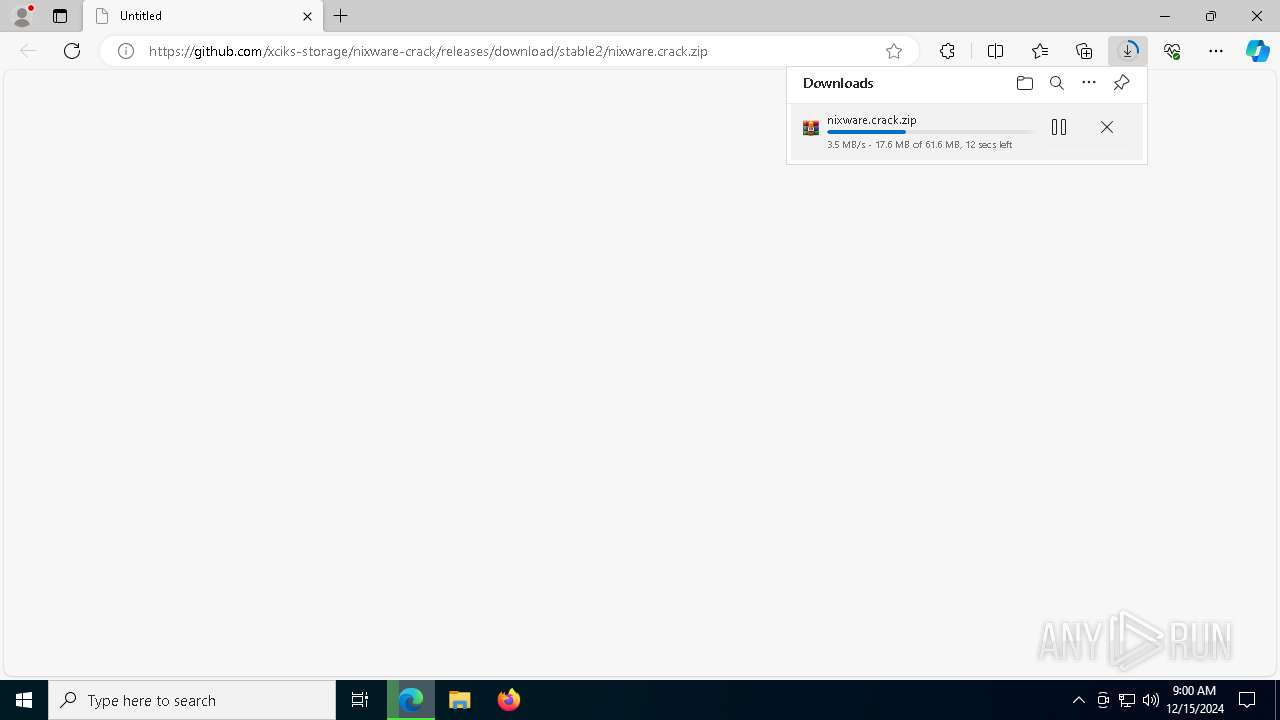
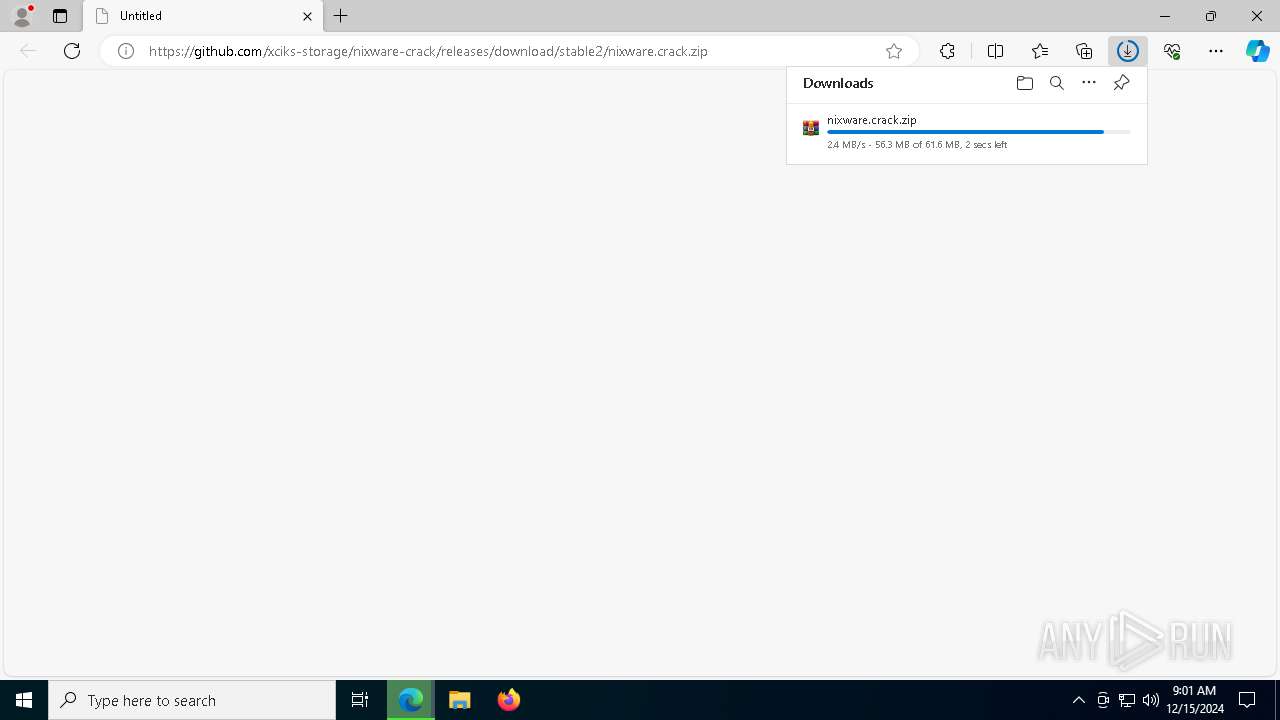
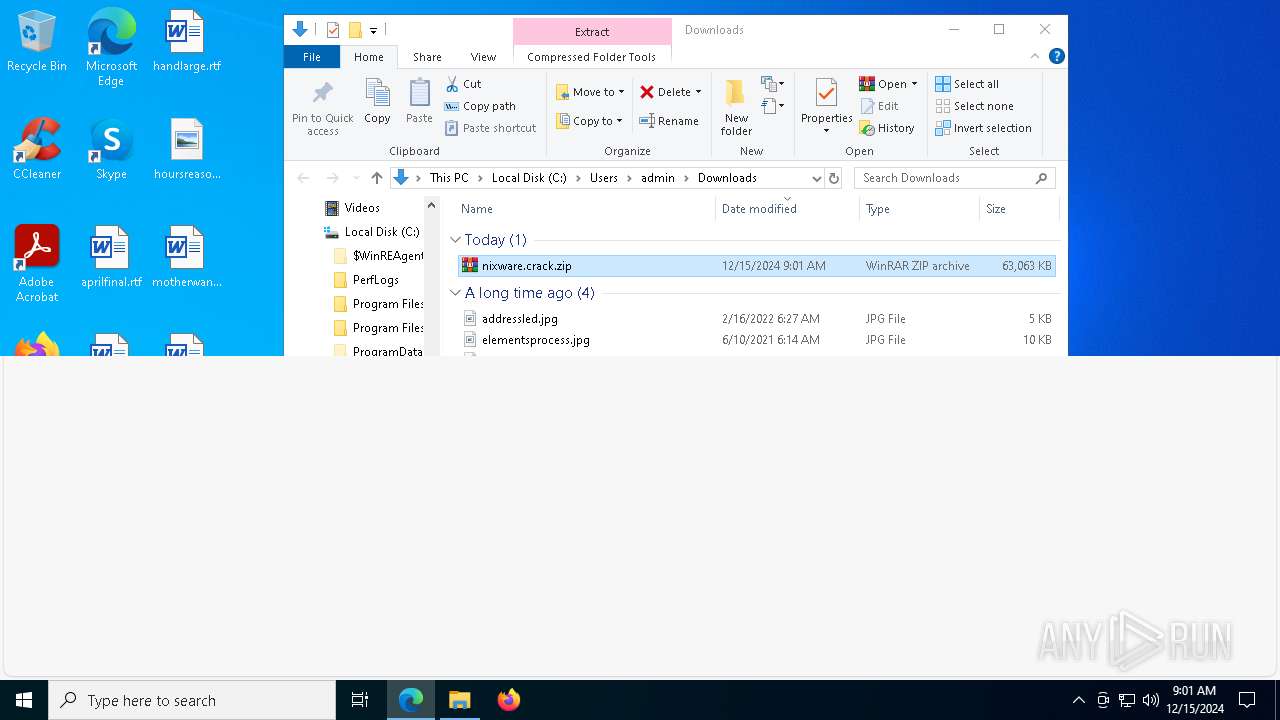
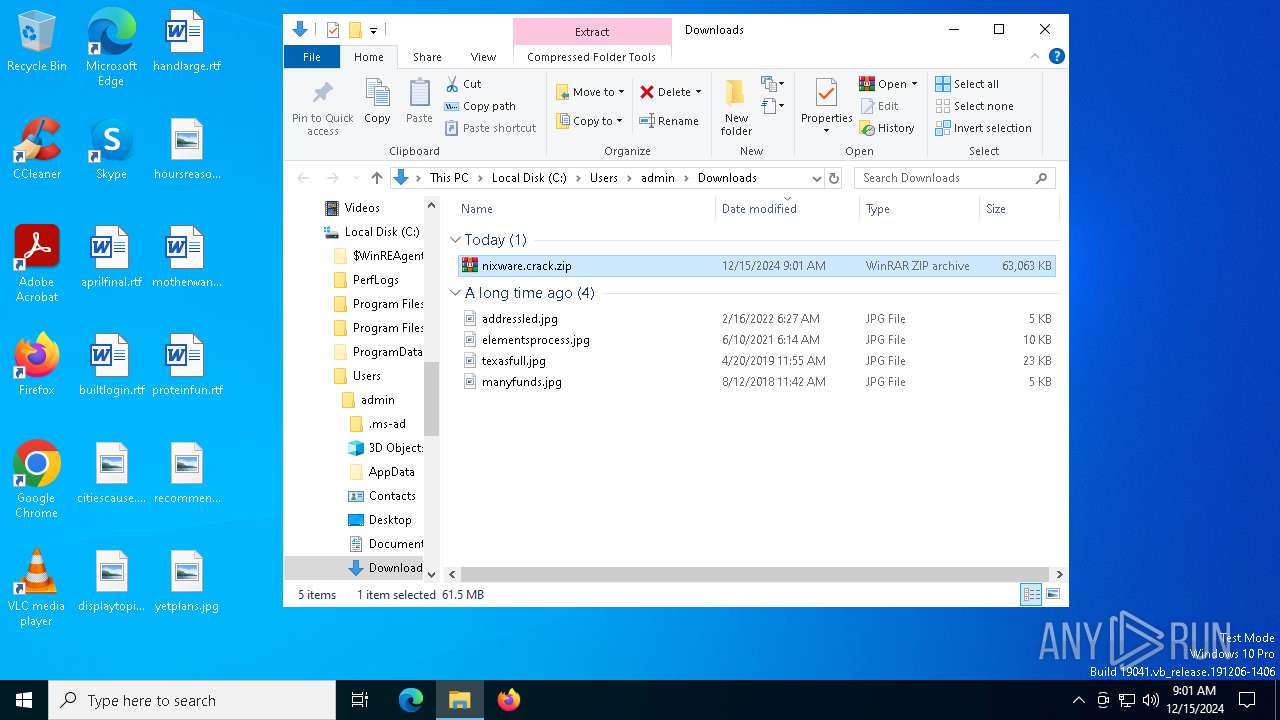
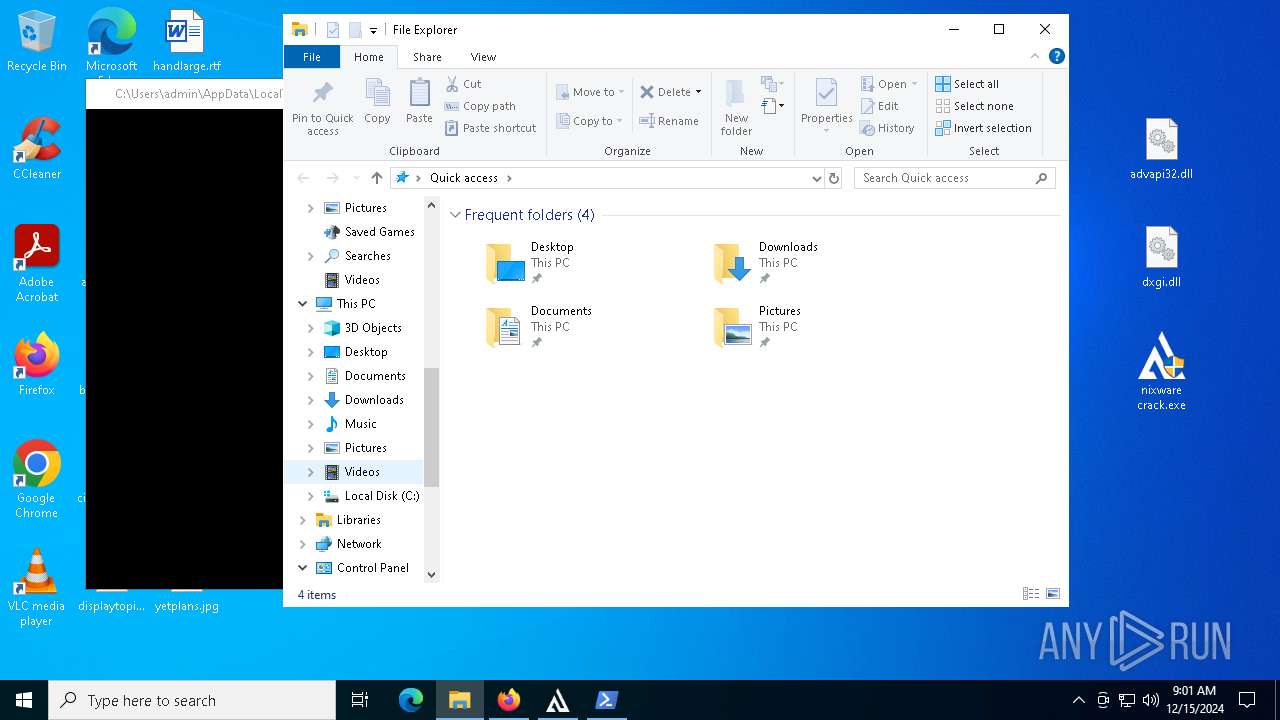
| URL: | https://github.com/xciks-storage/nixware-crack/releases/download/stable2/nixware.crack.zip |
| Full analysis: | https://app.any.run/tasks/062fe299-19b4-422f-80cf-1e5da04a6c0e |
| Verdict: | Malicious activity |
| Analysis date: | December 15, 2024, 09:00:38 |
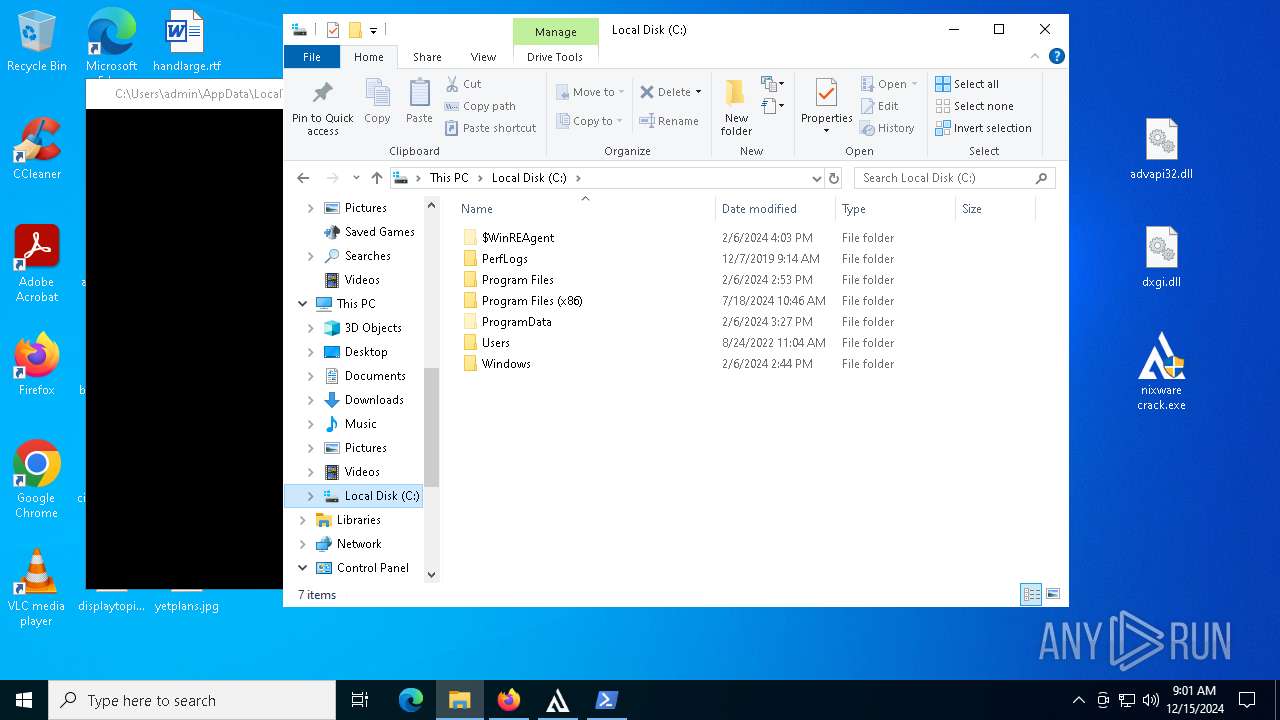
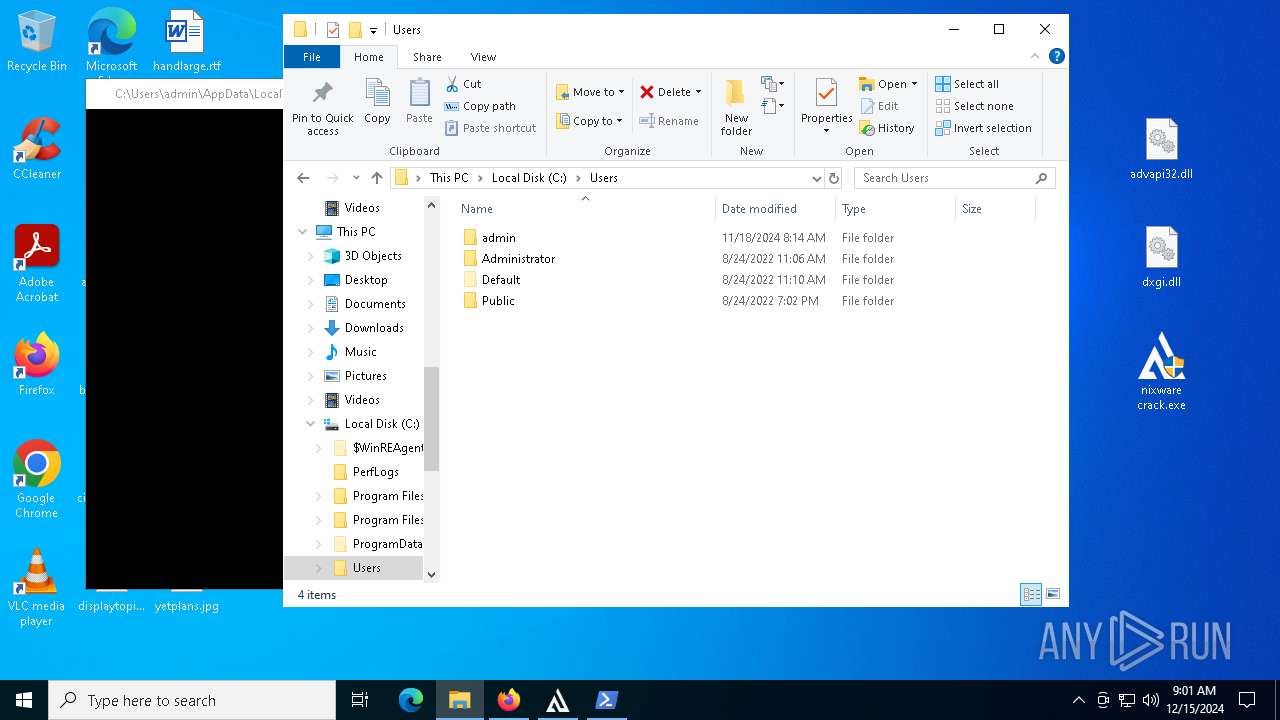
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | B095ED50E55F79BC760CC543ACBA59D0 |
| SHA1: | 6A0CECDD8704940CAE145C395DC3452E0B623AD9 |
| SHA256: | AD931FA7D9EC14F8D17490988A32CBDC4F6F87CB12F57CB28709ADA40CB5D44C |
| SSDEEP: | 3:N8tEdtGM2MxdIE2kCyXKeZeUn:2uC2xd0kXjZeU |
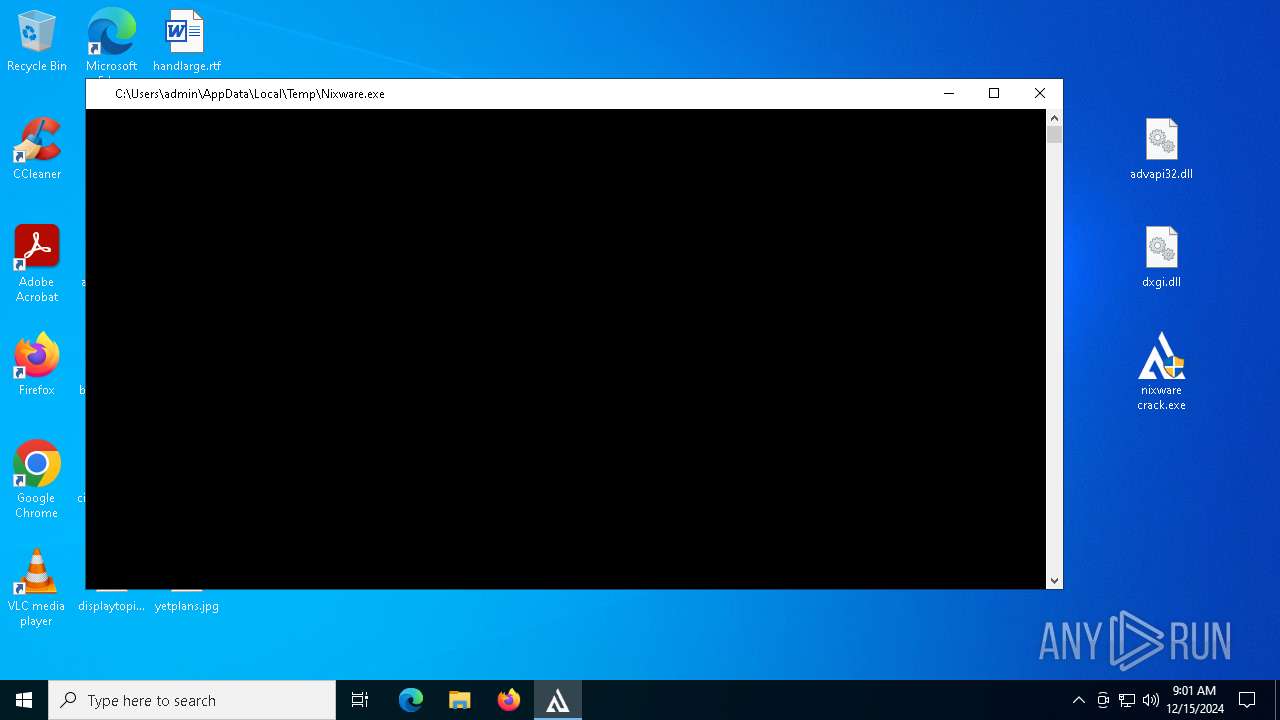
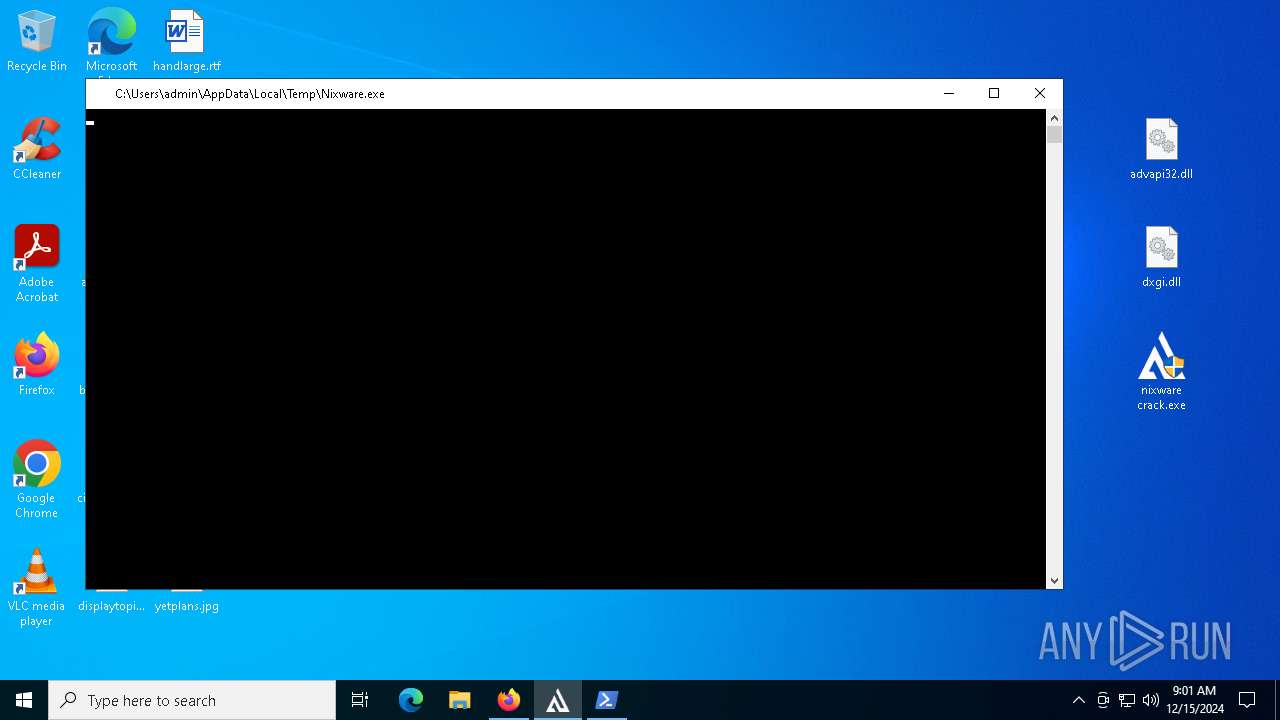
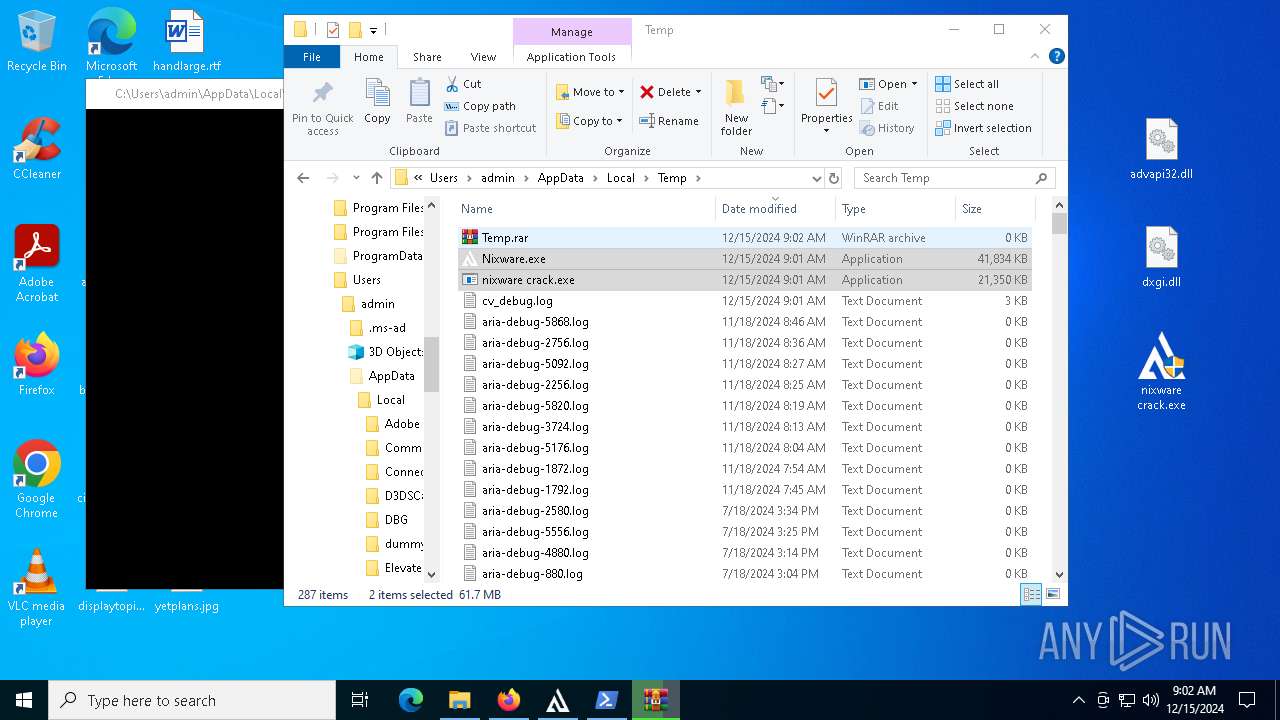
MALICIOUS
No malicious indicators.SUSPICIOUS
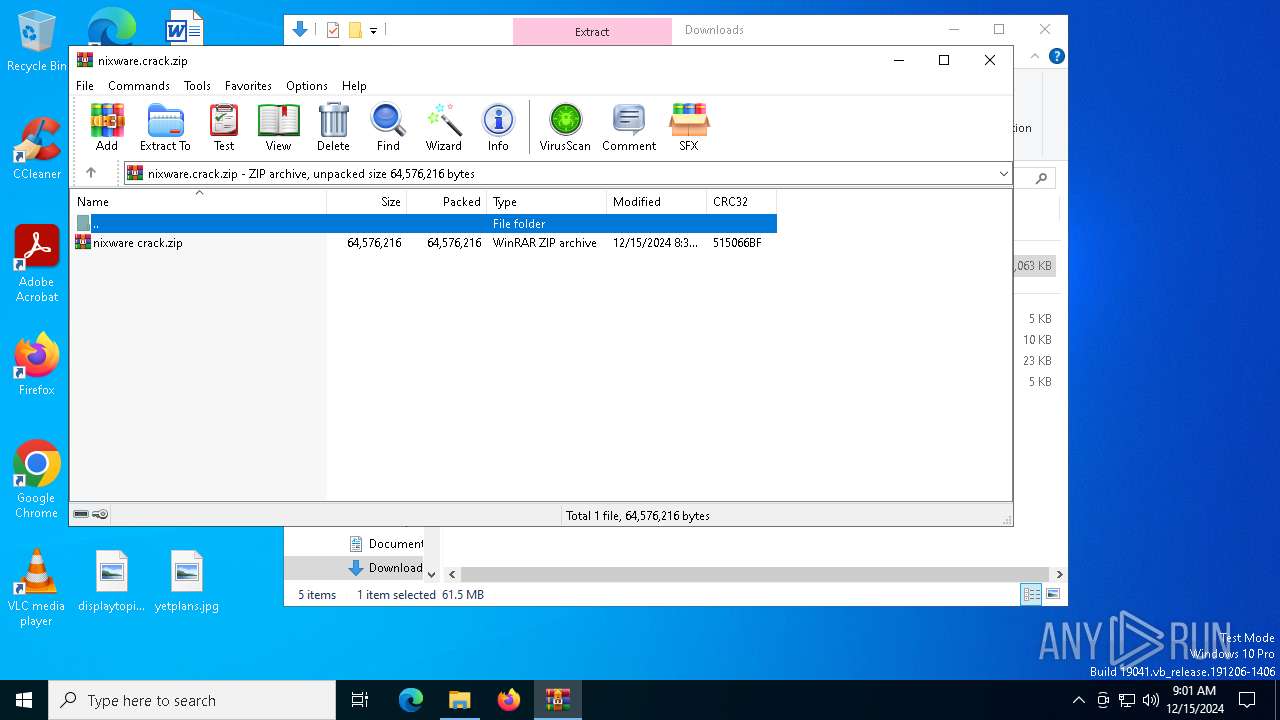
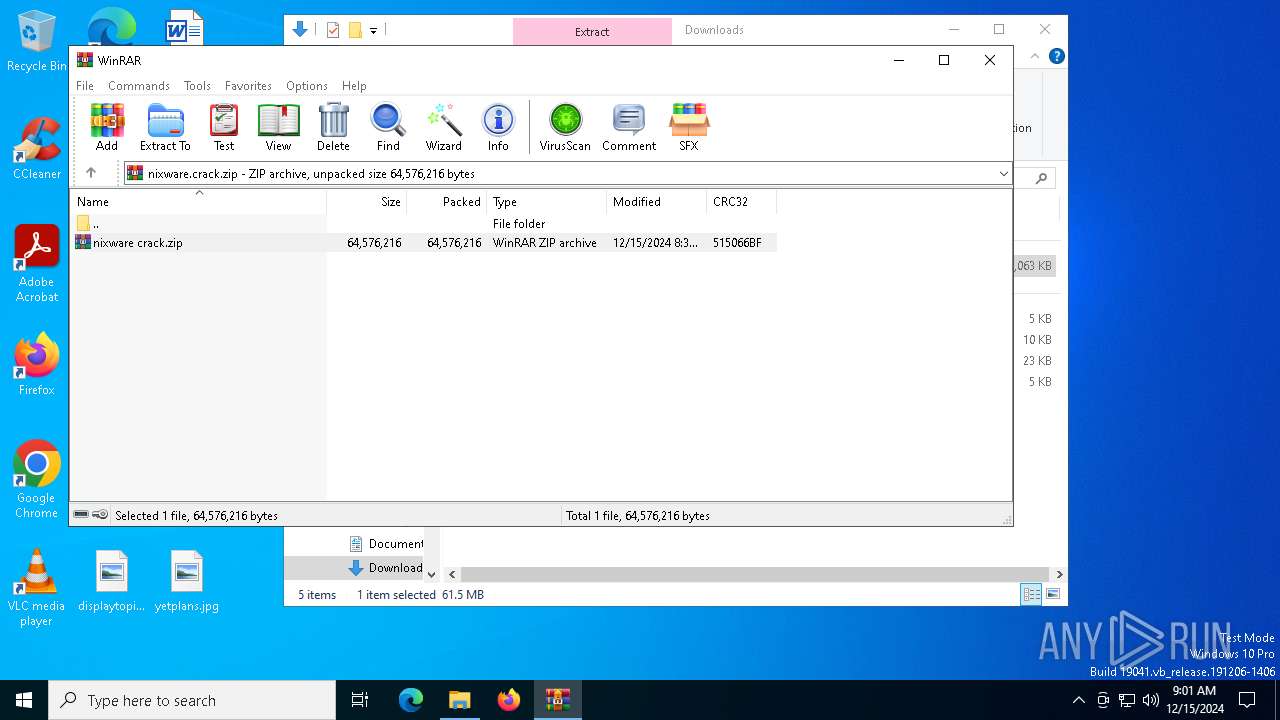
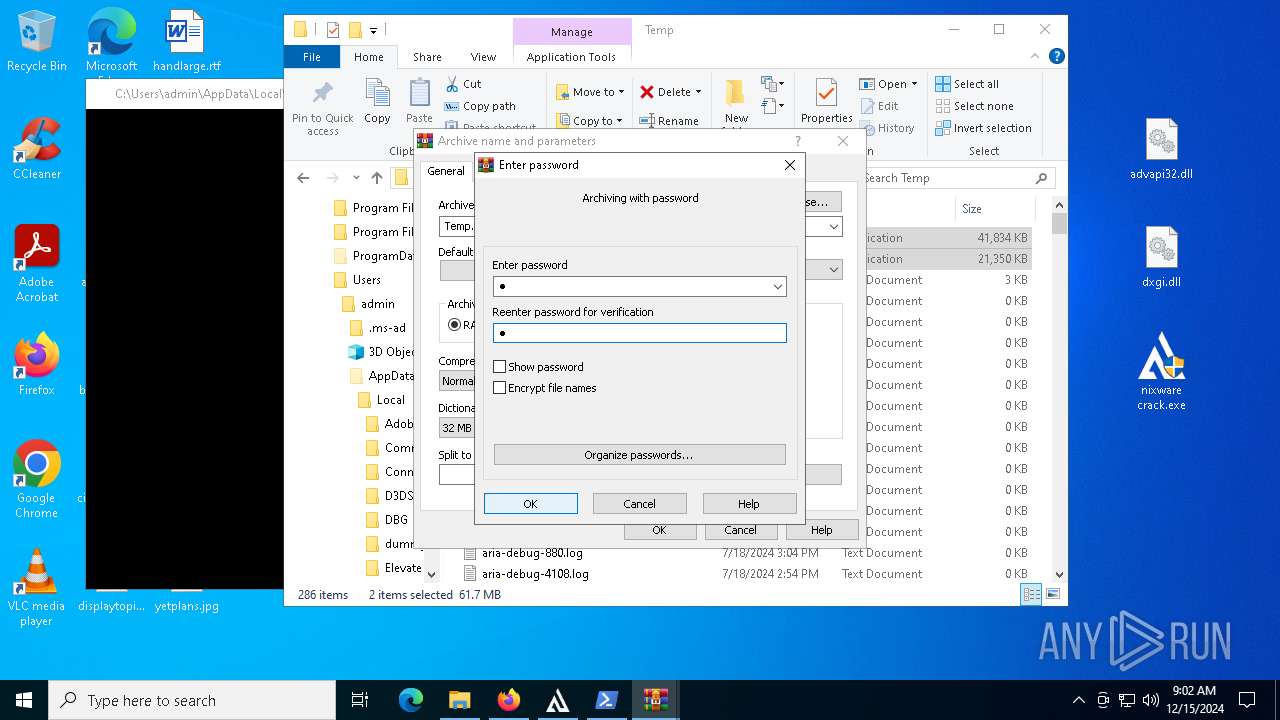
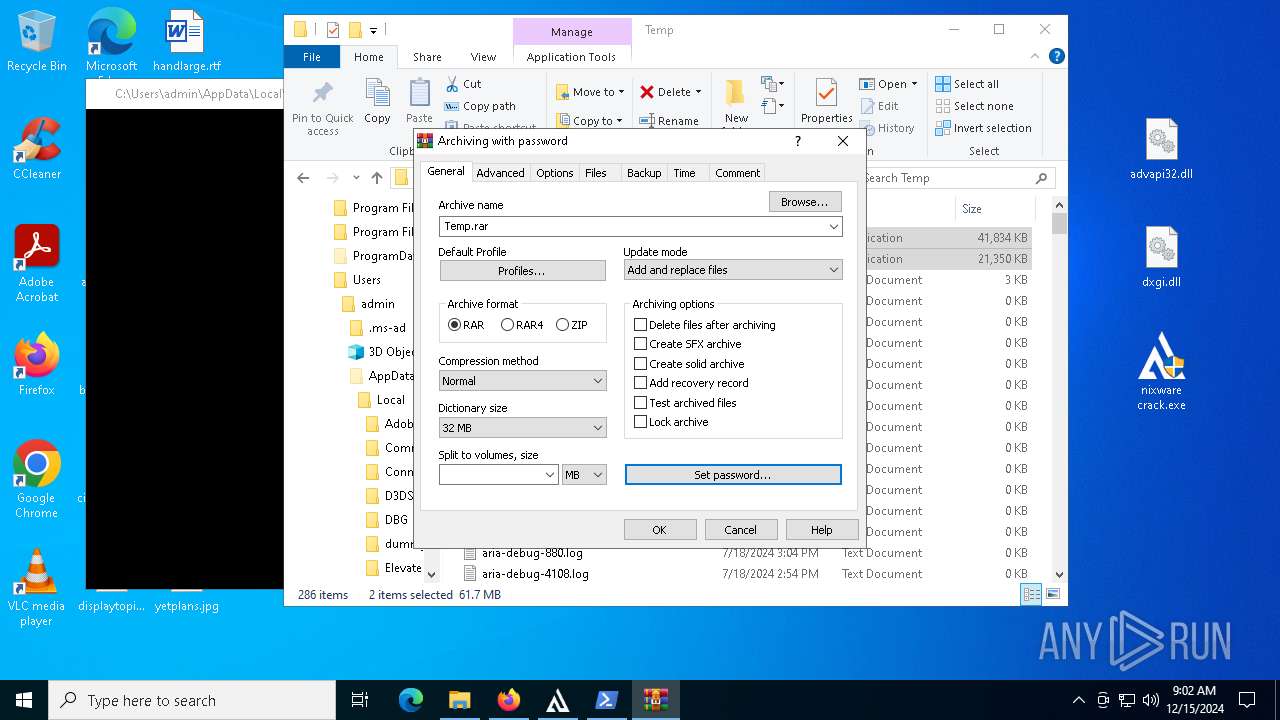
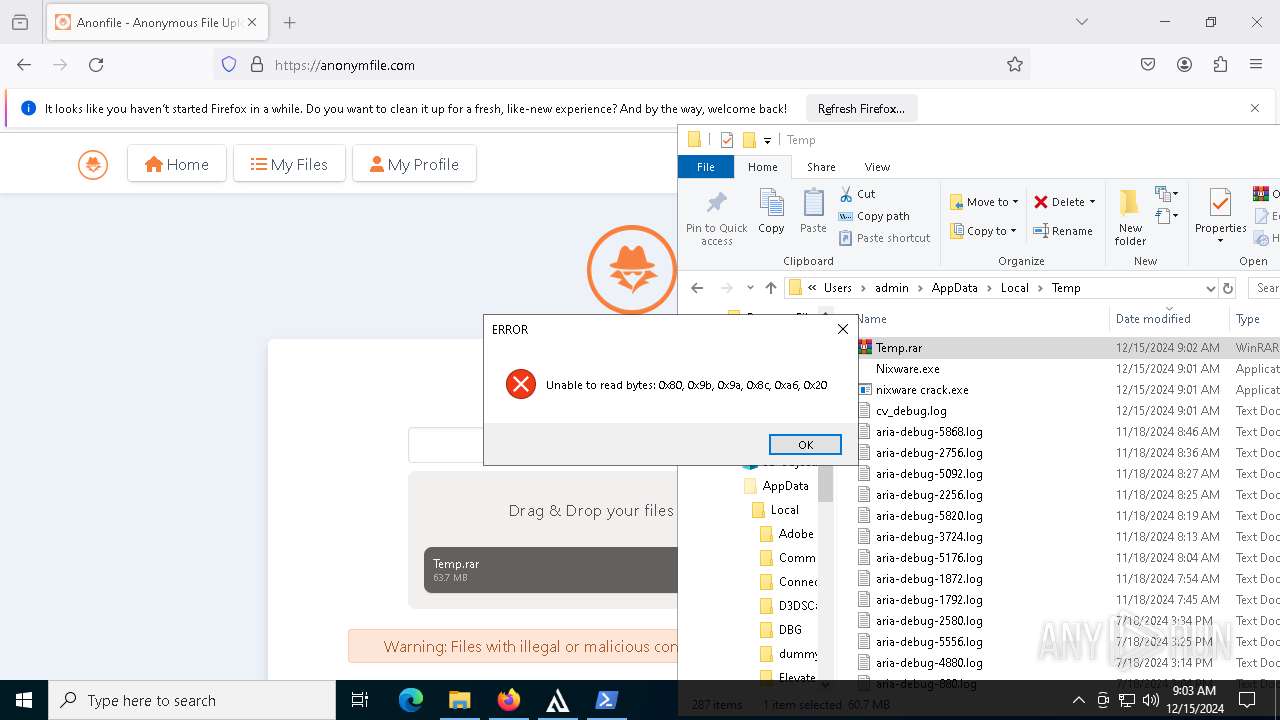
BASE64 encoded PowerShell command has been detected
- nixware crack.exe (PID: 7912)
Application launched itself
- WinRAR.exe (PID: 4128)
- nixware crack.exe (PID: 7308)
- Nixware.exe (PID: 7784)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 4128)
- nixware crack.exe (PID: 7912)
Starts POWERSHELL.EXE for commands execution
- nixware crack.exe (PID: 7912)
Base64-obfuscated command line is found
- nixware crack.exe (PID: 7912)
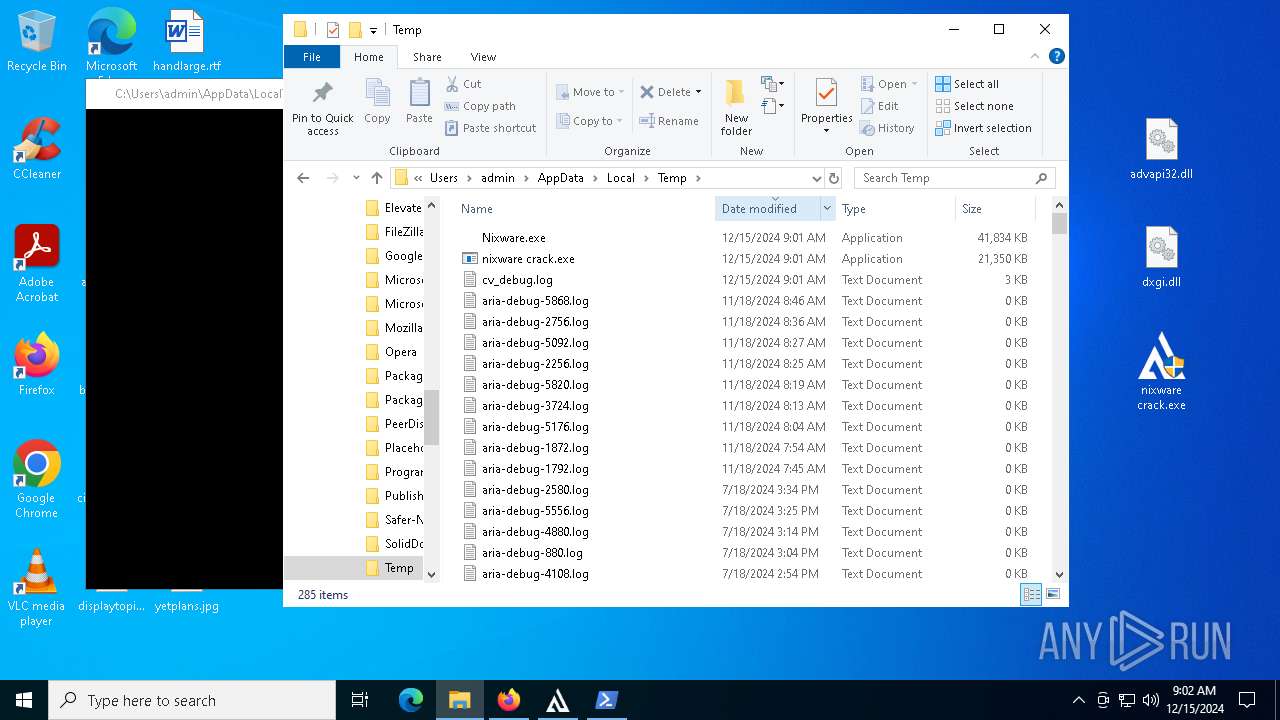
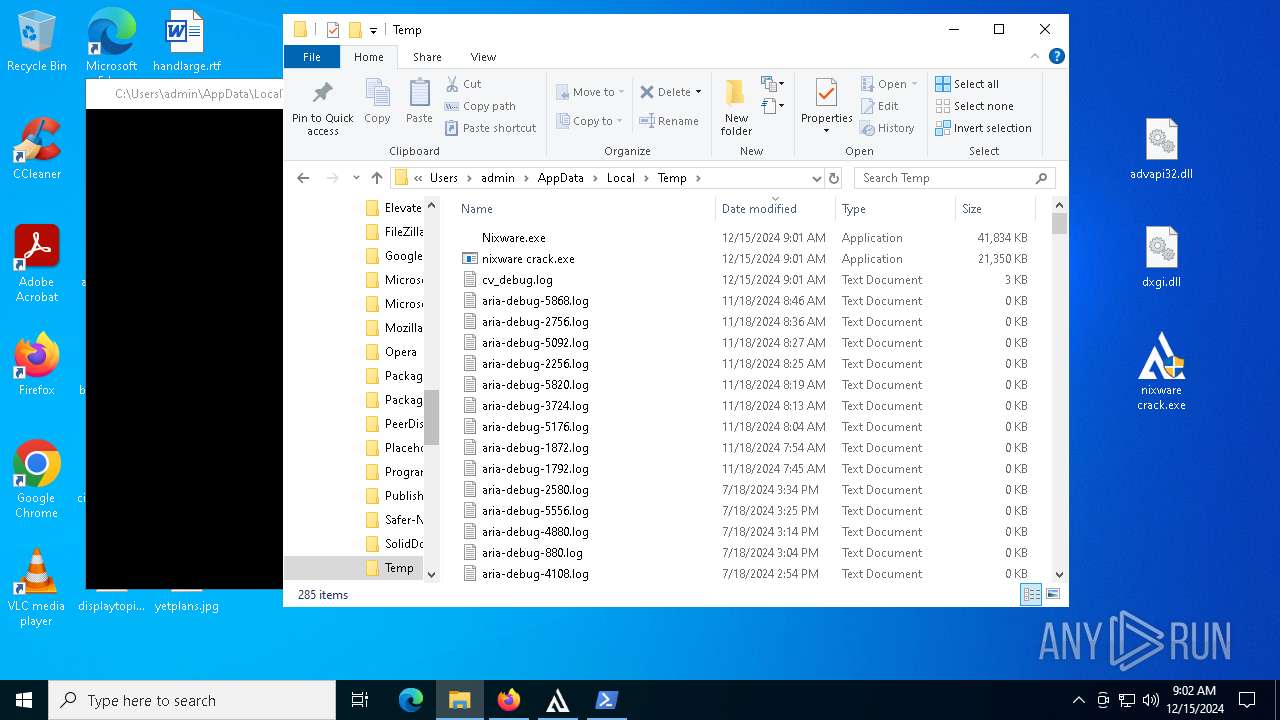
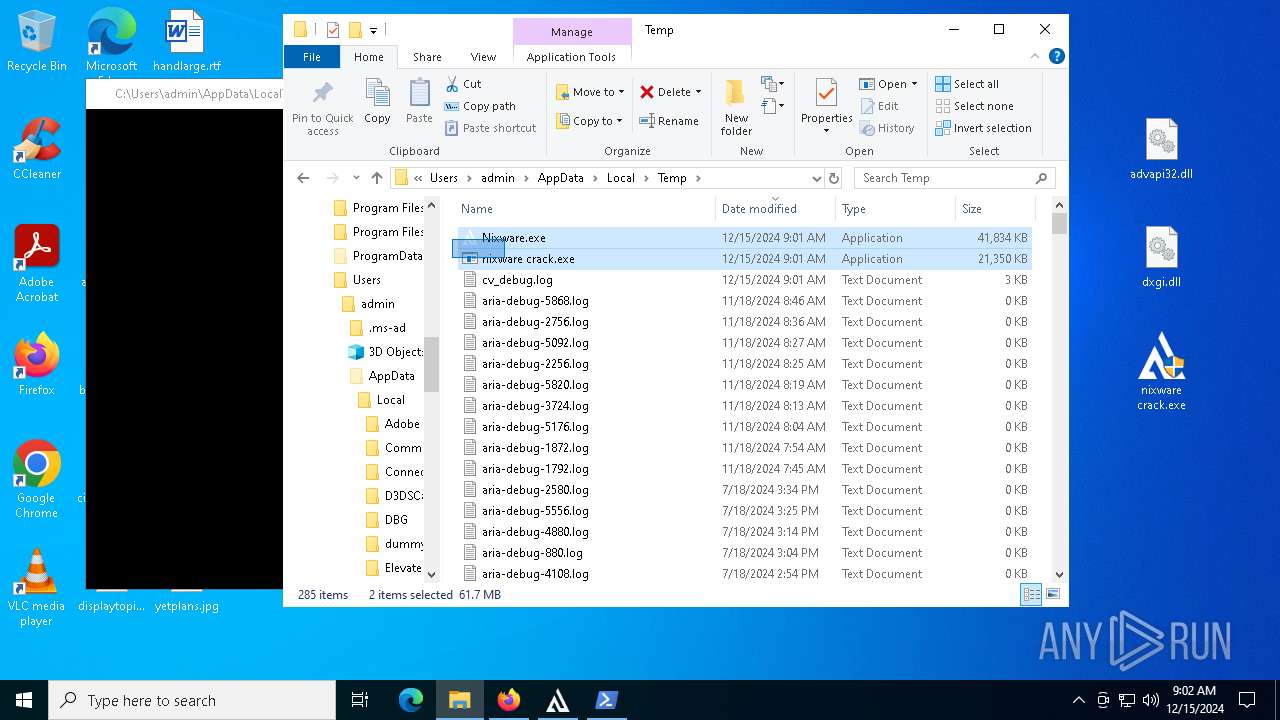
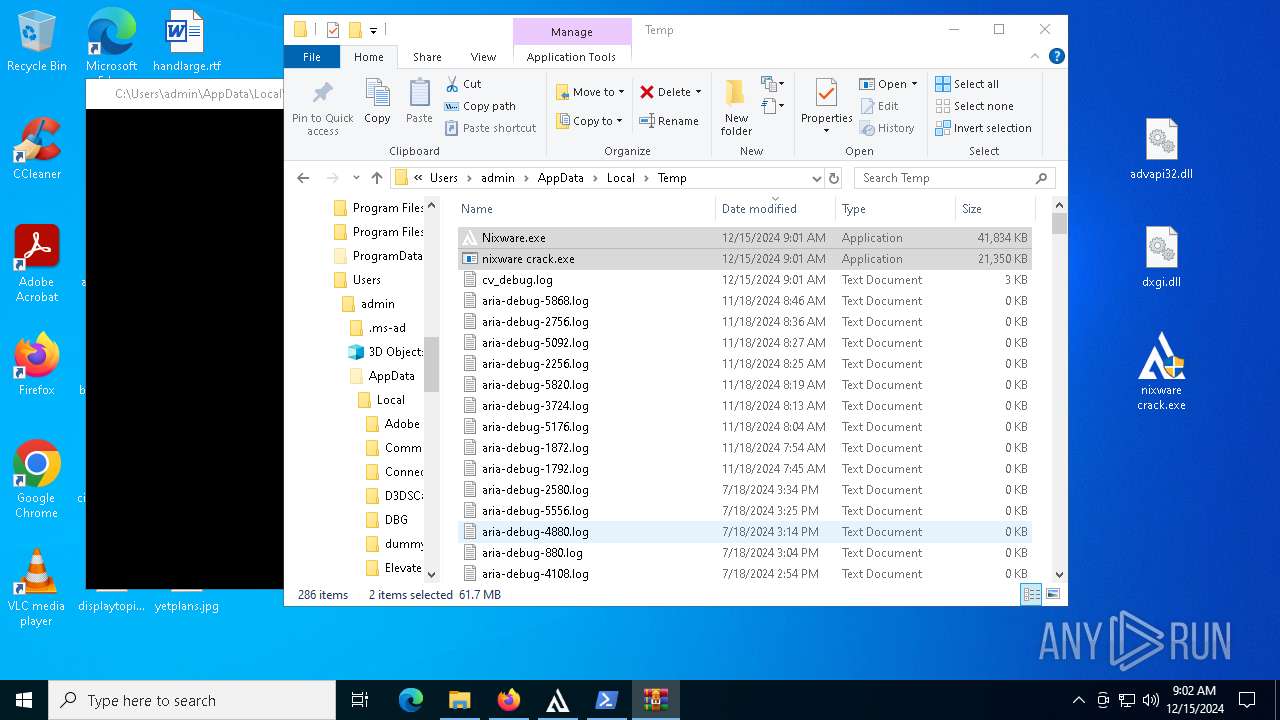
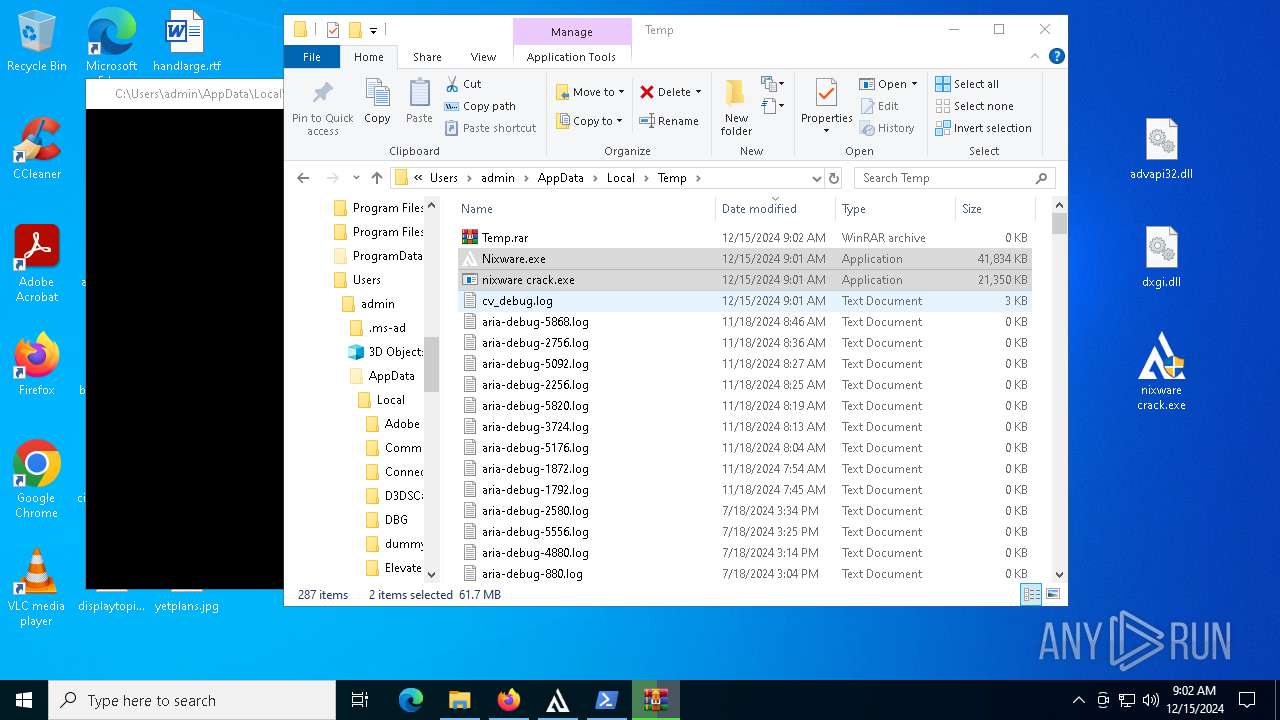
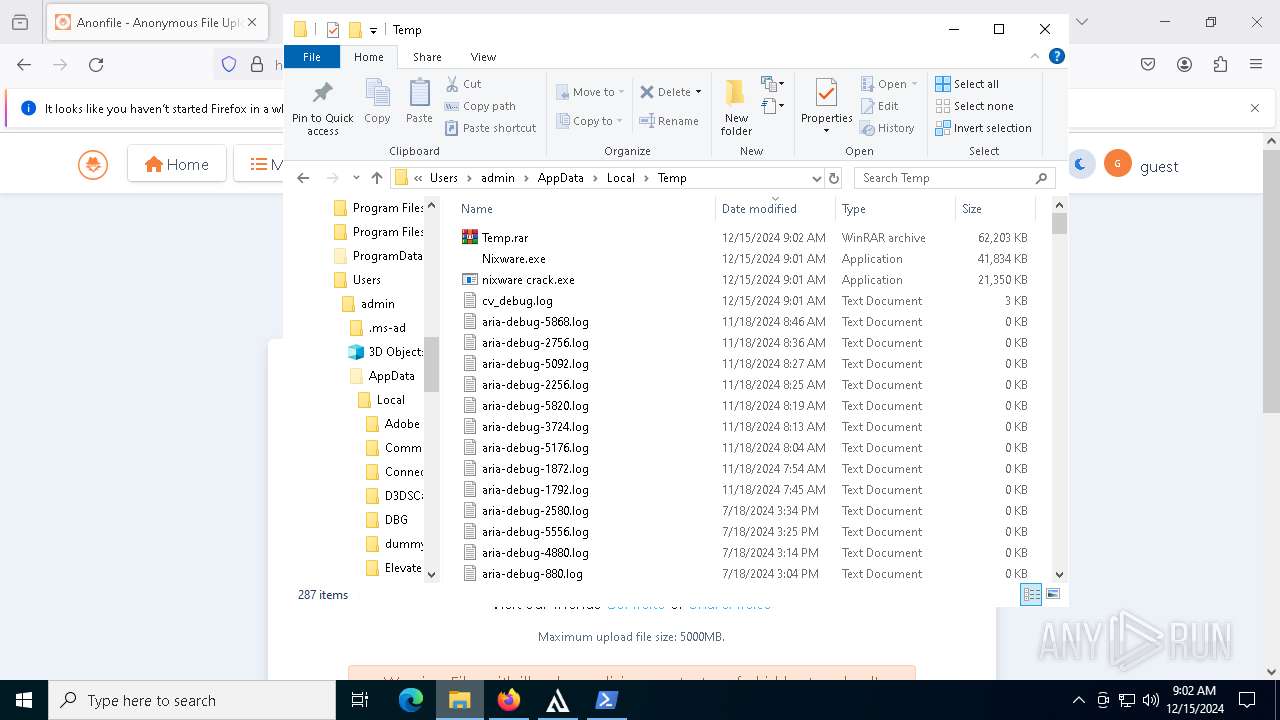
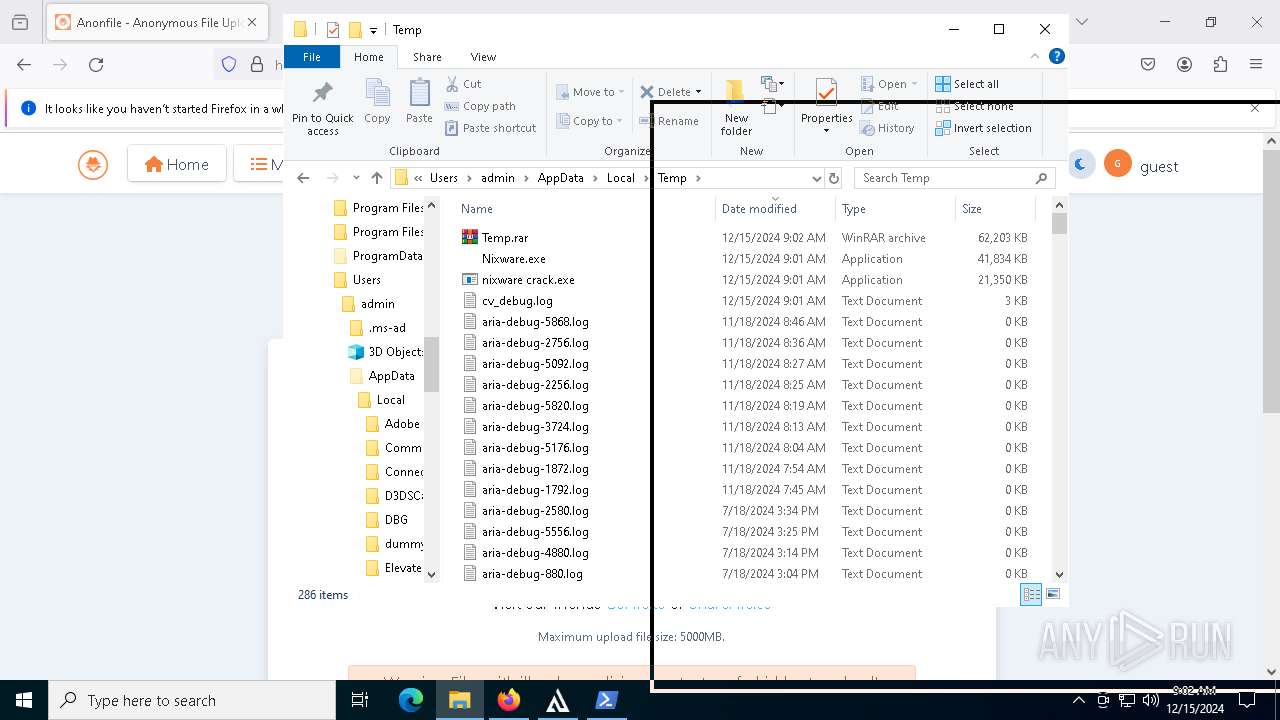
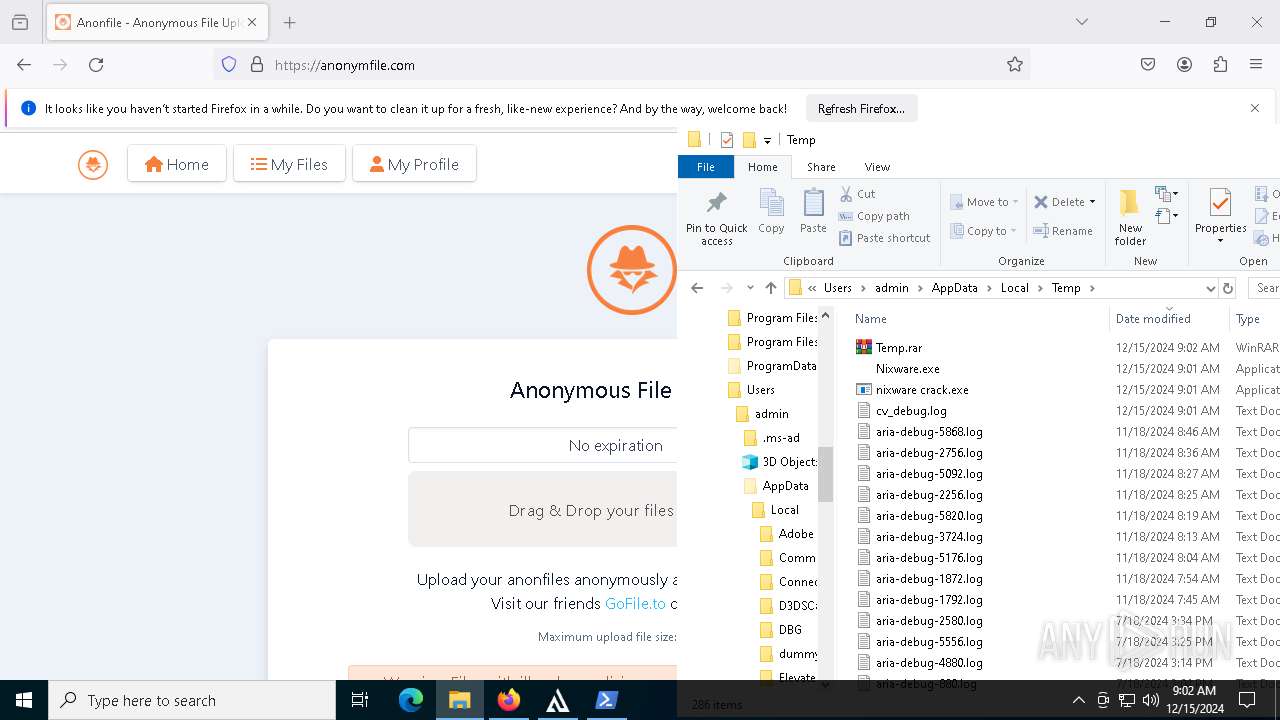
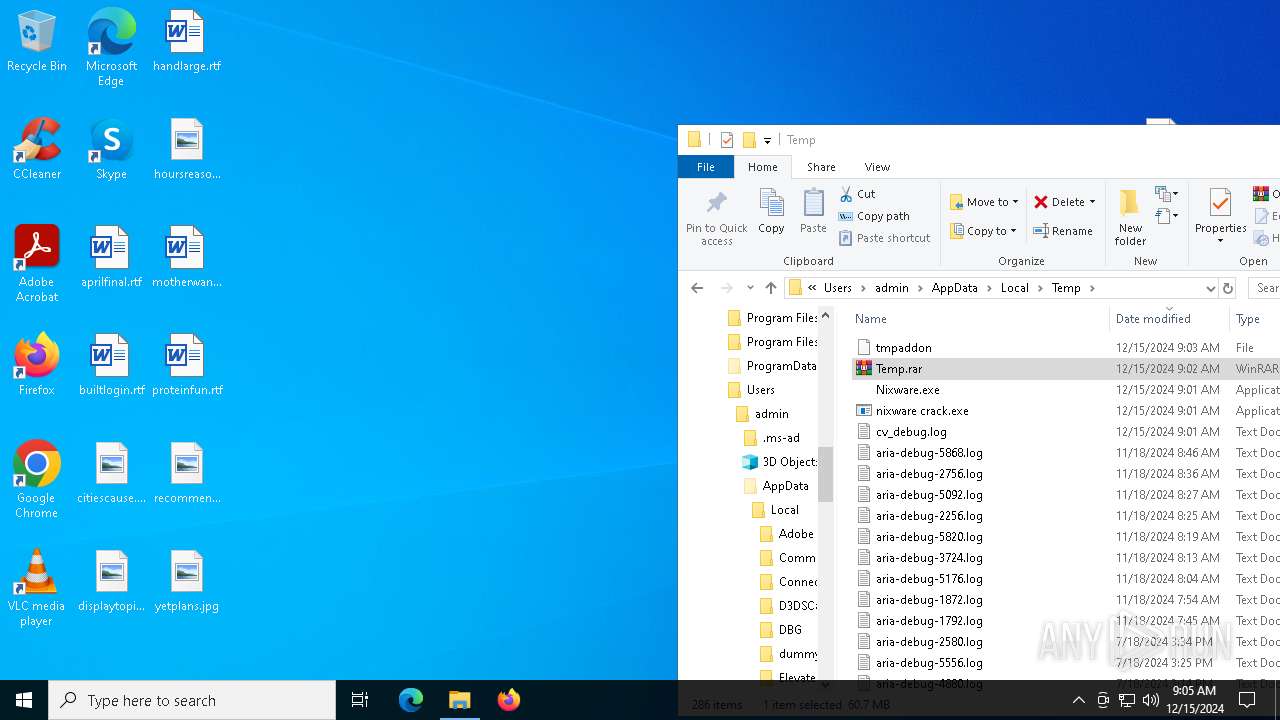
Executable content was dropped or overwritten
- Nixware.exe (PID: 7784)
- nixware crack.exe (PID: 7912)
- nixware crack.exe (PID: 7308)
The process drops C-runtime libraries
- nixware crack.exe (PID: 7308)
- Nixware.exe (PID: 7784)
Process drops legitimate windows executable
- nixware crack.exe (PID: 7308)
- Nixware.exe (PID: 7784)
Process drops python dynamic module
- Nixware.exe (PID: 7784)
- nixware crack.exe (PID: 7308)
Loads Python modules
- nixware crack.exe (PID: 7260)
- Nixware.exe (PID: 6404)
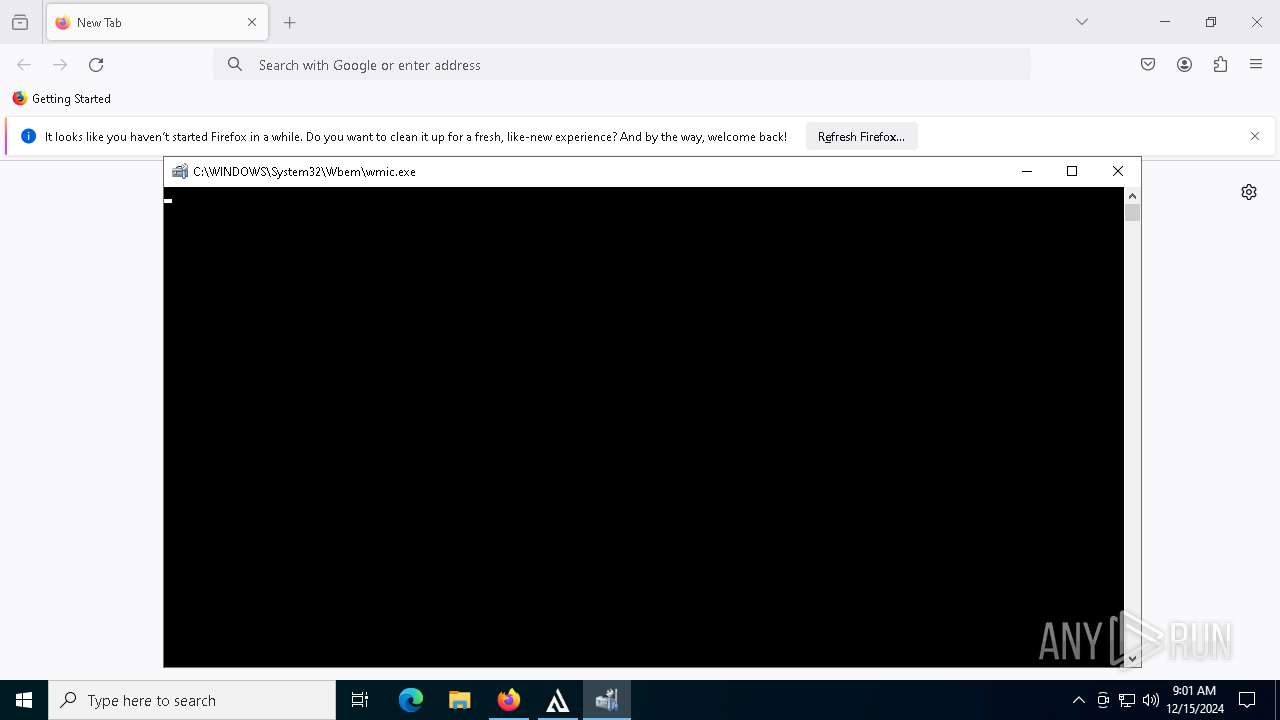
Uses WMIC.EXE to obtain Windows Installer data
- nixware crack.exe (PID: 7260)
Accesses product unique identifier via WMI (SCRIPT)
- WMIC.exe (PID: 6360)
Uses WMIC.EXE to obtain a list of video controllers
- nixware crack.exe (PID: 7260)
Accesses video controller name via WMI (SCRIPT)
- WMIC.exe (PID: 4596)
Uses SYSTEMINFO.EXE to read the environment
- nixware crack.exe (PID: 7260)
INFO
Application launched itself
- msedge.exe (PID: 6236)
- msedge.exe (PID: 7956)
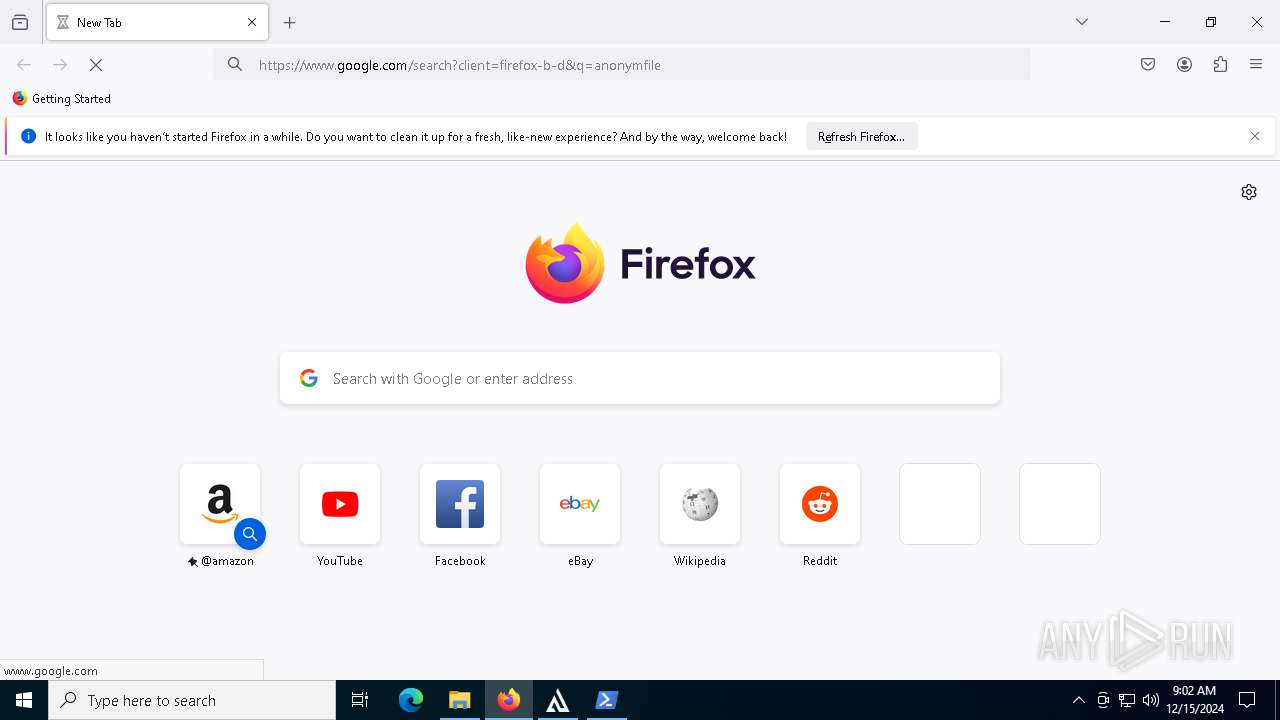
- firefox.exe (PID: 7364)
- firefox.exe (PID: 5628)
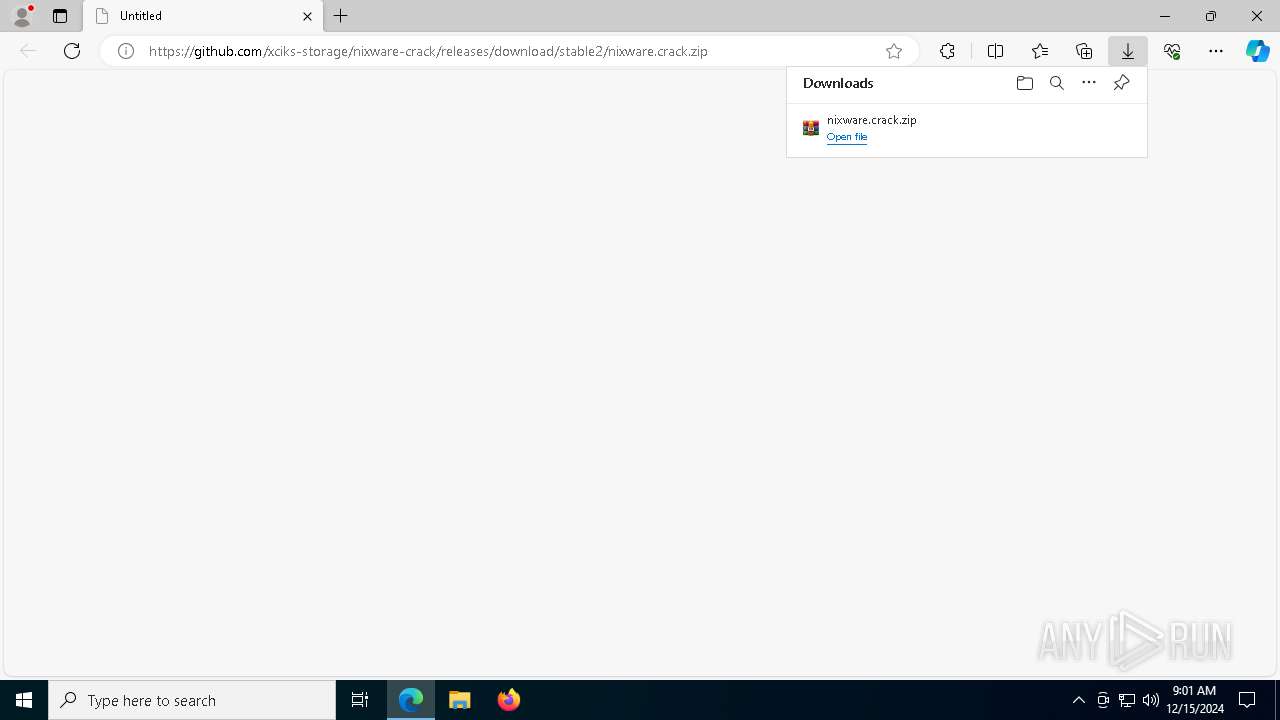
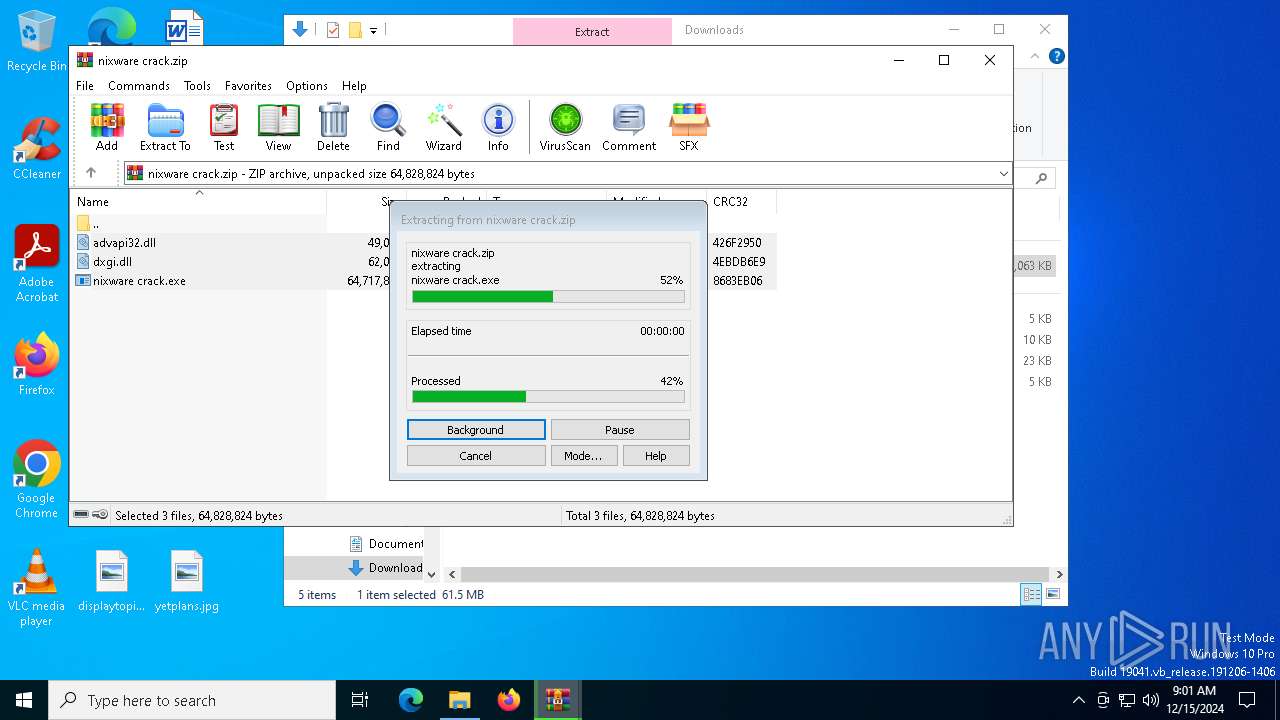
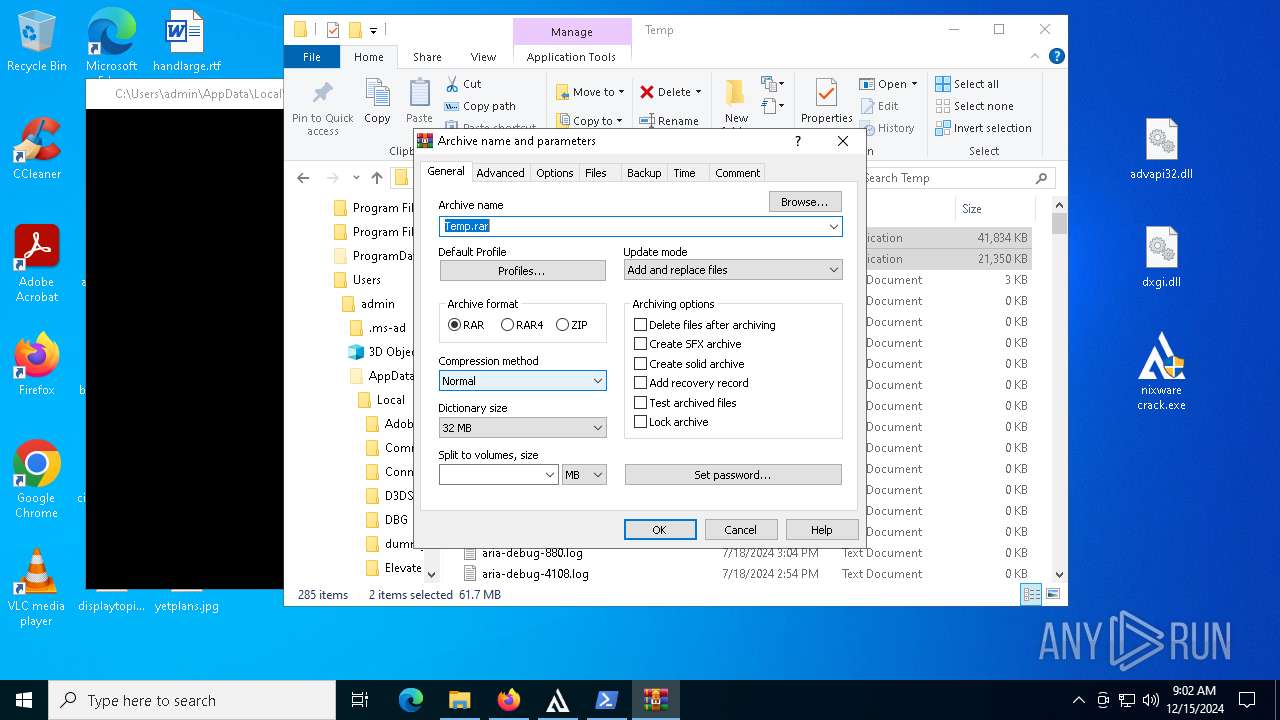
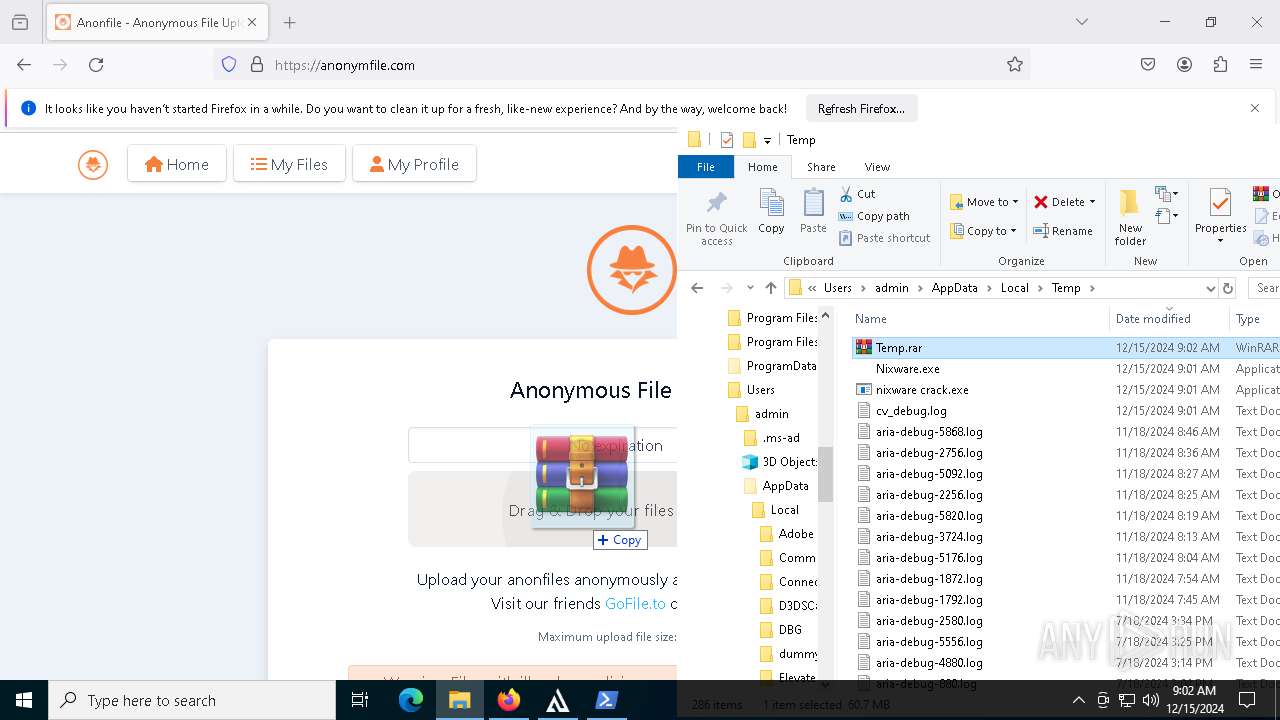
The process uses the downloaded file
- msedge.exe (PID: 5640)
- WinRAR.exe (PID: 3696)
- WinRAR.exe (PID: 4128)
- nixware crack.exe (PID: 7912)
- powershell.exe (PID: 7492)
Reads the computer name
- identity_helper.exe (PID: 7648)
- identity_helper.exe (PID: 3364)
- nixware crack.exe (PID: 7912)
- nixware crack.exe (PID: 7308)
- Nixware.exe (PID: 7784)
- nixware crack.exe (PID: 7260)
- Nixware.exe (PID: 6404)
Reads Environment values
- identity_helper.exe (PID: 3364)
- identity_helper.exe (PID: 7648)
Checks supported languages
- identity_helper.exe (PID: 3364)
- identity_helper.exe (PID: 7648)
- nixware crack.exe (PID: 7308)
- Nixware.exe (PID: 7784)
- nixware crack.exe (PID: 7912)
- nixware crack.exe (PID: 7260)
- Nixware.exe (PID: 6404)
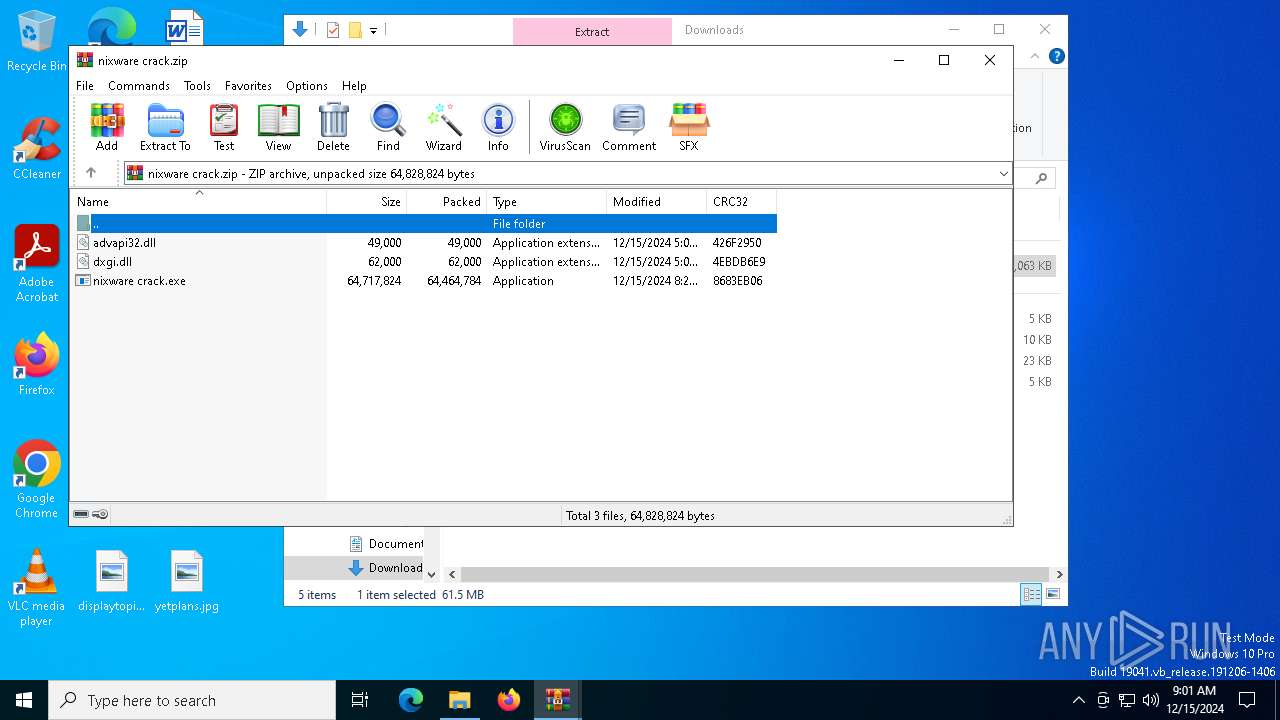
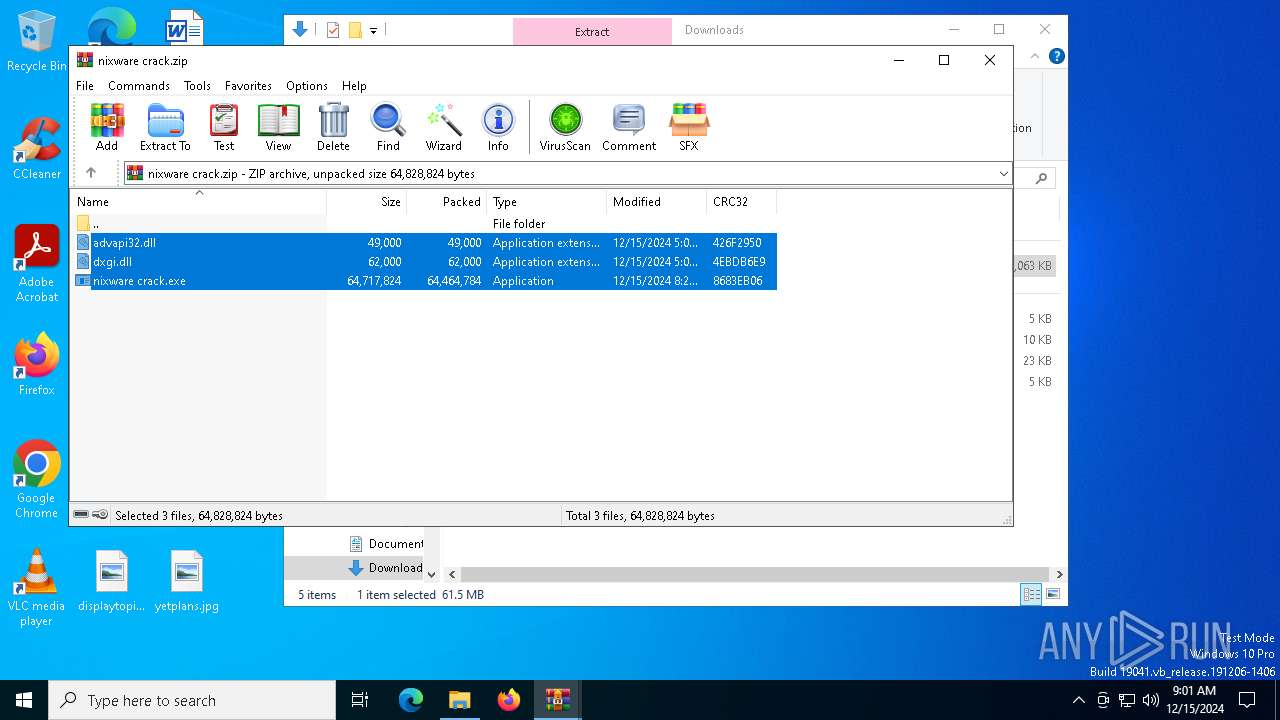
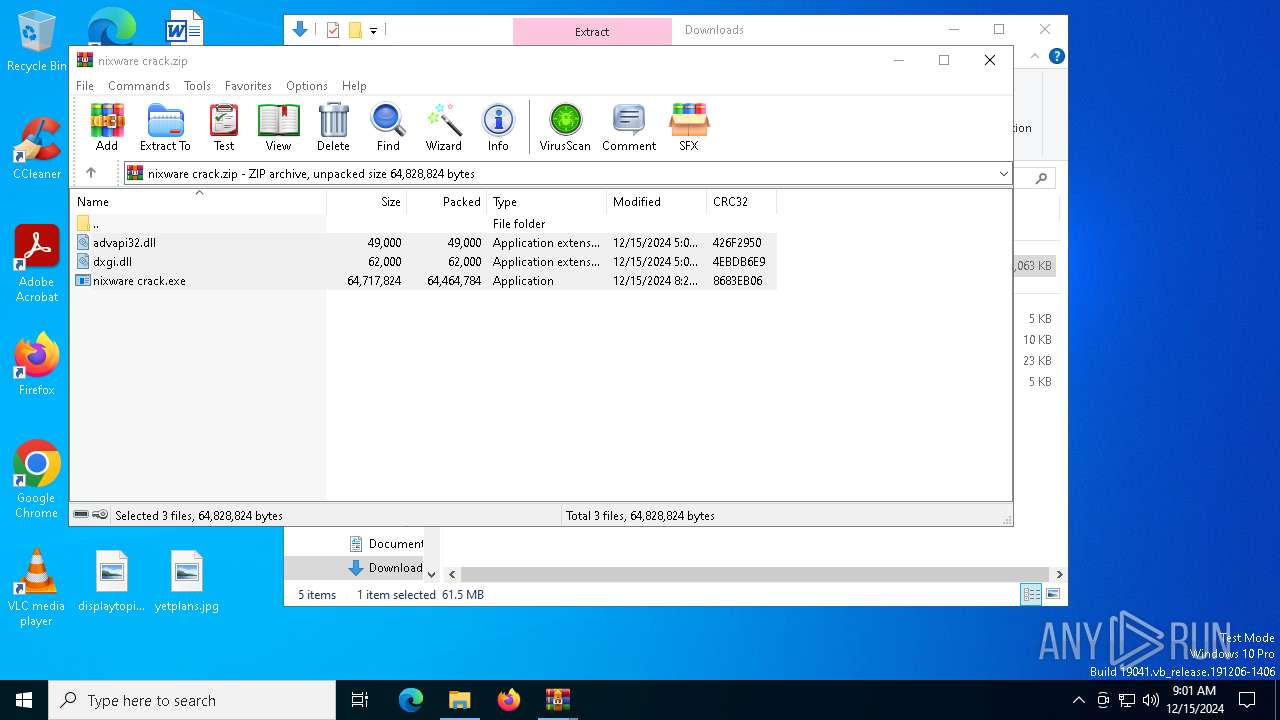
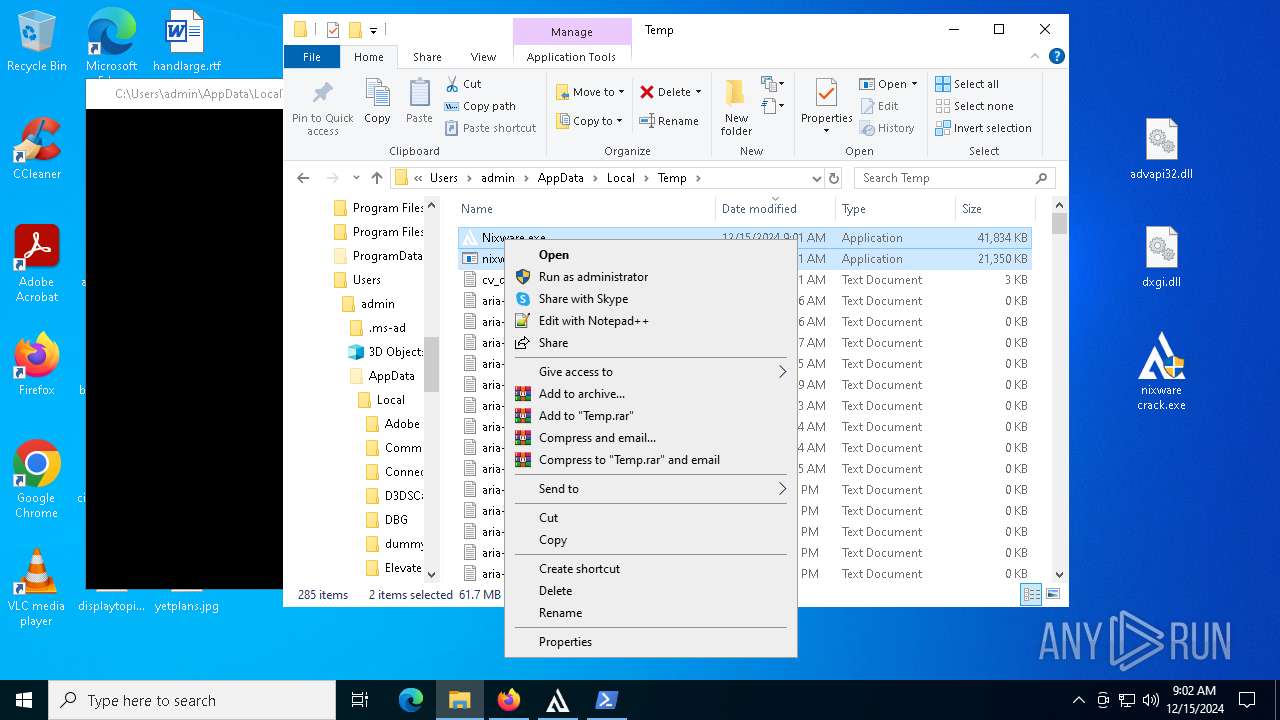
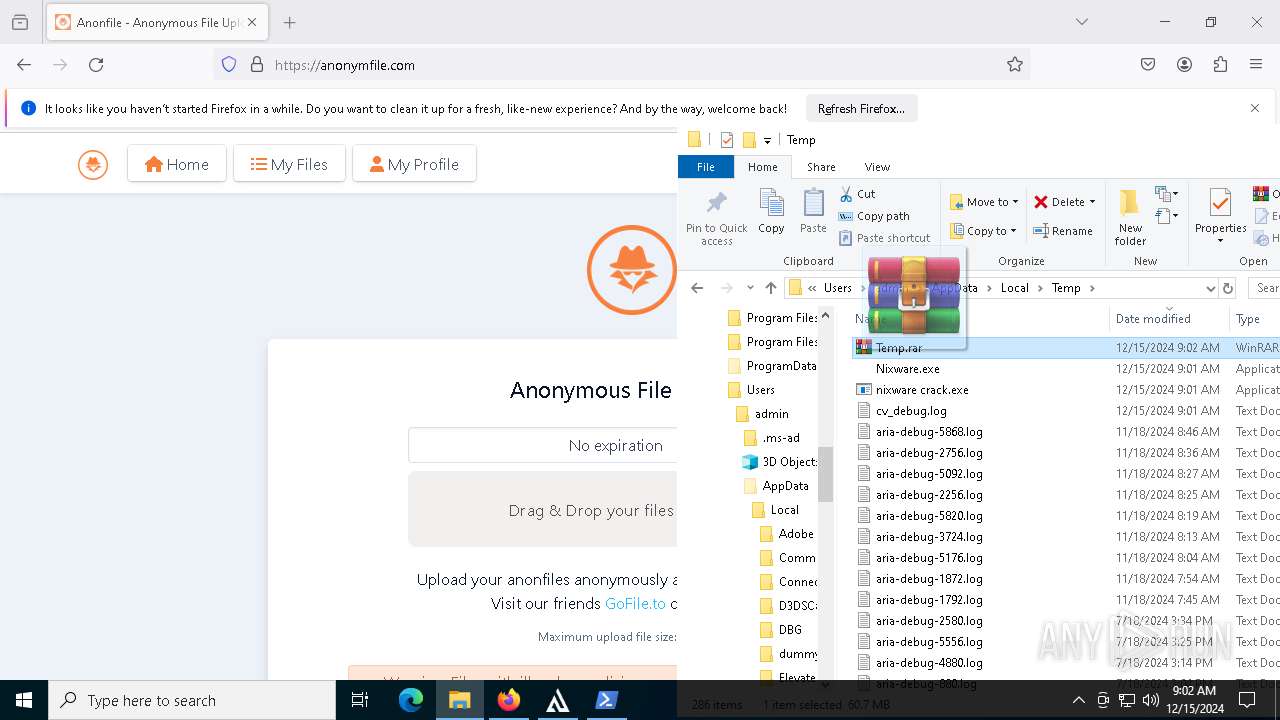
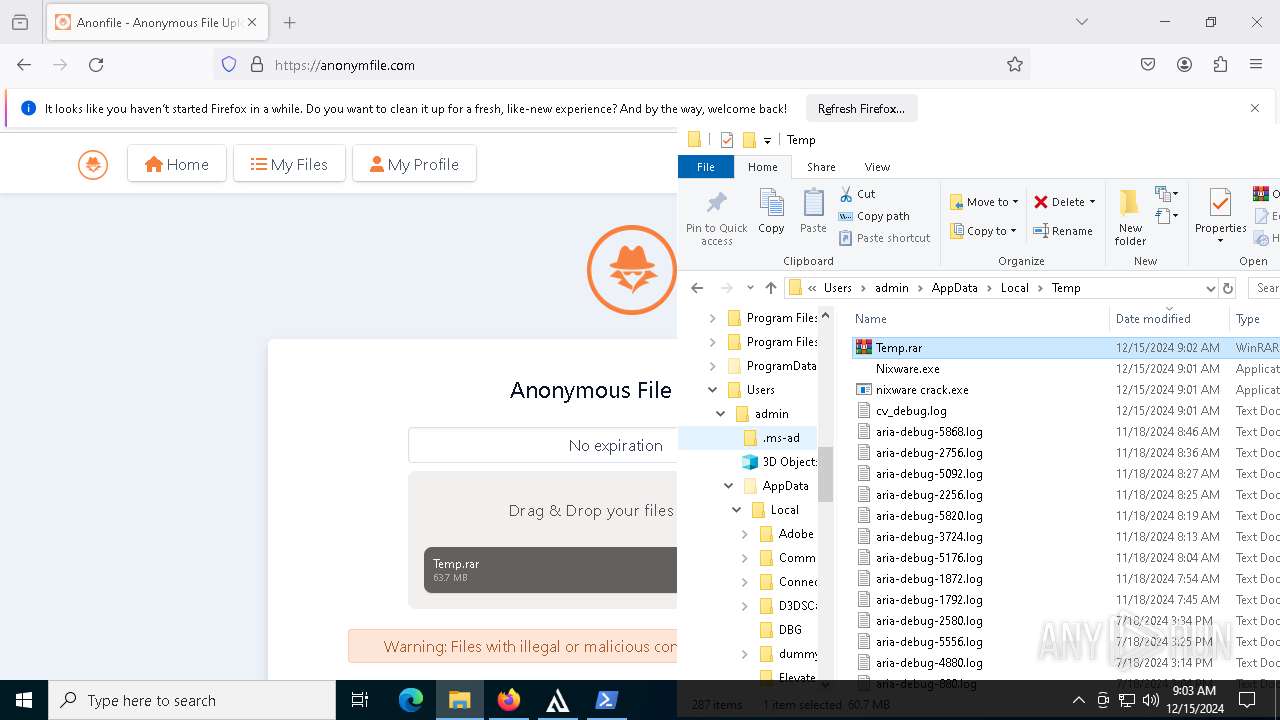
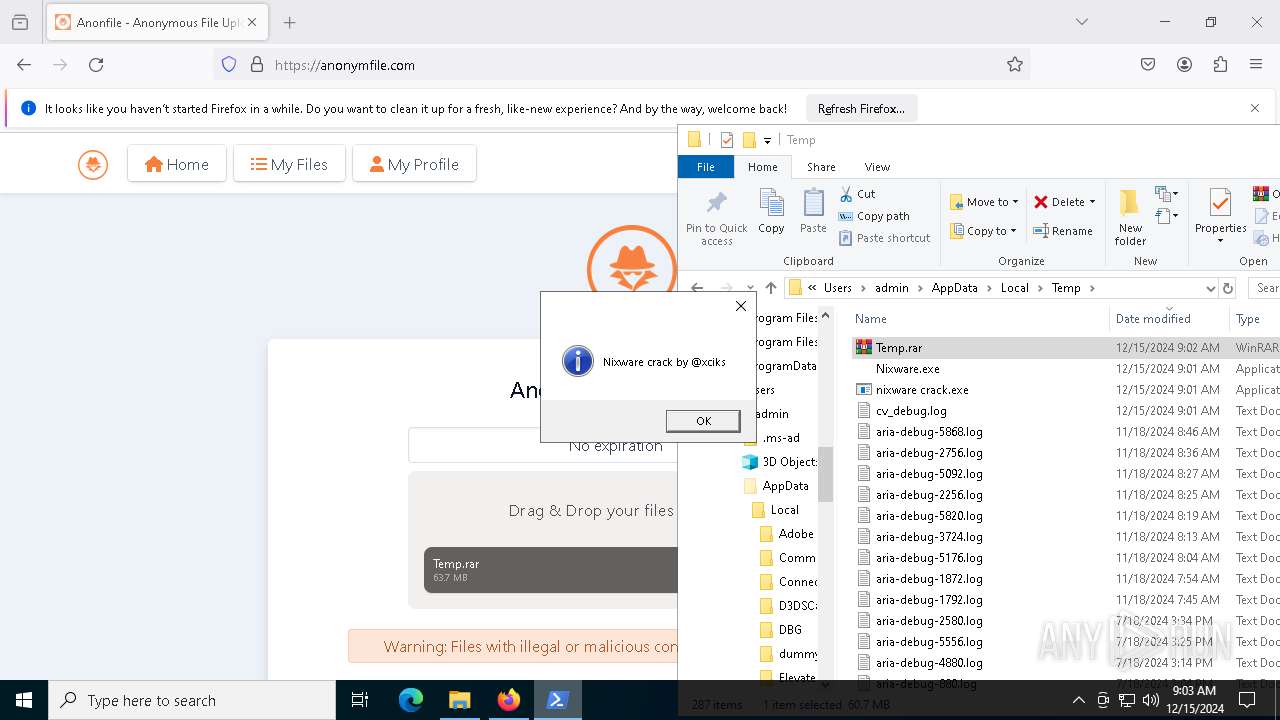
Manual execution by a user
- WinRAR.exe (PID: 4128)
- nixware crack.exe (PID: 7068)
- nixware crack.exe (PID: 7912)
- firefox.exe (PID: 7364)
- WinRAR.exe (PID: 7408)
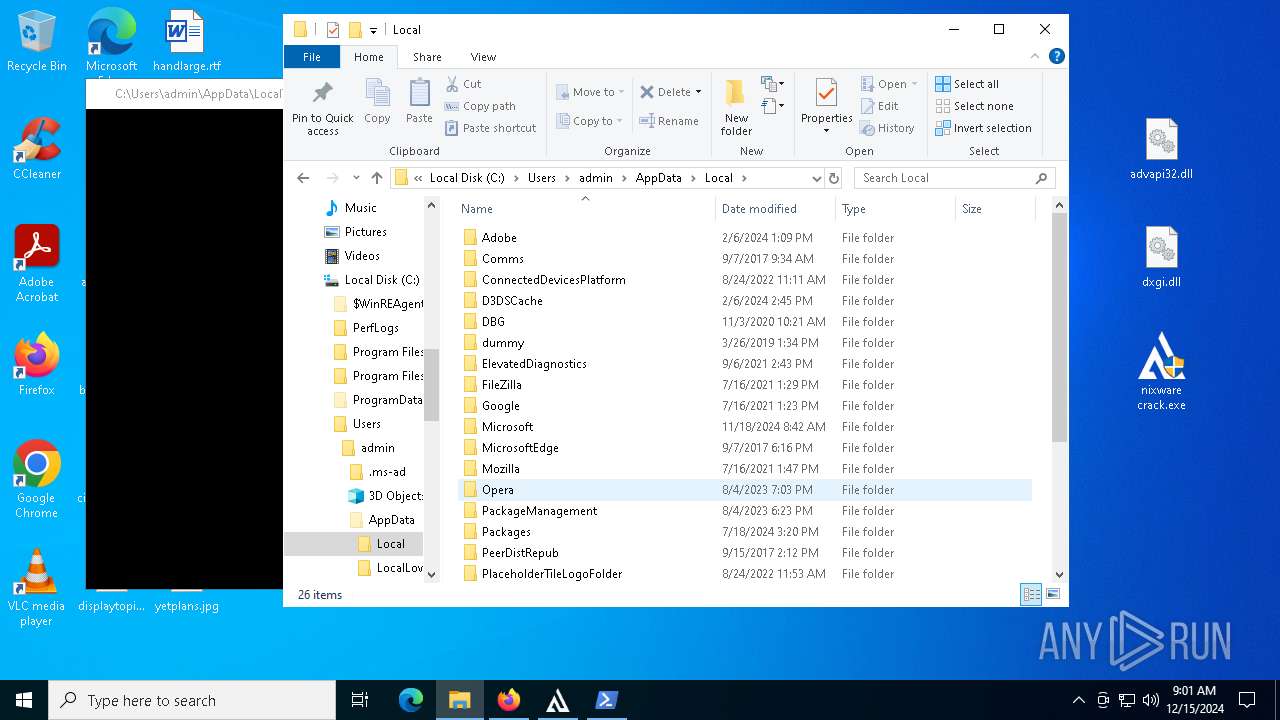
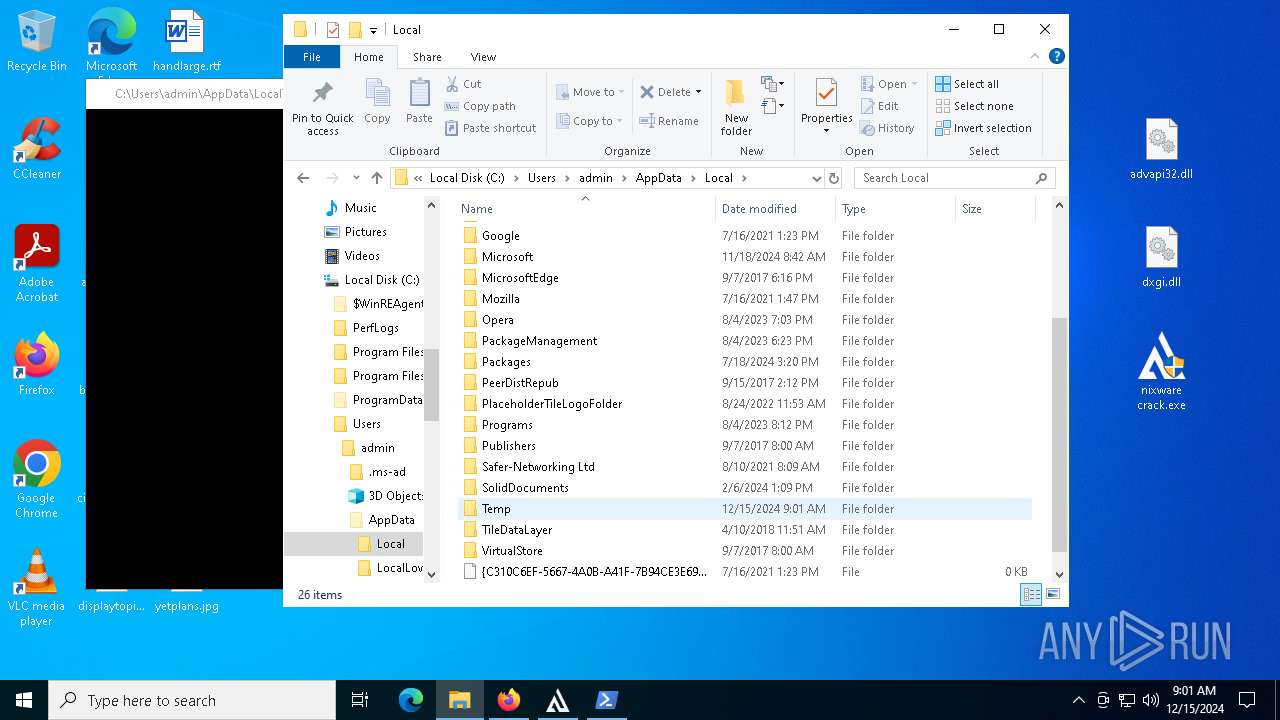
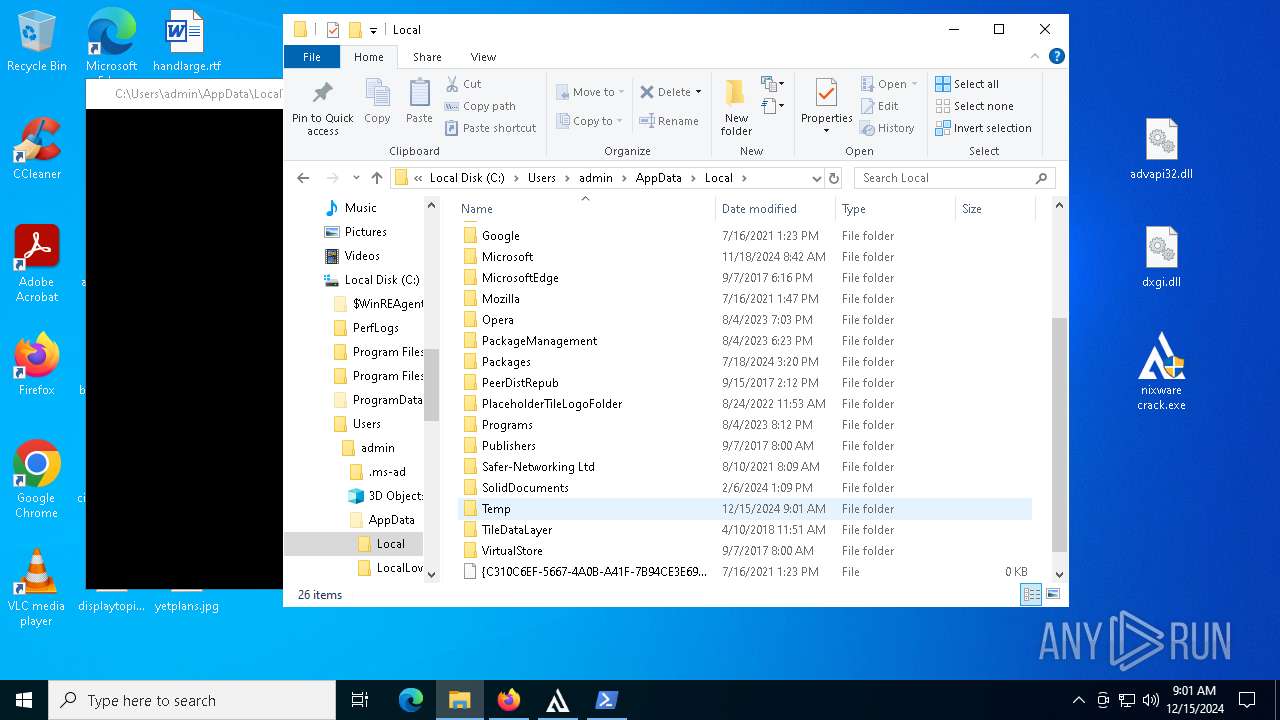
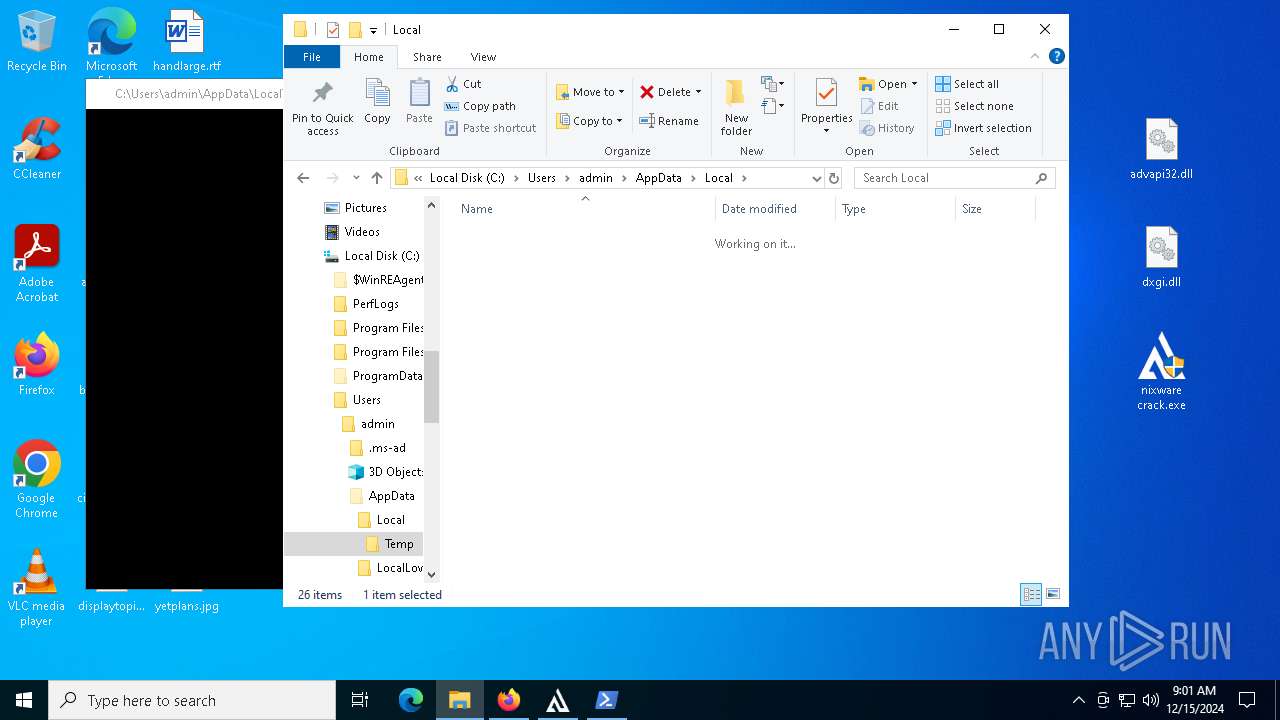
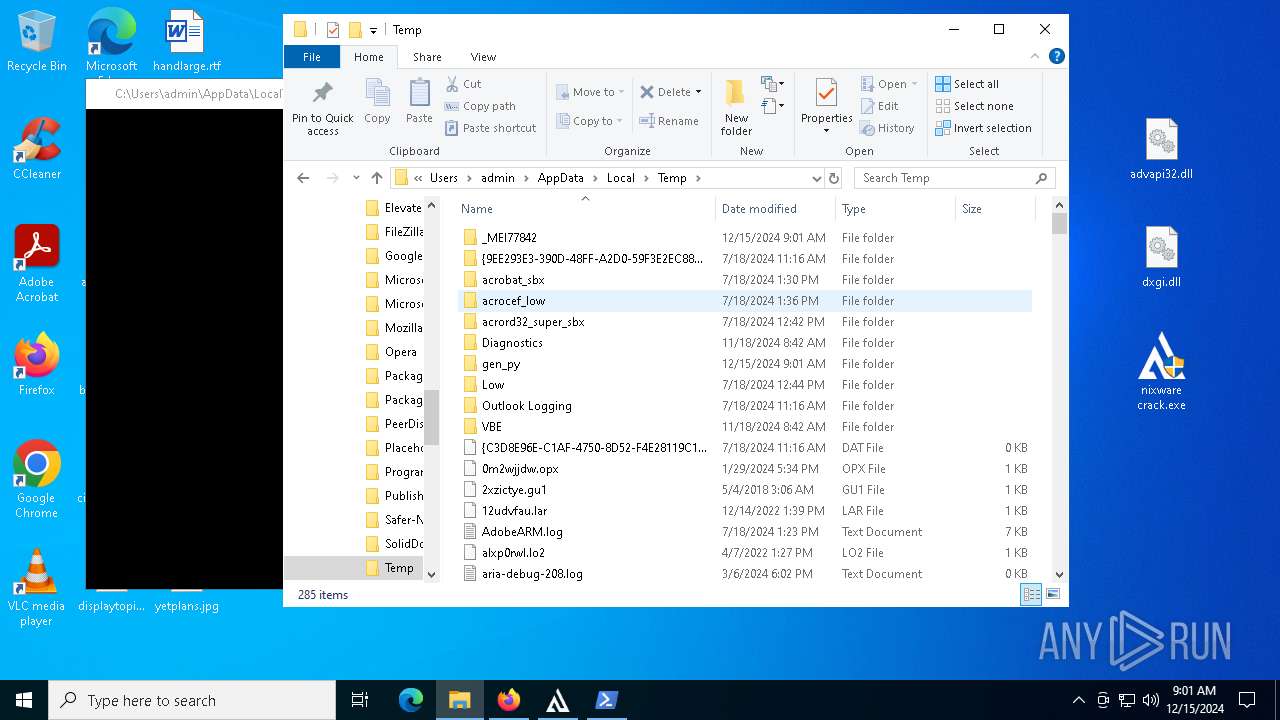
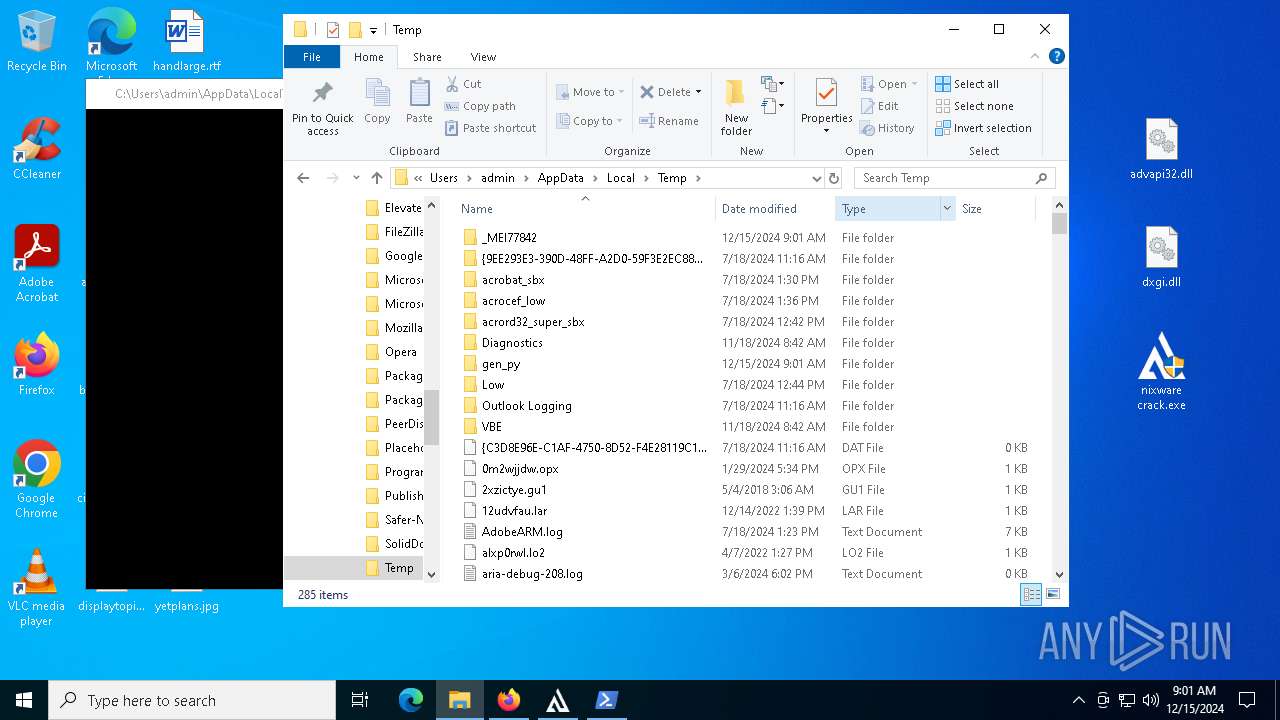
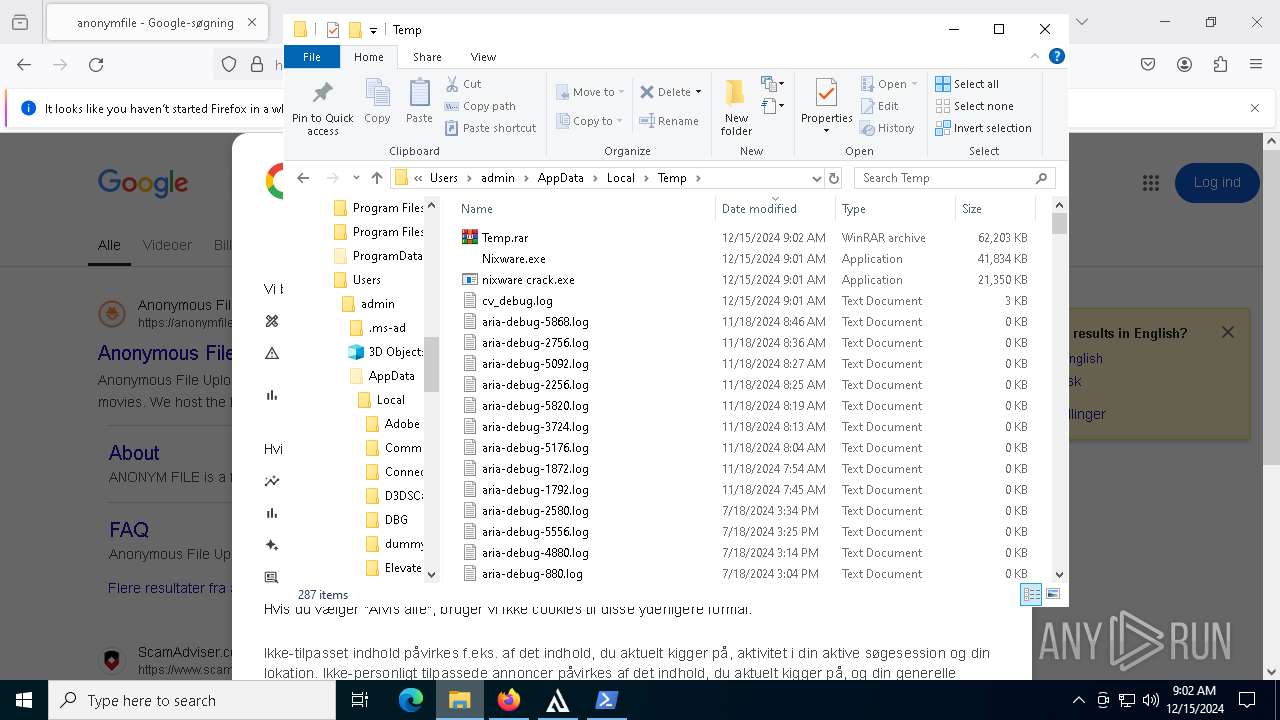
Create files in a temporary directory
- nixware crack.exe (PID: 7308)
- nixware crack.exe (PID: 7912)
- Nixware.exe (PID: 7784)
- nixware crack.exe (PID: 7260)
The sample compiled with english language support
- nixware crack.exe (PID: 7308)
- Nixware.exe (PID: 7784)
- msedge.exe (PID: 7612)
Process checks computer location settings
- nixware crack.exe (PID: 7912)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 4596)
- WMIC.exe (PID: 6360)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7492)
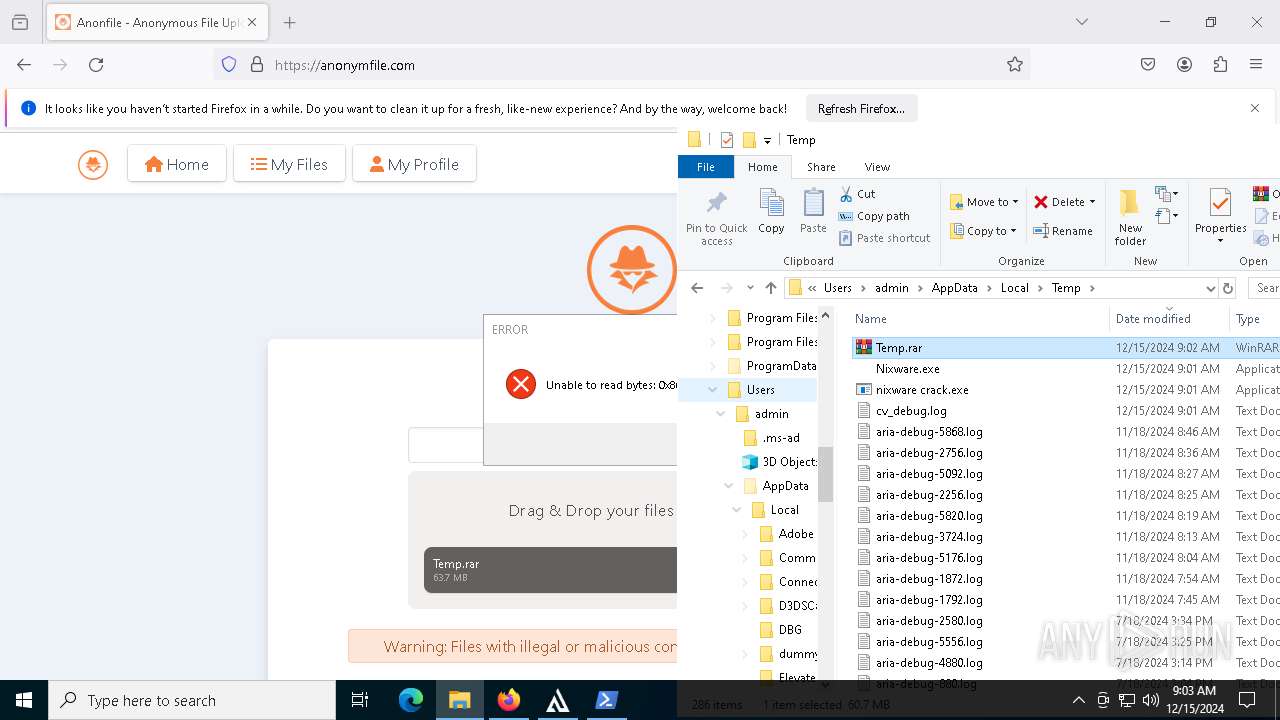
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7492)
Found Base64 encoded reflection usage via PowerShell (YARA)
- powershell.exe (PID: 7424)
PyInstaller has been detected (YARA)
- Nixware.exe (PID: 7784)
Executable content was dropped or overwritten
- firefox.exe (PID: 5628)
- msedge.exe (PID: 7612)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
232
Monitored processes
98
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 936 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | WMIC.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1200 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5372 --field-trial-handle=2240,i,17220903467859138591,3647384376662284553,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1304 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3688 --field-trial-handle=2240,i,17220903467859138591,3647384376662284553,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1988 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=4312 --field-trial-handle=2240,i,17220903467859138591,3647384376662284553,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2040 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3516 --field-trial-handle=2240,i,17220903467859138591,3647384376662284553,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2132 | C:\WINDOWS\winsxs\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe -Embedding | C:\Windows\WinSxS\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Modules Installer Worker Exit code: 0 Version: 10.0.19041.3989 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2828 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5216 --field-trial-handle=2240,i,17220903467859138591,3647384376662284553,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3052 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4348 --field-trial-handle=2240,i,17220903467859138591,3647384376662284553,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3128 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=6192 -childID 10 -isForBrowser -prefsHandle 6176 -prefMapHandle 4420 -prefsLen 32105 -prefMapSize 244583 -jsInitHandle 1500 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {21bb0c0b-1e7a-4820-85f2-b837b49596a4} 5628 "\\.\pipe\gecko-crash-server-pipe.5628" 1e60ced7f50 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 3364 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=4312 --field-trial-handle=2240,i,17220903467859138591,3647384376662284553,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
43 596
Read events
43 527
Write events
69
Delete events
0
Modification events
| (PID) Process: | (6236) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 143C0695E1872F00 | |||
| (PID) Process: | (6236) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328402 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {3BB6D5A8-8E0E-4B4F-8C41-A3B1269BB2F2} | |||
| (PID) Process: | (6236) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328402 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {59555075-77D1-40B1-B14E-E76034EADF47} | |||
| (PID) Process: | (6236) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6236) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6236) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6236) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6236) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 3211FA94E1872F00 | |||
| (PID) Process: | (6236) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: E4CF6C95E1872F00 | |||
| (PID) Process: | (6236) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\Profiles |
| Operation: | write | Name: | EnhancedLinkOpeningDefault |
Value: Default | |||
Executable files
233
Suspicious files
1 184
Text files
1 164
Unknown types
49
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6236 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1353b1.TMP | — | |
MD5:— | SHA256:— | |||
| 6236 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6236 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1353c1.TMP | — | |
MD5:— | SHA256:— | |||
| 6236 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6236 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1353b1.TMP | — | |
MD5:— | SHA256:— | |||
| 6236 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6236 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1353c1.TMP | — | |
MD5:— | SHA256:— | |||
| 6236 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6236 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1353c1.TMP | — | |
MD5:— | SHA256:— | |||
| 6236 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
84
TCP/UDP connections
184
DNS requests
207
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5872 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6832 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5872 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5628 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
5628 | firefox.exe | POST | 200 | 142.250.181.227:80 | http://o.pki.goog/wr2 | unknown | — | — | whitelisted |
5628 | firefox.exe | POST | 200 | 142.250.181.227:80 | http://o.pki.goog/s/wr3/yvU | unknown | — | — | whitelisted |
5628 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4328 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 104.126.37.153:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6236 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
github.com |
| shared |
business.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
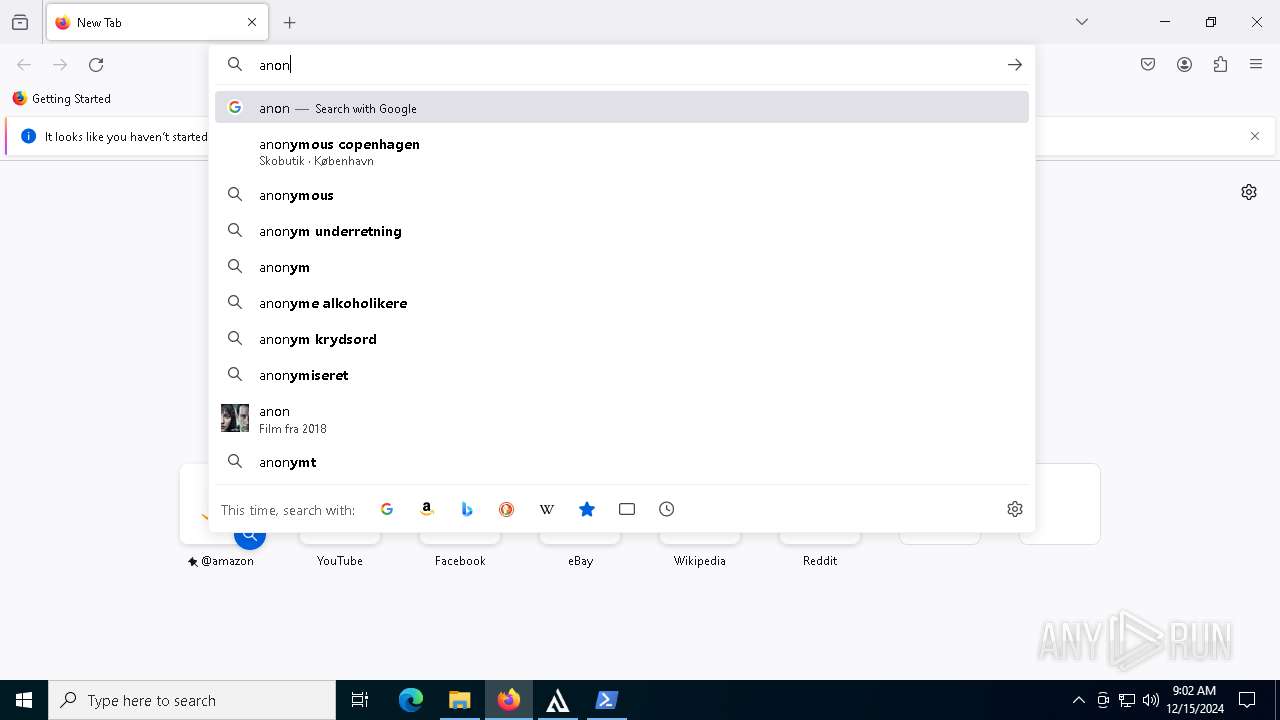
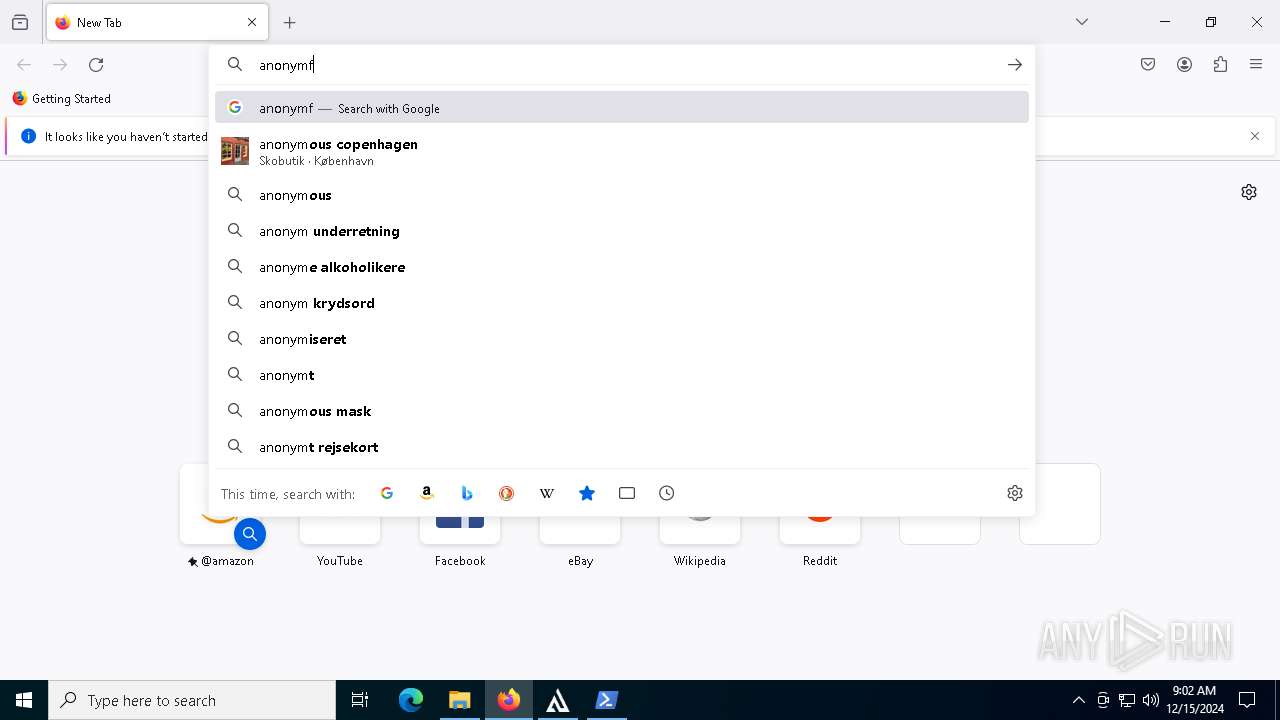
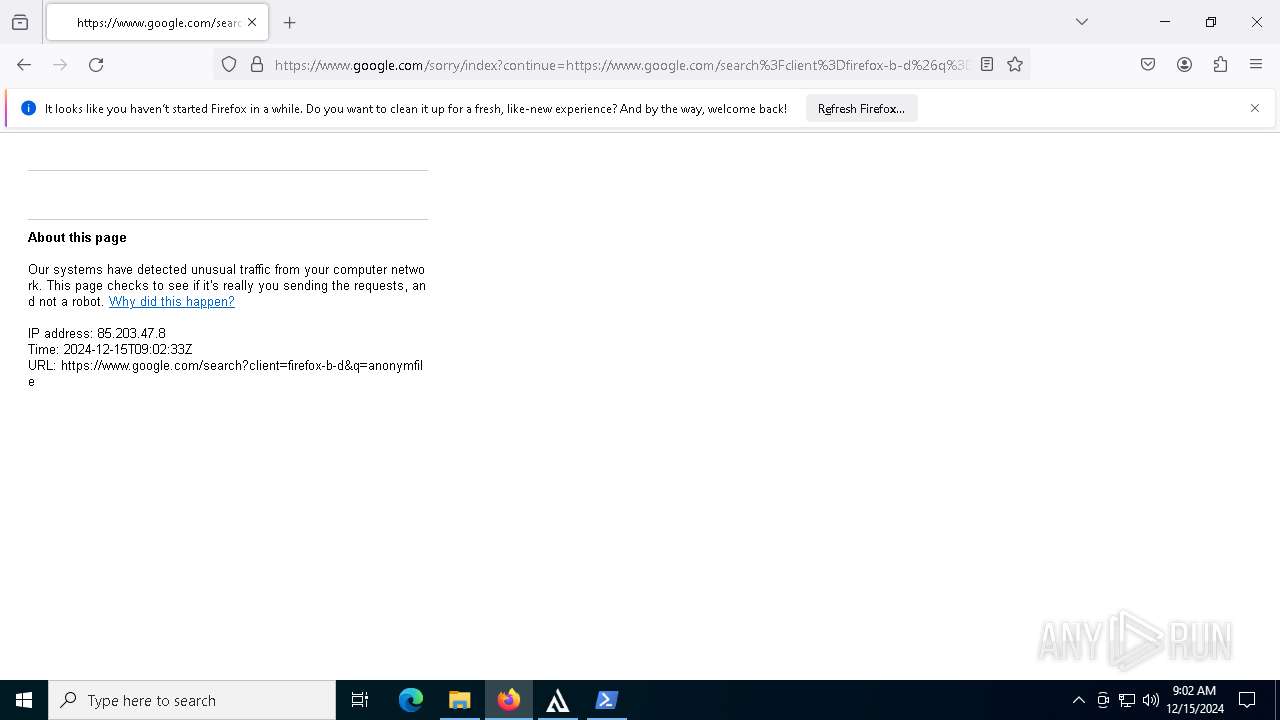
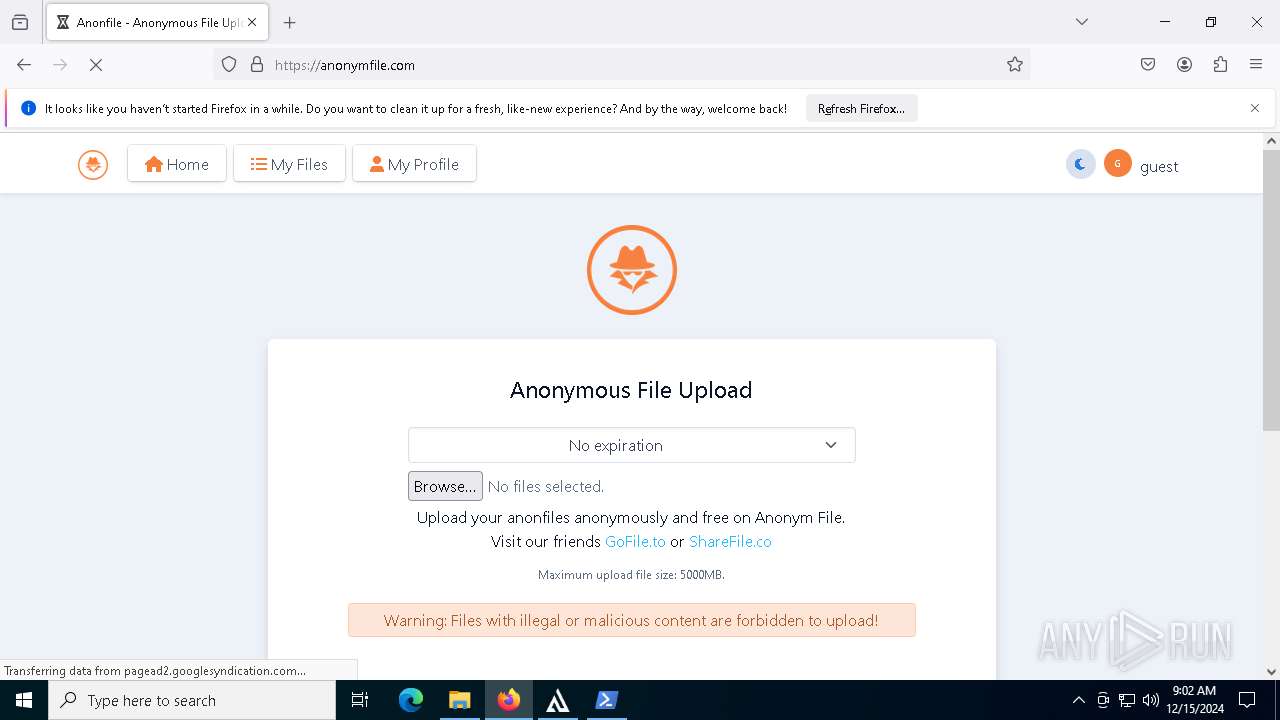
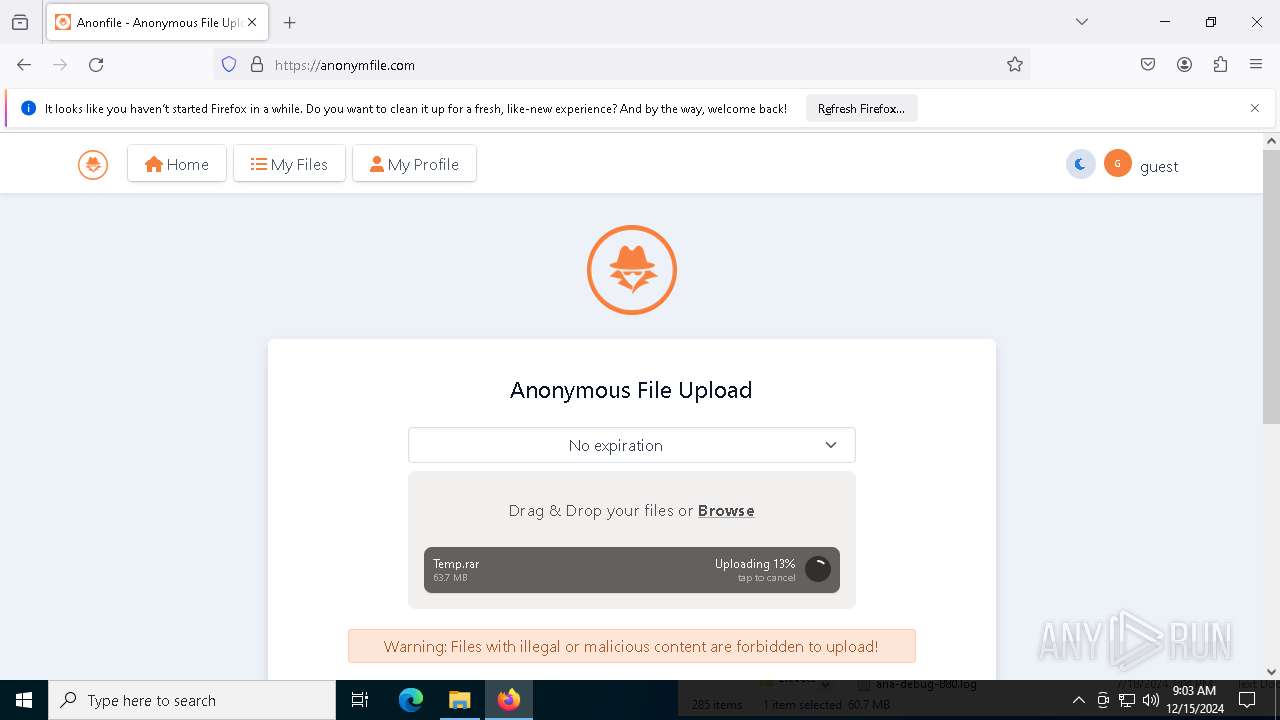
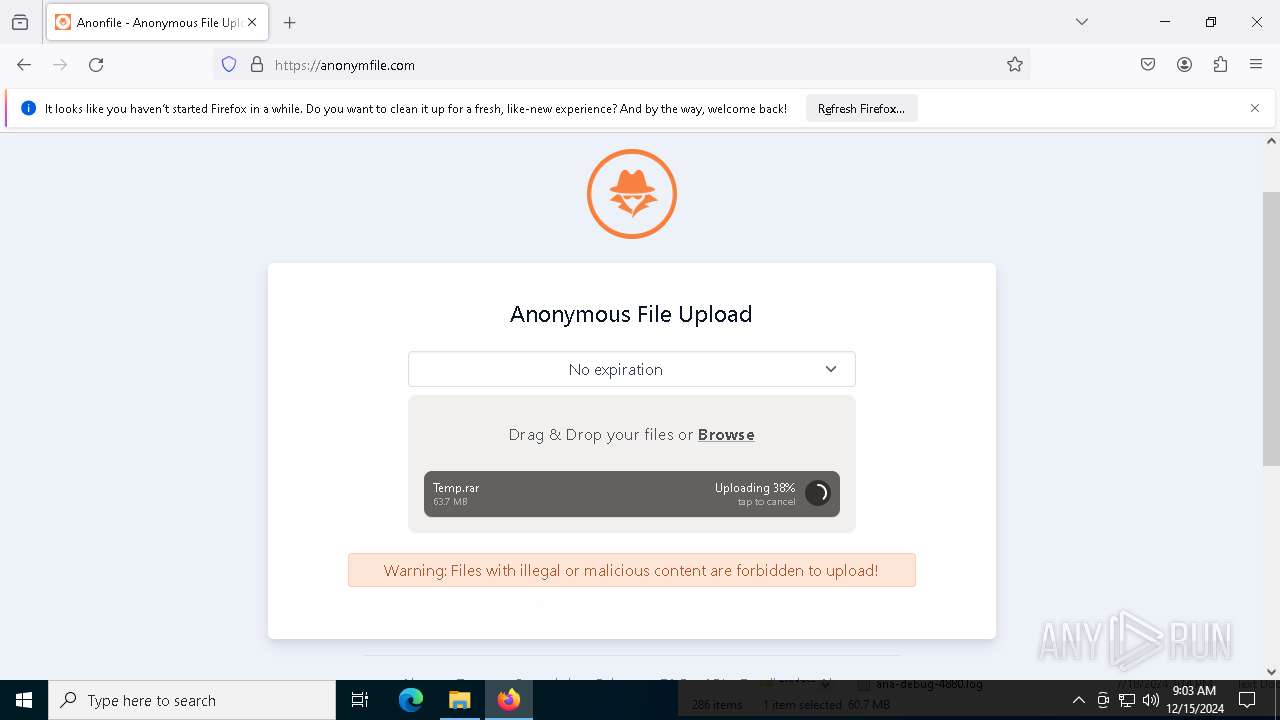
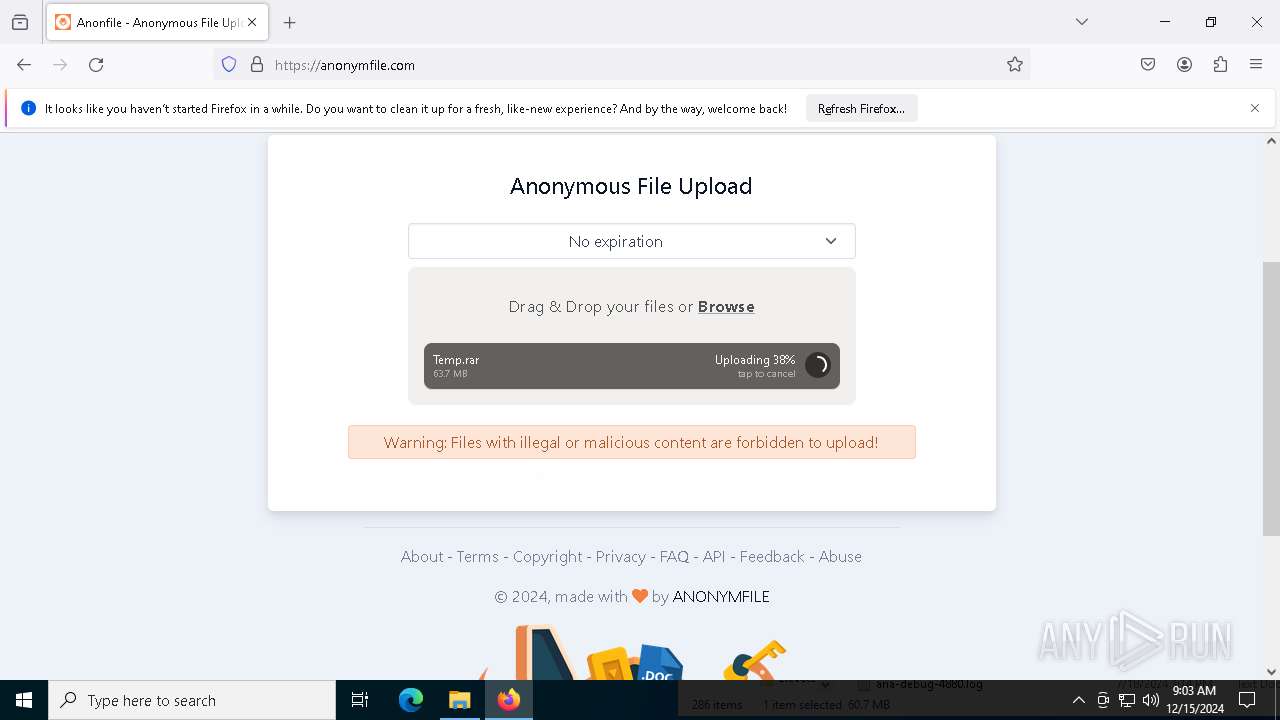
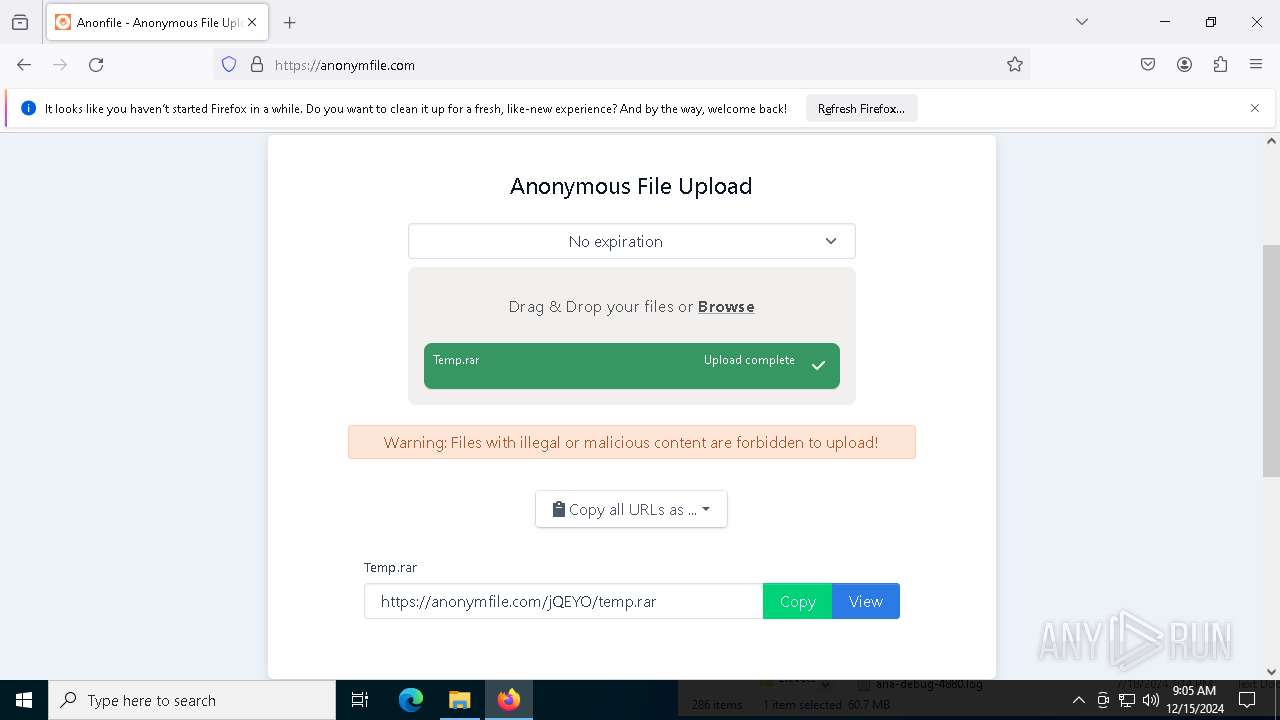
2192 | svchost.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (anonymfile .com) |
2192 | svchost.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (anonymfile .com) |
2192 | svchost.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (anonymfile .com) |
5628 | firefox.exe | Misc activity | ET INFO File Sharing Domain Observed in TLS SNI (anonymfile .com) |
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Global content delivery network (unpkg .com) |
5628 | firefox.exe | Misc activity | ET INFO File Sharing Domain Observed in TLS SNI (anonymfile .com) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Global content delivery network (unpkg .com) |