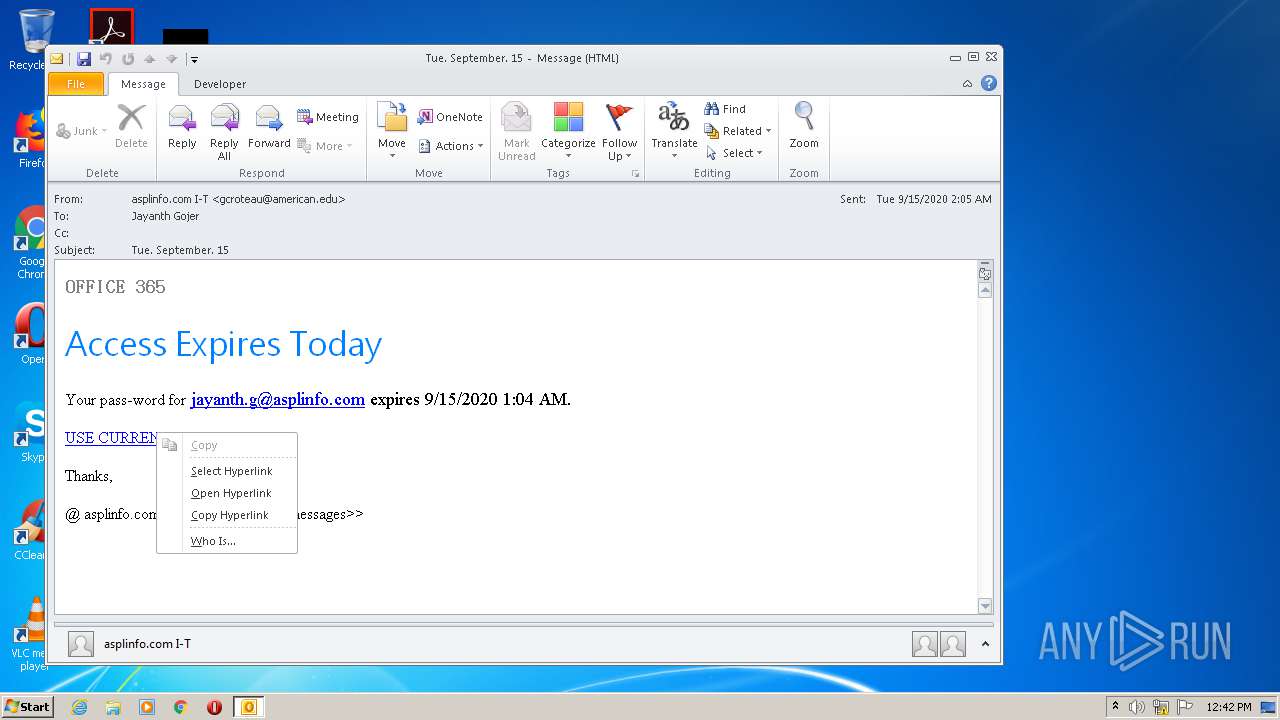
| File name: | Tue. September. 15.msg |
| Full analysis: | https://app.any.run/tasks/fae4c9cb-f73a-449f-bdd5-c246582910d9 |
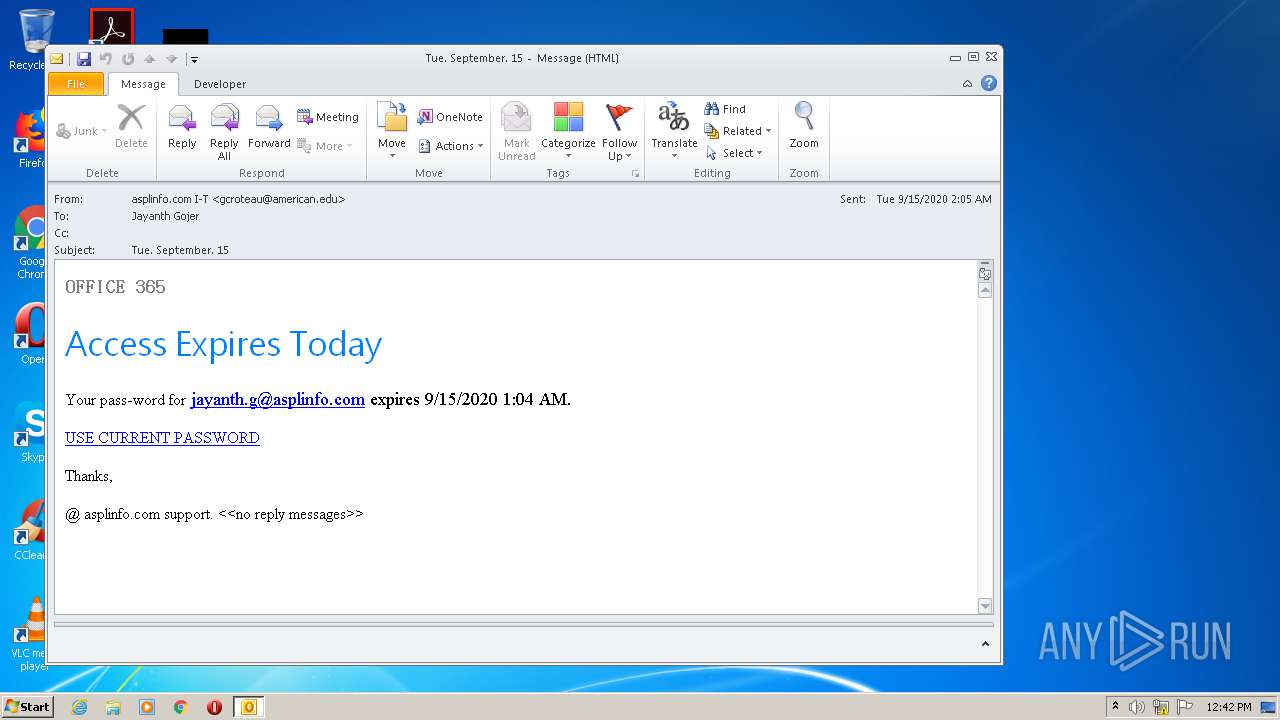
| Verdict: | Malicious activity |
| Analysis date: | October 20, 2020, 11:41:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 778F1FB4BB1CD530B891798B3742E2D8 |
| SHA1: | DA460604786B592618B2E47C36D28356937C9360 |
| SHA256: | ADBFDFCC6EF225D535545CDFDE7CEB43E09E88BD5558754392F663E7CBD9D809 |
| SSDEEP: | 1536:3iiZNrYWjolr7ndQzOnNWyWGvaKr/OPktt/cnH/oSpXzW:3iiZNrBmr7n6zOnFva8ONnH/omzW |
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 2064)
SUSPICIOUS
Starts Internet Explorer
- OUTLOOK.EXE (PID: 2064)
INFO
Creates files in the user directory
- OUTLOOK.EXE (PID: 2064)
- iexplore.exe (PID: 984)
- iexplore.exe (PID: 1480)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2064)
- iexplore.exe (PID: 1480)
- iexplore.exe (PID: 984)
Application launched itself
- iexplore.exe (PID: 1480)
Changes internet zones settings
- iexplore.exe (PID: 1480)
Reads settings of System Certificates
- iexplore.exe (PID: 984)
- iexplore.exe (PID: 1480)
Reads internet explorer settings
- iexplore.exe (PID: 984)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1480)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2064)
Changes settings of System certificates
- iexplore.exe (PID: 1480)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
41
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 984 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1480 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
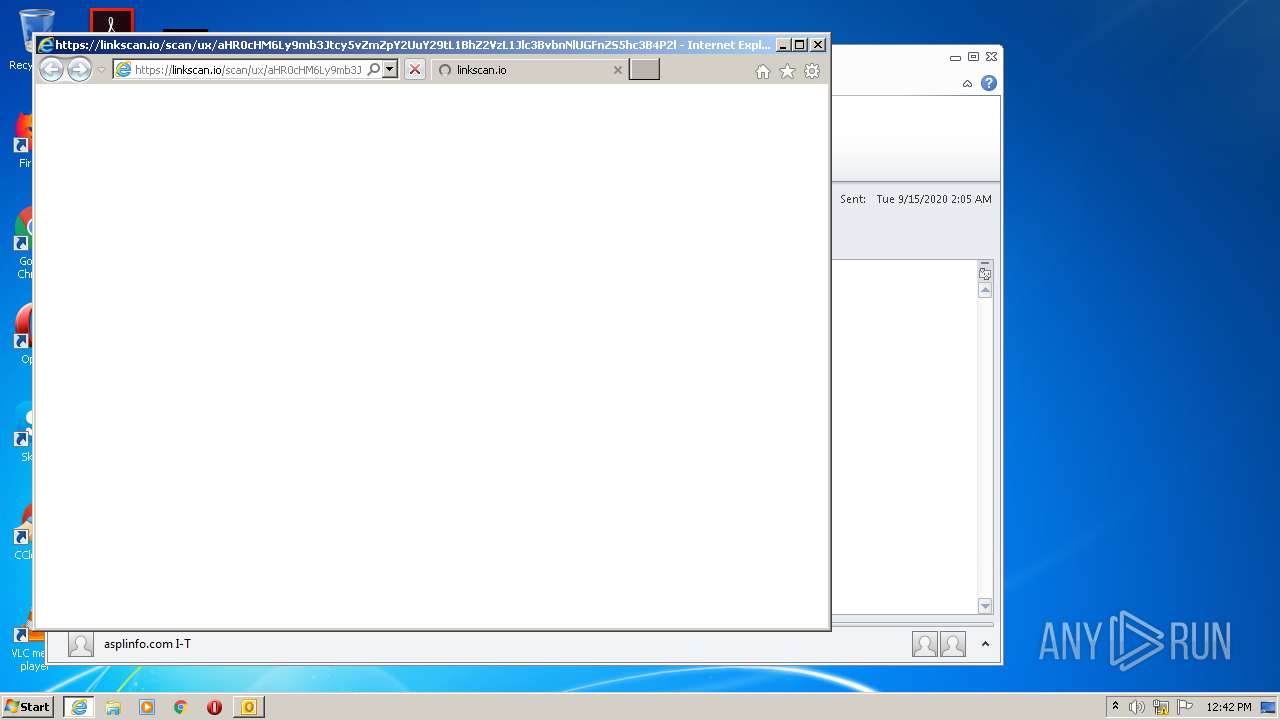
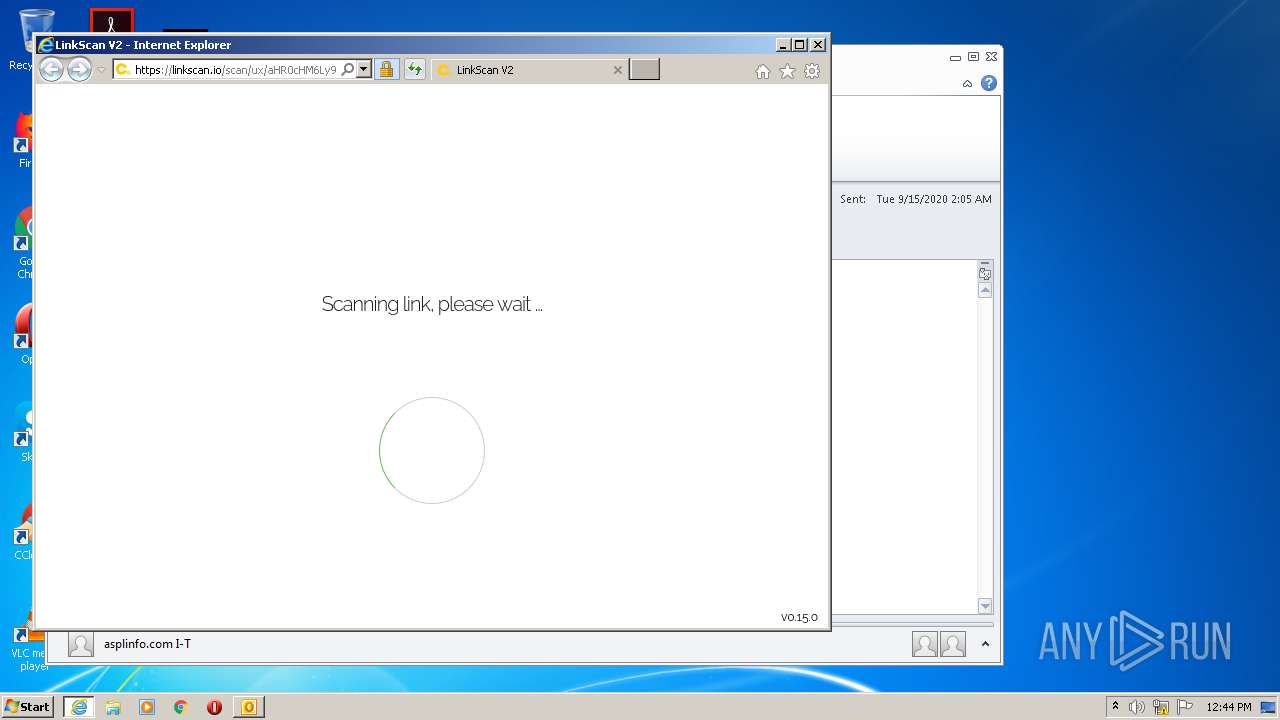
| 1480 | "C:\Program Files\Internet Explorer\iexplore.exe" https://linkscan.io/scan/ux/aHR0cHM6Ly9mb3Jtcy5vZmZpY2UuY29tL1BhZ2VzL1Jlc3BvbnNlUGFnZS5hc3B4P2lkPUlHZXU2VFFPX2tpb0pUakplWm1JdjFJc1hFWWplM0JGbk9GRU5nc2RTajlVUWtwR1RWQXlPRVF3VlRGRFRVWmFNazFWUWpaU1UwZEhWQzR1/C00A15FA87DFF85B7CF4AD0D6679E3A873B58D7D3E5FA748333FC354E2A8BA21?c=1&i=1&docs=1 | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2064 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Tue. September. 15.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
Total events
2 429
Read events
1 404
Write events
1 001
Delete events
24
Modification events
| (PID) Process: | (2064) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2064) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2064) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2064) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2064) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2064) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2064) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2064) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2064) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (2064) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
57
Text files
50
Unknown types
32
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2064 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR3EE2.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2064 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 984 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabEE1E.tmp | — | |
MD5:— | SHA256:— | |||
| 984 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarEE1F.tmp | — | |
MD5:— | SHA256:— | |||
| 2064 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 2064 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\StructuredQuery.log | text | |
MD5:— | SHA256:— | |||
| 984 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6A2279C2CA42EBEE26F14589F0736E50 | der | |
MD5:— | SHA256:— | |||
| 984 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6A2279C2CA42EBEE26F14589F0736E50 | binary | |
MD5:— | SHA256:— | |||
| 984 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\BAD725C80F9E10846F35D039A996E4A8_88B6AE015495C1ECC395D19C1DD02894 | der | |
MD5:— | SHA256:— | |||
| 984 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\75CA58072B9926F763A91F0CC2798706_93E4B2BA79A897B3100CCB27F2D3BF4F | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
44
DNS requests
22
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2064 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
984 | iexplore.exe | GET | 200 | 13.35.253.198:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
984 | iexplore.exe | GET | 200 | 172.217.22.67:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCOUTy4wn8XWggAAAAAWy8I | US | der | 472 b | whitelisted |
984 | iexplore.exe | GET | 200 | 13.35.253.78:80 | http://s.ss2.us/r.crl | US | der | 434 b | whitelisted |
984 | iexplore.exe | GET | 200 | 13.35.253.18:80 | http://s.ss2.us/r.crl | US | der | 434 b | whitelisted |
984 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
984 | iexplore.exe | GET | 200 | 172.217.22.67:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCECiWpPQxRDpPAgAAAAB8NWE%3D | US | der | 471 b | whitelisted |
984 | iexplore.exe | GET | 200 | 13.35.253.128:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
984 | iexplore.exe | GET | 200 | 13.35.253.198:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
984 | iexplore.exe | GET | 200 | 172.217.22.67:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCECiWpPQxRDpPAgAAAAB8NWE%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
984 | iexplore.exe | 172.217.16.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
984 | iexplore.exe | 23.111.9.35:443 | use.fontawesome.com | netDNA | US | suspicious |
984 | iexplore.exe | 13.35.253.7:80 | ocsp.sca1b.amazontrust.com | — | US | whitelisted |
984 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
984 | iexplore.exe | 142.250.74.195:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2064 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
984 | iexplore.exe | 99.86.2.2:443 | linkscan.io | AT&T Services, Inc. | US | unknown |
984 | iexplore.exe | 13.35.253.128:80 | o.ss2.us | — | US | suspicious |
1480 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
984 | iexplore.exe | 13.35.253.18:80 | s.ss2.us | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
linkscan.io |
| malicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
o.ss2.us |
| whitelisted |
s.ss2.us |
| whitelisted |
ocsp.rootg2.amazontrust.com |
| whitelisted |
ocsp.rootca1.amazontrust.com |
| shared |
ocsp.sca1b.amazontrust.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |