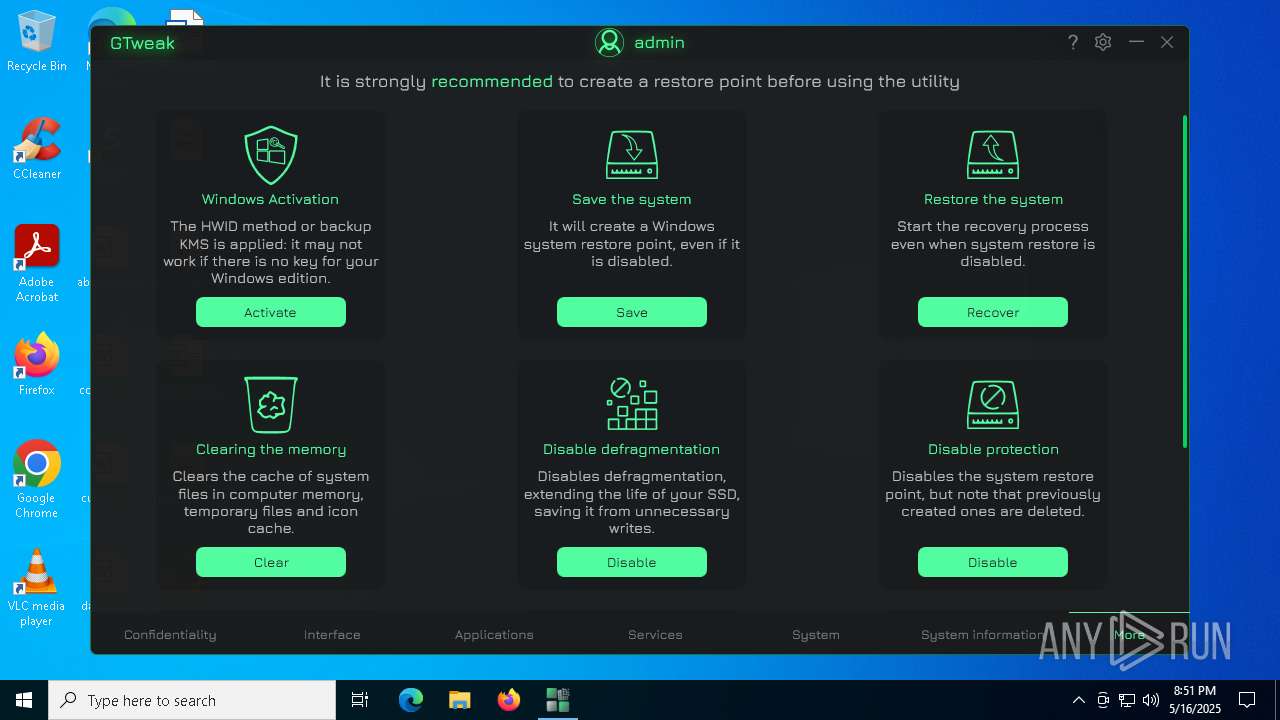
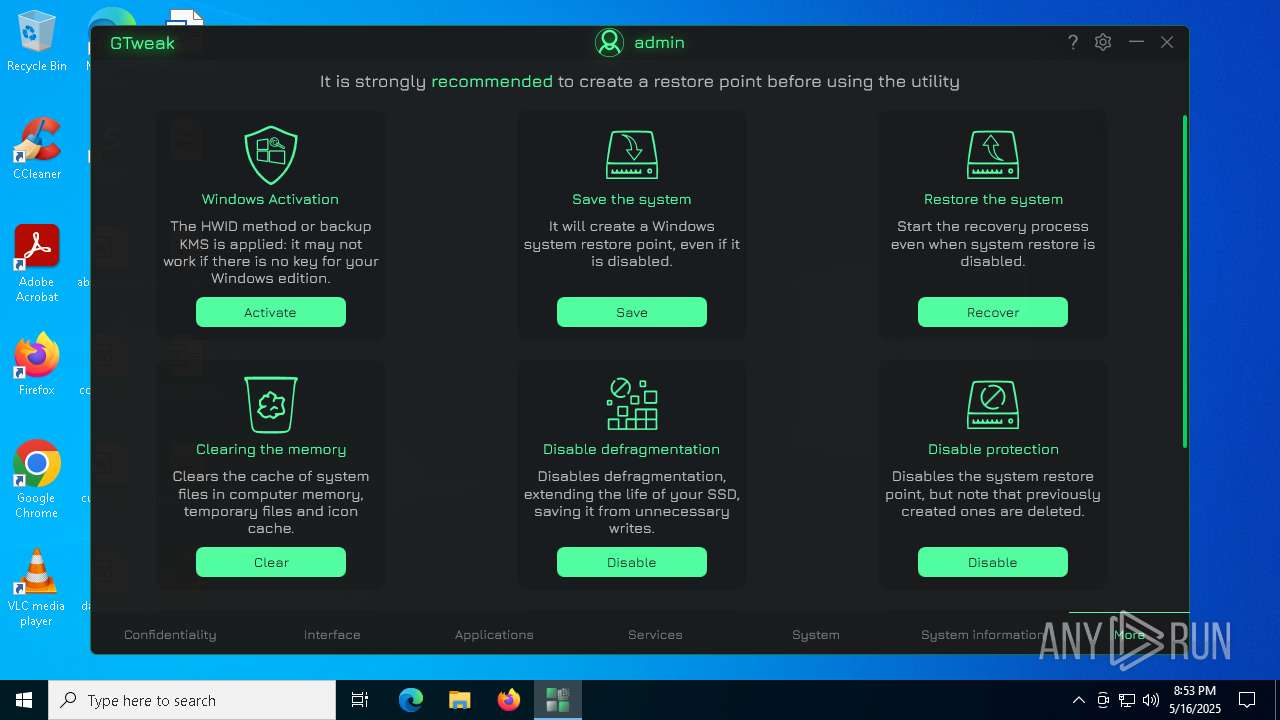
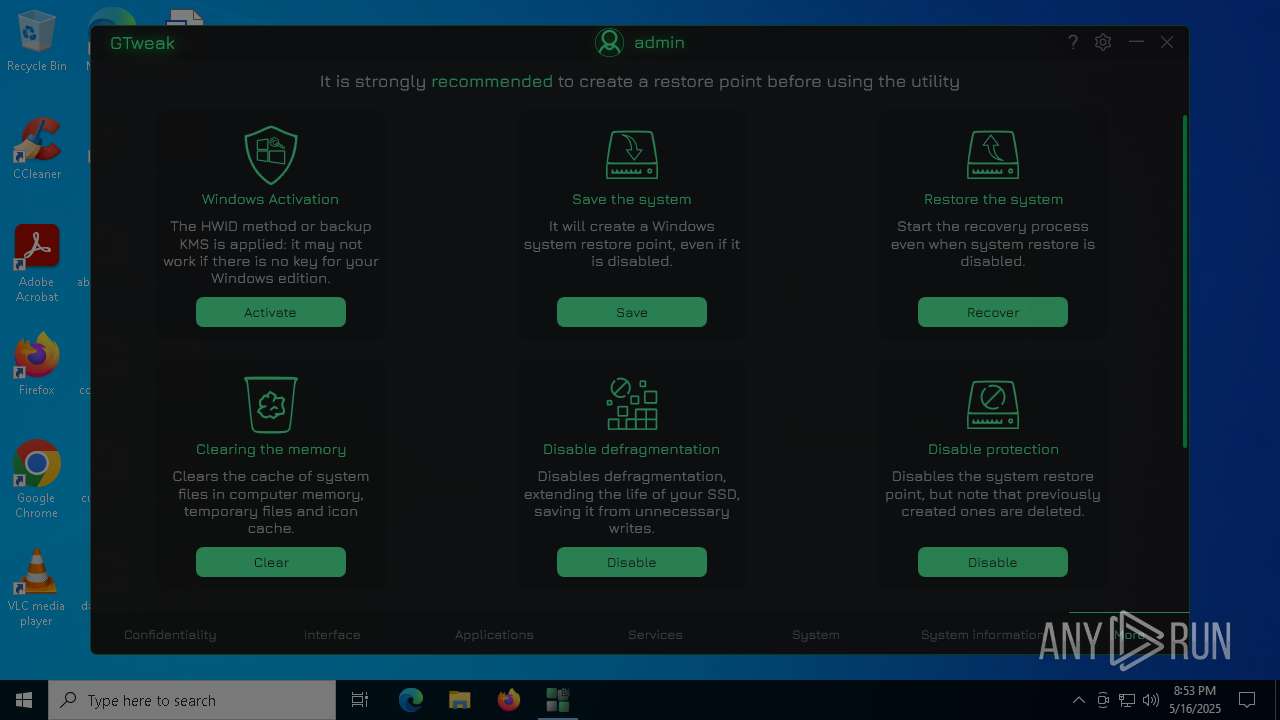
| File name: | GTweak.exe |
| Full analysis: | https://app.any.run/tasks/536b7dcc-98f7-42e2-9408-cfd8fa83f14a |
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2025, 20:51:18 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64 Mono/.Net assembly, for MS Windows, 2 sections |
| MD5: | 7D64A7011F5CA82C8D85DA8A98D73227 |
| SHA1: | CC410DAE8CB2ED86D74F74065439B8C2607E2803 |
| SHA256: | AD1A12CC39DABA500B992A9275BAA07DBC42FF9B5AAF12FF1205E8B4A9A5E034 |
| SSDEEP: | 98304:x9axC5aXJXIdSorCngK5AdzUqbXIdSorCngK5JsrDczjl7Dg4q8Ntm769D6flB2d:2r |
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 5112)
- powershell.exe (PID: 5260)
Changes powershell execution policy (Bypass)
- GTweak.exe (PID: 6112)
SUSPICIOUS
Reads security settings of Internet Explorer
- GTweak.exe (PID: 6112)
The process hides Powershell's copyright startup banner
- GTweak.exe (PID: 6112)
The process bypasses the loading of PowerShell profile settings
- GTweak.exe (PID: 6112)
Starts POWERSHELL.EXE for commands execution
- GTweak.exe (PID: 6112)
The process hide an interactive prompt from the user
- GTweak.exe (PID: 6112)
Starts application with an unusual extension
- cmd.exe (PID: 5384)
Starts SC.EXE for service management
- cmd.exe (PID: 1568)
- cmd.exe (PID: 7620)
- cmd.exe (PID: 7932)
- cmd.exe (PID: 7672)
- cmd.exe (PID: 3192)
- cmd.exe (PID: 7472)
- cmd.exe (PID: 7972)
- cmd.exe (PID: 2852)
- cmd.exe (PID: 5984)
- cmd.exe (PID: 4980)
- cmd.exe (PID: 7728)
Suspicious use of NETSH.EXE
- cmd.exe (PID: 5384)
Starts CMD.EXE for commands execution
- GTweak.exe (PID: 6112)
Windows service management via SC.EXE
- sc.exe (PID: 2148)
- sc.exe (PID: 1912)
- sc.exe (PID: 7660)
- sc.exe (PID: 8092)
- sc.exe (PID: 7704)
- sc.exe (PID: 8028)
- sc.exe (PID: 7724)
- sc.exe (PID: 8048)
- sc.exe (PID: 7684)
- sc.exe (PID: 8072)
- sc.exe (PID: 7084)
- sc.exe (PID: 1056)
- sc.exe (PID: 5600)
- sc.exe (PID: 5304)
- sc.exe (PID: 968)
- sc.exe (PID: 7720)
- sc.exe (PID: 8028)
- sc.exe (PID: 7740)
- sc.exe (PID: 7640)
- sc.exe (PID: 7752)
- sc.exe (PID: 8064)
- sc.exe (PID: 7256)
- sc.exe (PID: 1912)
- sc.exe (PID: 2148)
- sc.exe (PID: 6468)
- sc.exe (PID: 5744)
- sc.exe (PID: 7728)
- sc.exe (PID: 7628)
- sc.exe (PID: 7708)
- sc.exe (PID: 7000)
- sc.exe (PID: 6980)
- sc.exe (PID: 7944)
- sc.exe (PID: 8000)
- sc.exe (PID: 7724)
- sc.exe (PID: 7260)
- sc.exe (PID: 7280)
- sc.exe (PID: 4728)
- sc.exe (PID: 6208)
- sc.exe (PID: 7716)
- sc.exe (PID: 5576)
- sc.exe (PID: 7796)
- sc.exe (PID: 7816)
- sc.exe (PID: 4688)
- sc.exe (PID: 7704)
Executes as Windows Service
- VSSVC.exe (PID: 6800)
Checks for external IP
- svchost.exe (PID: 2196)
Searches for installed software
- dllhost.exe (PID: 6644)
INFO
Reads the computer name
- GTweak.exe (PID: 6112)
Reads product name
- GTweak.exe (PID: 6112)
Checks supported languages
- GTweak.exe (PID: 6112)
- chcp.com (PID: 2420)
Reads Environment values
- GTweak.exe (PID: 6112)
Reads the machine GUID from the registry
- GTweak.exe (PID: 6112)
Disables trace logs
- netsh.exe (PID: 1388)
- GTweak.exe (PID: 6112)
- netsh.exe (PID: 1568)
- netsh.exe (PID: 736)
- netsh.exe (PID: 1040)
Checks proxy server information
- GTweak.exe (PID: 6112)
Changes the display of characters in the console
- cmd.exe (PID: 5384)
Reads the software policy settings
- GTweak.exe (PID: 6112)
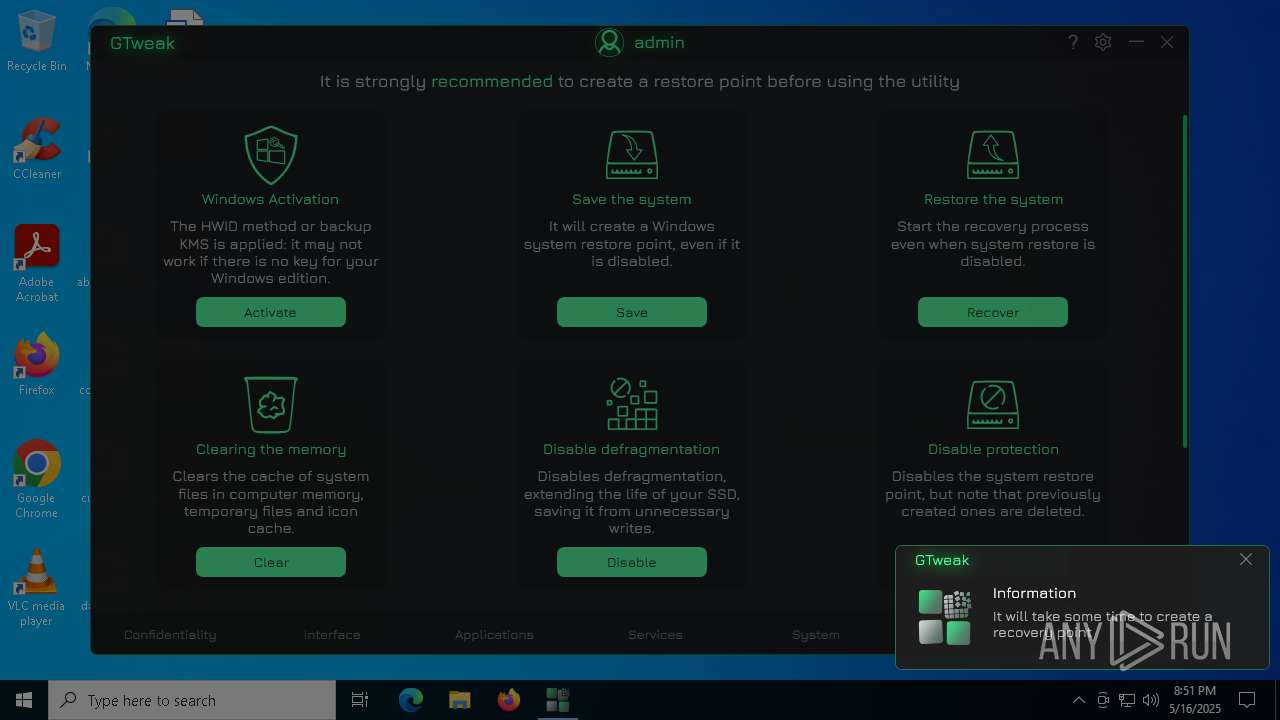
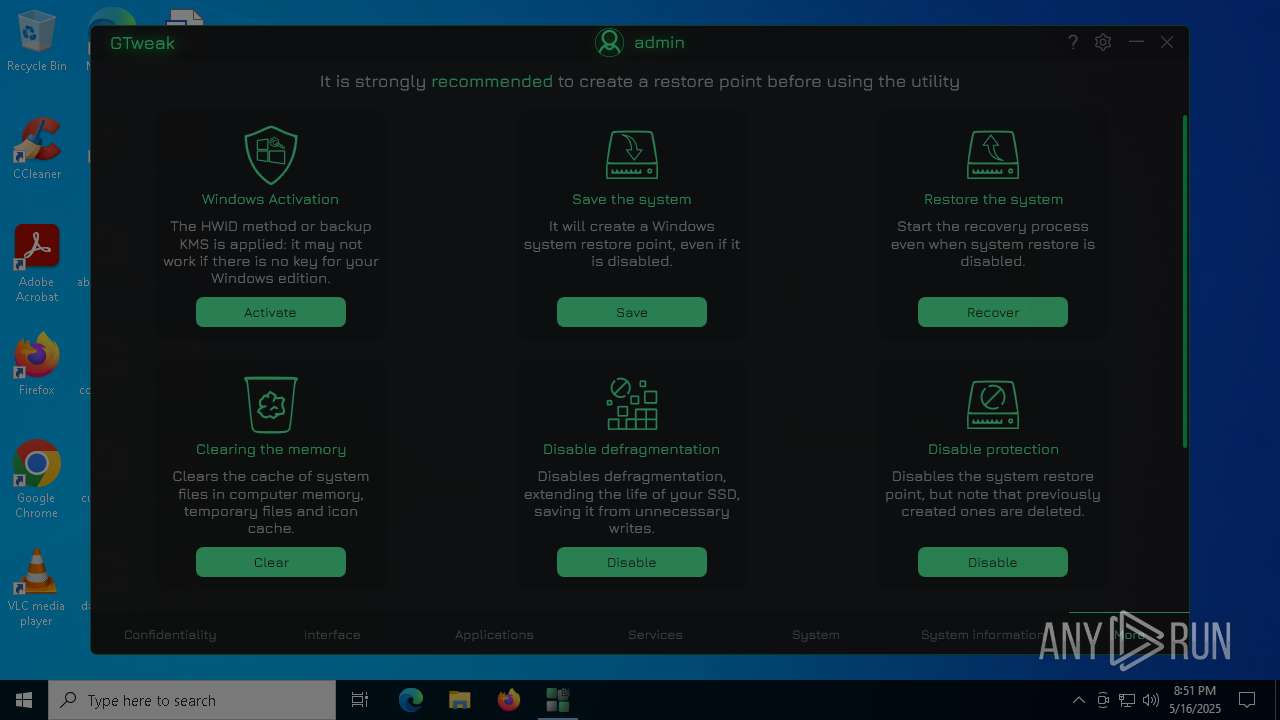
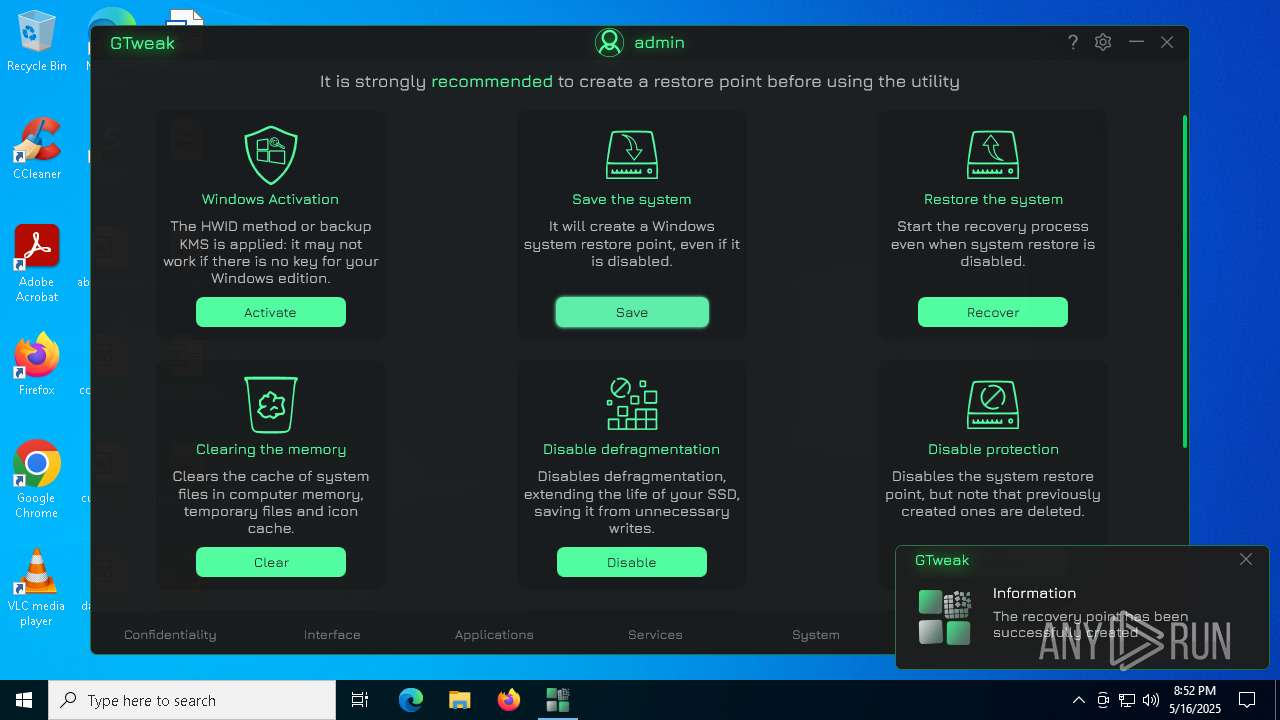
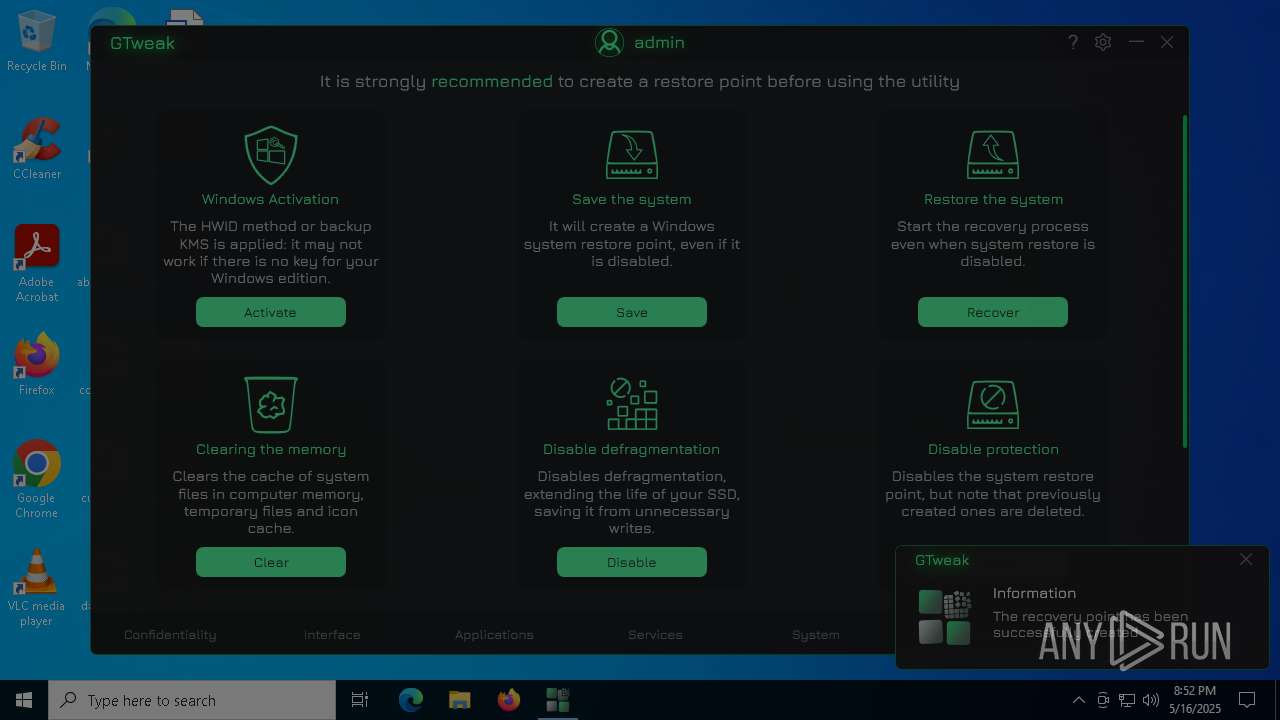
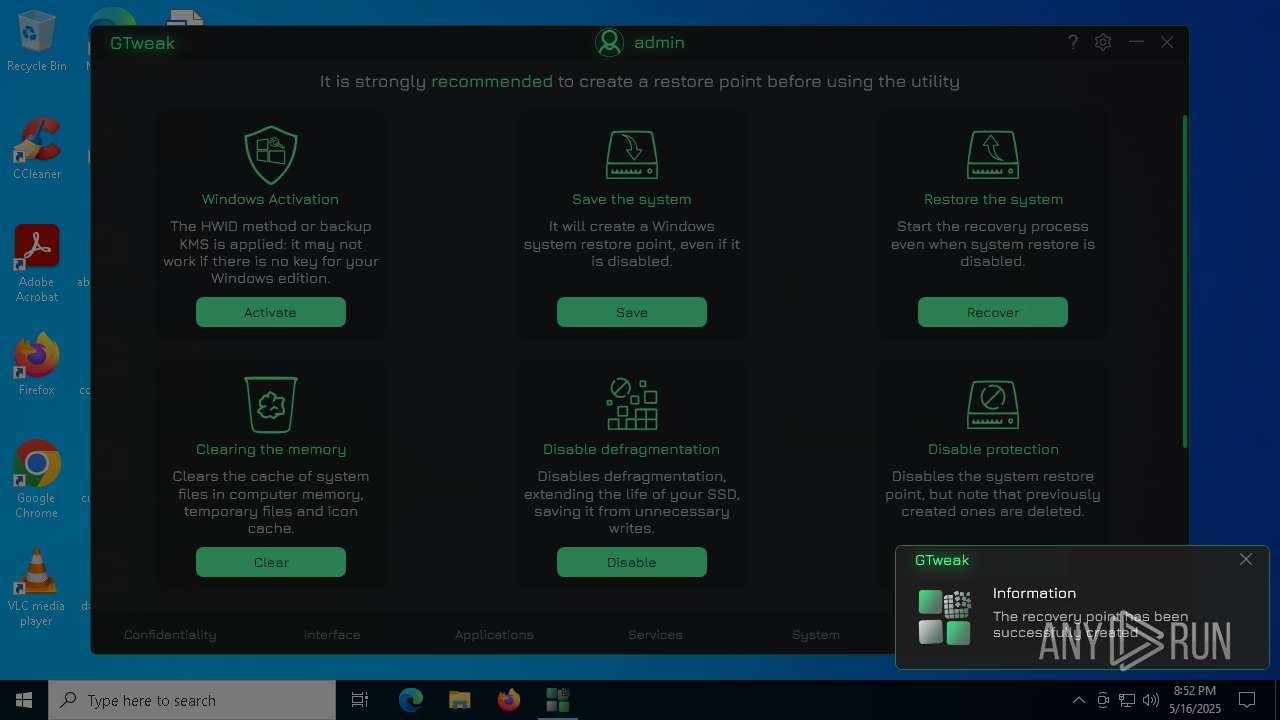
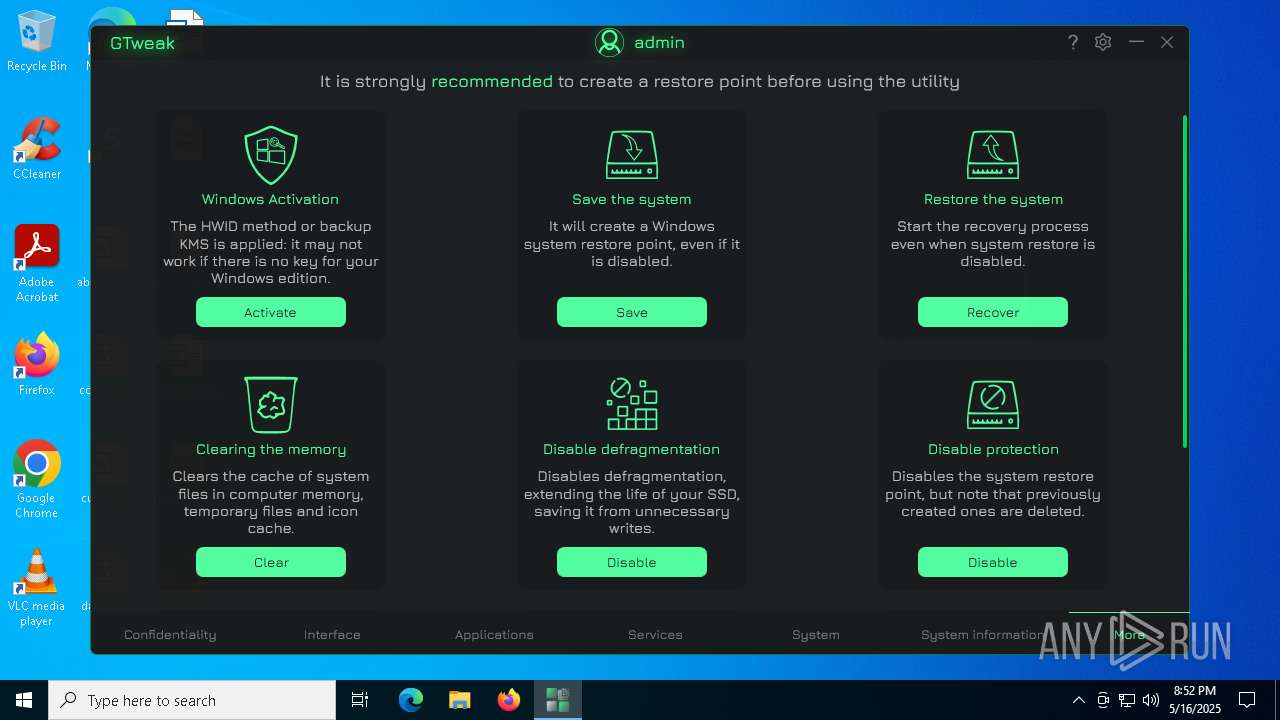
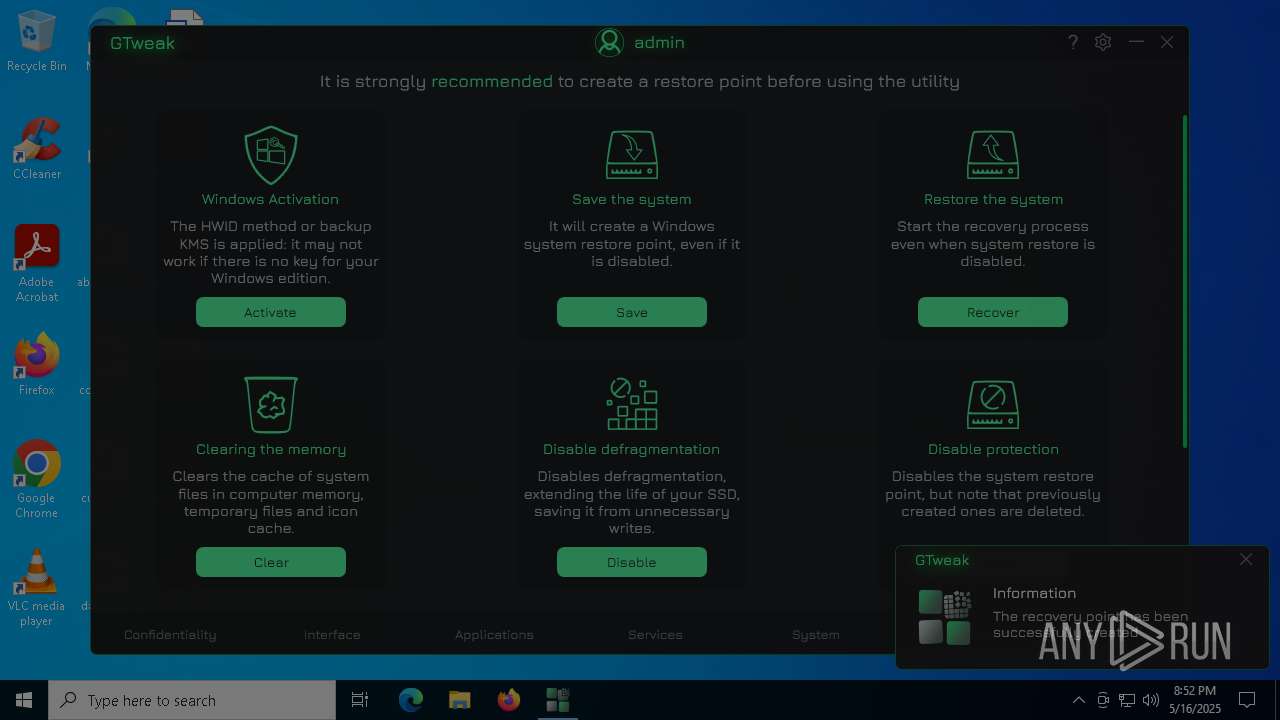
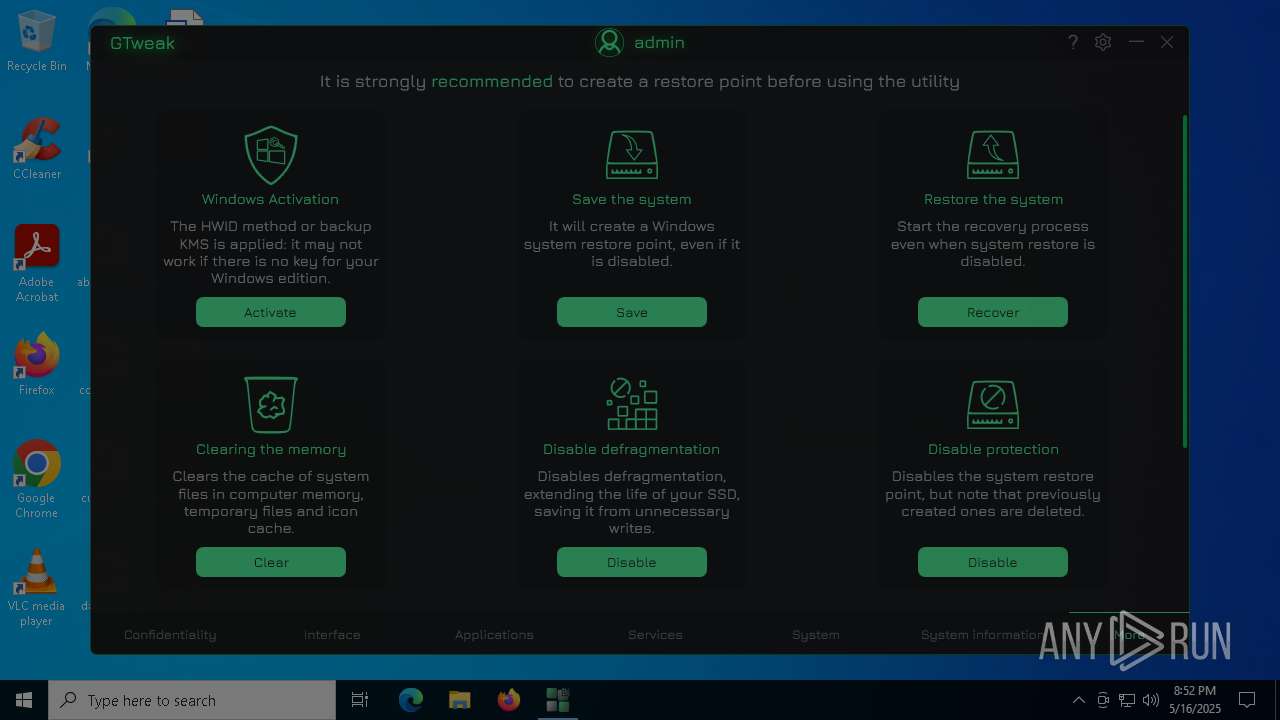
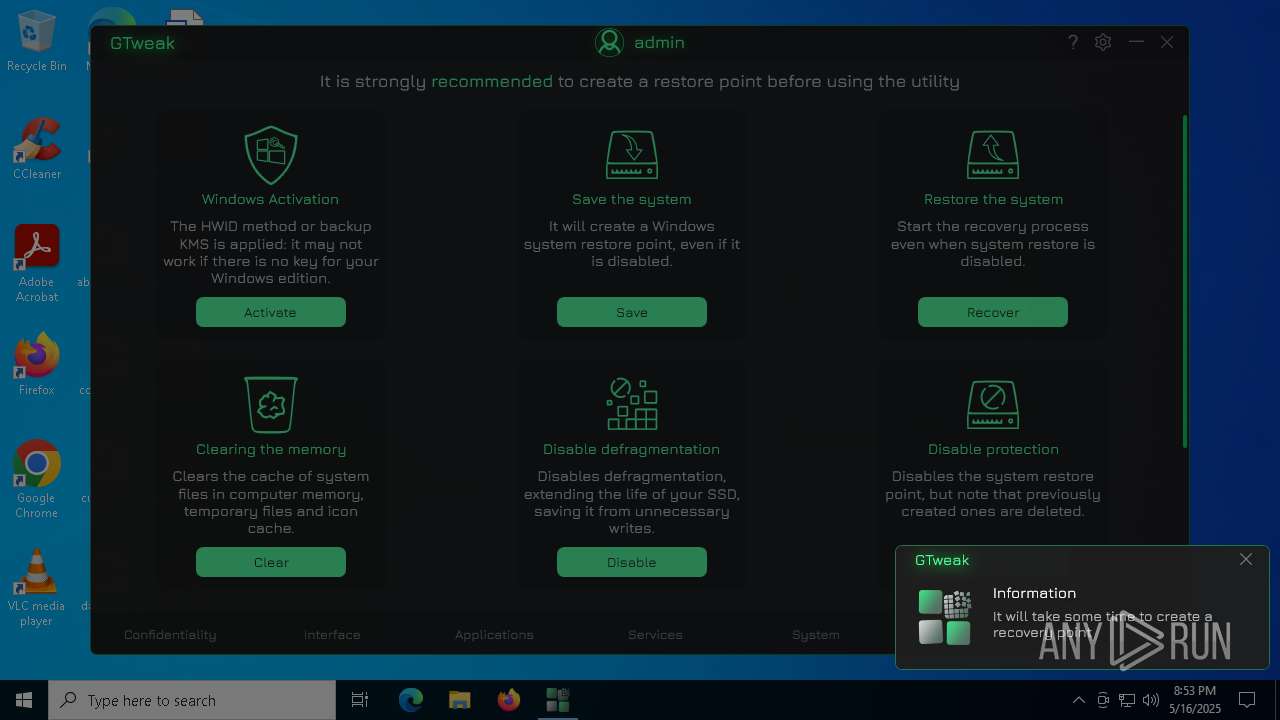
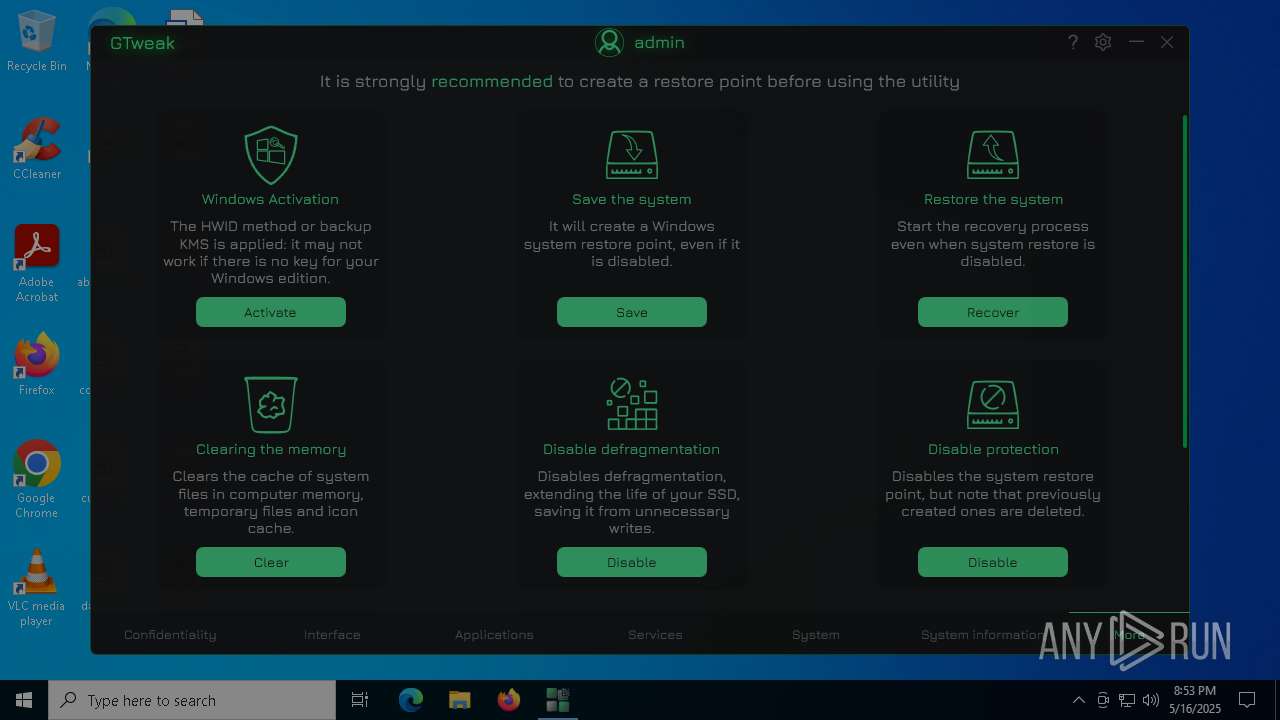
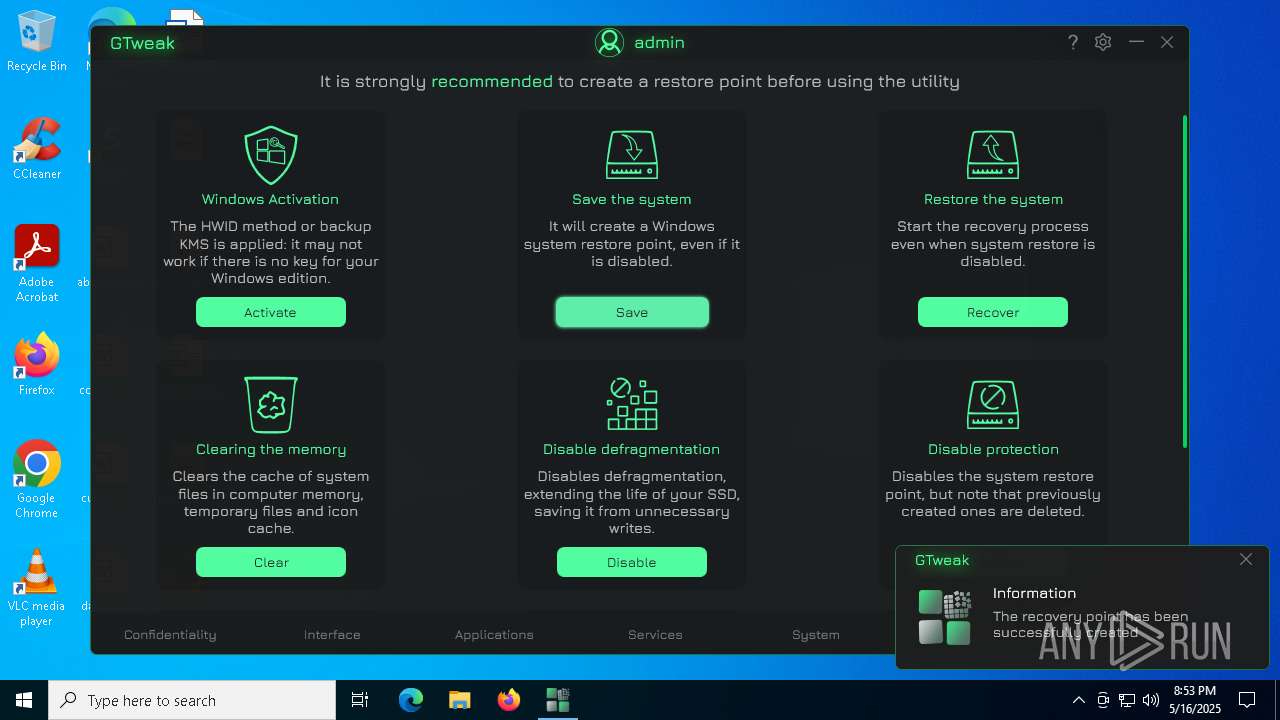
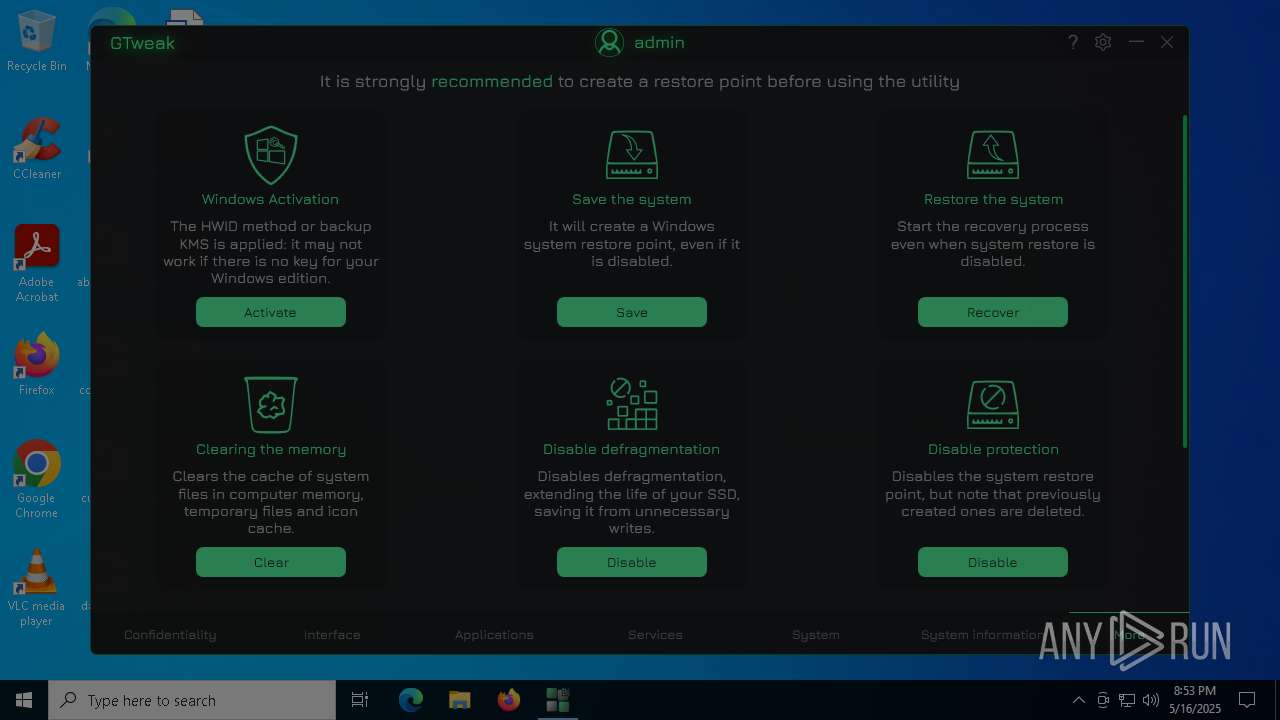
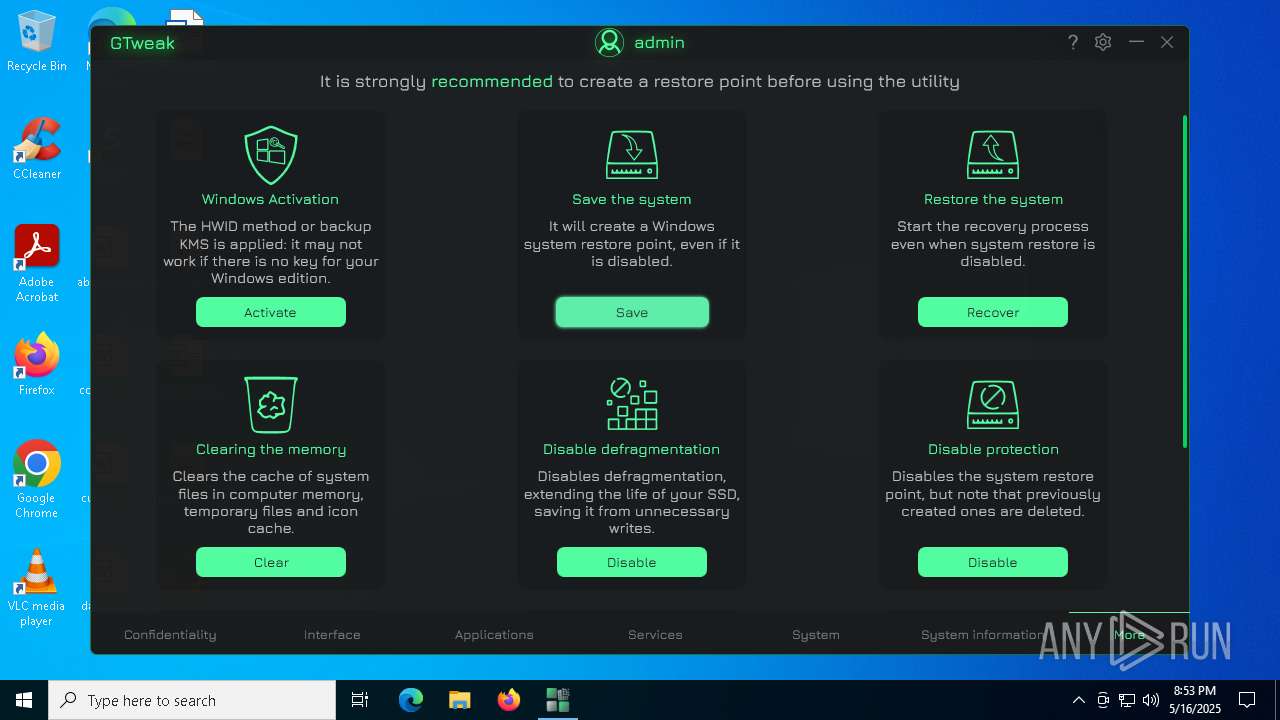
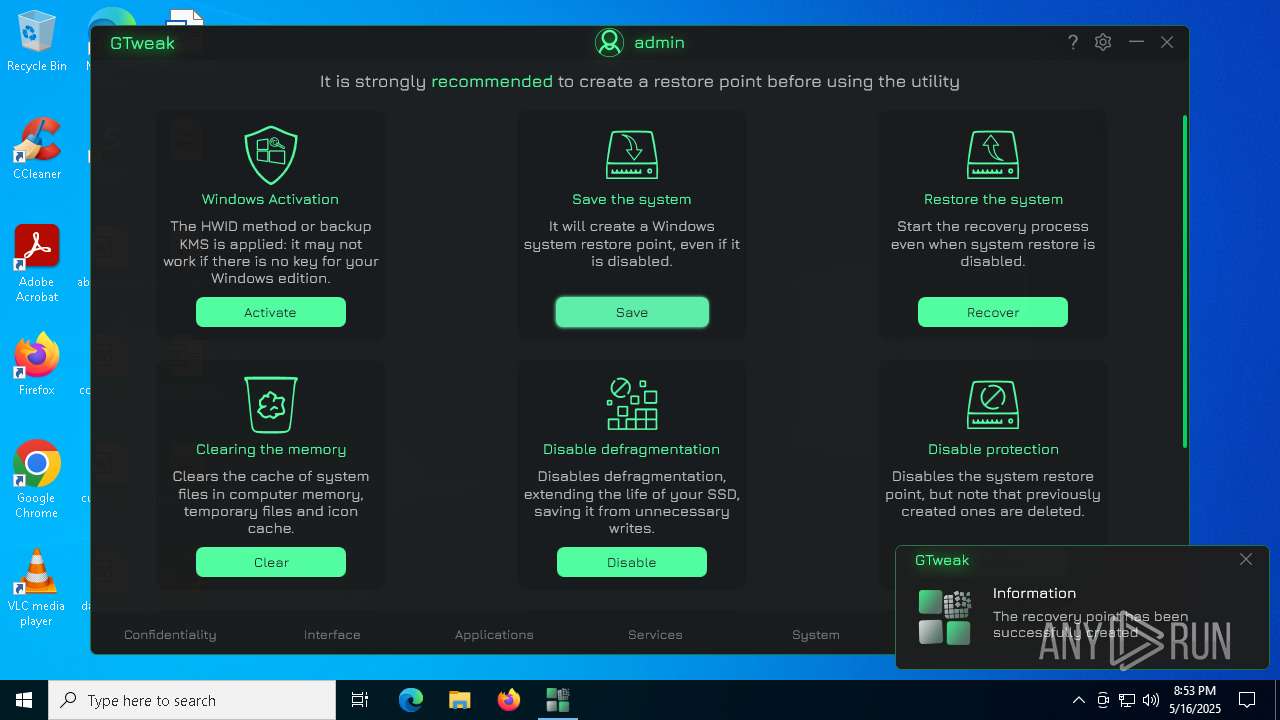
Manages system restore points
- SrTasks.exe (PID: 7484)
- SrTasks.exe (PID: 7860)
- SrTasks.exe (PID: 1280)
- SrTasks.exe (PID: 928)
- SrTasks.exe (PID: 6404)
- SrTasks.exe (PID: 7536)
- SrTasks.exe (PID: 3804)
- SrTasks.exe (PID: 8140)
- SrTasks.exe (PID: 7884)
- SrTasks.exe (PID: 4024)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:05:05 09:14:29+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 48 |
| CodeSize: | 2795520 |
| InitializedDataSize: | 218624 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x0000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.2.31.104 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | Perfect setup of Windows 10 & Windows 11 with the choice of options you need for better convenience and performance |
| FileDescription: | GTweak |
| FileVersion: | 5.2.31.104 |
| InternalName: | GTweak.exe |
| LegalCopyright: | © 2024-2025 Greedeks |
| LegalTrademarks: | Greedeks |
| OriginalFileName: | GTweak.exe |
| ProductName: | GTweak |
| ProductVersion: | Build: 5.2.2 |
| AssemblyVersion: | 5.2.31.104 |
Total processes
231
Monitored processes
104
Malicious processes
12
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 632 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 732 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 736 | netsh int isatap show state | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 928 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:14 | C:\Windows\System32\SrTasks.exe | — | dllhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Windows System Protection background tasks. Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 968 | sc config VSS start= demand | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1040 | netsh int ipv6 isatap show state | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1056 | sc config wbengine start= demand | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1280 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:13 | C:\Windows\System32\SrTasks.exe | — | dllhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Windows System Protection background tasks. Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1388 | netsh int ipv6 6to4 show state | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1568 | netsh int teredo show state | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
30 863
Read events
28 786
Write events
1 939
Delete events
138
Modification events
| (PID) Process: | (6112) GTweak.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\GTweak |
| Operation: | write | Name: | HiddenIP |
Value: True | |||
| (PID) Process: | (6112) GTweak.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\GTweak |
| Operation: | write | Name: | Theme |
Value: Dark | |||
| (PID) Process: | (6112) GTweak.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\GTweak |
| Operation: | write | Name: | Language |
Value: en | |||
| (PID) Process: | (6112) GTweak.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\GTweak |
| Operation: | write | Name: | Volume |
Value: 50 | |||
| (PID) Process: | (6112) GTweak.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\GTweak |
| Operation: | write | Name: | Sound |
Value: True | |||
| (PID) Process: | (6112) GTweak.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\GTweak |
| Operation: | write | Name: | TopMost |
Value: False | |||
| (PID) Process: | (6112) GTweak.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\GTweak |
| Operation: | write | Name: | Update |
Value: True | |||
| (PID) Process: | (6112) GTweak.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\GTweak |
| Operation: | write | Name: | Notification |
Value: True | |||
| (PID) Process: | (2268) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\11000001 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (2268) bcdedit.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\11000001 |
| Operation: | write | Name: | Element |
Value: 0000000000000000000000000000000006000000000000004800000000000000715E5C2FA985EB1190A89A9B763584210000000000000000745E5C2FA985EB1190A89A9B7635842100000000000000000000000000000000 | |||
Executable files
0
Suspicious files
23
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6644 | dllhost.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 5260 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_zkq50llh.3ez.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5112 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_lsjskgd1.r05.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5260 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_yl151oee.3ph.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5112 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_h5pg5c3z.weo.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6644 | dllhost.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{8d328b8a-d0c8-49c7-ac0d-e981e67837dc}_OnDiskSnapshotProp | binary | |
MD5:D08EA202CA30A935294DE5BD461BEFFB | SHA256:81F4DAAF9EDBA3DE02982B93E57871F2E48731573976295AB0FBA185CBB32D22 | |||
| 6644 | dllhost.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{11e312b9-8952-431f-a8a3-5a7367f93bae}_OnDiskSnapshotProp | binary | |
MD5:DE23CD3267E53907B24CA94D66A5411D | SHA256:80009D20FAC6B6C66DC080B43CB7D56B78E07C59A0F802D434C0DE7B63FE4452 | |||
| 5260 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:6014CEDEFAAA52169271AD81D0A2BC11 | SHA256:A5972BF83BA736C5C548853BBAF5566A3795087C62893C9EDD8FA9F4AACC6E9D | |||
| 6644 | dllhost.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:D08EA202CA30A935294DE5BD461BEFFB | SHA256:81F4DAAF9EDBA3DE02982B93E57871F2E48731573976295AB0FBA185CBB32D22 | |||
| 6644 | dllhost.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{f370fd9a-93c3-4222-9517-afd57770ec4e}_OnDiskSnapshotProp | binary | |
MD5:8CDAC89A91A13A77E9C2E60C110766A5 | SHA256:2AEB31773F98540D76DE8270256F4938FF2481B12B205F79359C493A66FA0BC1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
68
DNS requests
20
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7200 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
7200 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
7200 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
7200 | SIHClient.exe | GET | 200 | 104.124.11.17:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7200 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
7200 | SIHClient.exe | GET | 200 | 104.124.11.17:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
7200 | SIHClient.exe | GET | 200 | 104.124.11.17:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
7200 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 20.190.160.5:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.5:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6112 | GTweak.exe | 140.82.121.5:443 | api.github.com | GITHUB | US | whitelisted |
6112 | GTweak.exe | 104.26.9.44:443 | ipapi.co | CLOUDFLARENET | US | shared |
6112 | GTweak.exe | 104.26.5.15:443 | api.db-ip.com | CLOUDFLARENET | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
google.com |
| whitelisted |
api.github.com |
| whitelisted |
ipapi.co |
| shared |
api.db-ip.com |
| shared |
slscr.update.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain (ipapi .co in DNS lookup) |
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (api.db-ip.com) |
— | — | Potential Corporate Privacy Violation | ET INFO External Geo IP Lookup (api .db-ip .com) |