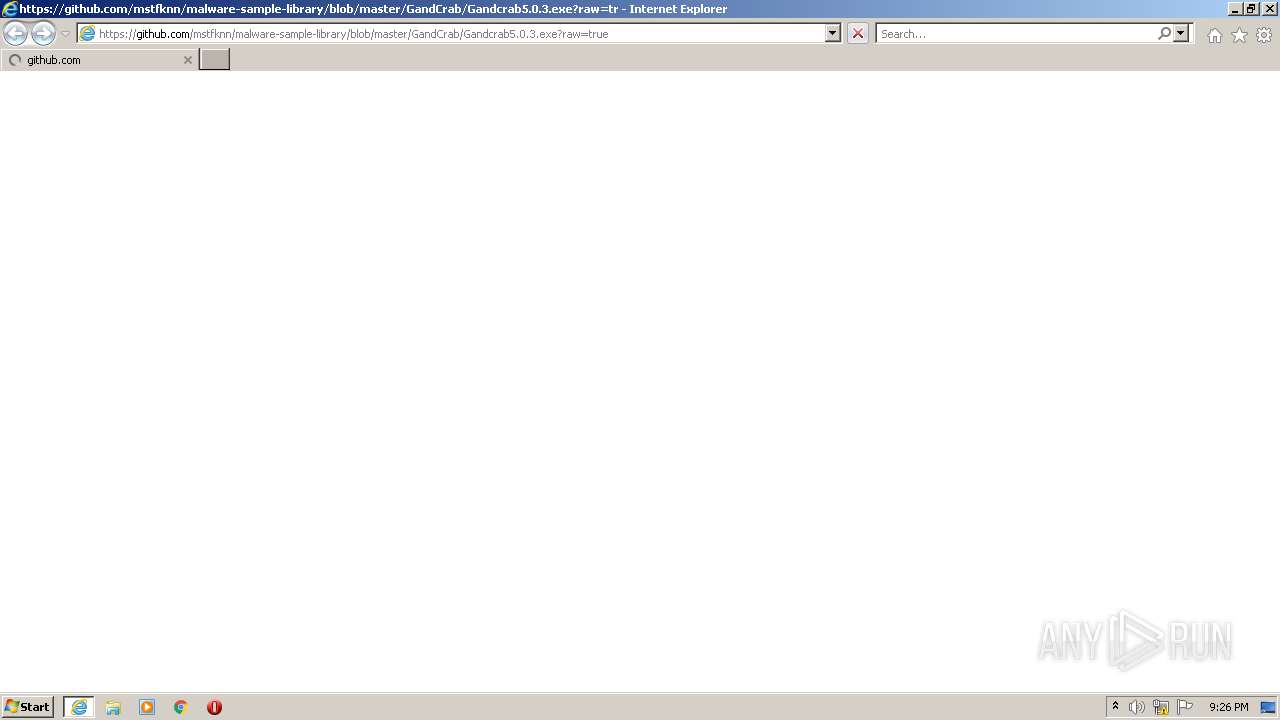
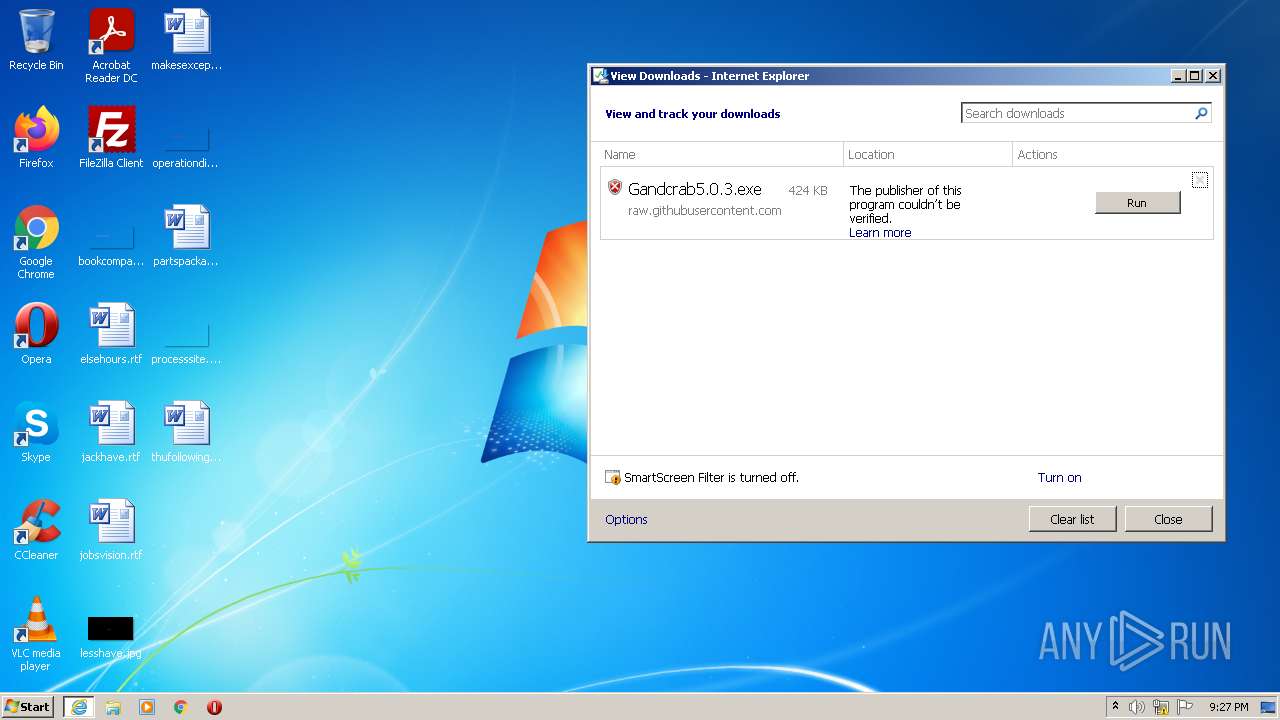
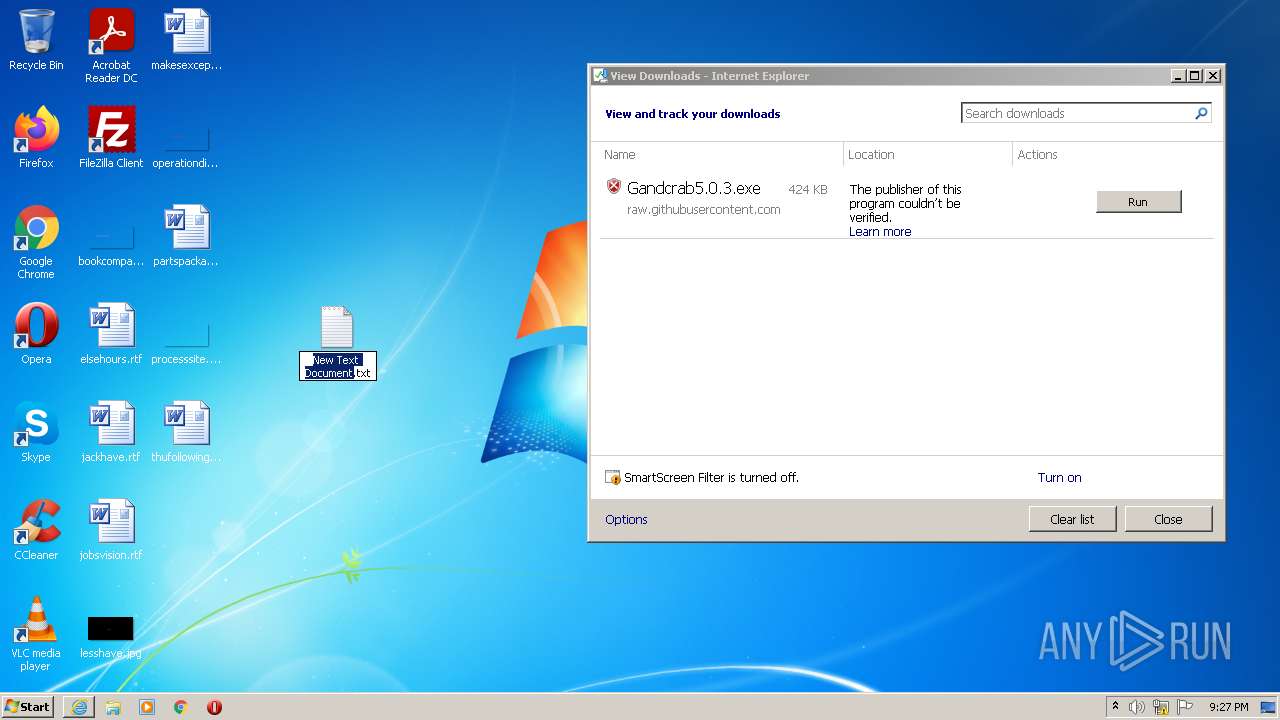
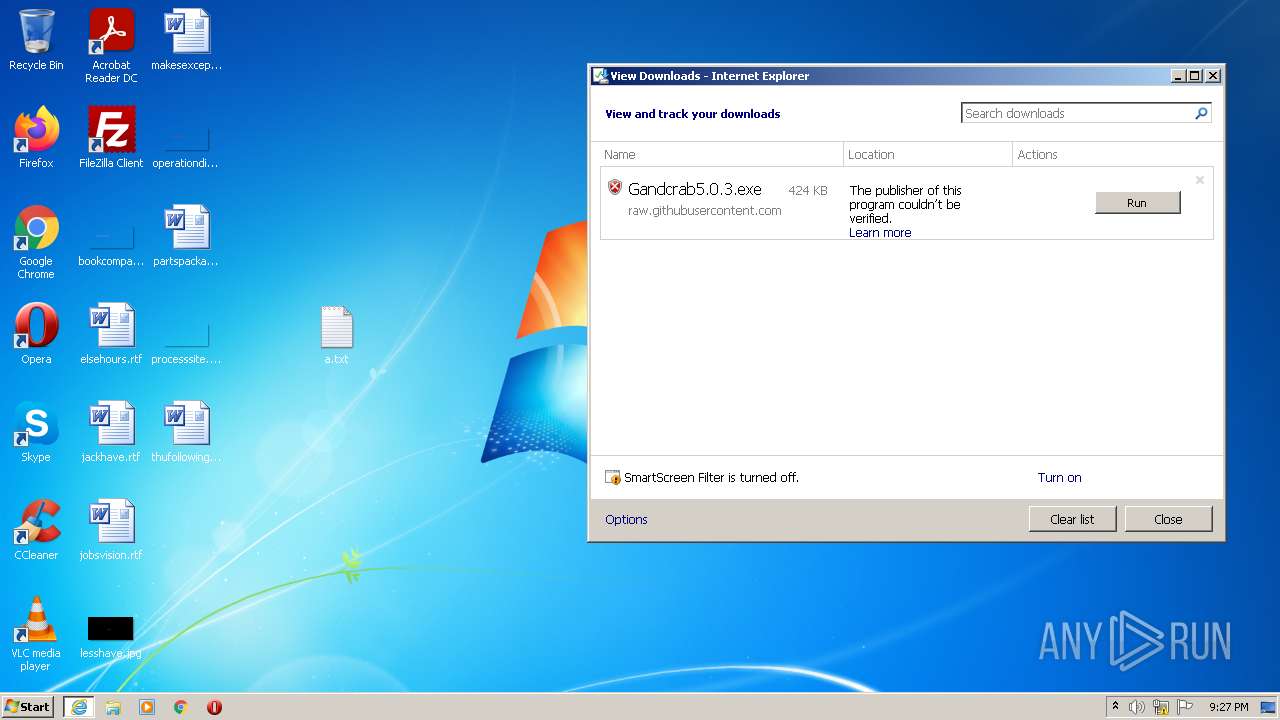
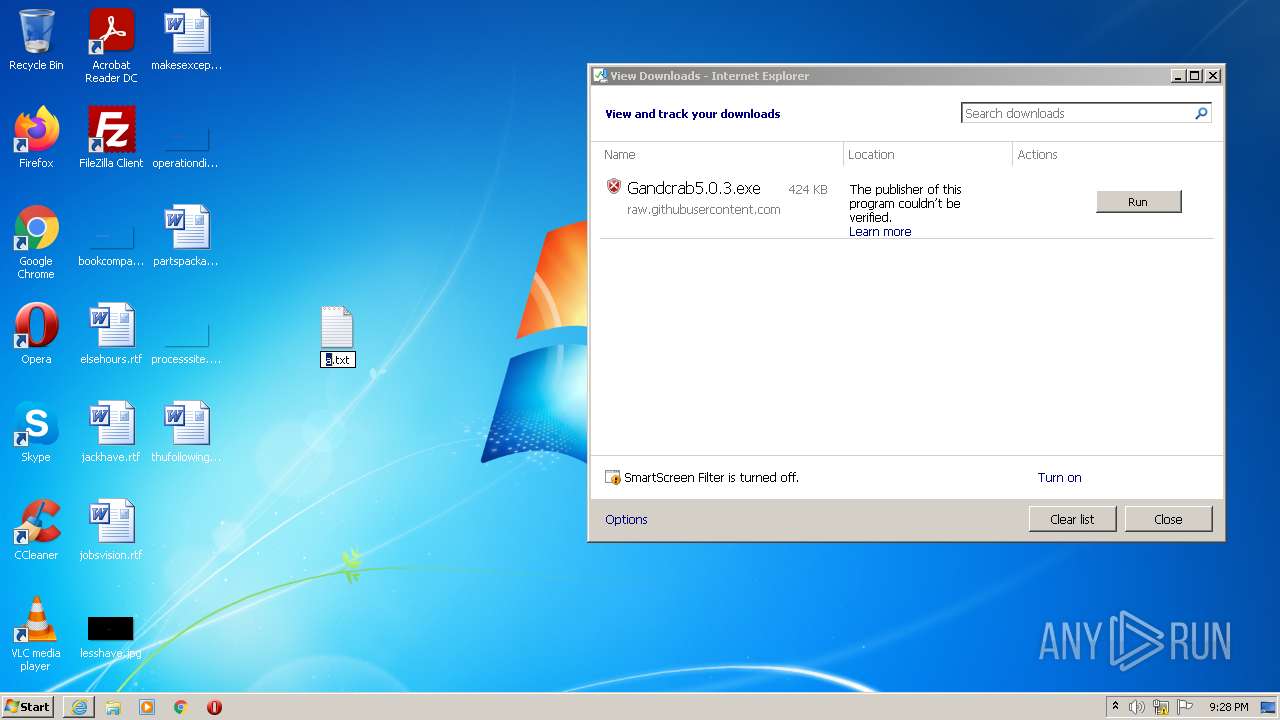
| URL: | https://github.com/mstfknn/malware-sample-library/blob/master/GandCrab/Gandcrab5.0.3.exe?raw=true |
| Full analysis: | https://app.any.run/tasks/bb01d10c-39ae-4cb6-9157-94a61b75e399 |
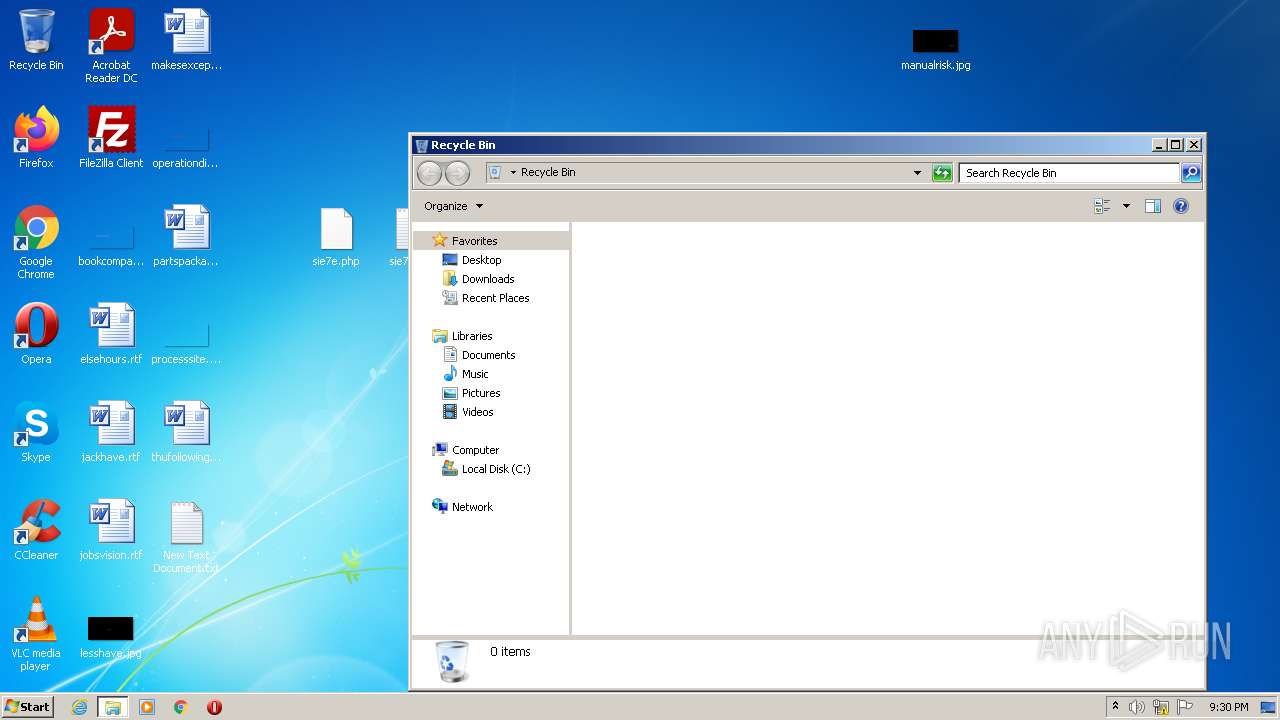
| Verdict: | Malicious activity |
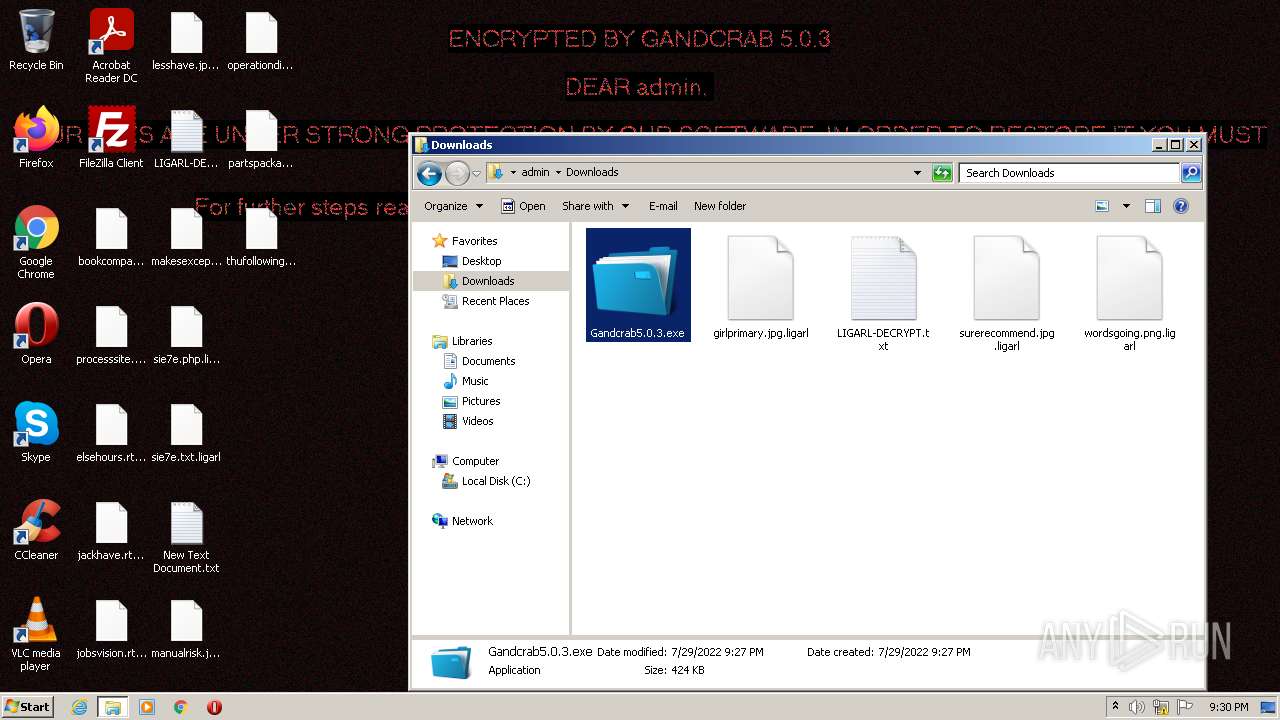
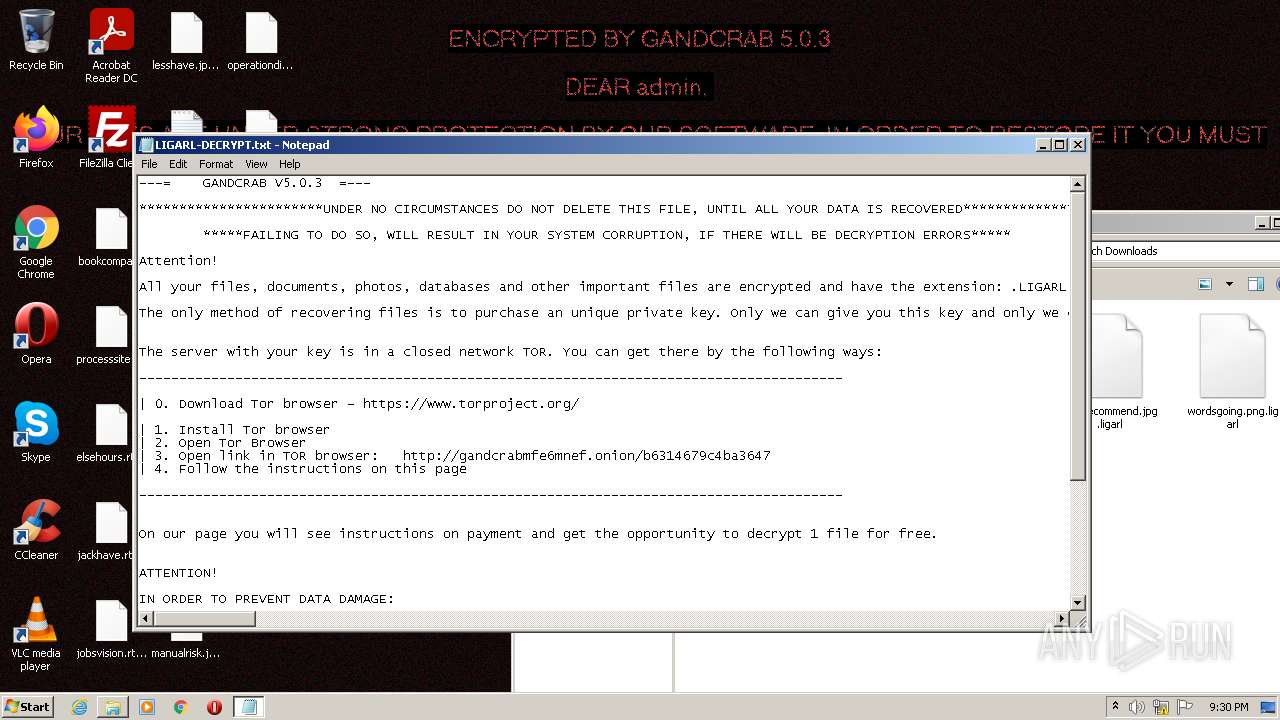
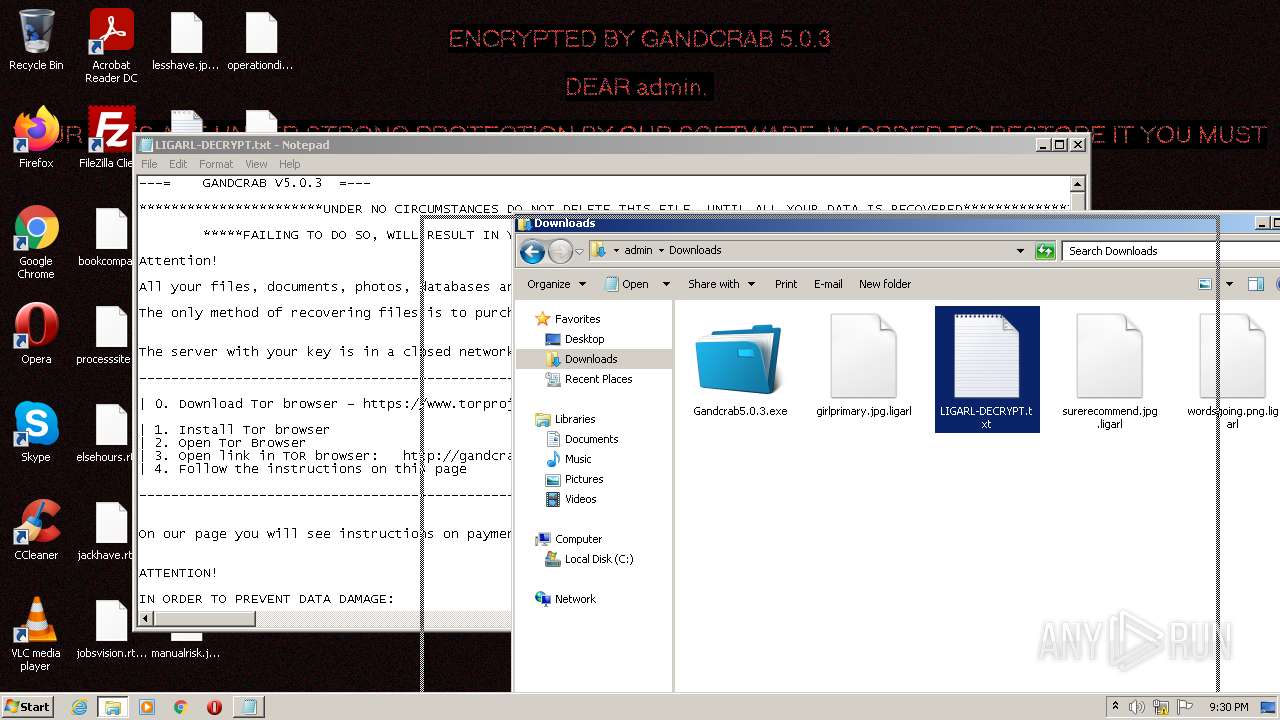
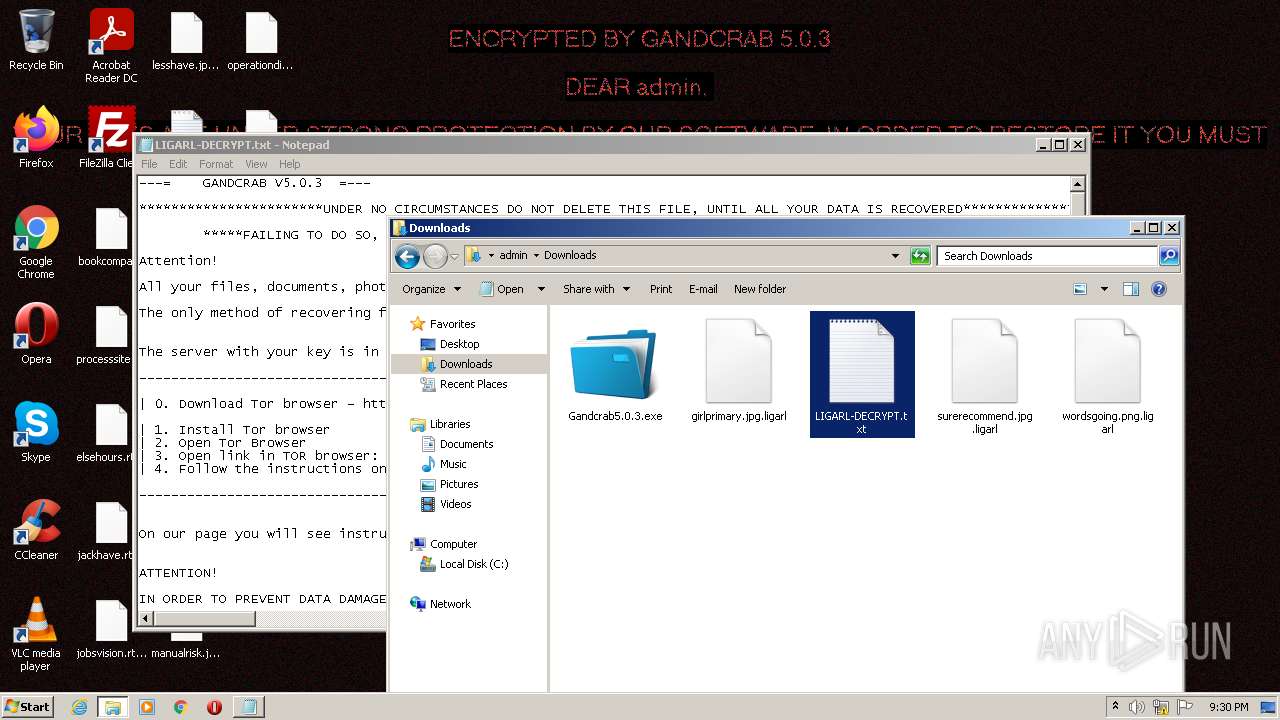
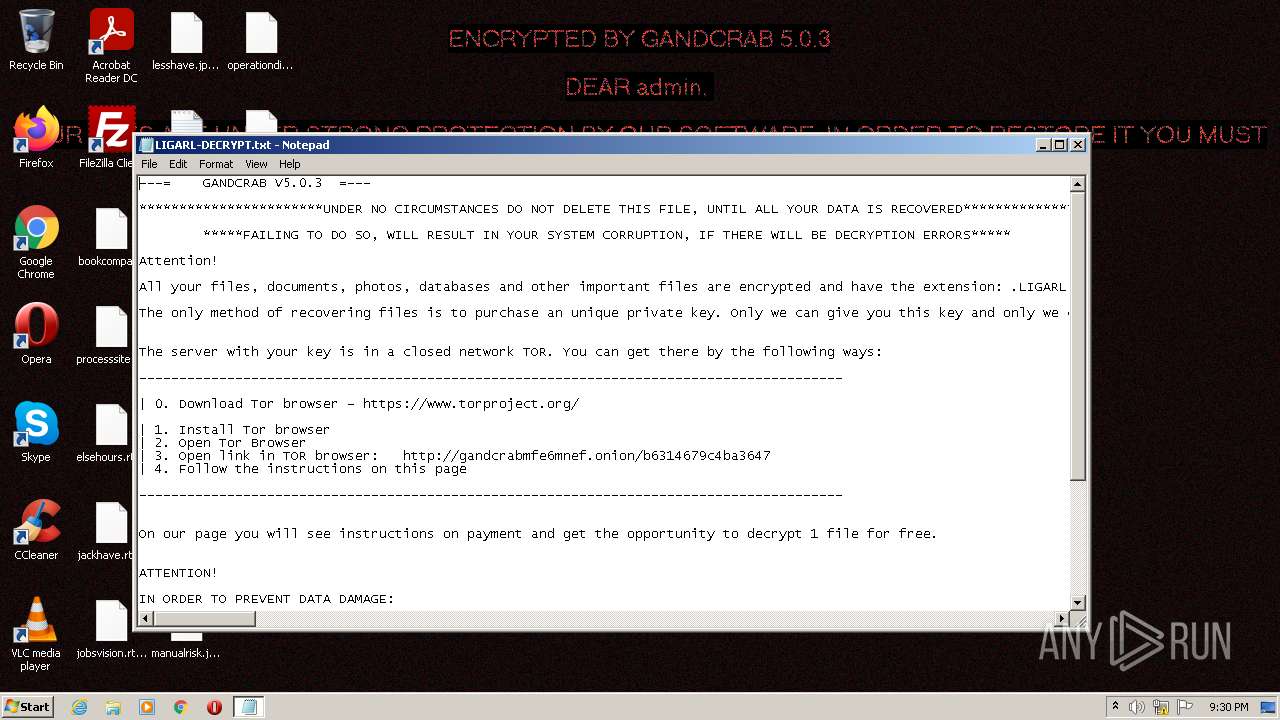
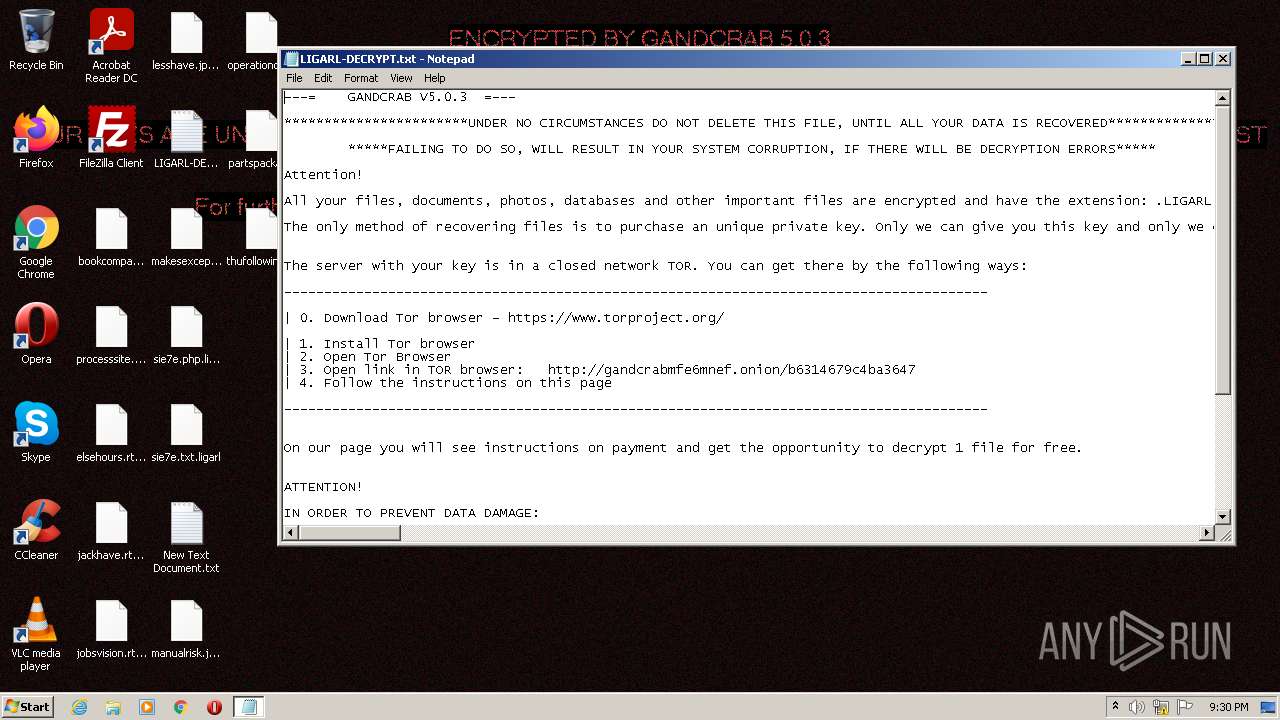
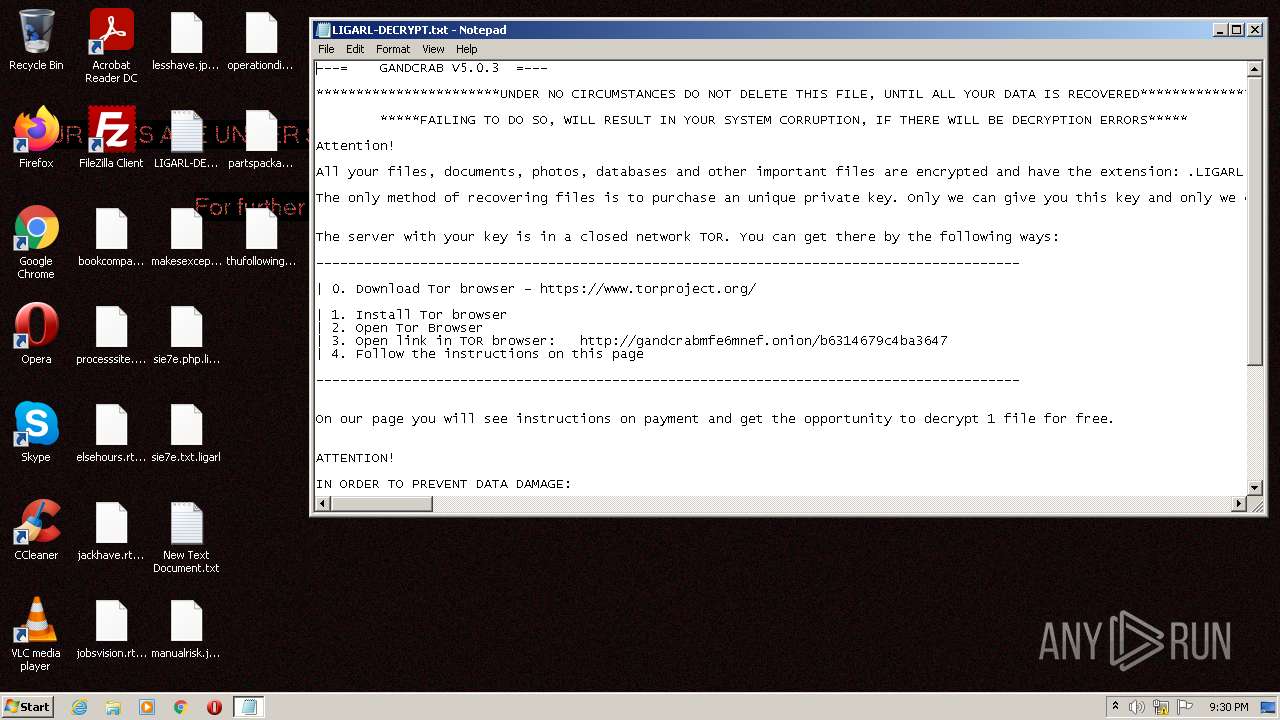
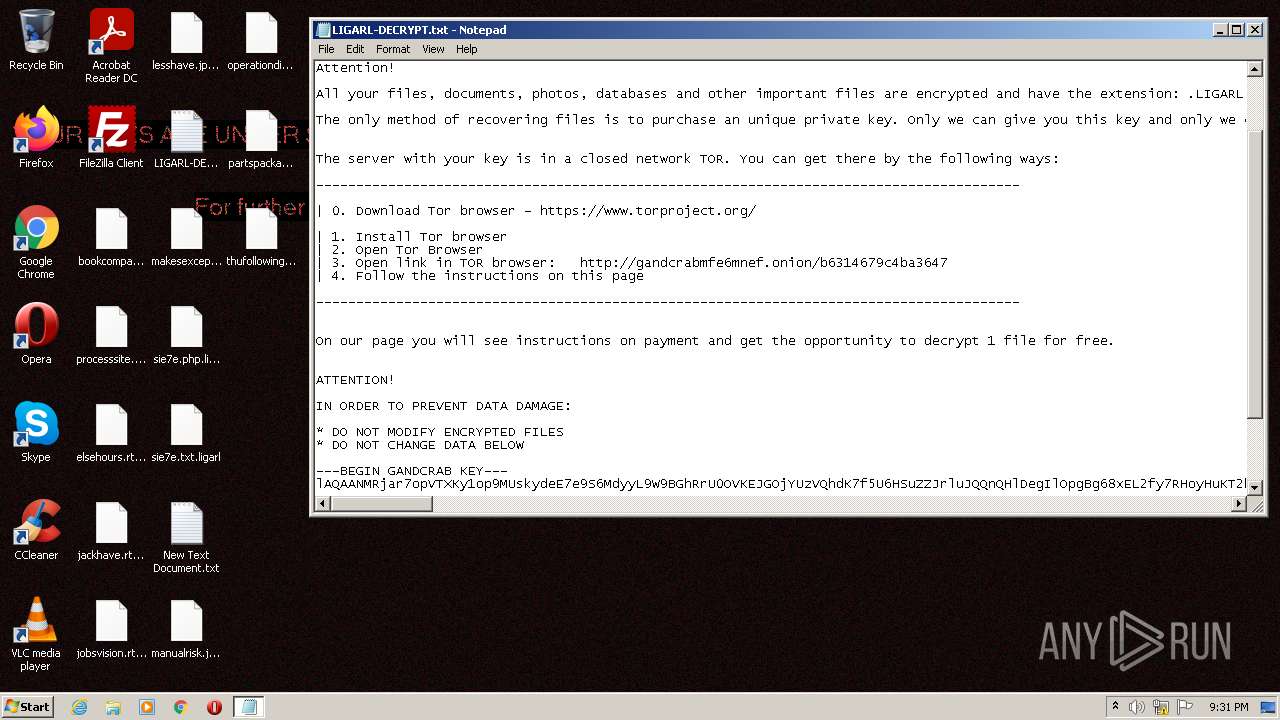
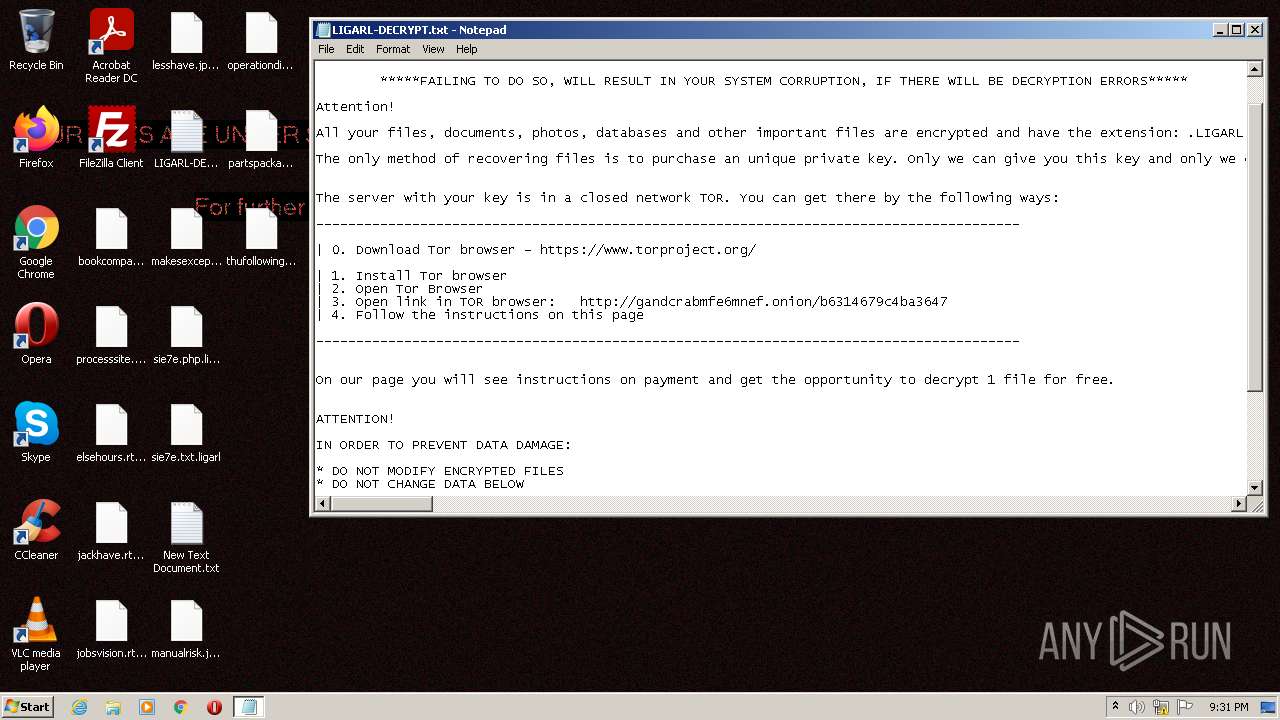
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
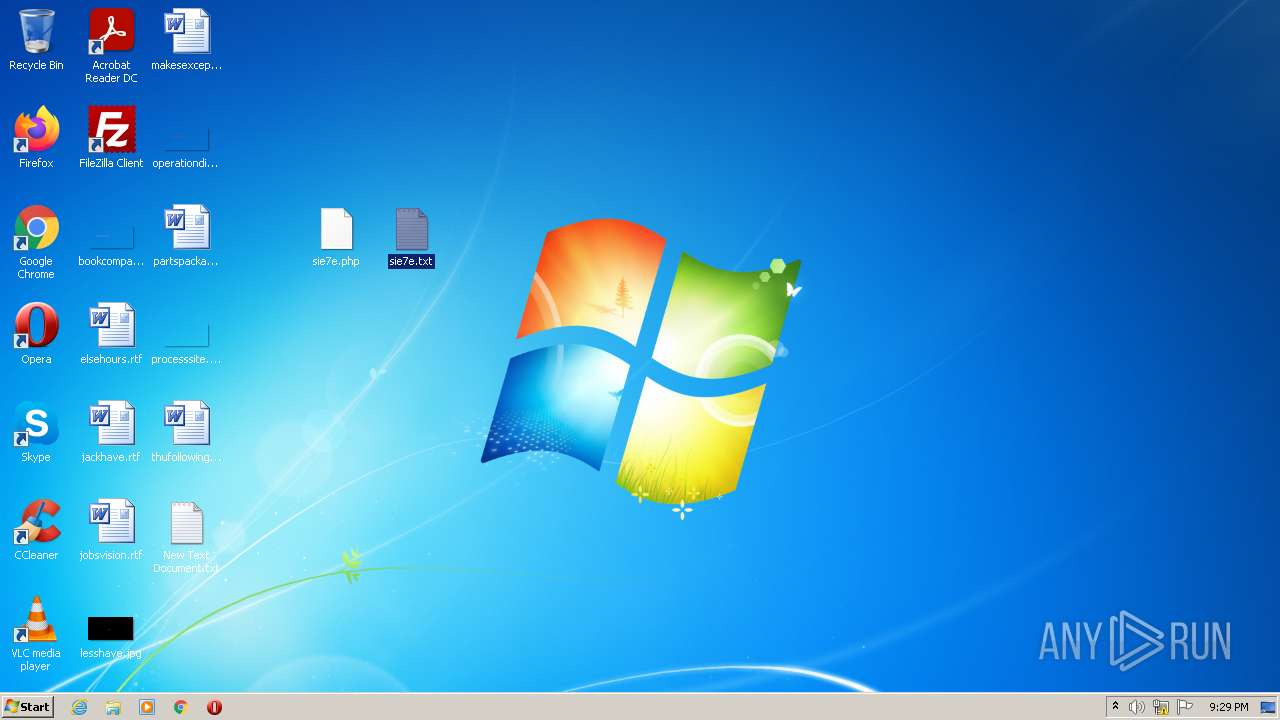
| Analysis date: | July 29, 2022, 20:26:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | BF20FE9896DE938E17CFC54C629375F9 |
| SHA1: | 28CADB9731D6D46689A3C982CA8C59B3FC9944A1 |
| SHA256: | AD24BBB316242D7AE898DF4D350F6A34E46A445F54980F5EA7686133CA56DC97 |
| SSDEEP: | 3:N8tEd4LLKIEZ1HbqIEHwBgEPjhWLAC1rH:2uu/IZ1+wBlA0C1rH |
MALICIOUS
Drops executable file immediately after starts
- iexplore.exe (PID: 3376)
- iexplore.exe (PID: 2928)
- wermgr.exe (PID: 2556)
Application was dropped or rewritten from another process
- Gandcrab5.0.3.exe (PID: 1016)
Steals credentials from Web Browsers
- wermgr.exe (PID: 2556)
Actions looks like stealing of personal data
- wermgr.exe (PID: 2556)
GandCrab keys found
- wermgr.exe (PID: 2556)
Writes file to Word startup folder
- wermgr.exe (PID: 2556)
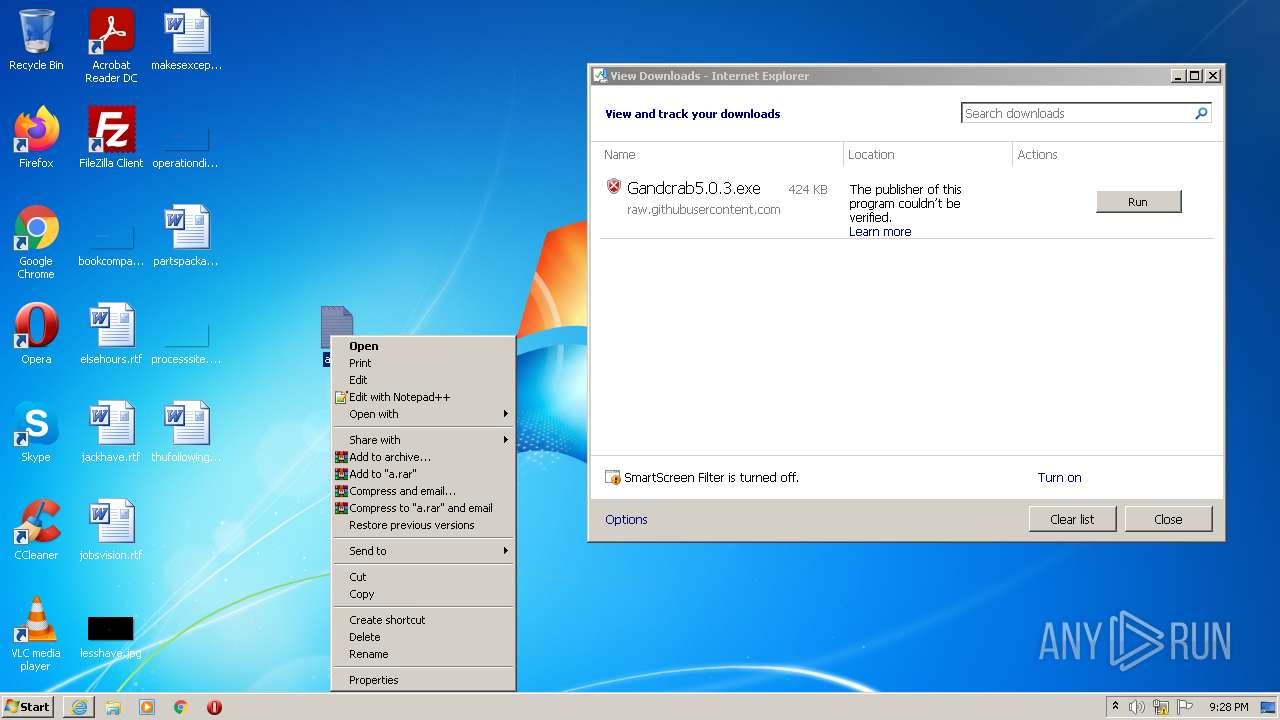
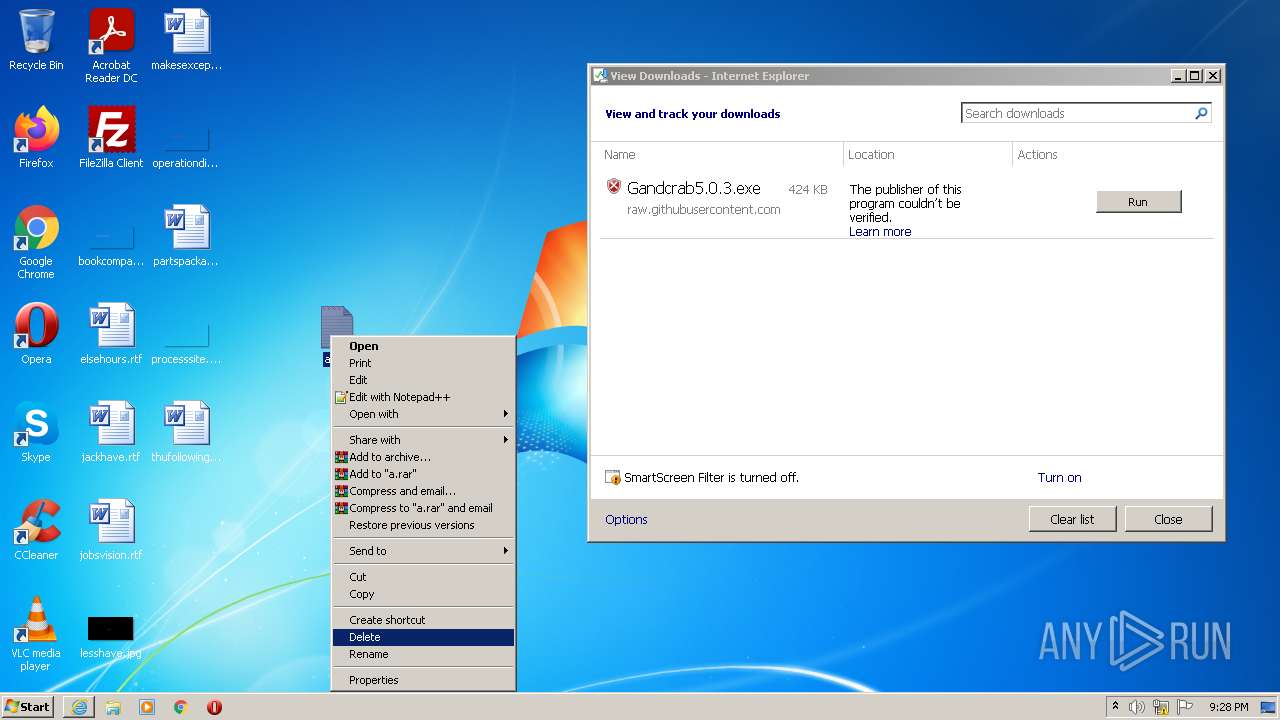
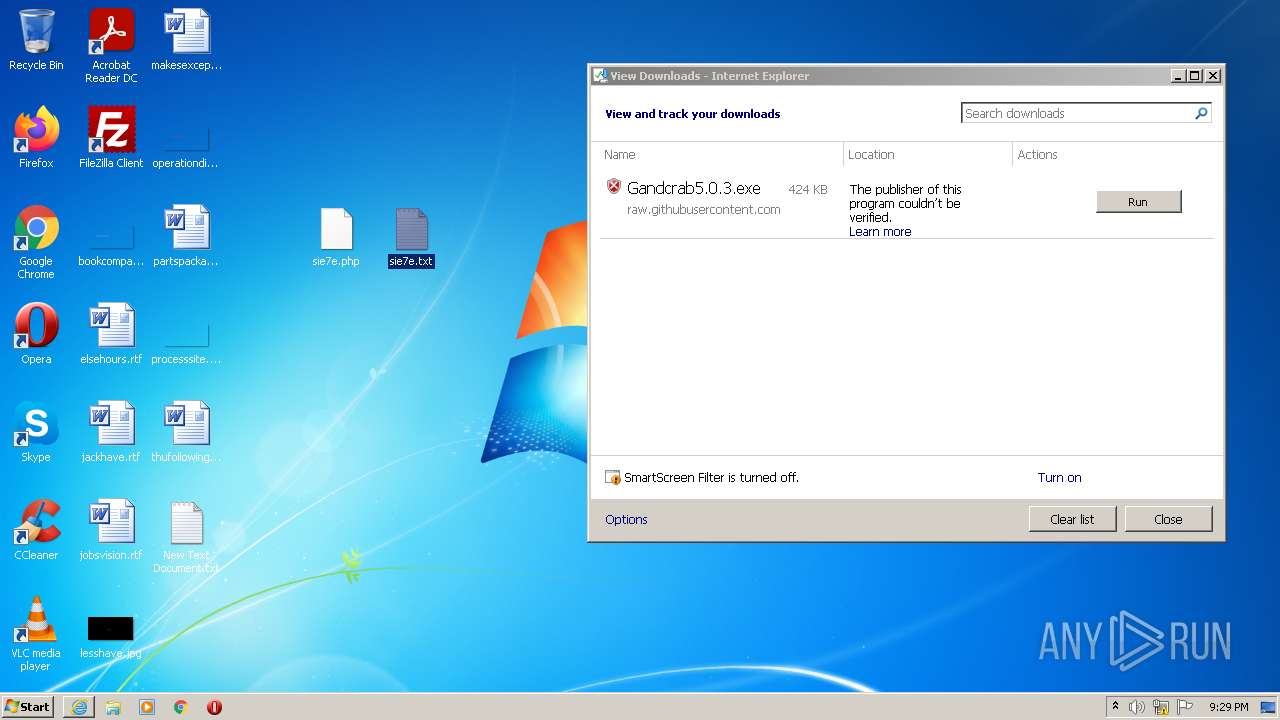
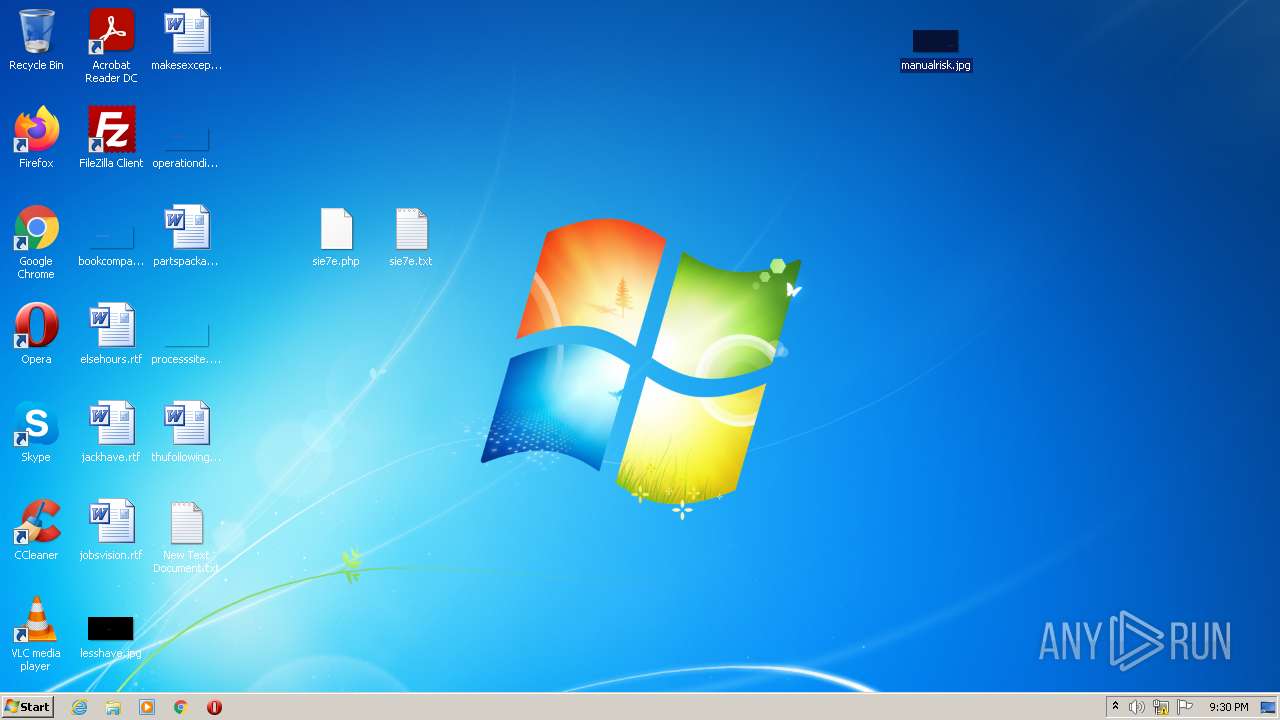
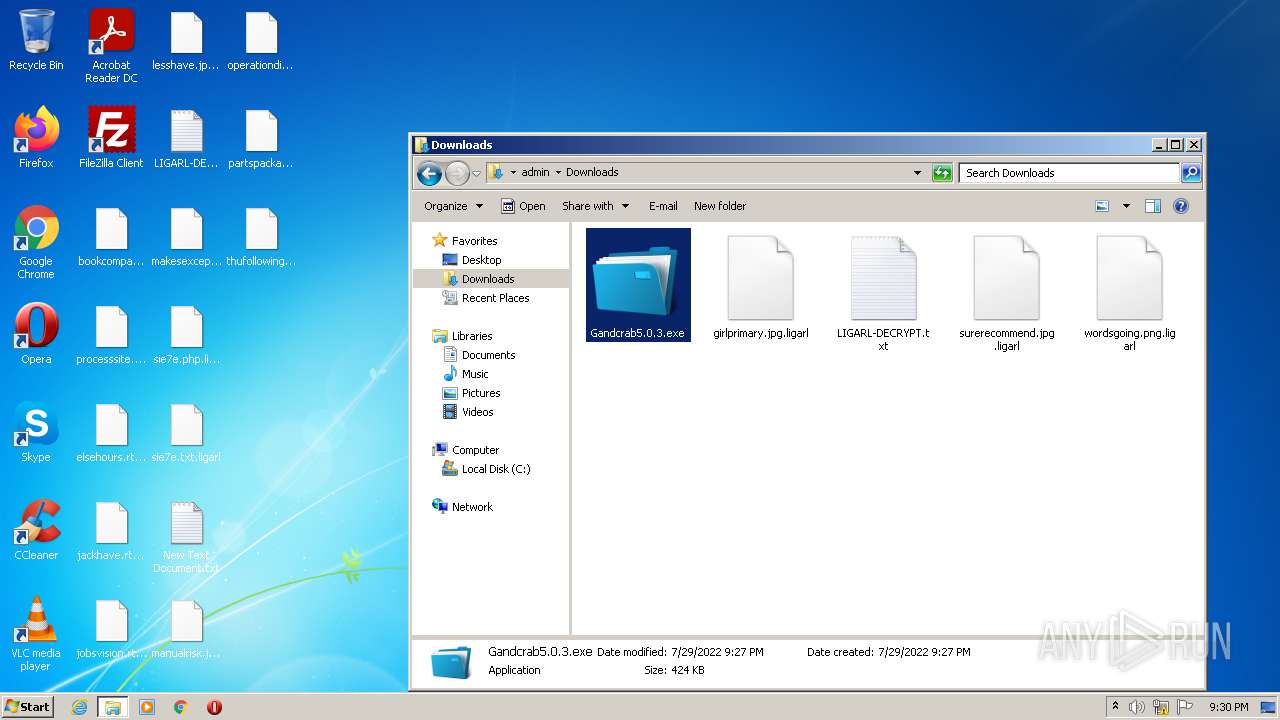
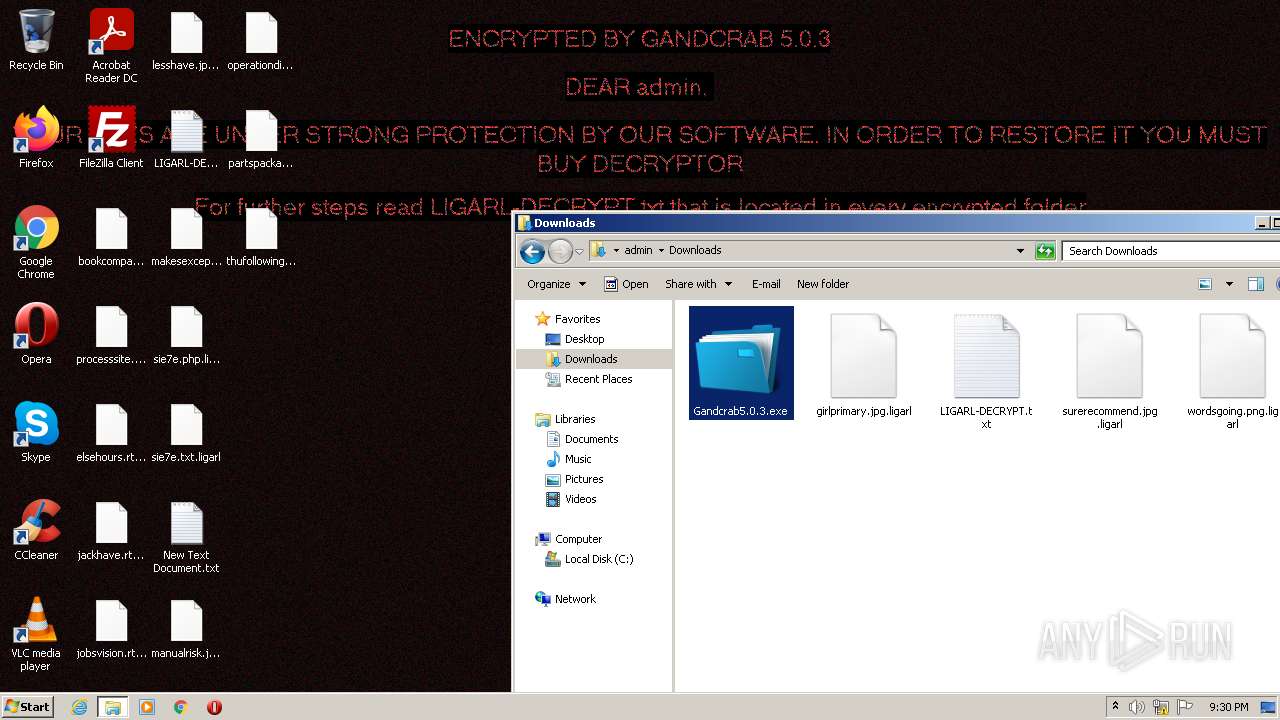
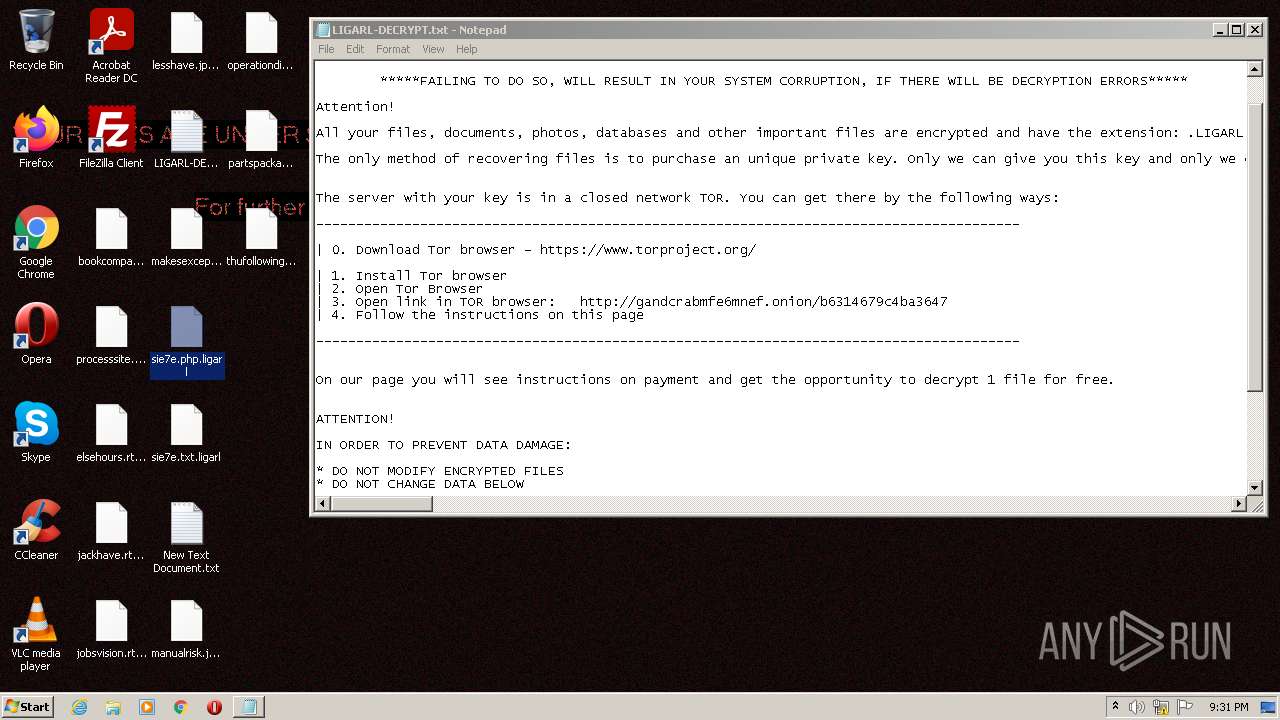
Renames files like Ransomware
- wermgr.exe (PID: 2556)
GANDCRAB detected
- wermgr.exe (PID: 2556)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3376)
Executable content was dropped or overwritten
- iexplore.exe (PID: 3376)
- iexplore.exe (PID: 2928)
Drops a file with a compile date too recent
- iexplore.exe (PID: 3376)
- iexplore.exe (PID: 2928)
- wermgr.exe (PID: 2556)
Checks supported languages
- Gandcrab5.0.3.exe (PID: 1016)
- wmic.exe (PID: 452)
- notepad++.exe (PID: 1388)
- gup.exe (PID: 3192)
Reads Environment values
- wermgr.exe (PID: 2556)
Reads the computer name
- wmic.exe (PID: 452)
- gup.exe (PID: 3192)
- notepad++.exe (PID: 1388)
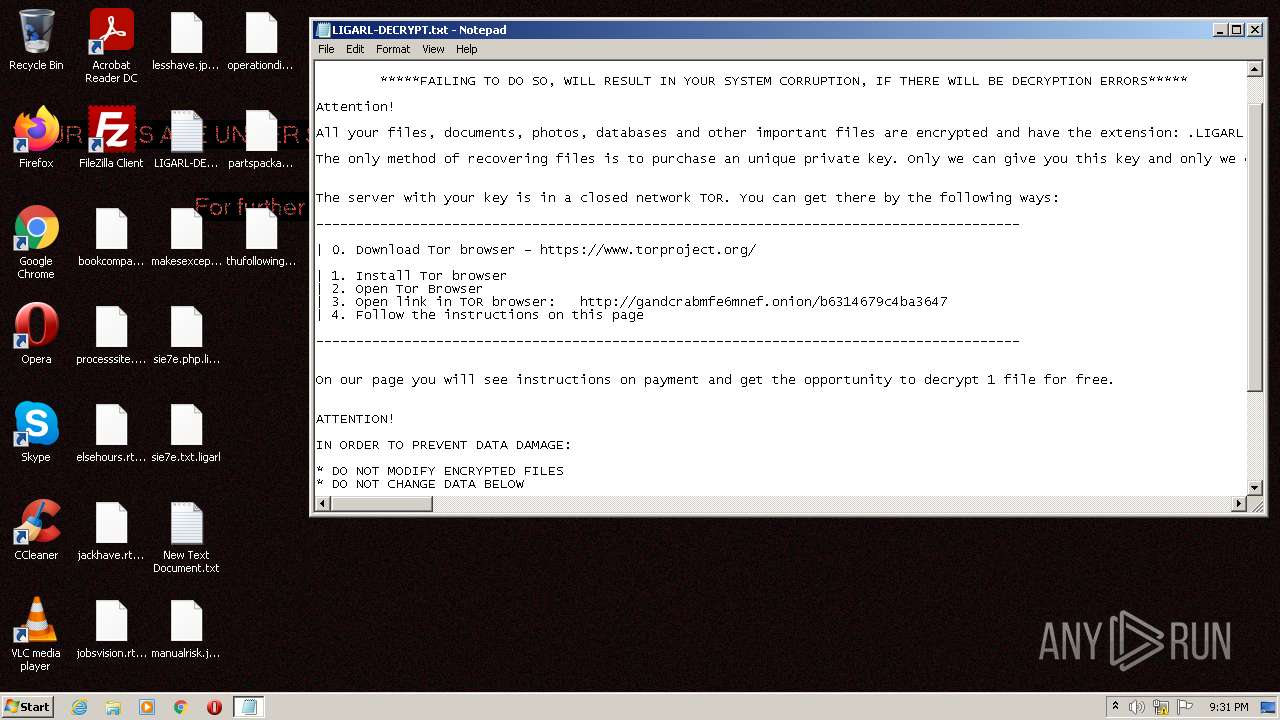
Creates files like Ransomware instruction
- wermgr.exe (PID: 2556)
INFO
Checks supported languages
- iexplore.exe (PID: 2928)
- iexplore.exe (PID: 3376)
- NOTEPAD.EXE (PID: 2876)
- NOTEPAD.EXE (PID: 2648)
- wermgr.exe (PID: 2556)
- NOTEPAD.EXE (PID: 1068)
Reads the computer name
- iexplore.exe (PID: 2928)
- iexplore.exe (PID: 3376)
- NOTEPAD.EXE (PID: 2648)
- wermgr.exe (PID: 2556)
Reads settings of System Certificates
- iexplore.exe (PID: 3376)
- iexplore.exe (PID: 2928)
- wermgr.exe (PID: 2556)
Changes internet zones settings
- iexplore.exe (PID: 2928)
Application launched itself
- iexplore.exe (PID: 2928)
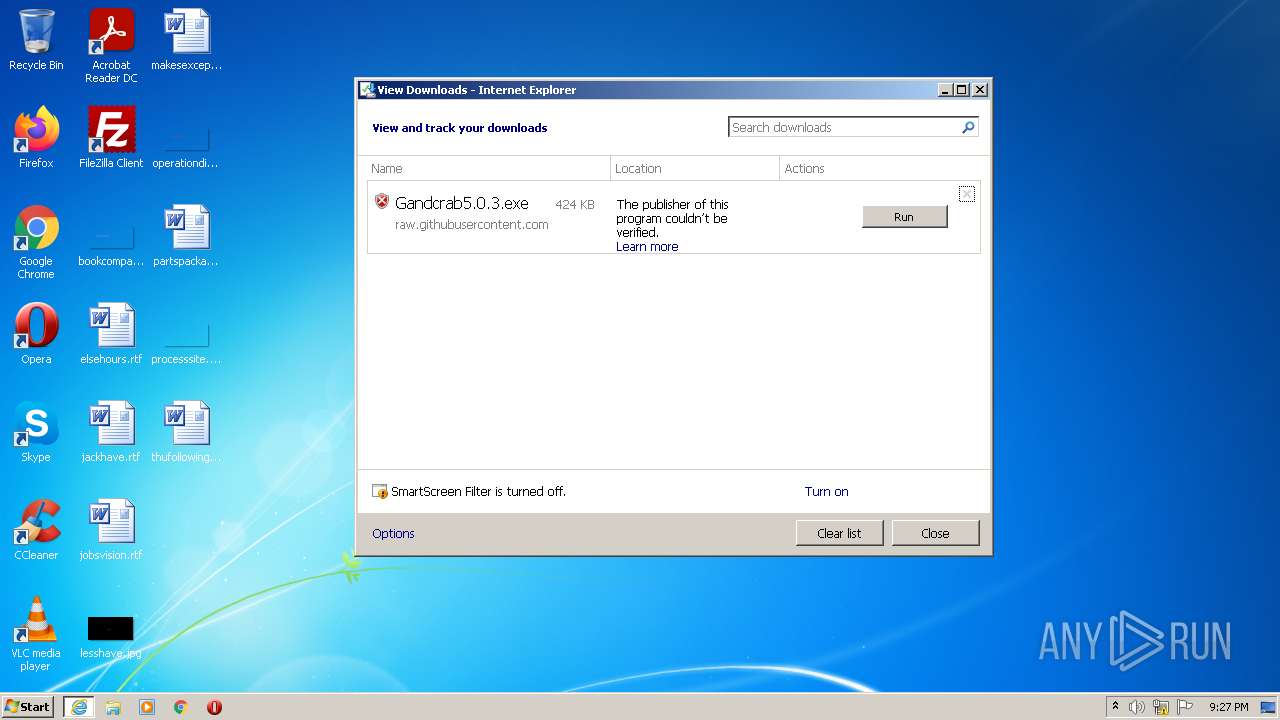
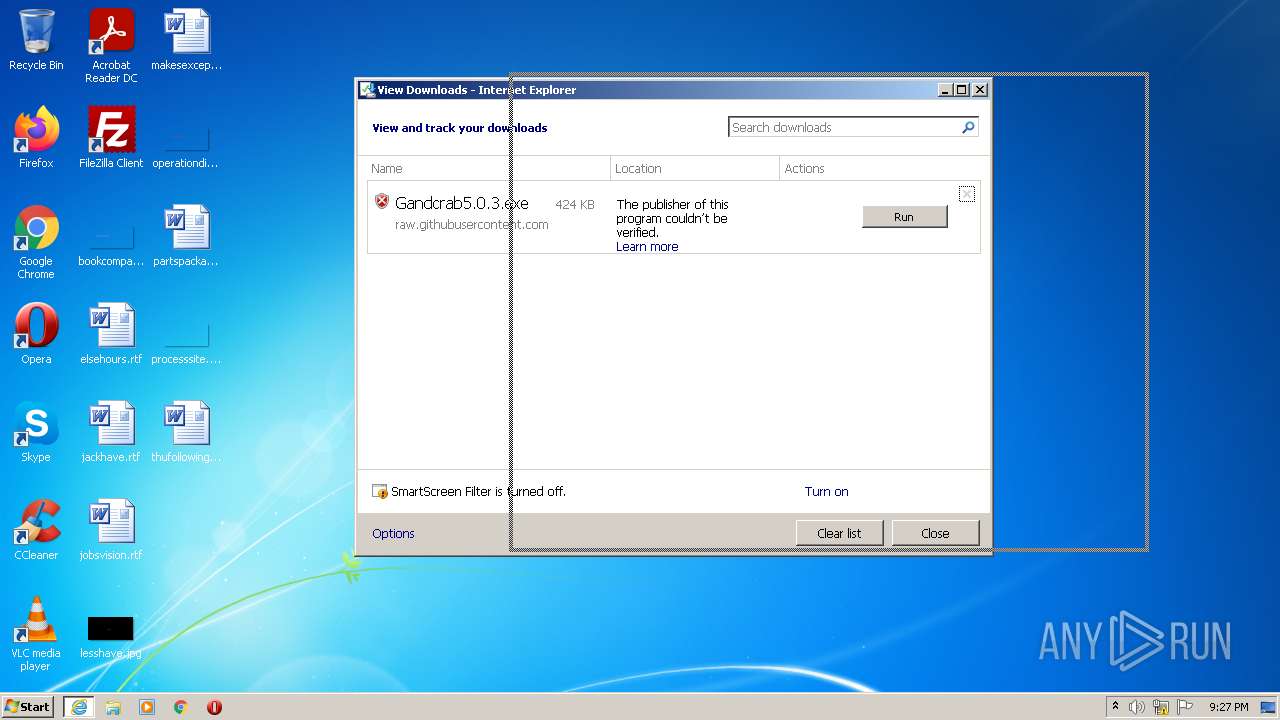
Checks Windows Trust Settings
- iexplore.exe (PID: 3376)
- iexplore.exe (PID: 2928)
- wermgr.exe (PID: 2556)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2928)
Reads the date of Windows installation
- iexplore.exe (PID: 2928)
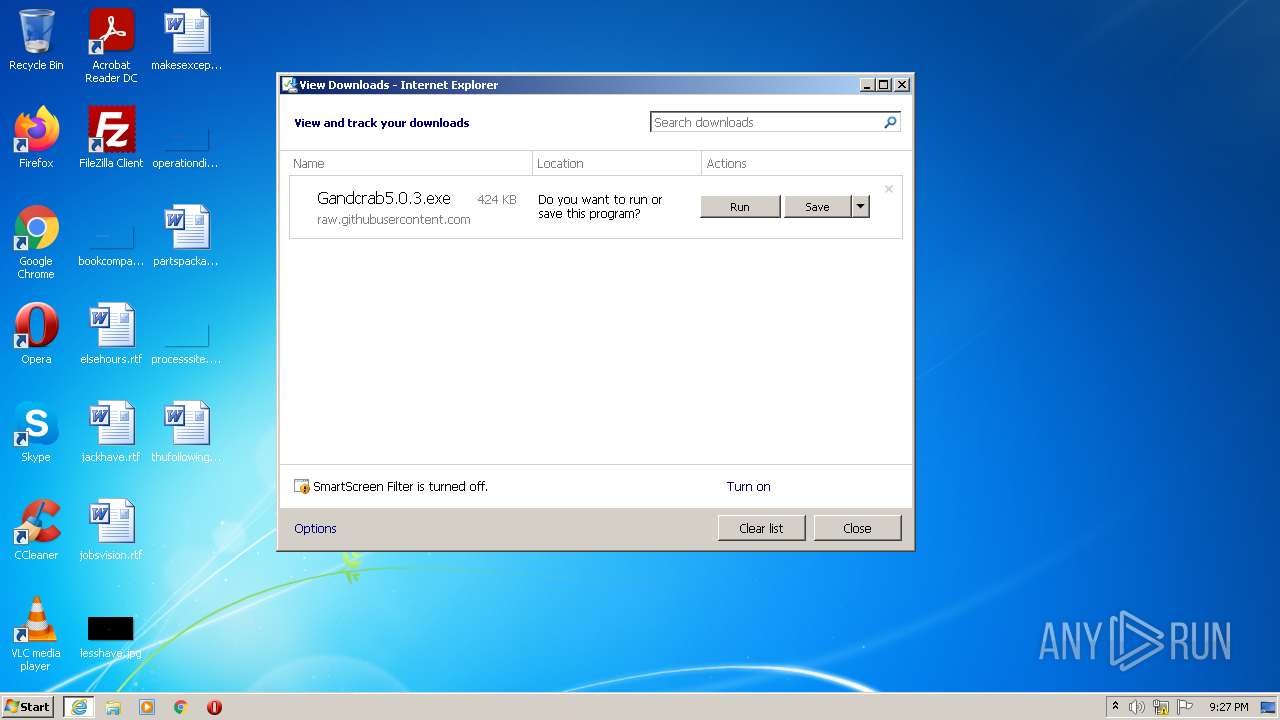
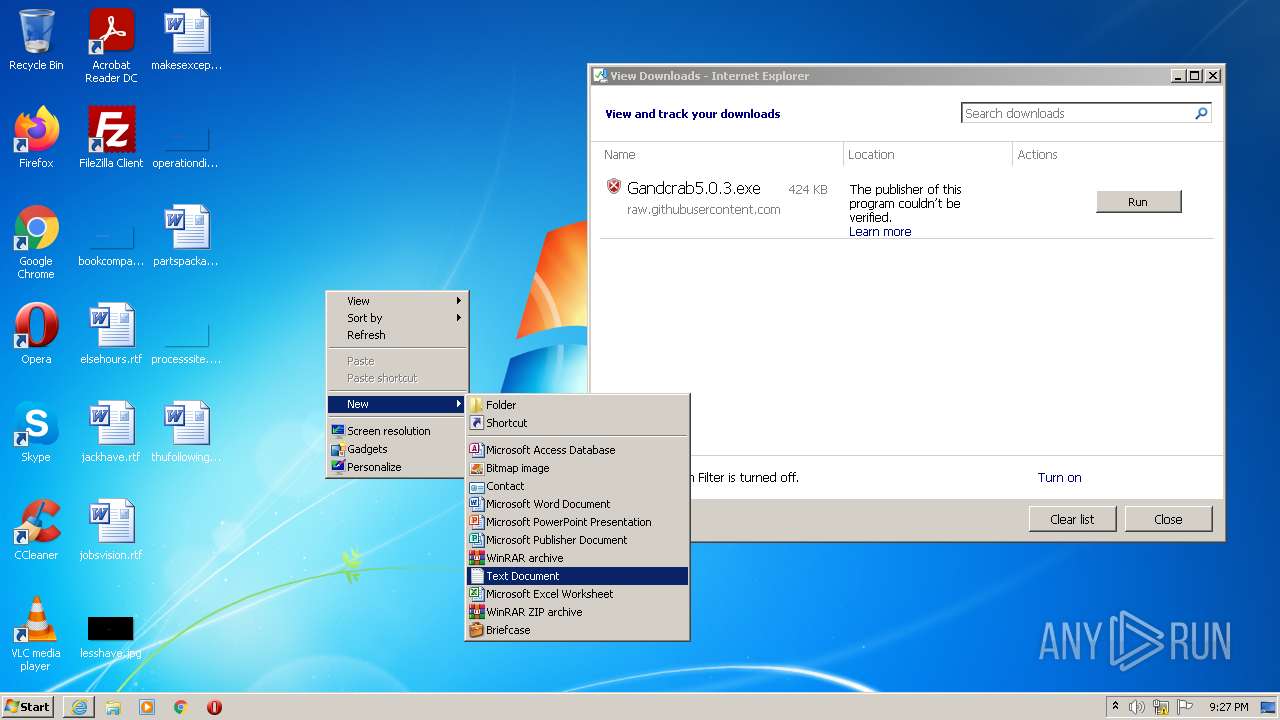
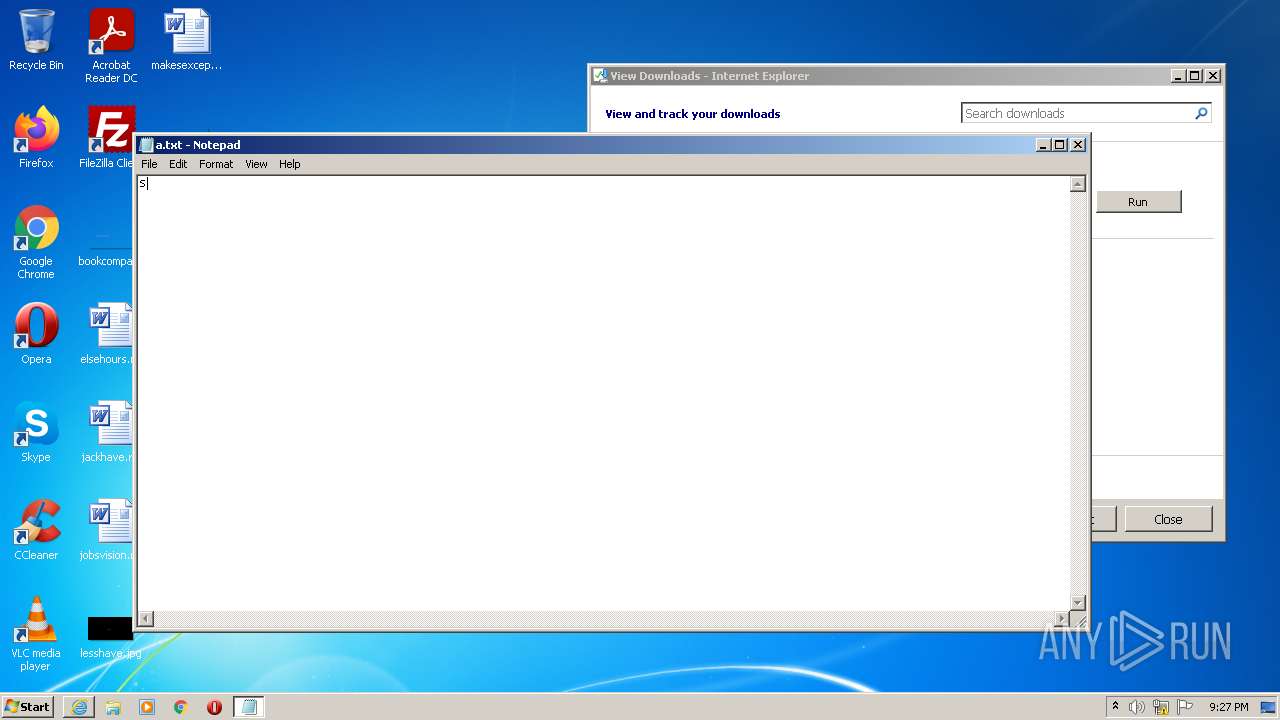
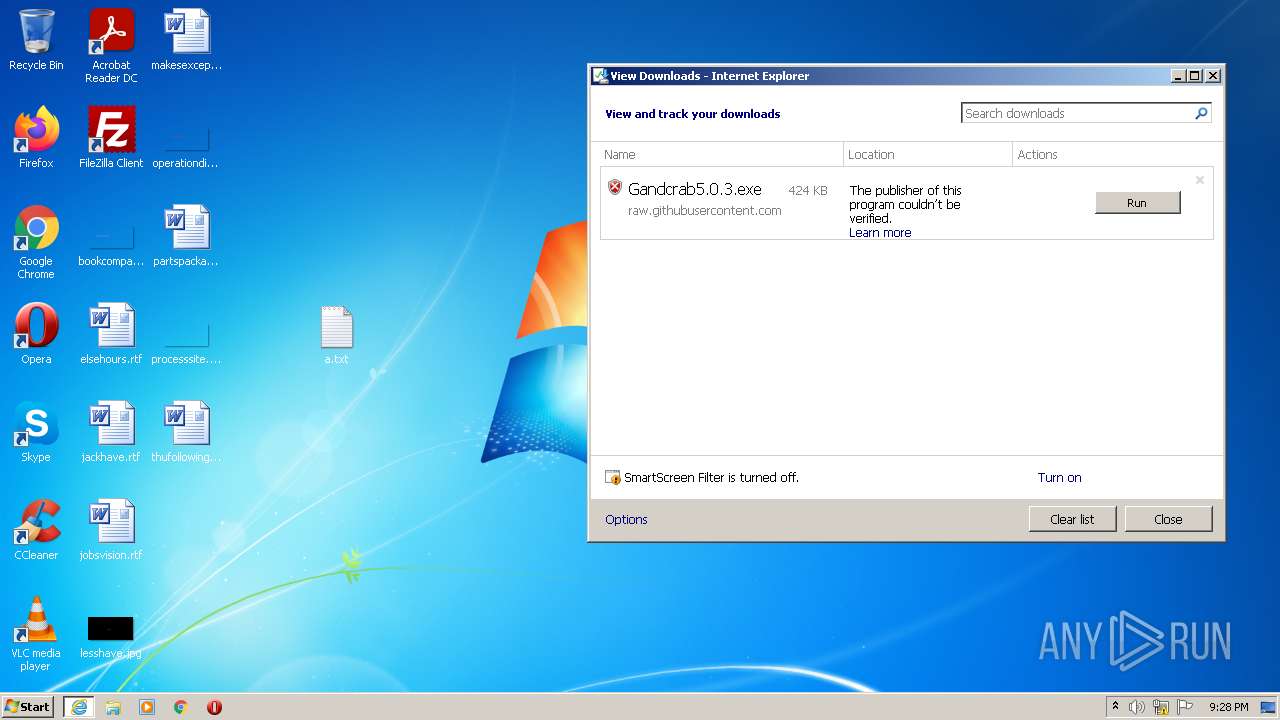
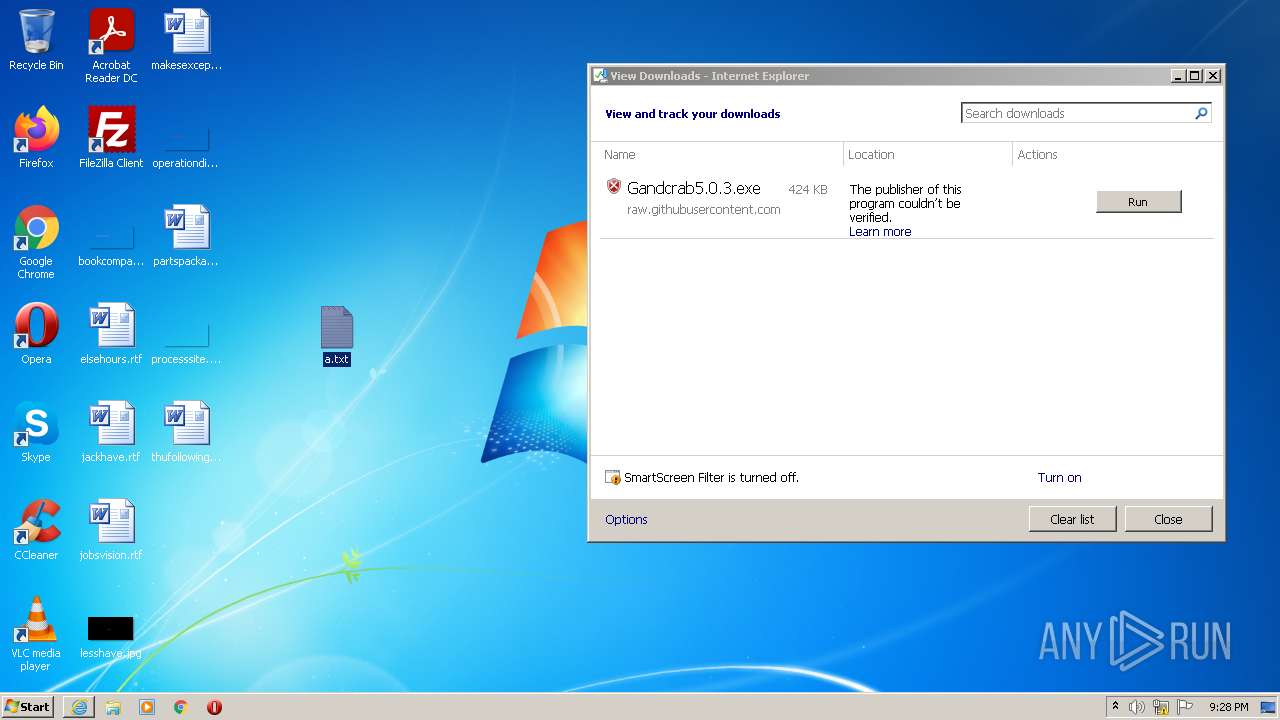
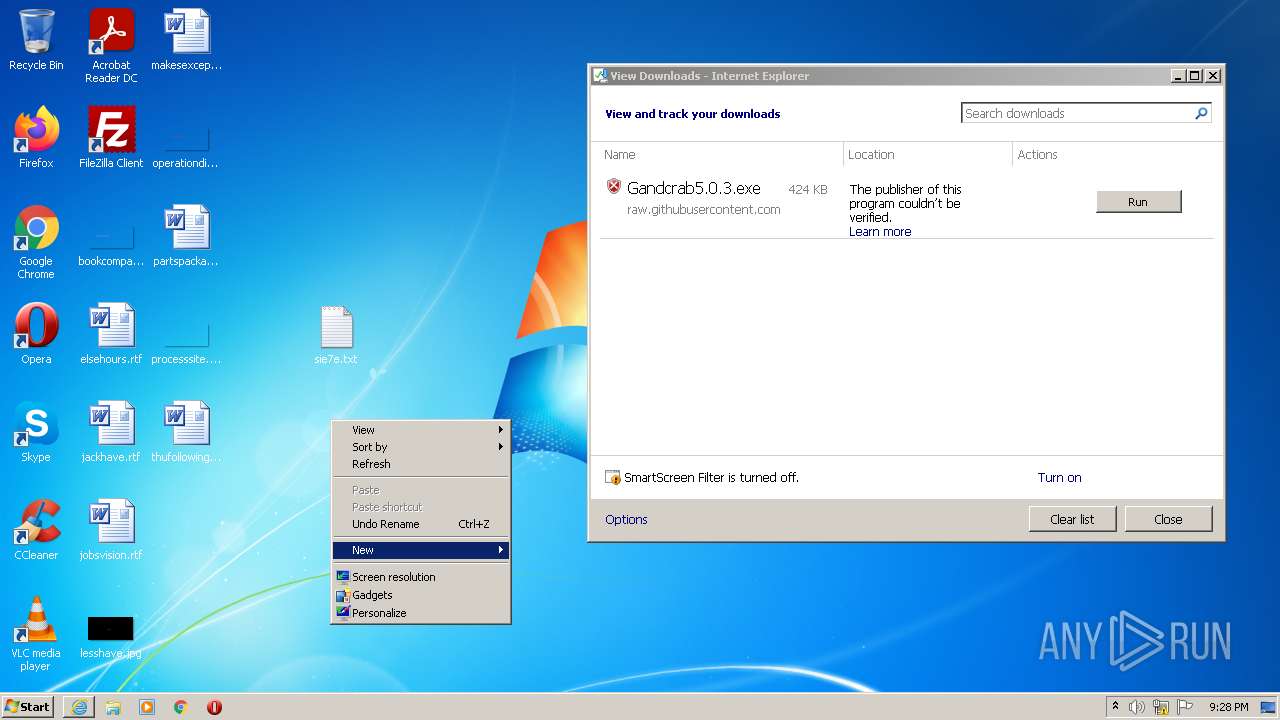
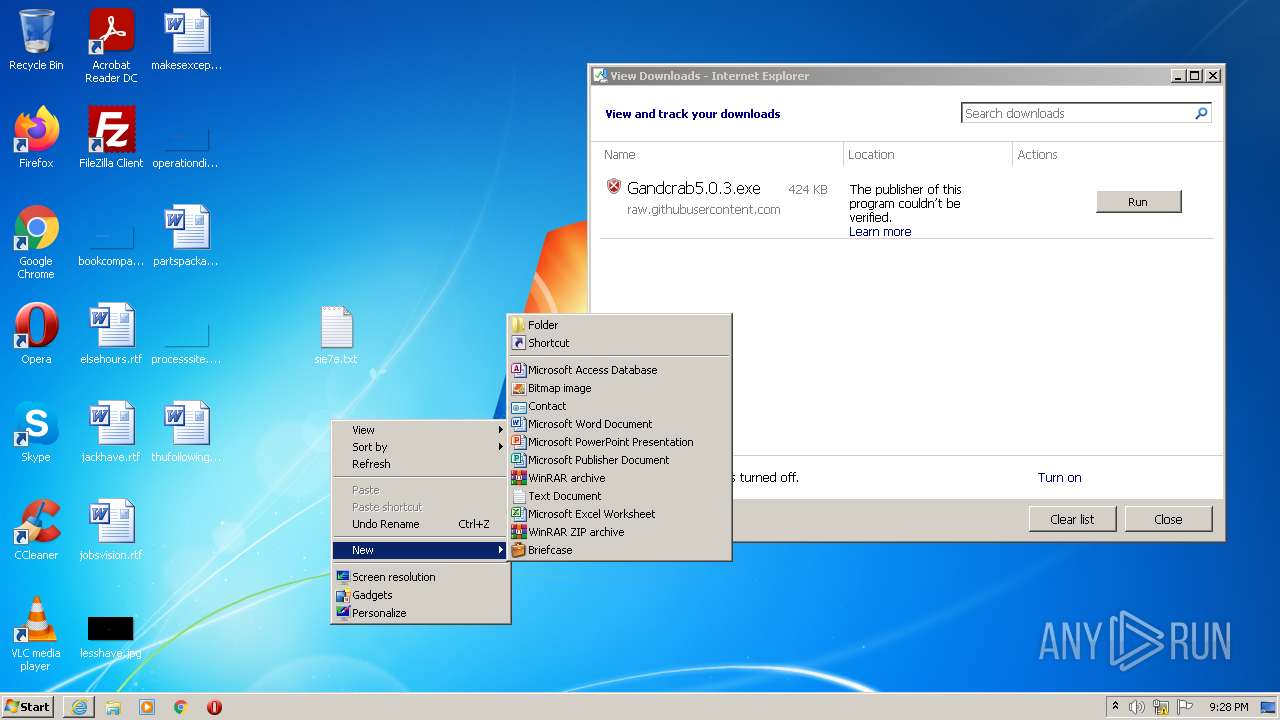
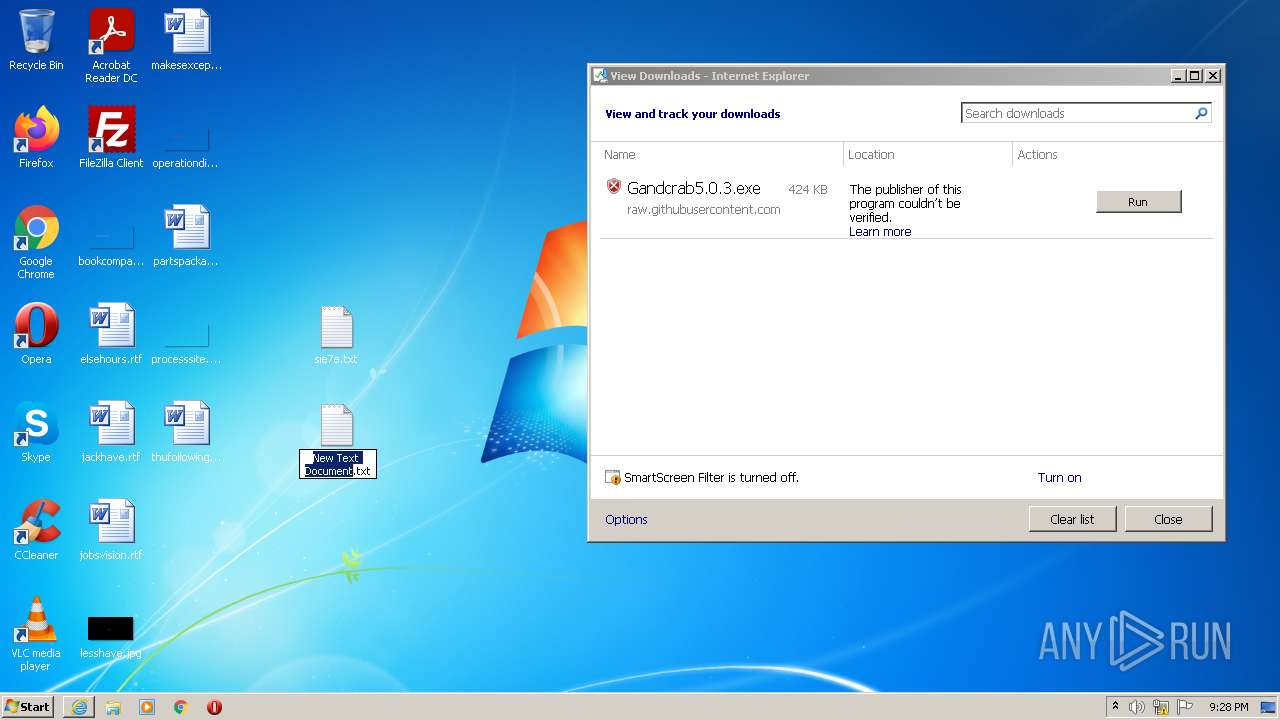
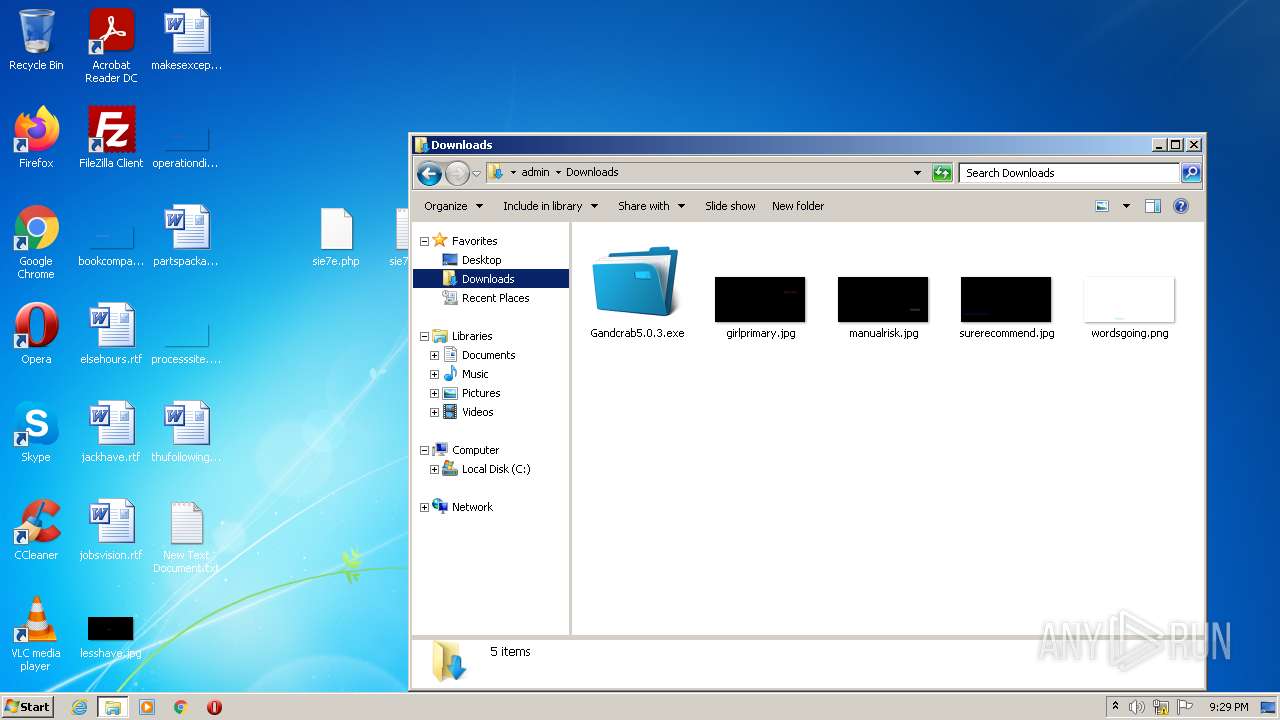
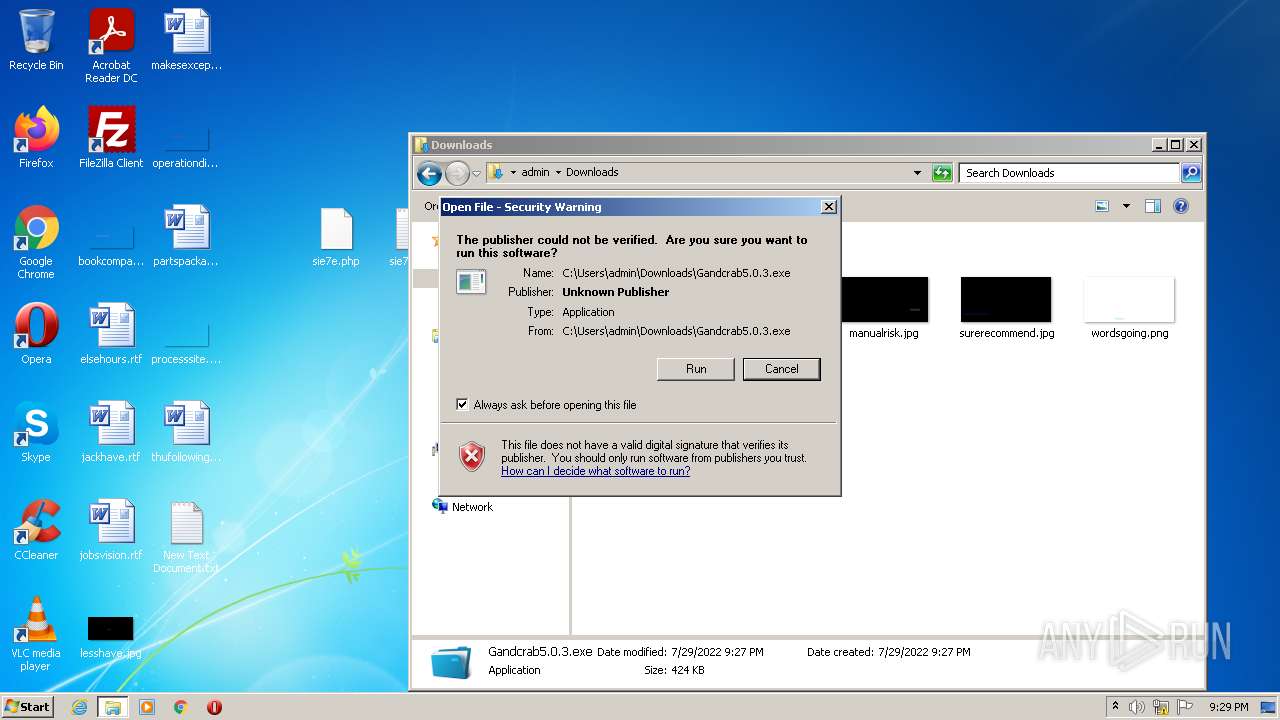
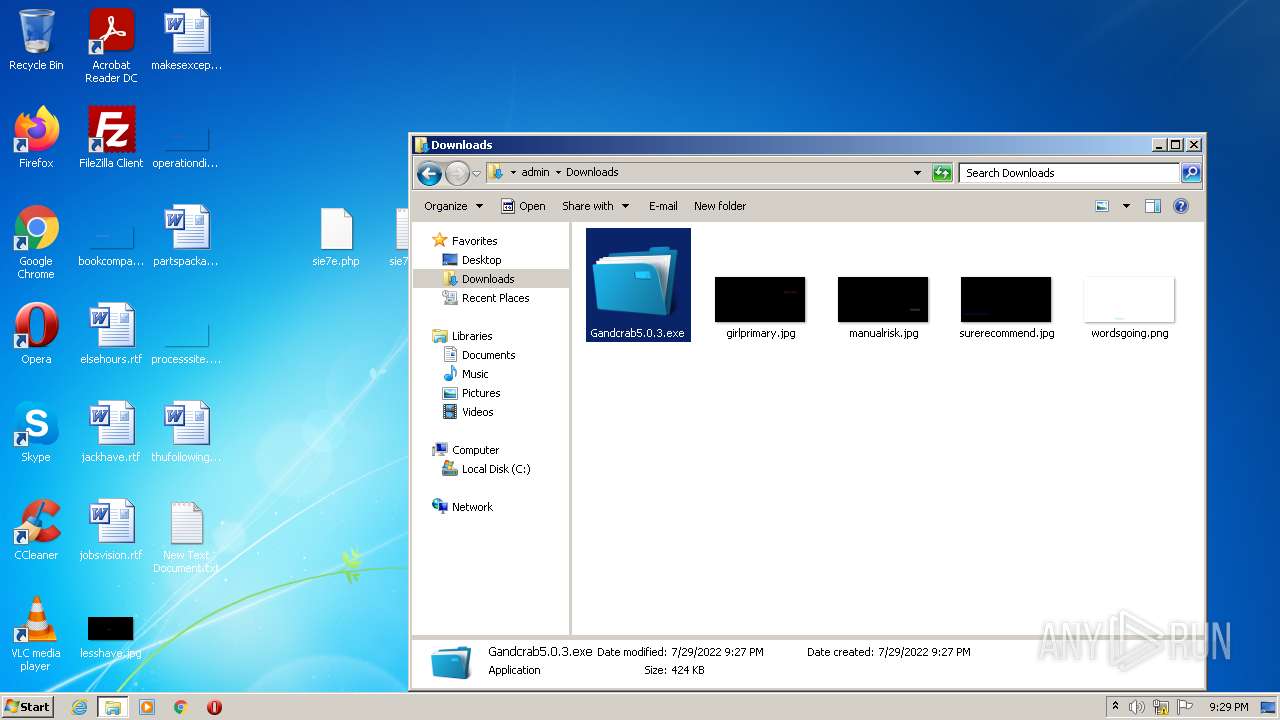
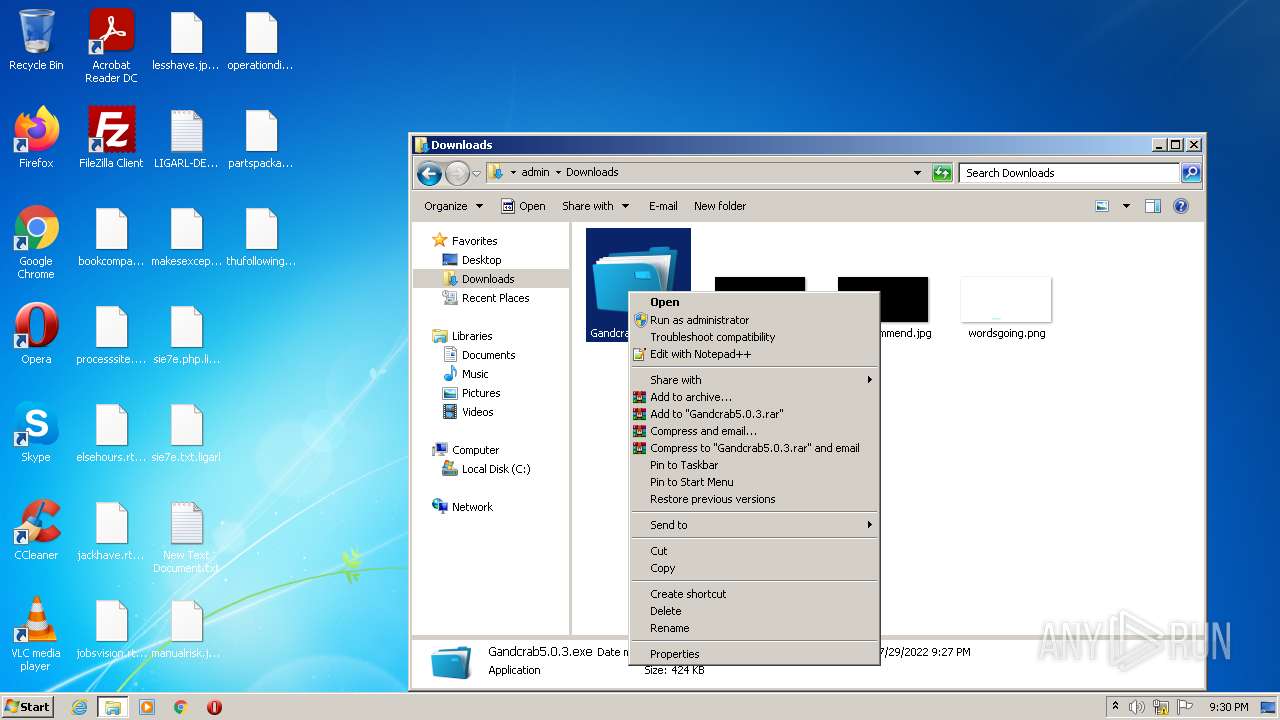
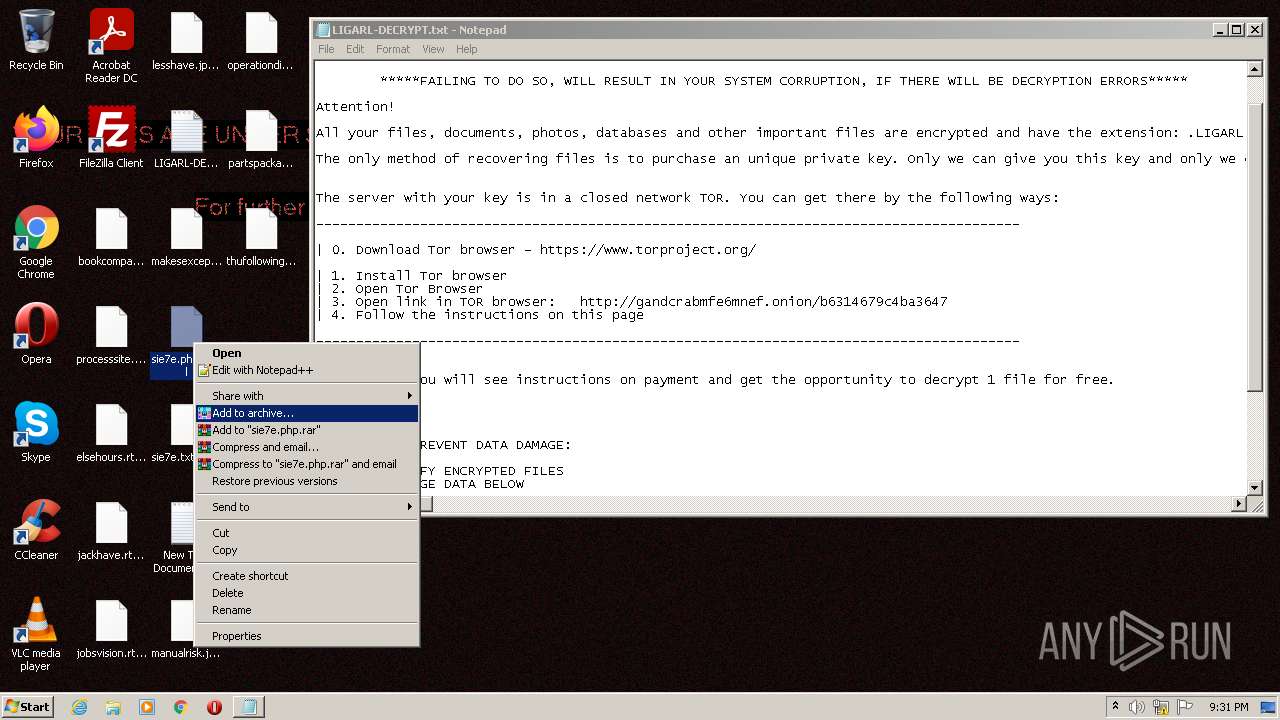
Manual execution by user
- NOTEPAD.EXE (PID: 2876)
- NOTEPAD.EXE (PID: 2648)
- Gandcrab5.0.3.exe (PID: 1016)
- NOTEPAD.EXE (PID: 1068)
- notepad++.exe (PID: 1388)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 2928)
- wermgr.exe (PID: 2556)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2928)
Changes settings of System certificates
- iexplore.exe (PID: 2928)
Reads CPU info
- wermgr.exe (PID: 2556)
Dropped object may contain TOR URL's
- wermgr.exe (PID: 2556)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
57
Monitored processes
10
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 452 | "C:\Windows\system32\wbem\wmic.exe" shadowcopy delete | C:\Windows\system32\wbem\wmic.exe | — | wermgr.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 2147749908 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
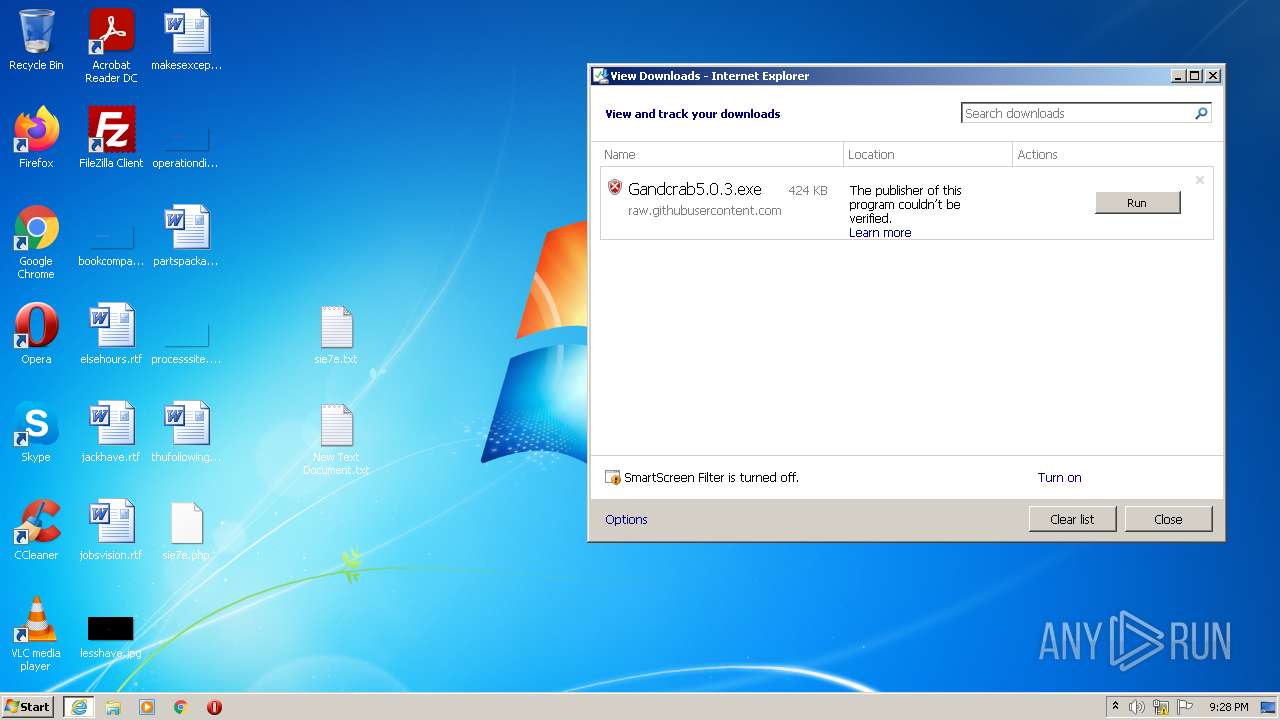
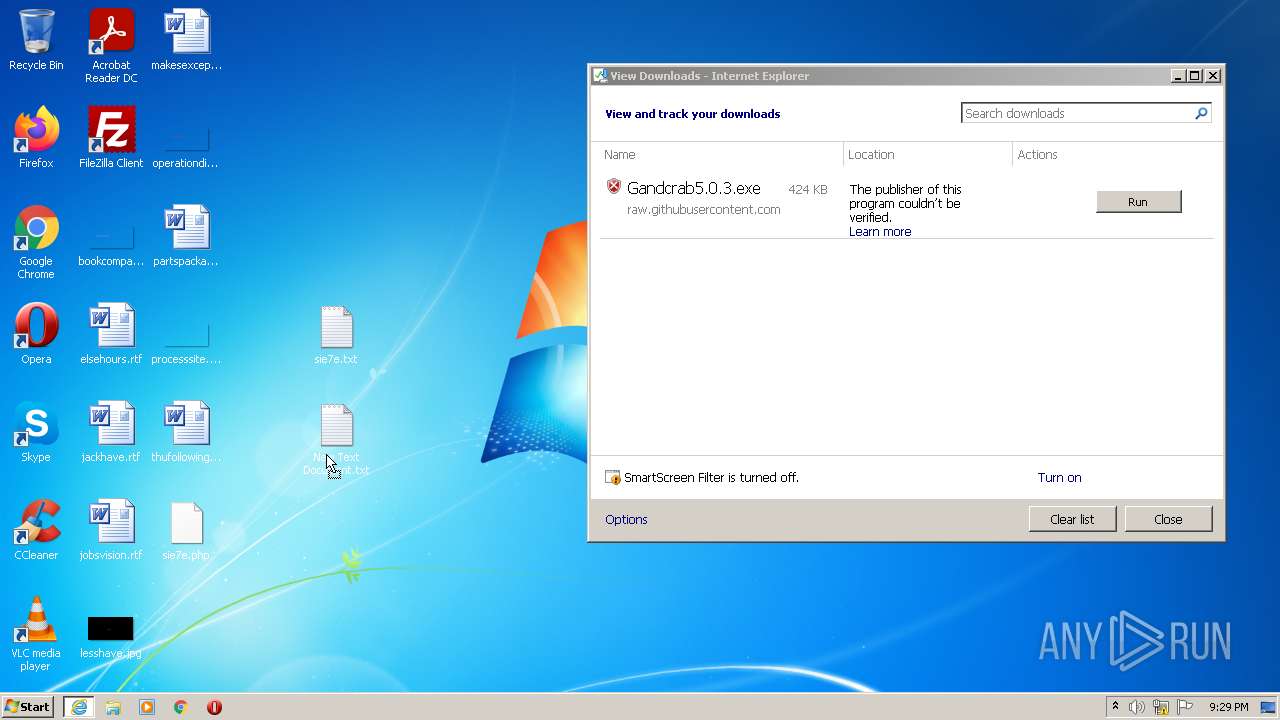
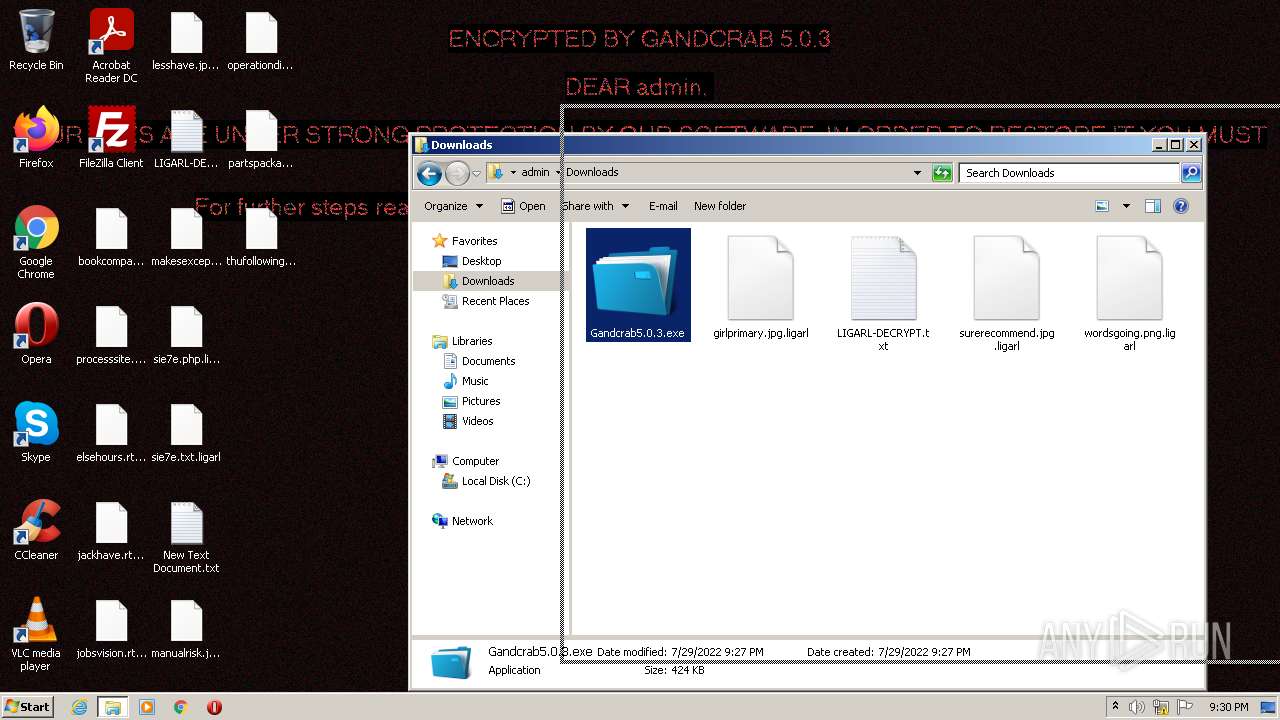
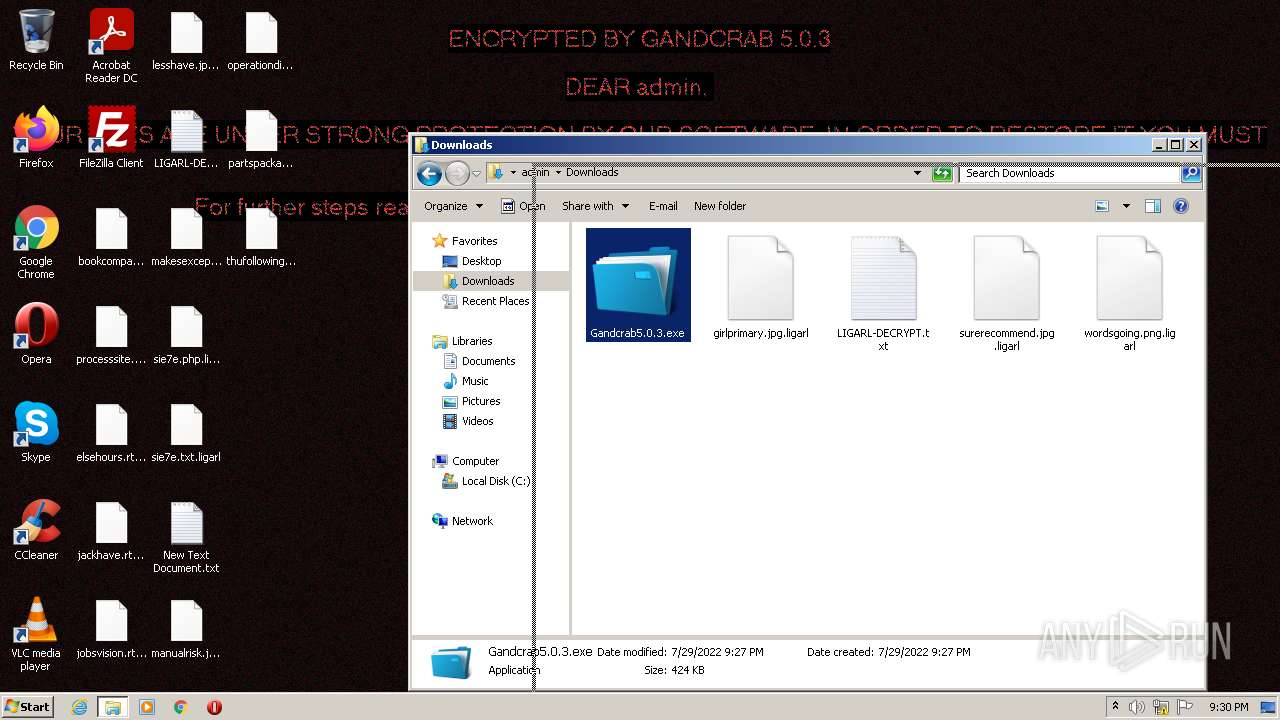
| 1016 | "C:\Users\admin\Downloads\Gandcrab5.0.3.exe" | C:\Users\admin\Downloads\Gandcrab5.0.3.exe | — | Explorer.EXE | |||||||||||
User: admin Company: www.sopcast.com Integrity Level: MEDIUM Description: SopCast Main Application Exit code: 0 Version: 4.2.0.800 Modules
| |||||||||||||||
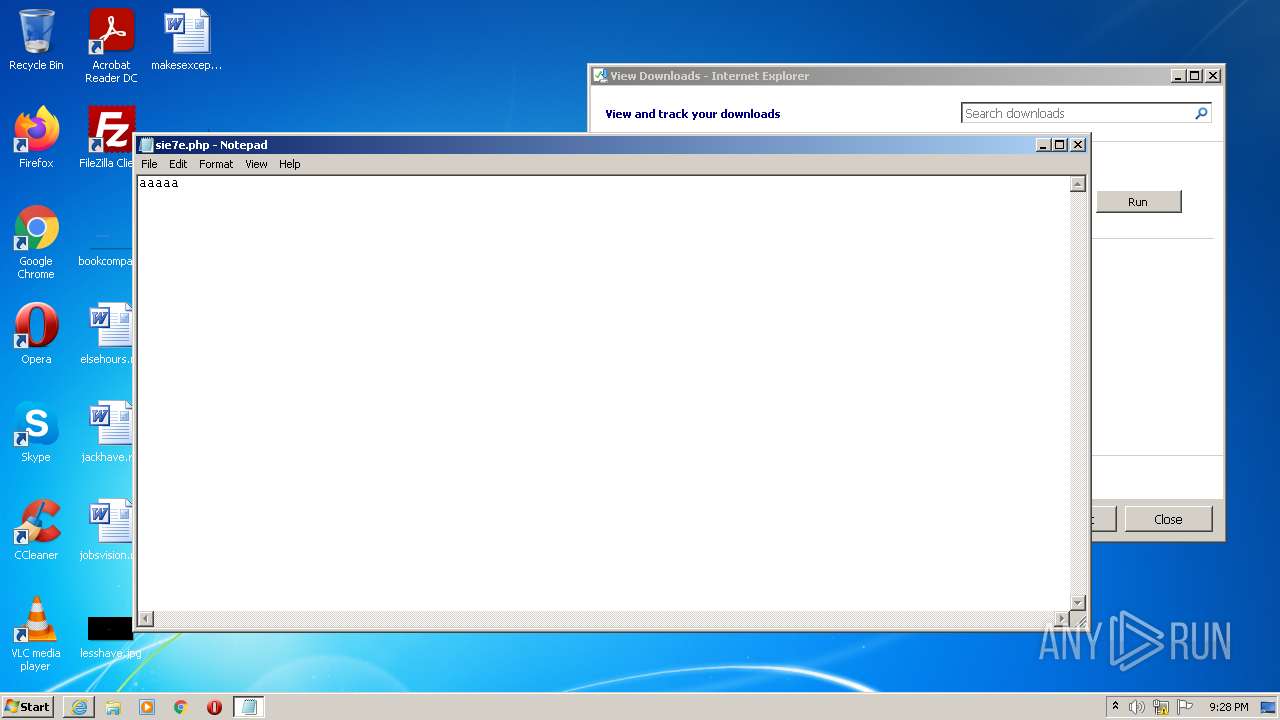
| 1068 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Downloads\LIGARL-DECRYPT.txt | C:\Windows\system32\NOTEPAD.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
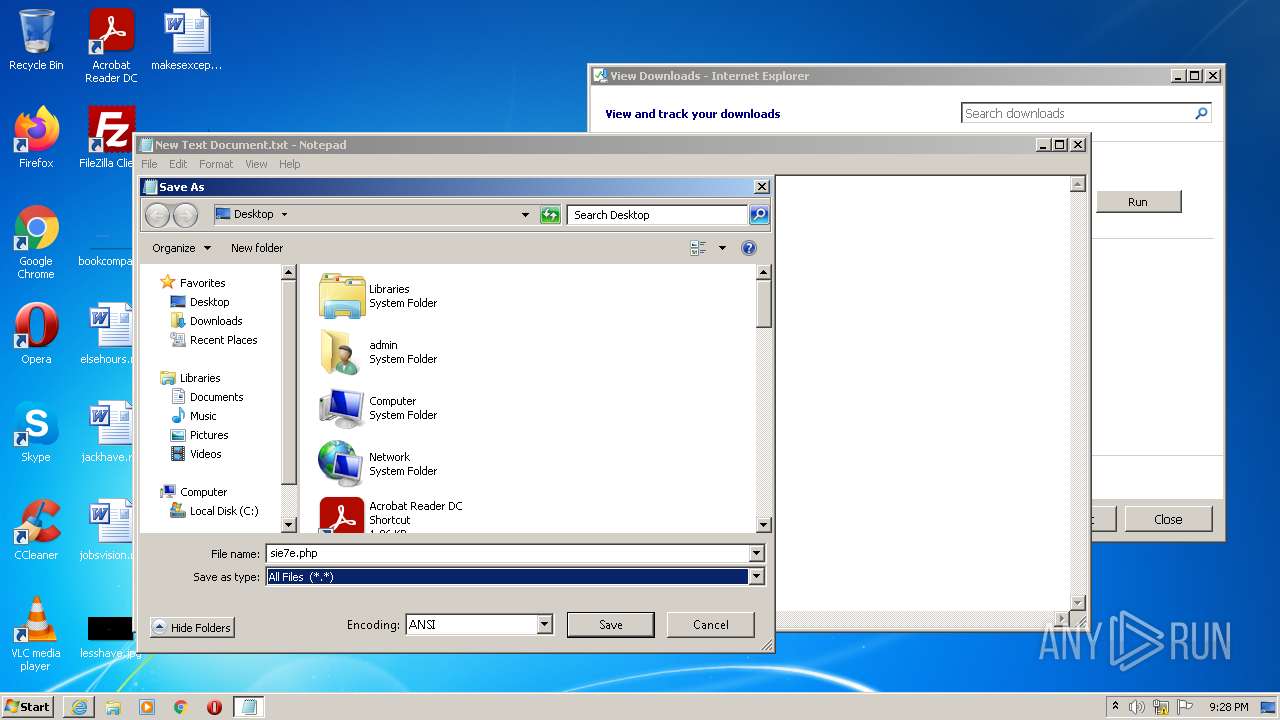
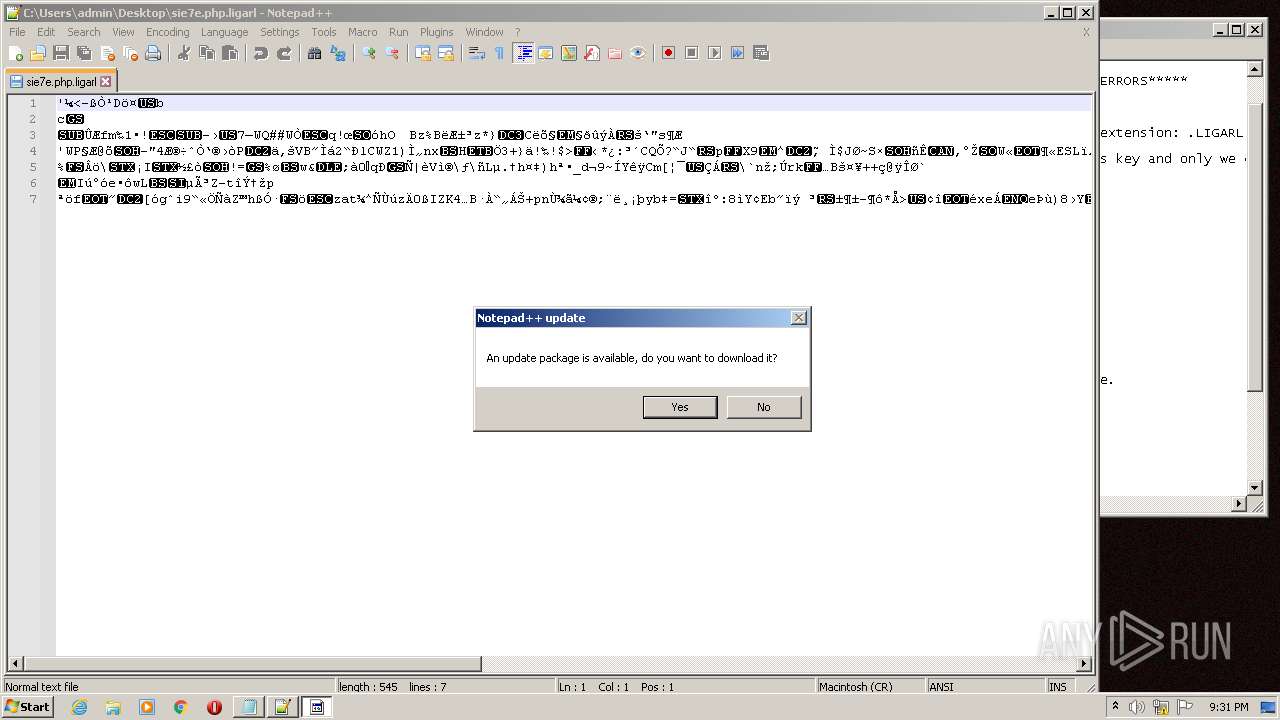
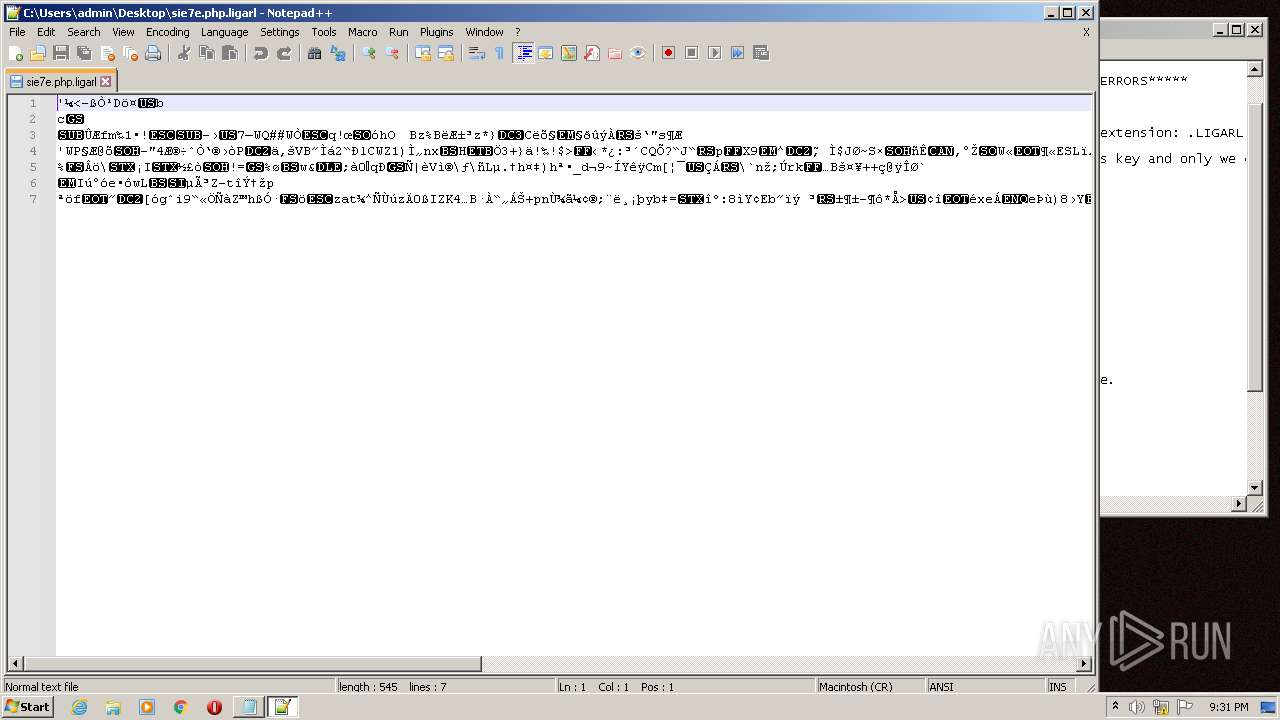
| 1388 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\Desktop\sie7e.php.ligarl" | C:\Program Files\Notepad++\notepad++.exe | Explorer.EXE | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.91 Modules
| |||||||||||||||
| 2556 | "C:\Windows\System32\wermgr.exe" | C:\Windows\System32\wermgr.exe | Gandcrab5.0.3.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7601.24521 (win7sp1_ldr_escrow.190909-1704) Modules
| |||||||||||||||
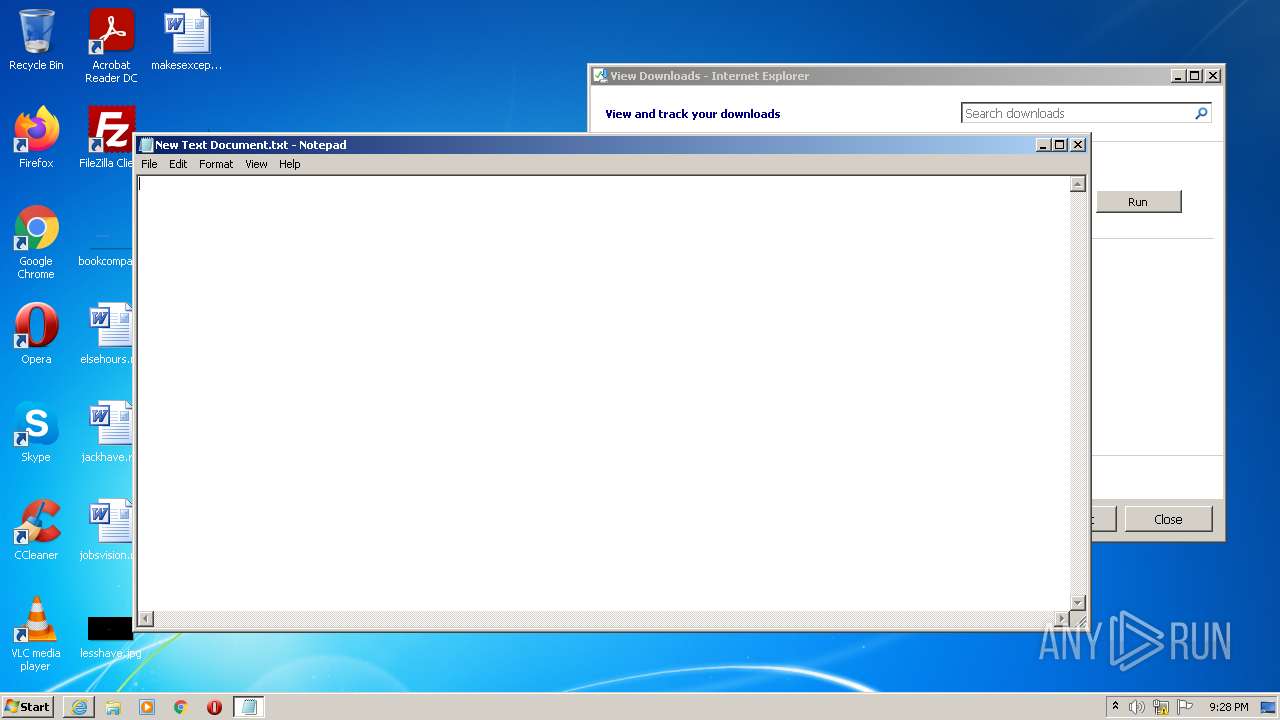
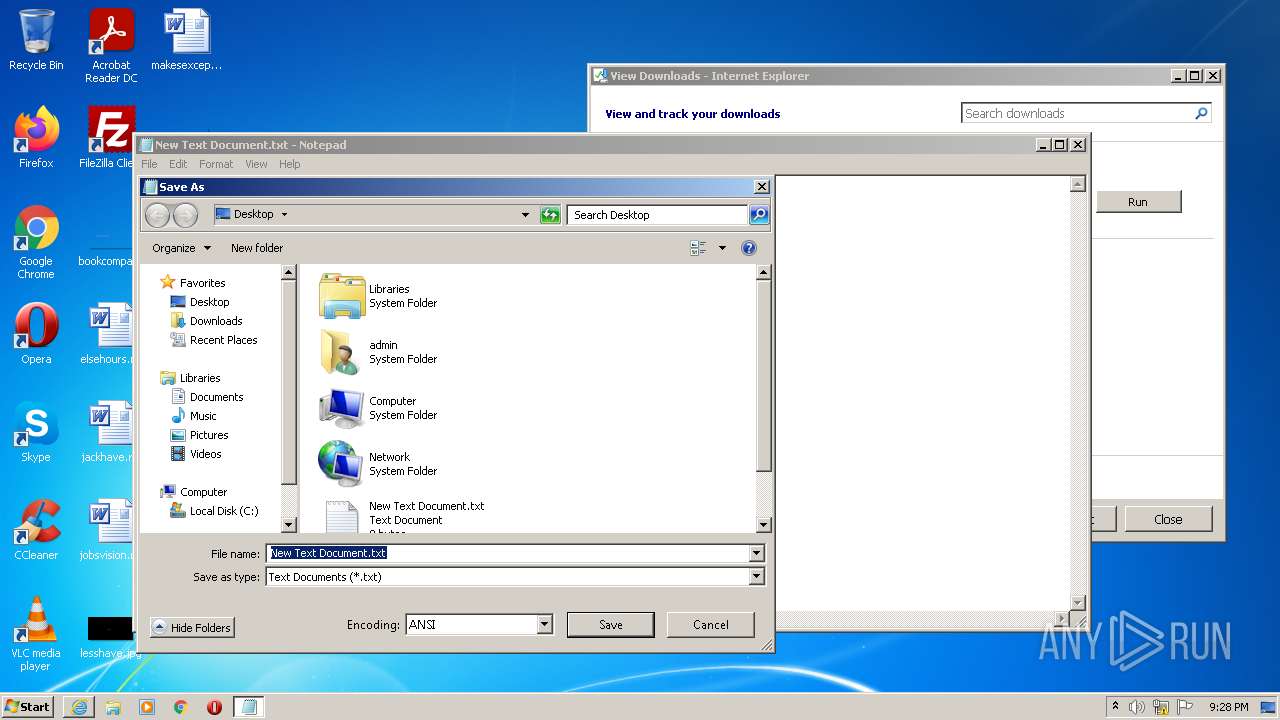
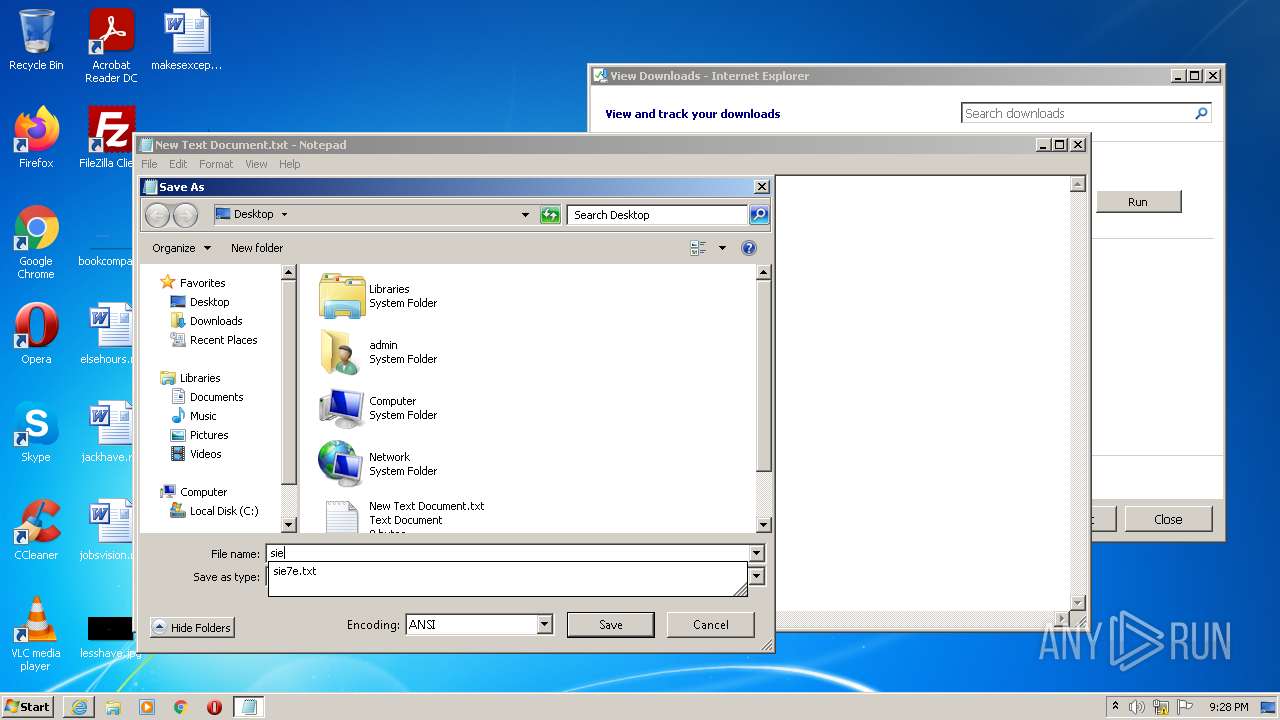
| 2648 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\New Text Document.txt | C:\Windows\system32\NOTEPAD.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2876 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\a.txt | C:\Windows\system32\NOTEPAD.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2928 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://github.com/mstfknn/malware-sample-library/blob/master/GandCrab/Gandcrab5.0.3.exe?raw=true" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3192 | "C:\Program Files\Notepad++\updater\gup.exe" -v7.91 | C:\Program Files\Notepad++\updater\gup.exe | notepad++.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: WinGup for Notepad++ Exit code: 0 Version: 5.11 Modules
| |||||||||||||||
| 3376 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2928 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
36 458
Read events
36 238
Write events
214
Delete events
6
Modification events
| (PID) Process: | (2928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30974857 | |||
| (PID) Process: | (2928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30974857 | |||
| (PID) Process: | (2928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2928) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
2
Suspicious files
710
Text files
261
Unknown types
40
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3376 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\50CD3D75D026C82E2E718570BD6F44D0_60E83F2095C16CA099C94596E7B8AA5D | binary | |
MD5:— | SHA256:— | |||
| 3376 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_ADE4E4D3A3BCBCA5C39C54D362D88565 | der | |
MD5:— | SHA256:— | |||
| 3376 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\BL9ZN3SG.txt | text | |
MD5:— | SHA256:— | |||
| 3376 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3376 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | der | |
MD5:— | SHA256:— | |||
| 3376 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_ADE4E4D3A3BCBCA5C39C54D362D88565 | binary | |
MD5:— | SHA256:— | |||
| 2928 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\82CB34DD3343FE727DF8890D352E0D8F | der | |
MD5:— | SHA256:— | |||
| 3376 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\Gandcrab5.0.3[1].exe | executable | |
MD5:— | SHA256:— | |||
| 3376 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\50CD3D75D026C82E2E718570BD6F44D0_60E83F2095C16CA099C94596E7B8AA5D | der | |
MD5:— | SHA256:— | |||
| 2928 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\82CB34DD3343FE727DF8890D352E0D8F | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
58
DNS requests
39
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2928 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3376 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQrHR6YzPN2BNbByL0VoiTIBBMAOAQUCrwIKReMpTlteg7OM8cus%2B37w3oCEAUYmlTr6MfpA%2BCrDZJVRd4%3D | US | der | 314 b | whitelisted |
2928 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 7.78 Kb | whitelisted |
2556 | wermgr.exe | GET | 200 | 184.24.77.48:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgM9n2vFBEl1fiY3ETZCgeewWw%3D%3D | US | der | 503 b | shared |
2928 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEALnkXH7gCHpP%2BLZg4NMUMA%3D | US | der | 471 b | whitelisted |
2556 | wermgr.exe | GET | 200 | 23.216.77.80:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?f8cd6be2d75c4198 | US | compressed | 60.2 Kb | whitelisted |
3376 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAfy81yHqHeveu%2FpR5k1Jb0%3D | US | der | 471 b | whitelisted |
2556 | wermgr.exe | GET | 200 | 104.18.32.68:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 1.42 Kb | whitelisted |
2556 | wermgr.exe | GET | 200 | 184.24.77.48:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgPX7KW3SfYCXOea4etqk3CdRg%3D%3D | US | der | 503 b | shared |
2556 | wermgr.exe | GET | 200 | 199.59.243.220:80 | http://survey-smiles.com/ | US | html | 1.13 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2928 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2928 | iexplore.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2928 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2928 | iexplore.exe | 96.16.143.41:443 | go.microsoft.com | Akamai International B.V. | US | whitelisted |
2928 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2928 | iexplore.exe | 204.79.197.203:443 | www.msn.com | Microsoft Corporation | US | malicious |
2928 | iexplore.exe | 20.25.53.147:443 | query.prod.cms.msn.com | — | US | unknown |
2556 | wermgr.exe | 77.75.249.22:443 | www.2mmotorsport.biz | Profihost AG | DE | malicious |
2556 | wermgr.exe | 96.16.145.230:80 | x1.c.lencr.org | Akamai Technologies, Inc. | US | suspicious |
2556 | wermgr.exe | 23.216.77.80:80 | ctldl.windowsupdate.com | NTT DOCOMO, INC. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
github.com |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
raw.githubusercontent.com |
| shared |
crl3.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
2556 | wermgr.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\plugins\Config\nppPluginList.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|