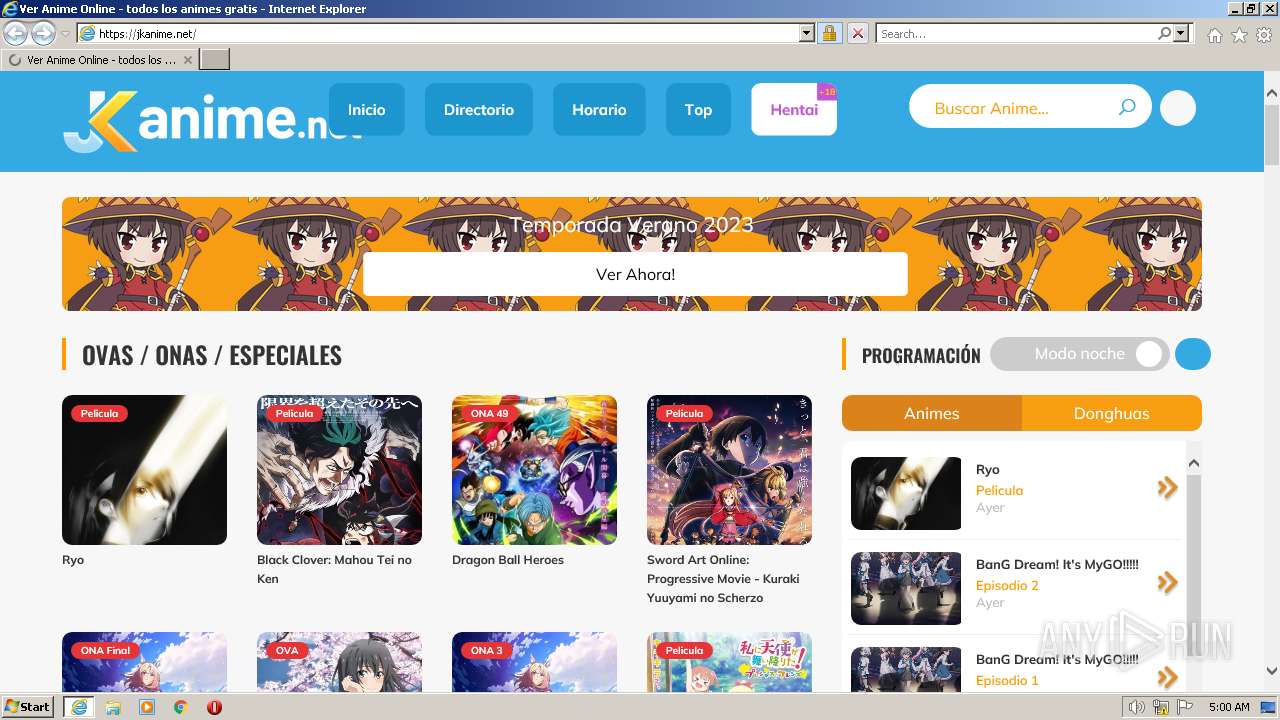
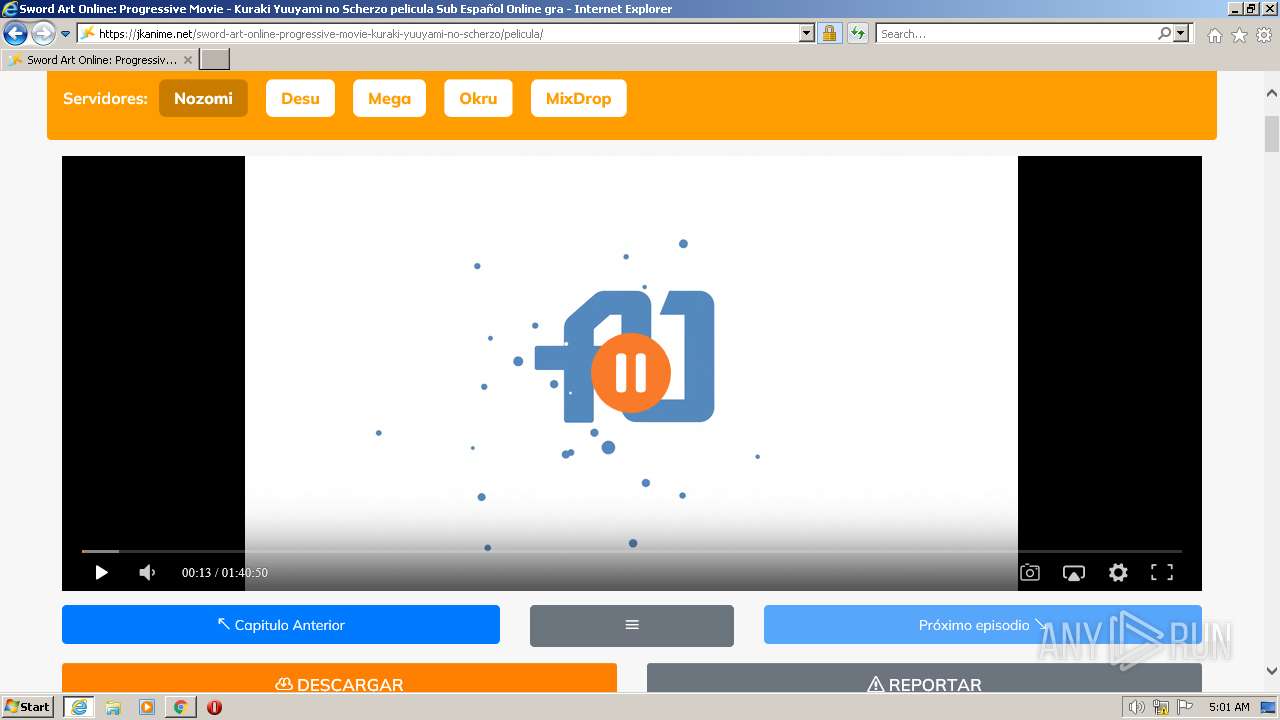
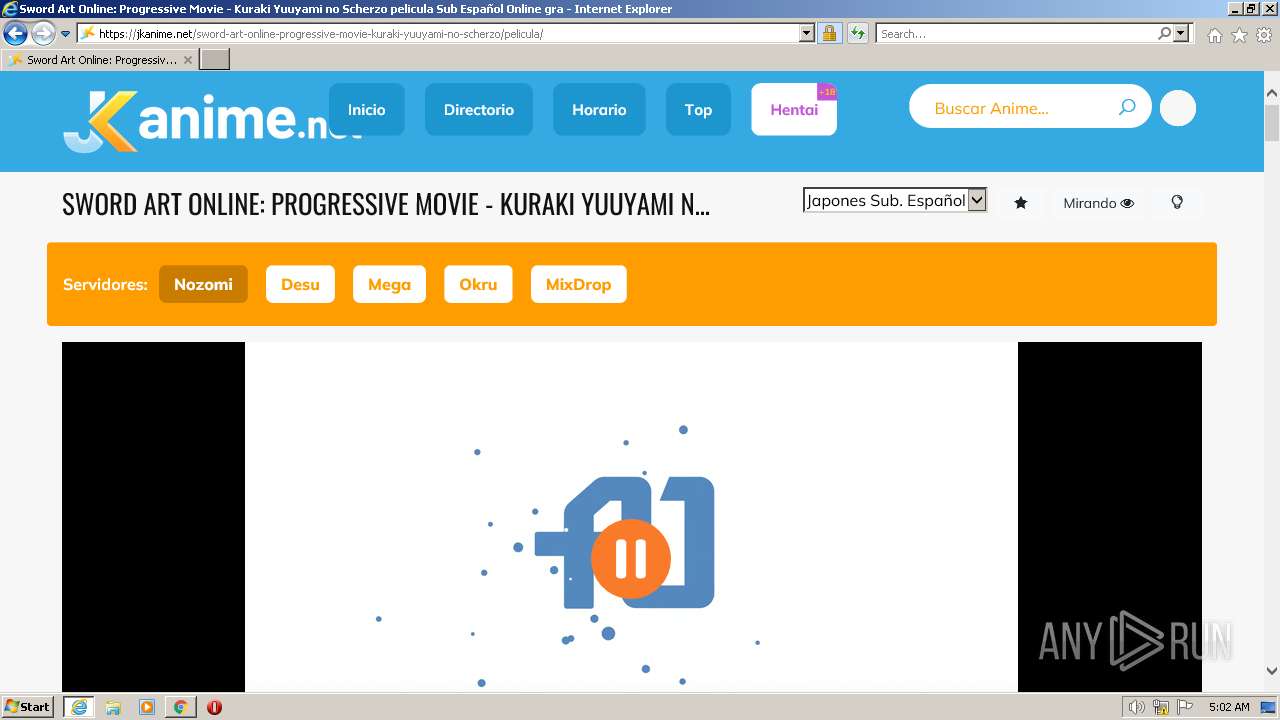
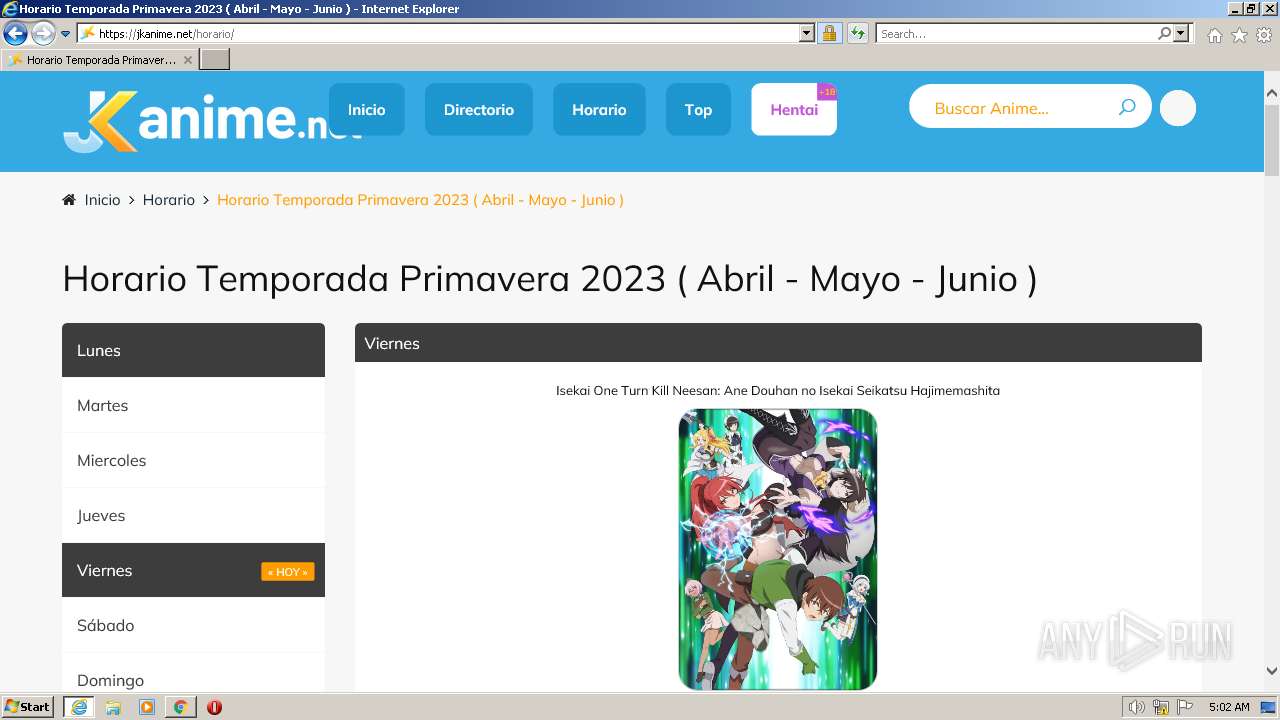
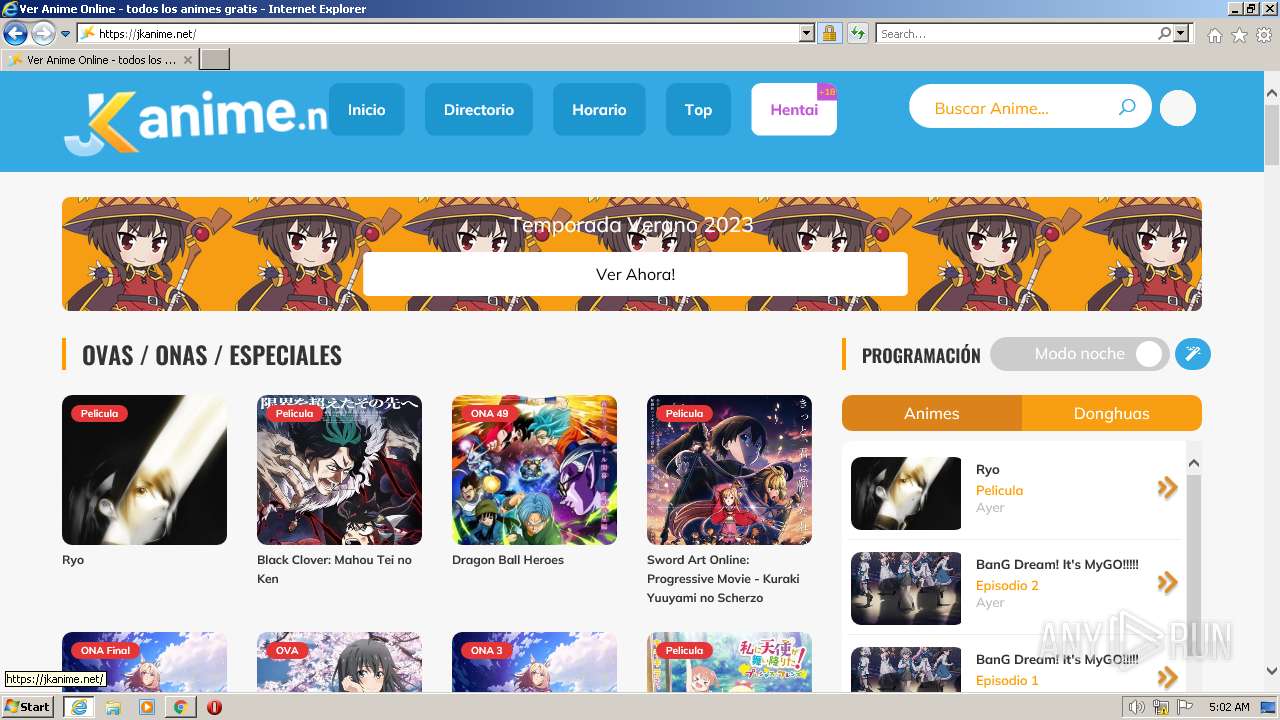
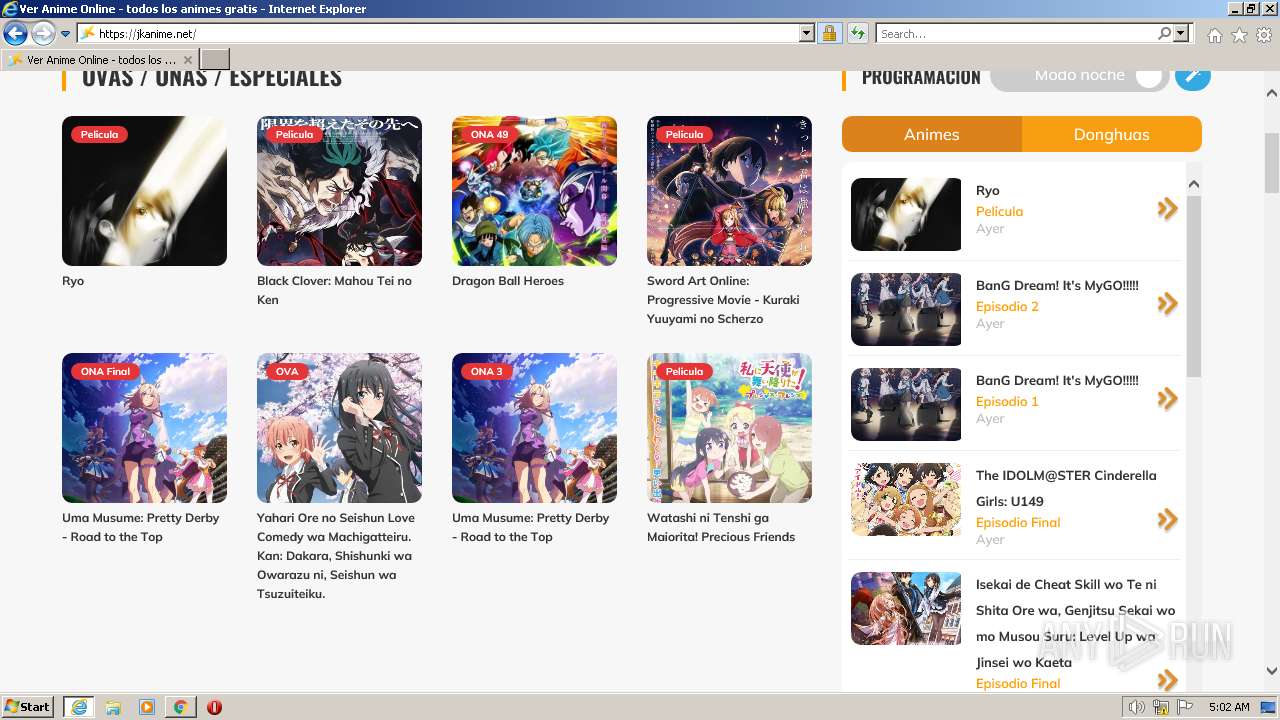
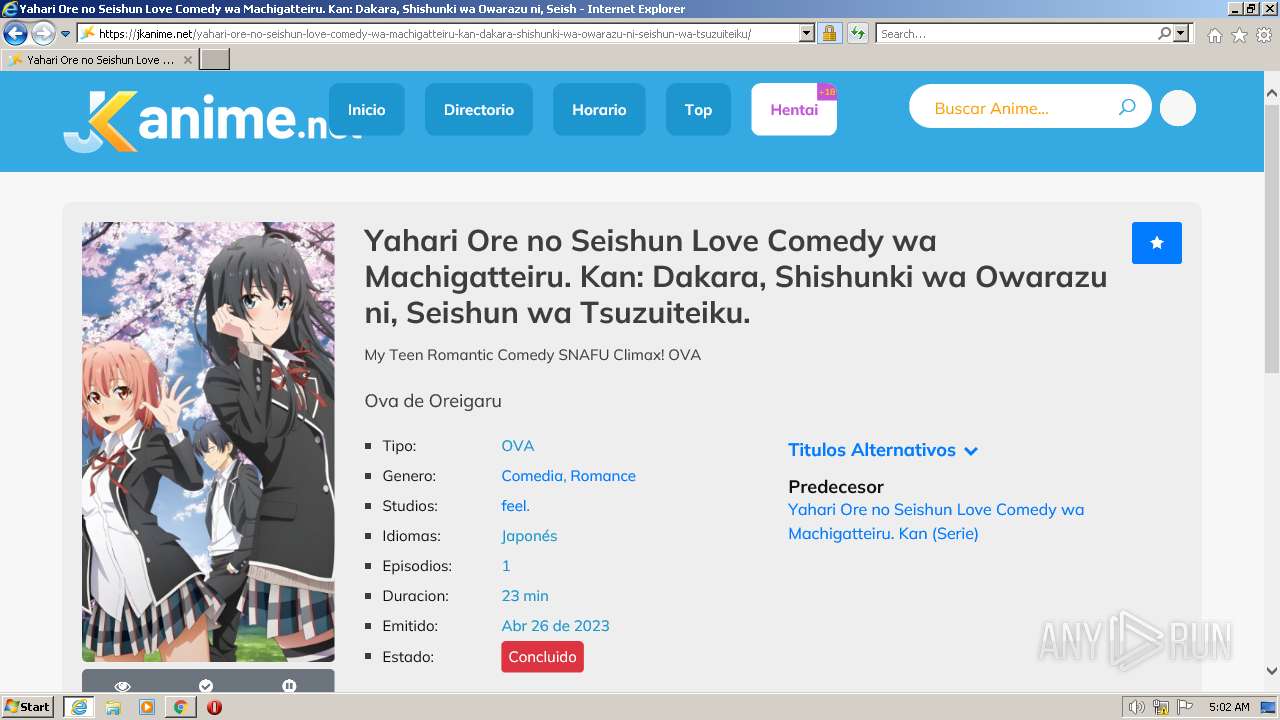
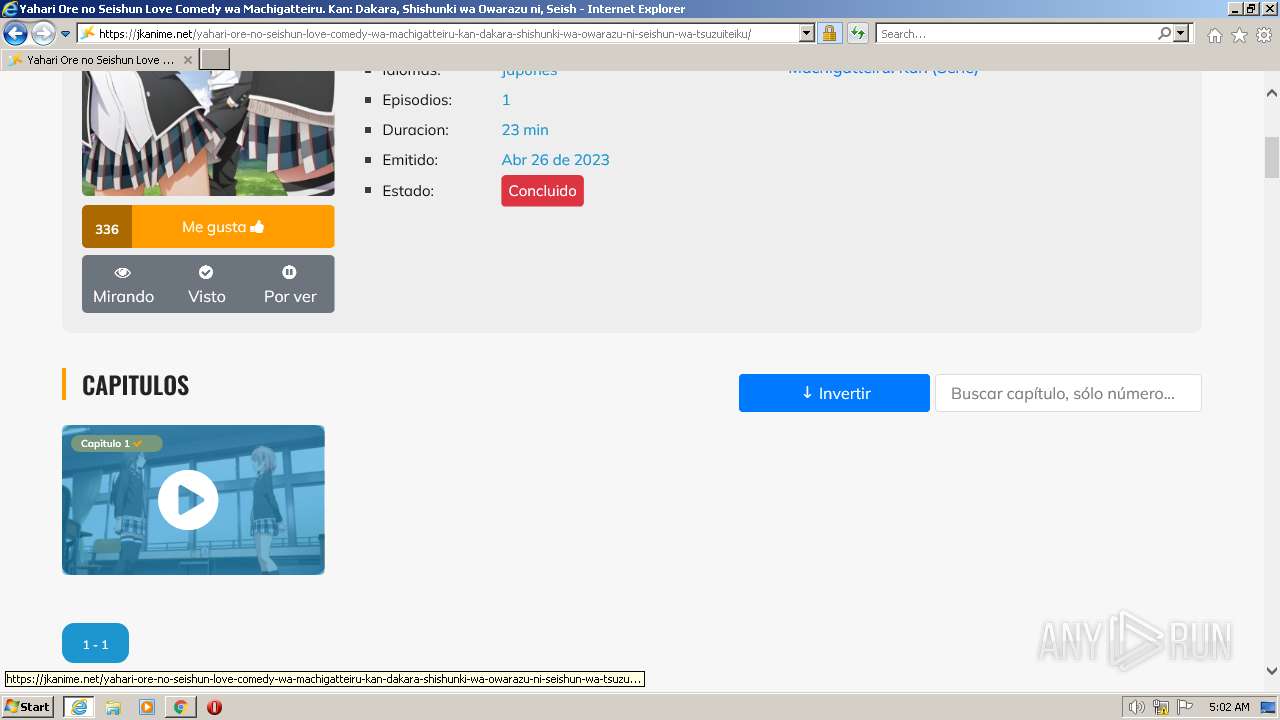
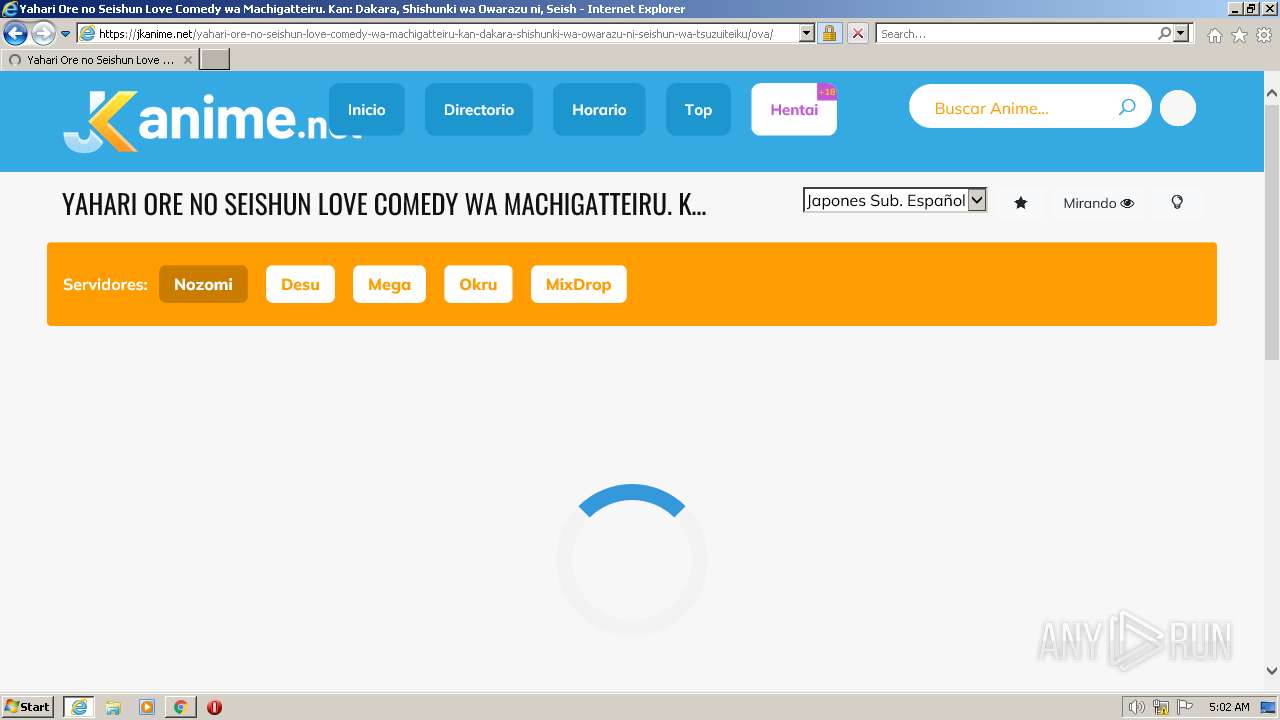
| URL: | https://jkanime.net |
| Full analysis: | https://app.any.run/tasks/6a932389-ab40-46c8-a83e-3bb938e74192 |
| Verdict: | Malicious activity |
| Analysis date: | June 30, 2023, 04:00:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 4C0349737462974B68559E29454A0E16 |
| SHA1: | DEC2A4A4C6B6A3455EDEDDA62F2381218FE7A7F7 |
| SHA256: | AD0BDADCD121C3F934D59771729382945F56287C58F1D9F98B77135ED847BF62 |
| SSDEEP: | 3:N8lJuL0:2PuL0 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 2544)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
41
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2544 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://jkanime.net" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2620 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2544 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
28 370
Read events
28 205
Write events
161
Delete events
4
Modification events
| (PID) Process: | (2544) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (2544) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (2544) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (2544) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2544) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2544) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2544) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2544) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2544) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2544) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
4
Suspicious files
86
Text files
318
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2620 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:1C3F170133C0A6BE59883681A5A75F72 | SHA256:2B94D69DDB3A887331E86AD0B92F84F2C1A48E7F42008BFBFD61386926E850BD | |||
| 2620 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:F4C16A1D69F12A0D502FDACF020D8052 | SHA256:A56F1B87A3210019409F22650761855F54BB759C07933061EAB04D1A702E0517 | |||
| 2620 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | binary | |
MD5:AA62F8CE77E072C8160C71B5DF3099B0 | SHA256:3EB4927C4D9097DC924FCDE21B56D01D5D1EF61B7D22BFB6786E3B546B33E176 | |||
| 2620 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:807C111B1B67A40EF8FEB993E0782AF3 | SHA256:985FEAA942F67397E297E7F8801D9868F0717596B042D176FDF5FE108CD7F377 | |||
| 2620 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_F2DAF19C1F776537105D08FC8D978464 | binary | |
MD5:CFBC16E33DCBEF6F773F0F79AF528F45 | SHA256:F0937890FB1053069BAAC97B7992C6D22CB74CAE20317FC05D51070D96950FFA | |||
| 2620 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\X2PNAUQD.htm | html | |
MD5:2BE275EDF72AD2AF1526B466D522446F | SHA256:BFF677E5706B8DEDC54393205FC21FF799AFE83B2B1921B469B78A6D415BB38F | |||
| 2620 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:50684547F2E5F813B06BD4EBF0B8BB02 | SHA256:1F01D764CA9610EA6254452DAAC617E77F6FAC8D81C5B6CEB35FADAEC8FA4AD1 | |||
| 2620 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:53D0734AC5169468A6238B1C80623DA5 | SHA256:E1B614807E3BA0F17B558E4B5DE72E910574779F9C29FF73440DE76A2B1C4503 | |||
| 2620 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\Y3QL058Z.txt | text | |
MD5:B51CB2CC2A09565E0461B930D3044222 | SHA256:4C795C4CF0802F4F446946D656292543C0D77BAB4DF27B25748622B398C945A9 | |||
| 2620 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\elegant-icons[1].css | text | |
MD5:08A9FD9CAF72E09D7228B68A6FCCAB17 | SHA256:728C73D086CF05538ACA199B47E25A5B18A0458EEFEDF9F2687F27EBF25848D9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
33
TCP/UDP connections
161
DNS requests
49
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2620 | iexplore.exe | GET | — | 142.250.186.35:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | — | — | whitelisted |
2620 | iexplore.exe | GET | — | 142.250.186.35:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEHFqGvcZW4luEC%2Bj74dtJbY%3D | US | — | — | whitelisted |
2620 | iexplore.exe | GET | — | 41.63.96.128:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?6528e97b337d6f20 | ZA | — | — | whitelisted |
2544 | iexplore.exe | GET | — | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | — | — | whitelisted |
2620 | iexplore.exe | GET | — | 2.16.107.43:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgMJnL7QJxBNgFGT1AhzLcwJfQ%3D%3D | unknown | — | — | shared |
2620 | iexplore.exe | GET | — | 41.63.96.128:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?5842ebba22e15166 | ZA | — | — | whitelisted |
2620 | iexplore.exe | GET | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQC7ovYBEye4sBKjzD2eimWd | US | der | 472 b | whitelisted |
2620 | iexplore.exe | GET | 200 | 41.63.96.128:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?1e838ca0fbdf23e2 | ZA | compressed | 4.70 Kb | whitelisted |
2620 | iexplore.exe | GET | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDMWFjT1ARdrAqhcDtNyM%2BH | US | der | 472 b | whitelisted |
2620 | iexplore.exe | GET | 200 | 142.250.186.35:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1076 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2620 | iexplore.exe | 172.67.73.66:443 | jkanime.net | CLOUDFLARENET | US | unknown |
3996 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2620 | iexplore.exe | 41.63.96.128:80 | ctldl.windowsupdate.com | LLNW | ZA | suspicious |
2620 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2620 | iexplore.exe | 142.250.184.234:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
2620 | iexplore.exe | 188.114.97.3:443 | cdn.jkdesu.com | CLOUDFLARENET | NL | malicious |
2620 | iexplore.exe | 139.45.197.244:443 | soocaips.com | RETN Limited | GB | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
jkanime.net |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
cdn.jkdesu.com |
| malicious |
fonts.googleapis.com |
| whitelisted |
soocaips.com |
| malicious |
gratifiedtrot.com |
| suspicious |
www.googletagmanager.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
x1.c.lencr.org |
| whitelisted |