| File name: | EUInstall.exe |
| Full analysis: | https://app.any.run/tasks/728209ad-4c90-495e-8620-c539a6f9bfa4 |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2020, 12:26:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 4C78B388AFACD6E037D2707D76315F3F |
| SHA1: | 02AF0115C24B826FC0532EF55E17A0C20A8CAE61 |
| SHA256: | AD2ED7CFF4CA5EB7491A90C49C2F5E0CB74637D86566F13A66AF6026936F1457 |
| SSDEEP: | 196608:gVEkEVTOqqtpkhf+8EB9tWhtdwin3cKmty0e6nmcS2wLB:6JEwqqtpkUxWhtqit0e6mcS5V |
MALICIOUS
Application was dropped or rewritten from another process
- HDPreinstall.exe (PID: 3816)
Registers / Runs the DLL via REGSVR32.EXE
- EUInstall.tmp (PID: 2056)
Loads dropped or rewritten executable
- regsvr32.exe (PID: 2096)
SUSPICIOUS
Executable content was dropped or overwritten
- EUInstall.exe (PID: 2740)
- EUInstall.exe (PID: 2536)
- DrvInst.exe (PID: 2772)
- HDPreinstall.exe (PID: 3816)
- EUInstall.tmp (PID: 2056)
Reads the Windows organization settings
- EUInstall.tmp (PID: 2056)
Reads Windows owner or organization settings
- EUInstall.tmp (PID: 2056)
Executed via COM
- DrvInst.exe (PID: 2772)
Creates files in the Windows directory
- EUInstall.tmp (PID: 2056)
- DrvInst.exe (PID: 2772)
Modifies the open verb of a shell class
- EUInstall.tmp (PID: 2056)
Creates files in the driver directory
- DrvInst.exe (PID: 2772)
Removes files from Windows directory
- DrvInst.exe (PID: 2772)
Creates COM task schedule object
- regsvr32.exe (PID: 2096)
Starts CMD.EXE for commands execution
- EUInstall.tmp (PID: 2056)
INFO
Application was dropped or rewritten from another process
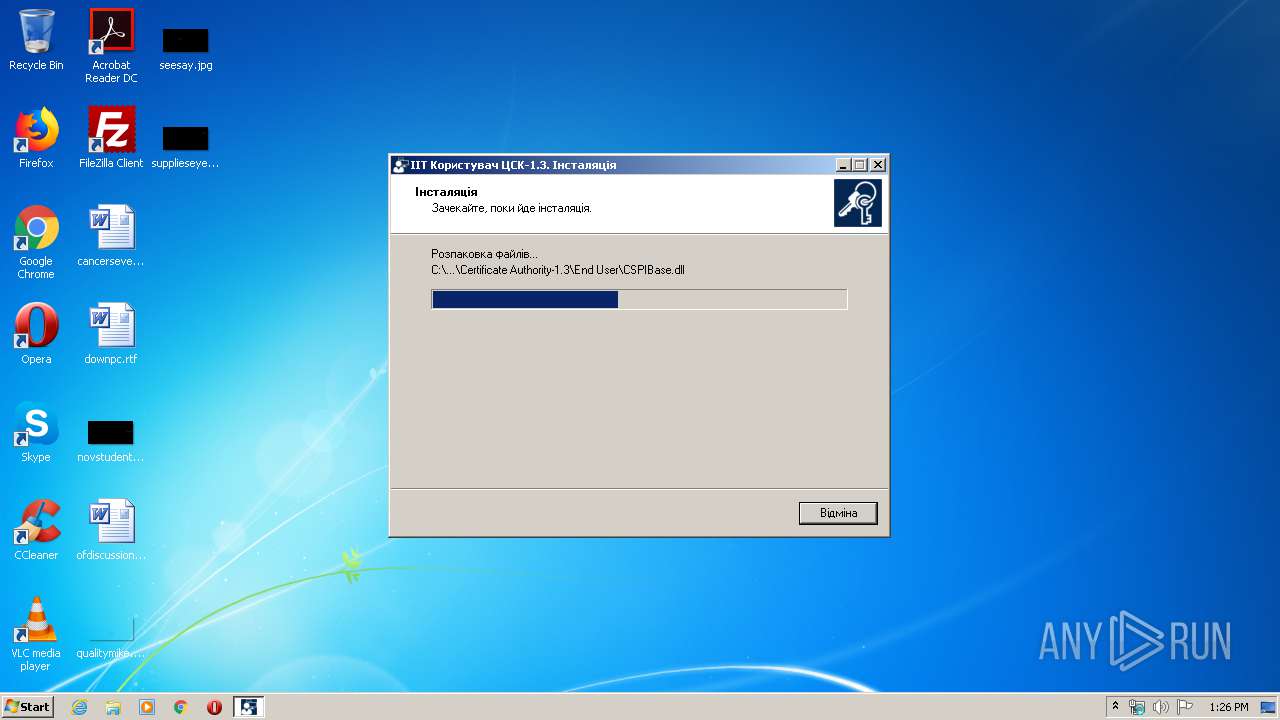
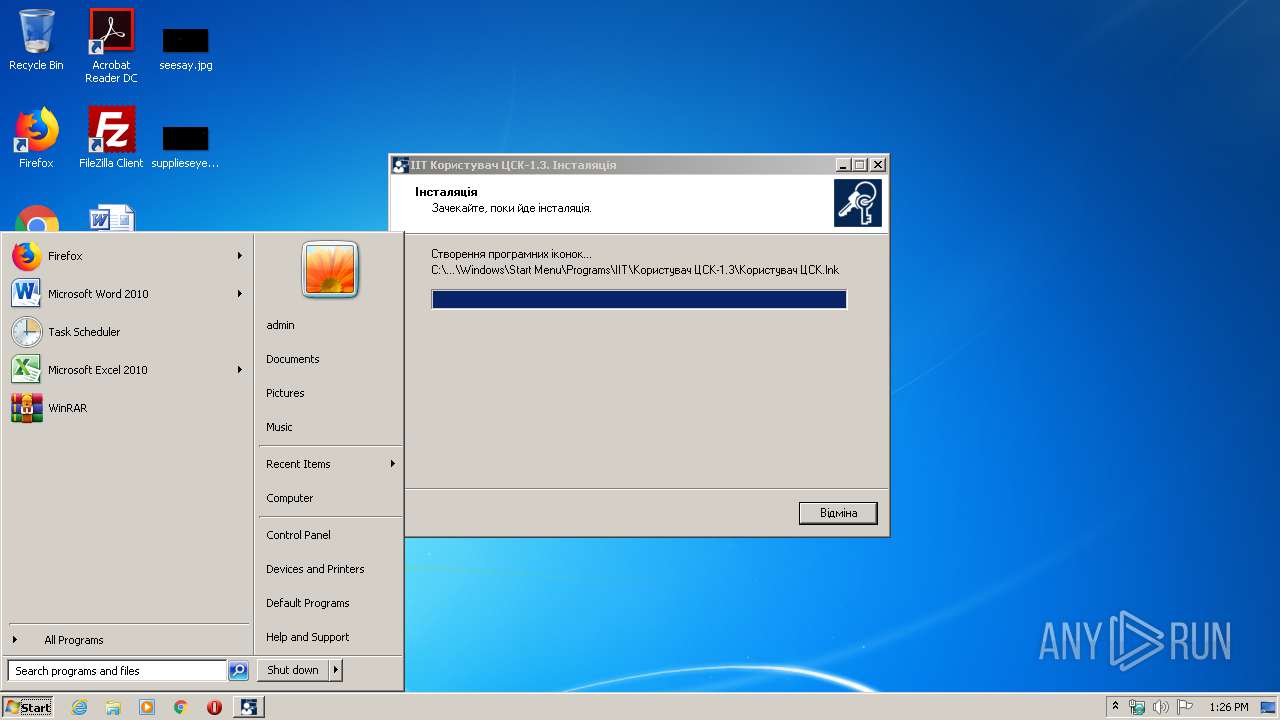
- EUInstall.tmp (PID: 2056)
- EUInstall.tmp (PID: 3664)
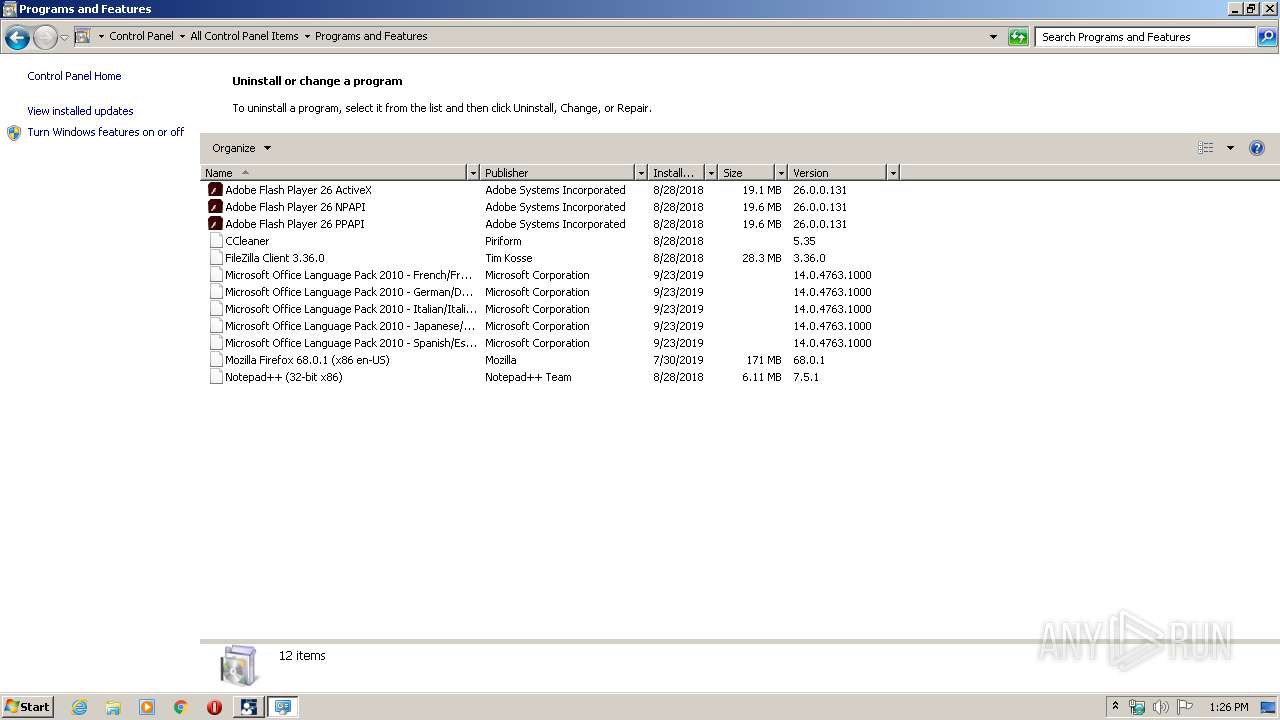
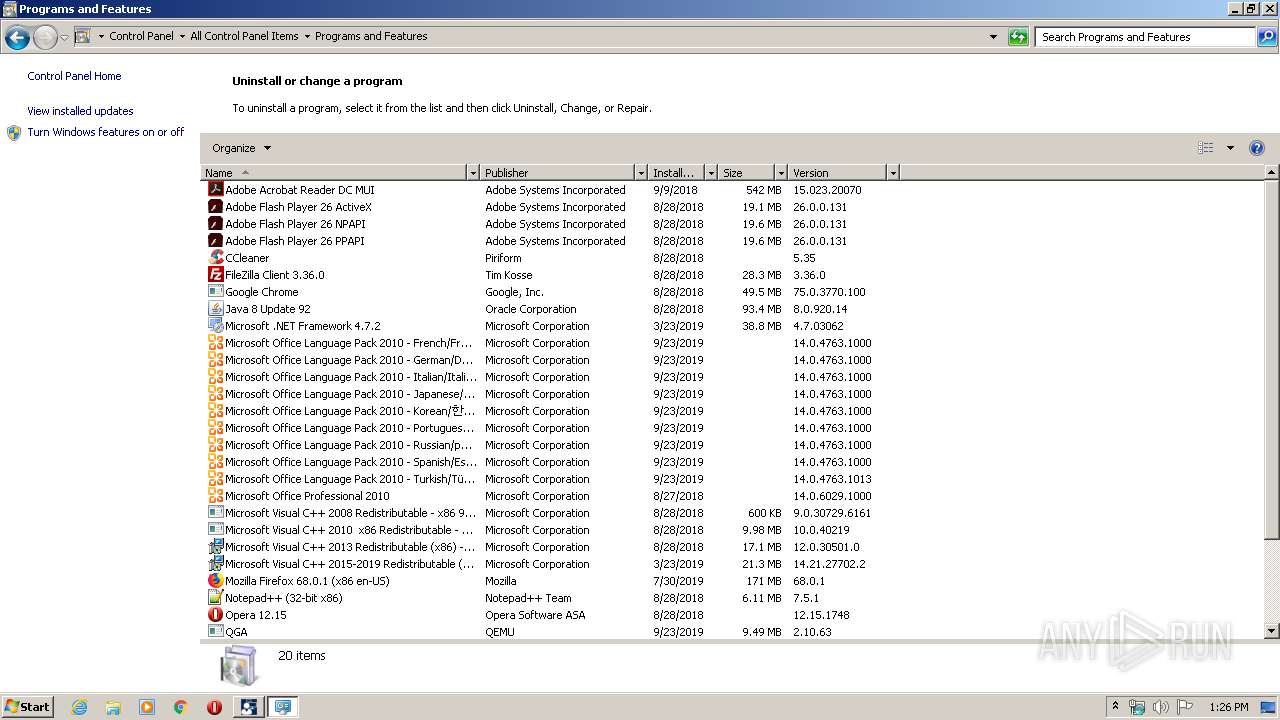
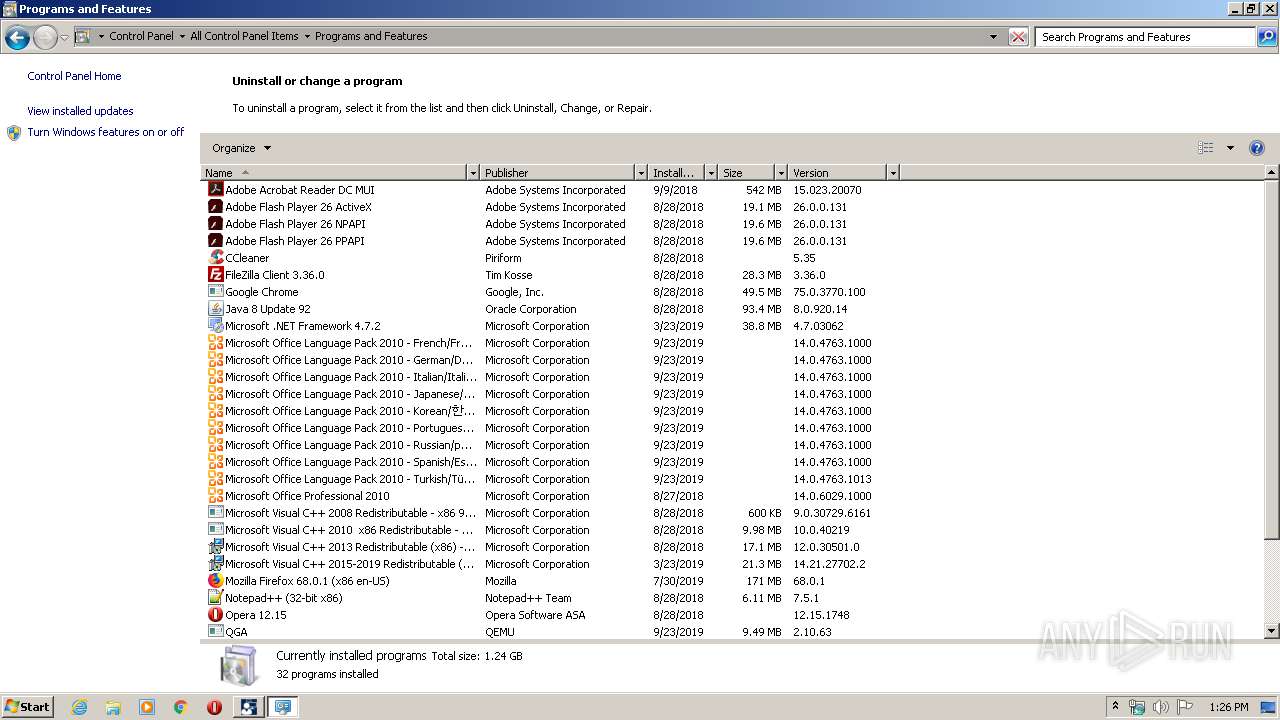
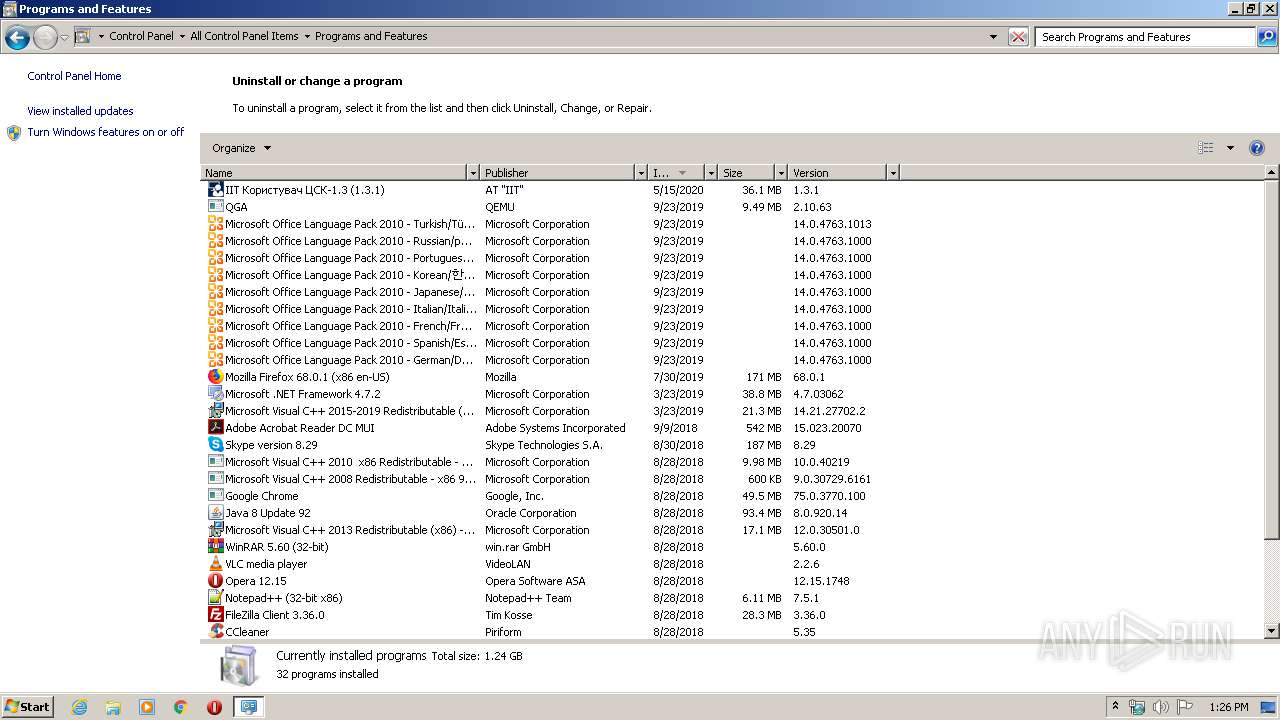
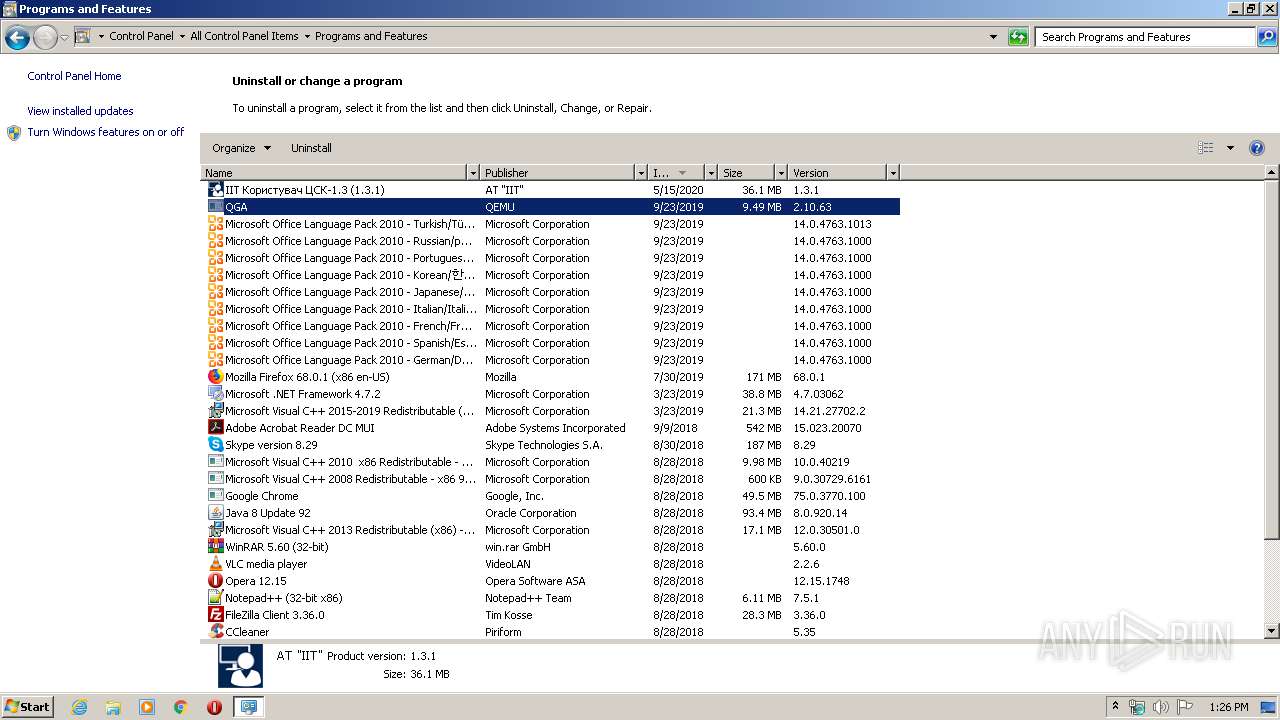
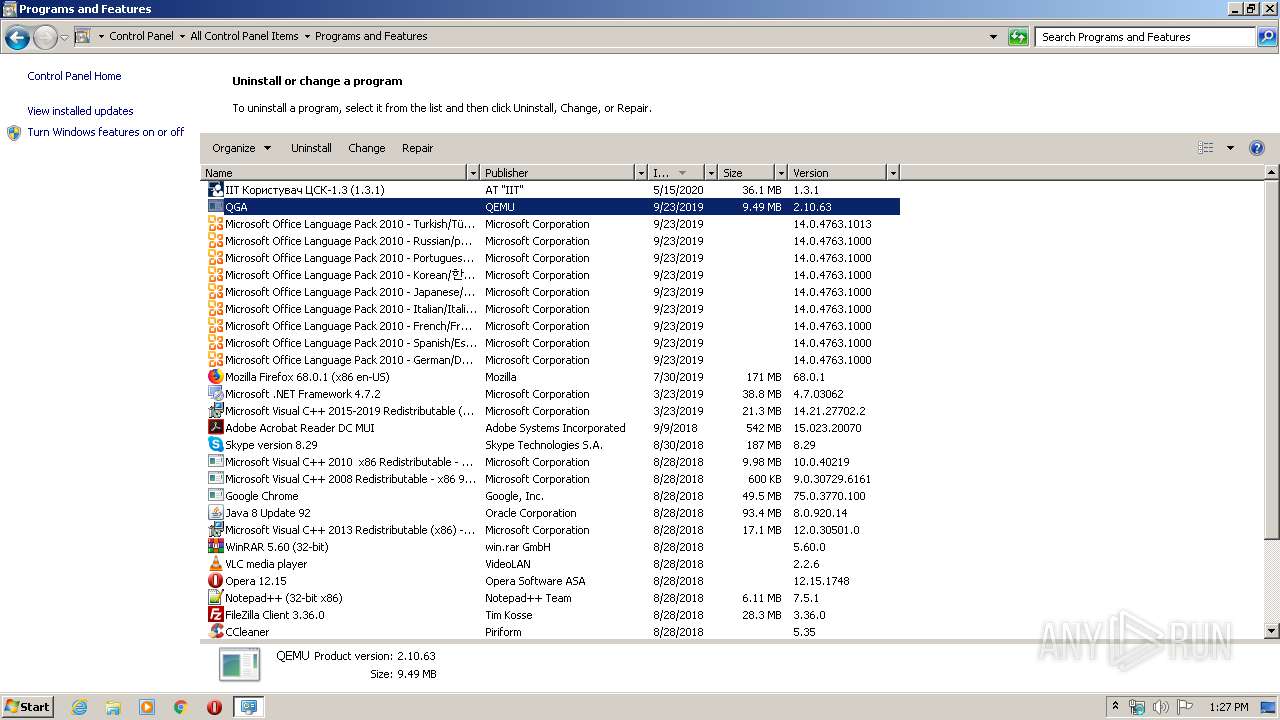
Creates a software uninstall entry
- EUInstall.tmp (PID: 2056)
Creates files in the program directory
- EUInstall.tmp (PID: 2056)
Reads settings of System Certificates
- DrvInst.exe (PID: 2772)
Adds / modifies Windows certificates
- DrvInst.exe (PID: 2772)
Changes settings of System certificates
- DrvInst.exe (PID: 2772)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (57.2) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (18.2) |
| .exe | | | Win16/32 Executable Delphi generic (8.3) |
| .exe | | | Generic Win/DOS Executable (8) |
| .exe | | | DOS Executable Generic (8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:06:14 15:27:46+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 66560 |
| InitializedDataSize: | 106496 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1181c |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.3.1.0 |
| ProductVersionNumber: | 1.3.1.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
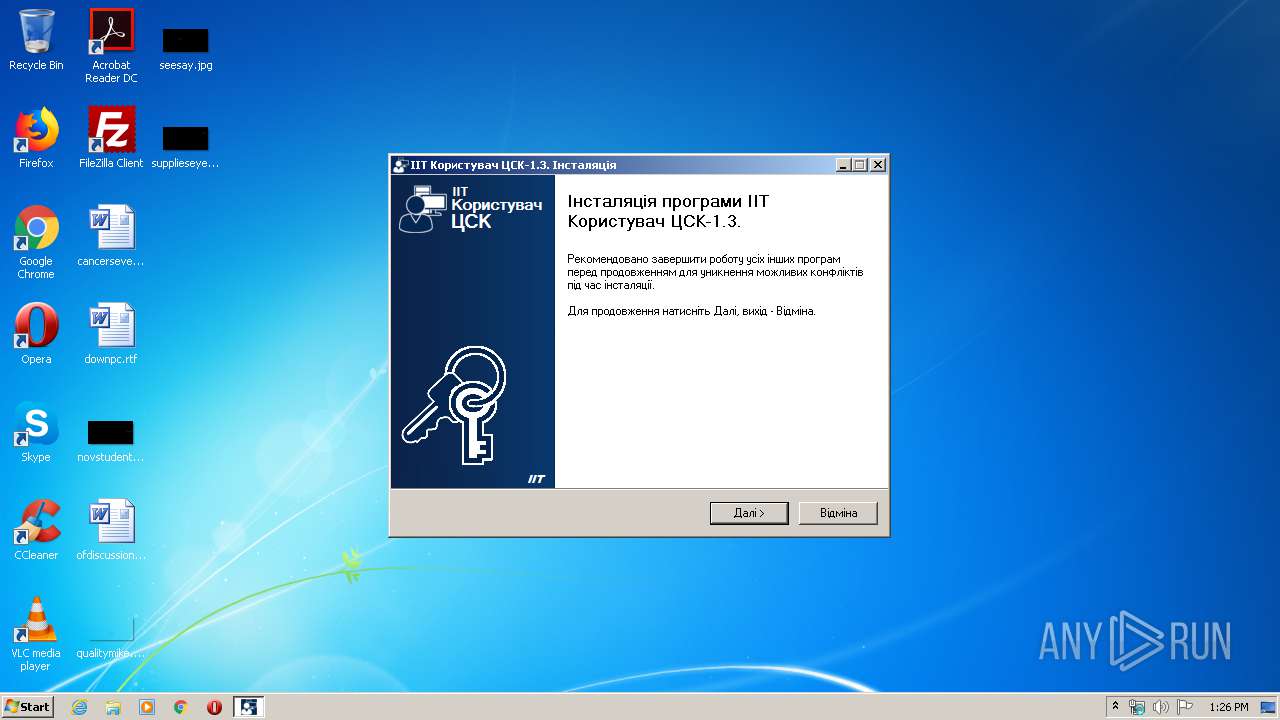
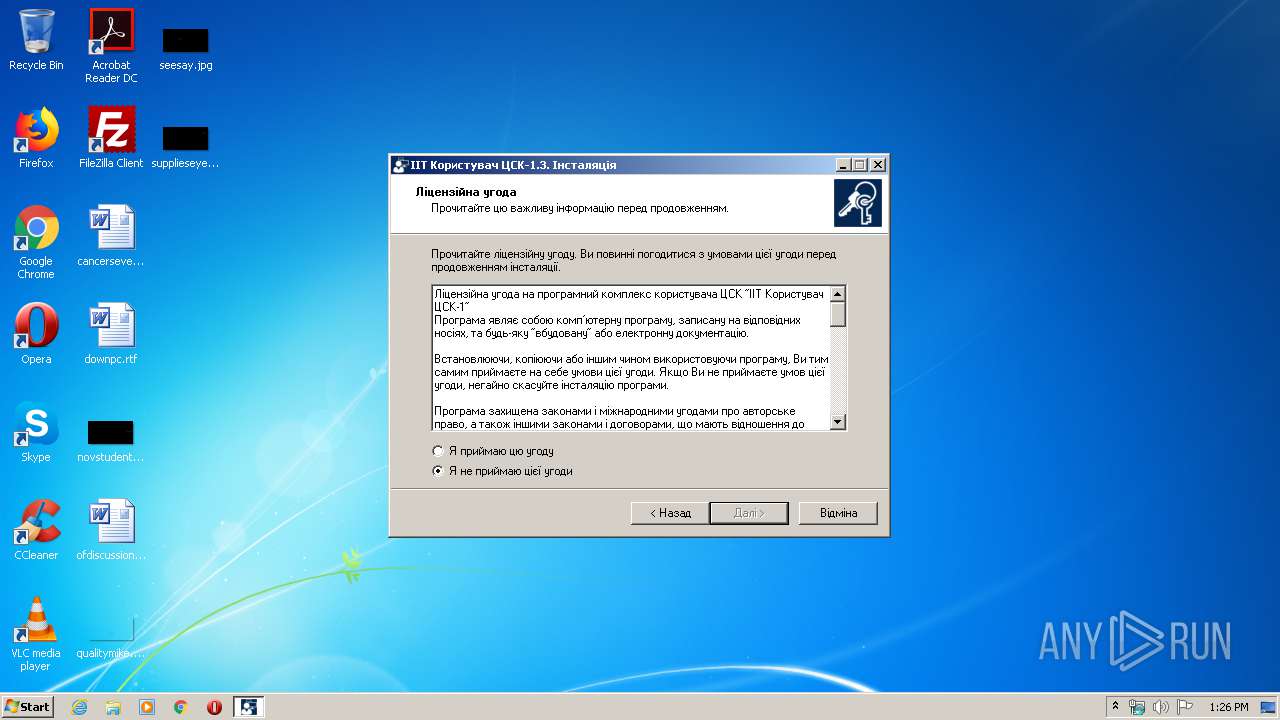
| CompanyName: | АТ "ІІТ" |
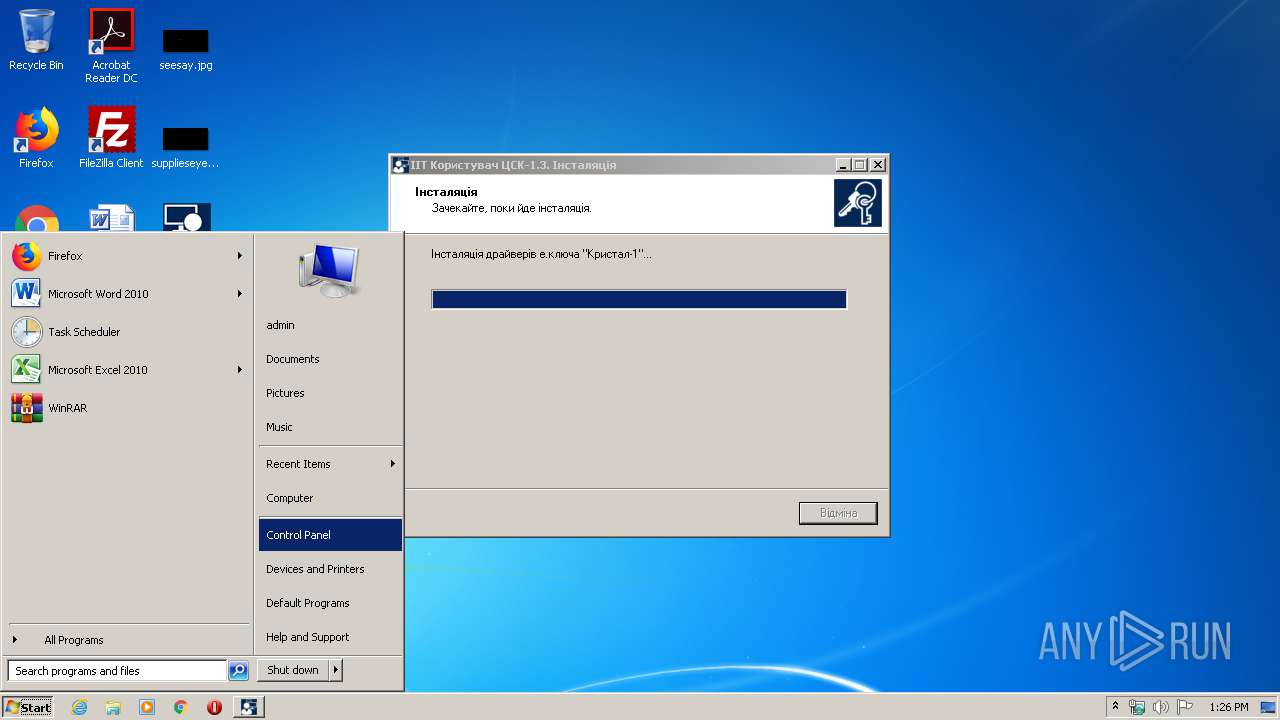
| FileDescription: | ІІТ Користувач ЦСК-1.3 |
| FileVersion: | 1.3.1 |
| LegalCopyright: | |
| ProductName: | ІІТ Користувач ЦСК-1.3 |
| ProductVersion: | 1.3.1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Jun-2018 13:27:46 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | АТ "ІІТ" |
| FileDescription: | ІІТ Користувач ЦСК-1.3 |
| FileVersion: | 1.3.1 |
| LegalCopyright: | - |
| ProductName: | ІІТ Користувач ЦСК-1.3 |
| ProductVersion: | 1.3.1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 14-Jun-2018 13:27:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000F25C | 0x0000F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.37588 |
.itext | 0x00011000 | 0x00000FA4 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.77877 |
.data | 0x00012000 | 0x00000C8C | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.30283 |
.bss | 0x00013000 | 0x000056BC | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00019000 | 0x00000E04 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.59781 |
.tls | 0x0001A000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001B000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.rsrc | 0x0001C000 | 0x00017E44 | 0x00018000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.27875 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.37935 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 4.46577 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 5.32749 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.36377 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 7.80299 | 20332 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 7.93867 | 13190 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 4.24157 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 4.63816 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 5.56681 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
53
Monitored processes
9
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 312 | "cmd" /C regedit /s "C:\Users\admin\AppData\Local\Temp\EU.reg" | C:\Windows\system32\cmd.exe | — | EUInstall.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1840 | regedit /s "C:\Users\admin\AppData\Local\Temp\EU.reg" | C:\Windows\regedit.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Editor Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2056 | "C:\Users\admin\AppData\Local\Temp\is-ALC8N.tmp\EUInstall.tmp" /SL5="$C020C,10245342,174080,C:\Users\admin\AppData\Local\Temp\EUInstall.exe" /SPAWNWND=$801C0 /NOTIFYWND=$D01A0 | C:\Users\admin\AppData\Local\Temp\is-ALC8N.tmp\EUInstall.tmp | EUInstall.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2096 | "C:\Windows\system32\regsvr32" /s EUShellMenu.dll | C:\Windows\system32\regsvr32.exe | — | EUInstall.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2536 | "C:\Users\admin\AppData\Local\Temp\EUInstall.exe" /SPAWNWND=$801C0 /NOTIFYWND=$D01A0 | C:\Users\admin\AppData\Local\Temp\EUInstall.exe | EUInstall.tmp | ||||||||||||
User: admin Company: АТ "ІІТ" Integrity Level: HIGH Description: ІІТ Користувач ЦСК-1.3 Exit code: 0 Version: 1.3.1 Modules
| |||||||||||||||
| 2740 | "C:\Users\admin\AppData\Local\Temp\EUInstall.exe" | C:\Users\admin\AppData\Local\Temp\EUInstall.exe | explorer.exe | ||||||||||||
User: admin Company: АТ "ІІТ" Integrity Level: MEDIUM Description: ІІТ Користувач ЦСК-1.3 Exit code: 0 Version: 1.3.1 Modules
| |||||||||||||||
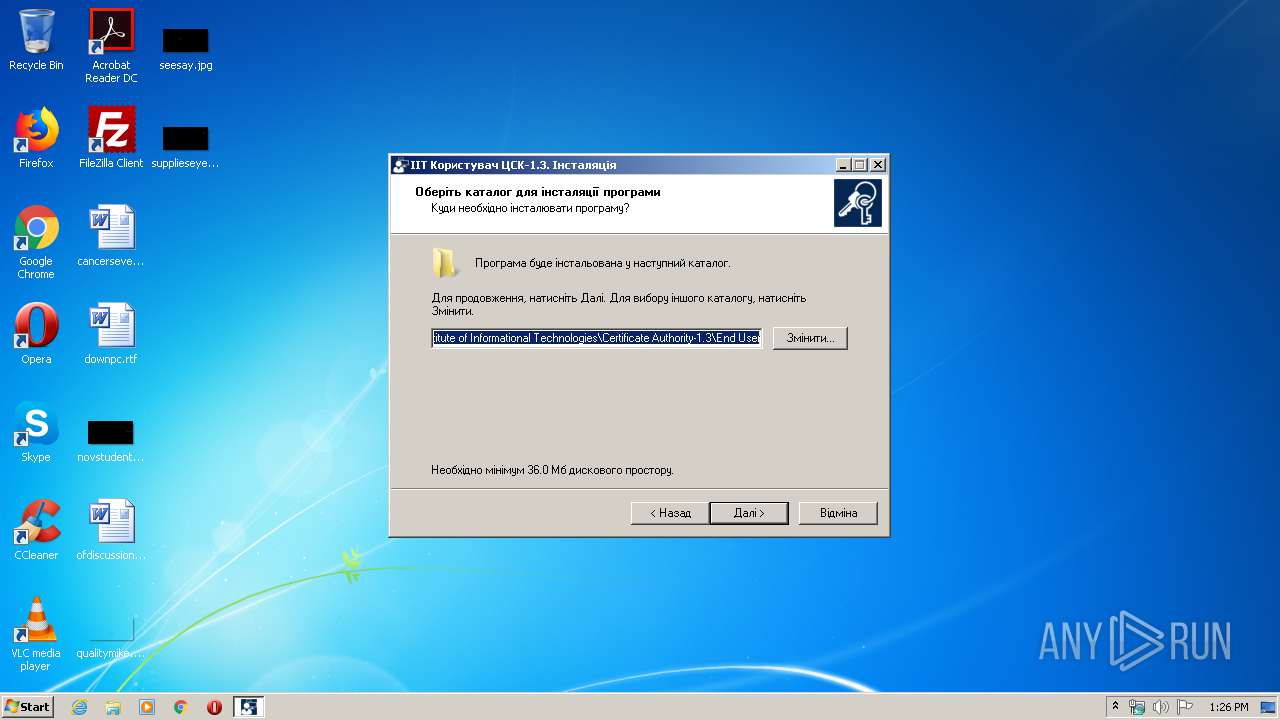
| 2772 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{6f80ff3a-24d5-79d3-a00d-ee2827f4c41f}\EKeyCr1.inf" "0" "6f386499f" "000004BC" "WinSta0\Default" "000003C0" "208" "C:\Program Files\Institute of Informational Technologies\Certificate Authority-1.3\End User\KeyMedias\EKeyCrystal1\Drivers" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3664 | "C:\Users\admin\AppData\Local\Temp\is-3P79B.tmp\EUInstall.tmp" /SL5="$D01A0,10245342,174080,C:\Users\admin\AppData\Local\Temp\EUInstall.exe" | C:\Users\admin\AppData\Local\Temp\is-3P79B.tmp\EUInstall.tmp | — | EUInstall.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 3816 | "C:\Program Files\Institute of Informational Technologies\Certificate Authority-1.3\End User\KeyMedias\EKeyCrystal1\Drivers\HDPreinstall.exe" | C:\Program Files\Institute of Informational Technologies\Certificate Authority-1.3\End User\KeyMedias\EKeyCrystal1\Drivers\HDPreinstall.exe | EUInstall.tmp | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
1 835
Read events
555
Write events
1 274
Delete events
6
Modification events
| (PID) Process: | (2056) EUInstall.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 08080000440B960EB42AD601 | |||
| (PID) Process: | (2056) EUInstall.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 35B15124FF64668C88400036761813FD9CE52242A154812F58E13323A817C8FC | |||
| (PID) Process: | (2056) EUInstall.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2056) EUInstall.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files\Institute of Informational Technologies\Certificate Authority-1.3\End User\EU.exe | |||
| (PID) Process: | (2056) EUInstall.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 9A94BFE546D8C582B6D6C0BECD51D02F5EB82FE5669A94DDD1CA3D30CDB4CF8A | |||
| (PID) Process: | (2056) EUInstall.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Institute of Informational Technologies\Certificate Authority-1.3\End User\FileStore |
| Operation: | write | Name: | Path |
Value: C:\My Certificates and CRLs 13 | |||
| (PID) Process: | (2056) EUInstall.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Institute of Informational Technologies\Certificate Authority-1.3\End User\FileStore |
| Operation: | write | Name: | CheckCRLs |
Value: 0 | |||
| (PID) Process: | (2056) EUInstall.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Institute of Informational Technologies\Certificate Authority-1.3\End User\FileStore |
| Operation: | write | Name: | AutoRefresh |
Value: 1 | |||
| (PID) Process: | (2056) EUInstall.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Institute of Informational Technologies\Certificate Authority-1.3\End User\FileStore |
| Operation: | write | Name: | OnlyOwnCRLs |
Value: 1 | |||
| (PID) Process: | (2056) EUInstall.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Institute of Informational Technologies\Certificate Authority-1.3\End User\FileStore |
| Operation: | write | Name: | FullAndDeltaCRLs |
Value: 0 | |||
Executable files
49
Suspicious files
18
Text files
27
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2056 | EUInstall.tmp | C:\Program Files\Institute of Informational Technologies\Certificate Authority-1.3\End User\is-INI0Q.tmp | — | |
MD5:— | SHA256:— | |||
| 2056 | EUInstall.tmp | C:\Program Files\Institute of Informational Technologies\Certificate Authority-1.3\End User\is-GESOQ.tmp | — | |
MD5:— | SHA256:— | |||
| 2056 | EUInstall.tmp | C:\Program Files\Institute of Informational Technologies\Certificate Authority-1.3\End User\is-KKPC0.tmp | — | |
MD5:— | SHA256:— | |||
| 2056 | EUInstall.tmp | C:\Program Files\Institute of Informational Technologies\Certificate Authority-1.3\End User\is-DBIK6.tmp | — | |
MD5:— | SHA256:— | |||
| 2056 | EUInstall.tmp | C:\Program Files\Institute of Informational Technologies\Certificate Authority-1.3\End User\is-ICC6C.tmp | — | |
MD5:— | SHA256:— | |||
| 2056 | EUInstall.tmp | C:\Program Files\Institute of Informational Technologies\Certificate Authority-1.3\End User\is-JBSFJ.tmp | — | |
MD5:— | SHA256:— | |||
| 2056 | EUInstall.tmp | C:\Program Files\Institute of Informational Technologies\Certificate Authority-1.3\End User\is-2984U.tmp | — | |
MD5:— | SHA256:— | |||
| 2056 | EUInstall.tmp | C:\Program Files\Institute of Informational Technologies\Certificate Authority-1.3\End User\is-KADJT.tmp | — | |
MD5:— | SHA256:— | |||
| 2056 | EUInstall.tmp | C:\Program Files\Institute of Informational Technologies\Certificate Authority-1.3\End User\is-748JT.tmp | — | |
MD5:— | SHA256:— | |||
| 2056 | EUInstall.tmp | C:\Program Files\Institute of Informational Technologies\Certificate Authority-1.3\End User\is-96LU5.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
regedit.exe | REGEDIT: CreateFile failed, GetLastError() = 2
|