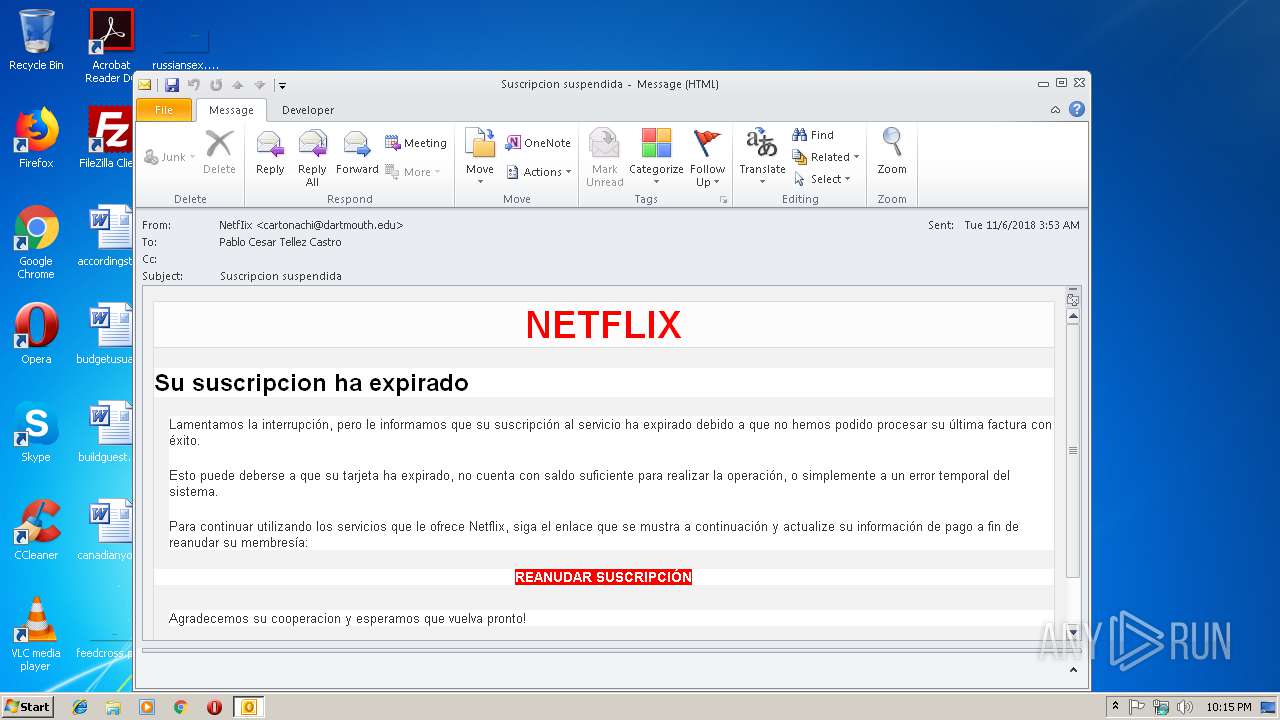
| File name: | Suscripcion suspendida (758 KB).msg |
| Full analysis: | https://app.any.run/tasks/179ed7a6-6f04-4947-bd25-e2887450b8f0 |
| Verdict: | Malicious activity |
| Analysis date: | November 08, 2018, 22:14:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | B639938B4C90DBF7F71C167CCF6774EC |
| SHA1: | F052AEA17394E1EFD5D9EF6FF79DB116235599FA |
| SHA256: | AE1477F93C1E60B0804D00A60DE88F0133B30FCC88E9A2E40142DD8D6E3E3E6F |
| SSDEEP: | 384:rrAO1RSWj2DXYhG60zad6T7RKJhOt6/UQtZS/5:rsOHbSXYhG6jd6T7RrA/UQta5 |
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 3644)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 3644)
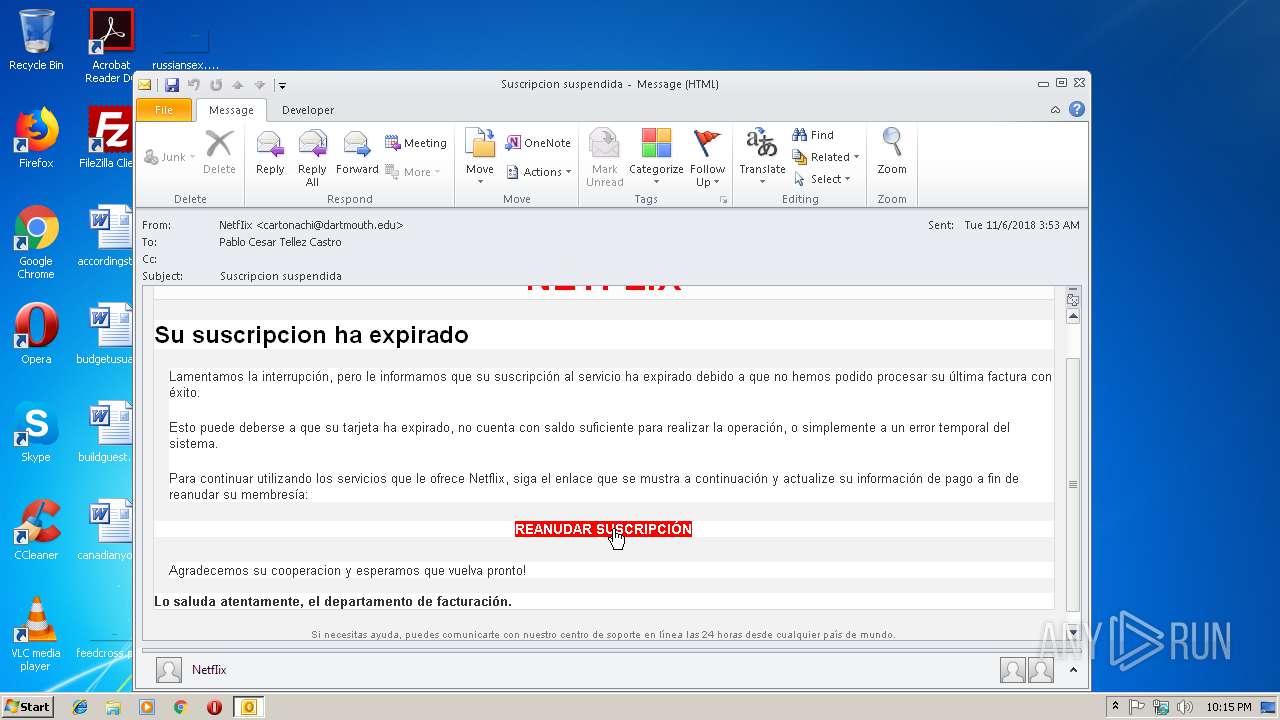
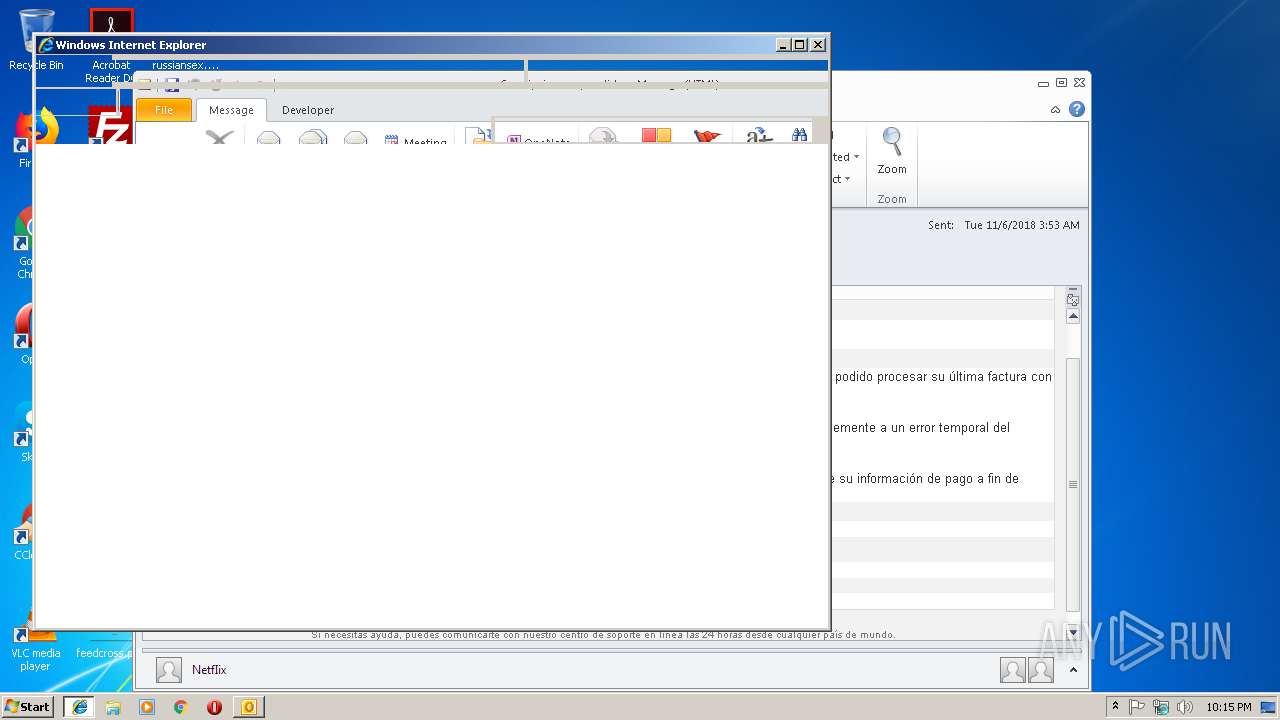
Starts Internet Explorer
- OUTLOOK.EXE (PID: 3644)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 2012)
Changes internet zones settings
- iexplore.exe (PID: 2588)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3644)
Reads internet explorer settings
- iexplore.exe (PID: 2012)
Application launched itself
- iexplore.exe (PID: 2588)
Creates files in the user directory
- iexplore.exe (PID: 2012)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
34
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2012 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2588 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
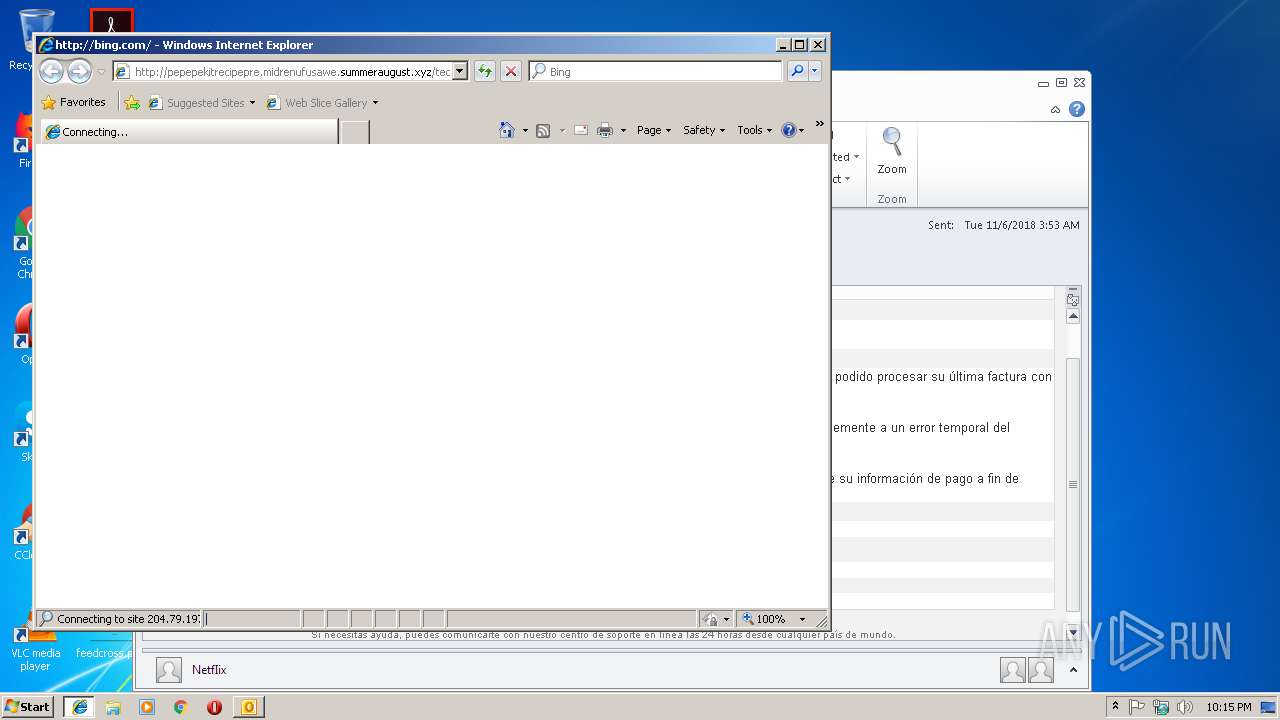
| 2588 | "C:\Program Files\Internet Explorer\iexplore.exe" http://pepepekitrecipepre.midrenufusawe.summeraugust.xyz/tedroprequecruwe/ikNWevE4 | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3644 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Suscripcion suspendida (758 KB).msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
Total events
1 668
Read events
1 195
Write events
451
Delete events
22
Modification events
| (PID) Process: | (3644) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3644) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3644) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | k"& |
Value: 6B2226003C0E0000010000000000000000000000 | |||
| (PID) Process: | (3644) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: 3C0E00004EB04C7FB077D40100000000 | |||
| (PID) Process: | (3644) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (3644) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 219768480 | |||
| (PID) Process: | (3644) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (3644) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (3644) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (3644) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1298661397 | |||
Executable files
0
Suspicious files
0
Text files
47
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3644 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR2EEB.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2588 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2588 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2012 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@bing[2].txt | — | |
MD5:— | SHA256:— | |||
| 2012 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\bing_com[1].txt | — | |
MD5:— | SHA256:— | |||
| 2588 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\0UU90R59\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2012 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\BWPPCY0O\render[1].txt | — | |
MD5:— | SHA256:— | |||
| 2012 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@bing[1].txt | text | |
MD5:— | SHA256:— | |||
| 3644 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3644 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_Calendar_2_7CA00B42382CC749BD7ACCBDDB1B0986.dat | xml | |
MD5:B21ED3BD946332FF6EBC41A87776C6BB | SHA256:B1AAC4E817CD10670B785EF8E5523C4A883F44138E50486987DC73054A46F6F4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
13
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2012 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/az/hprichbg/rb/ManateeAwareness_EN-GB8913276028_1920x1080.jpg | US | image | 339 Kb | whitelisted |
2012 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/fd/ls/l?IG=6760003EEB7B4772875E54C8CF96D040&CID=0F5F1C89197669E726C51028189A68B7&Type=Event.CPT&DATA={"pp":{"S":"L","FC":-1,"BC":-1,"SE":-1,"TC":-1,"H":390,"BP":5234,"CT":5250,"IL":1},"ad":[-1,-1,772,444,772,444,0]}&P=SERP&DA=DB5 | US | image | 339 Kb | whitelisted |
2012 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/2W/1N/cj,nj/9cdb352b/ff9070db.js | US | text | 841 b | whitelisted |
2012 | iexplore.exe | GET | 301 | 204.79.197.200:80 | http://bing.com/ | US | — | — | whitelisted |
2012 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rb/14/cj,nj/1b7dfb88/cc8437ad.js?bu=DikuWWltcWVdYaoBrgEungEu | US | text | 7.54 Kb | whitelisted |
2588 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2012 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rs/2W/23/cj,nj/4c7364c5/40e1b425.js | US | text | 816 b | whitelisted |
2012 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/az/hprichbg/rb/ManateeAwareness_EN-GB8913276028_1920x1080.jpg | US | image | 339 Kb | whitelisted |
2012 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rms/BingCore.Bundle/cj,nj/3e6a7d75/9a358300.js?bu=rms+answers+Shared+BingCore%24ClientInstV2%24DuplicateXlsDefaultConfig*BingCore%24ClientInstV2%24SharedLocalStorageConfigDefault*BingCore%24shared*BingCore%24env.override*Empty*BingCore%24event.custom.fix*BingCore%24event.native*BingCore%24onHTML*BingCore%24dom*BingCore%24cookies*BingCore%24rmsajax*BingCore%24ClientInstV2%24LogUploadCapFeatureDisabled*BingCore%24ClientInstV2%24ClientInstConfigSeparateOfflineQueue*BingCore%24clientinst*BingCore%24replay*BingCore%24Animation*BingCore%24fadeAnimation*BingCore%24framework | US | text | 4.95 Kb | whitelisted |
2012 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/notifications/render?bnptrigger=%7B%22PartnerId%22%3A%22HomePage%22%2C%22IID%22%3A%22SERP.2000%22%2C%22Attributes%22%3A%7B%22RawRequestURL%22%3A%22%2F%22%7D%7D&IG=6760003EEB7B4772875E54C8CF96D040&IID=SERP.2000 | US | html | 3.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3644 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
2012 | iexplore.exe | 23.95.11.83:80 | pepepekitrecipepre.midrenufusawe.summeraugust.xyz | ColoCrossing | US | unknown |
2588 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2012 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2012 | iexplore.exe | 65.55.163.78:443 | login.live.com | Microsoft Corporation | US | whitelisted |
2012 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2012 | iexplore.exe | 2.16.106.96:80 | a4.bing.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
pepepekitrecipepre.midrenufusawe.summeraugust.xyz |
| unknown |
www.bing.com |
| whitelisted |
bing.com |
| whitelisted |
login.live.com |
| whitelisted |
a4.bing.com |
| whitelisted |