| File name: | KMSPico 11.2.1.exe |
| Full analysis: | https://app.any.run/tasks/543286ad-a59b-4d54-9a49-5244cddd148c |
| Verdict: | Malicious activity |
| Analysis date: | July 02, 2021, 15:22:10 |
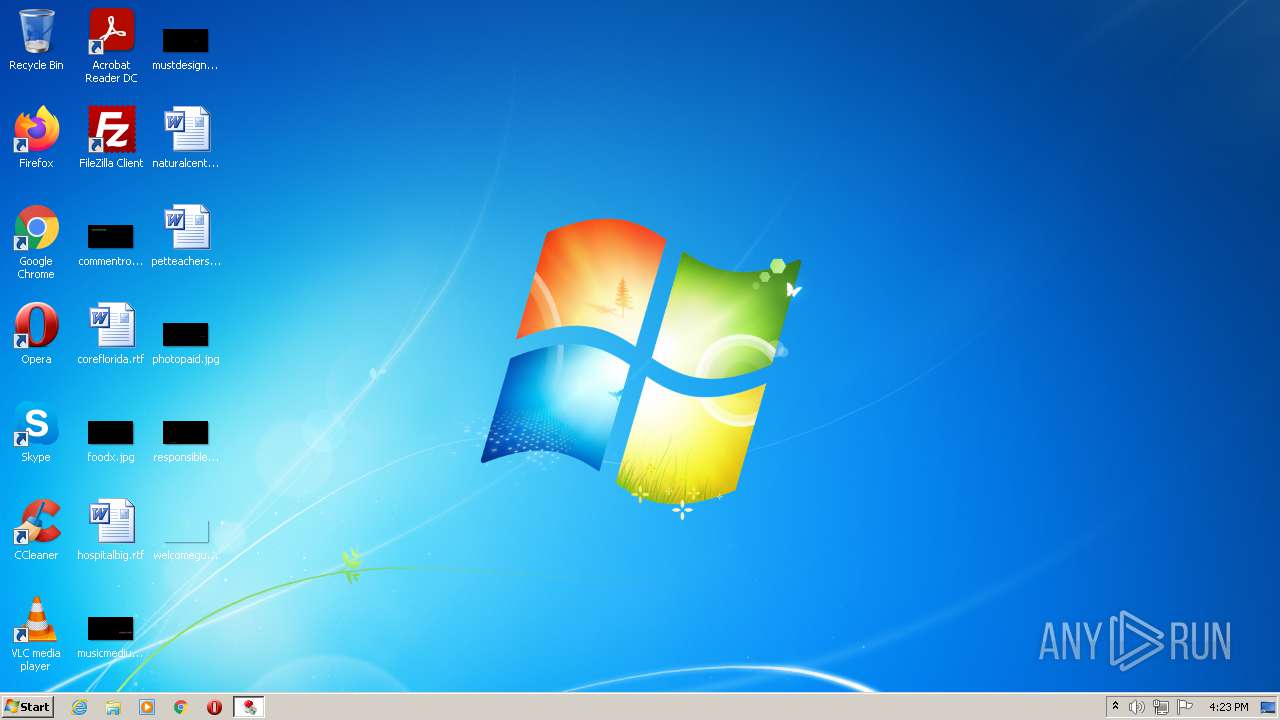
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 9DCFAD9454F9D4FC64E14F829C3E49AD |
| SHA1: | D948F568FEA434999AE3C429AD5DBCCFBE56A6BD |
| SHA256: | ADD0FC5F32E919997A4BC3763562E3859B08C24230DCEF1714027945A0DAA9F6 |
| SSDEEP: | 196608:99B0xcE6pAGbQhgiQWY3gFE3mNRxNf39EhD2jh0IgRYLqrnU8LxBxCLS3xZCsFW:97U10bwHFE3mNRz3SwOIgRYLqYoX/zng |
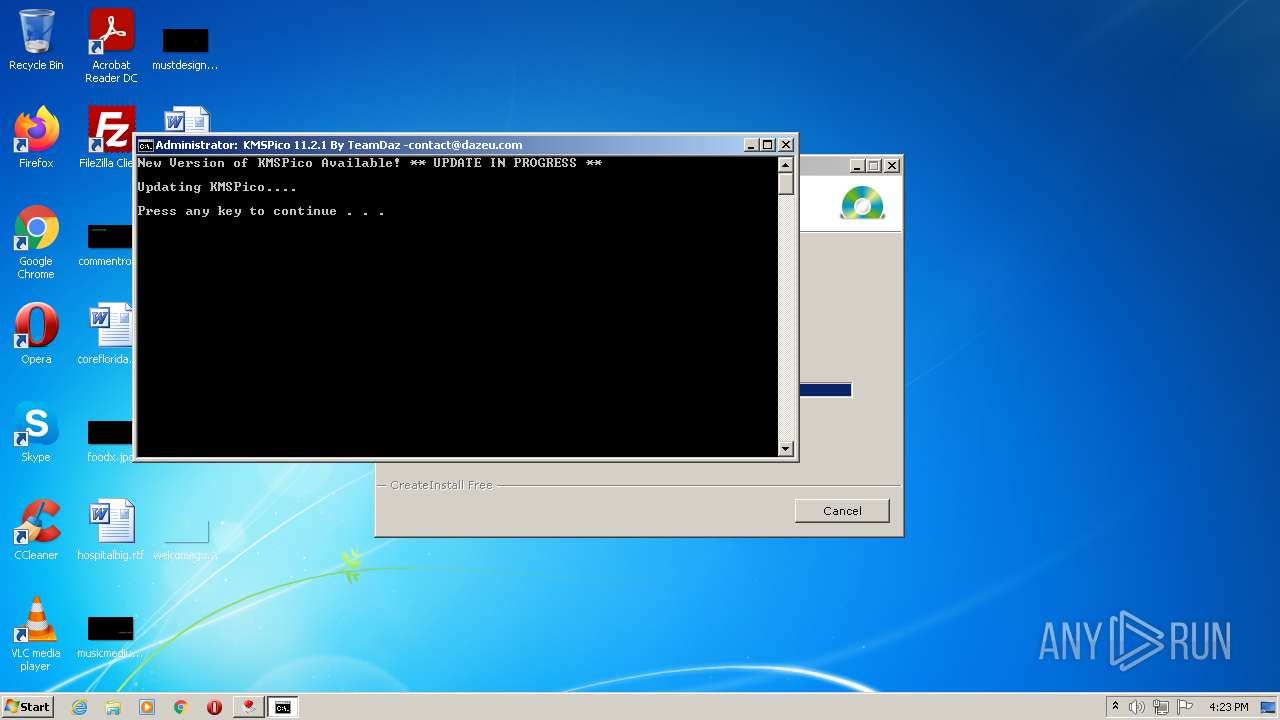
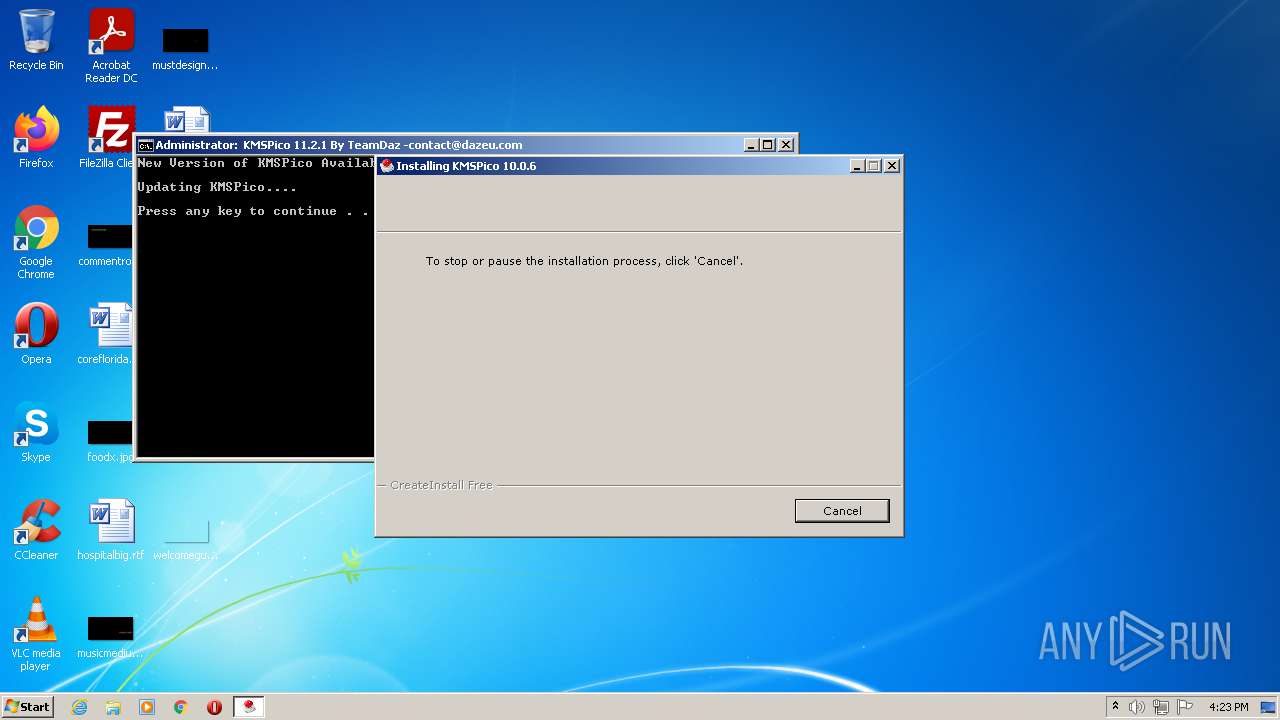
MALICIOUS
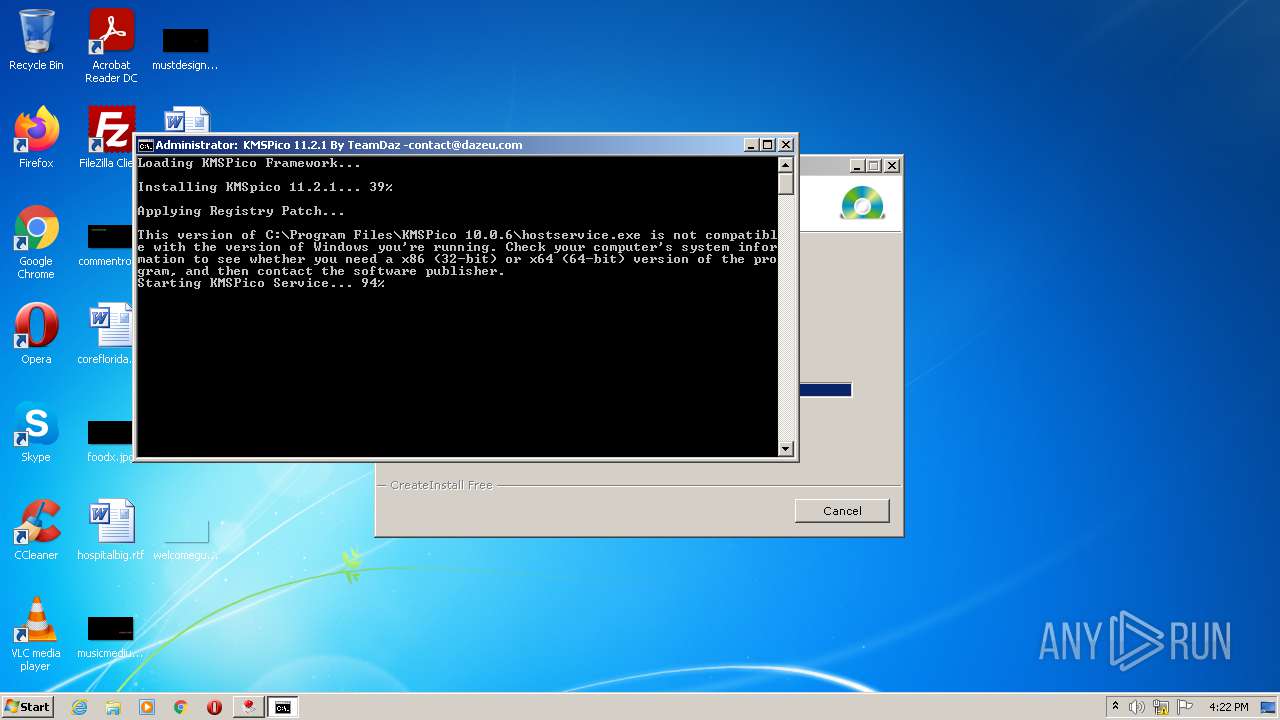
Drops executable file immediately after starts
- KMSPico 11.2.1.exe (PID: 3512)
- kmsservice.exe (PID: 3132)
- cmd.exe (PID: 2700)
- KMSpico_setup.exe (PID: 2936)
- KMSpico_setup.tmp (PID: 368)
Modifies Windows Defender service settings
- KMS.exe (PID: 3944)
- KMS.exe (PID: 2080)
Disables Windows Defender
- KMS.exe (PID: 3944)
- KMS.exe (PID: 2080)
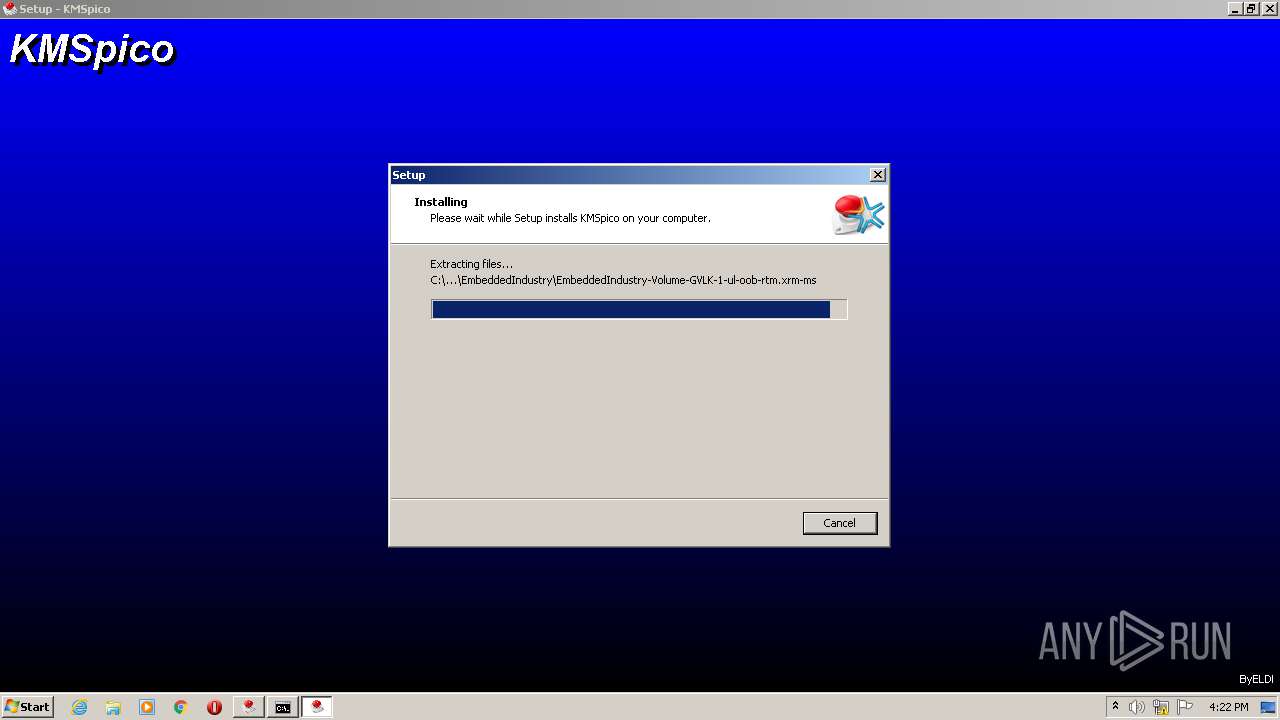
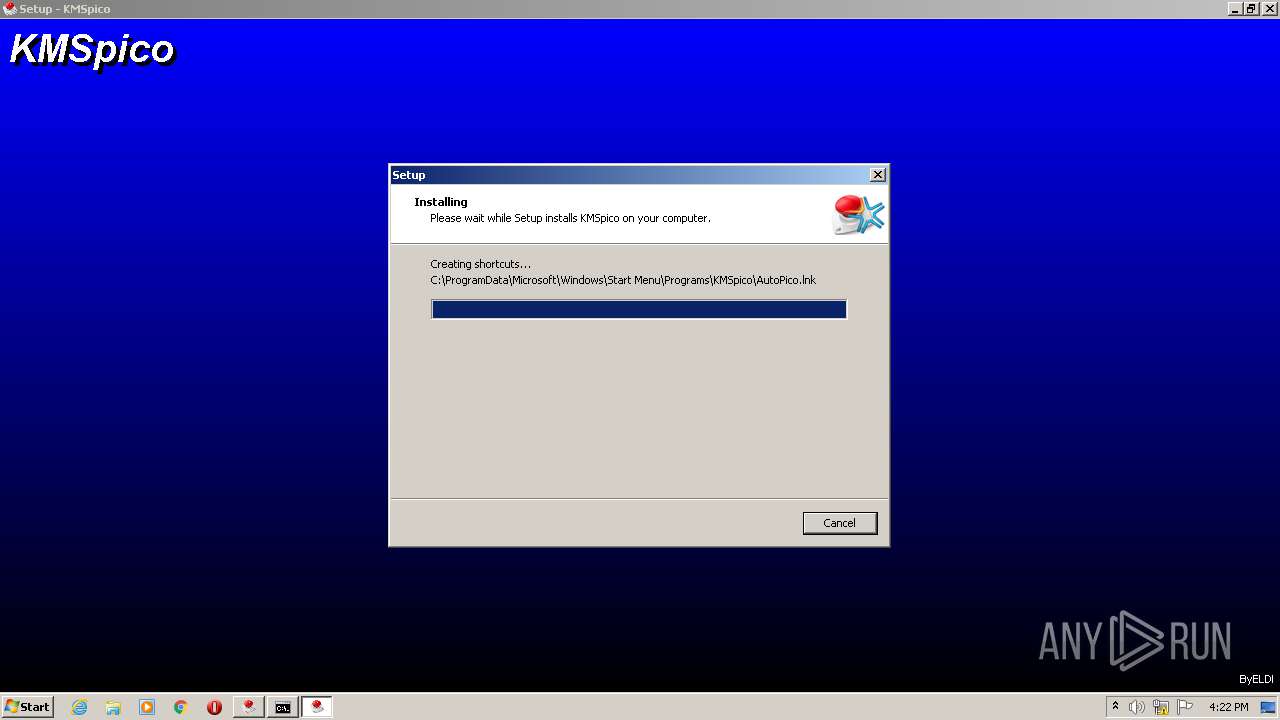
Writes to a start menu file
- cmd.exe (PID: 2700)
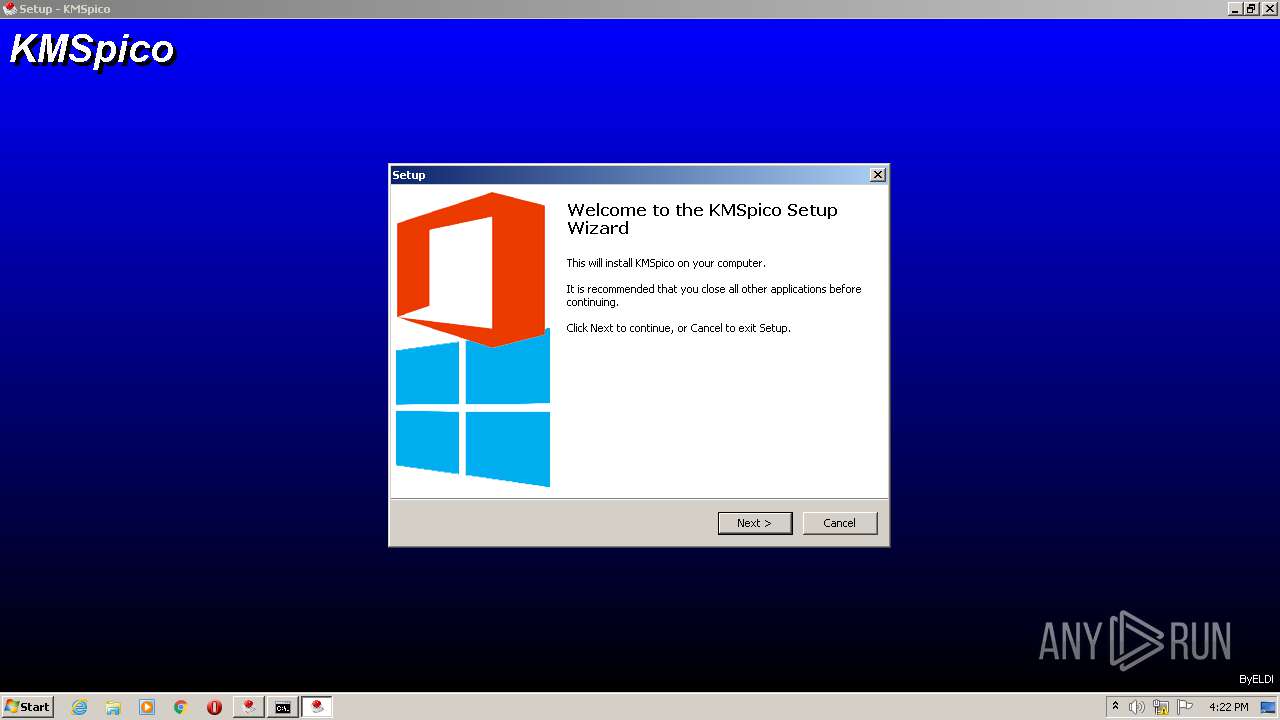
Application was dropped or rewritten from another process
- KMSpico_setup.exe (PID: 2936)
- KMS.exe (PID: 3944)
- KMS.exe (PID: 2080)
- kmsservice.exe (PID: 3132)
- UninsHs.exe (PID: 3620)
- KMSELDI.exe (PID: 1024)
- AutoPico.exe (PID: 3452)
- KMSELDI.exe (PID: 1336)
- KMSELDI.exe (PID: 3044)
Loads dropped or rewritten executable
- KMSPico 11.2.1.exe (PID: 3512)
- KMSELDI.exe (PID: 1024)
- KMSELDI.exe (PID: 3044)
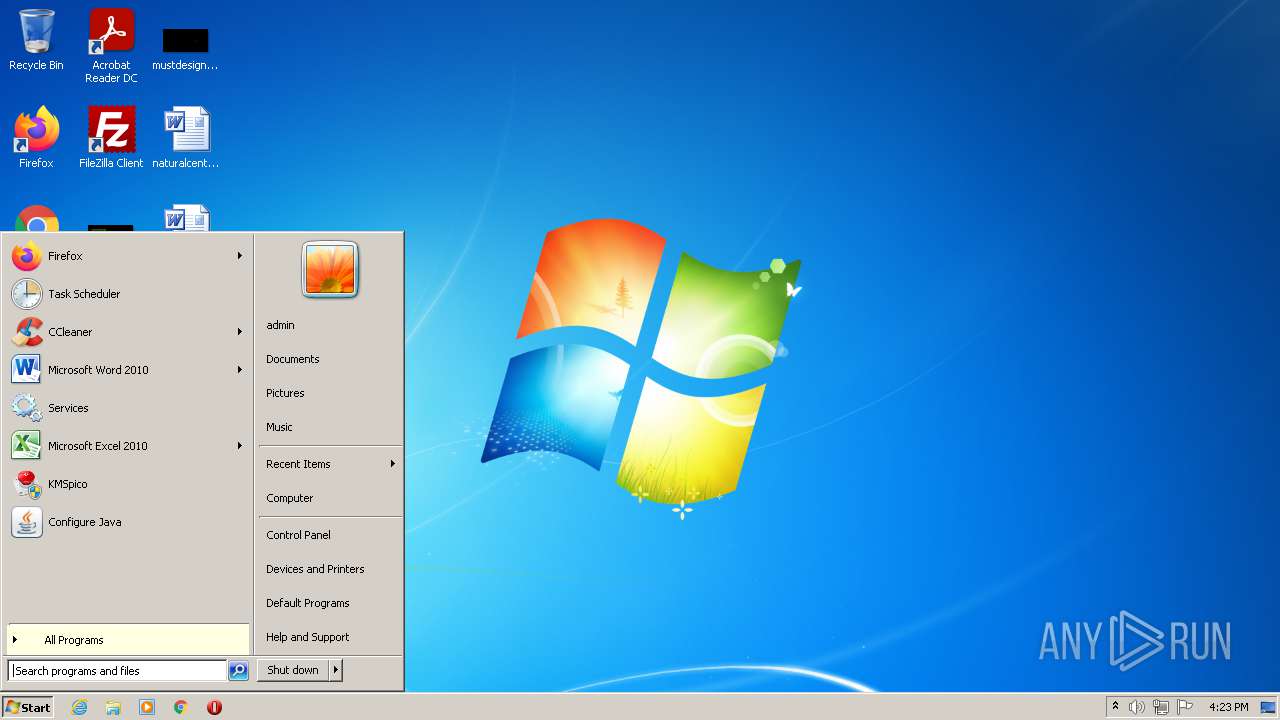
Uses Task Scheduler to run other applications
- cmd.exe (PID: 3608)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2260)
SUSPICIOUS
Reads the Windows organization settings
- KMSPico 11.2.1.exe (PID: 3512)
- KMSpico_setup.tmp (PID: 368)
Checks supported languages
- KMSPico 11.2.1.exe (PID: 3512)
- cmd.exe (PID: 3292)
- KMS.exe (PID: 3944)
- KMS.exe (PID: 2080)
- kmsservice.exe (PID: 3132)
- cmd.exe (PID: 2700)
- KMSpico_setup.tmp (PID: 368)
- KMSpico_setup.exe (PID: 2936)
- cmd.exe (PID: 3400)
- UninsHs.exe (PID: 3620)
- cmd.exe (PID: 3608)
- KMSELDI.exe (PID: 1024)
- AutoPico.exe (PID: 3452)
- cmd.exe (PID: 3668)
- KMSELDI.exe (PID: 3044)
Reads the computer name
- KMSPico 11.2.1.exe (PID: 3512)
- KMS.exe (PID: 3944)
- KMS.exe (PID: 2080)
- kmsservice.exe (PID: 3132)
- KMSpico_setup.tmp (PID: 368)
- KMSELDI.exe (PID: 1024)
- AutoPico.exe (PID: 3452)
- KMSELDI.exe (PID: 3044)
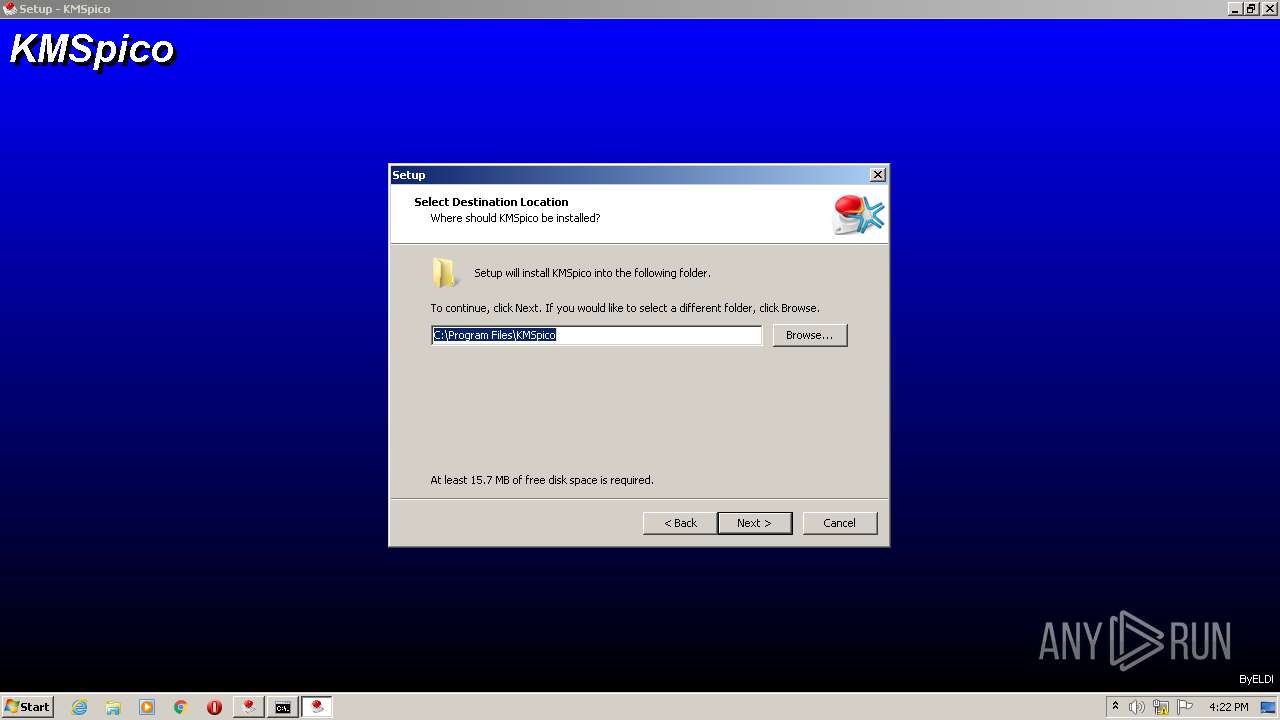
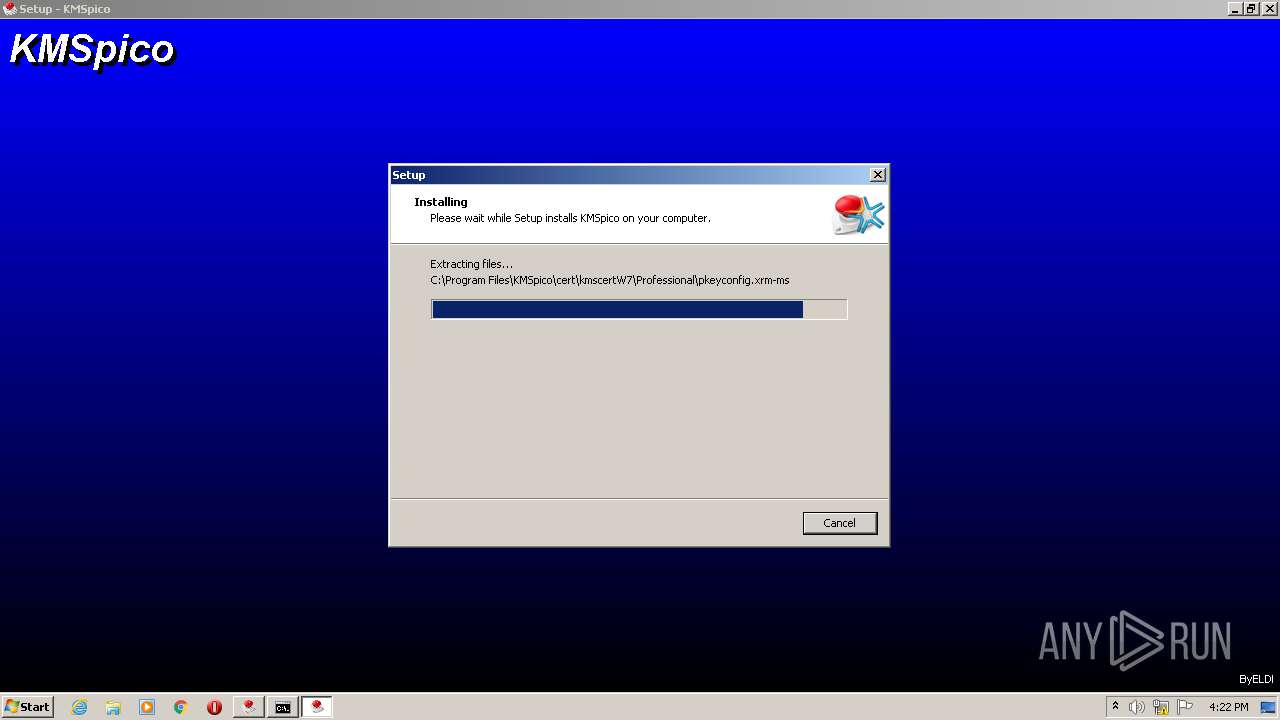
Creates a directory in Program Files
- KMSPico 11.2.1.exe (PID: 3512)
- KMSpico_setup.tmp (PID: 368)
- KMSELDI.exe (PID: 1024)
Creates files in the program directory
- KMSPico 11.2.1.exe (PID: 3512)
- KMSELDI.exe (PID: 1024)
- AutoPico.exe (PID: 3452)
- KMSELDI.exe (PID: 3044)
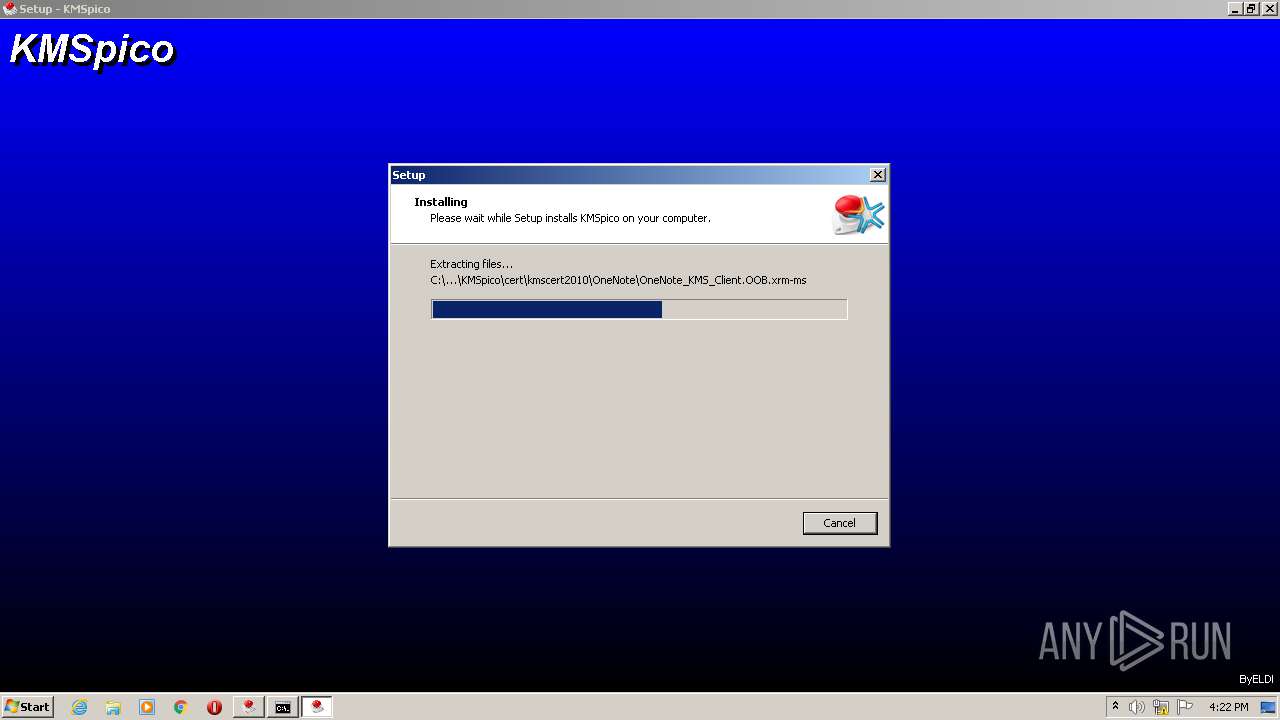
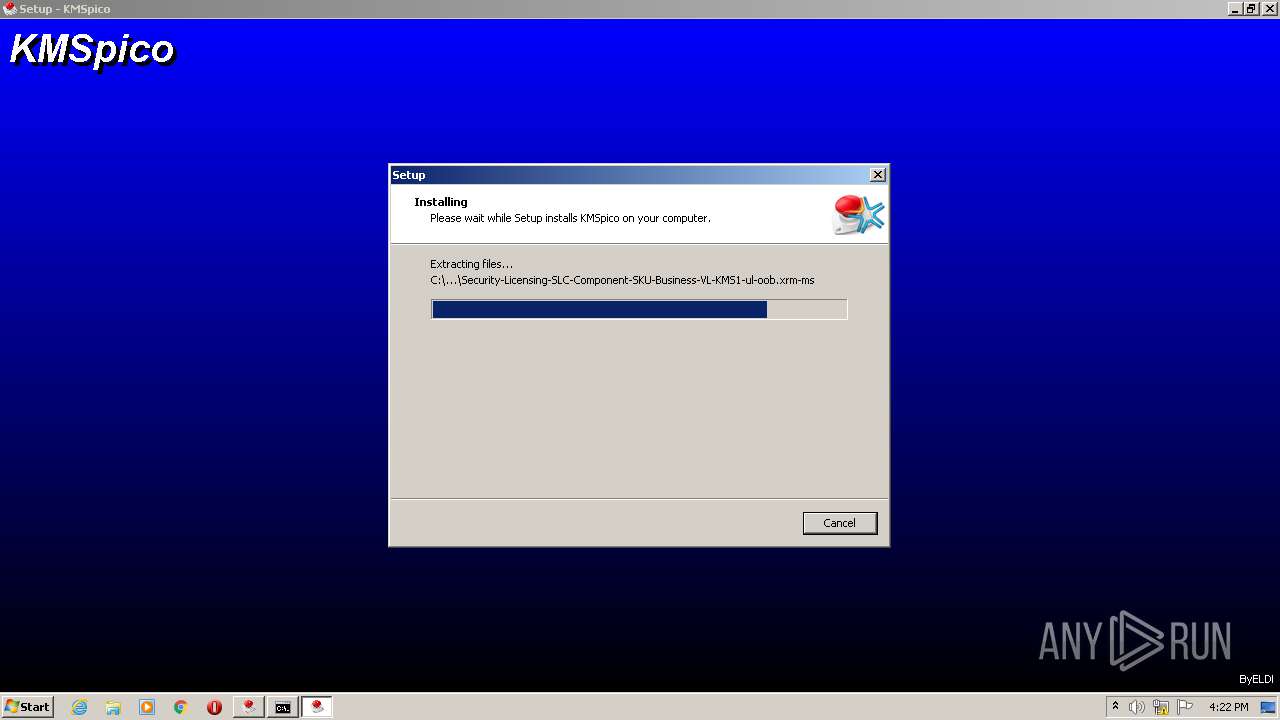
Drops a file with too old compile date
- KMSPico 11.2.1.exe (PID: 3512)
- kmsservice.exe (PID: 3132)
- cmd.exe (PID: 2700)
- KMSpico_setup.exe (PID: 2936)
- KMSpico_setup.tmp (PID: 368)
Reads Windows owner or organization settings
- KMSPico 11.2.1.exe (PID: 3512)
- KMSpico_setup.tmp (PID: 368)
Executable content was dropped or overwritten
- KMSPico 11.2.1.exe (PID: 3512)
- kmsservice.exe (PID: 3132)
- cmd.exe (PID: 2700)
- KMSpico_setup.tmp (PID: 368)
- KMSpico_setup.exe (PID: 2936)
Drops a file with a compile date too recent
- KMSPico 11.2.1.exe (PID: 3512)
Starts CMD.EXE for commands execution
- KMSPico 11.2.1.exe (PID: 3512)
- kmsservice.exe (PID: 3132)
- KMSpico_setup.tmp (PID: 368)
Reads mouse settings
- KMS.exe (PID: 3944)
- KMS.exe (PID: 2080)
Application launched itself
- KMS.exe (PID: 3944)
Creates files in the Windows directory
- KMS.exe (PID: 2080)
- KMSpico_setup.tmp (PID: 368)
Removes files from Windows directory
- KMS.exe (PID: 2080)
Drops a file that was compiled in debug mode
- kmsservice.exe (PID: 3132)
- cmd.exe (PID: 2700)
- KMSpico_setup.tmp (PID: 368)
Creates files in the user directory
- cmd.exe (PID: 2700)
Starts SC.EXE for service management
- cmd.exe (PID: 3400)
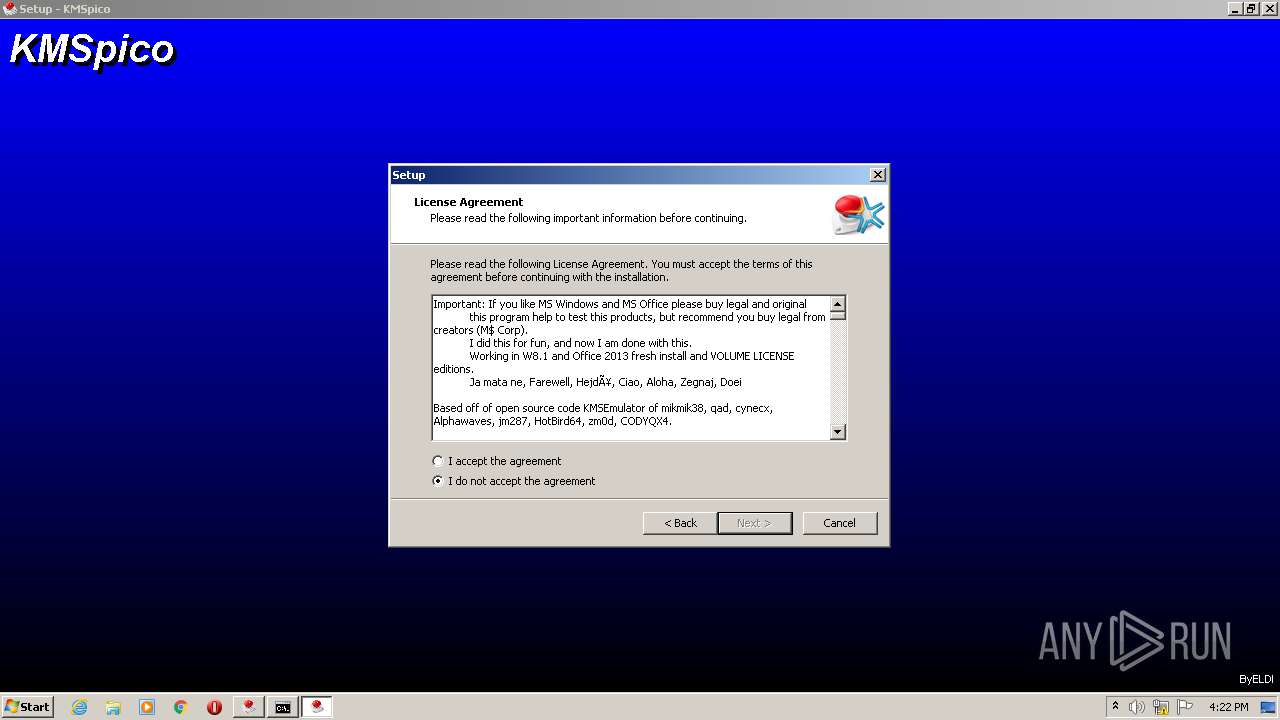
Modifies the phishing filter of IE
- KMSpico_setup.tmp (PID: 368)
Reads Environment values
- KMSELDI.exe (PID: 1024)
- AutoPico.exe (PID: 3452)
- KMSELDI.exe (PID: 3044)
Creates or modifies windows services
- KMSELDI.exe (PID: 1024)
Reads Windows Product ID
- KMSELDI.exe (PID: 1024)
INFO
Loads dropped or rewritten executable
- KMSpico_setup.tmp (PID: 368)
Application was dropped or rewritten from another process
- KMSpico_setup.tmp (PID: 368)
Creates a software uninstall entry
- KMSpico_setup.tmp (PID: 368)
Checks supported languages
- sc.exe (PID: 4080)
- schtasks.exe (PID: 2260)
Reads the computer name
- sc.exe (PID: 4080)
- schtasks.exe (PID: 2260)
Reads Microsoft Office registry keys
- KMSELDI.exe (PID: 1024)
- AutoPico.exe (PID: 3452)
- KMSELDI.exe (PID: 3044)
Creates files in the program directory
- KMSpico_setup.tmp (PID: 368)
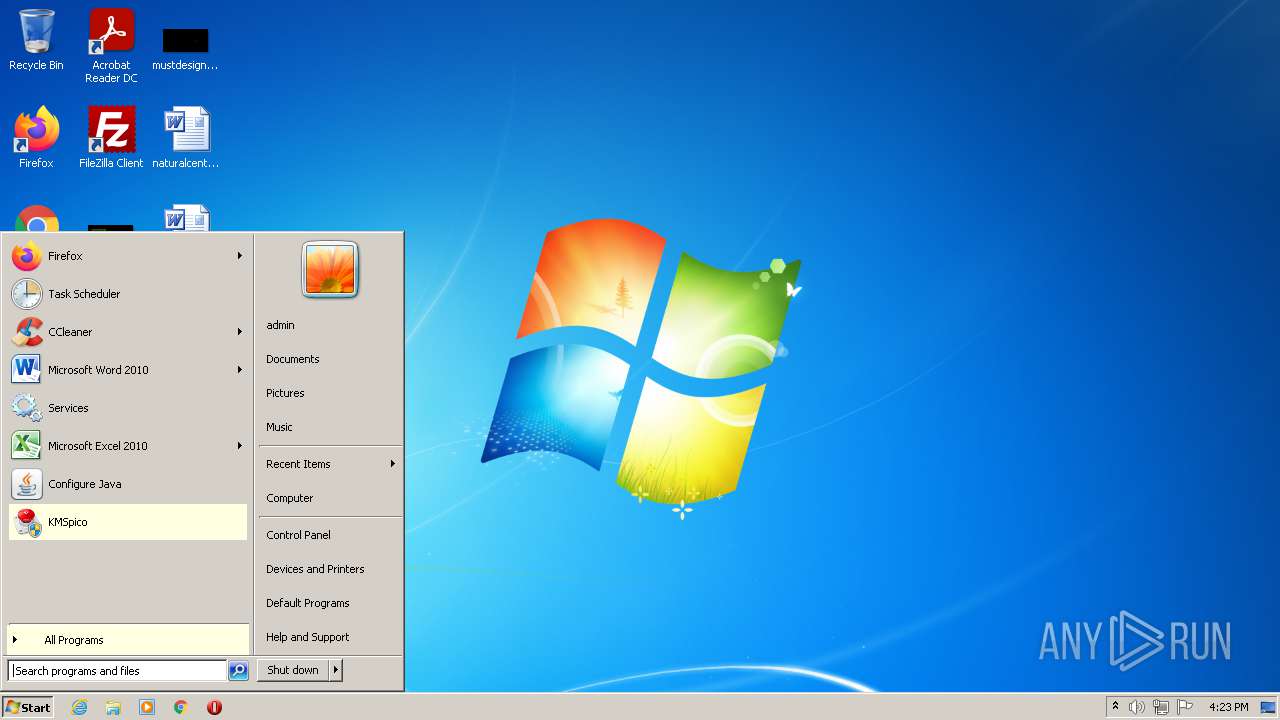
Manual execution by user
- KMSELDI.exe (PID: 1336)
- KMSELDI.exe (PID: 3044)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (52.5) |
|---|---|---|
| .scr | | | Windows screen saver (22) |
| .dll | | | Win32 Dynamic Link Library (generic) (11) |
| .exe | | | Win32 Executable (generic) (7.5) |
| .exe | | | Generic Win/DOS Executable (3.3) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x1d20 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 110592 |
| CodeSize: | 4096 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| TimeStamp: | 2011:01:31 18:44:13+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 31-Jan-2011 17:44:13 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 31-Jan-2011 17:44:13 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00000EAC | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.942 |
.rdata | 0x00002000 | 0x00000488 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.73353 |
.data | 0x00003000 | 0x00000560 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.01054 |
.gentee | 0x00004000 | 0x00010A04 | 0x00011000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.95777 |
.rsrc | 0x00015000 | 0x00007BBC | 0x00008000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.47158 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.07336 | 1907 | Latin 1 / Western European | English - United States | RT_MANIFEST |
1000 | 2.23119 | 54 | Latin 1 / Western European | English - United States | RT_DIALOG |
IDD_DLGPROG | 2.78207 | 600 | Latin 1 / Western European | English - United States | RT_DIALOG |
SETUP_TEMP | 7.96692 | 11662 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
SETUP_ICON | 2.01924 | 20 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
Imports
KERNEL32.dll |
MSVCRT.dll |
USER32.dll |
Total processes
68
Monitored processes
19
Malicious processes
10
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 368 | "C:\Users\admin\AppData\Local\Temp\is-IDV9J.tmp\KMSpico_setup.tmp" /SL5="$40162,2952592,69120,C:\Program Files\KMSPico 10.0.6\KMSpico_setup.exe" | C:\Users\admin\AppData\Local\Temp\is-IDV9J.tmp\KMSpico_setup.tmp | KMSpico_setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
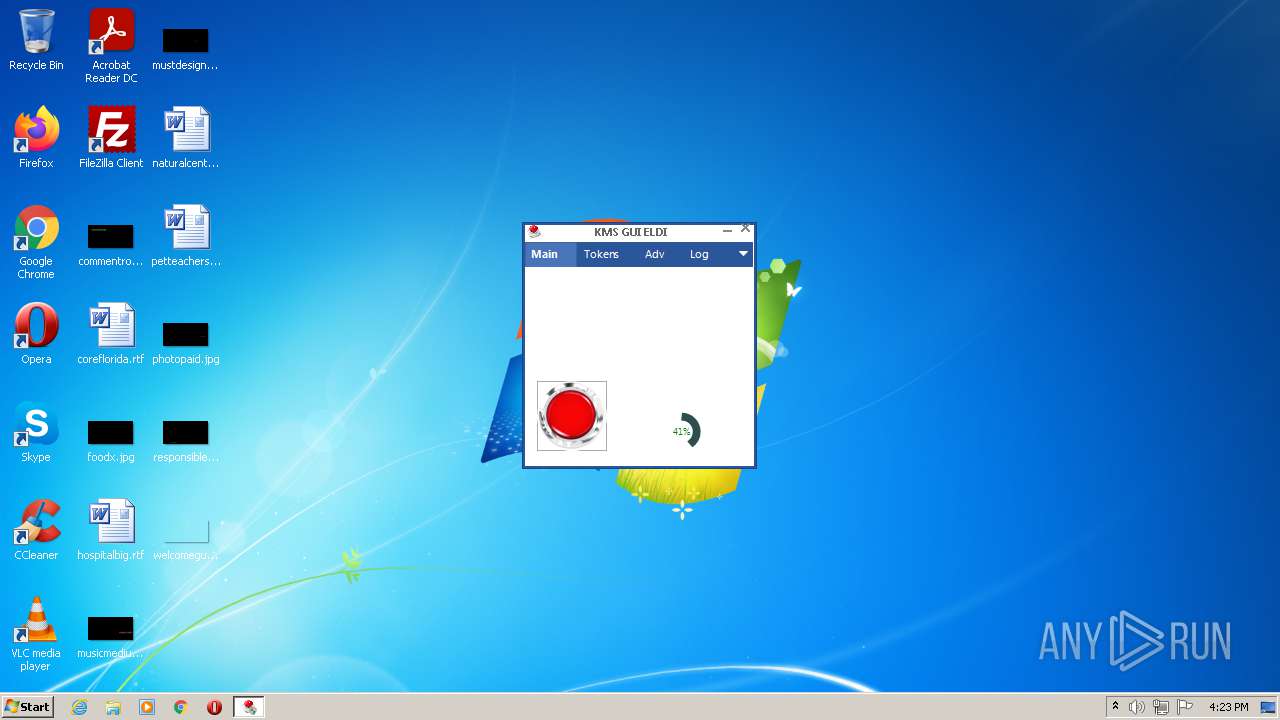
| 1024 | "C:\Program Files\KMSpico\KMSELDI.exe" /silent /backup | C:\Program Files\KMSpico\KMSELDI.exe | KMSpico_setup.tmp | ||||||||||||
User: admin Company: @ByELDI Integrity Level: HIGH Description: KMS GUI ELDI Exit code: 4294967295 Version: 37.1.0.0 Modules
| |||||||||||||||
| 1336 | "C:\Program Files\KMSpico\KMSELDI.exe" | C:\Program Files\KMSpico\KMSELDI.exe | — | Explorer.EXE | |||||||||||
User: admin Company: @ByELDI Integrity Level: MEDIUM Description: KMS GUI ELDI Exit code: 3221226540 Version: 37.1.0.0 Modules
| |||||||||||||||
| 1988 | "C:\Users\admin\AppData\Local\Temp\KMSPico 11.2.1.exe" | C:\Users\admin\AppData\Local\Temp\KMSPico 11.2.1.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2080 | "C:\Program Files\KMSPico 10.0.6\KMS.exe" /SYS 1 | C:\Program Files\KMSPico 10.0.6\KMS.exe | KMS.exe | ||||||||||||
User: SYSTEM Company: www.sordum.org Integrity Level: SYSTEM Description: dControl v1.9 Exit code: 0 Version: 1.9.0.0 Modules
| |||||||||||||||
| 2260 | SCHTASKS /Create /TN "AutoPico Daily Restart" /TR "'C:\Program Files\KMSpico\AutoPico.exe' /silent" /SC DAILY /ST 23:59:59 /RU "NT AUTHORITY\SYSTEM" /RL Highest /F | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2700 | "C:\Windows\system32\cmd.exe" /c "C:\Users\admin\AppData\Local\Temp\693A.tmp\693B.tmp\693C.bat "C:\Program Files\KMSPico 10.0.6\kmsservice.exe"" | C:\Windows\system32\cmd.exe | kmsservice.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2936 | "KMSpico_setup.exe" | C:\Program Files\KMSPico 10.0.6\KMSpico_setup.exe | cmd.exe | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: KMSpico Setup Exit code: 0 Version: 10.2.0 Modules
| |||||||||||||||
| 3044 | "C:\Program Files\KMSpico\KMSELDI.exe" | C:\Program Files\KMSpico\KMSELDI.exe | Explorer.EXE | ||||||||||||
User: admin Company: @ByELDI Integrity Level: HIGH Description: KMS GUI ELDI Exit code: 3221225547 Version: 37.1.0.0 Modules
| |||||||||||||||
| 3132 | "kmsservice.exe" | C:\Program Files\KMSPico 10.0.6\kmsservice.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
4 336
Read events
4 229
Write events
100
Delete events
7
Modification events
| (PID) Process: | (3512) KMSPico 11.2.1.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\tmp |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3944) KMS.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender |
| Operation: | write | Name: | DisableAntiSpyware |
Value: 1 | |||
| (PID) Process: | (3944) KMS.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\WinDefend |
| Operation: | write | Name: | Start |
Value: 3 | |||
| (PID) Process: | (2080) KMS.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows Defender |
| Operation: | write | Name: | DisableAntiSpyware |
Value: 1 | |||
| (PID) Process: | (2080) KMS.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Defender |
| Operation: | write | Name: | DisableAntiSpyware |
Value: 1 | |||
| (PID) Process: | (2080) KMS.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Defender\Real-Time Protection |
| Operation: | write | Name: | DisableRealtimeMonitoring |
Value: 1 | |||
| (PID) Process: | (2080) KMS.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\WinDefend |
| Operation: | write | Name: | Start |
Value: 3 | |||
| (PID) Process: | (3132) kmsservice.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3132) kmsservice.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3132) kmsservice.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
Executable files
32
Suspicious files
6
Text files
723
Unknown types
34
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3512 | KMSPico 11.2.1.exe | C:\Program Files\KMSPico 10.0.6\kmsservice.exe | executable | |
MD5:— | SHA256:— | |||
| 3512 | KMSPico 11.2.1.exe | C:\Program Files\KMSPico 10.0.6\RUN.bat | text | |
MD5:— | SHA256:— | |||
| 3512 | KMSPico 11.2.1.exe | C:\Users\admin\AppData\Local\Temp\gentee29\setup_temp.gea | bs | |
MD5:— | SHA256:— | |||
| 3512 | KMSPico 11.2.1.exe | C:\Program Files\KMSPico 10.0.6\hostservice.exe | executable | |
MD5:— | SHA256:— | |||
| 3512 | KMSPico 11.2.1.exe | C:\Users\admin\AppData\Local\Temp\gentee29\3default - 1.bmp | image | |
MD5:14A455E9EEF9FE7FEA4DE14D579A3E84 | SHA256:B666E6BD71EFF3547FB2F5580AC61C64527F6F9BE6A2178FA00F80E32431460A | |||
| 3944 | KMS.exe | C:\Users\admin\AppData\Local\Temp\xdmvipe | text | |
MD5:07232B64BE72593980CD952E8F85017E | SHA256:EF342BCC3C938C2FA9B38BC84019D8DCE94D018372F7D9C29A8EE7FF3F0FC3A8 | |||
| 3512 | KMSPico 11.2.1.exe | C:\Program Files\KMSPico 10.0.6\KMS.exe | executable | |
MD5:0A50081A6CD37AEA0945C91DE91C5D97 | SHA256:6606D759667FBDFAA46241DB7FFB4839D2C47B88A20120446F41E916CAD77D0B | |||
| 3944 | KMS.exe | C:\Users\admin\AppData\Local\Temp\aut67B3.tmp | binary | |
MD5:8D480A0FD29840481C0C9DEB3953A57A | SHA256:DACE58FA3CC9E42ADB073AFEAE10712529A4EF7E4AF6E2053439F1007ED76AE8 | |||
| 3944 | KMS.exe | C:\Windows\System32\GroupPolicy\gpt.ini | text | |
MD5:18BD917DCFE60A77F3BDA05E1A35B407 | SHA256:657581D7C48DDB8643C3396C49A00C7177ACD7B4922CEC22D6F45F30A606DB7A | |||
| 3944 | KMS.exe | C:\Windows\System32\GroupPolicy\Machine\Registry.pol | binary | |
MD5:D15A332CBA4FC6D5062F42728CF751B4 | SHA256:9C064D5E80AB78FF046430CB6A6CA1B32266AF43500313CC13AD092534EE4A6F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
3
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
2.pool.ntp.org |
| whitelisted |
1.pool.ntp.org |
| whitelisted |
3.pool.ntp.org |
| whitelisted |