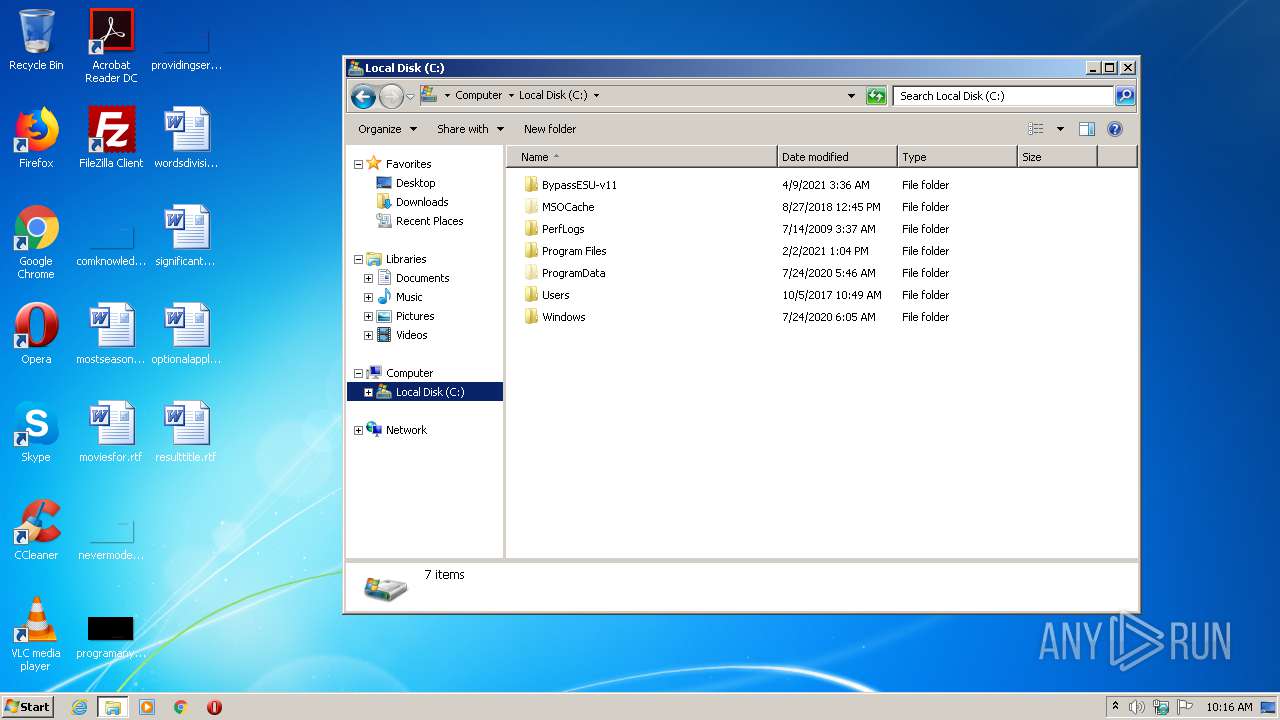
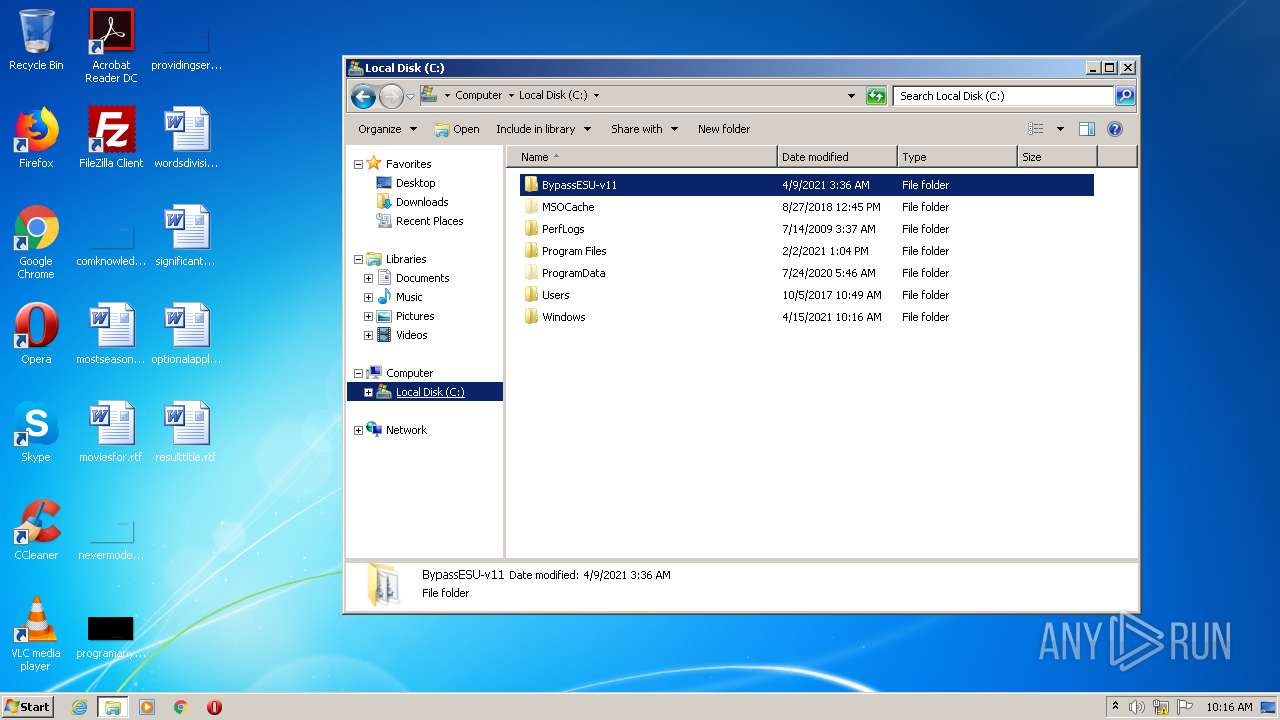
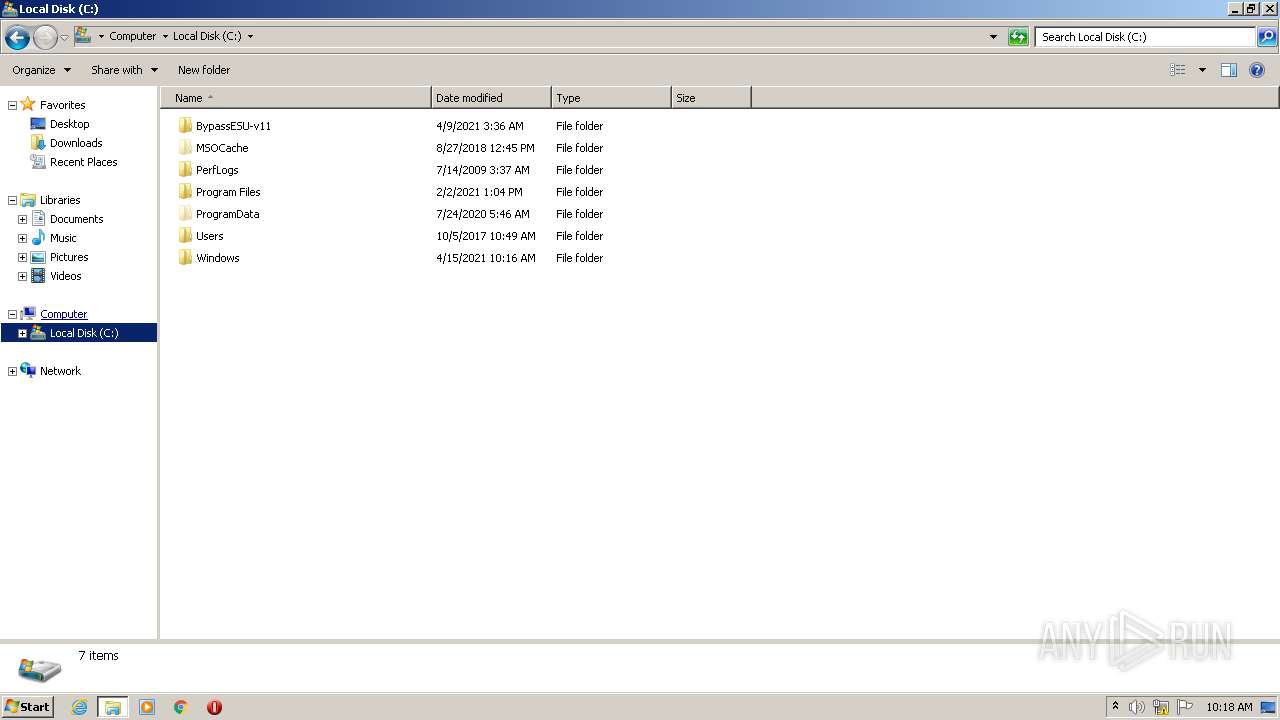
| File name: | BypassESU-v11.exe |
| Full analysis: | https://app.any.run/tasks/de55c008-e1c0-4110-9335-b9121592a20d |
| Verdict: | Malicious activity |
| Analysis date: | April 15, 2021, 09:15:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | F9631E7F44FB896F99F6E72DAE4EED88 |
| SHA1: | 71FB0188387B4721EE44E8BDA0DF449759346F38 |
| SHA256: | ADAD58131A9F8130646B342B94BDA894FF66C59C2063A55B27EA175EEE28CA37 |
| SSDEEP: | 12288:0RZ+IoG/n9IQxW3OBseNX+t/RbSVkqmSKWgy9Y4S+alMBC11HivuY0oWVDWfXSA+:O2G/nvxW3WKtSmqm1Wgy9Yx+agG1CvzI |
MALICIOUS
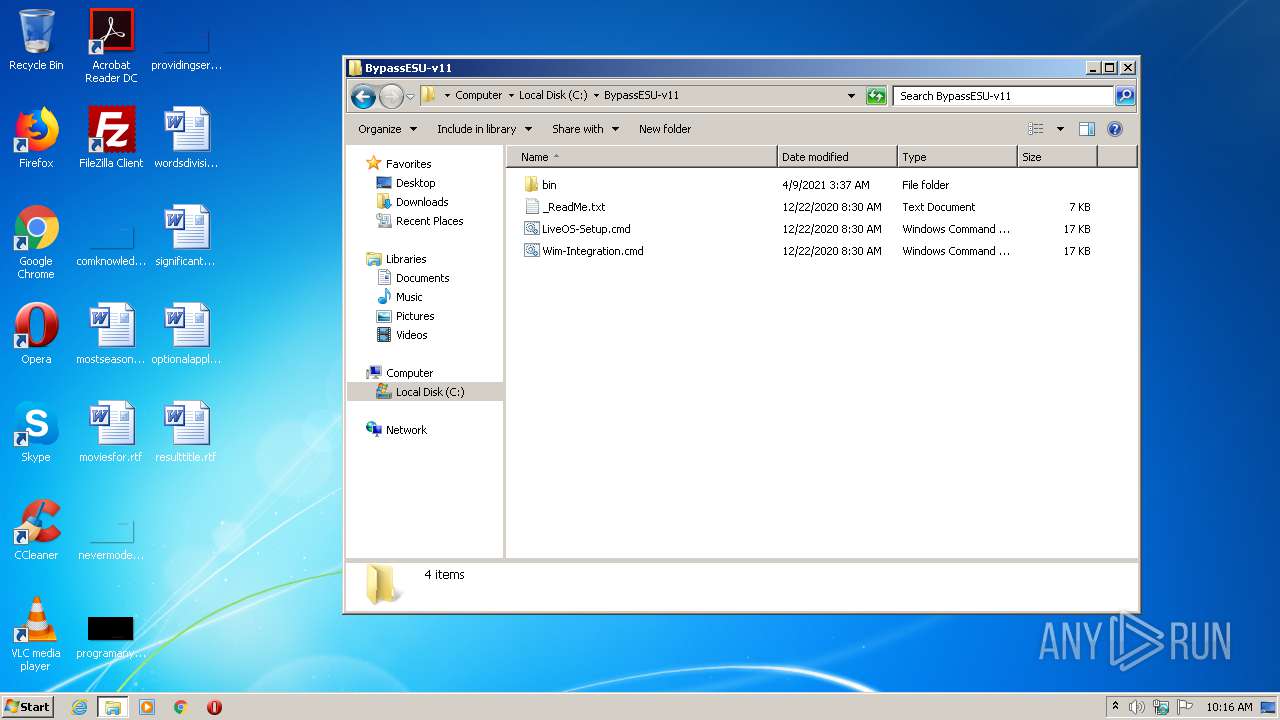
Drops executable file immediately after starts
- BypassESU-v11.exe (PID: 3404)
- bbe.exe (PID: 1548)
- bbe.exe (PID: 3212)
- Dism.exe (PID: 1148)
Application was dropped or rewritten from another process
- superUser32.exe (PID: 1428)
- bbe.exe (PID: 1920)
- bbe.exe (PID: 1548)
- bbe.exe (PID: 3212)
- superUser32.exe (PID: 2456)
- superUser32.exe (PID: 3904)
- bbe.exe (PID: 3676)
- superUser32.exe (PID: 444)
- dismhost.exe (PID: 2496)
Runs injected code in another process
- superUser32.exe (PID: 1428)
- superUser32.exe (PID: 2456)
- superUser32.exe (PID: 3904)
- superUser32.exe (PID: 444)
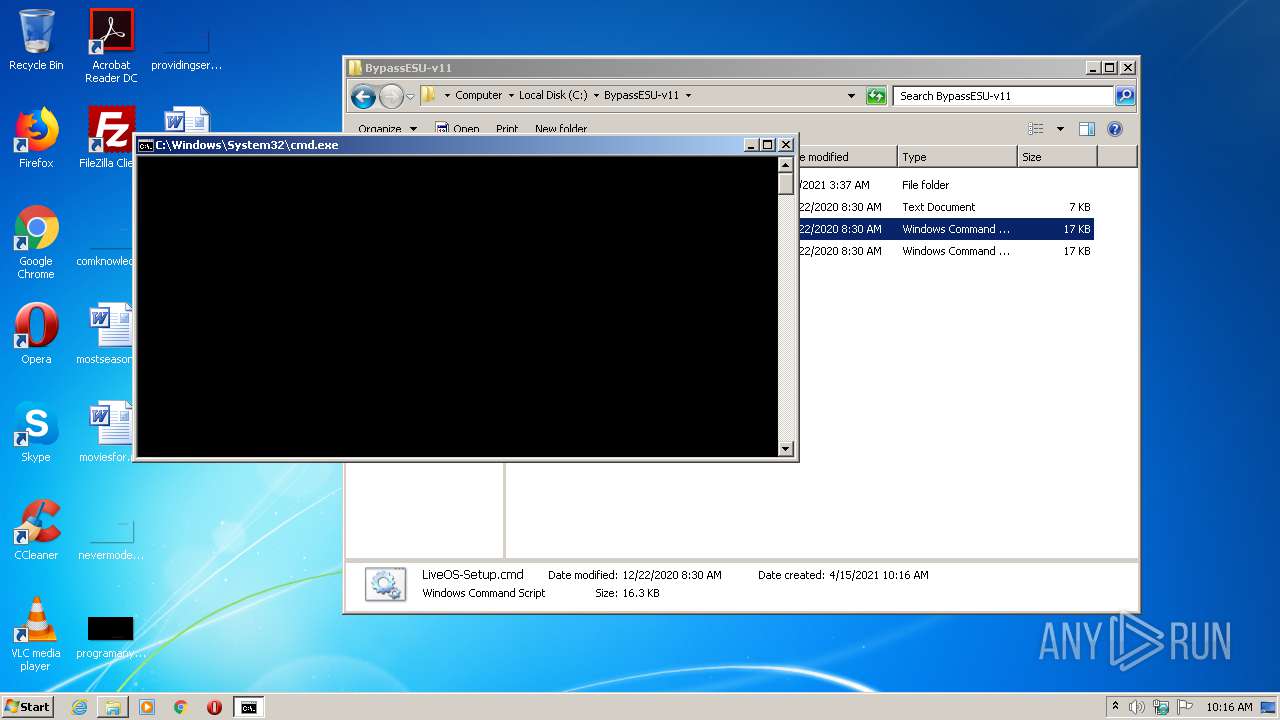
Application was injected by another process
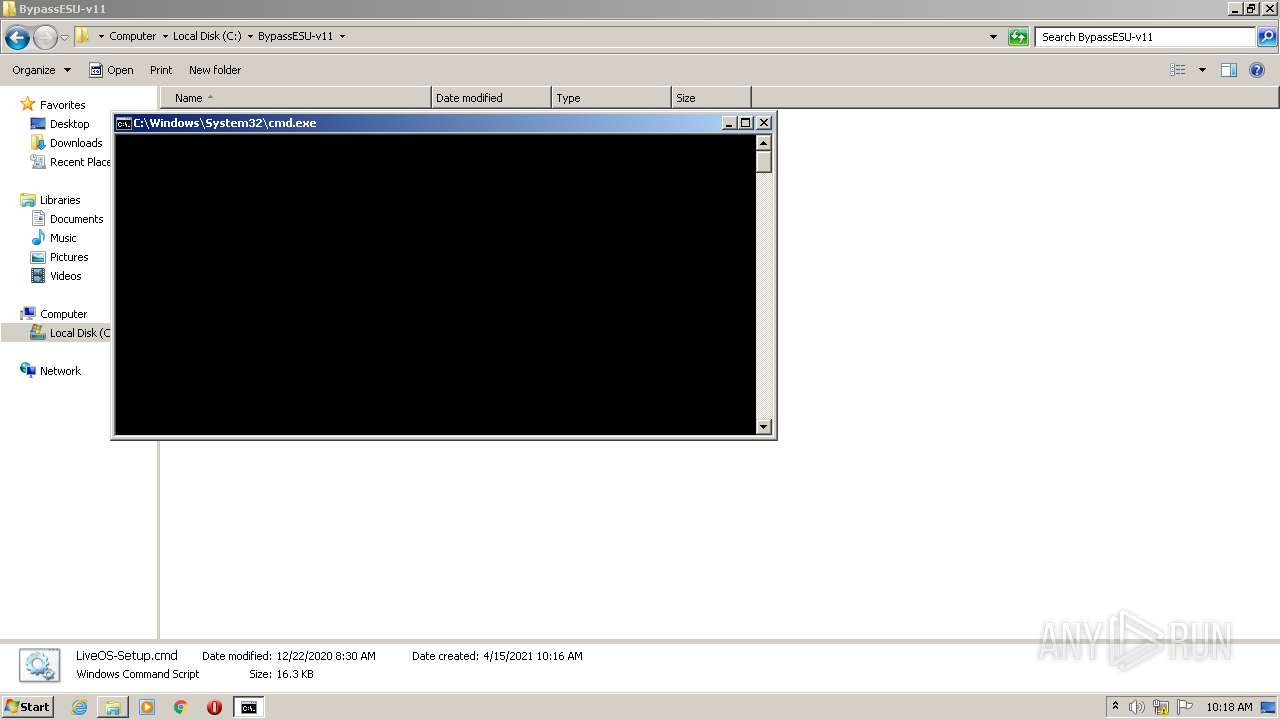
- cmd.exe (PID: 1044)
- cmd.exe (PID: 2332)
- cmd.exe (PID: 1896)
- cmd.exe (PID: 3652)
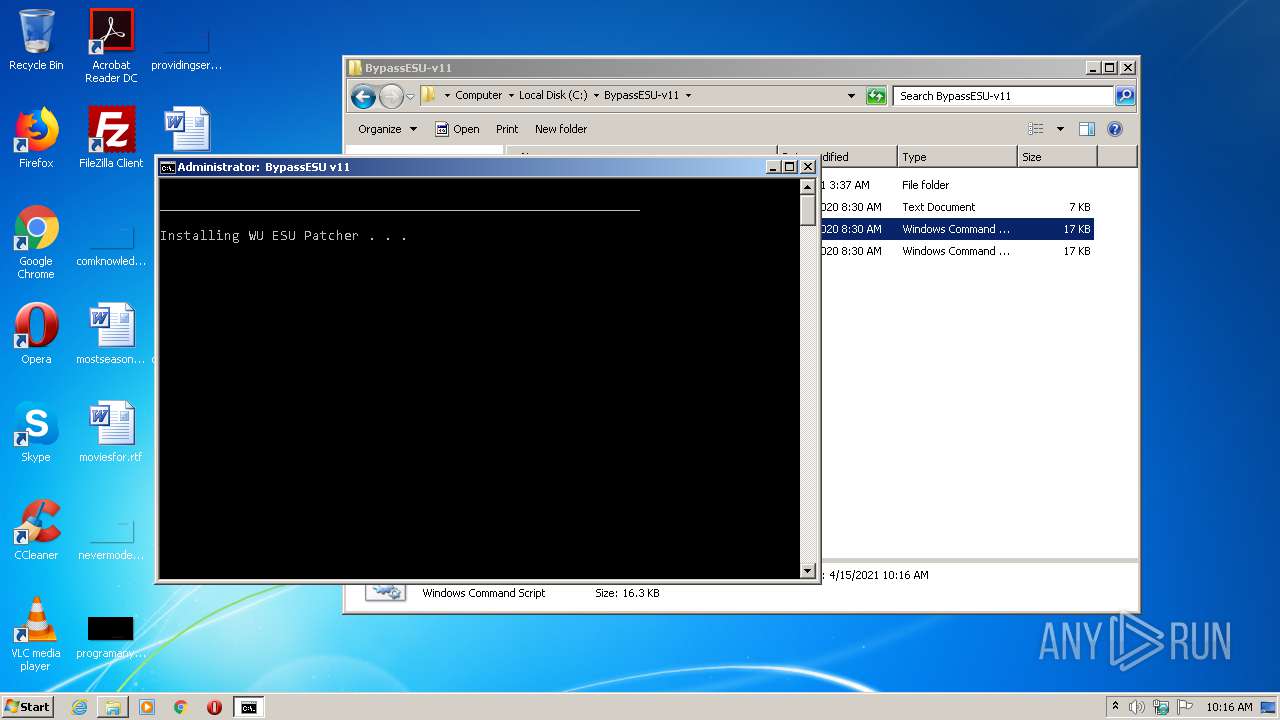
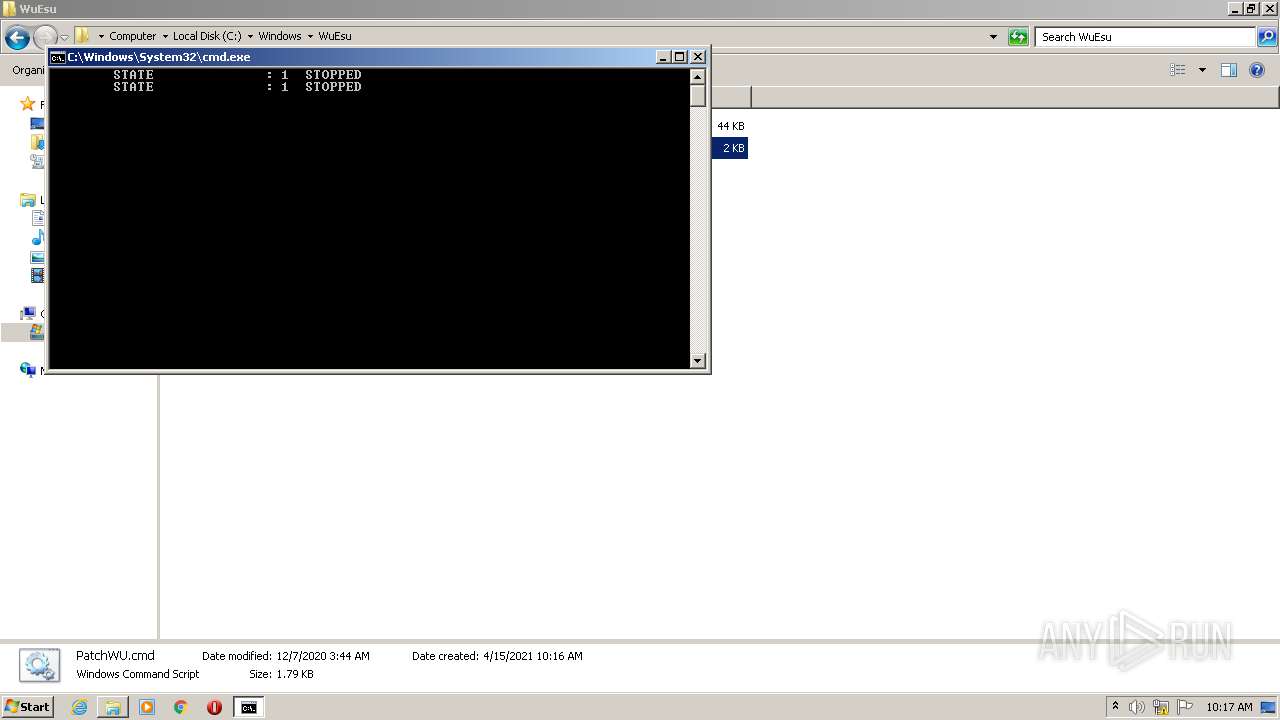
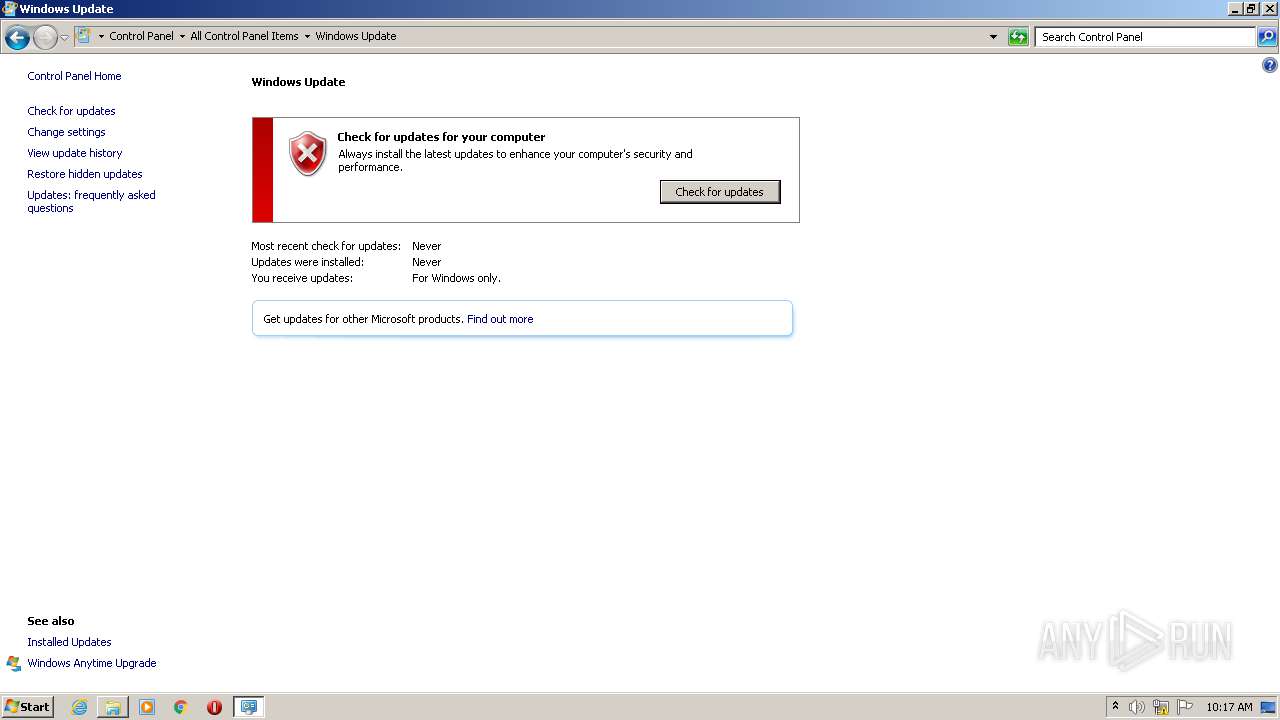
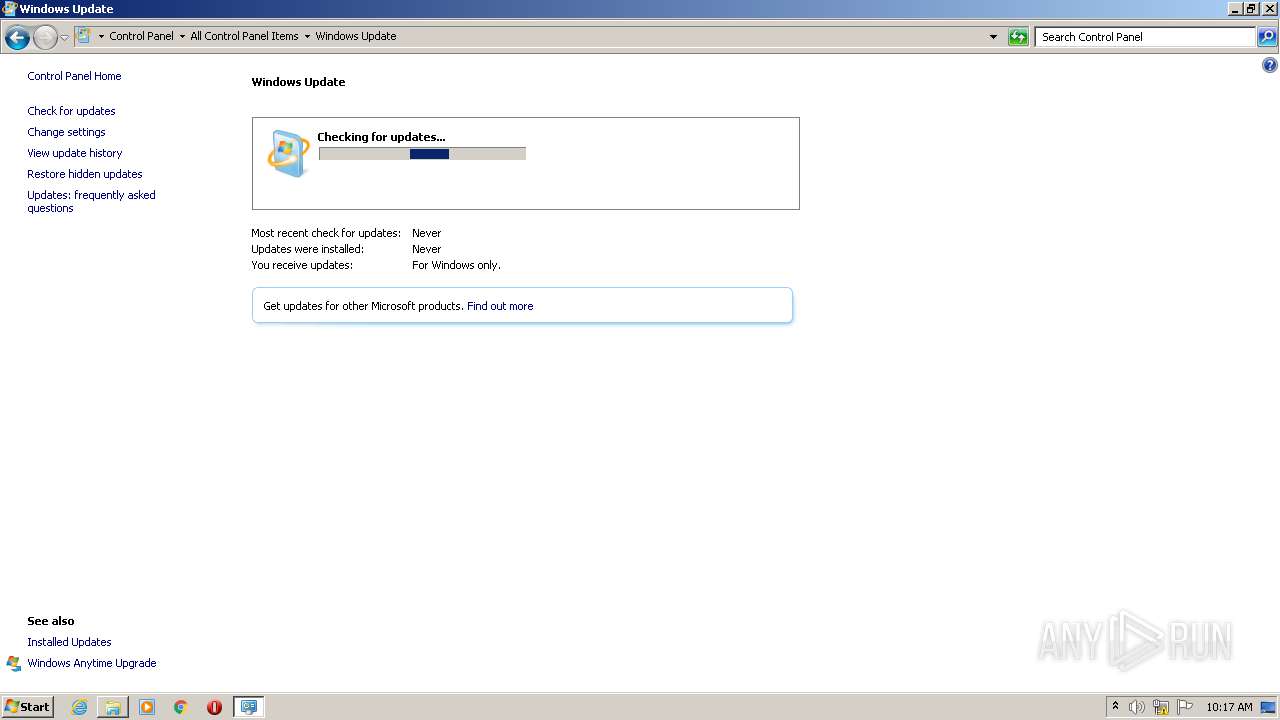
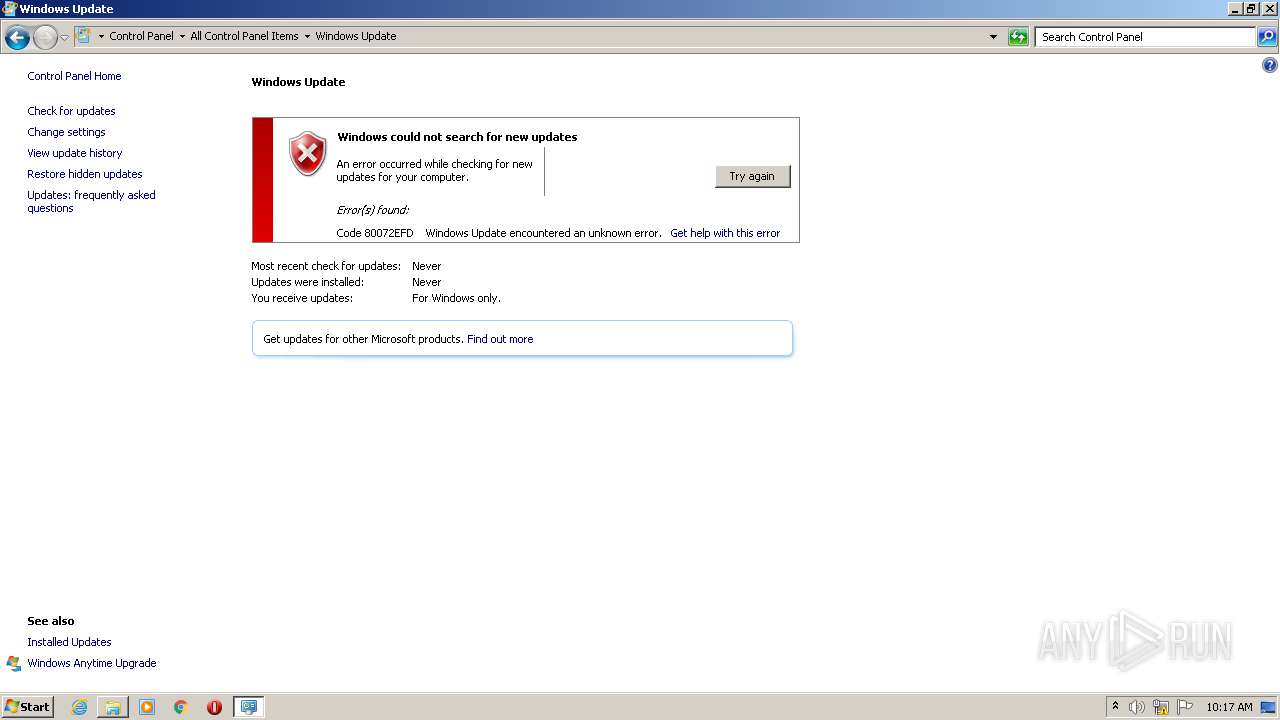
Uses NET.EXE to stop Windows Update service
- cmd.exe (PID: 1044)
- cmd.exe (PID: 2332)
Starts NET.EXE for service management
- cmd.exe (PID: 1044)
- cmd.exe (PID: 2692)
- cmd.exe (PID: 2332)
- cmd.exe (PID: 3228)
- cmd.exe (PID: 2712)
- cmd.exe (PID: 1928)
- cmd.exe (PID: 3652)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2196)
- schtasks.exe (PID: 3000)
- schtasks.exe (PID: 3564)
- schtasks.exe (PID: 2940)
- schtasks.exe (PID: 3644)
- schtasks.exe (PID: 1196)
- schtasks.exe (PID: 2716)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 1044)
- cmd.exe (PID: 2332)
- cmd.exe (PID: 1896)
Creates or modifies windows services
- reg.exe (PID: 2288)
- reg.exe (PID: 3552)
- reg.exe (PID: 2720)
- reg.exe (PID: 2516)
Loads dropped or rewritten executable
- svchost.exe (PID: 876)
- svchost.exe (PID: 772)
- Dism.exe (PID: 1148)
- dismhost.exe (PID: 2496)
- TrustedInstaller.exe (PID: 2088)
- TrustedInstaller.exe (PID: 768)
SUSPICIOUS
Executable content was dropped or overwritten
- BypassESU-v11.exe (PID: 3404)
- cmd.exe (PID: 1044)
- bbe.exe (PID: 1548)
- bbe.exe (PID: 3212)
- cmd.exe (PID: 1896)
- bbe.exe (PID: 3676)
- Dism.exe (PID: 1148)
Application launched itself
- BypassESU-v11.exe (PID: 1940)
- cmd.exe (PID: 2712)
- cmd.exe (PID: 2384)
- cmd.exe (PID: 1936)
- cmd.exe (PID: 2280)
- cmd.exe (PID: 2692)
- cmd.exe (PID: 2332)
- cmd.exe (PID: 3228)
- cmd.exe (PID: 1896)
- cmd.exe (PID: 1928)
- cmd.exe (PID: 3828)
- cmd.exe (PID: 3652)
Drops a file with too old compile date
- BypassESU-v11.exe (PID: 3404)
- cmd.exe (PID: 1044)
- cmd.exe (PID: 1896)
- Dism.exe (PID: 1148)
Reads internet explorer settings
- BypassESU-v11.exe (PID: 1940)
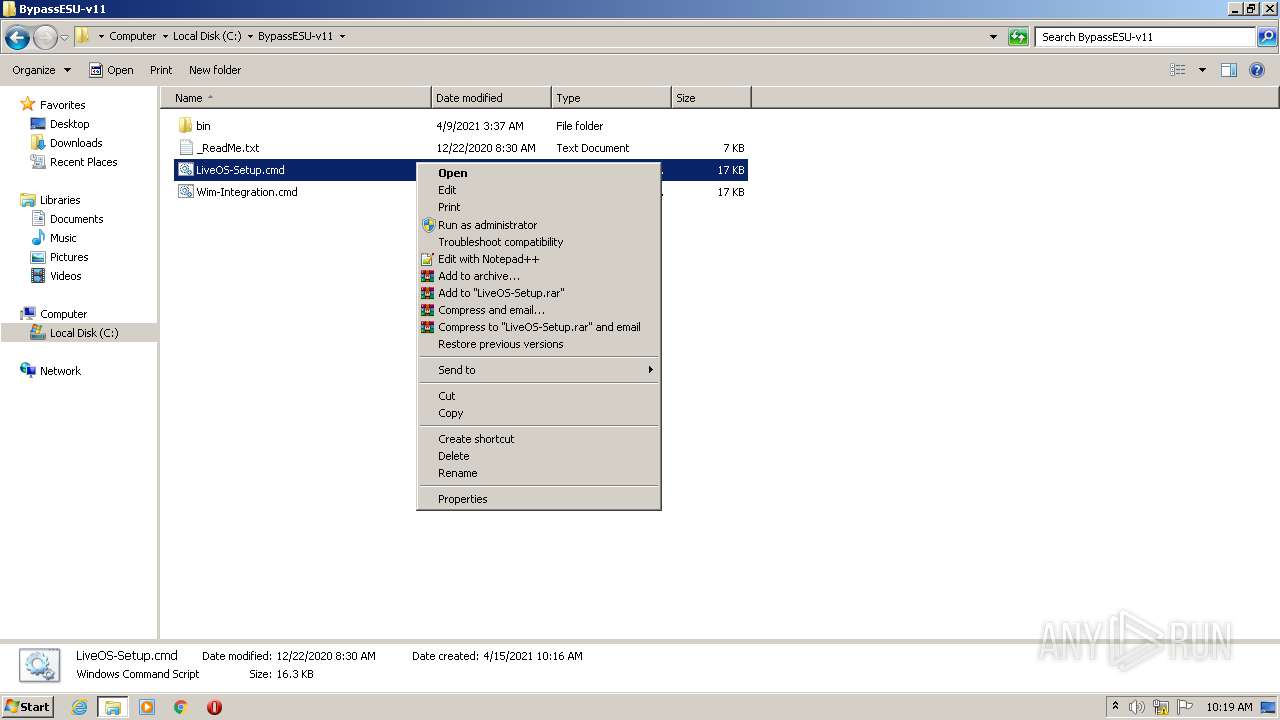
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 1044)
- cmd.exe (PID: 2384)
- cmd.exe (PID: 1936)
- cmd.exe (PID: 2280)
- cmd.exe (PID: 2692)
- cmd.exe (PID: 2332)
- cmd.exe (PID: 3228)
- cmd.exe (PID: 2712)
- cmd.exe (PID: 1896)
- cmd.exe (PID: 3828)
- cmd.exe (PID: 1928)
- cmd.exe (PID: 3652)
- cmd.exe (PID: 2536)
Starts CMD.EXE for commands execution
- TrustedInstaller.exe (PID: 2088)
- cmd.exe (PID: 1044)
- cmd.exe (PID: 2384)
- cmd.exe (PID: 2280)
- cmd.exe (PID: 1936)
- cmd.exe (PID: 2692)
- cmd.exe (PID: 2332)
- cmd.exe (PID: 3228)
- cmd.exe (PID: 2712)
- cmd.exe (PID: 1896)
- cmd.exe (PID: 3828)
- cmd.exe (PID: 1928)
- cmd.exe (PID: 3652)
Starts CHOICE.EXE (used to create a delay)
- cmd.exe (PID: 1044)
- cmd.exe (PID: 2332)
- cmd.exe (PID: 1896)
- cmd.exe (PID: 3652)
Uses WHOAMI.EXE to obtaining logged on user information
- cmd.exe (PID: 1044)
- cmd.exe (PID: 2692)
- cmd.exe (PID: 2332)
- cmd.exe (PID: 3228)
- cmd.exe (PID: 2712)
- cmd.exe (PID: 1896)
- cmd.exe (PID: 1928)
- cmd.exe (PID: 3652)
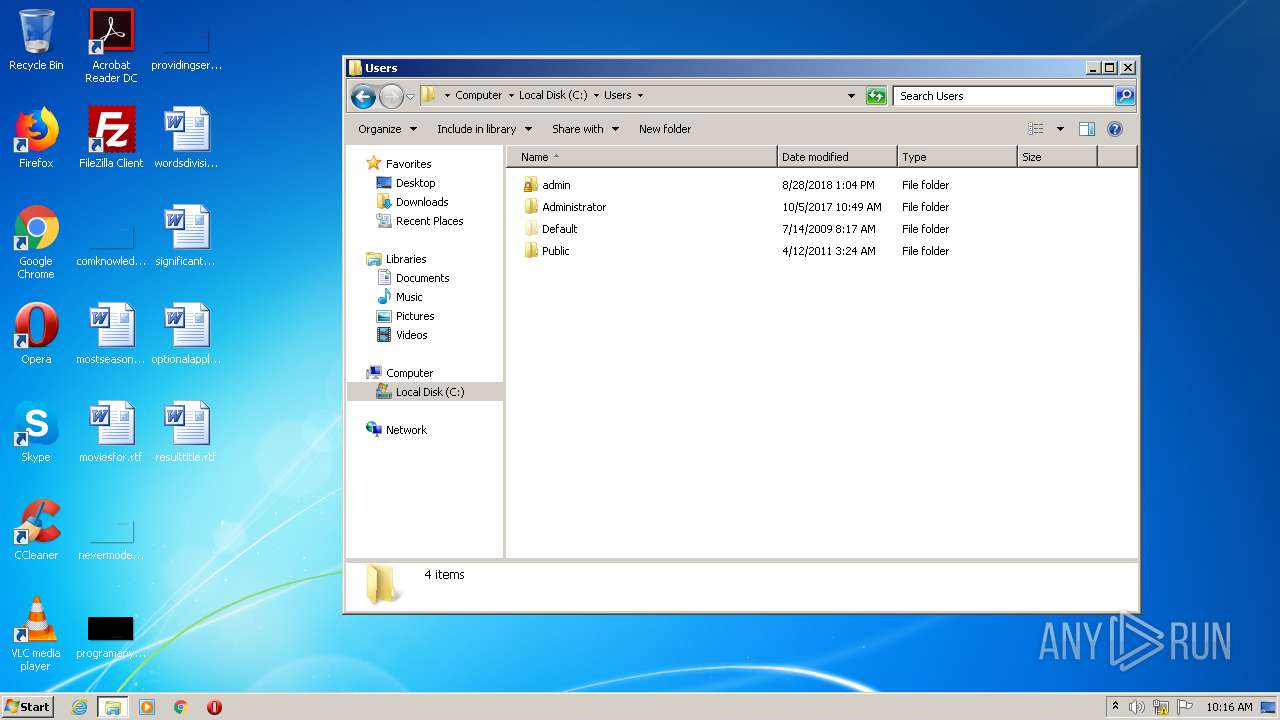
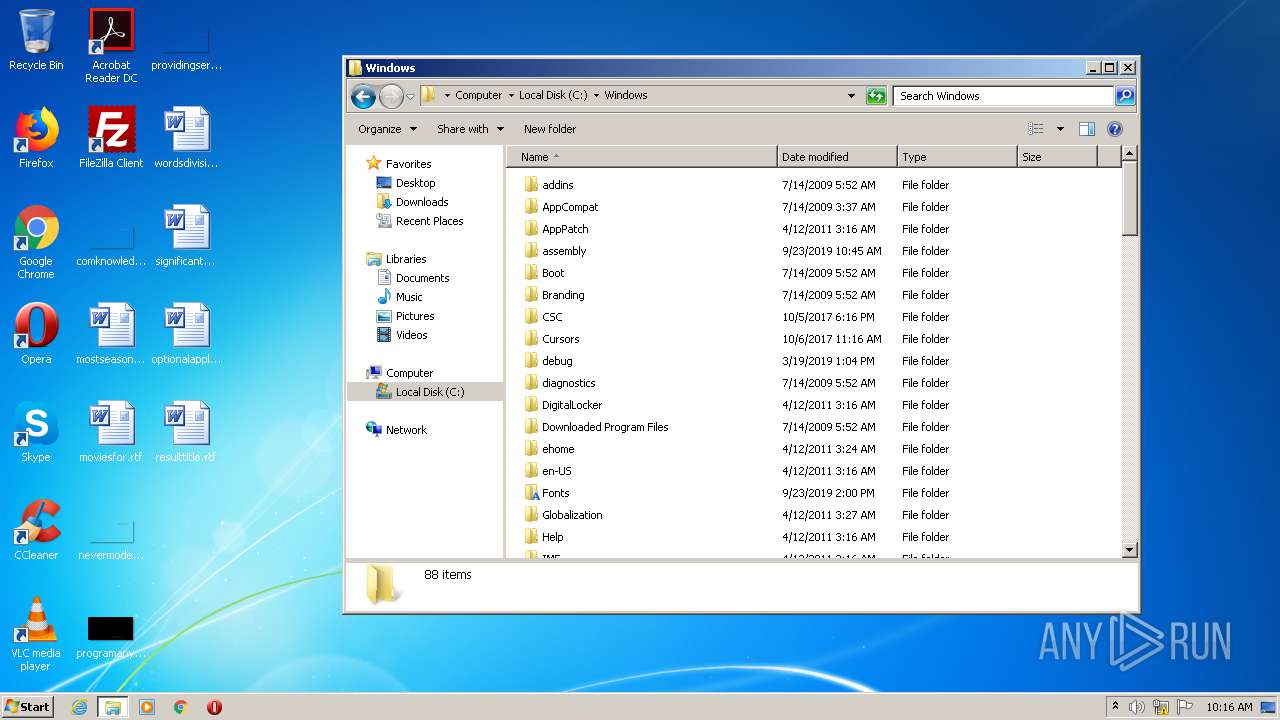
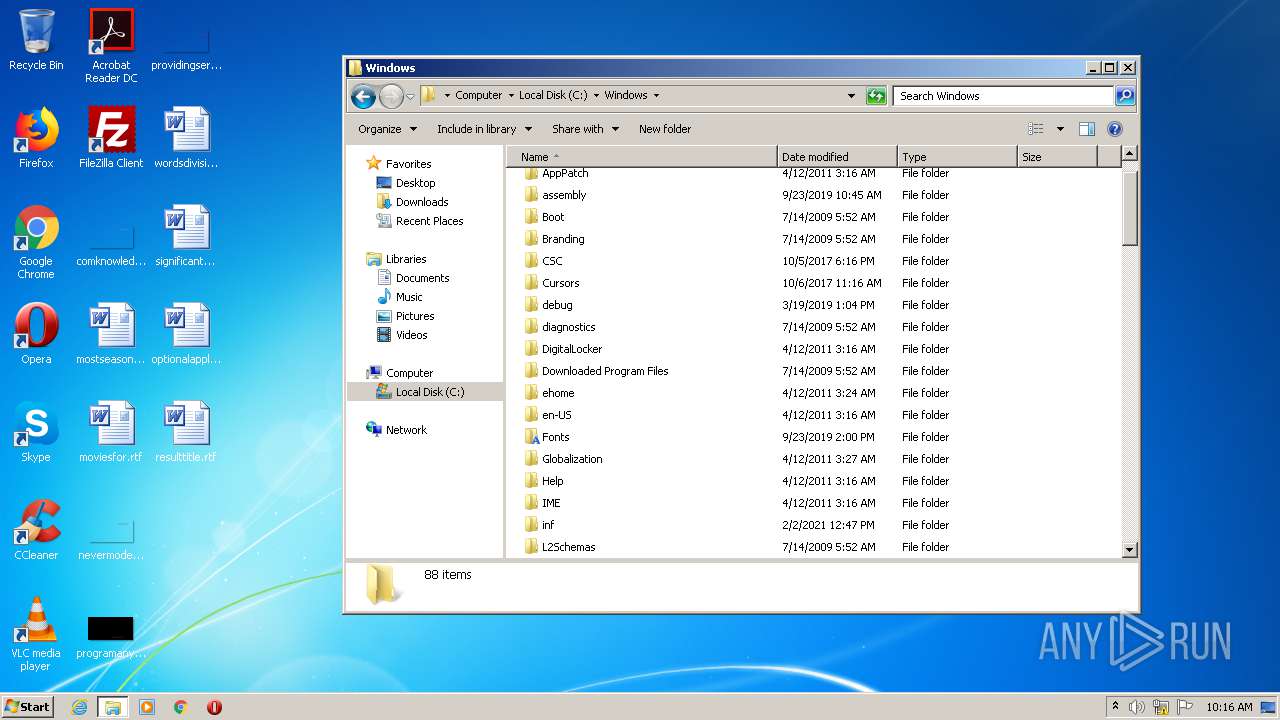
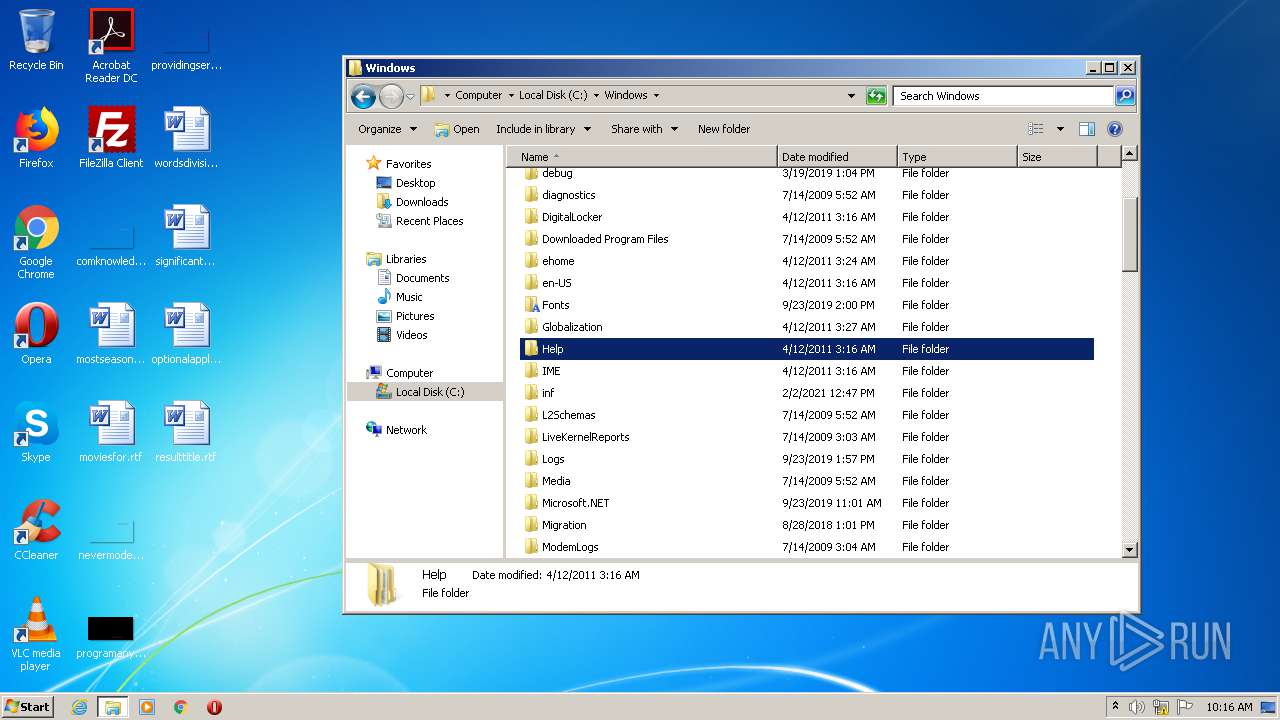
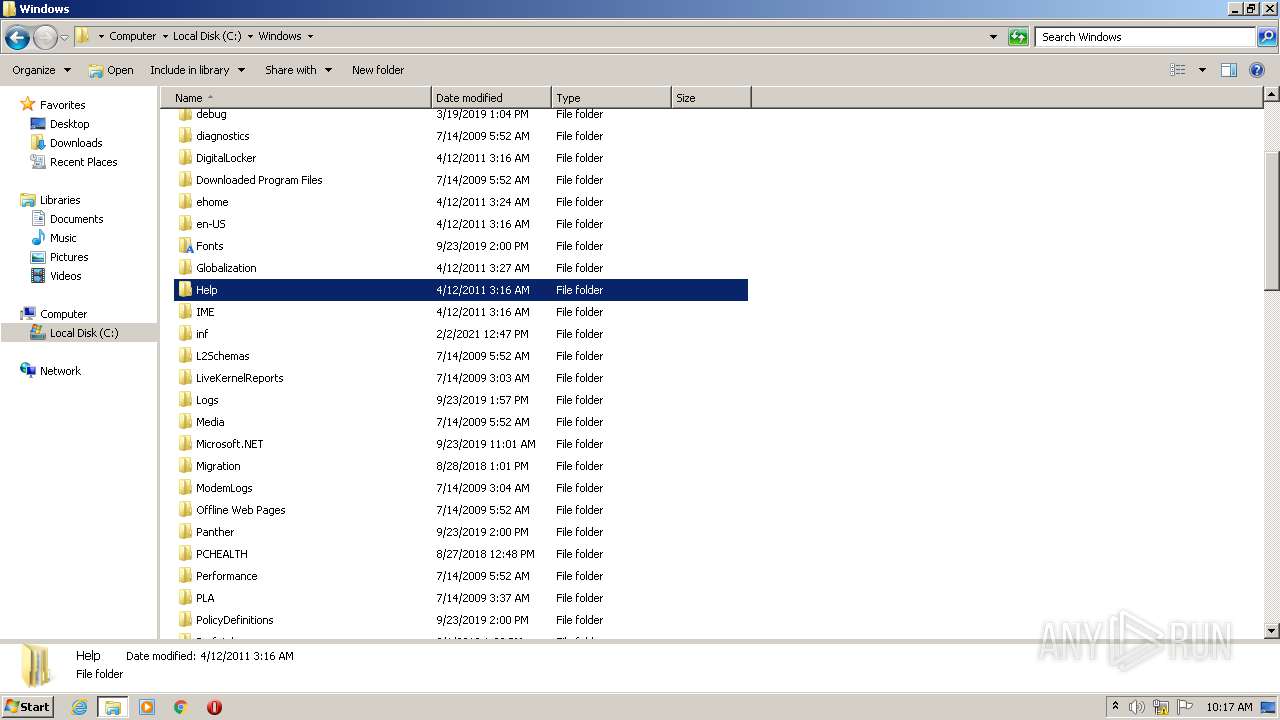
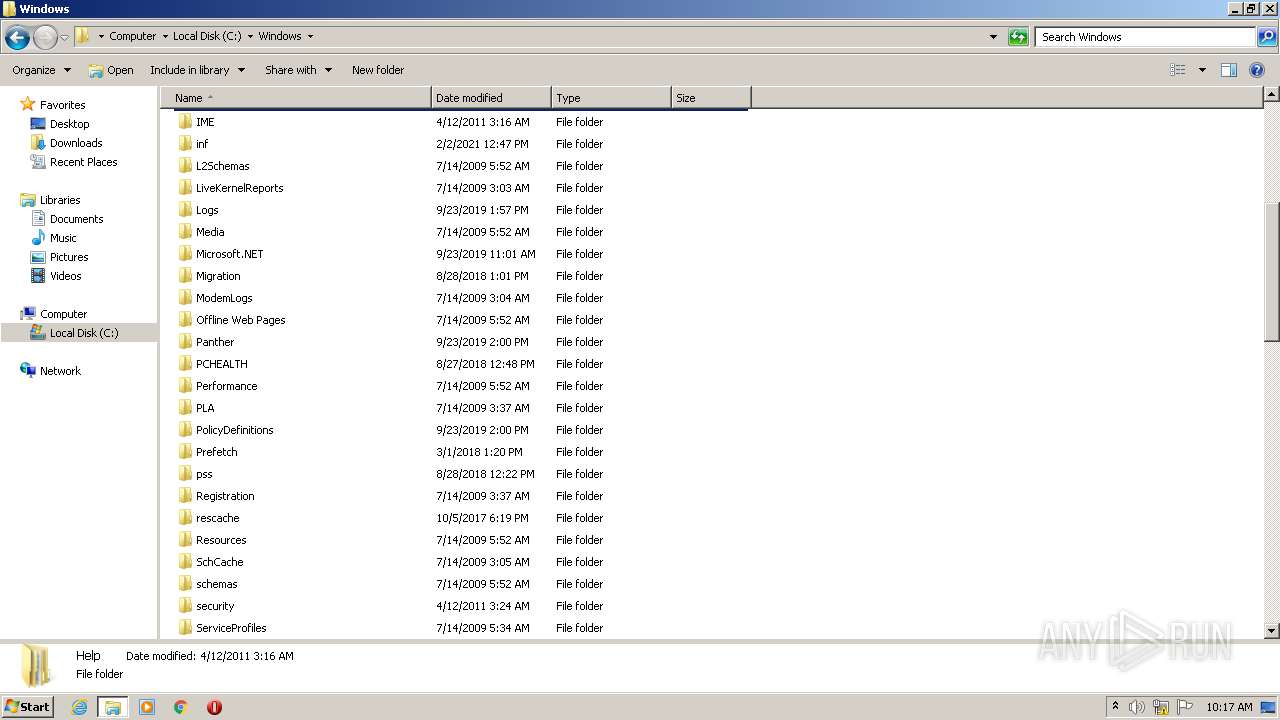
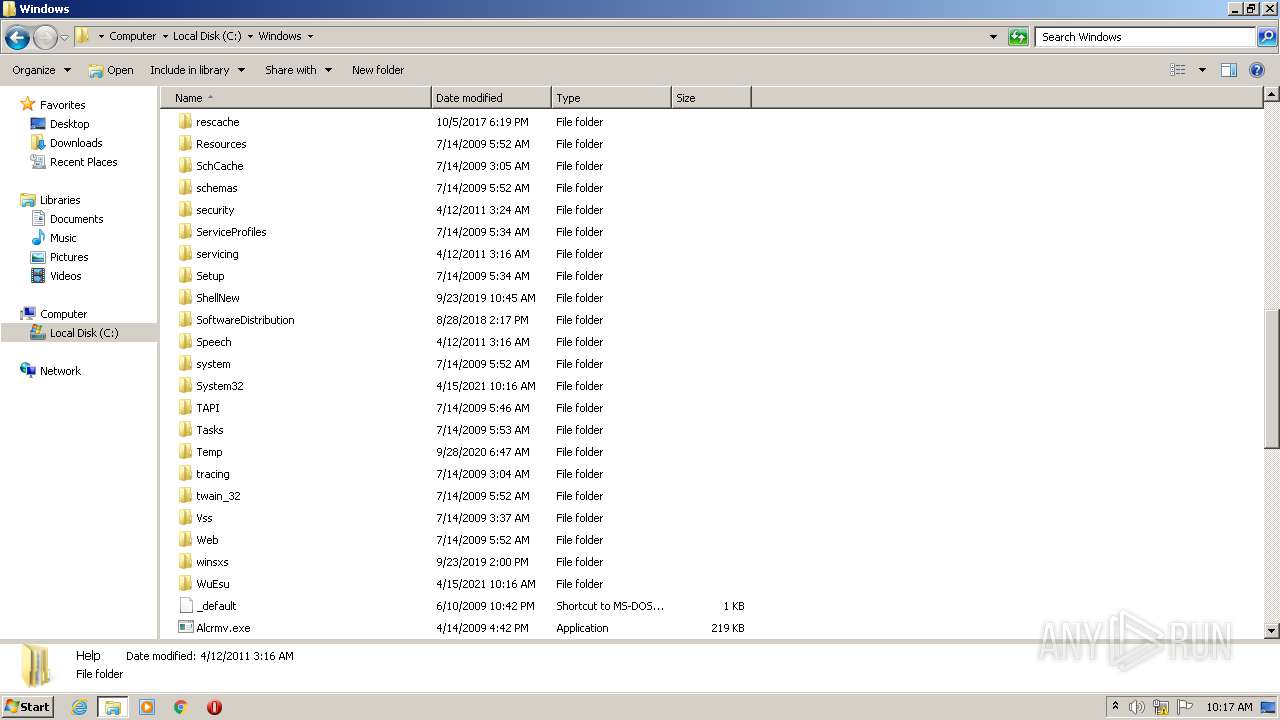
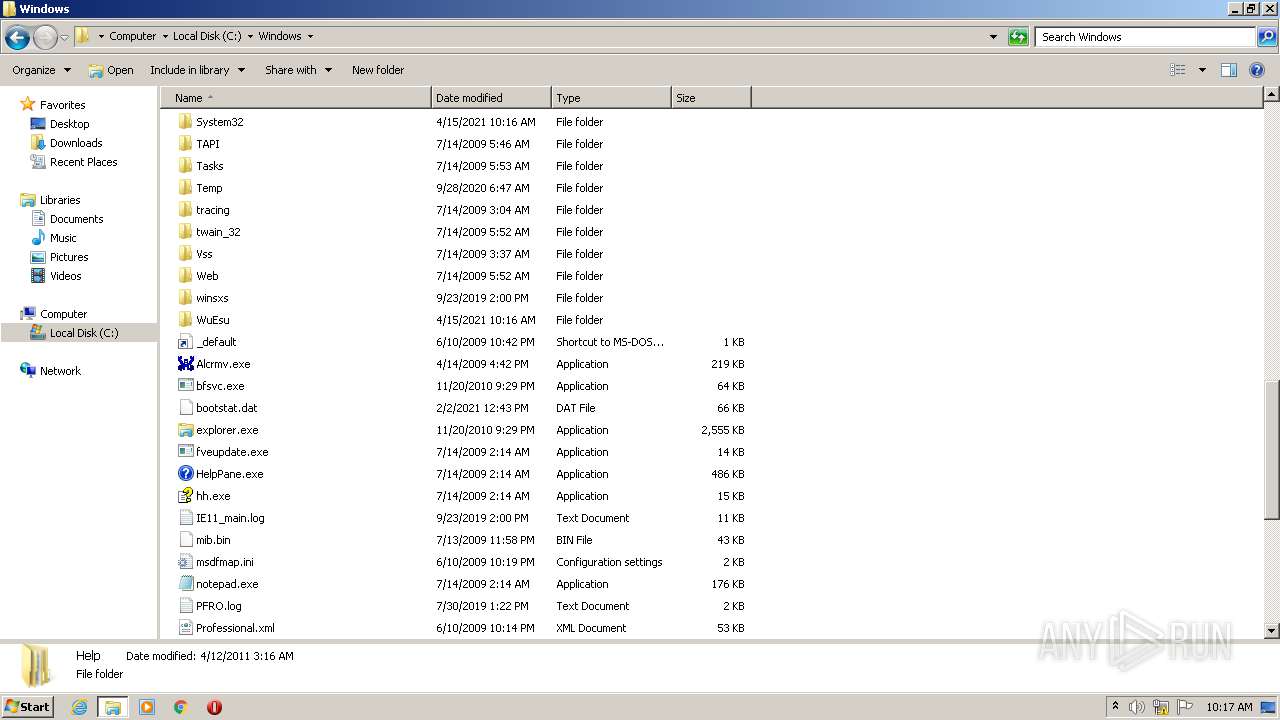
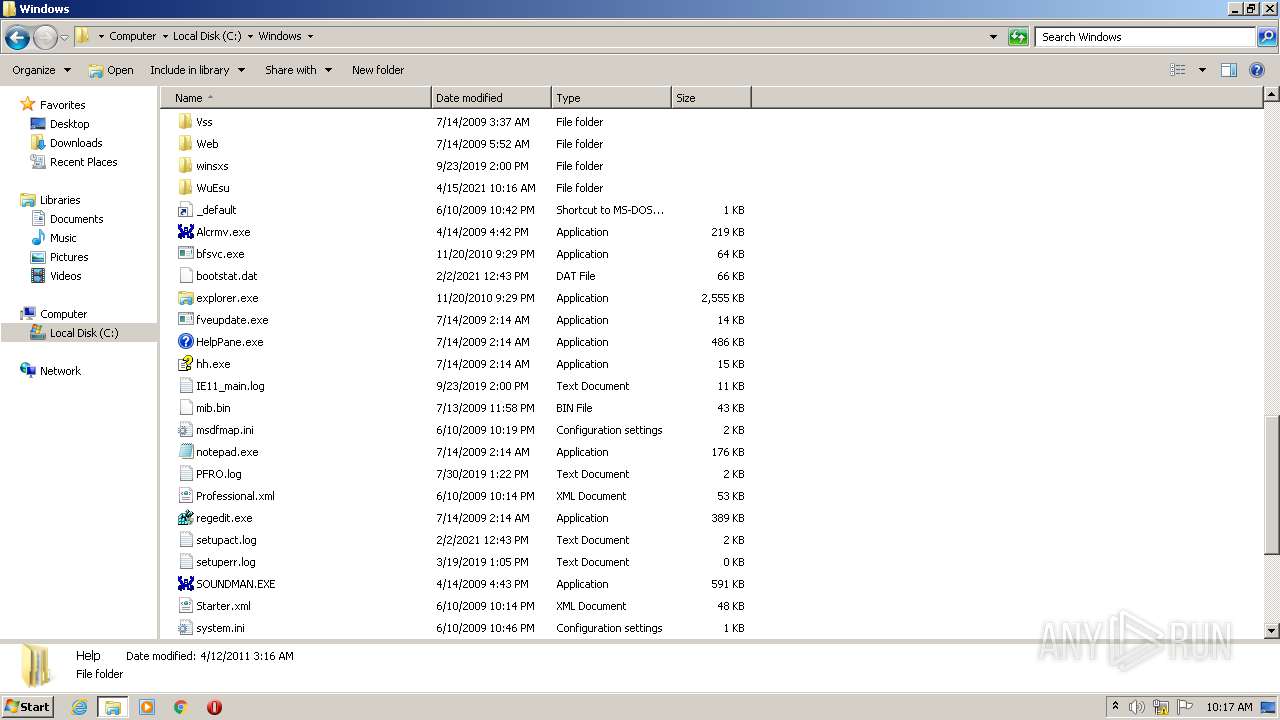
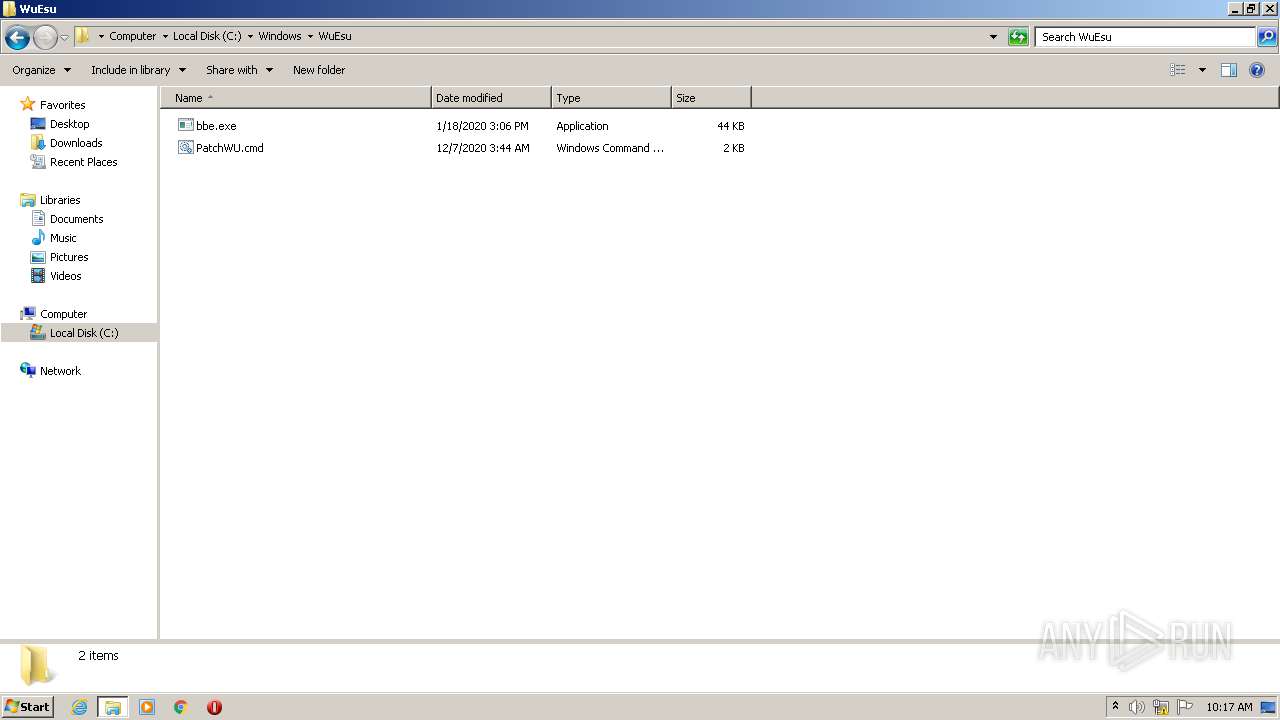
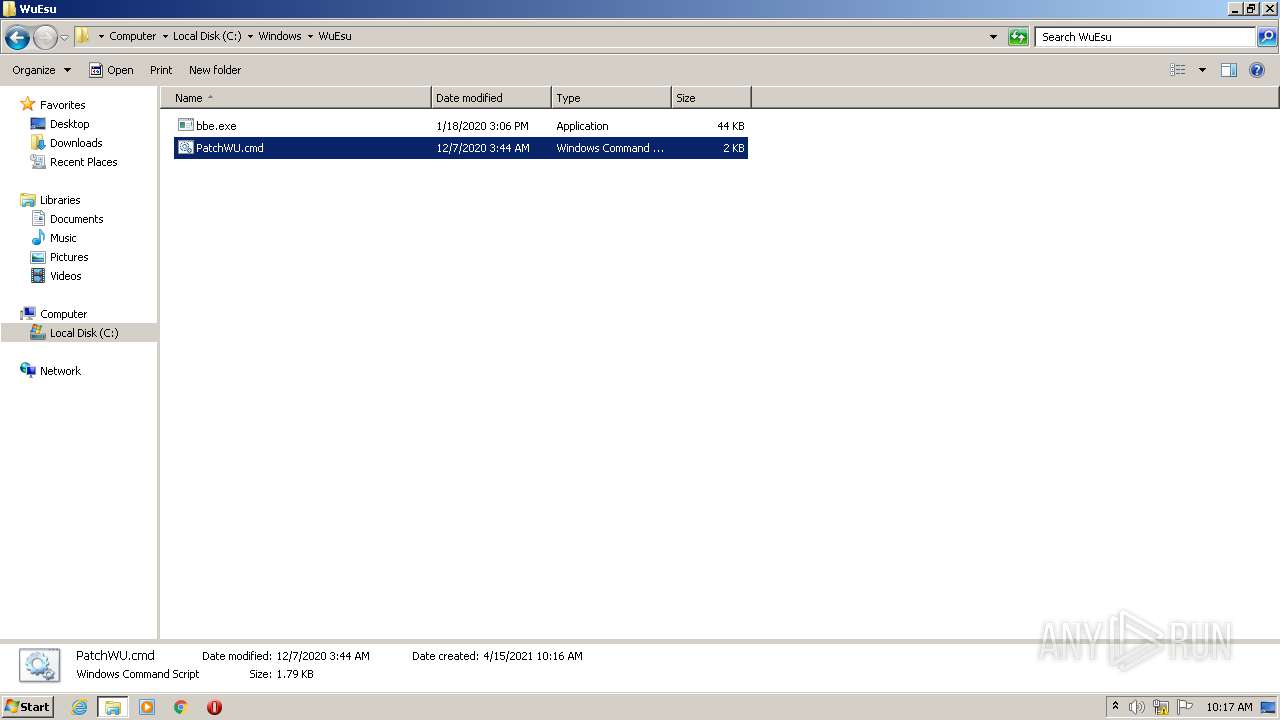
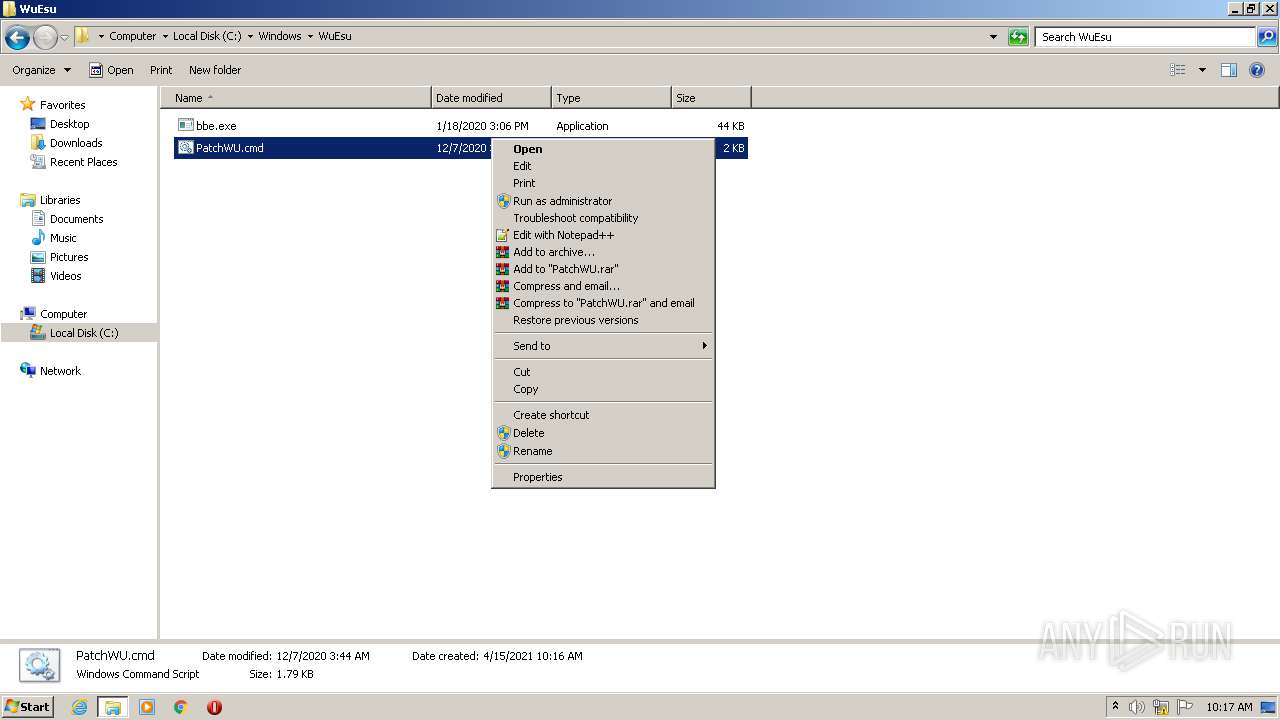
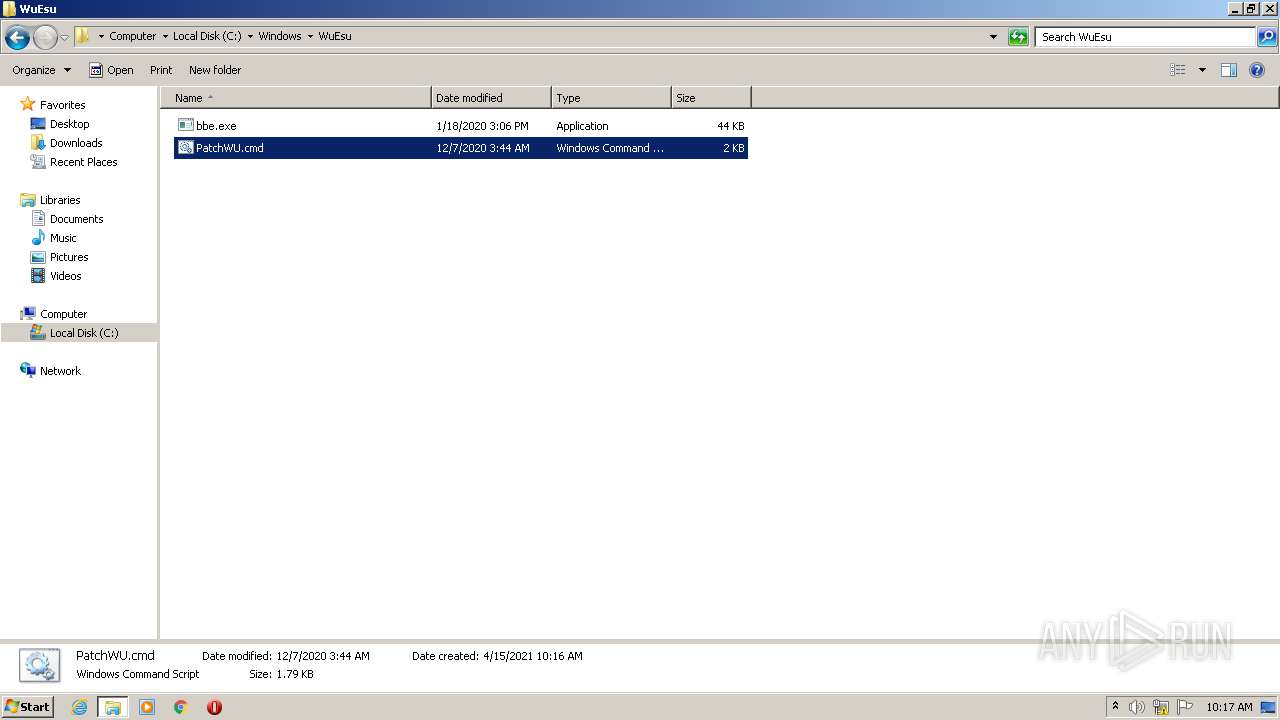
Creates files in the Windows directory
- cmd.exe (PID: 1044)
- svchost.exe (PID: 876)
- bbe.exe (PID: 1548)
- TrustedInstaller.exe (PID: 2088)
- cmd.exe (PID: 1896)
- bbe.exe (PID: 3676)
- cmd.exe (PID: 3652)
- TrustedInstaller.exe (PID: 768)
Executed via Task Scheduler
- cmd.exe (PID: 2384)
- cmd.exe (PID: 3828)
Starts SC.EXE for service management
- cmd.exe (PID: 2384)
- cmd.exe (PID: 1044)
- cmd.exe (PID: 1936)
- cmd.exe (PID: 2280)
- cmd.exe (PID: 2332)
- cmd.exe (PID: 1896)
- cmd.exe (PID: 3828)
- cmd.exe (PID: 3652)
Drops a file that was compiled in debug mode
- bbe.exe (PID: 1548)
- bbe.exe (PID: 3212)
- bbe.exe (PID: 3676)
- Dism.exe (PID: 1148)
Uses WMIC.EXE to obtain a system information
- cmd.exe (PID: 2860)
- cmd.exe (PID: 3564)
- cmd.exe (PID: 1080)
- cmd.exe (PID: 2564)
- cmd.exe (PID: 3020)
- cmd.exe (PID: 3776)
- cmd.exe (PID: 3448)
Creates files in the program directory
- wermgr.exe (PID: 3004)
Removes files from Windows directory
- wermgr.exe (PID: 3004)
- svchost.exe (PID: 876)
- cmd.exe (PID: 2332)
- TrustedInstaller.exe (PID: 2088)
INFO
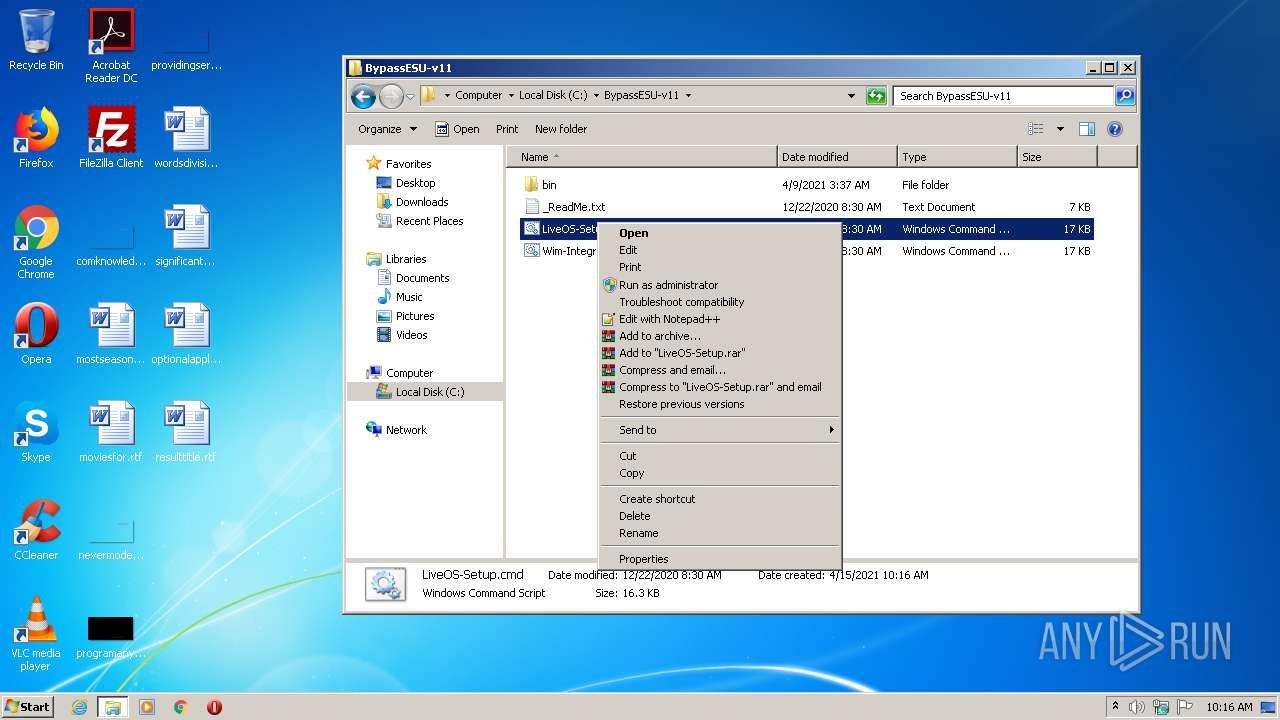
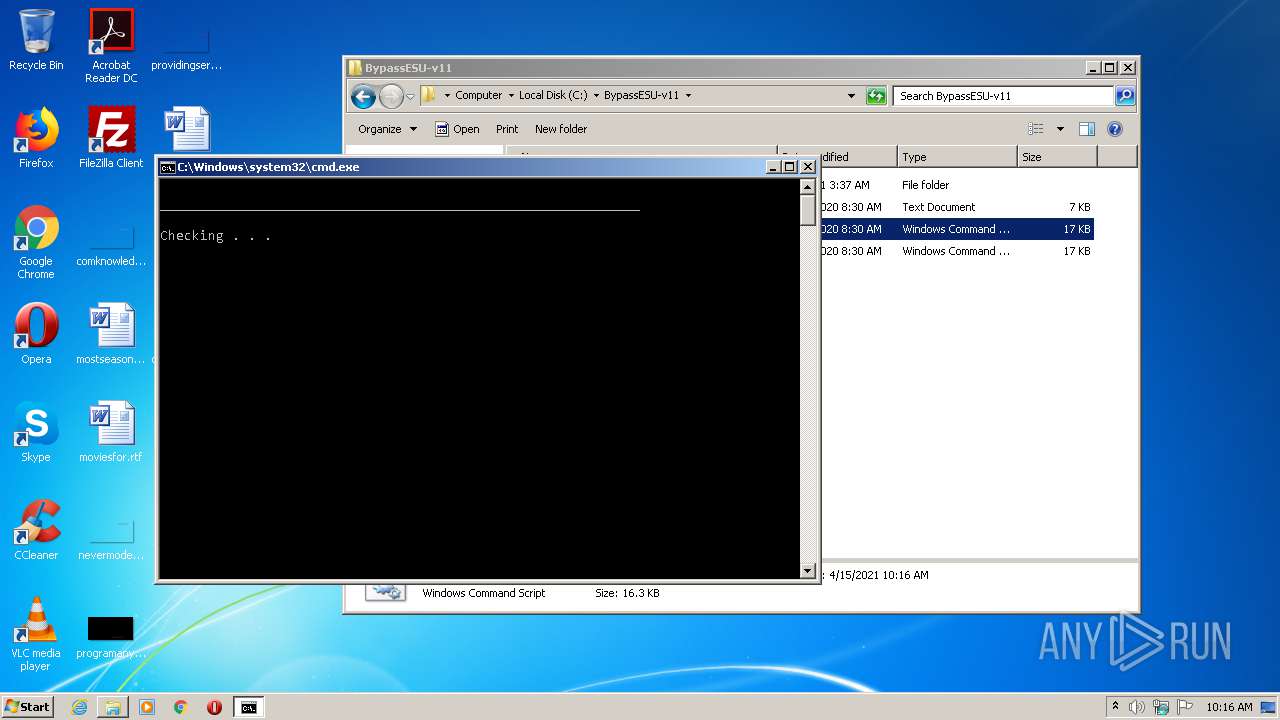
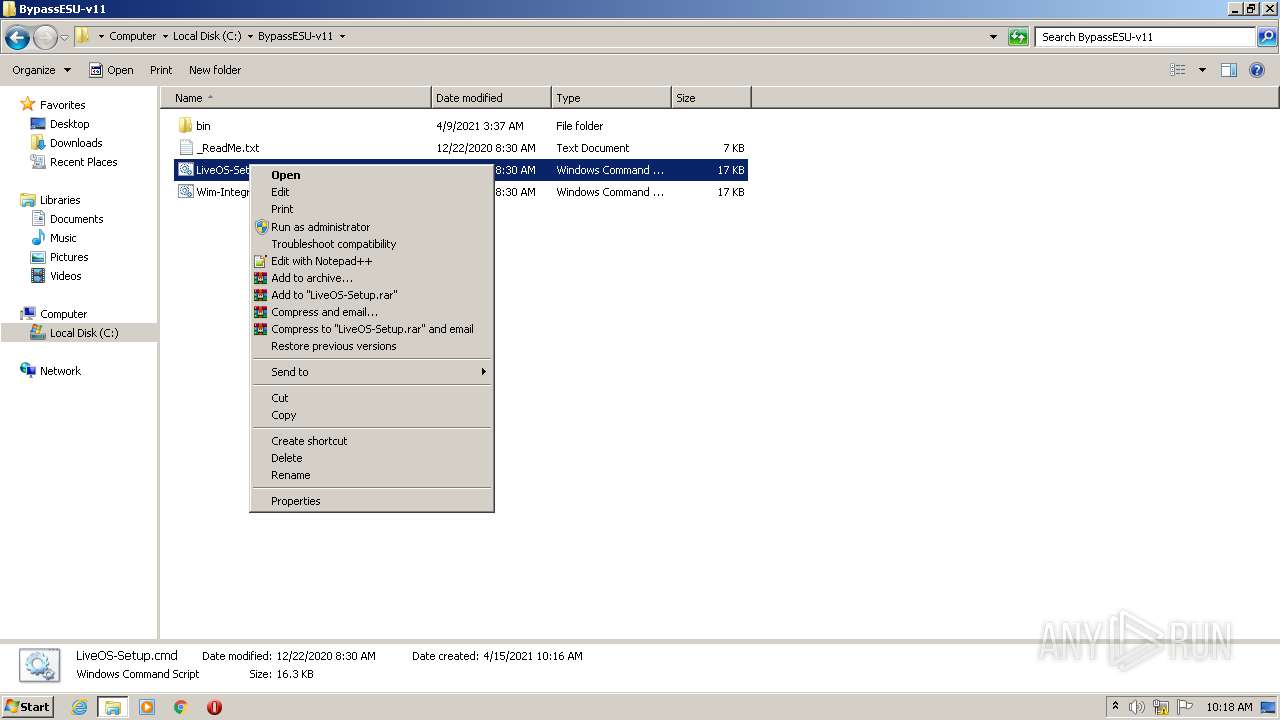
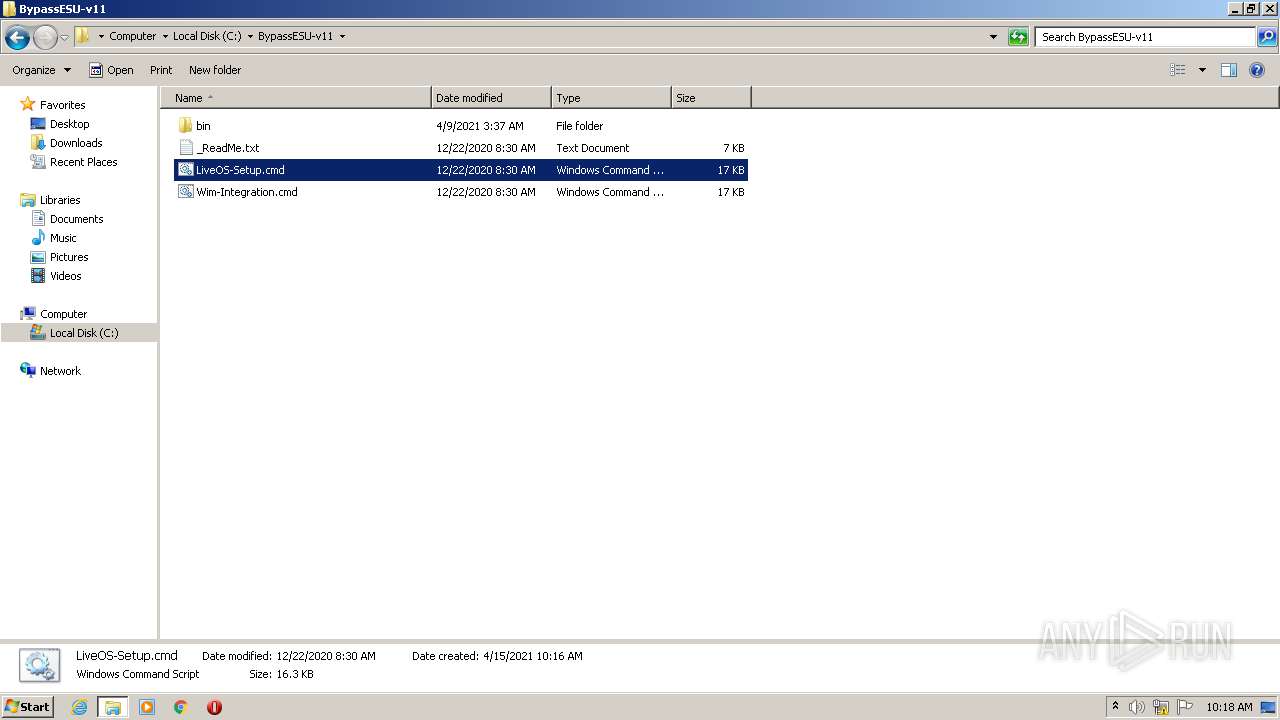
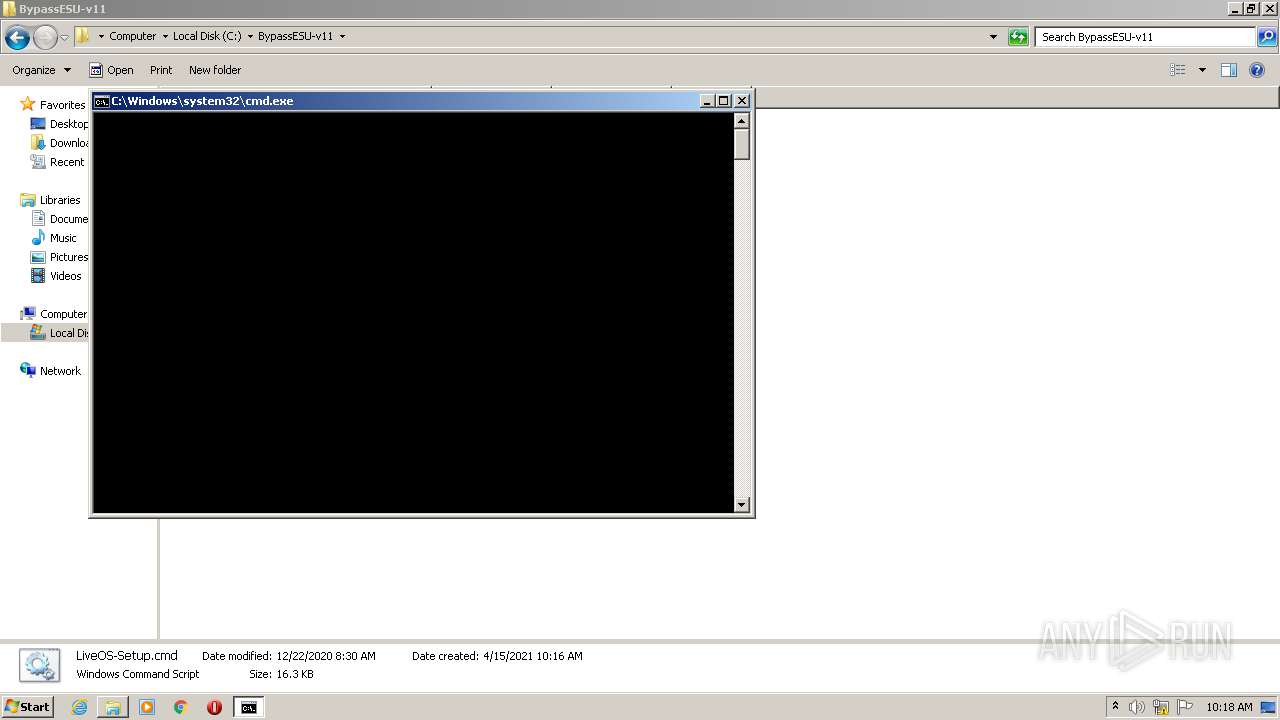
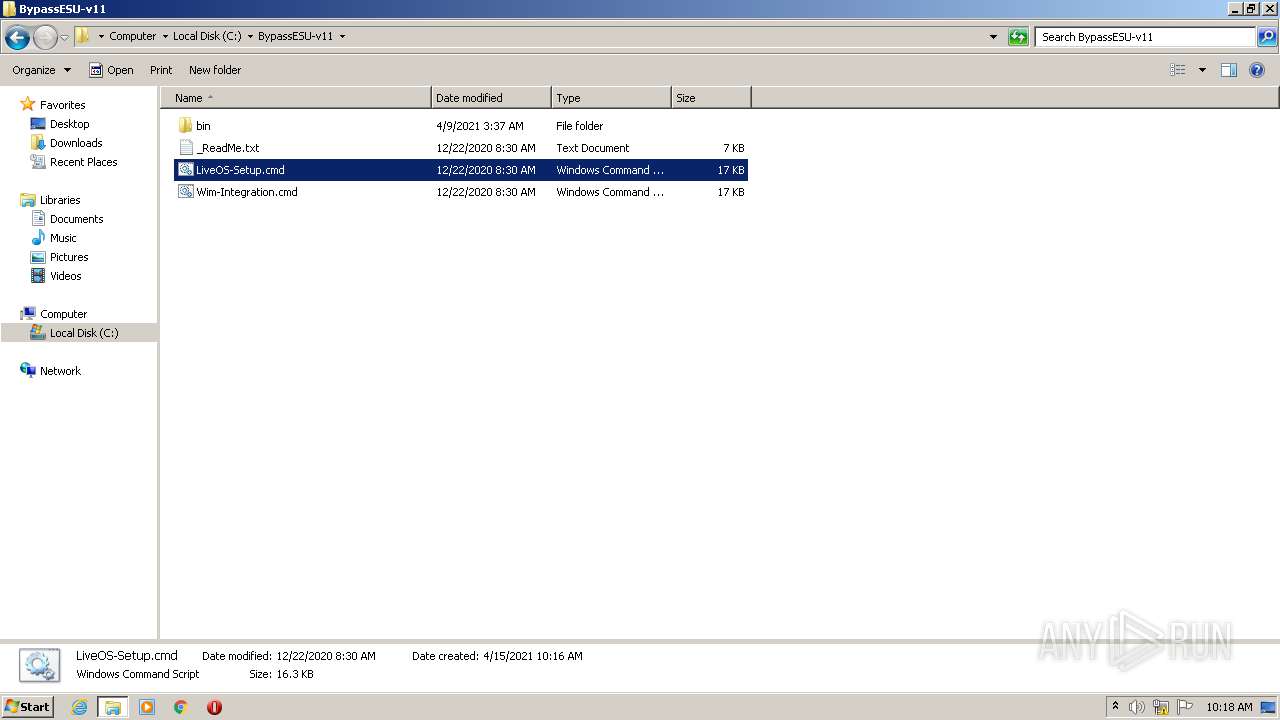
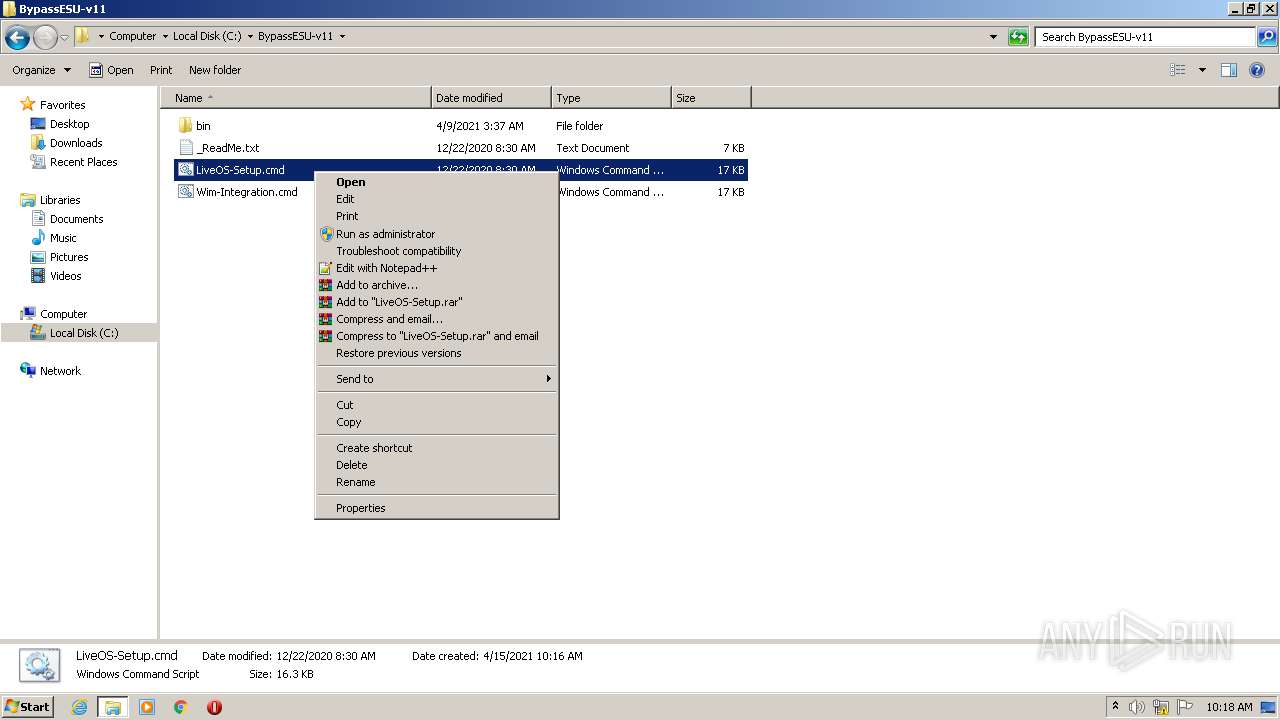
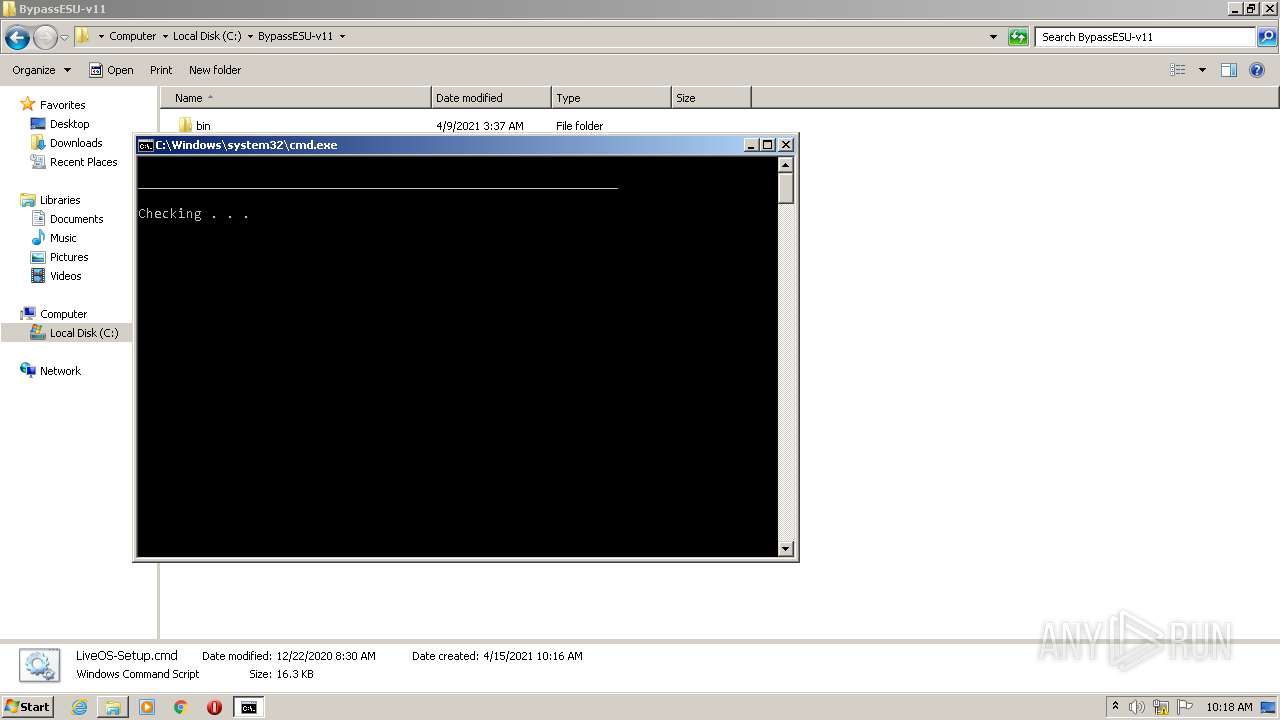
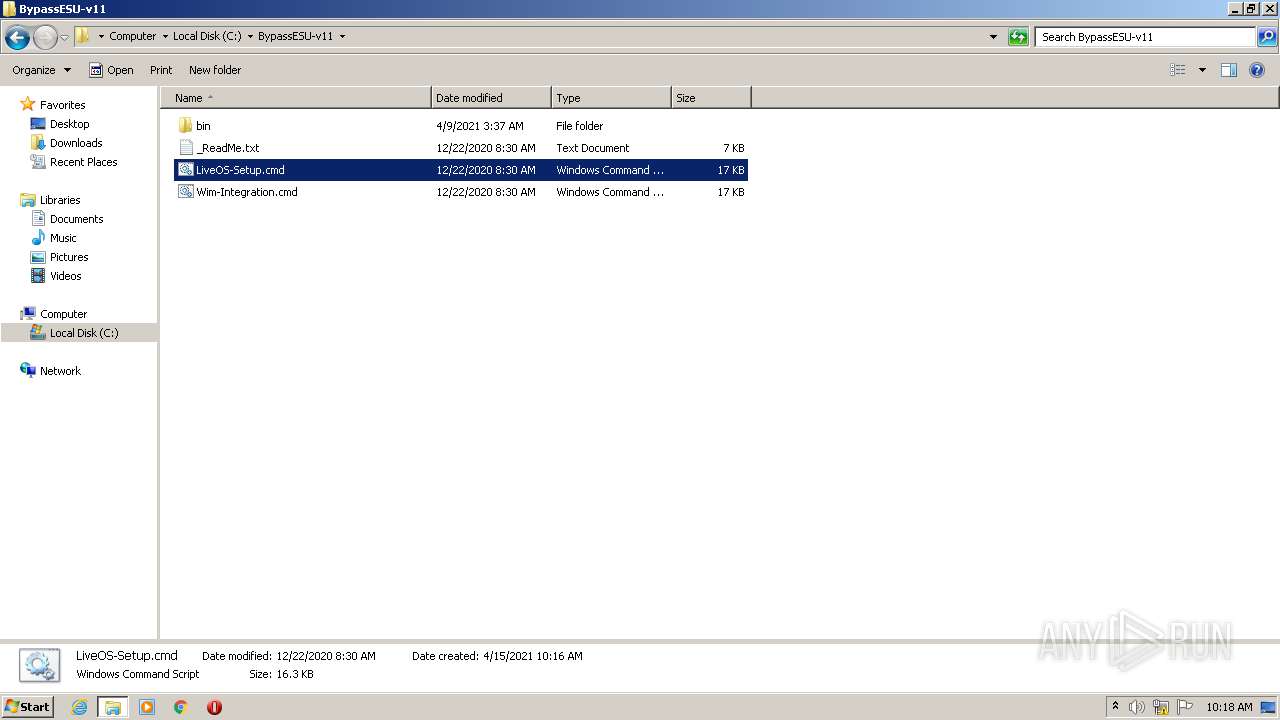
Manual execution by user
- cmd.exe (PID: 2712)
- cmd.exe (PID: 1936)
- cmd.exe (PID: 2280)
- explorer.exe (PID: 3664)
- cmd.exe (PID: 2692)
- cmd.exe (PID: 3228)
- cmd.exe (PID: 1928)
Reads settings of System Certificates
- svchost.exe (PID: 876)
- consent.exe (PID: 2276)
- consent.exe (PID: 3212)
Dropped object may contain Bitcoin addresses
- TrustedInstaller.exe (PID: 2088)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0x1ec40 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 252928 |
| CodeSize: | 201216 |
| LinkerVersion: | 14 |
| PEType: | PE32 |
| TimeStamp: | 2020:12:01 19:00:55+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Dec-2020 18:00:55 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 01-Dec-2020 18:00:55 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000310EA | 0x00031200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.70808 |
.rdata | 0x00033000 | 0x0000A612 | 0x0000A800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.22174 |
.data | 0x0003E000 | 0x00023728 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.70882 |
.didat | 0x00062000 | 0x00000188 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.29825 |
.rsrc | 0x00063000 | 0x0000E000 | 0x0000D600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.81678 |
.reloc | 0x00071000 | 0x00002268 | 0x00002400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.55486 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25329 | 1875 | Latin 1 / Western European | Chinese - PRC | RT_MANIFEST |
2 | 5.10026 | 2216 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
3 | 5.25868 | 3752 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
4 | 5.02609 | 1128 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
5 | 5.18109 | 4264 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
6 | 5.04307 | 9640 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
7 | 5.24197 | 182 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
8 | 5.27357 | 214 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
9 | 5.21038 | 188 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
10 | 5.11103 | 116 | Latin 1 / Western European | Chinese - PRC | RT_STRING |
Imports
KERNEL32.dll |
USER32.dll (delay-loaded) |
gdiplus.dll |
Total processes
269
Monitored processes
168
Malicious processes
22
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 376 | C:\Windows\system32\cmd.exe /c ver | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 444 | wmic OS Get OperatingSystemSKU /value | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
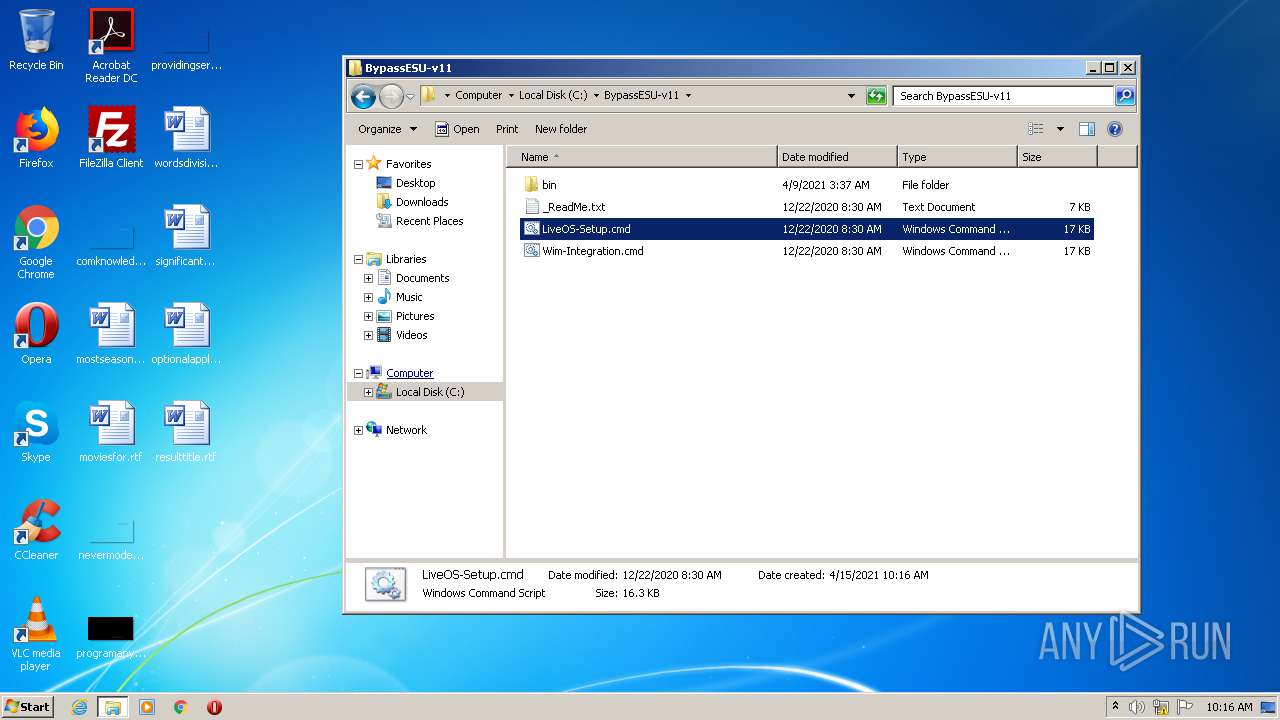
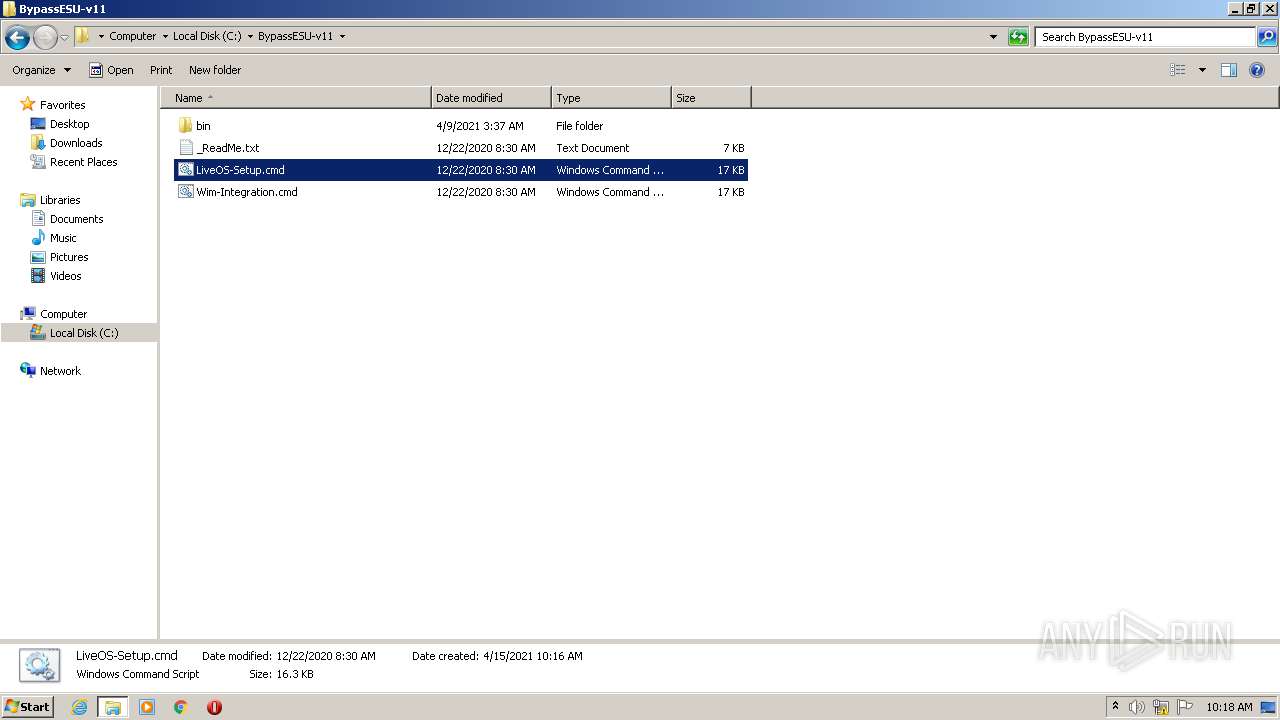
| 444 | superUser32.exe /c cmd.exe /c ""C:\BypassESU-v11\LiveOS-Setup.cmd" -su" | C:\BypassESU-v11\bin\superUser32.exe | — | cmd.exe | |||||||||||
User: admin Company: Awoo~ Integrity Level: HIGH Description: Run any process with TrustedInstaller privileges Exit code: 0 Version: 4.0.0.0 Modules
| |||||||||||||||
| 620 | sc query wuauserv | C:\Windows\System32\sc.exe | cmd.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 664 | net start TrustedInstaller | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 768 | C:\Windows\servicing\TrustedInstaller.exe | C:\Windows\servicing\TrustedInstaller.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Modules Installer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 772 | C:\Windows\System32\svchost.exe -k LocalServiceNetworkRestricted | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 876 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 888 | consent.exe 876 318 01BAF688 | C:\Windows\system32\consent.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Consent UI for administrative applications Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 948 | wmic OS Get OperatingSystemSKU /value | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
44 381
Read events
3 712
Write events
17 617
Delete events
23 052
Modification events
| (PID) Process: | (1940) BypassESU-v11.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1940) BypassESU-v11.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1940) BypassESU-v11.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1940) BypassESU-v11.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1940) BypassESU-v11.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (876) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\ProfileList\S-1-5-21-1302019708-1500728564-335382590-1000 |
| Operation: | write | Name: | RefCount |
Value: 2 | |||
| (PID) Process: | (876) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\ProfileList\S-1-5-21-1302019708-1500728564-335382590-1000 |
| Operation: | write | Name: | RefCount |
Value: 1 | |||
| (PID) Process: | (876) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\ProfileList\S-1-5-21-1302019708-1500728564-335382590-1000 |
| Operation: | write | Name: | RefCount |
Value: 3 | |||
| (PID) Process: | (2552) reg.exe | Key: | HKEY_USERS\.DEFAULT\Console |
| Operation: | write | Name: | FontSize |
Value: 1048576 | |||
| (PID) Process: | (3244) reg.exe | Key: | HKEY_USERS\.DEFAULT\Console |
| Operation: | write | Name: | FontWeight |
Value: 400 | |||
Executable files
48
Suspicious files
6
Text files
31
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
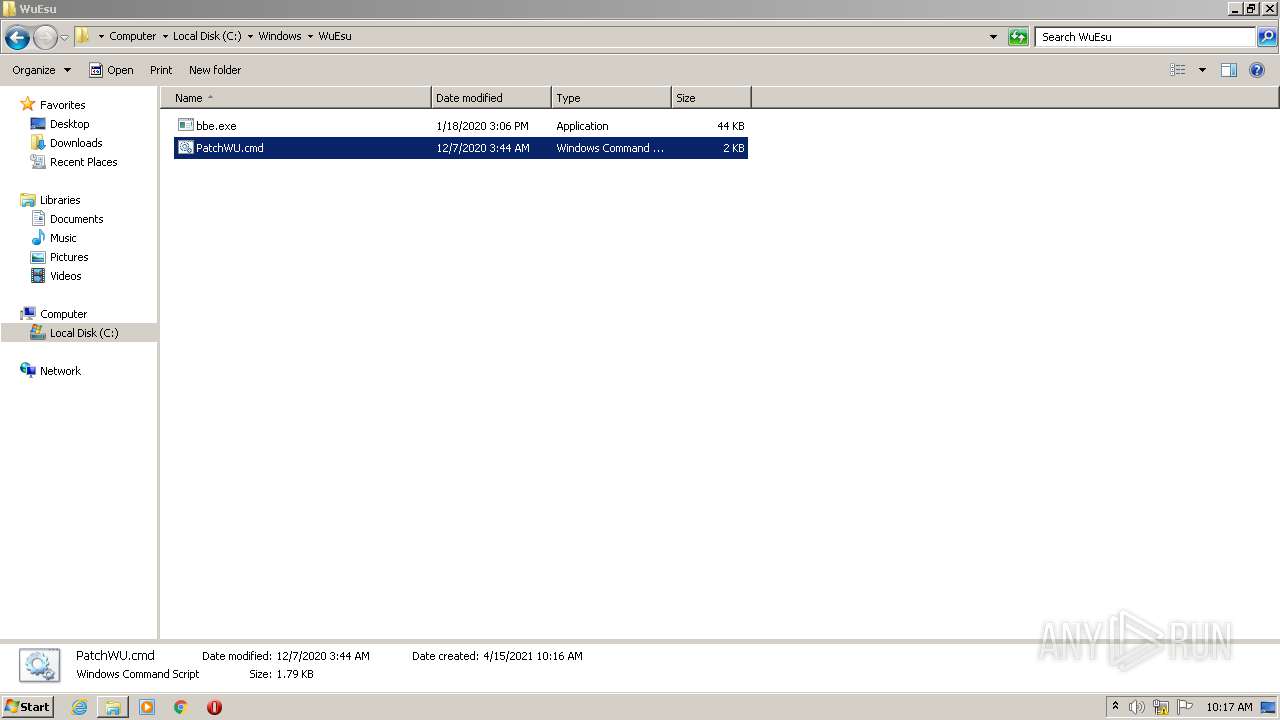
| 3404 | BypassESU-v11.exe | C:\BypassESU-v11\bin\PatchWU.txt | text | |
MD5:A0ADC3B30D674E2E966E9B296AE02136 | SHA256:00042135242BF9443A8CD5084DEAF26EC5B0F94BB639CA5FD14C15E138D8F67B | |||
| 3404 | BypassESU-v11.exe | C:\BypassESU-v11\bin\PatchWU.reg | text | |
MD5:681B8CFAEA42776751CC231FE4242DED | SHA256:4885CEB1875DB33A083F06EE436CC48D8CB1BCA4D46E58785A7059AE55F0A70D | |||
| 3404 | BypassESU-v11.exe | C:\BypassESU-v11\bin\x64\ActionCenter.dll.3.Manifest | xml | |
MD5:— | SHA256:— | |||
| 3404 | BypassESU-v11.exe | C:\BypassESU-v11\bin\x64\msiexec.exe.manifest | xml | |
MD5:— | SHA256:— | |||
| 3404 | BypassESU-v11.exe | C:\BypassESU-v11\bin\wimfile.cmd | text | |
MD5:— | SHA256:— | |||
| 3404 | BypassESU-v11.exe | C:\BypassESU-v11\bin\x64\pnidui.dll.3.Manifest | xml | |
MD5:— | SHA256:— | |||
| 3404 | BypassESU-v11.exe | C:\BypassESU-v11\bin\x64\perfmon.exe.3.Manifest | xml | |
MD5:— | SHA256:— | |||
| 3404 | BypassESU-v11.exe | C:\BypassESU-v11\bin\x64\msislc.dll | executable | |
MD5:— | SHA256:— | |||
| 3404 | BypassESU-v11.exe | C:\BypassESU-v11\bin\x64\timedate.cpl.3.Manifest | xml | |
MD5:— | SHA256:— | |||
| 3404 | BypassESU-v11.exe | C:\BypassESU-v11\bin\amd64_microsoft-windows-s..edsecurityupdatesai_31bf3856ad364e35_6.1.7603.25000_none_caceb5163345f228.manifest | xml | |
MD5:246592AD66B1996B1F6E829F90051193 | SHA256:45D0AE442FD92CE32EE1DDC38EA3B875EAD9A53D6A17155A10FA9D9E16BEDEB2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
11
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 200 | 205.185.216.10:80 | http://download.windowsupdate.com/v9/windowsupdate/redir/muv4wuredir.cab?2104150917 | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.70.224.146:443 | www.update.microsoft.com | Microsoft Corporation | US | malicious |
— | — | 192.168.100.154:137 | — | — | — | malicious |
— | — | 205.185.216.10:80 | download.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
— | — | 192.168.100.154:64549 | — | — | — | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.windowsupdate.com |
| whitelisted |
www.update.microsoft.com |
| whitelisted |