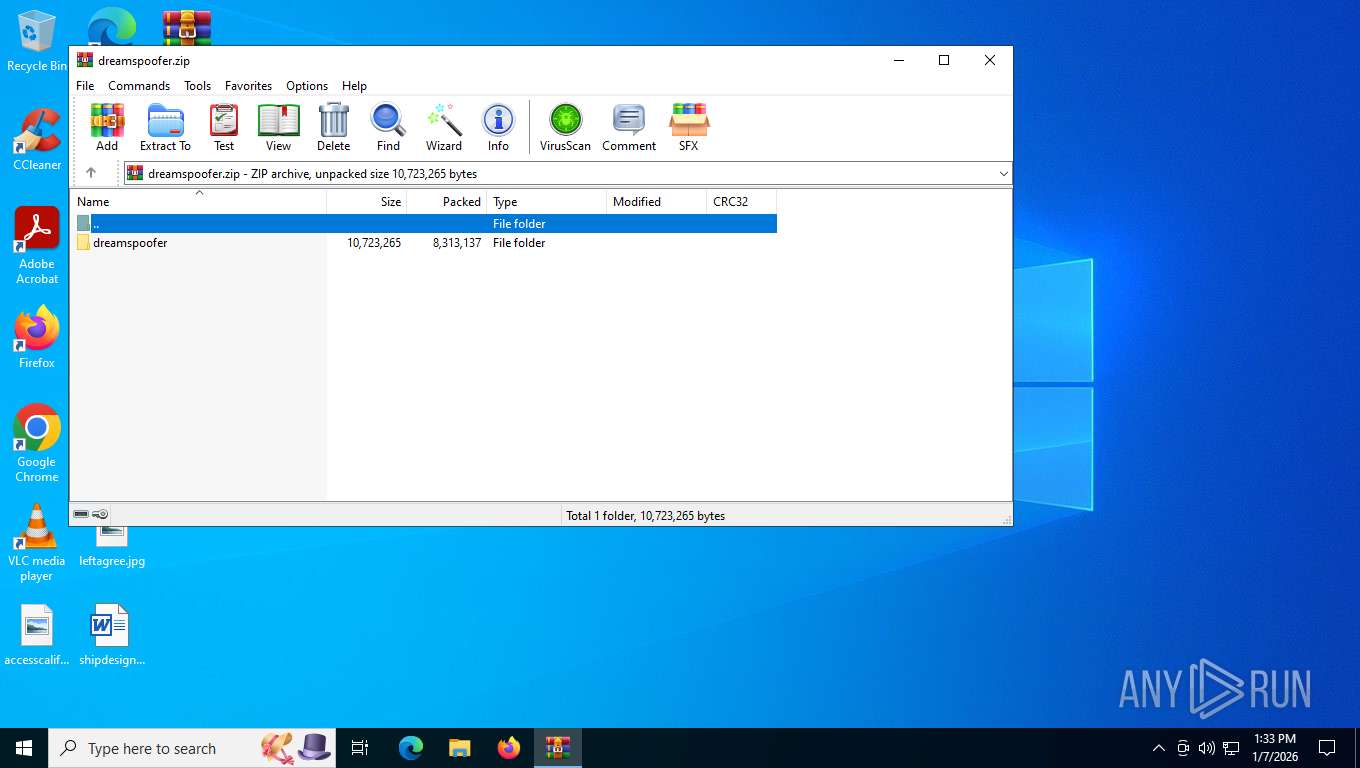
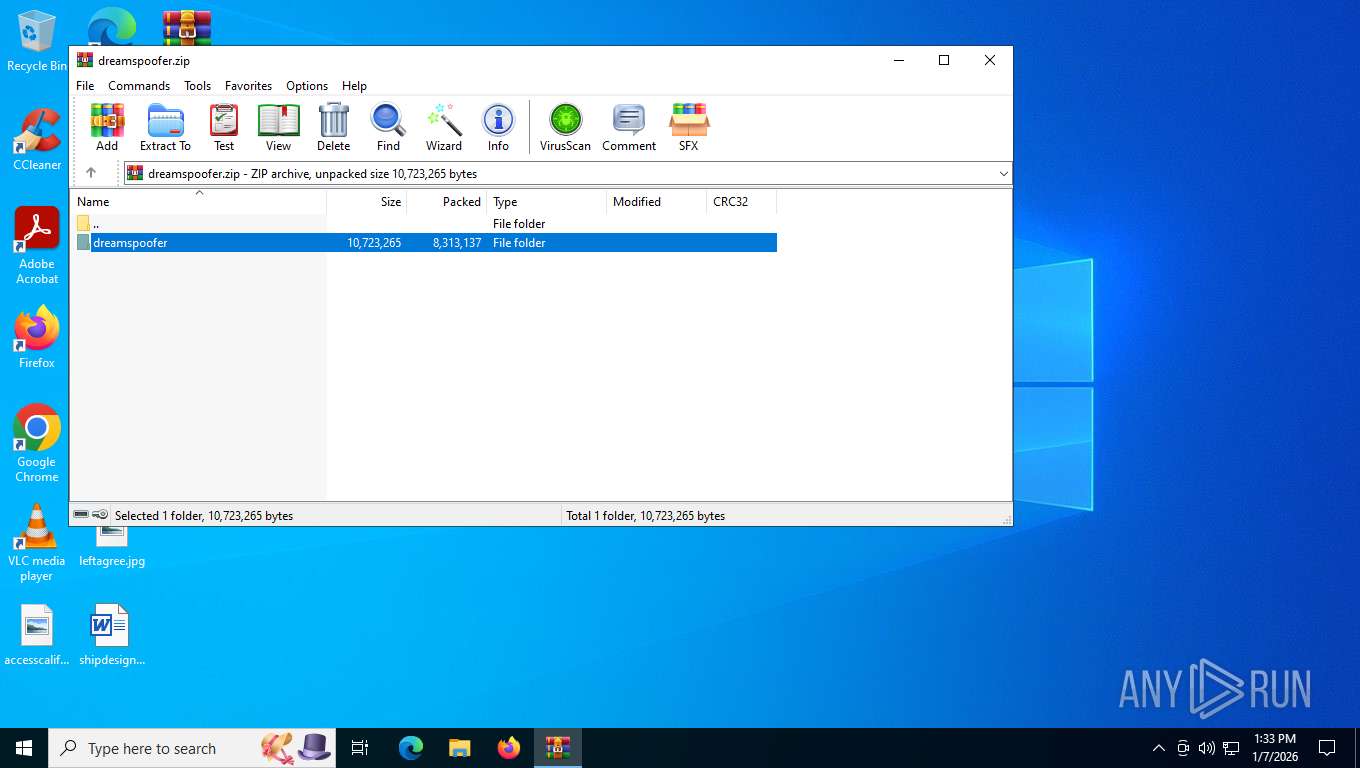
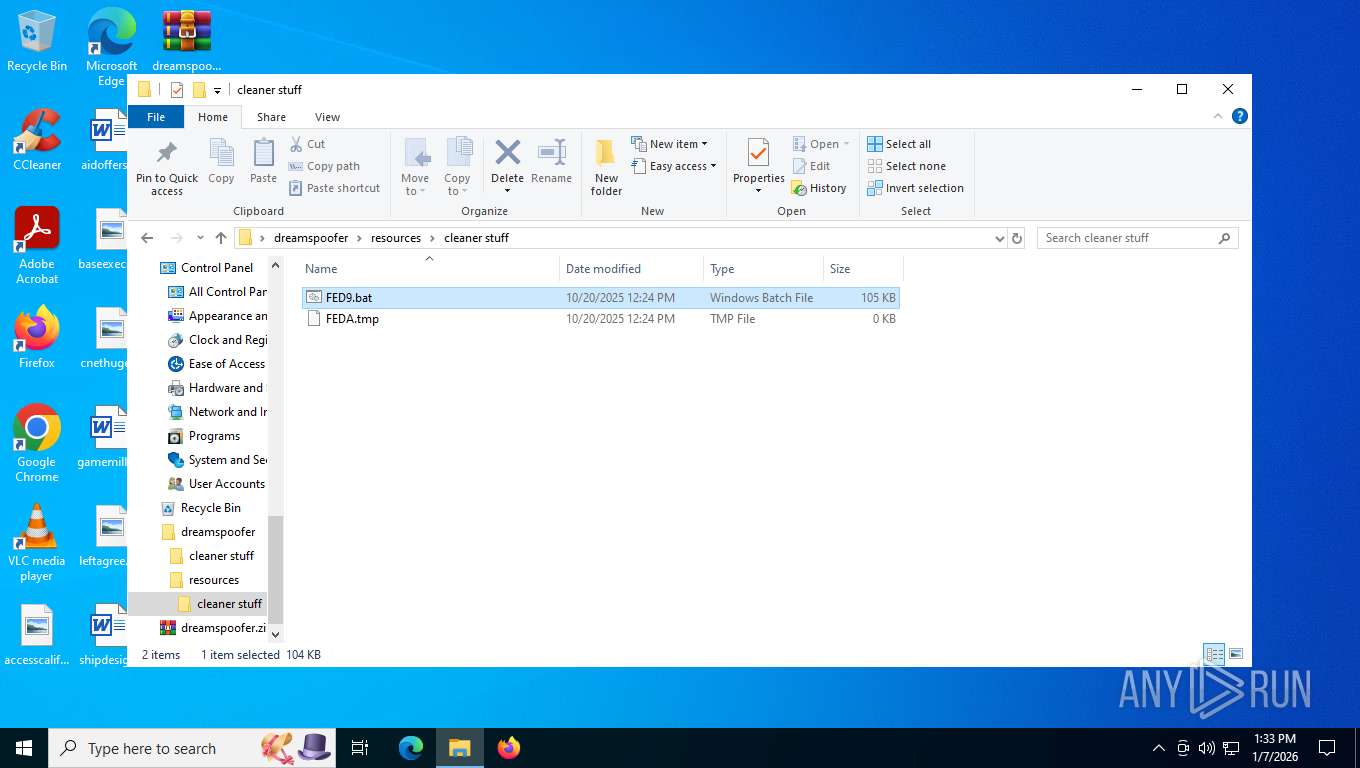
| File name: | dreamspoofer.zip |
| Full analysis: | https://app.any.run/tasks/b8fbb673-fb1e-44e6-830f-0f035695544d |
| Verdict: | Malicious activity |
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | January 07, 2026, 18:33:09 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
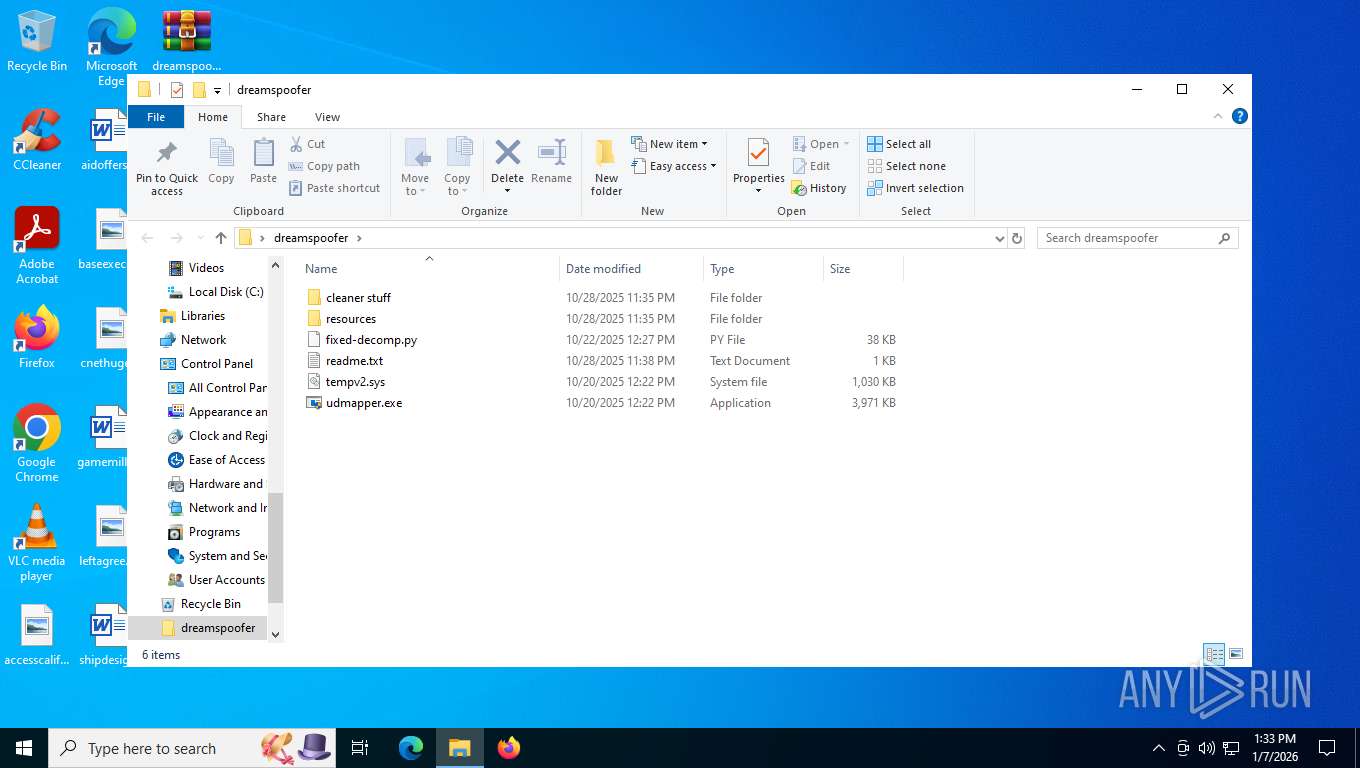
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | 34934994770750CFDA9E7A49795B931F |
| SHA1: | 04DA59BEE72B155B2B1C36F56314B91BDAAB7C8D |
| SHA256: | AE3EC63290A5B41C097C00B5904D024F00A1ED8DCA921E2D0CC965808688FF6E |
| SSDEEP: | 98304:AiM182Ru1IgWUVTgXD1Keqezp3Oht7w6R6hF35c7OR3a3kLX7Xo0Buppca8Z0Adu:AVOhOc |
MALICIOUS
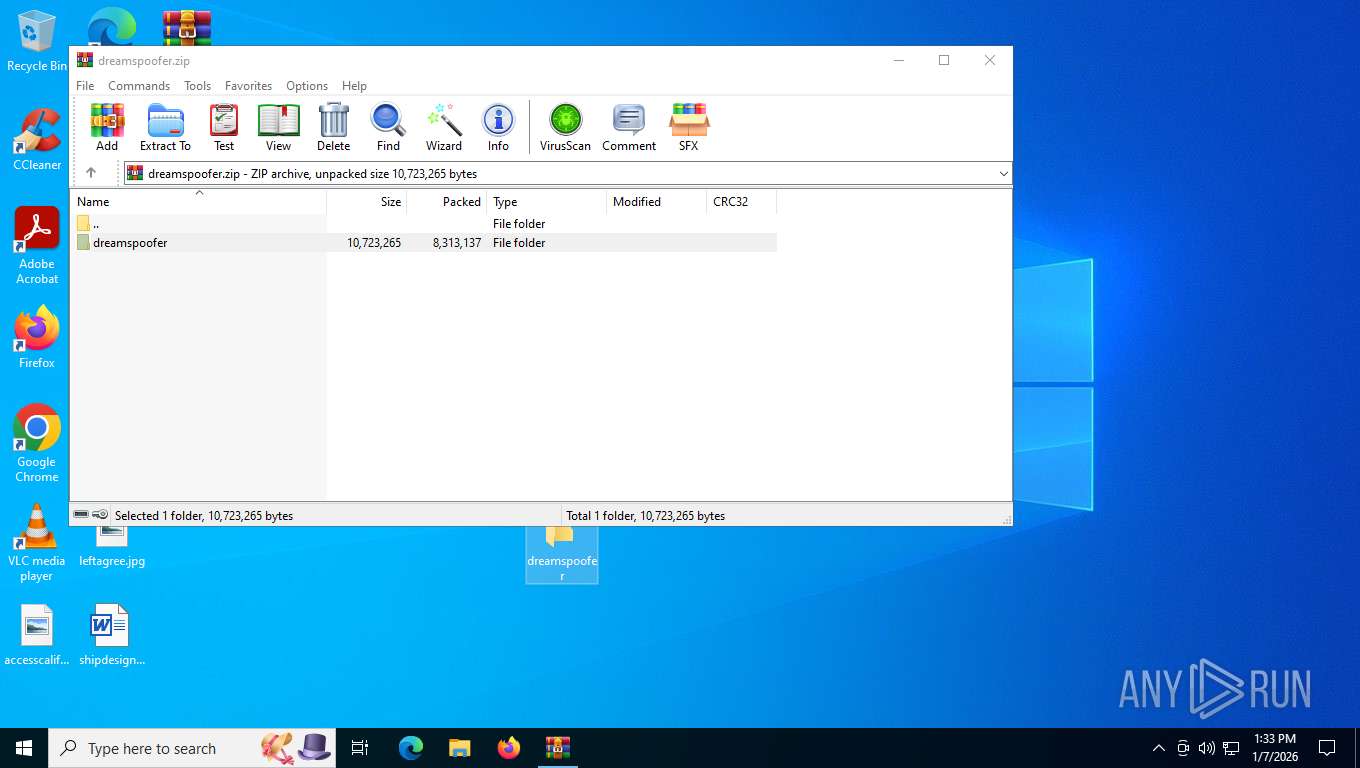
Generic archive extractor
- WinRAR.exe (PID: 7476)
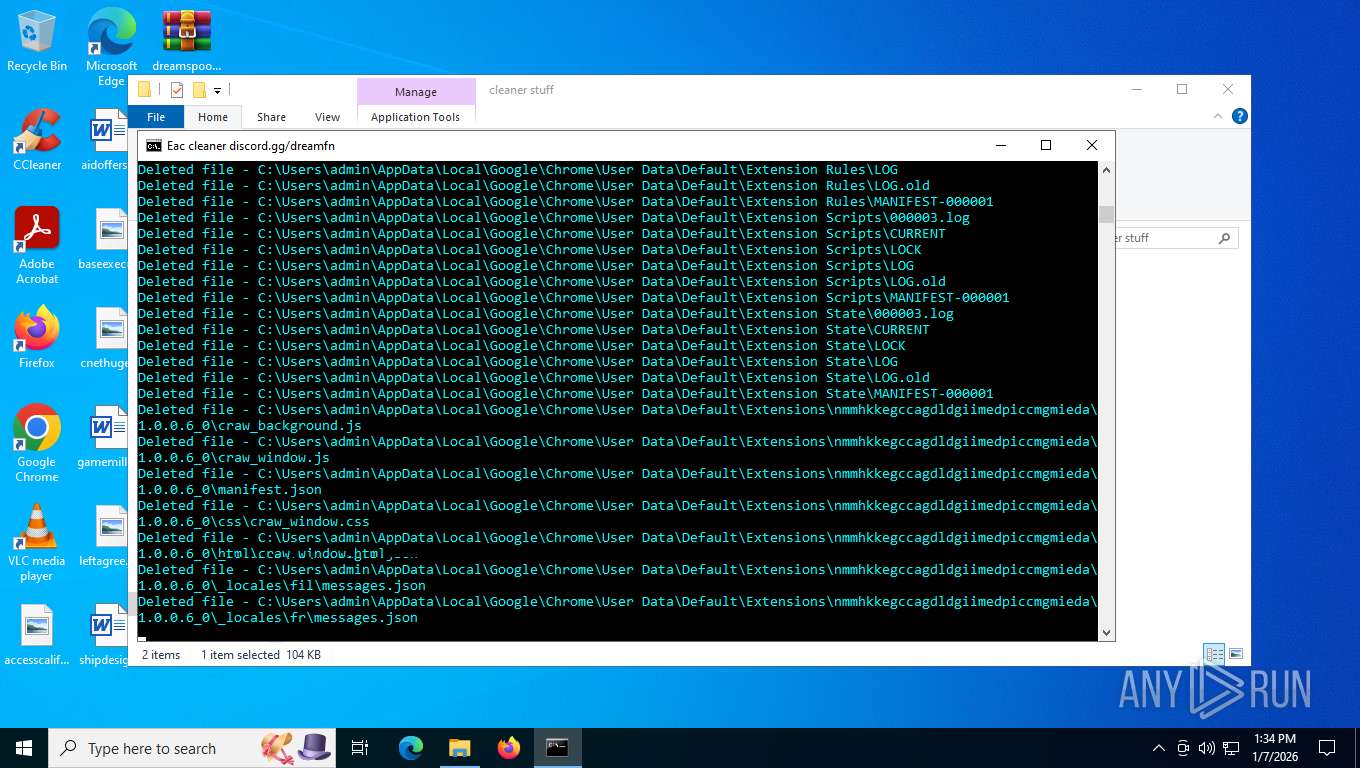
Steals credentials from Web Browsers
- cmd.exe (PID: 8044)
Starts CertUtil for downloading files
- cmd.exe (PID: 8044)
SUSPICIOUS
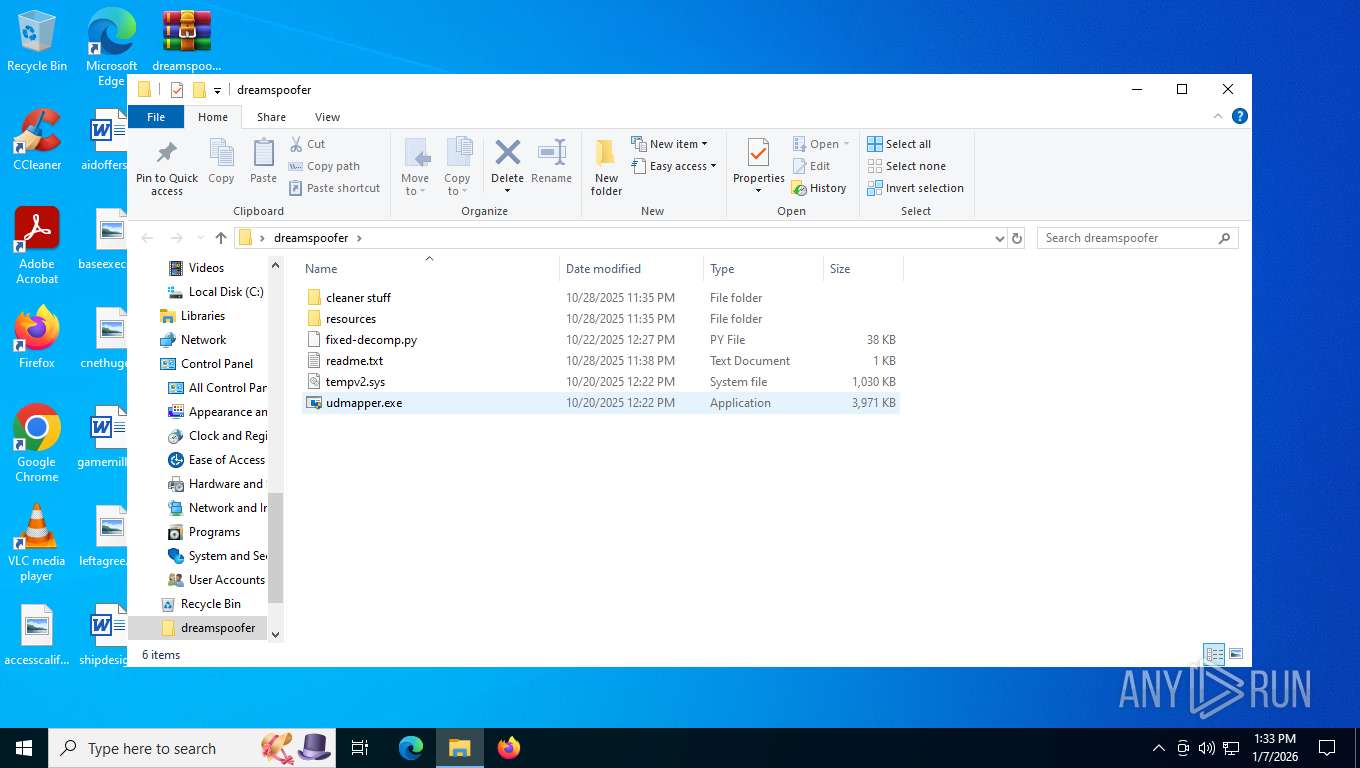
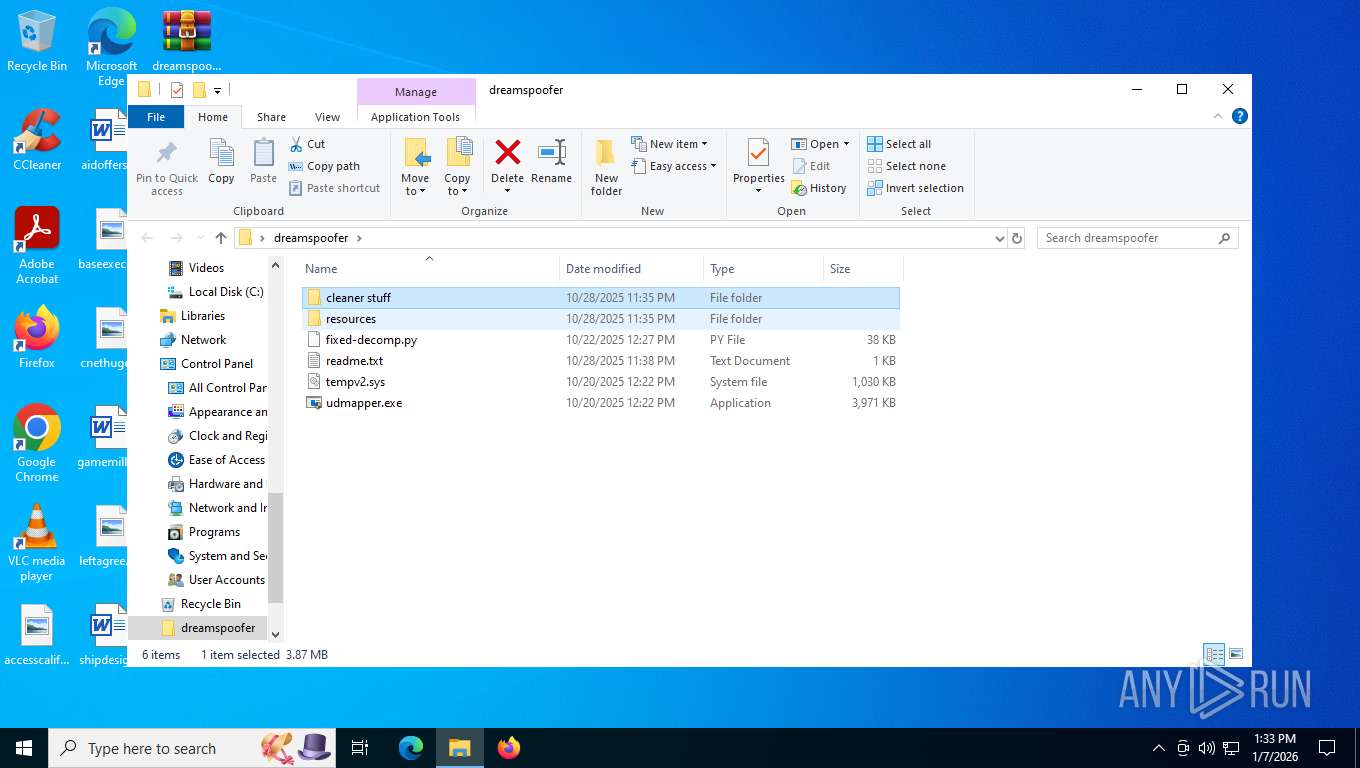
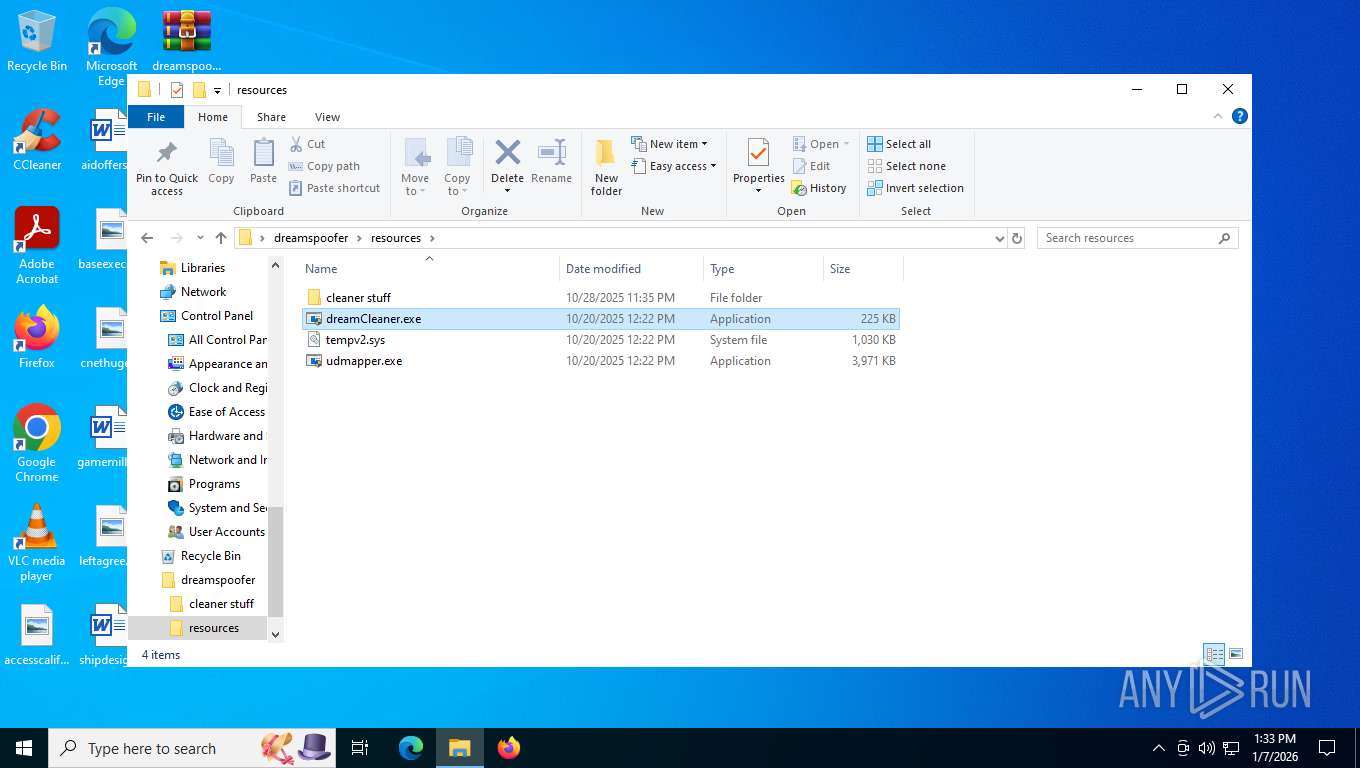
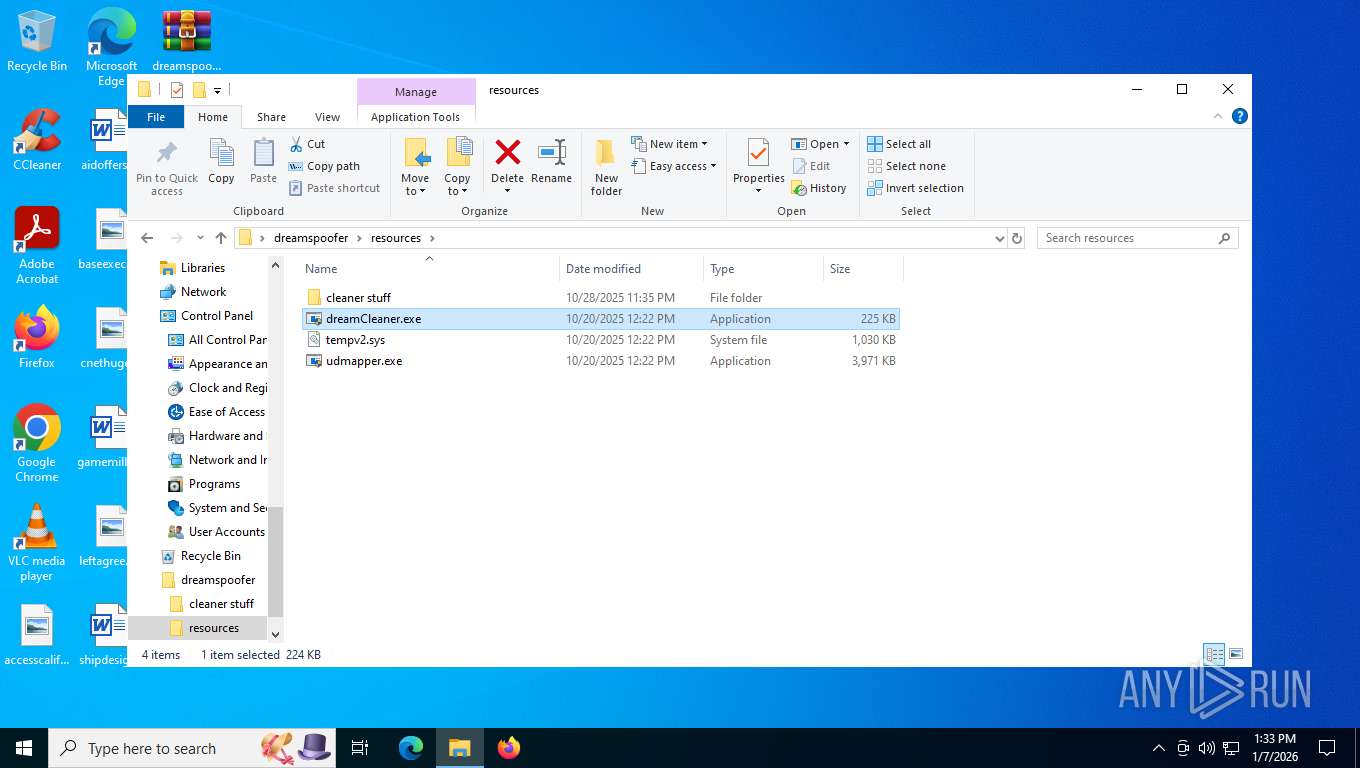
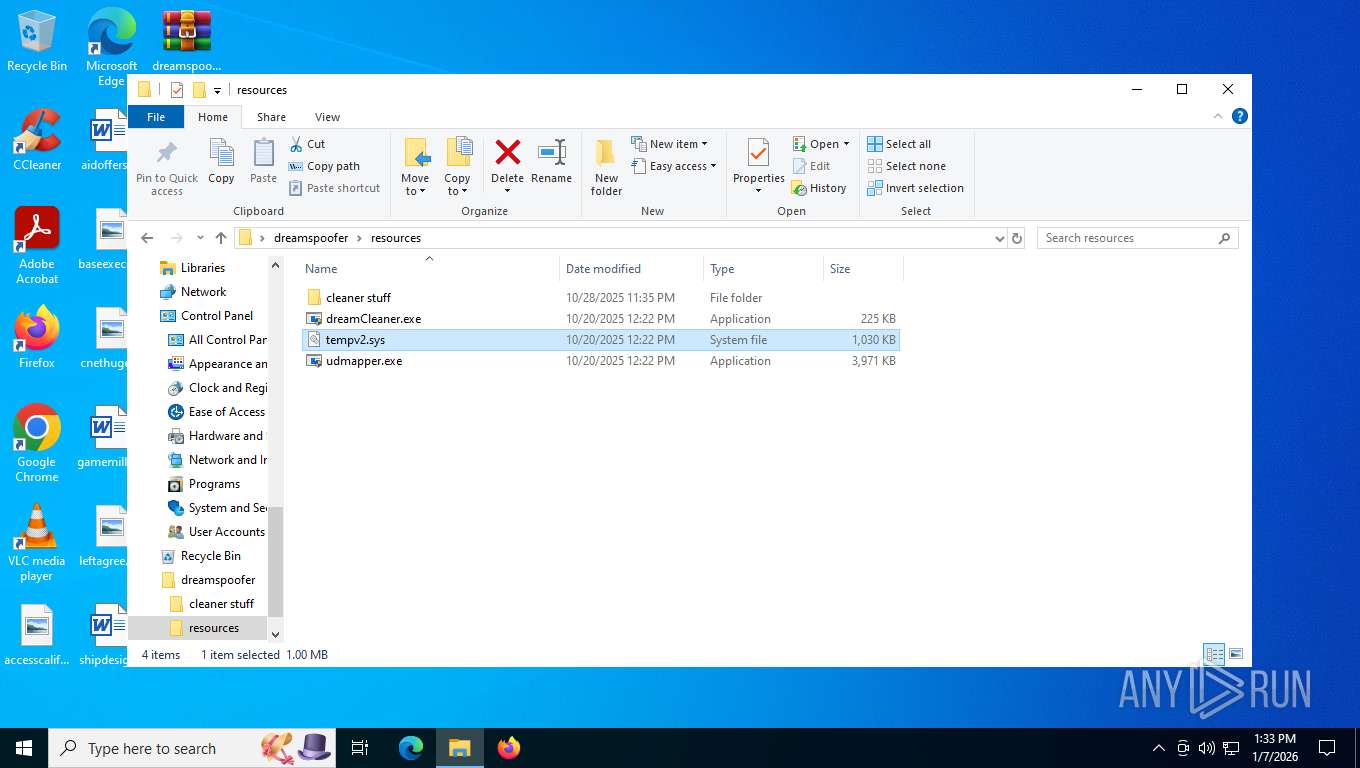
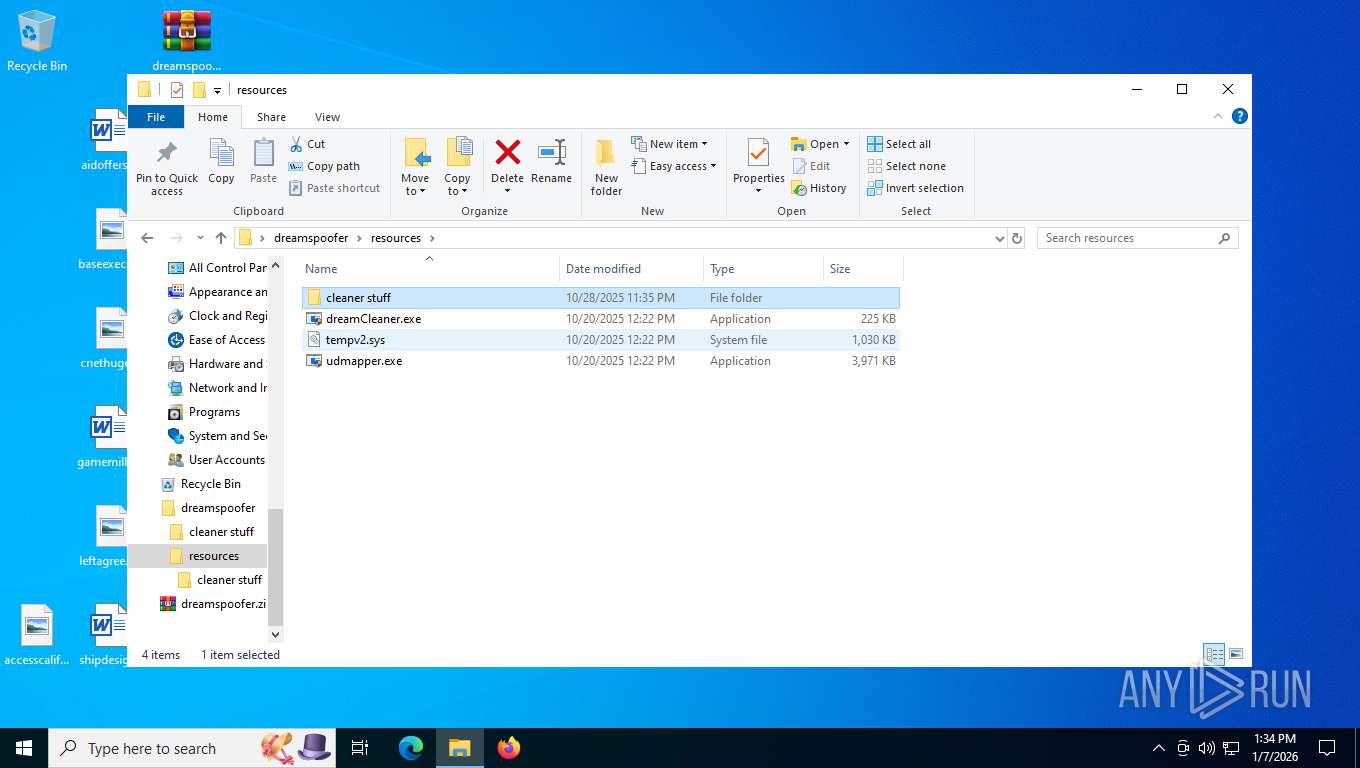
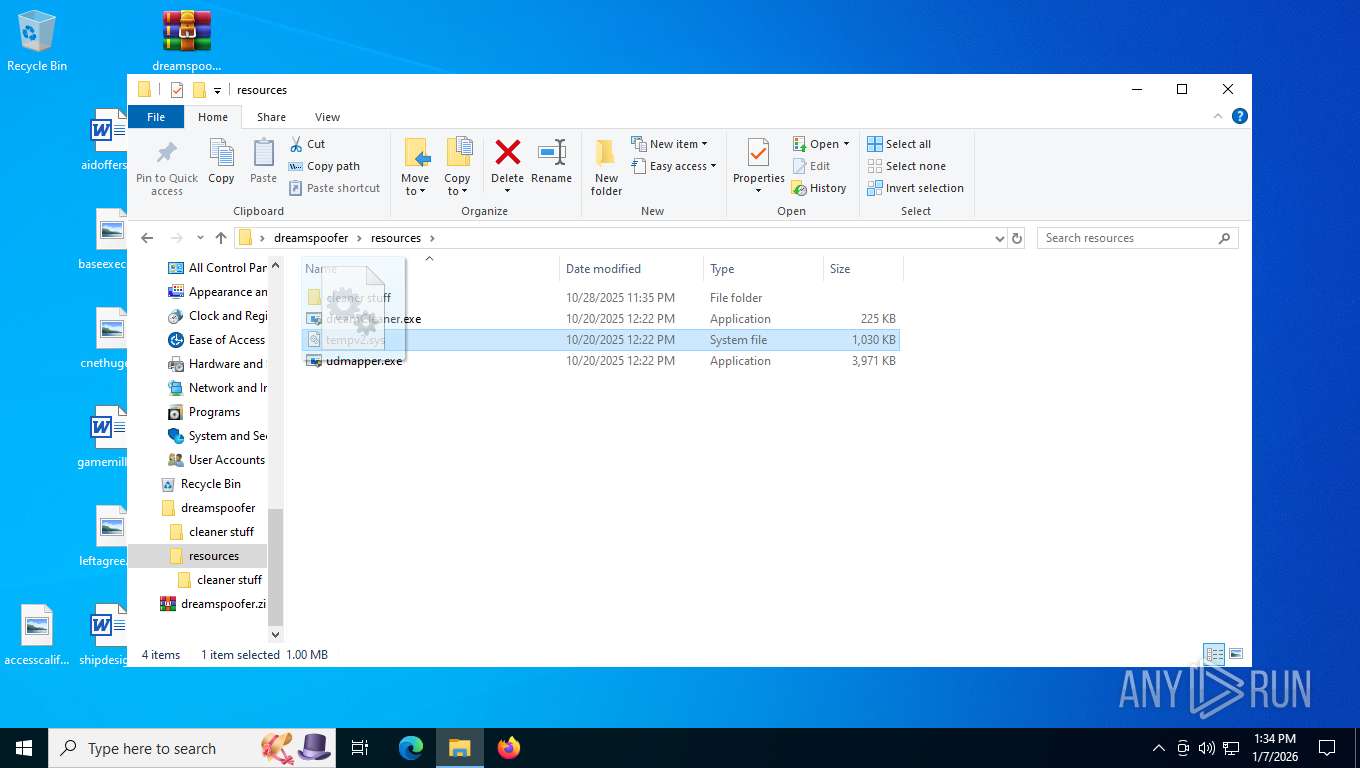
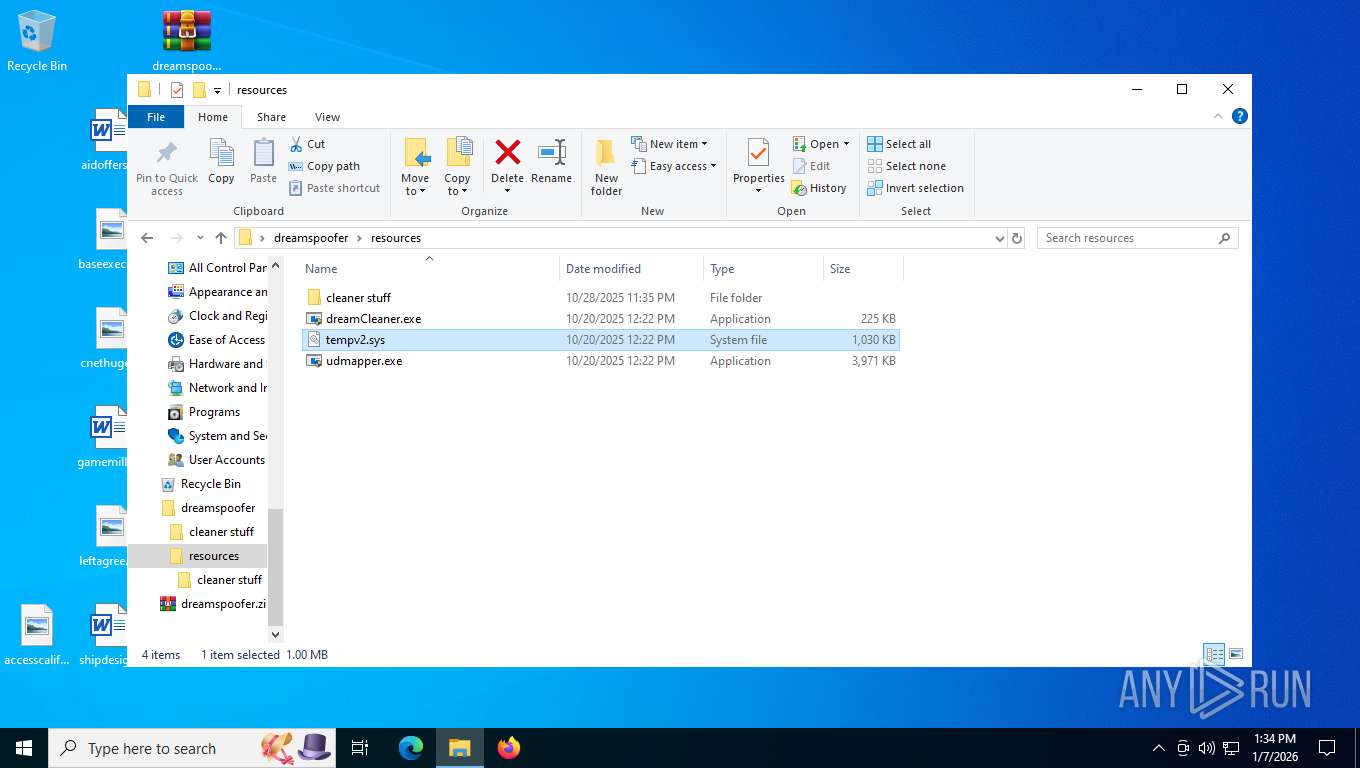
Drops a system driver (possible attempt to evade defenses)
- WinRAR.exe (PID: 7476)
Reads security settings of Internet Explorer
- dreamCleaner.exe (PID: 7904)
Reads the date of Windows installation
- dreamCleaner.exe (PID: 7904)
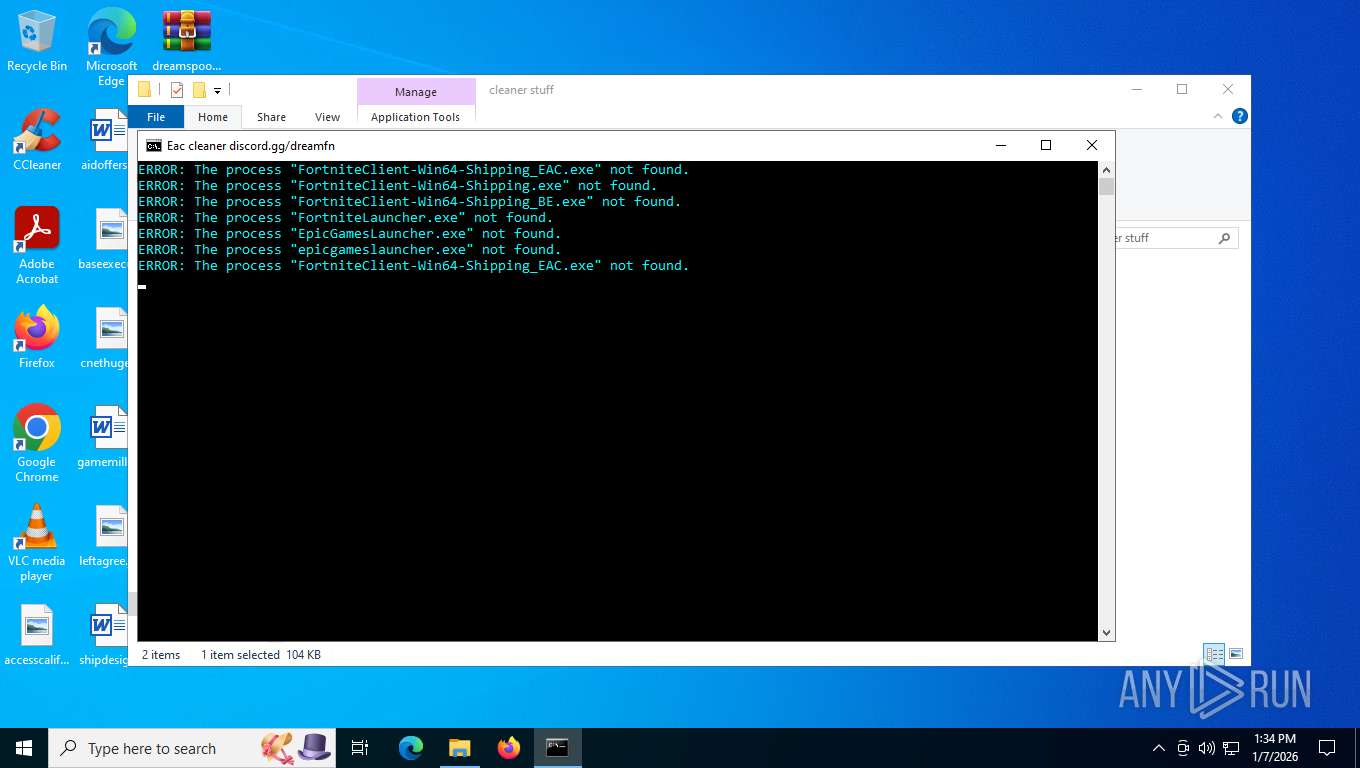
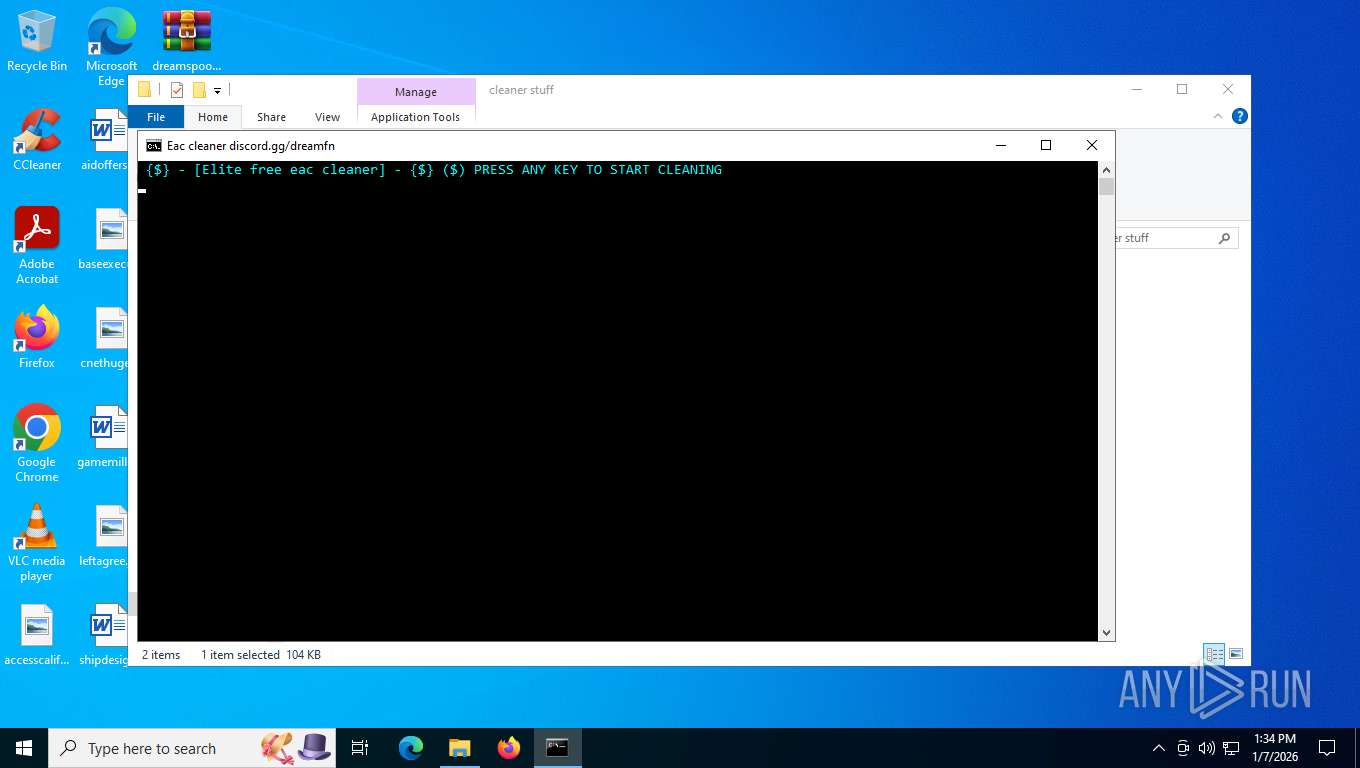
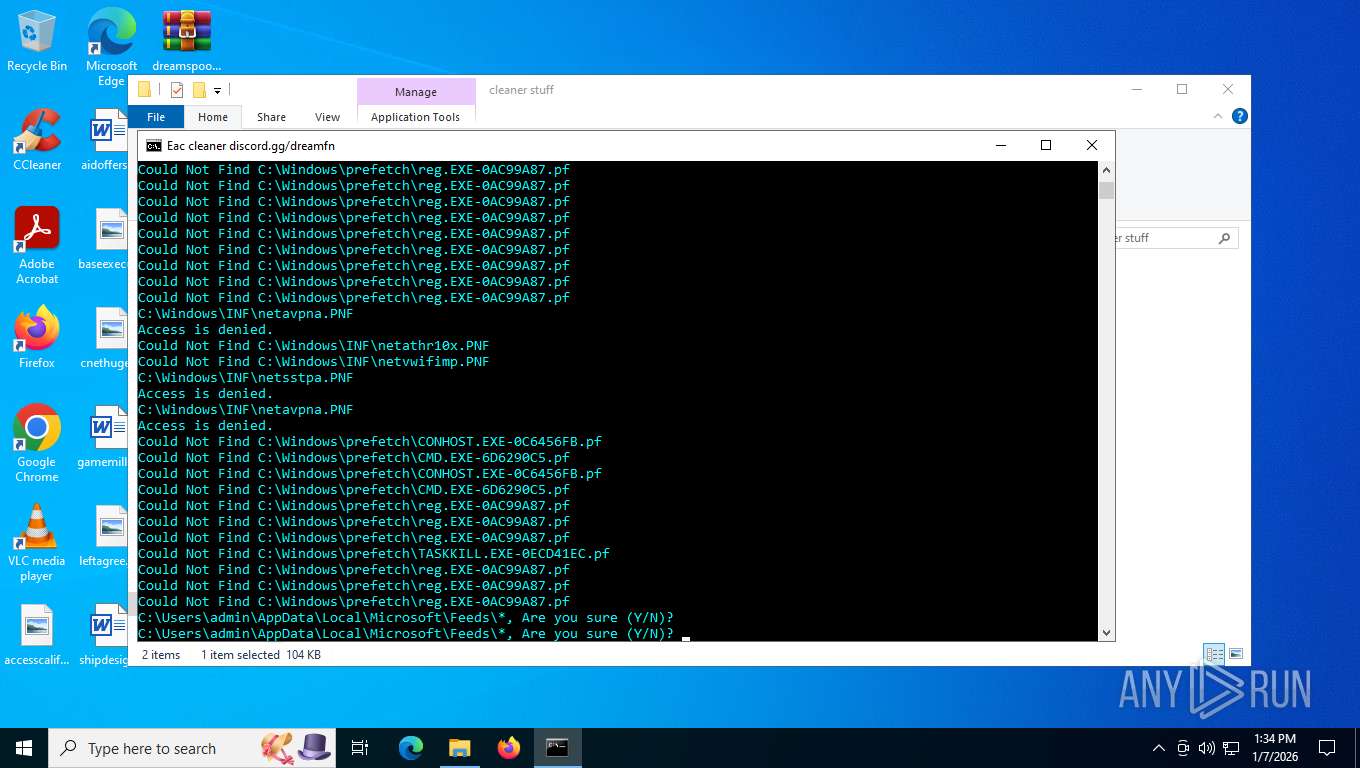
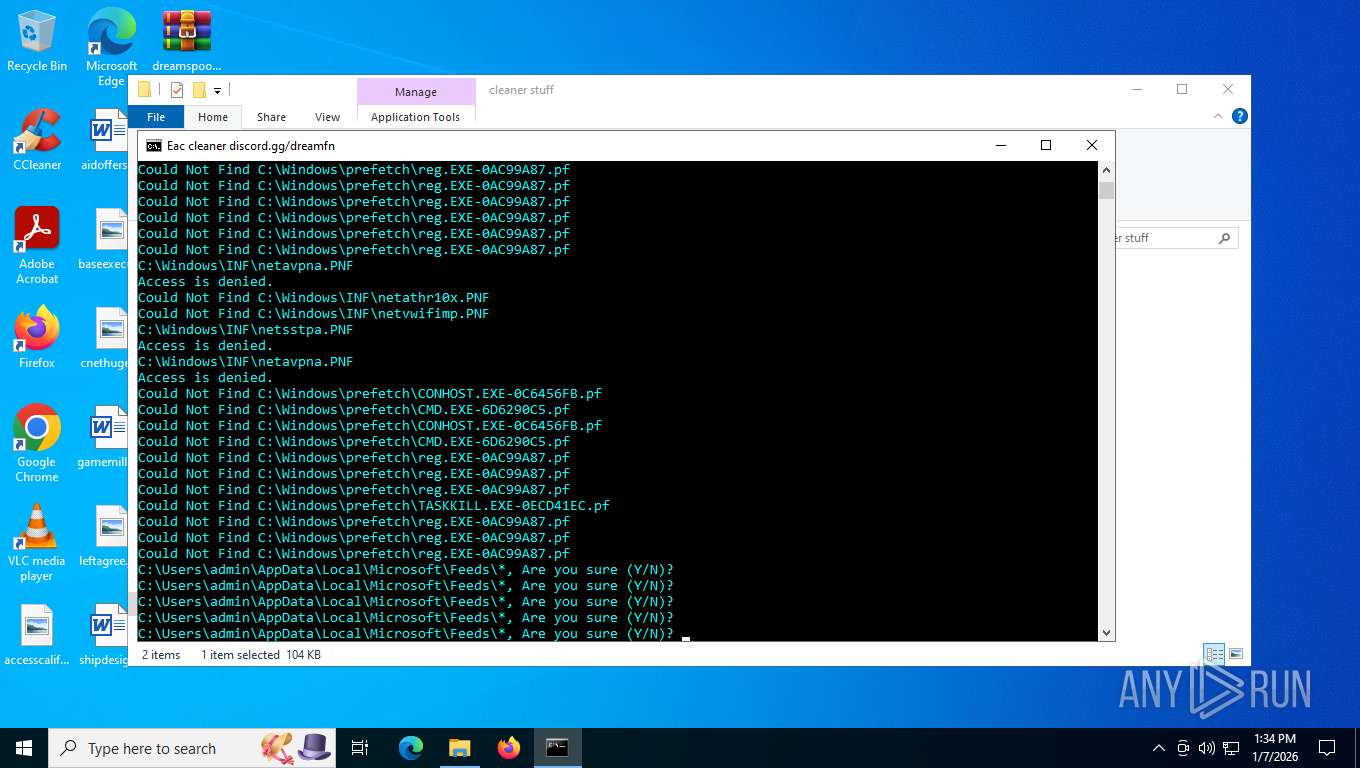
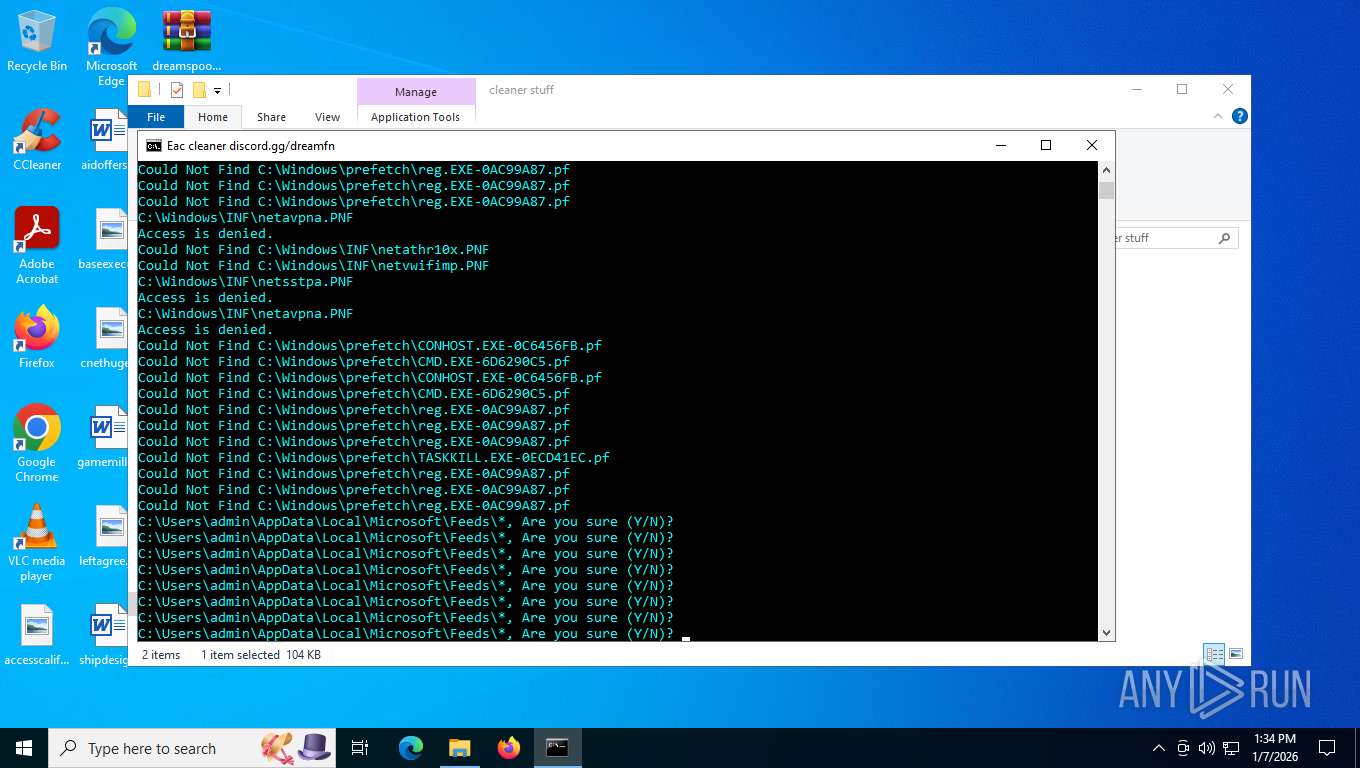
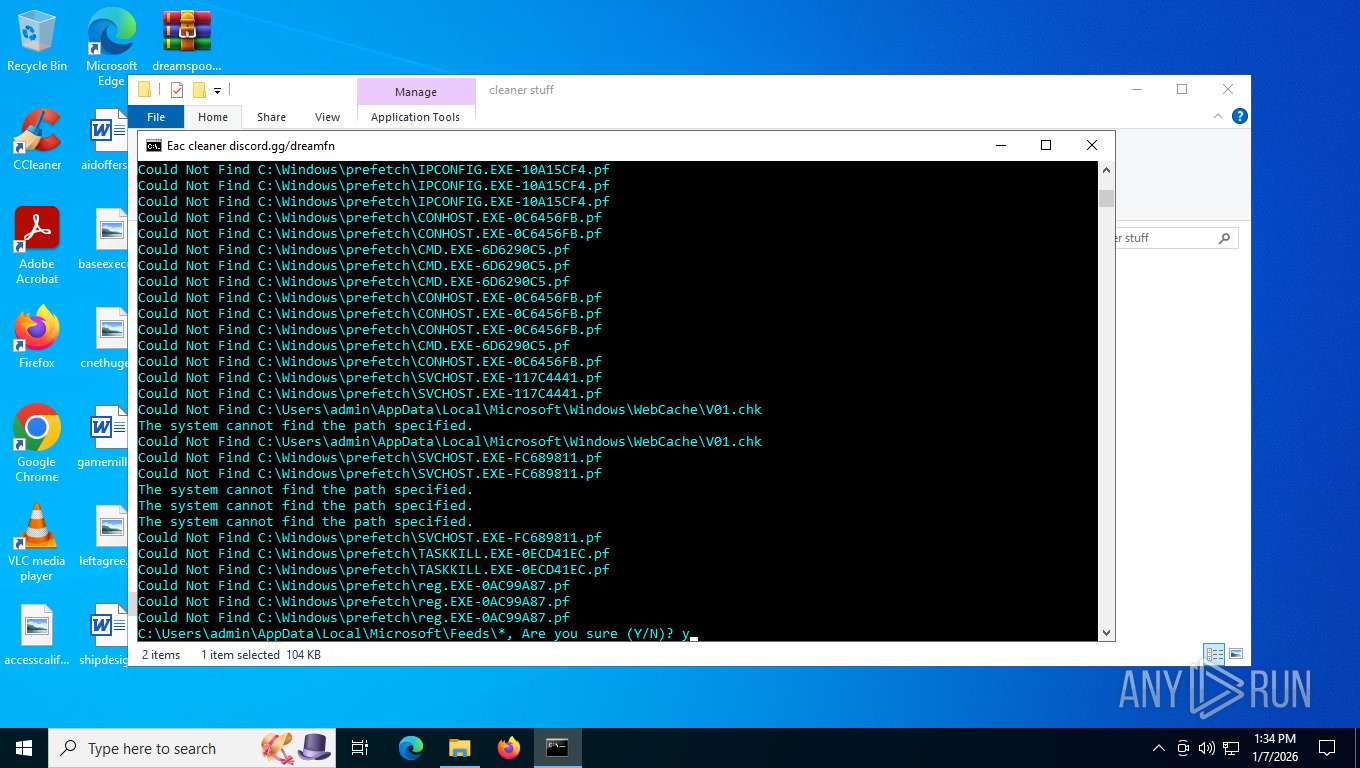
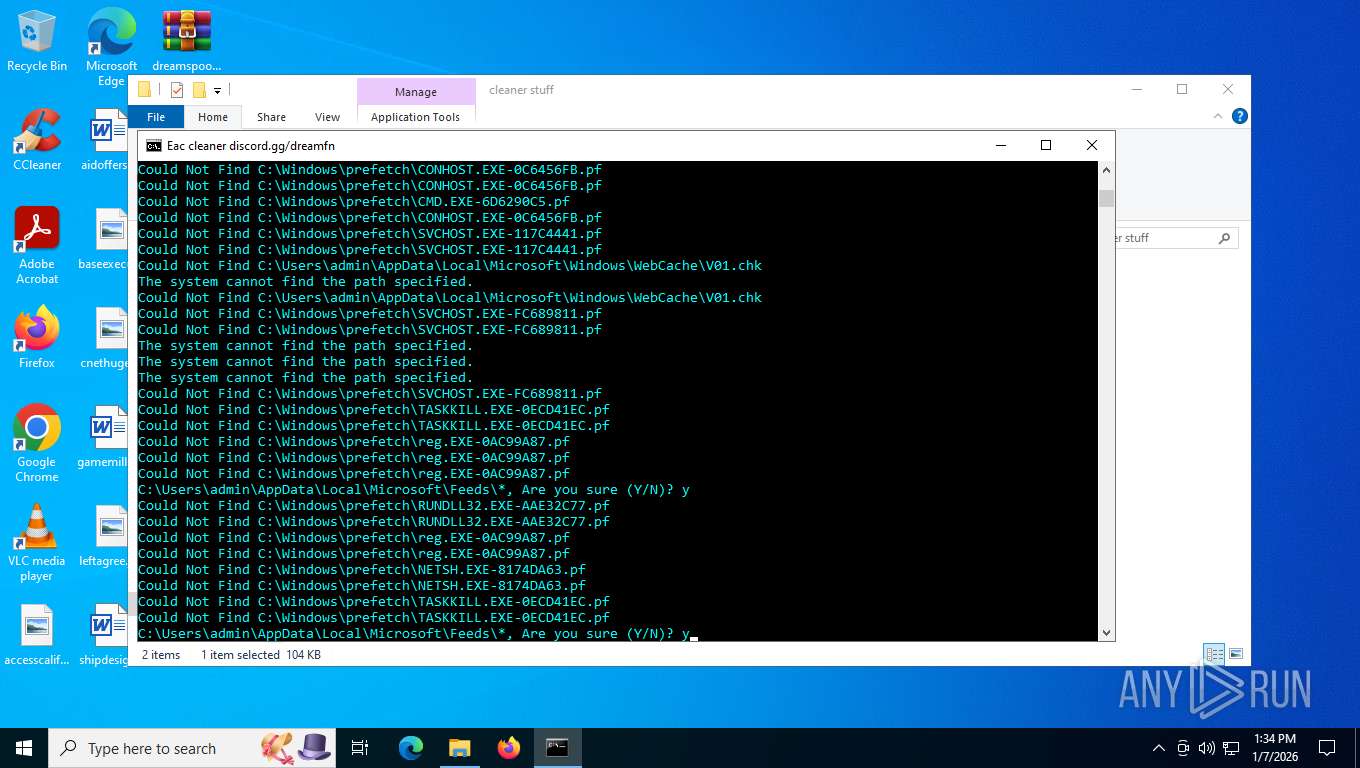
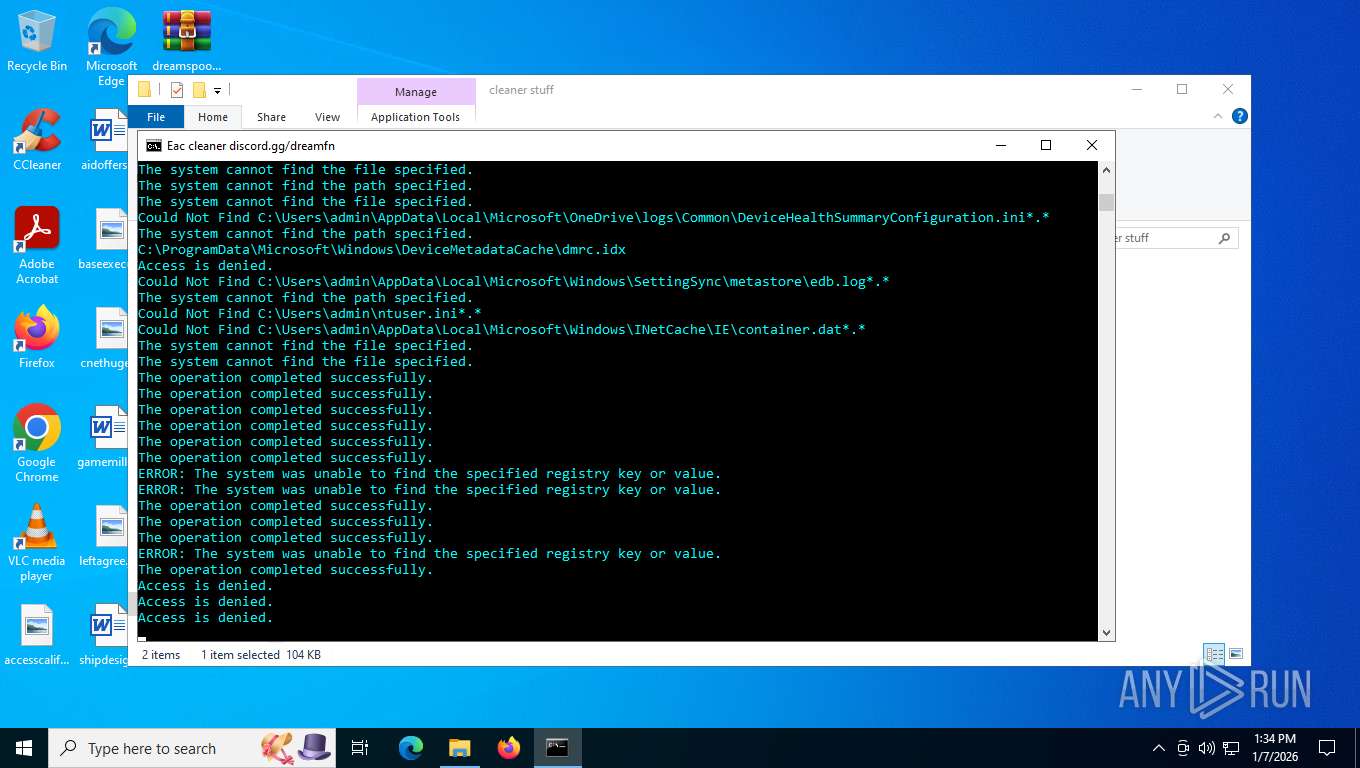
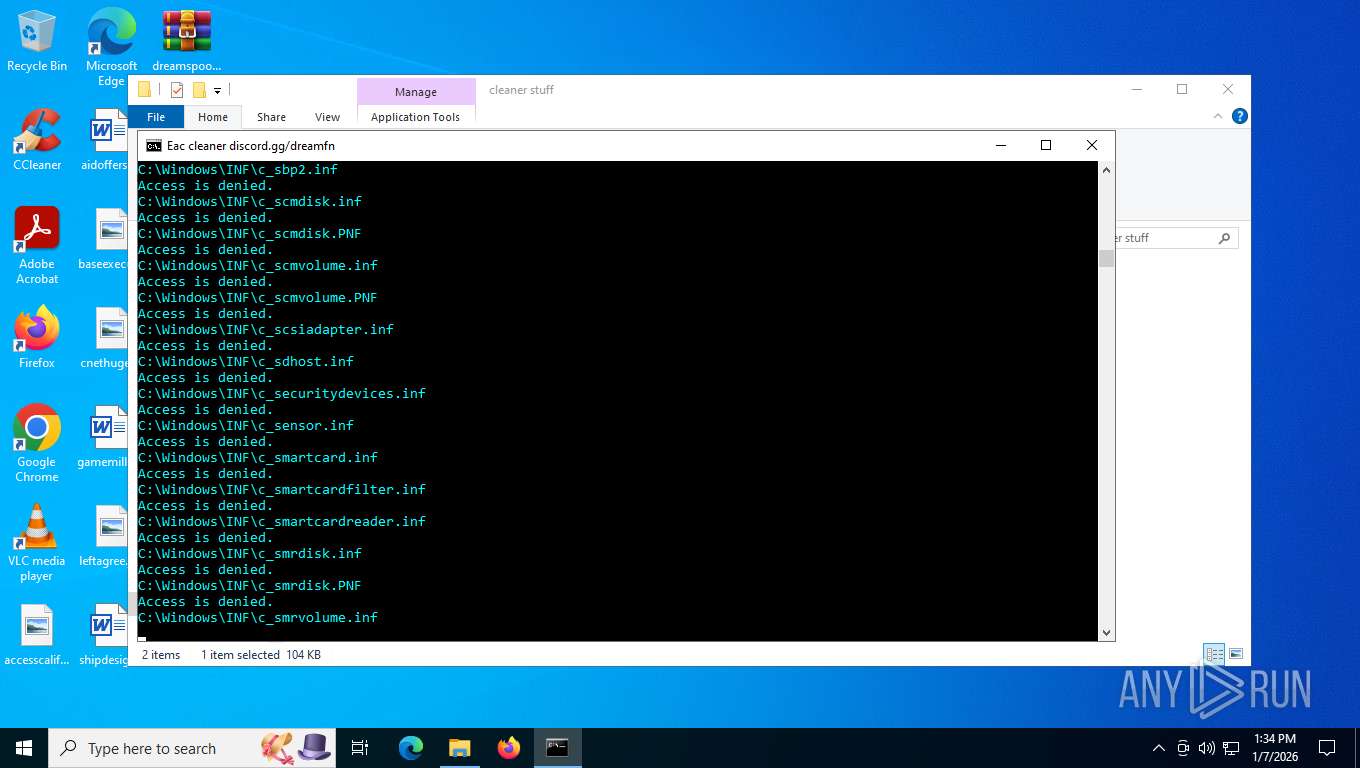
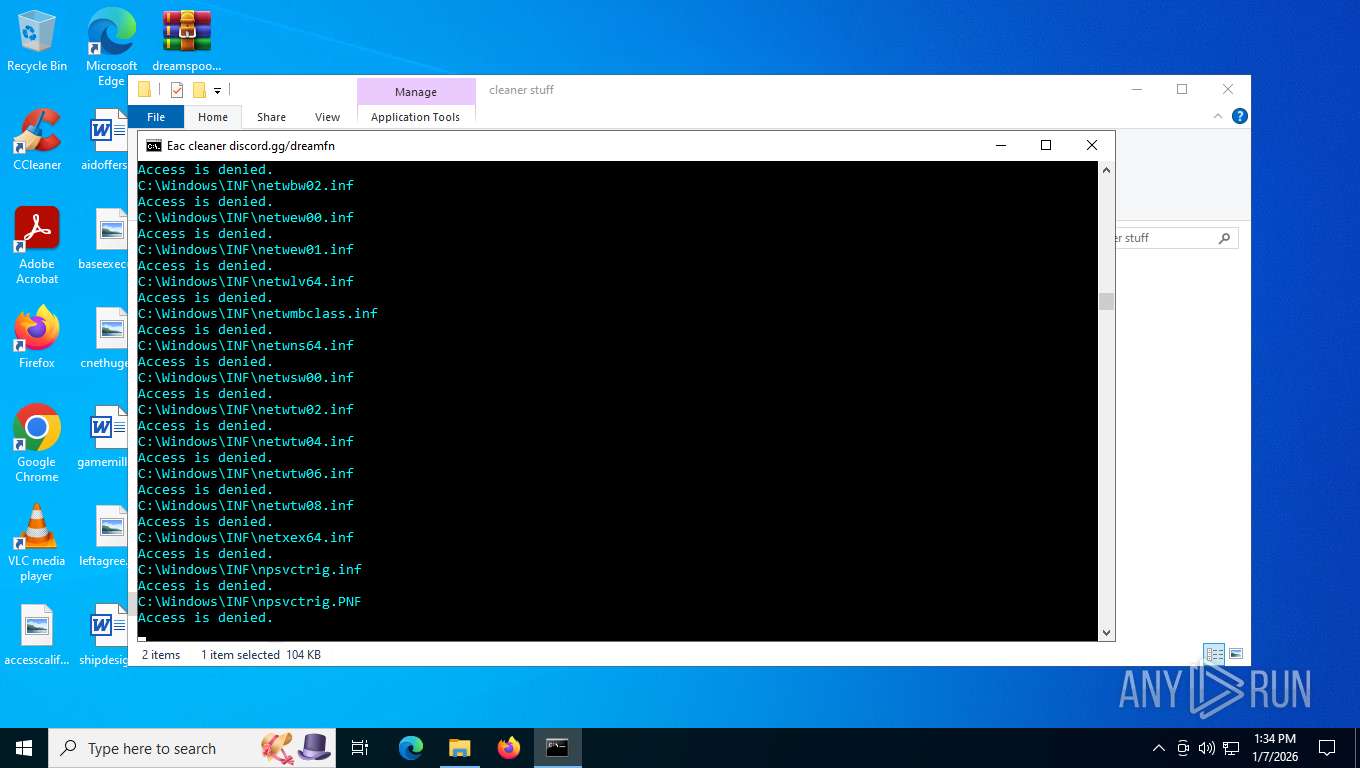
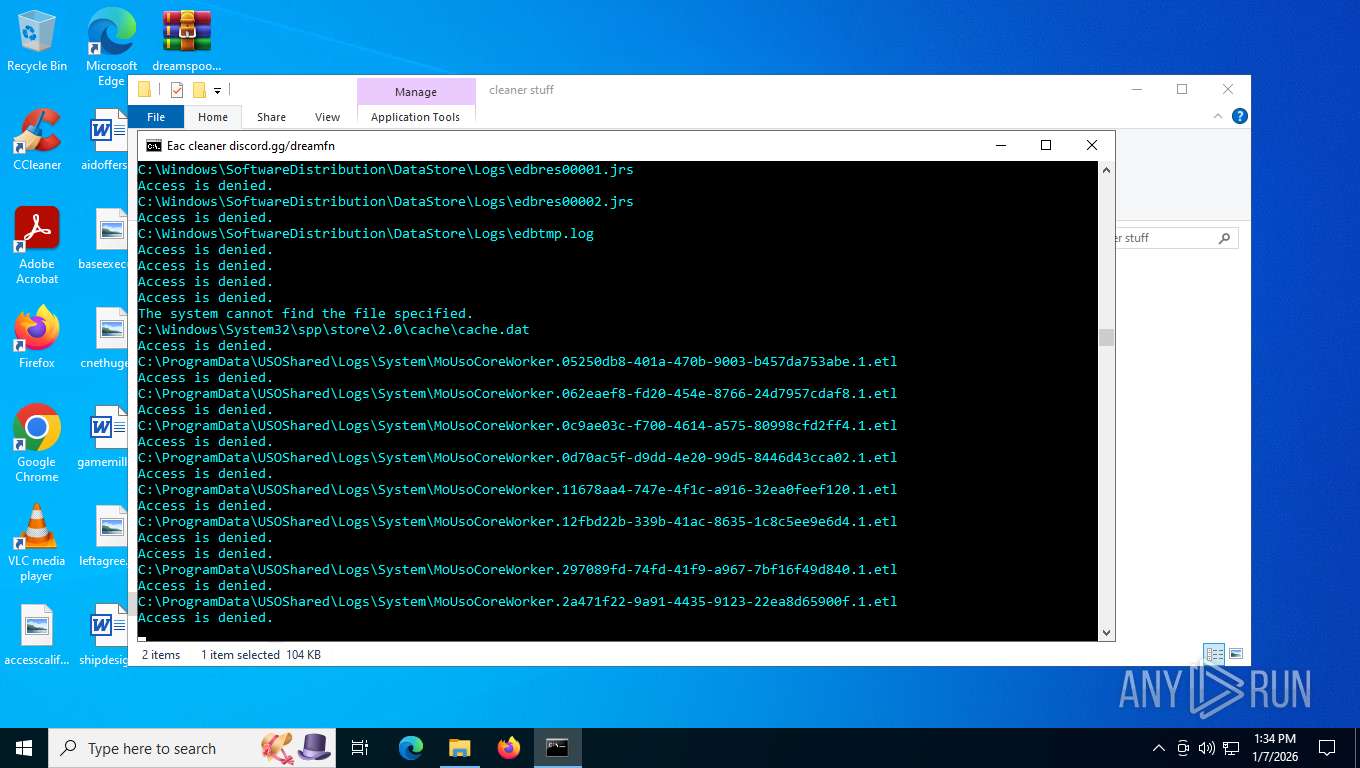
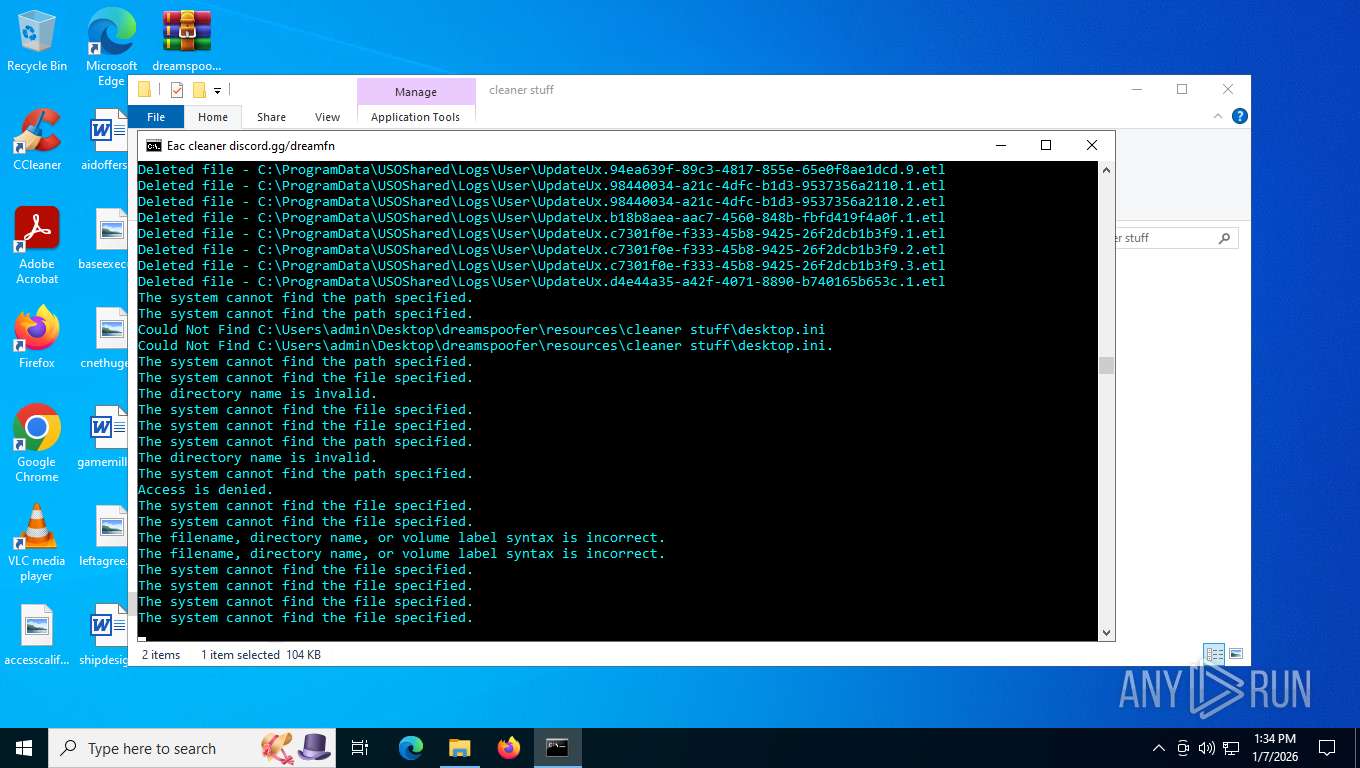
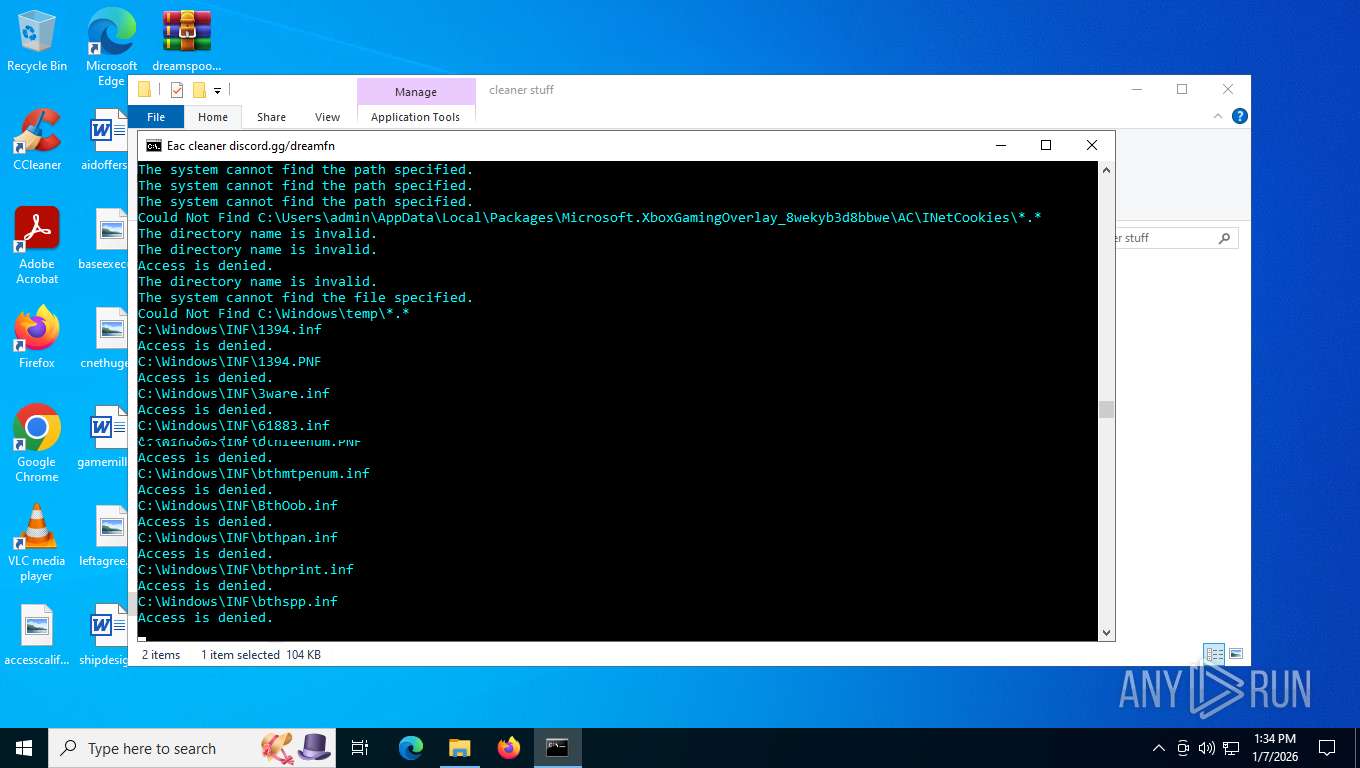
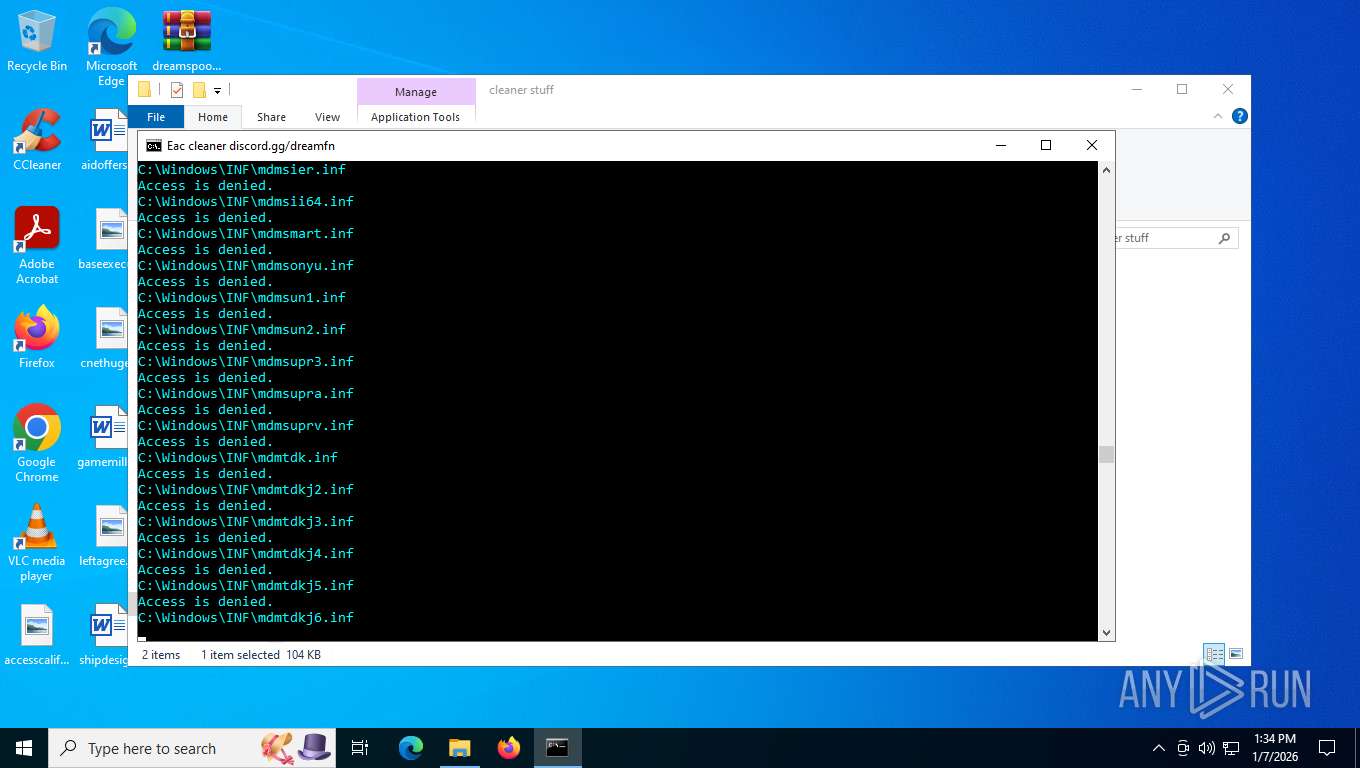
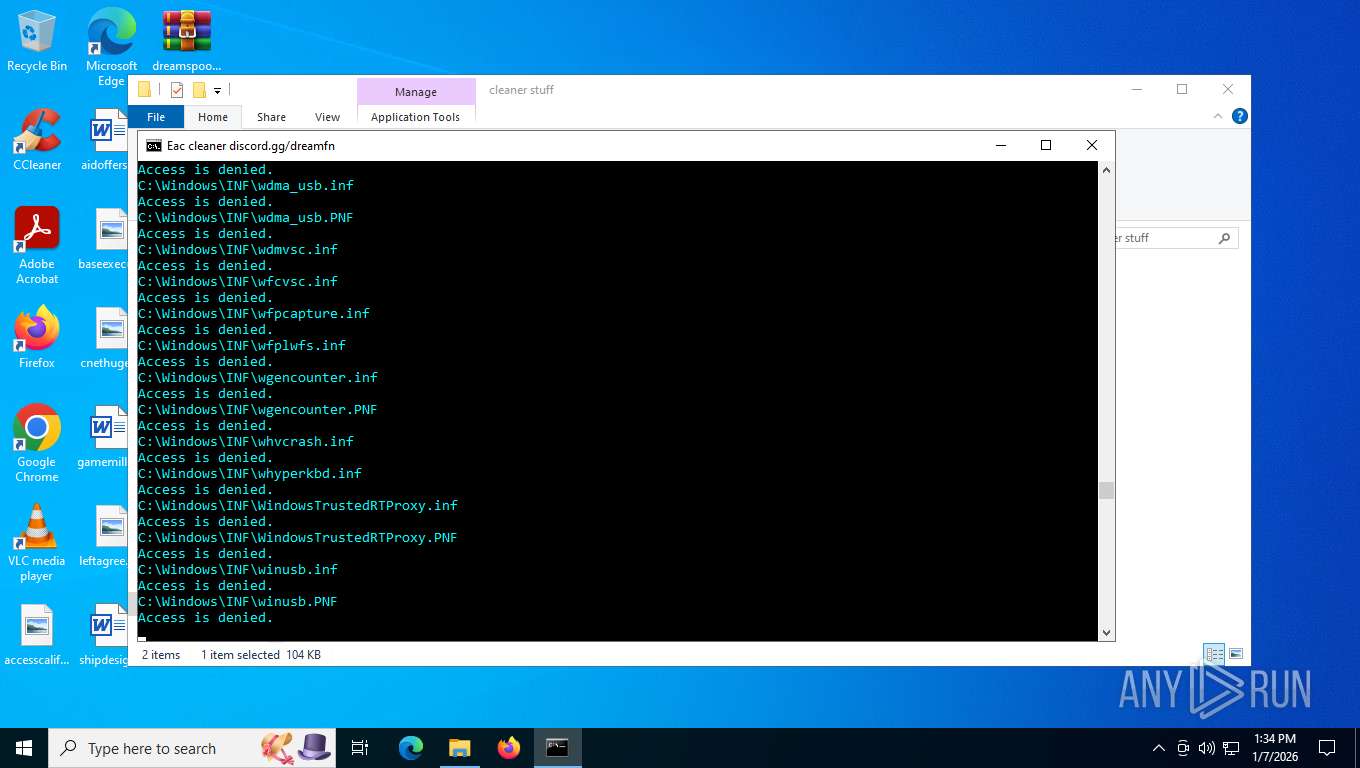
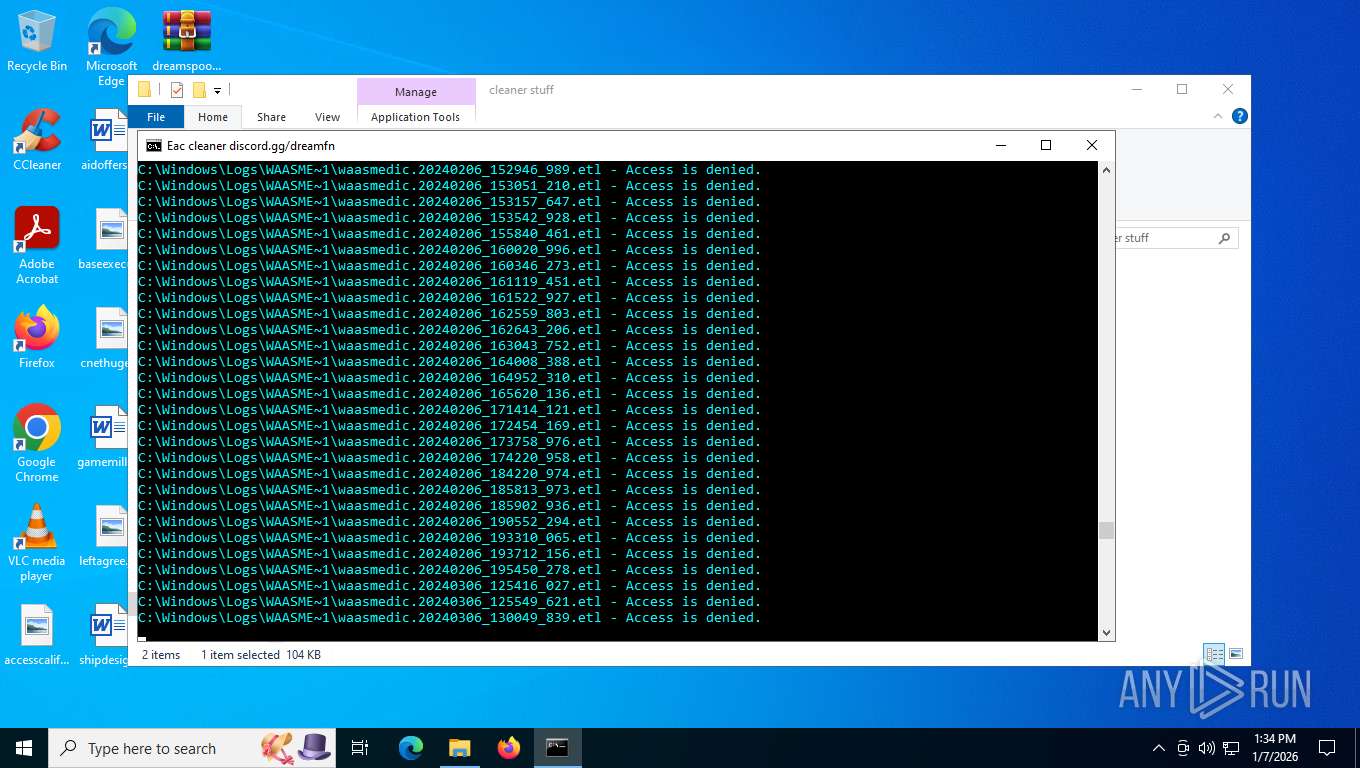
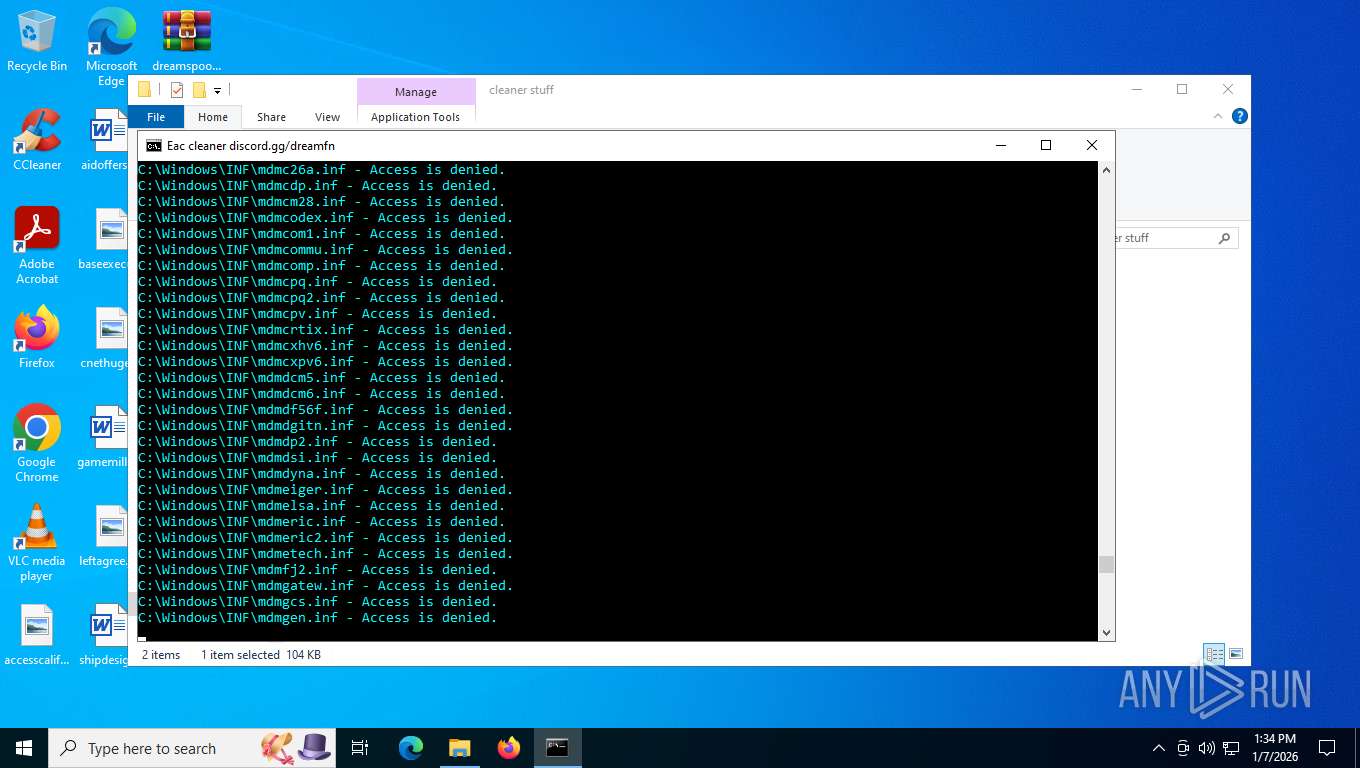
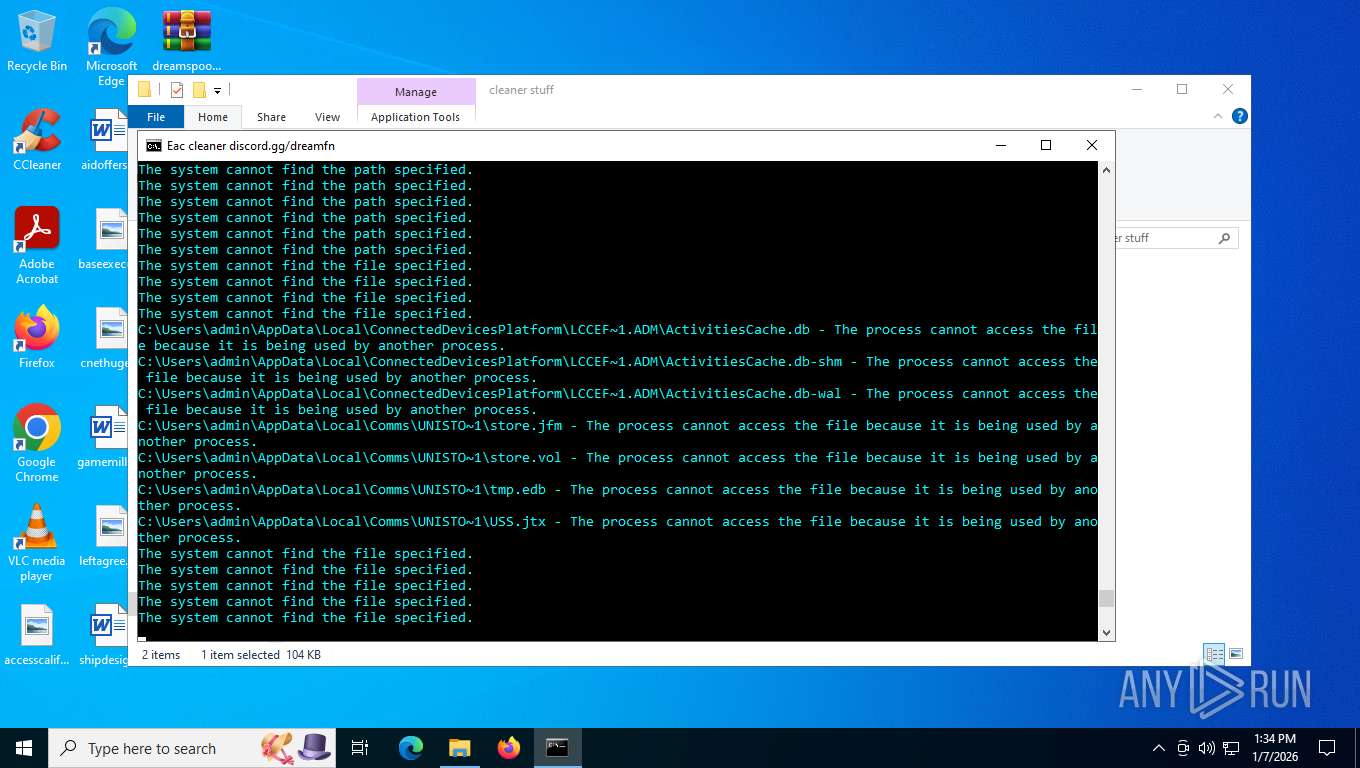
Executing commands from a ".bat" file
- dreamCleaner.exe (PID: 7904)
Starts application with an unusual extension
- cmd.exe (PID: 7956)
- cmd.exe (PID: 8044)
Starts CMD.EXE for commands execution
- dreamCleaner.exe (PID: 7904)
- cmd.exe (PID: 8044)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 7956)
- cmd.exe (PID: 8044)
Stops a currently running service
- sc.exe (PID: 7472)
- sc.exe (PID: 7632)
Starts SC.EXE for service management
- cmd.exe (PID: 7956)
- cmd.exe (PID: 8044)
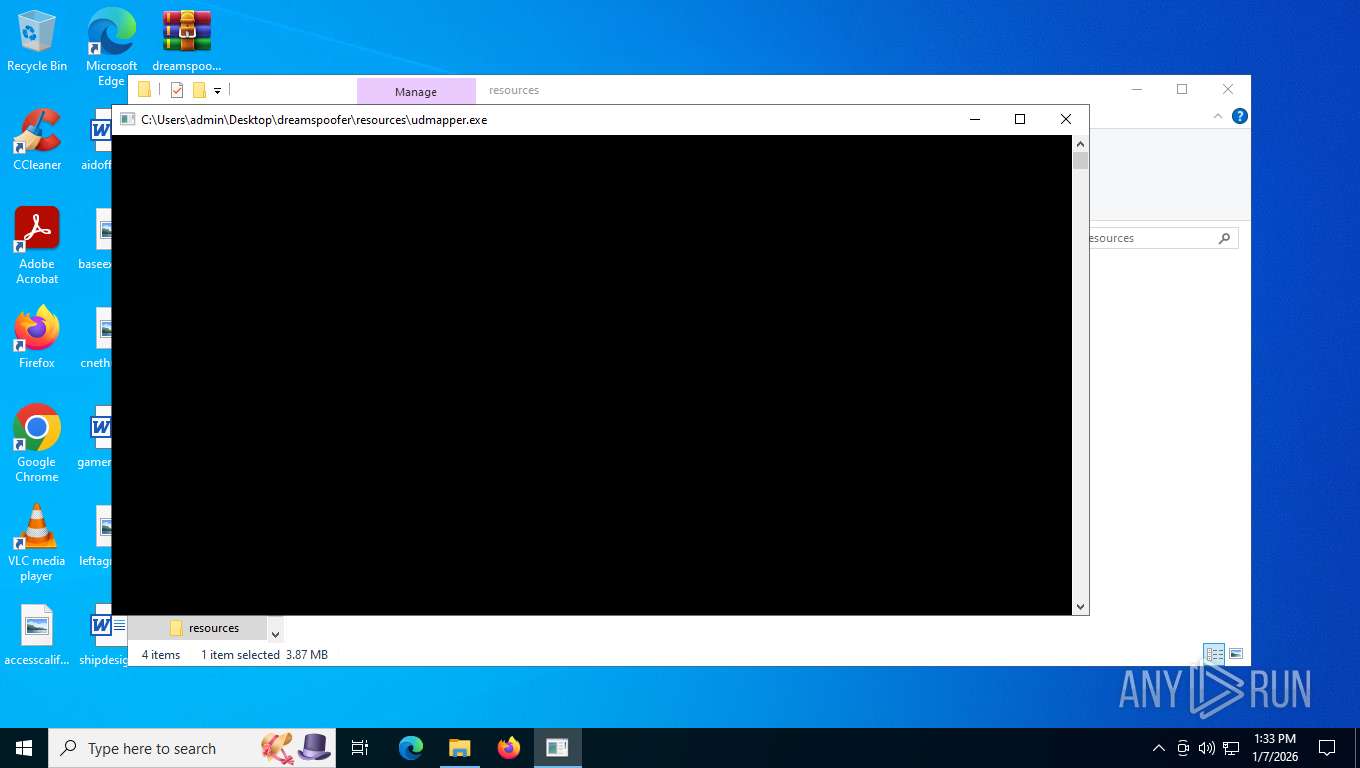
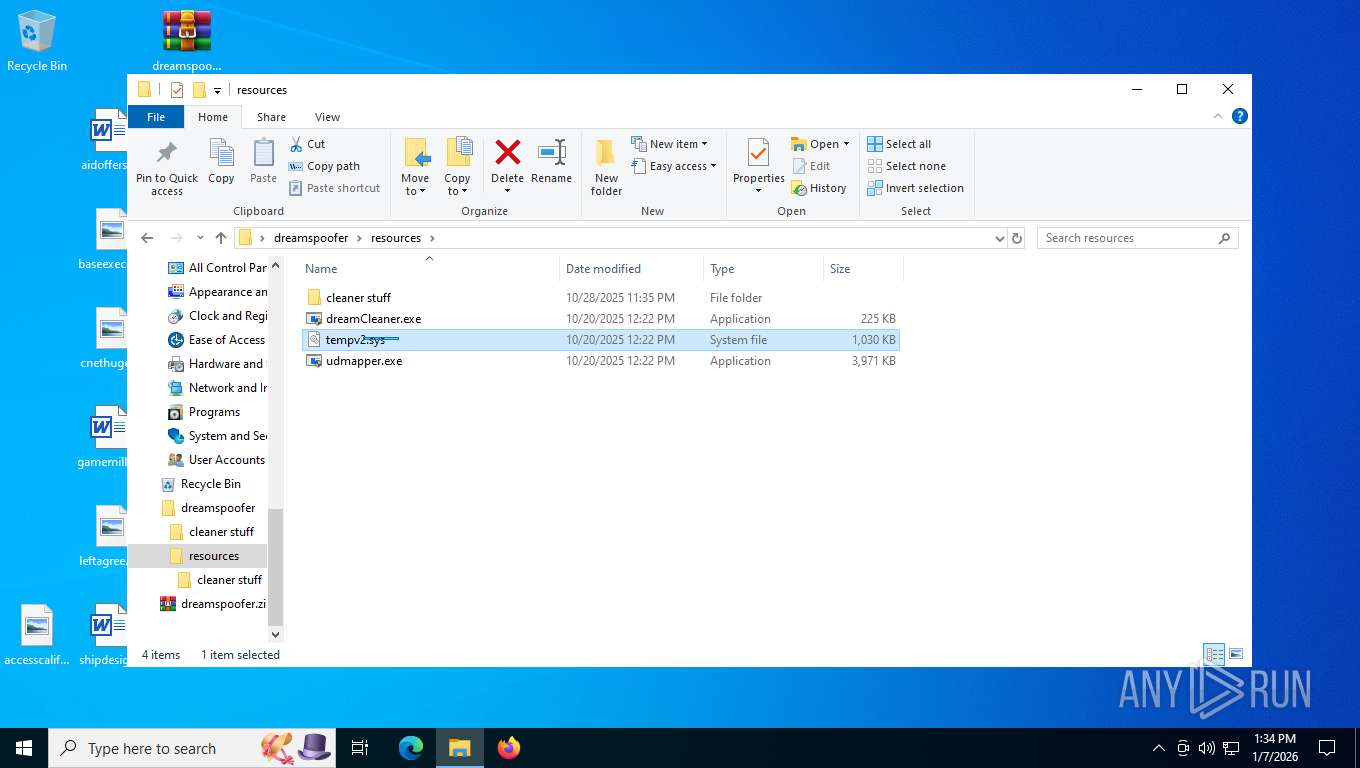
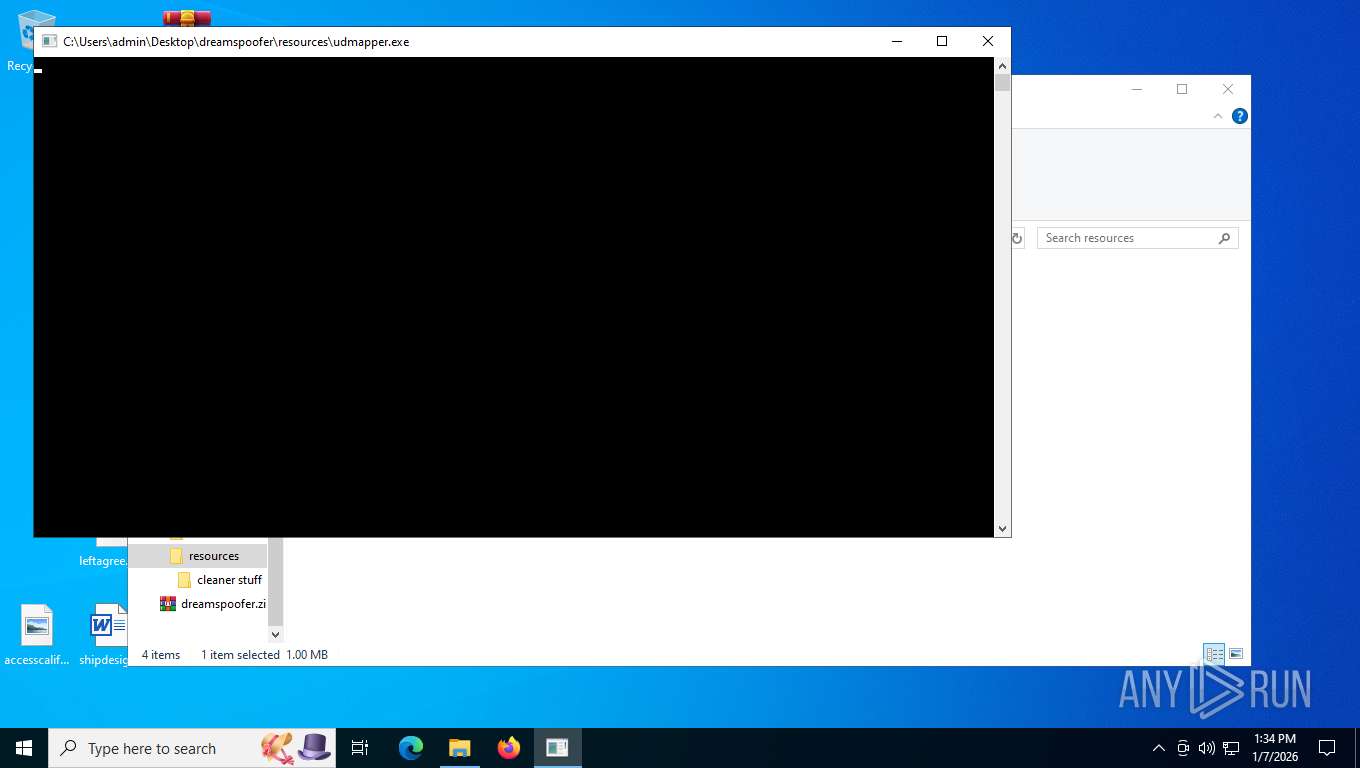
Reads the BIOS version
- udmapper.exe (PID: 7888)
- udmapper.exe (PID: 5984)
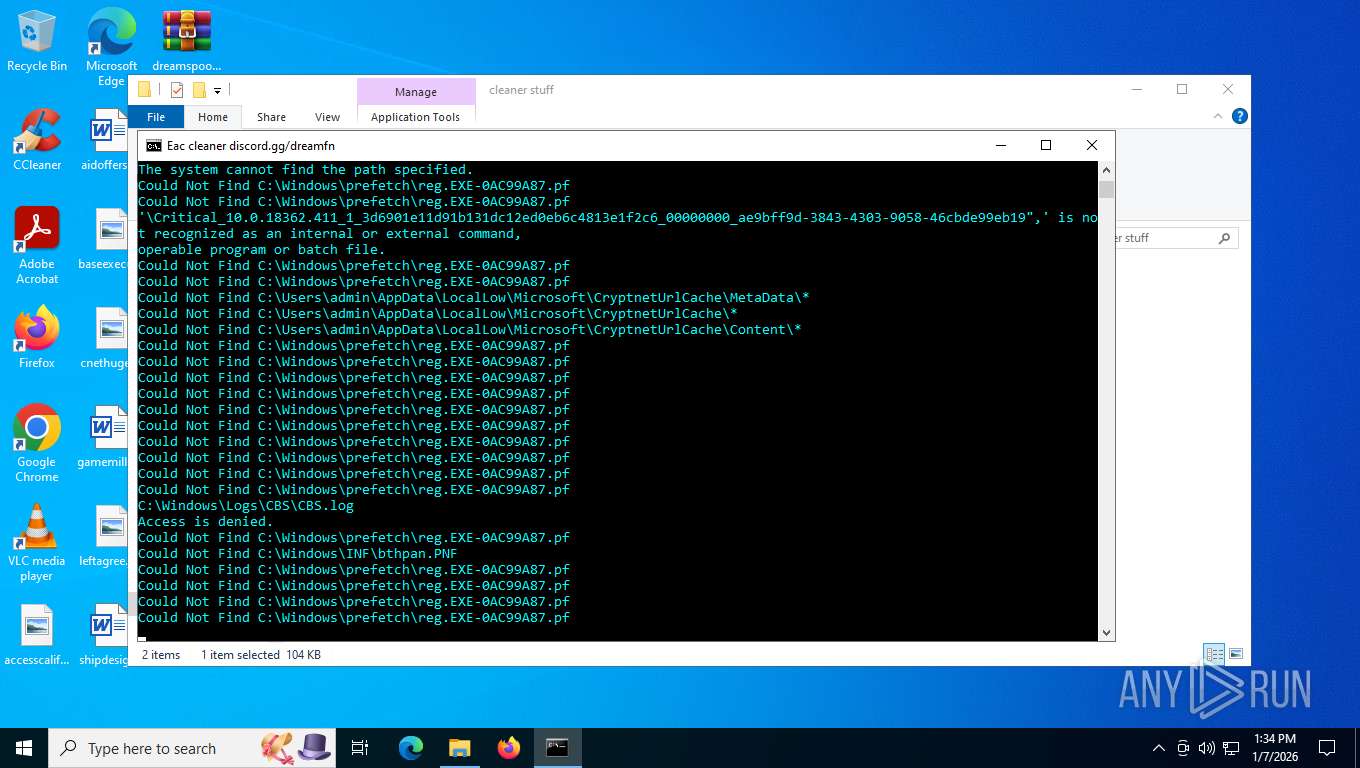
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 8044)
Application launched itself
- cmd.exe (PID: 8044)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 4752)
Possible stealing of VPN data
- cmd.exe (PID: 8044)
Using the short paths format
- cmd.exe (PID: 8044)
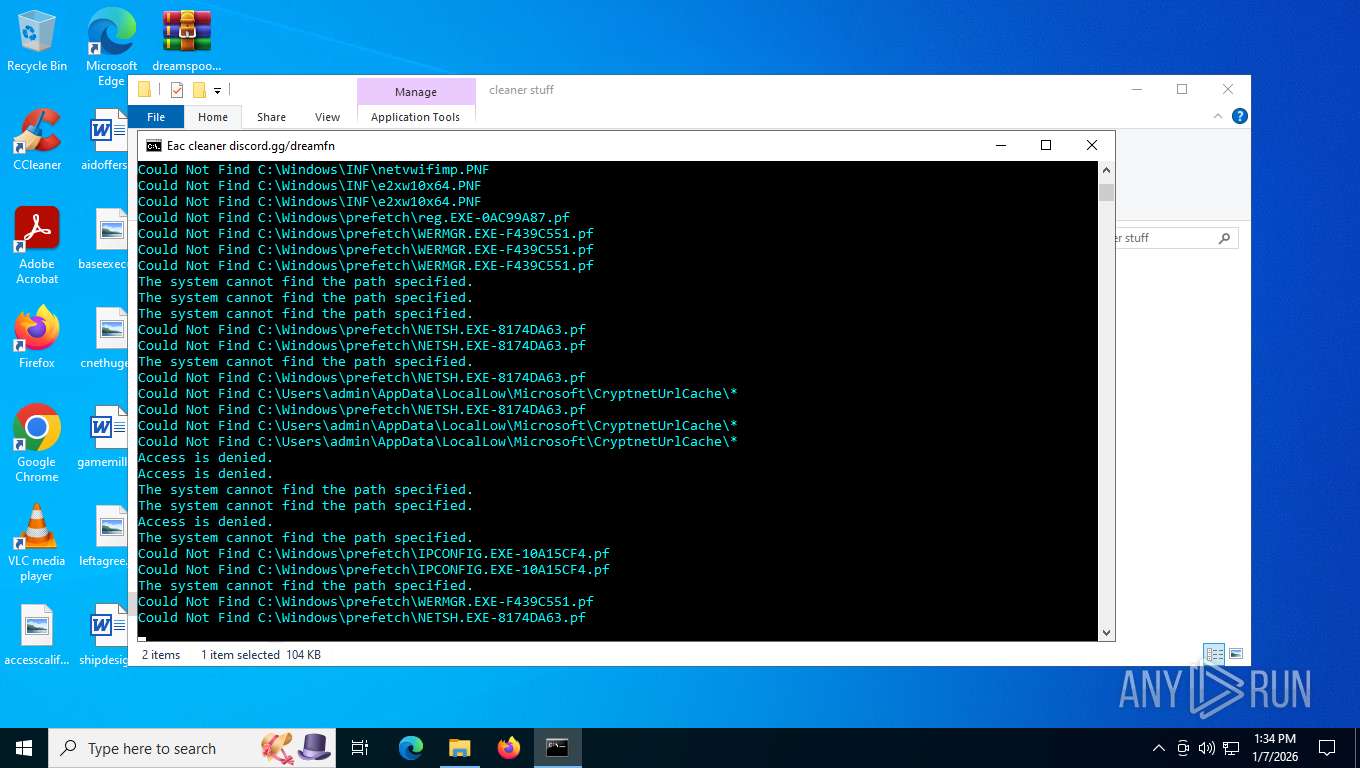
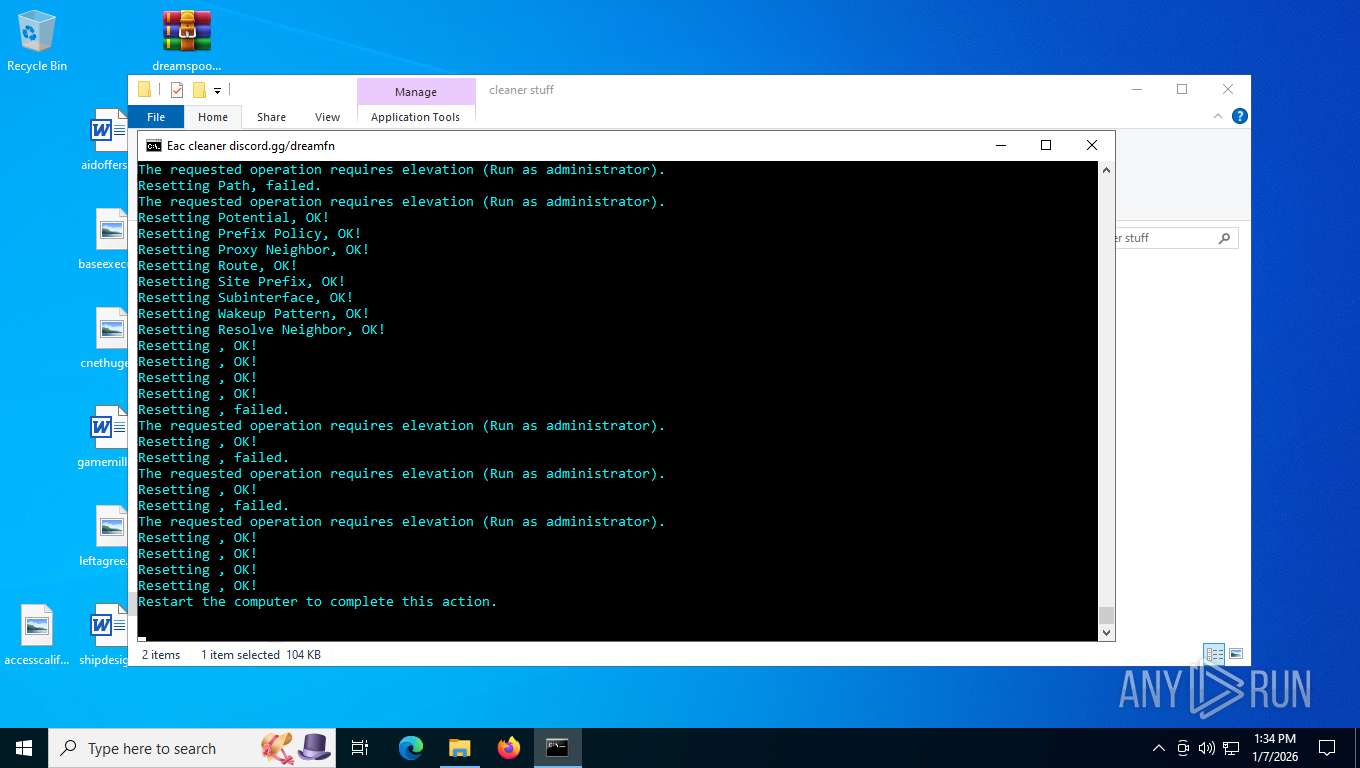
Suspicious use of NETSH.EXE
- cmd.exe (PID: 8044)
Process uses IPCONFIG to clear DNS cache
- cmd.exe (PID: 8044)
Process uses IPCONFIG to discard the IP address configuration
- cmd.exe (PID: 8044)
Process uses IPCONFIG to get network configuration information
- cmd.exe (PID: 8044)
Process uses IPCONFIG to renew DHCP configuration
- cmd.exe (PID: 8044)
INFO
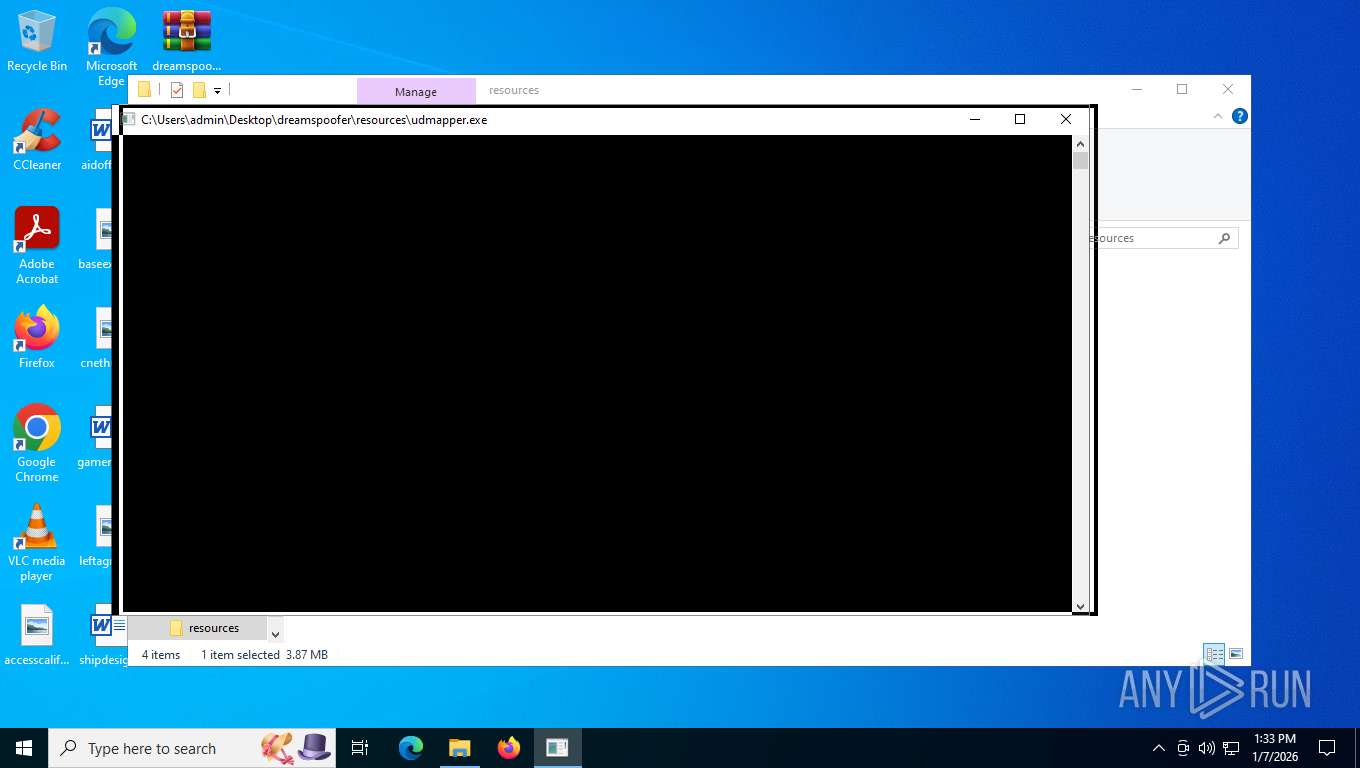
Manual execution by a user
- dreamCleaner.exe (PID: 7904)
- dreamCleaner.exe (PID: 7852)
- udmapper.exe (PID: 3004)
- udmapper.exe (PID: 7888)
- cmd.exe (PID: 8044)
- udmapper.exe (PID: 7708)
- udmapper.exe (PID: 5984)
Reads the computer name
- dreamCleaner.exe (PID: 7904)
Process checks computer location settings
- dreamCleaner.exe (PID: 7904)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7476)
Create files in a temporary directory
- dreamCleaner.exe (PID: 7904)
Checks supported languages
- dreamCleaner.exe (PID: 7904)
- chcp.com (PID: 8016)
- udmapper.exe (PID: 7888)
- chcp.com (PID: 8168)
- udmapper.exe (PID: 5984)
Changes the display of characters in the console
- cmd.exe (PID: 7956)
- cmd.exe (PID: 8044)
Process checks whether UAC notifications are on
- udmapper.exe (PID: 7888)
- udmapper.exe (PID: 5984)
Disables trace logs
- netsh.exe (PID: 7624)
- netsh.exe (PID: 3548)
- netsh.exe (PID: 6956)
- netsh.exe (PID: 7832)
- netsh.exe (PID: 7780)
- netsh.exe (PID: 468)
- netsh.exe (PID: 7716)
- netsh.exe (PID: 7860)
- netsh.exe (PID: 7892)
- netsh.exe (PID: 6556)
Reads security settings of Internet Explorer
- certutil.exe (PID: 3568)
- certutil.exe (PID: 7444)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2025:10:28 23:35:58 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | dreamspoofer/cleaner stuff/ |
Total processes
278
Monitored processes
135
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 148 | taskkill /f /im epicgameslauncher.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 148 | taskkill /f /im EpicGamesLauncher.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 468 | netsh int ip reset | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 756 | reg delete "HKLM\SYSTEM\ControlSet001\Services\EasyAntiCheat\Start: 0x00000003" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 792 | taskkill /f /im FortniteLauncher.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 792 | reg delete "HKEY_CURRENT_USER\Software\Epic Games\Unreal Engine" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1068 | taskkill /f /im FortniteClient-Win64-Shipping_BE.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1136 | reg delete "HKEY_LOCAL_MACHINE\Hardware\Description\System\BIOS" /v BIOSVendor /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1412 | reg delete "HKEY_LOCAL_MACHINE\Software\Epic Games" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1700 | netsh winsock reset | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Network Command Shell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
11 751
Read events
10 546
Write events
24
Delete events
1 181
Modification events
| (PID) Process: | (7476) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7476) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7476) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7476) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\dreamspoofer.zip | |||
| (PID) Process: | (7476) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7476) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7476) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7476) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7476) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (7476) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
5
Suspicious files
0
Text files
5
Unknown types
0
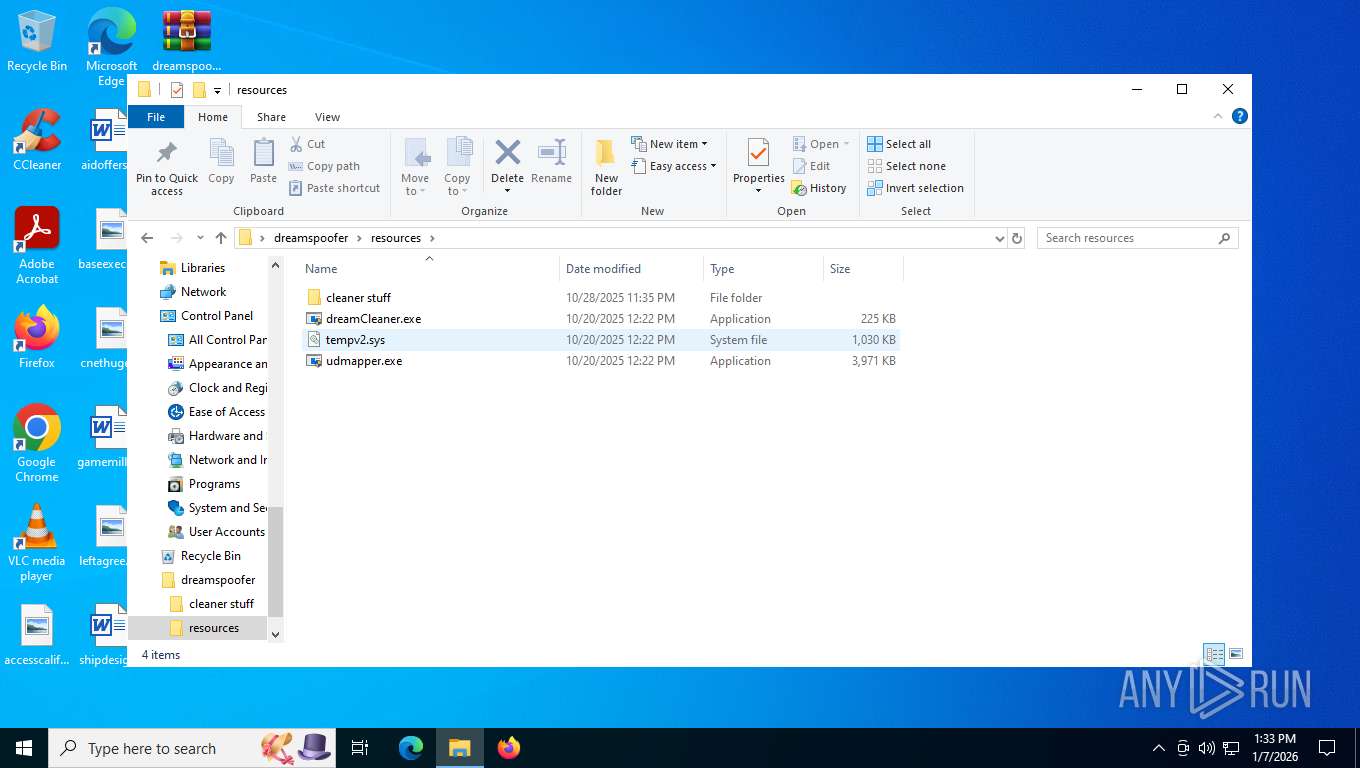
Dropped files
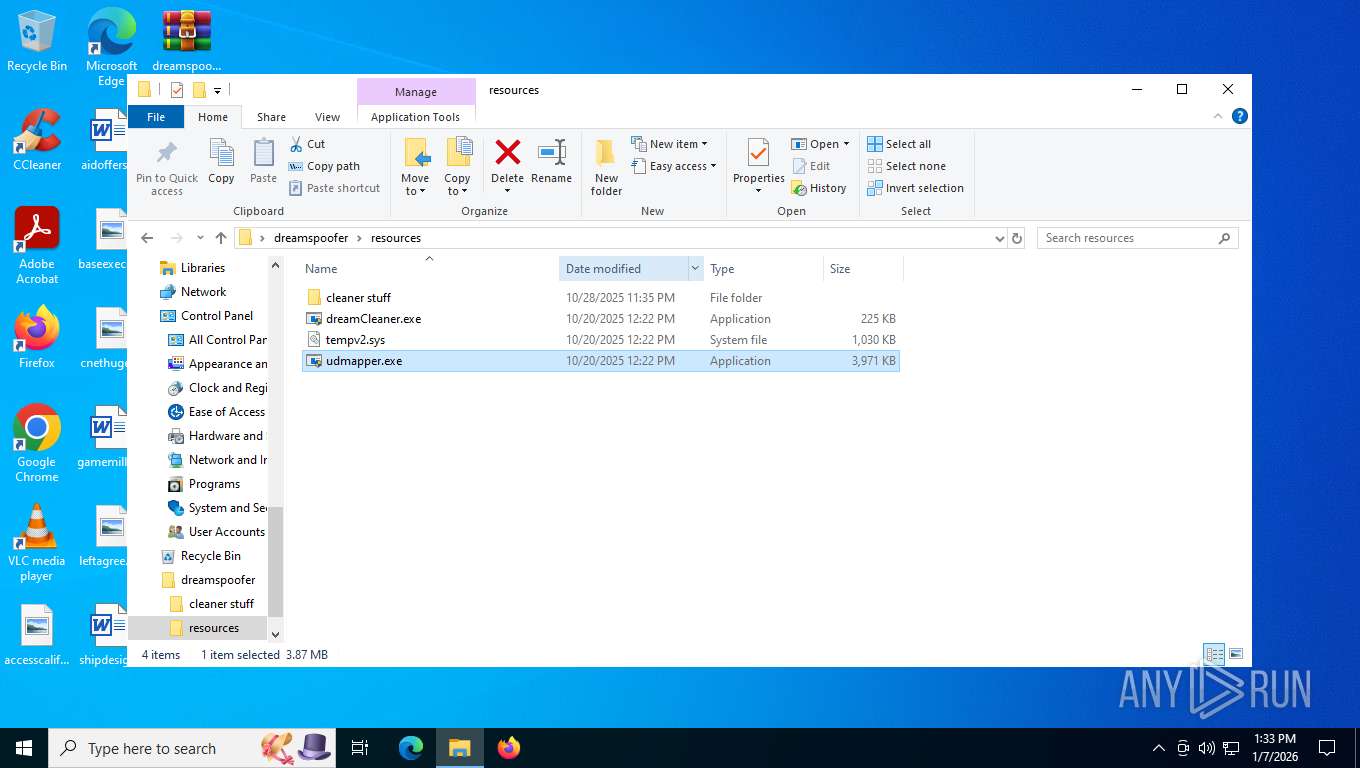
PID | Process | Filename | Type | |
|---|---|---|---|---|
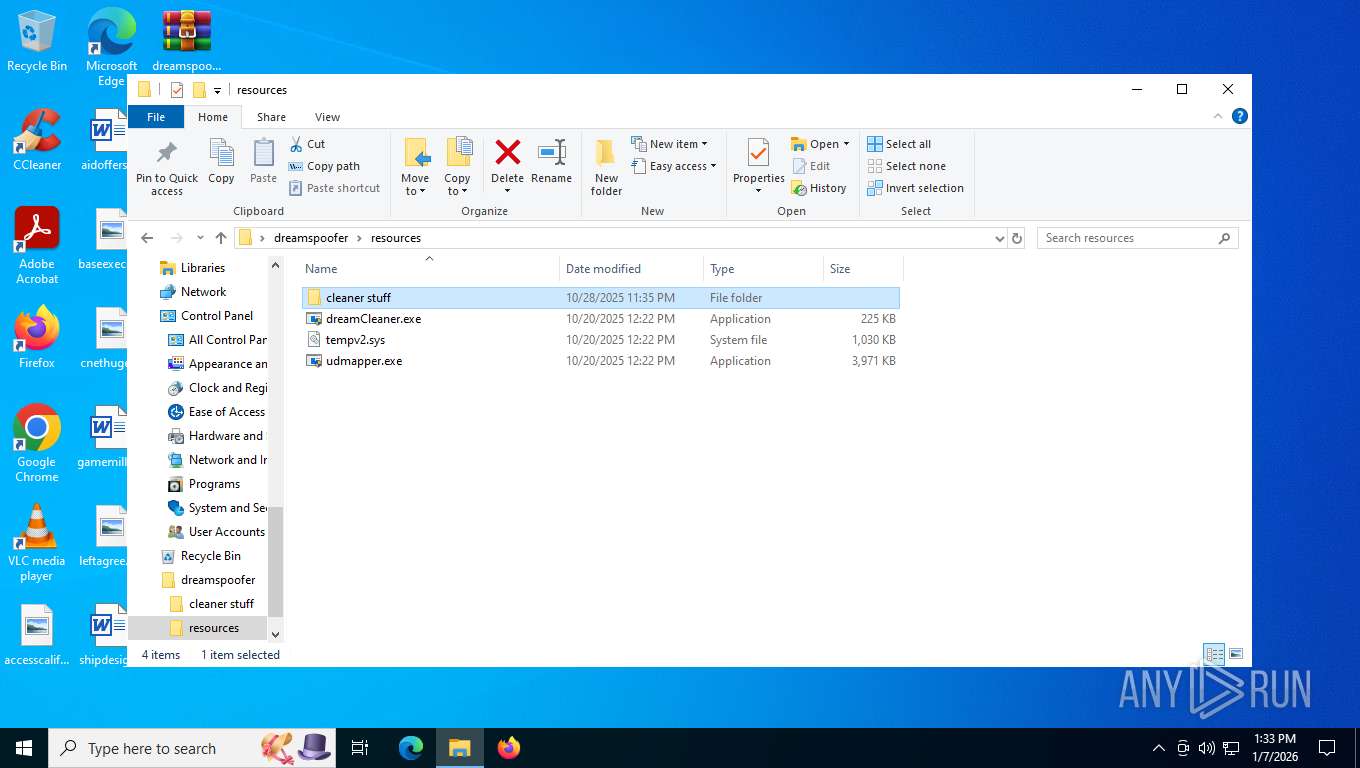
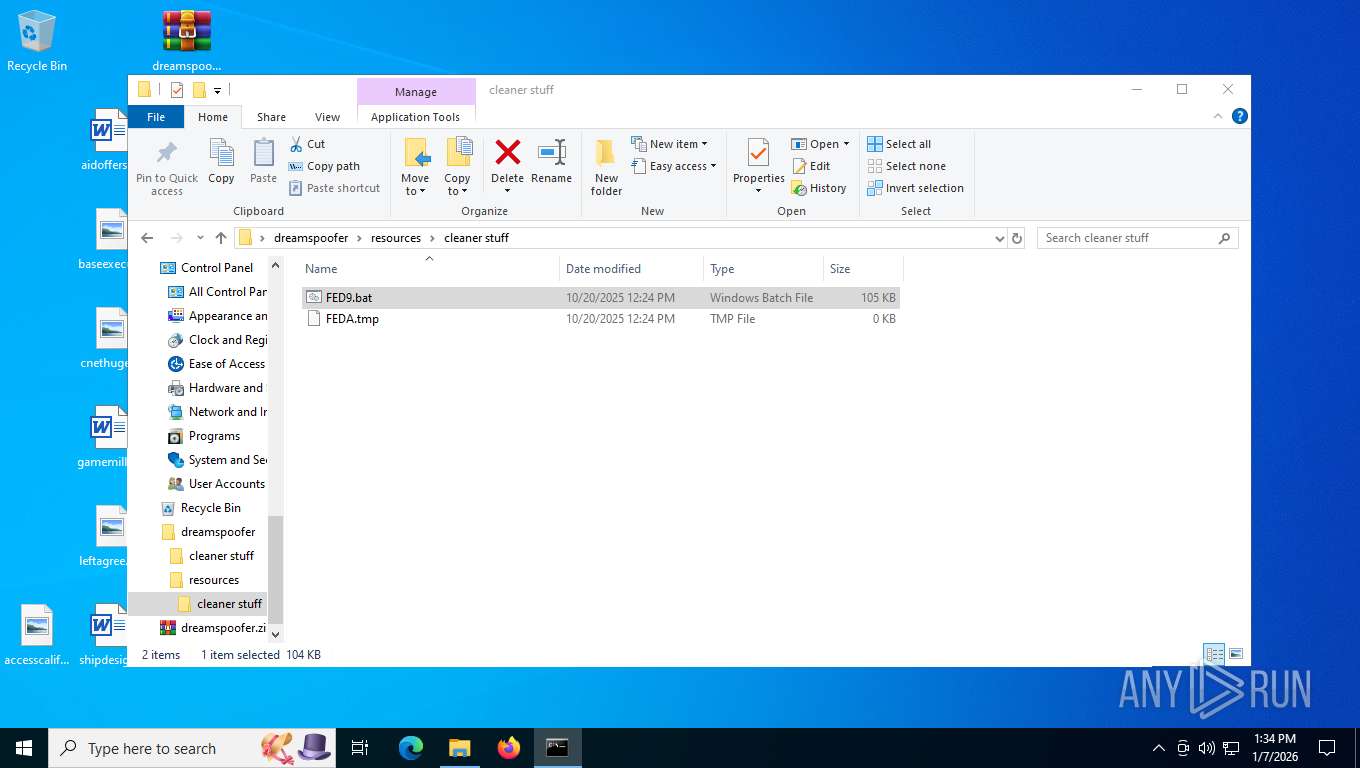
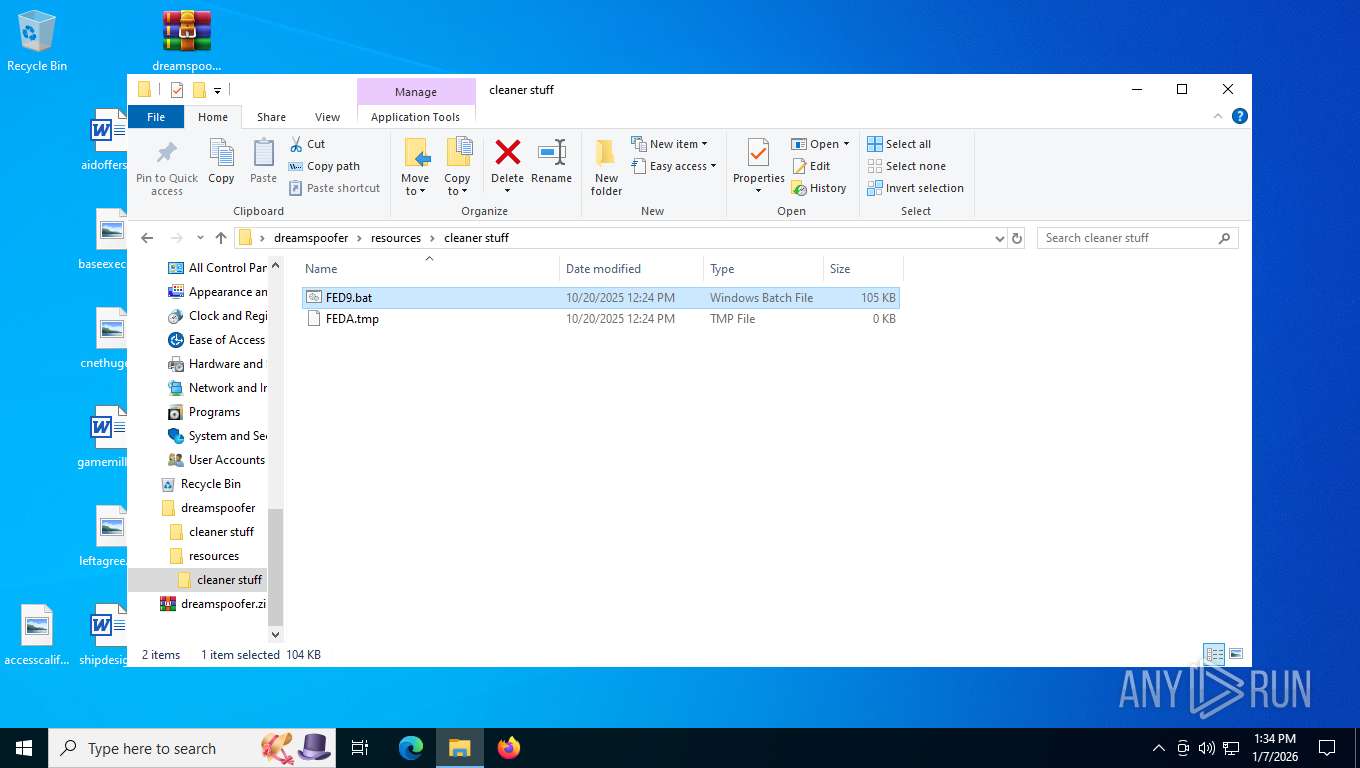
| 7476 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7476.43720\dreamspoofer\resources\cleaner stuff\FED9.bat | text | |
MD5:CBE07887333A77B4B80E15B4421EC6F1 | SHA256:BAE4759483DA860870BFCF32FBF9995BD92096F29C4F8507836A3038D8B2FD7F | |||
| 7476 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7476.43720\dreamspoofer\readme.txt | text | |
MD5:02E8333875507BB872F0AE6476A7DF69 | SHA256:4E8A3F5E2CC44FC230CD3FBF616CCA02D5AA1289A61DDEA930A25A2C87E3562C | |||
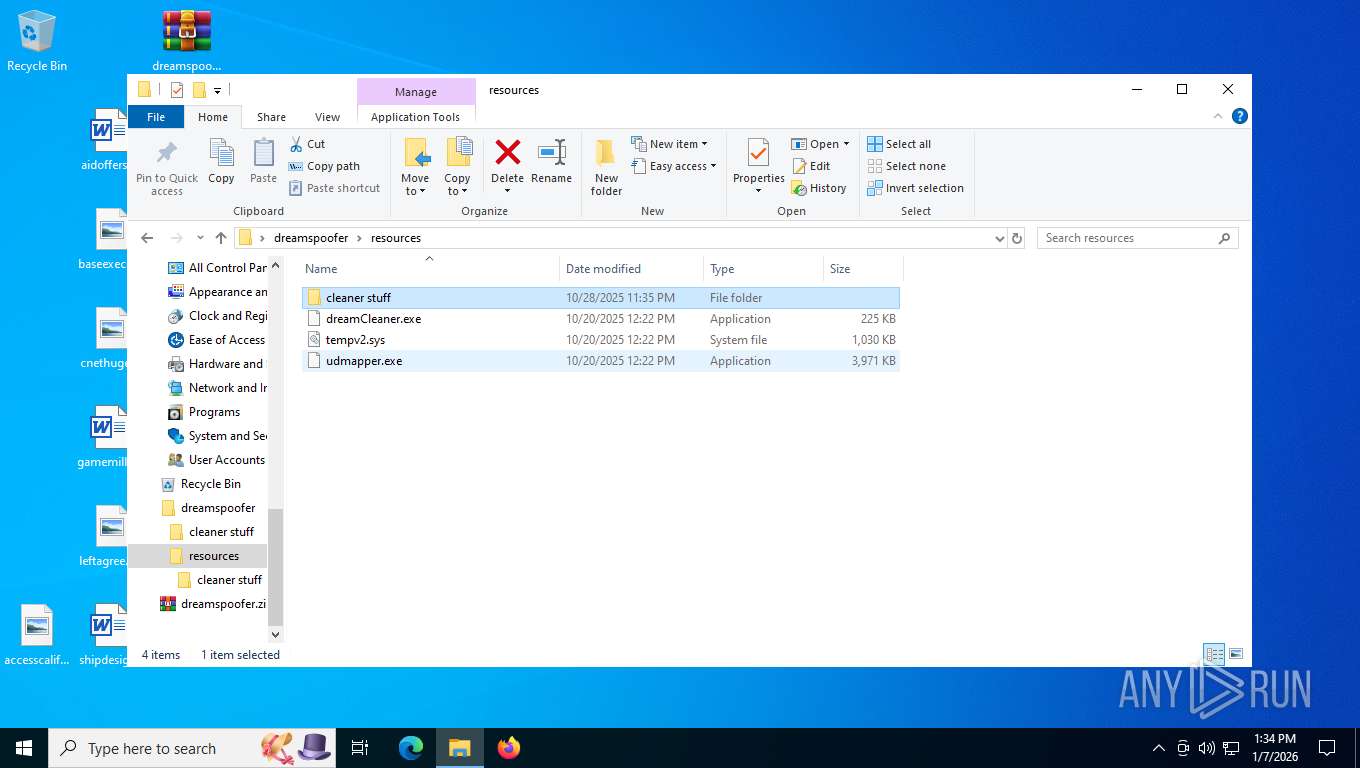
| 7476 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7476.43720\dreamspoofer\udmapper.exe | executable | |
MD5:B7A6AAE627A16E3E67825503C826933F | SHA256:57ED53BA0AC715C8DE18C67EB2E8DC0D04A061208F4A9947FED350E83A5FDA72 | |||
| 7476 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7476.43720\dreamspoofer\resources\dreamCleaner.exe | executable | |
MD5:1C55C014E426A853488CEB2B9E3E1E4C | SHA256:172F6C873B246E71C6ECF1C0FFFB57CA96BC93B7C55046433B4218F514EDDF29 | |||
| 7476 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7476.43720\dreamspoofer\resources\tempv2.sys | executable | |
MD5:1D4A330B99E381728A2F1AA6694BFC1A | SHA256:B395103A618EC58C406EBD3D02FAB1EA312B60F6E6287F94CA8A6BD5BB429470 | |||
| 7476 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7476.43720\dreamspoofer\resources\udmapper.exe | executable | |
MD5:B7A6AAE627A16E3E67825503C826933F | SHA256:57ED53BA0AC715C8DE18C67EB2E8DC0D04A061208F4A9947FED350E83A5FDA72 | |||
| 7476 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7476.43720\dreamspoofer\cleaner stuff\FED9.bat | text | |
MD5:CBE07887333A77B4B80E15B4421EC6F1 | SHA256:BAE4759483DA860870BFCF32FBF9995BD92096F29C4F8507836A3038D8B2FD7F | |||
| 7904 | dreamCleaner.exe | C:\Users\admin\AppData\Local\Temp\9D5.tmp\9D6.tmp\9D7.bat | text | |
MD5:CBE07887333A77B4B80E15B4421EC6F1 | SHA256:BAE4759483DA860870BFCF32FBF9995BD92096F29C4F8507836A3038D8B2FD7F | |||
| 7476 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7476.43720\dreamspoofer\tempv2.sys | executable | |
MD5:1D4A330B99E381728A2F1AA6694BFC1A | SHA256:B395103A618EC58C406EBD3D02FAB1EA312B60F6E6287F94CA8A6BD5BB429470 | |||
| 7476 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7476.43720\dreamspoofer\fixed-decomp.py | text | |
MD5:8EA4434AAE6D379A2A5E1BE42D69F045 | SHA256:44C671DCE0F559A2B9C79964F50927BAFC857605D0CEB62C61BA52C10C5BC26D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
25
DNS requests
18
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6768 | MoUsoCoreWorker.exe | GET | 304 | 51.104.136.2:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | unknown | — | — | whitelisted |
7764 | SIHClient.exe | GET | 200 | 52.165.164.15:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | unknown | — | — | whitelisted |
7764 | SIHClient.exe | GET | 200 | 74.178.76.128:443 | https://slscr.update.microsoft.com/sls/ping | unknown | — | — | whitelisted |
7764 | SIHClient.exe | GET | 304 | 74.178.76.128:443 | https://slscr.update.microsoft.com/SLS/%7BE7A50285-D08D-499D-9FF8-180FDC2332BC%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | whitelisted |
7764 | SIHClient.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | unknown | — | — | whitelisted |
7764 | SIHClient.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | unknown | — | — | whitelisted |
7764 | SIHClient.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.3.crl | unknown | — | — | whitelisted |
7764 | SIHClient.exe | GET | 200 | 184.24.77.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
7764 | SIHClient.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
7764 | SIHClient.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6936 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5304 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
6936 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6936 | svchost.exe | 184.24.77.35:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
6936 | svchost.exe | 23.59.18.102:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
3412 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |