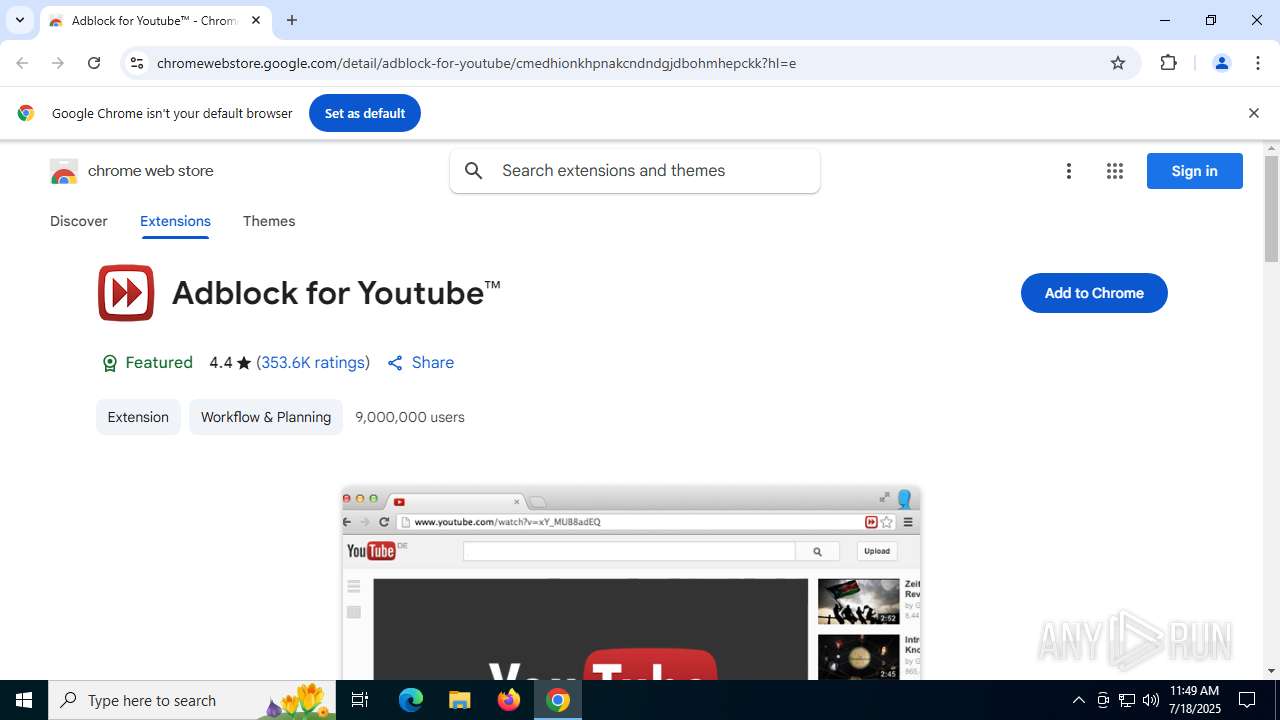
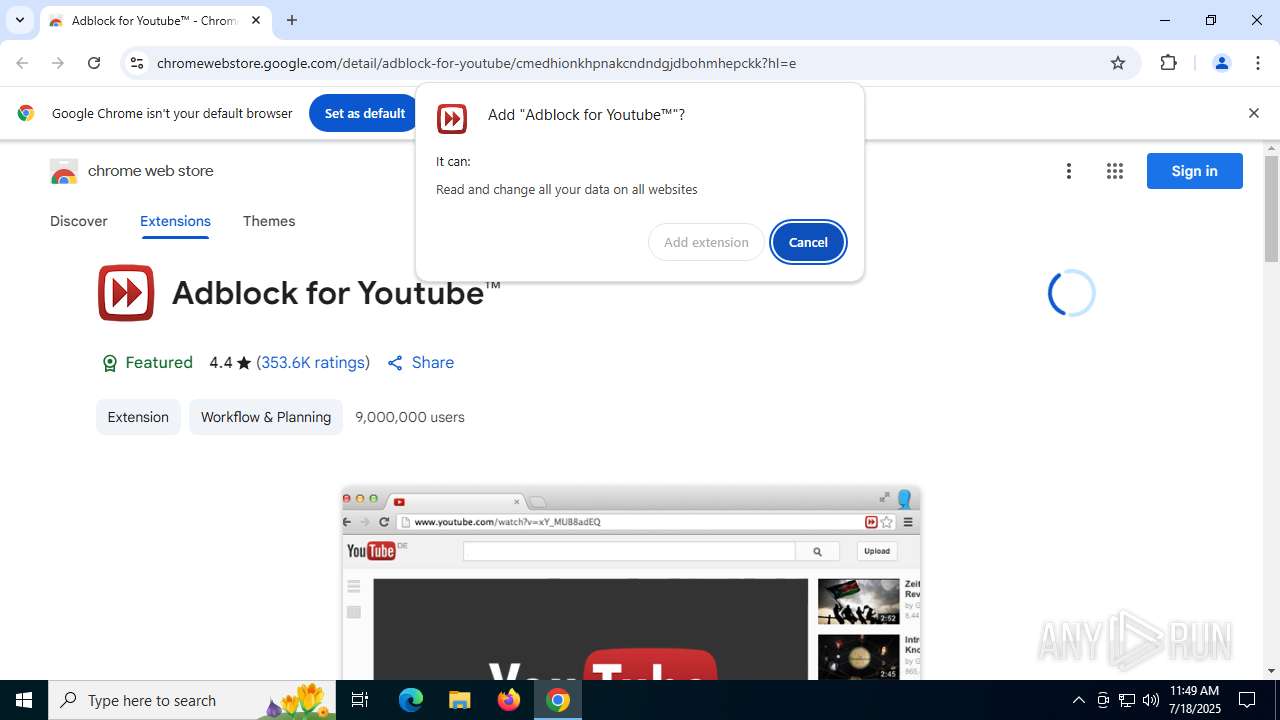
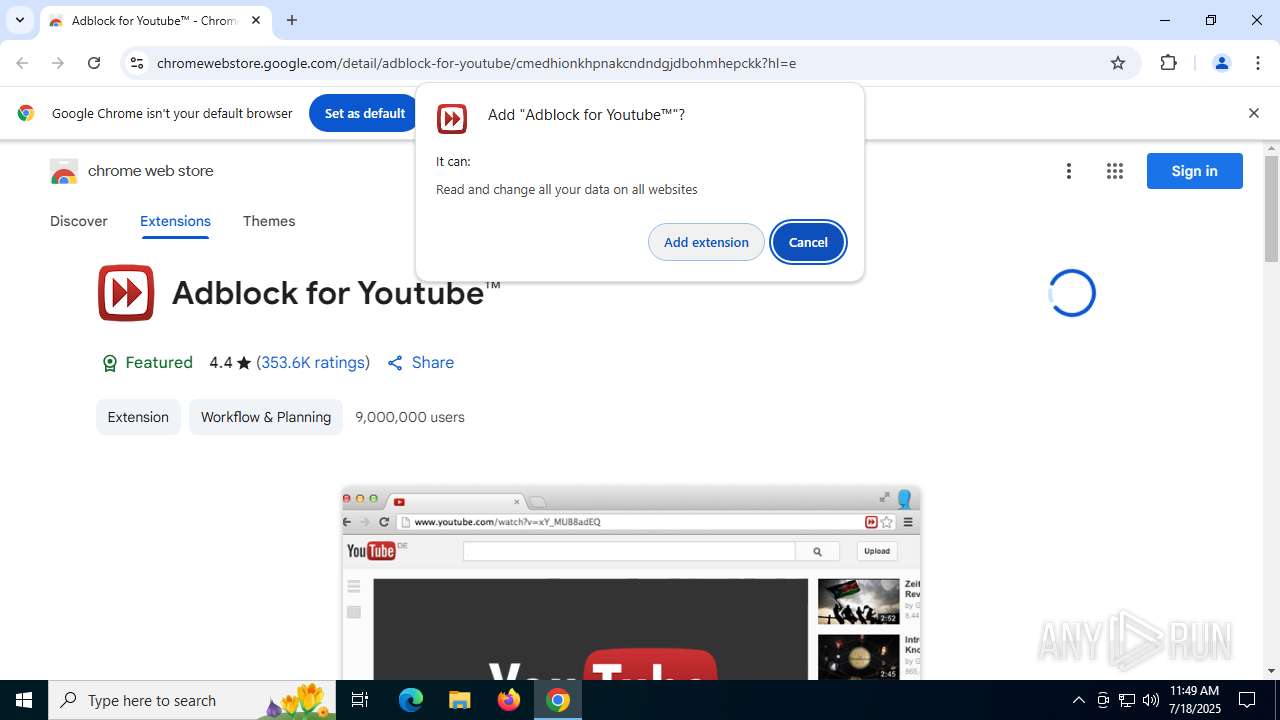
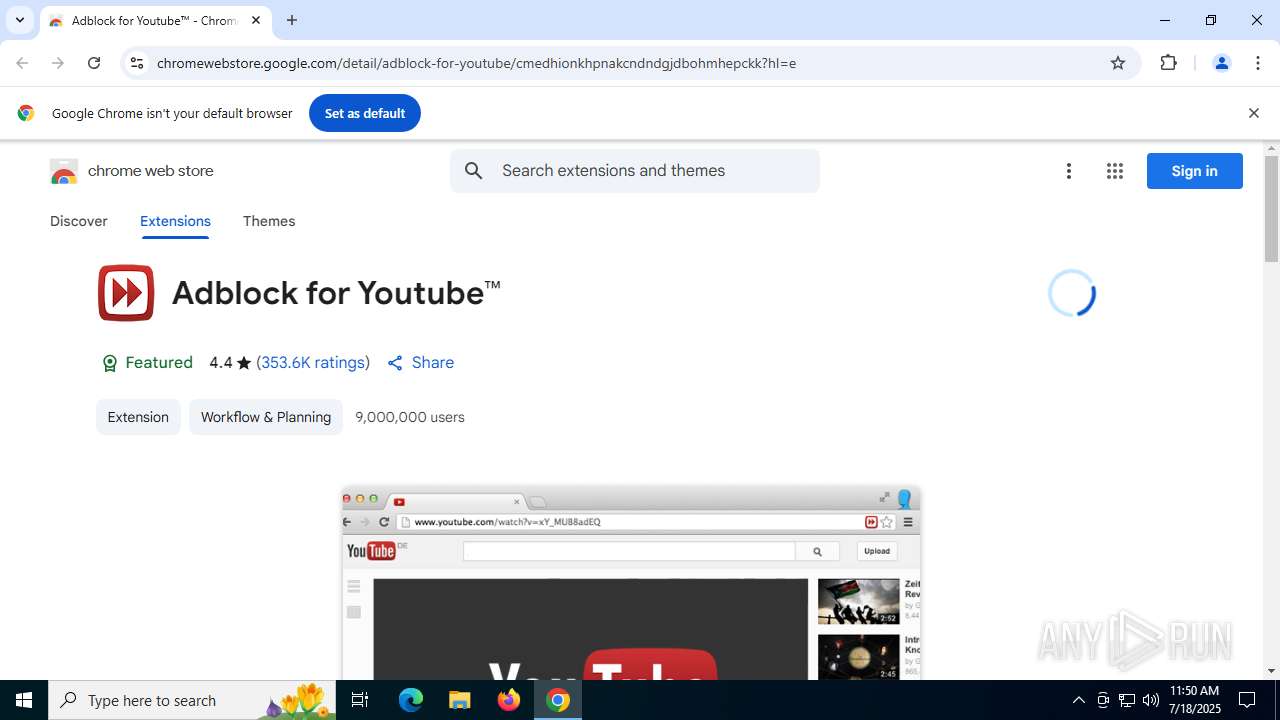
| URL: | https://chromewebstore.google.com/detail/adblock-para-youtube/cmedhionkhpnakcndndgjdbohmhepckk?hl=e |
| Full analysis: | https://app.any.run/tasks/b85fd00f-0275-44ba-bac7-33fd4eed0f95 |
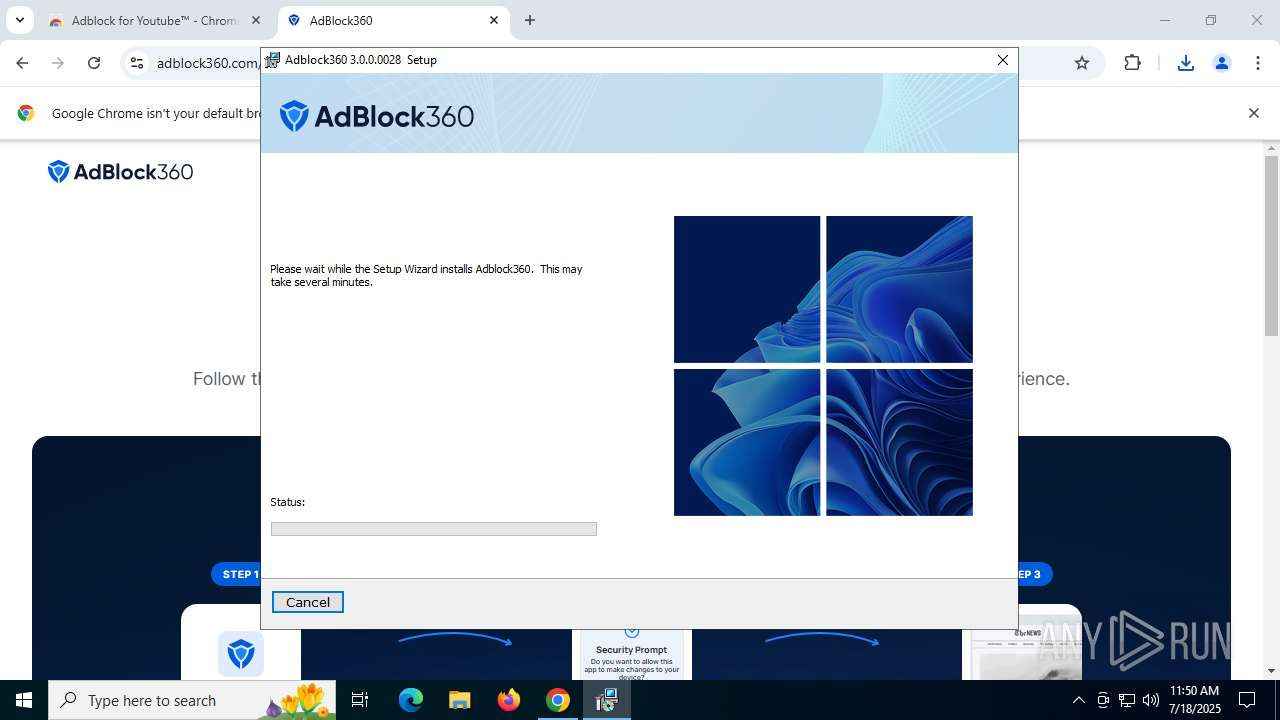
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2025, 11:49:41 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 2D99C8DCDD956459D2C9E4C40E0AAD62 |
| SHA1: | 8B7E80B30AB162A697E66CBF95A4A05EACF03420 |
| SHA256: | ADC5CB3C8EB3E32A71B56A4F62AE7672A6427B08FEDEFFA622E475DA5F82B3DA |
| SSDEEP: | 3:N8Qa9znAunARTngUcEmImV7c92cvOHAn:2Qa9znRARTngGPi7tceAn |
MALICIOUS
Changes powershell execution policy (Bypass)
- msiexec.exe (PID: 7000)
- msiexec.exe (PID: 7140)
Bypass execution policy to execute commands
- powershell.exe (PID: 8076)
- powershell.exe (PID: 5968)
- powershell.exe (PID: 7220)
- powershell.exe (PID: 7432)
- powershell.exe (PID: 6776)
- powershell.exe (PID: 2588)
Changes the autorun value in the registry
- powershell.exe (PID: 6776)
- powershell.exe (PID: 2588)
Uses Task Scheduler to run other applications
- Adblock360.exe (PID: 2432)
SUSPICIOUS
Starts POWERSHELL.EXE for commands execution
- msiexec.exe (PID: 7000)
- msiexec.exe (PID: 7140)
The process executes Powershell scripts
- msiexec.exe (PID: 7000)
- msiexec.exe (PID: 7140)
The process hide an interactive prompt from the user
- msiexec.exe (PID: 7000)
- msiexec.exe (PID: 7140)
The process bypasses the loading of PowerShell profile settings
- msiexec.exe (PID: 7000)
- msiexec.exe (PID: 7140)
Executes as Windows Service
- VSSVC.exe (PID: 1096)
Detects AdvancedInstaller (YARA)
- msiexec.exe (PID: 1712)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 1568)
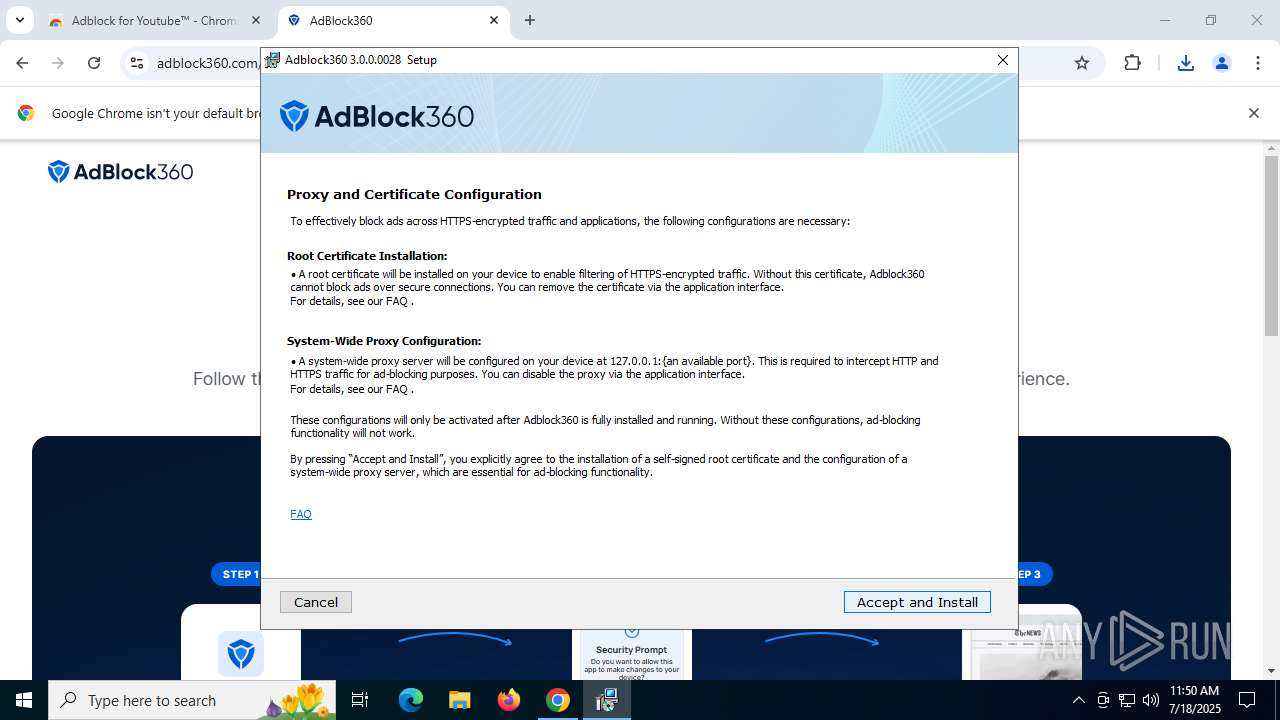
Adds/modifies Windows certificates
- Adblock360.exe (PID: 2432)
INFO
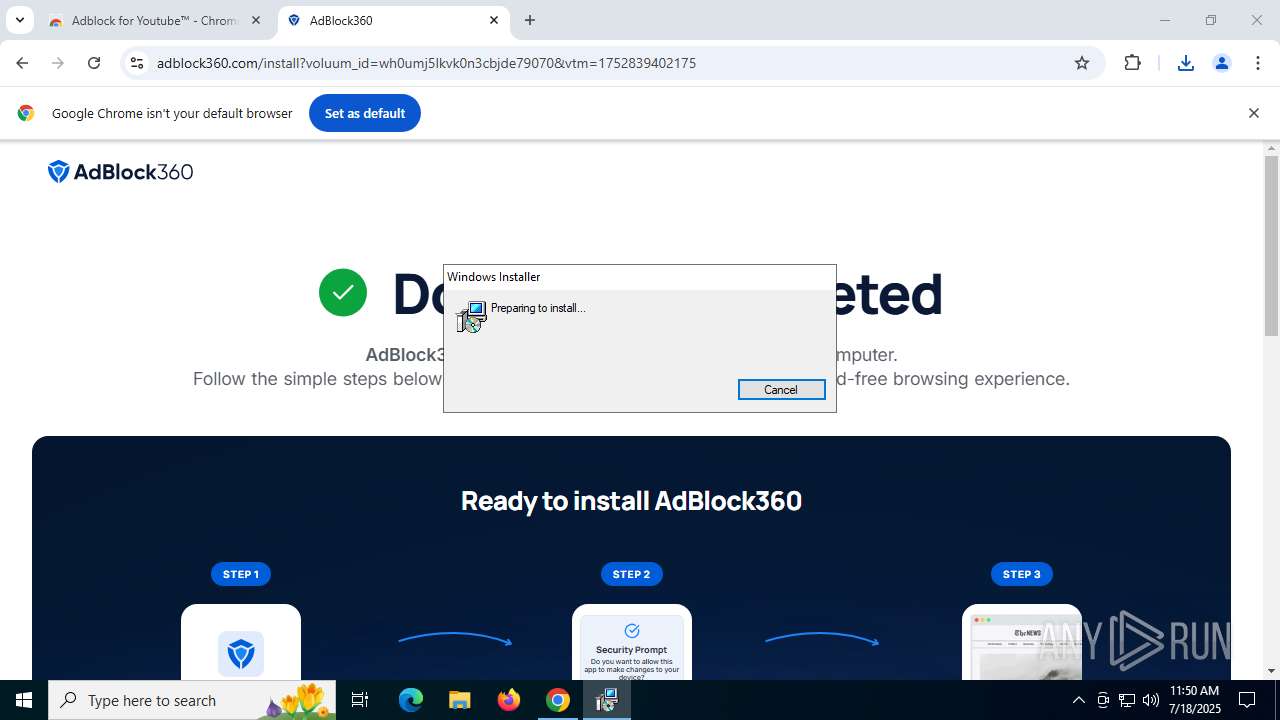
Create files in a temporary directory
- msiexec.exe (PID: 1712)
- AdBlock360Setup.exe (PID: 1148)
- msiexec.exe (PID: 7000)
- powershell.exe (PID: 7220)
- powershell.exe (PID: 8076)
- powershell.exe (PID: 5968)
- msiexec.exe (PID: 7140)
- powershell.exe (PID: 7432)
- powershell.exe (PID: 6776)
- powershell.exe (PID: 2588)
Checks proxy server information
- msiexec.exe (PID: 1712)
Reads the software policy settings
- AdBlock360Setup.exe (PID: 1148)
- msiexec.exe (PID: 1712)
- powershell.exe (PID: 8076)
- powershell.exe (PID: 7220)
- powershell.exe (PID: 5968)
- msiexec.exe (PID: 1568)
- powershell.exe (PID: 7432)
- powershell.exe (PID: 6776)
- powershell.exe (PID: 2588)
- Adblock360.exe (PID: 2432)
Application launched itself
- chrome.exe (PID: 6948)
Reads the computer name
- AdBlock360Setup.exe (PID: 1148)
- msiexec.exe (PID: 1568)
- msiexec.exe (PID: 7140)
- msiexec.exe (PID: 7000)
- Adblock360.exe (PID: 2432)
The sample compiled with english language support
- chrome.exe (PID: 6948)
- msiexec.exe (PID: 1712)
- msiexec.exe (PID: 1568)
Drops encrypted JS script (Microsoft Script Encoder)
- AdBlock360Setup.exe (PID: 1148)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 1712)
- powershell.exe (PID: 8076)
- powershell.exe (PID: 7220)
- powershell.exe (PID: 5968)
- powershell.exe (PID: 7432)
- powershell.exe (PID: 6776)
- powershell.exe (PID: 2588)
Executable content was dropped or overwritten
- chrome.exe (PID: 6948)
- msiexec.exe (PID: 1712)
- msiexec.exe (PID: 1568)
Reads the machine GUID from the registry
- AdBlock360Setup.exe (PID: 1148)
- msiexec.exe (PID: 1568)
- Adblock360.exe (PID: 2432)
Checks supported languages
- AdBlock360Setup.exe (PID: 1148)
- msiexec.exe (PID: 7140)
- msiexec.exe (PID: 7000)
- msiexec.exe (PID: 1568)
- Adblock360.exe (PID: 2432)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 7220)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 7220)
- powershell.exe (PID: 8076)
- powershell.exe (PID: 5968)
- powershell.exe (PID: 7432)
- powershell.exe (PID: 2588)
- powershell.exe (PID: 6776)
Detects GO elliptic curve encryption (YARA)
- AdBlock360Setup.exe (PID: 1148)
Application based on Golang
- AdBlock360Setup.exe (PID: 1148)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7220)
- powershell.exe (PID: 7432)
Manages system restore points
- SrTasks.exe (PID: 4444)
Creates files or folders in the user directory
- msiexec.exe (PID: 1712)
- msiexec.exe (PID: 1568)
- Adblock360.exe (PID: 2432)
Reads Environment values
- msiexec.exe (PID: 7000)
- msiexec.exe (PID: 7140)
Launching a file from a Registry key
- powershell.exe (PID: 6776)
- powershell.exe (PID: 2588)
Manual execution by a user
- Adblock360.exe (PID: 2432)
Creates a software uninstall entry
- msiexec.exe (PID: 1568)
Launching a file from Task Scheduler
- Adblock360.exe (PID: 2432)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
199
Monitored processes
52
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 892 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1096 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1128 | schtasks.exe /Create /TN Adblock360UpdatesDownloader /SC DAILY /ST 11:00 /F /TR "conhost.exe --headless 'C:\Users\admin\AppData\Local\Adblock360\updates\download-and-update.cmd'" | C:\Windows\SysWOW64\schtasks.exe | — | Adblock360.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1136 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
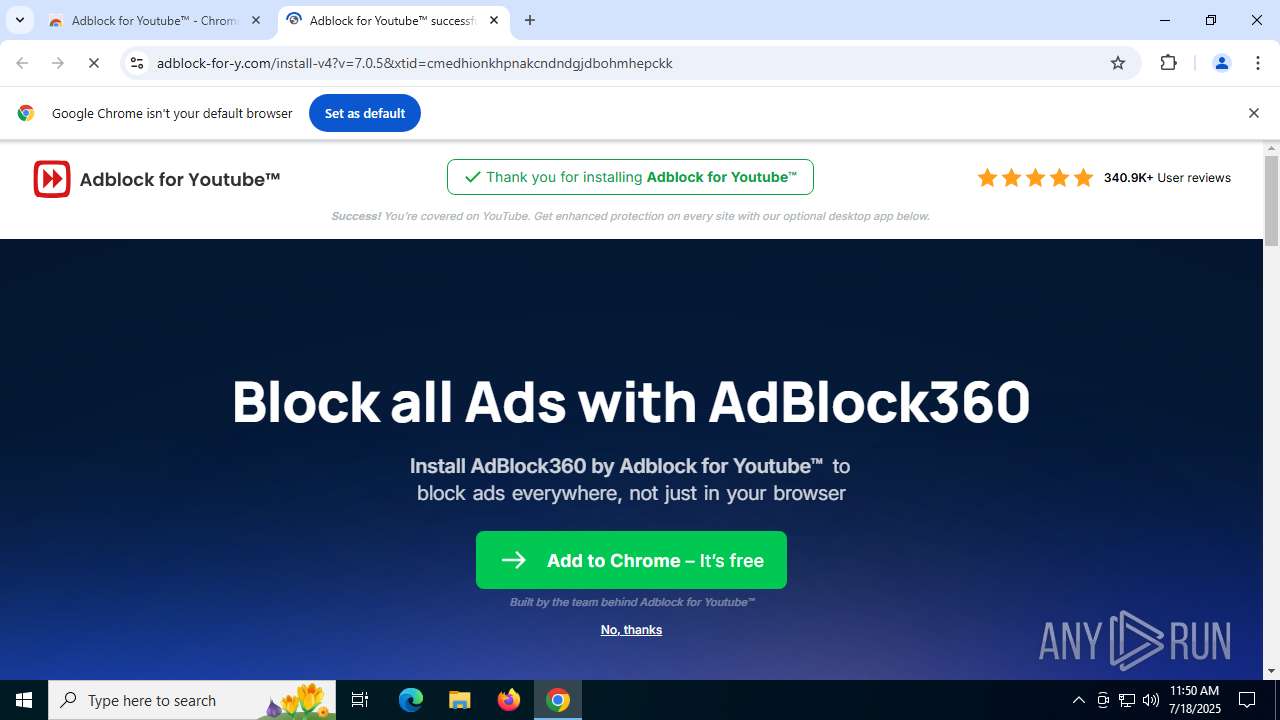
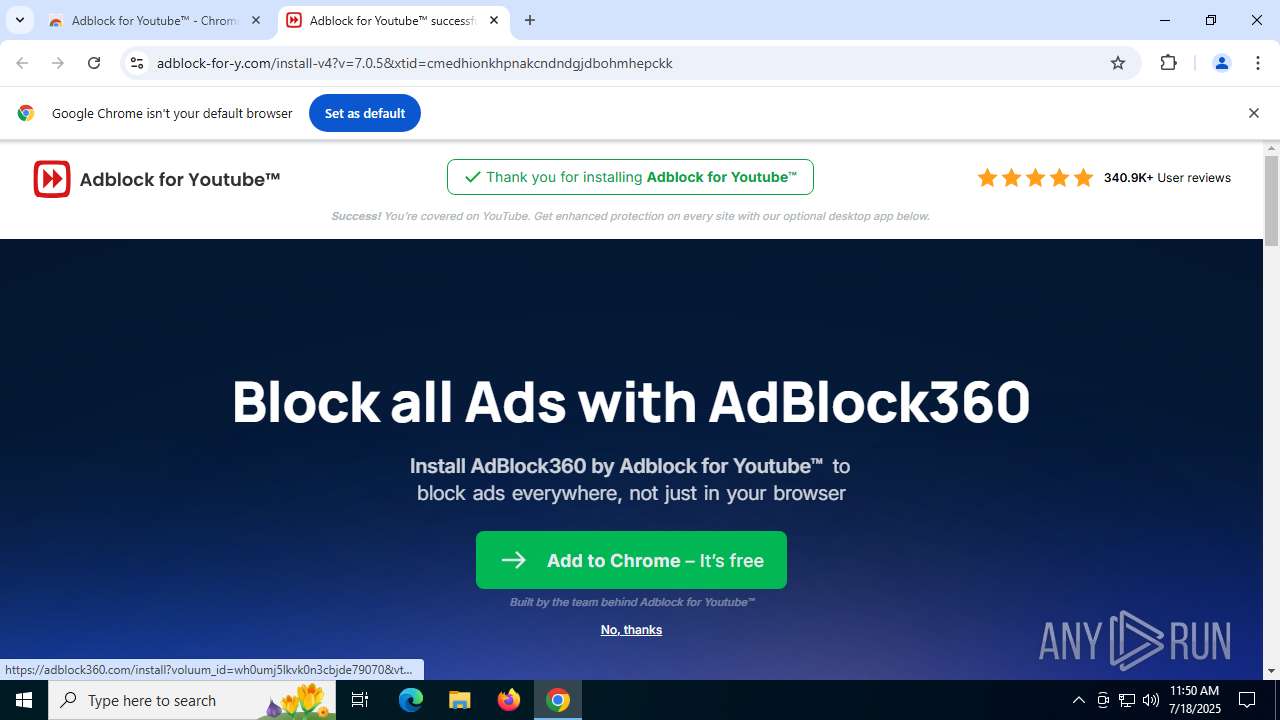
| 1148 | "C:\Users\admin\Downloads\AdBlock360Setup.exe" | C:\Users\admin\Downloads\AdBlock360Setup.exe | chrome.exe | ||||||||||||
User: admin Company: ADBLOCK LIMITED Integrity Level: HIGH Description: AdBlock360Setup Downloader and Installer Exit code: 0 Version: 1.1.0.0 Modules
| |||||||||||||||
| 1568 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1636 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=2008,i,9836729209045147160,10869439535383799289,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=2156 /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1712 | msiexec.exe /i C:\Users\admin\AppData\Local\Temp\Adblock360-Setup_3.0.0.0028.msi /L*V C:\Users\admin\AppData\Local\Temp/Adblock360-installer.log | C:\Windows\SysWOW64\msiexec.exe | AdBlock360Setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2432 | "C:\Users\admin\AppData\Roaming\ADBLOCK LIMITED\Adblock360\Adblock360.exe" --install --thankyou | C:\Users\admin\AppData\Roaming\ADBLOCK LIMITED\Adblock360\Adblock360.exe | explorer.exe | ||||||||||||
User: admin Company: ADBLOCK LIMITED Integrity Level: MEDIUM Description: AdBlock360 Version: 3.0.0 Modules
| |||||||||||||||
| 2588 | -NoProfile -Noninteractive -ExecutionPolicy Bypass -File "C:\Users\admin\AppData\Local\Temp\pss2968.ps1" -propFile "C:\Users\admin\AppData\Local\Temp\msi2956.txt" -scriptFile "C:\Users\admin\AppData\Local\Temp\scr2957.ps1" -scriptArgsFile "C:\Users\admin\AppData\Local\Temp\scr2958.txt" -propSep " :<->: " -lineSep " <<:>> " -testPrefix "_testValue." | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
76 000
Read events
75 649
Write events
322
Delete events
29
Modification events
| (PID) Process: | (6948) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6948) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6948) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6948) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6948) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6948) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\PreferenceMACs\Default\extensions.settings |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6948) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\PreferenceMACs\Default\extensions.settings |
| Operation: | write | Name: | ahfgeienlihckogmohjhadlkjgocpleb |
Value: 3B08F722C14555E595AF269F140EE426CE8DEBAD90D03EE9FF33B95CB34233F6 | |||
| (PID) Process: | (6948) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\PreferenceMACs\Default\extensions.settings |
| Operation: | write | Name: | bjbddleefiddlmdfdfbgodgacjjldihj |
Value: 5CFE6AD362B9AABBD07085580BC6C063CF1C79A0B22ECB6BCBA21EECA68BA07F | |||
| (PID) Process: | (6948) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\PreferenceMACs\Default\extensions.settings |
| Operation: | write | Name: | cmedhionkhpnakcndndgjdbohmhepckk |
Value: 0DFF74CD0770341C00AD16129E4C4D3EED8FCF954D1E86159DD4A12ECC4BB2C6 | |||
| (PID) Process: | (6948) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\PreferenceMACs\Default\extensions.settings |
| Operation: | write | Name: | mhjfbmdgcfjbbpaeojofohoefgiehjai |
Value: F6EE482B70E472BD0FE04C8E130D7E2A0D87334BDC8F199AD874C100863BC5BE | |||
Executable files
43
Suspicious files
220
Text files
106
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RF18cdea.TMP | — | |
MD5:— | SHA256:— | |||
| 6948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF18cdf9.TMP | — | |
MD5:— | SHA256:— | |||
| 6948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF18cdf9.TMP | — | |
MD5:— | SHA256:— | |||
| 6948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF18ce09.TMP | — | |
MD5:— | SHA256:— | |||
| 6948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF18ce09.TMP | — | |
MD5:— | SHA256:— | |||
| 6948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6948 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF18ce09.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
119
DNS requests
131
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1636 | chrome.exe | GET | 200 | 142.250.186.78:80 | http://clients2.google.com/time/1/current?cup2key=8:WV9zyuxa9U0YZF2SSeqwZMS5M2grRepwvjS76KPiTWQ&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.53.40.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7668 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7668 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1712 | msiexec.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
1712 | msiexec.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
6936 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1712 | msiexec.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAEldo4y1XhTxXnw4hY%2Bw5A%3D | unknown | — | — | whitelisted |
3640 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjhkYWYwZDctOTExOS00MGQ5LTgyNjAtN2FlY2ZjMDg0NmNj/1.0.0.17_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
236 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1636 | chrome.exe | 142.250.186.78:80 | clients2.google.com | GOOGLE | US | whitelisted |
1636 | chrome.exe | 142.250.184.202:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
1636 | chrome.exe | 142.250.186.99:443 | fonts.gstatic.com | GOOGLE | US | whitelisted |
1636 | chrome.exe | 142.250.184.238:443 | chromewebstore.google.com | GOOGLE | US | whitelisted |
1636 | chrome.exe | 142.250.102.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
chromewebstore.google.com |
| whitelisted |
accounts.google.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
lh3.googleusercontent.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1636 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
1636 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
1636 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
1636 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
1636 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
1636 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
Process | Message |
|---|---|
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |