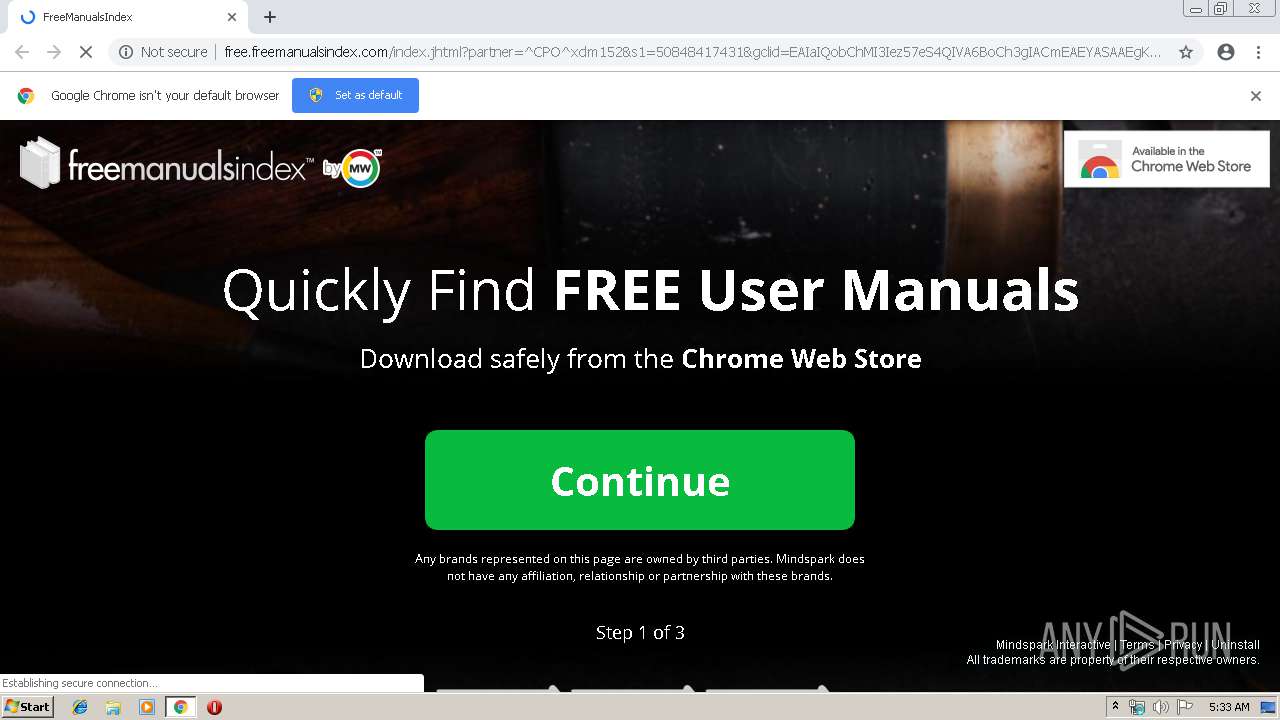
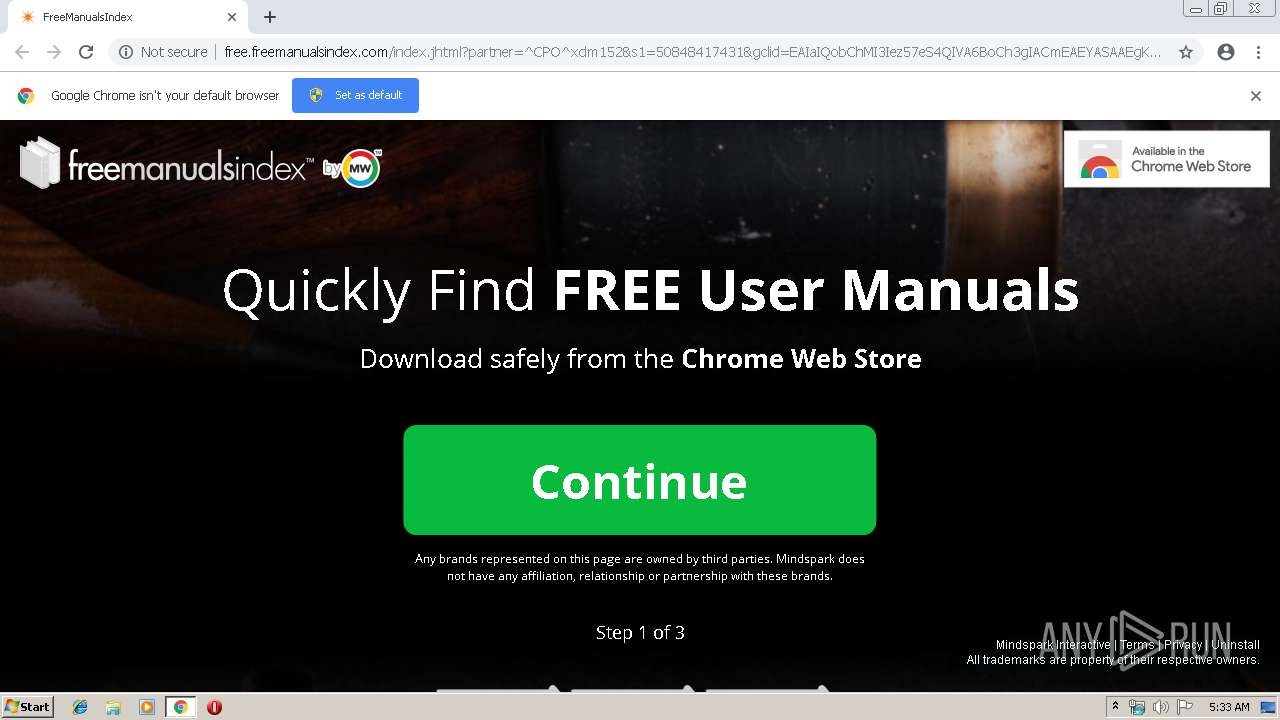
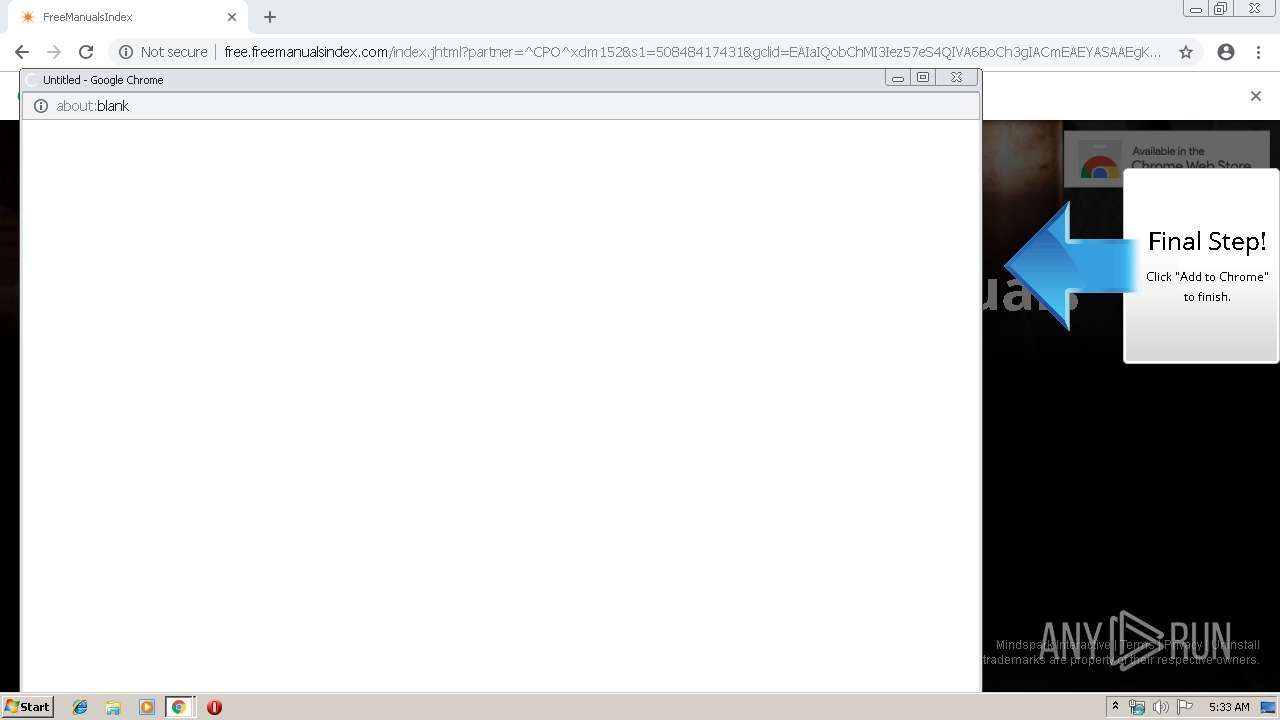
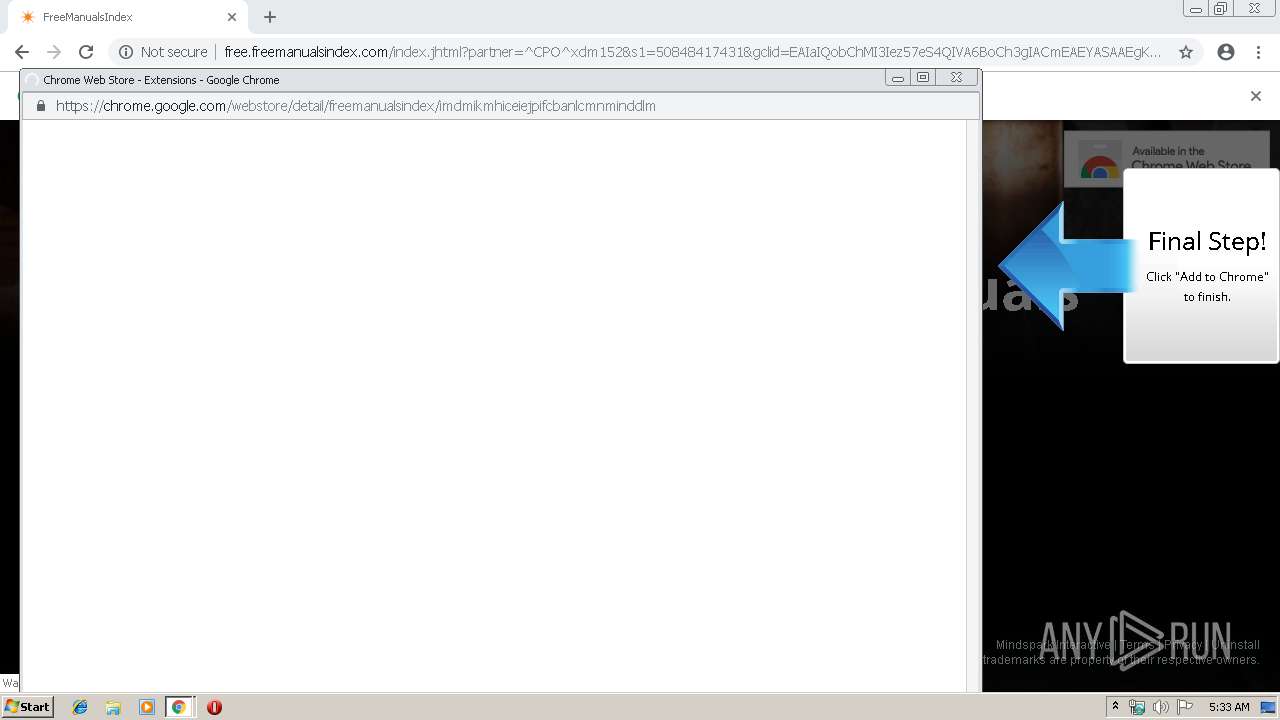
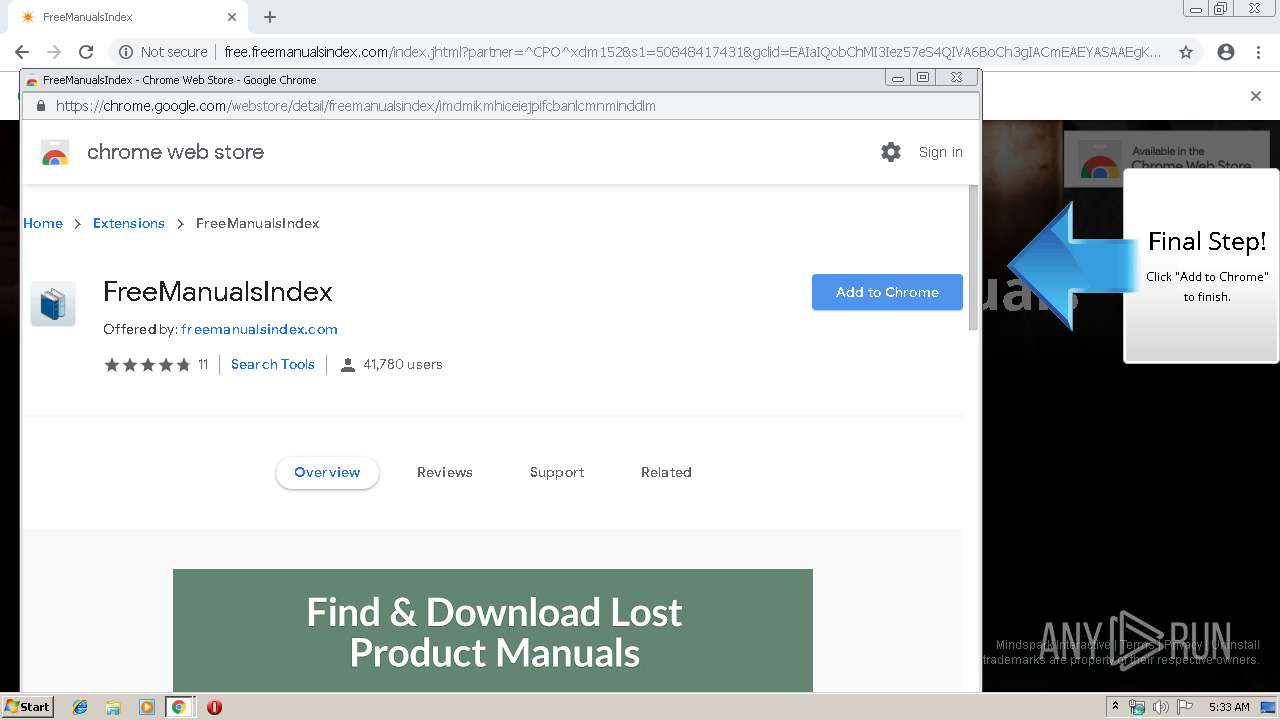
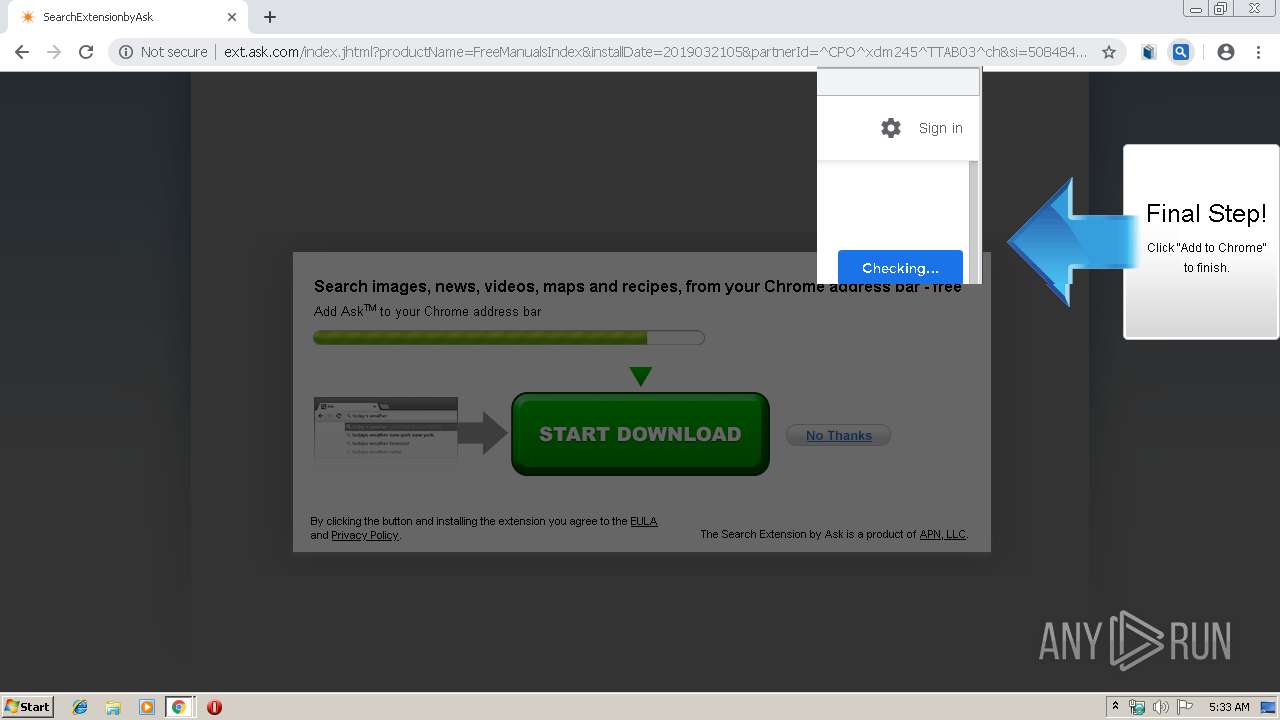
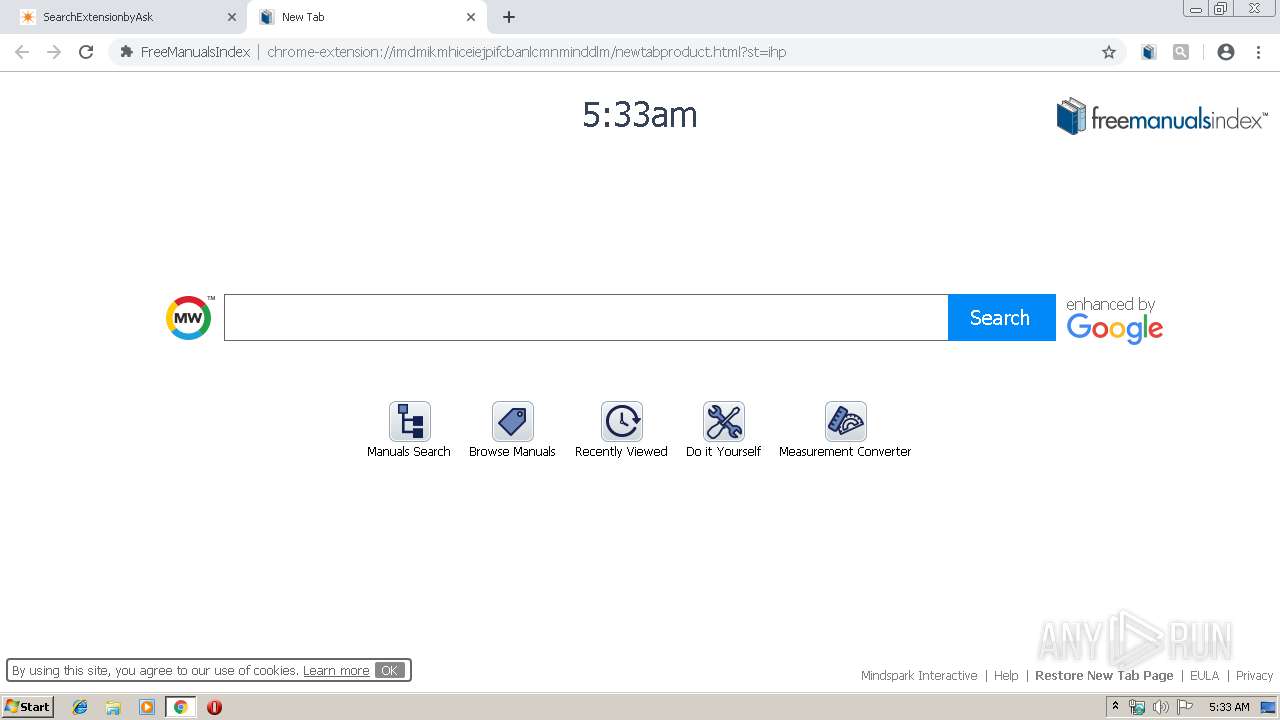
| URL: | https://www.googleadservices.com/pagead/aclk?sa=L&ai=CQHVTQhiTXNzeHoPAogPgwYCwCtzgpslTssXetMQGwI23ARABIPbDpyRgpaCVgJgBoAHv7YaeA8gBAuACAKgDAcgDmQSqBJQCT9BVLynl4ODojWqzYUhfwVG_MDxdacOXE4f1PyaINfotiqMeTaQBccR16UPOjFue9Nx7WV4M8oCaYXix0uJrzxmCwNP1ASuPsE7C_cK18udeA4XbfLbj8s7tIWPfyt7NqqkPmSqIfyXNAAQ_YJEoly6lxnccs3JlsJPWMewHk-8basH18MW-L0bLmBDVG2zlBWsNPoyOi03mLJR6zWxyrT989kEeIKJrF-1z-uAioIKai6sjOEoRqhPrraWVwO9uJ6gIDv_nK7_X2rZo_sFRe4A6OYNc55ouNYnNoUmwhvAQ76DlrlJnF3CVDbcXjRsAmdf-EB6JkS8ZsTeGUYwp6VIMfHusxC7iJ3pWkwPo31wnjdc64AQBoAYCgAf5kflhqAeOzhuoB9XJG6gH4NMbqAeoBqgH2csbqAfPzBuoB6a-G9gHAdIIBwiAYRABGAGxCUvP3FCTCDGZgAoD2BMM&num=1&cid=CAASEuRocoJgisB6tdXdIo8bgBOpCg&sig=AOD64_0vrV0G5r2F9TA2sj9JiGDMu3VhrA&client=ca-pub-3448704589648193&nm=5&nx=204&ny=32&mb=2&adurl=http://free.freemanualsindex.com/index.jhtml%3Fpartner%3D%5ECPO%5Exdm152%26s1%3D50848417431 |
| Full analysis: | https://app.any.run/tasks/6fd7ee7e-28af-4f96-9290-2b3779fca49c |
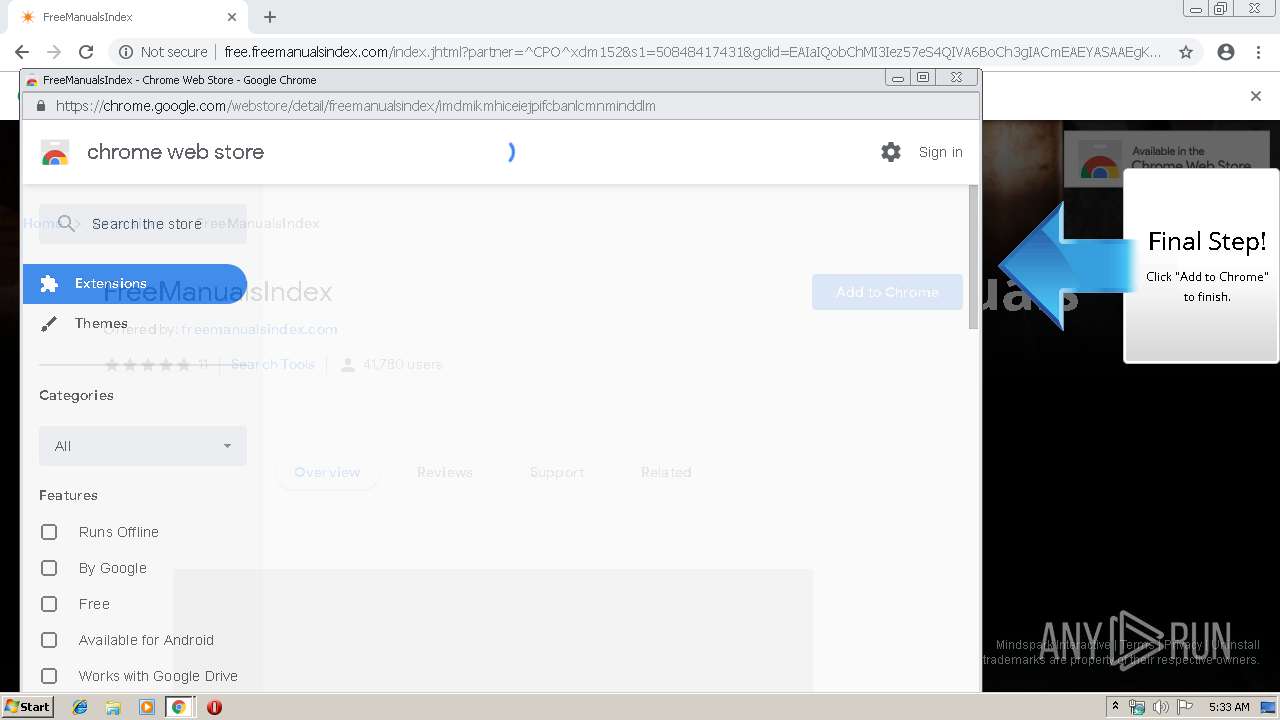
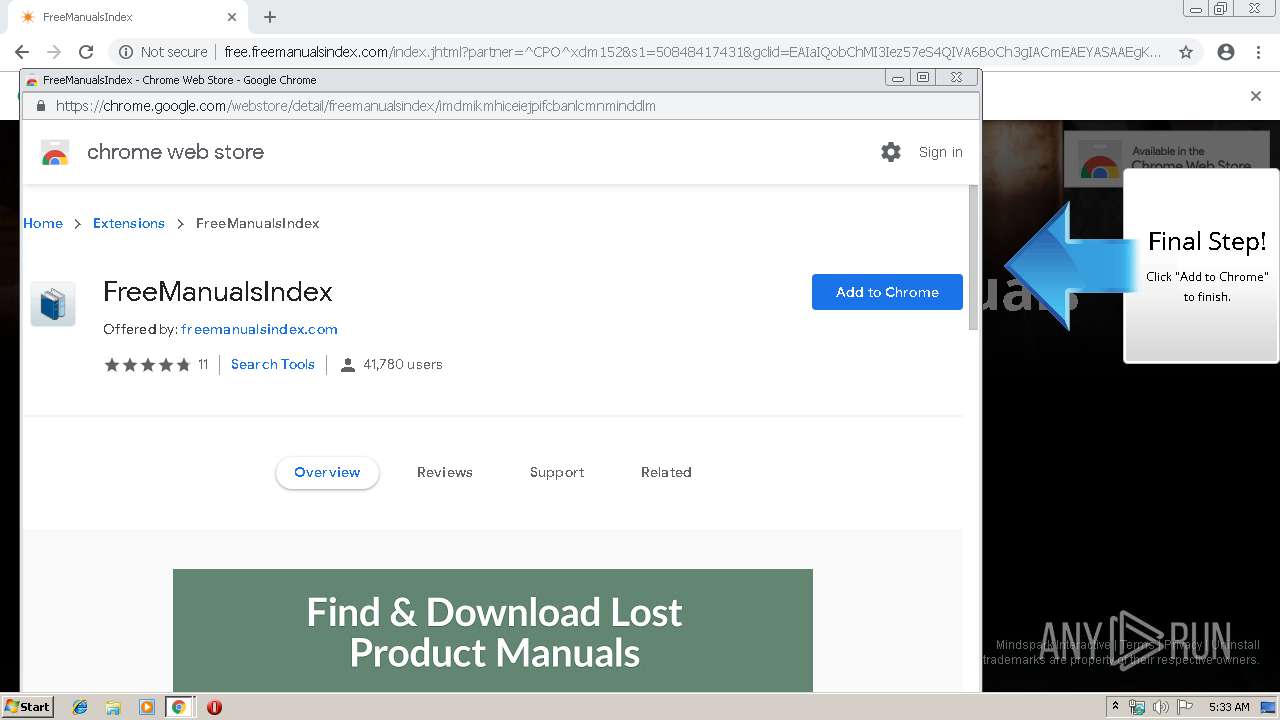
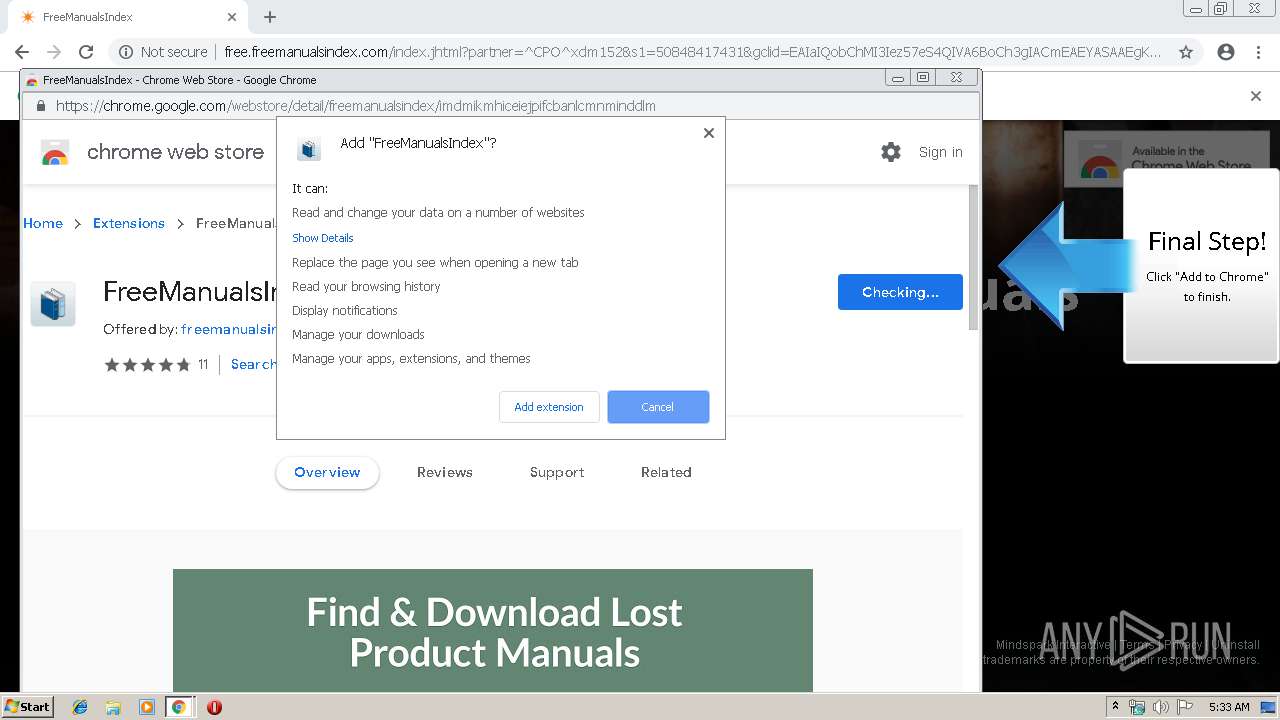
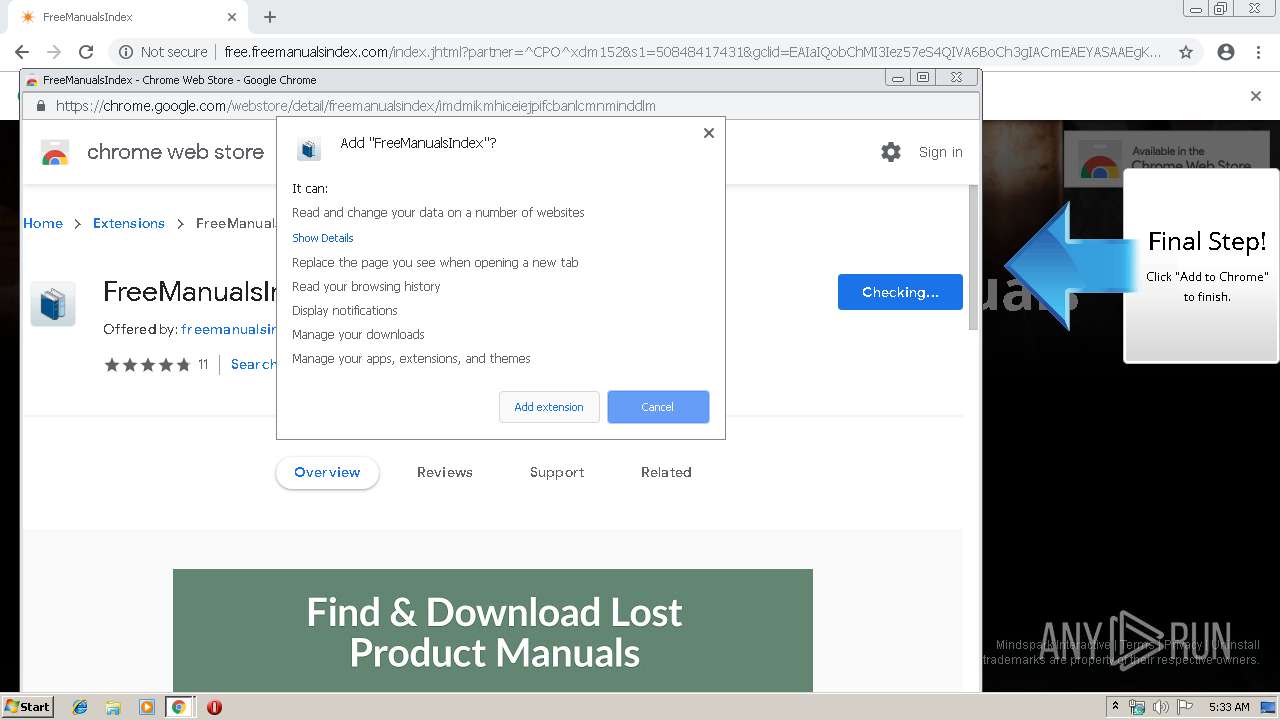
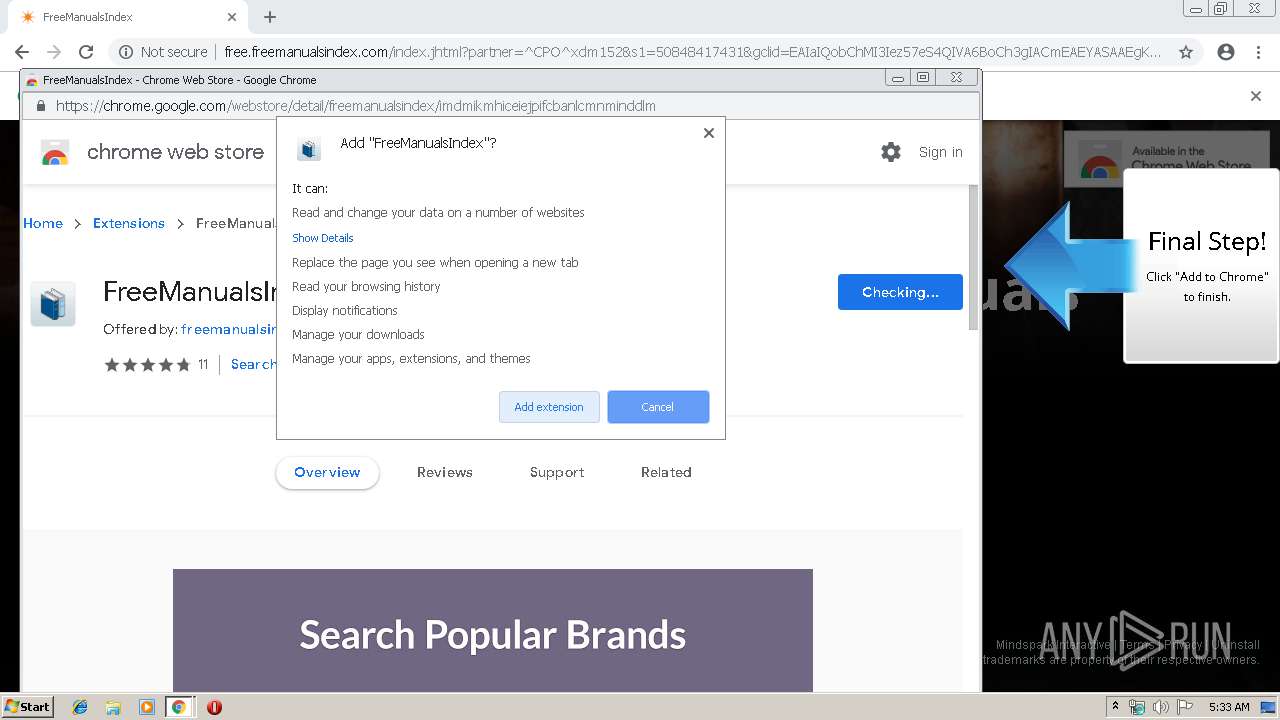
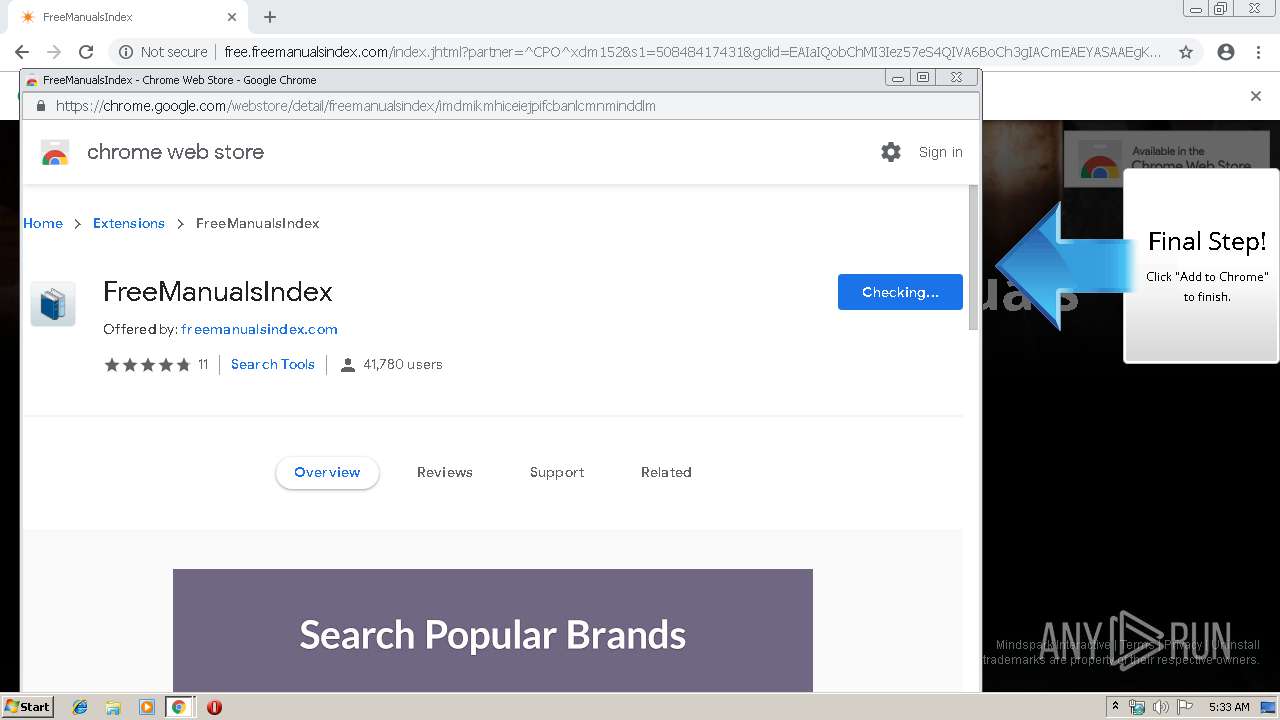
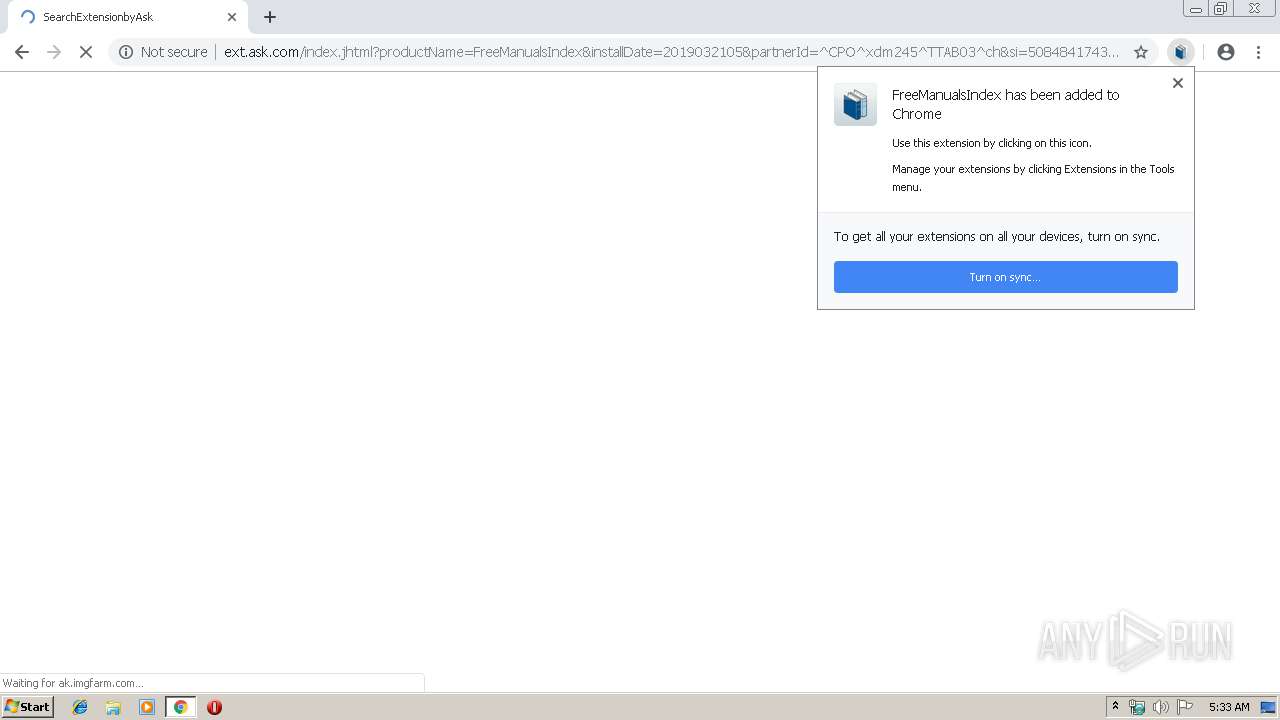
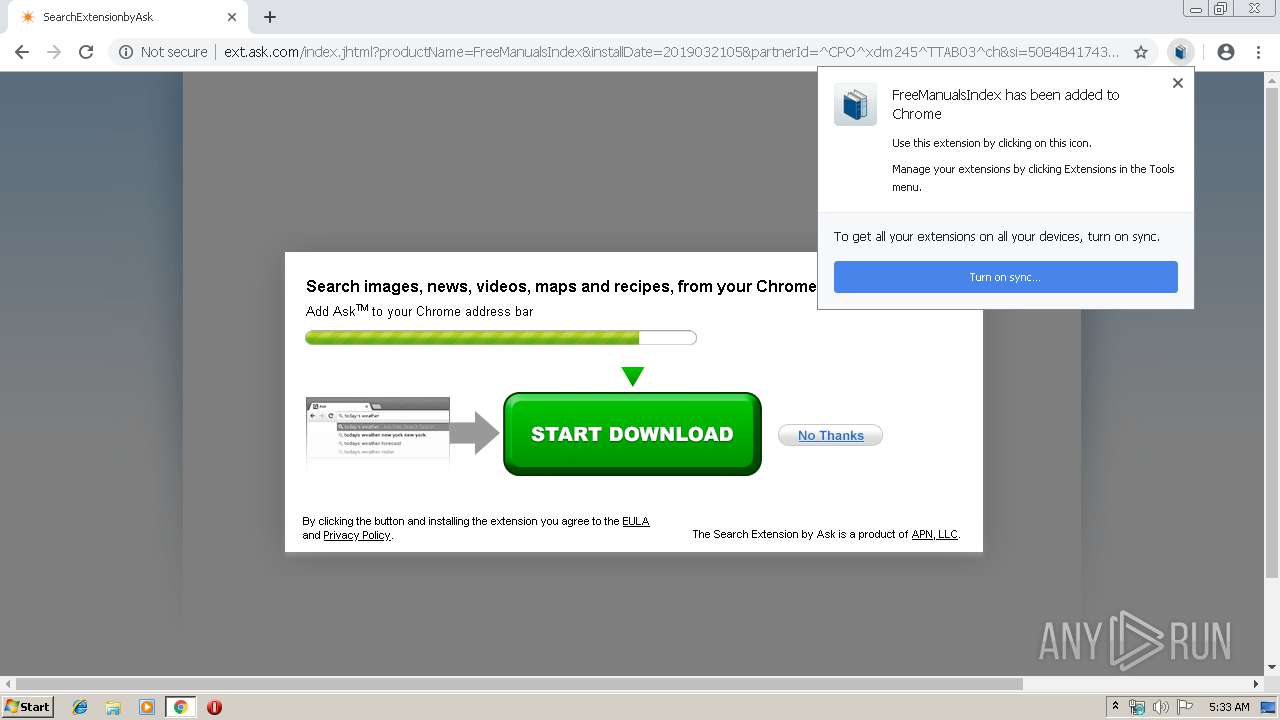
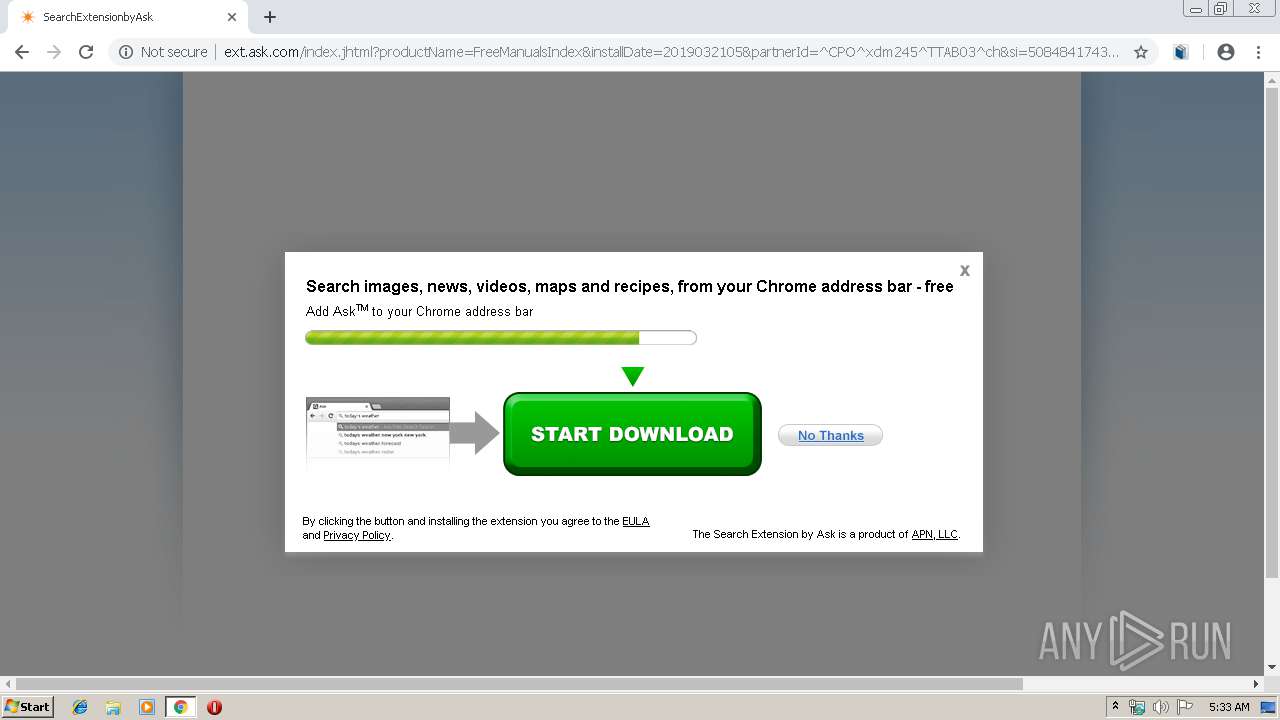
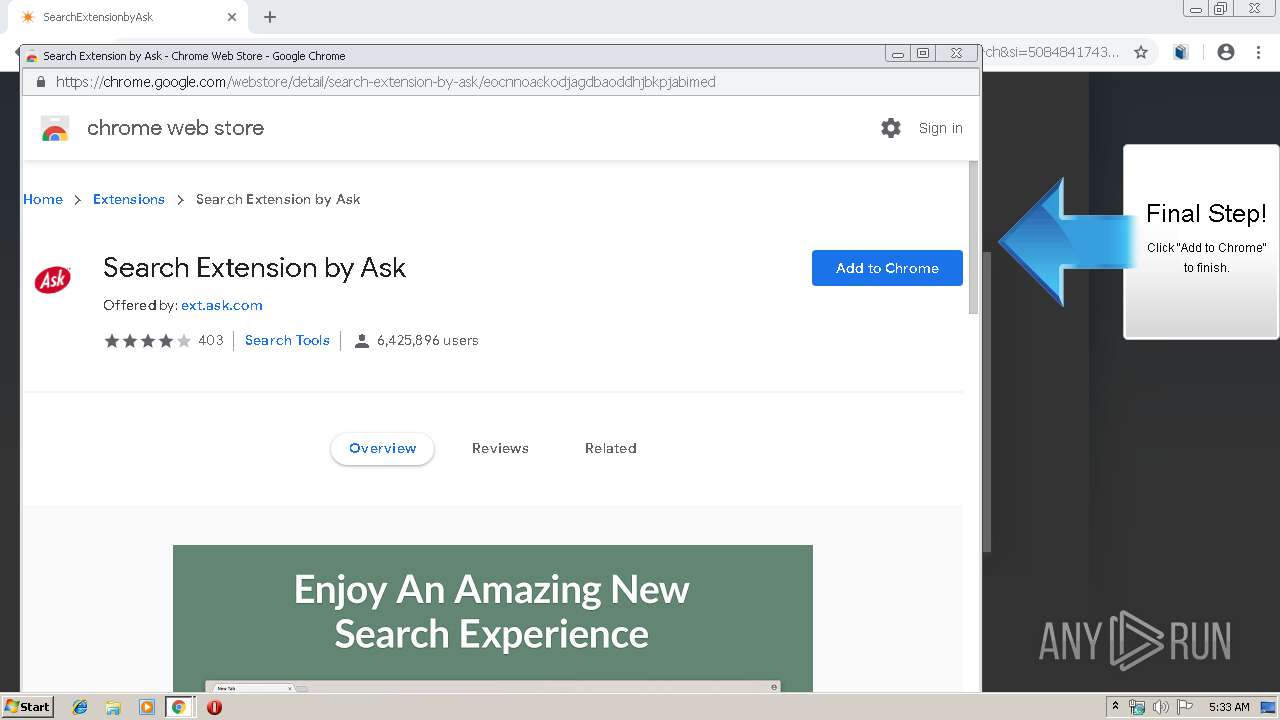
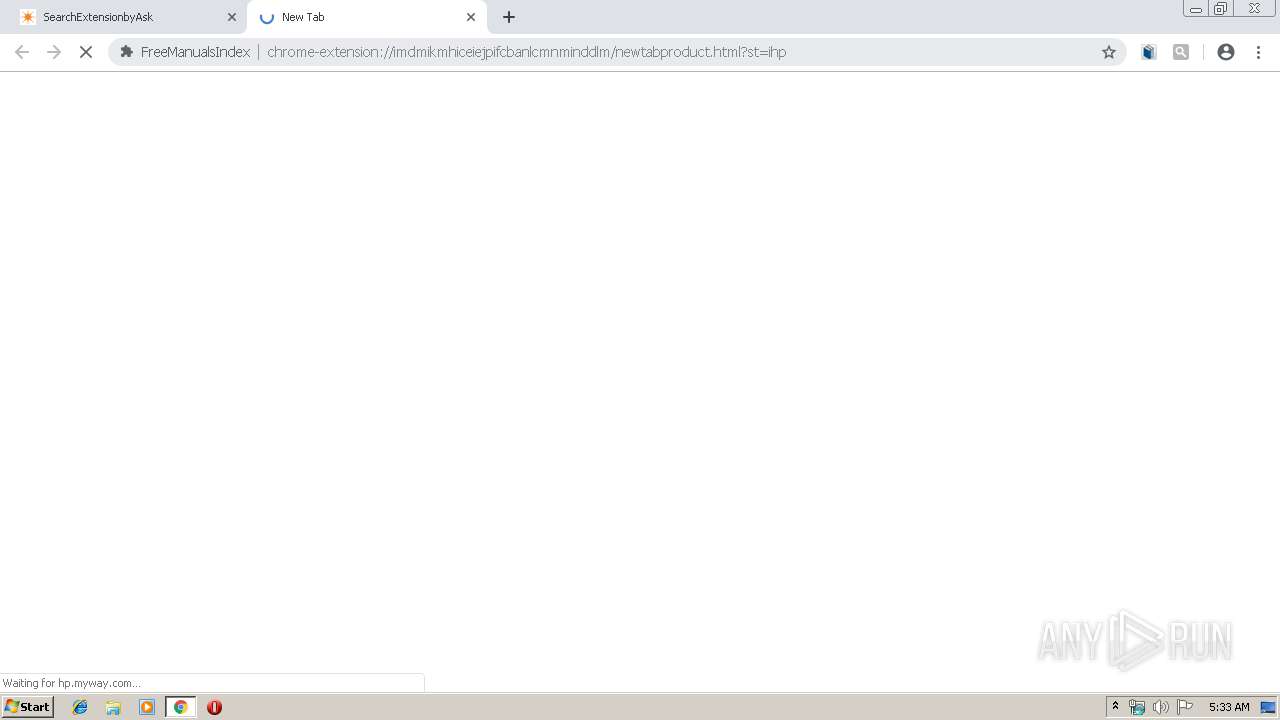
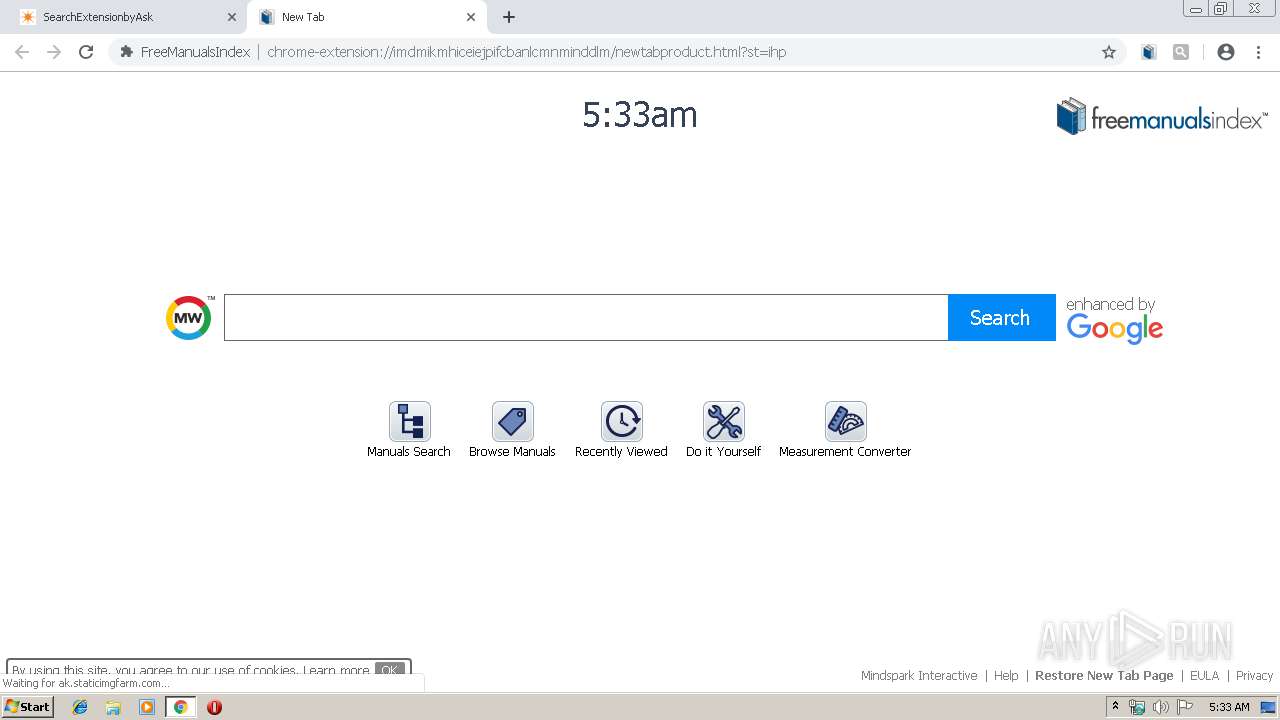
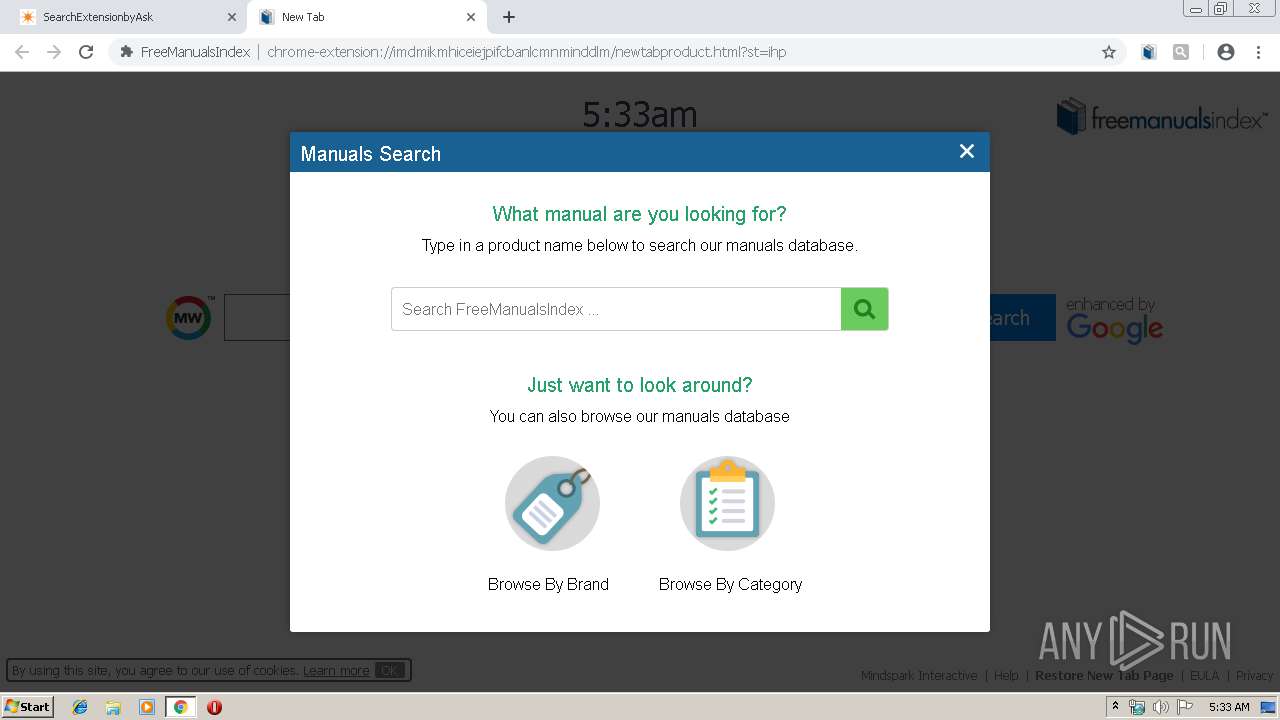
| Verdict: | Malicious activity |
| Analysis date: | March 21, 2019, 05:32:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | D72BB7837CD4F6013A1F4BCBC049F4A2 |
| SHA1: | 5C11458F38D3AA1390375C4060A0AABDDBAD07A7 |
| SHA256: | ADB1C1C6E4A4AC69B8C25A0F72E2843DEDB60A9CEFCA60378CE554FEDC3945D5 |
| SSDEEP: | 24:2DGx2Zd2DHVu6wjPyWDDK7nRFTSGEPrqPRshm:5xhRuLrFWlF+pOPRsc |
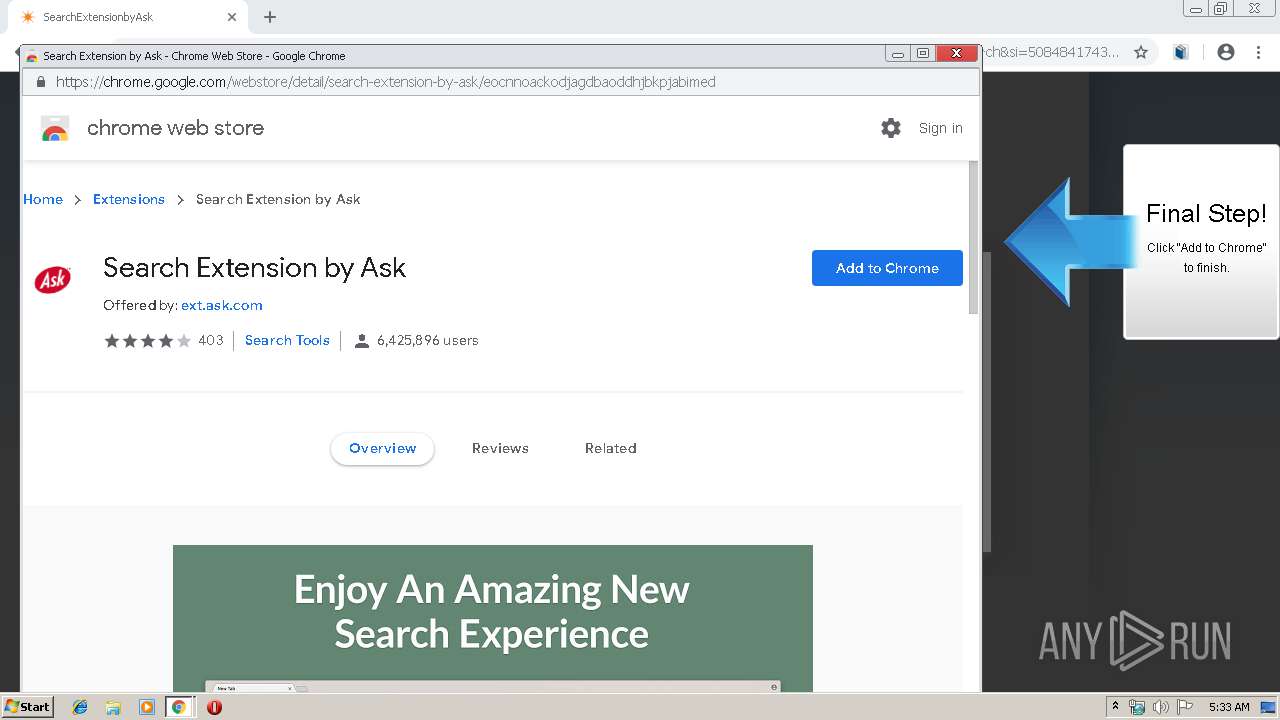
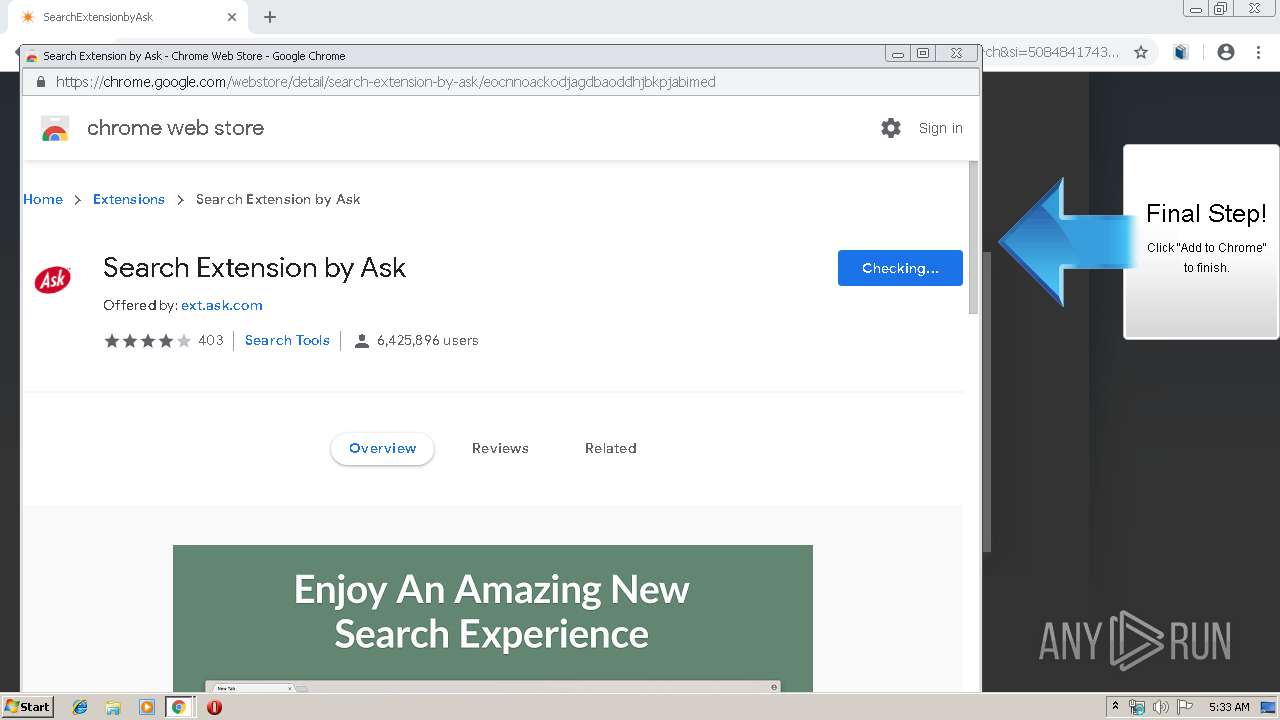
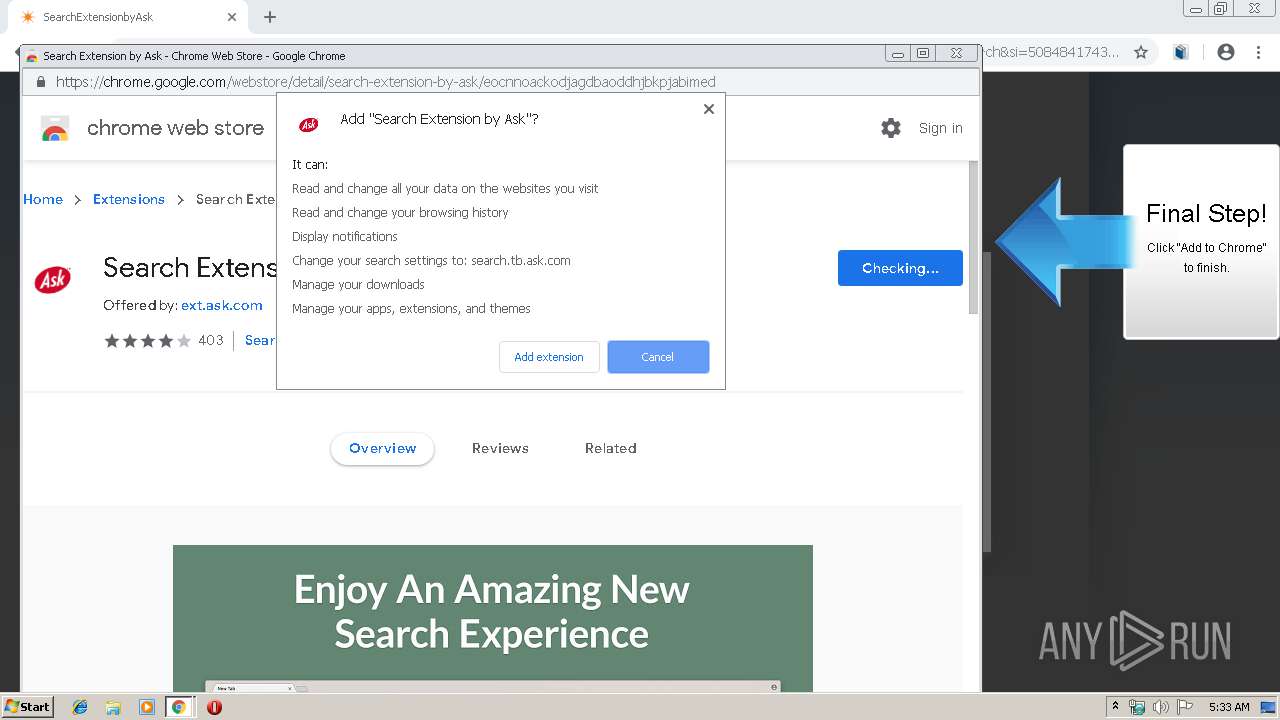
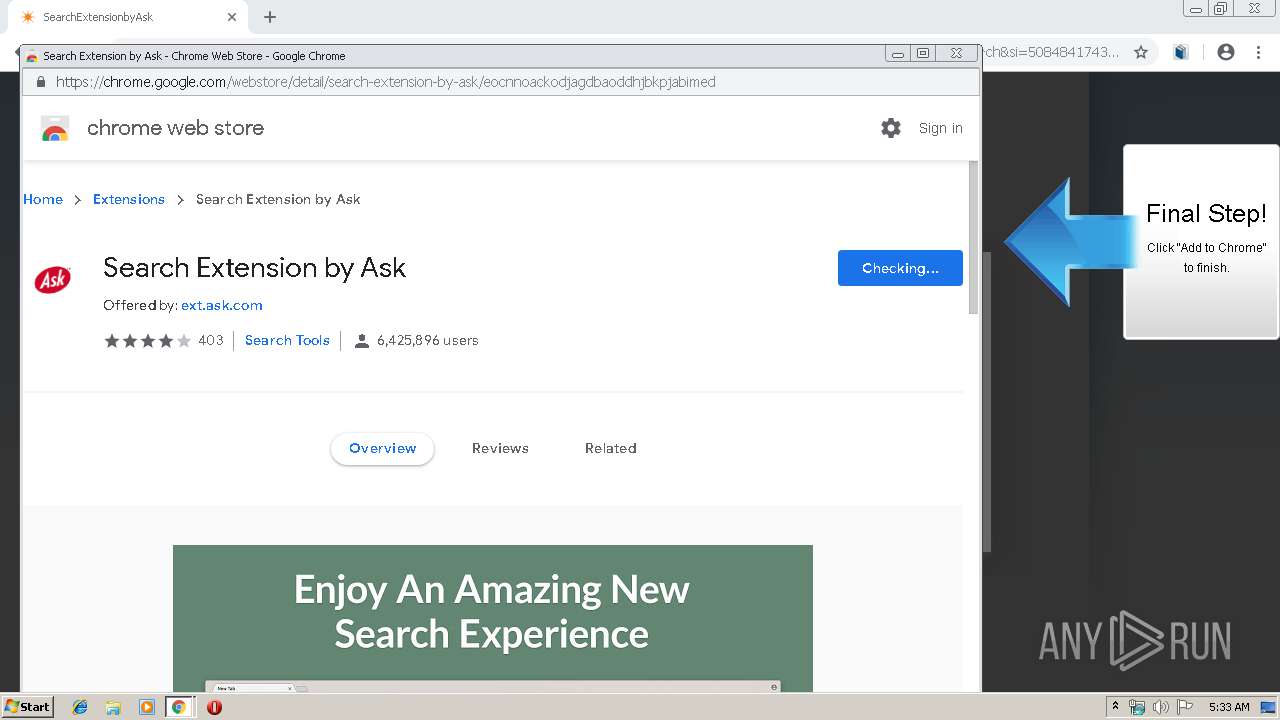
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 916)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 304)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 916)
Application launched itself
- chrome.exe (PID: 916)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
75
Monitored processes
46
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=972,10472020817386206667,17024858077240079286,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=10958127139020453963 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10958127139020453963 --renderer-client-id=29 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2280 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 264 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1336 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=972,10472020817386206667,17024858077240079286,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=819762846999301004 --mojo-platform-channel-handle=1532 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=972,10472020817386206667,17024858077240079286,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=13716767255667194028 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13716767255667194028 --renderer-client-id=39 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3520 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 396 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=972,10472020817386206667,17024858077240079286,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=17137516346551147039 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17137516346551147039 --renderer-client-id=43 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4064 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 580 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=972,10472020817386206667,17024858077240079286,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13716700312138483334 --mojo-platform-channel-handle=3920 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 628 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6f650f18,0x6f650f28,0x6f650f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 688 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=972,10472020817386206667,17024858077240079286,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12067975076939027939 --mojo-platform-channel-handle=3768 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" https://www.googleadservices.com/pagead/aclk?sa=L&ai=CQHVTQhiTXNzeHoPAogPgwYCwCtzgpslTssXetMQGwI23ARABIPbDpyRgpaCVgJgBoAHv7YaeA8gBAuACAKgDAcgDmQSqBJQCT9BVLynl4ODojWqzYUhfwVG_MDxdacOXE4f1PyaINfotiqMeTaQBccR16UPOjFue9Nx7WV4M8oCaYXix0uJrzxmCwNP1ASuPsE7C_cK18udeA4XbfLbj8s7tIWPfyt7NqqkPmSqIfyXNAAQ_YJEoly6lxnccs3JlsJPWMewHk-8basH18MW-L0bLmBDVG2zlBWsNPoyOi03mLJR6zWxyrT989kEeIKJrF-1z-uAioIKai6sjOEoRqhPrraWVwO9uJ6gIDv_nK7_X2rZo_sFRe4A6OYNc55ouNYnNoUmwhvAQ76DlrlJnF3CVDbcXjRsAmdf-EB6JkS8ZsTeGUYwp6VIMfHusxC7iJ3pWkwPo31wnjdc64AQBoAYCgAf5kflhqAeOzhuoB9XJG6gH4NMbqAeoBqgH2csbqAfPzBuoB6a-G9gHAdIIBwiAYRABGAGxCUvP3FCTCDGZgAoD2BMM&num=1&cid=CAASEuRocoJgisB6tdXdIo8bgBOpCg&sig=AOD64_0vrV0G5r2F9TA2sj9JiGDMu3VhrA&client=ca-pub-3448704589648193&nm=5&nx=204&ny=32&mb=2&adurl=http://free.freemanualsindex.com/index.jhtml%3Fpartner%3D%5ECPO%5Exdm152%26s1%3D50848417431 | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=972,10472020817386206667,17024858077240079286,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=6243633007518773936 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6243633007518773936 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4116 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
705
Read events
578
Write events
122
Delete events
5
Modification events
| (PID) Process: | (916) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (916) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (916) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (916) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (916) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (264) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 916-13197619980245750 |
Value: 259 | |||
| (PID) Process: | (916) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (916) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (916) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (916) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
56
Text files
211
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 916 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 916 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 916 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 916 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 916 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 916 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\48f430b9-197f-4809-b8c5-b3747cdb460e.tmp | — | |
MD5:— | SHA256:— | |||
| 916 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 916 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 916 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 916 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
58
TCP/UDP connections
104
DNS requests
57
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
304 | chrome.exe | GET | 204 | 35.244.218.203:80 | http://free.freemanualsindex.com/anemone.jhtml?anxuu=B50FC615-7937-4FAA-A4FA-34C07C9E41FA&anxa=CAPDownloadProcess&anxv=1.0.0&anxd=2011-06-01T00%3A00%3A00Z&anxsn=prod-dlp-europe-west1-zmkr&anxu=http%3A%2F%2Ffree.freemanualsindex.com%2Findex.jhtml&anxl=en-US&anxlv=1553146383271&anxsq=5&cookiesEnabled=1&pageLoad=1017&anxe=SplashLanding&anxr=1964566380 | US | — | — | whitelisted |
304 | chrome.exe | GET | 302 | 185.31.128.128:80 | http://20787046p.rfihub.com/ca.gif?rb=32555&ca=20787046&_o=32555&_t=20787046&ra=REPLACE_ME_WITH_YOUR_CACHE_BUSTING | US | — | — | whitelisted |
304 | chrome.exe | GET | 307 | 213.19.162.90:80 | http://pixel.rubiconproject.com/tap.php?v=13490&nid=2596&put=1040964855205552440&expires=30&next=http%3A%2F%2Fib.adnxs.com%2Fsetuid%3Fentity%3D18%26code%3D1040964855205552440http%253A%252F%252Fus-u.openx.net%252Fw%252F1.0%252Fsd%253Fid%253D537073062%2526val%253D1040964855205552440%2526r%253Dhttp%25253A%25252F%25252Fimage2.pubmatic.com%25252FAdServer%25252FPug%25253Fvcode%25253Dbz0yJnR5cGU9MSZjb2RlPTI3MzkmdGw9MTU3NjgwMA%25253D%25253D%252526piggybackCookie%25253D1040964855205552440%252526r%25253Dhttp%2525253A%2525252F%2525252Fdsum.casalemedia.com%2525252Frum%2525253Fcm_dsp_id%2525253D57%25252526external_user_id%2525253D1040964855205552440%25252526forward%2525253Dhttp%252525253A%252525252F%252525252Ftapestry.tapad.com%252525252Ftapestry%252525252F1%252525253Fta_partner_id%252525253D937%2525252526ta_partner_did%252525253D1040964855205552440%2525252526ta_format%252525253Dgif | GB | — | — | whitelisted |
304 | chrome.exe | GET | 302 | 185.31.128.129:80 | http://p.rfihub.com/cm?forward=http%3A%2F%2Fpixel.rubiconproject.com%2Ftap.php%3Fv%3D13490%26nid%3D2596%26put%3D1040964855205552440%26expires%3D30%26next%3Dhttp%253A%252F%252Fib.adnxs.com%252Fsetuid%253Fentity%253D18%2526code%253D1040964855205552440http%25253A%25252F%25252Fus-u.openx.net%25252Fw%25252F1.0%25252Fsd%25253Fid%25253D537073062%252526val%25253D1040964855205552440%252526r%25253Dhttp%2525253A%2525252F%2525252Fimage2.pubmatic.com%2525252FAdServer%2525252FPug%2525253Fvcode%2525253Dbz0yJnR5cGU9MSZjb2RlPTI3MzkmdGw9MTU3NjgwMA%2525253D%2525253D%25252526piggybackCookie%2525253D1040964855205552440%25252526r%2525253Dhttp%252525253A%252525252F%252525252Fdsum.casalemedia.com%252525252Frum%252525253Fcm_dsp_id%252525253D57%2525252526external_user_id%252525253D1040964855205552440%2525252526forward%252525253Dhttp%25252525253A%25252525252F%25252525252Ftapestry.tapad.com%25252525252Ftapestry%25252525252F1%25252525253Fta_partner_id%25252525253D937%252525252526ta_partner_did%25252525253D1040964855205552440%252525252526ta_format%25252525253Dgif&google_gid=CAESEO14VgQDcROr6vfDS5BGMhI&google_cver=1 | US | — | — | whitelisted |
304 | chrome.exe | GET | 200 | 2.18.232.251:80 | http://ak.staticimgfarm.com/images/webtooltab/ttdetect-2/prd/ttDetectUtil.js | unknown | text | 3.81 Kb | whitelisted |
304 | chrome.exe | GET | 200 | 35.244.218.203:80 | http://free.freemanualsindex.com/index.jhtml?partner=^CPO^xdm152&s1=50848417431&gclid=EAIaIQobChMI3Iez57eS4QIVA6BoCh3gIACmEAEYASAAEgKcGvD_BwE | US | html | 42.7 Kb | whitelisted |
304 | chrome.exe | GET | 204 | 35.244.218.203:80 | http://free.freemanualsindex.com/anemone.jhtml?anxuu=B50FC615-7937-4FAA-A4FA-34C07C9E41FA&anxa=CAPDownloadProcess&anxv=1.0.0&anxd=2011-06-01T00%3A00%3A00Z&anxsn=prod-dlp-europe-west1-zmkr&anxu=http%3A%2F%2Ffree.freemanualsindex.com%2Findex.jhtml&anxl=en-US&anxlv=1553146382664&anxrd=none&anxrp=-&anxrk=-&anxrm=-&anxrb=-&anxrc=-&anxrs=-&anxsq=1&anxi=5F7B289A-6244-4B18-A676-0C6DA291D1CA&anxe=backFill&anxr=327787801 | US | compressed | 42.7 Kb | whitelisted |
304 | chrome.exe | POST | 200 | 35.244.218.203:80 | http://freemanualsindex.dl.myway.com/mirrorCookies.jhtml | US | html | 93 b | whitelisted |
304 | chrome.exe | GET | 204 | 35.244.218.203:80 | http://free.freemanualsindex.com/anemone.jhtml?anxuu=B50FC615-7937-4FAA-A4FA-34C07C9E41FA&anxa=CAPDownloadProcess&anxv=1.0.0&anxd=2011-06-01T00%3A00%3A00Z&anxsn=prod-dlp-europe-west1-zmkr&anxu=http%3A%2F%2Ffree.freemanualsindex.com%2Findex.jhtml&anxl=en-US&anxlv=1553146382671&anxsq=3&present=false&anxe=ToolbarDetect&anxr=760290238 | US | compressed | 42.7 Kb | whitelisted |
304 | chrome.exe | GET | 200 | 35.244.218.203:80 | http://freemanualsindex.dl.tb.ask.com/localStorage.jhtml | US | html | 2.20 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
304 | chrome.exe | 216.58.208.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
304 | chrome.exe | 35.244.218.203:80 | free.freemanualsindex.com | — | US | whitelisted |
304 | chrome.exe | 216.58.205.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
304 | chrome.exe | 2.18.232.251:80 | ak.staticimgfarm.com | Akamai International B.V. | — | whitelisted |
304 | chrome.exe | 172.217.18.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
304 | chrome.exe | 216.58.207.66:443 | www.googleadservices.com | Google Inc. | US | whitelisted |
304 | chrome.exe | 2.18.232.251:443 | ak.staticimgfarm.com | Akamai International B.V. | — | whitelisted |
304 | chrome.exe | 216.58.207.66:80 | www.googleadservices.com | Google Inc. | US | whitelisted |
304 | chrome.exe | 185.31.128.128:80 | 20787046p.rfihub.com | Rocket Fuel Inc. | US | suspicious |
304 | chrome.exe | 172.217.16.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.googleadservices.com |
| whitelisted |
accounts.google.com |
| shared |
free.freemanualsindex.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
ak.staticimgfarm.com |
| whitelisted |
ak.imgfarm.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
akz.imgfarm.com |
| whitelisted |
eula.mindspark.com |
| malicious |