\v4.0.30319\System.EnterpriseServices.tlb" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\regtlibv12.exe | — | MsiExec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: RegTLib Exit code: 0 Version: 14.6.1590.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 1824 | C:\c4136493dd89ffd43a1abb85c6\\Setup.exe /q /norestart /ChainingPackage "MYOB AccountRight 2019.1" /log "C:\Users\admin\AppData\Local\Temp\MYOB_AccountRight_2019.1_20190322023823_000_NetFx462Web.log.html" /pipe NetFxSection.{DFE3BC7C-4964-4EE1-8706-EBAE454ECF69} /x86 /x64 /web | C:\c4136493dd89ffd43a1abb85c6\Setup.exe | NDP462-KB3151802-Web.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Setup Installer Exit code: 0 Version: 14.6.1590.0 built by: NETFXREL2 Modules
| |||||||||||||||
Total events
16 743
Read events
6 703
Write events
8 316
Delete events
1 724
Modification events
| (PID) Process: | (3452) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3452) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3452) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3452) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3452) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3280) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3452-13197695811902875 |
Value: 259 | |||
| (PID) Process: | (3452) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3452) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3452) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (3452) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
489
Suspicious files
55
Text files
458
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3452 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3452 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3452 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3452 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 3452 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 3452 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\6a5c16ae-204c-42a2-8f10-3842c05c81ec.tmp | — | |
MD5:— | SHA256:— | |||
| 3452 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3452 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3452 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3452 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
8
DNS requests
5
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2676 | chrome.exe | GET | — | 52.95.134.28:80 | http://download.myob.com/arl/Current/MYOB_AccountRight.exe?ajs_aid=f306253d-c47d-433f-be23-44e8775a2cff | AU | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2676 | chrome.exe | 172.217.23.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2676 | chrome.exe | 172.217.18.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
2676 | chrome.exe | 52.95.134.28:80 | download.myob.com | Amazon.com, Inc. | AU | suspicious |
2676 | chrome.exe | 216.58.208.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2676 | chrome.exe | 216.58.207.67:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
download.myob.com |
| malicious |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2676 | chrome.exe | Potentially Bad Traffic | ET POLICY Executable served from Amazon S3 |
2676 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2676 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
1352 | MYOB_AccountRight.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
— | — | Misc activity | ET INFO Packed Executable Download |
— | — | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
— | — | Misc activity | ET INFO EXE - Served Attached HTTP |