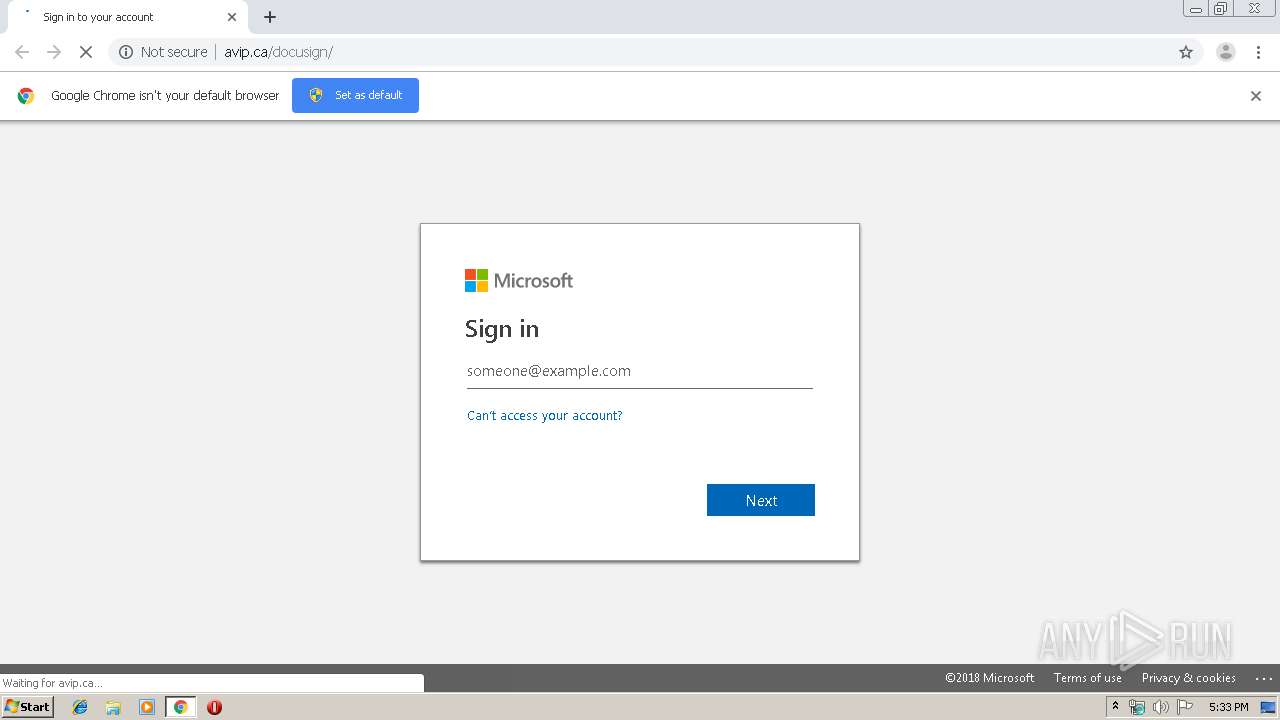
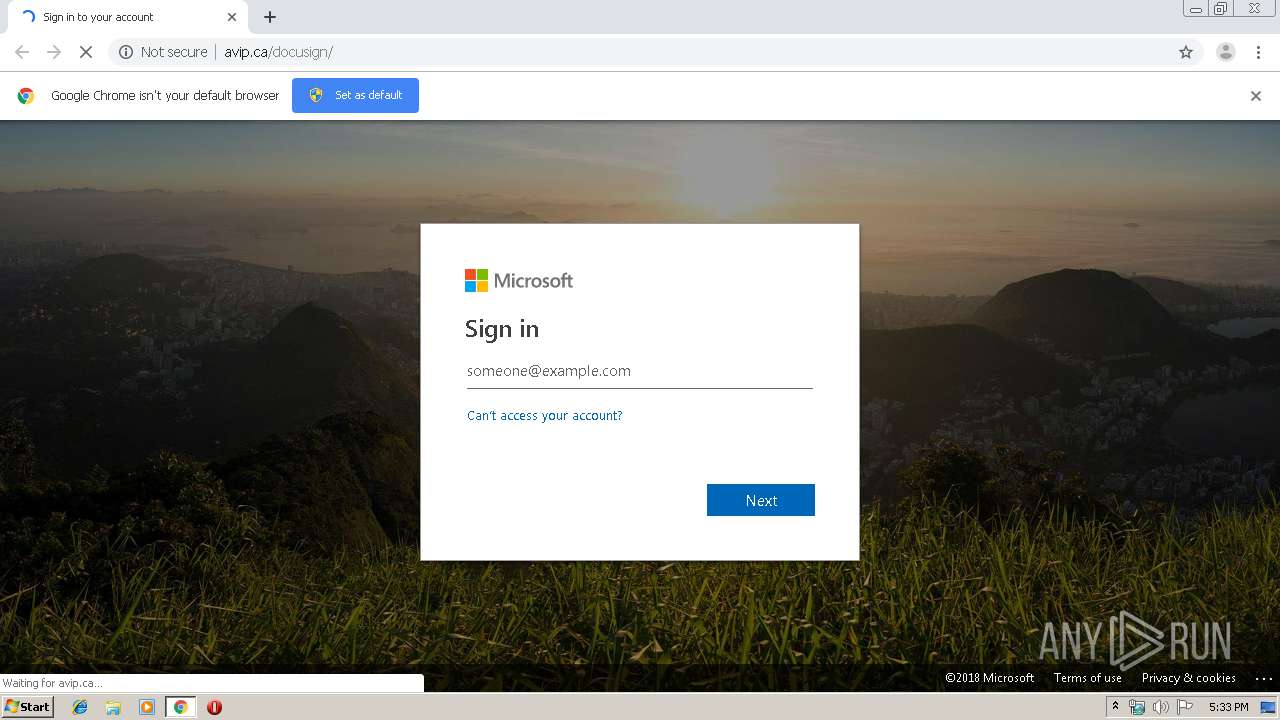
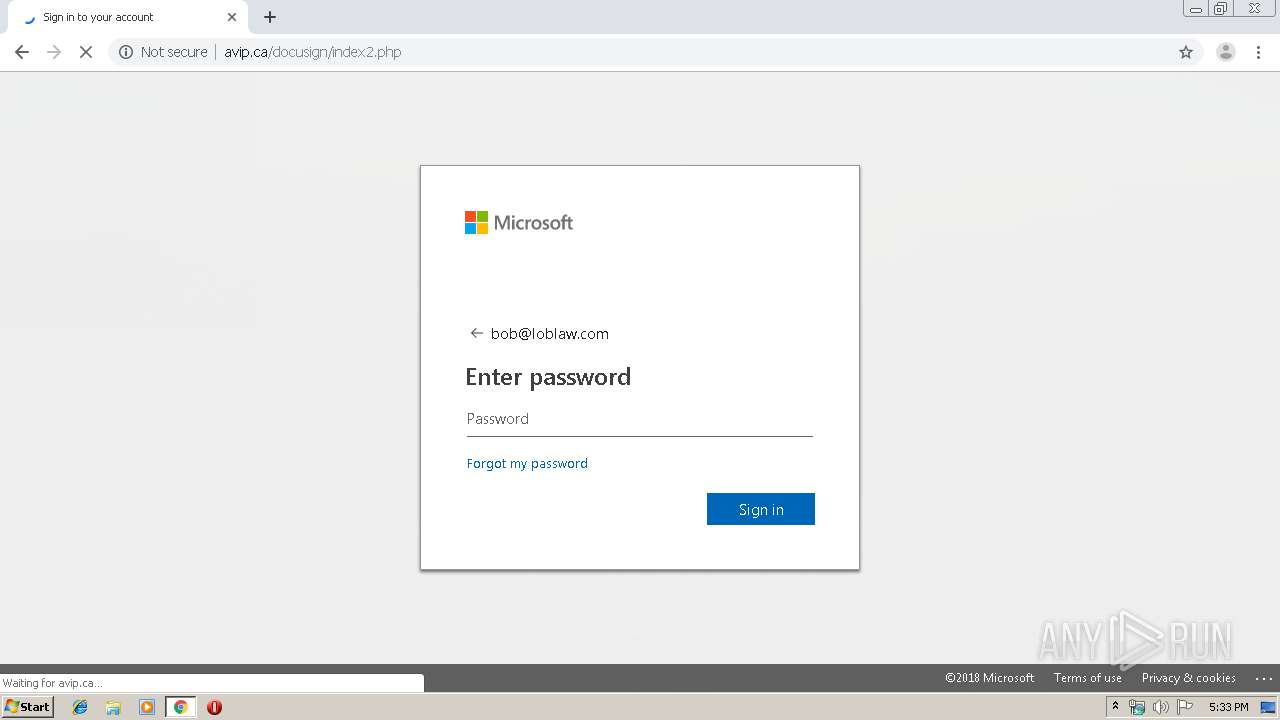
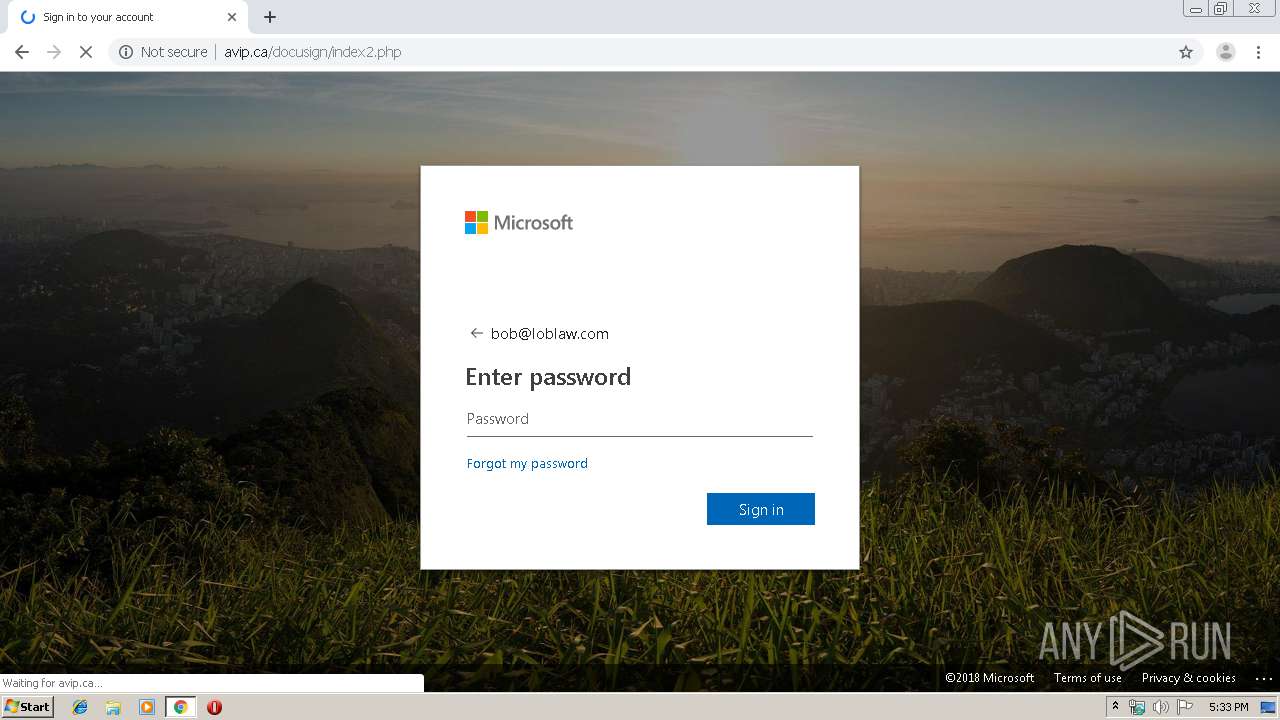
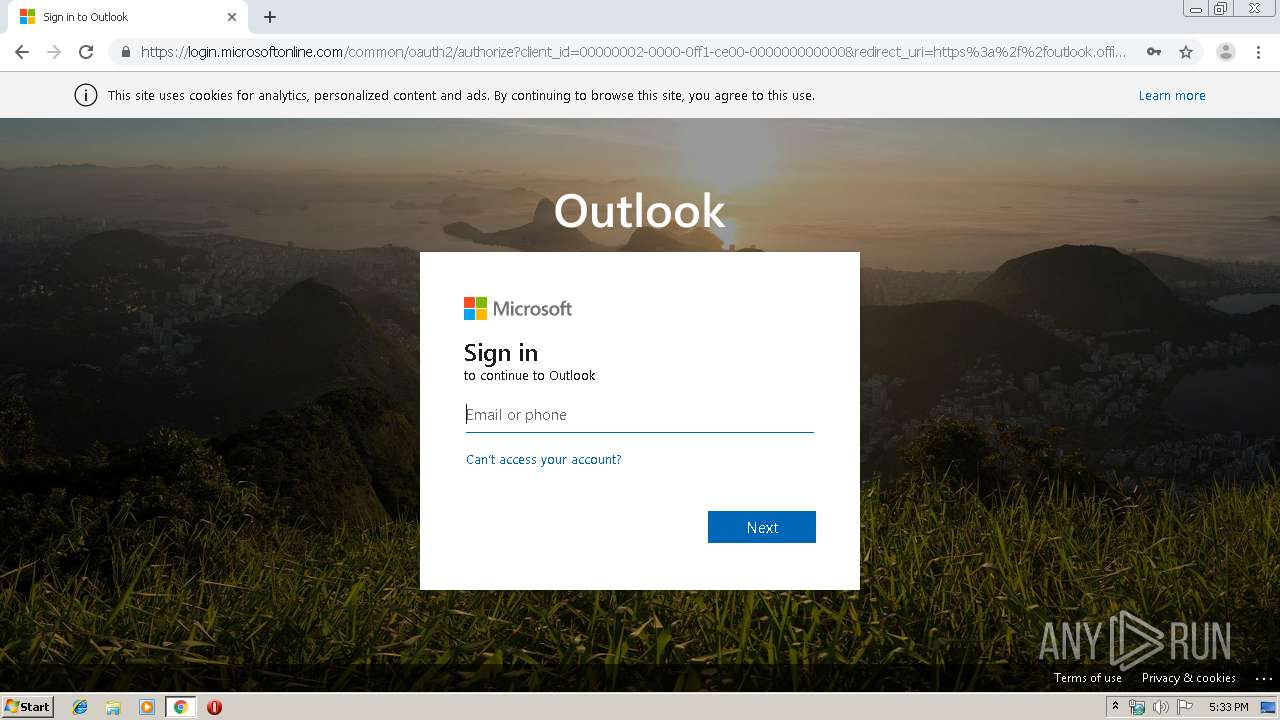
| URL: | http://avip.ca/docusign/ |
| Full analysis: | https://app.any.run/tasks/d4250e3c-4d70-4d93-9618-943f77b1b54b |
| Verdict: | Malicious activity |
| Analysis date: | October 09, 2019, 16:33:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | A5D0D8C52BA5B05407147376279E0350 |
| SHA1: | 181EA89C2445D34978964616106017A43C6FCE90 |
| SHA256: | AD8CBCE3575F23E6D8D9A42D20600F2C943F131471CE7A6946A9B354D1131264 |
| SSDEEP: | 3:N1KfAse:CZe |
MALICIOUS
Loads Microsoft favicon from HTTP
- chrome.exe (PID: 1136)
Microsoft phishing was detected
- chrome.exe (PID: 1136)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3088)
INFO
Reads the hosts file
- chrome.exe (PID: 3088)
- chrome.exe (PID: 1136)
Application launched itself
- chrome.exe (PID: 3088)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
60
Monitored processes
26
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,9071438225451997203,8108427640440313636,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12441316048299275457 --mojo-platform-channel-handle=4036 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1100 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,9071438225451997203,8108427640440313636,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9373876389752010455 --mojo-platform-channel-handle=3940 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1136 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,9071438225451997203,8108427640440313636,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=9062475422287734228 --mojo-platform-channel-handle=1632 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1704 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,9071438225451997203,8108427640440313636,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5788557475735068509 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3492 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1896 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,9071438225451997203,8108427640440313636,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17552914997854603630 --mojo-platform-channel-handle=4172 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1948 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,9071438225451997203,8108427640440313636,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9483159283944847289 --mojo-platform-channel-handle=4012 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,9071438225451997203,8108427640440313636,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8931303967798124014 --renderer-client-id=24 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2828 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,9071438225451997203,8108427640440313636,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5525672405264591169 --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3716 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2560 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=988,9071438225451997203,8108427640440313636,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13769531092261602166 --mojo-platform-channel-handle=3952 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2652 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=988,9071438225451997203,8108427640440313636,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8591922055377354849 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2224 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
205
Read events
142
Write events
59
Delete events
4
Modification events
| (PID) Process: | (3088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3064) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3088-13215112401315875 |
Value: 259 | |||
| (PID) Process: | (3088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3088) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
32
Text files
196
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\dffec702-61b8-4e61-98ca-8991c949d821.tmp | — | |
MD5:— | SHA256:— | |||
| 3088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF186472.TMP | text | |
MD5:— | SHA256:— | |||
| 3088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF186481.TMP | text | |
MD5:— | SHA256:— | |||
| 3088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF186472.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
33
DNS requests
23
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
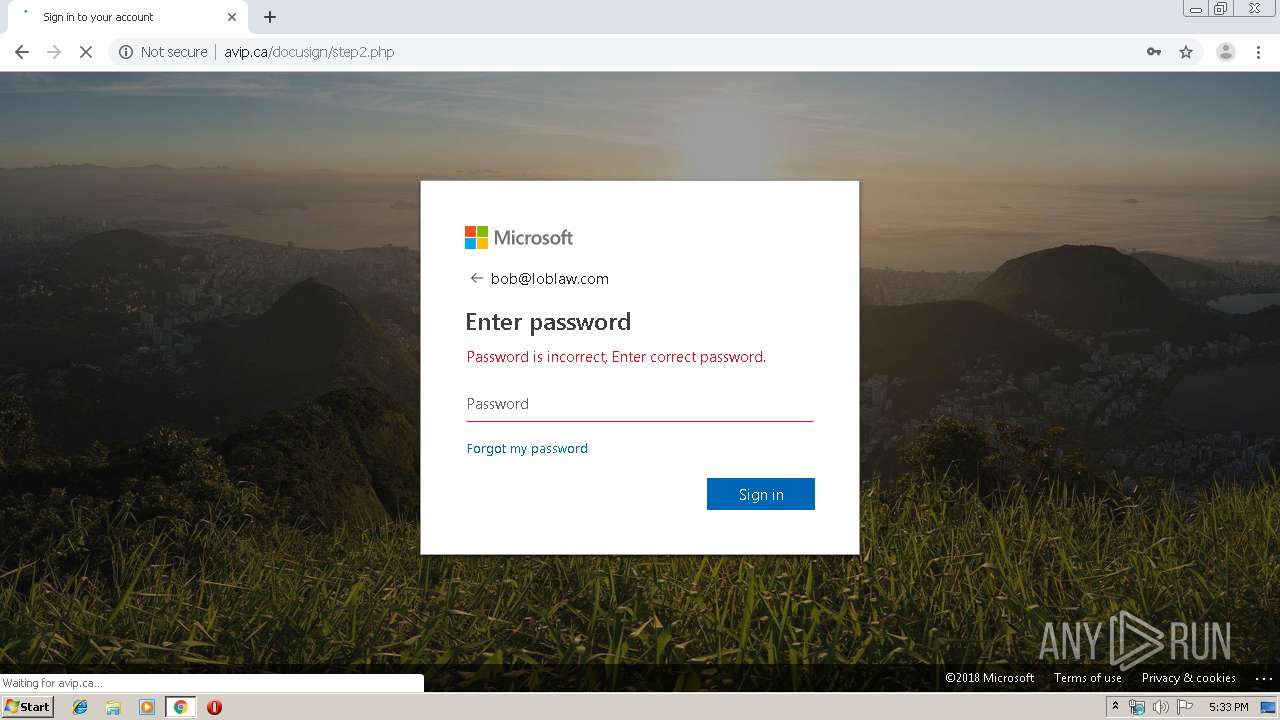
1136 | chrome.exe | GET | 302 | 104.18.61.153:80 | http://avip.ca/docusign/s.php?mail=bob%40loblaw.com&passwd=&ps=&psRNGCDefaultType=&psRNGCEntropy=&psRNGCSLK=&canary=4qQgTnDKNPGpFjIyyxWb%2BiZFSkaqH%2BYkJssPnR6gDy8%3D1%3A1&ctx=rQIIAdNiNtQztFIxgAAjXRCpa5CWZqibnApiIYEiIS6BRLtqhTc_brrMWmrusZ1l1cVVjPIZJSUFxVb6-vmlJTn5-dl6-Wlpmcmpesn5ufr55Yn6OxgZLzAyrmIyNzM2M7M0Mja1MDA3MrM0NLQ01rNMTjUxTTaz0E00NU7WNTE3TdG1SEux1DVMNk1OMzZOTDIyMr3FxO_vWFqSYQQi8osyq1I_MXGm5RflxhfkF5fMYk5wSS5xcst3THd2dAoq8kupCPYMc_SPNM1Iyikxig_LsjAKNXBOdzEs9owK9fRzDwvzNI1KdS_MC0vMq0wMME01Scmocs7KSQ3JjDD0K9ctysw0zksO8vLJDEjzMc9KK3dZxUxU6GxiZgN6OTc_7xQzW35Bal5mygUWxlcsPAasVhwcXAK8EmwKDD9YGBexAkNR4LtR2op8bde2TxX81-tZGE6x6psUBqaH5Ll4-wW4F7hleVZWVoQnaWdGuQVnJxZ6aEdmexUXB-QFmaW7VFrYGloZTmBjnMDG9oKN8QMbYwc7wy5OQtEAAA2&hpgrequestid=6632f710-6fa8-452b-86f2-780fd77f0400&flowToken=AQABAAEAAADXzZ3ifr-GRbDT45zNSEFEl-C_bh9vDXwBpmCPT_JVZD88DwuiI8QRin6Qiyu4ymKd6LEbBmslQA2QYDgiwq5XGFeRcQelzsfPL6GTvioEPgp2OLXK0dpe2APto9DukIKLbb_ofE3pXFwS503FZotevos6swUF0WECuZyXgvvco0NOuVd5i9CjMYsInmHzPQhiDHOZTnSrFh9YDRqxILdj3E9K9jOk882B3A2eXoEZ3Jl8apwMK8-UvQpmyCsRxmWJvbtRdPFxnypbmUaetCqgTCT-ZuHEdj7AuGVKOW3bvPMFsDXZZEBtaKv34Z9r2xw0TQ9OhzQJyFTyGTxogqVXDS2050RHj_ztjS66PzTuR6Ebt-8zY0-HV3R9mLLqOntYK9g5svb5rGub0YvQhX5WIAA&PPSX=&NewUser=1&FoundMSAs=&fspost=0&i21=0&CookieDisclosure=0&IsFidoSupported=1&i2=102&i17=&i18=&i19= | US | — | 507 b | suspicious |
1136 | chrome.exe | GET | 200 | 104.18.61.153:80 | http://avip.ca/docusign/ | US | html | 5.39 Kb | suspicious |
1136 | chrome.exe | GET | 302 | 172.217.22.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 529 b | whitelisted |
1136 | chrome.exe | GET | 200 | 104.18.61.153:80 | http://avip.ca/docusign/index_files/ellipsis_grey.svg | US | image | 263 b | suspicious |
1136 | chrome.exe | GET | 200 | 104.18.61.153:80 | http://avip.ca/docusign/index_files/ellipsis_white.svg | US | image | 264 b | suspicious |
1136 | chrome.exe | GET | 200 | 104.18.61.153:80 | http://avip.ca/docusign/back.jpg?x=a5dbd4393ff6a725c7e62b61df7e72f0 | US | image | 276 Kb | suspicious |
1136 | chrome.exe | GET | 200 | 104.18.61.153:80 | http://avip.ca/docusign/index_files/sprite1.mouse.css | US | text | 1.07 Kb | suspicious |
1136 | chrome.exe | GET | 404 | 104.18.61.153:80 | http://avip.ca/docusign/index_files/boot.worldwide.1.mouse.js | US | html | 238 b | suspicious |
1136 | chrome.exe | GET | 404 | 104.18.61.153:80 | http://avip.ca/docusign/index_files/boot.worldwide.2.mouse.js | US | html | 238 b | suspicious |
1136 | chrome.exe | GET | 200 | 104.18.61.153:80 | http://avip.ca/docusign/index_files/favicon_a.ico | US | image | 507 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1136 | chrome.exe | 172.217.18.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1136 | chrome.exe | 104.18.61.153:80 | avip.ca | Cloudflare Inc | US | shared |
1136 | chrome.exe | 172.217.23.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
1136 | chrome.exe | 172.217.22.14:443 | clients1.google.com | Google Inc. | US | whitelisted |
1136 | chrome.exe | 2.18.232.137:443 | r4.res.office365.com | Akamai International B.V. | — | whitelisted |
1136 | chrome.exe | 216.58.207.68:443 | www.google.com | Google Inc. | US | whitelisted |
1136 | chrome.exe | 172.217.22.110:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
1136 | chrome.exe | 172.217.18.1:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
1136 | chrome.exe | 216.58.206.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
— | — | 216.58.206.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
avip.ca |
| suspicious |
accounts.google.com |
| shared |
clients1.google.com |
| whitelisted |
r4.res.office365.com |
| whitelisted |
clients2.google.com |
| whitelisted |
www.google.com |
| malicious |
redirector.gvt1.com |
| whitelisted |
r3---sn-n02xgoxufvg3-8pxe.gvt1.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
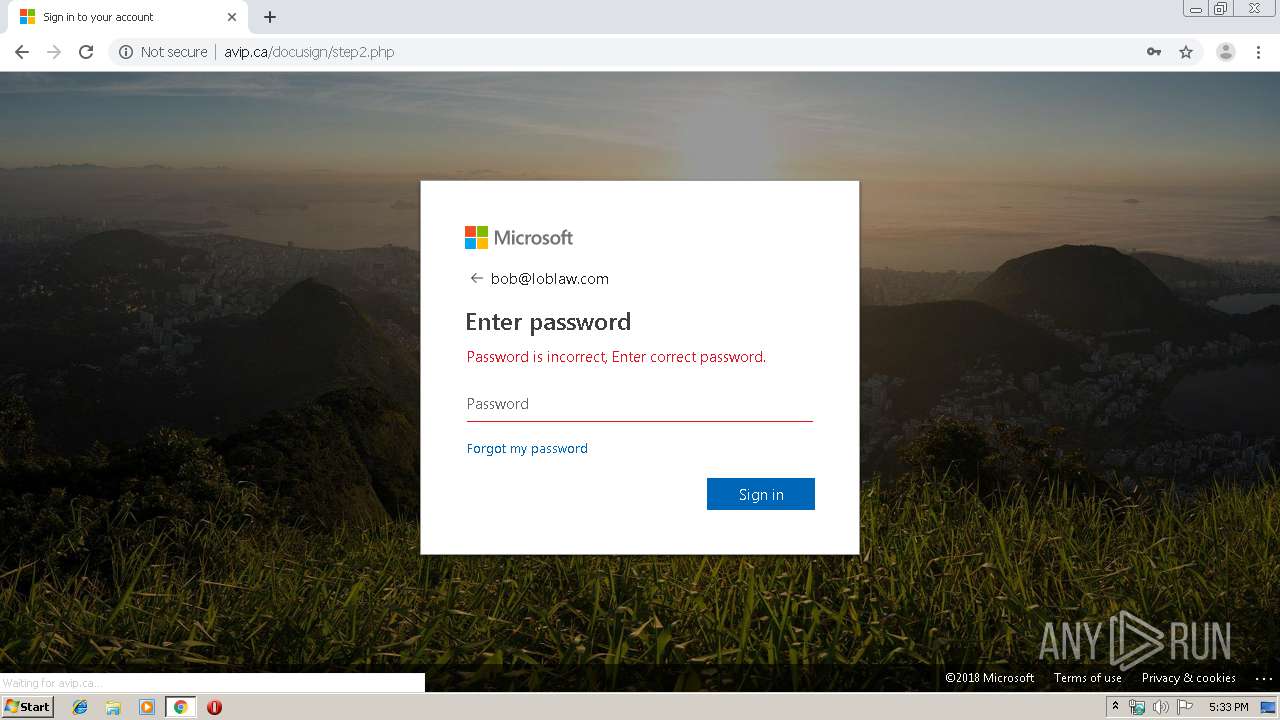
1136 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains passwd= in cleartext |
1136 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains passwd= in cleartext |
4 ETPRO signatures available at the full report