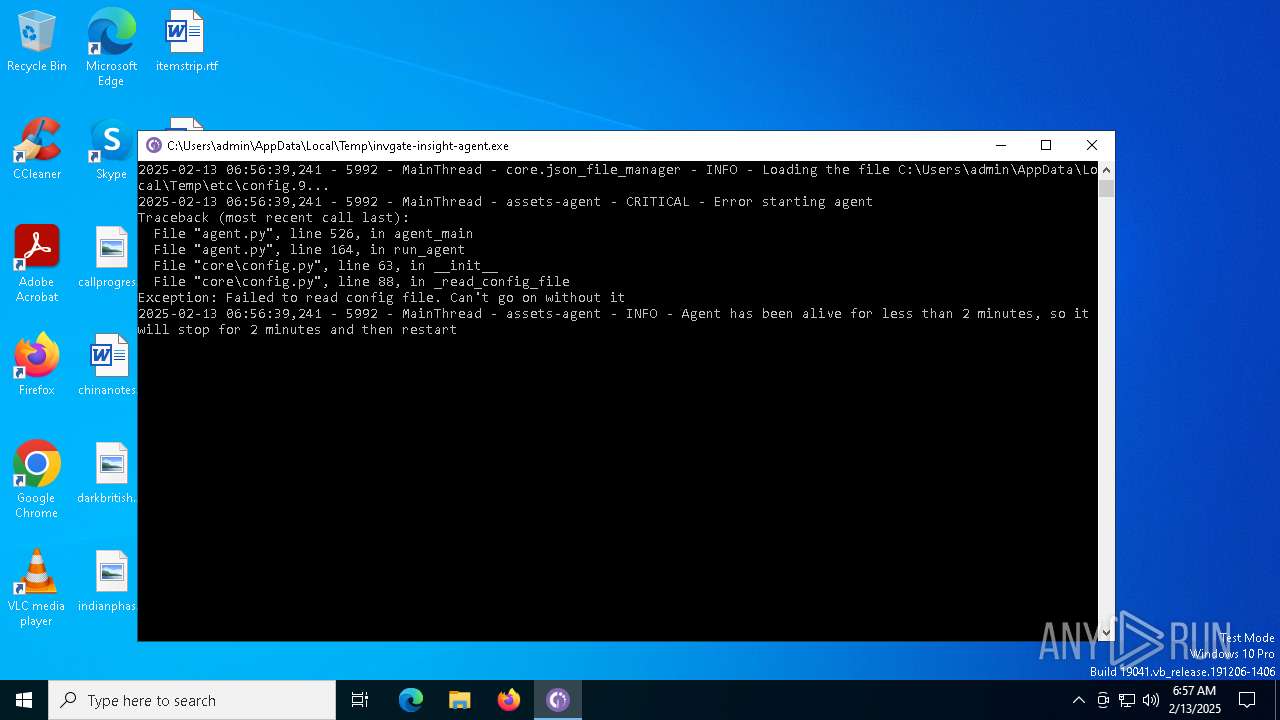
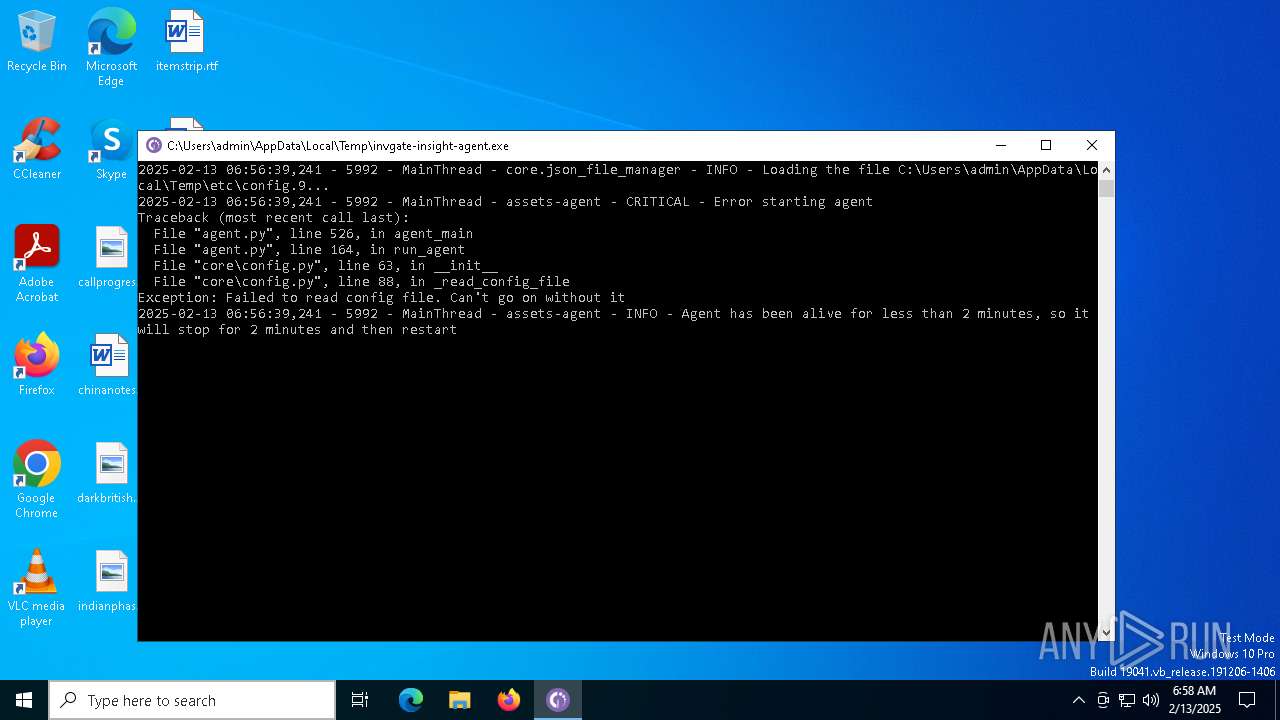
| File name: | invgate-insight-agent.exe |
| Full analysis: | https://app.any.run/tasks/706b9e3f-2dce-43bf-a760-851135e6524e |
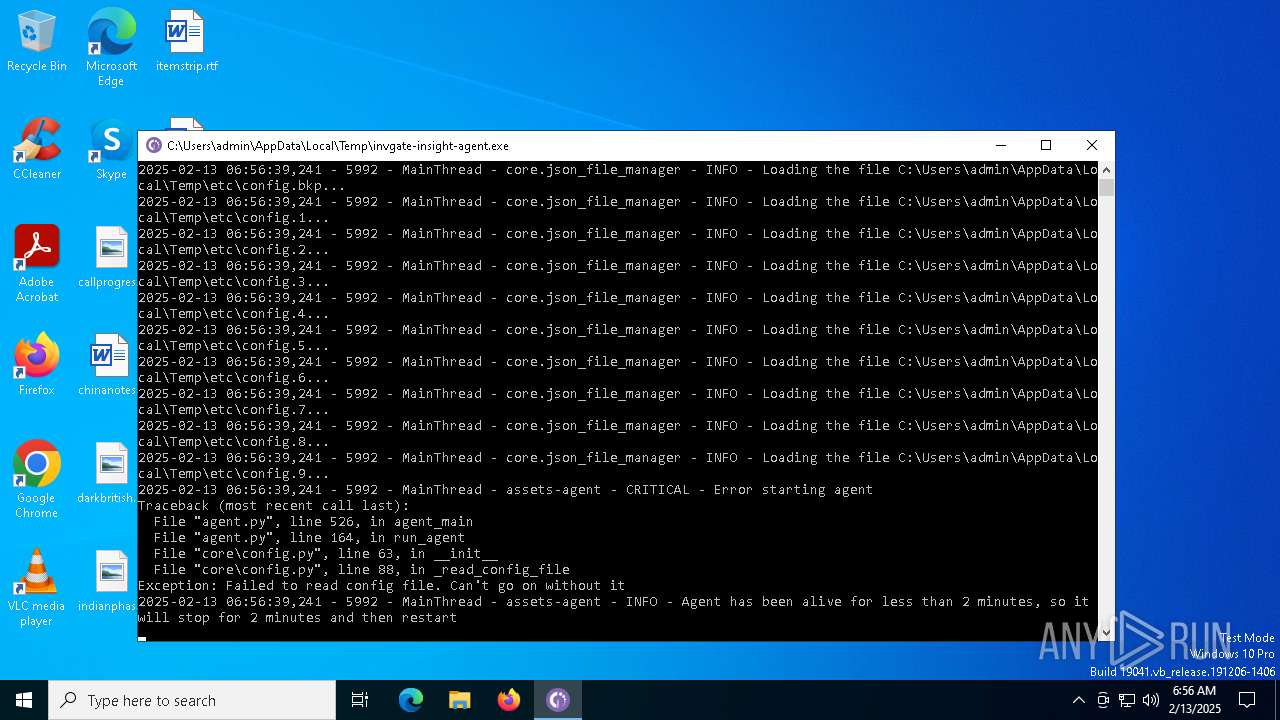
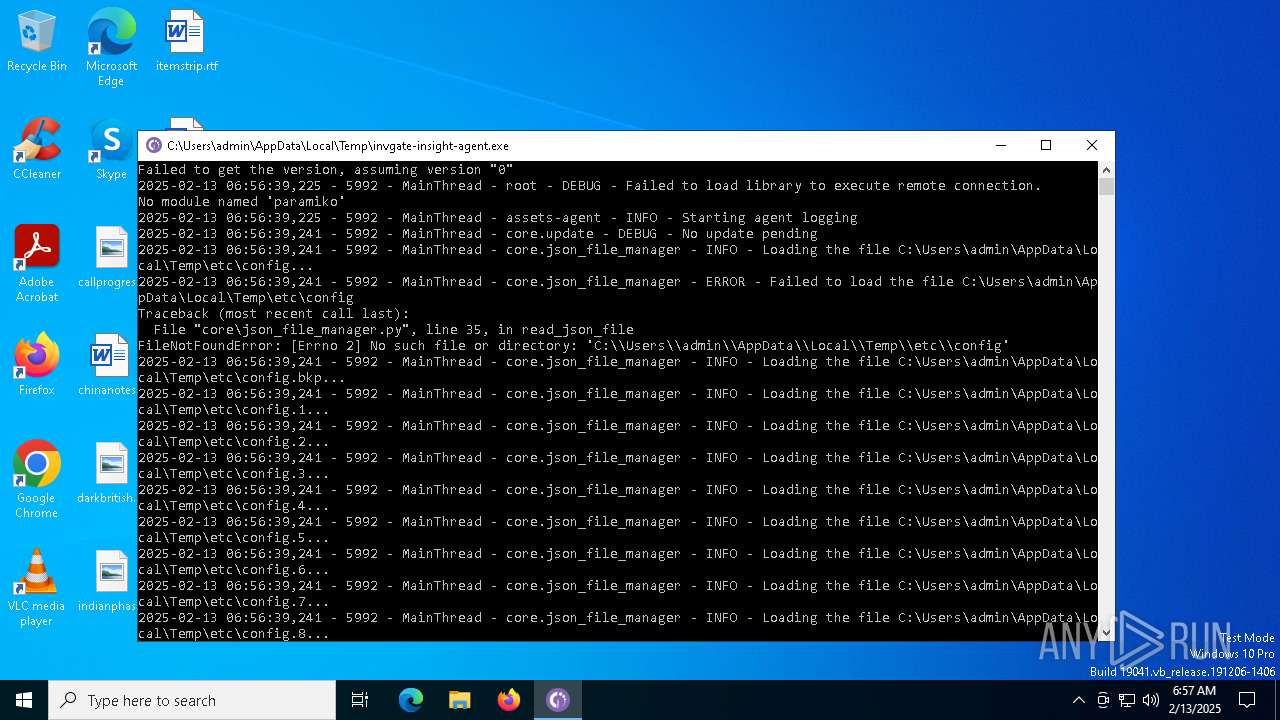
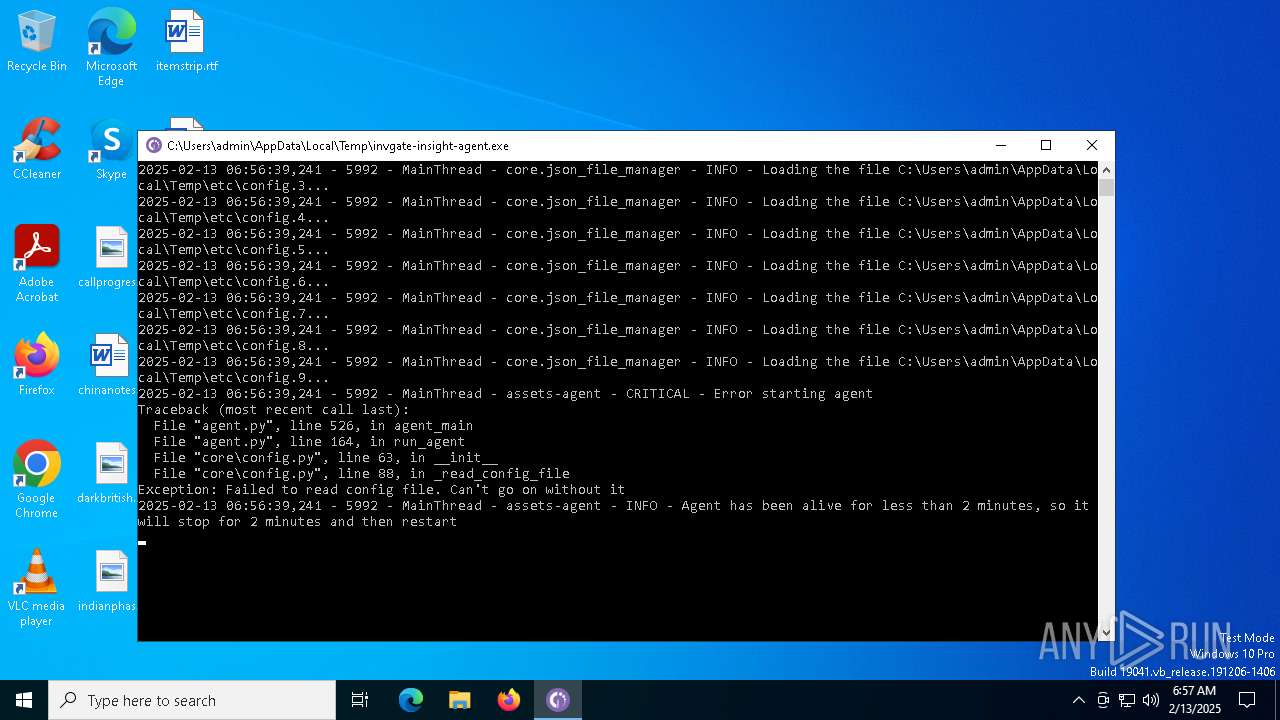
| Verdict: | Malicious activity |
| Analysis date: | February 13, 2025, 06:55:58 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (console) Intel 80386, for MS Windows, 5 sections |
| MD5: | AB9B30AD762905D53138D9A077982FA2 |
| SHA1: | 0C158790ABB012830DC9EA02CF3354FEB7190A4C |
| SHA256: | AD303DCE81EDB26E92EEDE53C552A9645C2660F1DA88E3F7EDF1FD78C76B9289 |
| SSDEEP: | 98304:+AgN7yvI8OkqsgfEmwfFne+T7OUJKQkKT+s7OIykr8qoiBDcTDDqrlmVbnM8gPa6:jCv+2kHEm3A4ajardWOee |
MALICIOUS
No malicious indicators.SUSPICIOUS
Process drops legitimate windows executable
- invgate-insight-agent.exe (PID: 6276)
The process drops C-runtime libraries
- invgate-insight-agent.exe (PID: 6276)
Executable content was dropped or overwritten
- invgate-insight-agent.exe (PID: 6276)
Process drops python dynamic module
- invgate-insight-agent.exe (PID: 6276)
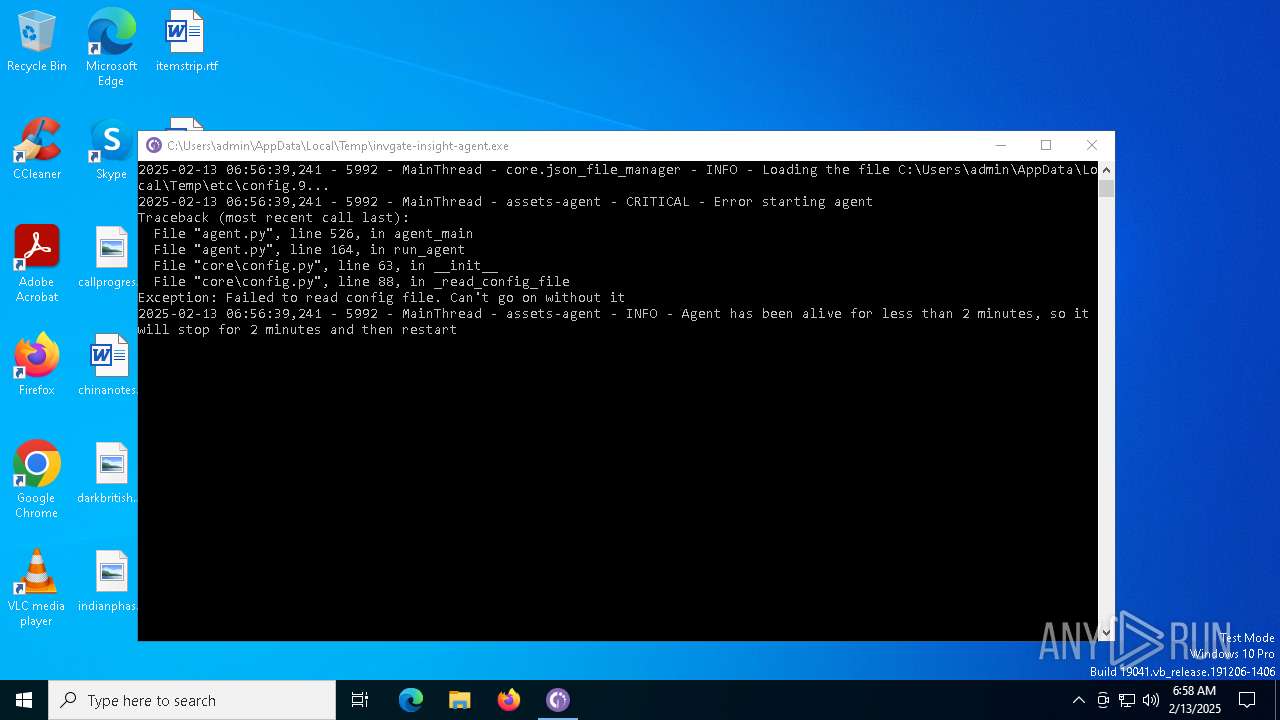
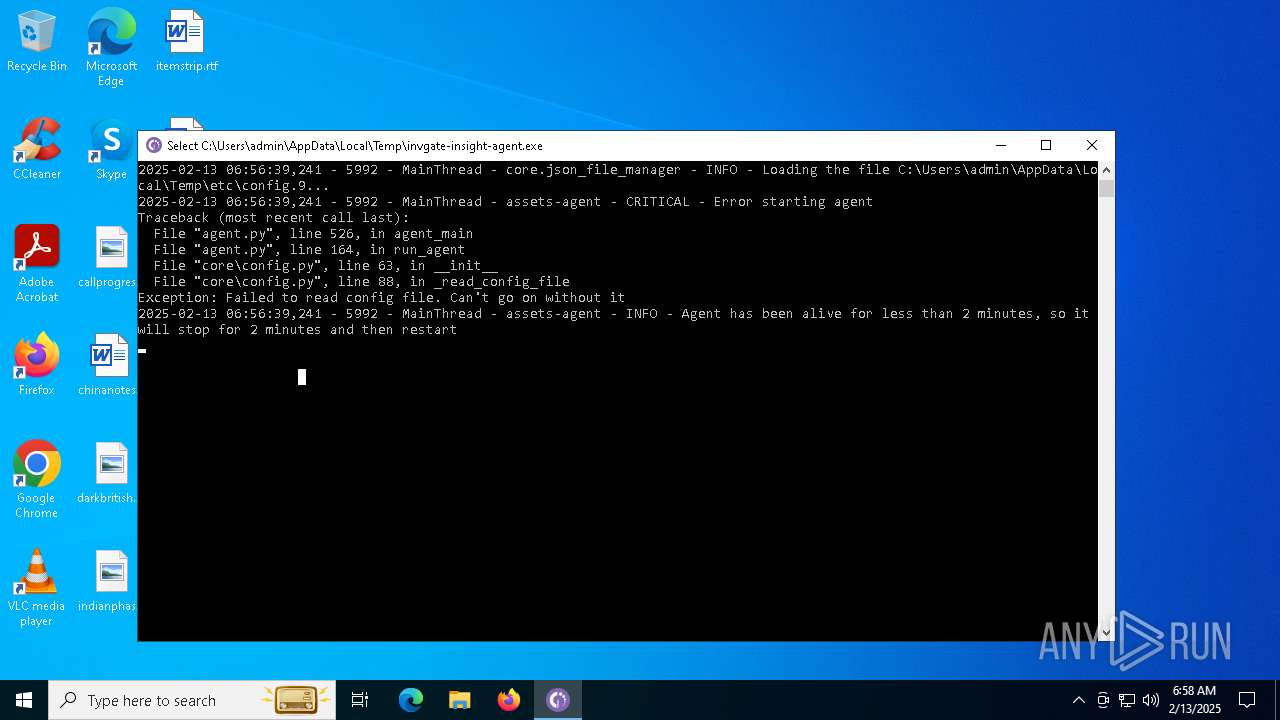
Application launched itself
- invgate-insight-agent.exe (PID: 6276)
Starts CMD.EXE for commands execution
- invgate-insight-agent.exe (PID: 3808)
Loads Python modules
- invgate-insight-agent.exe (PID: 3808)
INFO
Checks supported languages
- invgate-insight-agent.exe (PID: 6276)
- invgate-insight-agent.exe (PID: 3808)
Reads the computer name
- invgate-insight-agent.exe (PID: 6276)
- invgate-insight-agent.exe (PID: 3808)
The sample compiled with english language support
- invgate-insight-agent.exe (PID: 6276)
Create files in a temporary directory
- invgate-insight-agent.exe (PID: 6276)
- invgate-insight-agent.exe (PID: 3808)
PyInstaller has been detected (YARA)
- invgate-insight-agent.exe (PID: 6276)
- invgate-insight-agent.exe (PID: 3808)
Reads the machine GUID from the registry
- invgate-insight-agent.exe (PID: 3808)
Checks operating system version
- invgate-insight-agent.exe (PID: 3808)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:11:11 17:31:20+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.36 |
| CodeSize: | 151552 |
| InitializedDataSize: | 361984 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9ab0 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows command line |
Total processes
133
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2928 | C:\WINDOWS\system32\cmd.exe /c "ver" | C:\Windows\SysWOW64\cmd.exe | — | invgate-insight-agent.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3808 | "C:\Users\admin\AppData\Local\Temp\invgate-insight-agent.exe" | C:\Users\admin\AppData\Local\Temp\invgate-insight-agent.exe | — | invgate-insight-agent.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 6276 | "C:\Users\admin\AppData\Local\Temp\invgate-insight-agent.exe" | C:\Users\admin\AppData\Local\Temp\invgate-insight-agent.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 6284 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | invgate-insight-agent.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
250
Read events
250
Write events
0
Delete events
0
Modification events
Executable files
86
Suspicious files
651
Text files
55
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6276 | invgate-insight-agent.exe | C:\Users\admin\AppData\Local\Temp\_MEI62762\VCRUNTIME140.dll | executable | |
MD5:A37EE36B536409056A86F50E67777DD7 | SHA256:8934AAEB65B6E6D253DFE72DEA5D65856BD871E989D5D3A2A35EDFE867BB4825 | |||
| 6276 | invgate-insight-agent.exe | C:\Users\admin\AppData\Local\Temp\_MEI62762\Pythonwin\mfc140u.dll | executable | |
MD5:EC85D7A09109D1F52F165CFBA6DB8B33 | SHA256:CFBA55B3D6891A0F9E90726094DC4E57553C3443CEF156E5FFCD5965AC4E8E3F | |||
| 6276 | invgate-insight-agent.exe | C:\Users\admin\AppData\Local\Temp\_MEI62762\_ctypes.pyd | executable | |
MD5:9033E078A2EC5B7828AFE043A7F44E48 | SHA256:5117E63E41F4399B4BAFE45AE63F311A8E908822A46E7DC7AFC5D36993188B1A | |||
| 6276 | invgate-insight-agent.exe | C:\Users\admin\AppData\Local\Temp\_MEI62762\_asyncio.pyd | executable | |
MD5:7D7CA088F47CD323AC7F04B94BBE46A4 | SHA256:D426CC6AF9E9135553EE920EDADFC5BB7BF689D20A63D6A623AABE1C5FE0C629 | |||
| 6276 | invgate-insight-agent.exe | C:\Users\admin\AppData\Local\Temp\_MEI62762\_decimal.pyd | executable | |
MD5:ECB399CB2E6366FBFD51411A194075E0 | SHA256:E80C2B93207C20ACFA089922277EC30FFDBADF624A4C231E185773193D285F09 | |||
| 6276 | invgate-insight-agent.exe | C:\Users\admin\AppData\Local\Temp\_MEI62762\_multiprocessing.pyd | executable | |
MD5:A2E0D6585A9C79D5C690541F6827A8B7 | SHA256:807EA775E7CA55B302F8B1A15125C4D3BB72D5122C83C3AC9F3EC545650F9009 | |||
| 6276 | invgate-insight-agent.exe | C:\Users\admin\AppData\Local\Temp\_MEI62762\_hashlib.pyd | executable | |
MD5:831087524BEDED5624BA25EA854736F9 | SHA256:447DAC4D9F76BFA0F1359F2CEBAB8F99D92F762CE6B174485837564959C6513D | |||
| 6276 | invgate-insight-agent.exe | C:\Users\admin\AppData\Local\Temp\_MEI62762\_cffi_backend.cp38-win32.pyd | executable | |
MD5:0C51B8553B877FF120E7A6E5EADFBAE1 | SHA256:91C2BF559A5CBF201EE453729858654DFADEBE8176E38878032B0EB3C68A25D6 | |||
| 6276 | invgate-insight-agent.exe | C:\Users\admin\AppData\Local\Temp\_MEI62762\_overlapped.pyd | executable | |
MD5:07D2269A1F89411F70F223C1EDCDDBF6 | SHA256:D701BAB0EF4E5C30316C2ACF88D77DF5C7D1C146790F1660AC967C6CA451FDF4 | |||
| 6276 | invgate-insight-agent.exe | C:\Users\admin\AppData\Local\Temp\_MEI62762\api-ms-win-core-console-l1-1-0.dll | executable | |
MD5:37DA7F6961082DD96A537235DD89B114 | SHA256:6EE46C6B6727EB77BCBCDD54DC506680CA34AF7BC7CA433B77775DE90358844E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
38
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.9:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.222.10.99:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6236 | SIHClient.exe | GET | 200 | 23.222.10.99:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6236 | SIHClient.exe | GET | 200 | 23.222.10.99:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6428 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 184.86.11.11:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 2.16.164.9:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.222.10.99:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5064 | SearchApp.exe | 2.19.122.17:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
1076 | svchost.exe | 2.19.106.8:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
1176 | svchost.exe | 40.126.31.1:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 184.86.251.4:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |