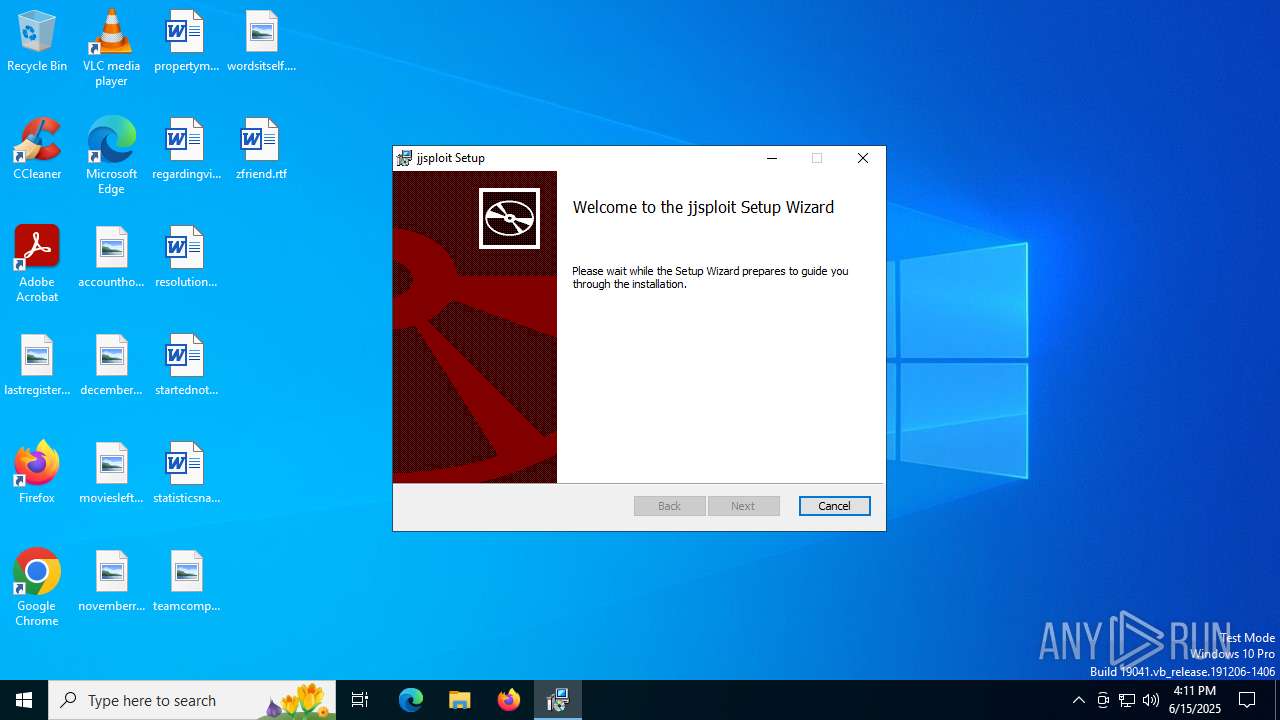
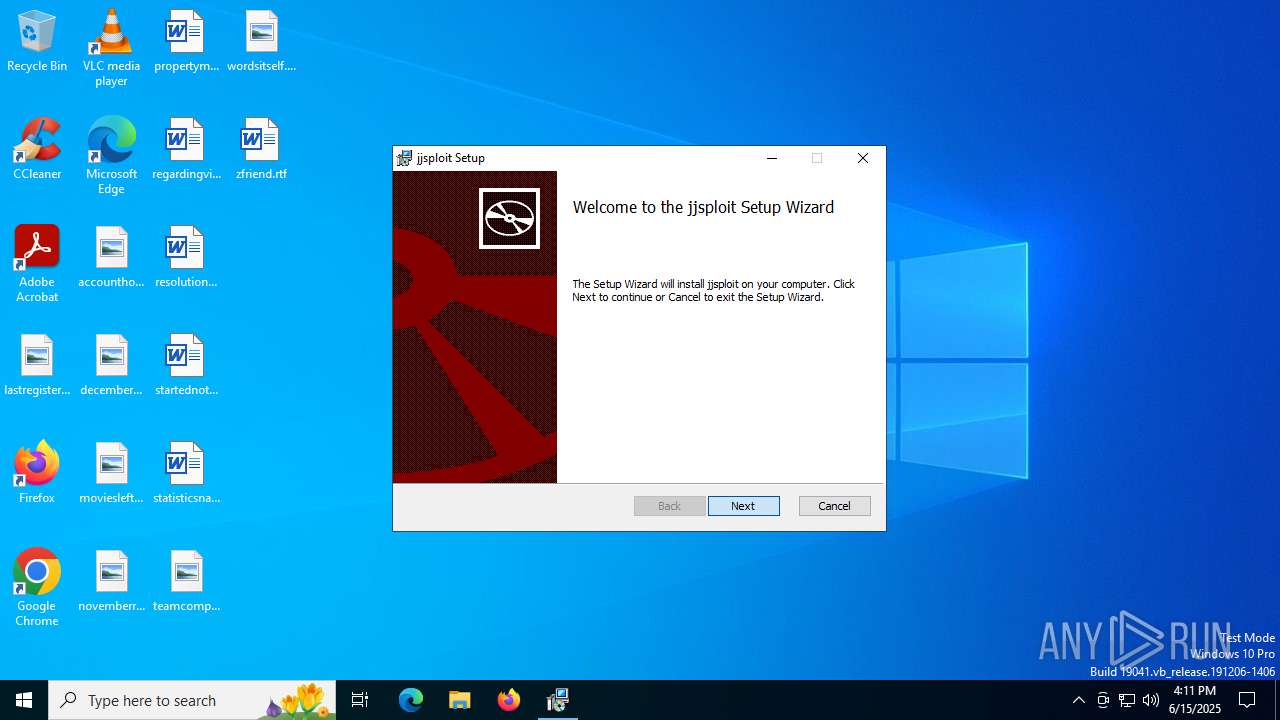
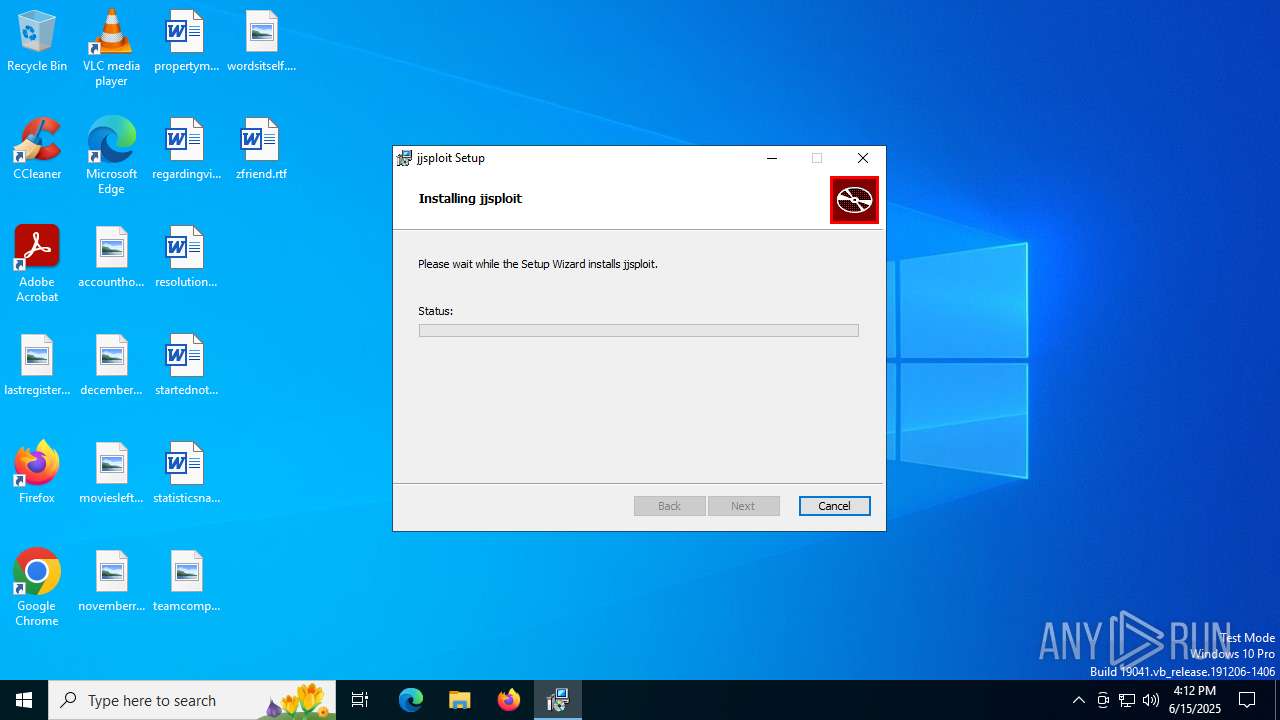
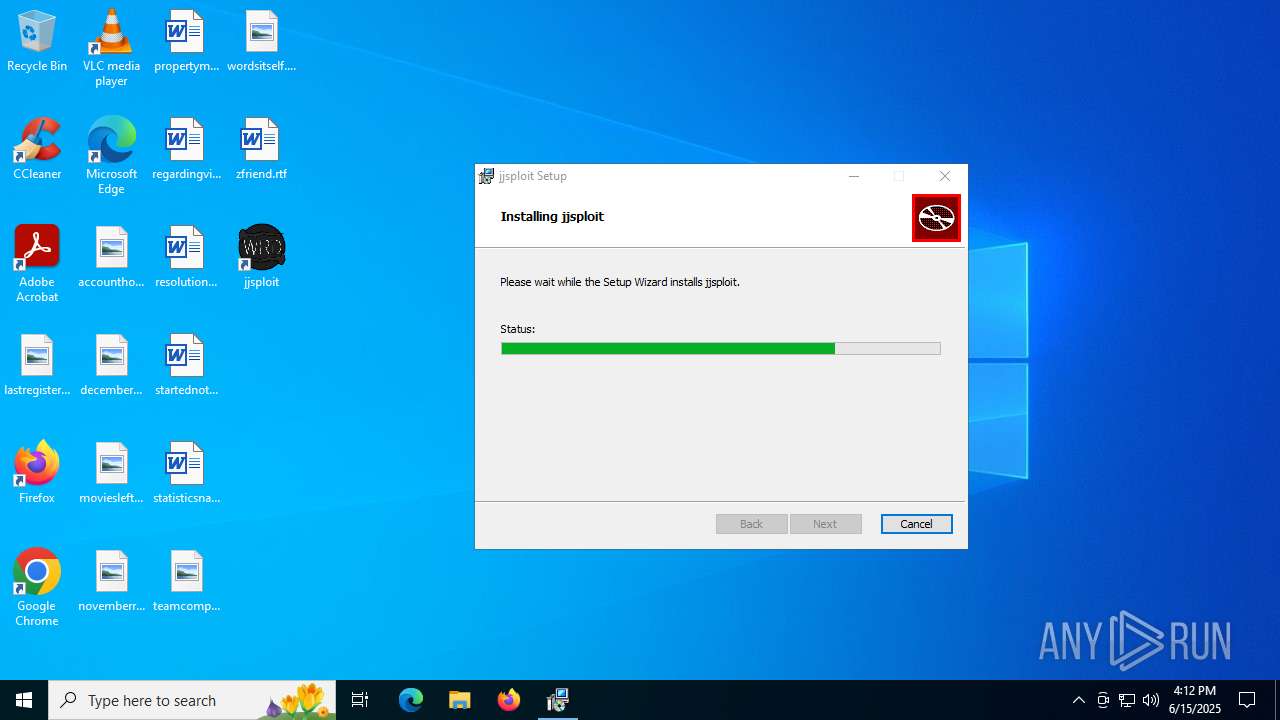
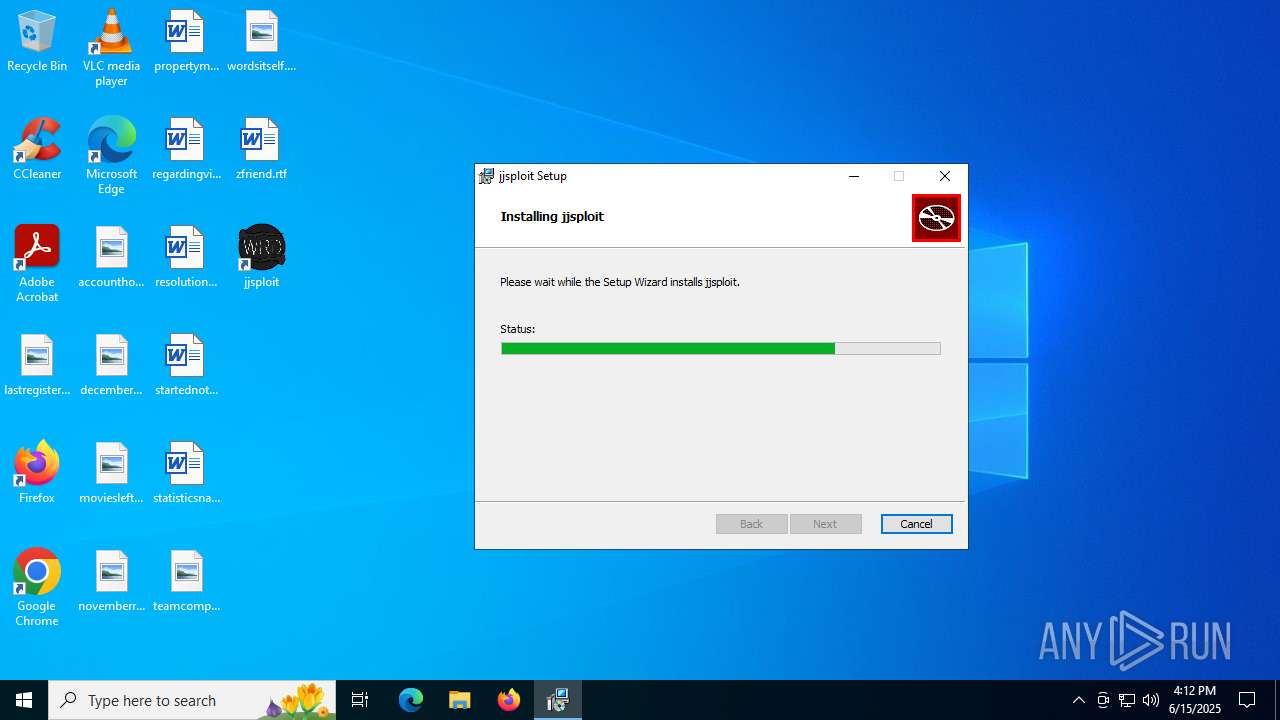
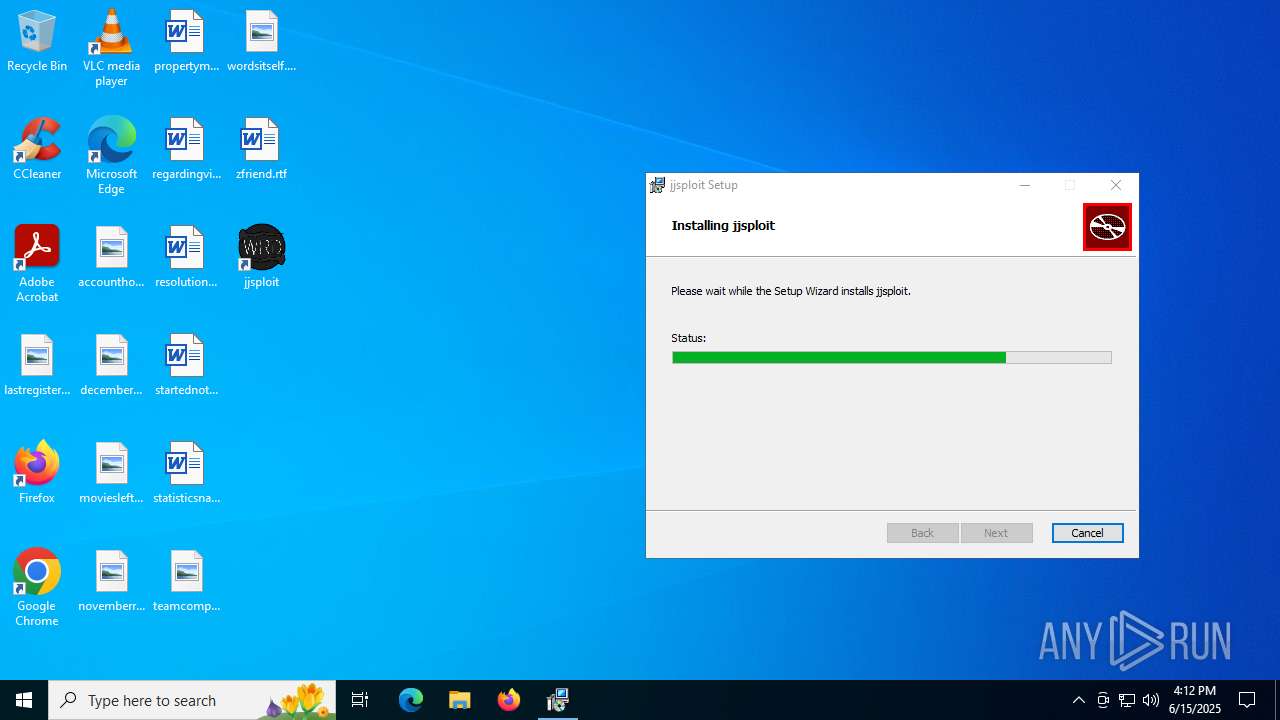
| File name: | jjsploit_8.15.0_x64_en-US.msi |
| Full analysis: | https://app.any.run/tasks/138e67f6-4945-4480-9e48-bdfa5c9f9437 |
| Verdict: | Malicious activity |
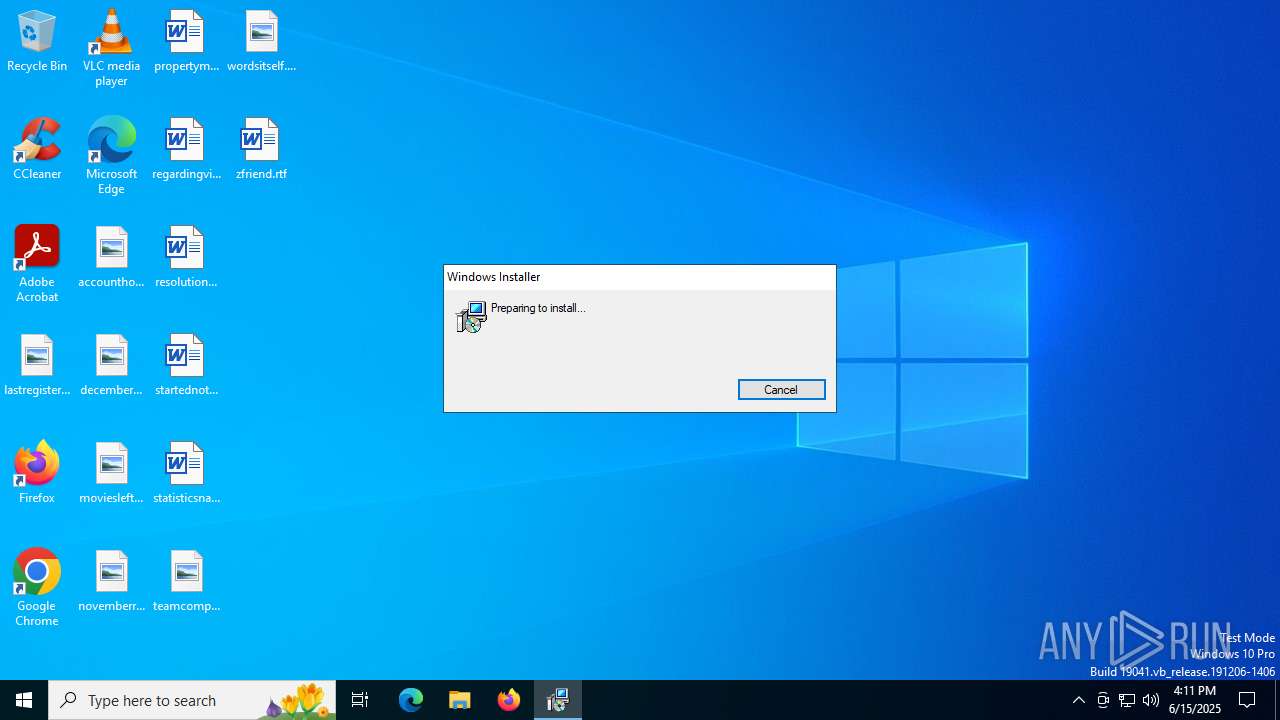
| Analysis date: | June 15, 2025, 16:11:49 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Title: Installation Database, Subject: jjsploit, Author: wearedevs, Keywords: Installer, Comments: This installer database contains the logic and data required to install jjsploit., Template: x64;0, Revision Number: {49DFFAA3-FEB8-4E58-BC46-81486C0333EF}, Create Time/Date: Fri Jun 6 02:20:14 2025, Last Saved Time/Date: Fri Jun 6 02:20:14 2025, Number of Pages: 450, Number of Words: 2, Name of Creating Application: Windows Installer XML Toolset (3.14.1.8722), Security: 2 |
| MD5: | 6DD4892FD3BC8525C71E969B352D0F8D |
| SHA1: | 17ED006056B30CFDDAC36CBAEBB5A713D72D709D |
| SHA256: | AD2A6842EF69E07E7994ED712619022AD408C8B9537969CC85B46E0947FAEB92 |
| SSDEEP: | 98304:NoQGjibHm+DMK8l9v0R7rQBD+Rt2bshD1lIlu8ia83KPdiK18y0tks/cpXNusn7v:aJ2TD5a |
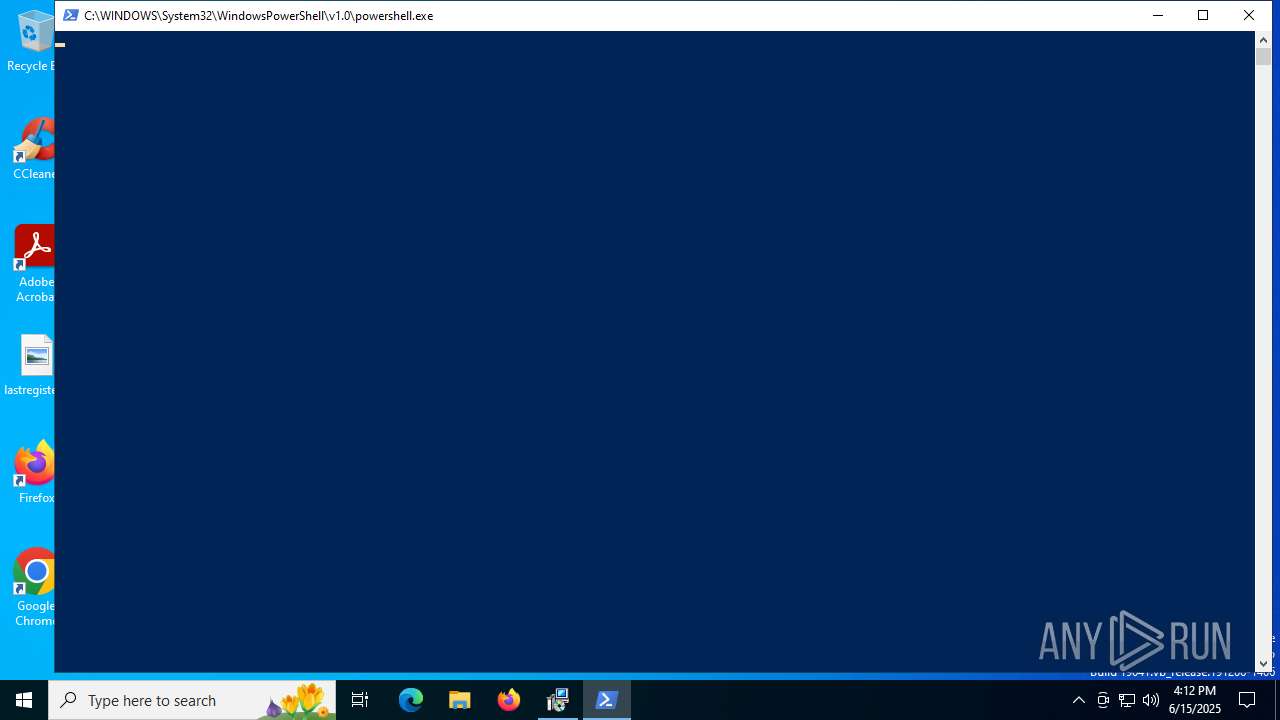
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 6408)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 2716)
Starts process via Powershell
- powershell.exe (PID: 6408)
Manipulates environment variables
- powershell.exe (PID: 6408)
The process bypasses the loading of PowerShell profile settings
- msiexec.exe (PID: 6268)
Downloads file from URI via Powershell
- powershell.exe (PID: 6408)
Starts POWERSHELL.EXE for commands execution
- msiexec.exe (PID: 6268)
Starts a Microsoft application from unusual location
- MicrosoftEdgeWebview2Setup.exe (PID: 1136)
- MicrosoftEdgeUpdate.exe (PID: 5896)
Executable content was dropped or overwritten
- powershell.exe (PID: 6408)
- MicrosoftEdgeWebview2Setup.exe (PID: 1136)
- MicrosoftEdgeUpdate.exe (PID: 5896)
- MicrosoftEdge_X64_137.0.3296.83.exe (PID: 1564)
- setup.exe (PID: 5400)
Process drops legitimate windows executable
- powershell.exe (PID: 6408)
- MicrosoftEdgeWebview2Setup.exe (PID: 1136)
- MicrosoftEdgeUpdate.exe (PID: 5896)
- MicrosoftEdge_X64_137.0.3296.83.exe (PID: 1564)
- setup.exe (PID: 5400)
Application launched itself
- setup.exe (PID: 5400)
Starts itself from another location
- MicrosoftEdgeUpdate.exe (PID: 5896)
INFO
Reads the computer name
- msiexec.exe (PID: 6268)
- msiexec.exe (PID: 5496)
Executable content was dropped or overwritten
- msiexec.exe (PID: 1944)
- msiexec.exe (PID: 6268)
Checks supported languages
- msiexec.exe (PID: 6268)
- msiexec.exe (PID: 5496)
An automatically generated document
- msiexec.exe (PID: 1944)
Manages system restore points
- SrTasks.exe (PID: 2132)
The sample compiled with english language support
- powershell.exe (PID: 6408)
- MicrosoftEdgeWebview2Setup.exe (PID: 1136)
- MicrosoftEdgeUpdate.exe (PID: 5896)
- MicrosoftEdge_X64_137.0.3296.83.exe (PID: 1564)
- setup.exe (PID: 5400)
The executable file from the user directory is run by the Powershell process
- MicrosoftEdgeWebview2Setup.exe (PID: 1136)
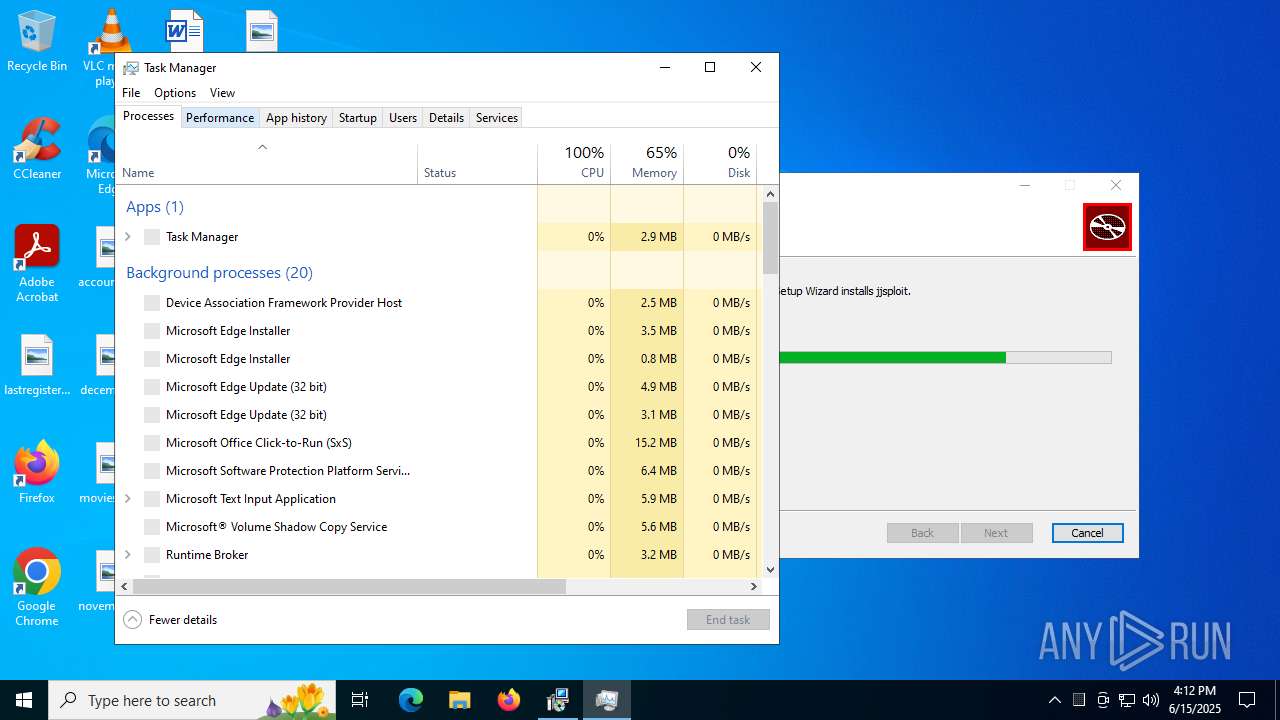
Manual execution by a user
- jjsploit.exe (PID: 2144)
- jjsploit.exe (PID: 3628)
- Taskmgr.exe (PID: 2168)
- Taskmgr.exe (PID: 3860)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
| Subject: | jjsploit |
| Author: | wearedevs |
| Keywords: | Installer |
| Comments: | This installer database contains the logic and data required to install jjsploit. |
| Template: | x64;0 |
| RevisionNumber: | {49DFFAA3-FEB8-4E58-BC46-81486C0333EF} |
| CreateDate: | 2025:06:06 02:20:14 |
| ModifyDate: | 2025:06:06 02:20:14 |
| Pages: | 450 |
| Words: | 2 |
| Software: | Windows Installer XML Toolset (3.14.1.8722) |
| Security: | Read-only recommended |
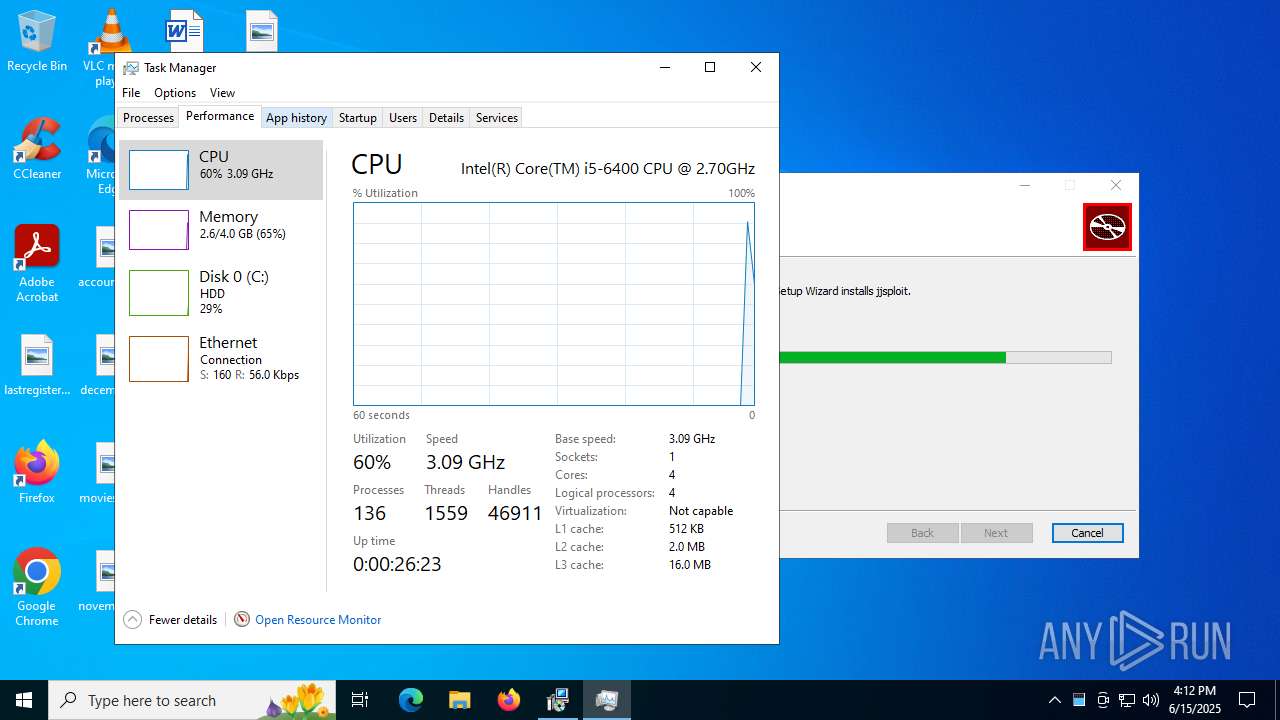
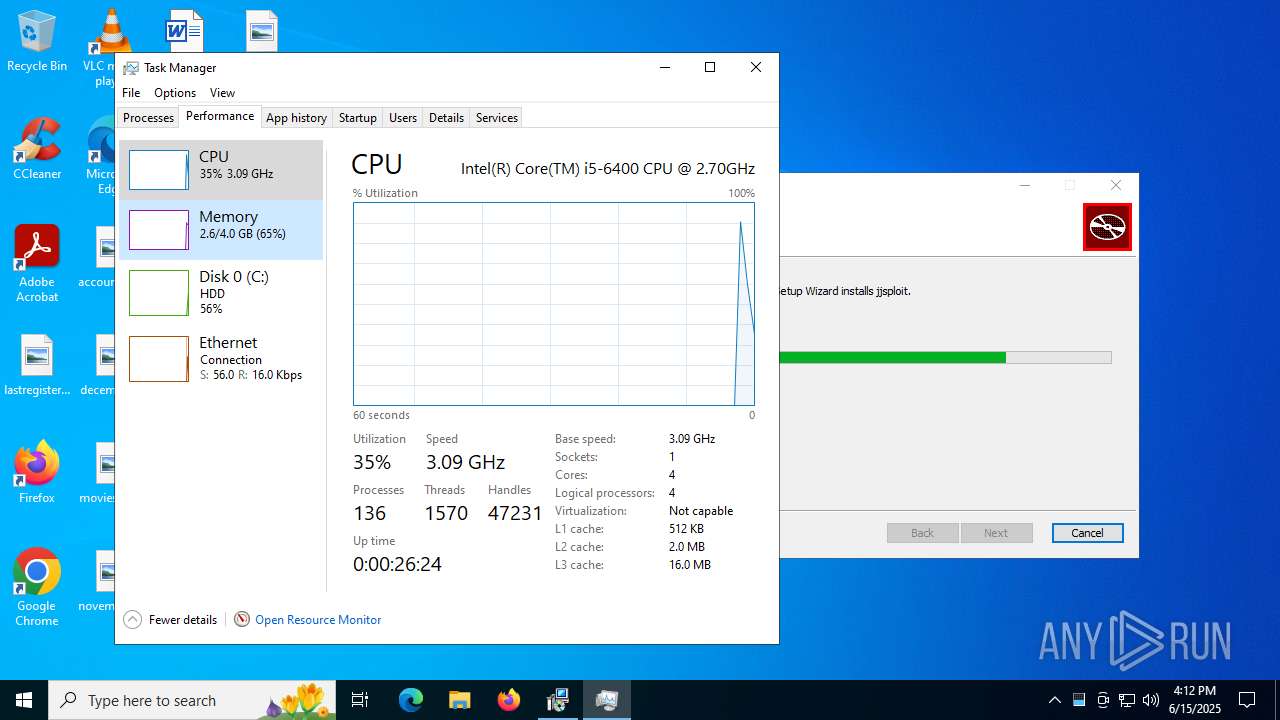
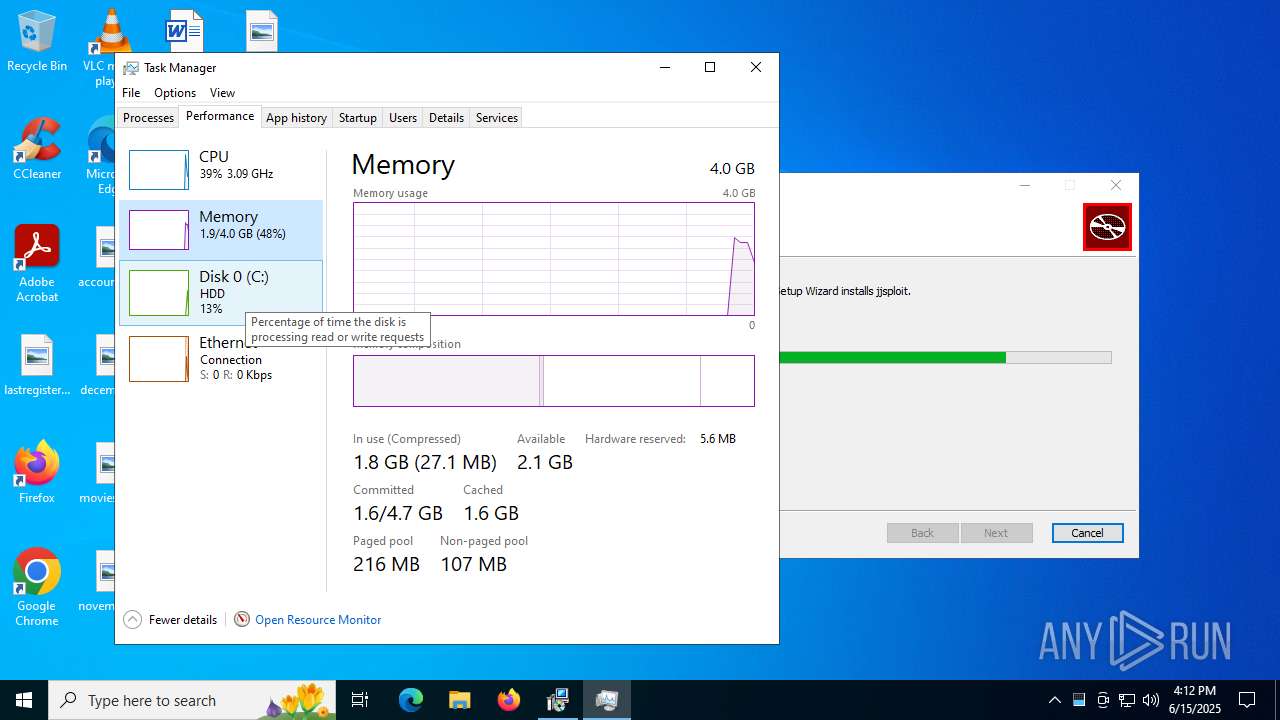
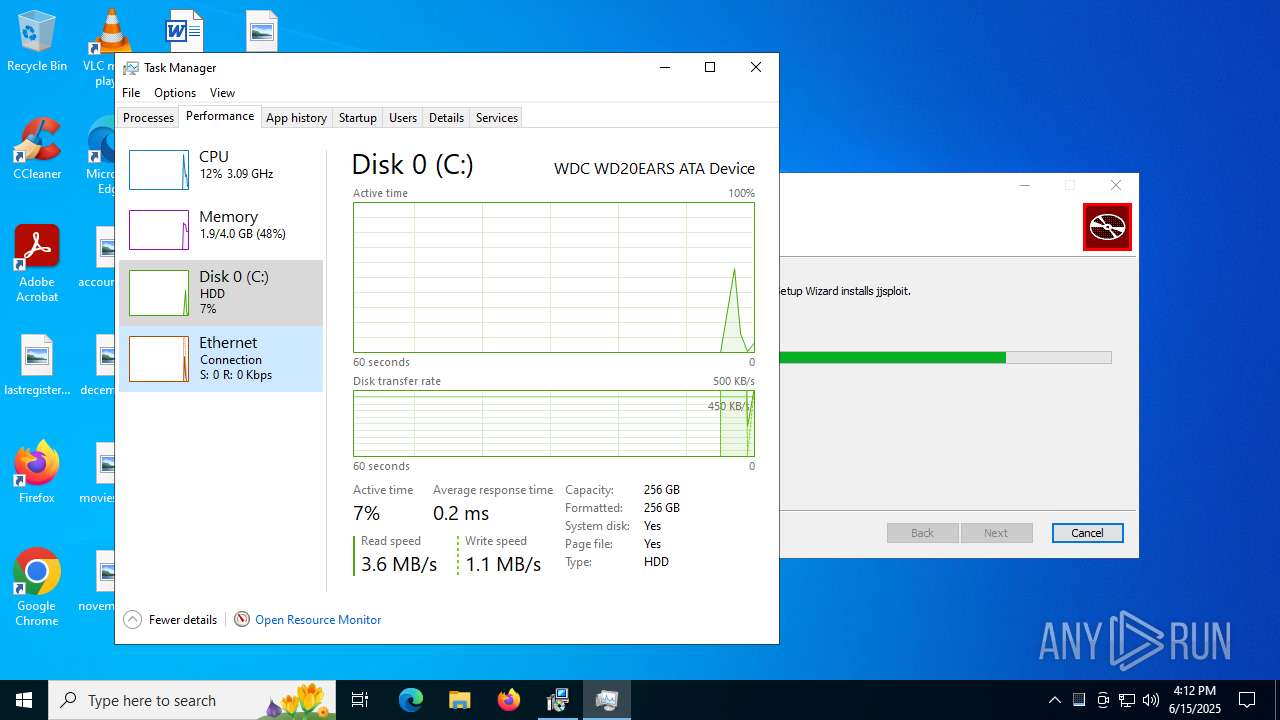
Total processes
168
Monitored processes
25
Malicious processes
4
Suspicious processes
0
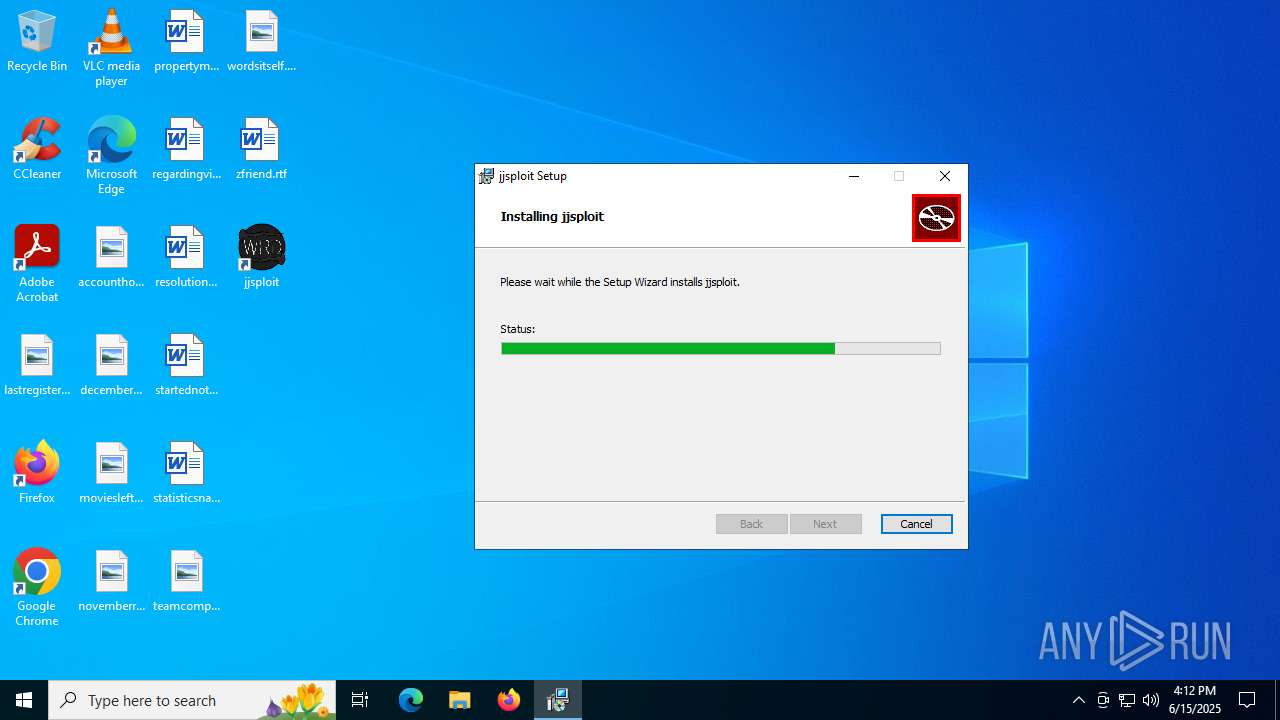
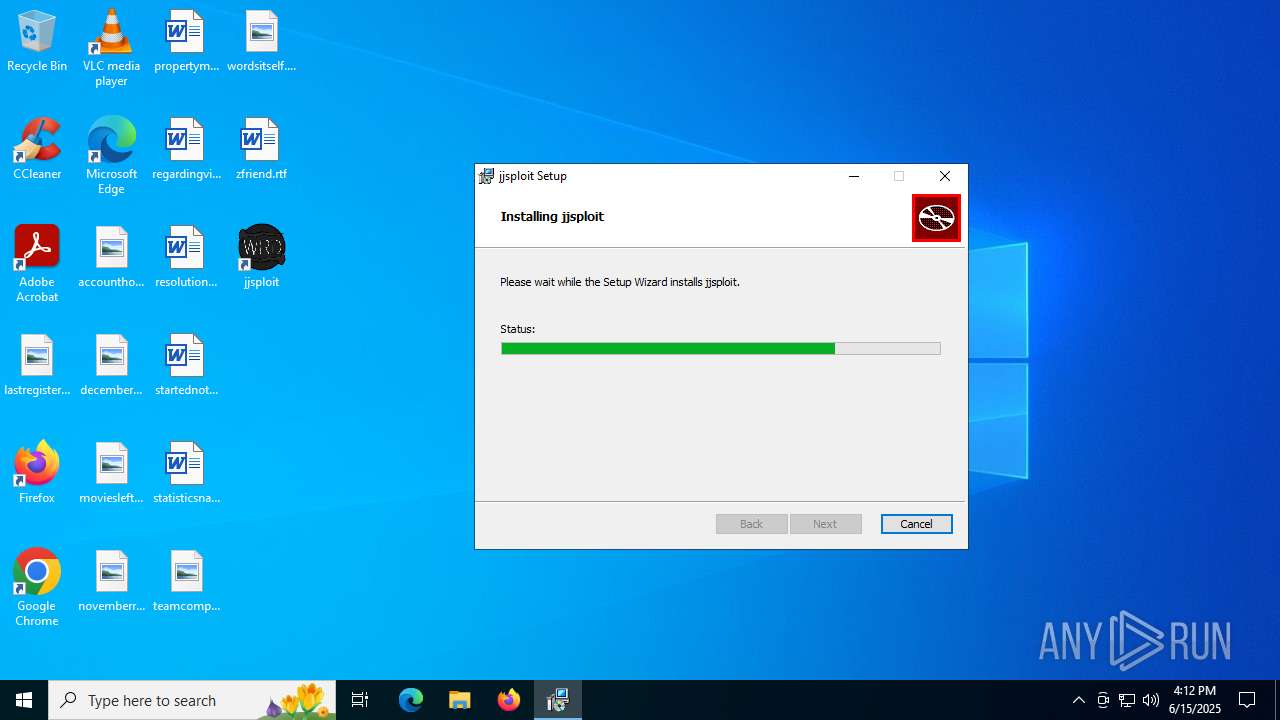
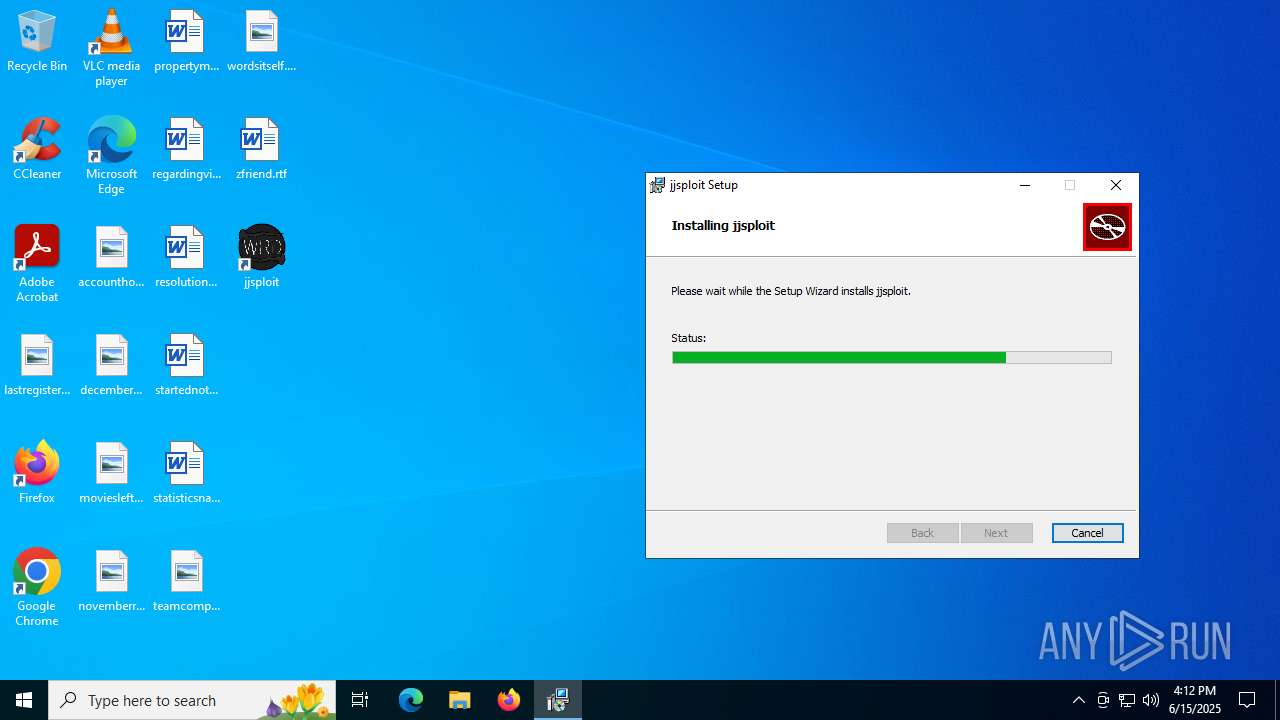
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1136 | "C:\Users\admin\AppData\Local\Temp\MicrosoftEdgeWebview2Setup.exe" /silent /install | C:\Users\admin\AppData\Local\Temp\MicrosoftEdgeWebview2Setup.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Setup Version: 1.3.195.61 Modules
| |||||||||||||||
| 1564 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\Install\{BC5D55E0-5F5B-4712-80CE-E3746640BA77}\MicrosoftEdge_X64_137.0.3296.83.exe" --msedgewebview --verbose-logging --do-not-launch-msedge --user-level | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\Install\{BC5D55E0-5F5B-4712-80CE-E3746640BA77}\MicrosoftEdge_X64_137.0.3296.83.exe | MicrosoftEdgeUpdate.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Installer Version: 137.0.3296.83 Modules
| |||||||||||||||
| 1800 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.195.61\MicrosoftEdgeUpdateComRegisterShell64.exe" /user | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.195.61\MicrosoftEdgeUpdateComRegisterShell64.exe | — | MicrosoftEdgeUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update COM Registration Helper Exit code: 0 Version: 1.3.195.61 Modules
| |||||||||||||||
| 1944 | "C:\Windows\System32\msiexec.exe" /i C:\Users\admin\AppData\Local\Temp\jjsploit_8.15.0_x64_en-US.msi | C:\Windows\System32\msiexec.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1964 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe" /handoff "appguid={F3017226-FE2A-4295-8BDF-00C3A9A7E4C5}&appname=Microsoft%20Edge%20Webview2%20Runtime&needsadmin=false" /installsource otherinstallcmd /sessionid "{B904D87C-86B5-48C8-9C4E-537361B05CC7}" /silent | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe | — | MicrosoftEdgeUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Version: 1.3.195.61 Modules
| |||||||||||||||
| 2132 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
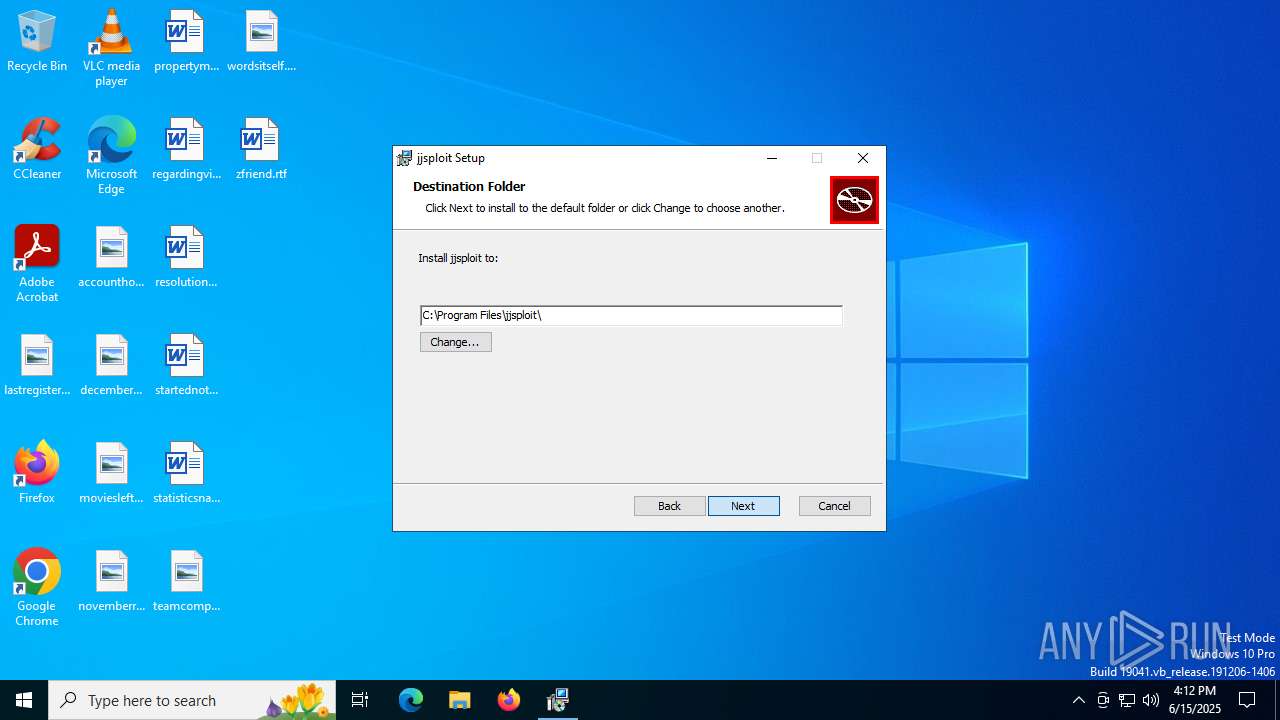
| 2144 | "C:\Program Files\jjsploit\jjsploit.exe" | C:\Program Files\jjsploit\jjsploit.exe | explorer.exe | ||||||||||||
User: admin Company: wearedevs Integrity Level: MEDIUM Description: jjsploit Version: 8.15.0 Modules
| |||||||||||||||
| 2168 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\Windows\System32\Taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Manager Exit code: 3221226540 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2232 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.195.61\MicrosoftEdgeUpdateComRegisterShell64.exe" /user | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.195.61\MicrosoftEdgeUpdateComRegisterShell64.exe | — | MicrosoftEdgeUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update COM Registration Helper Exit code: 0 Version: 1.3.195.61 Modules
| |||||||||||||||
| 2716 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
17 786
Read events
16 344
Write events
1 384
Delete events
58
Modification events
| (PID) Process: | (6268) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 48000000000000004EBA993A10DEDB017C1800003C0D0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6268) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 48000000000000004EBA993A10DEDB017C1800003C0D0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6268) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 480000000000000047B9B83A10DEDB017C1800003C0D0000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6268) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 480000000000000047B9B83A10DEDB017C1800003C0D0000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6268) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 480000000000000047B9B83A10DEDB017C1800003C0D0000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6268) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4800000000000000226FBD3A10DEDB017C1800003C0D0000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6268) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4800000000000000F8C0EA3A10DEDB017C1800003C0D0000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6268) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (6268) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000F453ED3A10DEDB017C180000880F0000E8030000010000000000000000000000F272A4E61EA24A469C2664C2816CD65200000000000000000000000000000000 | |||
| (PID) Process: | (2716) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 48000000000000006E70FB3A10DEDB019C0A0000D8130000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
206
Suspicious files
25
Text files
23
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6268 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 6268 | msiexec.exe | C:\Windows\Installer\1799af.msi | — | |
MD5:— | SHA256:— | |||
| 1944 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI6561.tmp | executable | |
MD5:CFBB8568BD3711A97E6124C56FCFA8D9 | SHA256:7F47D98AB25CFEA9B3A2E898C3376CC9BA1CD893B4948B0C27CAA530FD0E34CC | |||
| 6268 | msiexec.exe | C:\Windows\Installer\inprogressinstallinfo.ipi | binary | |
MD5:46F98894AA7F4CA6354C66759EEF9566 | SHA256:7759C283E18D394F986646B1118C237B34F0F04C031EDD67945FC19C0141B524 | |||
| 6268 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:05399852733C304D14C672F3BEC82348 | SHA256:45B38A420BFBC44369EE4D5734779288E9DE594D87D59B0DAC7921BBEDB75EE9 | |||
| 6268 | msiexec.exe | C:\Windows\Temp\~DF45E03F3FBA0DC253.TMP | binary | |
MD5:BF619EAC0CDF3F68D496EA9344137E8B | SHA256:076A27C79E5ACE2A3D47F9DD2E83E4FF6EA8872B3C2218F66C92B89B55F36560 | |||
| 6268 | msiexec.exe | C:\Program Files\jjsploit\resources\luascripts\jailbreak\removewalls.lua | text | |
MD5:00BC897C4BCBDF5660C3B1F703602F0B | SHA256:A477FFE6D4C769E2E859417AF43ED4E21107E174DF8274BC9487963659462F31 | |||
| 6268 | msiexec.exe | C:\Program Files\jjsploit\resources\luascripts\beesim\autodig.lua | text | |
MD5:A99F423612E047906C288D32DED6F773 | SHA256:AFD46C7CD01F271454C96D9BC71ECD4778D508C23D5C66103A85B8BA180DBC8A | |||
| 6268 | msiexec.exe | C:\Windows\Temp\~DF2738298F1CF3AC87.TMP | binary | |
MD5:46F98894AA7F4CA6354C66759EEF9566 | SHA256:7759C283E18D394F986646B1118C237B34F0F04C031EDD67945FC19C0141B524 | |||
| 6268 | msiexec.exe | C:\Program Files\jjsploit\resources\luascripts\animations\levitate.lua | text | |
MD5:D09DA2B730602A59C3289B72E63137BB | SHA256:2AF3980171CC17A4D7687B7489FE8B0BB193E5080C0CA76E5501983A0B3EFADB | |||
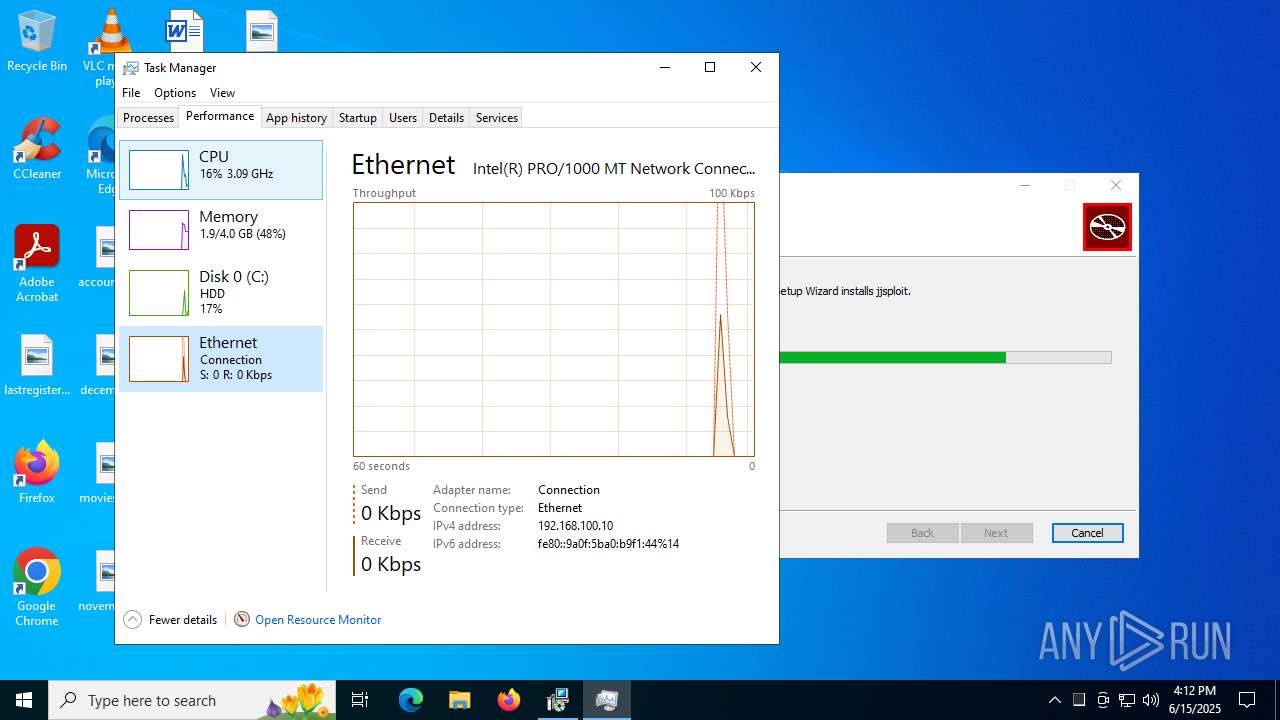
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
37
DNS requests
21
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3884 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 420 b | whitelisted |
1268 | svchost.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | RU | binary | 825 b | whitelisted |
5012 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
1268 | svchost.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | CL | binary | 868 b | whitelisted |
6828 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.f.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/ba88ddc9-9956-4b1b-a5d1-91758faaa81f?P1=1750608744&P2=404&P3=2&P4=OOIGyI9jE0yecRox6CG%2fF1C28igCjmEgsjiywIGuP2uJ%2b%2bjY9chsibUXRRgRMdJimp1XgCGbObXSjJFILojvNQ%3d%3d | US | — | — | whitelisted |
3884 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
6828 | svchost.exe | GET | — | 199.232.210.172:80 | http://msedge.f.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/ba88ddc9-9956-4b1b-a5d1-91758faaa81f?P1=1750608744&P2=404&P3=2&P4=OOIGyI9jE0yecRox6CG%2fF1C28igCjmEgsjiywIGuP2uJ%2b%2bjY9chsibUXRRgRMdJimp1XgCGbObXSjJFILojvNQ%3d%3d | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5708 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2336 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
5012 | svchost.exe | 40.126.31.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5012 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
msedge.sf.dl.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6828 | svchost.exe | Misc activity | ET INFO Packed Executable Download |
Process | Message |
|---|---|
jjsploit.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
jjsploit.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
jjsploit.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
jjsploit.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|