| File name: | 89700.exe |
| Full analysis: | https://app.any.run/tasks/cddf9b93-f426-49a6-9073-e739f83e99fd |
| Verdict: | Suspicious activity |
| Analysis date: | May 10, 2019, 03:20:06 |
| OS: | Windows 10 Professional (build: 16299, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | BAD406778156028E33084D82CF0A1966 |
| SHA1: | 916992A259BA60E0B4E0215E800F36B48CFBD6B5 |
| SHA256: | AD81F3294E0777D7434EAEE40EEA05EABC28DA834578D33B792963415B06F0C9 |
| SSDEEP: | 12288:LgHWkTqbm62usp7Rr1kwTq5gWu7Q7YSgTZ6aMcxk7YsJ+CrQTMA+t/yO7EFc21Gr:8HA5fDFUu+NO9K9zbGpIkHbWTWjvm8LJ |
MALICIOUS
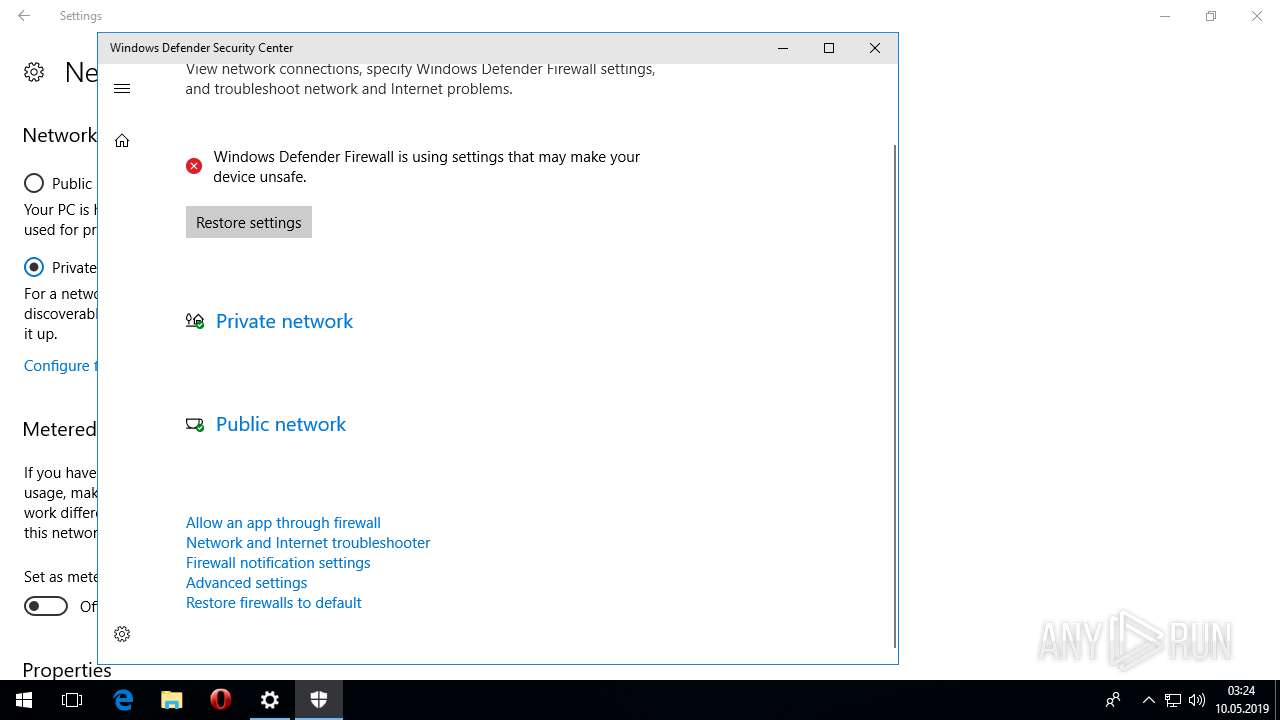
No malicious indicators.SUSPICIOUS
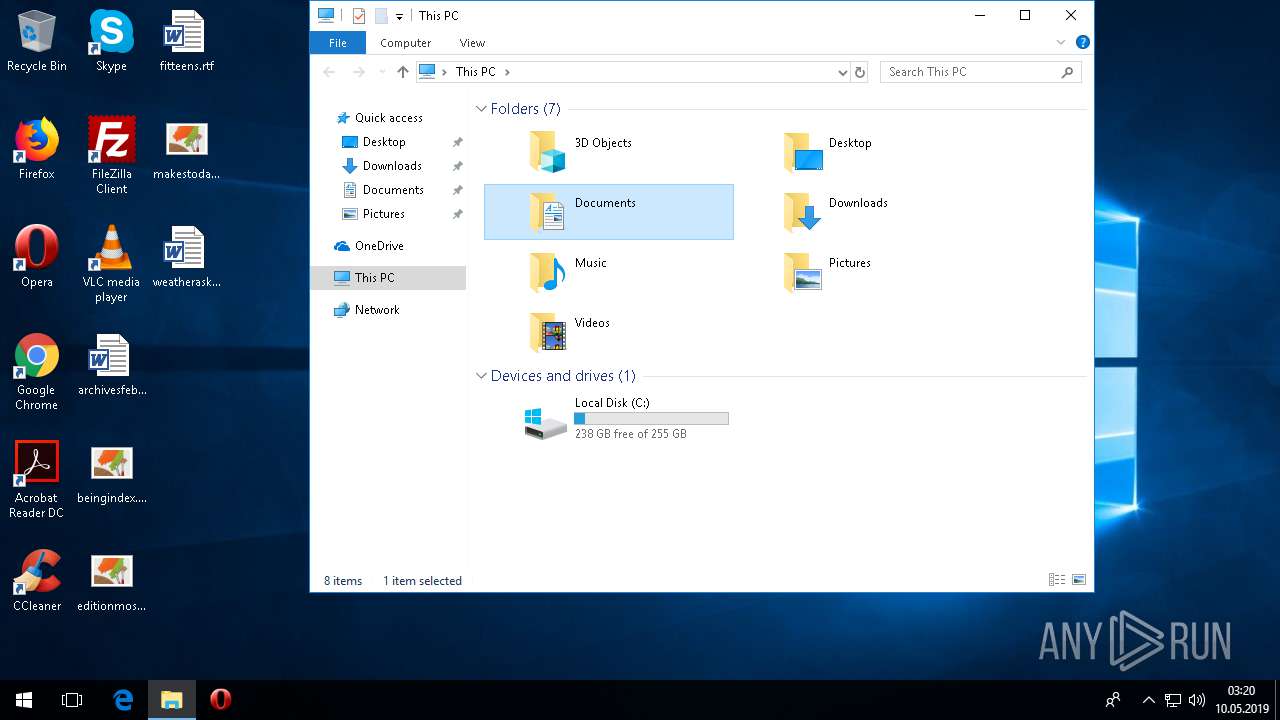
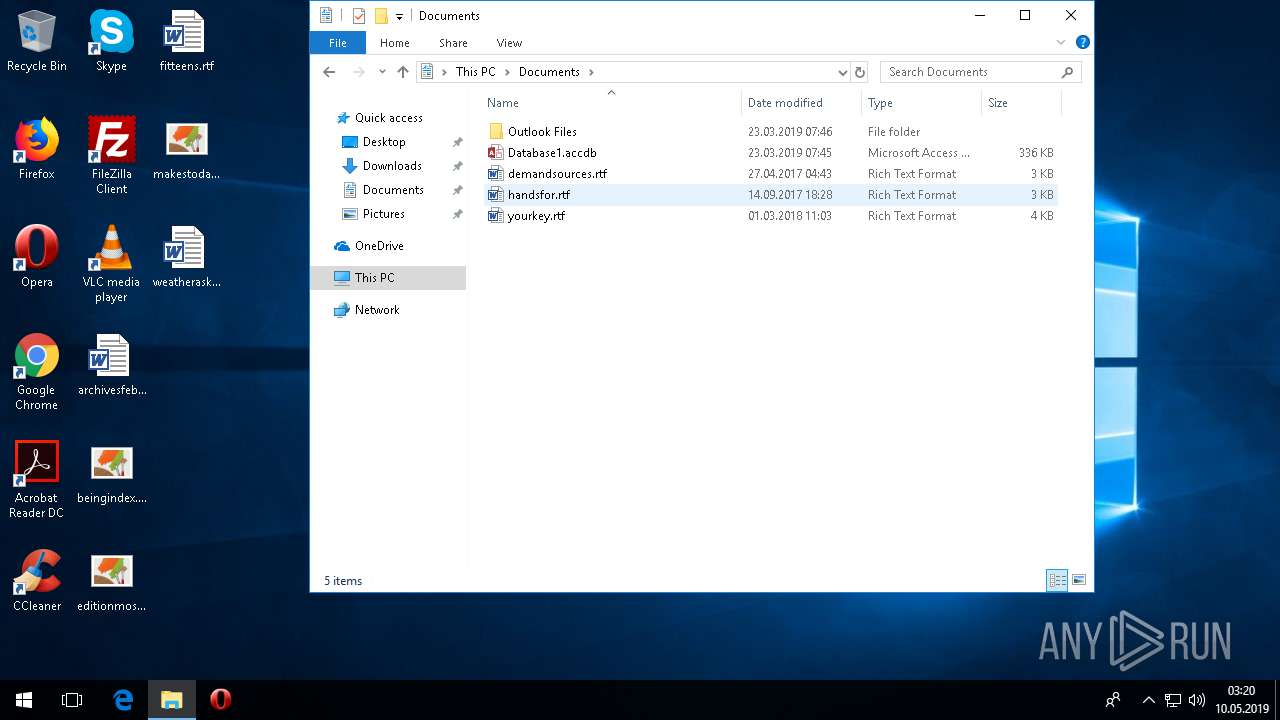
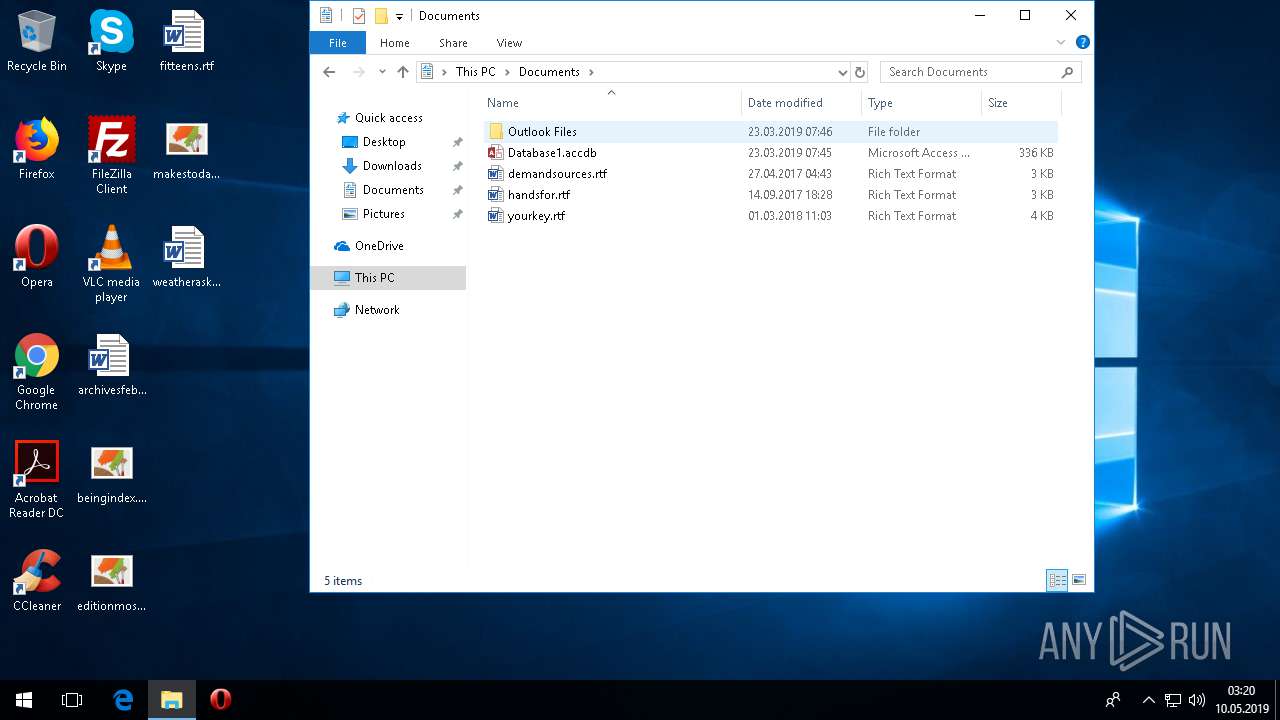
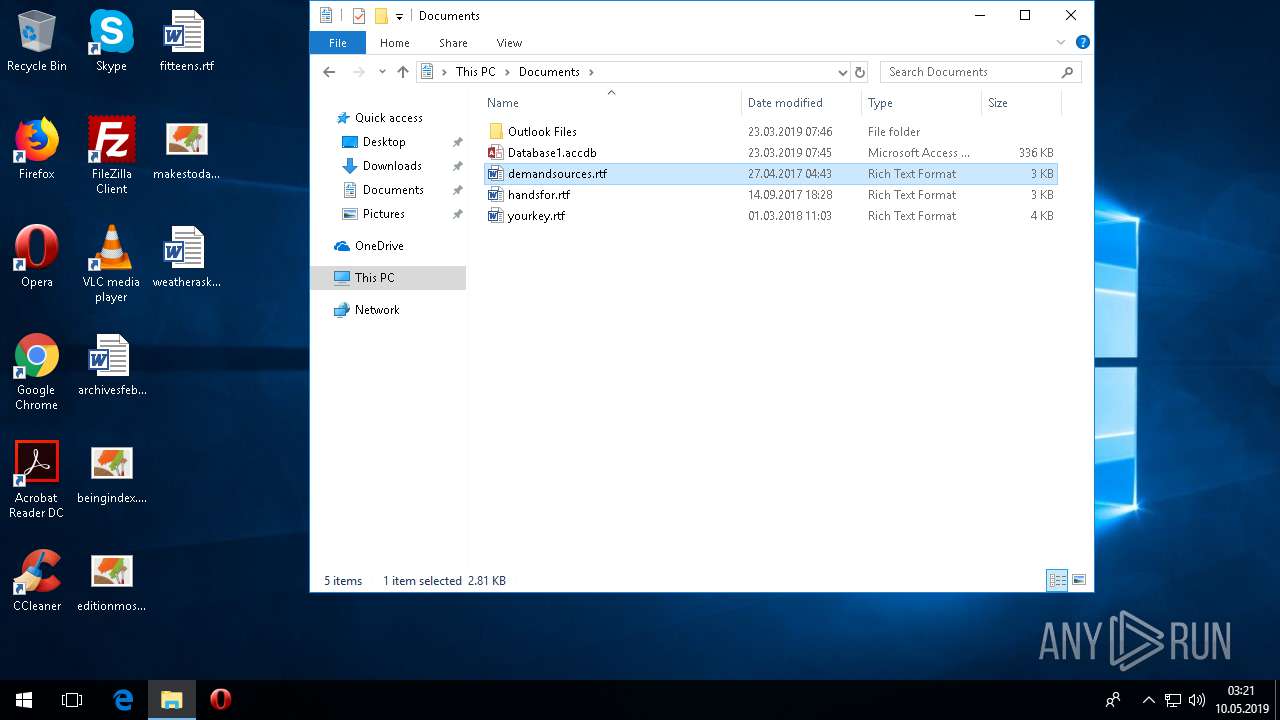
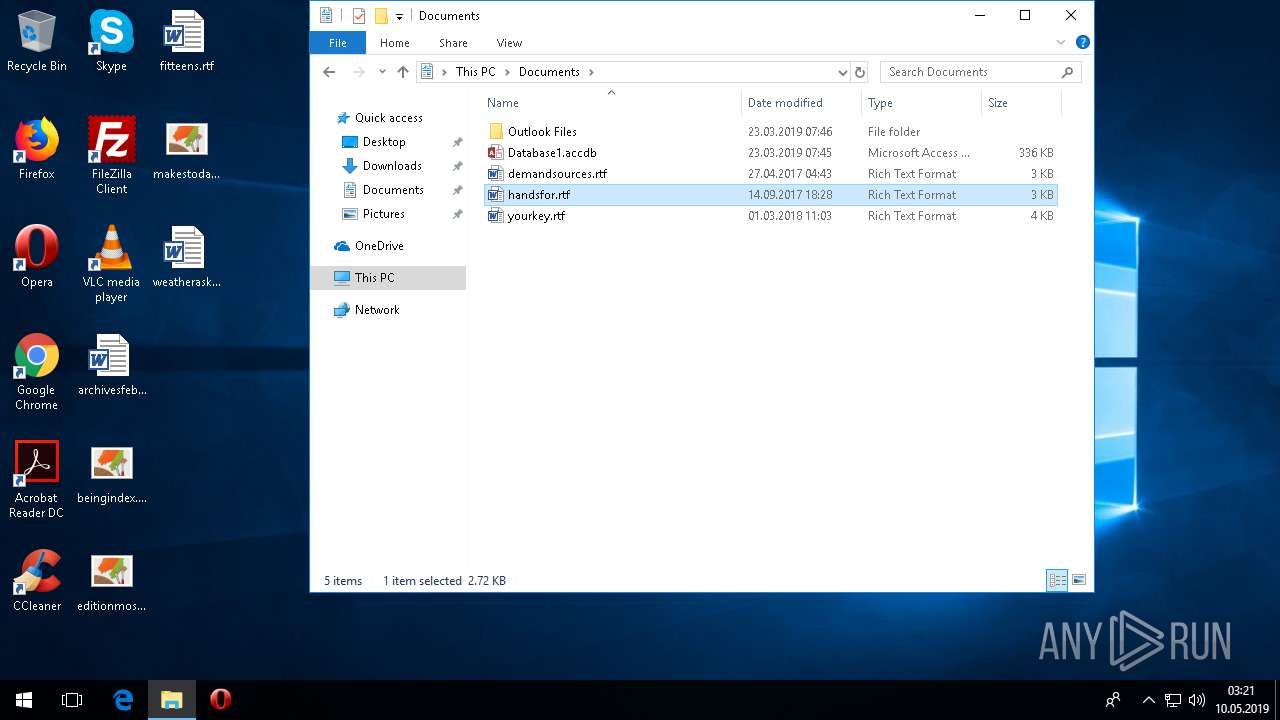
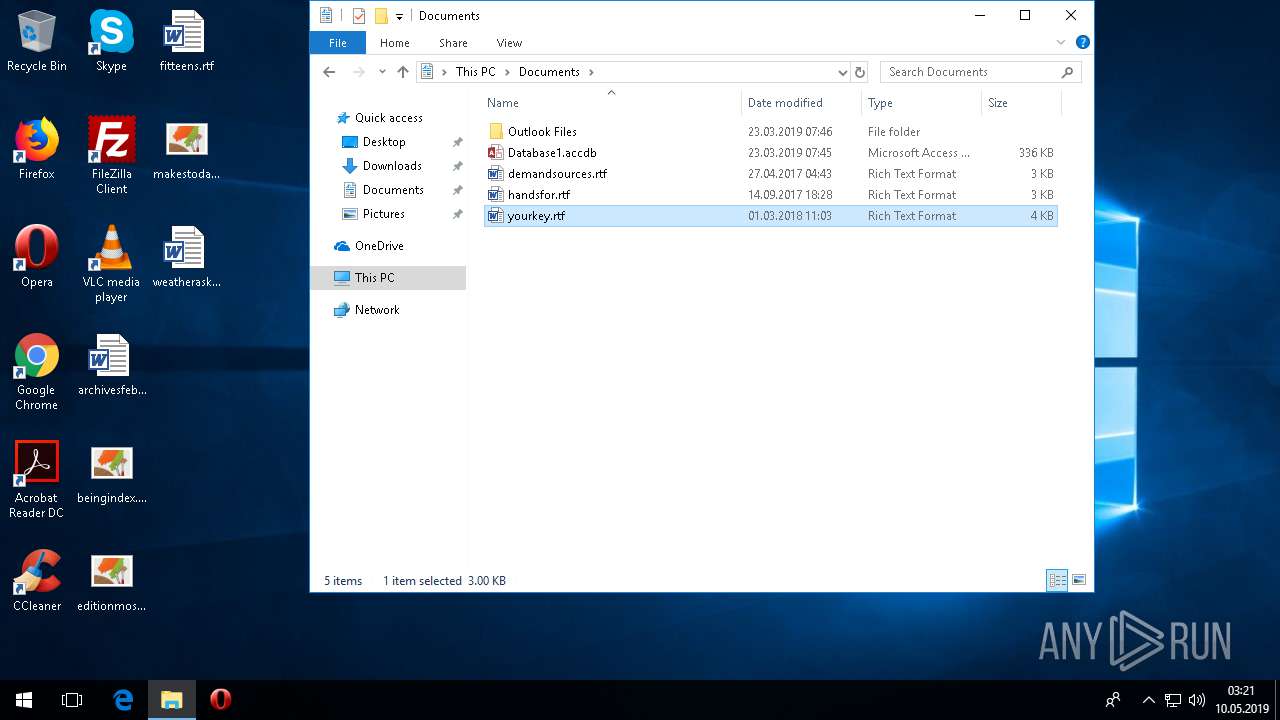
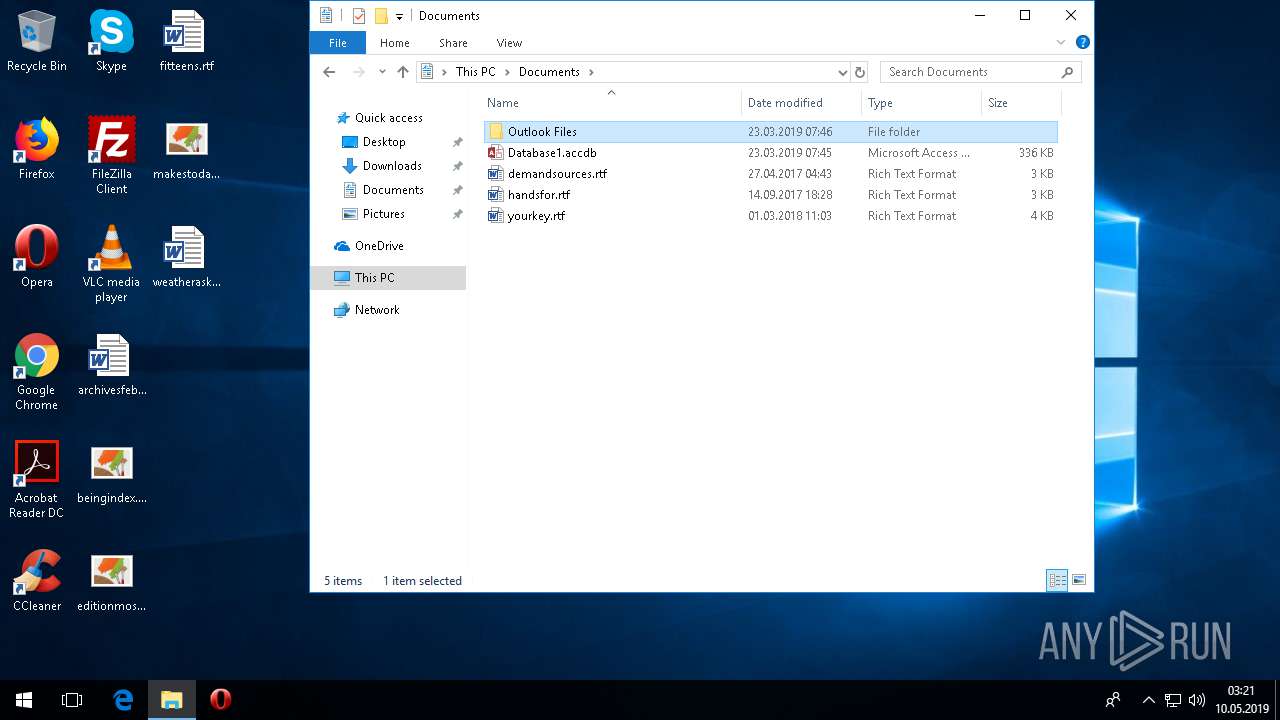
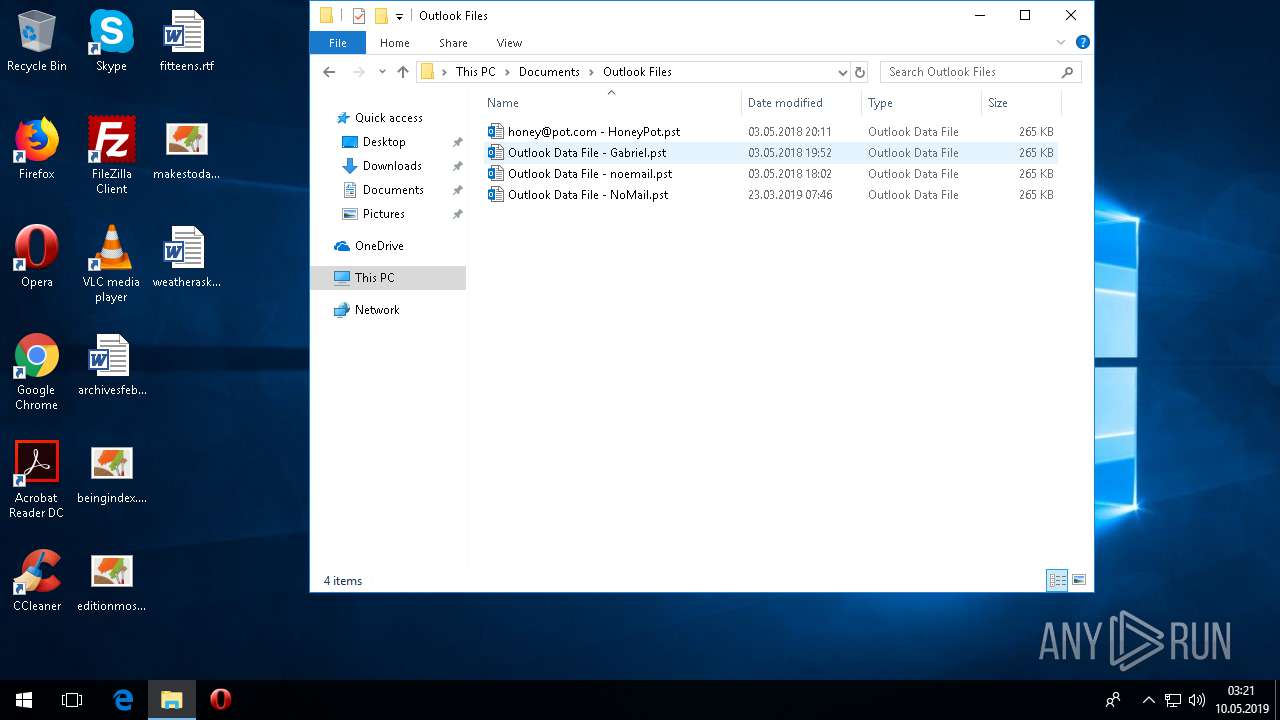
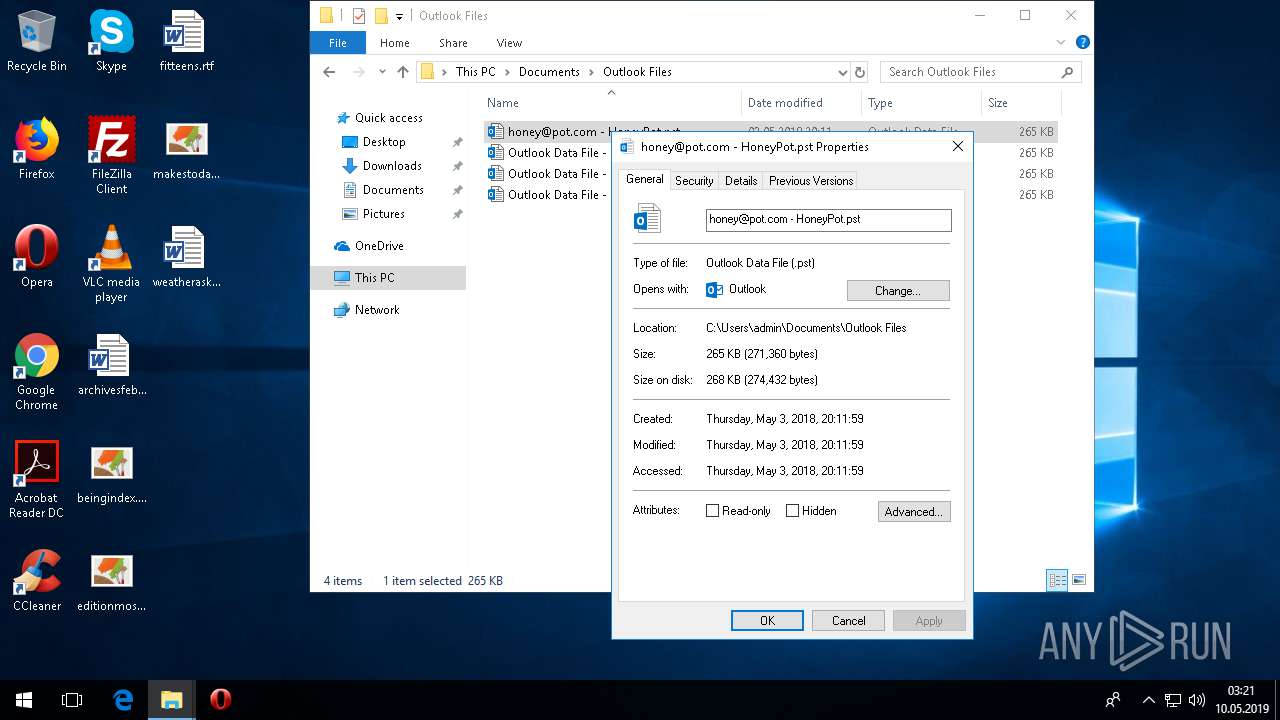
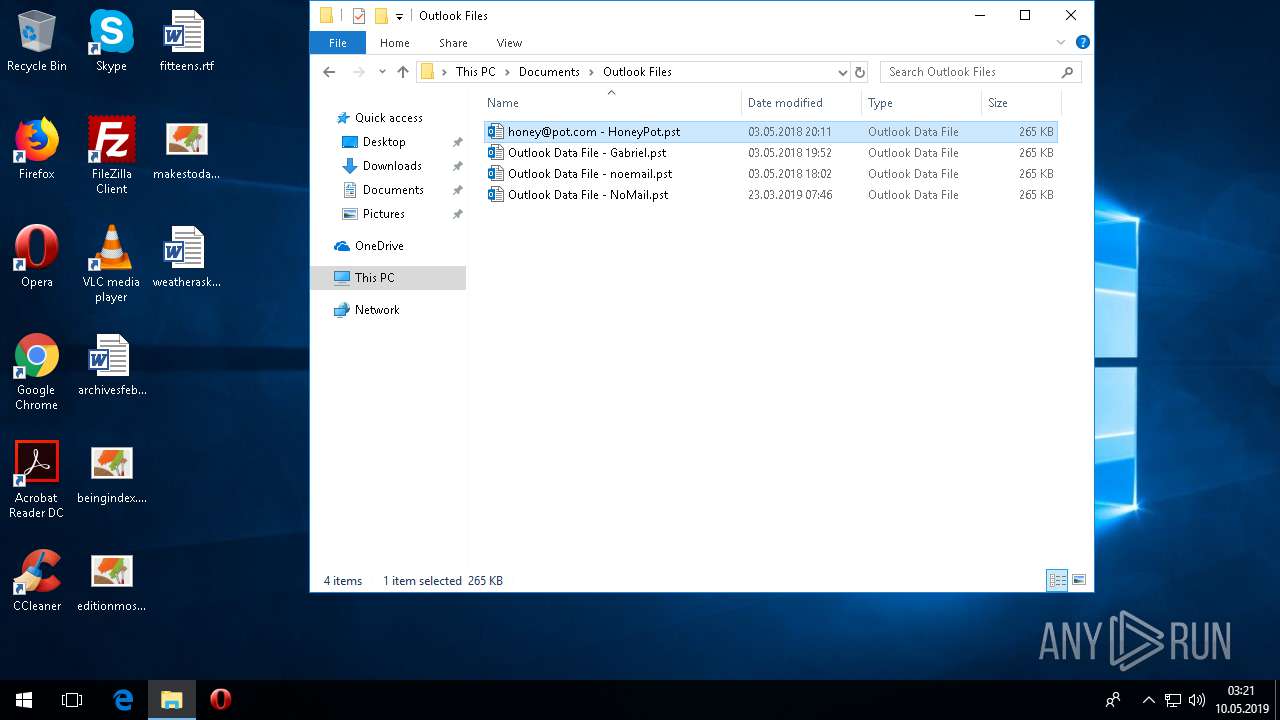
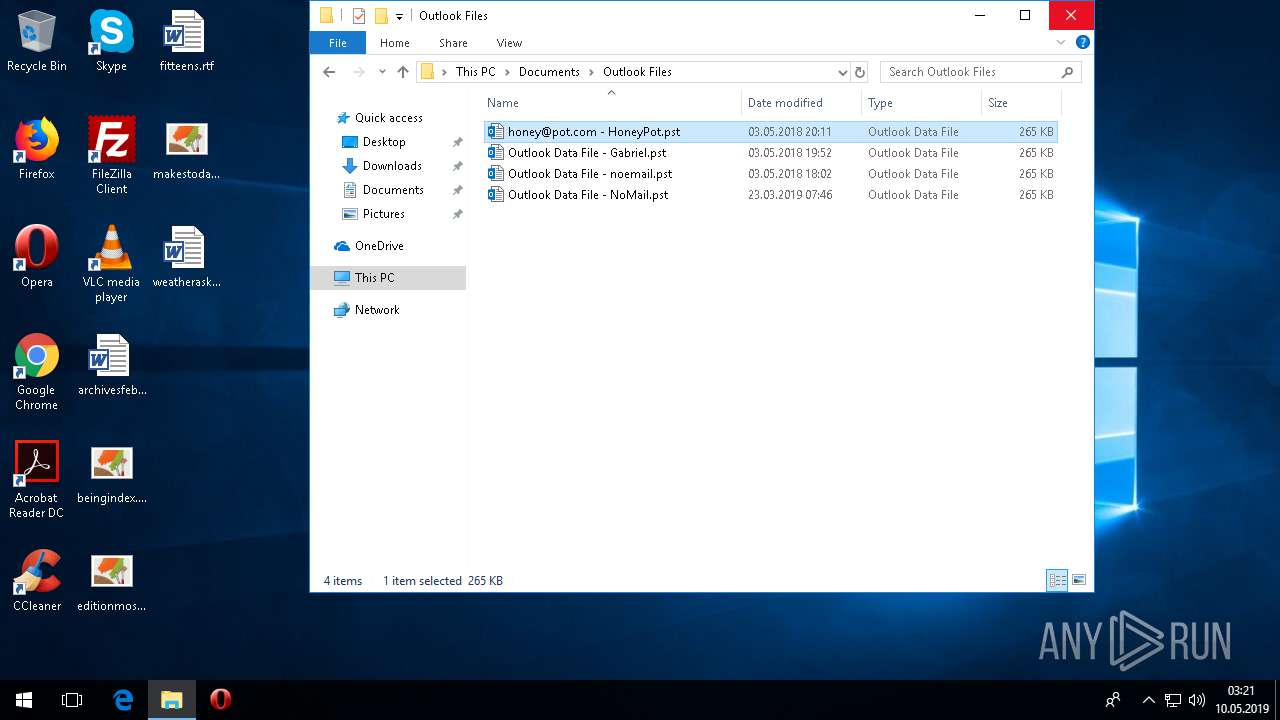
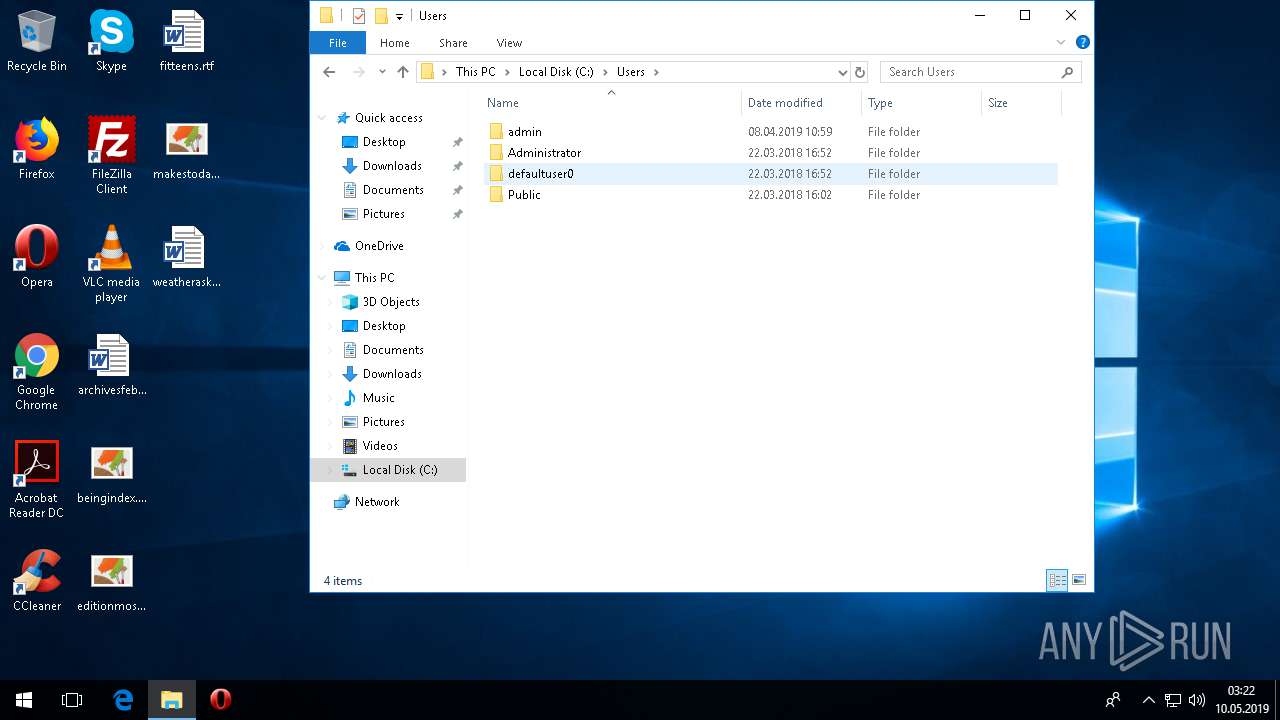
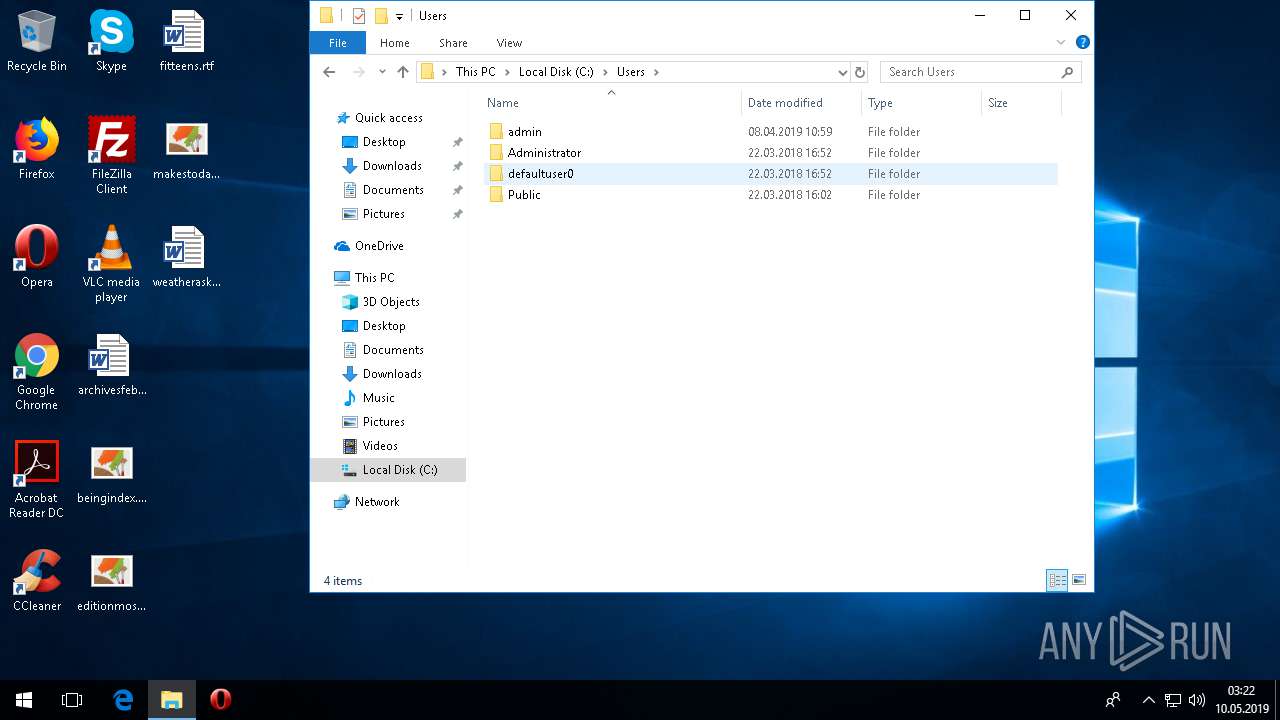
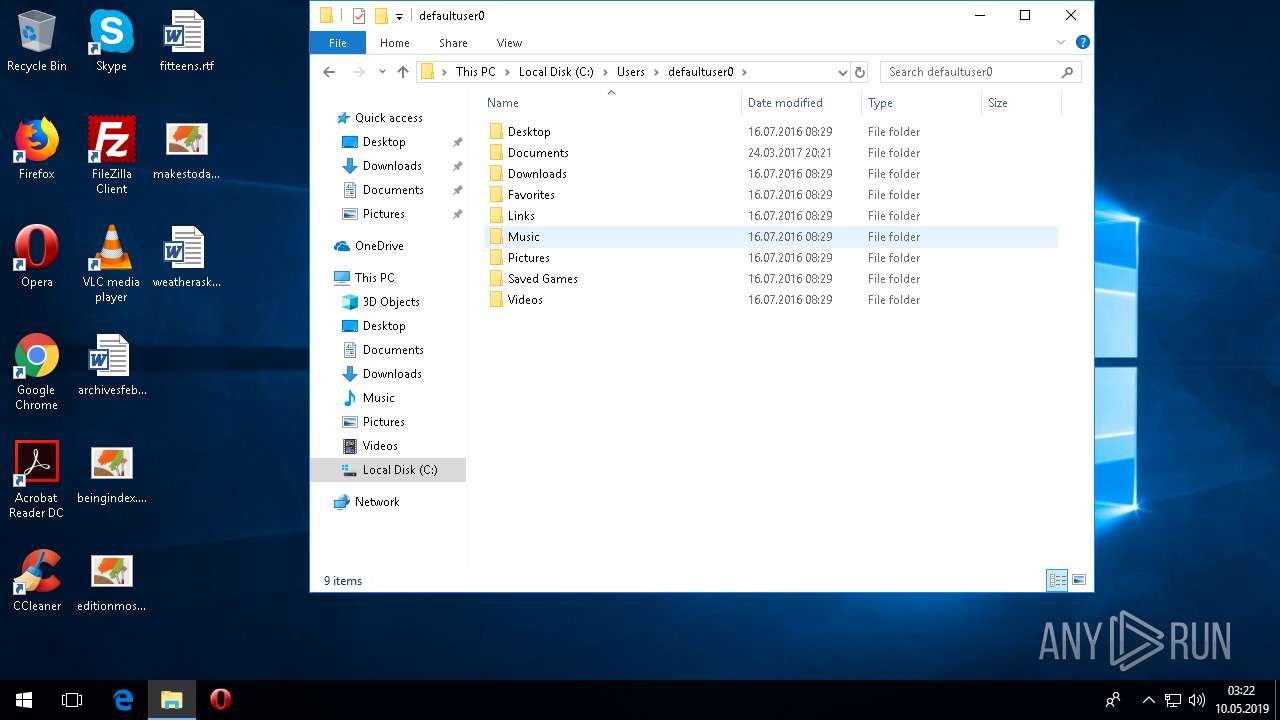
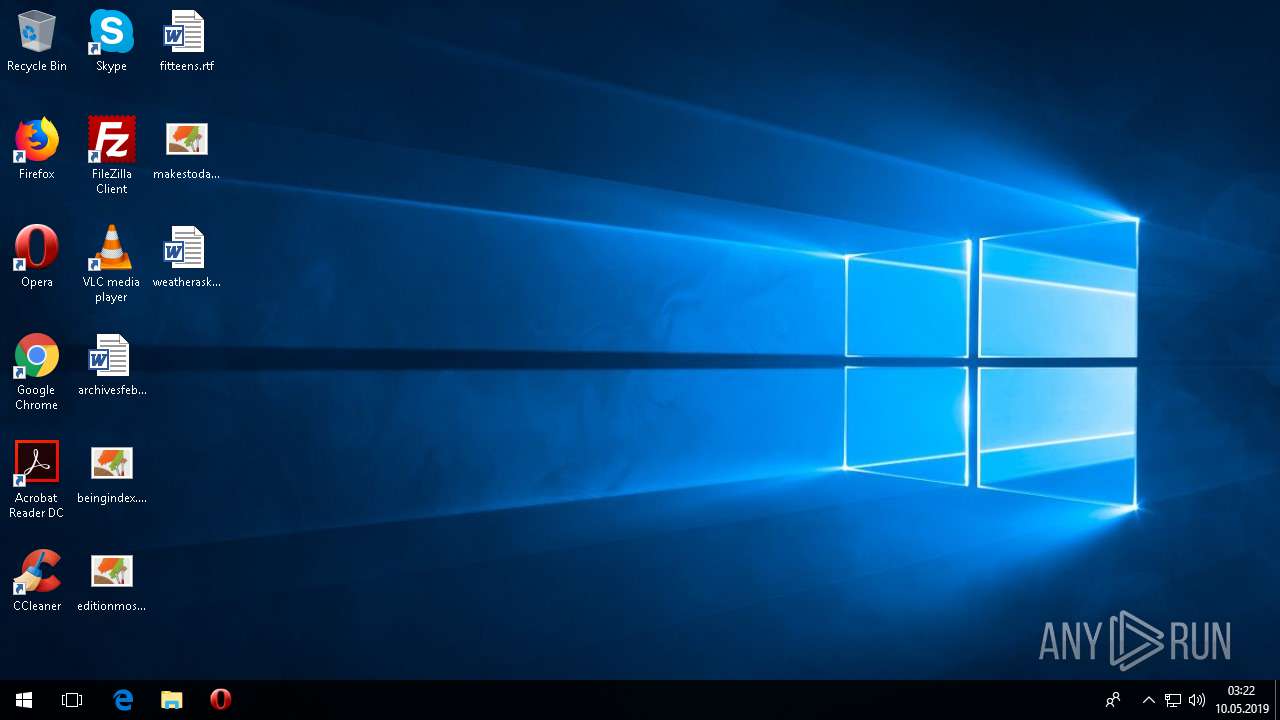
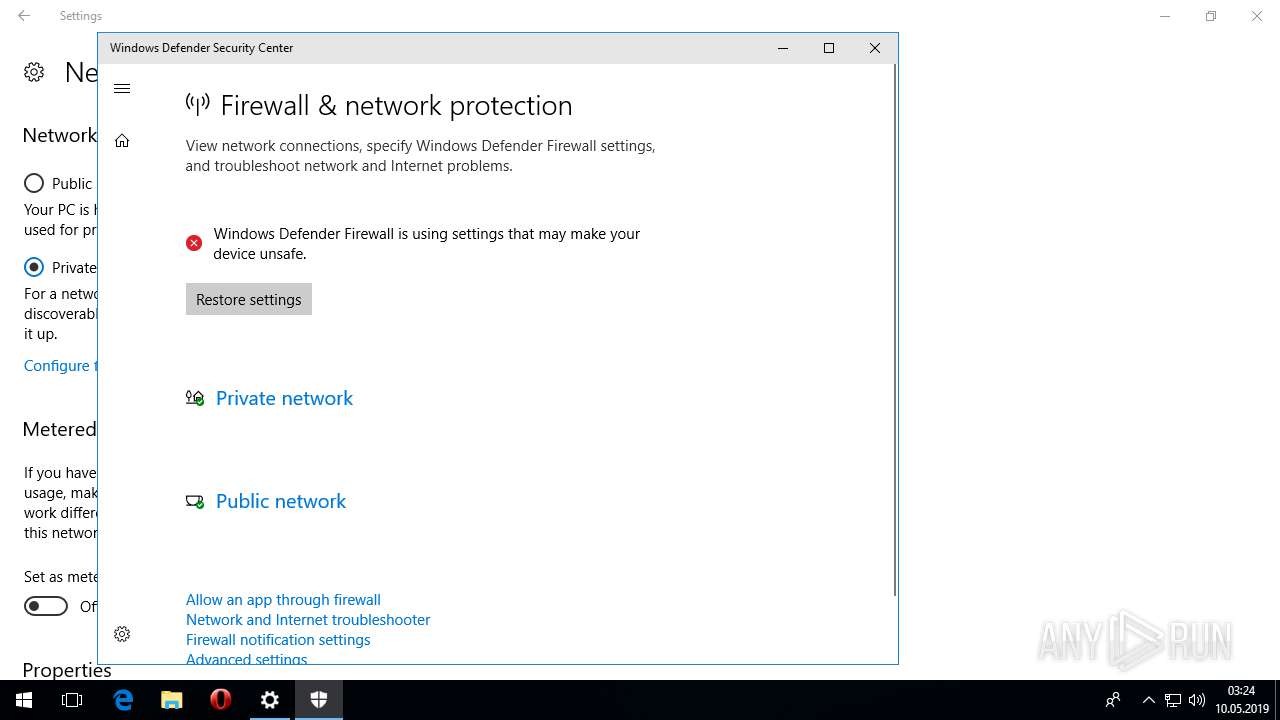
Creates files in the user directory
- 89700.exe (PID: 3064)
- SystemSettings.exe (PID: 5840)
Application launched itself
- fexplor.exe (PID: 1804)
- fexplor.exe (PID: 3148)
- fexplor.exe (PID: 2456)
- fexplor.exe (PID: 3336)
- fexplor.exe (PID: 3128)
- fexplor.exe (PID: 3544)
- fexplor.exe (PID: 892)
- fexplor.exe (PID: 2272)
- fexplor.exe (PID: 3464)
- fexplor.exe (PID: 5372)
- fexplor.exe (PID: 2000)
- fexplor.exe (PID: 6116)
- fexplor.exe (PID: 2916)
- fexplor.exe (PID: 2936)
- fexplor.exe (PID: 5260)
- fexplor.exe (PID: 4752)
- fexplor.exe (PID: 5884)
- fexplor.exe (PID: 5552)
- fexplor.exe (PID: 4360)
- fexplor.exe (PID: 4572)
- fexplor.exe (PID: 3740)
- fexplor.exe (PID: 2404)
- fexplor.exe (PID: 3196)
Starts itself from another location
- 89700.exe (PID: 3064)
Executable content was dropped or overwritten
- 89700.exe (PID: 3064)
INFO
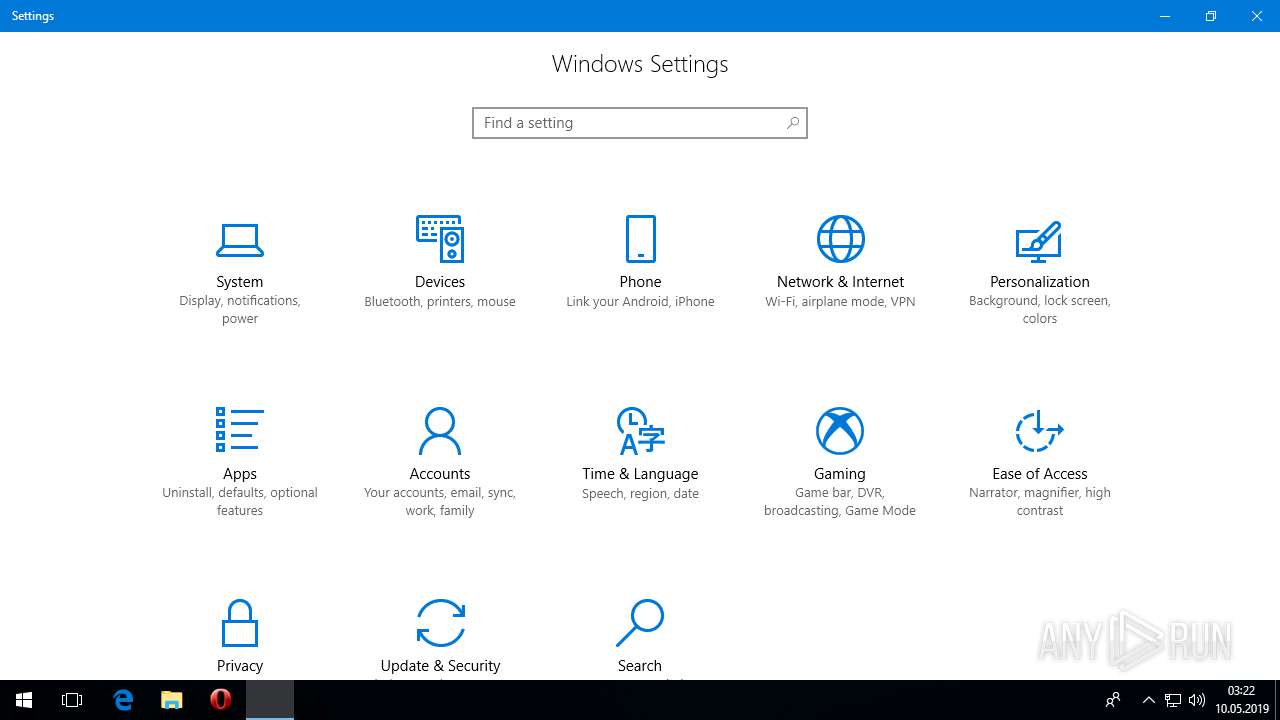
Reads the software policy settings
- SystemSettings.exe (PID: 5840)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (37.4) |
|---|---|---|
| .scr | | | Windows screen saver (34.5) |
| .exe | | | Win32 Executable (generic) (11.9) |
| .exe | | | Win16/32 Executable Delphi generic (5.4) |
| .exe | | | Generic Win/DOS Executable (5.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:02:24 19:38:25+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 523264 |
| InitializedDataSize: | 231936 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x80b9c |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Feb-1992 18:38:25 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 24-Feb-1992 18:38:25 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x0007FBE4 | 0x0007FC00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.53294 |
DATA | 0x00081000 | 0x00009820 | 0x00009A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.98742 |
BSS | 0x0008B000 | 0x00000D81 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0008C000 | 0x000024BA | 0x00002600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.93963 |
.tls | 0x0008F000 | 0x00000010 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00090000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.181202 |
.reloc | 0x00091000 | 0x00008F90 | 0x00009000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.65896 |
.rsrc | 0x0009A000 | 0x00023690 | 0x00023800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.99469 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 2.95601 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
2 | 2.80231 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
3 | 3.00046 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
4 | 2.56318 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
5 | 2.6949 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
6 | 2.62527 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
7 | 2.91604 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
8 | 2.6633 | 308 | Latin 1 / Western European | UNKNOWN | RT_CURSOR |
266 | 6.98777 | 4723 | Latin 1 / Western European | English - United States | RT_CURSOR |
267 | 7.4665 | 4723 | Latin 1 / Western European | English - United States | RT_CURSOR |
Imports
advapi32.dll |
comctl32.dll |
comdlg32.dll |
gdi32.dll |
kernel32.dll |
ole32.dll |
oleaut32.dll |
user32.dll |
version.dll |
Total processes
99
Monitored processes
38
Malicious processes
0
Suspicious processes
19
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 864 | C:\WINDOWS\system32\DllHost.exe /Processid:{46B988E8-BEC2-401F-A1C5-16C694F26D3E} | C:\WINDOWS\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 892 | "C:\Users\admin\AppData\Roaming\\fexplor.exe" | C:\Users\admin\AppData\Roaming\fexplor.exe | — | fexplor.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1600 | C:\WINDOWS\system32\DllHost.exe /Processid:{7E55A26D-EF95-4A45-9F55-21E52ADF9887} | C:\WINDOWS\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1804 | "C:\Users\admin\AppData\Roaming\\fexplor.exe" | C:\Users\admin\AppData\Roaming\fexplor.exe | — | fexplor.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2000 | "C:\Users\admin\AppData\Roaming\\fexplor.exe" | C:\Users\admin\AppData\Roaming\fexplor.exe | — | fexplor.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2180 | "C:\Users\admin\AppData\Roaming\\fexplor.exe" | C:\Users\admin\AppData\Roaming\fexplor.exe | — | fexplor.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2272 | "C:\Users\admin\AppData\Roaming\\fexplor.exe" | C:\Users\admin\AppData\Roaming\fexplor.exe | — | fexplor.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2364 | C:\Windows\System32\PickerHost.exe -Embedding | C:\Windows\System32\PickerHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: File Picker UI Host Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2404 | "C:\Users\admin\AppData\Roaming\\fexplor.exe" | C:\Users\admin\AppData\Roaming\fexplor.exe | — | 89700.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2416 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\WINDOWS\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.16299.15 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 753
Read events
3 292
Write events
451
Delete events
10
Modification events
| (PID) Process: | (3056) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\2f\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3056) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\2f\52C64B7E |
| Operation: | write | Name: | @C:\WINDOWS\System32\display.dll,-4 |
Value: &Display settings | |||
| (PID) Process: | (3056) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\2f\52C64B7E |
| Operation: | write | Name: | @C:\Program Files\Common Files\System\wab32res.dll,-4602 |
Value: Contact file | |||
| (PID) Process: | (3056) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\2f\52C64B7E |
| Operation: | write | Name: | @C:\WINDOWS\system32\themecpl.dll,-10 |
Value: Pe&rsonalize | |||
| (PID) Process: | (3056) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\2f\52C64B7E |
| Operation: | write | Name: | @C:\Program Files\Microsoft Office\Root\VFS\ProgramFilesCommonX86\Microsoft Shared\Office16\oregres.dll,-123 |
Value: Microsoft Word Document | |||
| (PID) Process: | (3056) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\2f\52C64B7E |
| Operation: | write | Name: | @C:\Program Files\Microsoft Office\Root\VFS\ProgramFilesCommonX86\Microsoft Shared\Office16\oregres.dll,-174 |
Value: Microsoft PowerPoint Presentation | |||
| (PID) Process: | (3056) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\2f\52C64B7E |
| Operation: | write | Name: | @C:\Program Files\Microsoft Office\Root\VFS\ProgramFilesCommonX86\Microsoft Shared\Office16\oregres.dll,-131 |
Value: Rich Text Format | |||
| (PID) Process: | (3056) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\2f\52C64B7E |
| Operation: | write | Name: | @C:\Program Files\Microsoft Office\Root\VFS\ProgramFilesCommonX86\Microsoft Shared\Office16\oregres.dll,-101 |
Value: Microsoft Excel Worksheet | |||
| (PID) Process: | (3056) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Discardable\PostSetup\ShellNew |
| Operation: | write | Name: | Classes |
Value: .accdb | |||
| (PID) Process: | (3056) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Discardable\PostSetup\ShellNew |
| Operation: | write | Name: | ~reserved~ |
Value: 0800000000000600 | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3064 | 89700.exe | C:\Users\admin\AppData\Roaming\fexplor.exe:ZoneIdentifier | — | |
MD5:— | SHA256:— | |||
| 2404 | fexplor.exe | C:\Users\admin\AppData\Roaming\fexplor.exe:ZoneIdentifier | — | |
MD5:— | SHA256:— | |||
| 3196 | fexplor.exe | C:\Users\admin\AppData\Roaming\fexplor.exe:ZoneIdentifier | — | |
MD5:— | SHA256:— | |||
| 3148 | fexplor.exe | C:\Users\admin\AppData\Roaming\fexplor.exe:ZoneIdentifier | — | |
MD5:— | SHA256:— | |||
| 3740 | fexplor.exe | C:\Users\admin\AppData\Roaming\fexplor.exe:ZoneIdentifier | — | |
MD5:— | SHA256:— | |||
| 3336 | fexplor.exe | C:\Users\admin\AppData\Roaming\fexplor.exe:ZoneIdentifier | — | |
MD5:— | SHA256:— | |||
| 2456 | fexplor.exe | C:\Users\admin\AppData\Roaming\fexplor.exe:ZoneIdentifier | — | |
MD5:— | SHA256:— | |||
| 1804 | fexplor.exe | C:\Users\admin\AppData\Roaming\fexplor.exe:ZoneIdentifier | — | |
MD5:— | SHA256:— | |||
| 3544 | fexplor.exe | C:\Users\admin\AppData\Roaming\fexplor.exe:ZoneIdentifier | — | |
MD5:— | SHA256:— | |||
| 3128 | fexplor.exe | C:\Users\admin\AppData\Roaming\fexplor.exe:ZoneIdentifier | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
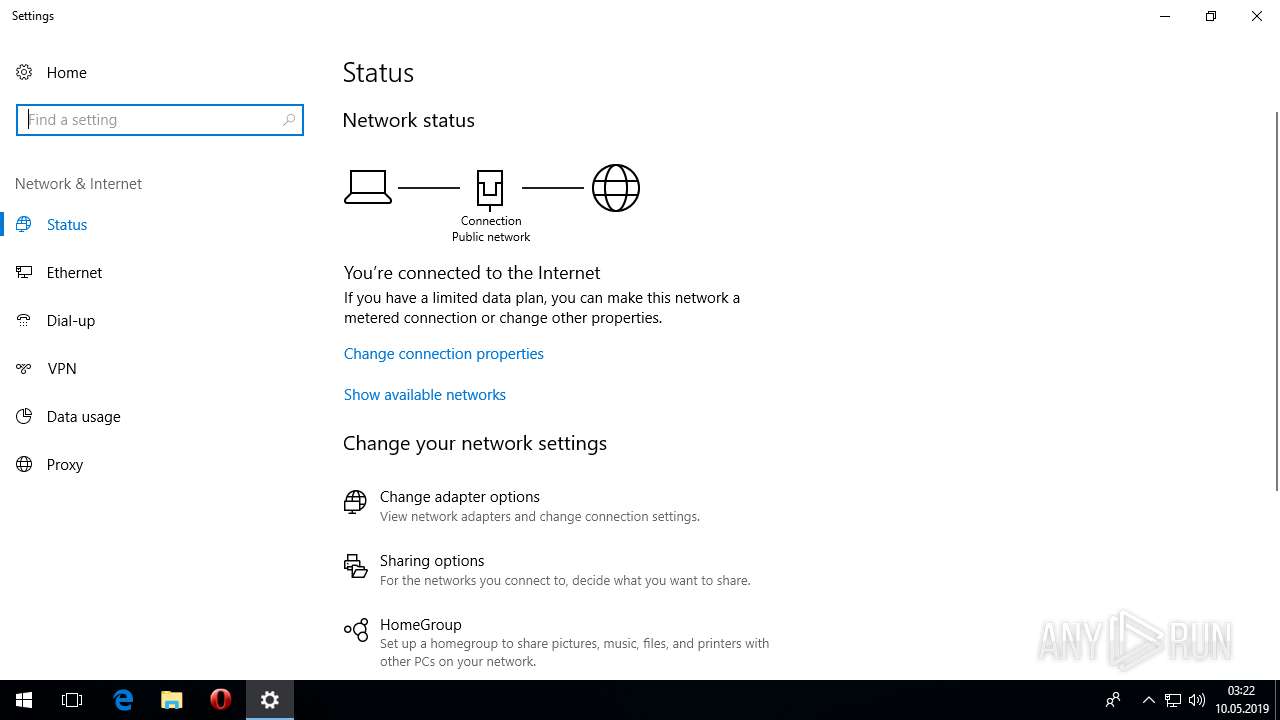
HTTP(S) requests
6
TCP/UDP connections
6
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1080 | SystemSettings.exe | GET | 200 | 152.199.19.161:443 | https://onecs-live.azureedge.net/api/settings/en-US/xml/settings-tipset | US | html | 15.6 Kb | whitelisted |
1480 | svchost.exe | GET | 200 | 2.16.186.74:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | der | 1.11 Kb | whitelisted |
1480 | svchost.exe | GET | 200 | 2.23.106.83:80 | http://www.microsoft.com/pkiops/crl/MicWinProPCA2011_2011-10-19.crl | unknown | der | 564 b | whitelisted |
— | — | POST | 200 | 65.55.163.76:443 | https://login.live.com/RST2.srf | US | xml | 10.5 Kb | whitelisted |
1480 | svchost.exe | GET | 200 | 2.16.186.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | der | 1.11 Kb | whitelisted |
— | — | POST | 200 | 65.55.163.90:443 | https://login.live.com/RST2.srf | US | xml | 9.85 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1480 | svchost.exe | 2.16.186.74:80 | crl.microsoft.com | Akamai International B.V. | — | whitelisted |
1480 | svchost.exe | 2.23.106.83:80 | www.microsoft.com | Akamai International B.V. | — | whitelisted |
1080 | SystemSettings.exe | 152.199.19.161:443 | onecs-live.azureedge.net | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 65.55.163.76:443 | login.live.com | Microsoft Corporation | US | whitelisted |
1480 | svchost.exe | 2.16.186.120:80 | crl.microsoft.com | Akamai International B.V. | — | whitelisted |
— | — | 65.55.163.90:443 | login.live.com | Microsoft Corporation | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
onecs-live.azureedge.net |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
sls.update.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
SystemSettings.exe | ERROR FindDefaultInterface:CM_Get_Device_Interface_List_Size failed:0x00000000, InterfaceListSize = 1
|
SystemSettings.exe | ERROR SensorOpenByType:Failed to open sensor error:0x00000490
|
SystemSettings.exe | ERROR FindDefaultInterface:CM_Get_Device_Interface_List_Size failed:0x00000000, InterfaceListSize = 1
|
SystemSettings.exe | ERROR SensorOpenByType:Failed to open sensor error:0x00000490
|