| URL: | https://www.airdroid.com/es/cast/ |
| Full analysis: | https://app.any.run/tasks/6e61e4e9-c004-44a4-982a-6463ea3524ce |
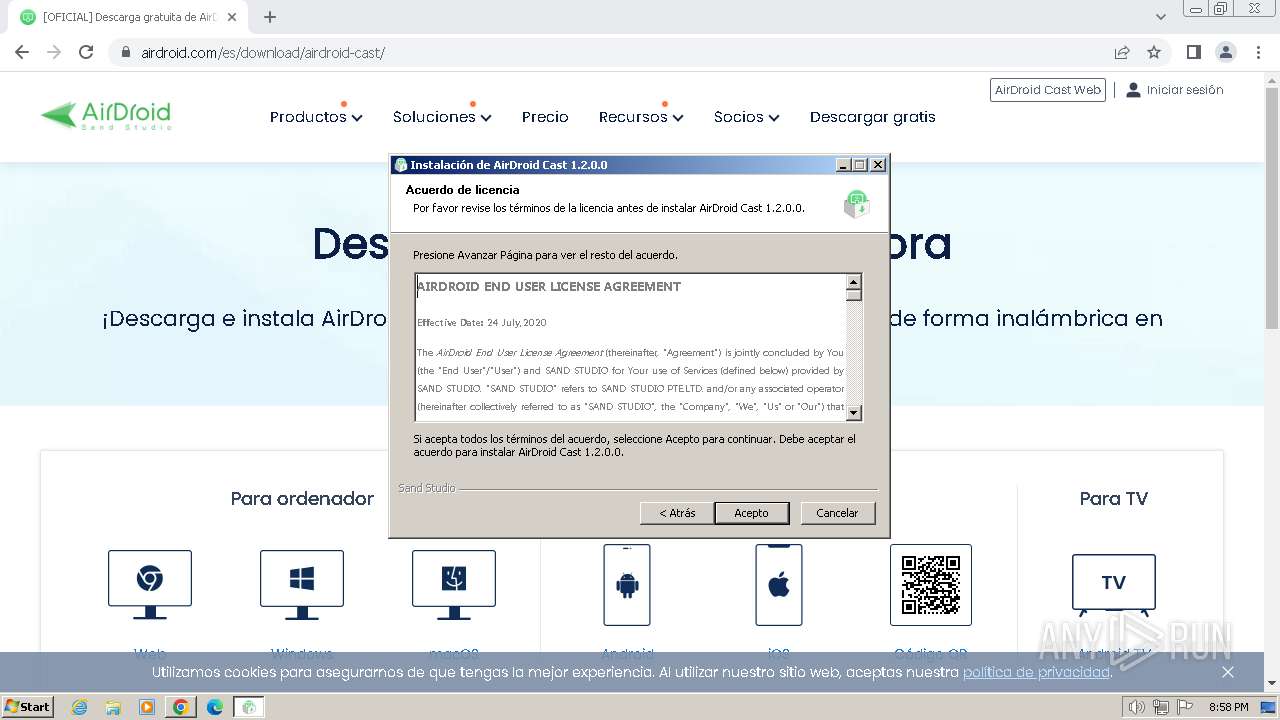
| Verdict: | Malicious activity |
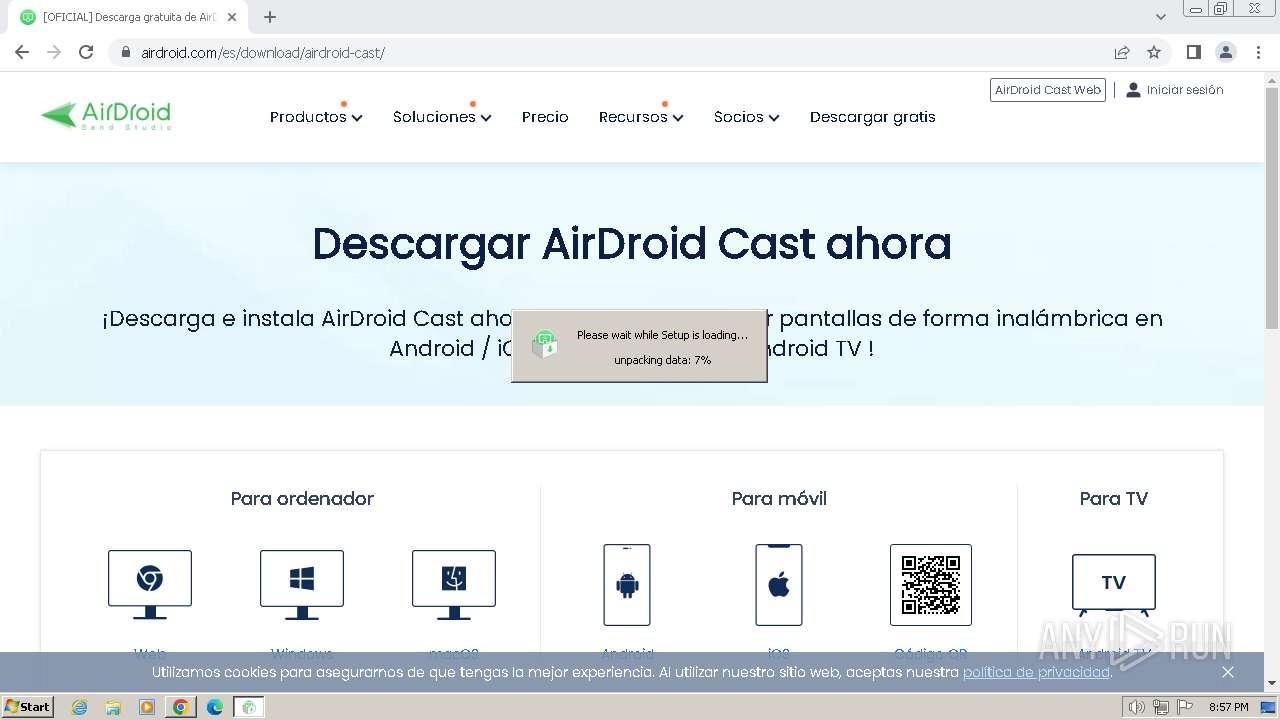
| Analysis date: | June 21, 2024, 19:53:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 94C95C6A3060C11CC80CE0D61CAA3DF1 |
| SHA1: | FA4E43B3E3B3EB80DA19383CC9DC17826430F23A |
| SHA256: | AD39A74C34D355D158BD44D12BB46B1F7CBA78DE9E125574024937789A9A5A04 |
| SSDEEP: | 3:N8DSLuMBz/sn:2OLDBQn |
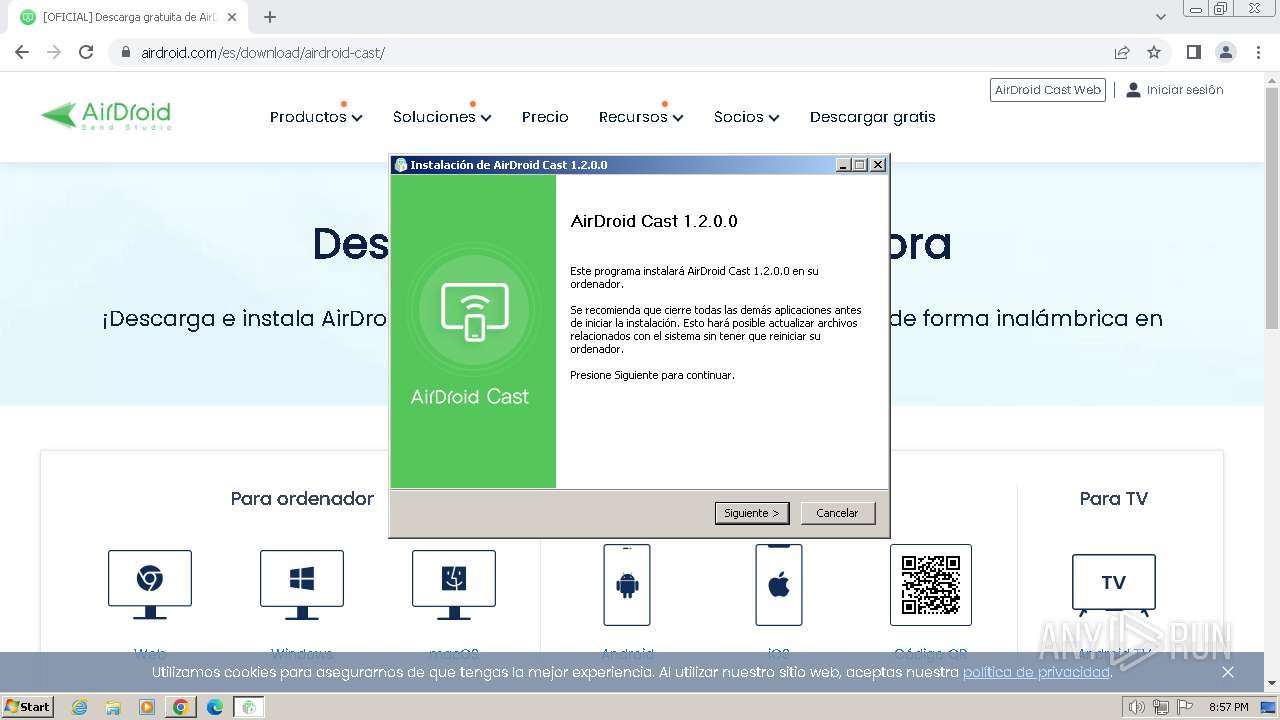
MALICIOUS
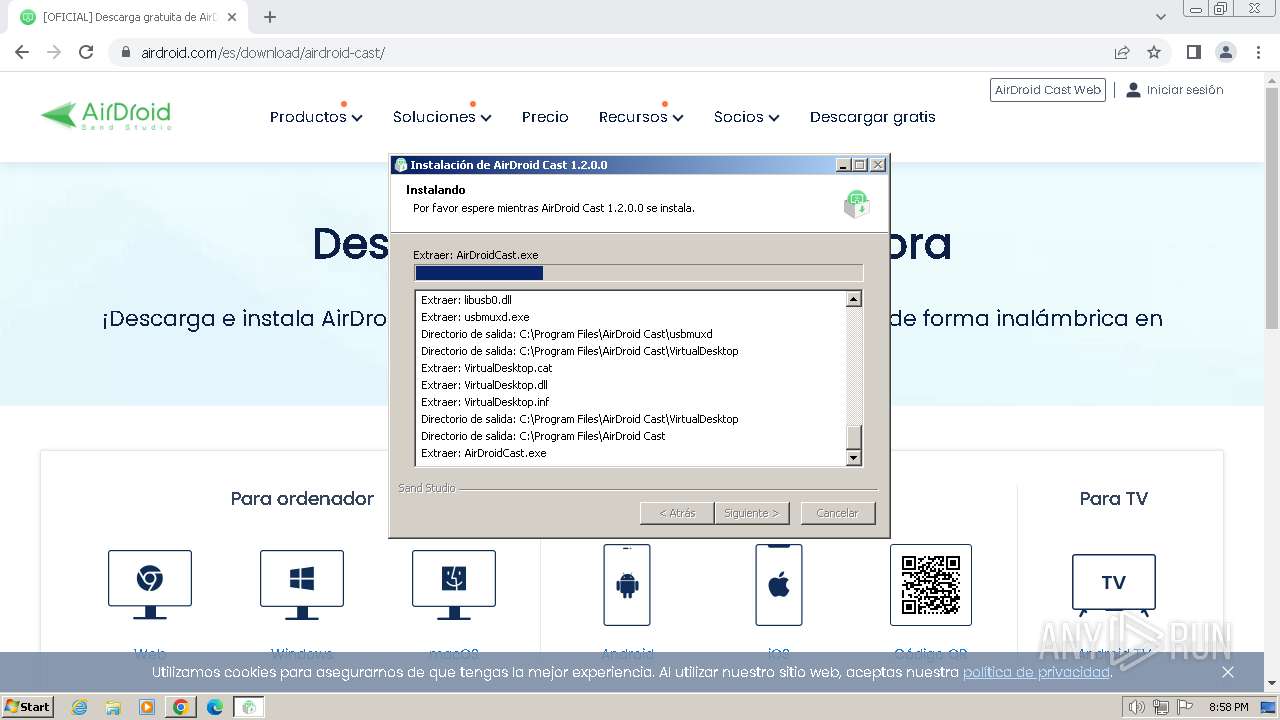
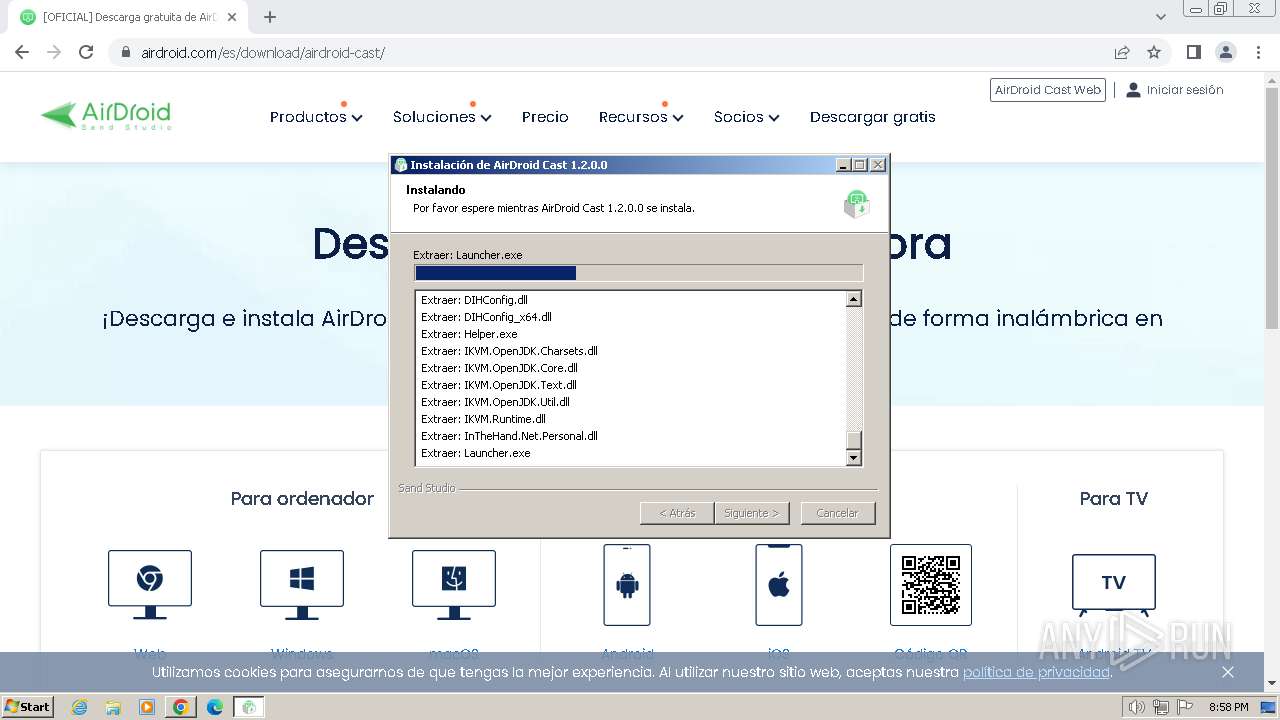
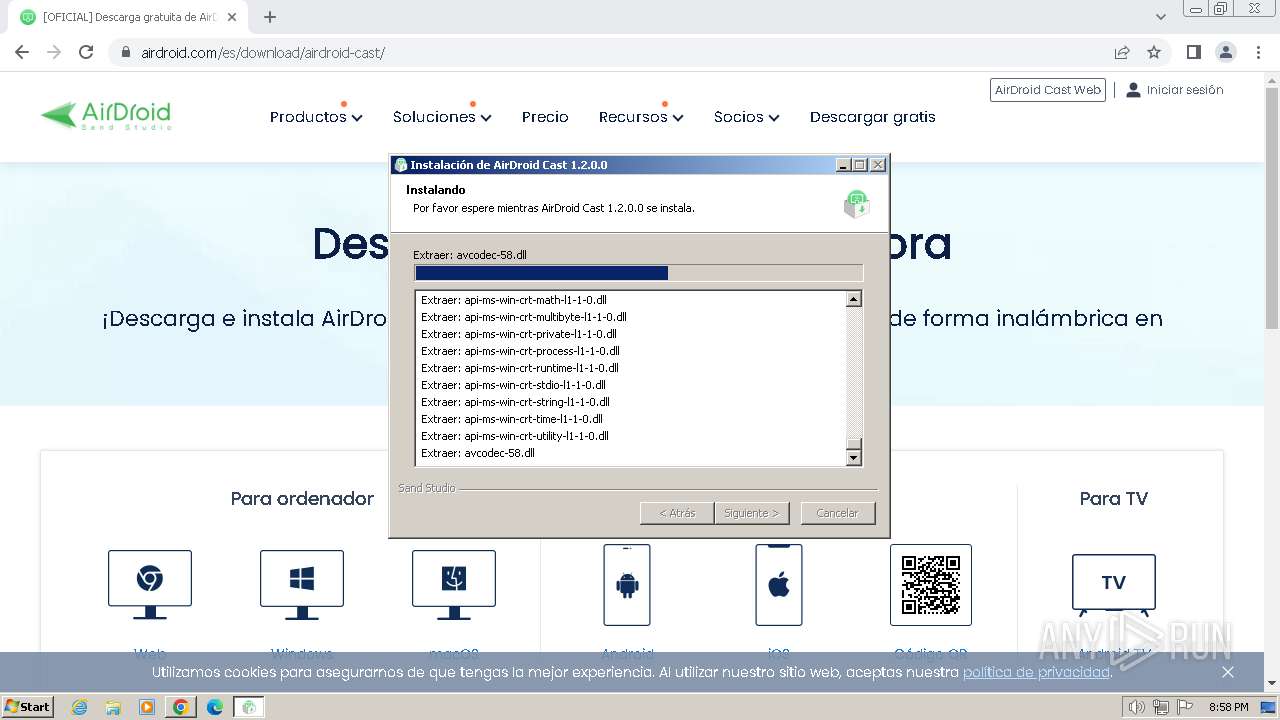
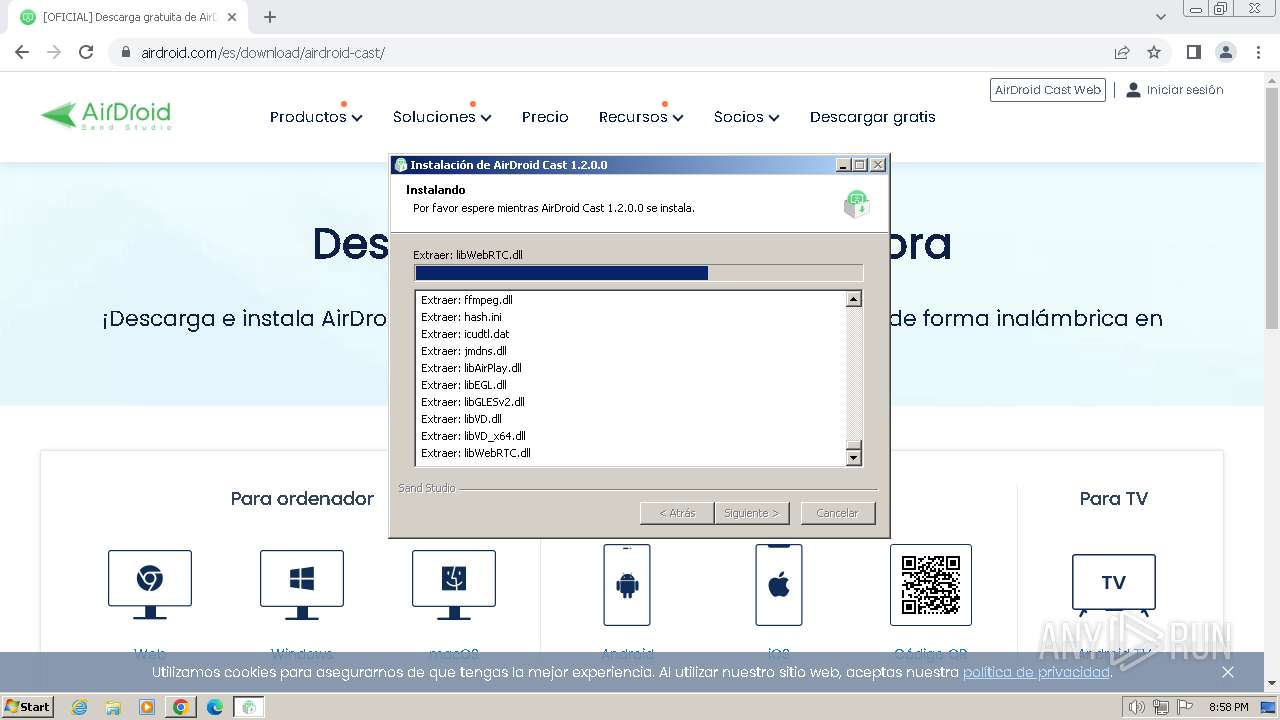
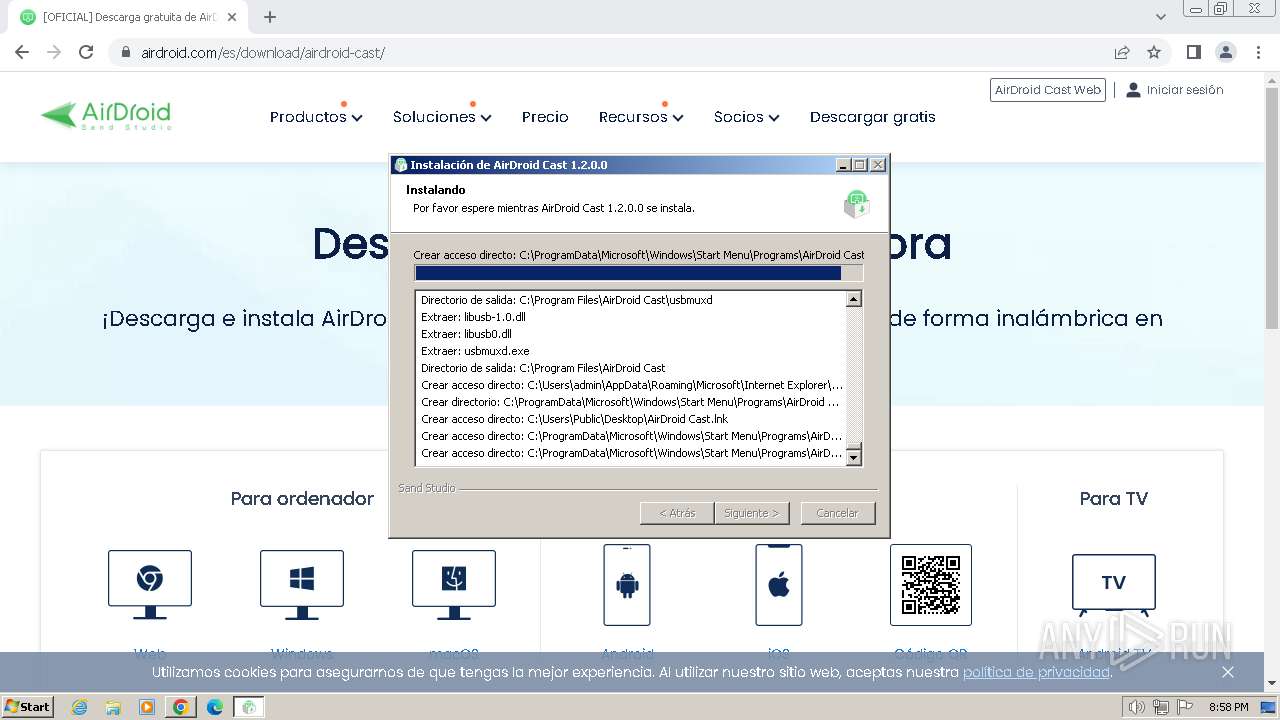
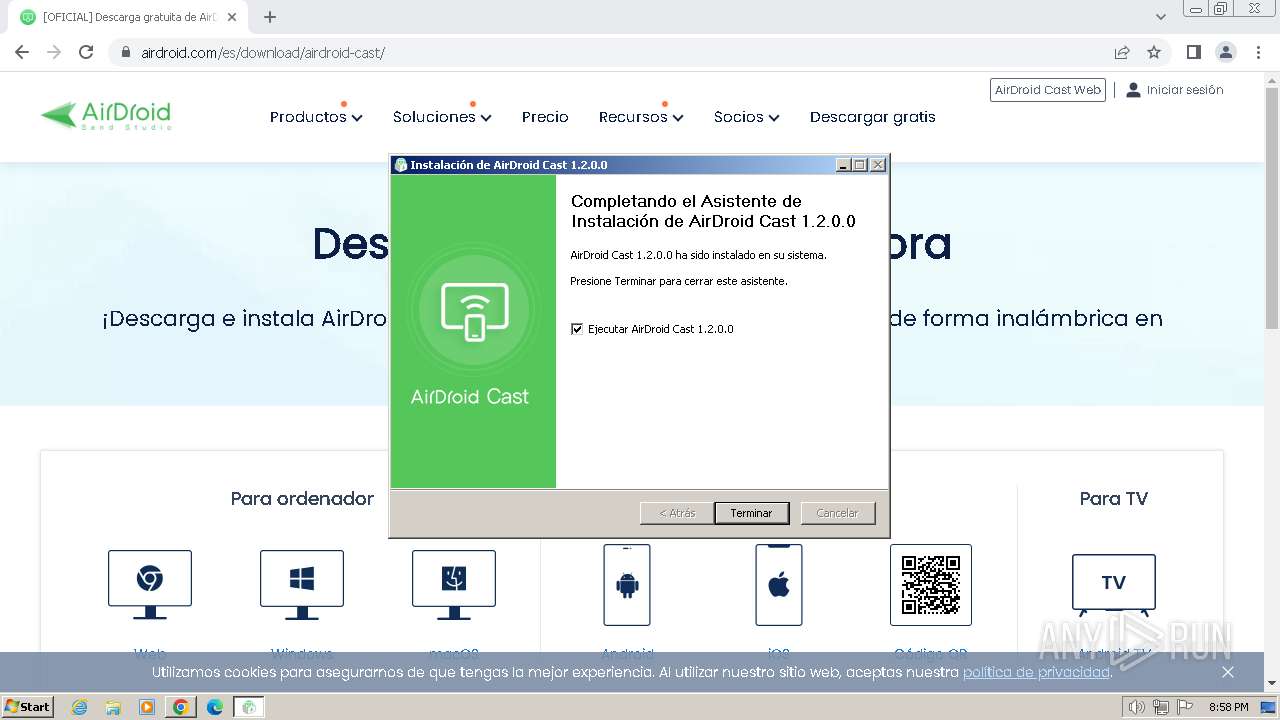
Drops the executable file immediately after the start
- AirDroid_Cast_Desktop_Client_1.2.0.0.exe (PID: 4016)
SUSPICIOUS
The process creates files with name similar to system file names
- AirDroid_Cast_Desktop_Client_1.2.0.0.exe (PID: 4016)
Malware-specific behavior (creating "System.dll" in Temp)
- AirDroid_Cast_Desktop_Client_1.2.0.0.exe (PID: 4016)
Executable content was dropped or overwritten
- AirDroid_Cast_Desktop_Client_1.2.0.0.exe (PID: 4016)
Reads the Internet Settings
- AirDroid_Cast_Desktop_Client_1.2.0.0.exe (PID: 4016)
- AirDroidCast.exe (PID: 1488)
- Helper.exe (PID: 1624)
Reads settings of System Certificates
- AirDroid_Cast_Desktop_Client_1.2.0.0.exe (PID: 4016)
- AirDroidCast.exe (PID: 1488)
- Helper.exe (PID: 1624)
Reads security settings of Internet Explorer
- AirDroid_Cast_Desktop_Client_1.2.0.0.exe (PID: 4016)
Checks Windows Trust Settings
- AirDroid_Cast_Desktop_Client_1.2.0.0.exe (PID: 4016)
The process drops C-runtime libraries
- AirDroid_Cast_Desktop_Client_1.2.0.0.exe (PID: 4016)
Process drops legitimate windows executable
- AirDroid_Cast_Desktop_Client_1.2.0.0.exe (PID: 4016)
Drops a system driver (possible attempt to evade defenses)
- AirDroid_Cast_Desktop_Client_1.2.0.0.exe (PID: 4016)
Creates a software uninstall entry
- AirDroid_Cast_Desktop_Client_1.2.0.0.exe (PID: 4016)
Application launched itself
- adb_helper.exe (PID: 1616)
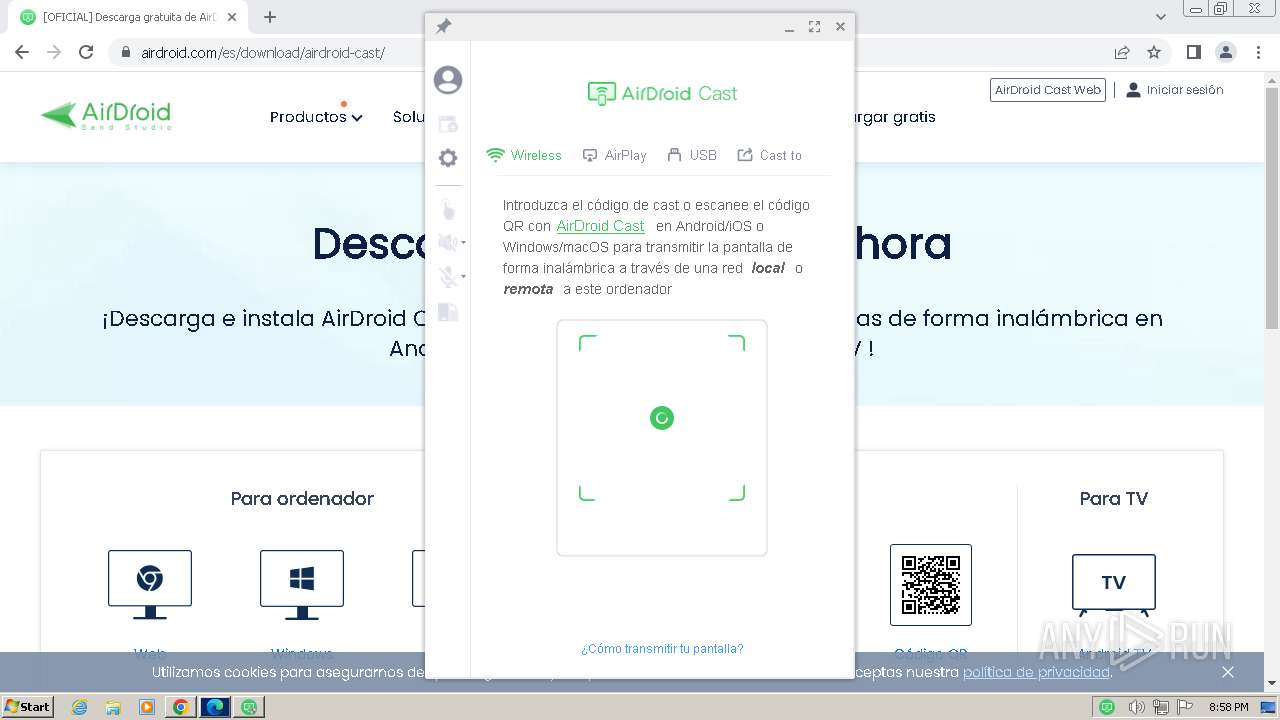
Connects to unusual port
- AirDroidCast.exe (PID: 1488)
INFO
Connects to unusual port
- chrome.exe (PID: 2100)
Drops the executable file immediately after the start
- chrome.exe (PID: 3700)
- chrome.exe (PID: 2984)
Executable content was dropped or overwritten
- chrome.exe (PID: 3700)
- chrome.exe (PID: 2984)
Application launched itself
- chrome.exe (PID: 3700)
- msedge.exe (PID: 580)
- msedge.exe (PID: 2296)
Create files in a temporary directory
- AirDroid_Cast_Desktop_Client_1.2.0.0.exe (PID: 4016)
- adb_helper.exe (PID: 900)
Reads the computer name
- AirDroid_Cast_Desktop_Client_1.2.0.0.exe (PID: 4016)
- Helper.exe (PID: 856)
- Launcher.exe (PID: 3248)
- AirDroidCast.exe (PID: 1488)
- usbmuxd.exe (PID: 2156)
- adb_helper.exe (PID: 900)
- Helper.exe (PID: 1624)
Reads Environment values
- AirDroid_Cast_Desktop_Client_1.2.0.0.exe (PID: 4016)
- Helper.exe (PID: 856)
- AirDroidCast.exe (PID: 1488)
- Helper.exe (PID: 1624)
Reads the machine GUID from the registry
- AirDroid_Cast_Desktop_Client_1.2.0.0.exe (PID: 4016)
- Helper.exe (PID: 856)
- AirDroidCast.exe (PID: 1488)
- Helper.exe (PID: 1624)
Checks proxy server information
- AirDroid_Cast_Desktop_Client_1.2.0.0.exe (PID: 4016)
Creates files or folders in the user directory
- AirDroid_Cast_Desktop_Client_1.2.0.0.exe (PID: 4016)
- Helper.exe (PID: 856)
- AirDroidCast.exe (PID: 1488)
Reads the software policy settings
- AirDroid_Cast_Desktop_Client_1.2.0.0.exe (PID: 4016)
- AirDroidCast.exe (PID: 1488)
- Helper.exe (PID: 1624)
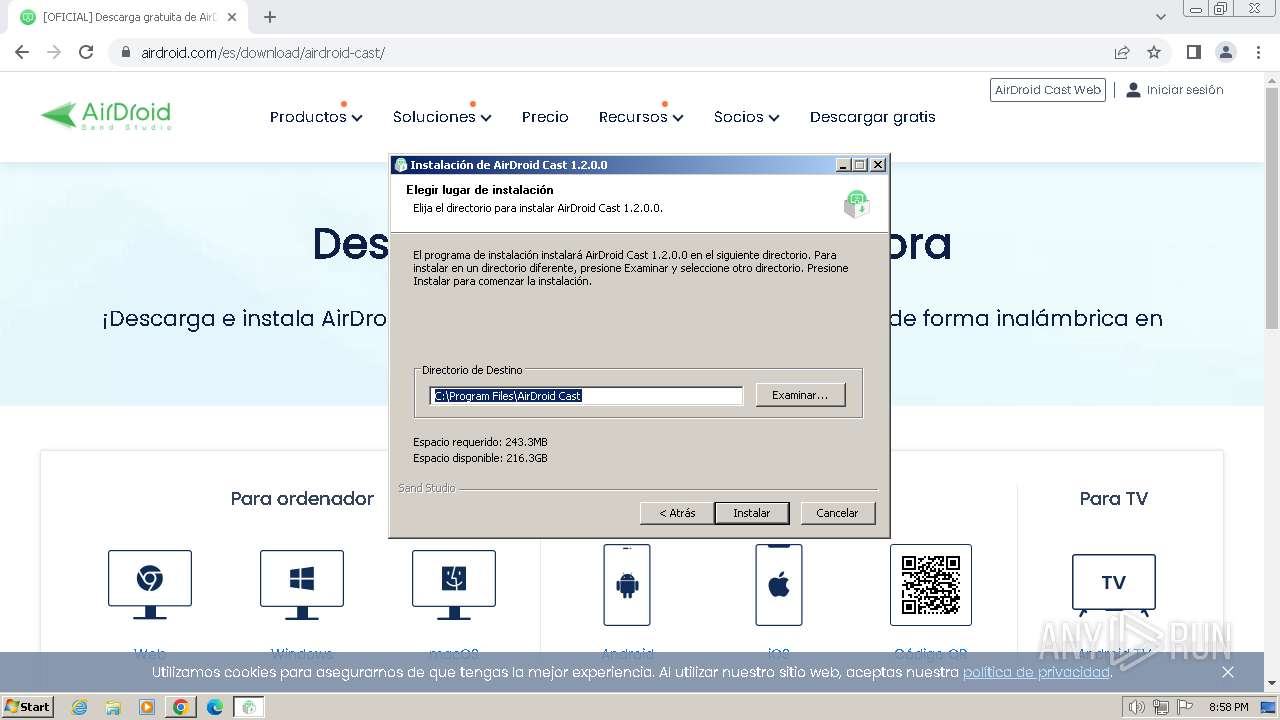
Creates files in the program directory
- AirDroid_Cast_Desktop_Client_1.2.0.0.exe (PID: 4016)
- Helper.exe (PID: 856)
- AirDroidCast.exe (PID: 1488)
- usbmuxd.exe (PID: 2156)
Checks supported languages
- Helper.exe (PID: 856)
- Launcher.exe (PID: 3248)
- AirDroidCast.exe (PID: 1488)
- adb_helper.exe (PID: 1616)
- usbmuxd.exe (PID: 2156)
- adb_helper.exe (PID: 900)
- Helper.exe (PID: 1624)
- AirDroid_Cast_Desktop_Client_1.2.0.0.exe (PID: 4016)
Manual execution by a user
- msedge.exe (PID: 2296)
Process checks computer location settings
- Helper.exe (PID: 856)
- AirDroidCast.exe (PID: 1488)
- Helper.exe (PID: 1624)
Disables trace logs
- Helper.exe (PID: 856)
- AirDroidCast.exe (PID: 1488)
- Helper.exe (PID: 1624)
Reads CPU info
- AirDroidCast.exe (PID: 1488)
.NET Reactor protector has been detected
- AirDroidCast.exe (PID: 1488)
The process uses the downloaded file
- chrome.exe (PID: 1916)
- chrome.exe (PID: 3700)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
101
Monitored processes
54
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 368 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=1112 --field-trial-handle=1092,i,13439446498662264084,12360342081122698839,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 580 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --single-argument https://www.airdroid.com/thankyou/install-airdroid-cast.html | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | AirDroid_Cast_Desktop_Client_1.2.0.0.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 856 | "/C:\Program Files\AirDroid Cast\helper.exe" "/shortcut" "C:\Program Files\AirDroid Cast\AirDroidCast.exe" | C:\Program Files\AirDroid Cast\Helper.exe | Launcher.exe | ||||||||||||
User: admin Company: Sand Studio Integrity Level: HIGH Description: AirDroid Cast Helper Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 900 | adb -L tcp:5037 fork-server server --reply-fd 332 | C:\Program Files\AirDroid Cast\IncludeAdb\adb_helper.exe | adb_helper.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 1488 | "C:\Program Files\AirDroid Cast\AirDroidCast.exe" | C:\Program Files\AirDroid Cast\AirDroidCast.exe | Launcher.exe | ||||||||||||
User: admin Company: Sand Studio Integrity Level: HIGH Description: AirDroid Cast Version: 1.2.0.0 Modules
| |||||||||||||||
| 1616 | "C:\Program Files\AirDroid Cast\IncludeAdb\adb_helper.exe" devices | C:\Program Files\AirDroid Cast\IncludeAdb\adb_helper.exe | AirDroidCast.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1624 | "C:\Program Files\AirDroid Cast\Helper.exe" /update /silent "C:\Program Files\AirDroid Cast\AirDroidCast.exe" "AirDroid Cast" https://srv3.airdroid.com/p20/cast/pcupgrade?v=1.2.0.0&type=63&lang=es-es&inner_version=1200&beta=0&app_ver=1.2.0.0&device_type=63&app_channel=0&language=es-es&version=1200&os_verion=6.1&jtoken=&mode_type=2&account_id=0&incremental_update=1 "" 0 0 0 0 1 "C:\Users\admin\AppData\Roaming\AirDroidCast\Cache\CacheInfo.txt" https://www.airdroid.com/{0}/cast/?_t=1718999909&app_ver=1.2.0.0&device_type=63&app_channel=0&language=es-es&version=1200&os_verion=6.1&jtoken=&mode_type=2&account_id=0 "" -999 | C:\Program Files\AirDroid Cast\Helper.exe | AirDroidCast.exe | ||||||||||||
User: admin Company: Sand Studio Integrity Level: HIGH Description: AirDroid Cast Helper Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3852 --field-trial-handle=1092,i,13439446498662264084,12360342081122698839,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1840 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --first-renderer-process --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2120 --field-trial-handle=1240,i,18421677357265817675,10775664050766390778,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3712 --field-trial-handle=1092,i,13439446498662264084,12360342081122698839,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
53 776
Read events
53 483
Write events
276
Delete events
17
Modification events
| (PID) Process: | (3700) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3700) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3700) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3700) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3700) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3700) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3700) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3700) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3700) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3700) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
130
Suspicious files
282
Text files
559
Unknown types
230
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF4f171.TMP | — | |
MD5:— | SHA256:— | |||
| 3700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF4f142.TMP | text | |
MD5:358570F689377CE6838812643E03734B | SHA256:5B41FCC2E1A843AEAB9437B06E27B798870FF10D86A51B163BF48862BCD32590 | |||
| 3700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF4f171.TMP | text | |
MD5:ECD3386BCC950E73B86EB128A5F57622 | SHA256:C9A068EAFBC587EDFC89392F64DDD350EEB96C5CF195CDB030BAB8F6DD33833B | |||
| 3700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 3700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\d8fbae4d-43dc-4d48-a7fe-dcac5e212ae3.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 3700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF4fd29.TMP | — | |
MD5:— | SHA256:— | |||
| 3700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:456D3EF989973A7C218E338A6CFFAD25 | SHA256:75631D994431F254B94255C50038A3657BFC45D76FCE9D794D514E57CA678872 | |||
| 3700 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF4f374.TMP | text | |
MD5:AD0DB8476493577A67FA94A162B646C4 | SHA256:304FB5B4FD83D4A9FF1EF4CF20232A1783169C148297BFE37ED24A1D22A74F2B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
47
TCP/UDP connections
138
DNS requests
203
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1060 | svchost.exe | GET | 304 | 23.211.242.80:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a9f83325acc8ca75 | unknown | — | — | unknown |
1372 | svchost.exe | GET | 304 | 88.221.87.139:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33775f6043c93e33 | unknown | — | — | unknown |
844 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 88.221.87.160:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 23.200.189.225:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | — | — | unknown |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | — | — | unknown |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | — | — | unknown |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ad3rm3ciqs3fjr4bc4x5vwuildeq_9.49.1/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.49.1_all_ixzyrcu7pvmgu5pjv6enfqq6wa.crx3 | unknown | — | — | unknown |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/lvx4ng4qhhp4kpddwmwjgzrumu_2024.6.5.140657/eeigpngbgcognadeebkilcpcaedhellh_2024.06.05.140657_all_ccj7nw5iotmqmvpbhiiji4wfca.crx3 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2564 | svchost.exe | 239.255.255.250:3702 | — | — | — | whitelisted |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3700 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2100 | chrome.exe | 108.177.96.84:443 | accounts.google.com | GOOGLE | US | unknown |
2100 | chrome.exe | 75.2.2.223:443 | www.airdroid.com | AMAZON-02 | US | unknown |
2100 | chrome.exe | 142.250.186.99:443 | fonts.gstatic.com | GOOGLE | US | whitelisted |
2100 | chrome.exe | 143.204.215.116:443 | img-4-cdn.airdroid.com | AMAZON-02 | US | unknown |
2100 | chrome.exe | 142.250.185.142:443 | www.google-analytics.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.airdroid.com |
| whitelisted |
accounts.google.com |
| shared |
css-1-cdn.airdroid.com |
| unknown |
js-1-cdn.airdroid.com |
| unknown |
fonts.gstatic.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
cdn1.airdroid.com |
| whitelisted |
img-3-cdn.airdroid.com |
| unknown |
img-4-cdn.airdroid.com |
| unknown |
img-5-cdn.airdroid.com |
| unknown |
Threats
Process | Message |
|---|---|
Helper.exe | FTH: (856): *** Fault tolerant heap shim applied to current process. This is usually due to previous crashes. ***
|
AirDroidCast.exe | FTH: (1488): *** Fault tolerant heap shim applied to current process. This is usually due to previous crashes. ***
|
adb_helper.exe | FTH: (1616): *** Fault tolerant heap shim applied to current process. This is usually due to previous crashes. ***
|
usbmuxd.exe | FTH: (2156): *** Fault tolerant heap shim applied to current process. This is usually due to previous crashes. ***
|
adb_helper.exe | FTH: (900): *** Fault tolerant heap shim applied to current process. This is usually due to previous crashes. ***
|
Helper.exe | FTH: (1624): *** Fault tolerant heap shim applied to current process. This is usually due to previous crashes. ***
|