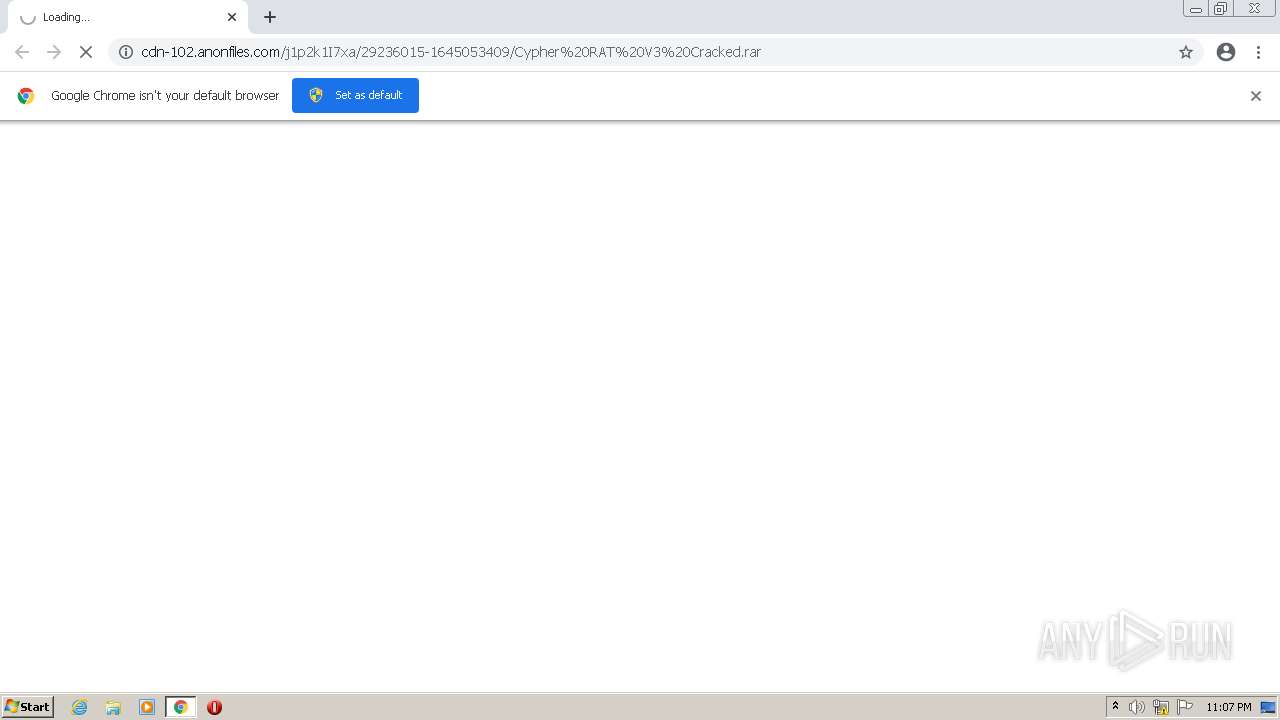
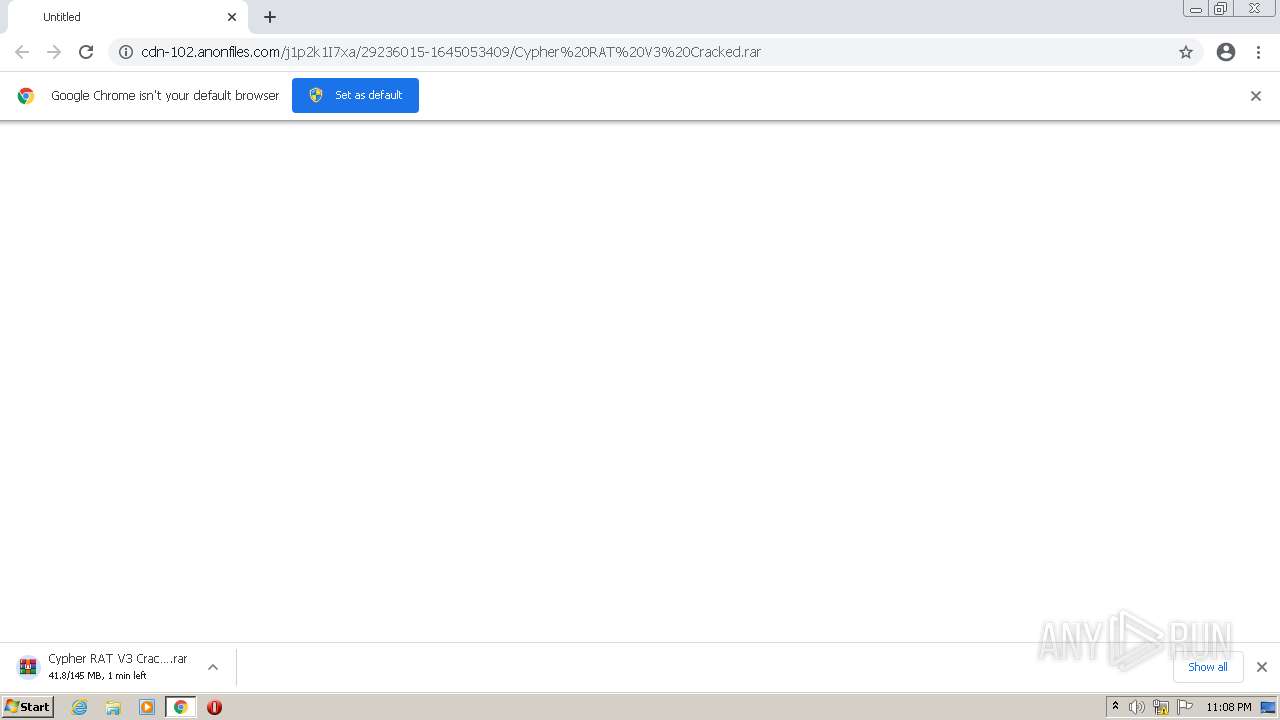
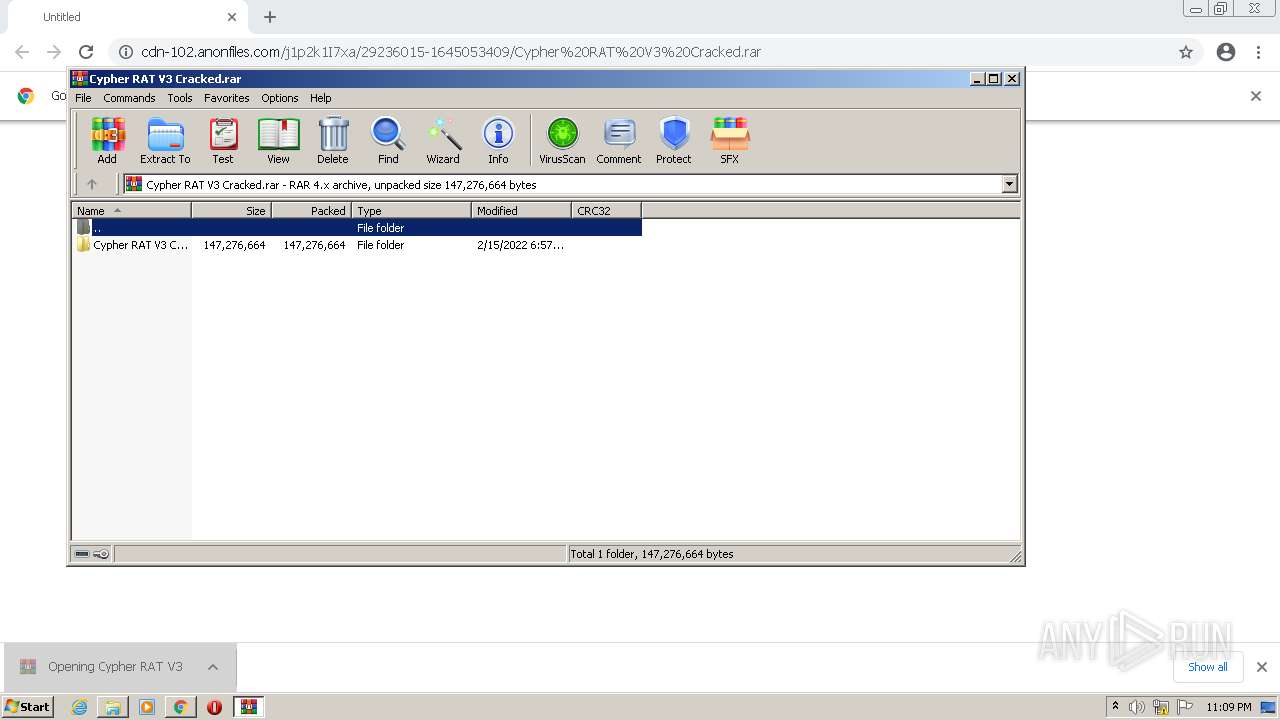
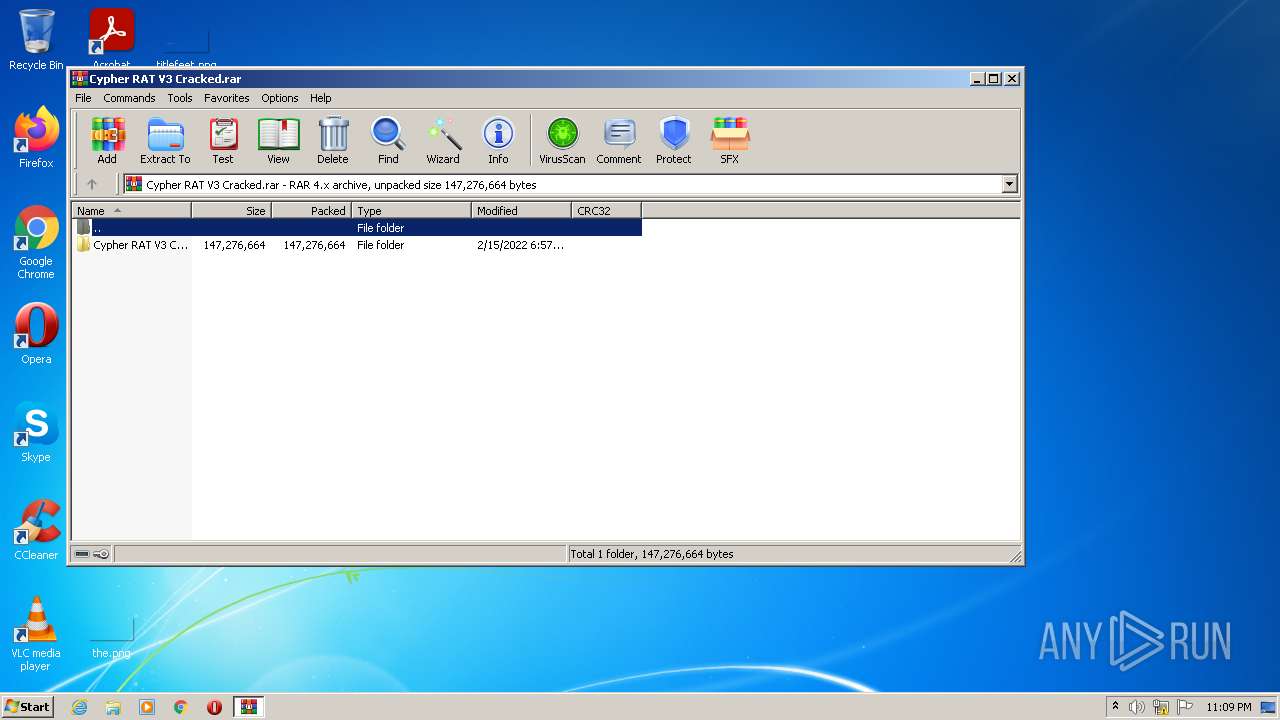
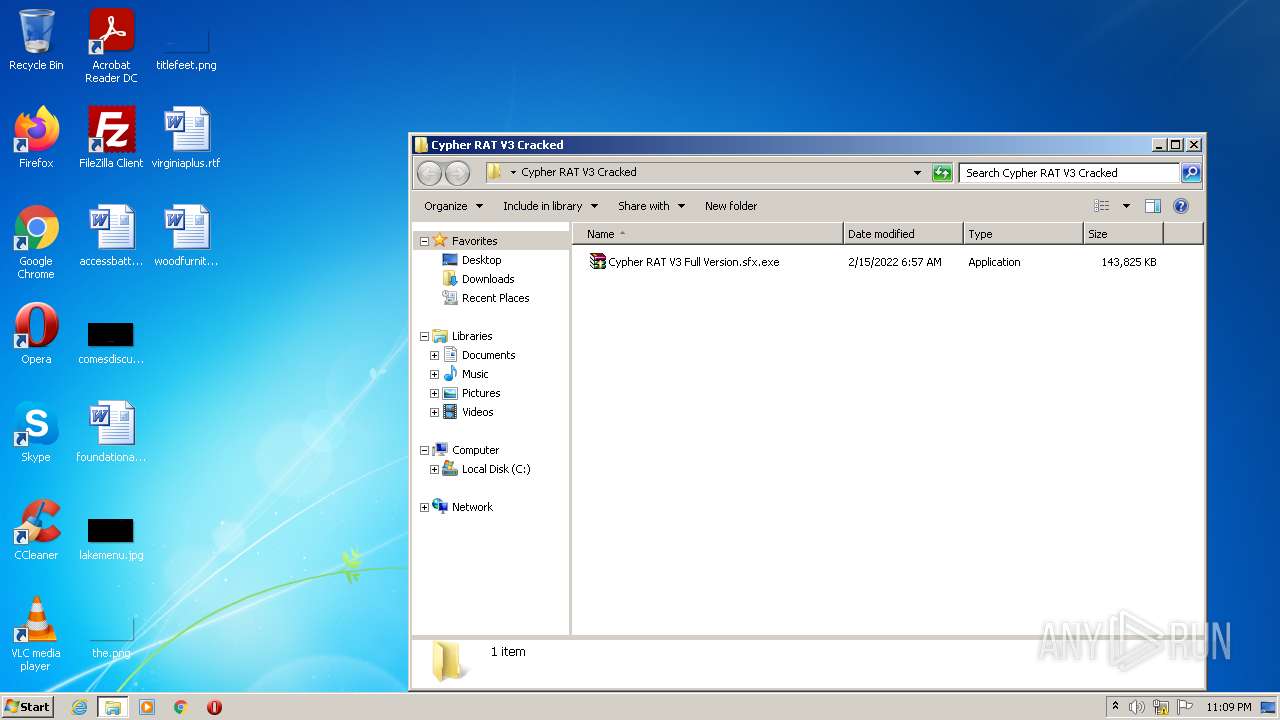
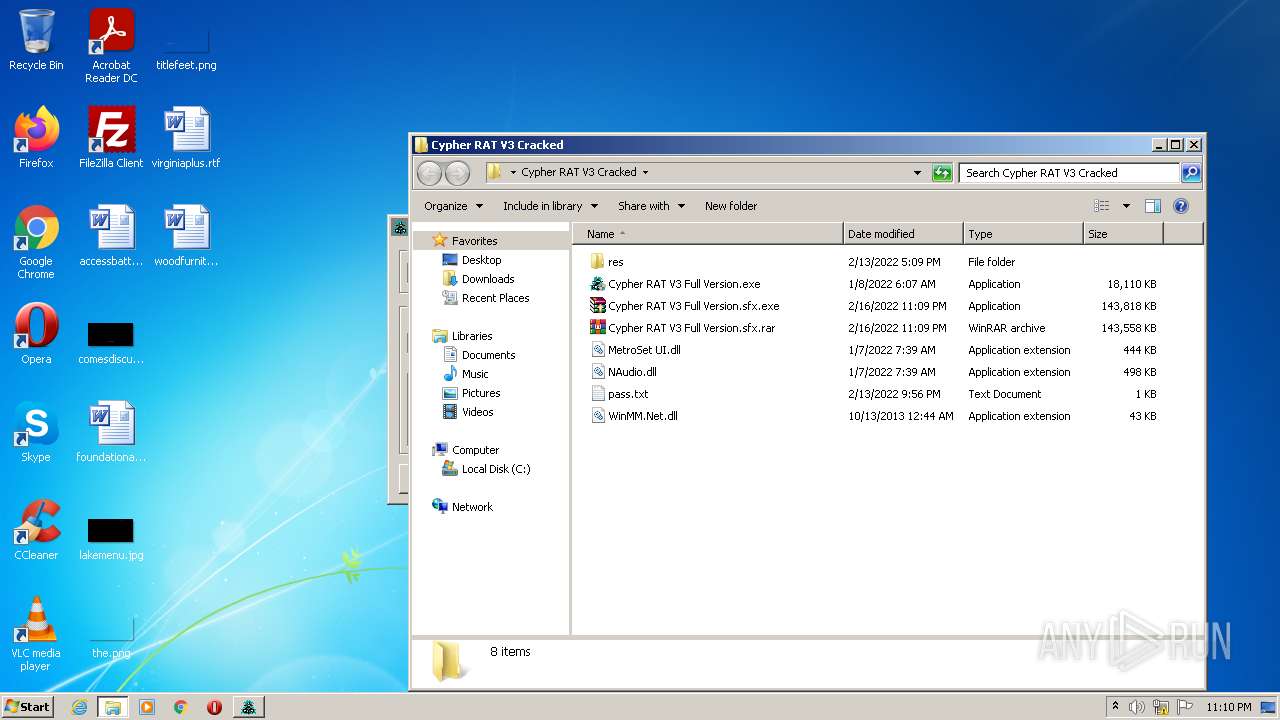
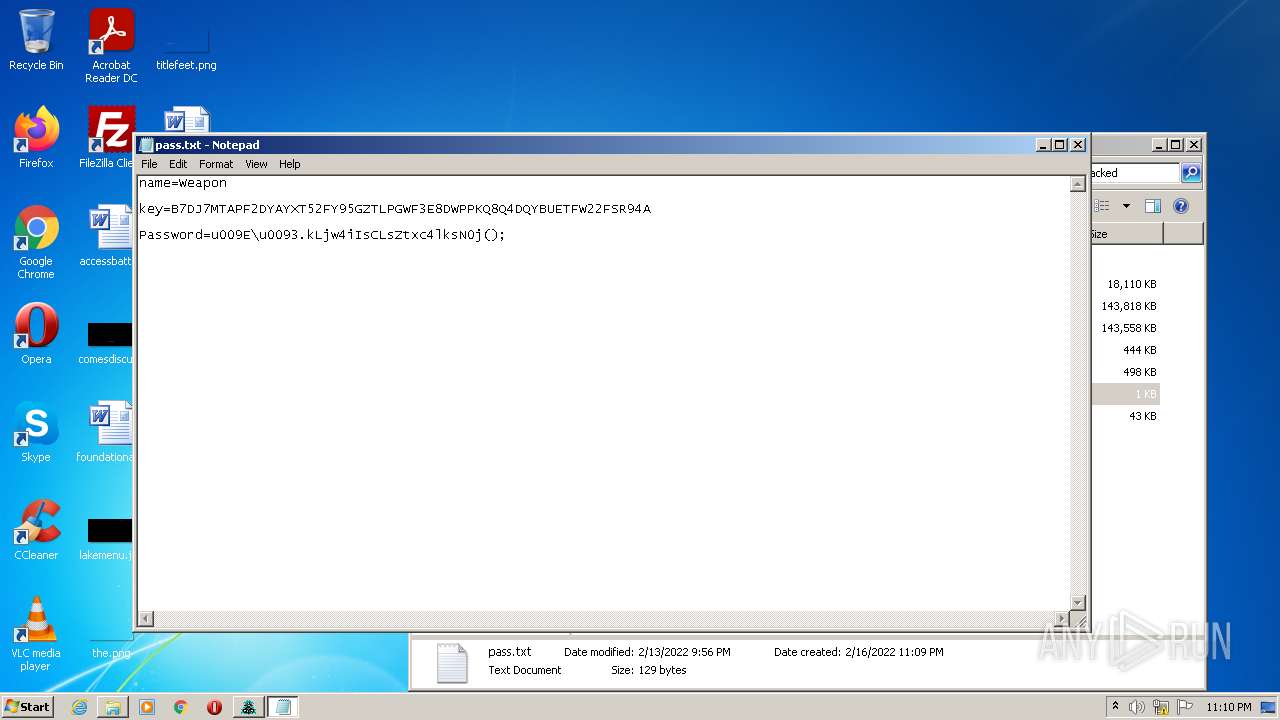
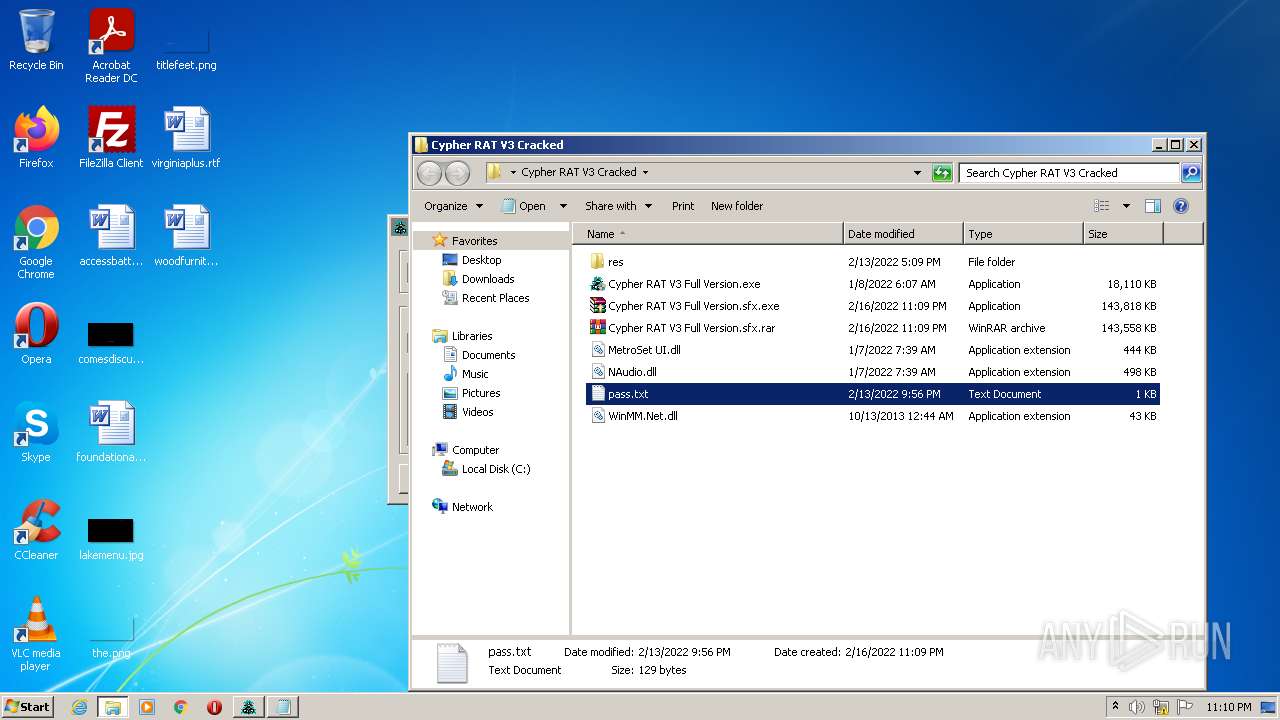
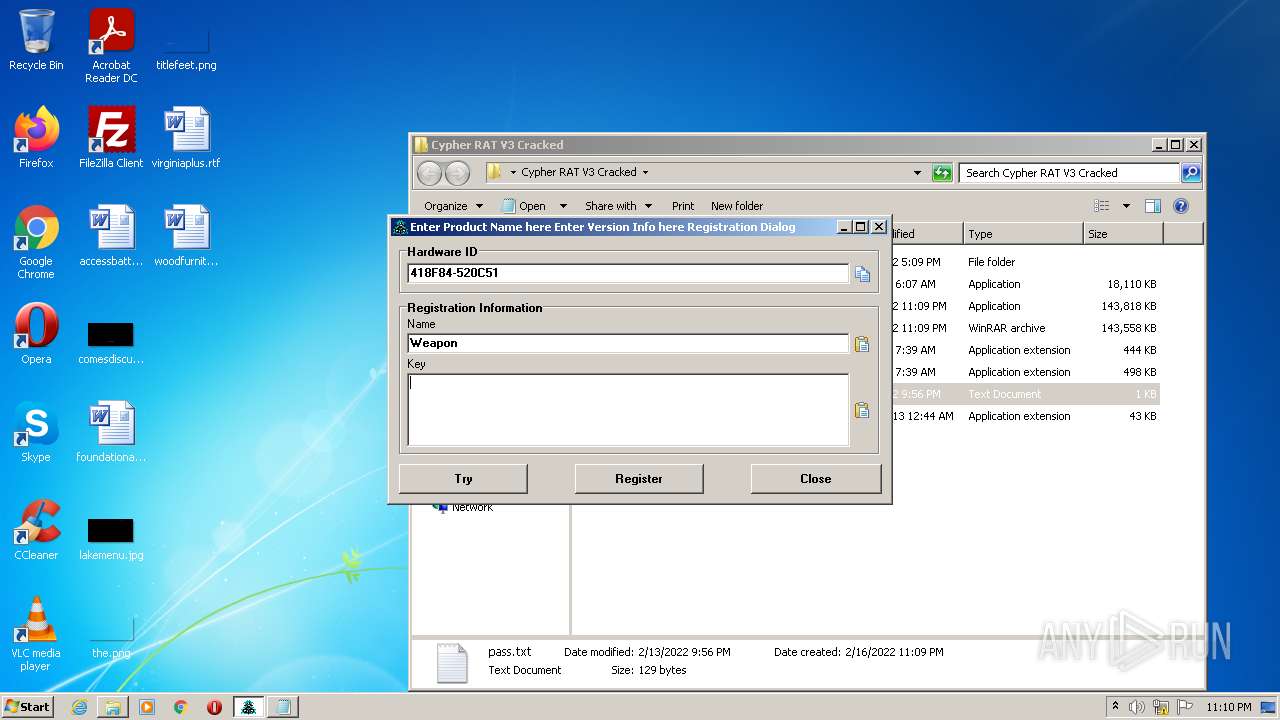
| URL: | https://cdn-102.anonfiles.com/j1p2k1I7xa/29236015-1645053409/Cypher%20RAT%20V3%20Cracked.rar |
| Full analysis: | https://app.any.run/tasks/c9db4bad-c1f7-4833-9172-e8f7afdd32c5 |
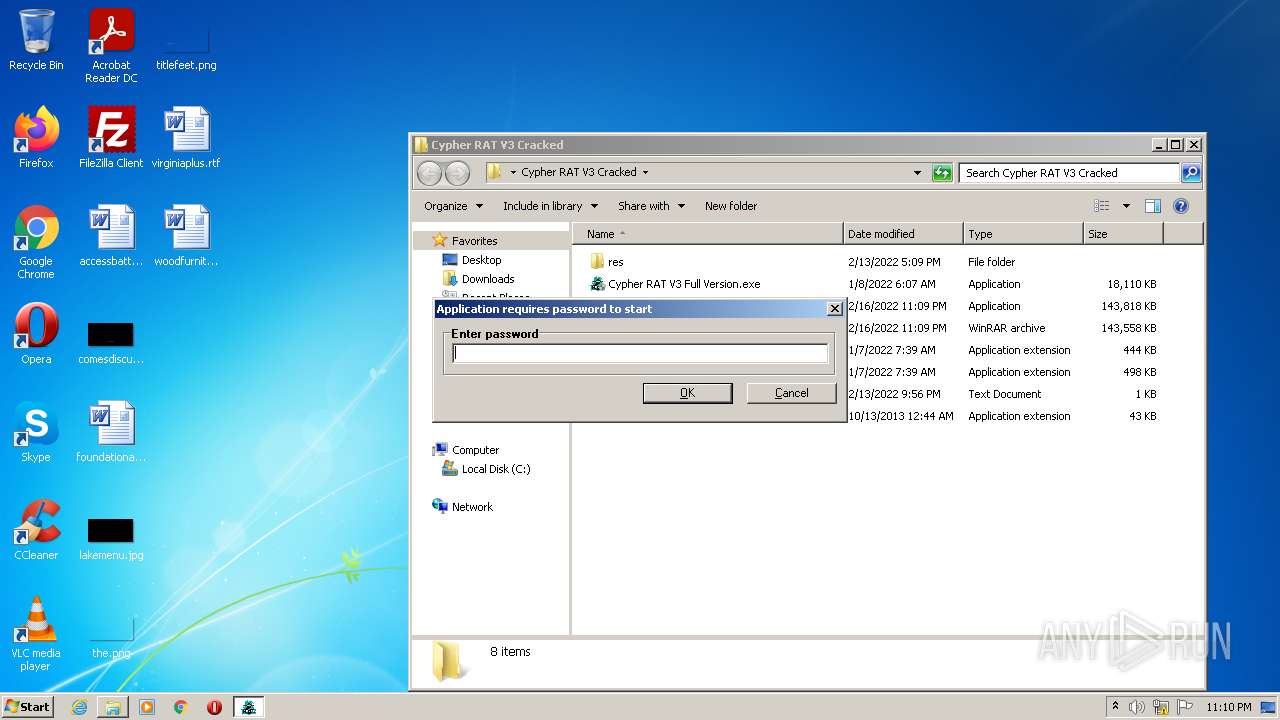
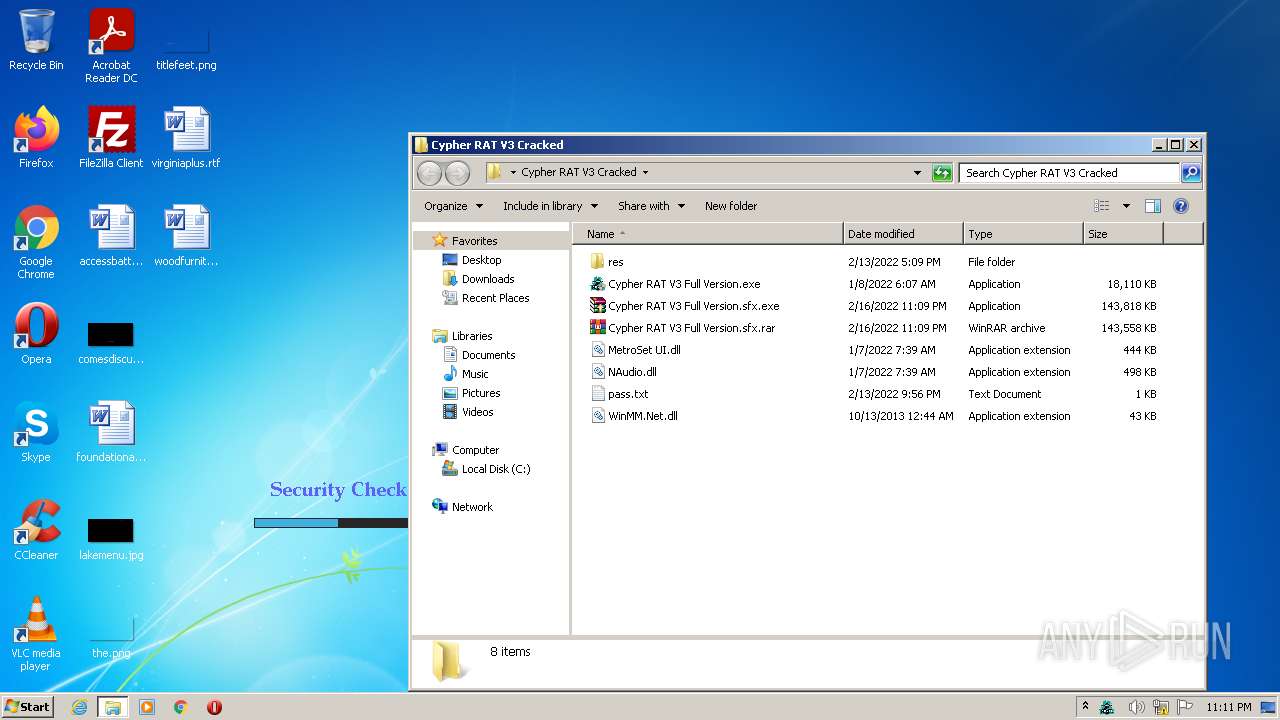
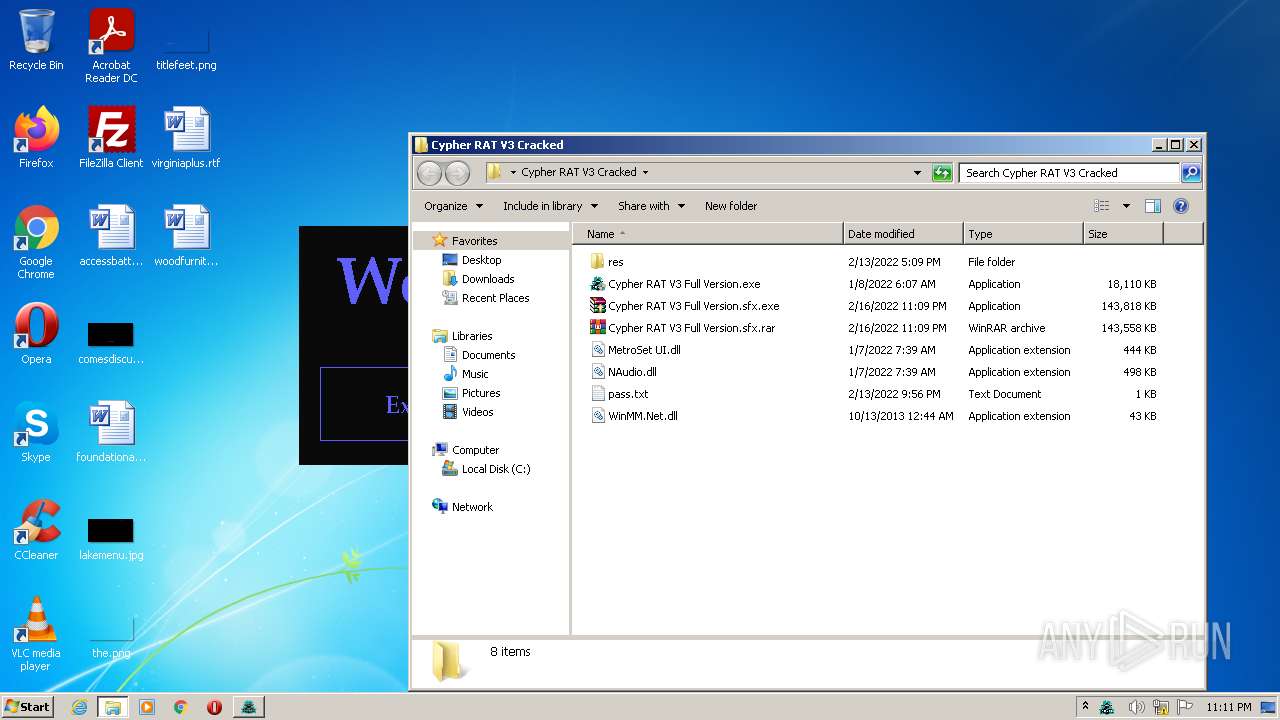
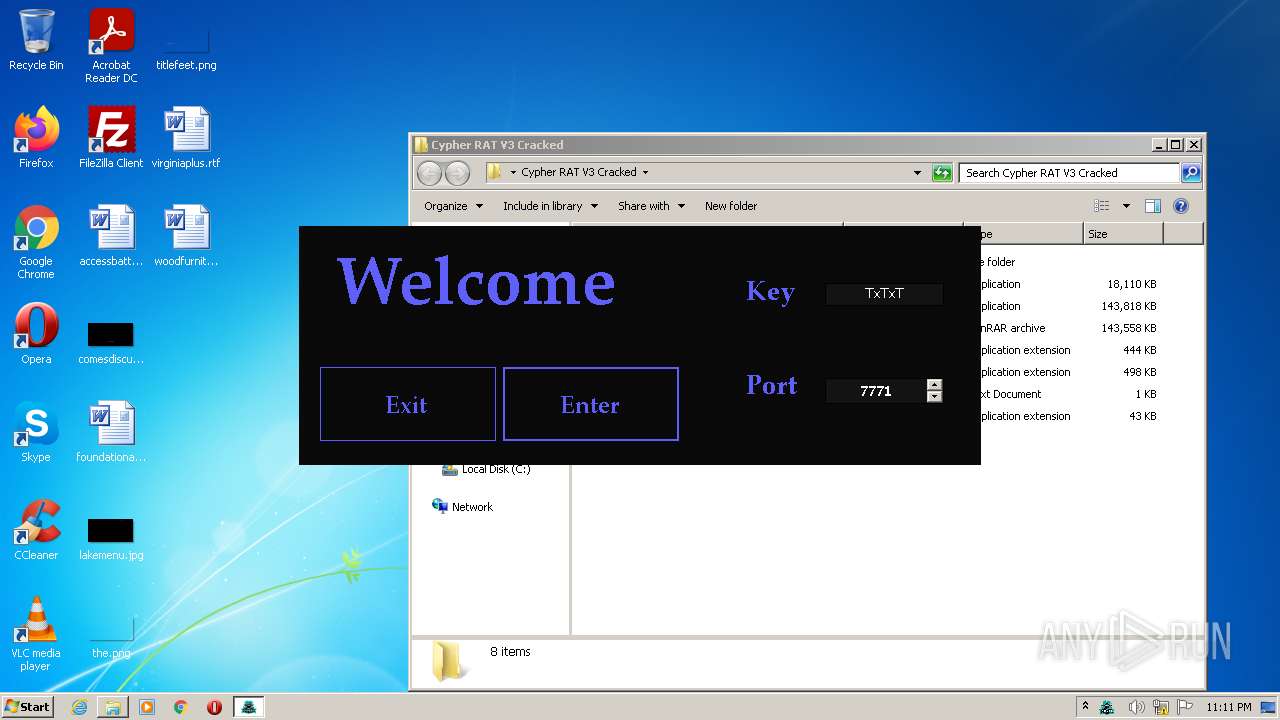
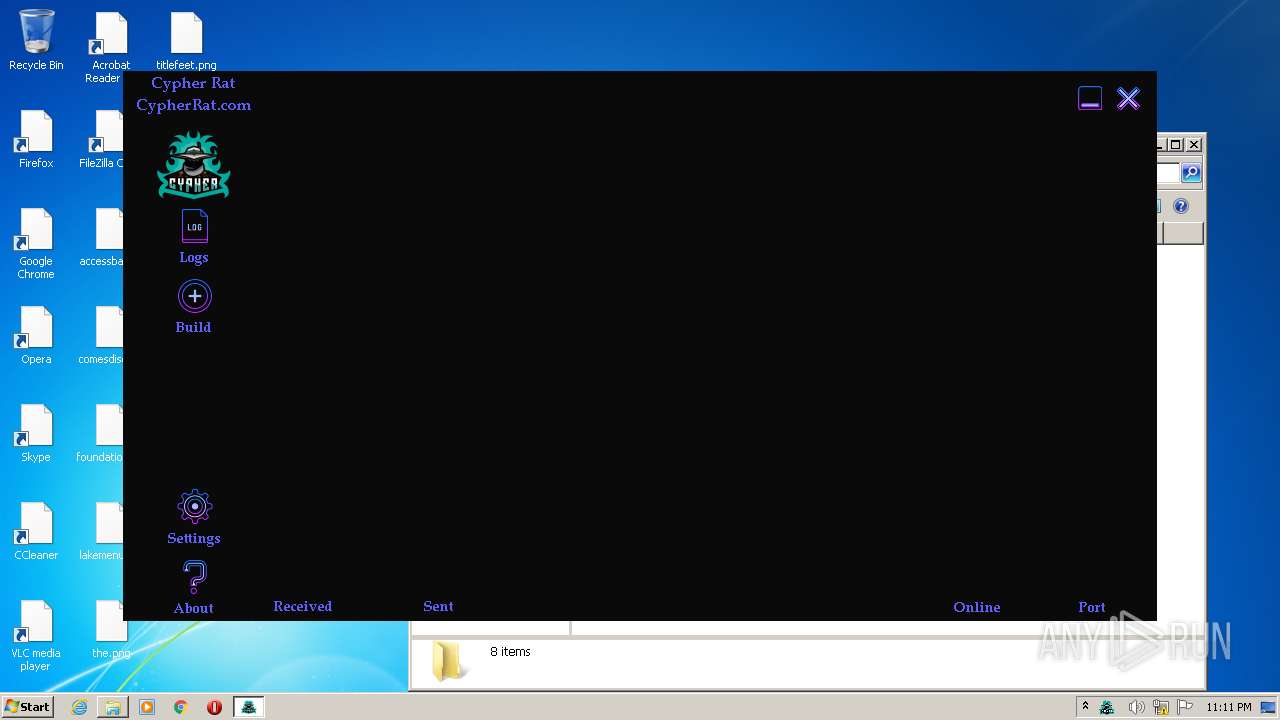
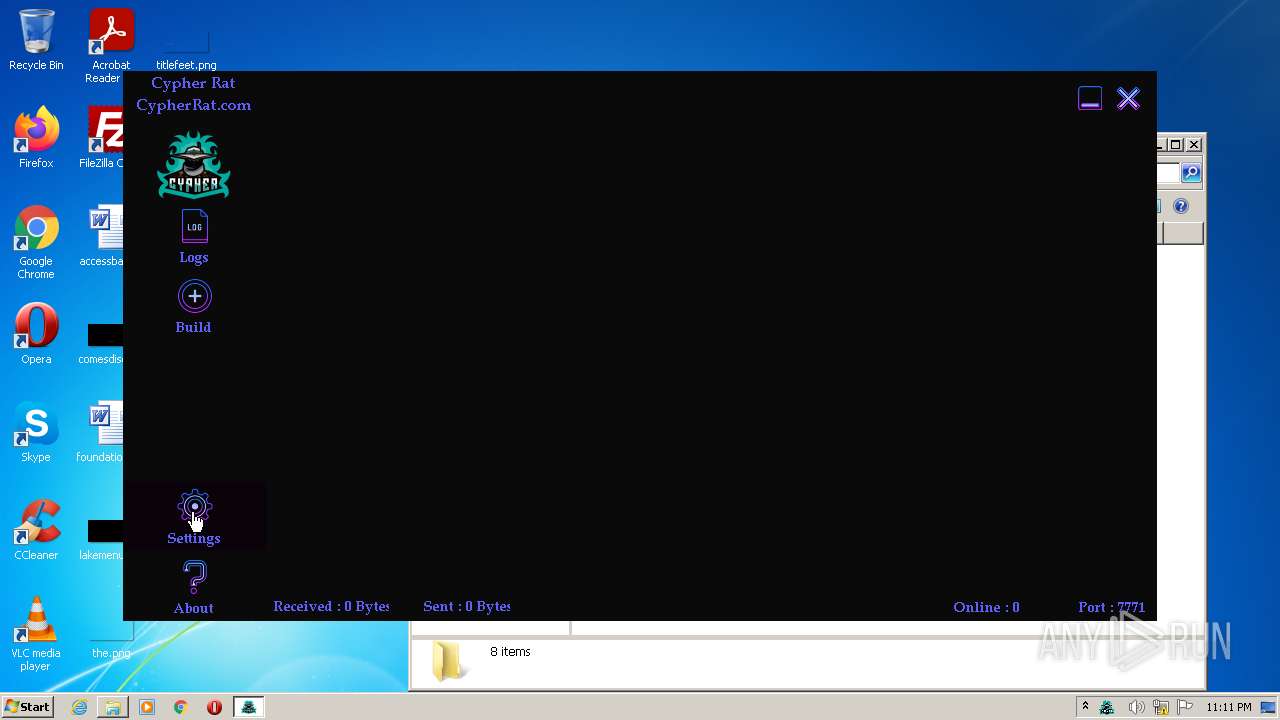
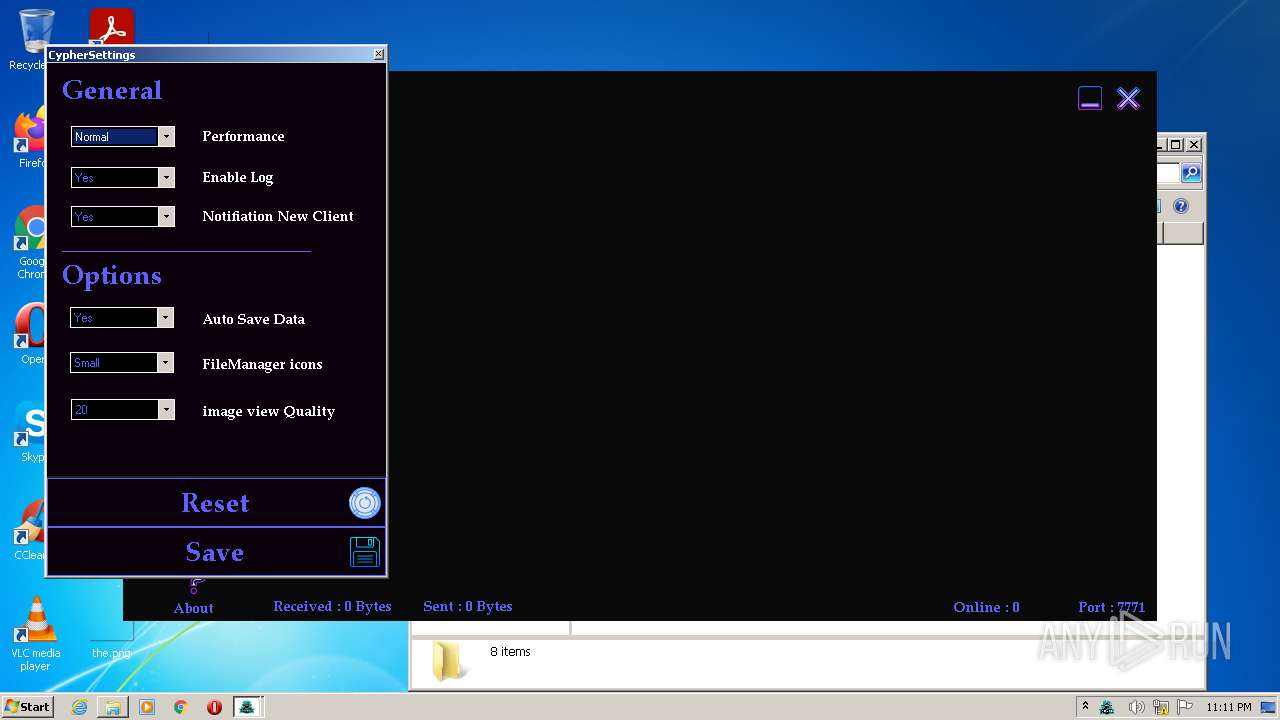
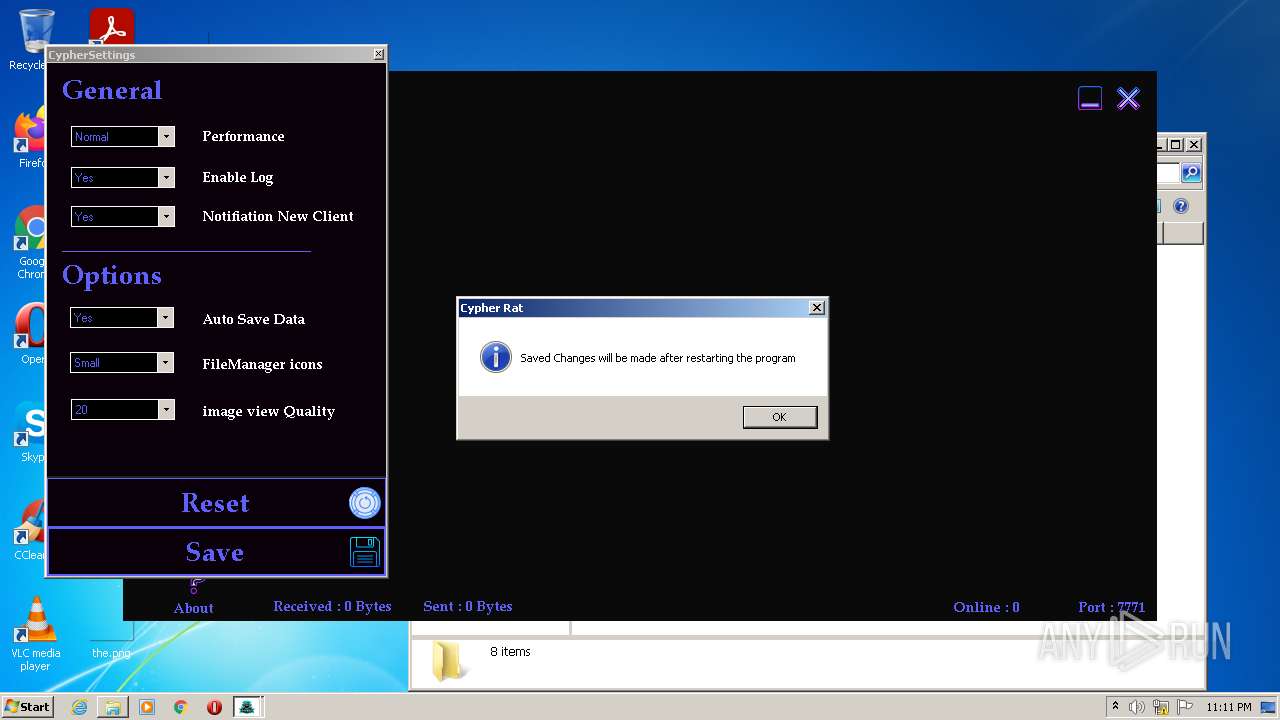
| Verdict: | Malicious activity |
| Analysis date: | February 16, 2022, 23:07:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 189ADC115A526CA8F4FF20B5F77729E5 |
| SHA1: | 9E7CC76E8C7B6C7953BB0173FC237934C8942F2F |
| SHA256: | ACFDCB7111CF6C60E2A00E02D83FE748662D5872109CD51FFEA88CEE72CA3E71 |
| SSDEEP: | 3:N8cFVg52UUVXeC+tVN227/BZUEX:2cFM2NVXeC+tzlx |
MALICIOUS
Drops executable file immediately after starts
- Explorer.EXE (PID: 1096)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3312)
- Explorer.EXE (PID: 1096)
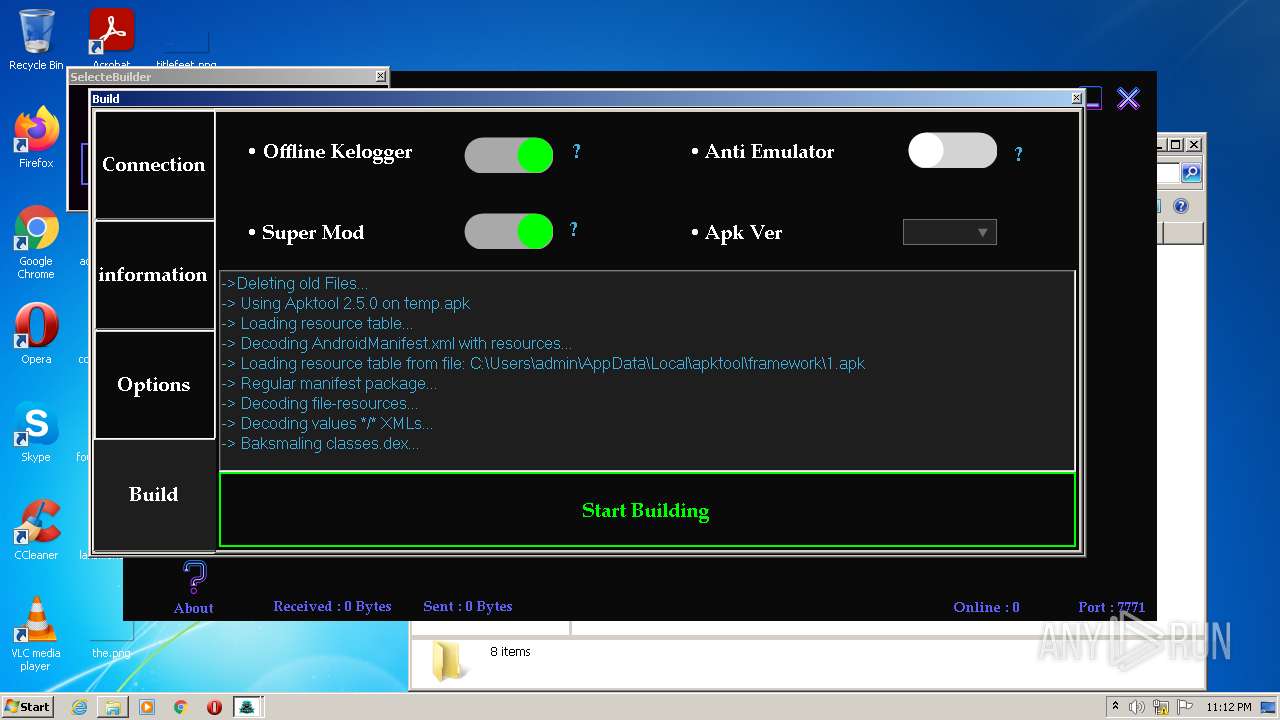
- Cypher RAT V3 Full Version.exe (PID: 3708)
- cmd.exe (PID: 3296)
- java.exe (PID: 2976)
- java.exe (PID: 1696)
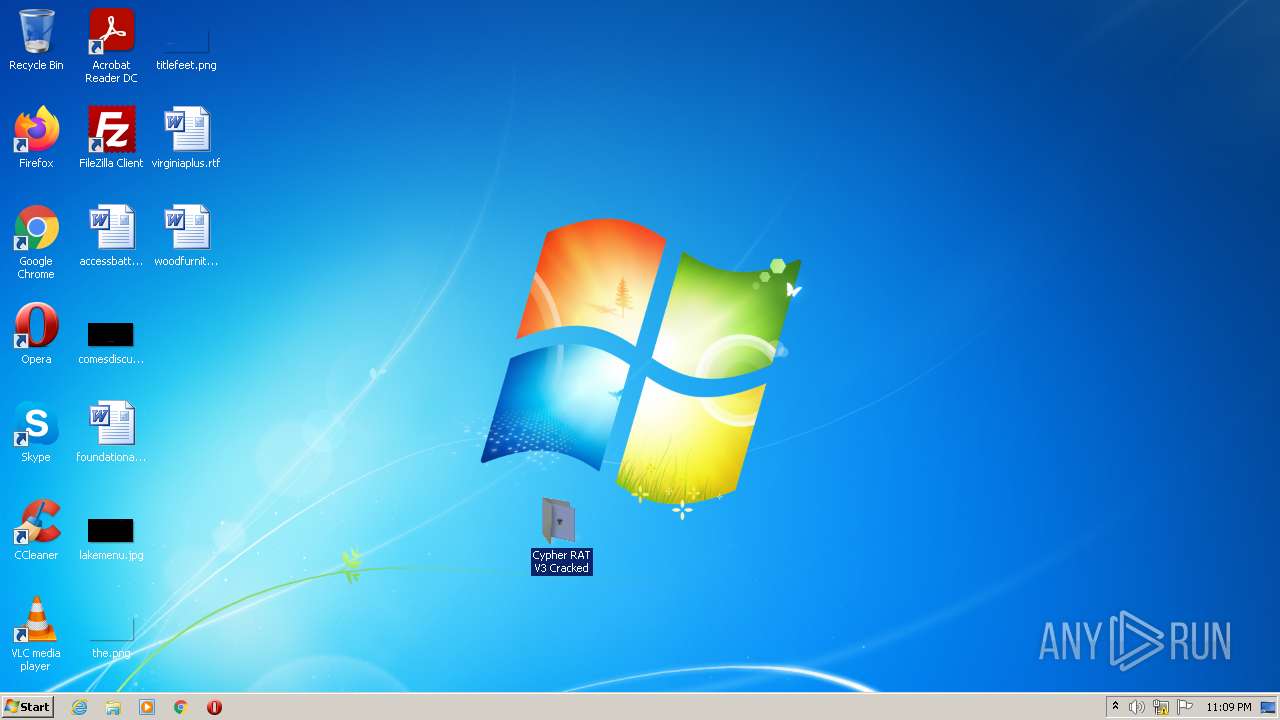
Application was dropped or rewritten from another process
- Cypher RAT V3 Full Version.exe (PID: 2700)
- Cypher RAT V3 Full Version.exe (PID: 3708)
- java.exe (PID: 2976)
- java.exe (PID: 1696)
Runs app for hidden code execution
- Cypher RAT V3 Full Version.exe (PID: 3708)
SUSPICIOUS
Reads the computer name
- WinRAR.exe (PID: 3912)
- WinRAR.exe (PID: 3904)
- Cypher RAT V3 Full Version.exe (PID: 3708)
- java.exe (PID: 1696)
Checks supported languages
- WinRAR.exe (PID: 3904)
- WinRAR.exe (PID: 3912)
- Cypher RAT V3 Full Version.exe (PID: 3708)
- java.exe (PID: 1696)
- cmd.exe (PID: 3296)
- java.exe (PID: 2976)
Creates files in the user directory
- Explorer.EXE (PID: 1096)
- Cypher RAT V3 Full Version.exe (PID: 3708)
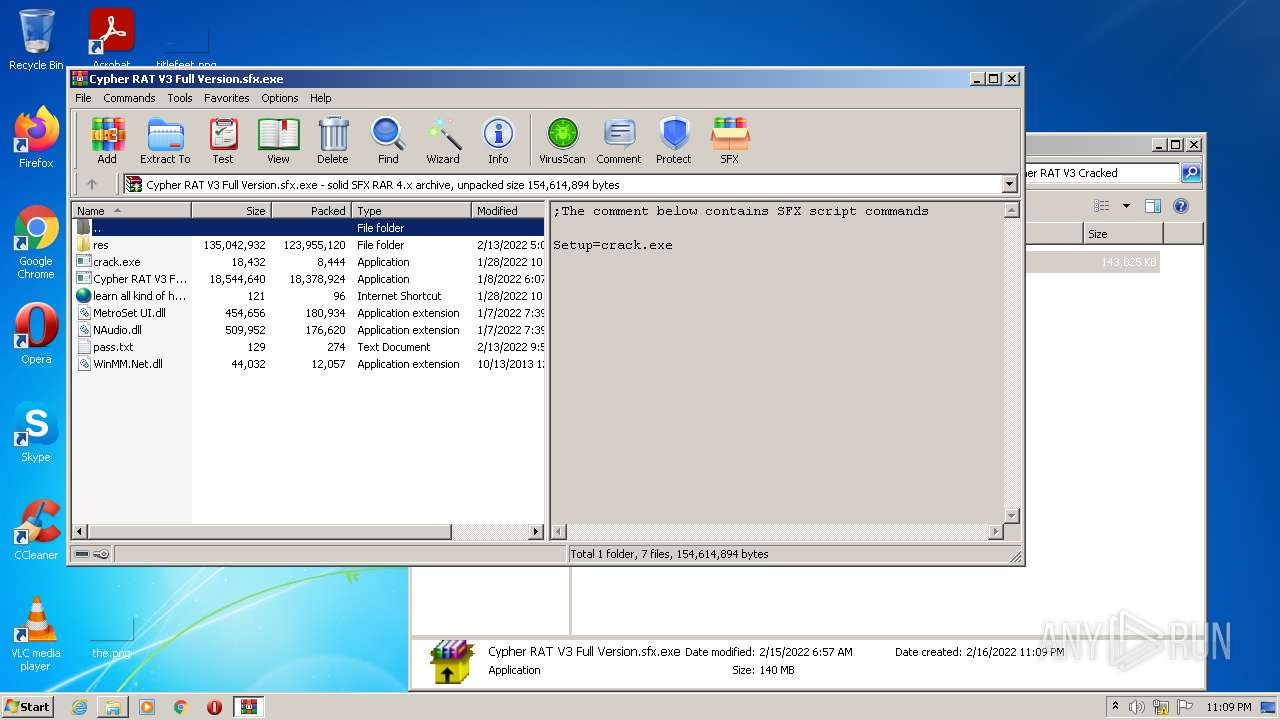
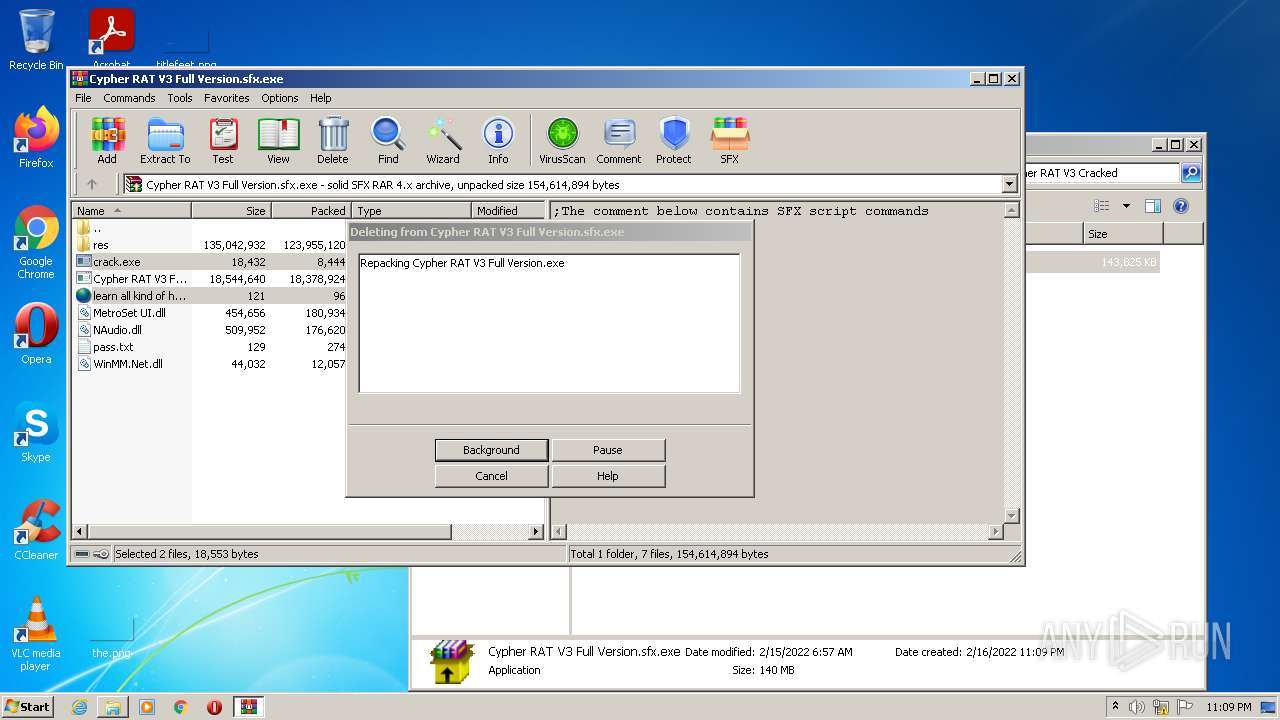
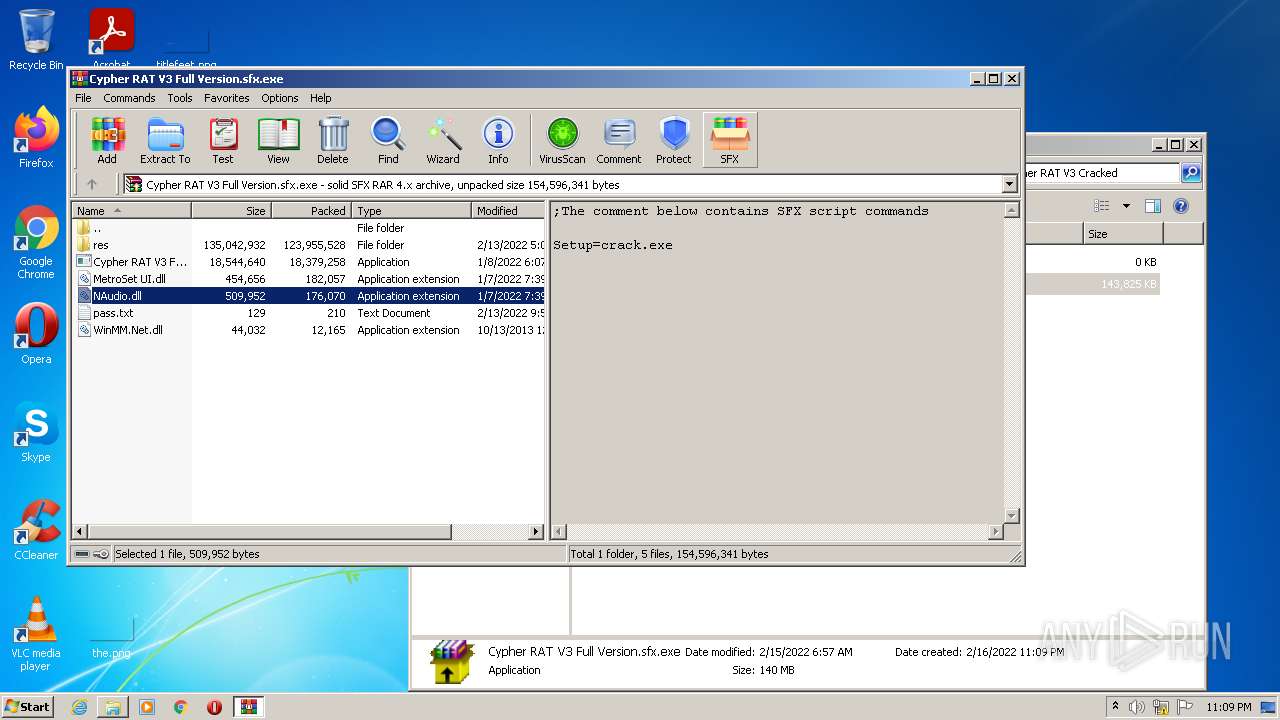
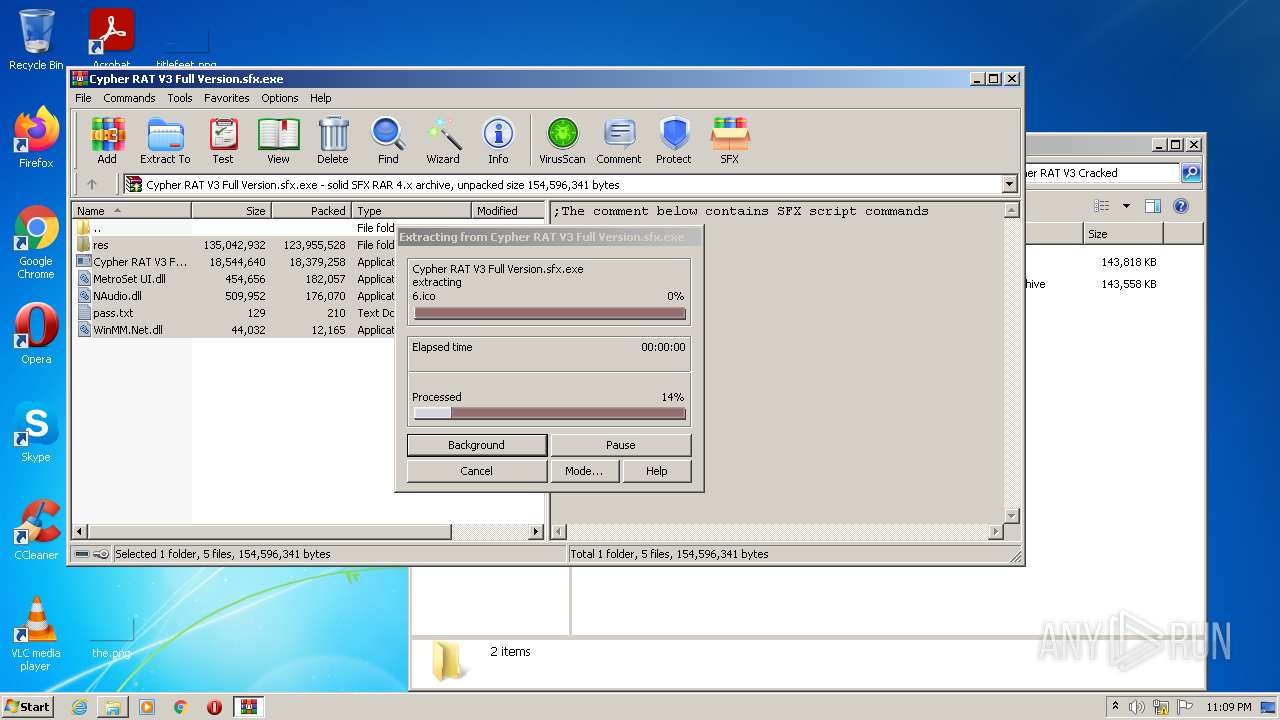
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3912)
- Explorer.EXE (PID: 1096)
- Cypher RAT V3 Full Version.exe (PID: 3708)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 3912)
- Explorer.EXE (PID: 1096)
- Cypher RAT V3 Full Version.exe (PID: 3708)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 3912)
- Explorer.EXE (PID: 1096)
- Cypher RAT V3 Full Version.exe (PID: 3708)
Reads Environment values
- Cypher RAT V3 Full Version.exe (PID: 3708)
Reads default file associations for system extensions
- Explorer.EXE (PID: 1096)
Starts CMD.EXE for commands execution
- Cypher RAT V3 Full Version.exe (PID: 3708)
INFO
Application launched itself
- chrome.exe (PID: 3724)
Checks supported languages
- chrome.exe (PID: 3724)
- chrome.exe (PID: 3100)
- chrome.exe (PID: 1040)
- chrome.exe (PID: 1444)
- chrome.exe (PID: 2112)
- chrome.exe (PID: 2168)
- chrome.exe (PID: 596)
- chrome.exe (PID: 3840)
- chrome.exe (PID: 3936)
- chrome.exe (PID: 404)
- chrome.exe (PID: 2896)
- chrome.exe (PID: 3068)
- chrome.exe (PID: 3120)
- chrome.exe (PID: 1072)
- chrome.exe (PID: 2428)
- chrome.exe (PID: 2068)
- NOTEPAD.EXE (PID: 3292)
Reads the computer name
- chrome.exe (PID: 3724)
- chrome.exe (PID: 1040)
- chrome.exe (PID: 3840)
- chrome.exe (PID: 1444)
- chrome.exe (PID: 3936)
- chrome.exe (PID: 2896)
- chrome.exe (PID: 1072)
- chrome.exe (PID: 2068)
- chrome.exe (PID: 3120)
- chrome.exe (PID: 404)
Reads the hosts file
- chrome.exe (PID: 3724)
- chrome.exe (PID: 1444)
Reads settings of System Certificates
- chrome.exe (PID: 1444)
Reads the date of Windows installation
- chrome.exe (PID: 2896)
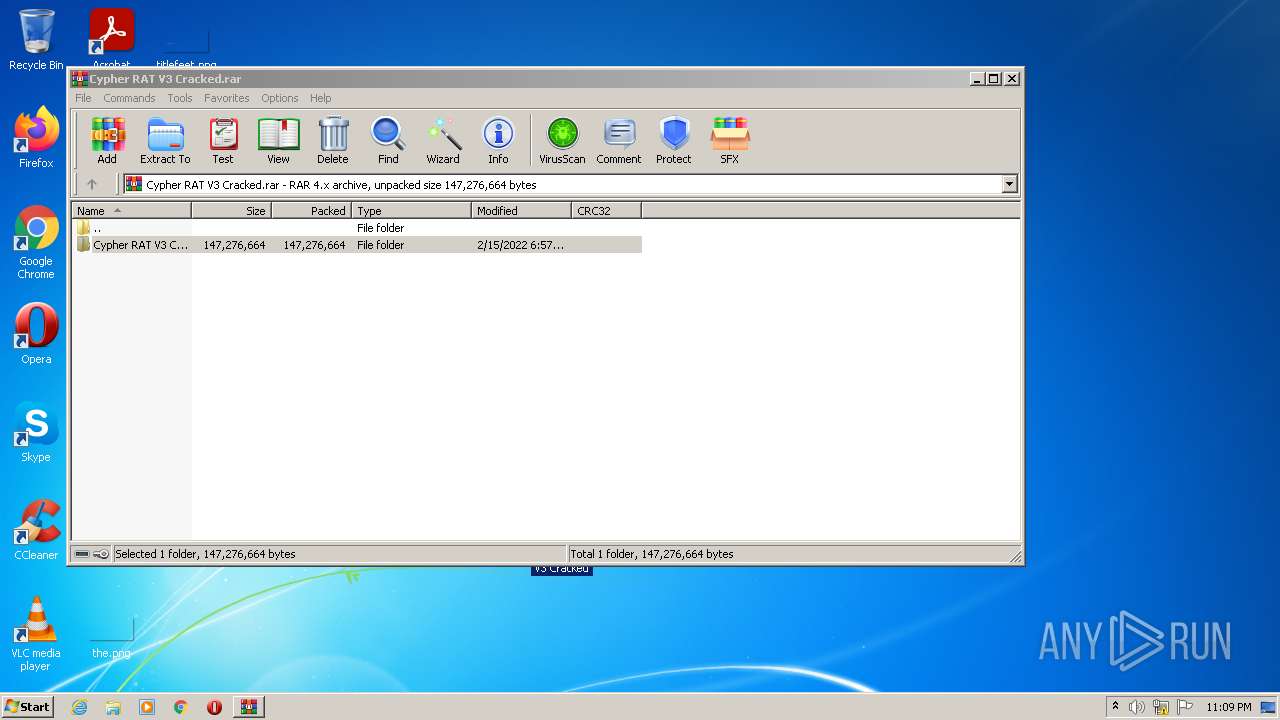
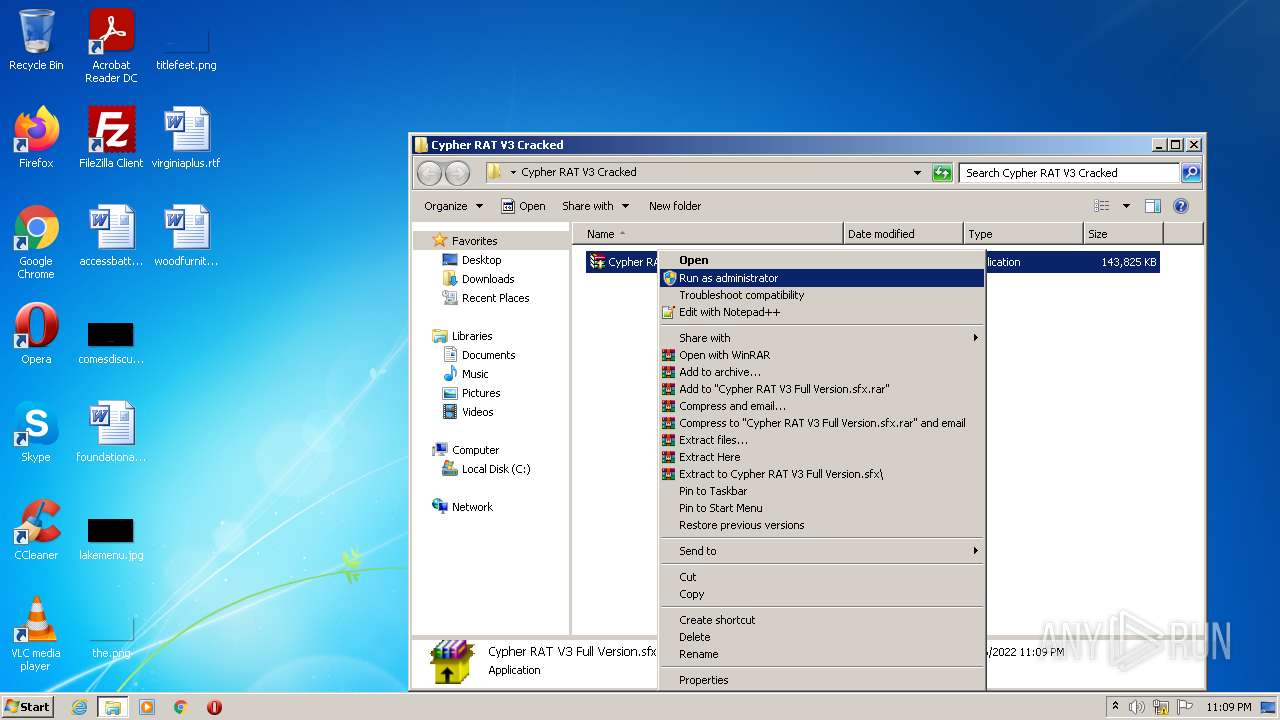
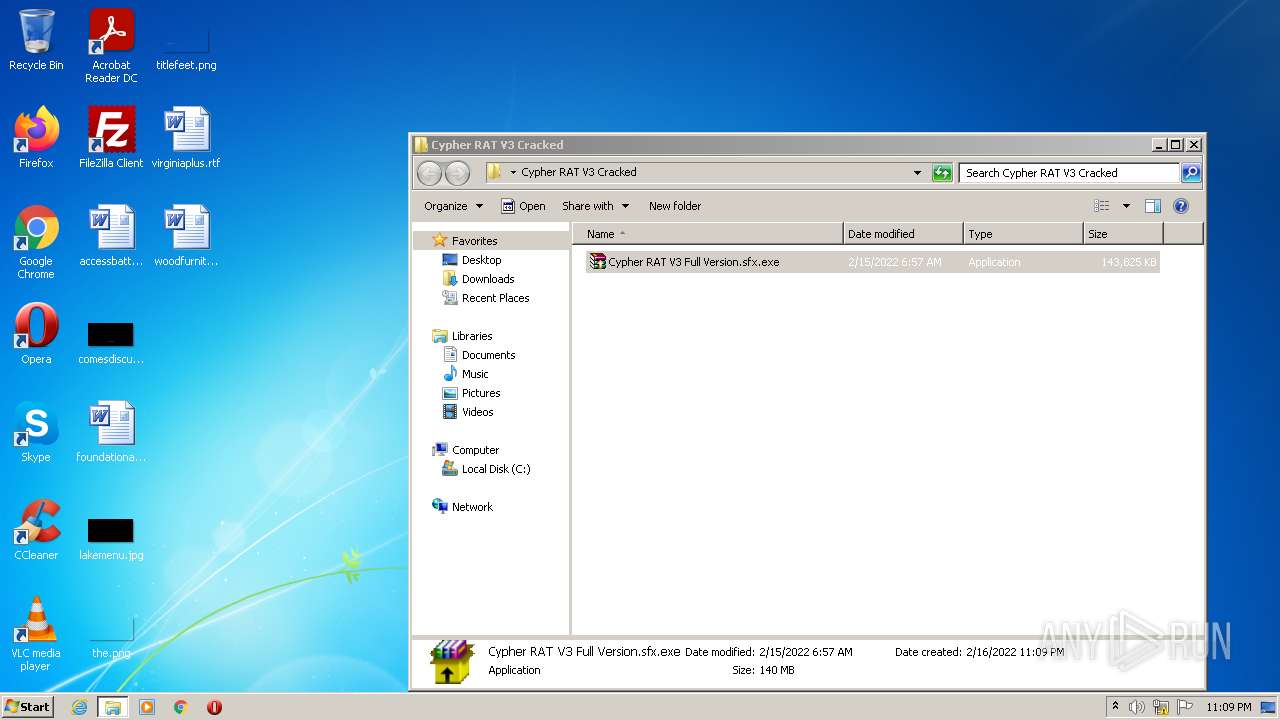
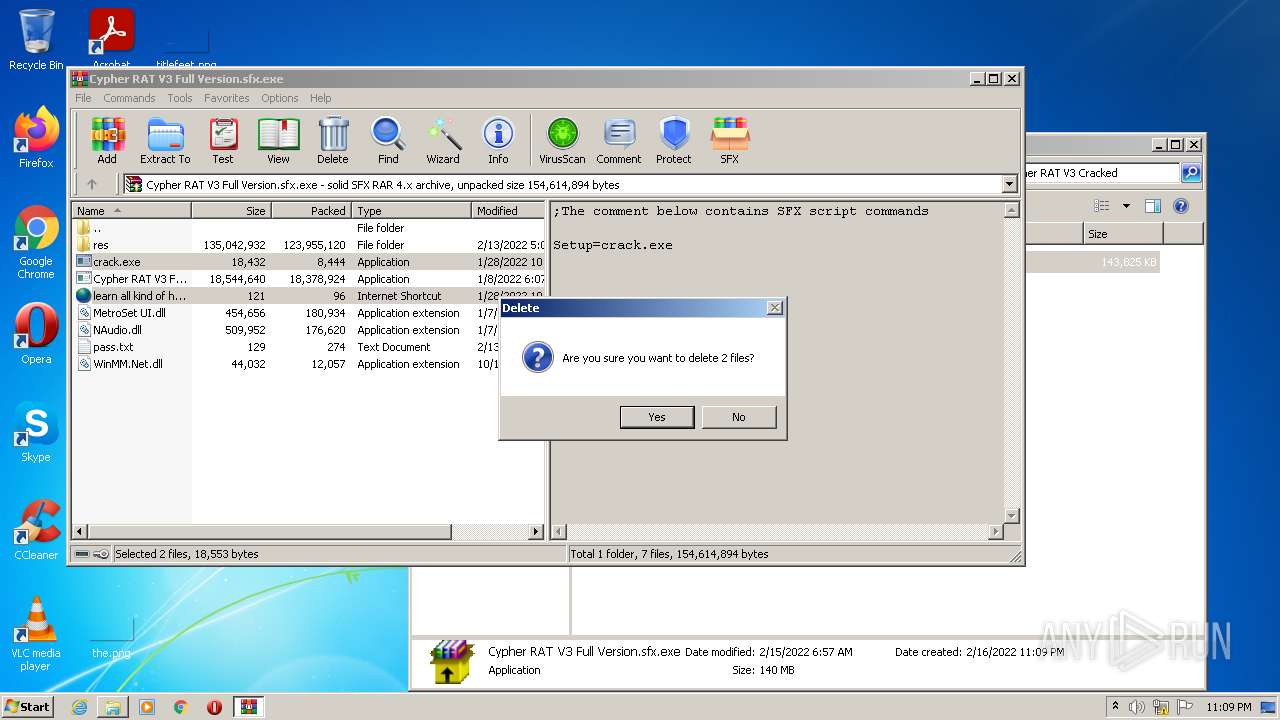
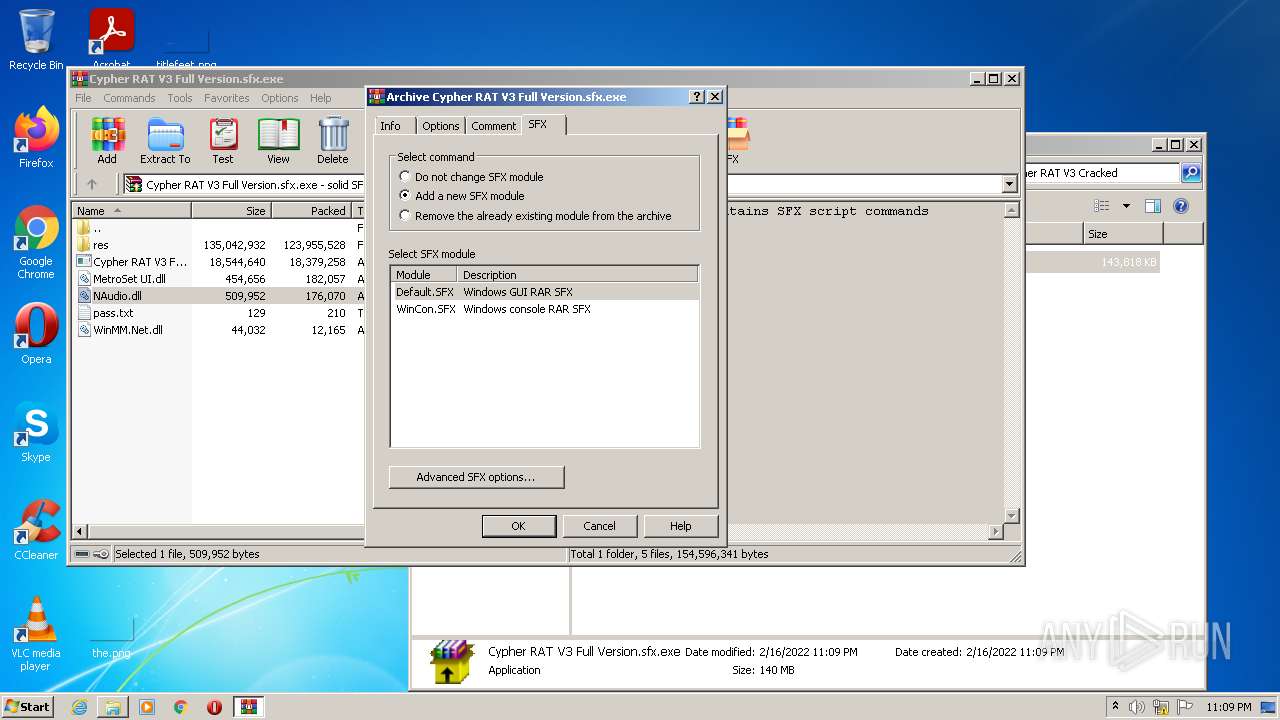
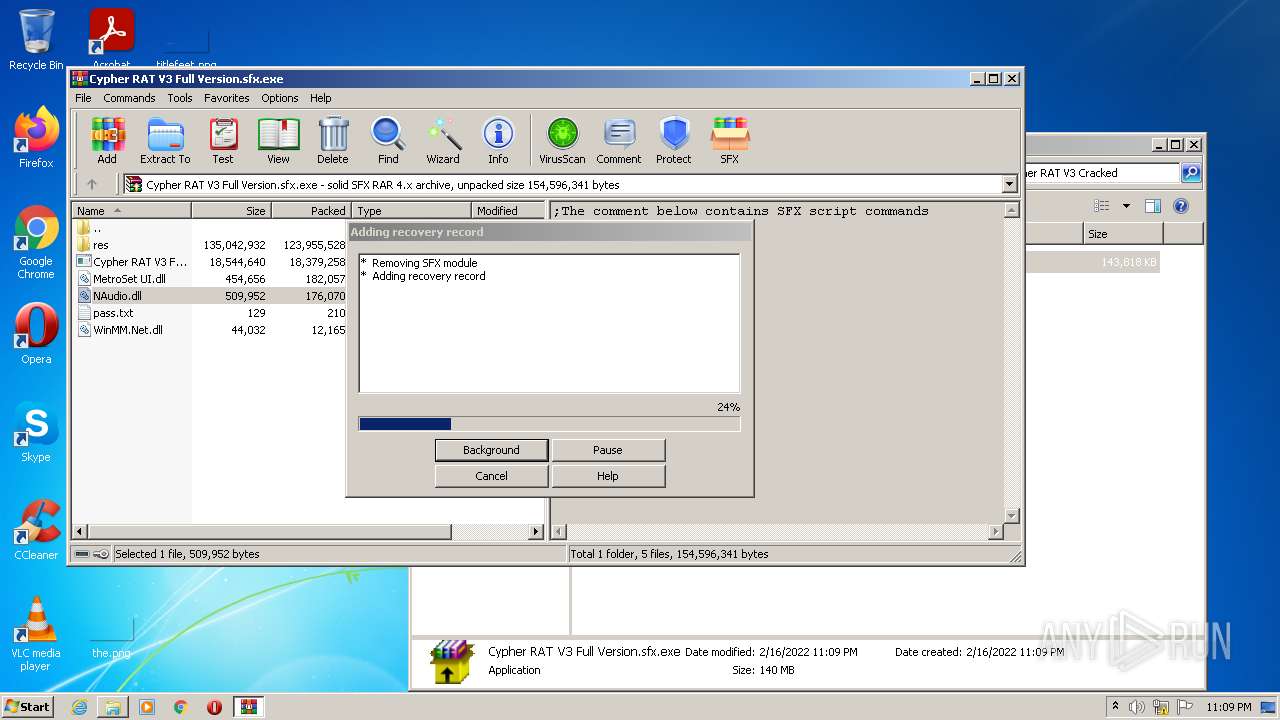
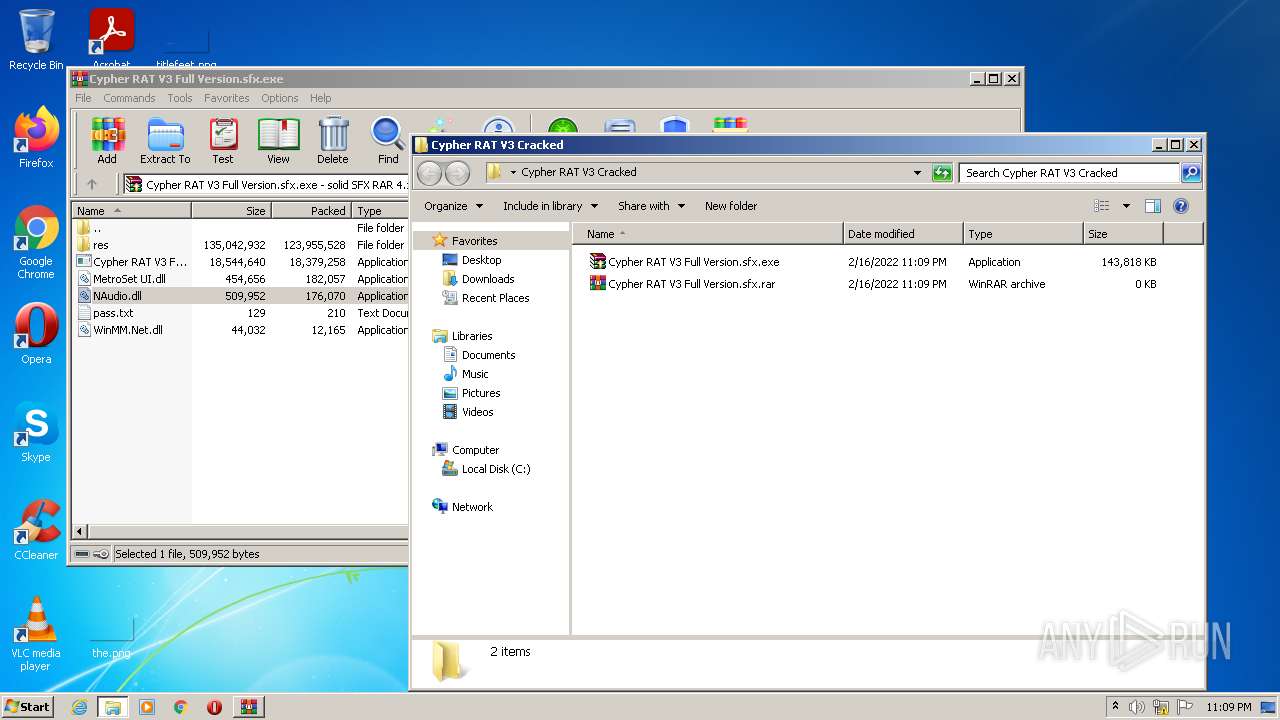
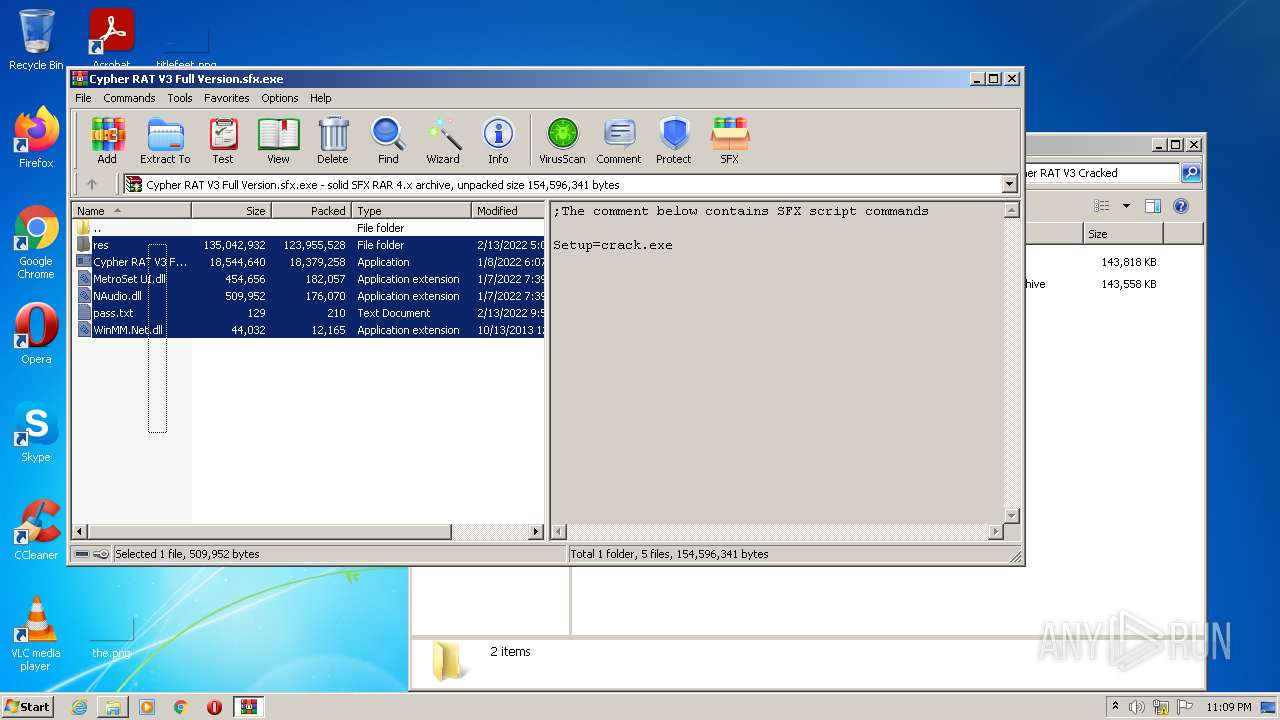
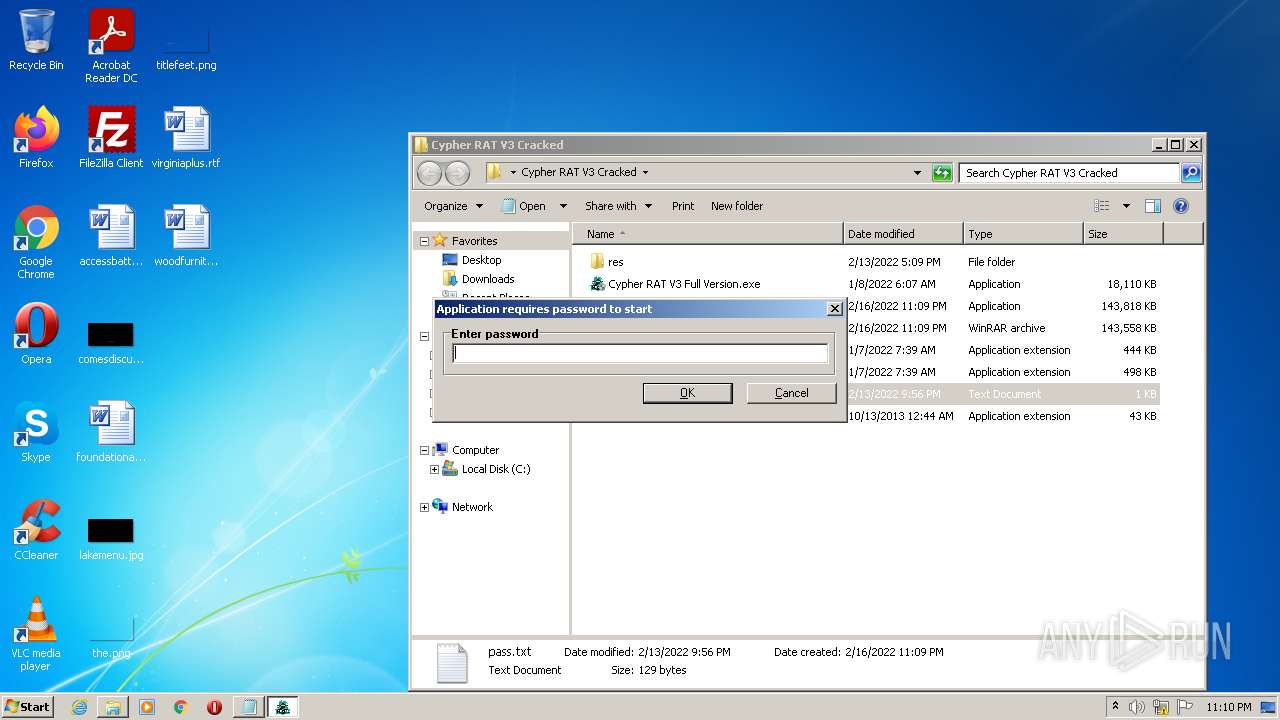
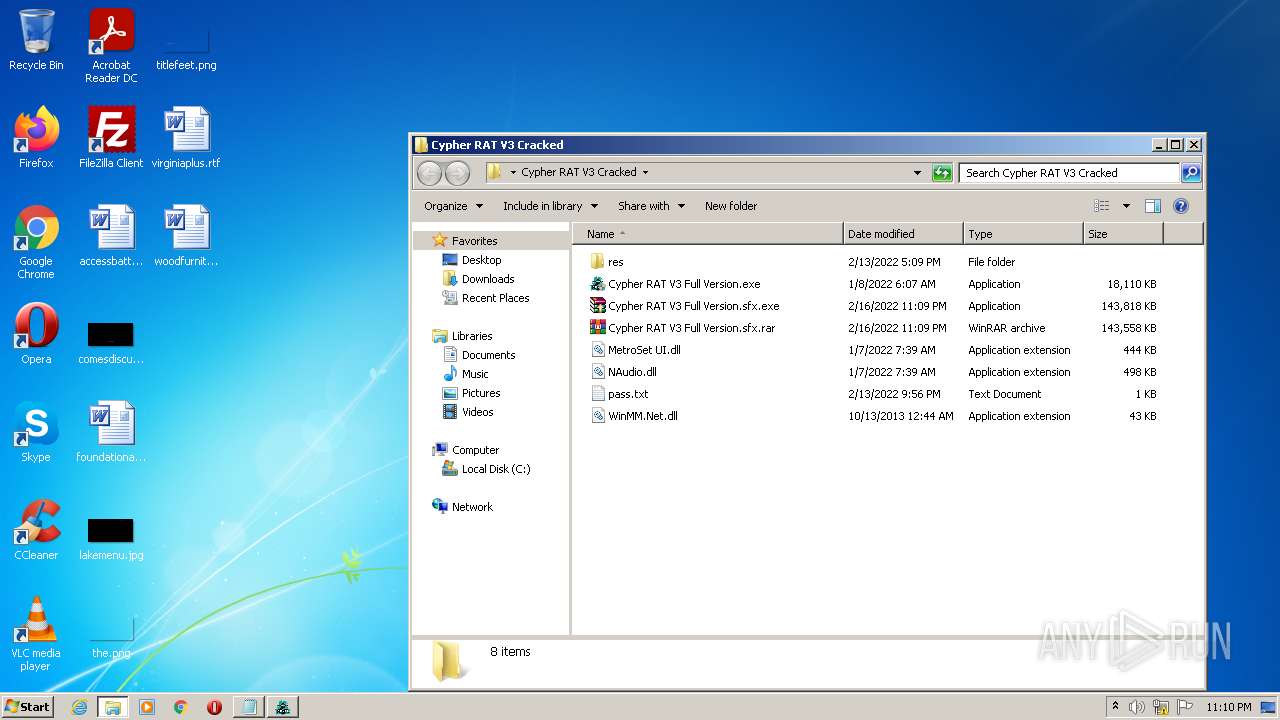
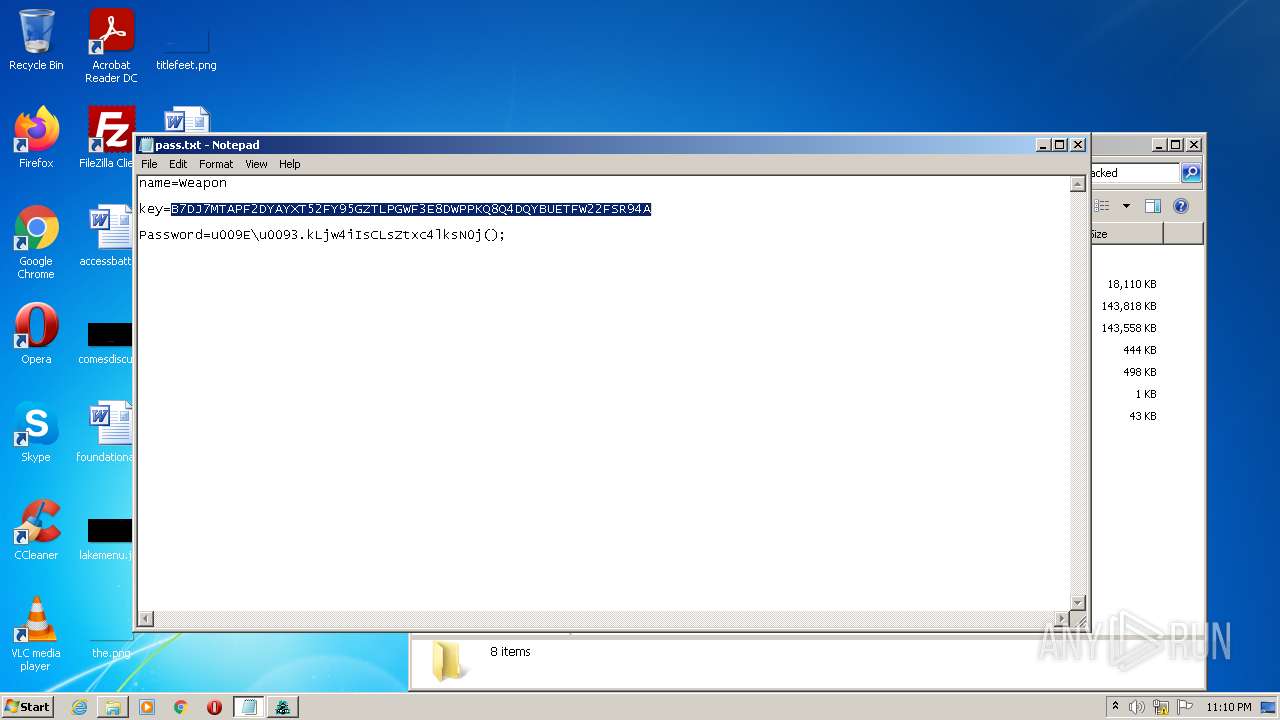
Manual execution by user
- WinRAR.exe (PID: 3912)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
70
Monitored processes
26
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 404 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1020,12818854655705898441,17777998216335483303,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1808 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 596 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,12818854655705898441,17777998216335483303,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2188 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1040 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,12818854655705898441,17777998216335483303,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1028 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1072 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1020,12818854655705898441,17777998216335483303,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1820 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1096 | C:\Windows\Explorer.EXE | C:\Windows\Explorer.EXE | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1444 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1020,12818854655705898441,17777998216335483303,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1228 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
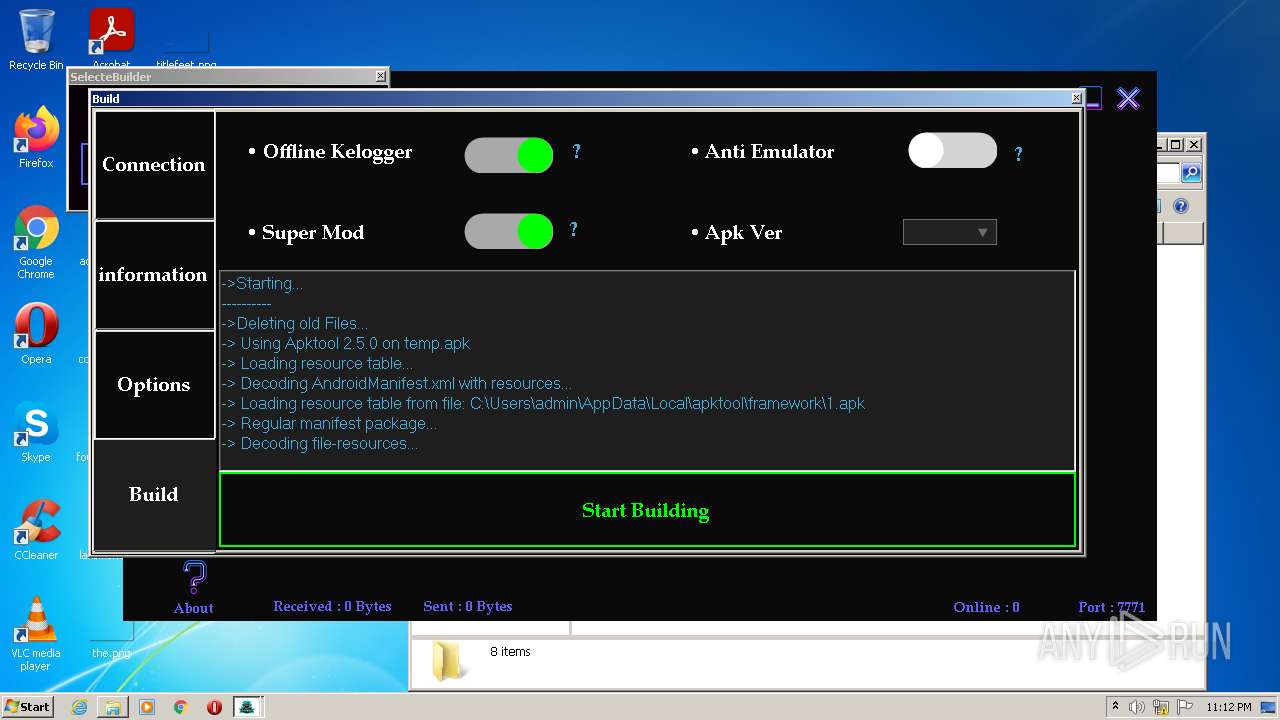
| 1696 | java -jar -Duser.language=en "C:\CypherRat_Bilder\platformBinary32\bin\\apktool.jar" d temp.apk | C:\CypherRat_Bilder\platformBinary32\bin\java.exe | — | cmd.exe | |||||||||||
User: admin Company: Azul Systems Inc. Integrity Level: HIGH Description: Zulu Platform x32 Architecture Exit code: 0 Version: 8.38.0.13 Modules
| |||||||||||||||
| 2068 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --field-trial-handle=1020,12818854655705898441,17777998216335483303,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3208 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2112 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,12818854655705898441,17777998216335483303,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1760 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2168 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,12818854655705898441,17777998216335483303,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1864 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
23 204
Read events
22 744
Write events
453
Delete events
7
Modification events
| (PID) Process: | (3724) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3724) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3724) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3724) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3724) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3724) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3724) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3724) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3724) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (3724) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
169
Suspicious files
61
Text files
1 492
Unknown types
53
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-620D83A8-E8C.pma | — | |
MD5:— | SHA256:— | |||
| 3724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\87451f5b-264d-4b2c-bb45-0033f3dd397b.tmp | text | |
MD5:— | SHA256:— | |||
| 3724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 3724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 3724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:EF1D5606A483BB6C72C81A3F649BEB18 | SHA256:BA083E7585ADA9936944FE56BC0141A544F18A01C3424E5C9F02375B34FE3D45 | |||
| 3724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Extension Settings\pkedcjkdefgpdelpbcmbmeomcjbeemfm\LOG.old | text | |
MD5:5202CA4D6AF0C37DAEC0D528CC7F2986 | SHA256:8F5B8FF94B14C36EA0CBE8FA0A4D165A632B45F834BBB7239E1A6CF6685F256C | |||
| 3724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF1935bc.TMP | text | |
MD5:B628564B8042F6E2CC2F53710AAECDC0 | SHA256:1D3B022BDEE9F48D79E3EC1E93F519036003642D3D72D10B05CFD47F43EFBF13 | |||
| 3724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RF1935cb.TMP | text | |
MD5:109A25C32EE1132ECD6D9F3ED9ADF01A | SHA256:DA6028DB9485C65E683643658326F02B1D0A1566DE14914EF28E5248EB94F0DD | |||
| 3724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Extension Settings\pkedcjkdefgpdelpbcmbmeomcjbeemfm\LOG.old~RF1938b9.TMP | text | |
MD5:D0BA19096D6C8F8DE58312E8D938E893 | SHA256:AADE90A7B0984F3C719D528E4E6FAE3854E28B30363BDD4DF65037E69784A078 | |||
| 3724 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Extension State\LOG.old~RF193c82.TMP | text | |
MD5:D097F8EB2230B3F32C41C5D75790508C | SHA256:ADDF87D20CD455CFB4AACB6B76719629C0277A4CF70B496343047BB73ABBAEF5 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
26
TCP/UDP connections
20
DNS requests
11
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
884 | svchost.exe | HEAD | 200 | 74.125.104.234:80 | http://r5---sn-ixh7yn7e.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3?cms_redirect=yes&mh=bj&mip=196.244.192.6&mm=28&mn=sn-ixh7yn7e&ms=nvh&mt=1645052428&mv=m&mvi=5&pl=25&rmhost=r3---sn-ixh7yn7e.gvt1.com&shardbypass=yes | US | — | — | whitelisted |
884 | svchost.exe | GET | 206 | 74.125.104.234:80 | http://r5---sn-ixh7yn7e.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3?cms_redirect=yes&mh=bj&mip=196.244.192.6&mm=28&mn=sn-ixh7yn7e&ms=nvh&mt=1645052674&mv=m&mvi=5&pl=25&rmhost=r3---sn-ixh7yn7e.gvt1.com&shardbypass=yes | US | binary | 9.49 Kb | whitelisted |
884 | svchost.exe | GET | 206 | 74.125.104.234:80 | http://r5---sn-ixh7yn7e.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3?cms_redirect=yes&mh=bj&mip=196.244.192.6&mm=28&mn=sn-ixh7yn7e&ms=nvh&mt=1645052674&mv=m&mvi=5&pl=25&rmhost=r3---sn-ixh7yn7e.gvt1.com&shardbypass=yes | US | binary | 43.3 Kb | whitelisted |
884 | svchost.exe | GET | 206 | 74.125.104.234:80 | http://r5---sn-ixh7yn7e.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3?cms_redirect=yes&mh=bj&mip=196.244.192.6&mm=28&mn=sn-ixh7yn7e&ms=nvh&mt=1645052674&mv=m&mvi=5&pl=25&rmhost=r3---sn-ixh7yn7e.gvt1.com&shardbypass=yes | US | binary | 20.7 Kb | whitelisted |
884 | svchost.exe | GET | 302 | 142.250.181.238:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | html | 575 b | whitelisted |
884 | svchost.exe | GET | 206 | 74.125.104.234:80 | http://r5---sn-ixh7yn7e.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3?cms_redirect=yes&mh=bj&mip=196.244.192.6&mm=28&mn=sn-ixh7yn7e&ms=nvh&mt=1645052674&mv=m&mvi=5&pl=25&rmhost=r3---sn-ixh7yn7e.gvt1.com&shardbypass=yes | US | binary | 9.49 Kb | whitelisted |
884 | svchost.exe | GET | 302 | 142.250.181.238:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | html | 575 b | whitelisted |
884 | svchost.exe | GET | 302 | 142.250.181.238:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | html | 575 b | whitelisted |
884 | svchost.exe | GET | 302 | 142.250.181.238:80 | http://redirector.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | html | 575 b | whitelisted |
884 | svchost.exe | GET | 206 | 74.125.104.234:80 | http://r5---sn-ixh7yn7e.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3?cms_redirect=yes&mh=bj&mip=196.244.192.6&mm=28&mn=sn-ixh7yn7e&ms=nvh&mt=1645052674&mv=m&mvi=5&pl=25&rmhost=r3---sn-ixh7yn7e.gvt1.com&shardbypass=yes | US | binary | 178 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1444 | chrome.exe | 217.64.149.200:443 | cdn-102.anonfiles.com | — | IR | unknown |
1444 | chrome.exe | 142.250.186.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
1444 | chrome.exe | 142.250.186.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
1444 | chrome.exe | 2.16.106.171:80 | ctldl.windowsupdate.com | Akamai International B.V. | — | whitelisted |
1444 | chrome.exe | 142.250.185.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1444 | chrome.exe | 142.250.185.99:443 | update.googleapis.com | Google Inc. | US | whitelisted |
884 | svchost.exe | 142.250.181.238:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
1444 | chrome.exe | 142.250.185.238:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
884 | svchost.exe | 74.125.104.234:80 | r5---sn-ixh7yn7e.gvt1.com | Google Inc. | US | whitelisted |
884 | svchost.exe | 74.125.104.202:80 | r5---sn-ixh7rn76.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
cdn-102.anonfiles.com |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r5---sn-ixh7yn7e.gvt1.com |
| whitelisted |
r5---sn-ixh7rn76.gvt1.com |
| whitelisted |
clients1.google.com |
| whitelisted |
Threats
Process | Message |
|---|---|
Cypher RAT V3 Full Version.exe | %s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s |