| File name: | AntiTest.exe |
| Full analysis: | https://app.any.run/tasks/a2d2da61-d694-4893-bb93-8b3db224afdd |
| Verdict: | Suspicious activity |
| Analysis date: | July 03, 2020, 09:51:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 02344AB1EDCEA91C773CA5D8B2D80F4F |
| SHA1: | 119BD795D192B1F58A6DD5B1AC9B674587CF68BC |
| SHA256: | AD1FDBC1ED95EB6887C7F2993EF7DAC91009510F00A2C712DFF885632366F533 |
| SSDEEP: | 49152:RemH5RXjsSsvIS3fMRu2QN/HS0jsAP5uQtCG4QlOAB8lt5Wk7TzTFq3g5ePfNI:RzZuAQNa0jtP1wRuB8RWCrePf |
MALICIOUS
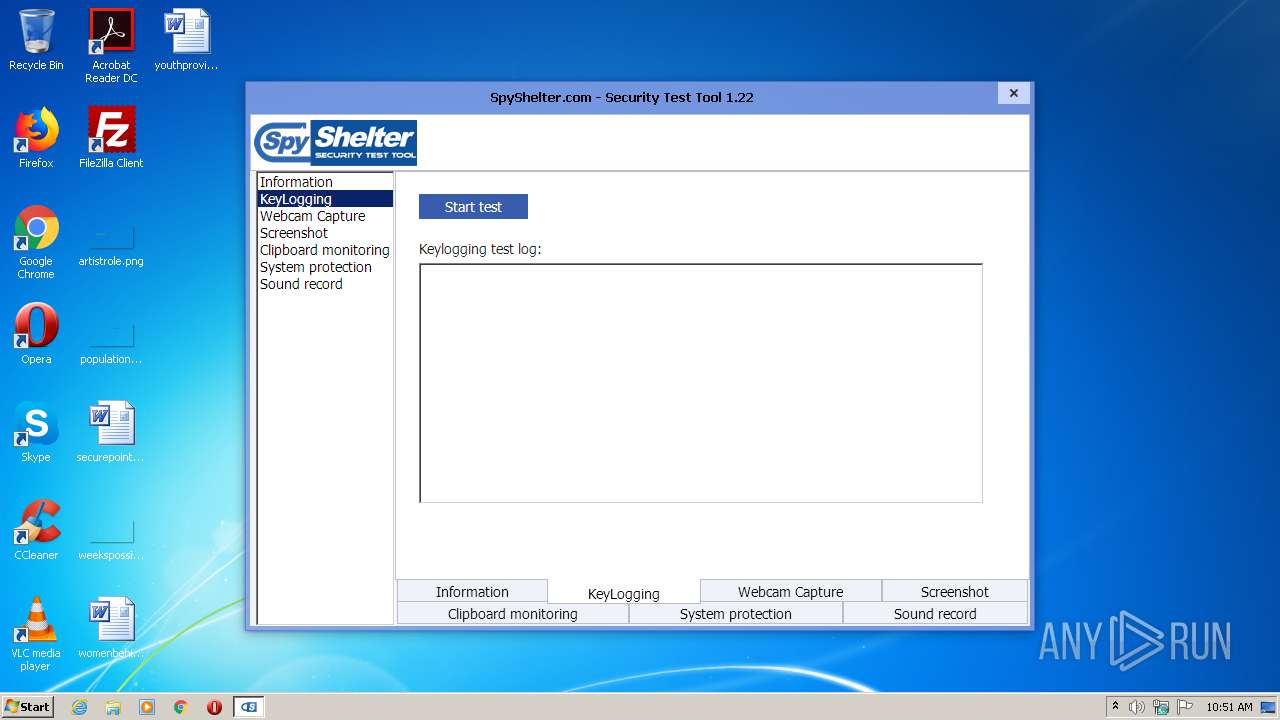
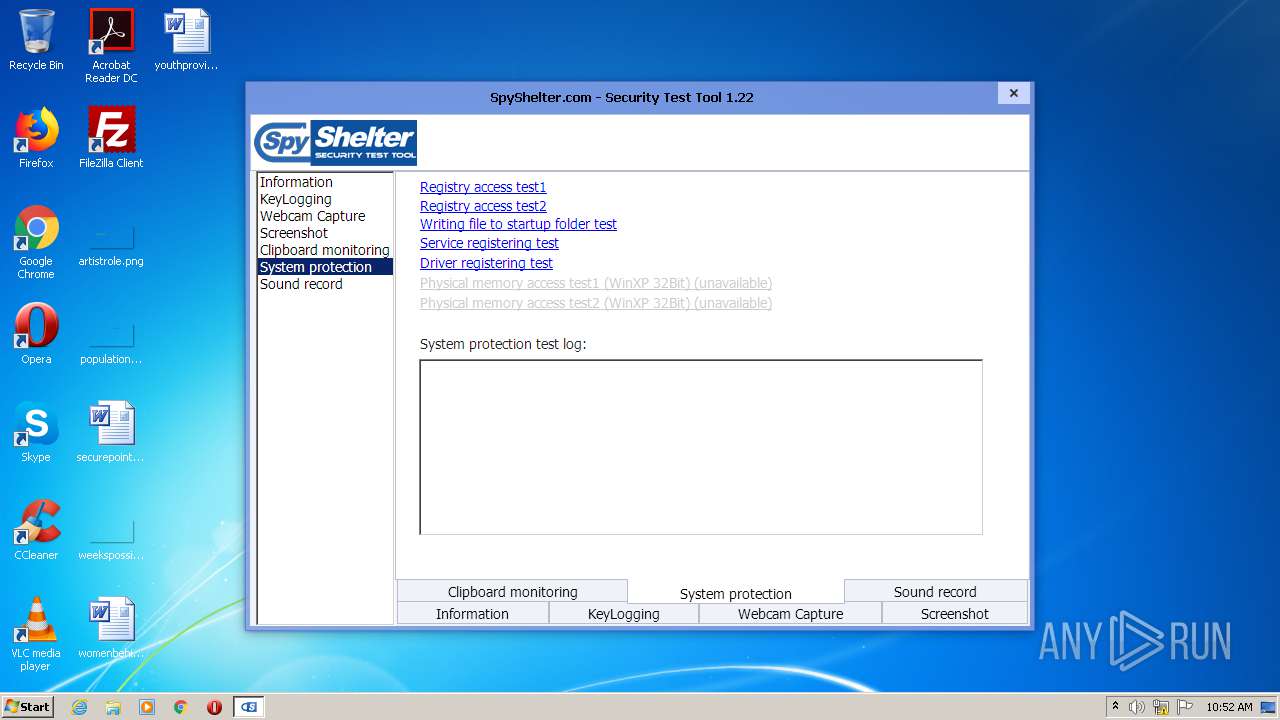
Changes the autorun value in the registry
- AntiTest.exe (PID: 2748)
SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 EXE PECompact compressed (generic) (79.7) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (8.6) |
| .exe | | | Win16/32 Executable Delphi generic (3.9) |
| .exe | | | Generic Win/DOS Executable (3.8) |
| .exe | | | DOS Executable Generic (3.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:04:06 16:58:18+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 4136960 |
| InitializedDataSize: | 1118720 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3f3030 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.2.1.0 |
| ProductVersionNumber: | 1.2.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Datpol |
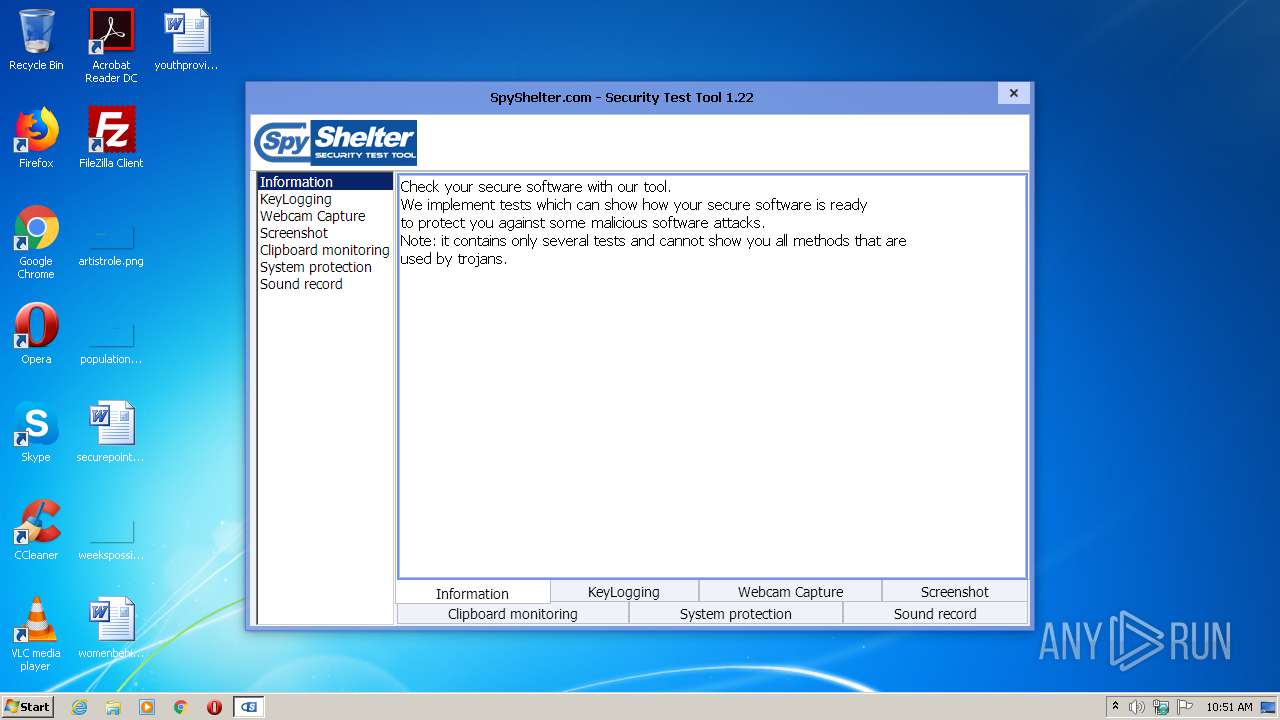
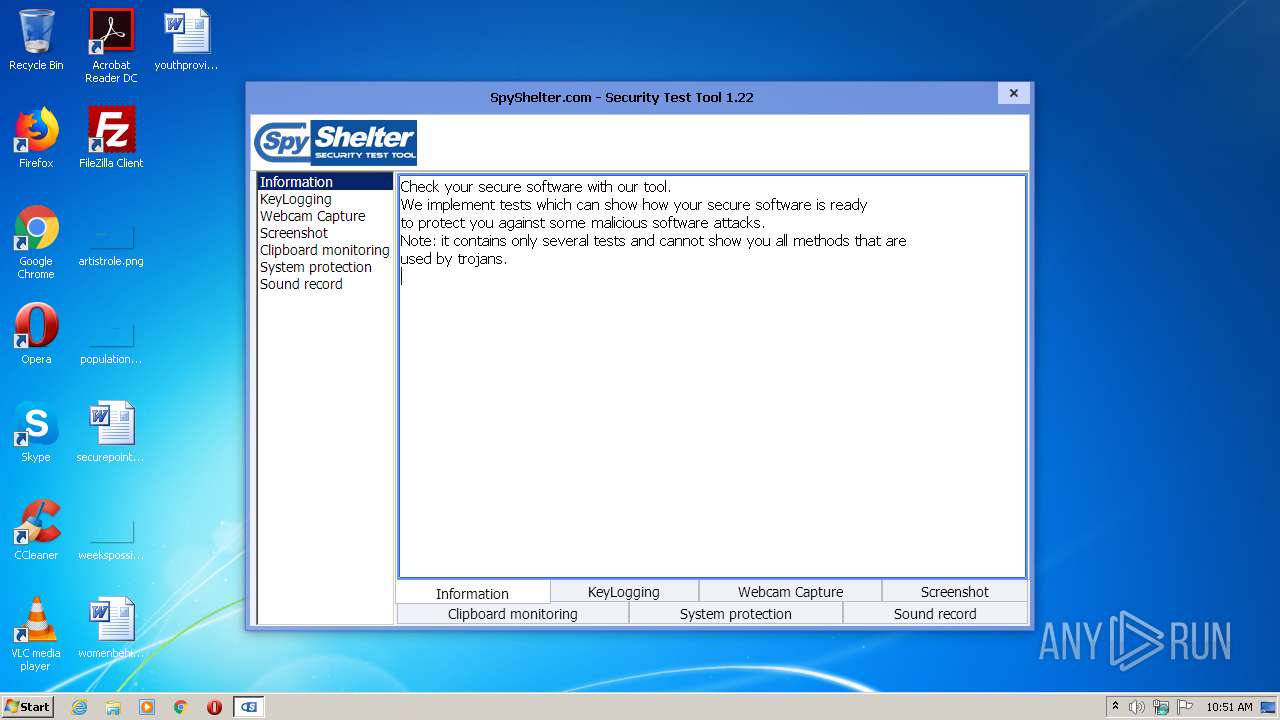
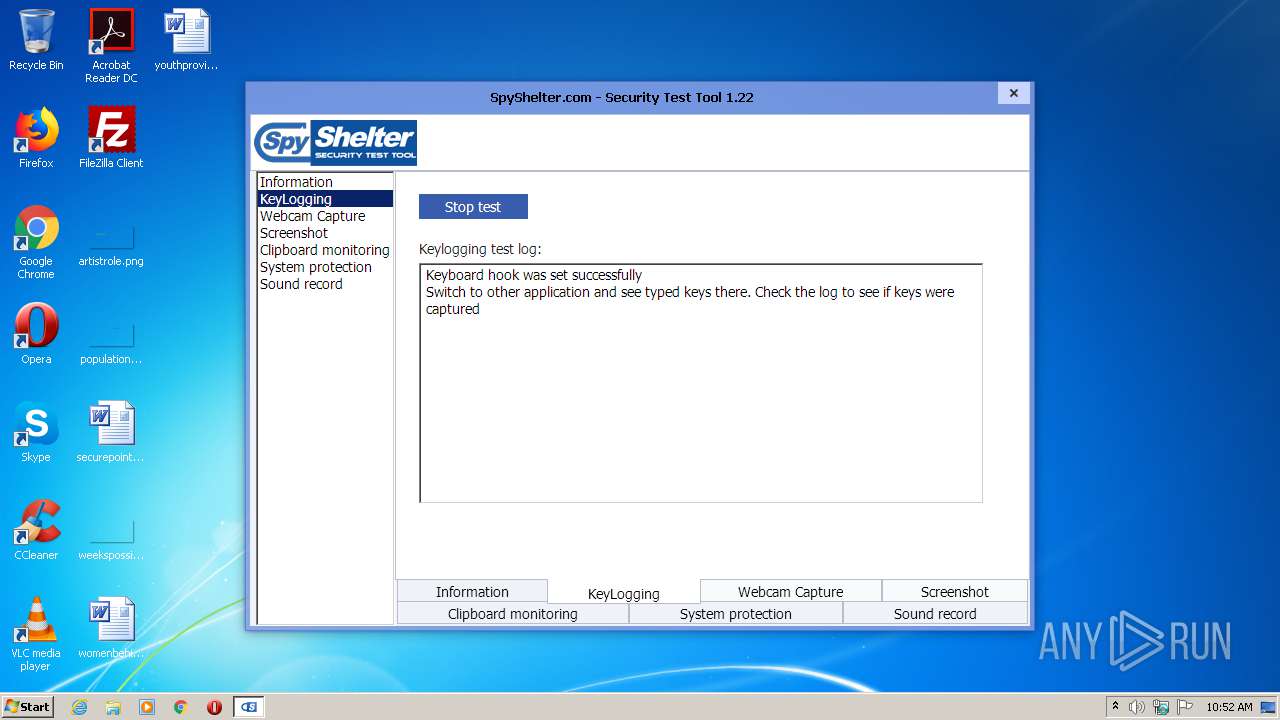
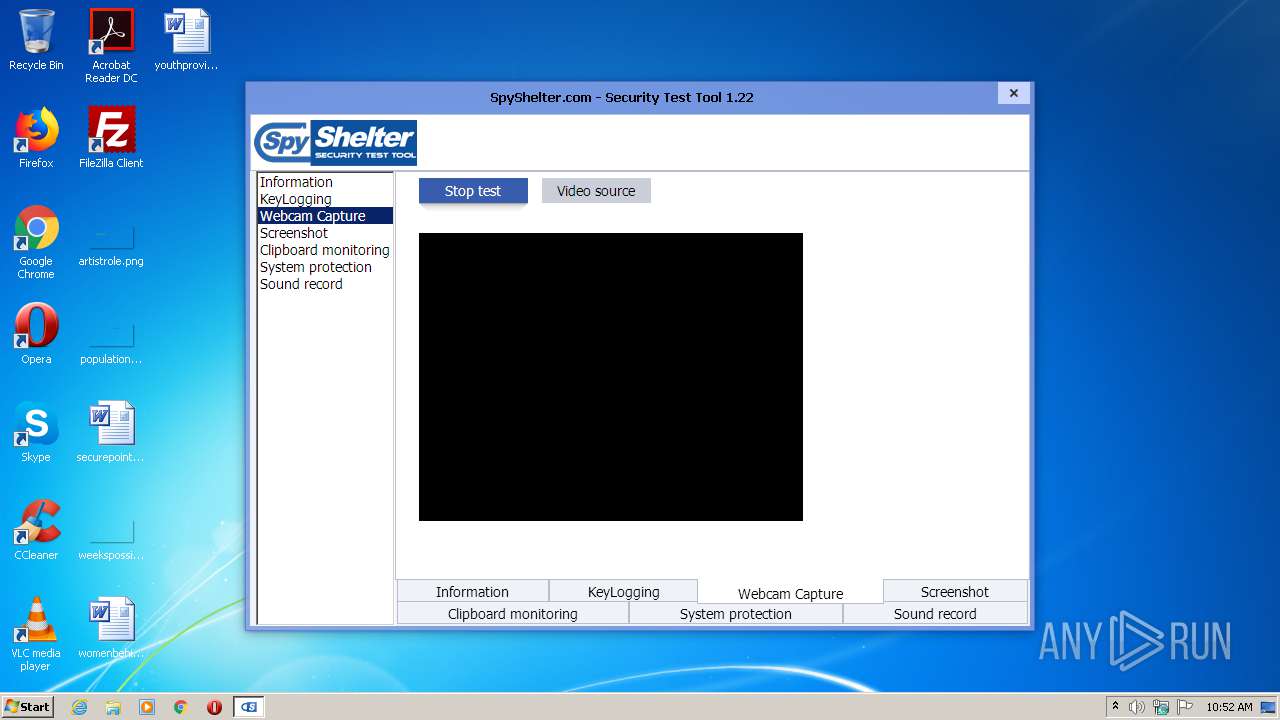
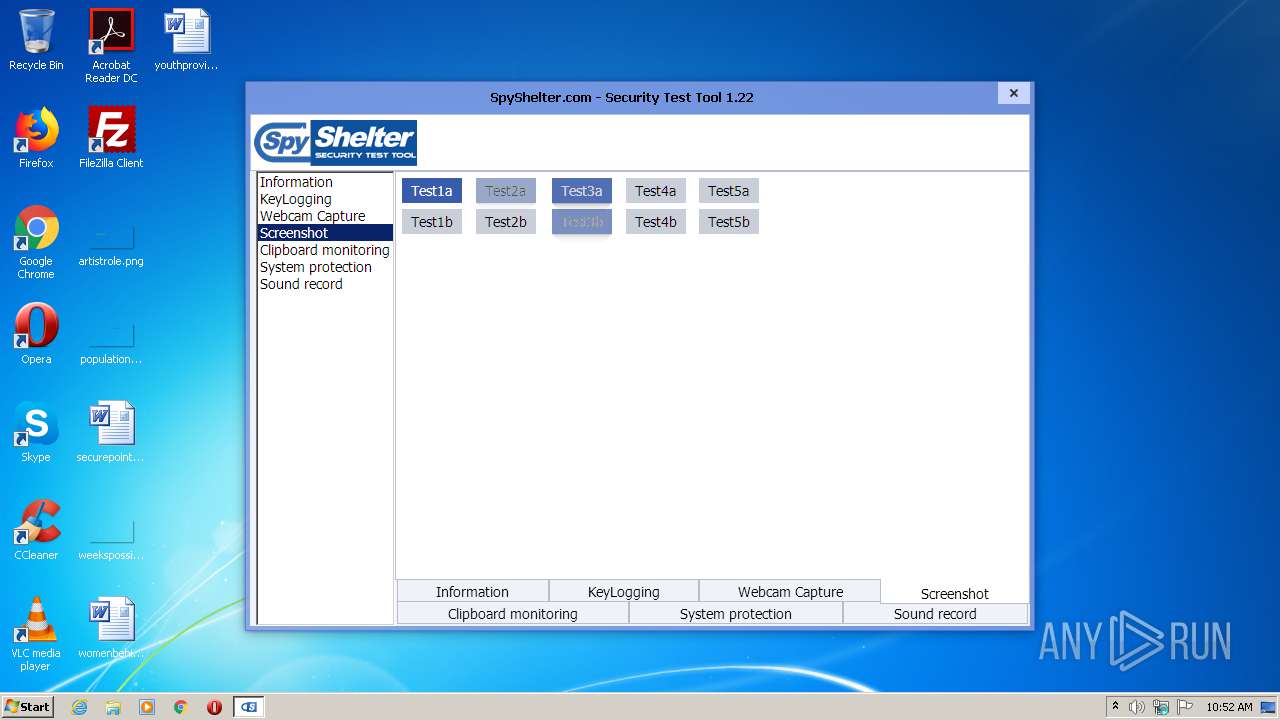
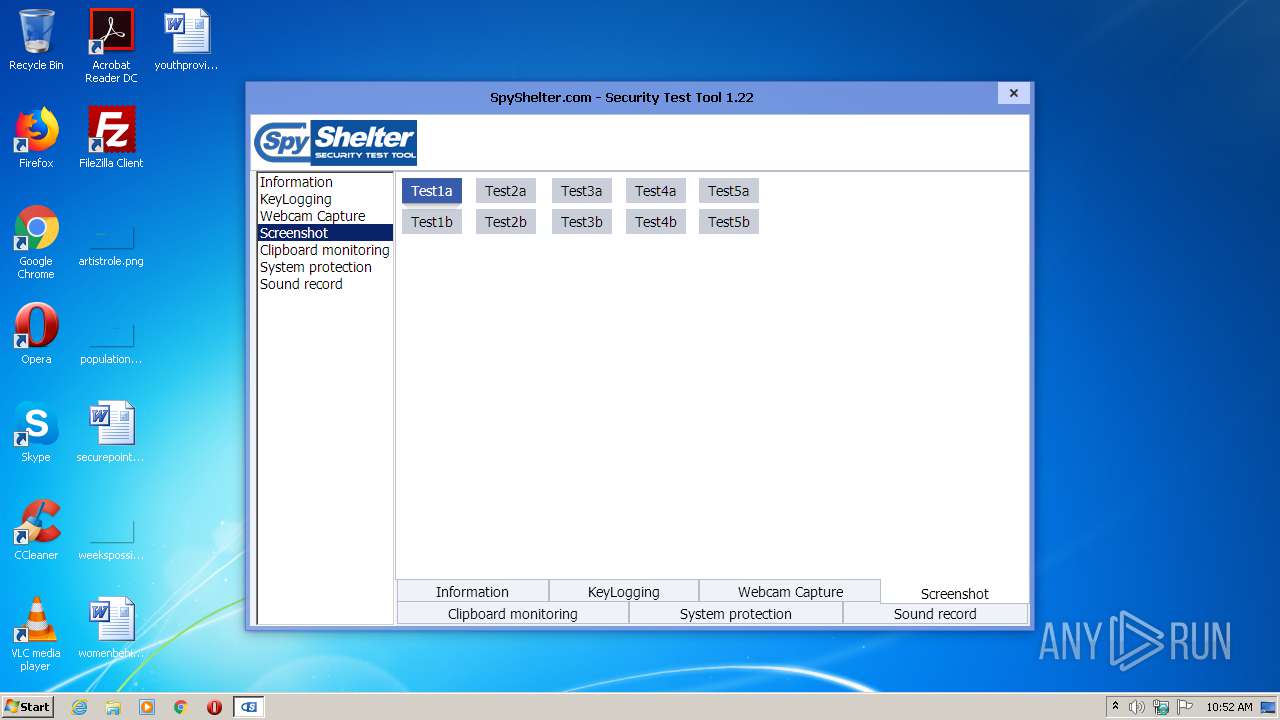
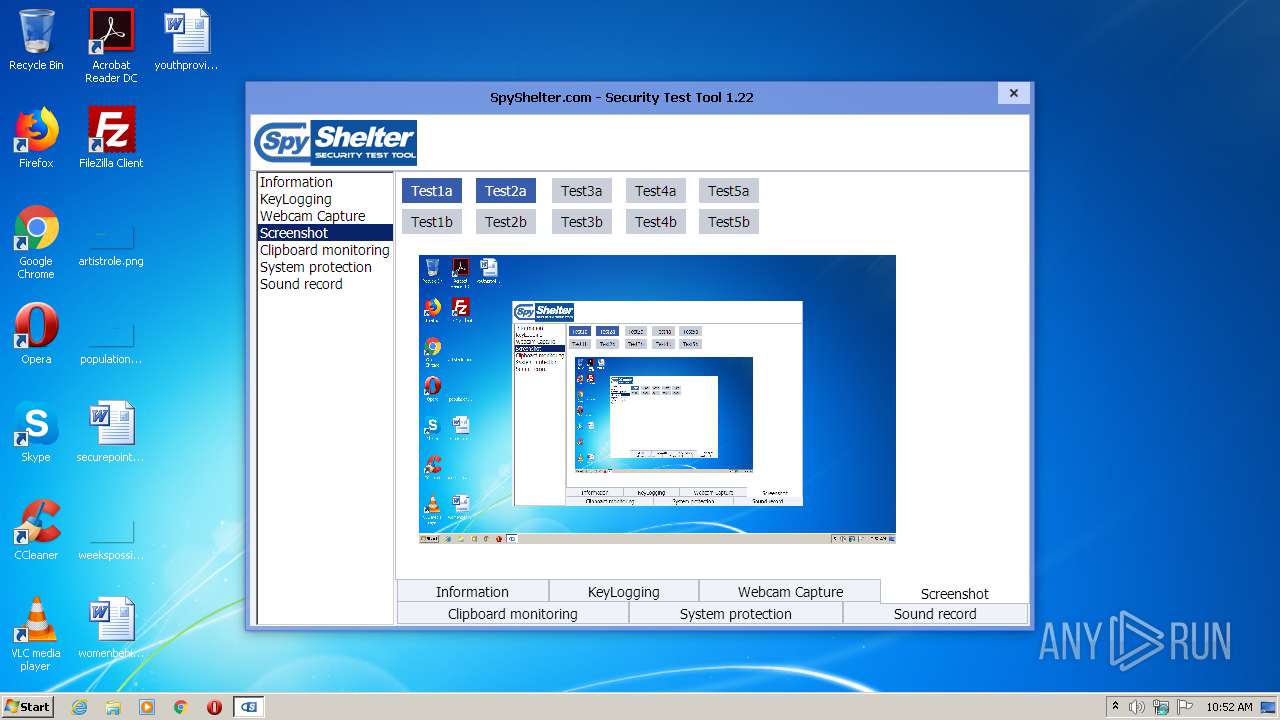
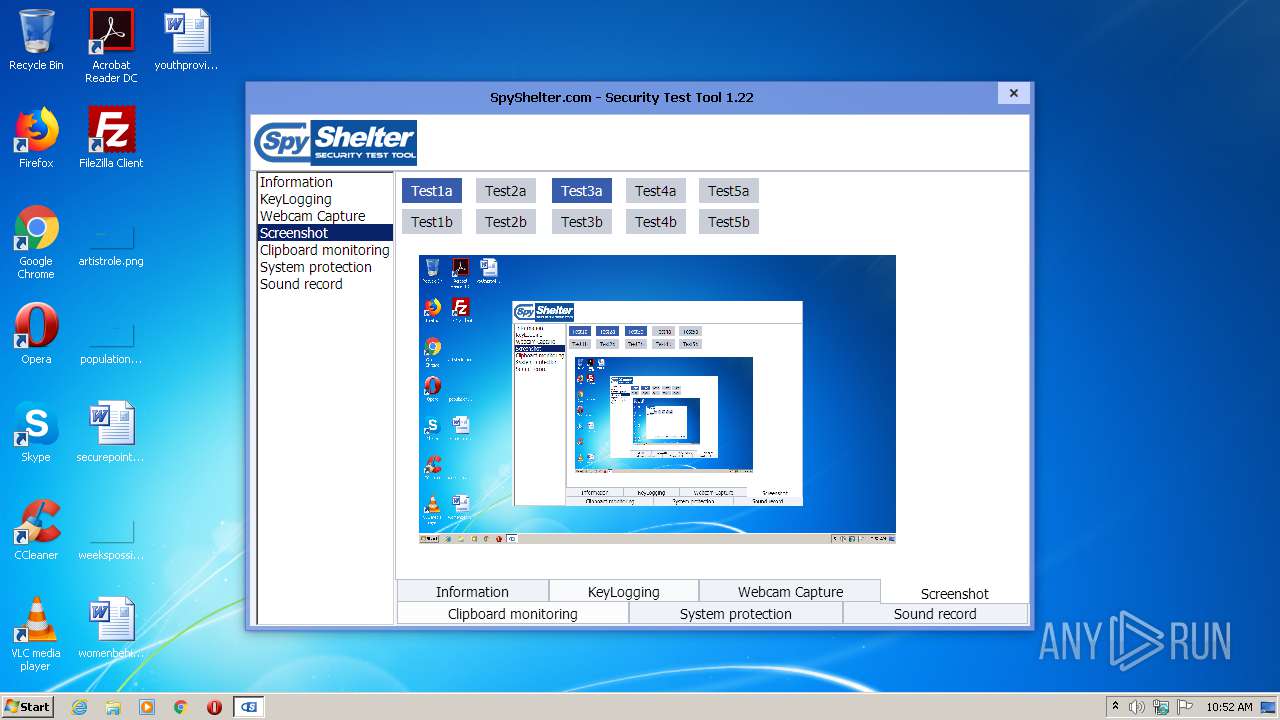
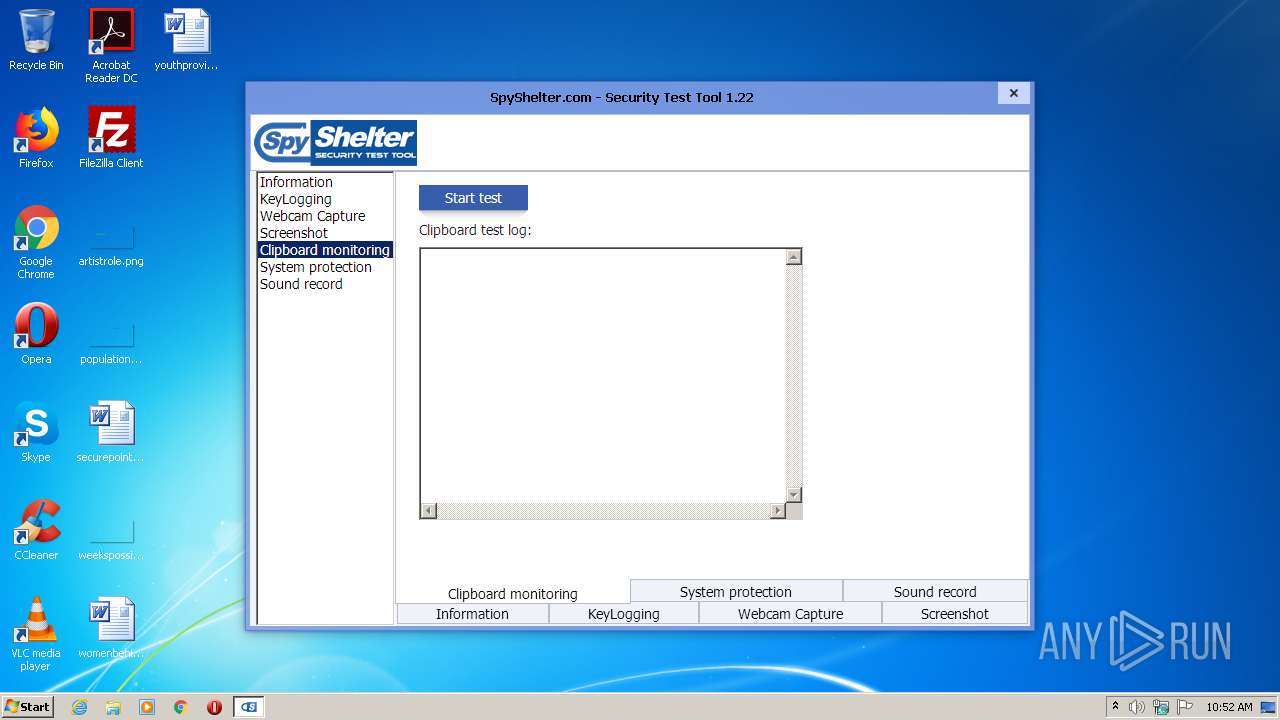
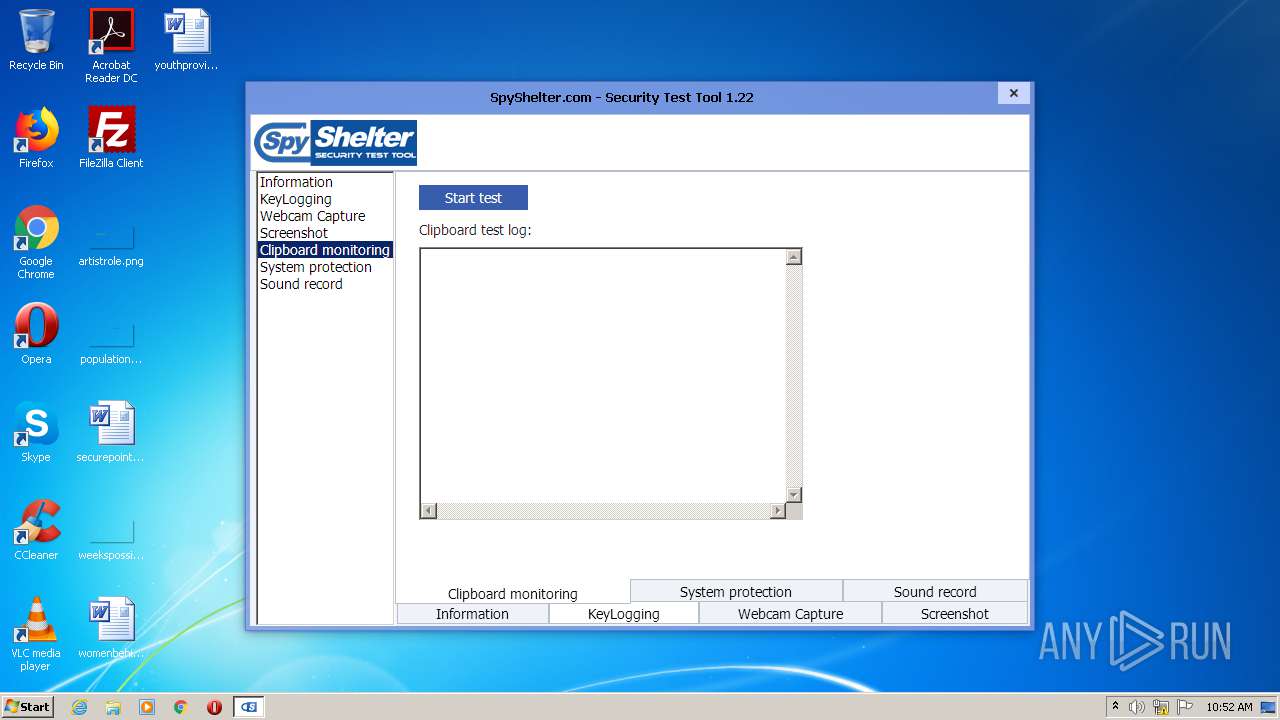
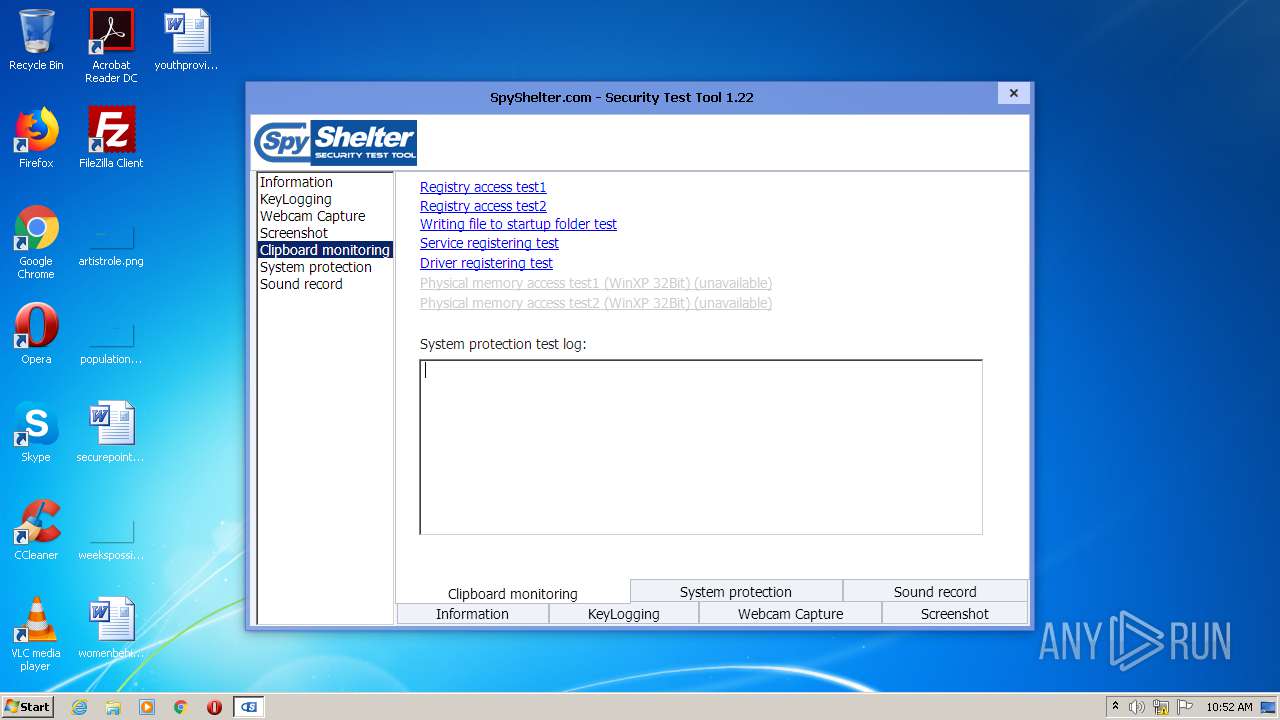
| FileDescription: | SpySheter Security Test Tool |
| FileVersion: | 1.2.1.0 |
| InternalName: | SpySheter Security Test Tool |
| LegalCopyright: | Datpol |
| OriginalFileName: | AntiTest.exe |
| ProductName: | SpyShelter Security Test Tool |
| ProductVersion: | 1.2.0.0 |
| ProgramID: | com.embarcadero.KAntiTest |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Apr-2020 14:58:18 |
| Detected languages: |
|
| CompanyName: | Datpol |
| FileDescription: | SpySheter Security Test Tool |
| FileVersion: | 1.2.1.0 |
| InternalName: | SpySheter Security Test Tool |
| LegalCopyright: | Datpol |
| OriginalFilename: | AntiTest.exe |
| ProductName: | SpyShelter Security Test Tool |
| ProductVersion: | 1.2.0.0 |
| ProgramID: | com.embarcadero.KAntiTest |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 11 |
| Time date stamp: | 06-Apr-2020 14:58:18 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x003EDC3C | 0x003EDE00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.48859 |
.itext | 0x003EF000 | 0x000040CC | 0x00004200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.91374 |
.data | 0x003F4000 | 0x0001BC7C | 0x0001BE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.29114 |
.bss | 0x00410000 | 0x0001B17C | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0042C000 | 0x00003C96 | 0x00003E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.19445 |
.didata | 0x00430000 | 0x00000B5E | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.12294 |
.edata | 0x00431000 | 0x0000009B | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.90234 |
.tls | 0x00432000 | 0x00000054 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00433000 | 0x0000005D | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.36412 |
.reloc | 0x00434000 | 0x00049FB0 | 0x0004A000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.71875 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.8622 | 725 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.64018 | 67624 | UNKNOWN | English - United States | RT_ICON |
3 | 3.81224 | 16936 | UNKNOWN | English - United States | RT_ICON |
4 | 4.20125 | 9640 | UNKNOWN | English - United States | RT_ICON |
5 | 4.26452 | 4264 | UNKNOWN | English - United States | RT_ICON |
6 | 5.11705 | 2440 | UNKNOWN | English - United States | RT_ICON |
7 | 4.76297 | 1128 | UNKNOWN | English - United States | RT_ICON |
8 | 1.77511 | 308 | UNKNOWN | English - United States | RT_CURSOR |
9 | 2.6633 | 308 | UNKNOWN | English - United States | RT_CURSOR |
3682 | 2.04342 | 76 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
AVICAP32.DLL |
MSVFW32.DLL |
SHFolder.dll |
advapi32.dll |
comctl32.dll |
gdi32.dll |
kernel32.dll |
kernel32.dll (delay-loaded) |
msvcrt.dll |
netapi32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
dbkFCallWrapperAddr | 1 | 0x0041363C |
__dbk_fcall_wrapper | 2 | 0x00010AF8 |
TMethodImplementationIntercept | 3 | 0x000DA470 |
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2072 | "C:\Users\admin\AppData\Local\Temp\AntiTest.exe" | C:\Users\admin\AppData\Local\Temp\AntiTest.exe | — | explorer.exe | |||||||||||
User: admin Company: Datpol Integrity Level: MEDIUM Description: SpySheter Security Test Tool Exit code: 3221226540 Version: 1.2.1.0 Modules
| |||||||||||||||
| 2748 | "C:\Users\admin\AppData\Local\Temp\AntiTest.exe" | C:\Users\admin\AppData\Local\Temp\AntiTest.exe | explorer.exe | ||||||||||||
User: admin Company: Datpol Integrity Level: HIGH Description: SpySheter Security Test Tool Exit code: 0 Version: 1.2.1.0 Modules
| |||||||||||||||
Total events
358
Read events
355
Write events
2
Delete events
1
Modification events
| (PID) Process: | (2748) AntiTest.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Multimedia\DrawDib |
| Operation: | write | Name: | vga.drv 1280x720x32(BGR 0) |
Value: 31,31,31,31 | |||
| (PID) Process: | (2748) AntiTest.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | AntiTest |
Value: C:\Users\admin\AppData\Local\Temp\AntiTest.exe | |||
| (PID) Process: | (2748) AntiTest.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | AntiTest |
Value: C:\Users\admin\AppData\Local\Temp\AntiTest.exe | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report