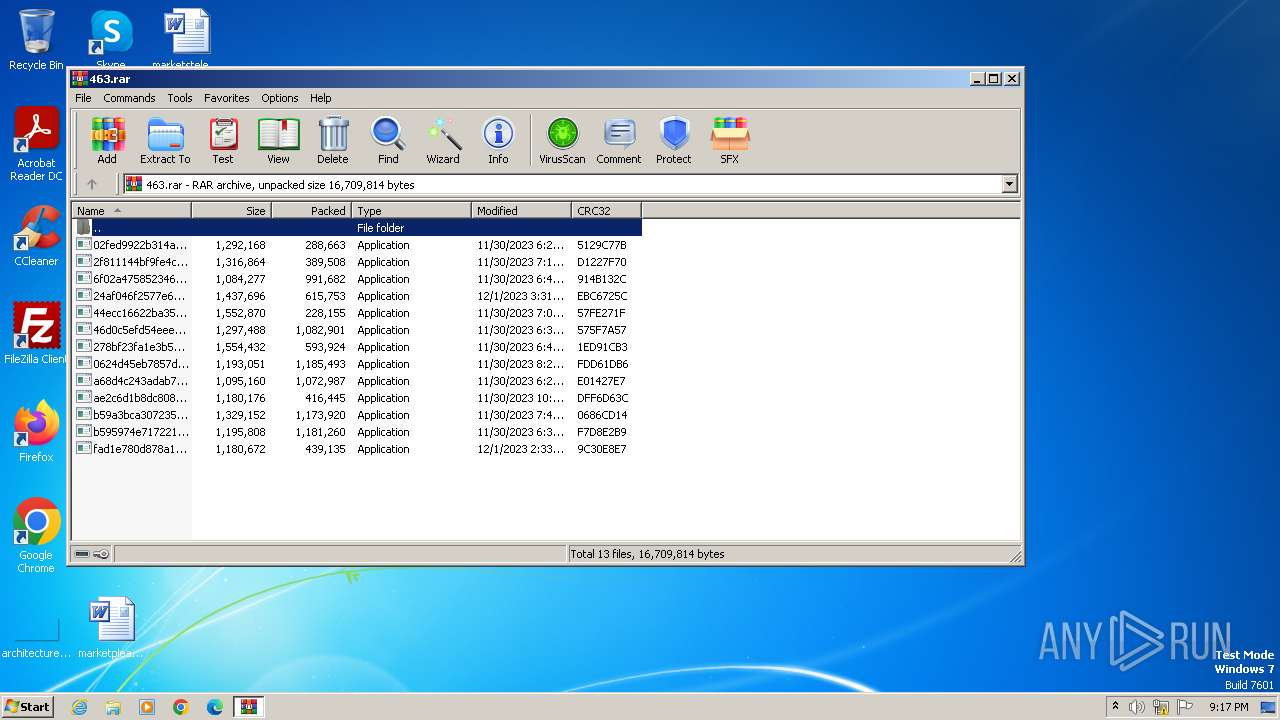
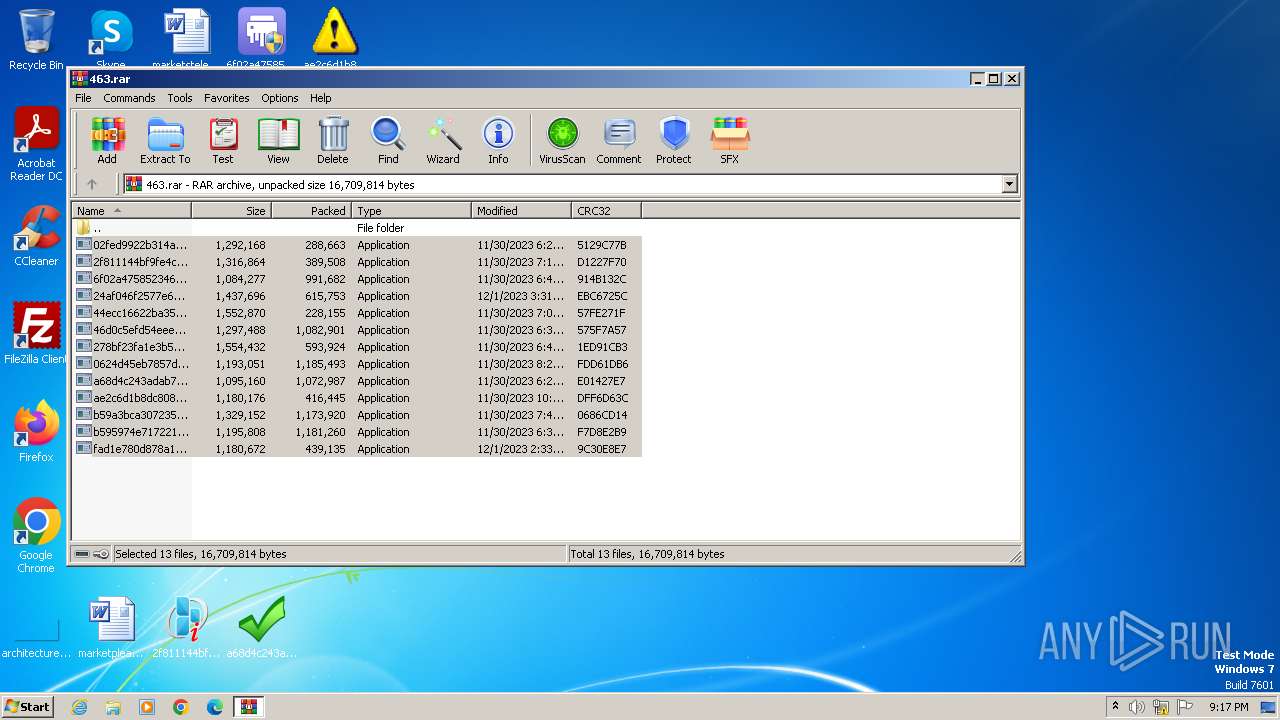
| File name: | 463.rar |
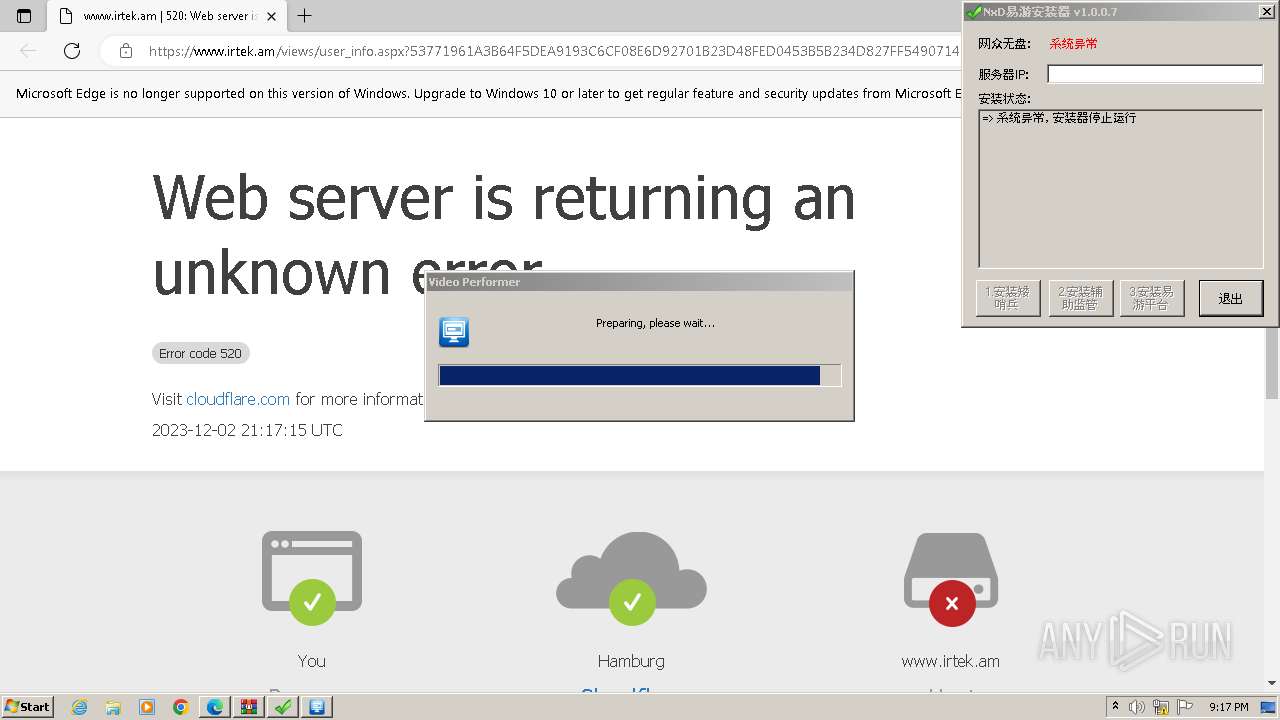
| Full analysis: | https://app.any.run/tasks/c13e4e9b-0a7c-4439-b9c9-3a3eaa904da5 |
| Verdict: | Malicious activity |
| Analysis date: | December 02, 2023, 21:16:53 |
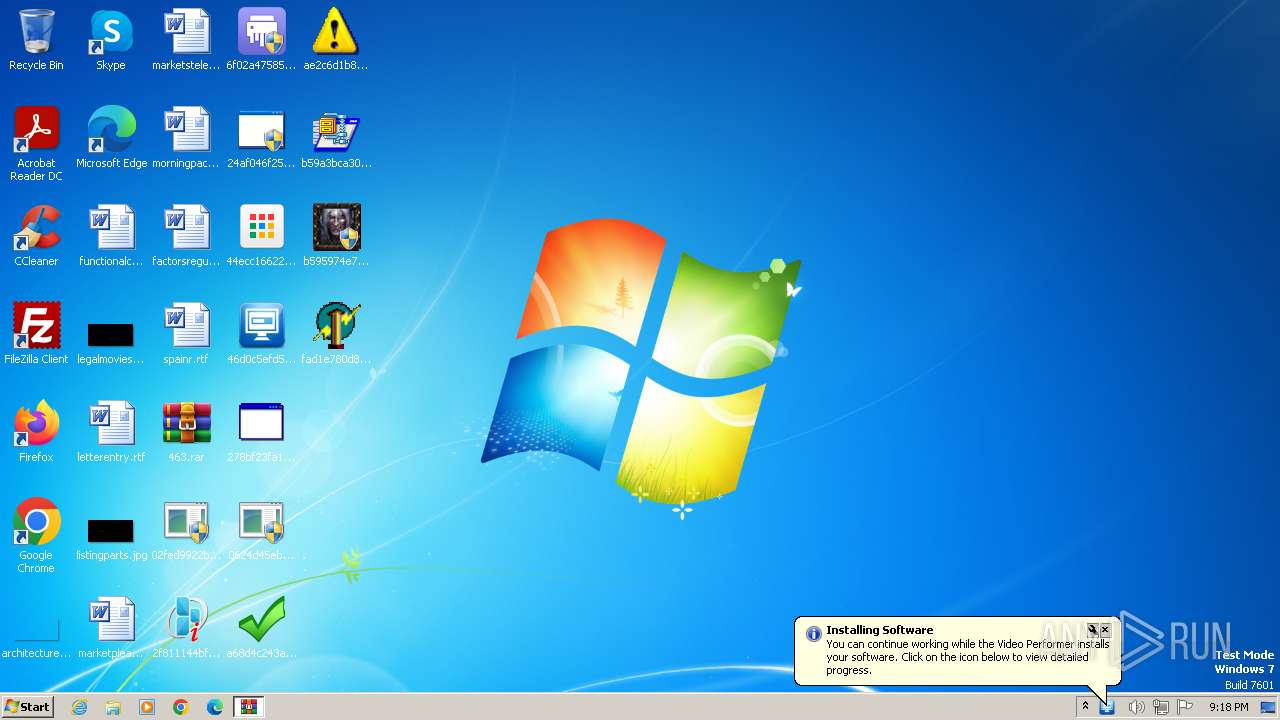
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 52F181A6E2609CCC6862C5E98EECCADF |
| SHA1: | AF6FB07C84E6147CC893C5CDF6D4BB45126873E6 |
| SHA256: | AE10E56E75DB1984FA7011CD6A02C838B1B1A8FE144958FEA924042505702F65 |
| SSDEEP: | 98304:Z5DKD4mbjExqi57EoWrFJJzE4TuUyVPleu+5aHFvFJmWFXuN5ctZaeiONtTQtGaf:WGTJaKmtSjmQT/qSyMIv39 |
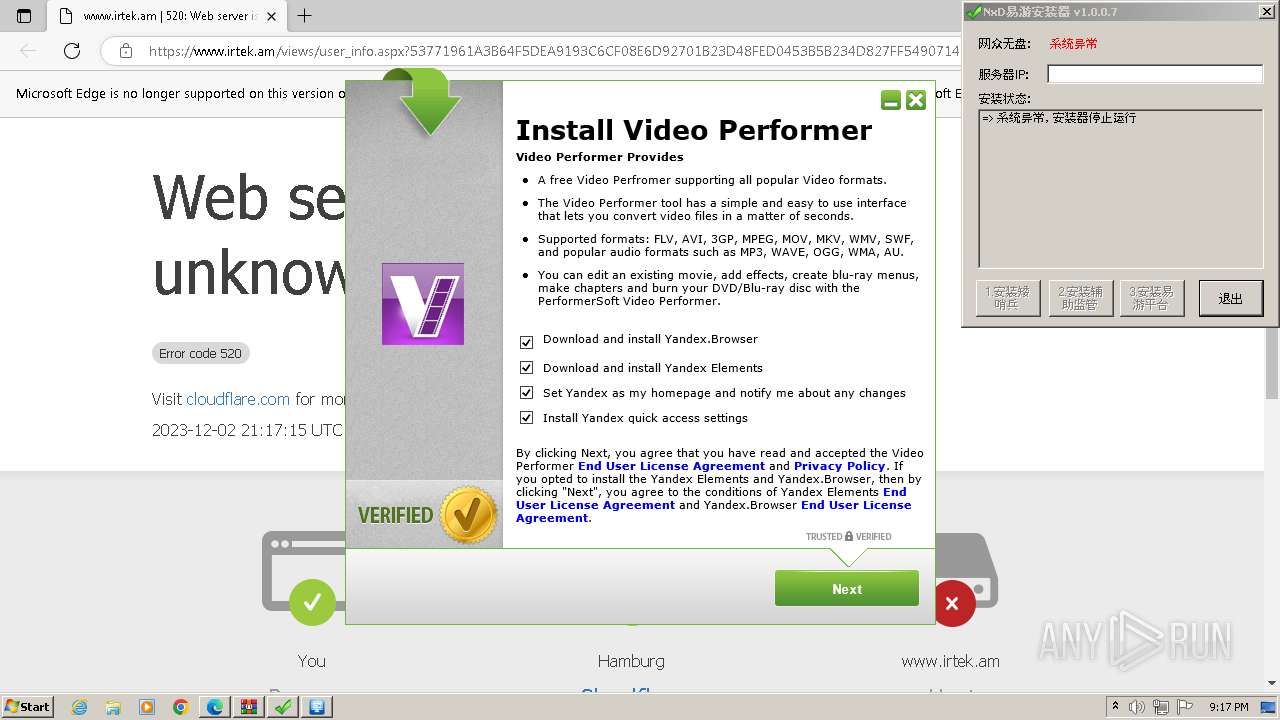
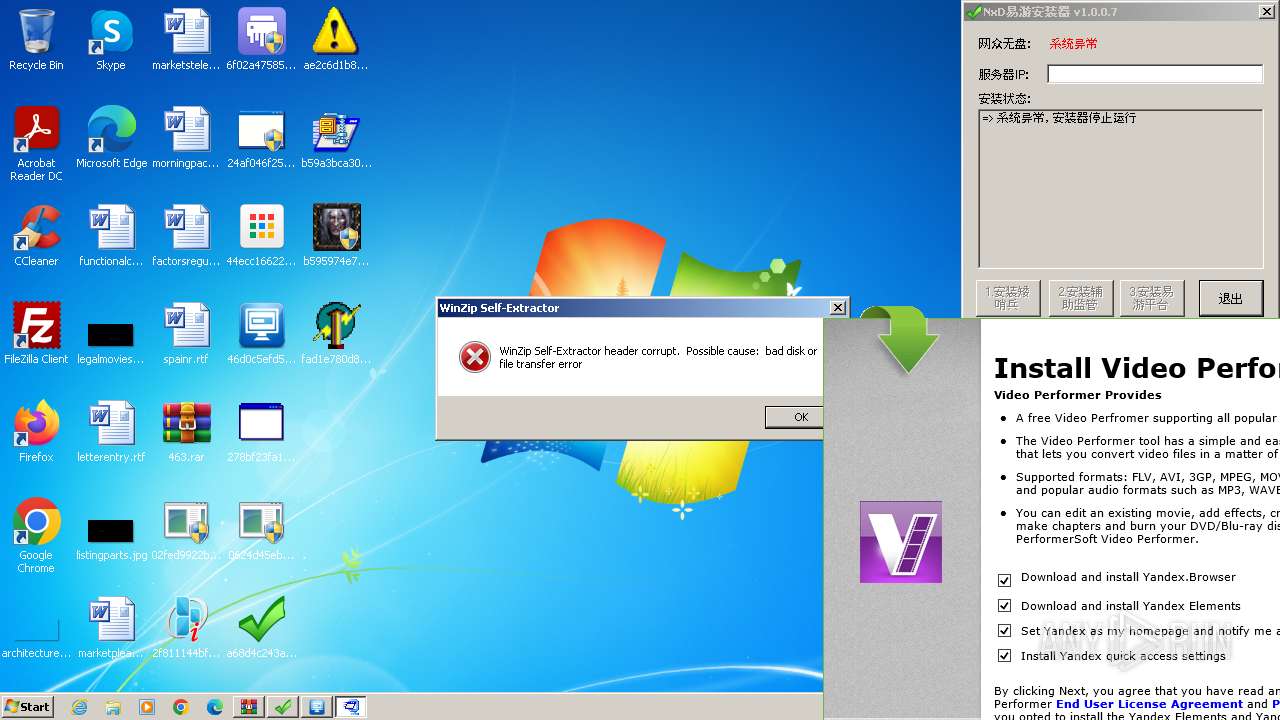
MALICIOUS
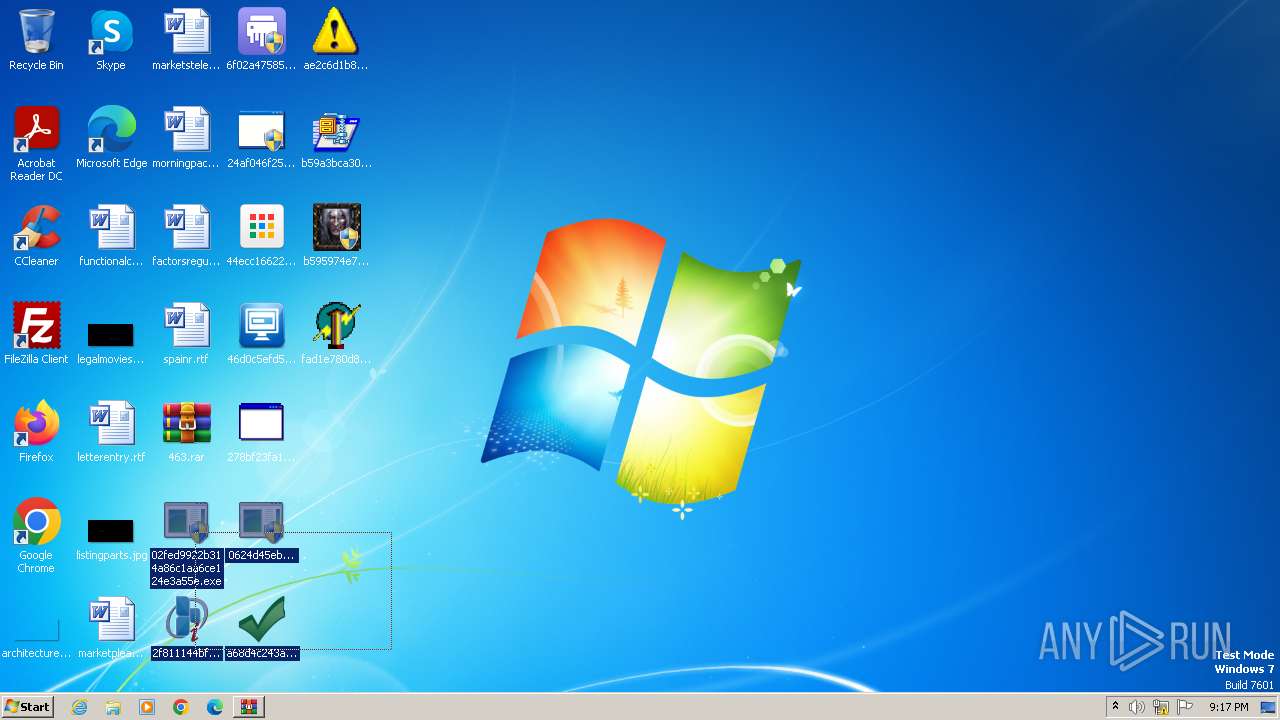
Drops the executable file immediately after the start
- 0624d45eb7857dc944c4ee0c3f9cfbc9.exe (PID: 684)
- 44ecc16622ba35e77eff157947175c5a.exe (PID: 3260)
- 278bf23fa1e3b539ebeb7504b3d83618.exe (PID: 3132)
- 02fed9922b314a86c1aa6ce124e3a55e.exe (PID: 2820)
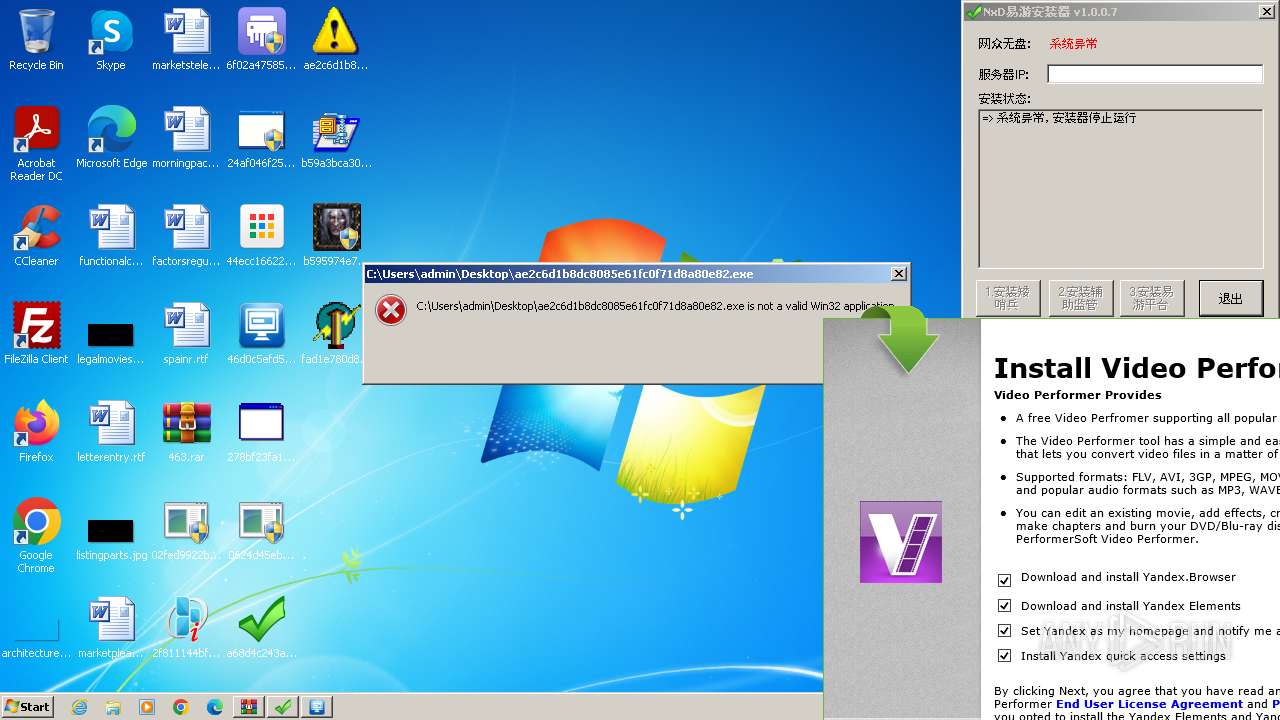
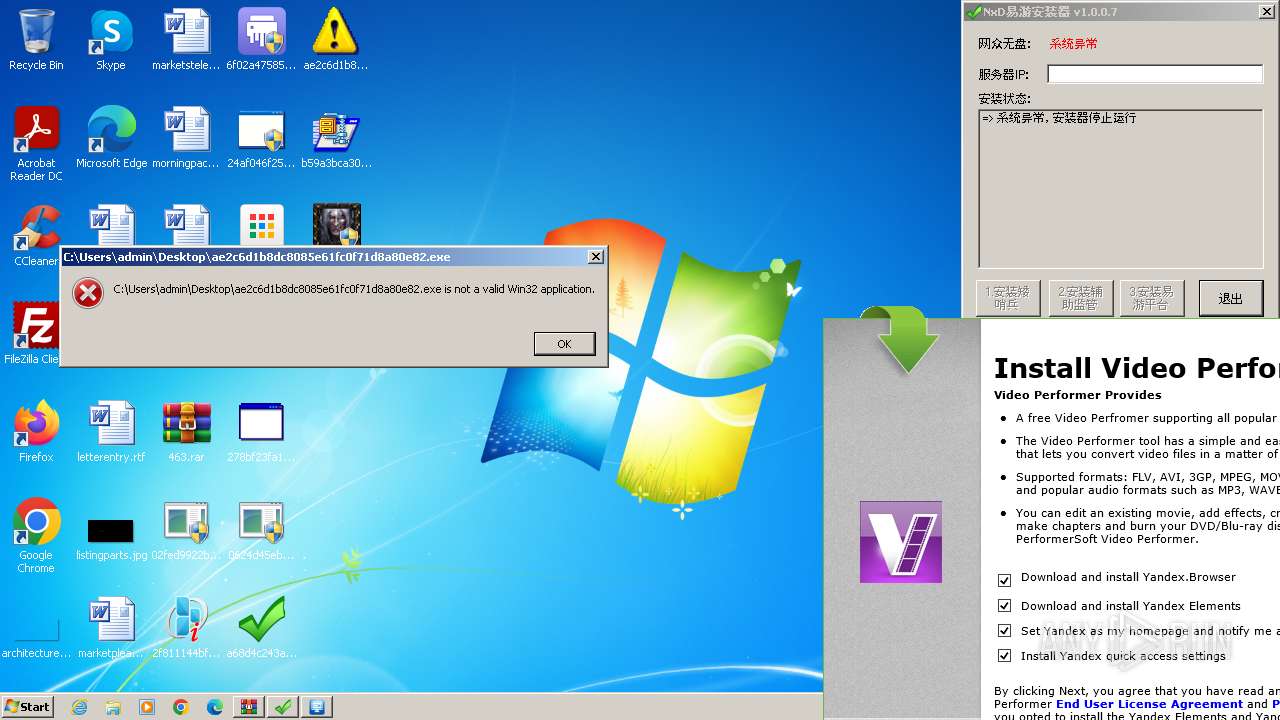
Actions looks like stealing of personal data
- 46d0c5efd54eee864227c1659614ed24.exe (PID: 1904)
- 278bf23fa1e3b539ebeb7504b3d83618.exe (PID: 3132)
Steals credentials from Web Browsers
- 46d0c5efd54eee864227c1659614ed24.exe (PID: 1904)
Reads the value of a key from the registry (SCRIPT)
- 46d0c5efd54eee864227c1659614ed24.exe (PID: 1904)
Connects to the CnC server
- 278bf23fa1e3b539ebeb7504b3d83618.exe (PID: 3132)
SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 3060)
- 278bf23fa1e3b539ebeb7504b3d83618.exe (PID: 3132)
- 44ecc16622ba35e77eff157947175c5a.exe (PID: 3260)
Starts itself from another location
- 0624d45eb7857dc944c4ee0c3f9cfbc9.exe (PID: 684)
Reads the Internet Settings
- 2f811144bf9fe4cf0fb688aa837a8df7.exe (PID: 2964)
- 46d0c5efd54eee864227c1659614ed24.exe (PID: 3192)
- 46d0c5efd54eee864227c1659614ed24.exe (PID: 1904)
- 02fed9922b314a86c1aa6ce124e3a55e.exe (PID: 2820)
Application launched itself
- 46d0c5efd54eee864227c1659614ed24.exe (PID: 3192)
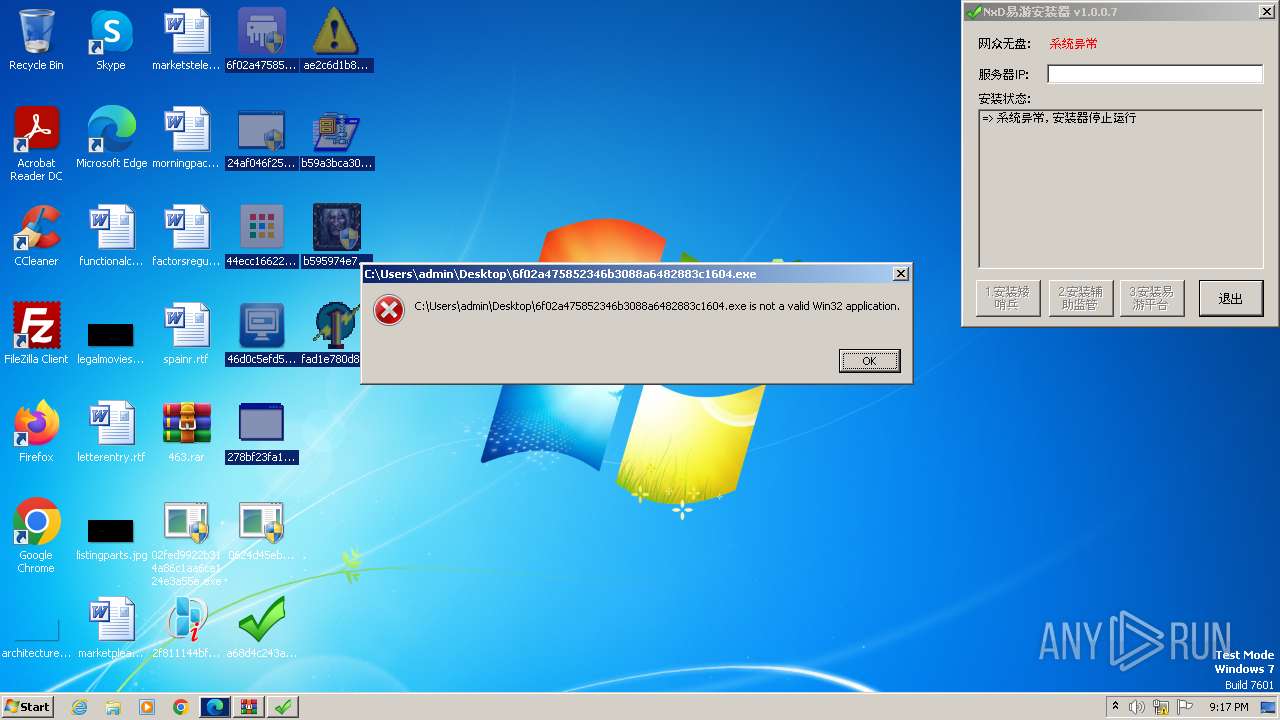
Starts CMD.EXE for commands execution
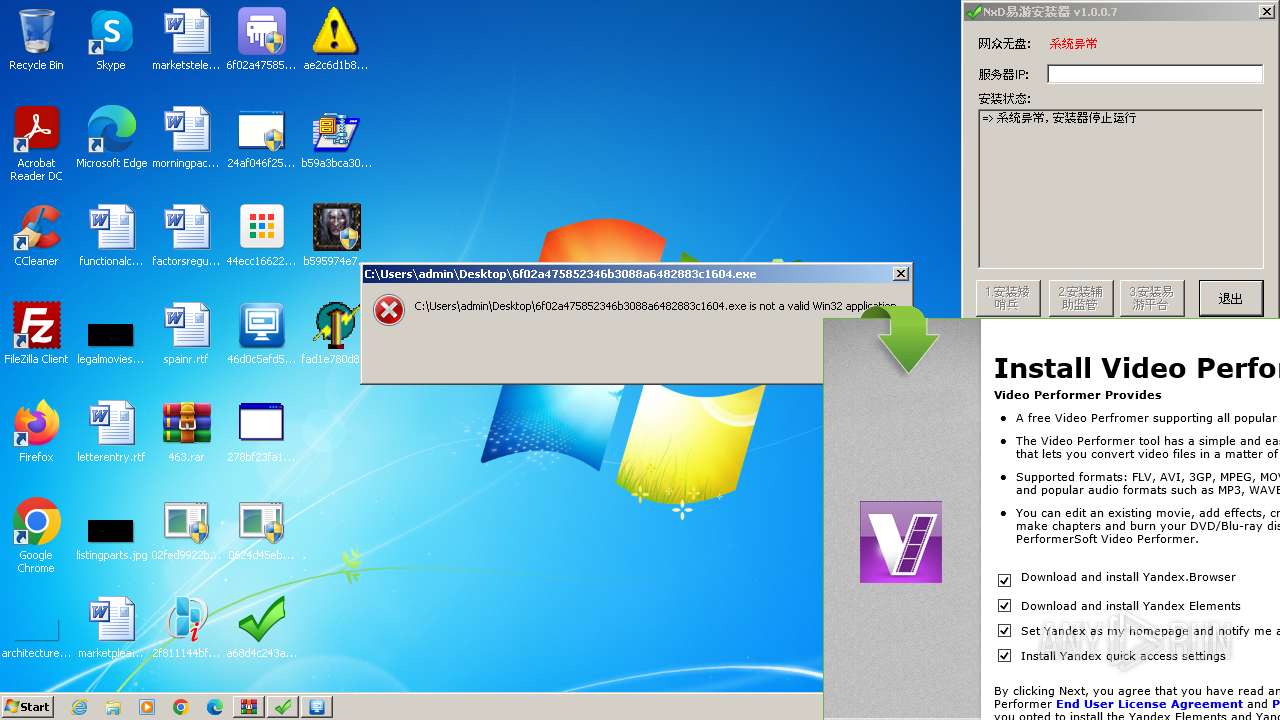
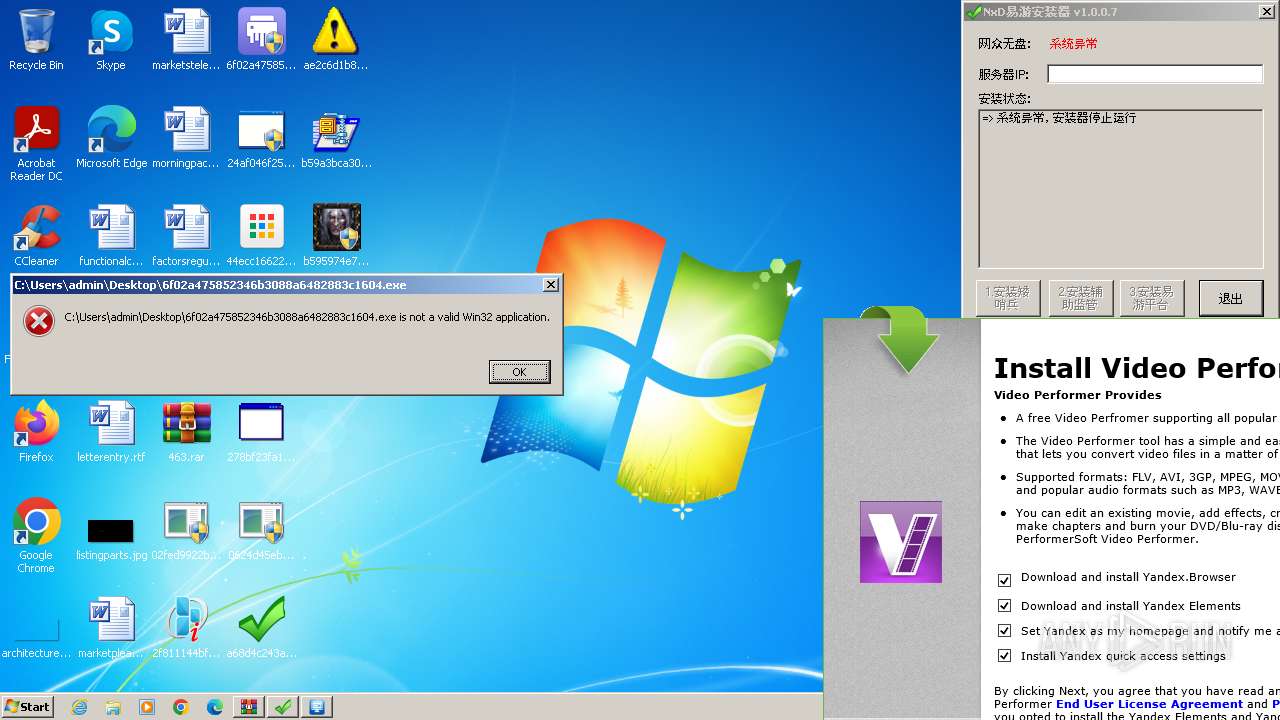
- 6f02a475852346b3088a6482883c1604.exe (PID: 4012)
- 6f02a475852346b3088a6482883c1604.exe (PID: 1036)
- 6f02a475852346b3088a6482883c1604.exe (PID: 3220)
Reads Internet Explorer settings
- 46d0c5efd54eee864227c1659614ed24.exe (PID: 1904)
Reads Microsoft Outlook installation path
- 46d0c5efd54eee864227c1659614ed24.exe (PID: 1904)
Searches for installed software
- 46d0c5efd54eee864227c1659614ed24.exe (PID: 1904)
Connects to unusual port
- 02fed9922b314a86c1aa6ce124e3a55e.exe (PID: 2820)
INFO
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3060)
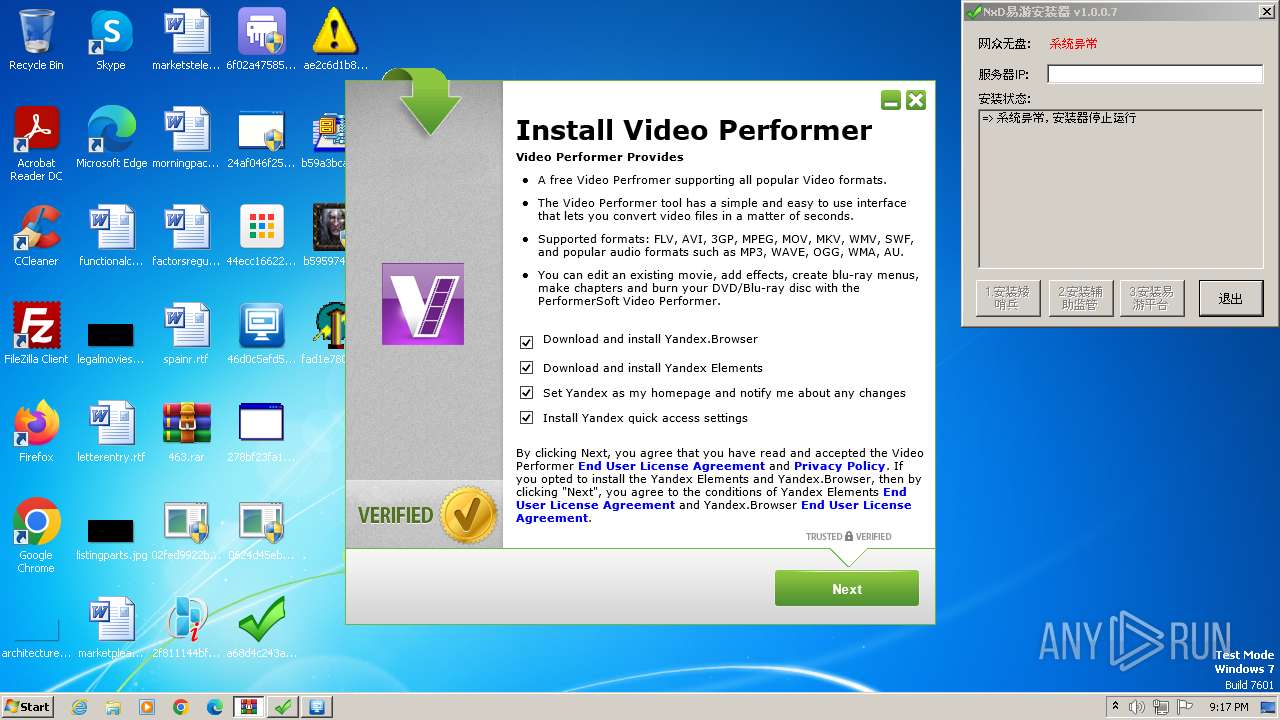
Manual execution by a user
- 02fed9922b314a86c1aa6ce124e3a55e.exe (PID: 124)
- 2f811144bf9fe4cf0fb688aa837a8df7.exe (PID: 2964)
- 02fed9922b314a86c1aa6ce124e3a55e.exe (PID: 2820)
- 0624d45eb7857dc944c4ee0c3f9cfbc9.exe (PID: 604)
- a68d4c243adab76714d47b27a7d2189a.exe (PID: 600)
- 0624d45eb7857dc944c4ee0c3f9cfbc9.exe (PID: 684)
- 6f02a475852346b3088a6482883c1604.exe (PID: 4012)
- 6f02a475852346b3088a6482883c1604.exe (PID: 3640)
- 24af046f2577e61eed8f5da4193eb0f1.exe (PID: 944)
- 46d0c5efd54eee864227c1659614ed24.exe (PID: 3192)
- 24af046f2577e61eed8f5da4193eb0f1.exe (PID: 3268)
- 44ecc16622ba35e77eff157947175c5a.exe (PID: 3260)
- 278bf23fa1e3b539ebeb7504b3d83618.exe (PID: 3132)
- wmpnscfg.exe (PID: 1244)
- 46d0c5efd54eee864227c1659614ed24.exe (PID: 2524)
- 6f02a475852346b3088a6482883c1604.exe (PID: 2620)
- 6f02a475852346b3088a6482883c1604.exe (PID: 1036)
- 24af046f2577e61eed8f5da4193eb0f1.exe (PID: 3680)
- 24af046f2577e61eed8f5da4193eb0f1.exe (PID: 1452)
- 44ecc16622ba35e77eff157947175c5a.exe (PID: 3224)
- 278bf23fa1e3b539ebeb7504b3d83618.exe (PID: 2236)
- 6f02a475852346b3088a6482883c1604.exe (PID: 3820)
- 6f02a475852346b3088a6482883c1604.exe (PID: 3220)
- 24af046f2577e61eed8f5da4193eb0f1.exe (PID: 3336)
- 24af046f2577e61eed8f5da4193eb0f1.exe (PID: 3548)
- 44ecc16622ba35e77eff157947175c5a.exe (PID: 3604)
- b59a3bca307235a9aebadb38a6f0afaf.exe (PID: 3884)
- b595974e717221122d9bb3a4dfe141e5.exe (PID: 2040)
- b595974e717221122d9bb3a4dfe141e5.exe (PID: 3424)
Checks supported languages
- 02fed9922b314a86c1aa6ce124e3a55e.exe (PID: 2820)
- 2f811144bf9fe4cf0fb688aa837a8df7.exe (PID: 2964)
- 0624d45eb7857dc944c4ee0c3f9cfbc9.exe (PID: 684)
- a68d4c243adab76714d47b27a7d2189a.exe (PID: 600)
- 6f02a475852346b3088a6482883c1604.exe (PID: 4012)
- 44ecc16622ba35e77eff157947175c5a.exe (PID: 3260)
- wymn.exe (PID: 3940)
- 278bf23fa1e3b539ebeb7504b3d83618.exe (PID: 3132)
- 46d0c5efd54eee864227c1659614ed24.exe (PID: 1904)
- 24af046f2577e61eed8f5da4193eb0f1.exe (PID: 3268)
- 46d0c5efd54eee864227c1659614ed24.exe (PID: 3192)
- wmpnscfg.exe (PID: 1244)
- 46d0c5efd54eee864227c1659614ed24.exe (PID: 2524)
- 6f02a475852346b3088a6482883c1604.exe (PID: 1036)
- 278bf23fa1e3b539ebeb7504b3d83618.exe (PID: 2236)
- 6f02a475852346b3088a6482883c1604.exe (PID: 3220)
- 24af046f2577e61eed8f5da4193eb0f1.exe (PID: 3336)
- b59a3bca307235a9aebadb38a6f0afaf.exe (PID: 3884)
- 44ecc16622ba35e77eff157947175c5a.exe (PID: 3224)
- 24af046f2577e61eed8f5da4193eb0f1.exe (PID: 1452)
- 44ecc16622ba35e77eff157947175c5a.exe (PID: 3604)
- b595974e717221122d9bb3a4dfe141e5.exe (PID: 2040)
Reads the computer name
- 2f811144bf9fe4cf0fb688aa837a8df7.exe (PID: 2964)
- 6f02a475852346b3088a6482883c1604.exe (PID: 4012)
- a68d4c243adab76714d47b27a7d2189a.exe (PID: 600)
- 24af046f2577e61eed8f5da4193eb0f1.exe (PID: 3268)
- 46d0c5efd54eee864227c1659614ed24.exe (PID: 3192)
- 278bf23fa1e3b539ebeb7504b3d83618.exe (PID: 3132)
- 46d0c5efd54eee864227c1659614ed24.exe (PID: 1904)
- wmpnscfg.exe (PID: 1244)
- 02fed9922b314a86c1aa6ce124e3a55e.exe (PID: 2820)
- 6f02a475852346b3088a6482883c1604.exe (PID: 1036)
- 278bf23fa1e3b539ebeb7504b3d83618.exe (PID: 2236)
- 24af046f2577e61eed8f5da4193eb0f1.exe (PID: 1452)
- 6f02a475852346b3088a6482883c1604.exe (PID: 3220)
- 24af046f2577e61eed8f5da4193eb0f1.exe (PID: 3336)
- b595974e717221122d9bb3a4dfe141e5.exe (PID: 2040)
Reads the machine GUID from the registry
- 2f811144bf9fe4cf0fb688aa837a8df7.exe (PID: 2964)
- 46d0c5efd54eee864227c1659614ed24.exe (PID: 1904)
- 02fed9922b314a86c1aa6ce124e3a55e.exe (PID: 2820)
- a68d4c243adab76714d47b27a7d2189a.exe (PID: 600)
Application launched itself
- msedge.exe (PID: 3344)
Creates files in the program directory
- 0624d45eb7857dc944c4ee0c3f9cfbc9.exe (PID: 684)
Creates files or folders in the user directory
- 278bf23fa1e3b539ebeb7504b3d83618.exe (PID: 3132)
- 44ecc16622ba35e77eff157947175c5a.exe (PID: 3260)
- 44ecc16622ba35e77eff157947175c5a.exe (PID: 3224)
- 02fed9922b314a86c1aa6ce124e3a55e.exe (PID: 2820)
- 44ecc16622ba35e77eff157947175c5a.exe (PID: 3604)
Create files in a temporary directory
- 24af046f2577e61eed8f5da4193eb0f1.exe (PID: 3268)
- 46d0c5efd54eee864227c1659614ed24.exe (PID: 1904)
Checks proxy server information
- 46d0c5efd54eee864227c1659614ed24.exe (PID: 1904)
- 02fed9922b314a86c1aa6ce124e3a55e.exe (PID: 2820)
Process checks are UAC notifies on
- 46d0c5efd54eee864227c1659614ed24.exe (PID: 1904)
Reads Environment values
- 46d0c5efd54eee864227c1659614ed24.exe (PID: 1904)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
101
Monitored processes
46
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Users\admin\Desktop\02fed9922b314a86c1aa6ce124e3a55e.exe" | C:\Users\admin\Desktop\02fed9922b314a86c1aa6ce124e3a55e.exe | — | explorer.exe | |||||||||||
User: admin Company: VAIO Corporation Integrity Level: MEDIUM Description: VAIO Shared Library (Service Module) Exit code: 3221226540 Version: 2.2.2.07220 Modules
| |||||||||||||||
| 556 | cmd.exe /c set | C:\Windows\System32\cmd.exe | — | 6f02a475852346b3088a6482883c1604.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
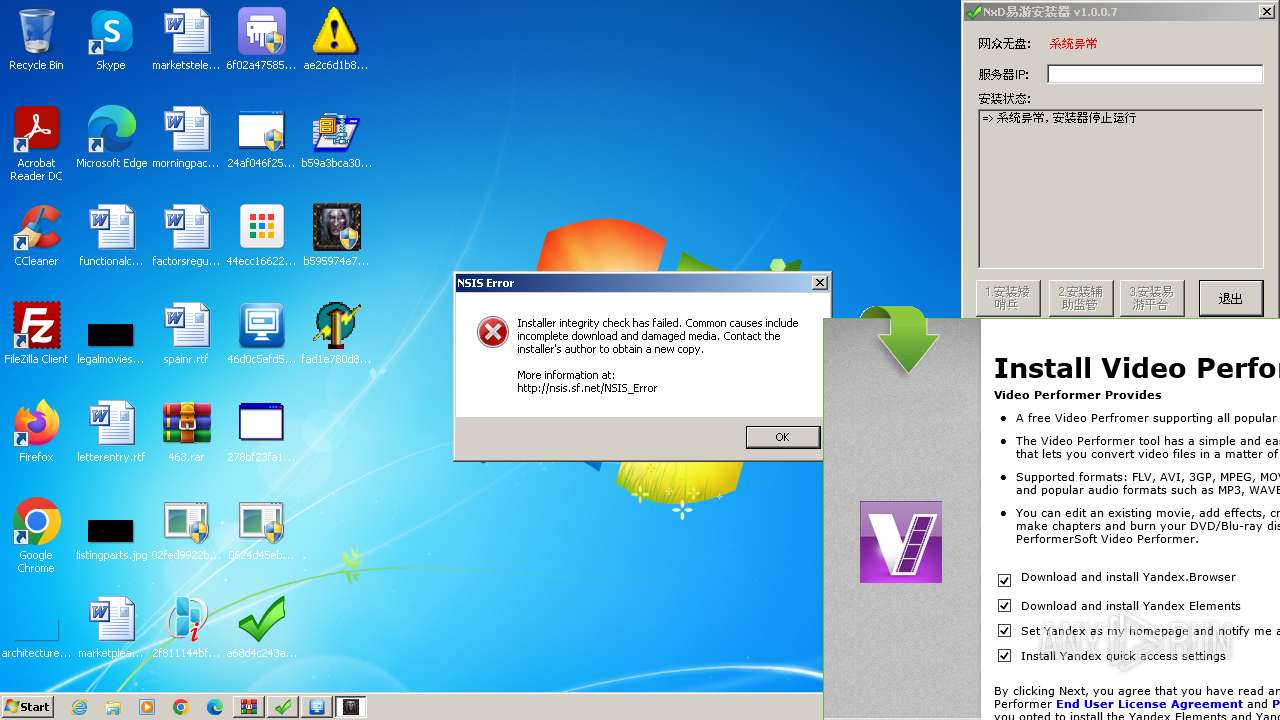
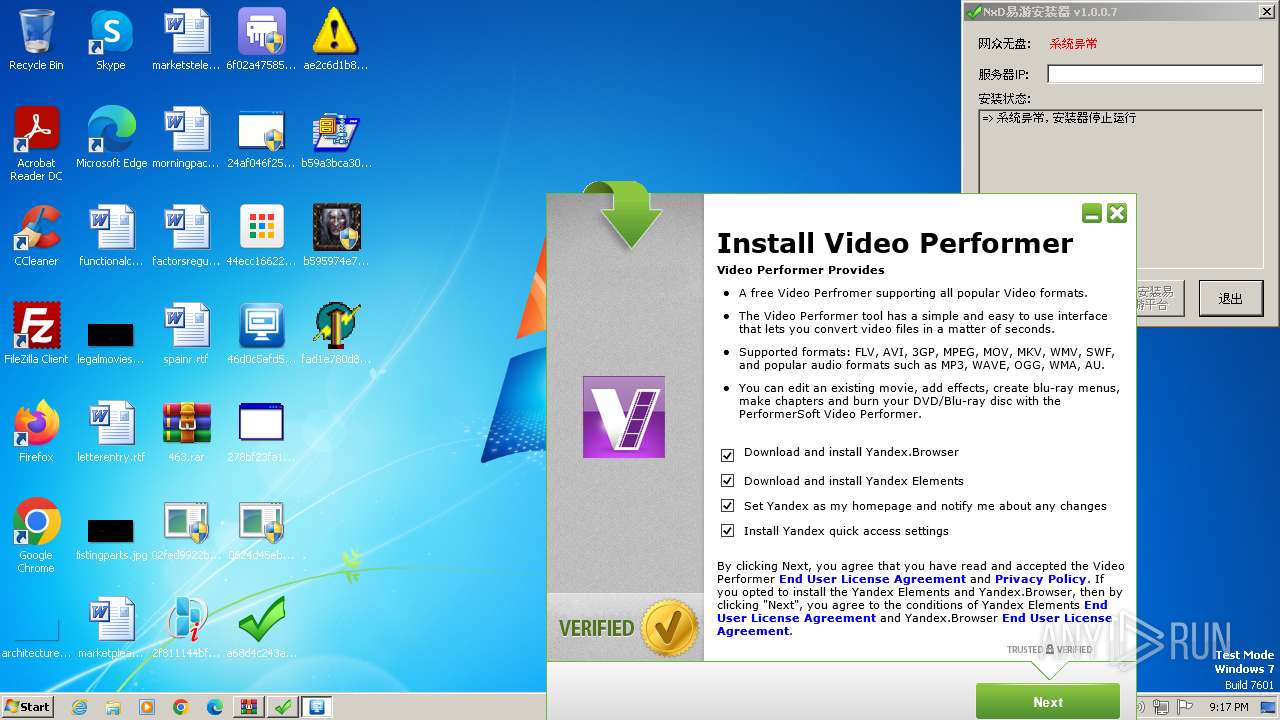
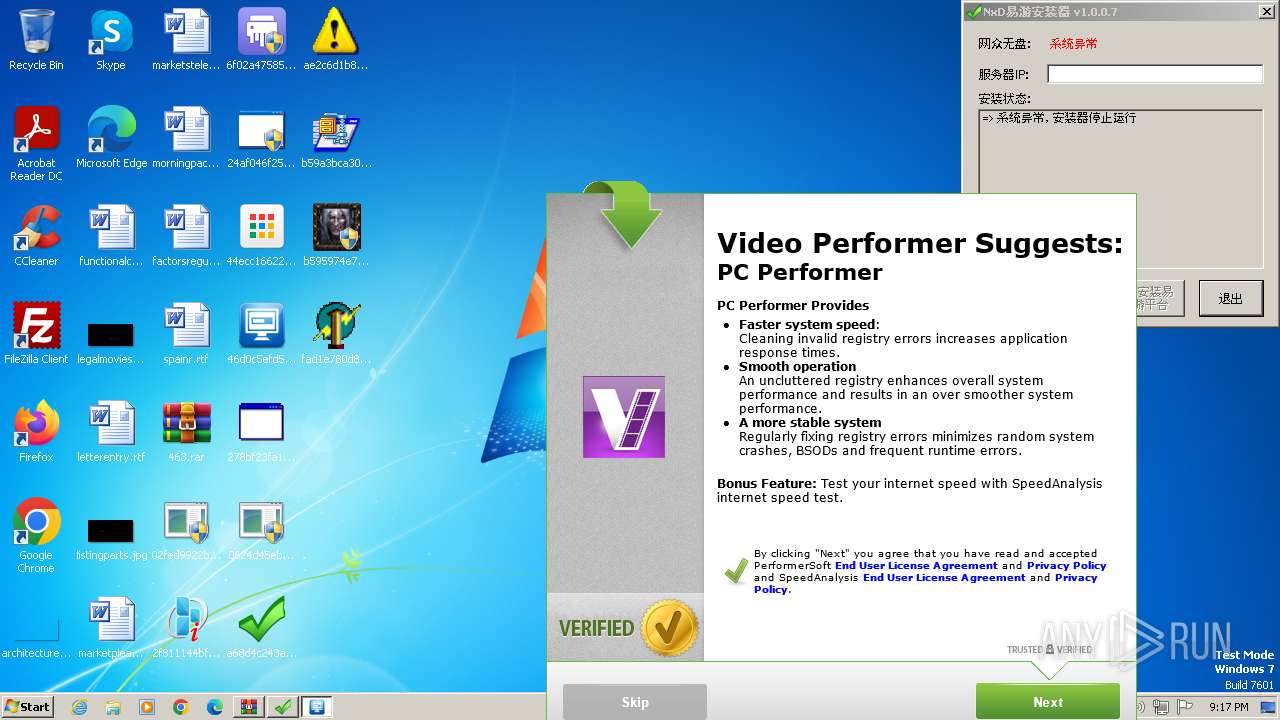
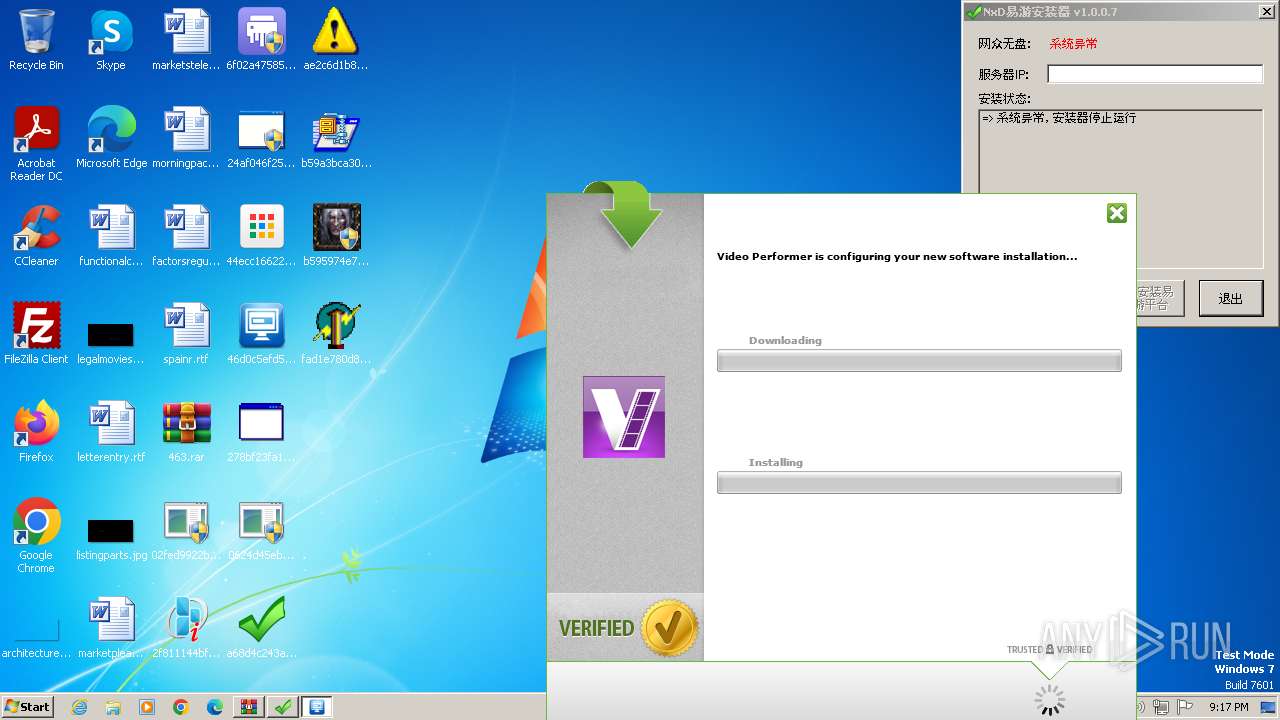
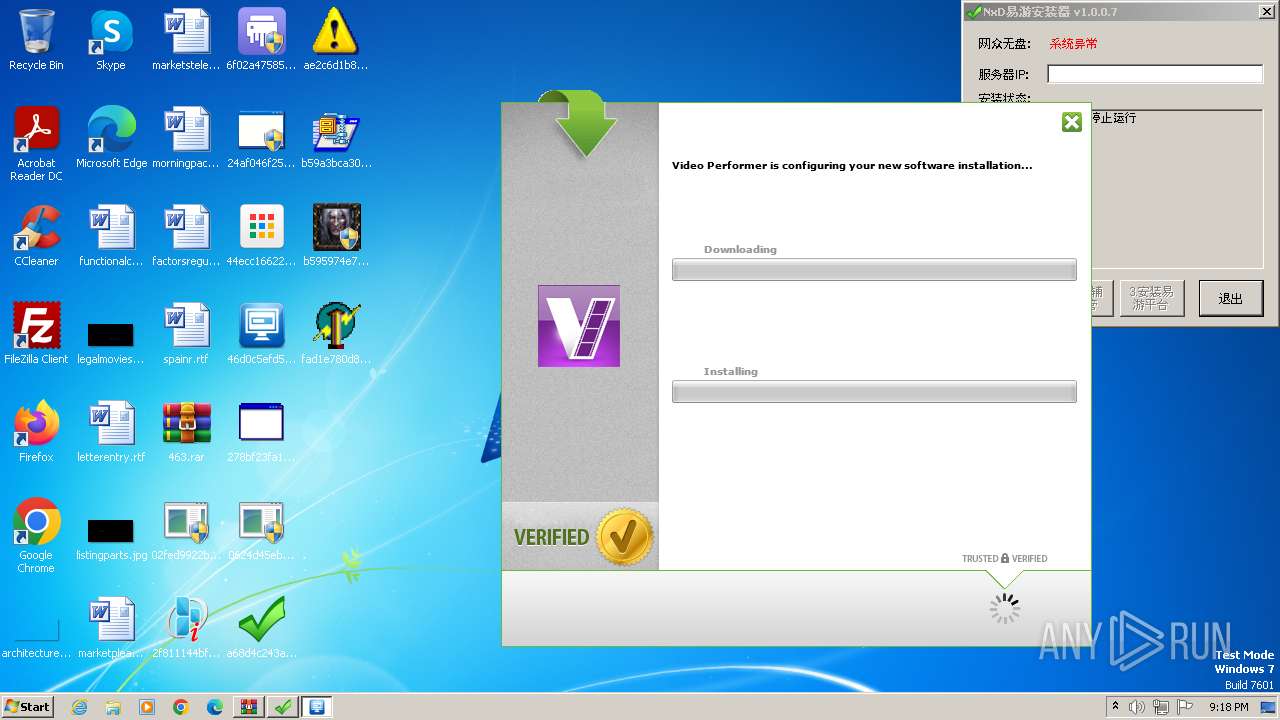
| 600 | "C:\Users\admin\Desktop\a68d4c243adab76714d47b27a7d2189a.exe" | C:\Users\admin\Desktop\a68d4c243adab76714d47b27a7d2189a.exe | — | explorer.exe | |||||||||||
User: admin Company: 2008xp Integrity Level: MEDIUM Description: NxD易游安装器 Exit code: 0 Version: 1.0.0.7 Modules
| |||||||||||||||
| 604 | "C:\Users\admin\Desktop\0624d45eb7857dc944c4ee0c3f9cfbc9.exe" | C:\Users\admin\Desktop\0624d45eb7857dc944c4ee0c3f9cfbc9.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 684 | "C:\Users\admin\Desktop\0624d45eb7857dc944c4ee0c3f9cfbc9.exe" | C:\Users\admin\Desktop\0624d45eb7857dc944c4ee0c3f9cfbc9.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 944 | "C:\Users\admin\Desktop\24af046f2577e61eed8f5da4193eb0f1.exe" | C:\Users\admin\Desktop\24af046f2577e61eed8f5da4193eb0f1.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: UPD Co-Installer Exit code: 3221226540 Version: 3, 0, 0, 0 Modules
| |||||||||||||||
| 1036 | "C:\Users\admin\Desktop\6f02a475852346b3088a6482883c1604.exe" | C:\Users\admin\Desktop\6f02a475852346b3088a6482883c1604.exe | explorer.exe | ||||||||||||
User: admin Company: Beijing Huorong Network Technology Co., Ltd. Integrity Level: HIGH Description: Huorong File Shredder Exit code: 0 Version: 5.0.1.1 Modules
| |||||||||||||||
| 1244 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1452 | "C:\Users\admin\Desktop\24af046f2577e61eed8f5da4193eb0f1.exe" | C:\Users\admin\Desktop\24af046f2577e61eed8f5da4193eb0f1.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: UPD Co-Installer Exit code: 0 Version: 3, 0, 0, 0 Modules
| |||||||||||||||
| 1904 | "C:\Users\admin\Desktop\46d0c5efd54eee864227c1659614ed24.exe" | C:\Users\admin\Desktop\46d0c5efd54eee864227c1659614ed24.exe | 46d0c5efd54eee864227c1659614ed24.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 14.6.26.21 Modules
| |||||||||||||||
Total events
7 694
Read events
7 634
Write events
60
Delete events
0
Modification events
| (PID) Process: | (3060) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (3060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3344) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3344) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
Executable files
222
Suspicious files
45
Text files
131
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3060 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3060.30887\46d0c5efd54eee864227c1659614ed24.exe | executable | |
MD5:46D0C5EFD54EEE864227C1659614ED24 | SHA256:18D813D8F2C4BBB7370EE827B1A2F349D554863541B858DC8202845E7DED896F | |||
| 3060 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3060.30887\02fed9922b314a86c1aa6ce124e3a55e.exe | executable | |
MD5:02FED9922B314A86C1AA6CE124E3A55E | SHA256:53CD1037799B7874DDD574F514153A38FCAFB8F6242A47A0501A85FD987095AB | |||
| 3060 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3060.30887\b595974e717221122d9bb3a4dfe141e5.exe | executable | |
MD5:B595974E717221122D9BB3A4DFE141E5 | SHA256:E85D52E9311D23B917B1FF0897B1B2F3083714FD16061099EA63925F83F6EAD1 | |||
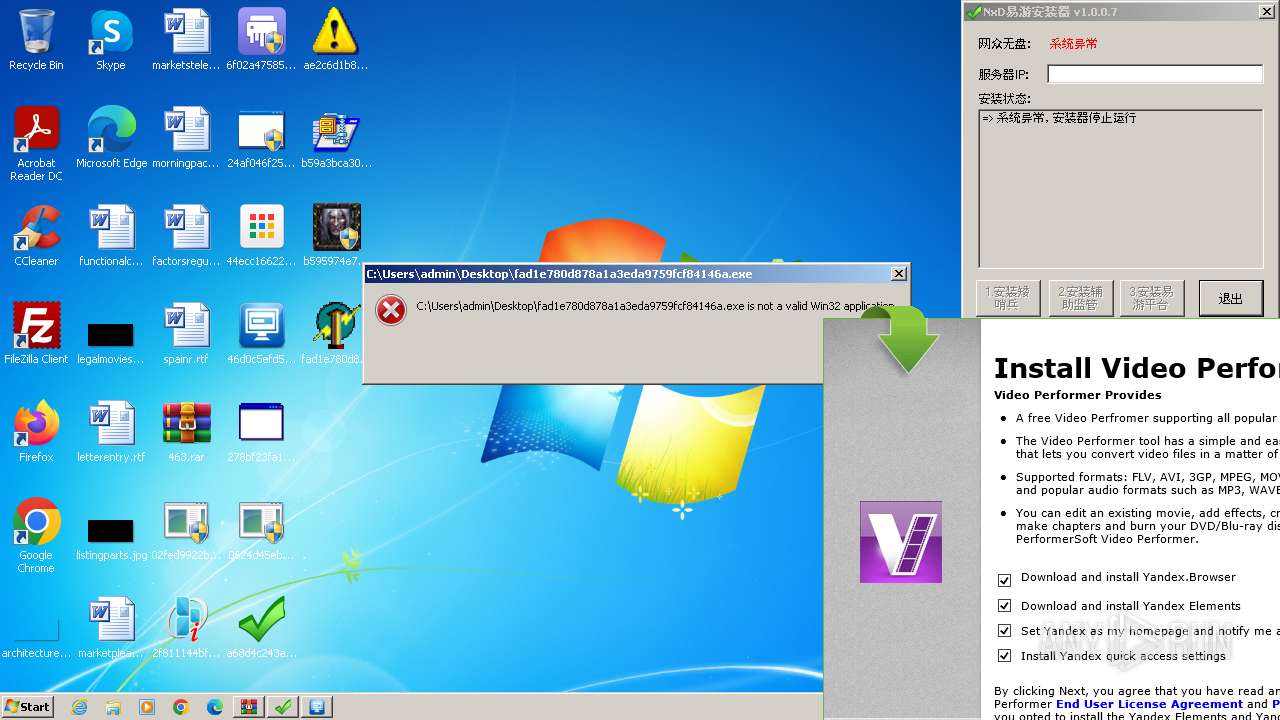
| 3060 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3060.30887\fad1e780d878a1a3eda9759fcf84146a.exe | executable | |
MD5:FAD1E780D878A1A3EDA9759FCF84146A | SHA256:BF4553726F79FED75DA22BB32A1F8A835DEAED6347BDD52442179D102E7882A8 | |||
| 3344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF2097cf.TMP | — | |
MD5:— | SHA256:— | |||
| 3344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3060 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3060.30887\0624d45eb7857dc944c4ee0c3f9cfbc9.exe | executable | |
MD5:0624D45EB7857DC944C4EE0C3F9CFBC9 | SHA256:418AE9198A56FB80AAADA0D3FE7A2D01DC054CA187F4698CF4725926026081D6 | |||
| 3344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3060 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3060.30887\278bf23fa1e3b539ebeb7504b3d83618.exe | executable | |
MD5:278BF23FA1E3B539EBEB7504B3D83618 | SHA256:758412FB075B628F9B9D8687D3E8EB47B16E8FE3AB0DA1CFF8AA50DF04D6E1E5 | |||
| 3060 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3060.30887\a68d4c243adab76714d47b27a7d2189a.exe | executable | |
MD5:A68D4C243ADAB76714D47B27A7D2189A | SHA256:38D808023C2846D12E244B714BE4E569FA86F53D59AC192570981BB9C658F660 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
30
DNS requests
33
Threats
27
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3132 | 278bf23fa1e3b539ebeb7504b3d83618.exe | POST | 200 | 34.128.82.12:80 | http://ssbzmoy.biz/huxgpkhtqhxmy | unknown | — | — | unknown |
3132 | 278bf23fa1e3b539ebeb7504b3d83618.exe | POST | 200 | 34.41.229.245:80 | http://pywolwnvd.biz/shpmwpdbcawmprlc | unknown | — | — | unknown |
2820 | 02fed9922b314a86c1aa6ce124e3a55e.exe | GET | 200 | 118.107.47.59:8000 | http://118.107.47.59:8000/j-30 | unknown | image | 75.6 Kb | unknown |
3132 | 278bf23fa1e3b539ebeb7504b3d83618.exe | POST | 200 | 104.198.2.251:80 | http://cvgrf.biz/pfvbbvrs | unknown | — | — | unknown |
2820 | 02fed9922b314a86c1aa6ce124e3a55e.exe | GET | — | 118.107.47.59:8000 | http://118.107.47.59:8000/1 | unknown | — | — | unknown |
3132 | 278bf23fa1e3b539ebeb7504b3d83618.exe | POST | 204 | 167.99.35.88:80 | http://przvgke.biz/jkxgspwhkkev | unknown | — | — | unknown |
3132 | 278bf23fa1e3b539ebeb7504b3d83618.exe | POST | 200 | 34.174.61.199:80 | http://npukfztj.biz/fbuivhn | unknown | — | — | unknown |
2820 | 02fed9922b314a86c1aa6ce124e3a55e.exe | GET | — | 118.107.47.59:8000 | http://118.107.47.59:8000/1 | unknown | — | — | unknown |
3132 | 278bf23fa1e3b539ebeb7504b3d83618.exe | POST | 200 | 34.128.82.12:80 | http://knjghuig.biz/rqxxvmtlj | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3344 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3000 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3000 | msedge.exe | 51.104.176.40:443 | nav-edge.smartscreen.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
3000 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
3000 | msedge.exe | 104.21.35.68:443 | www.irtek.am | CLOUDFLARENET | — | unknown |
3000 | msedge.exe | 20.105.95.163:443 | data-edge.smartscreen.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.edge.skype.com |
| whitelisted |
nav-edge.smartscreen.microsoft.com |
| whitelisted |
www.irtek.am |
| unknown |
edge.microsoft.com |
| whitelisted |
data-edge.smartscreen.microsoft.com |
| whitelisted |
a.nel.cloudflare.com |
| whitelisted |
pywolwnvd.biz |
| unknown |
inststats-1582571262.us-east-1.elb.amazonaws.com |
| unknown |
api.ibario.com |
| unknown |
msedgeextensions.sf.tlu.dl.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3000 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
3132 | 278bf23fa1e3b539ebeb7504b3d83618.exe | A Network Trojan was detected | ET MALWARE Possible Compromised Host AnubisNetworks Sinkhole Cookie Value Snkz |
3132 | 278bf23fa1e3b539ebeb7504b3d83618.exe | A Network Trojan was detected | ET MALWARE Possible Compromised Host AnubisNetworks Sinkhole Cookie Value btst |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
3132 | 278bf23fa1e3b539ebeb7504b3d83618.exe | A Network Trojan was detected | ET MALWARE Possible Compromised Host AnubisNetworks Sinkhole Cookie Value Snkz |
3132 | 278bf23fa1e3b539ebeb7504b3d83618.exe | A Network Trojan was detected | ET MALWARE Possible Compromised Host AnubisNetworks Sinkhole Cookie Value btst |
1 ETPRO signatures available at the full report