| URL: | https://app.any.run/ |
| Full analysis: | https://app.any.run/tasks/26bf8acd-c235-4694-a425-95285d4e4bd4 |
| Verdict: | Malicious activity |
| Analysis date: | October 22, 2020, 00:13:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 6C7580006806F7AB3BB5DFBEA939832B |
| SHA1: | 28B2EAA53D605AB443B1C4D38F0C3C65B0BB6601 |
| SHA256: | AD215FF223B3482E041F5BF0E6CEB73A2E7B0B15FAEB5B274F3AEEC2F4009341 |
| SSDEEP: | 3:N8a3XQ+:2aQ+ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2636)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 1948)
- iexplore.exe (PID: 1764)
- iexplore.exe (PID: 2896)
- iexplore.exe (PID: 1576)
Changes internet zones settings
- iexplore.exe (PID: 1948)
Reads settings of System Certificates
- iexplore.exe (PID: 1764)
- iexplore.exe (PID: 1948)
- iexplore.exe (PID: 1576)
- iexplore.exe (PID: 2896)
Application launched itself
- iexplore.exe (PID: 1948)
Reads internet explorer settings
- iexplore.exe (PID: 1764)
- iexplore.exe (PID: 2896)
- iexplore.exe (PID: 1576)
Creates files in the user directory
- iexplore.exe (PID: 1948)
- iexplore.exe (PID: 1764)
- iexplore.exe (PID: 2896)
- iexplore.exe (PID: 1576)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2636)
Changes settings of System certificates
- iexplore.exe (PID: 1948)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1948)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
41
Monitored processes
5
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1576 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1948 CREDAT:2168090 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1764 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1948 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1948 | "C:\Program Files\Internet Explorer\iexplore.exe" https://app.any.run/ | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2636 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
| 2896 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1948 CREDAT:2626912 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
2 216
Read events
1 878
Write events
332
Delete events
6
Modification events
| (PID) Process: | (1948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 1396753194 | |||
| (PID) Process: | (1948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30844936 | |||
| (PID) Process: | (1948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1948) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
316
Text files
545
Unknown types
185
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1764 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab4965.tmp | — | |
MD5:— | SHA256:— | |||
| 1764 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar4966.tmp | — | |
MD5:— | SHA256:— | |||
| 1948 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1764 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\c9468e3f00f96c3e597d07c94f67d2cc291bdc52[1].js | — | |
MD5:— | SHA256:— | |||
| 1764 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\9FF67FB3141440EED32363089565AE60_1F35A3B8DEE8E939204AB0B9B1169054 | der | |
MD5:958265ED9B935E02E9085C304D12ABDC | SHA256:EE293ADD6D1D982FCA23BDDF22E5C65FEE3F74C02E9FBBEEA8838CBEF3927820 | |||
| 1764 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\N06YQZ14.txt | text | |
MD5:8B463A2367E4BB423D65A567DD650141 | SHA256:01165A42AAFFAB2C64D60884A2DE5979D283724932BB19BA5A60F2A32AE46A4F | |||
| 1764 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\9FF67FB3141440EED32363089565AE60_1F35A3B8DEE8E939204AB0B9B1169054 | binary | |
MD5:B4D34BB98401BE92CD41E736F320F7D0 | SHA256:D66CDED0AA8D0C122E1DFDBA3EE4BF65B7A14D5D144D8A874BCB90567AA3D5B9 | |||
| 1764 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:13EAE655F4CE60F9188121453D589B4B | SHA256:5654F6A97F92D5EF4D5D27258F5901D8F2C8B836D34A5B6CACE7F03C8244E2E7 | |||
| 1764 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CFE86DBBE02D859DC92F1E17E0574EE8_46766FC45507C0B9E264E4C18BC7288B | binary | |
MD5:8493D78B66A5ED935FC65B9BEDC69350 | SHA256:127AFEA5652C3A5291A369937CA48EE1E2EFD67AEBBD163EFB026FD58707DAE9 | |||
| 1764 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:E0418AB5B6C1F5B1C752C97781F138D8 | SHA256:8C7B103D007BF649BDD3A22B66D7BC301EDD6C3CA9B2703FA9F3AC7868FC487C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
512
TCP/UDP connections
324
DNS requests
69
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1764 | iexplore.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
1764 | iexplore.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDopzvCvNaHRggAAAAAXcGw | US | der | 472 b | whitelisted |
1764 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
1948 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
1764 | iexplore.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCECiWpPQxRDpPAgAAAAB8NWE%3D | US | der | 471 b | whitelisted |
1764 | iexplore.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCOUTy4wn8XWggAAAAAWy8I | US | der | 472 b | whitelisted |
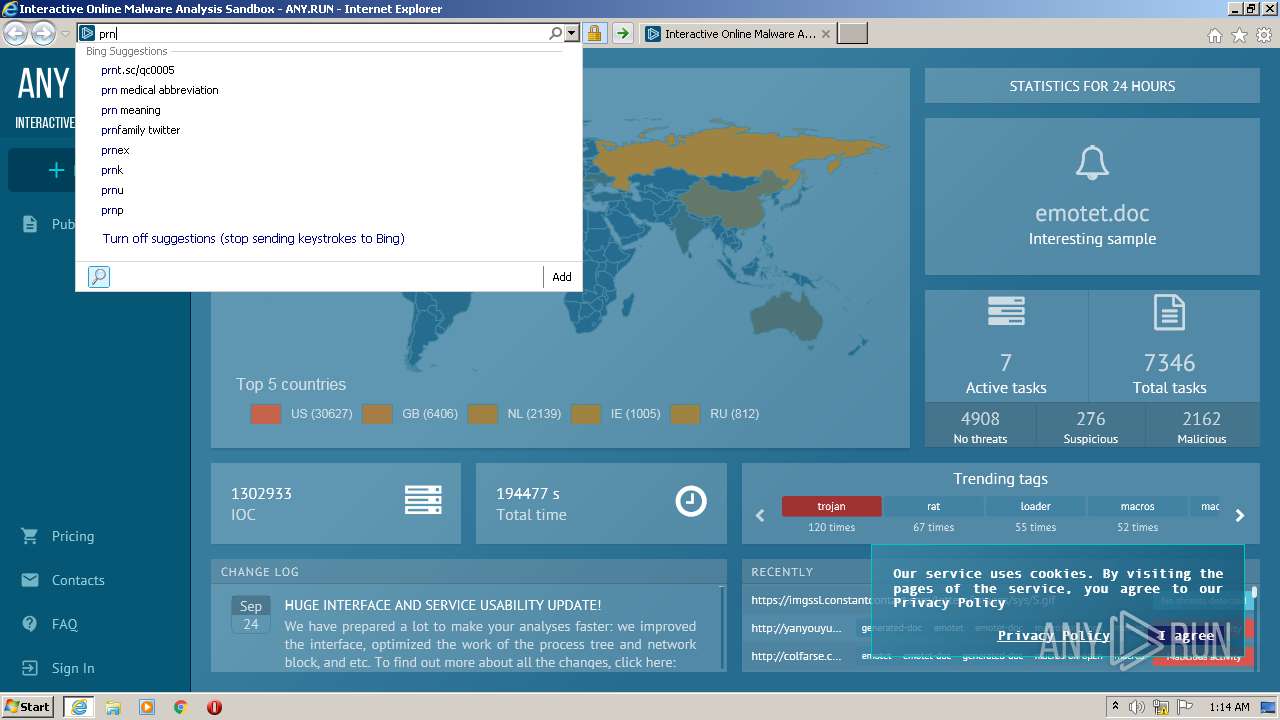
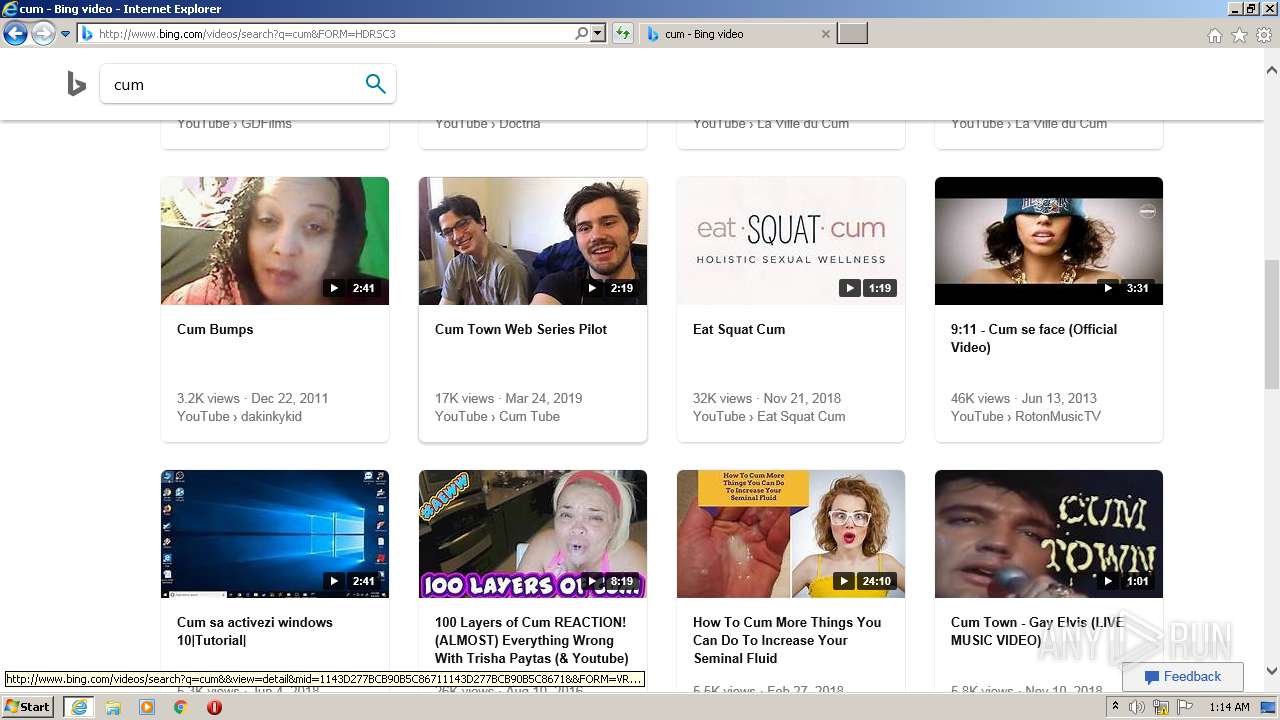
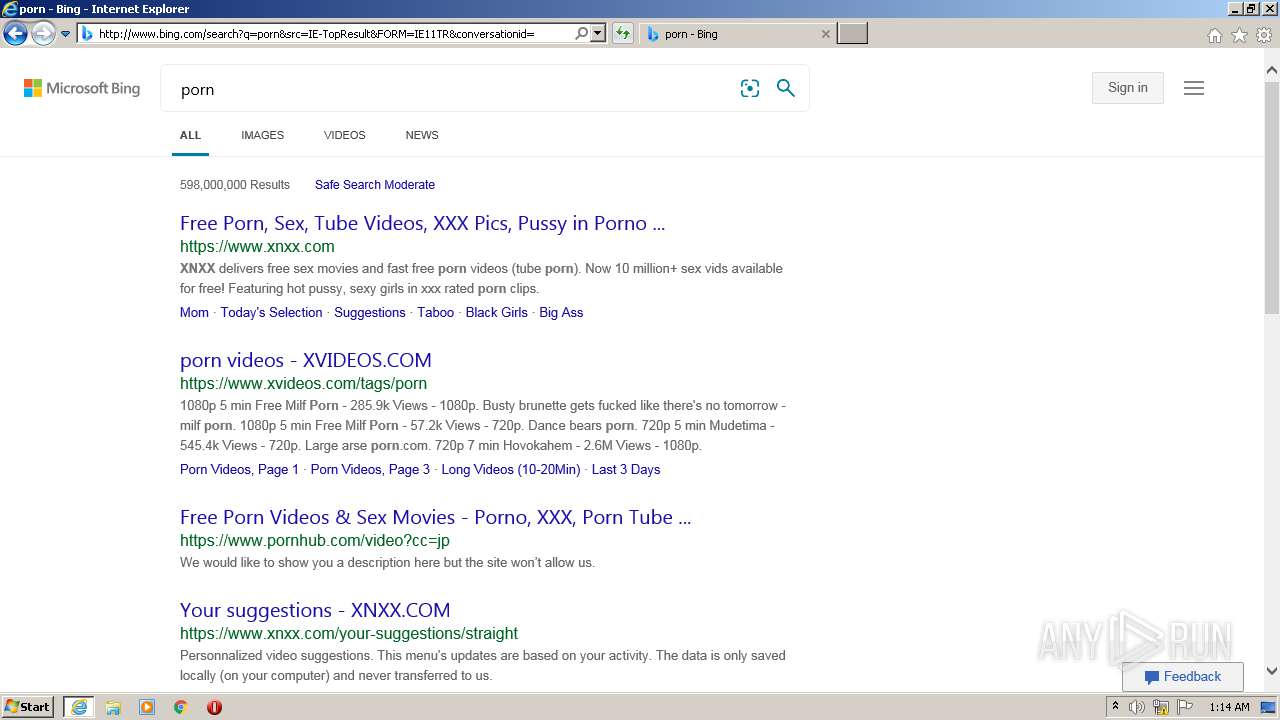
1764 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=p&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 238 b | whitelisted |
1764 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=pr&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 249 b | whitelisted |
1764 | iexplore.exe | GET | 200 | 13.107.5.80:80 | http://api.bing.com/qsml.aspx?query=prn&maxwidth=32765&rowheight=20§ionHeight=160&FORM=IE11SS&market=en-US | US | xml | 242 b | whitelisted |
1764 | iexplore.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCYiHlVi1YSqAgAAAAAWy82 | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1764 | iexplore.exe | 216.58.208.42:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1764 | iexplore.exe | 172.217.18.99:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
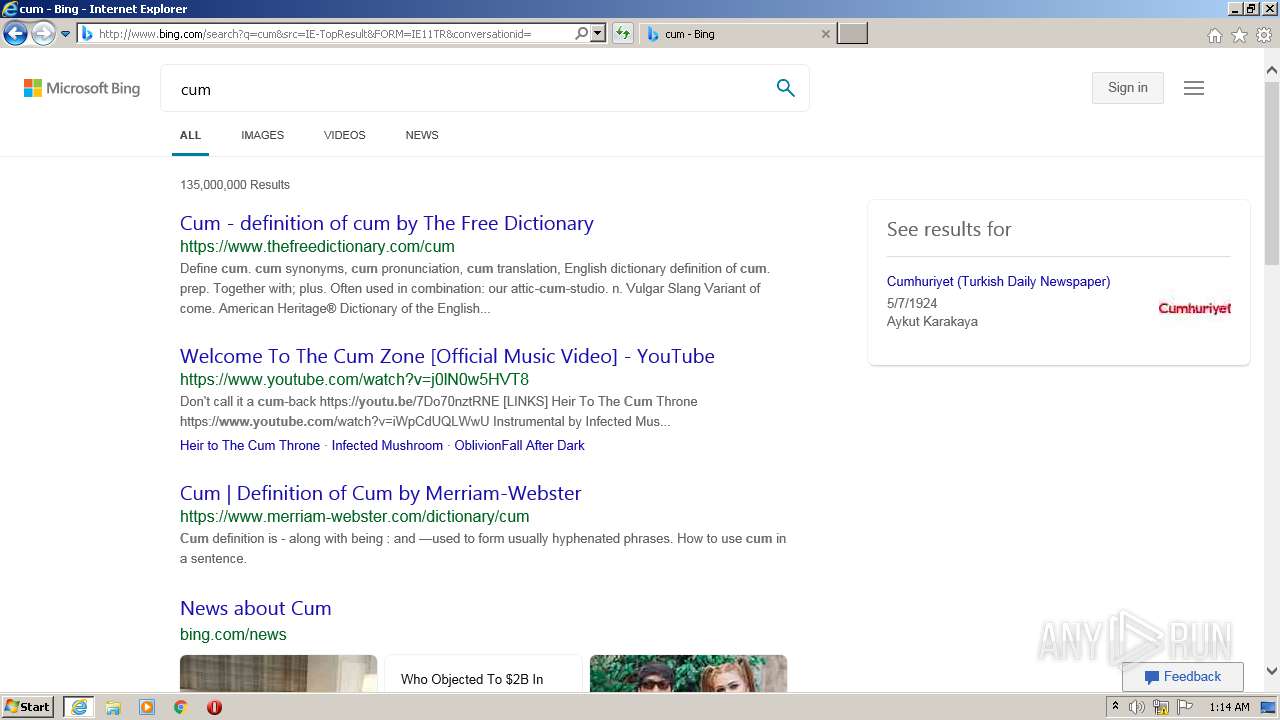
1948 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1764 | iexplore.exe | 216.58.210.8:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
1764 | iexplore.exe | 172.217.21.196:443 | www.google.com | Google Inc. | US | whitelisted |
1764 | iexplore.exe | 216.58.212.131:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1764 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1764 | iexplore.exe | 104.22.49.74:443 | app.any.run | Cloudflare Inc | US | malicious |
1764 | iexplore.exe | 172.217.22.14:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
1764 | iexplore.exe | 64.233.167.156:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
app.any.run |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
www.google.com |
| malicious |
www.gstatic.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1060 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1060 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1764 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY Outdated Flash Version M1 |
1764 | iexplore.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
2896 | iexplore.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
1576 | iexplore.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
1576 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY Observed iesnare/iovation Tracking Activity |
1576 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY Observed iesnare/iovation Tracking Activity |
2896 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY Observed iesnare/iovation Tracking Activity |
2896 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY Observed iesnare/iovation Tracking Activity |