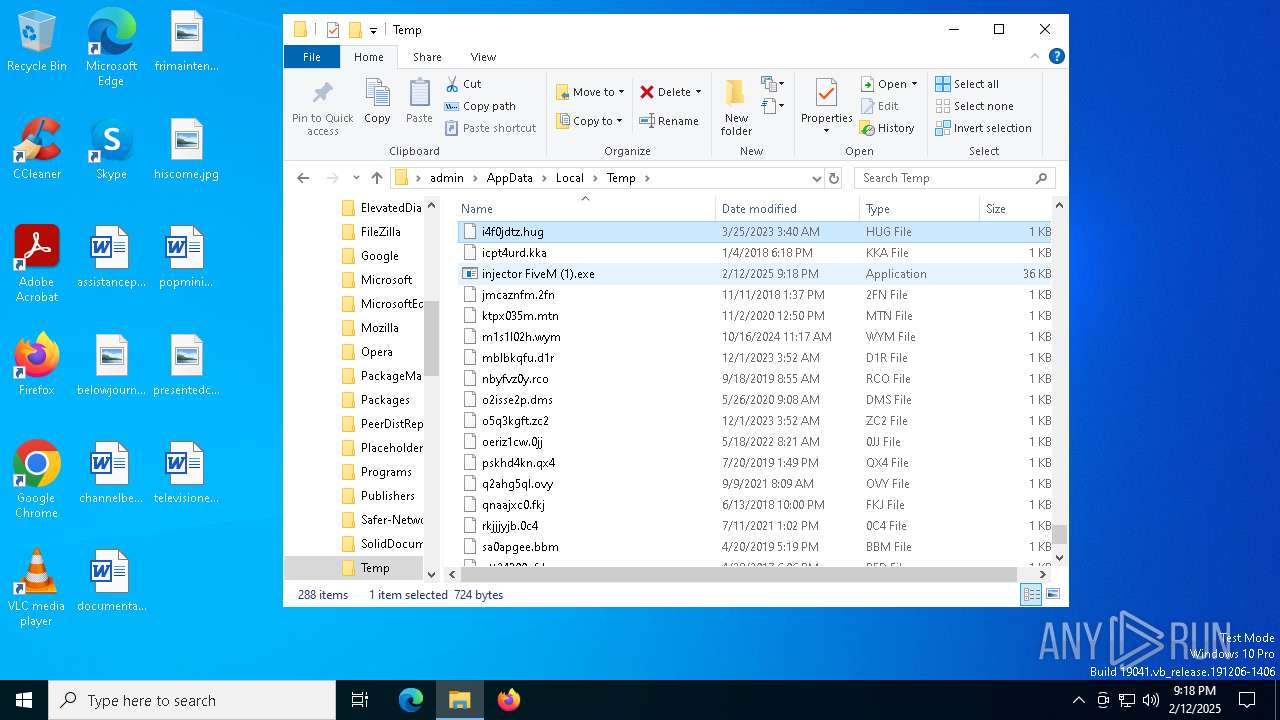
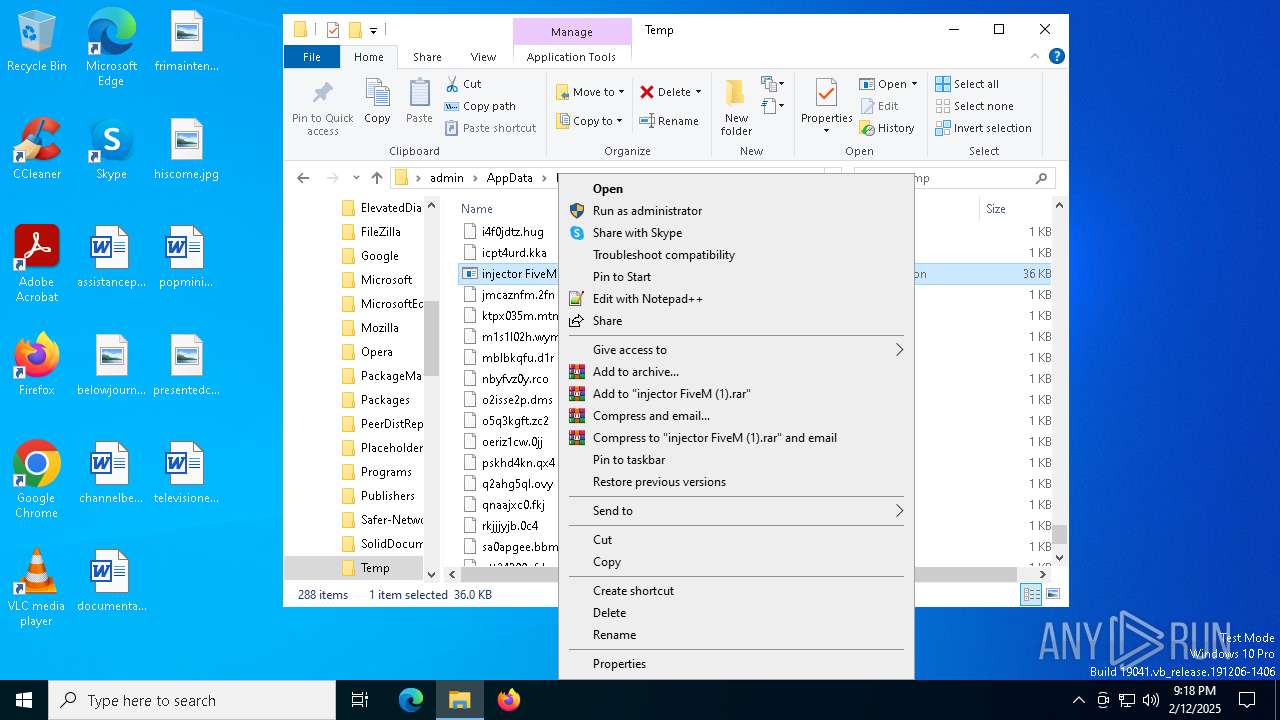
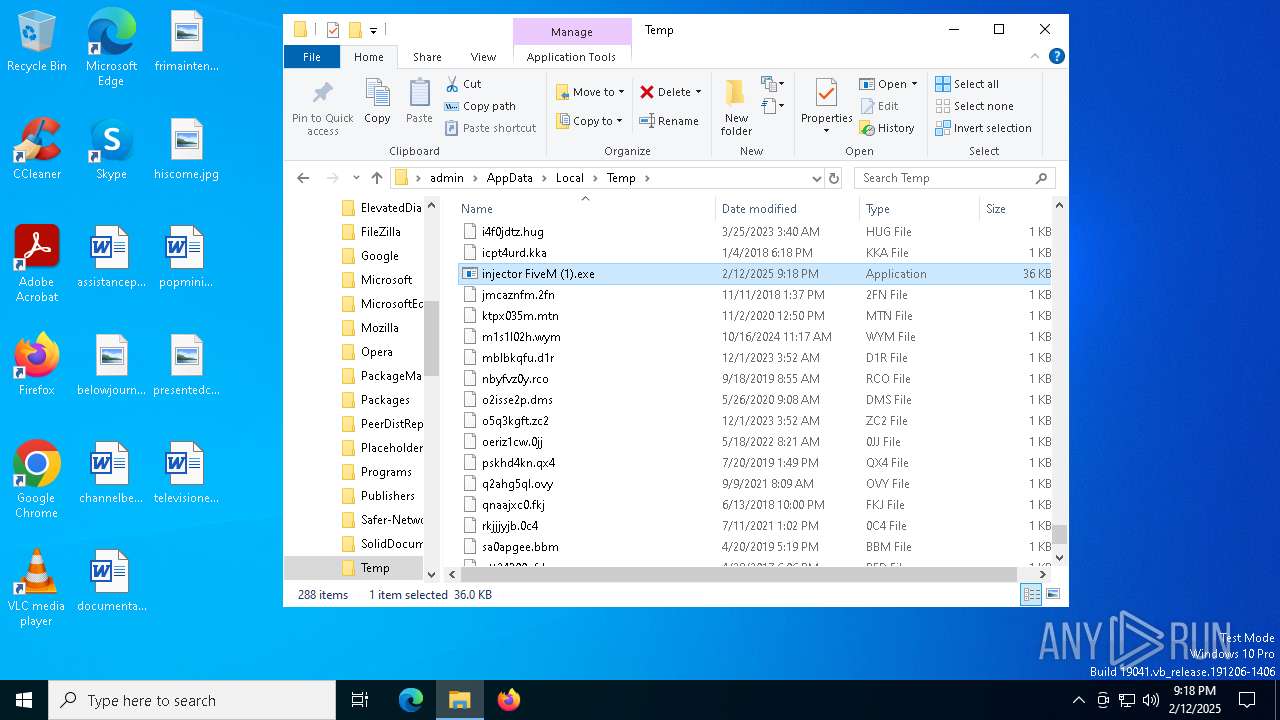
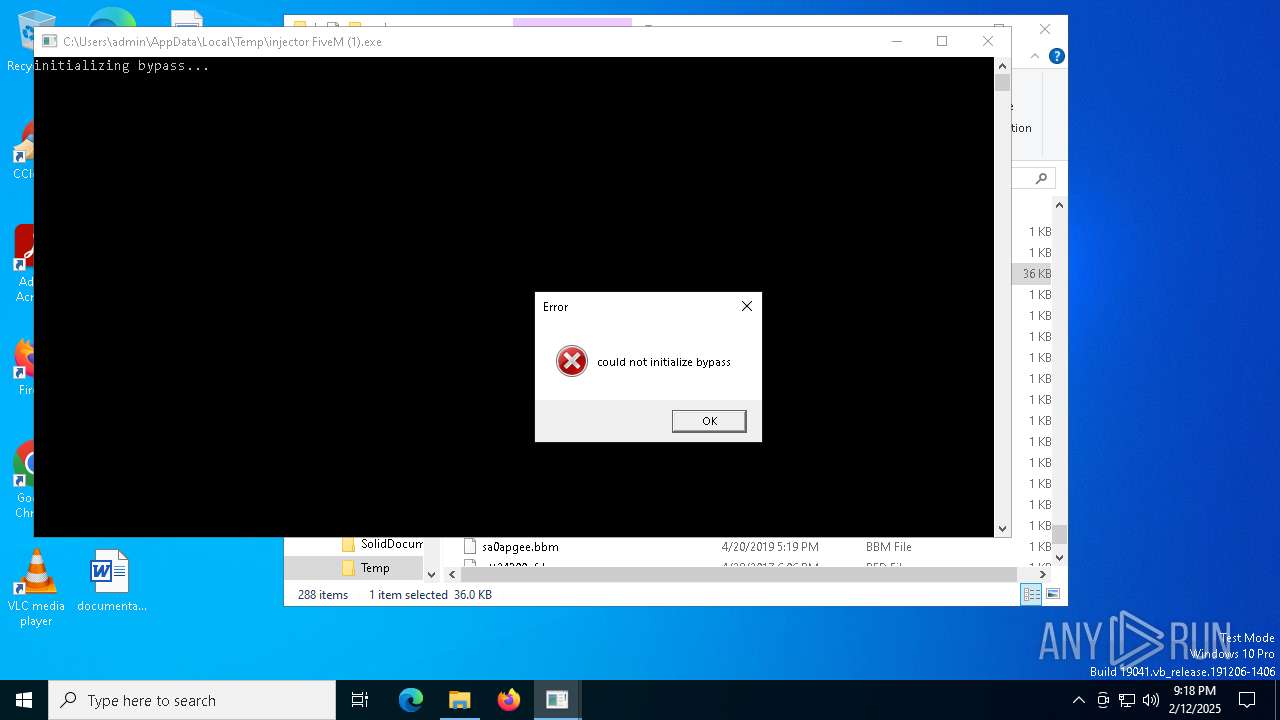
| File name: | injector FiveM (1).exe |
| Full analysis: | https://app.any.run/tasks/6befe383-b595-45ee-870e-0366ec741d5c |
| Verdict: | Malicious activity |
| Analysis date: | February 12, 2025, 21:18:01 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 6 sections |
| MD5: | 1467251D2067019EAFBF019275143679 |
| SHA1: | 5DD27DD4DC4F72E495DE6619F57536BB80B29B10 |
| SHA256: | ACFFEDA7C56BE41B2C281C1101E9682F0EBB2A193BC9E1740860E2B66E113822 |
| SSDEEP: | 1536:N45R/A4/RCz4ZRMR4rROB4AR0vf4+RS+4cR/X44Rxe4KRr34JR/w4/RVn4JRcT4a:N45R/A4/RCz4ZRMR4rROB4AR0X4+RS+S |
MALICIOUS
GENERIC has been found (auto)
- injector FiveM (1).exe (PID: 6500)
- injector FiveM (1).exe (PID: 3816)
SUSPICIOUS
Reads security settings of Internet Explorer
- injector FiveM (1).exe (PID: 6500)
- injector FiveM (1).exe (PID: 3816)
Checks Windows Trust Settings
- injector FiveM (1).exe (PID: 6500)
- injector FiveM (1).exe (PID: 3816)
Reads the date of Windows installation
- injector FiveM (1).exe (PID: 3816)
INFO
Checks supported languages
- injector FiveM (1).exe (PID: 6500)
- injector FiveM (1).exe (PID: 3816)
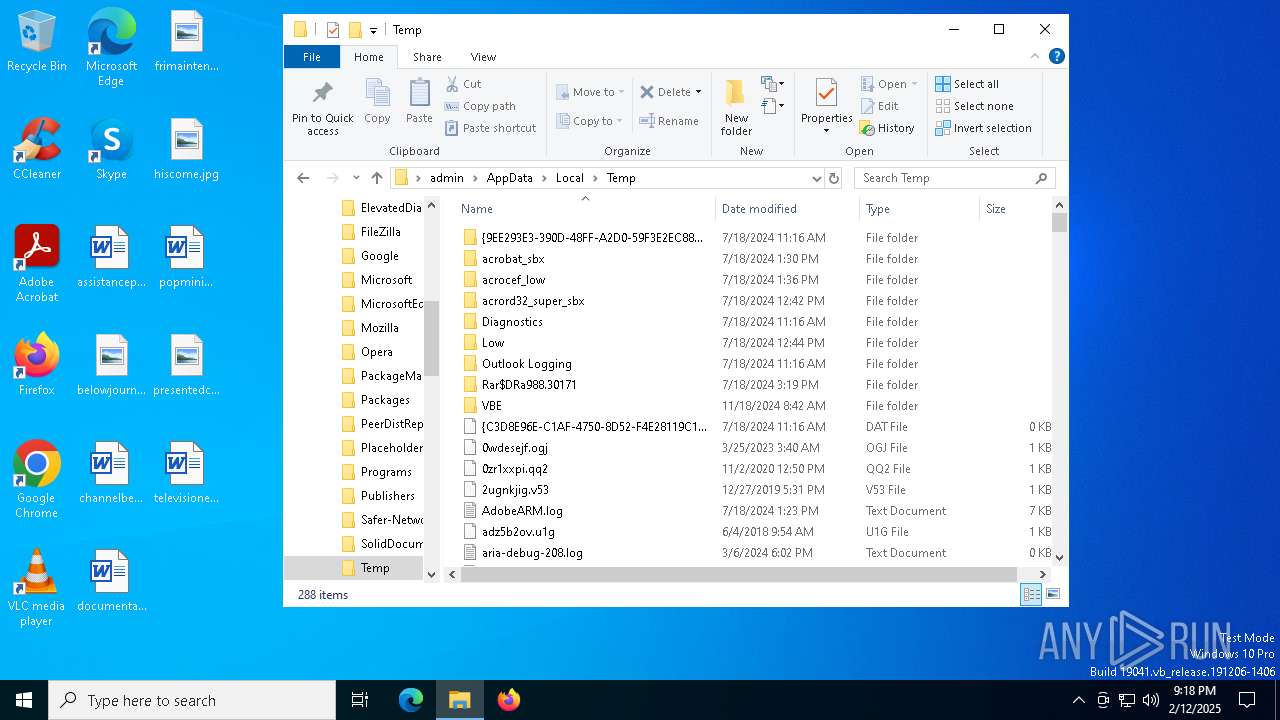
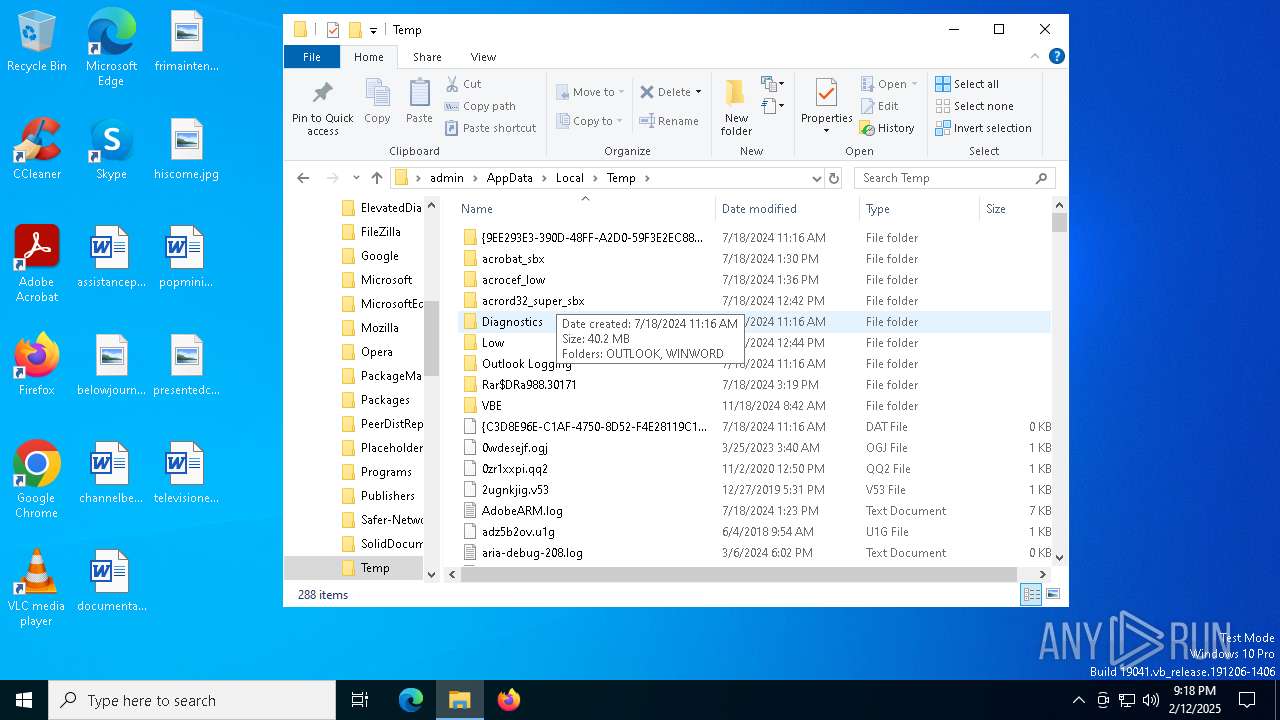
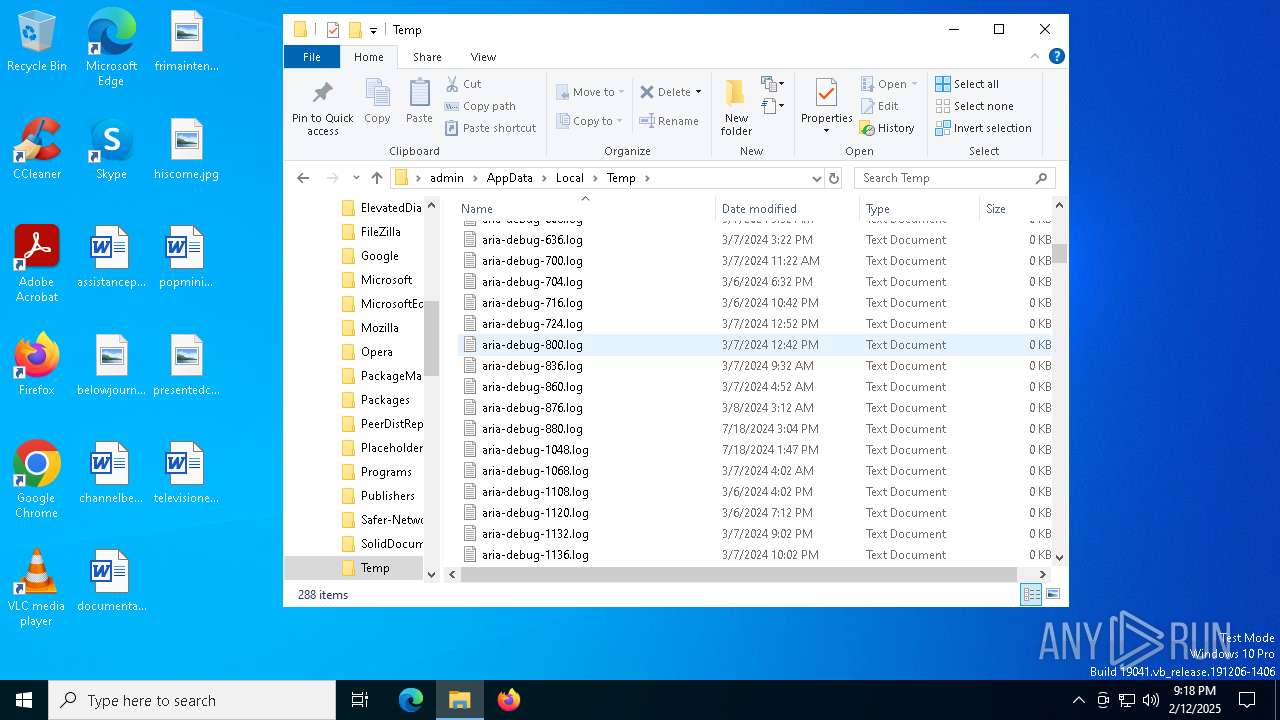
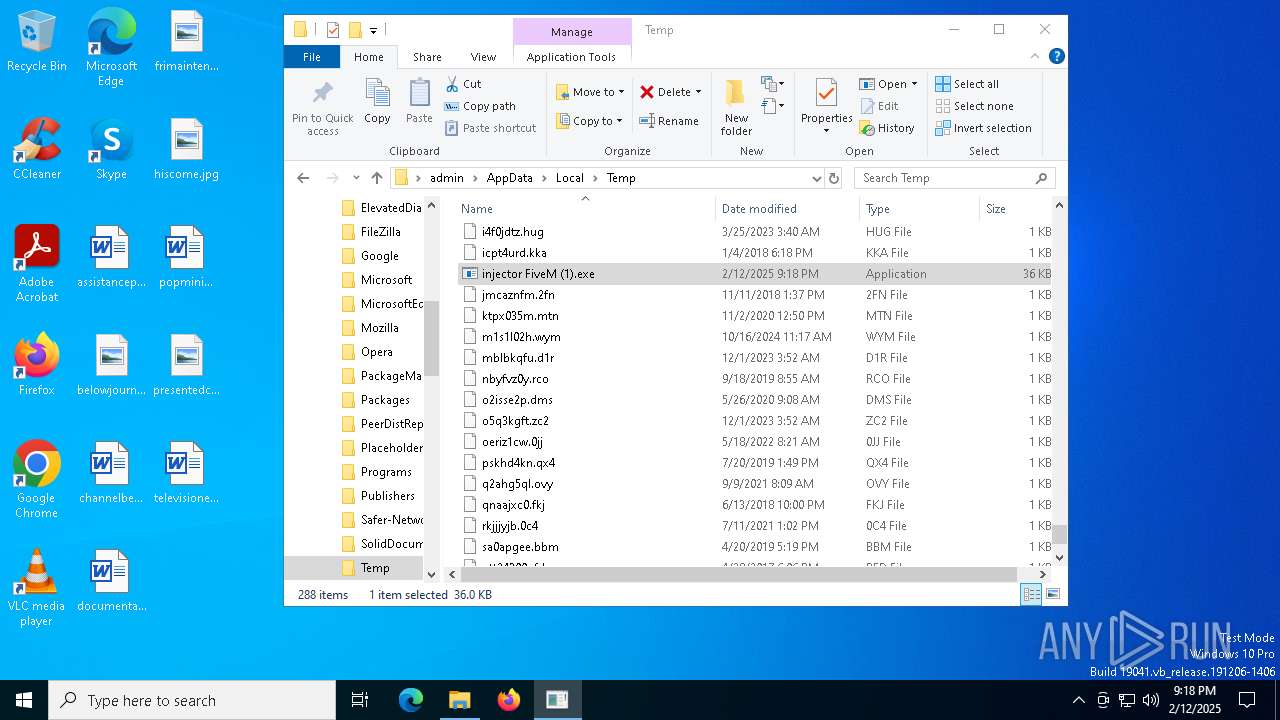
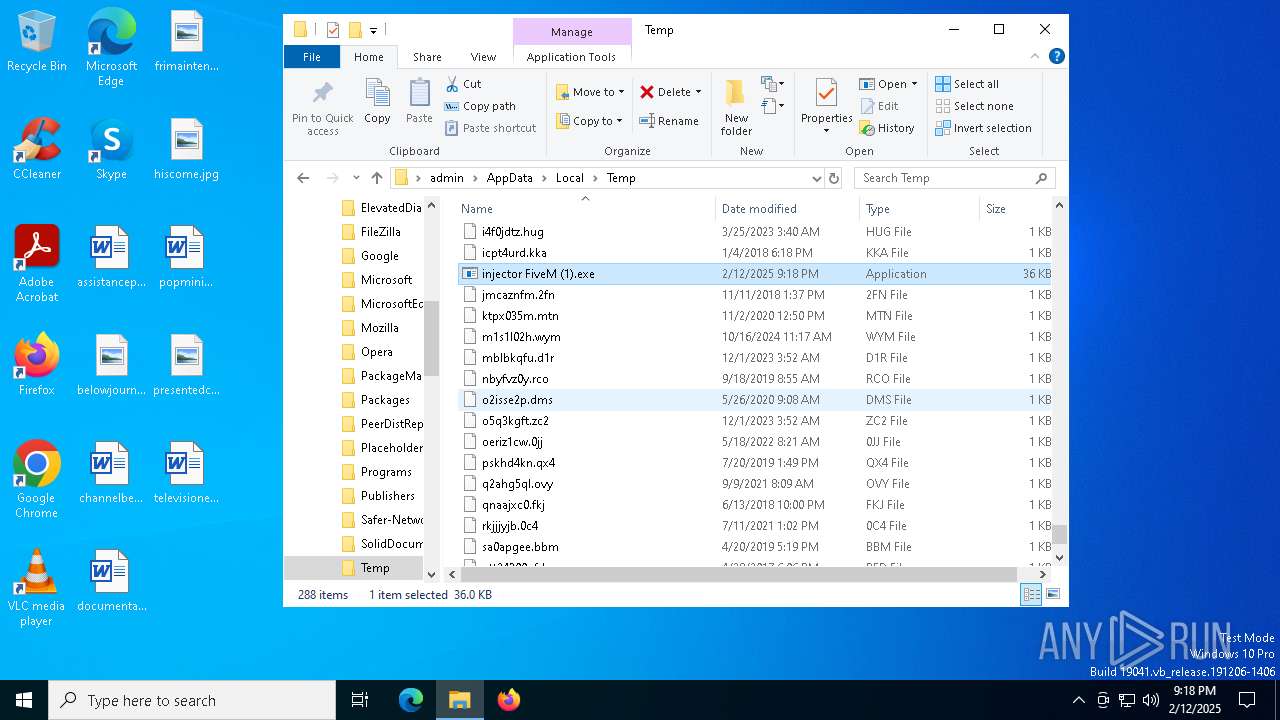
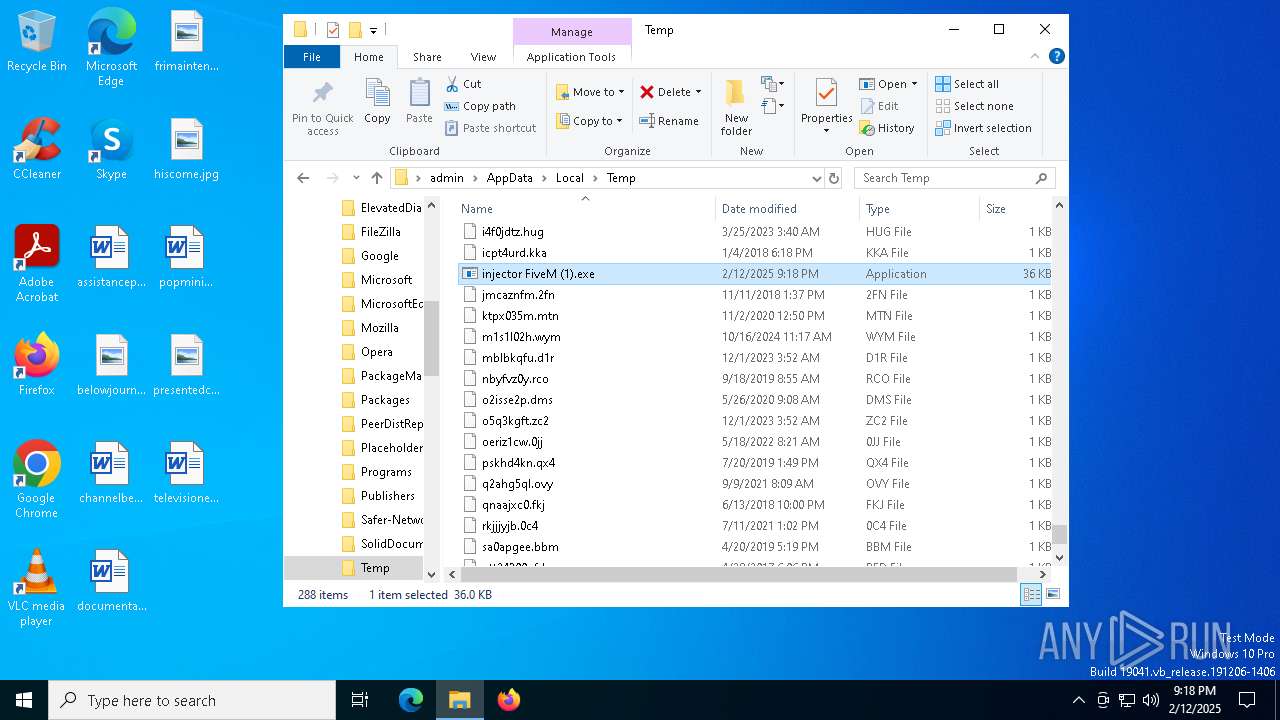
Creates files or folders in the user directory
- injector FiveM (1).exe (PID: 6500)
Reads the machine GUID from the registry
- injector FiveM (1).exe (PID: 6500)
- injector FiveM (1).exe (PID: 3816)
Reads the software policy settings
- injector FiveM (1).exe (PID: 6500)
- injector FiveM (1).exe (PID: 3816)
Failed to create an executable file in Windows directory
- injector FiveM (1).exe (PID: 6500)
Checks proxy server information
- injector FiveM (1).exe (PID: 6500)
- injector FiveM (1).exe (PID: 3816)
Reads the computer name
- injector FiveM (1).exe (PID: 6500)
- injector FiveM (1).exe (PID: 3816)
Manual execution by a user
- injector FiveM (1).exe (PID: 3816)
Process checks computer location settings
- injector FiveM (1).exe (PID: 3816)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:02:12 21:00:26+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.38 |
| CodeSize: | 25600 |
| InitializedDataSize: | 11776 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x68d0 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
143
Monitored processes
7
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
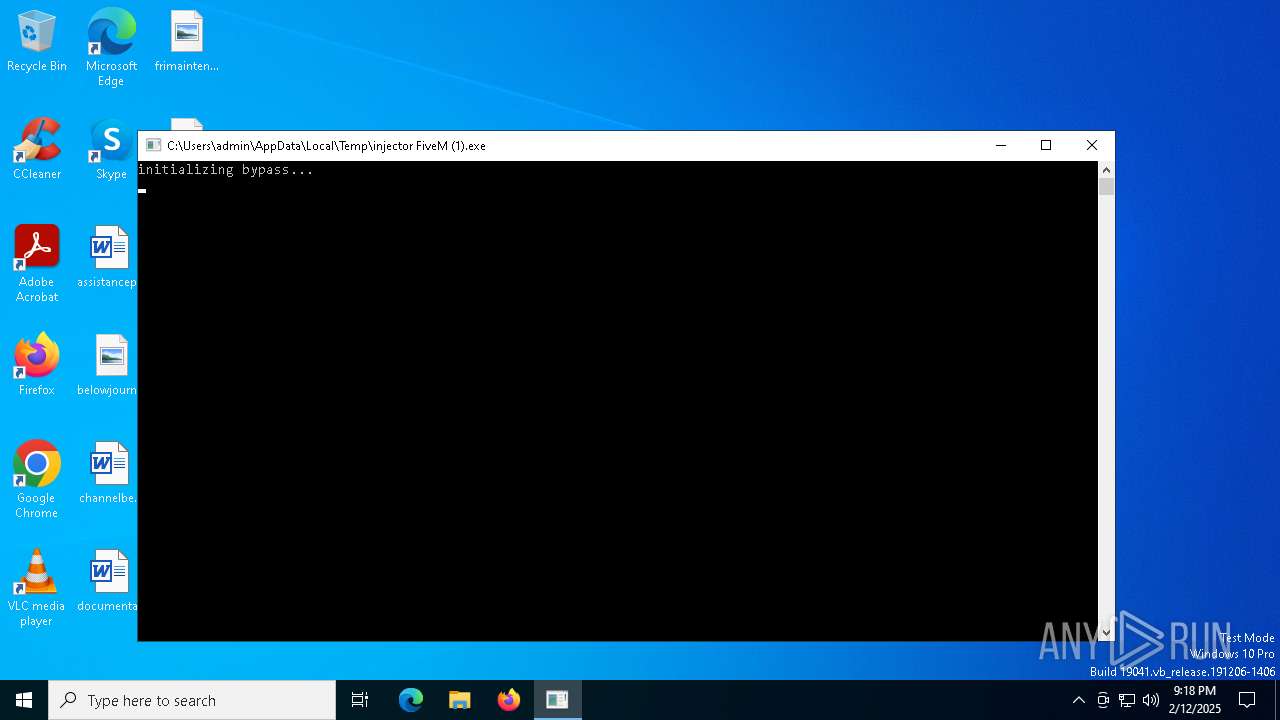
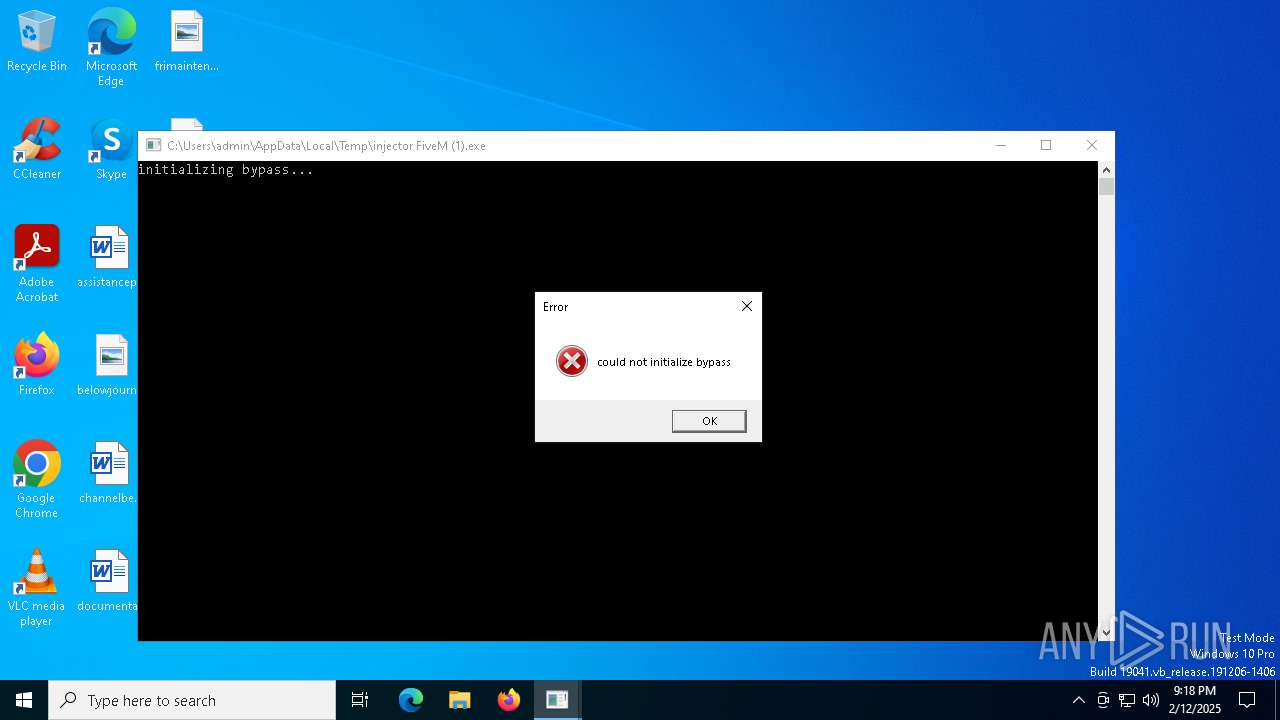
| 3816 | "C:\Users\admin\AppData\Local\Temp\injector FiveM (1).exe" | C:\Users\admin\AppData\Local\Temp\injector FiveM (1).exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 4624 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | injector FiveM (1).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5392 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6500 | "C:\Users\admin\AppData\Local\Temp\injector FiveM (1).exe" | C:\Users\admin\AppData\Local\Temp\injector FiveM (1).exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 6508 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | injector FiveM (1).exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7028 | "C:\WINDOWS\system32\UCPDMgr.exe" | C:\Windows\System32\UCPDMgr.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: User Choice Protection Manager Exit code: 0 Version: 1.0.0.414301 Modules
| |||||||||||||||
| 7132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | UCPDMgr.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 635
Read events
1 629
Write events
6
Delete events
0
Modification events
| (PID) Process: | (6500) injector FiveM (1).exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6500) injector FiveM (1).exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6500) injector FiveM (1).exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3816) injector FiveM (1).exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3816) injector FiveM (1).exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3816) injector FiveM (1).exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
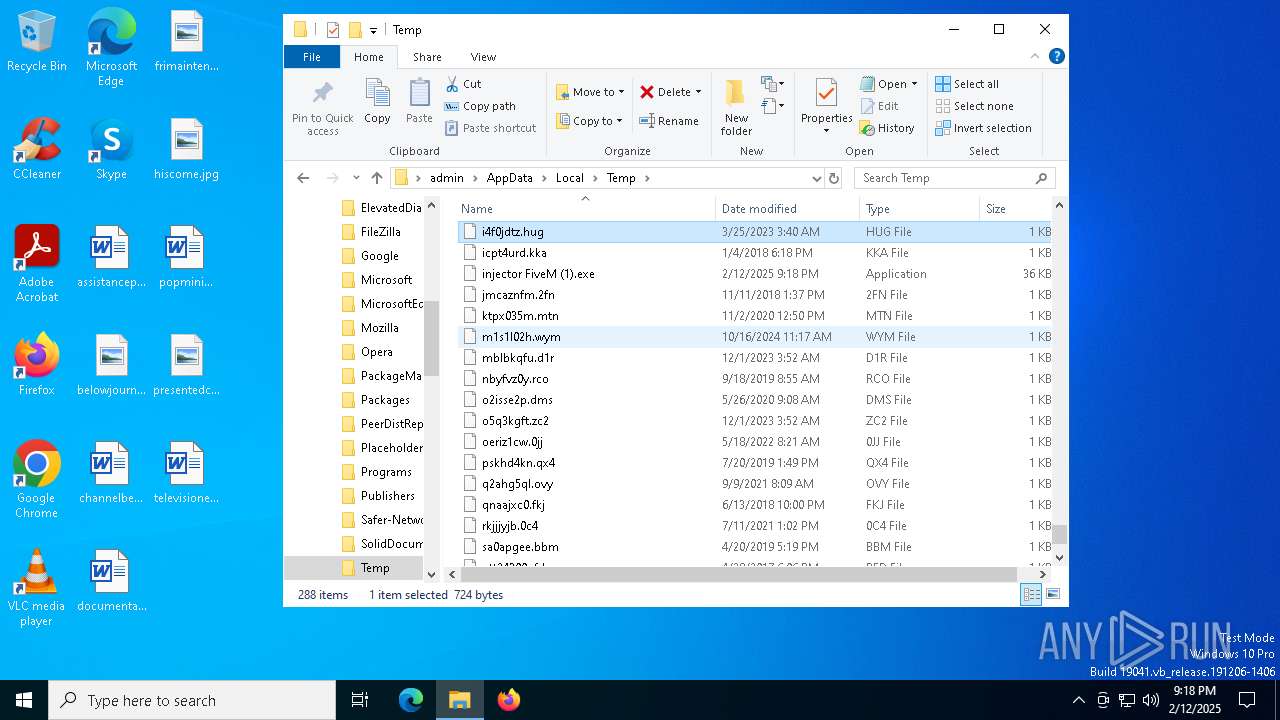
Executable files
0
Suspicious files
4
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6500 | injector FiveM (1).exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:E192462F281446B5D1500D474FBACC4B | SHA256:F1BA9F1B63C447682EBF9DE956D0DA2A027B1B779ABEF9522D347D3479139A60 | |||
| 6500 | injector FiveM (1).exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E61EB46045C11F5B1969320C4C98A9FB | binary | |
MD5:79EFE76EB3C2CCFCCFAF537E4EE619DC | SHA256:FD437877C303AA23384562427F33A289C08586F0A410EE73EC103CDED2BD9C14 | |||
| 6500 | injector FiveM (1).exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\fc96fbf5-4f36-4874-851d-a114d9ab3402[1].htm | html | |
MD5:AA5D13590623ABB5D3963A8AF5DFB85D | SHA256:4C6183029DCF2E4D604C473C2DFB4F72037B6A8F13D9183B0842FD201E422D7A | |||
| 3816 | injector FiveM (1).exe | C:\Windows\IME\5guard.exe | html | |
MD5:AA5D13590623ABB5D3963A8AF5DFB85D | SHA256:4C6183029DCF2E4D604C473C2DFB4F72037B6A8F13D9183B0842FD201E422D7A | |||
| 6500 | injector FiveM (1).exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E61EB46045C11F5B1969320C4C98A9FB | binary | |
MD5:D75093AB1031C06A75542C0704708A46 | SHA256:A3075D752EF69337DDCBA3F25A47C2CBA222ABC49D0B3930660D72A62A99DE30 | |||
| 6500 | injector FiveM (1).exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:CE196617B8D9A777B42BD9229F19F855 | SHA256:C5BC1C42B8B0E22D116FE0816978A793AB5603677497D97F5881C7219EAB6102 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
54
DNS requests
25
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4328 | svchost.exe | GET | 200 | 23.2.13.147:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 23.42.70.18:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4328 | svchost.exe | GET | 200 | 23.3.109.244:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 23.42.70.18:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6500 | injector FiveM (1).exe | GET | 200 | 23.3.109.48:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
3364 | SIHClient.exe | GET | 200 | 23.3.109.244:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6500 | injector FiveM (1).exe | GET | 200 | 92.122.244.8:80 | http://r10.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRpD%2BQVZ%2B1vf7U0RGQGBm8JZwdxcgQUdKR2KRcYVIUxN75n5gZYwLzFBXICEgQ3YOHvIdIvrlMKn5LcLrJVoQ%3D%3D | unknown | — | — | whitelisted |
6352 | backgroundTaskHost.exe | GET | 200 | 23.42.70.18:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
3364 | SIHClient.exe | GET | 200 | 23.3.109.244:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4328 | svchost.exe | 23.2.13.147:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4328 | svchost.exe | 23.3.109.244:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.19.193.136:443 | www.bing.com | Akamai International B.V. | TR | whitelisted |
5064 | SearchApp.exe | 23.42.70.18:80 | ocsp.digicert.com | AKAMAI-AS | JP | whitelisted |
1176 | svchost.exe | 20.190.160.131:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 23.42.70.18:80 | ocsp.digicert.com | AKAMAI-AS | JP | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
store-eu-par-4.gofile.io |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r10.o.lencr.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
6500 | injector FiveM (1).exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
6500 | injector FiveM (1).exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
— | — | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
3816 | injector FiveM (1).exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
3816 | injector FiveM (1).exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |