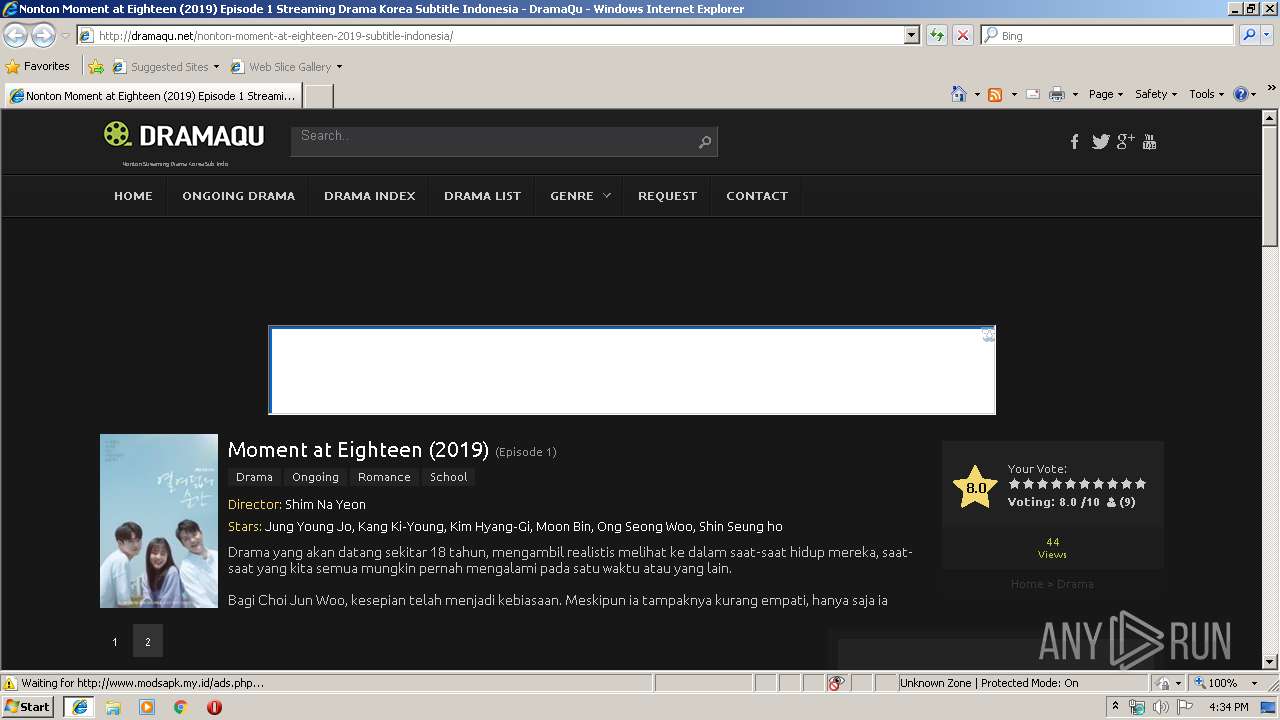
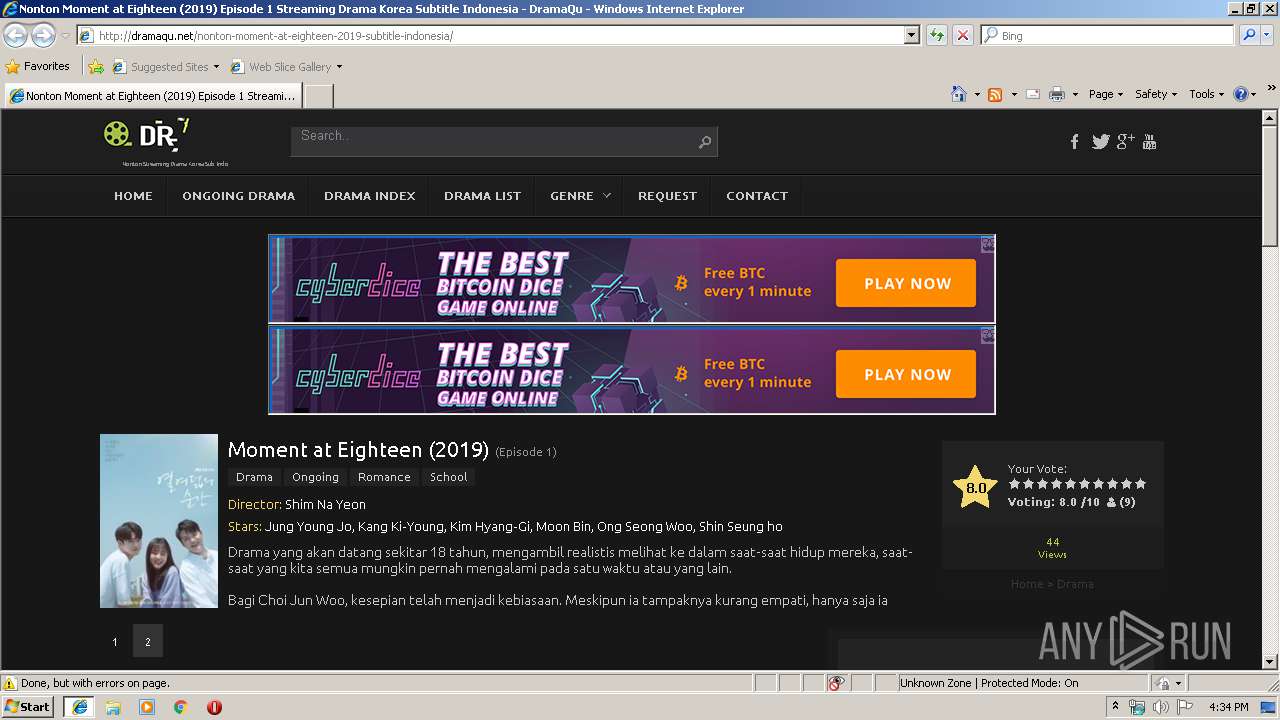
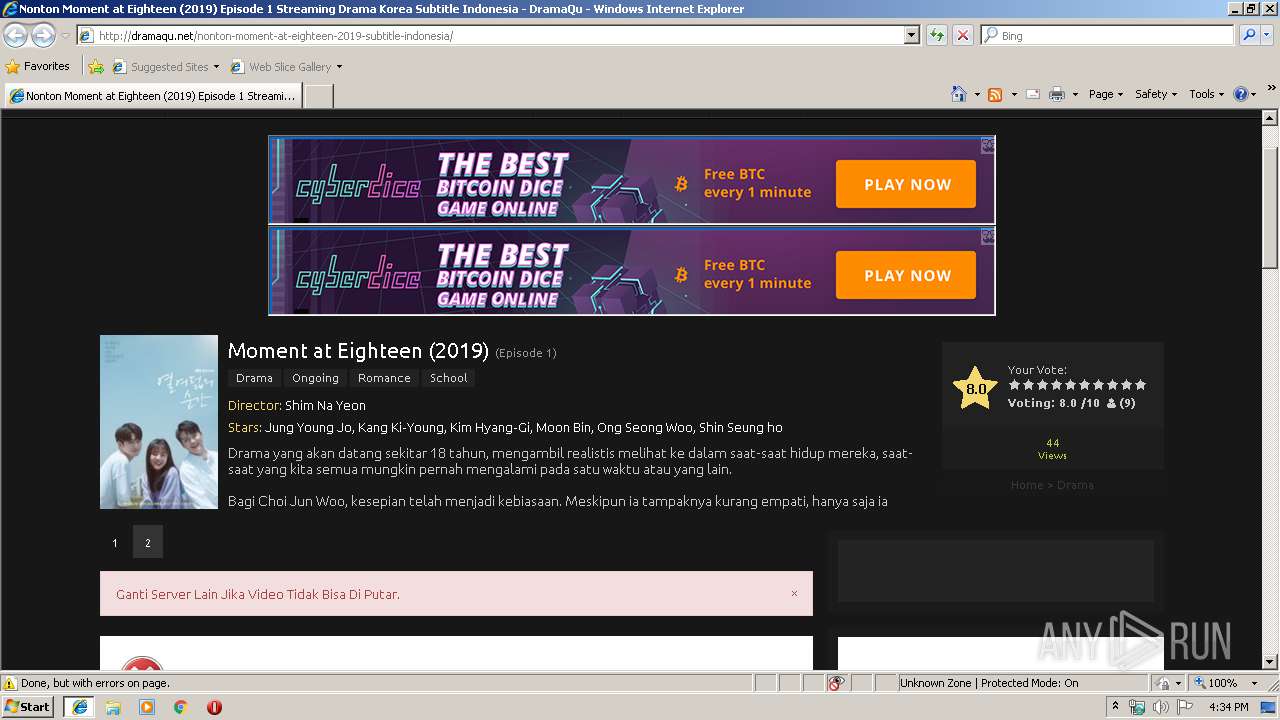
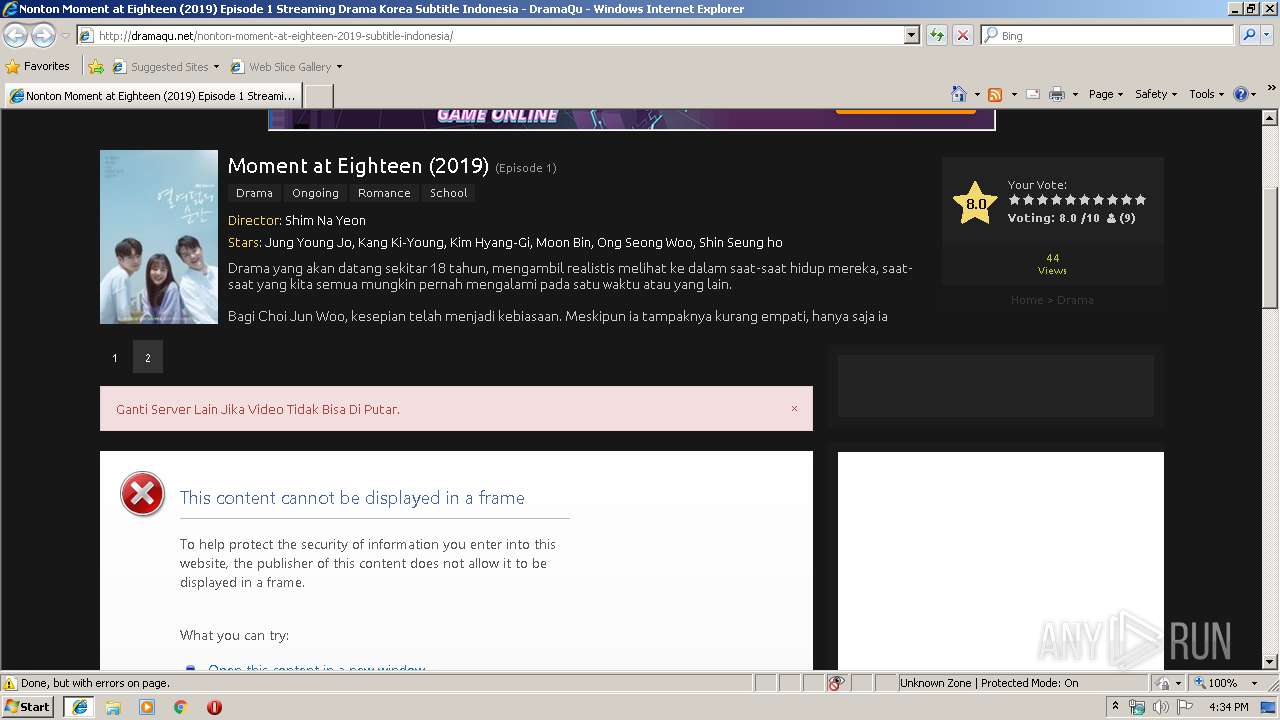
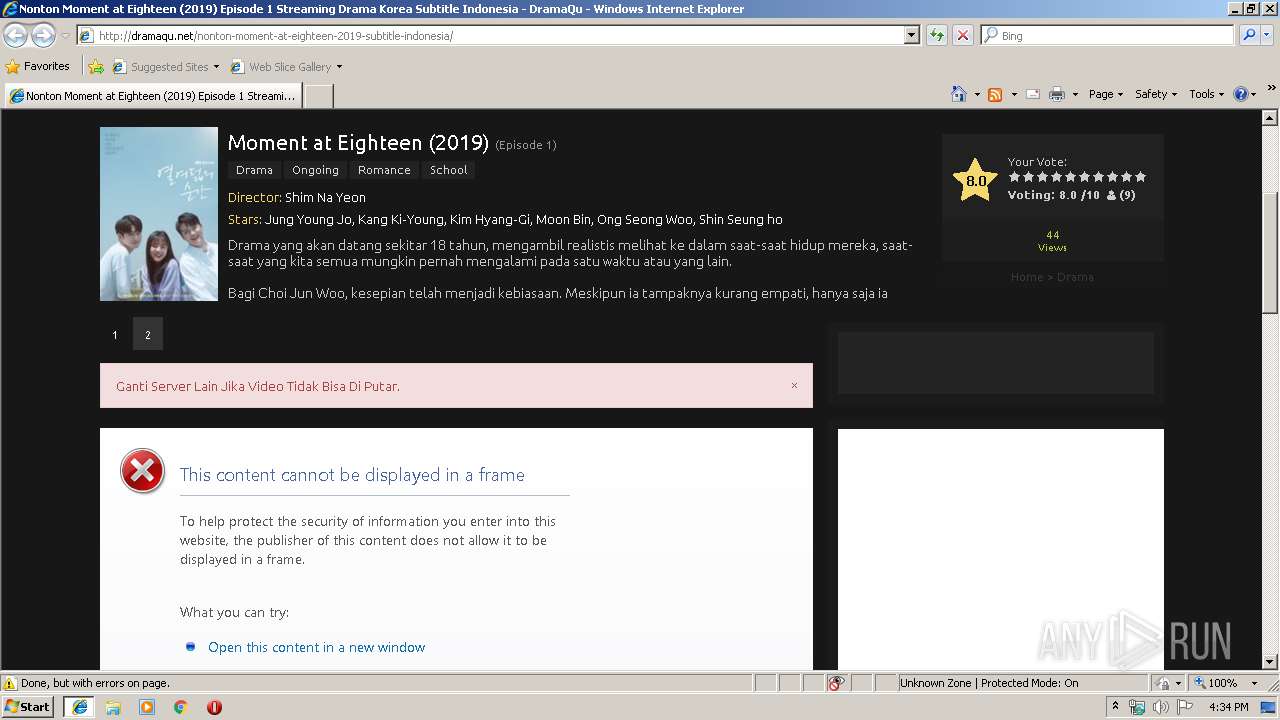
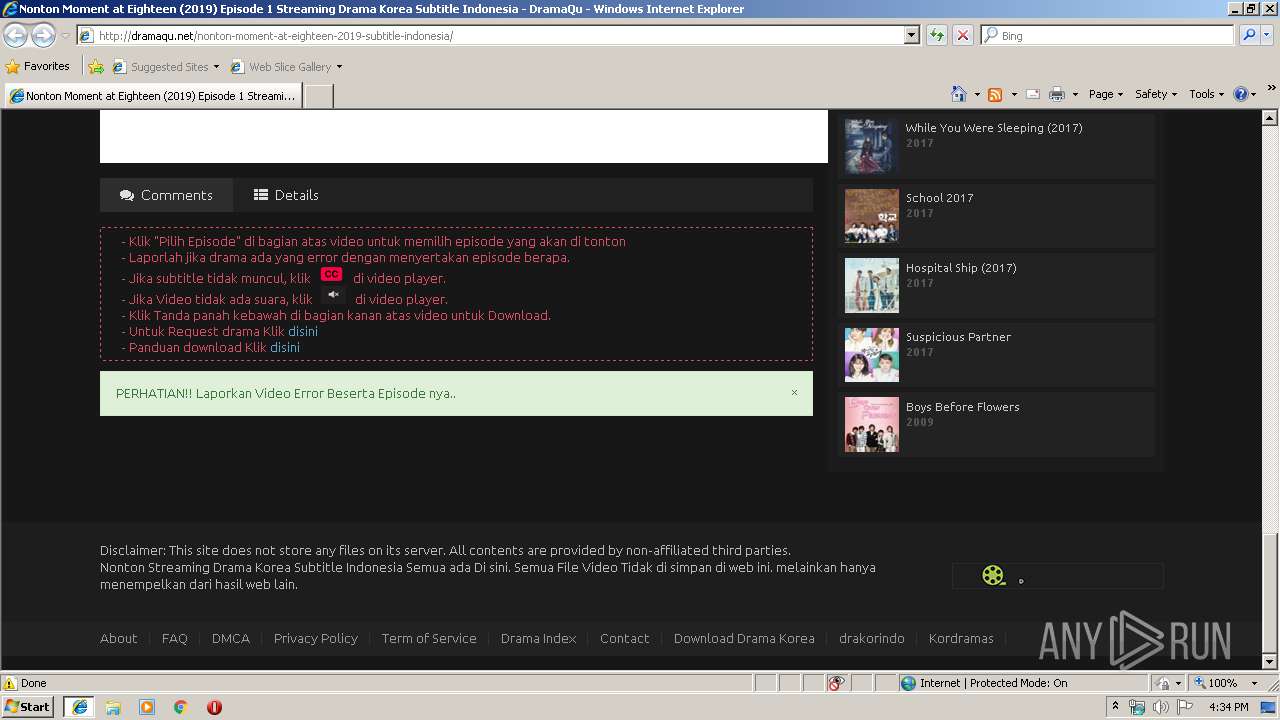
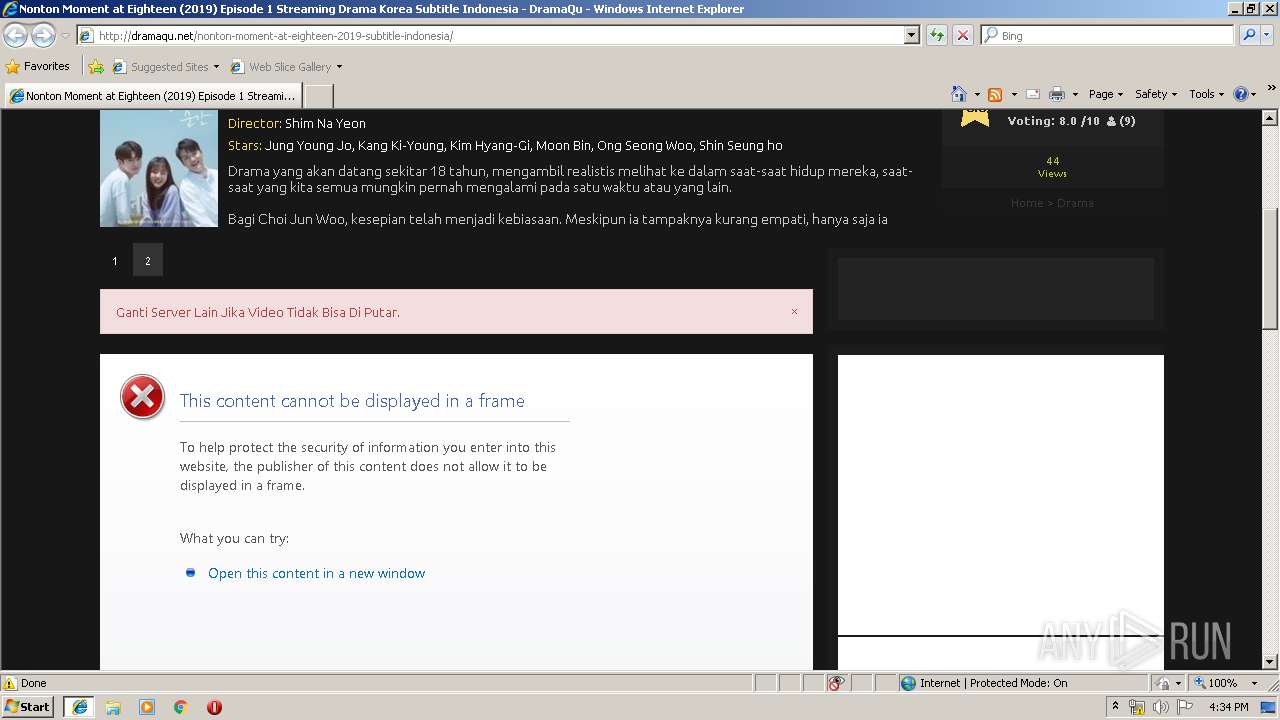
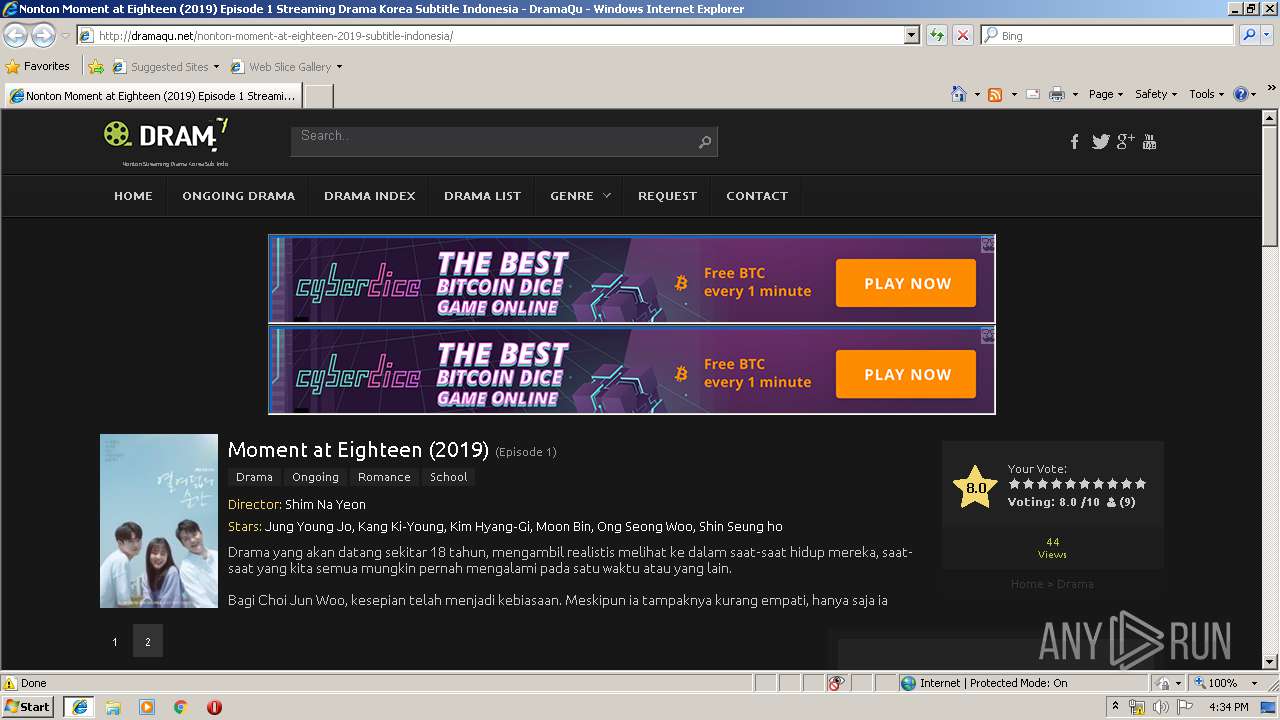
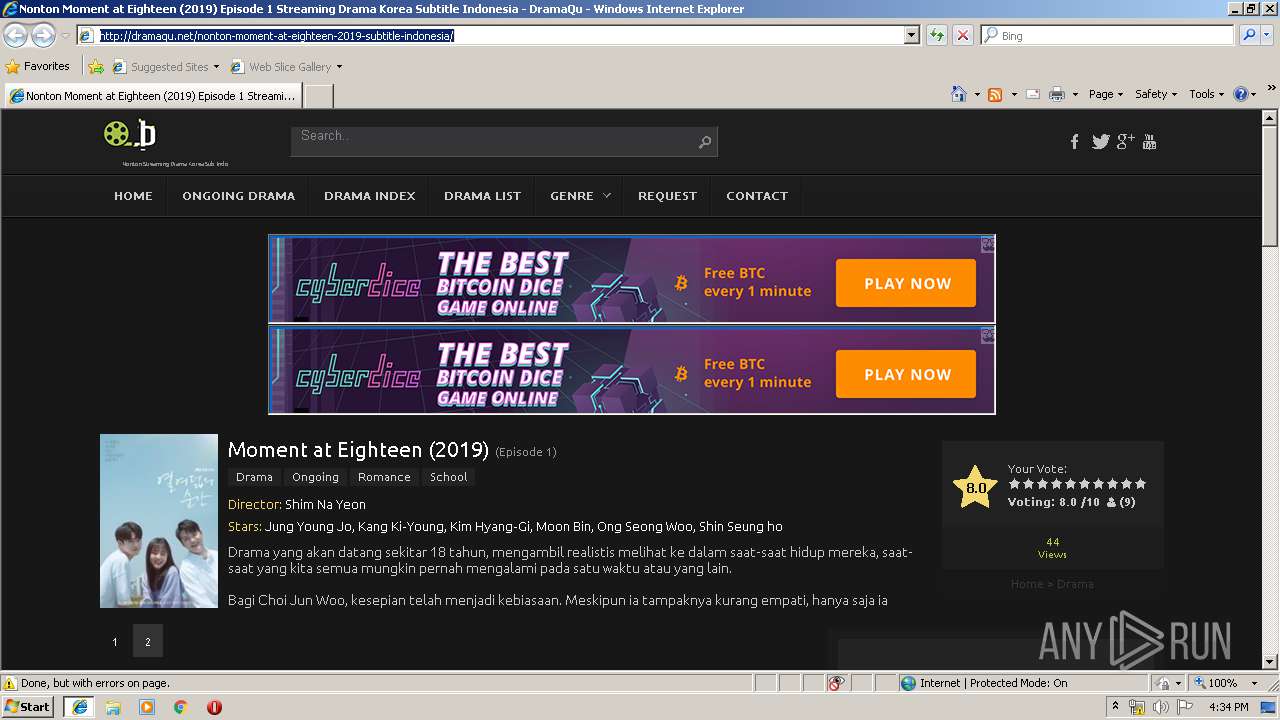
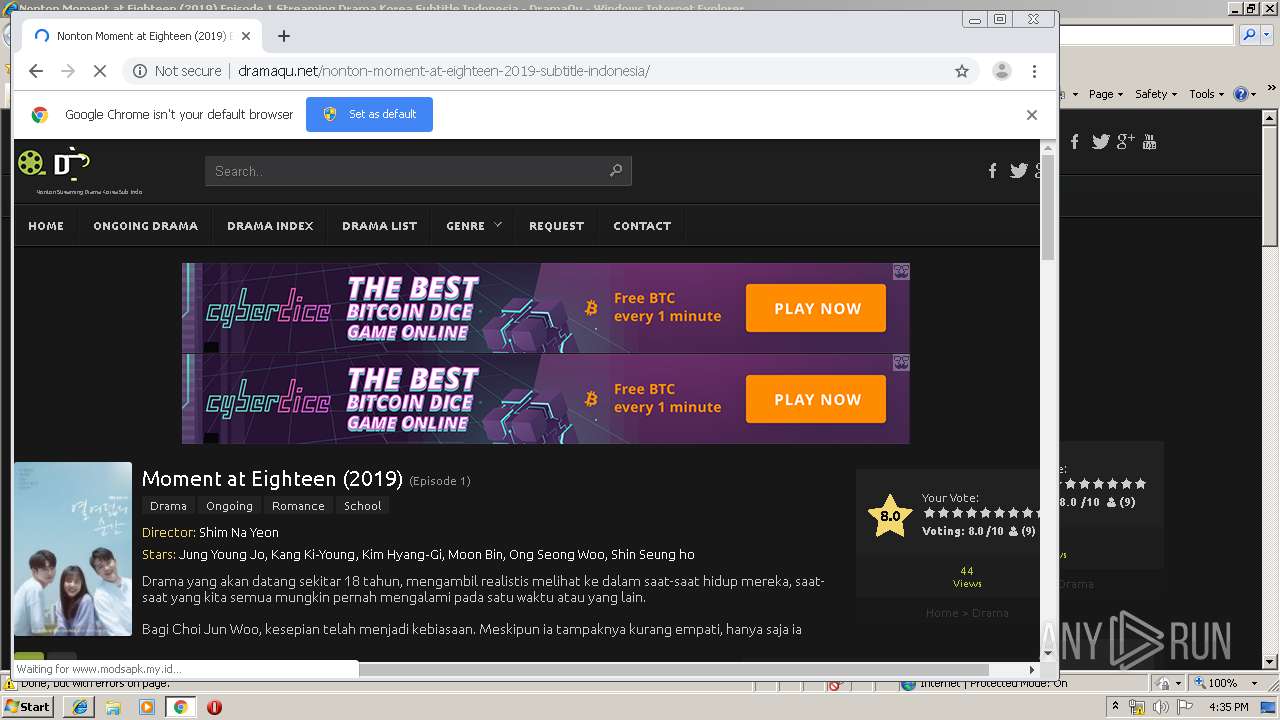
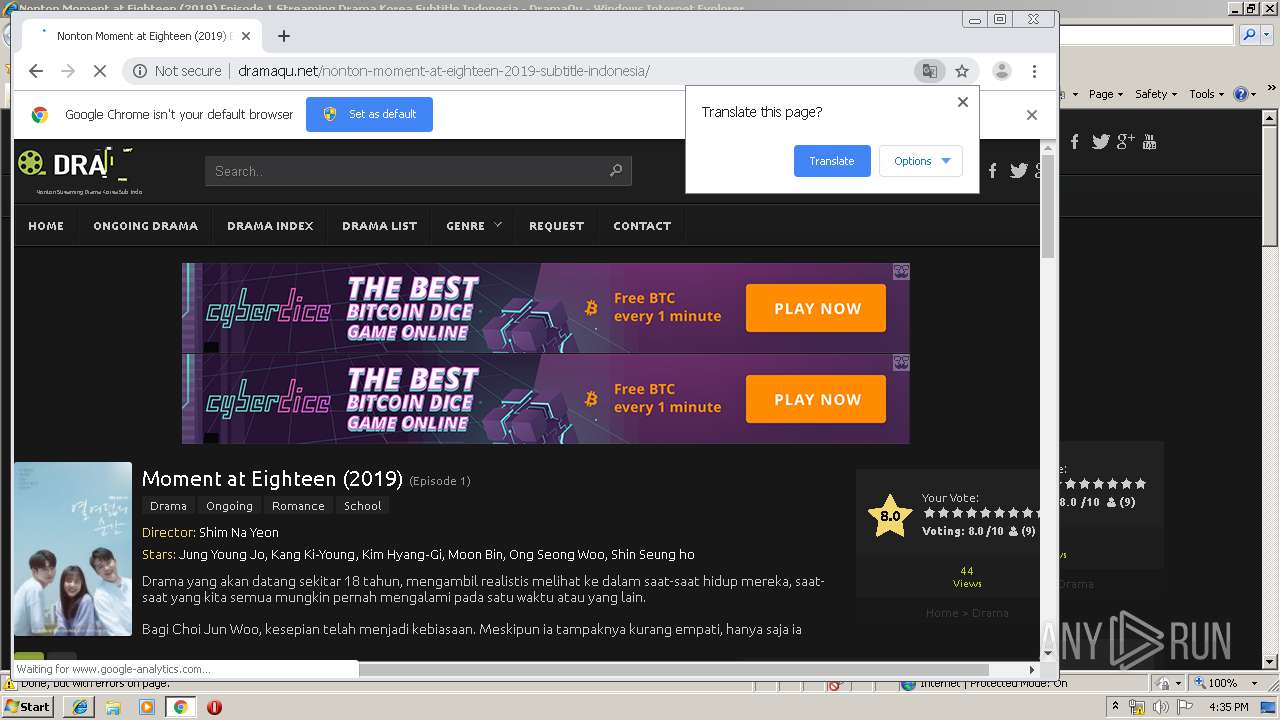
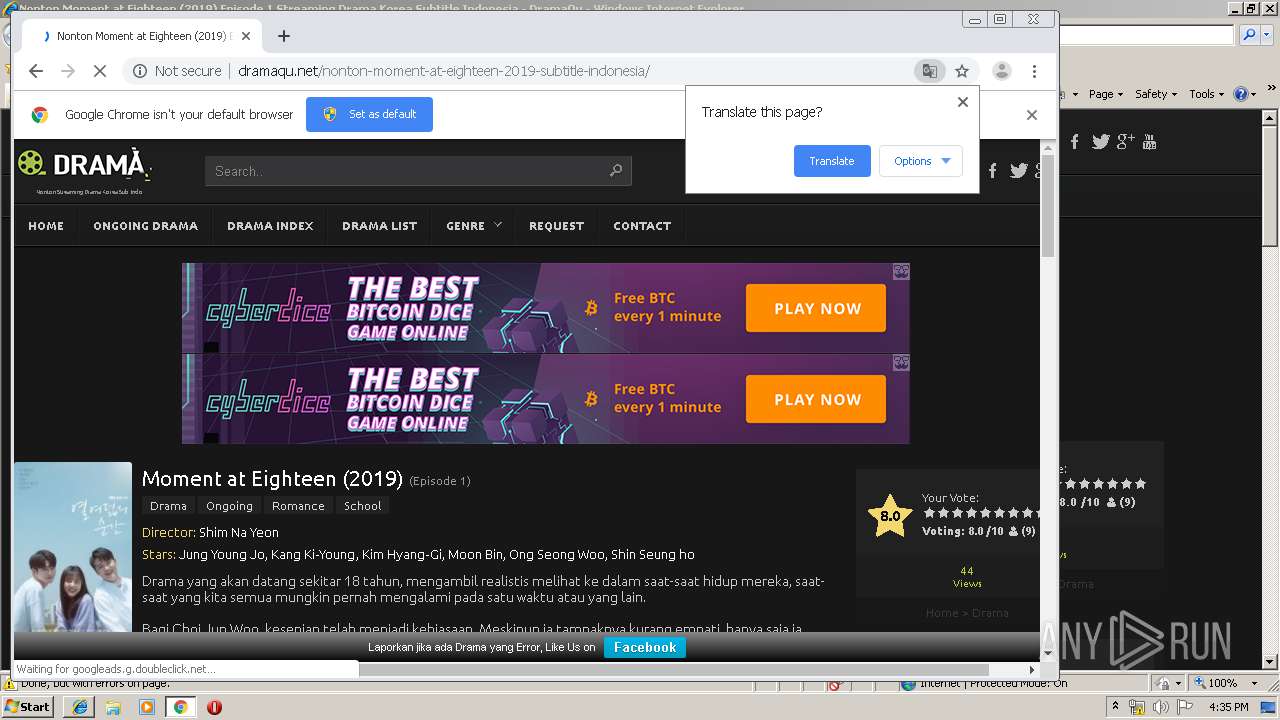
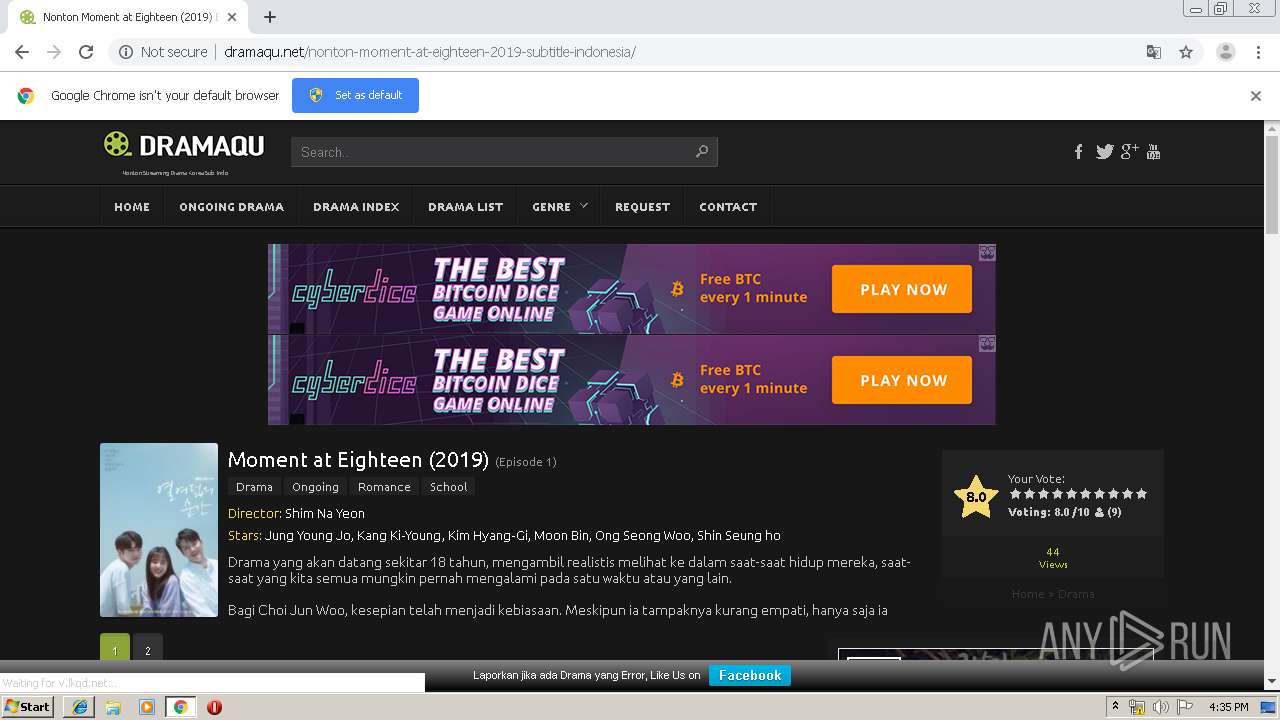
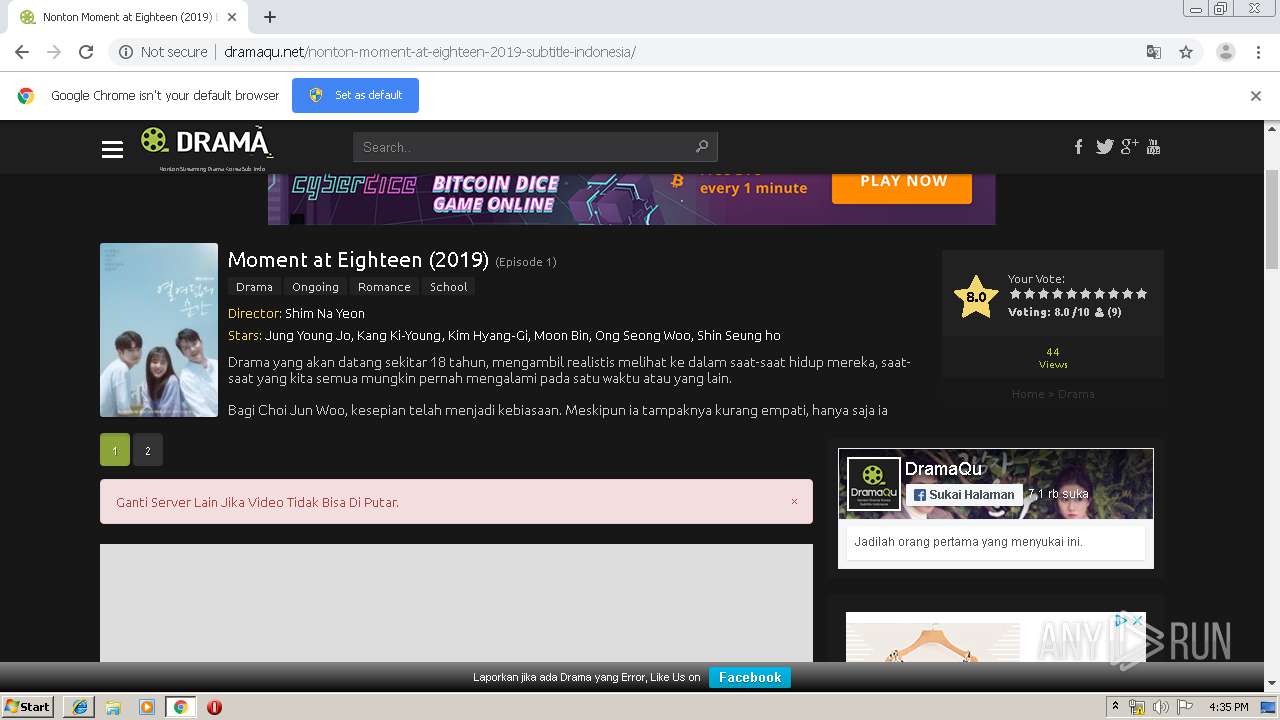
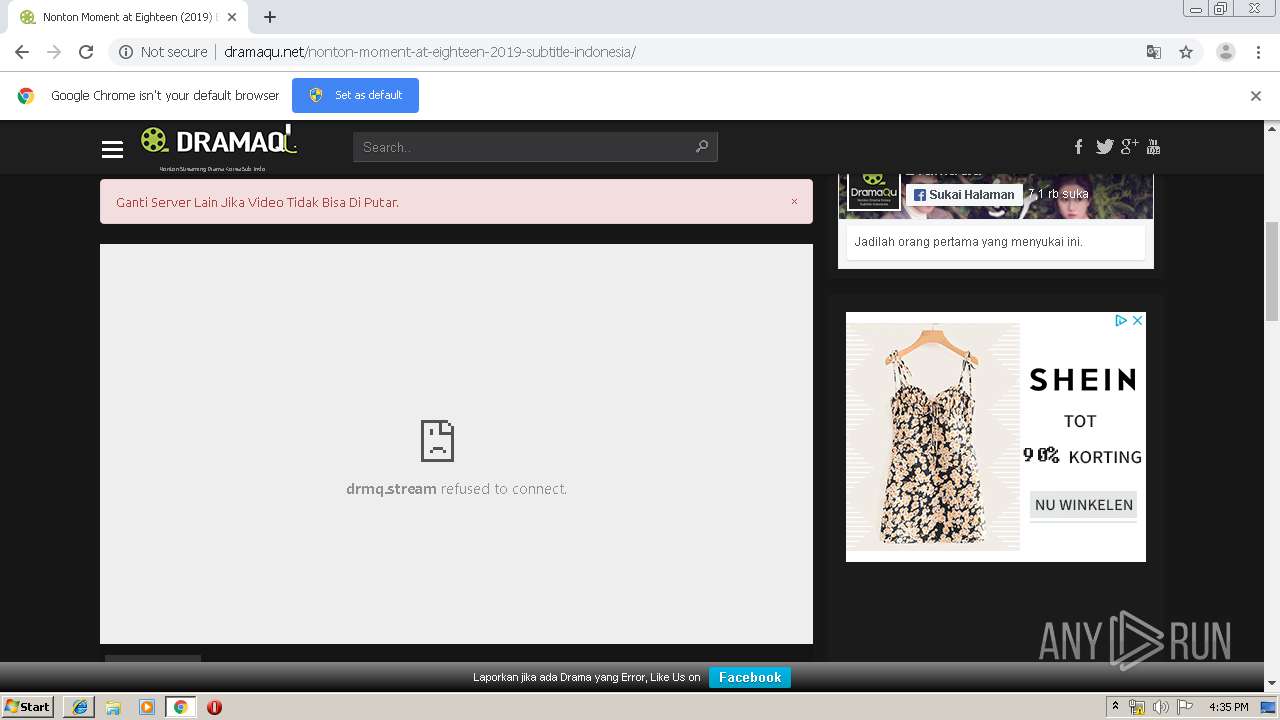
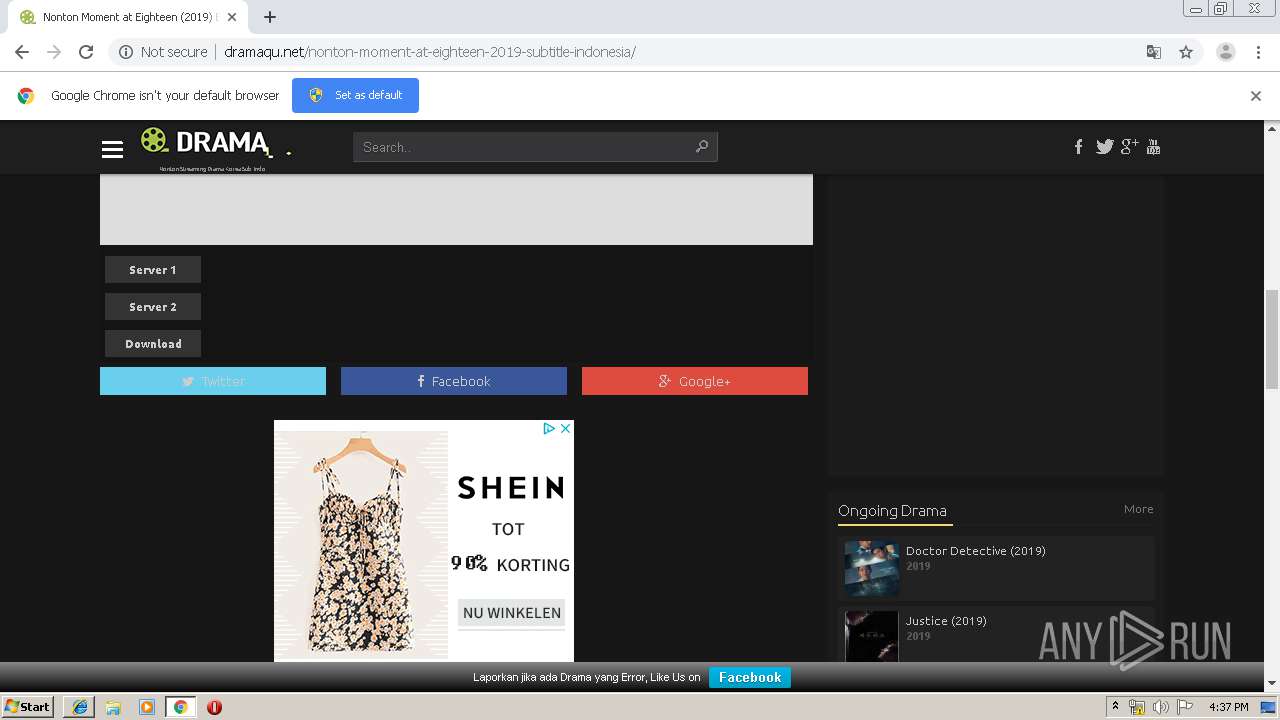
| URL: | http://dramaqu.net/nonton-moment-at-eighteen-2019-subtitle-indonesia/ |
| Full analysis: | https://app.any.run/tasks/d4cf1345-e244-429f-a10f-67539af5bbc2 |
| Verdict: | Malicious activity |
| Analysis date: | July 25, 2019, 15:33:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 28BE14CD90201848B0C3F4BF9937A76F |
| SHA1: | 2F188E1C047E078B80D4D0DDA8C6B30352AB51E0 |
| SHA256: | AD96652F7E1CFB2E7FEF0DCAFFDBEE5DD04D1CD00D788ED683EC09C5195DD648 |
| SSDEEP: | 3:N1KaXUn3AdMCNRuuqGn:CaX+8Mm3n |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3868)
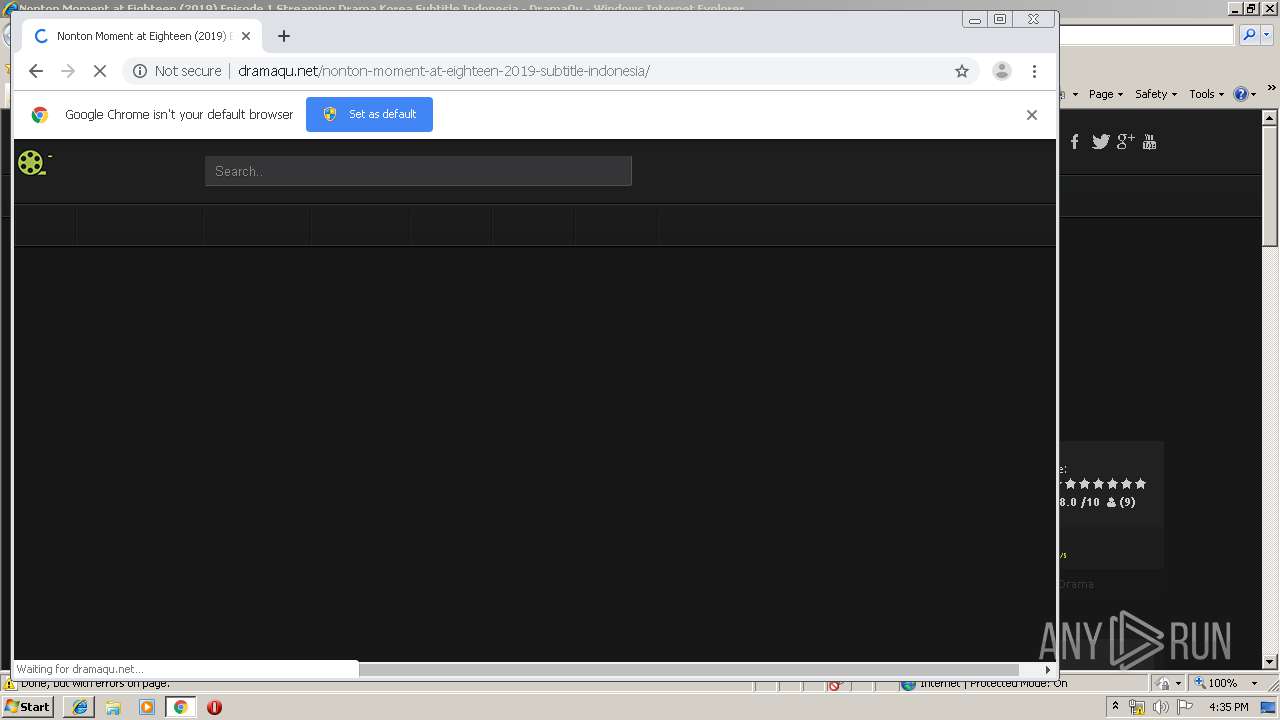
Modifies files in Chrome extension folder
- chrome.exe (PID: 3396)
INFO
Application launched itself
- iexplore.exe (PID: 2896)
- chrome.exe (PID: 3396)
Creates files in the user directory
- iexplore.exe (PID: 3372)
- iexplore.exe (PID: 2896)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3868)
Changes internet zones settings
- iexplore.exe (PID: 2896)
Reads Internet Cache Settings
- iexplore.exe (PID: 3372)
Reads internet explorer settings
- iexplore.exe (PID: 3372)
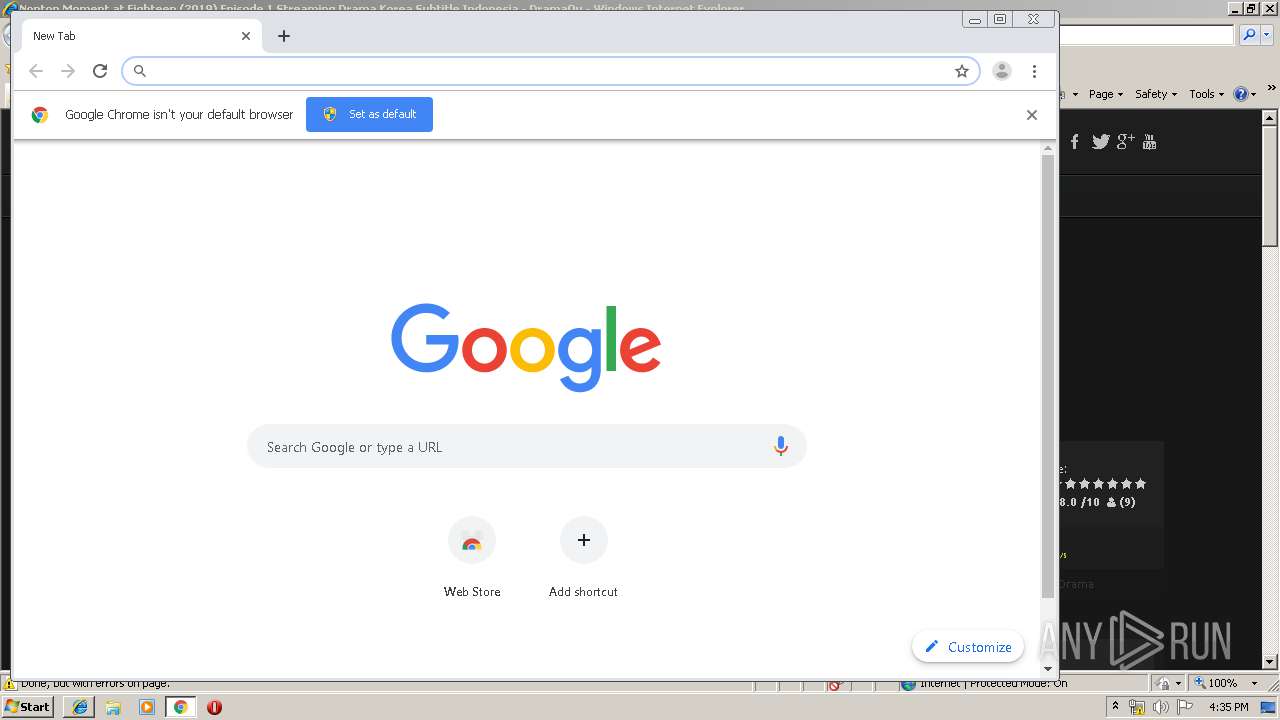
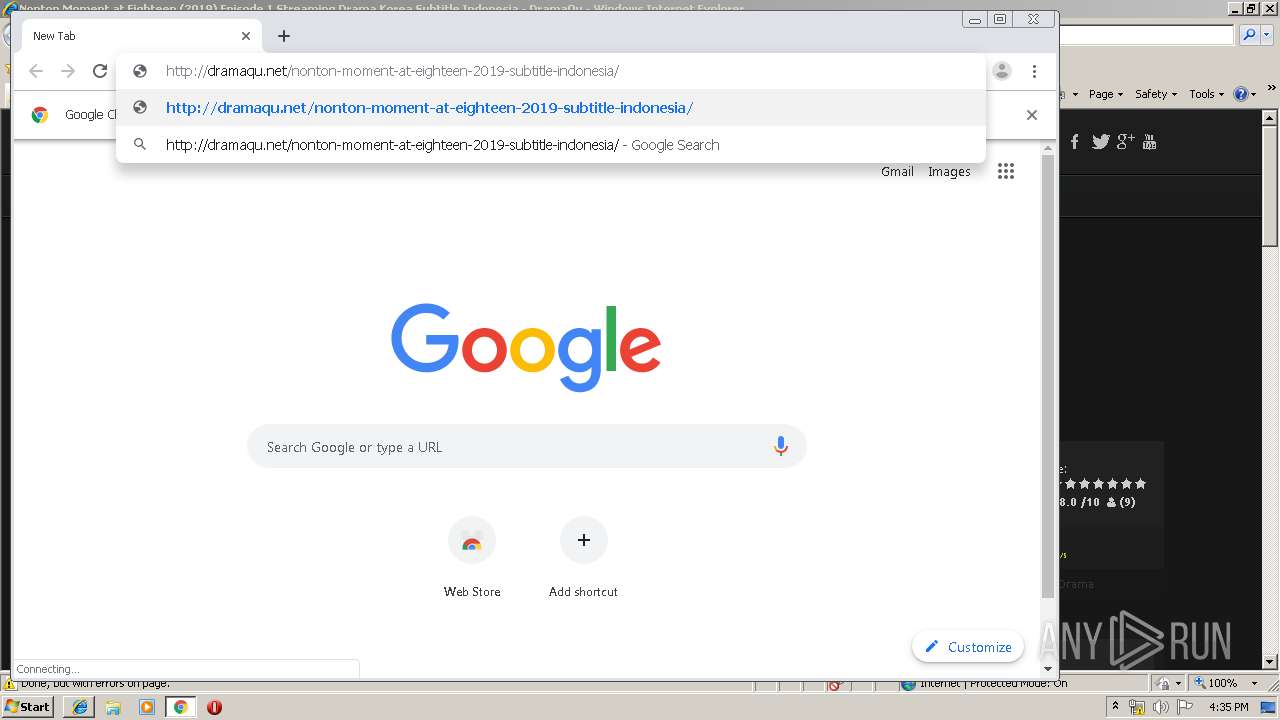
Manual execution by user
- chrome.exe (PID: 3396)
Dropped object may contain TOR URL's
- chrome.exe (PID: 3396)
Reads settings of System Certificates
- chrome.exe (PID: 3084)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
86
Monitored processes
52
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6a62a9d0,0x6a62a9e0,0x6a62a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,11261169243220313946,5833220385430080482,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15765624996614807808 --renderer-client-id=35 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5016 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,11261169243220313946,5833220385430080482,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6774974983715526044 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4160 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1068 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,11261169243220313946,5833220385430080482,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16125800771660194375 --mojo-platform-channel-handle=3260 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1196 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1016,11261169243220313946,5833220385430080482,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=8383860241747787797 --mojo-platform-channel-handle=1036 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,11261169243220313946,5833220385430080482,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11385338508813536800 --renderer-client-id=23 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3676 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,11261169243220313946,5833220385430080482,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17527408052179402456 --renderer-client-id=24 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4936 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1980 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,11261169243220313946,5833220385430080482,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9324366926630628164 --renderer-client-id=39 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4660 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,11261169243220313946,5833220385430080482,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7647490623645445453 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4520 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,11261169243220313946,5833220385430080482,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13381031233923971996 --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4672 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 096
Read events
931
Write events
160
Delete events
5
Modification events
| (PID) Process: | (2896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000077000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {9A2CE77D-AEF1-11E9-B506-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (2896) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070700040019000F00210034009C01 | |||
Executable files
0
Suspicious files
205
Text files
307
Unknown types
23
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2896 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2896 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3372 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\RAYCXA0V\nonton-moment-at-eighteen-2019-subtitle-indonesia[1].txt | — | |
MD5:— | SHA256:— | |||
| 3372 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@dramaqu[1].txt | text | |
MD5:— | SHA256:— | |||
| 3372 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3372 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\Low\History.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3372 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3372 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\RAYCXA0V\nonton-moment-at-eighteen-2019-subtitle-indonesia[1].htm | html | |
MD5:— | SHA256:— | |||
| 3372 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\RKUO65FN\responsive-min[1].css | text | |
MD5:— | SHA256:— | |||
| 3372 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\UY2T7F45\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
258
TCP/UDP connections
190
DNS requests
138
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3372 | iexplore.exe | GET | 200 | 104.25.245.114:80 | http://dramaqu.net/wp-content/themes/dramaqu/css/responsive-min.css | US | text | 2.22 Kb | whitelisted |
3372 | iexplore.exe | GET | 200 | 104.25.245.114:80 | http://dramaqu.net/nonton-moment-at-eighteen-2019-subtitle-indonesia/ | US | html | 14.9 Kb | whitelisted |
3372 | iexplore.exe | GET | 200 | 104.25.245.114:80 | http://dramaqu.net/ | US | html | 17.6 Kb | whitelisted |
3372 | iexplore.exe | GET | 200 | 104.25.245.114:80 | http://dramaqu.net/wp-content/uploads/2019/07/nonton-doctor-detective-2019-subtitle-indonesia-70x80.jpg | US | image | 2.18 Kb | whitelisted |
3372 | iexplore.exe | GET | 200 | 104.27.162.141:80 | http://www.modsapk.my.id/ads.php | US | html | 314 b | shared |
3372 | iexplore.exe | GET | 200 | 46.105.201.240:80 | http://s10.histats.com/js15_as.js | FR | html | 4.42 Kb | whitelisted |
3372 | iexplore.exe | GET | 200 | 5.9.10.165:80 | http://ad.a-ads.com/1193246?size=728x90 | DE | html | 1.89 Kb | whitelisted |
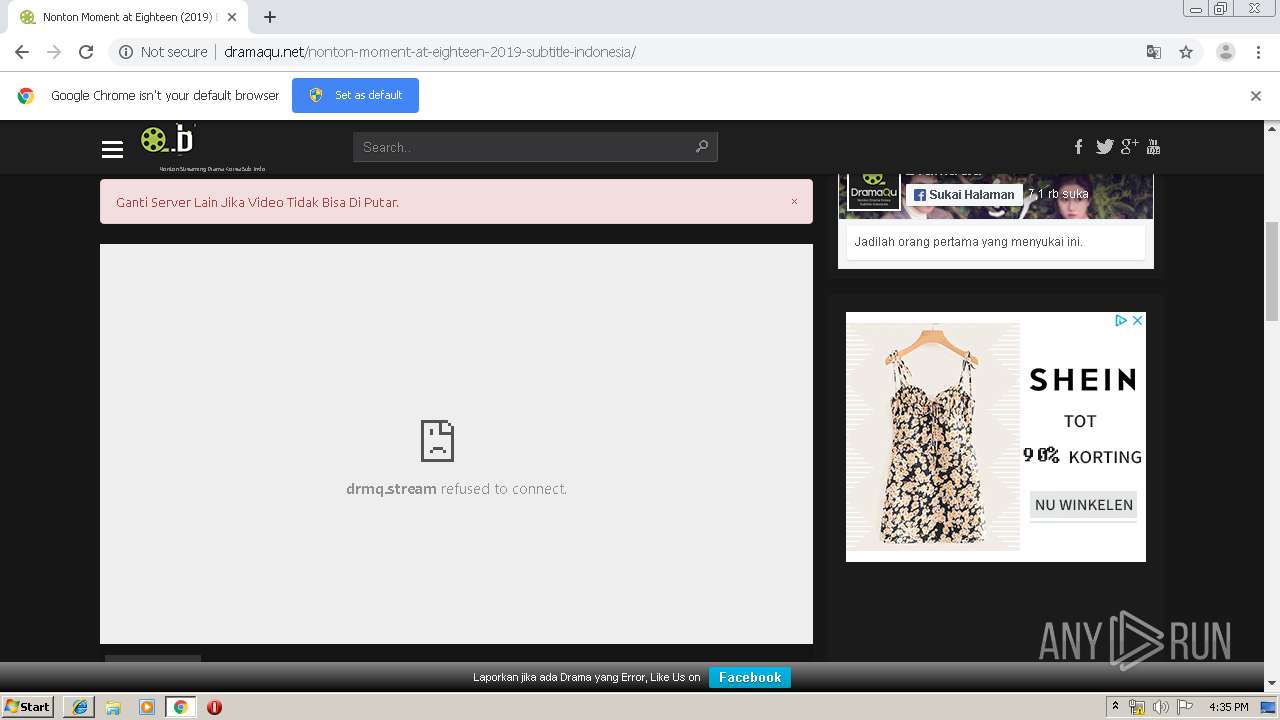
3372 | iexplore.exe | GET | 403 | 104.25.246.114:80 | http://drmq.stream/v3/play.php?id=QkJTMzBlQVdRQ010dENVREV0djNUMm90Y0RHMDlIb0NrcFdEYmVXK1g1MXFNQlZIUVc1WmMyVy9waEVHNHNTdk9TRDdmK1YvTDV5V09HeUdLaHNERXowMzVyZStqOU5HUkhKenhmMVlTTXpXS3RHUG52b00zVS9Ib01oMUxuNG1LWW9qeGlQTHBRZXFRMjZuWFo3SXlqY0pZVkUxdjQza0s1Um5ldndjL2p4WG41TVlUa0lTaGJMdjRmR1U0ZlJydE9pdTlHQUw5cVNXd2xXVmppVVJYMHdpQlBRbVJTN2hVVGZPTHcvQVRvcS84YTR3NjZqOFJBajBFS2R1SWhnRA== | US | html | 1.13 Kb | whitelisted |
3372 | iexplore.exe | GET | 301 | 104.25.245.114:80 | http://dramaqu.net/nonton-moment-at-eighteen-2019-subtitle-indonesia/adxoo.js | US | compressed | 1.32 Kb | whitelisted |
3372 | iexplore.exe | GET | 200 | 104.25.245.114:80 | http://dramaqu.net/wp-content/plugins/fruitful-shortcodes/fruitful-shortcodes-1.6.2/includes/shortcodes/js/tabs/easy-responsive-tabs.css?ver=5.2.2 | US | text | 944 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2896 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3372 | iexplore.exe | 172.217.23.131:80 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3372 | iexplore.exe | 185.60.216.35:443 | www.facebook.com | Facebook, Inc. | IE | whitelisted |
3372 | iexplore.exe | 185.60.216.19:443 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
3372 | iexplore.exe | 5.9.10.165:80 | ad.a-ads.com | Hetzner Online GmbH | DE | suspicious |
3372 | iexplore.exe | 3.17.116.255:443 | ads.vidoomy.com | — | US | unknown |
3372 | iexplore.exe | 104.27.162.141:80 | www.modsapk.my.id | Cloudflare Inc | US | shared |
3372 | iexplore.exe | 3.17.116.255:80 | ads.vidoomy.com | — | US | unknown |
3372 | iexplore.exe | 172.217.16.142:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3372 | iexplore.exe | 46.105.201.240:80 | s10.histats.com | OVH SAS | FR | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dramaqu.net |
| whitelisted |
www.bing.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
ads.vidoomy.com |
| unknown |
connect.facebook.net |
| whitelisted |
www.facebook.com |
| whitelisted |
ad.a-ads.com |
| whitelisted |
drmq.stream |
| whitelisted |
www.modsapk.my.id |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3084 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |