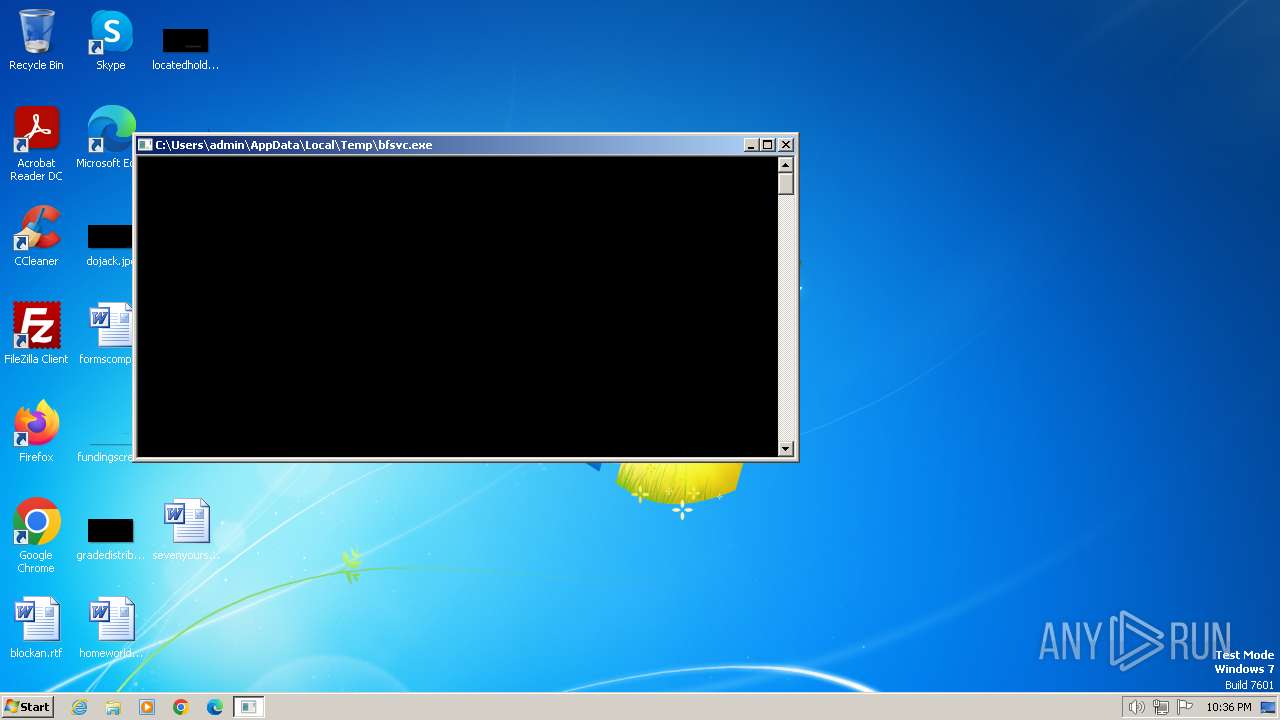
| File name: | bfsvc.exe |
| Full analysis: | https://app.any.run/tasks/65a1f406-a6f5-47a7-b3b9-a012077fbe1e |
| Verdict: | Malicious activity |
| Analysis date: | January 18, 2024, 22:36:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 7C5E42006469D4200ACA55BB28871D23 |
| SHA1: | CA963BE1ED6911EB05F3875D7658E2488083293B |
| SHA256: | ACE21809EBCD47A8ECD9C048B78279FBAA7D2118A3DDE7E44C77FD4C425D1B83 |
| SSDEEP: | 98304:/Krko2LEEX1u4OyZhoeC9B5/TSd1qdvuSZ+jT4MiRHAVIZK3i3aj9UF6YHnyjHam:/Pmlg28zGFjUsE2e |
MALICIOUS
Drops the executable file immediately after the start
- bfsvc.exe (PID: 116)
SPARKRAT has been detected (SURICATA)
- bfsvc.exe (PID: 1432)
Connects to the CnC server
- bfsvc.exe (PID: 1432)
SUSPICIOUS
Starts CMD.EXE for commands execution
- bfsvc.exe (PID: 1432)
Connects to unusual port
- bfsvc.exe (PID: 1432)
INFO
Checks supported languages
- bfsvc.exe (PID: 116)
- bfsvc.exe (PID: 1432)
Reads the computer name
- bfsvc.exe (PID: 116)
- bfsvc.exe (PID: 1432)
Manual execution by a user
- bfsvc.exe (PID: 1432)
Checks operating system version
- bfsvc.exe (PID: 1432)
Reads the machine GUID from the registry
- bfsvc.exe (PID: 1432)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.3) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:01:18 23:33:25+01:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 1.73 |
| CodeSize: | 8070656 |
| InitializedDataSize: | 512 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 1 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
37
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Users\admin\AppData\Local\Temp\bfsvc.exe" | C:\Users\admin\AppData\Local\Temp\bfsvc.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1432 | "C:\Users\admin\AppData\Local\Temp\bfsvc.exe" | C:\Users\admin\AppData\Local\Temp\bfsvc.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 2 Modules
| |||||||||||||||
| 2204 | cmd ver | C:\Windows\System32\cmd.exe | — | bfsvc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 043
Read events
1 043
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
6
DNS requests
1
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1432 | bfsvc.exe | POST | 200 | 185.196.10.224:8000 | http://web3standard.duckdns.org:8000/api/client/update?arch=386&commit=08059e95dacafe0bf6e5782f8e2c8ec9cd8c5a17&os=windows | unknown | binary | 10 b | unknown |
1432 | bfsvc.exe | GET | 101 | 185.196.10.224:8000 | http://web3standard.duckdns.org:8000/ws | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1432 | bfsvc.exe | 185.196.10.224:8000 | web3standard.duckdns.org | Simple Carrier LLC | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
web3standard.duckdns.org |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET INFO DYNAMIC_DNS Query to a *.duckdns .org Domain |
1080 | svchost.exe | Misc activity | ET INFO DYNAMIC_DNS Query to *.duckdns. Domain |
1432 | bfsvc.exe | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Websocket update request to external network |
1432 | bfsvc.exe | Malware Command and Control Activity Detected | ET MALWARE Win32/SparkRAT CnC Checkin (GET) |
1432 | bfsvc.exe | Misc activity | ET USER_AGENTS Go HTTP Client User-Agent |
1432 | bfsvc.exe | Potentially Bad Traffic | ET INFO DYNAMIC_DNS HTTP Request to a *.duckdns .org Domain |
1432 | bfsvc.exe | Potentially Bad Traffic | ET INFO DYNAMIC_DNS HTTP Request to a *.duckdns .org Domain |
1432 | bfsvc.exe | Potentially Bad Traffic | ET INFO HTTP POST Request to DuckDNS Domain |
1 ETPRO signatures available at the full report