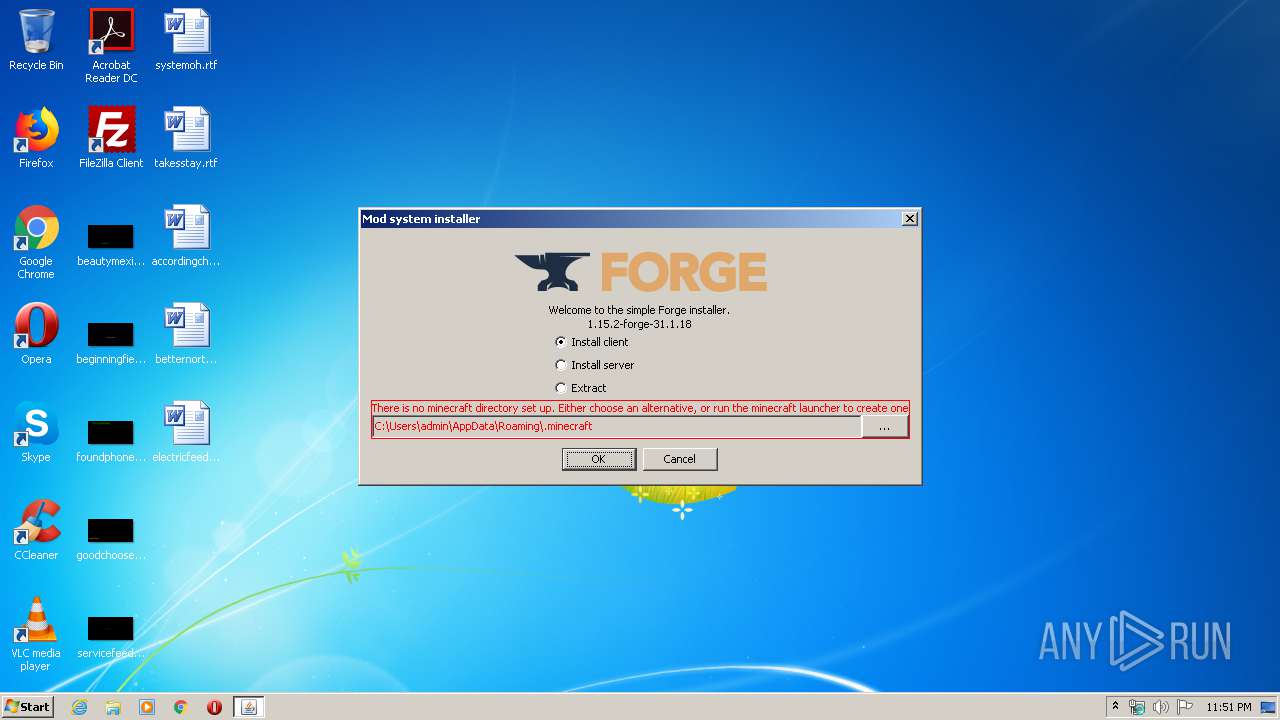
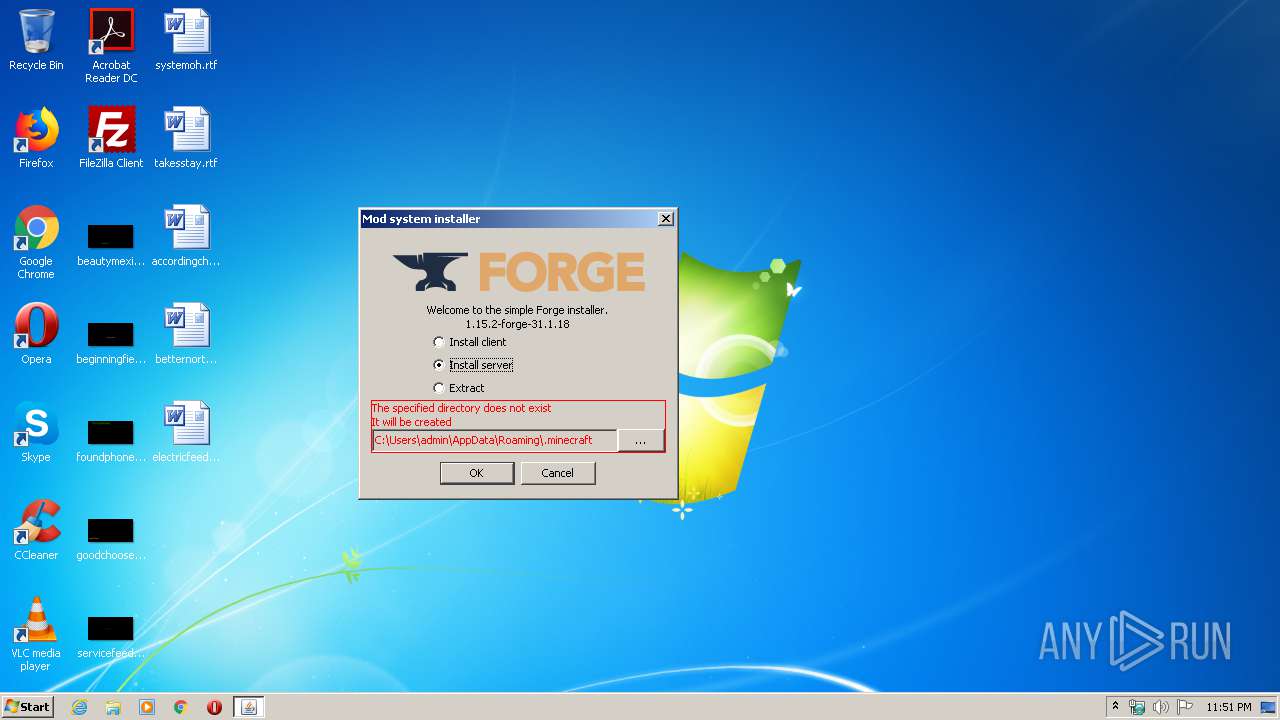
| File name: | forge-1.15.2-31.1.18-installer.jar |
| Full analysis: | https://app.any.run/tasks/8a5e9339-35ce-4b20-9e2f-d4355f54a861 |
| Verdict: | Malicious activity |
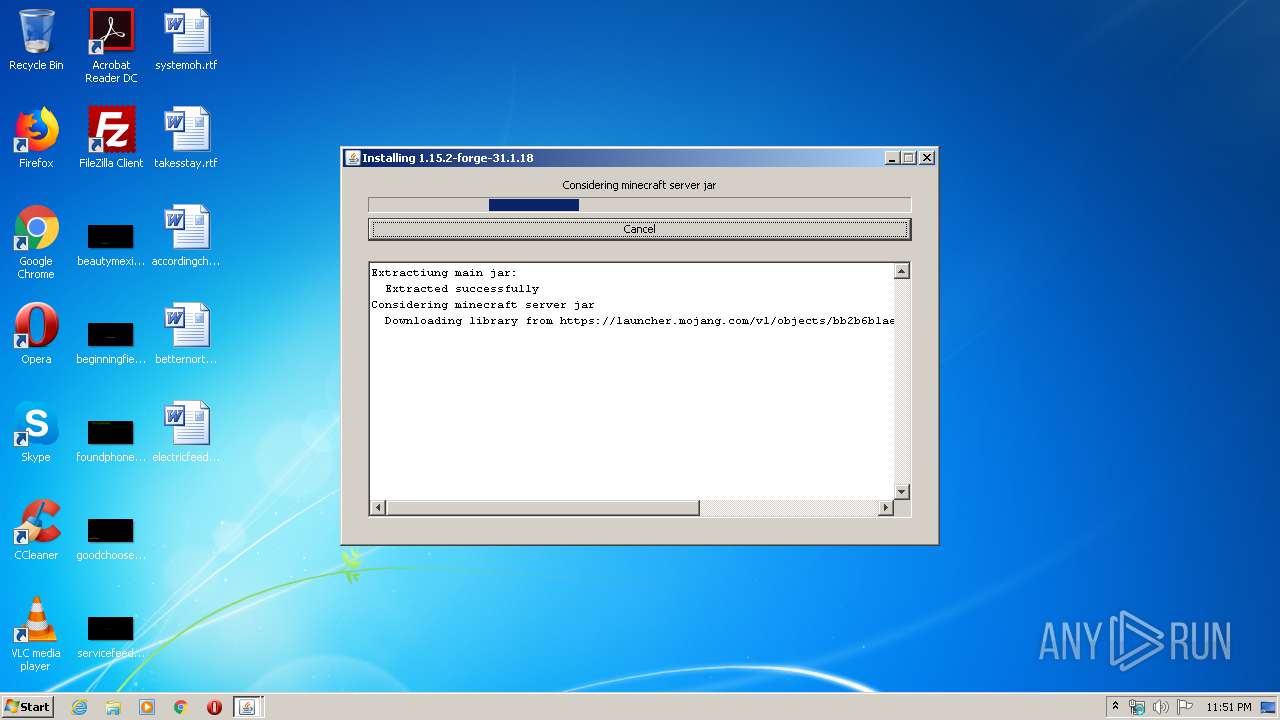
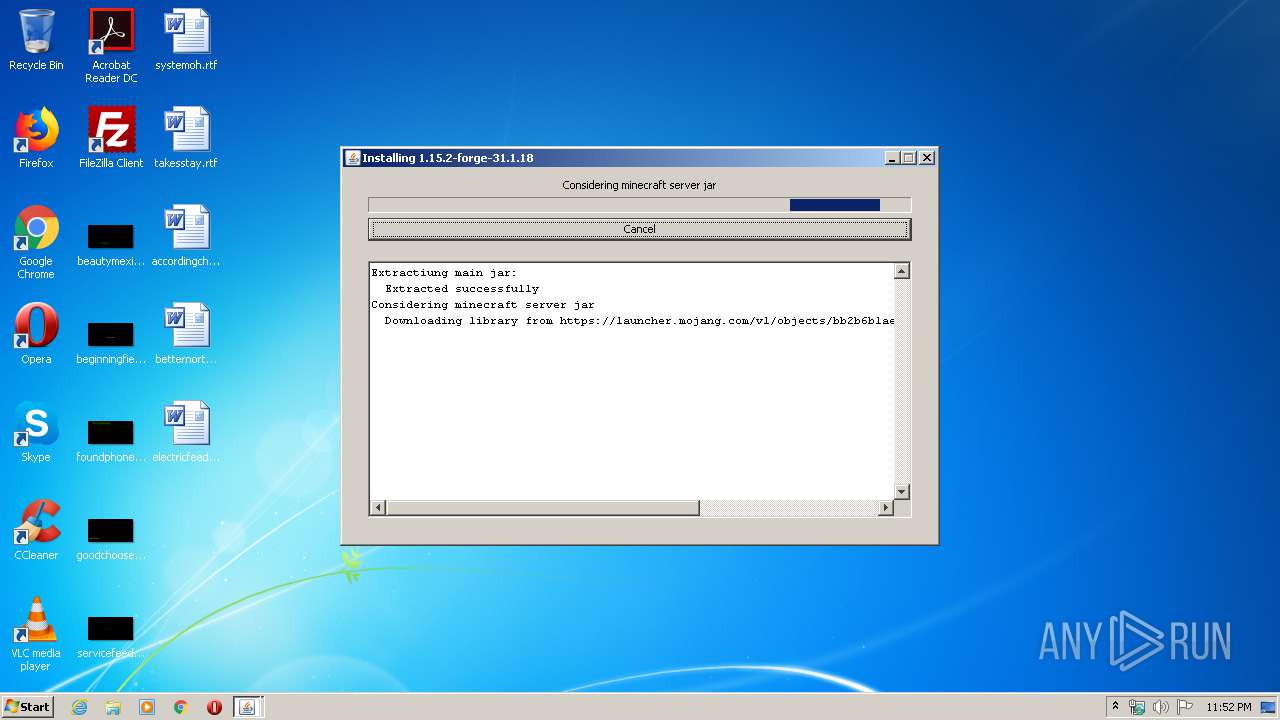
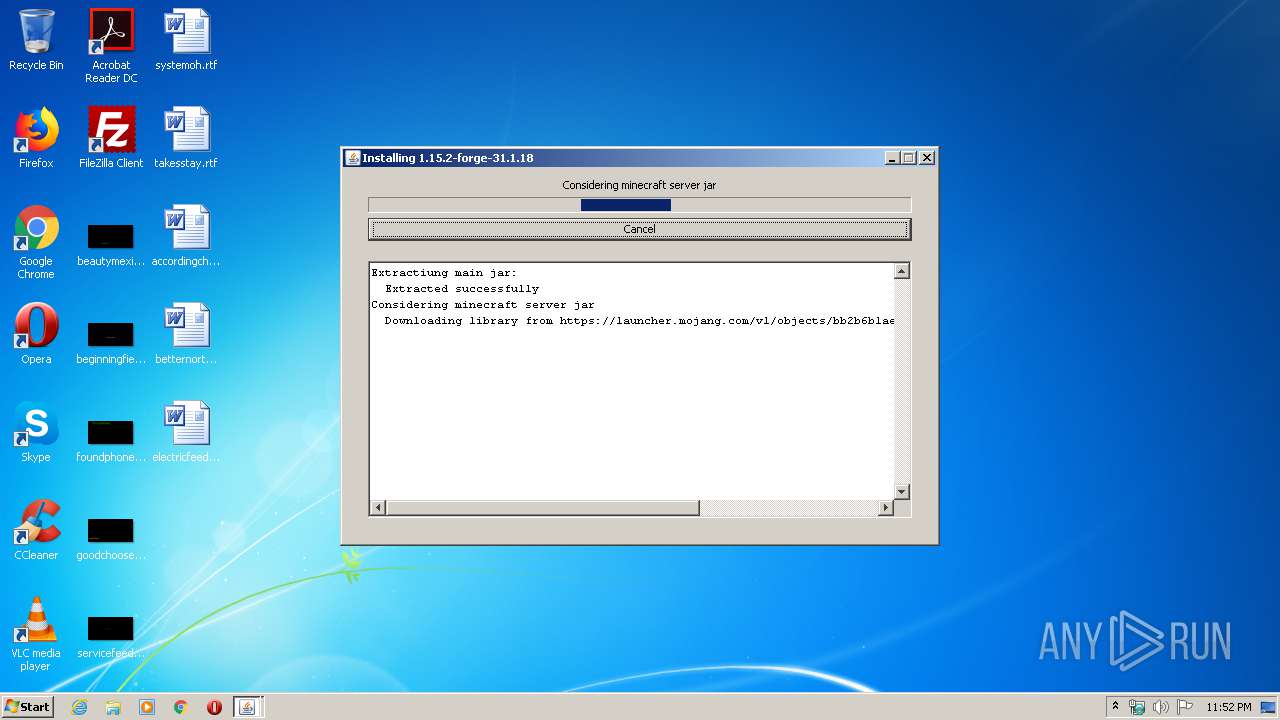
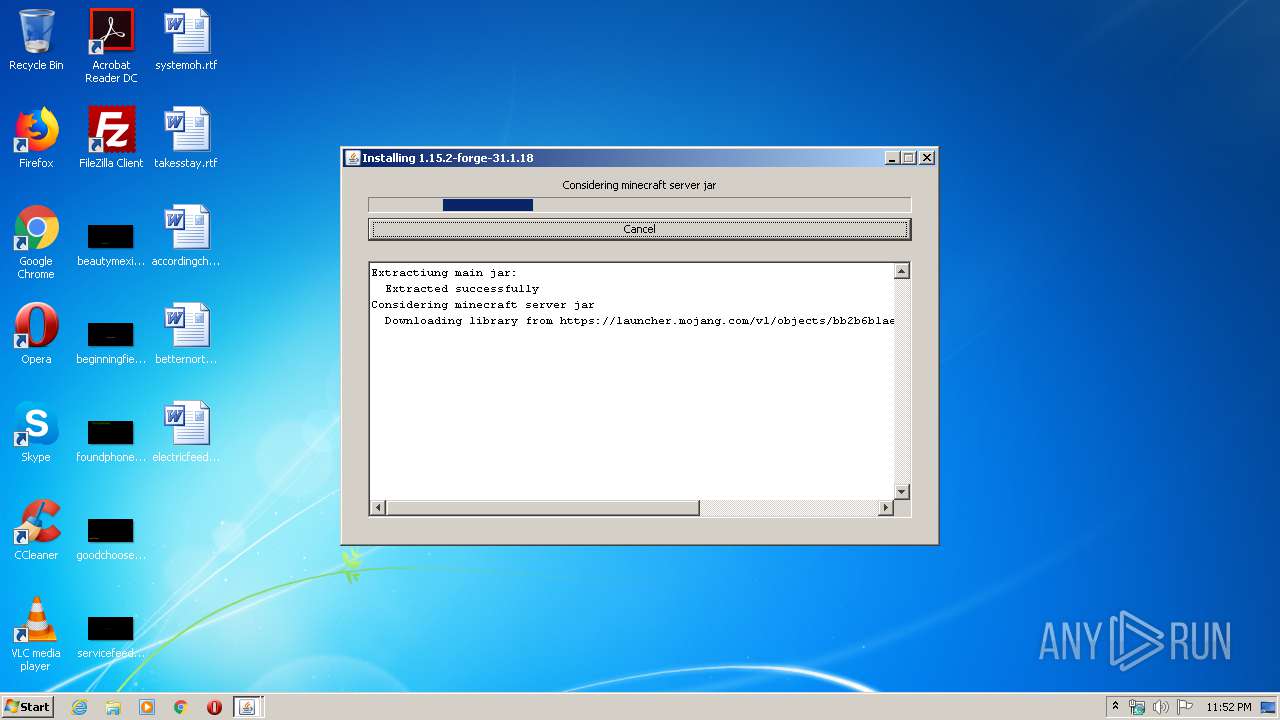
| Analysis date: | March 06, 2020, 23:51:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/java-archive |
| File info: | Java archive data (JAR) |
| MD5: | CA083CB95A657042D7EB4D23A742BC53 |
| SHA1: | 7F4AFCCEF48F07550F9175148B683CA62ACFD548 |
| SHA256: | ADF0381B22C85E2DB265C95D324CBE78FEA4646C0C15DBD15E168F8E06207730 |
| SSDEEP: | 196608:lnZ3Fq/E7VDsOs3pRGX66pHOZvd+/gqQzbYtRRTBx9t:FZ3FqcDi3Upud+ovzbMvTBxf |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the user directory
- javaw.exe (PID: 4092)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xpi | | | Mozilla Firefox browser extension (66.6) |
|---|---|---|
| .zip | | | ZIP compressed archive (33.3) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0808 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:02:27 06:19:18 |
| ZipCRC: | 0x52e6d791 |
| ZipCompressedSize: | 11800 |
| ZipUncompressedSize: | 31810 |
| ZipFileName: | META-INF/MANIFEST.MF |
Total processes
34
Monitored processes
1
Malicious processes
1
Suspicious processes
0
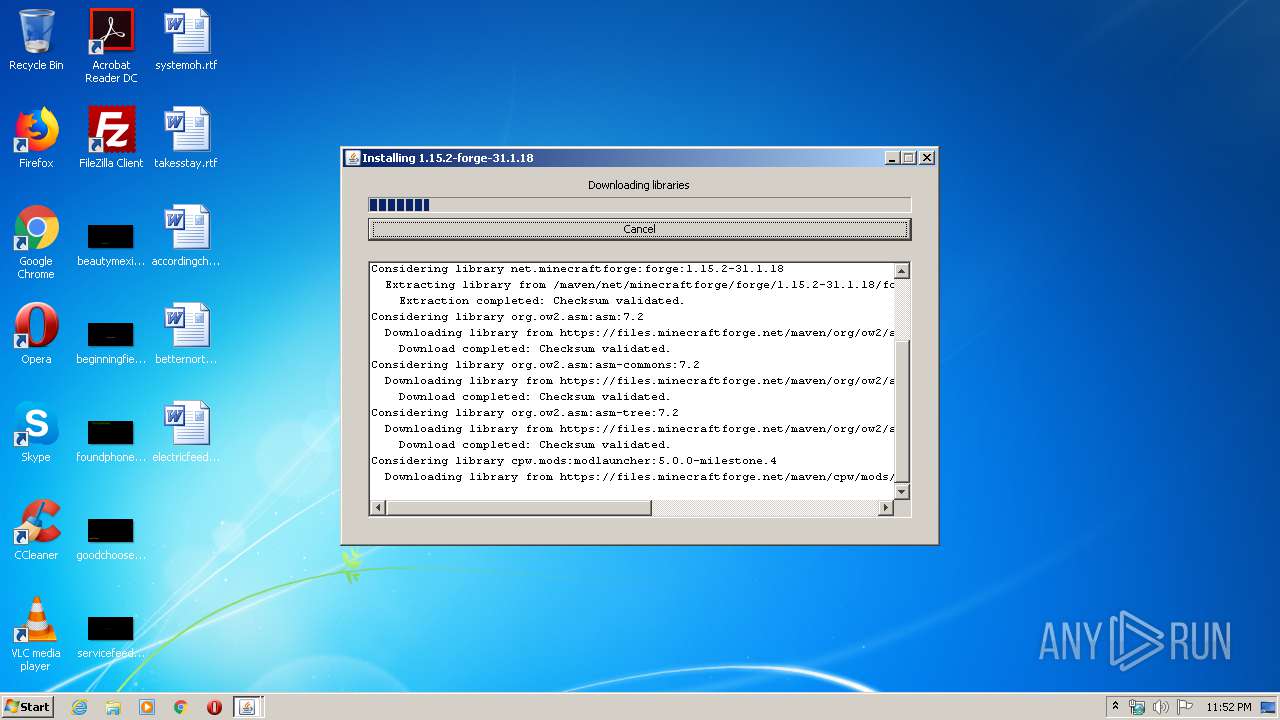
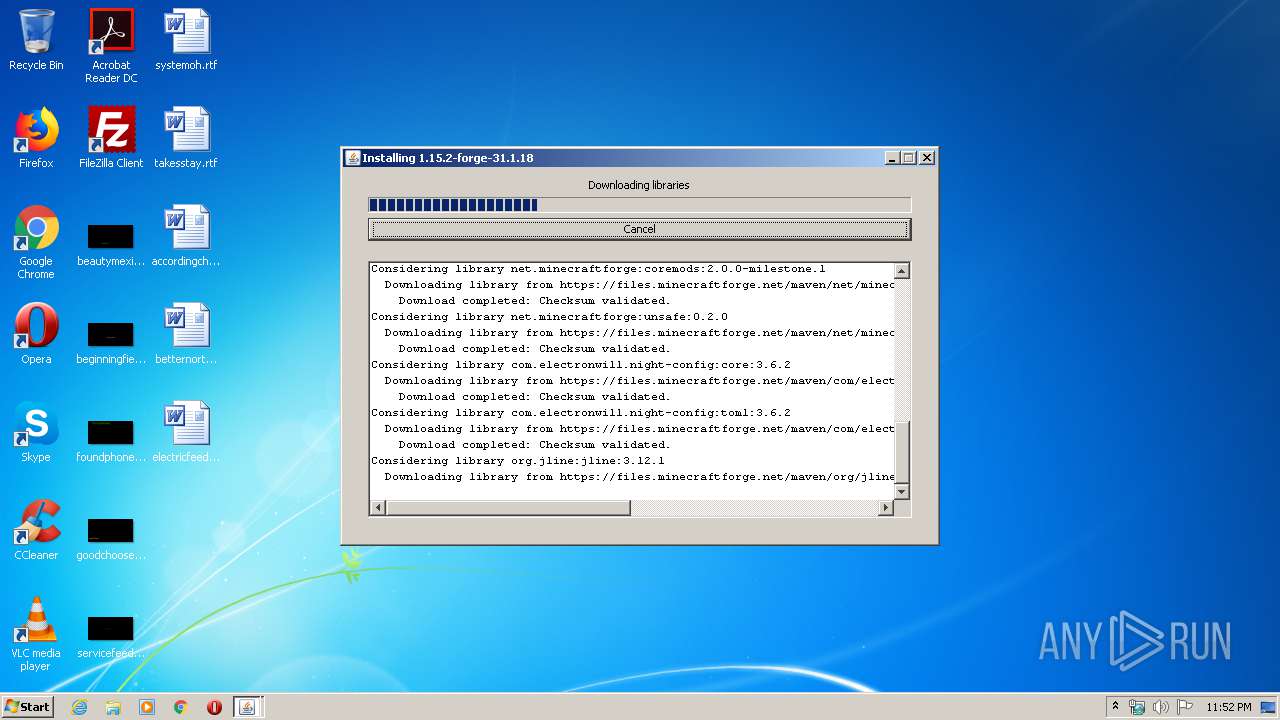
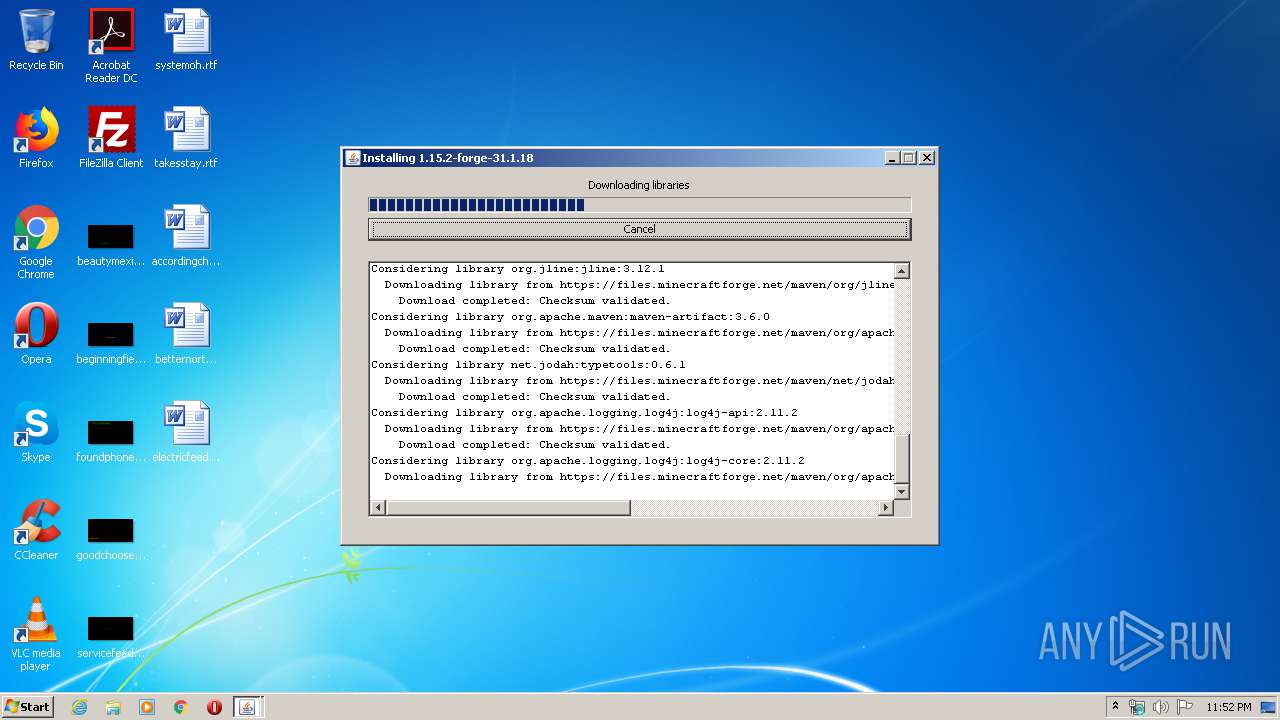
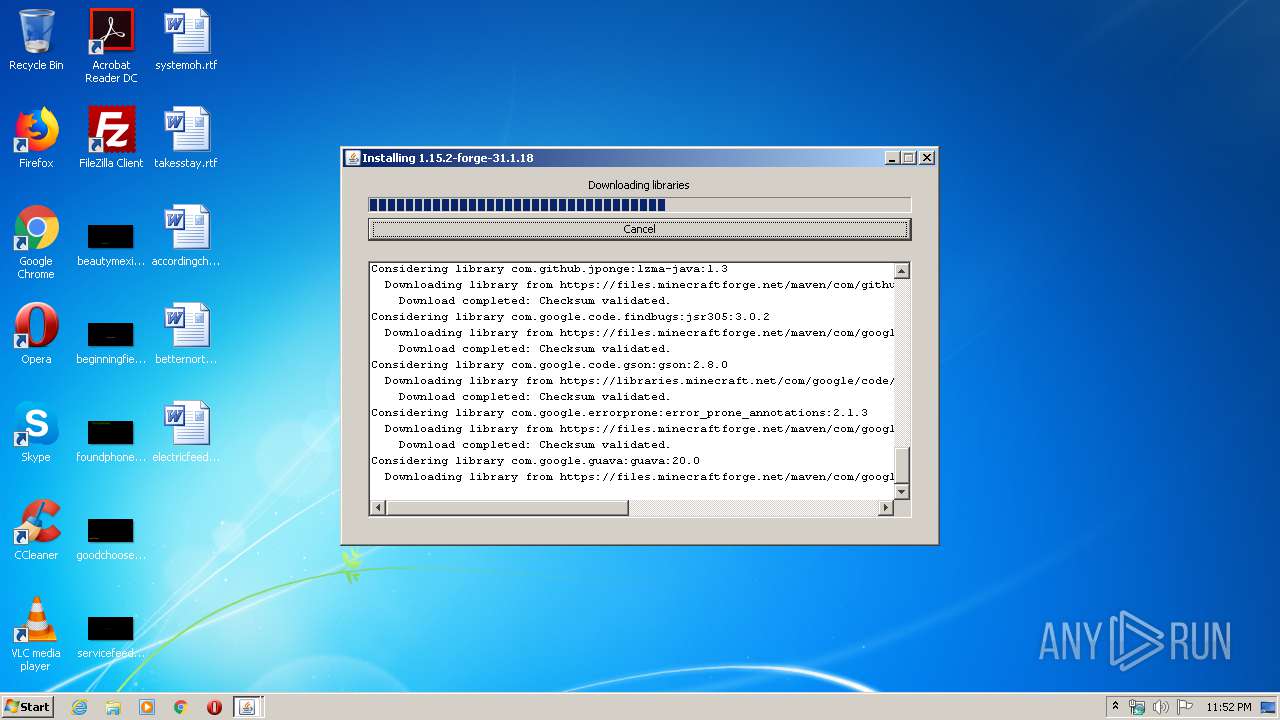
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
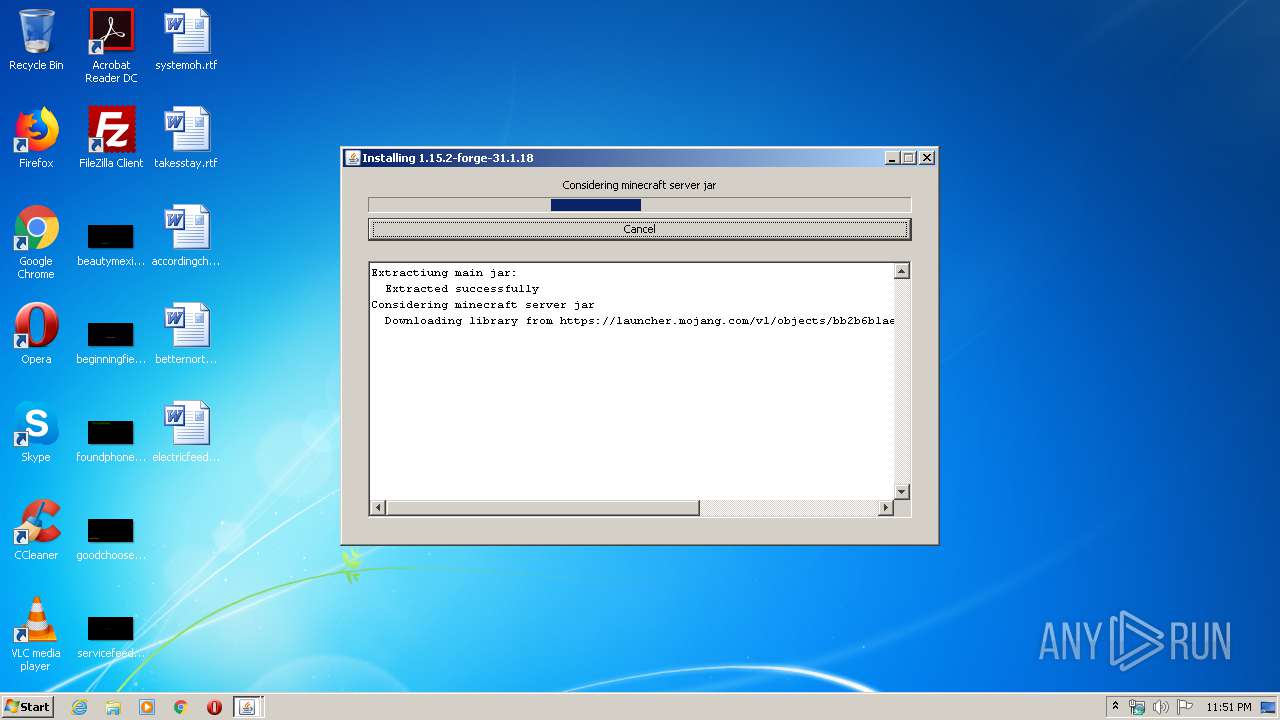
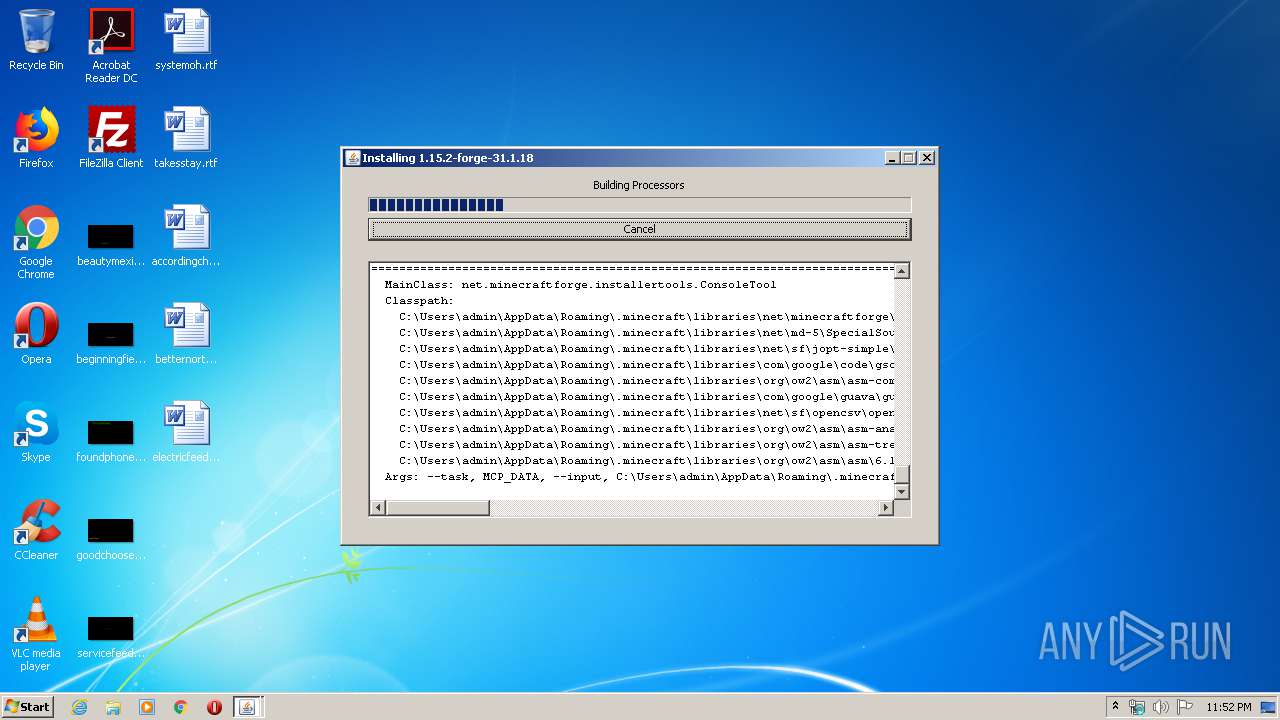
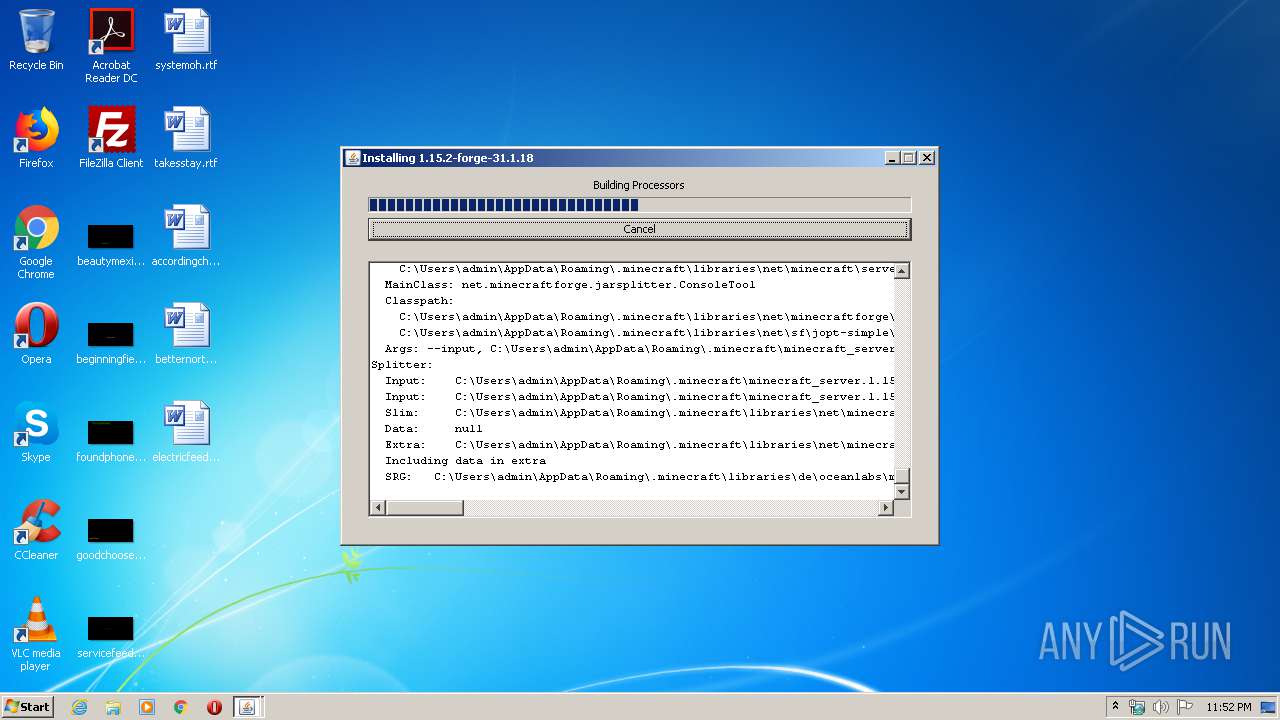
| 4092 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -jar "C:\Users\admin\AppData\Local\Temp\forge-1.15.2-31.1.18-installer.jar" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | explorer.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
Total events
23
Read events
22
Write events
1
Delete events
0
Modification events
| (PID) Process: | (4092) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: javaw.exe | |||
Executable files
16
Suspicious files
30
Text files
3
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4092 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio3548320383436903395.tmp | — | |
MD5:— | SHA256:— | |||
| 4092 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\minecraft_server.1.15.2.jar | — | |
MD5:— | SHA256:— | |||
| 4092 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 4092 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\libraries\net\minecraftforge\coremods\2.0.0-milestone.1\coremods-2.0.0-milestone.1.jar | compressed | |
MD5:— | SHA256:— | |||
| 4092 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\libraries\cpw\mods\modlauncher\5.0.0-milestone.4\modlauncher-5.0.0-milestone.4.jar | compressed | |
MD5:— | SHA256:— | |||
| 4092 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\1.15.2.json | text | |
MD5:— | SHA256:— | |||
| 4092 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\libraries\net\minecraftforge\forge\1.15.2-31.1.18\forge-1.15.2-31.1.18.jar | java | |
MD5:— | SHA256:— | |||
| 4092 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\forge-1.15.2-31.1.18.jar | java | |
MD5:— | SHA256:— | |||
| 4092 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\libraries\net\minecraftforge\eventbus\2.0.0-milestone.1-service\eventbus-2.0.0-milestone.1-service.jar | compressed | |
MD5:— | SHA256:— | |||
| 4092 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\libraries\cpw\mods\grossjava9hacks\1.1.0\grossjava9hacks-1.1.0.jar | compressed | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
4
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4092 | javaw.exe | 99.86.1.139:443 | launchermeta.mojang.com | AT&T Services, Inc. | US | unknown |
4092 | javaw.exe | 143.204.212.134:443 | launcher.mojang.com | — | US | unknown |
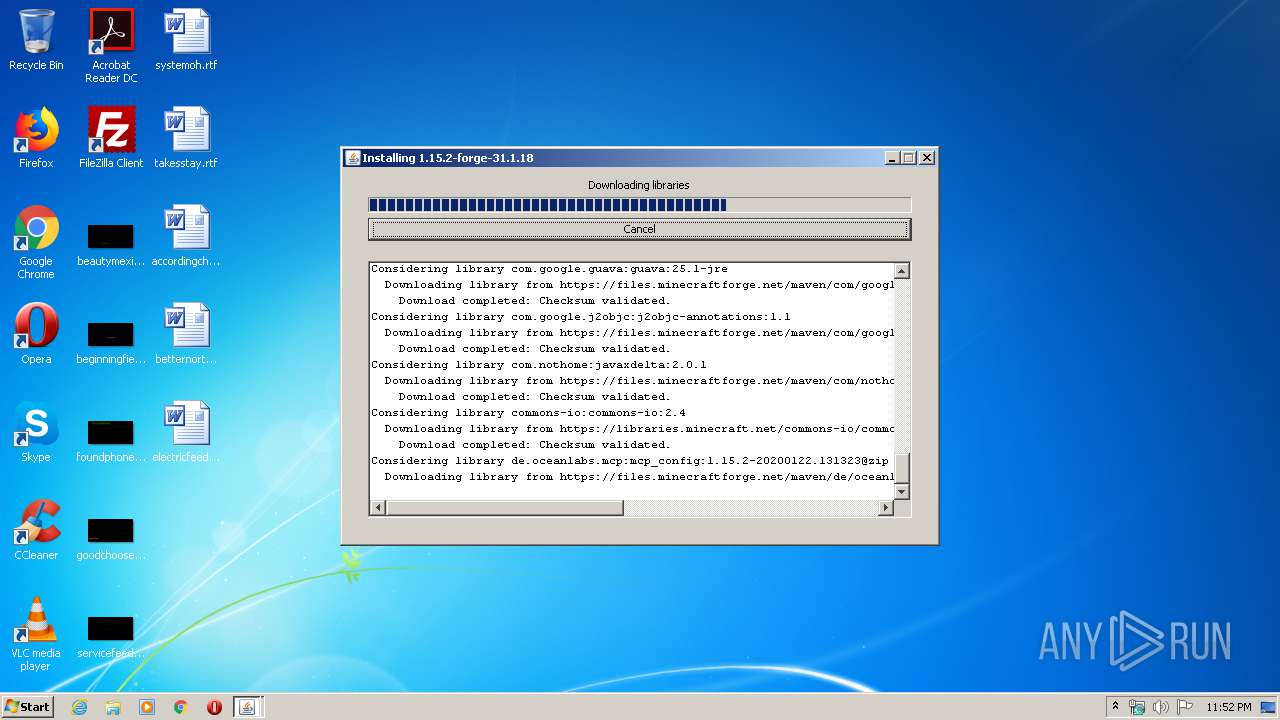
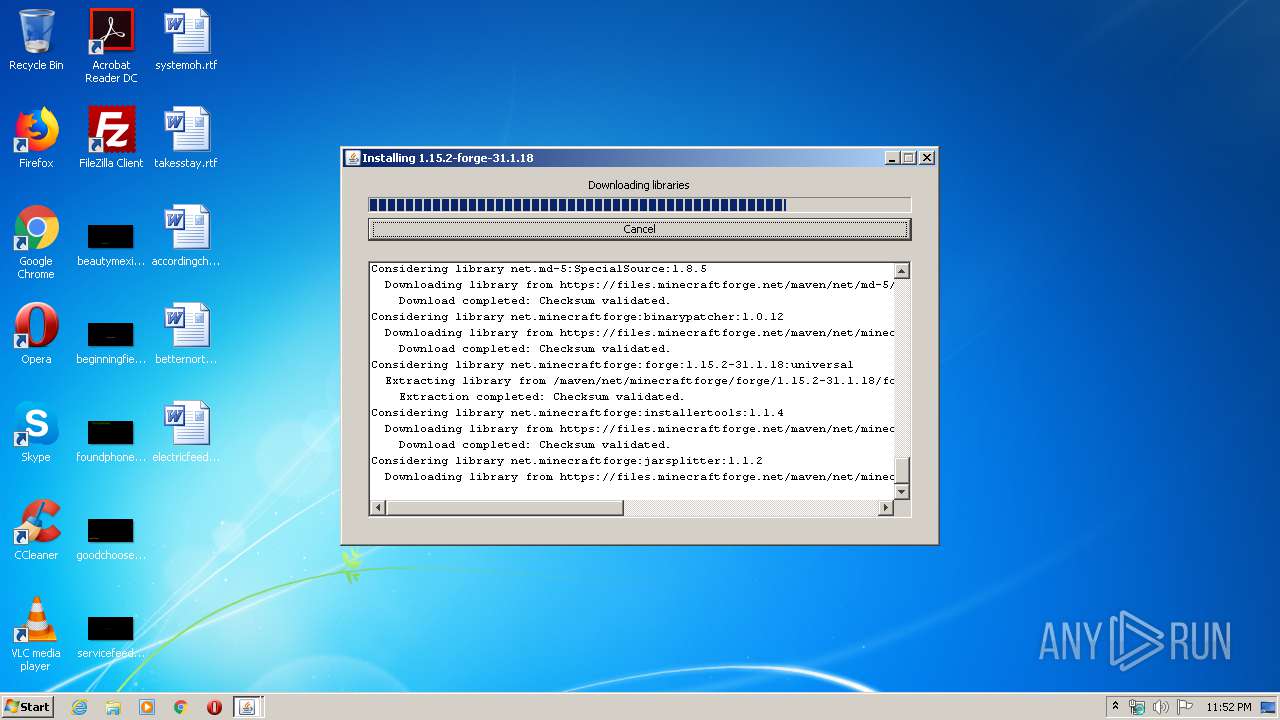
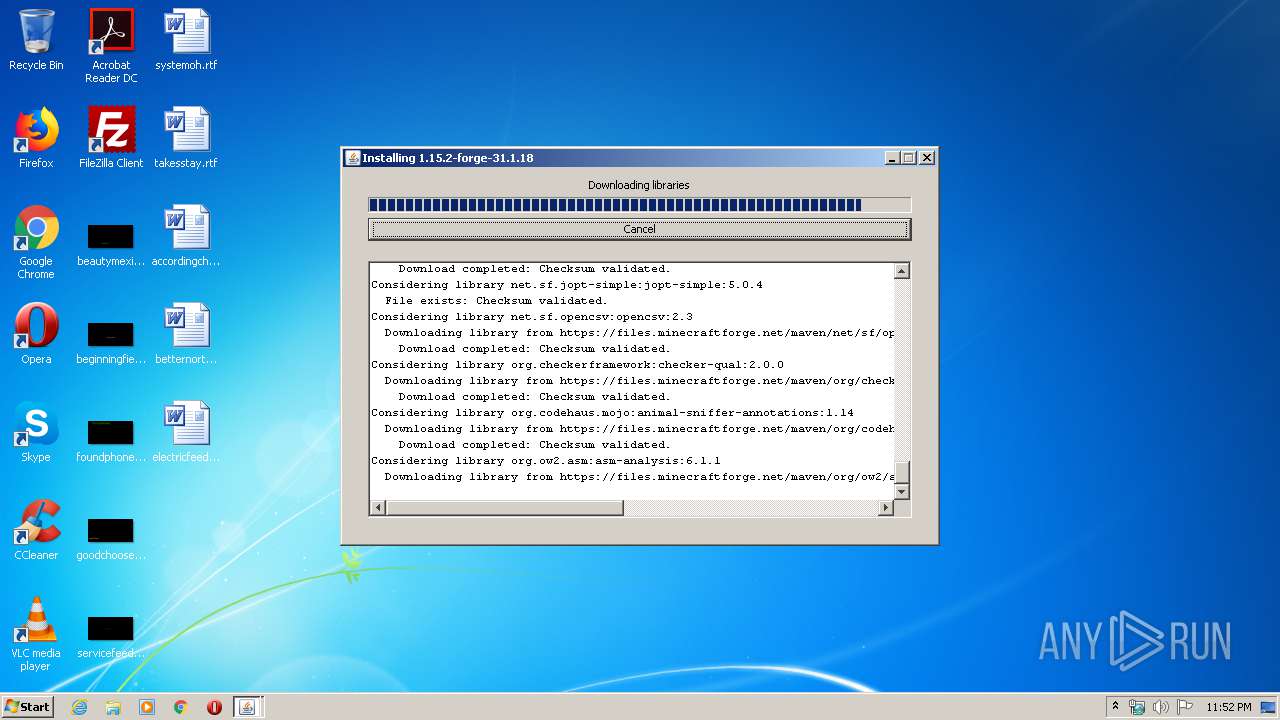
4092 | javaw.exe | 142.44.226.189:443 | files.minecraftforge.net | OVH SAS | CA | malicious |
4092 | javaw.exe | 99.86.4.83:443 | libraries.minecraft.net | AT&T Services, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
launchermeta.mojang.com |
| whitelisted |
launcher.mojang.com |
| whitelisted |
files.minecraftforge.net |
| suspicious |
libraries.minecraft.net |
| shared |