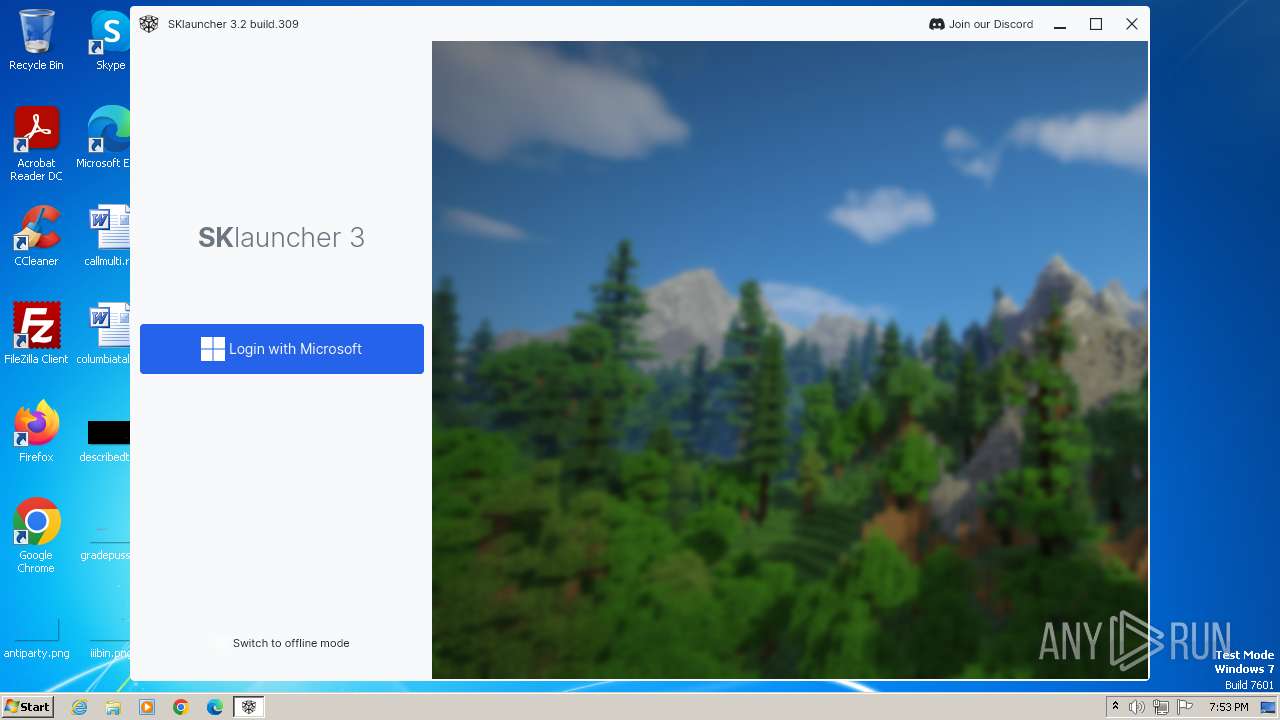
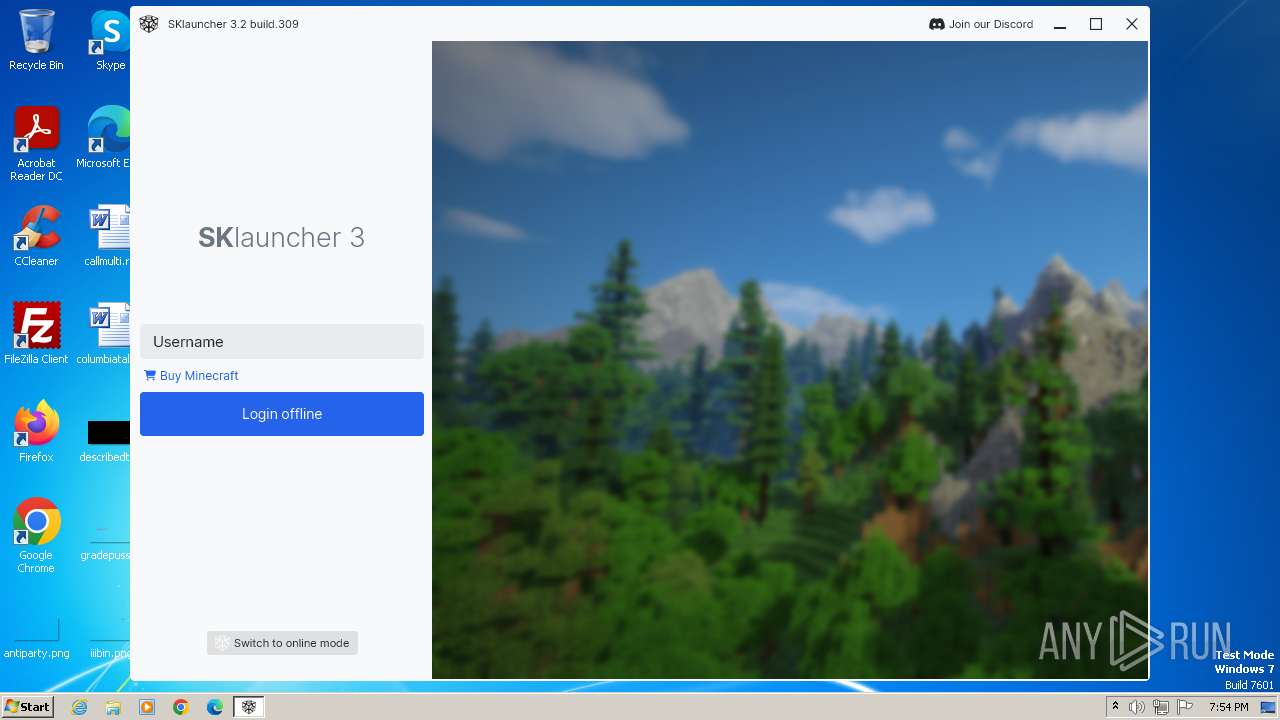
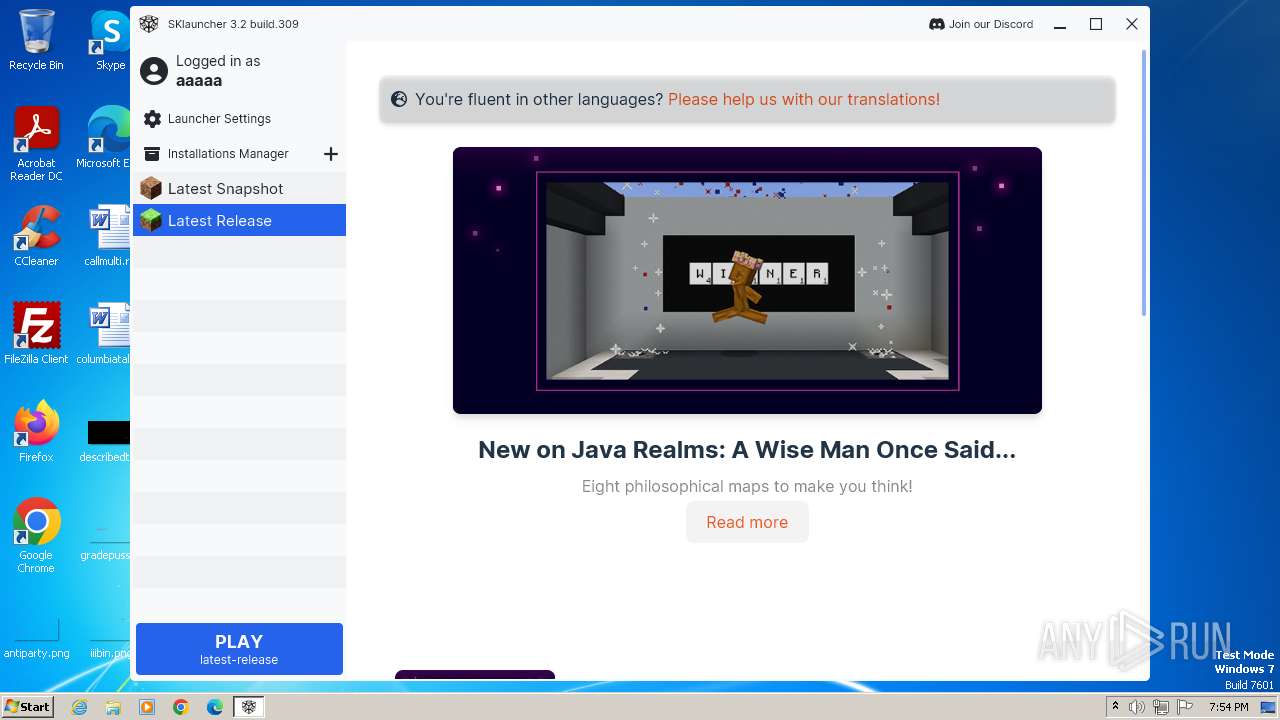
| File name: | SKlauncher-3.2.1.jar |
| Full analysis: | https://app.any.run/tasks/c6f255bb-61fb-4b37-8966-84c301c24006 |
| Verdict: | Malicious activity |
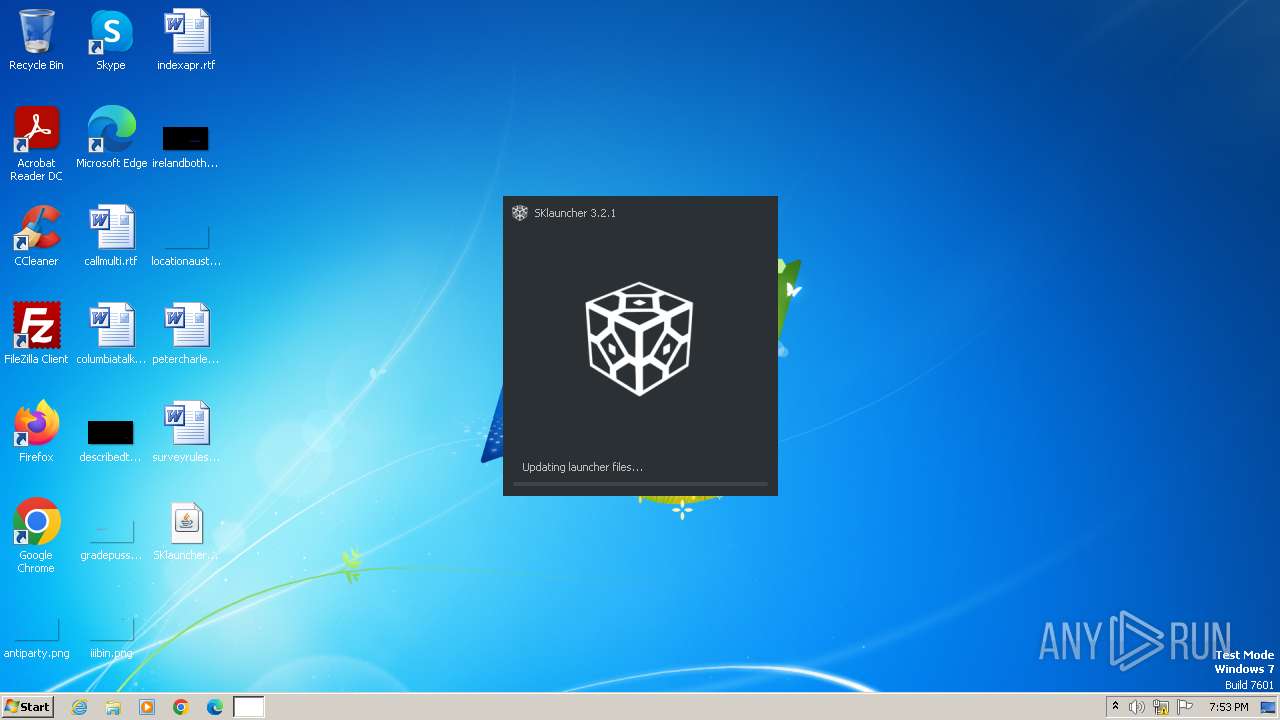
| Analysis date: | December 01, 2023, 19:53:11 |
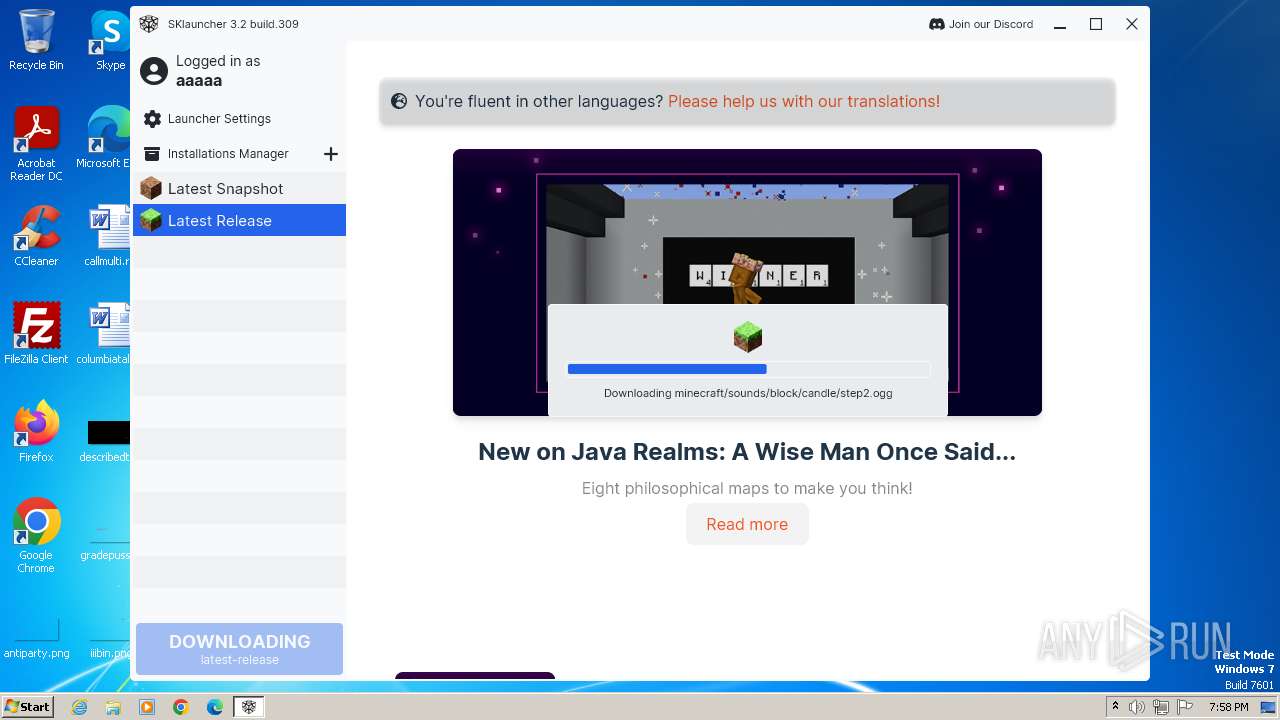
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | B1EC730355259BE5113D53B644F48AB1 |
| SHA1: | 63B1C55F472091F02D07C920C24A4ACBA1E66F98 |
| SHA256: | AD9C3A86C143AC75CC56E25C076F9F19EC60E9B48EC39104F2338029E2D43843 |
| SSDEEP: | 49152:P2FnjitiHj27XmnGq3+EM3iNvr0H7XcvL5zz6m8rnFCMHxjWSidSNrwHfz26JOdi:PMj7Hj2DmT3dBRrI7XqL5zzlkLidSOrf |
MALICIOUS
Drops the executable file immediately after the start
- javaw.exe (PID: 564)
SUSPICIOUS
Process drops legitimate windows executable
- javaw.exe (PID: 564)
The process creates files with name similar to system file names
- javaw.exe (PID: 564)
The process drops C-runtime libraries
- javaw.exe (PID: 564)
INFO
Checks supported languages
- javaw.exe (PID: 564)
- wmpnscfg.exe (PID: 3892)
Reads the computer name
- javaw.exe (PID: 564)
- wmpnscfg.exe (PID: 3892)
Creates files or folders in the user directory
- javaw.exe (PID: 564)
Create files in a temporary directory
- javaw.exe (PID: 564)
Manual execution by a user
- wmpnscfg.exe (PID: 3892)
Reads the machine GUID from the registry
- javaw.exe (PID: 564)
Creates files in the program directory
- javaw.exe (PID: 564)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .jar | | | Java Archive (78.3) |
|---|---|---|
| .zip | | | ZIP compressed archive (21.6) |
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | 0x0800 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2023:11:30 17:58:46 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | 2 |
| ZipUncompressedSize: | - |
| ZipFileName: | META-INF/ |
Total processes
42
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 564 | "C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe" -jar "C:\Users\admin\Desktop\SKlauncher-3.2.1.jar" | C:\Program Files\Java\jre1.8.0_271\bin\javaw.exe | explorer.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
| 2820 | reg query "HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Themes\Personalize" /v AppsUseLightTheme | C:\Windows\System32\reg.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3816 | C:\Windows\system32\icacls.exe C:\ProgramData\Oracle\Java\.oracle_jre_usage /grant "everyone":(OI)(CI)M | C:\Windows\System32\icacls.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3892 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
660
Read events
658
Write events
2
Delete events
0
Modification events
| (PID) Process: | (564) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: Explorer.EXE | |||
| (PID) Process: | (564) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: javaw.exe | |||
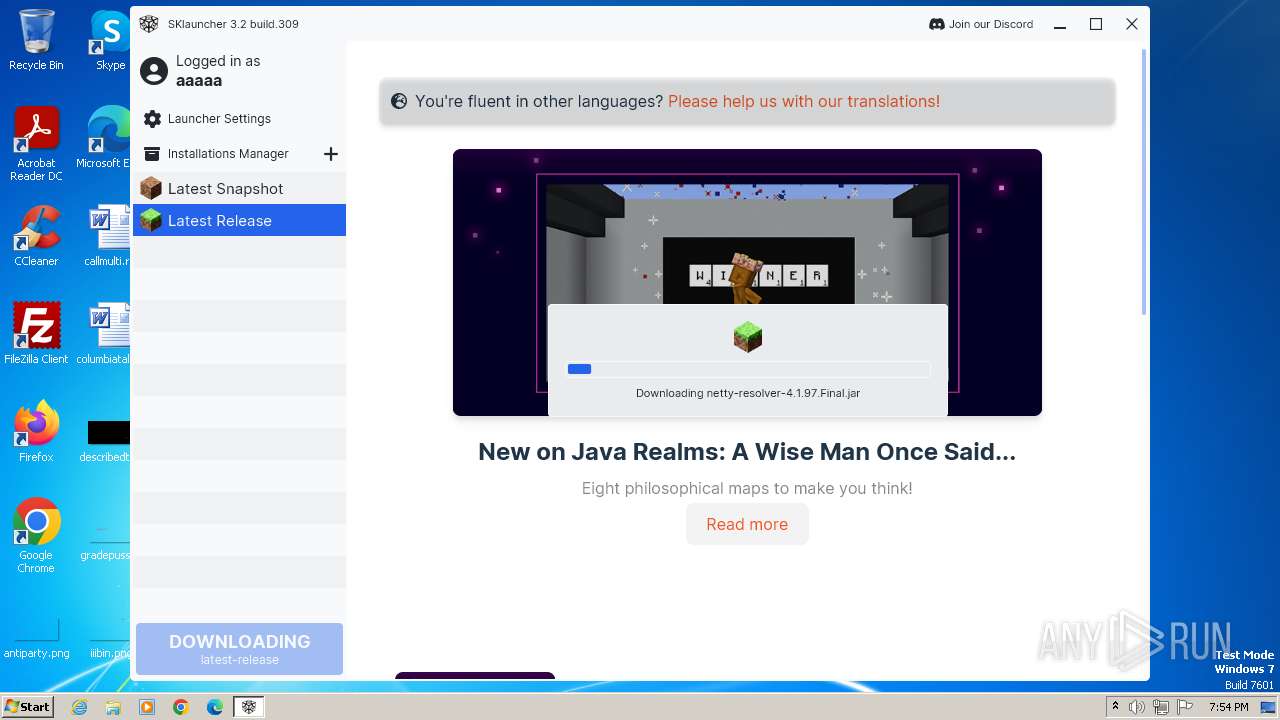
Executable files
166
Suspicious files
2 206
Text files
289
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 564 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\sklauncher\sklauncher-fx.jar.xz | — | |
MD5:— | SHA256:— | |||
| 564 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\sklauncher\sklauncher_data.bin | text | |
MD5:0214E6B68CE68F00D2F3FA46403431F2 | SHA256:F33C2314C1345AE8D9F53AC25B0439A62002AD3BD69BE11FDAF943722BBDE906 | |||
| 564 | javaw.exe | C:\Users\admin\AppData\Local\Temp\+JXF902244806814278238.tmp | binary | |
MD5:6531CC951551AB62277D8928F4294264 | SHA256:1CBE9C8CD83A2B04A0B8BD7B0FF1372A56E0935FEEA33AA132D91C2899291542 | |||
| 564 | javaw.exe | C:\ProgramData\Oracle\Java\.oracle_jre_usage\17dfc292991c8061.timestamp | text | |
MD5:25FAA53BF628C2C762F374D00F88BF01 | SHA256:D5475600EE77FD654B75DD13D2BAB350DEA1B69005D205B5E9CEA28FCF0D1AB6 | |||
| 564 | javaw.exe | C:\Users\admin\AppData\Local\Temp\imageio1765878294358240178.tmp | image | |
MD5:4BC22D05B225A34A3DDB4F17D2469B77 | SHA256:FACE76C9C4FAD9476A1D80483D41772C805808A1383012B1C22065E30D32EDE6 | |||
| 564 | javaw.exe | C:\Users\admin\AppData\Local\Temp\+JXF7427131355557099343.tmp | binary | |
MD5:F2684BCE39D701EF54F3C9A717508162 | SHA256:53A941C664BBA47E36A20FE71E89EAE3CC92C47B5ACB85D7436C39758DDAF530 | |||
| 564 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\sklauncher-fx.jar | compressed | |
MD5:2D9AB08F2A28DFB4B3EC38D349FF5BE3 | SHA256:8A139C972EFC331C2FCC8939C6DC0B2FDBB503EC6278673F3A410B6F257EA8DC | |||
| 564 | javaw.exe | C:\Users\admin\AppData\Roaming\.minecraft\sklauncher\sklauncher.vmoptions | text | |
MD5:616097195B6350DD5271AA6F30CC167A | SHA256:C0AD6503240446061D7DA9181B625F149574430135E0D6AB32FB61F176C831FE | |||
| 564 | javaw.exe | C:\Users\admin\AppData\Local\Temp\+JXF9158073456818652631.tmp | binary | |
MD5:52355593E805F6C172BFDC156A39A031 | SHA256:529BE850E06F62F8904F22BDA77E45BDE4834498FDBEC4FF4201FA3177447A3A | |||
| 564 | javaw.exe | C:\Users\admin\AppData\Local\Temp\+JXF1390947591790413747.tmp | binary | |
MD5:250894A9A597C4362471DCB111934943 | SHA256:E6C172FD8A2F957414A7A63EC8DEB7F2AA239182394CFA5EE2EA6927C6194389 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
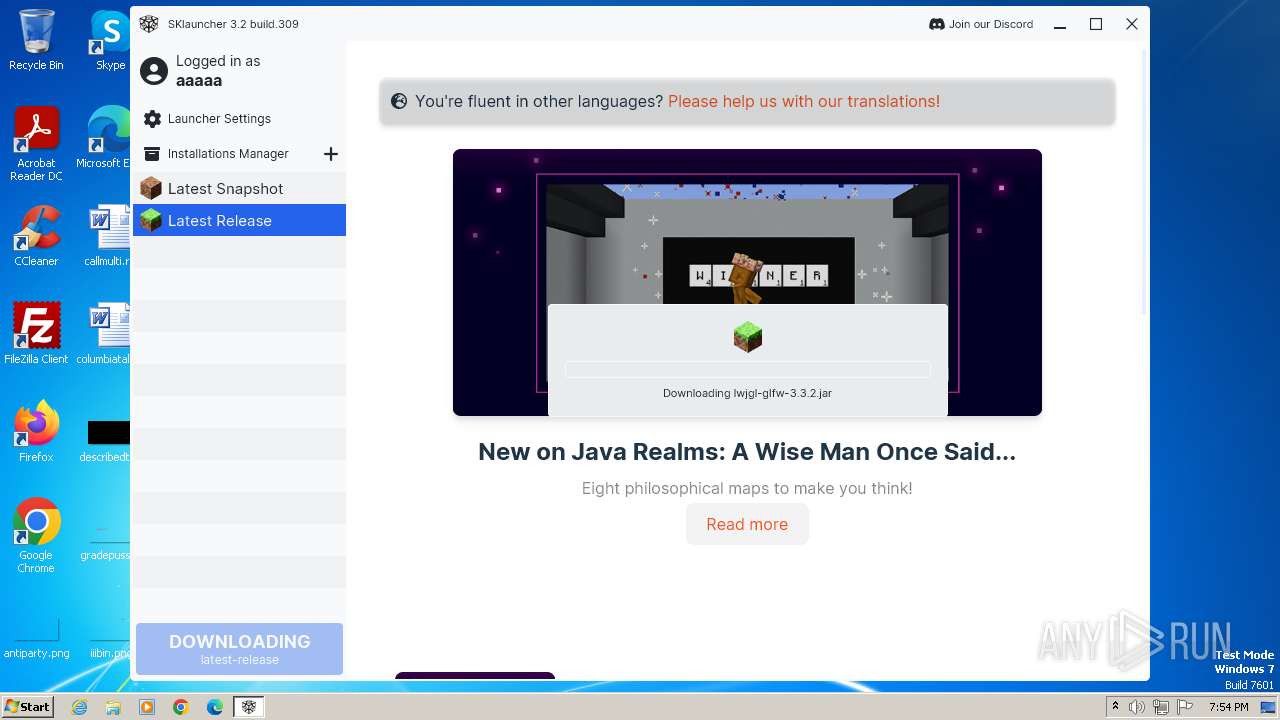
HTTP(S) requests
0
TCP/UDP connections
100
DNS requests
26
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
564 | javaw.exe | 188.114.96.3:443 | files.skmedix.pl | CLOUDFLARENET | NL | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
564 | javaw.exe | 13.107.246.45:443 | launchermeta.mojang.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
564 | javaw.exe | 13.107.213.45:443 | launchermeta.mojang.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
564 | javaw.exe | 188.114.97.3:443 | files.skmedix.pl | CLOUDFLARENET | NL | unknown |
564 | javaw.exe | 185.199.111.153:443 | meta.skmedix.pl | FASTLY | US | shared |
564 | javaw.exe | 142.250.186.72:443 | www.googletagmanager.com | GOOGLE | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
files.skmedix.pl |
| unknown |
launchermeta.mojang.com |
| whitelisted |
piston-meta.mojang.com |
| unknown |
resources.download.minecraft.net |
| shared |
libraries.minecraft.net |
| shared |
sessionserver.skmedix.pl |
| unknown |
textures.skmedix.pl |
| unknown |
beta.skmedix.pl |
| unknown |
meta.skmedix.pl |
| unknown |
rsms.me |
| whitelisted |