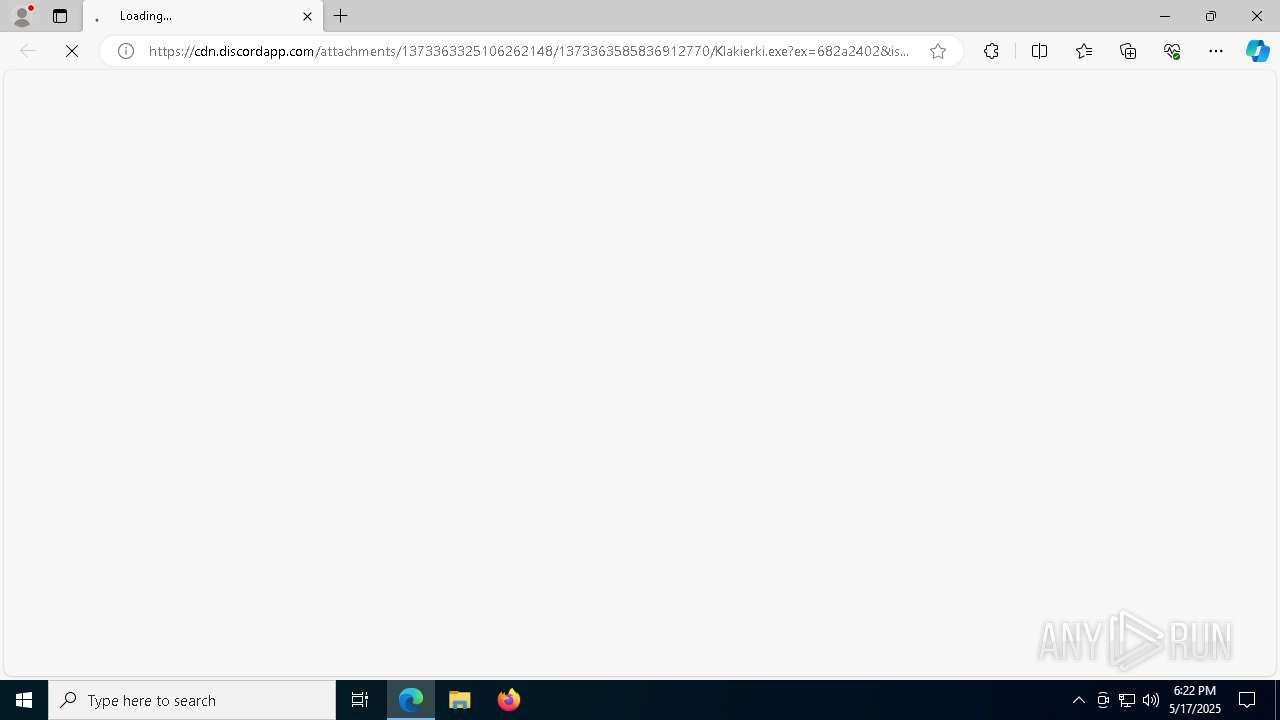
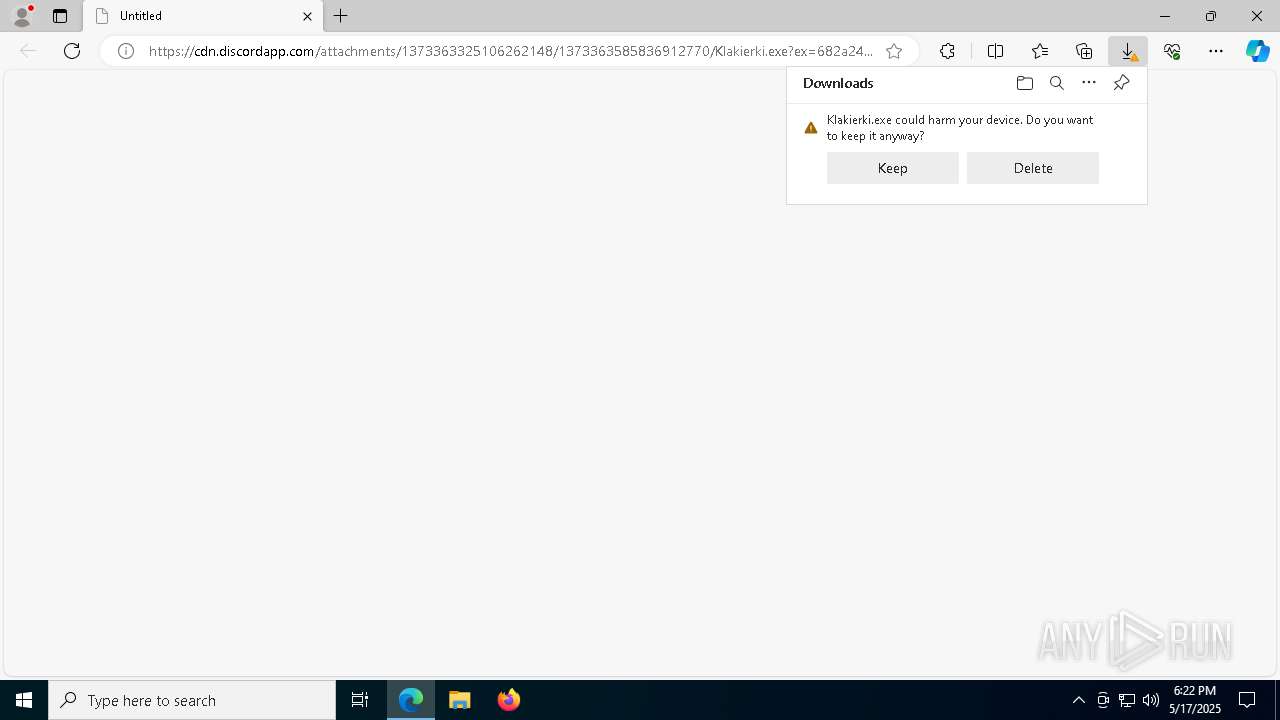
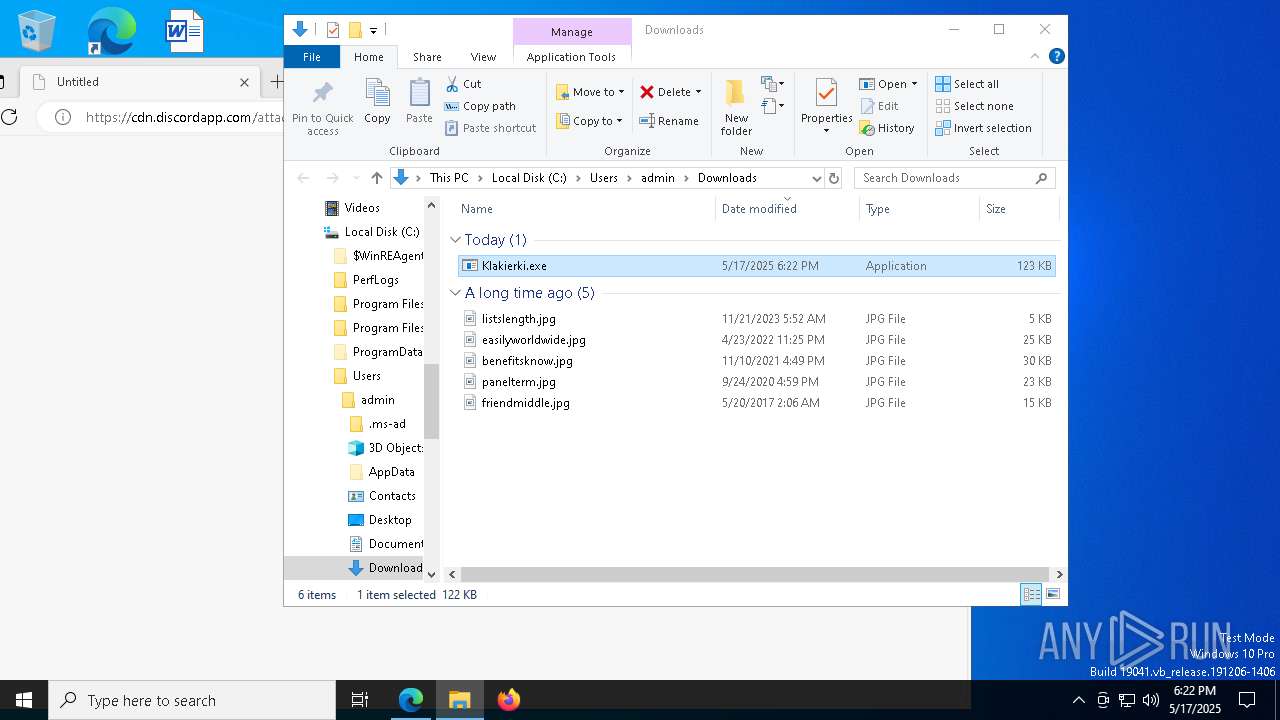
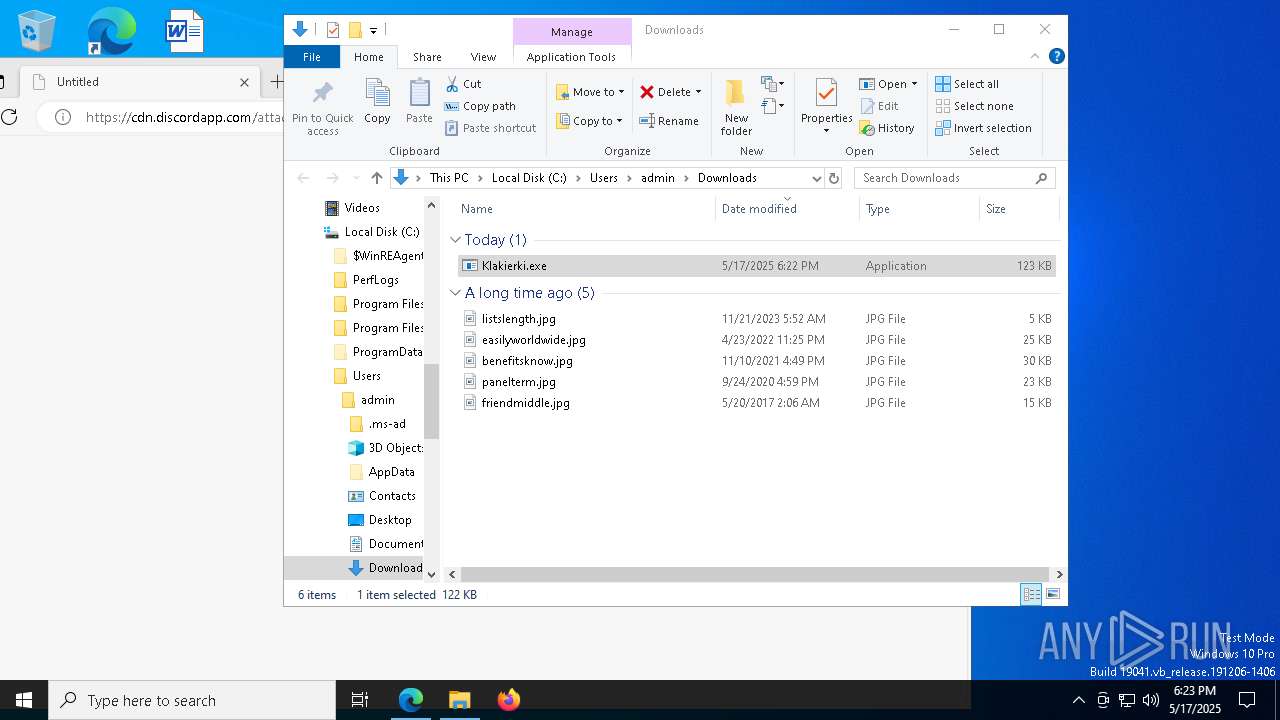
| URL: | https://cdn.discordapp.com/attachments/1373363325106262148/1373363585836912770/Klakierki.exe?ex=682a2402&is=6828d282&hm=d5db09493994521e91ba1a0f283a8ff3884c8c4fd0e84b221bfc057ef1559b3c& |
| Full analysis: | https://app.any.run/tasks/08d9c748-7f33-42c7-9ebd-f63b59f7f69d |
| Verdict: | Malicious activity |
| Analysis date: | May 17, 2025, 18:22:23 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 84CDB97EA3C4E9BD40D91611C55DA646 |
| SHA1: | ABCB18E08638FD1A60CA5596C6D086CA9FF41294 |
| SHA256: | AE149A454E3DCB58D41F38F1E717A090879380E68007526B3124FCC321E831D5 |
| SSDEEP: | 3:N8cCWdy6//PSxuIU81UhnnhObC2oTSNBHQQRncVEAlHEUSNDd+ddrKRlMQmn:2cry6XPSxu+1unYbUTSNBHH9sETNBKKU |
MALICIOUS
No malicious indicators.SUSPICIOUS
Discord domain found in command line (probably downloading payload)
- msedge.exe (PID: 7464)
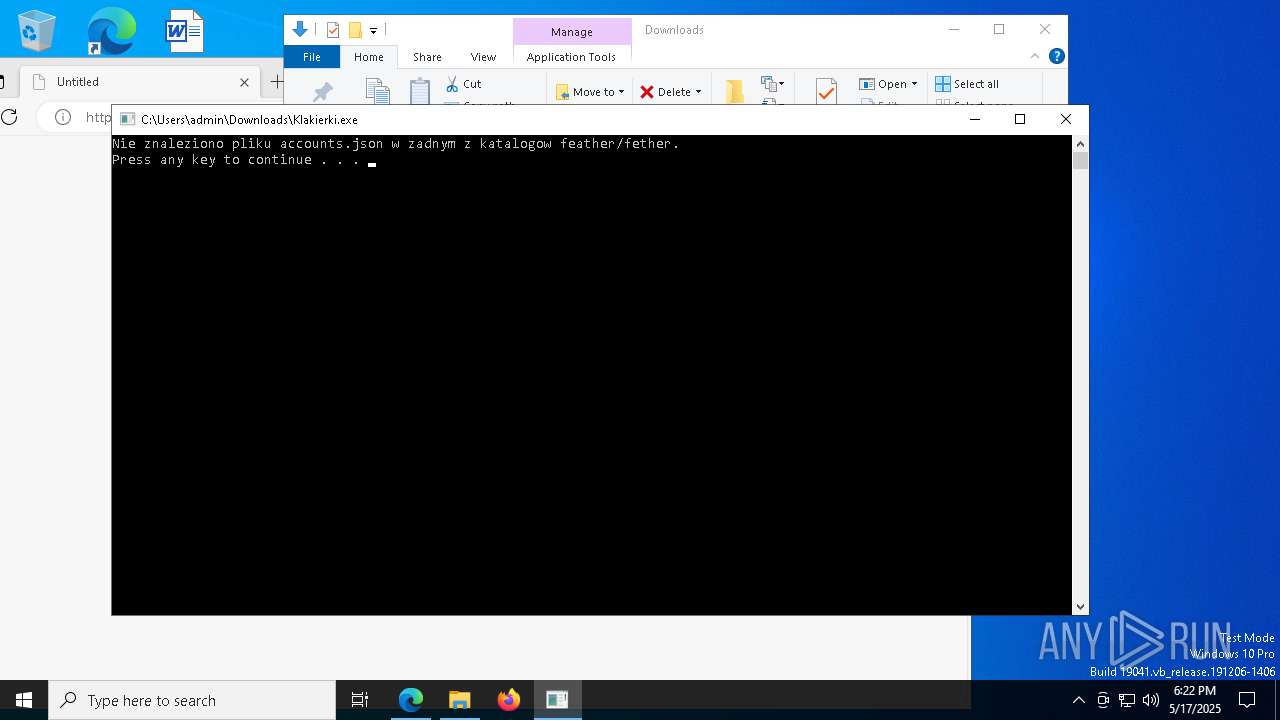
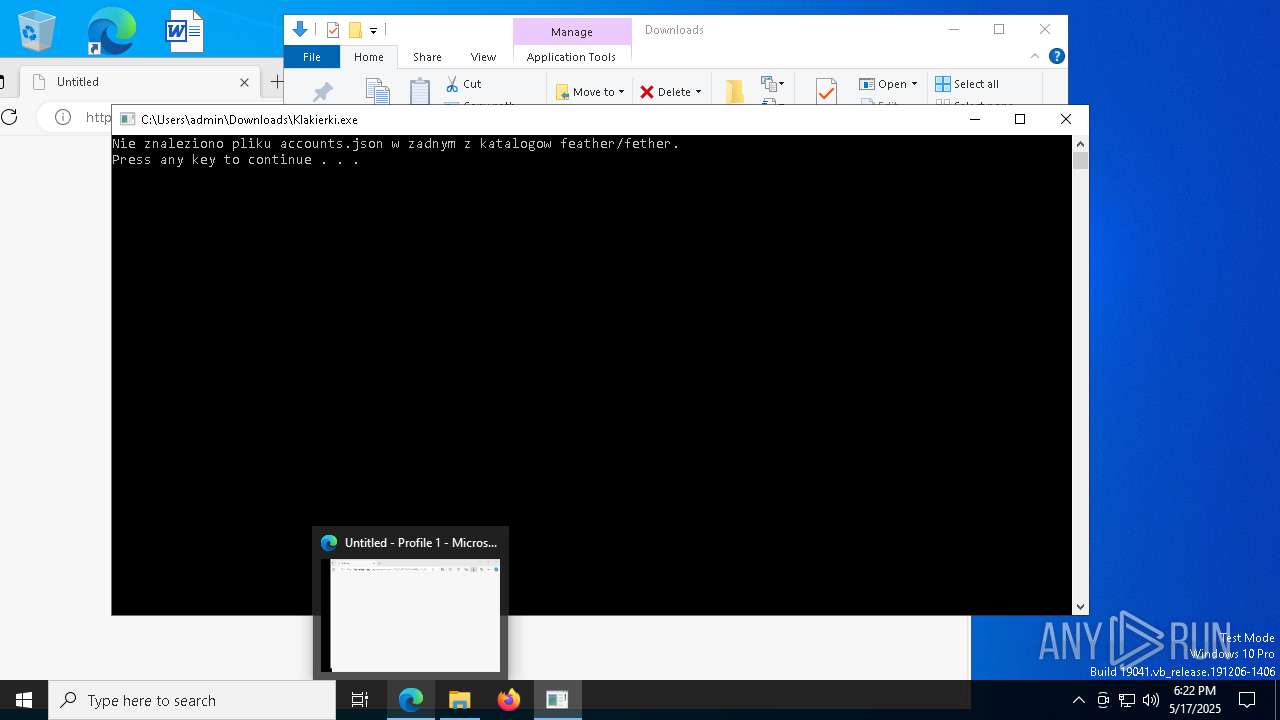
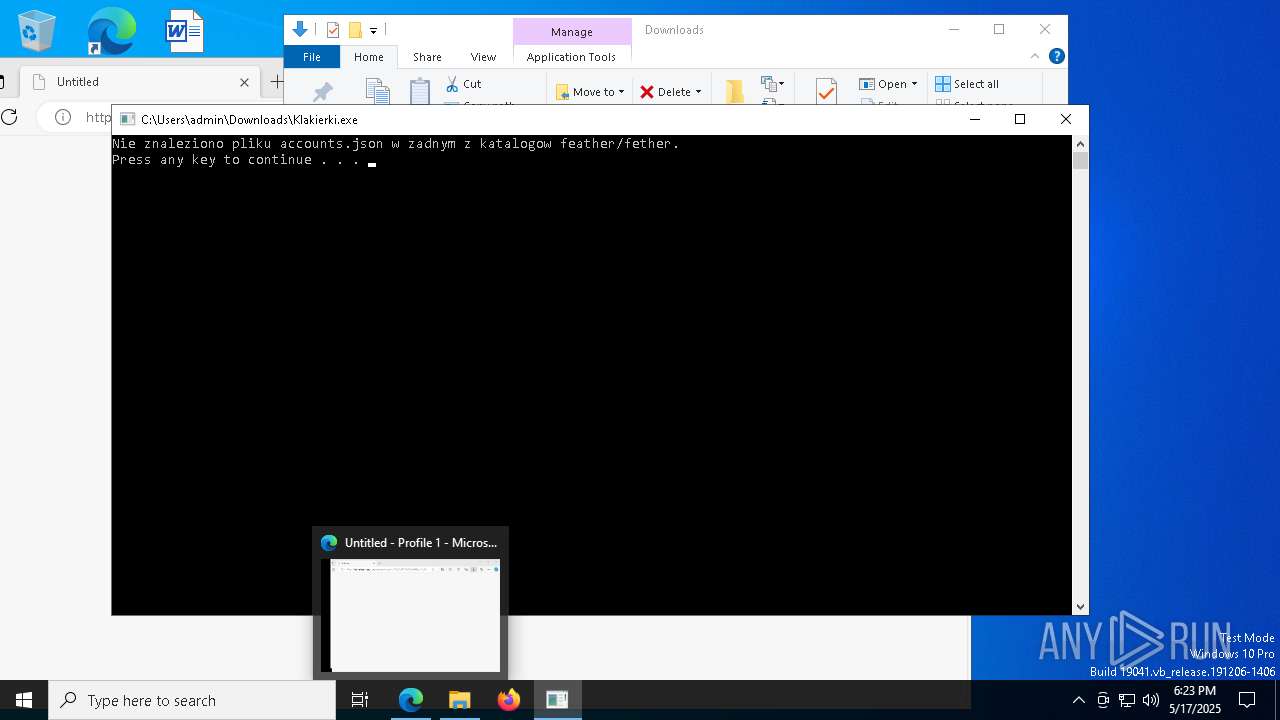
Executing commands from a ".bat" file
- Klakierki.exe (PID: 864)
Starts CMD.EXE for commands execution
- Klakierki.exe (PID: 864)
Possible usage of Discord/Telegram API has been detected (YARA)
- cmd.exe (PID: 1056)
- Klakierki.exe (PID: 864)
INFO
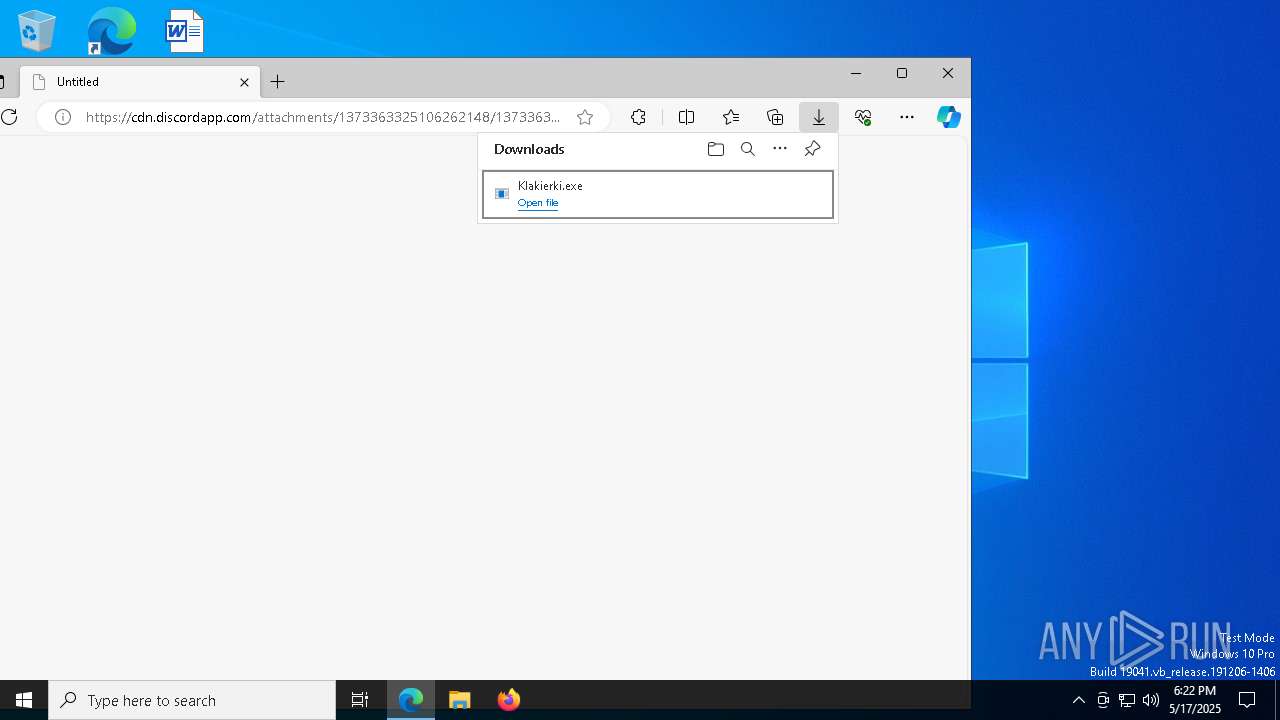
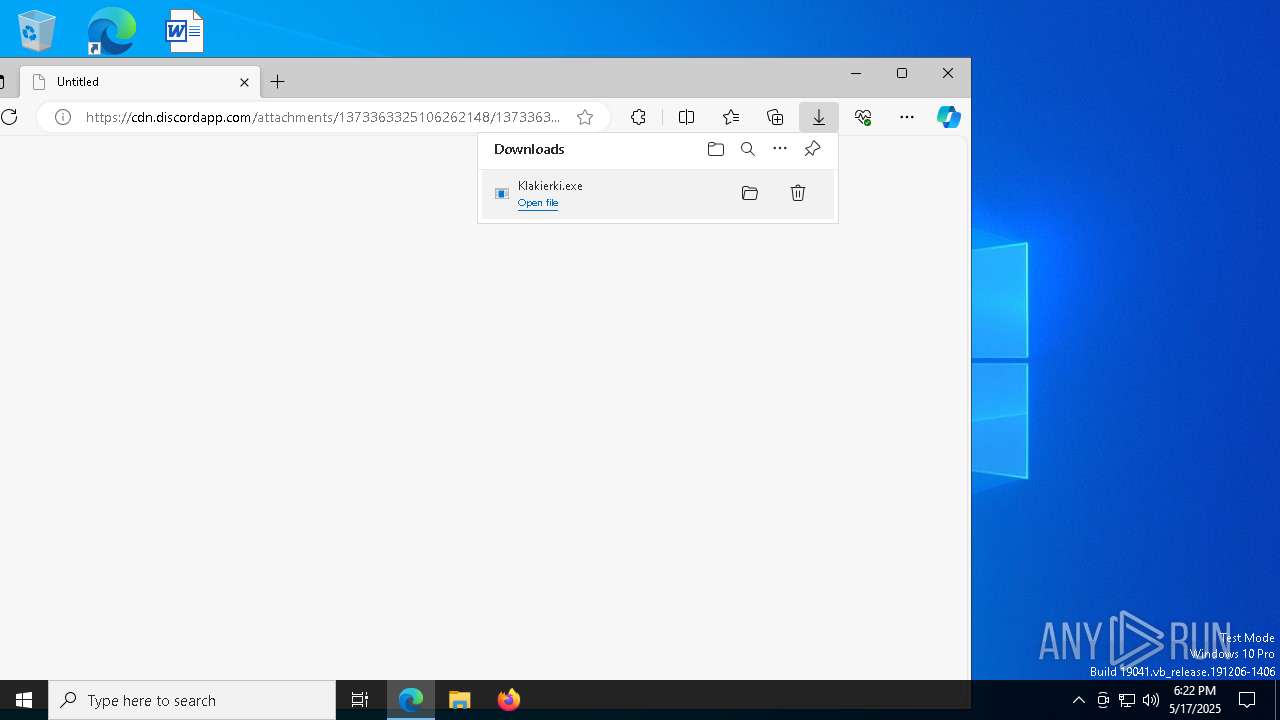
Executable content was dropped or overwritten
- msedge.exe (PID: 7752)
- msedge.exe (PID: 7464)
Checks supported languages
- identity_helper.exe (PID: 8612)
- Klakierki.exe (PID: 864)
Reads Environment values
- identity_helper.exe (PID: 8612)
Application launched itself
- msedge.exe (PID: 7464)
Reads the computer name
- identity_helper.exe (PID: 8612)
Attempting to use instant messaging service
- msedge.exe (PID: 7752)
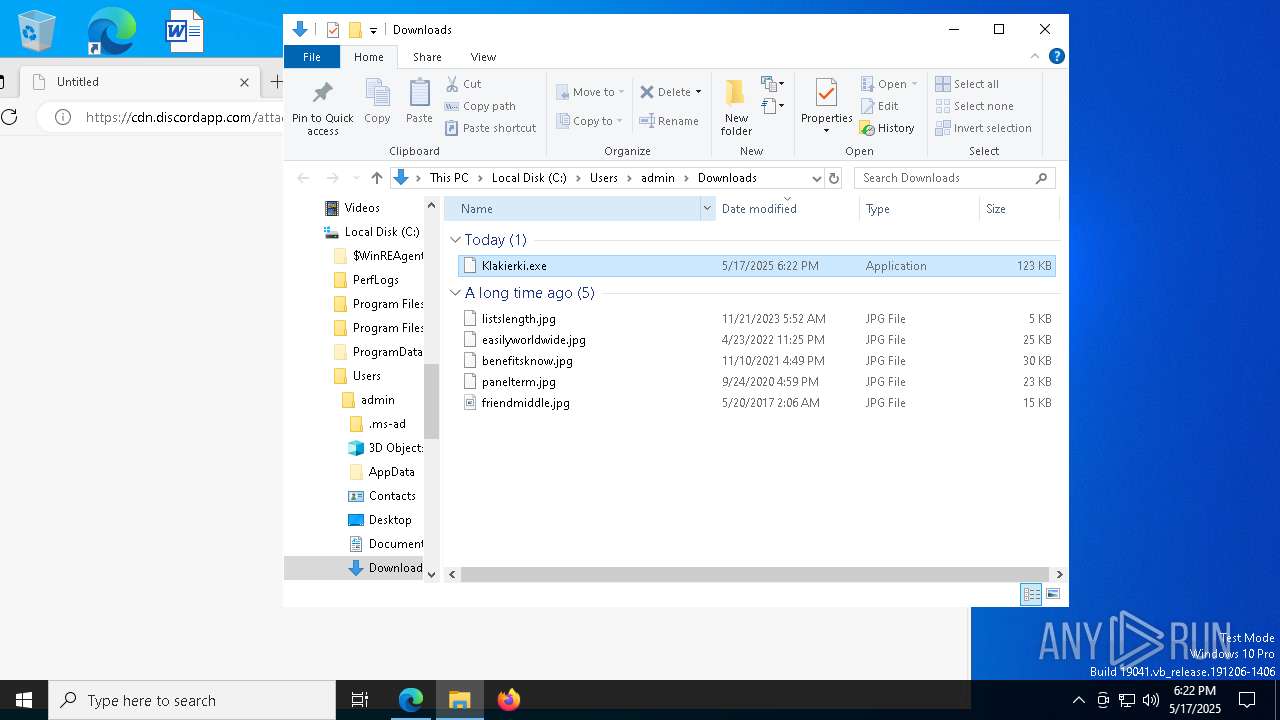
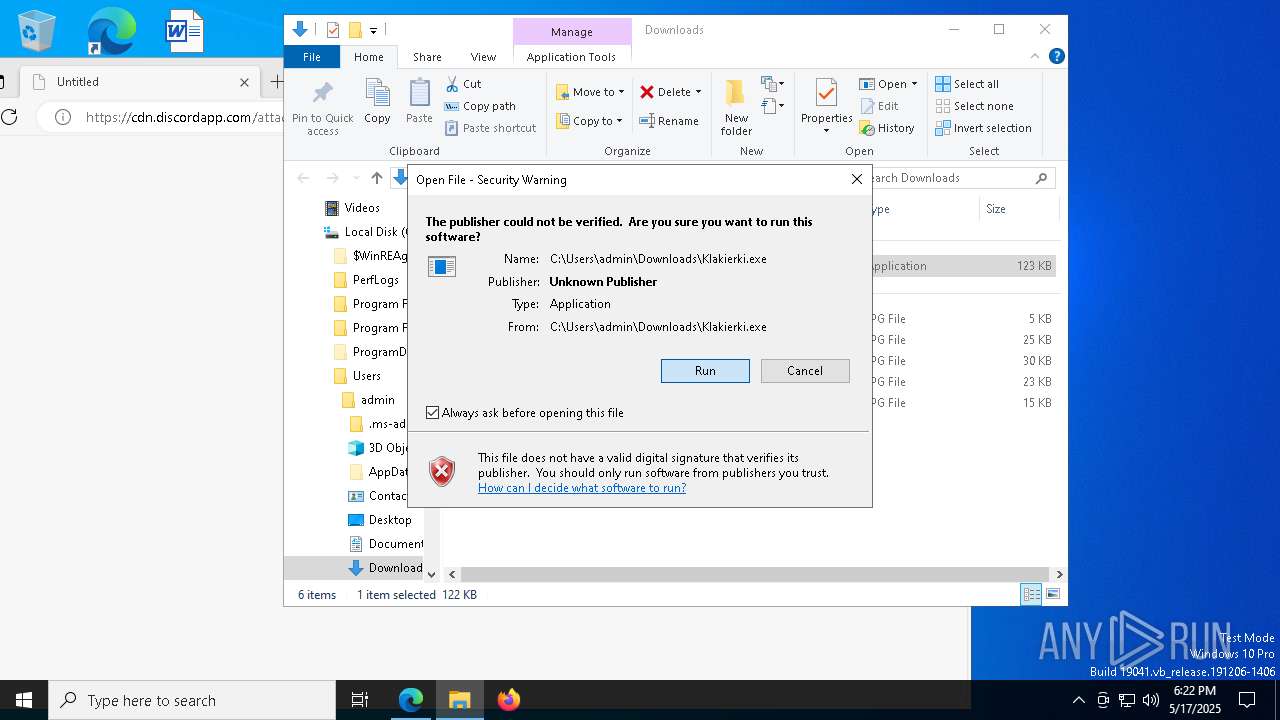
Manual execution by a user
- Klakierki.exe (PID: 864)
Create files in a temporary directory
- Klakierki.exe (PID: 864)
Checks proxy server information
- slui.exe (PID: 4180)
Reads the software policy settings
- slui.exe (PID: 4180)
- slui.exe (PID: 8528)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
ims-api
(PID) Process(864) Klakierki.exe
Discord-Webhook-Tokens (1)1371054433726758942/RjhunR6mCPXI2TrpI9_JYaY556spzJccqeSVYRyNgyk6MIltak-mPetKWw-1ke5zbs6D
Discord-Info-Links
1371054433726758942/RjhunR6mCPXI2TrpI9_JYaY556spzJccqeSVYRyNgyk6MIltak-mPetKWw-1ke5zbs6D
Get Webhook Infohttps://discord.com/api/webhooks/1371054433726758942/RjhunR6mCPXI2TrpI9_JYaY556spzJccqeSVYRyNgyk6MIltak-mPetKWw-1ke5zbs6D
(PID) Process(1056) cmd.exe
Discord-Webhook-Tokens (1)1371054433726758942/RjhunR6mCPXI2TrpI9_JYaY556spzJccqeSVYRyNgyk6MIltak-mPetKWw-1ke5zbs6D
Discord-Info-Links
1371054433726758942/RjhunR6mCPXI2TrpI9_JYaY556spzJccqeSVYRyNgyk6MIltak-mPetKWw-1ke5zbs6D
Get Webhook Infohttps://discord.com/api/webhooks/1371054433726758942/RjhunR6mCPXI2TrpI9_JYaY556spzJccqeSVYRyNgyk6MIltak-mPetKWw-1ke5zbs6D
Total processes
180
Monitored processes
47
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 864 | "C:\Users\admin\Downloads\Klakierki.exe" | C:\Users\admin\Downloads\Klakierki.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
ims-api(PID) Process(864) Klakierki.exe Discord-Webhook-Tokens (1)1371054433726758942/RjhunR6mCPXI2TrpI9_JYaY556spzJccqeSVYRyNgyk6MIltak-mPetKWw-1ke5zbs6D Discord-Info-Links 1371054433726758942/RjhunR6mCPXI2TrpI9_JYaY556spzJccqeSVYRyNgyk6MIltak-mPetKWw-1ke5zbs6D Get Webhook Infohttps://discord.com/api/webhooks/1371054433726758942/RjhunR6mCPXI2TrpI9_JYaY556spzJccqeSVYRyNgyk6MIltak-mPetKWw-1ke5zbs6D | |||||||||||||||
| 1056 | "C:\WINDOWS\system32\cmd" /c "C:\Users\admin\AppData\Local\Temp\FFAF.tmp\FFB0.tmp\FFB1.bat C:\Users\admin\Downloads\Klakierki.exe" | C:\Windows\System32\cmd.exe | Klakierki.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
ims-api(PID) Process(1056) cmd.exe Discord-Webhook-Tokens (1)1371054433726758942/RjhunR6mCPXI2TrpI9_JYaY556spzJccqeSVYRyNgyk6MIltak-mPetKWw-1ke5zbs6D Discord-Info-Links 1371054433726758942/RjhunR6mCPXI2TrpI9_JYaY556spzJccqeSVYRyNgyk6MIltak-mPetKWw-1ke5zbs6D Get Webhook Infohttps://discord.com/api/webhooks/1371054433726758942/RjhunR6mCPXI2TrpI9_JYaY556spzJccqeSVYRyNgyk6MIltak-mPetKWw-1ke5zbs6D | |||||||||||||||
| 1116 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Klakierki.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1196 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2384 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6096 --field-trial-handle=2380,i,3869308054080739892,176374734156830257,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3888 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6760 --field-trial-handle=2380,i,3869308054080739892,176374734156830257,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4180 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4188 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=900 --field-trial-handle=2380,i,3869308054080739892,176374734156830257,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4448 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --no-appcompat-clear --mojo-platform-channel-handle=4136 --field-trial-handle=2380,i,3869308054080739892,176374734156830257,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4696 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6508 --field-trial-handle=2380,i,3869308054080739892,176374734156830257,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
6 624
Read events
6 611
Write events
13
Delete events
0
Modification events
| (PID) Process: | (7464) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7464) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7464) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7464) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7464) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: F4AFBA43EF932F00 | |||
| (PID) Process: | (7464) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: CB99C643EF932F00 | |||
| (PID) Process: | (7464) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328338 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {2F581F9A-52CC-4525-8973-F82C6ADA7330} | |||
| (PID) Process: | (7464) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 9443FE43EF932F00 | |||
| (PID) Process: | (7464) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
| (PID) Process: | (7464) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\Profiles |
| Operation: | write | Name: | EnhancedLinkOpeningDefault |
Value: Default | |||
Executable files
11
Suspicious files
178
Text files
49
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7464 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b7d8.TMP | — | |
MD5:— | SHA256:— | |||
| 7464 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7464 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b7e8.TMP | — | |
MD5:— | SHA256:— | |||
| 7464 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b7e8.TMP | — | |
MD5:— | SHA256:— | |||
| 7464 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7464 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7464 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b7f7.TMP | — | |
MD5:— | SHA256:— | |||
| 7464 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7464 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b7f7.TMP | — | |
MD5:— | SHA256:— | |||
| 7464 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
29
TCP/UDP connections
54
DNS requests
64
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.171:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2600 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2600 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8948 | svchost.exe | HEAD | 200 | 208.89.74.21:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1747803060&P2=404&P3=2&P4=fCZdco5KzMeaWmWGCzlCC0%2fRnmc6TcCW28KK%2f1wqPTkdQo5NiWPglP6NIj6wzWsXL8a%2fPnAXSXj%2b0t8h%2fJMy%2fQ%3d%3d | unknown | — | — | whitelisted |
8948 | svchost.exe | GET | 206 | 208.89.74.21:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1747803060&P2=404&P3=2&P4=fCZdco5KzMeaWmWGCzlCC0%2fRnmc6TcCW28KK%2f1wqPTkdQo5NiWPglP6NIj6wzWsXL8a%2fPnAXSXj%2b0t8h%2fJMy%2fQ%3d%3d | unknown | — | — | whitelisted |
8948 | svchost.exe | HEAD | 200 | 208.89.74.21:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1747803061&P2=404&P3=2&P4=Hx9Ti9uNAmmilkvGrDgKa6yADO5DRMkOshgWHsN3tRGzF0TgYaLdWBglkOjKdUwSfqkLApAdlOiwzqTn%2fEtC3g%3d%3d | unknown | — | — | whitelisted |
8948 | svchost.exe | GET | 206 | 208.89.74.21:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1747803060&P2=404&P3=2&P4=fCZdco5KzMeaWmWGCzlCC0%2fRnmc6TcCW28KK%2f1wqPTkdQo5NiWPglP6NIj6wzWsXL8a%2fPnAXSXj%2b0t8h%2fJMy%2fQ%3d%3d | unknown | — | — | whitelisted |
8948 | svchost.exe | GET | 206 | 208.89.74.21:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1747803061&P2=404&P3=2&P4=Hx9Ti9uNAmmilkvGrDgKa6yADO5DRMkOshgWHsN3tRGzF0TgYaLdWBglkOjKdUwSfqkLApAdlOiwzqTn%2fEtC3g%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.48.23.171:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7464 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7752 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7752 | msedge.exe | 162.159.133.233:443 | cdn.discordapp.com | — | — | whitelisted |
7752 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
cdn.discordapp.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
edgeservices.bing.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7752 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
7752 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |