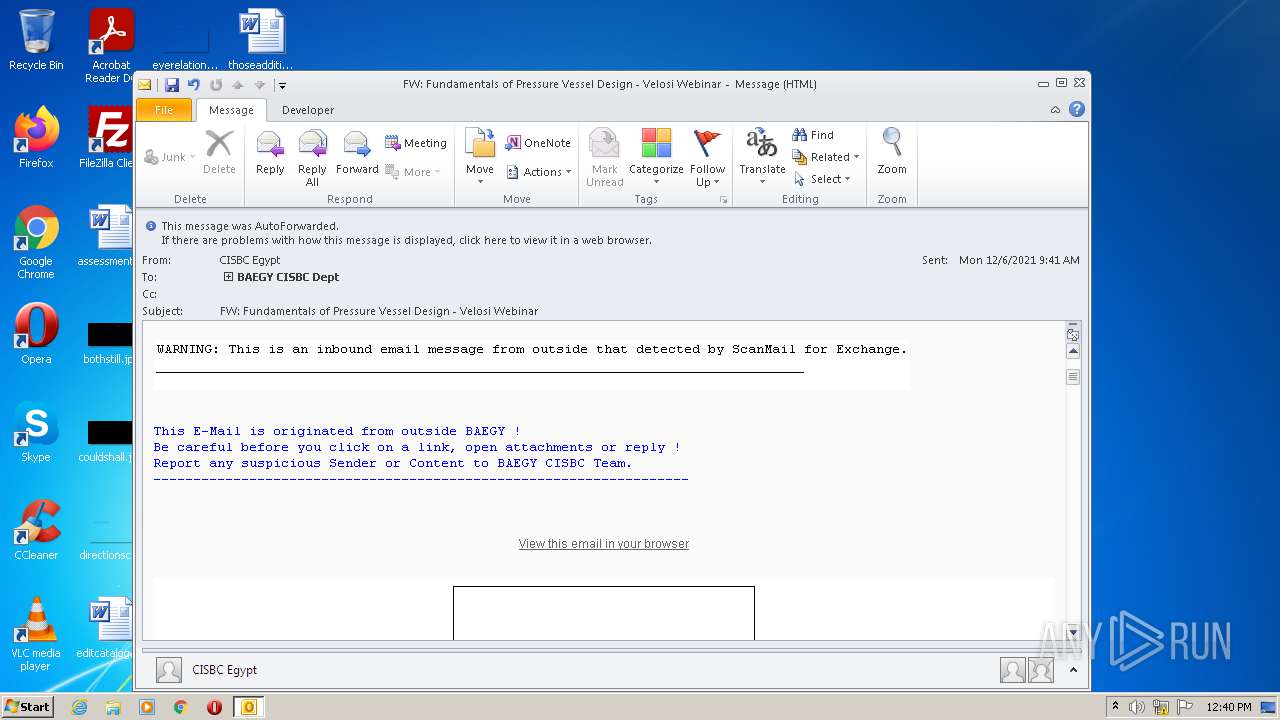
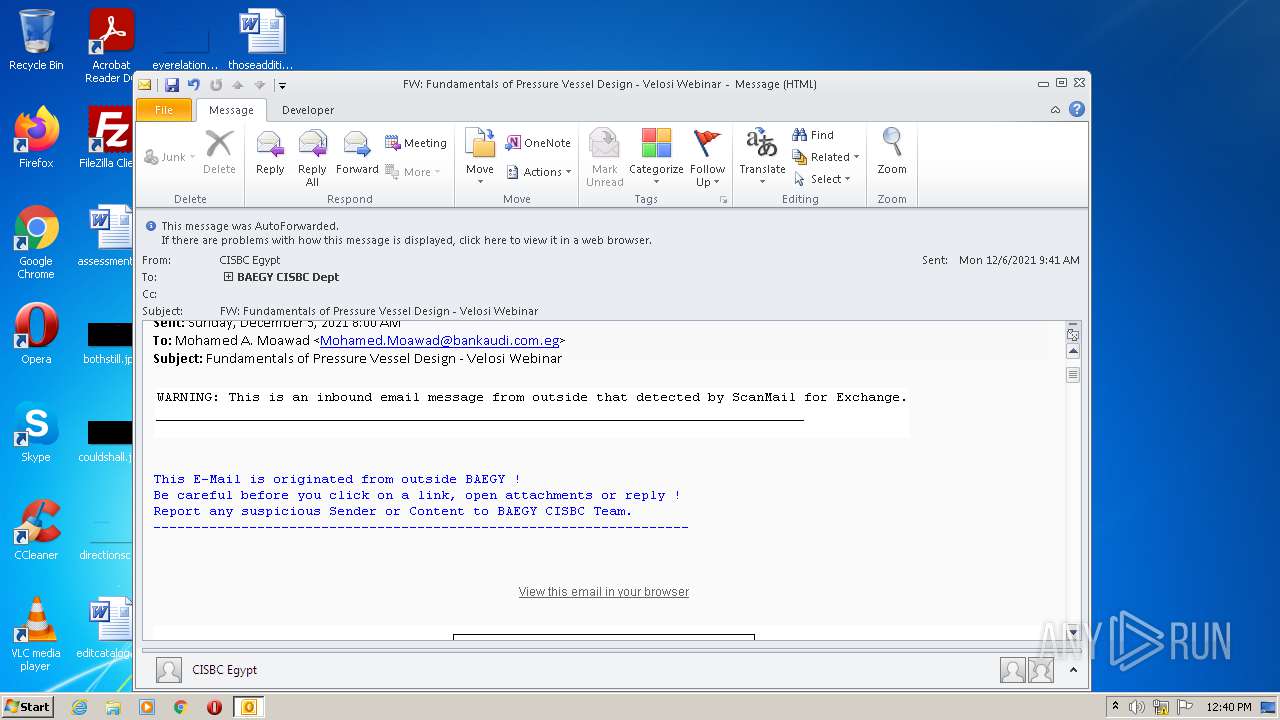
| File name: | spammr.msg |
| Full analysis: | https://app.any.run/tasks/f26dd7a3-4618-4ff1-a590-fcbb1f34b34c |
| Verdict: | Malicious activity |
| Analysis date: | December 07, 2021, 12:40:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
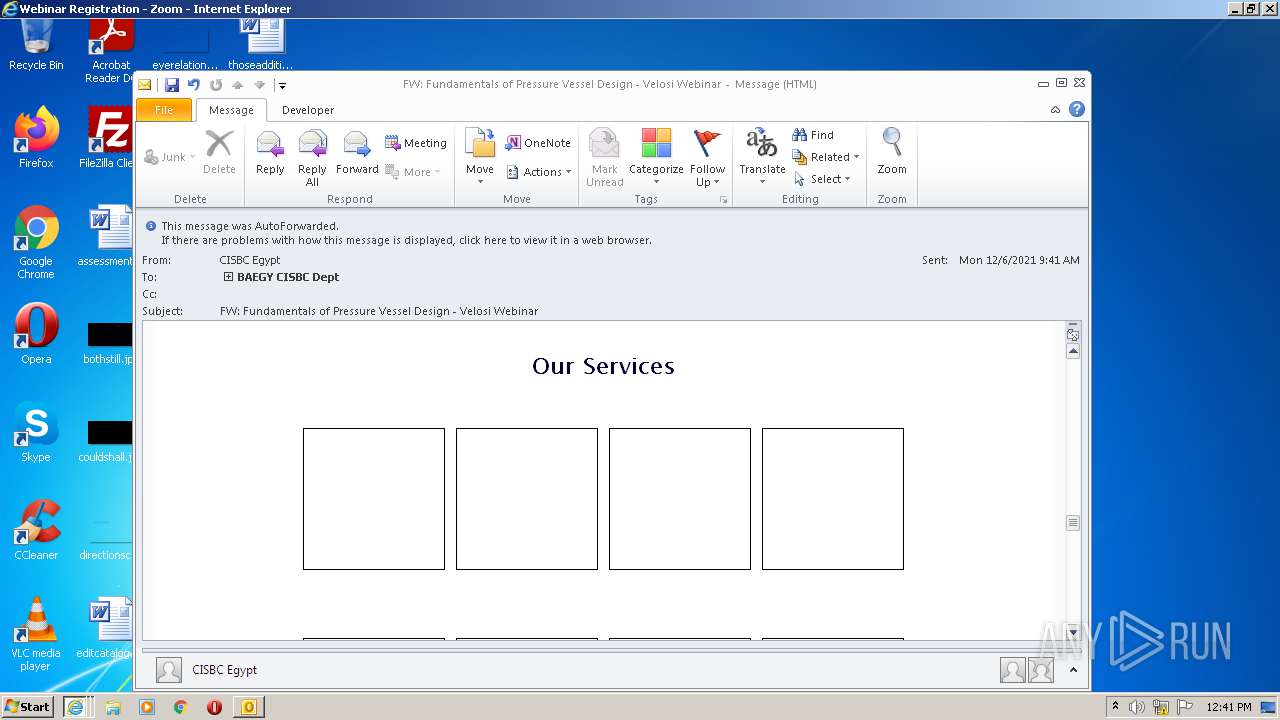
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | A4A4B71F1FE5A3EE6C78CA2DC8AB262E |
| SHA1: | 0904B912993A86F46447FD6D57DADA3AED8D0191 |
| SHA256: | AE41DF63E5179BC926FA96C57C3B9D3C64A2F79546E2A099167455EC00762B07 |
| SSDEEP: | 1536:R0xStEJaKLGM/djGzr9tI46+7+Y3vqqqtudO/BX3uONyNjnnJ9s9b1U:RYMb0/4P9G46+hqqqJ5X3vkjnMS |
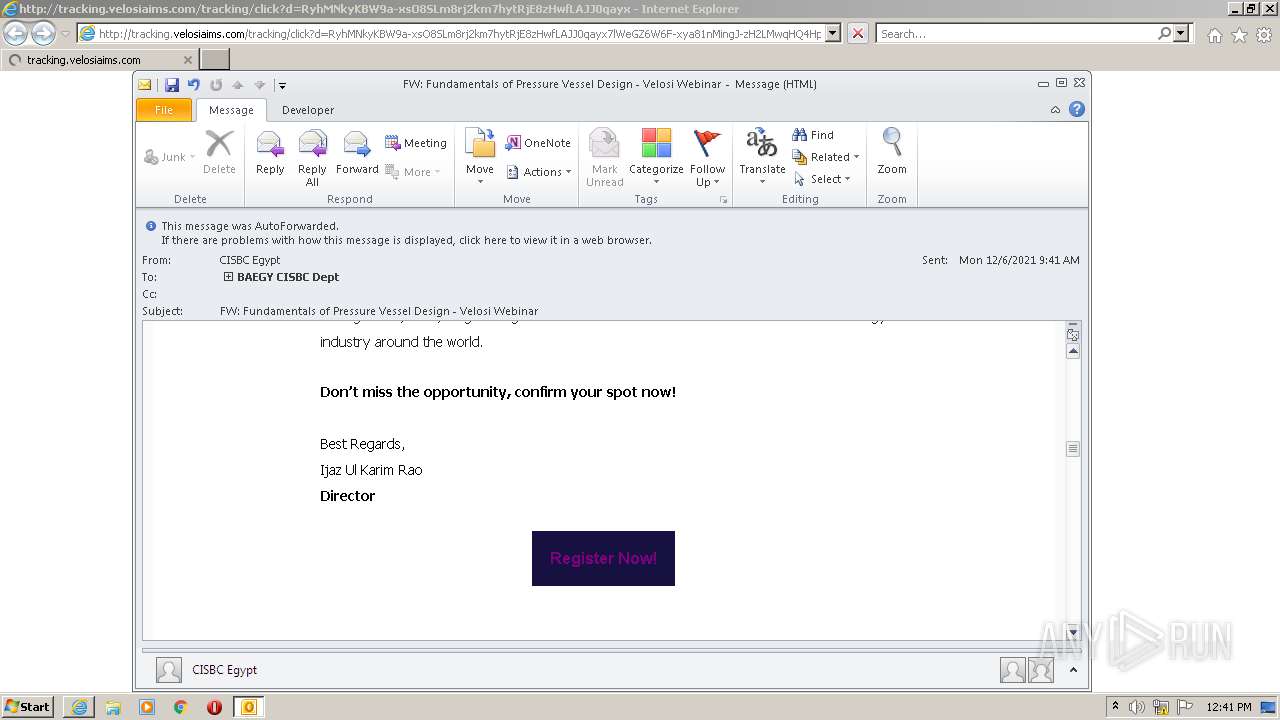
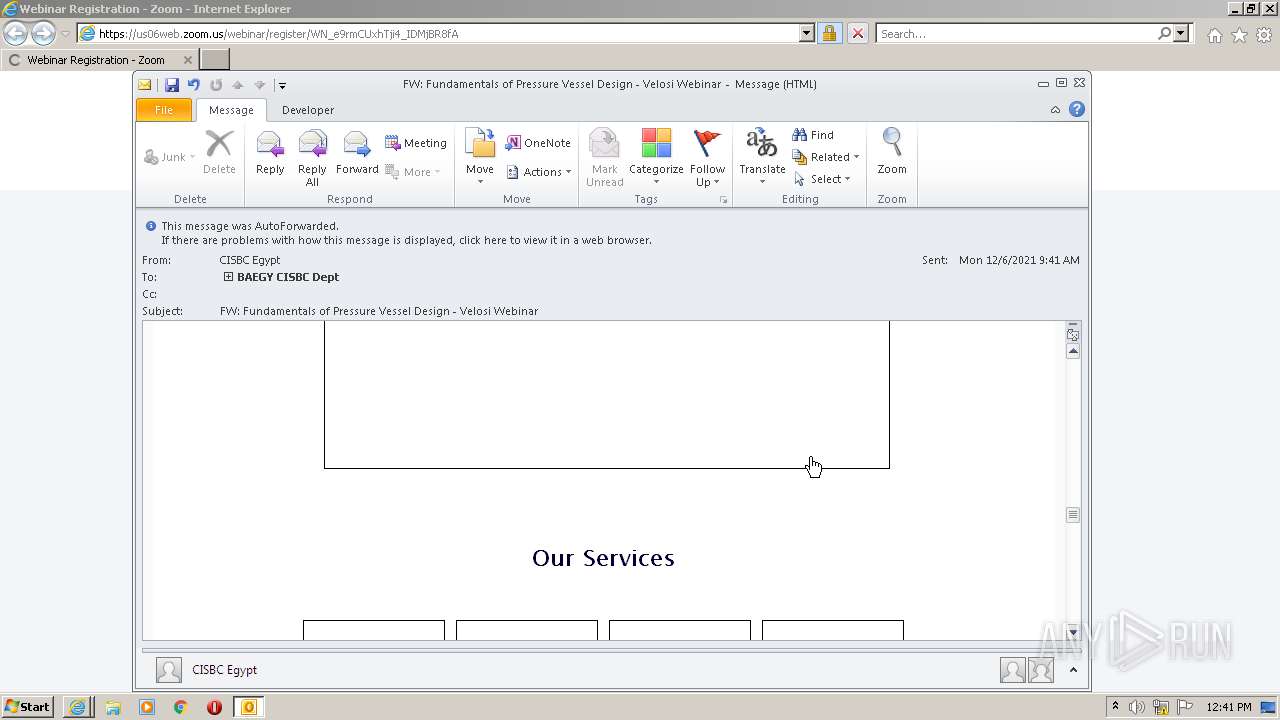
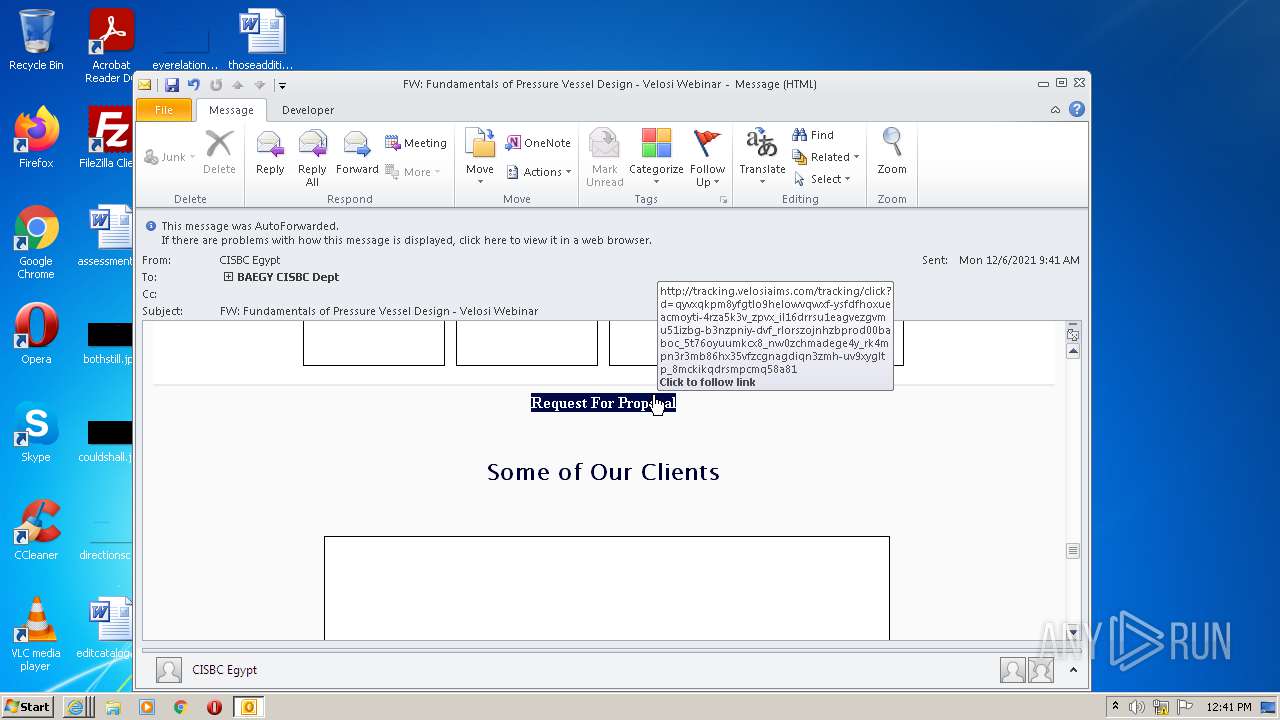
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 3572)
SUSPICIOUS
Starts Internet Explorer
- OUTLOOK.EXE (PID: 3572)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 1976)
- iexplore.exe (PID: 508)
- iexplore.exe (PID: 2608)
- iexplore.exe (PID: 3676)
- iexplore.exe (PID: 3656)
- iexplore.exe (PID: 3660)
Checks for external IP
- iexplore.exe (PID: 3676)
- iexplore.exe (PID: 2608)
- iexplore.exe (PID: 3660)
INFO
Reads the computer name
- OUTLOOK.EXE (PID: 3572)
- iexplore.exe (PID: 2020)
- iexplore.exe (PID: 508)
- iexplore.exe (PID: 1976)
- iexplore.exe (PID: 2872)
- iexplore.exe (PID: 2608)
- iexplore.exe (PID: 3676)
- iexplore.exe (PID: 3656)
- iexplore.exe (PID: 3660)
Checks supported languages
- iexplore.exe (PID: 1976)
- iexplore.exe (PID: 508)
- iexplore.exe (PID: 2872)
- OUTLOOK.EXE (PID: 3572)
- iexplore.exe (PID: 2020)
- iexplore.exe (PID: 2608)
- iexplore.exe (PID: 3676)
- iexplore.exe (PID: 3656)
- iexplore.exe (PID: 3660)
Application launched itself
- iexplore.exe (PID: 2872)
- iexplore.exe (PID: 2020)
Changes internet zones settings
- iexplore.exe (PID: 2020)
- iexplore.exe (PID: 2872)
Searches for installed software
- OUTLOOK.EXE (PID: 3572)
Creates files in the user directory
- OUTLOOK.EXE (PID: 3572)
- iexplore.exe (PID: 1976)
- iexplore.exe (PID: 508)
- iexplore.exe (PID: 2608)
- iexplore.exe (PID: 3676)
- iexplore.exe (PID: 3656)
- iexplore.exe (PID: 3660)
Checks Windows Trust Settings
- iexplore.exe (PID: 508)
- iexplore.exe (PID: 1976)
- iexplore.exe (PID: 2020)
- iexplore.exe (PID: 2872)
- iexplore.exe (PID: 2608)
- iexplore.exe (PID: 3676)
- iexplore.exe (PID: 3656)
- iexplore.exe (PID: 3660)
Reads settings of System Certificates
- iexplore.exe (PID: 2020)
- iexplore.exe (PID: 508)
- iexplore.exe (PID: 1976)
- iexplore.exe (PID: 2872)
- iexplore.exe (PID: 2608)
- iexplore.exe (PID: 3676)
- iexplore.exe (PID: 3656)
- iexplore.exe (PID: 3660)
Reads internet explorer settings
- iexplore.exe (PID: 1976)
- iexplore.exe (PID: 508)
- iexplore.exe (PID: 2608)
- iexplore.exe (PID: 3676)
- iexplore.exe (PID: 3656)
- iexplore.exe (PID: 3660)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3572)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
45
Monitored processes
9
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 508 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2872 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1976 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2020 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
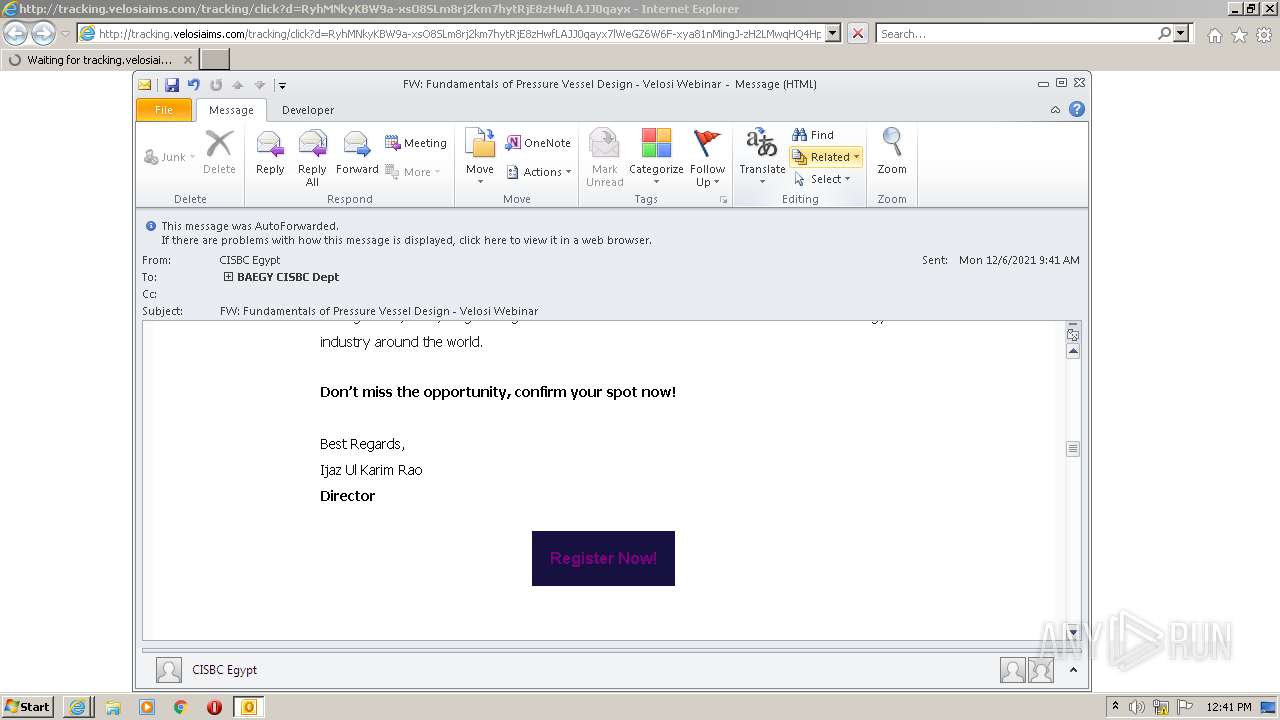
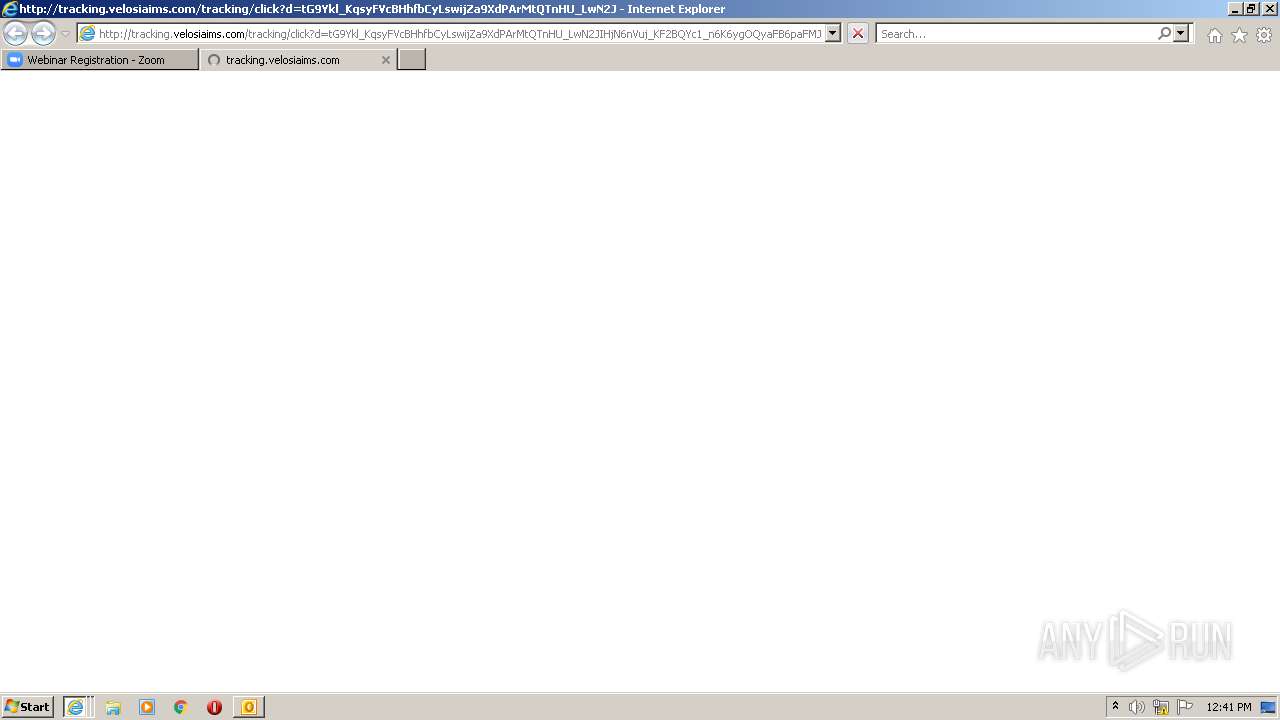
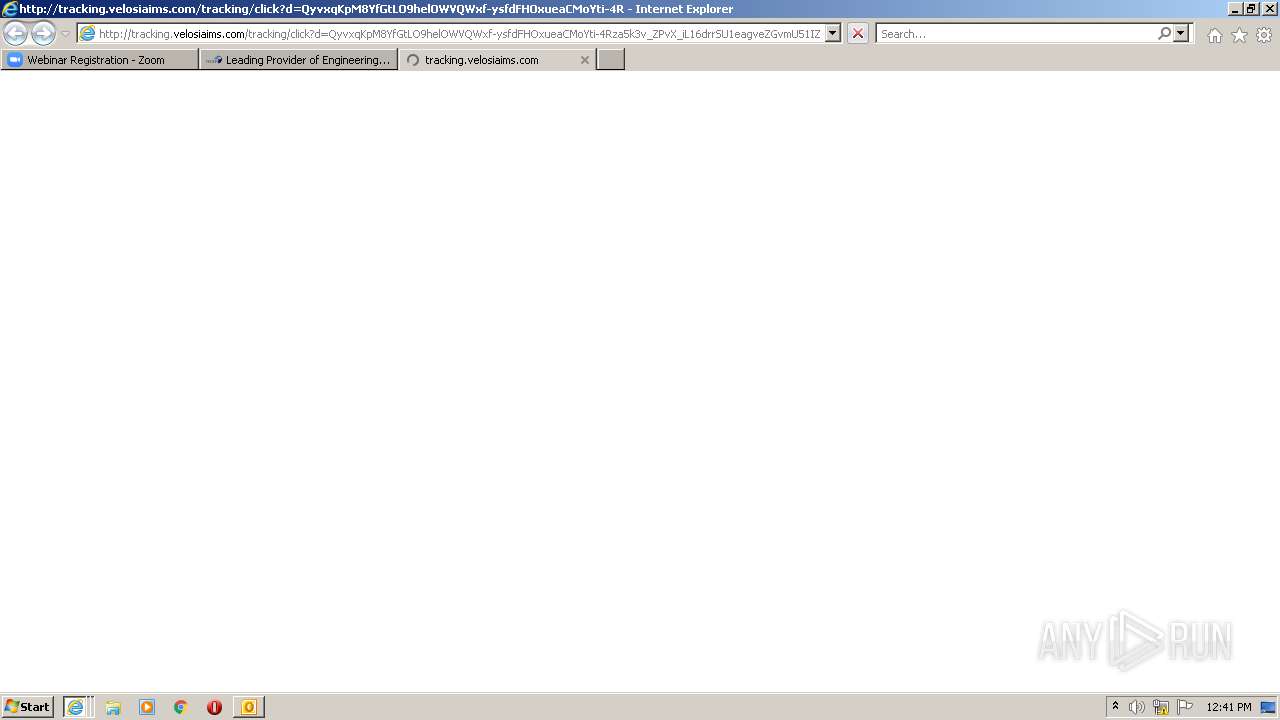
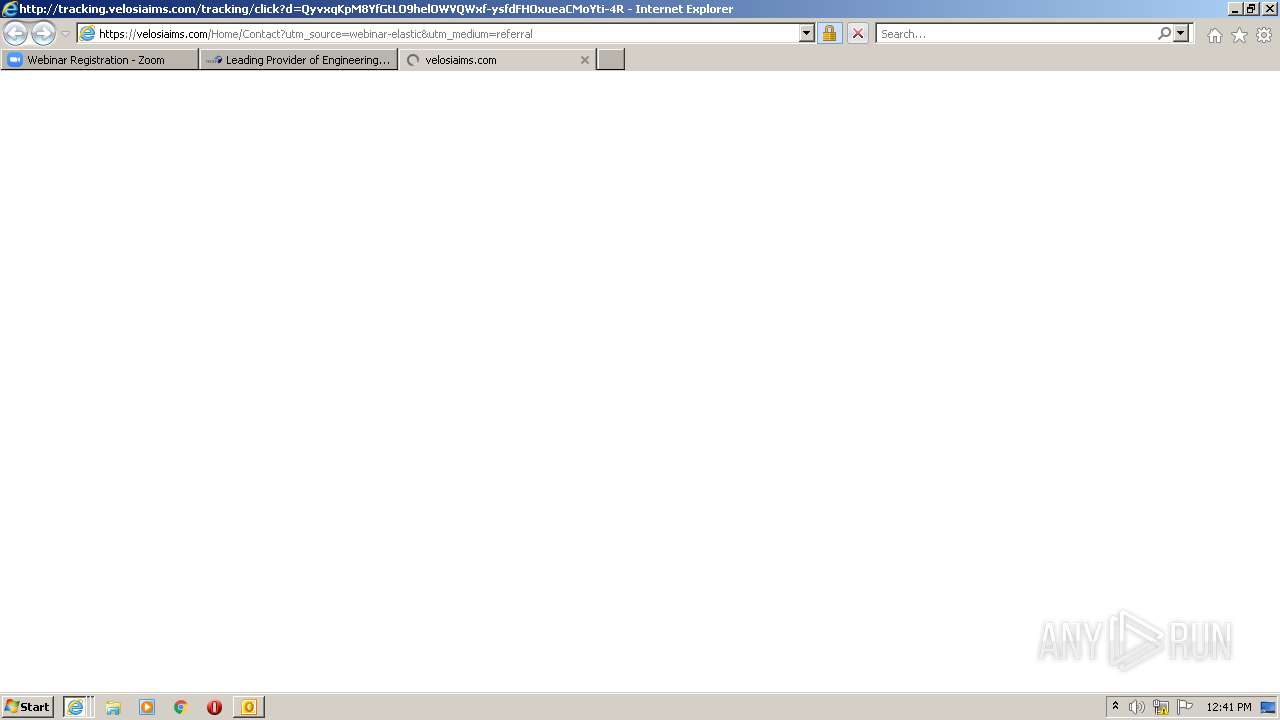
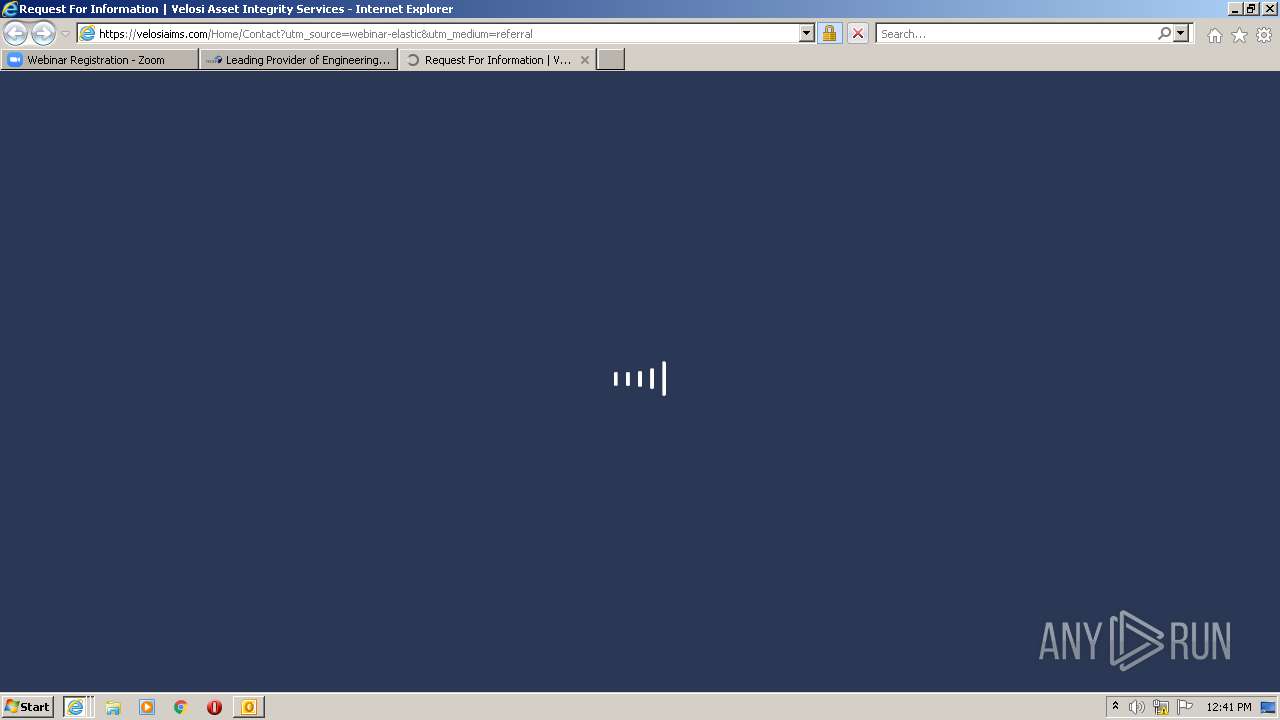
| 2020 | "C:\Program Files\Internet Explorer\iexplore.exe" http://tracking.velosiaims.com/tracking/click?d=RyhMNkyKBW9a-xsO8SLm8rj2km7hytRjE8zHwfLAJJ0qayx7lWeGZ6W6F-xya81nMingJ-zH2LMwqHQ4HpbCiotoPzl6sGe3UlIbDG8AjeMqWTF8ZMZ2jtcUz-nz1vTeqnBhpWA5ruMs1LRrh6szhThITjonEA3OtX8xq3ARw1RXFaatNx8S_KoplYgoWzY32w2 | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2608 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2020 CREDAT:988421 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2872 | "C:\Program Files\Internet Explorer\iexplore.exe" http://tracking.velosiaims.com/tracking/click?d=RyhMNkyKBW9a-xsO8SLm8rj2km7hytRjE8zHwfLAJJ0qayx7lWeGZ6W6F-xya81nMingJ-zH2LMwqHQ4HpbCiotoPzl6sGe3UlIbDG8AjeMqWTF8ZMZ2jtcUz-nz1vTeqnBhpWA5ruMs1LRrh6szhThITjonEA3OtX8xq3ARw1RXFaatNx8S_KoplYgoWzY32w2 | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3572 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\spammr.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3656 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2020 CREDAT:1578250 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3660 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2872 CREDAT:4003097 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3676 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2872 CREDAT:3413280 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
54 846
Read events
53 066
Write events
1 758
Delete events
22
Modification events
| (PID) Process: | (3572) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3572) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3572) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3572) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3572) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3572) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3572) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3572) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3572) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (3572) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
37
Text files
331
Unknown types
68
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3572 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR586E.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3572 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 3572 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1976 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_D975BBA8033175C8D112023D8A7A8AD6 | der | |
MD5:— | SHA256:— | |||
| 508 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3572 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\D1532AA.dat | image | |
MD5:— | SHA256:— | |||
| 3572 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 3572 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\ABF58D3C.dat | image | |
MD5:869AE6C28CE39EEEA0592B7FEC811AE3 | SHA256:C8546FA9F85D18AB54B470CD14CFF04A4B512C58755E95AA642F081046EA23D0 | |||
| 3572 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\{4AB05BFB-55F0-4DE7-B5D0-16947D9C2297}\{1C306CB1-771E-4B4B-A902-86E897877F5B}.png | image | |
MD5:4C61C12EDBC453D7AE184976E95258E1 | SHA256:296526F9A716C1AA91BA5D6F69F0EB92FDF79C2CB2CFCF0CEB22B7CCBC27035F | |||
| 3572 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_TCPrefs_2_5E67188FD0ADA6499ABC4209E3C291F7.dat | xml | |
MD5:F194B1FA12F9B6F46A47391FAE8BEEC2 | SHA256:FCD8D7E030BE6EA7588E5C6CB568E3F1BDFC263942074B693942A27DF9521A74 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
329
DNS requests
57
Threats
17
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2872 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
508 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
1976 | iexplore.exe | GET | 200 | 13.225.84.175:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
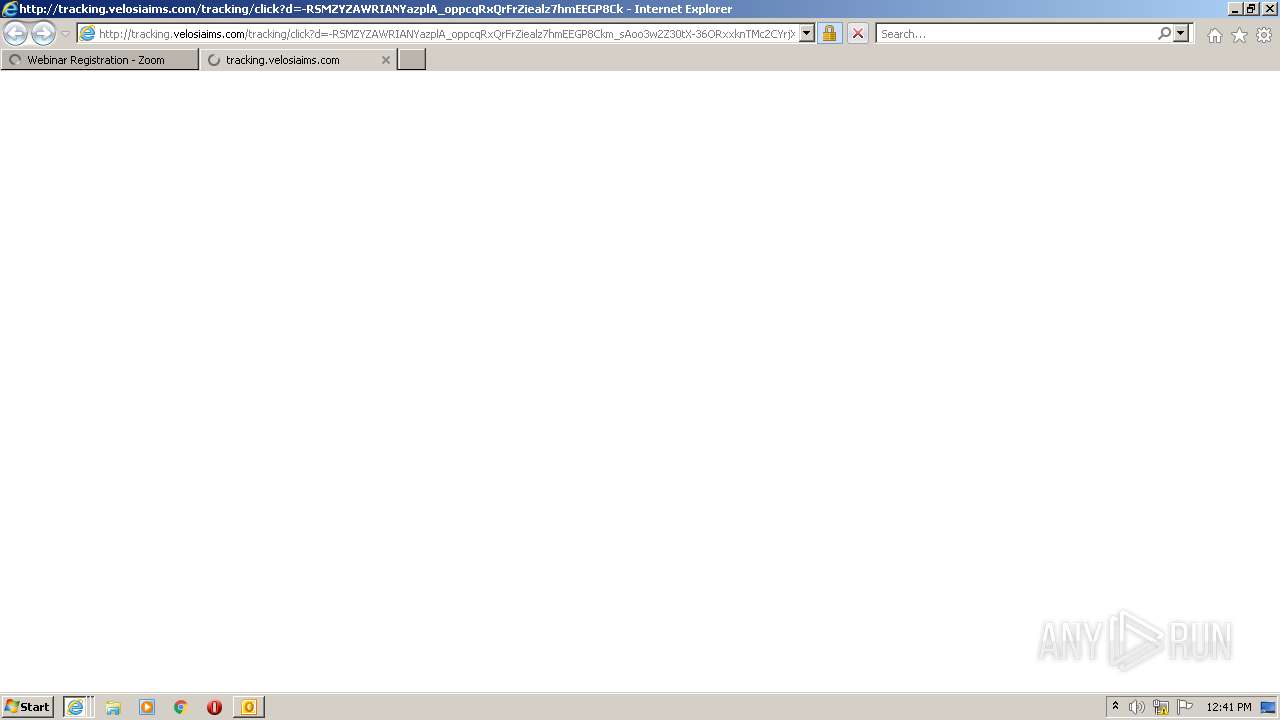
508 | iexplore.exe | GET | 302 | 46.105.88.234:80 | http://tracking.velosiaims.com/tracking/click?d=RyhMNkyKBW9a-xsO8SLm8rj2km7hytRjE8zHwfLAJJ0qayx7lWeGZ6W6F-xya81nMingJ-zH2LMwqHQ4HpbCiotoPzl6sGe3UlIbDG8AjeMqWTF8ZMZ2jtcUz-nz1vTeqnBhpWA5ruMs1LRrh6szhThITjonEA3OtX8xq3ARw1RXFaatNx8S_KoplYgoWzY32w2 | IE | html | 183 b | suspicious |
1976 | iexplore.exe | GET | 302 | 46.105.88.234:80 | http://tracking.velosiaims.com/tracking/click?d=RyhMNkyKBW9a-xsO8SLm8rj2km7hytRjE8zHwfLAJJ0qayx7lWeGZ6W6F-xya81nMingJ-zH2LMwqHQ4HpbCiotoPzl6sGe3UlIbDG8AjeMqWTF8ZMZ2jtcUz-nz1vTeqnBhpWA5ruMs1LRrh6szhThITjonEA3OtX8xq3ARw1RXFaatNx8S_KoplYgoWzY32w2 | IE | html | 183 b | suspicious |
1976 | iexplore.exe | GET | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
— | — | GET | 200 | 143.204.101.111:80 | http://s.ss2.us/r.crl | US | der | 434 b | whitelisted |
2608 | iexplore.exe | GET | 302 | 46.105.88.234:80 | http://tracking.velosiaims.com/tracking/click?d=-RSMZYZAWRIANYazplA_oppcqRxQrFrZiealz7hmEEGP8Ckm_sAoo3w2Z30tX-36ORxxknTMc2CYrjX7vL-mgv8gIfrGqnmrNS7vCdTQMv_fzqaxn0env732rB_-0ls1VDgY0r-SIihwg2codqXko3982XSMqUU5XRc5OfmbYhSne_fATM4bnkaDU_wb9kk_VhmNT1WptKacA4AJhyfOh-ppamg74ktXy8iIWQnVZpQ70 | IE | html | 219 b | suspicious |
1976 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
2020 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 7.68 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 46.105.88.234:80 | tracking.velosiaims.com | OVH SAS | IE | suspicious |
508 | iexplore.exe | 170.114.10.28:443 | us06web.zoom.us | — | US | unknown |
508 | iexplore.exe | 23.32.238.178:80 | ctldl.windowsupdate.com | XO Communications | US | suspicious |
1976 | iexplore.exe | 170.114.10.28:443 | us06web.zoom.us | — | US | unknown |
1976 | iexplore.exe | 104.16.148.64:443 | cdn.cookielaw.org | Cloudflare Inc | US | unknown |
1976 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2020 | iexplore.exe | 13.107.22.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
508 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
508 | iexplore.exe | 13.225.87.112:443 | static.ada.support | — | US | suspicious |
508 | iexplore.exe | 13.224.199.249:443 | us06st3.zoom.us | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
tracking.velosiaims.com |
| suspicious |
us06web.zoom.us |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
us06st3.zoom.us |
| suspicious |
us06st1.zoom.us |
| suspicious |
cdn.cookielaw.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET DNS Query for .to TLD |
3676 | iexplore.exe | A Network Trojan was detected | ET POLICY Possible External IP Lookup Domain Observed in SNI (ipinfo. io) |
3676 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY Possible External IP Lookup SSL Cert Observed (ipinfo.io) |
— | — | Potentially Bad Traffic | ET DNS Query for .to TLD |
2608 | iexplore.exe | A Network Trojan was detected | ET POLICY Possible External IP Lookup Domain Observed in SNI (ipinfo. io) |
2608 | iexplore.exe | A Network Trojan was detected | ET POLICY Possible External IP Lookup Domain Observed in SNI (ipinfo. io) |
2608 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY Possible External IP Lookup SSL Cert Observed (ipinfo.io) |
2608 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY Possible External IP Lookup SSL Cert Observed (ipinfo.io) |
— | — | Potentially Bad Traffic | ET DNS Query for .to TLD |
3660 | iexplore.exe | A Network Trojan was detected | ET POLICY Possible External IP Lookup Domain Observed in SNI (ipinfo. io) |