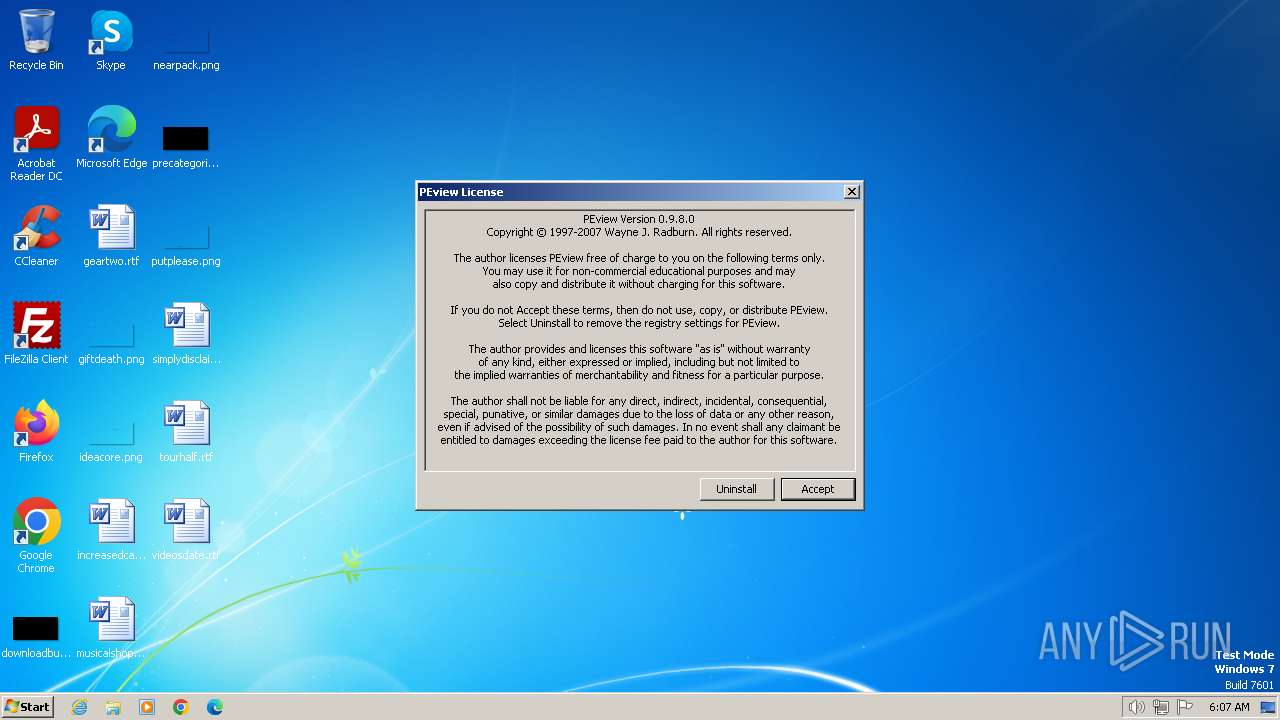
| File name: | PEview.exe |
| Full analysis: | https://app.any.run/tasks/34224805-04da-4d28-afc8-32b10c1848ae |
| Verdict: | Malicious activity |
| Analysis date: | February 14, 2024, 06:07:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | EC63E8BE0717BD92C0FFBF7A21749A54 |
| SHA1: | 285D712E45D0E20CBD3451F2FA28D922DD248EFB |
| SHA256: | AE40E285E70633F33D77AB3BE3DD32A03DD272B3A4298E4FFF5DE5A3A598D831 |
| SSDEEP: | 1536:j1G+oinWc8W6+DiLoXRxET/t756jDslnY8fURUIjc0dK6yP7zc7XrBK:jpoinzKNgD5R1yDKrBK |
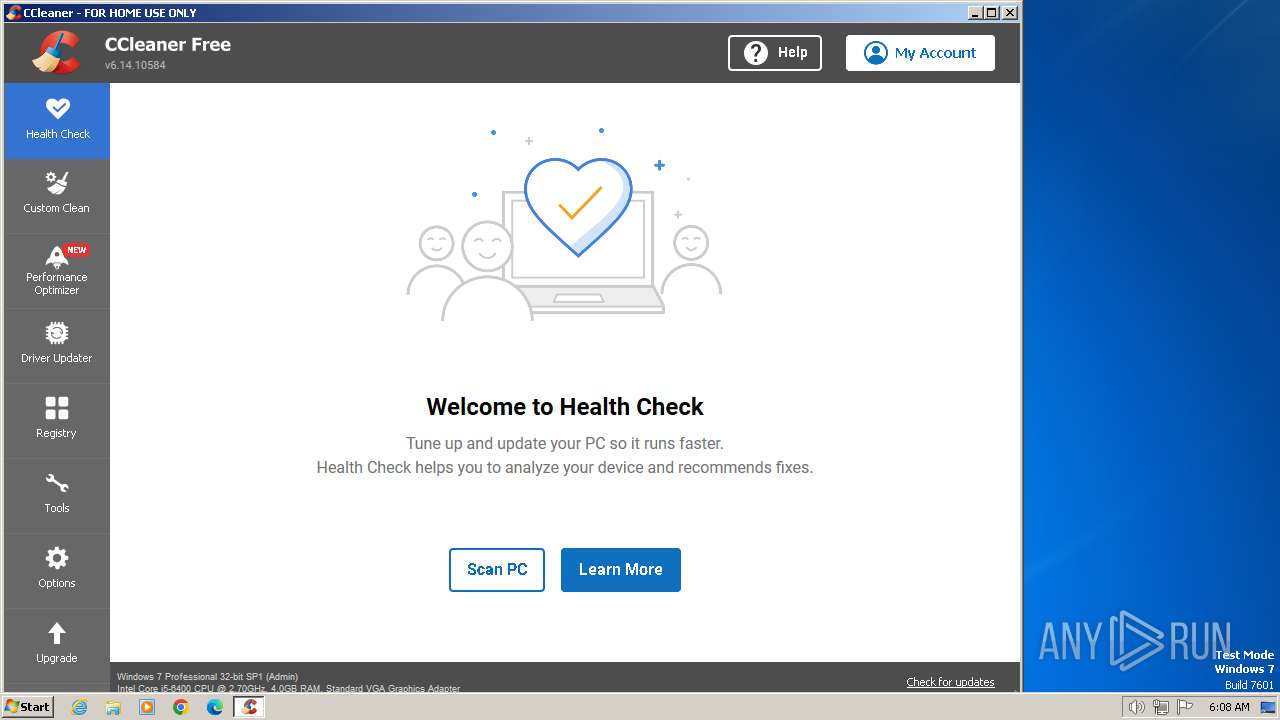
MALICIOUS
Drops the executable file immediately after the start
- PEview.exe (PID: 3656)
- CCleaner.exe (PID: 3960)
Actions looks like stealing of personal data
- CCleaner.exe (PID: 3960)
Steals credentials from Web Browsers
- CCleaner.exe (PID: 3960)
SUSPICIOUS
The process executes via Task Scheduler
- CCleaner.exe (PID: 3960)
Reads Internet Explorer settings
- CCleaner.exe (PID: 3960)
Executable content was dropped or overwritten
- CCleaner.exe (PID: 3960)
Reads security settings of Internet Explorer
- CCleaner.exe (PID: 3960)
Reads the date of Windows installation
- CCleaner.exe (PID: 3960)
Searches for installed software
- CCleaner.exe (PID: 3960)
Reads the Internet Settings
- CCleaner.exe (PID: 3960)
Reads Microsoft Outlook installation path
- CCleaner.exe (PID: 3960)
Checks Windows Trust Settings
- CCleaner.exe (PID: 3960)
Reads settings of System Certificates
- CCleaner.exe (PID: 3960)
INFO
Reads the machine GUID from the registry
- PEview.exe (PID: 3656)
- CCleaner.exe (PID: 3960)
Checks supported languages
- PEview.exe (PID: 3656)
- CCleaner.exe (PID: 3960)
- CCleaner.exe (PID: 1696)
Reads the computer name
- PEview.exe (PID: 3656)
- CCleaner.exe (PID: 3960)
- CCleaner.exe (PID: 1696)
Reads Environment values
- CCleaner.exe (PID: 3960)
- CCleaner.exe (PID: 1696)
Manual execution by a user
- CCleaner.exe (PID: 1696)
- chrome.exe (PID: 2576)
- msedge.exe (PID: 3364)
Reads product name
- CCleaner.exe (PID: 3960)
Creates files in the program directory
- CCleaner.exe (PID: 3960)
Reads CPU info
- CCleaner.exe (PID: 3960)
Reads the software policy settings
- CCleaner.exe (PID: 3960)
Checks proxy server information
- CCleaner.exe (PID: 3960)
Creates files or folders in the user directory
- CCleaner.exe (PID: 3960)
Application launched itself
- chrome.exe (PID: 2576)
- msedge.exe (PID: 3364)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
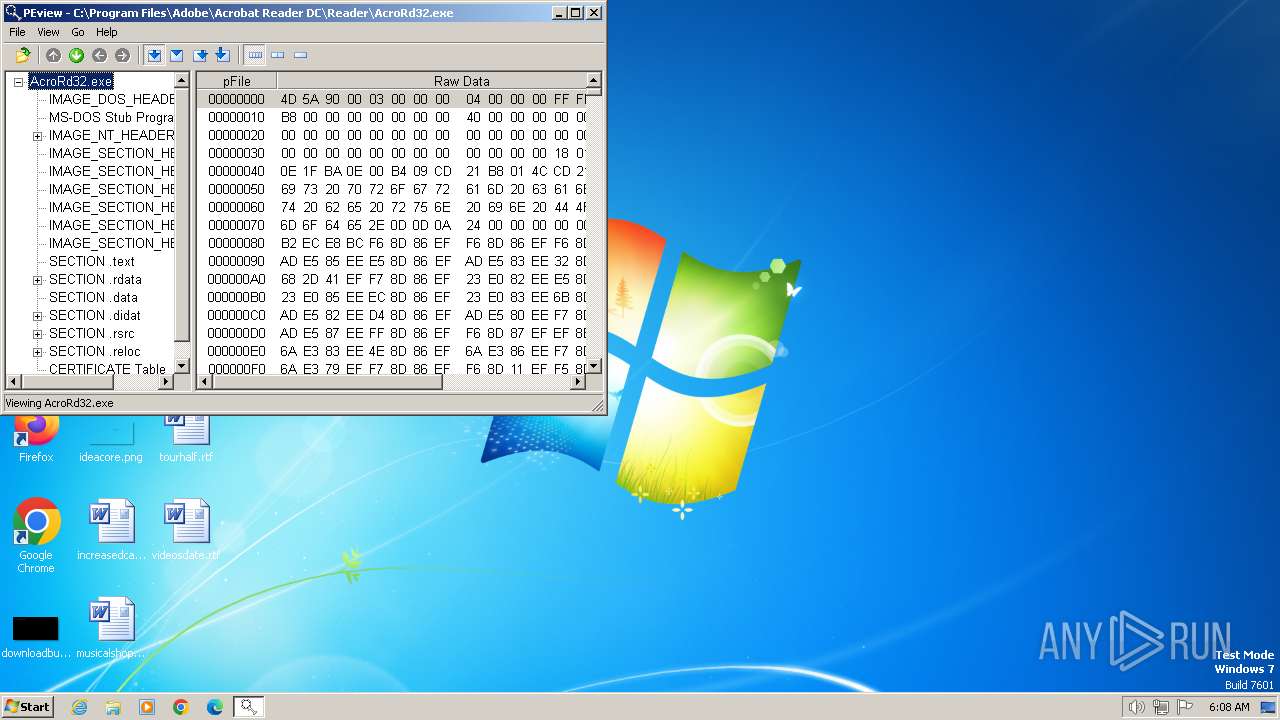
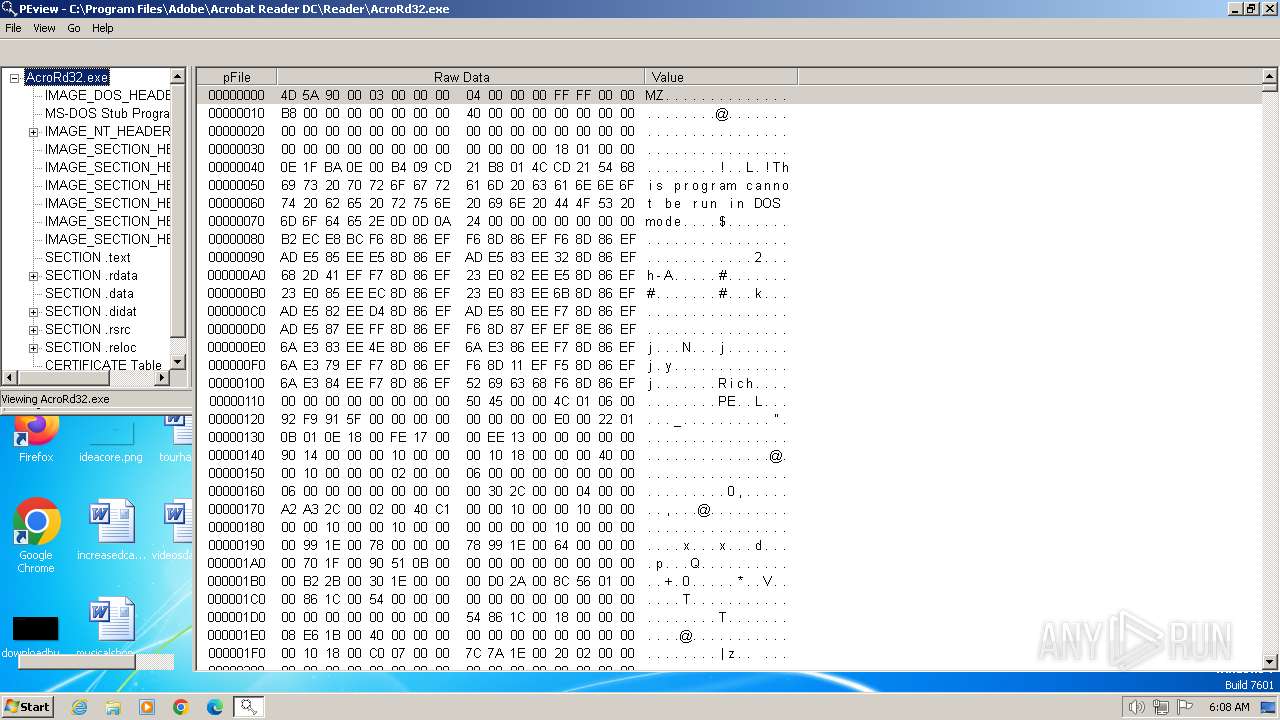
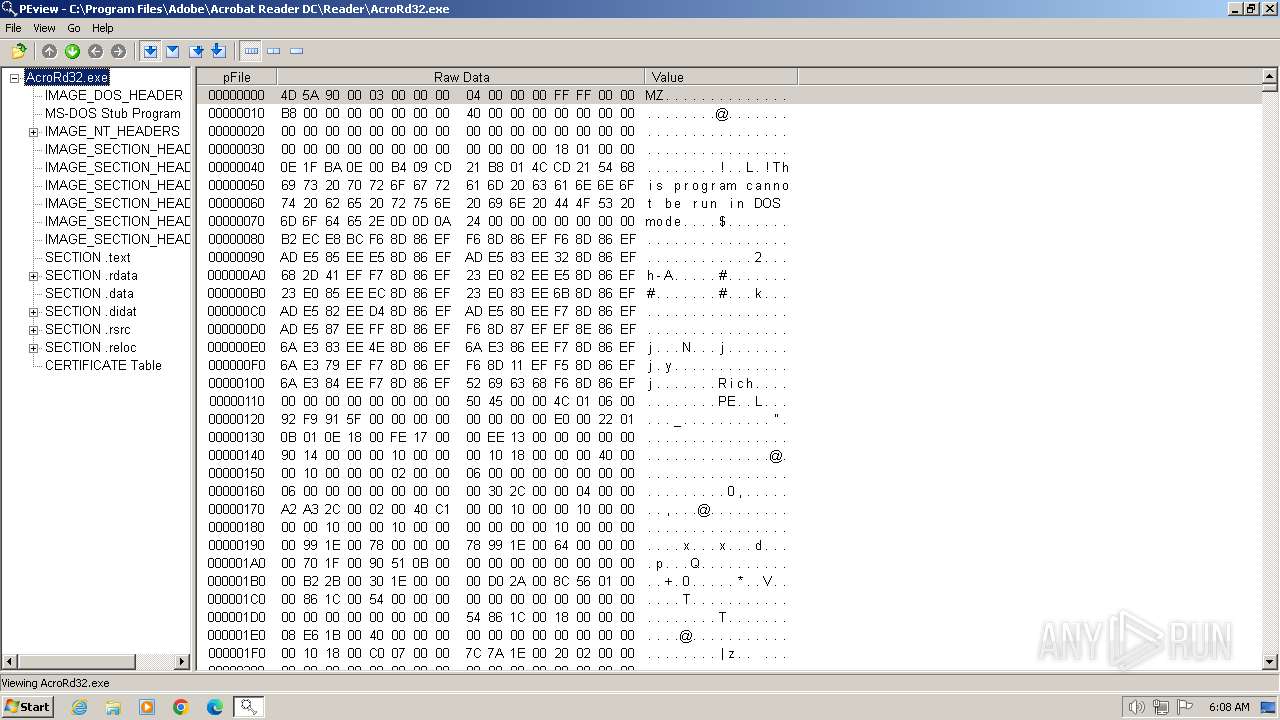
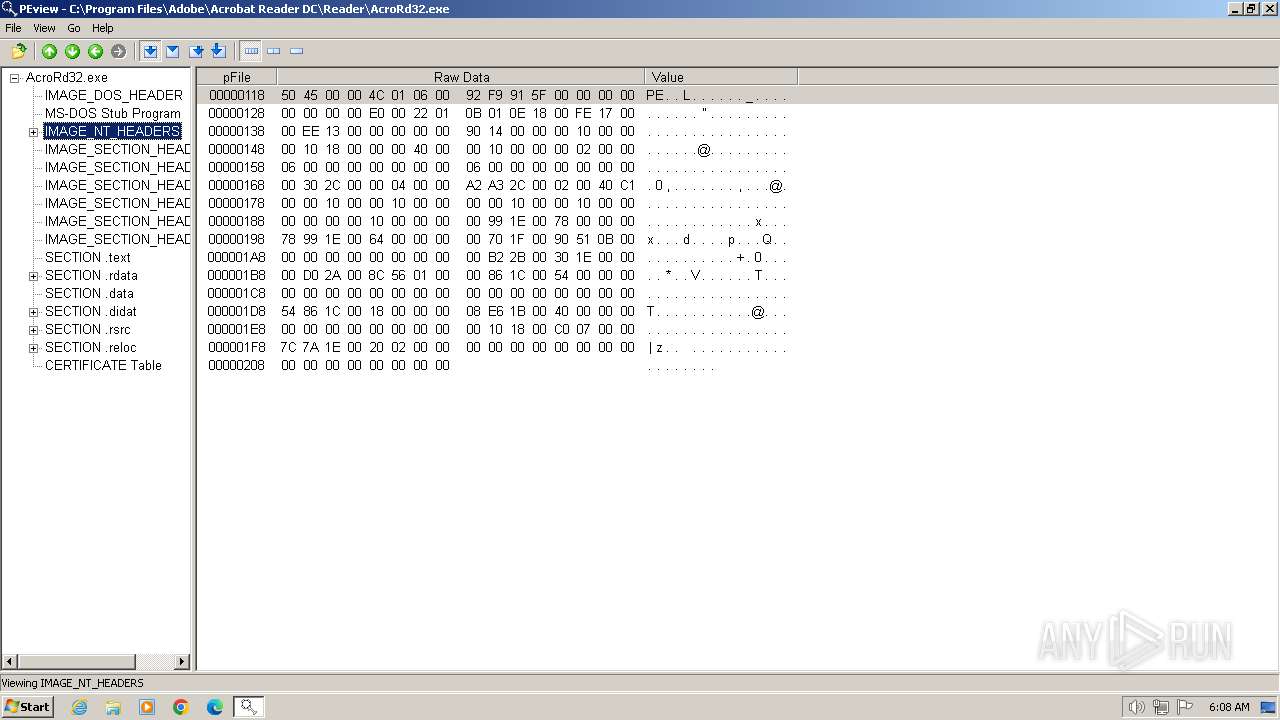
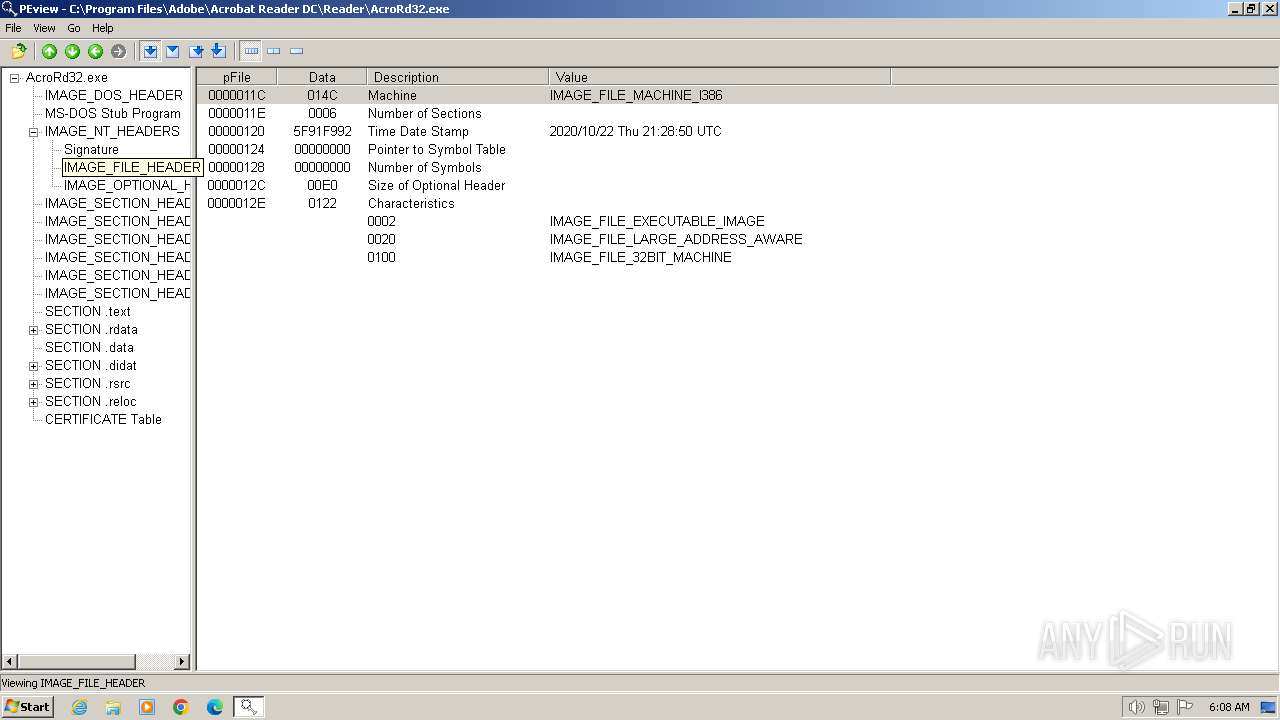
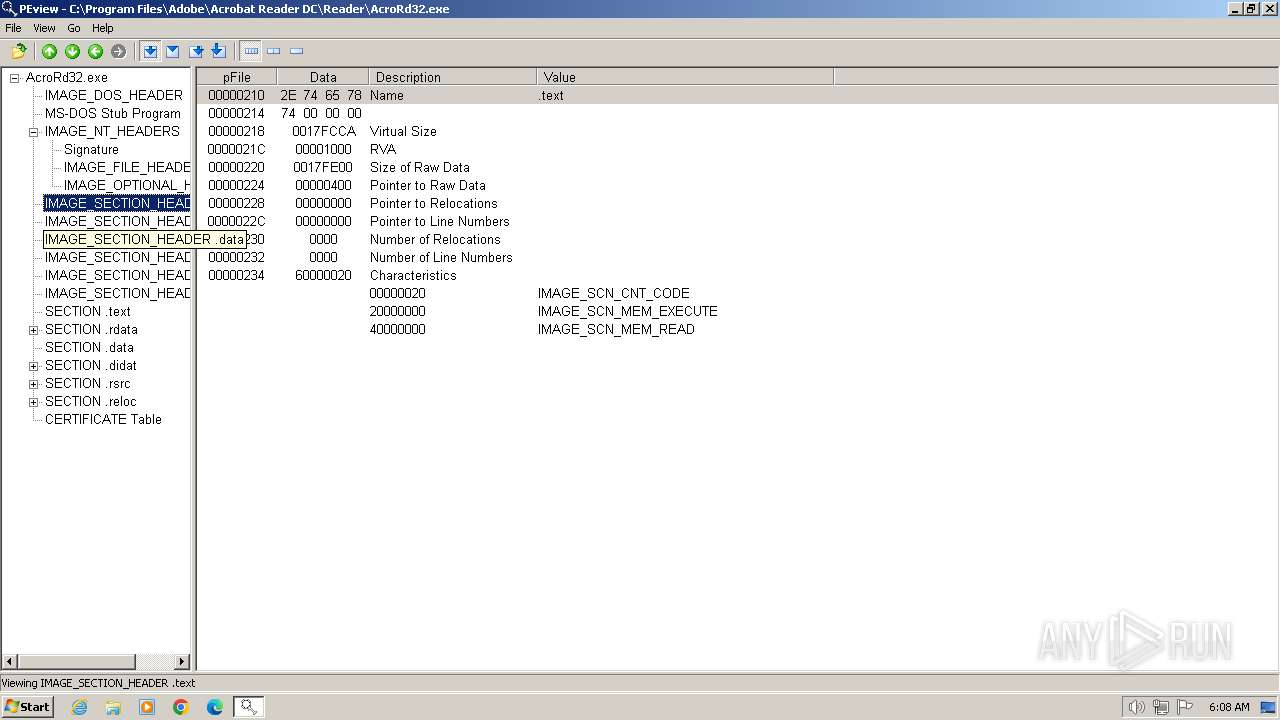
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2011:05:16 23:18:47+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 0.38 |
| CodeSize: | 33280 |
| InitializedDataSize: | 33280 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.9.9.0 |
| ProductVersionNumber: | 0.9.9.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Wayne J. Radburn |
| FileDescription: | PE/COFF File Viewer |
| FileVersion: | 0.9.9.0 |
| InternalName: | PEview |
| LegalCopyright: | Copyright© 1997-2011 Wayne J. Radburn |
| OriginalFileName: | PEview.exe |
| ProductName: | PEview |
| ProductVersion: | 0.9.9.0 |
Total processes
63
Monitored processes
24
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --mojo-platform-channel-handle=3284 --field-trial-handle=1168,i,16879185172505823380,9131545691263175881,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 752 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1268 --field-trial-handle=1168,i,16879185172505823380,9131545691263175881,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 884 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1284 --field-trial-handle=1308,i,15633692695018504415,5296227869330975937,131072 /prefetch:2 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 984 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --first-renderer-process --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2116 --field-trial-handle=1168,i,16879185172505823380,9131545691263175881,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1384 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1548 --field-trial-handle=1308,i,15633692695018504415,5296227869330975937,131072 /prefetch:3 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3748 --field-trial-handle=1168,i,16879185172505823380,9131545691263175881,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1692 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1408 --field-trial-handle=1308,i,15633692695018504415,5296227869330975937,131072 /prefetch:2 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
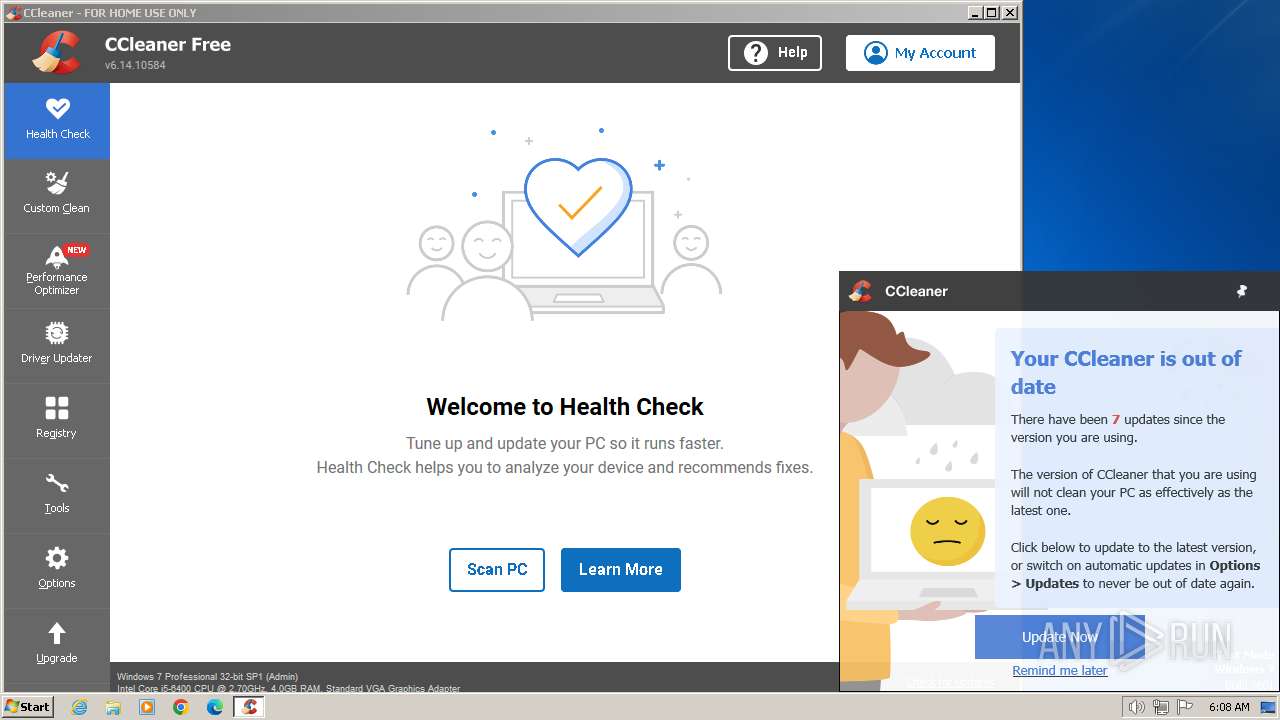
| 1696 | "C:\Program Files\CCleaner\CCleaner.exe" | C:\Program Files\CCleaner\CCleaner.exe | — | explorer.exe | |||||||||||
User: admin Company: Piriform Software Ltd Integrity Level: MEDIUM Description: CCleaner Exit code: 0 Version: 6.14.0.10584 Modules
| |||||||||||||||
| 2024 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1328 --field-trial-handle=1168,i,16879185172505823380,9131545691263175881,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 2096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6bcd8b38,0x6bcd8b48,0x6bcd8b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
28 893
Read events
28 461
Write events
343
Delete events
89
Modification events
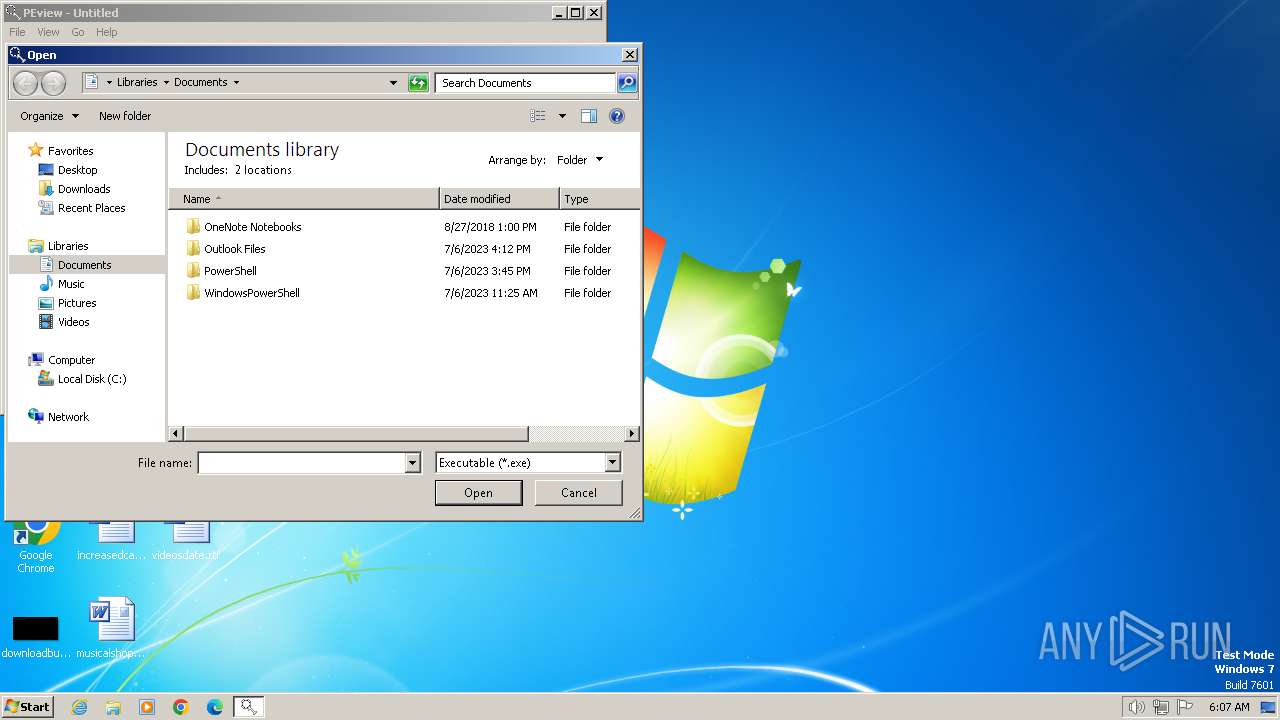
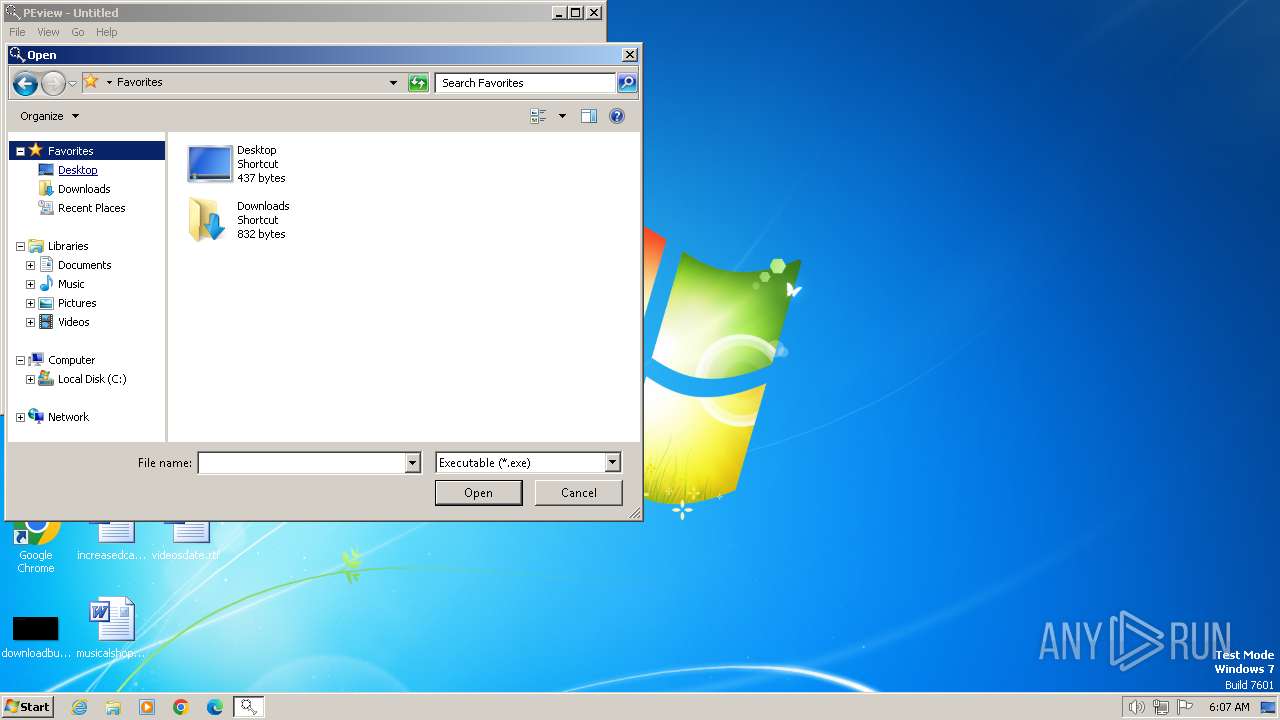
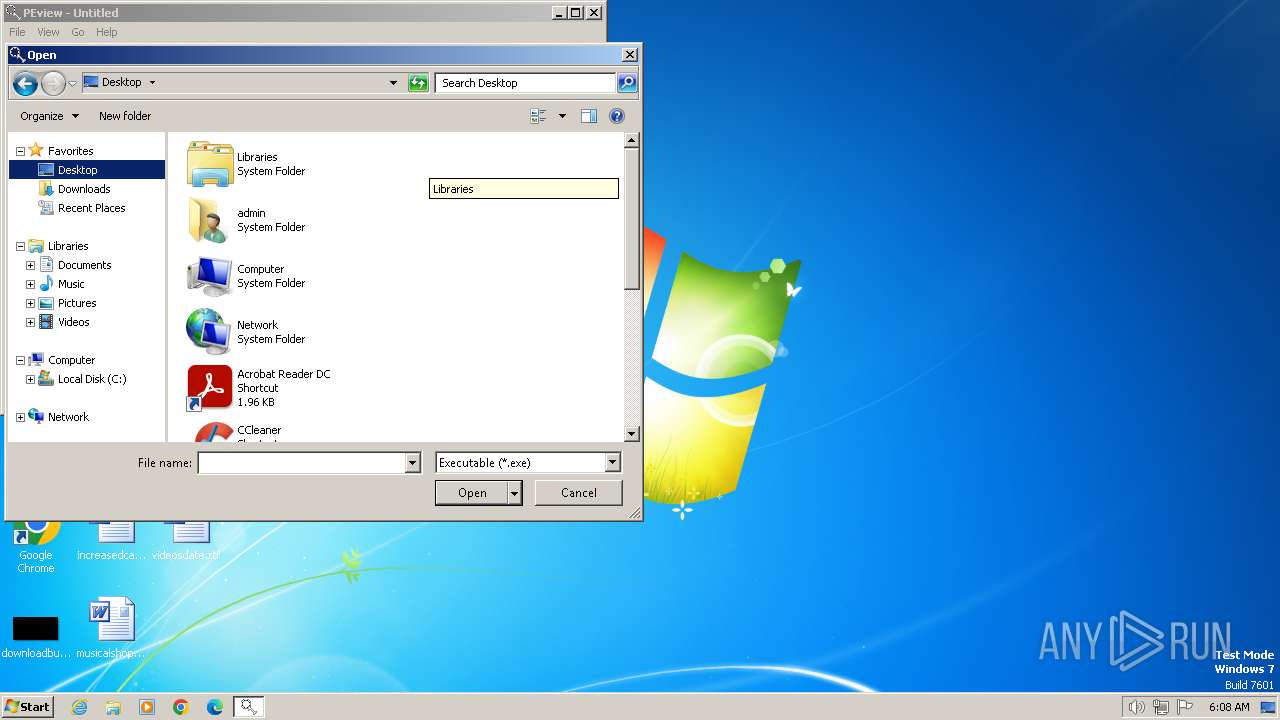
| (PID) Process: | (3656) PEview.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (3656) PEview.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 02000000070000000100000006000000000000000B0000000C0000000D0000000A0000000900000008000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (3656) PEview.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_FolderType |
Value: {FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9} | |||
| (PID) Process: | (3656) PEview.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewID |
Value: {82BA0782-5B7A-4569-B5D7-EC83085F08CC} | |||
| (PID) Process: | (3656) PEview.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewVersion |
Value: 0 | |||
| (PID) Process: | (3656) PEview.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3656) PEview.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\AllFolders\ComDlg\{FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9}\{82BA0782-5B7A-4569-B5D7-EC83085F08CC} |
| Operation: | write | Name: | Mode |
Value: 4 | |||
| (PID) Process: | (3656) PEview.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\AllFolders\ComDlg\{FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9}\{82BA0782-5B7A-4569-B5D7-EC83085F08CC} |
| Operation: | write | Name: | LogicalViewMode |
Value: 1 | |||
| (PID) Process: | (3656) PEview.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\AllFolders\ComDlg\{FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9}\{82BA0782-5B7A-4569-B5D7-EC83085F08CC} |
| Operation: | write | Name: | FFlags |
Value: | |||
| (PID) Process: | (3656) PEview.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\AllFolders\ComDlg\{FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9}\{82BA0782-5B7A-4569-B5D7-EC83085F08CC} |
| Operation: | write | Name: | IconSize |
Value: 16 | |||
Executable files
14
Suspicious files
164
Text files
139
Unknown types
127
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3960 | CCleaner.exe | C:\Program Files\CCleaner\gcapi_dll.dll | executable | |
MD5:F637D5D3C3A60FDDB5DD397556FE9B1D | SHA256:641B843CB6EE7538EC267212694C9EF0616B9AC9AB14A0ABD7CF020678D50B02 | |||
| 3960 | CCleaner.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | binary | |
MD5:2C21A1AA7C3B92A2FD2760F8DBCEDB73 | SHA256:A7CDE633BB9BBF2FE95CDE000EFE90F74C64ED4BBA65D16934710FF4224F9489 | |||
| 3960 | CCleaner.exe | C:\Program Files\CCleaner\gcapi_17078909053960.dll | executable | |
MD5:F637D5D3C3A60FDDB5DD397556FE9B1D | SHA256:641B843CB6EE7538EC267212694C9EF0616B9AC9AB14A0ABD7CF020678D50B02 | |||
| 3960 | CCleaner.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\X7OWOPGV8DGSKJ2K8KJN.temp | binary | |
MD5:4CD5742C436B5E1F55606FF262436888 | SHA256:549CC0B9945E6FCF768901C3D7DEBDB92994E641A87396BE13267E9848210CB9 | |||
| 3960 | CCleaner.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\07AA081570CE8F7F562E5C6477BAD20E_7881D466B78F0273455F202AEF93FB25 | der | |
MD5:8681D29F9F43B644747003EDB36A3153 | SHA256:34492FBB376AC76407A450EFD5234358215F4D5A61541FA2E0576252EA026B76 | |||
| 3960 | CCleaner.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\8C261816D8553C1624AEA5E26C220698_436D4E04BAA47A81072A1BF203324AE4 | binary | |
MD5:49366FD659B679C5451DC85E568E625B | SHA256:F2DE559C1613DCFC12A4950576476A2841A1216652FB1072A8AB627AB0E9DC76 | |||
| 3960 | CCleaner.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\JSVGB7KO.txt | ini | |
MD5:C9AF4D45EE80F6D77AD1003A600B7DCE | SHA256:A8310CE164B1707EAC4492B8F1B9DBDB08130F714F0DD5C4A75E6FC06BC947CA | |||
| 3960 | CCleaner.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\11FCEE8B05D544B1FF0953F6AB6EBAEF_BDCF2E8313FA7424AD8D56EE1EDC8B19 | der | |
MD5:4AB072A34BFAE8624BBE3058F30F86CE | SHA256:0F18140D013527BFB7D770AA8D94D7EE99A10984E801973E78D84F5198798AB1 | |||
| 3960 | CCleaner.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\07AA081570CE8F7F562E5C6477BAD20E_7881D466B78F0273455F202AEF93FB25 | binary | |
MD5:7E6CDC5DD501CBC11BE560582143A0A7 | SHA256:932BCDFE5760E29264E229B02BFC0B9F59EA91BF6E82EA39D9143E58380F8E32 | |||
| 3960 | CCleaner.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\11FCEE8B05D544B1FF0953F6AB6EBAEF_BDCF2E8313FA7424AD8D56EE1EDC8B19 | binary | |
MD5:DA4997CF63671A9E0458A96840E8FFD0 | SHA256:8631EA4A27D8C32035B071A99717DD219E326BD6C75D4D7DDDF0A99EFBD9B19A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
54
DNS requests
76
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3960 | CCleaner.exe | GET | 200 | 2.16.100.160:80 | http://ncc.avast.com/ncc.txt | unknown | text | 26 b | unknown |
3960 | CCleaner.exe | GET | 304 | 95.101.54.203:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?91e1ffede328701a | unknown | — | — | unknown |
3960 | CCleaner.exe | GET | 304 | 95.101.54.112:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?742c6b6cf3bb2580 | unknown | — | — | unknown |
3960 | CCleaner.exe | GET | 304 | 95.101.54.203:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?cc825aa46d2bef7a | unknown | — | — | unknown |
3960 | CCleaner.exe | GET | 304 | 95.101.54.203:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?1ffe4c71871ad2f0 | unknown | — | — | unknown |
3960 | CCleaner.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | unknown | binary | 471 b | unknown |
3960 | CCleaner.exe | GET | 200 | 142.250.186.99:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | binary | 1.41 Kb | unknown |
3960 | CCleaner.exe | GET | 200 | 142.250.186.99:80 | http://ocsp.pki.goog/s/gts1d4/dKa2DF3Ws7g/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBSMBFDqU0NJQdZdEGU3bkhj0FoRrQQUJeIYDrJXkZQq5dRdhpCD3lOzuJICEQCirF%2F66XssownTCQRm1ZB%2F | unknown | binary | 472 b | unknown |
3960 | CCleaner.exe | GET | 200 | 142.250.186.99:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIAjrICMzZli2TN25s%3D | unknown | binary | 724 b | unknown |
3960 | CCleaner.exe | GET | 200 | 142.250.186.99:80 | http://ocsp.pki.goog/s/gts1d4/NR-xsrnkFN0/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBSMBFDqU0NJQdZdEGU3bkhj0FoRrQQUJeIYDrJXkZQq5dRdhpCD3lOzuJICEQDy8%2F016576jRBISHseO2T7 | unknown | binary | 472 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3960 | CCleaner.exe | 2.16.100.160:80 | ncc.avast.com | Akamai International B.V. | DE | whitelisted |
3960 | CCleaner.exe | 34.117.223.223:443 | analytics.ff.avast.com | GOOGLE-CLOUD-PLATFORM | US | unknown |
3960 | CCleaner.exe | 34.111.24.1:443 | ipm-provider.ff.avast.com | GOOGLE | US | unknown |
3960 | CCleaner.exe | 34.160.176.28:443 | shepherd.ff.avast.com | GOOGLE | US | unknown |
3960 | CCleaner.exe | 23.206.209.82:443 | www.ccleaner.com | AKAMAI-AS | DE | unknown |
3960 | CCleaner.exe | 34.149.149.62:443 | ip-info.ff.avast.com | GOOGLE | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ncc.avast.com |
| whitelisted |
analytics.ff.avast.com |
| whitelisted |
www.ccleaner.com |
| whitelisted |
ipm-provider.ff.avast.com |
| whitelisted |
shepherd.ff.avast.com |
| whitelisted |
ip-info.ff.avast.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
ipmcdn.avast.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Misc activity | ET INFO External IP Lookup Service in DNS Query (ip-info .ff .avast .com) |
3960 | CCleaner.exe | Misc activity | ET INFO Observed External IP Lookup Domain (ip-info .ff .avast .com) in TLS SNI |
Process | Message |
|---|---|
CCleaner.exe | [2024-02-14 06:08:25.215] [error ] [settings ] [ 3960: 4004] [6000C4: 356] Failed to get program directory
Exception: Unable to determine program folder of product 'piriform-cc'!
Code: 0x000000c0 (192)
|
CCleaner.exe | Failed to open log file 'C:\Program Files\CCleaner' |
CCleaner.exe | OnLanguage - en
|
CCleaner.exe | [2024-02-14 06:08:25.903] [error ] [settings ] [ 3960: 2064] [9434E9: 359] Failed to get program directory
Exception: Unable to determine program folder of product 'piriform-cc'!
Code: 0x000000c0 (192)
|
CCleaner.exe | [2024-02-14 06:08:25.918] [error ] [Burger ] [ 3960: 2064] [FDA25D: 244] [23.1.806.0] [BurgerReporter.cpp] [244] asw::standalone_svc::BurgerReporter::BurgerSwitch: Could not read property BURGER_SETTINGS_PANCAKE_HOSTNAME (0x00000003)
|
CCleaner.exe | [2024-02-14 06:08:25.918] [error ] [Burger ] [ 3960: 2064] [FDA25D: 244] [23.1.806.0] [BurgerReporter.cpp] [244] asw::standalone_svc::BurgerReporter::BurgerSwitch: Could not read property BURGER_SETTINGS_PANCAKE_HOSTNAME (0x00000003)
|
CCleaner.exe | startCheckingLicense()
|
CCleaner.exe | OnLanguage - en
|
CCleaner.exe | OnLanguage - en
|
CCleaner.exe | OnLanguage - en
|