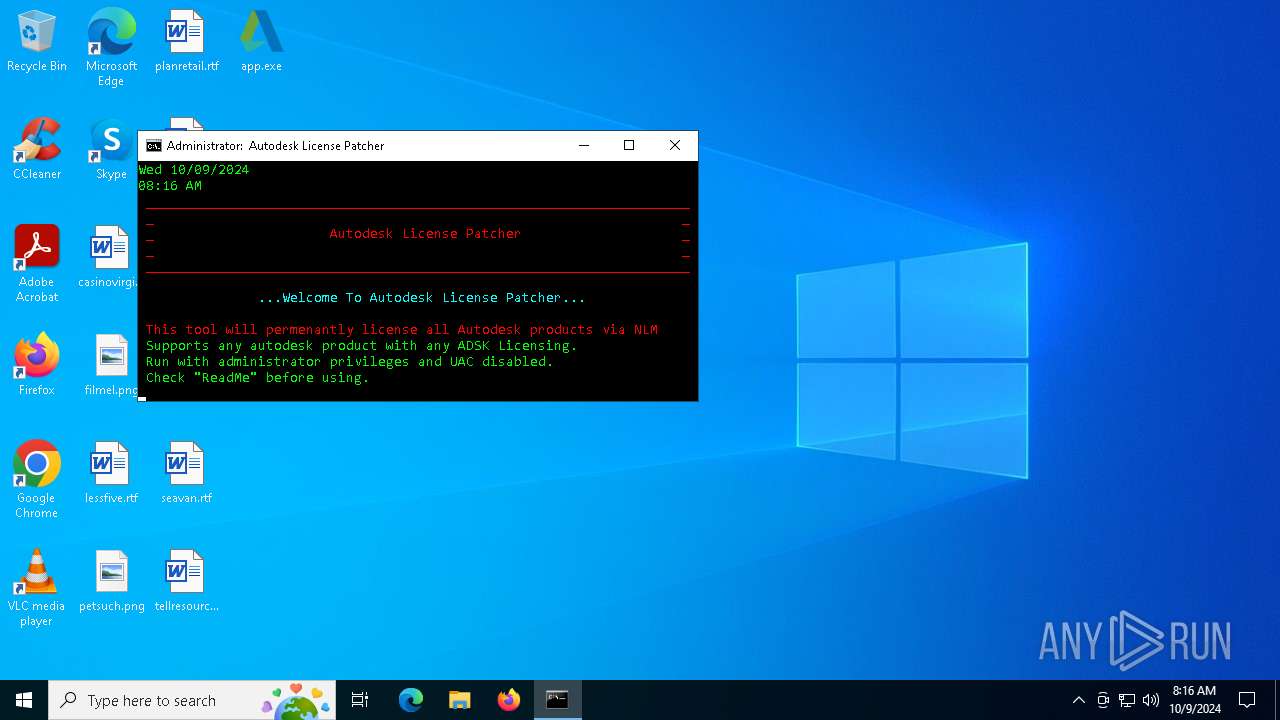
| File name: | app.exe |
| Full analysis: | https://app.any.run/tasks/f3efe2d8-0ca8-499f-b52a-b1f58e9ee2ab |
| Verdict: | Malicious activity |
| Analysis date: | October 09, 2024, 08:15:52 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 58BA20A38C3042D6A13DFEC3C561CFBD |
| SHA1: | EA3A47E6A46B990F6046BD77B96E9D42BDD3A55F |
| SHA256: | AE1FF3A27A9E826DE5B69D0A8C54BB8751DAED10BDD8AC4DD04F2539877B0DB1 |
| SSDEEP: | 24576:Lrr/9x2rDc30x5tUewSFYndCfeI+GajylnGhj9EirEuaXmSmmzpIT1:LH+zxbUJndWeMln8FrmXmSmaIT1 |
MALICIOUS
Starts NET.EXE for service management
- cmd.exe (PID: 5612)
- net.exe (PID: 3580)
Bypass execution policy to execute commands
- powershell.exe (PID: 7056)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 4692)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 5612)
SUSPICIOUS
Executable content was dropped or overwritten
- app.exe (PID: 5592)
- xcopy.exe (PID: 3824)
- xcopy.exe (PID: 6148)
- xcopy.exe (PID: 7000)
- xcopy.exe (PID: 864)
- xcopy.exe (PID: 5328)
- xcopy.exe (PID: 1376)
Reads security settings of Internet Explorer
- app.exe (PID: 5592)
Executing commands from a ".bat" file
- app.exe (PID: 5592)
- cmd.exe (PID: 5932)
Starts application with an unusual extension
- cmd.exe (PID: 5932)
- cmd.exe (PID: 5612)
Starts CMD.EXE for commands execution
- app.exe (PID: 5592)
- cmd.exe (PID: 5932)
- cmd.exe (PID: 5612)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 5932)
- cmd.exe (PID: 5612)
Application launched itself
- cmd.exe (PID: 5932)
- cmd.exe (PID: 5612)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 5612)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 5612)
- cmd.exe (PID: 4692)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 5612)
- cmd.exe (PID: 4692)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 5612)
Process copies executable file
- cmd.exe (PID: 5612)
Probably file/command deobfuscation
- cmd.exe (PID: 4692)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 4692)
- cmd.exe (PID: 5612)
Process uses powershell cmdlet to discover network configuration
- cmd.exe (PID: 4692)
Deletes scheduled task without confirmation
- schtasks.exe (PID: 1336)
INFO
Checks supported languages
- app.exe (PID: 5592)
- mode.com (PID: 5920)
- chcp.com (PID: 3844)
- chcp.com (PID: 944)
- mode.com (PID: 6884)
The process uses the downloaded file
- app.exe (PID: 5592)
- cmd.exe (PID: 5932)
Reads the computer name
- app.exe (PID: 5592)
Process checks computer location settings
- app.exe (PID: 5592)
Changes the display of characters in the console
- cmd.exe (PID: 5932)
- cmd.exe (PID: 5612)
Starts MODE.COM to configure console settings
- mode.com (PID: 5920)
- mode.com (PID: 6884)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:12:31 00:38:38+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 57344 |
| InitializedDataSize: | 176128 |
| UninitializedDataSize: | 258048 |
| EntryPoint: | 0x4cf60 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | Russian |
| CharacterSet: | Unicode |
| CompanyName: | - |
| FileDescription: | - |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| InternalName: | - |
| ProductName: | - |
| OriginalFileName: | - |
| FileVersion: | - |
| ProductVersion: | - |
| Comments: | - |
| PrivateBuild: | - |
| SpecialBuild: | - |
Total processes
175
Monitored processes
46
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 512 | taskkill /F /IM "lmgrd.exe" | C:\Windows\SysWOW64\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 864 | xcopy "C:\AutodeskLicensePatcherInstaller\Files\PatchedFiles\netapi32.dll" "C:\Program Files (x86)\Common Files\Autodesk Shared\AdskLicensing\Current\AdskLicensingAgent\" /Y /K /R /S /H /i | C:\Windows\SysWOW64\xcopy.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Extended Copy Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 944 | chcp 1254 | C:\Windows\SysWOW64\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1172 | Powershell -nop -c "Get-WmiObject -Query ' select * from Win32_Product where Name like \"%Autodesk Network License Manager%\" ' | ForEach-Object { ($_).Uninstall()}" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1336 | schtasks.exe /Delete /tn "\Microsoft\Windows\Autodesk\Autodesk" /f | C:\Windows\SysWOW64\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1376 | xcopy "C:\AutodeskLicensePatcherInstaller\Files\Service\Service.exe" "C:\Program Files (x86)\Common Files\Autodesk Shared\Network License Manager\" /Y /K /R /S /H /i | C:\Windows\SysWOW64\xcopy.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Extended Copy Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1752 | ping 127.0.0.1 -n 5 | C:\Windows\SysWOW64\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2360 | fltmc | C:\Windows\SysWOW64\fltMC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Filter Manager Control Program Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3580 | net stop AdskLicensingService | C:\Windows\SysWOW64\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3676 | ping 127.0.0.1 -n 5 | C:\Windows\SysWOW64\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
17 306
Read events
17 267
Write events
39
Delete events
0
Modification events
| (PID) Process: | (5932) cmd.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\WINDOWS\system32\cmd.exe.FriendlyAppName |
Value: Windows Command Processor | |||
| (PID) Process: | (5932) cmd.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\WINDOWS\system32\cmd.exe.ApplicationCompany |
Value: Microsoft Corporation | |||
| (PID) Process: | (5160) regedit.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Autodesk\MC3 |
| Operation: | write | Name: | OverridedByHKLM |
Value: 0 | |||
| (PID) Process: | (5160) regedit.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Autodesk\MC3 |
| Operation: | write | Name: | ADAOptIn |
Value: 0 | |||
| (PID) Process: | (5160) regedit.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Autodesk\MC3 |
| Operation: | write | Name: | ADARePrompted |
Value: 1 | |||
| (PID) Process: | (5160) regedit.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\FLEXlm License Manager |
| Operation: | write | Name: | ADSKFLEX_LICENSE_FILE |
Value: @LOCALHOST | |||
| (PID) Process: | (5160) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\FLEXlm License Manager |
| Operation: | write | Name: | lmtools_LM_A_DISABLE_ENV |
Value: 1 | |||
| (PID) Process: | (5160) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\FLEXlm License Manager |
| Operation: | write | Name: | Service |
Value: Flexlm Service | |||
| (PID) Process: | (5160) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\FLEXlm License Manager\Flexlm Service |
| Operation: | write | Name: | Lmgrd |
Value: C:\Program Files (x86)\Common Files\Autodesk Shared\Network License Manager\lmgrd.exe | |||
| (PID) Process: | (5160) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\FLEXlm License Manager\Flexlm Service |
| Operation: | write | Name: | LMGRD_LOG_FILE |
Value: C:\ProgramData\FLEXlm\lmgrd\debug.log | |||
Executable files
11
Suspicious files
4
Text files
13
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5592 | app.exe | C:\AutodeskLicensePatcherInstaller\Files\Task\Autodesk.xml | xml | |
MD5:DBFED3FF9DC6CA06E2CF0E2E63098D66 | SHA256:409A178ED9B9C0929FD9F3B8C3A58AFD1B3370C53BAF49B4956CF9A79F50D398 | |||
| 5592 | app.exe | C:\AutodeskLicensePatcherInstaller\Files\Tweak\UnNamed.json | binary | |
MD5:BA3088F87EDFCCEB1E084C971DB40601 | SHA256:E0371582686D18B48EDB9E956057B52AA97DE8C034EE79AAB10FFB5331711651 | |||
| 5592 | app.exe | C:\AutodeskLicensePatcherInstaller\Files\NetworkLicenseManager\lmgrd.exe | executable | |
MD5:219F8CEBEF26F1373062357B2F4A8489 | SHA256:CF025ECFB3556E334DDE501B95485998DE9E1B6A06CCBD56FFA1345D6B5A3973 | |||
| 5592 | app.exe | C:\AutodeskLicensePatcherInstaller\AutodeskLicensePatcherInstaller.bat | text | |
MD5:EE34A40FC63D11A232F59F9AD270C0E8 | SHA256:954F2F867E25511DF30BD119D2714F1DA7B01F49D9391651AA6BEB29B86D7E9D | |||
| 5592 | app.exe | C:\AutodeskLicensePatcherInstaller\Files\NetworkLicenseManager\adskflex.exe | executable | |
MD5:C00B8B7B1C084718EC5D63A53AEFB1EB | SHA256:05B24756D46CE216C84878DDDC97EF9E2EEB6ECA8EC12C97E780C4D0EEF63731 | |||
| 3824 | xcopy.exe | C:\Program Files (x86)\Common Files\Autodesk Shared\Network License Manager\adskflex.exe | executable | |
MD5:C00B8B7B1C084718EC5D63A53AEFB1EB | SHA256:05B24756D46CE216C84878DDDC97EF9E2EEB6ECA8EC12C97E780C4D0EEF63731 | |||
| 5592 | app.exe | C:\AutodeskLicensePatcherInstaller\Files\Service\Service.exe | executable | |
MD5:C944E7122CA3F75139661B05A7985A57 | SHA256:87CF3AFABAC4A8F0881F8C96D5E64B4A8C1A67E05A8351AD9A451C6301FBE5E4 | |||
| 5592 | app.exe | C:\AutodeskLicensePatcherInstaller\Files\Tweak\Tweak.reg | text | |
MD5:2859C8E3C69A5D627C88B6E695EA3A2E | SHA256:C41C2D93CA317CC19AA49C48DCF681D1074DCA34695A061202C202BE62DB3745 | |||
| 5592 | app.exe | C:\AutodeskLicensePatcherInstaller\Files\PatchedFiles\version.dll | executable | |
MD5:51F0E19B4CF164ECBA9A006C4CF3B2A5 | SHA256:6F13E52D797A732435C8BB456BE08C64D0B6FADEA29F85486F4B44559D6CC95F | |||
| 1172 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_irlr3ays.bu3.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
29
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6492 | WmiPrvSE.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | unknown | — | — | whitelisted |
6492 | WmiPrvSE.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEAQJGBtf1btmdVNDtW%2BVUAg%3D | unknown | — | — | whitelisted |
6492 | WmiPrvSE.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicWinProPCA2011_2011-10-19.crl | unknown | — | — | whitelisted |
6492 | WmiPrvSE.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | unknown | — | — | whitelisted |
6492 | WmiPrvSE.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
6492 | WmiPrvSE.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSnR4FoxLLkI7vkvsUIFlZt%2BlGH3gQUWsS5eyoKo6XqcQPAYPkt9mV1DlgCEAwVvkoVuwkDyQGx1sJlMC8%3D | unknown | — | — | whitelisted |
6492 | WmiPrvSE.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
6492 | WmiPrvSE.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEA5EGOLe3jbdKXTDRDr7XOU%3D | unknown | — | — | whitelisted |
6492 | WmiPrvSE.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSnR4FoxLLkI7vkvsUIFlZt%2BlGH3gQUWsS5eyoKo6XqcQPAYPkt9mV1DlgCEAkQWITrlZ07yLmU%2BRintu4%3D | unknown | — | — | whitelisted |
6492 | WmiPrvSE.exe | GET | 200 | 2.16.164.49:80 | http://crl.microsoft.com/pki/crl/products/MicCodSigPCA_08-31-2010.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6944 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2660 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5488 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.23.209.164:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
6944 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4020 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |