| File name: | Sayo_CLI_Windows.exe |
| Full analysis: | https://app.any.run/tasks/57e31639-2512-4713-b62b-8506961662a0 |
| Verdict: | Malicious activity |
| Analysis date: | December 30, 2022, 18:55:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 178C20C1250E0D1AC0E71517CAAB1CCC |
| SHA1: | 7110D4FEFBECE0A951FDF33A13886D711A7EF875 |
| SHA256: | AE0535CC607B7553CBEBD3C475C57D334678DDFD02201DFBE266E799CC91DB8A |
| SSDEEP: | 6144:kDF4y1Mk171PVwgWe8vDViyk+NKg8ypq:C1McwpemiyvQWp |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the Internet Settings
- Sayo_CLI_Windows.exe (PID: 1744)
Detected use of alternative data streams (AltDS)
- Sayo_CLI_Windows.exe (PID: 1744)
INFO
Checks supported languages
- Sayo_CLI_Windows.exe (PID: 1744)
Reads the computer name
- Sayo_CLI_Windows.exe (PID: 1744)
The process checks LSA protection
- iexplore.exe (PID: 3012)
- iexplore.exe (PID: 3572)
Application launched itself
- iexplore.exe (PID: 3012)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 2022-Sep-28 12:47:05 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | 山东小夜电子科技有限公司 |
| FileDescription: | SayoDevice键盘设定程序 |
| FileVersion: | 1.0.0.1 |
| InternalName: | Sayo_CLI_Windows.exe |
| LegalCopyright: | Copyright (C) 2022 |
| OriginalFilename: | Sayo_CLI_Windows.exe |
| ProductName: | SayoDevice |
| ProductVersion: | 1.0.0.1 |
DOS Header
| e_magic: | MZ |
|---|---|
| e_cblp: | 144 |
| e_cp: | 3 |
| e_crlc: | - |
| e_cparhdr: | 4 |
| e_minalloc: | - |
| e_maxalloc: | 65535 |
| e_ss: | - |
| e_sp: | 184 |
| e_csum: | - |
| e_ip: | - |
| e_cs: | - |
| e_ovno: | - |
| e_oemid: | - |
| e_oeminfo: | - |
| e_lfanew: | 264 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| NumberofSections: | 5 |
| TimeDateStamp: | 2022-Sep-28 12:47:05 |
| PointerToSymbolTable: | - |
| NumberOfSymbols: | - |
| SizeOfOptionalHeader: | 224 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 4096 | 164737 | 164864 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.42614 |
.rdata | 172032 | 40468 | 40960 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.78377 |
.data | 212992 | 3709016 | 1536 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.0962 |
.rsrc | 3923968 | 1296 | 1536 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.85838 |
.reloc | 3928064 | 12760 | 12800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.71028 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.64698 | 748 | UNKNOWN | Chinese - PRC | RT_VERSION |
1 (#2) | 4.91161 | 381 | UNKNOWN | English - United States | RT_MANIFEST |
Imports
KERNEL32.dll |
MSVCP140.dll |
SETUPAPI.dll |
SHELL32.dll |
USER32.dll |
VCRUNTIME140.dll |
WS2_32.dll |
api-ms-win-crt-convert-l1-1-0.dll |
api-ms-win-crt-filesystem-l1-1-0.dll |
api-ms-win-crt-heap-l1-1-0.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
hid_close | 1 | 68832 |
hid_enumerate | 2 | 66096 |
hid_error | 3 | 69168 |
hid_exit | 4 | 66048 |
hid_free_enumeration | 5 | 67152 |
hid_get_feature_report | 6 | 68576 |
hid_get_indexed_string | 7 | 69104 |
hid_get_input_report | 8 | 68704 |
hid_get_manufacturer_string | 9 | 68912 |
hid_get_product_string | 10 | 68976 |
Total processes
37
Monitored processes
3
Malicious processes
0
Suspicious processes
1
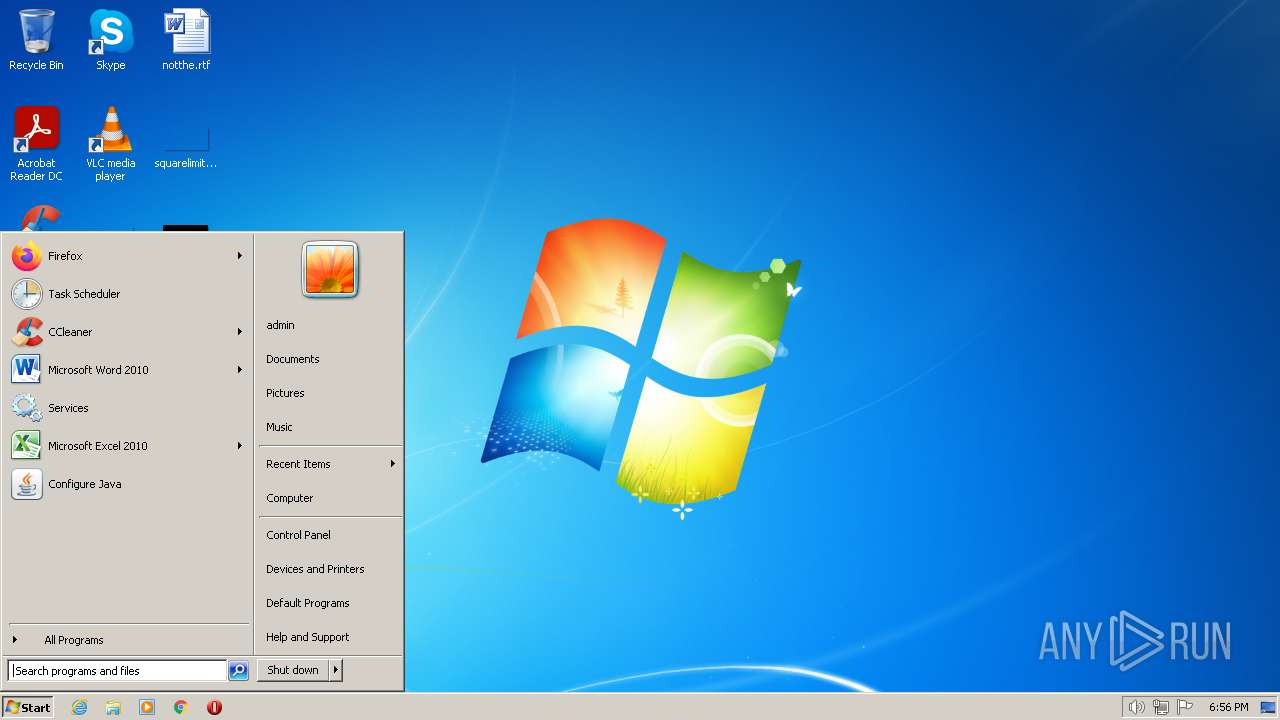
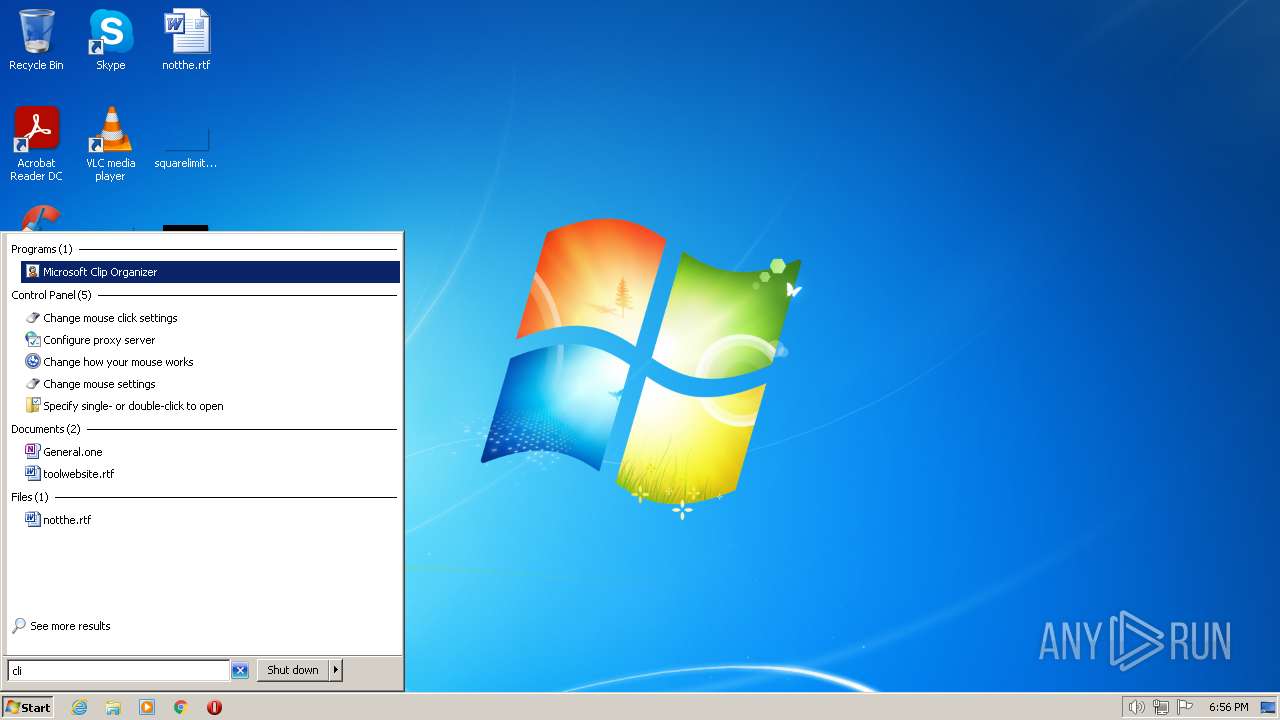
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
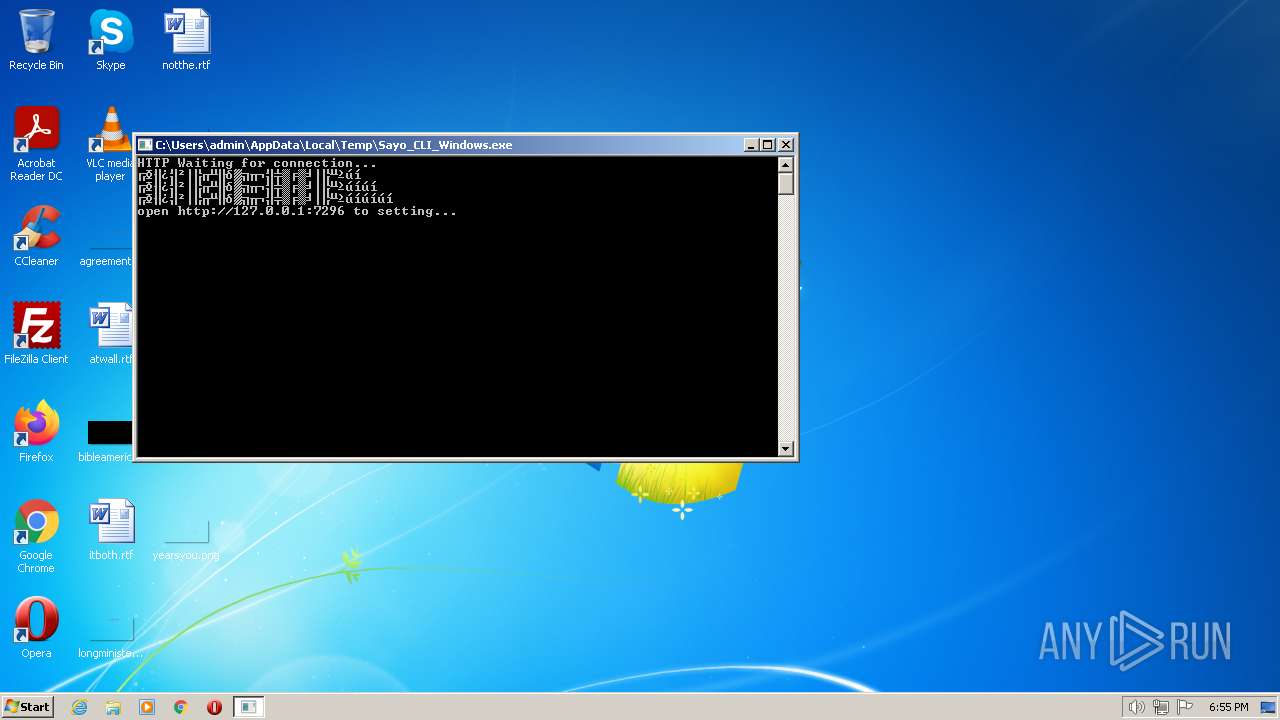
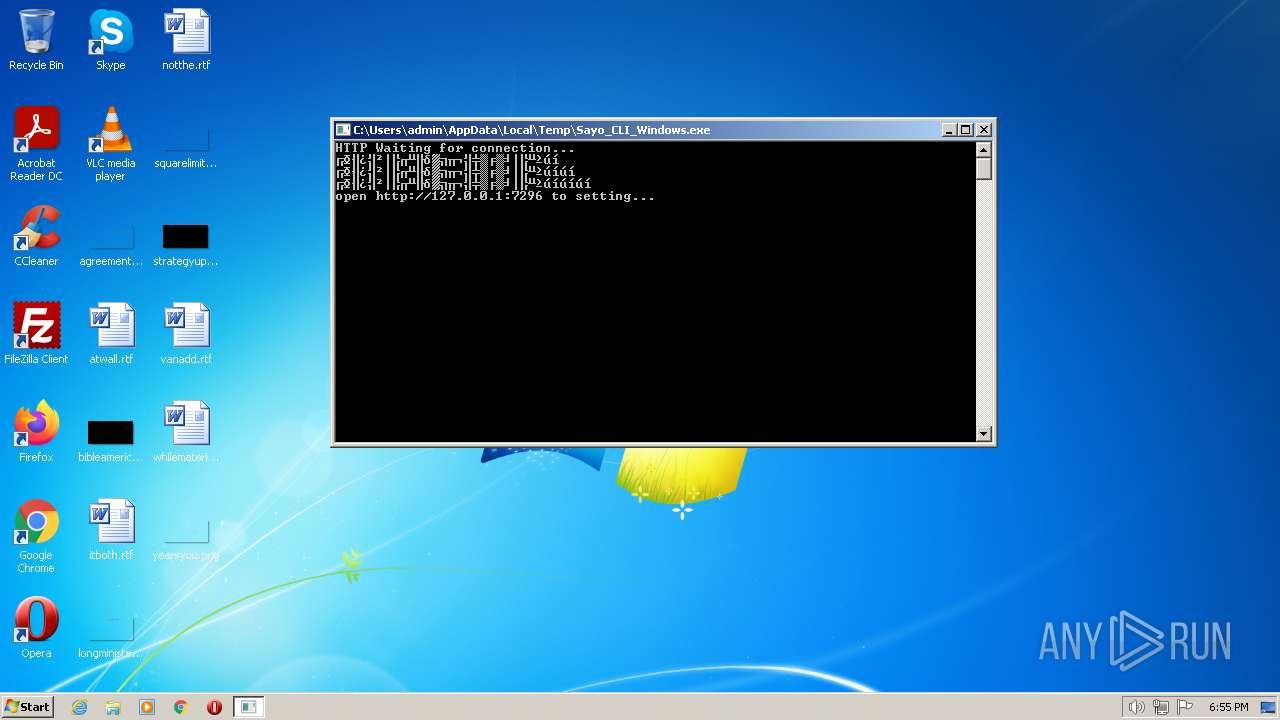
| 1744 | "C:\Users\admin\AppData\Local\Temp\Sayo_CLI_Windows.exe" | C:\Users\admin\AppData\Local\Temp\Sayo_CLI_Windows.exe | — | Explorer.EXE | |||||||||||
User: admin Company: 山东小夜电子科技有限公司 Integrity Level: MEDIUM Description: SayoDevice键盘设定程序 Exit code: 3221225786 Version: 1.0.0.1 Modules
| |||||||||||||||
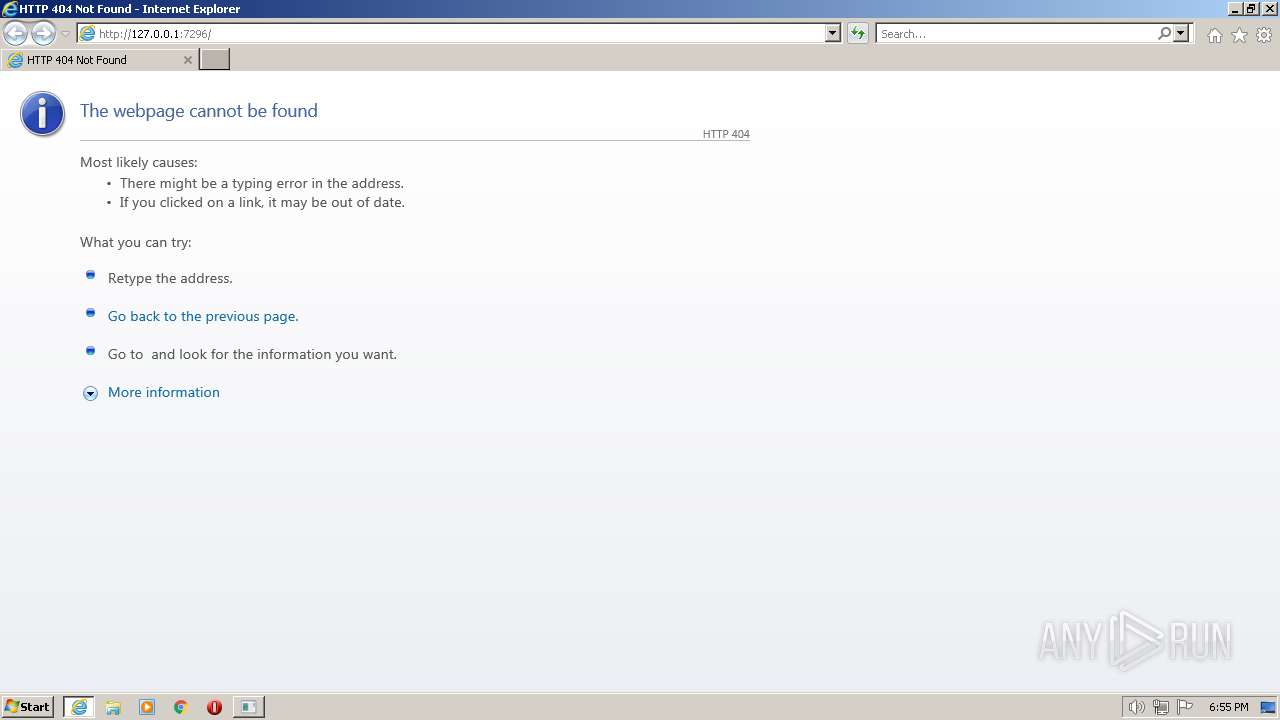
| 3012 | "C:\Program Files\Internet Explorer\iexplore.exe" http://127.0.0.1:7296/ | C:\Program Files\Internet Explorer\iexplore.exe | Sayo_CLI_Windows.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3572 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3012 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
18 476
Read events
18 240
Write events
232
Delete events
4
Modification events
| (PID) Process: | (3012) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3012) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3012) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31005824 | |||
| (PID) Process: | (3012) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3012) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31005824 | |||
| (PID) Process: | (3012) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3012) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3012) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3012) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3012) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
20
Text files
6
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3012 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\RecoveryStore.{42C873D0-1D90-11EB-BA2C-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 3012 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{7C2B6070-8873-11ED-80DA-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 3012 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF156483F2AD4C19D0.TMP | gmc | |
MD5:— | SHA256:— | |||
| 3012 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{7C2B606F-8873-11ED-80DA-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 3012 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF5FDF7FAC5AB2B6E4.TMP | gmc | |
MD5:— | SHA256:— | |||
| 3012 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3012 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | der | |
MD5:— | SHA256:— | |||
| 3012 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF7E03D6EB5B772F29.TMP | gmc | |
MD5:— | SHA256:— | |||
| 3012 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\{82809F7C-8873-11ED-80DA-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 3012 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
8
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3012 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
3012 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3012 | iexplore.exe | GET | 200 | 8.238.191.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?40d9f0034b78b6c2 | US | compressed | 4.70 Kb | whitelisted |
3012 | iexplore.exe | GET | 200 | 8.238.191.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?9b926f665869bdff | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3012 | iexplore.exe | 204.79.197.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3012 | iexplore.exe | 8.238.191.126:80 | ctldl.windowsupdate.com | LEVEL3 | US | suspicious |
3012 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | EDGECAST | GB | whitelisted |
3012 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |