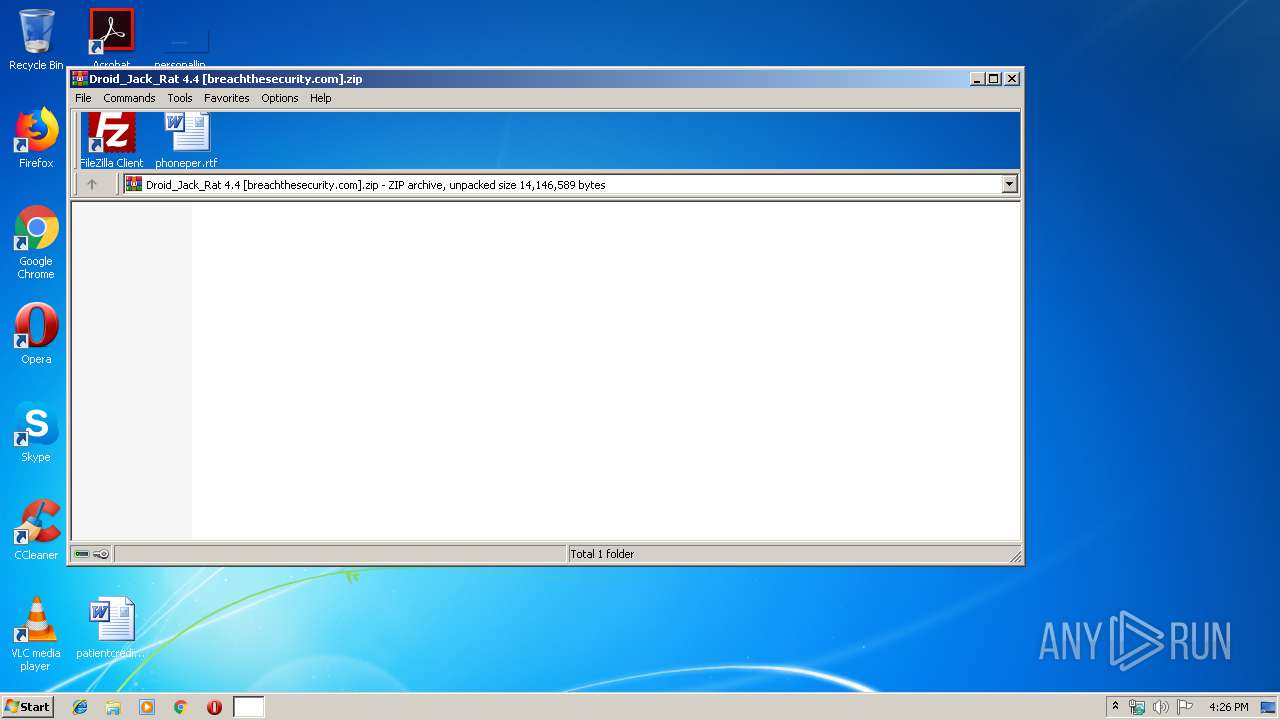
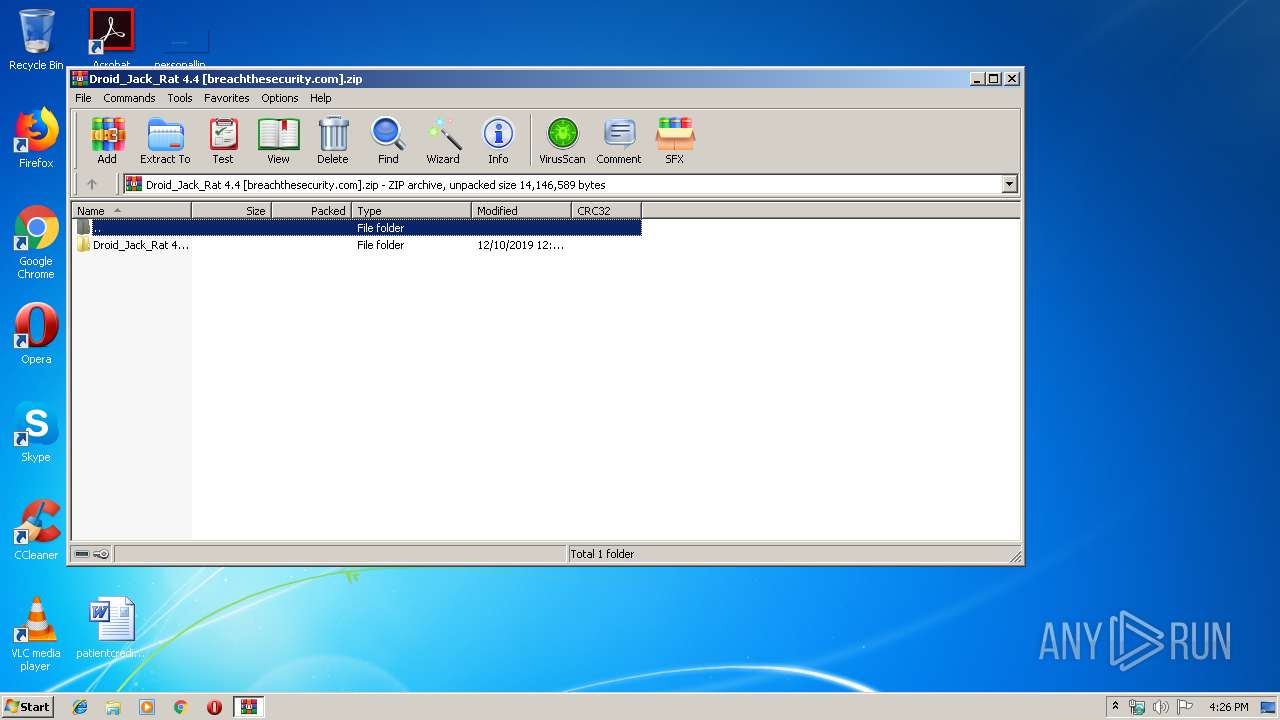
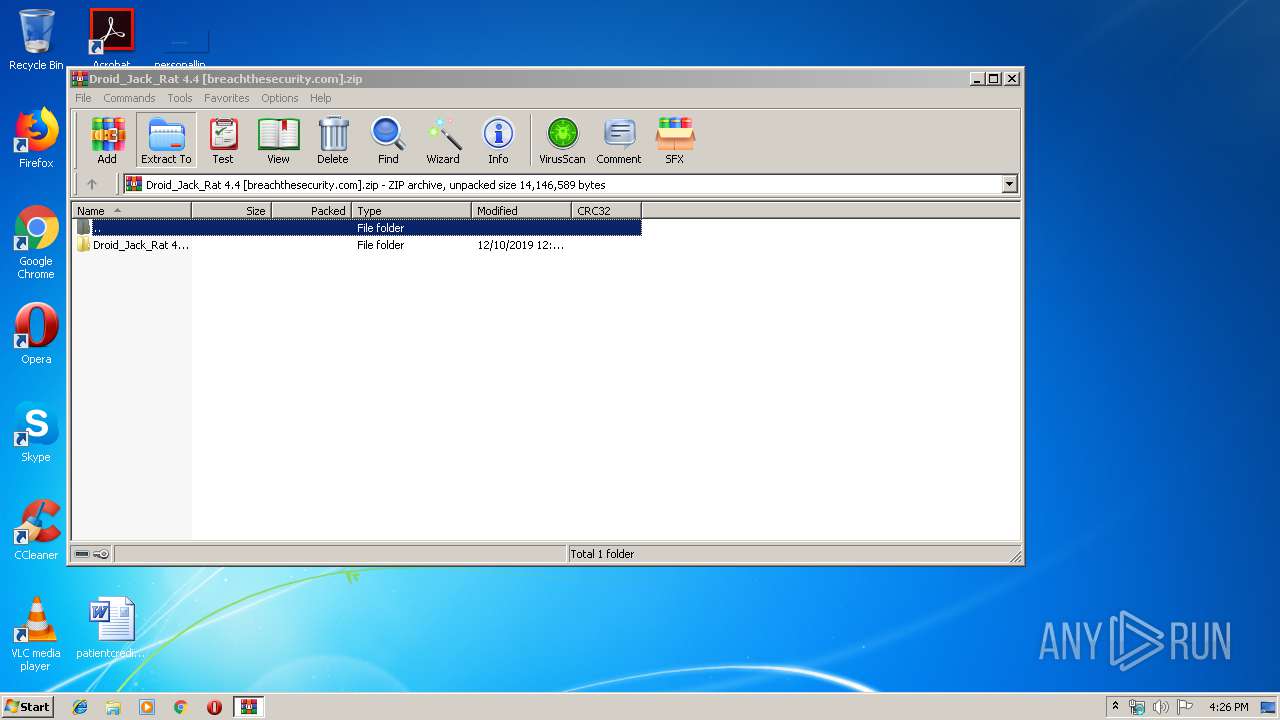
| File name: | Droid_Jack_Rat 4.4 [breachthesecurity.com].zip |
| Full analysis: | https://app.any.run/tasks/a55cb67f-39b9-4e4d-89e2-cc8f6096a81b |
| Verdict: | No threats detected |
| Analysis date: | December 09, 2019, 16:25:47 |
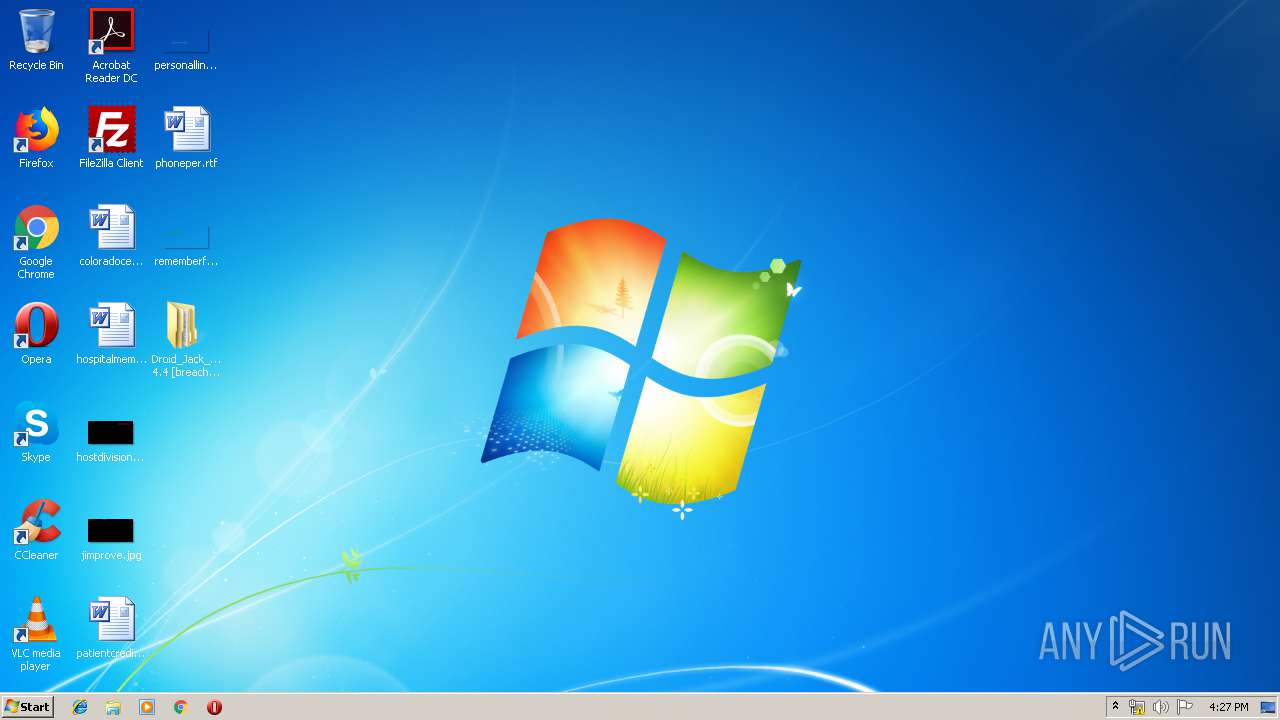
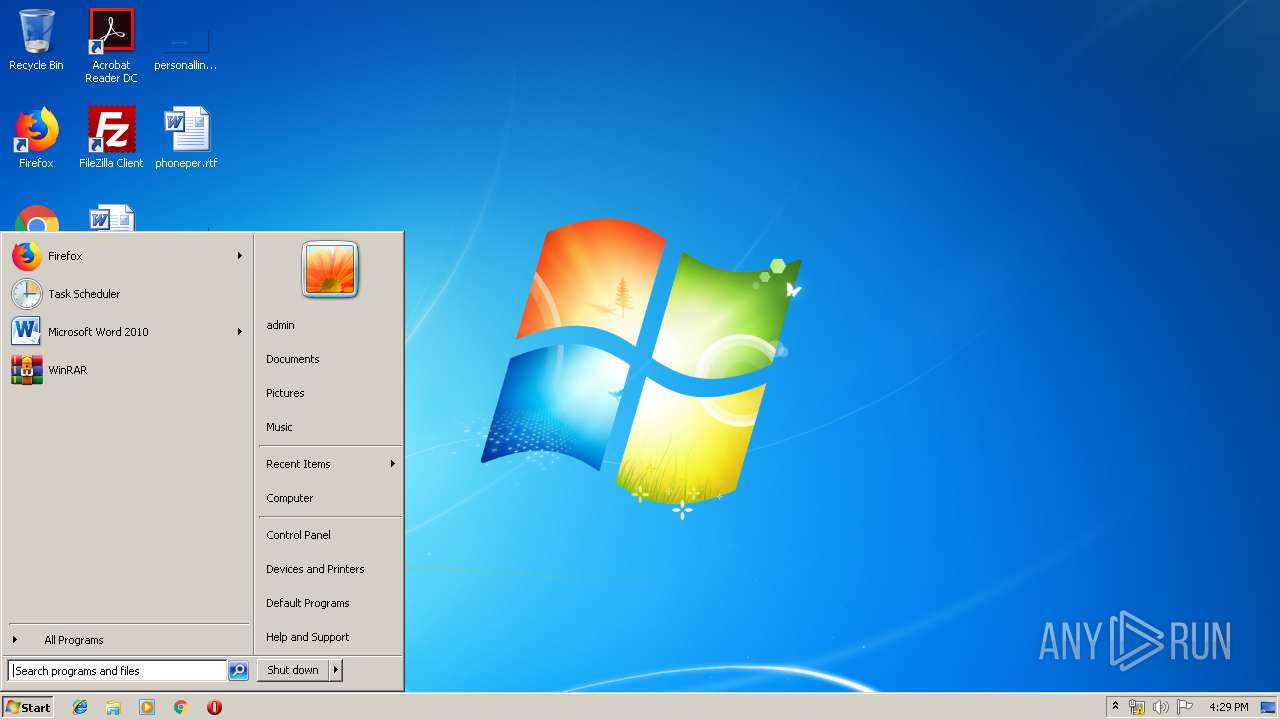
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 9008AE2EDFB3FA5BADBFE8AB034503F0 |
| SHA1: | 67E0F7A8040973676249F7E2F2AC06A42A1FC31A |
| SHA256: | ACD8FBE3A856A9CB6DF2781F4EF3864E0503A7C87FF80B3425423FBC47ABFAAB |
| SSDEEP: | 196608:eeh4W3dHjgq++lrv0YgquwqHxJ0bRronk9Jv3y7sPbARZeG09WB8OiV+dOf:vhpdJ+THxJGokjyCAGkBVLdO |
MALICIOUS
Loads dropped or rewritten executable
- javaw.exe (PID: 3700)
SUSPICIOUS
Executable content was dropped or overwritten
- javaw.exe (PID: 3700)
Creates files in the user directory
- javaw.exe (PID: 3700)
Executes JAVA applets
- javaw.exe (PID: 3700)
INFO
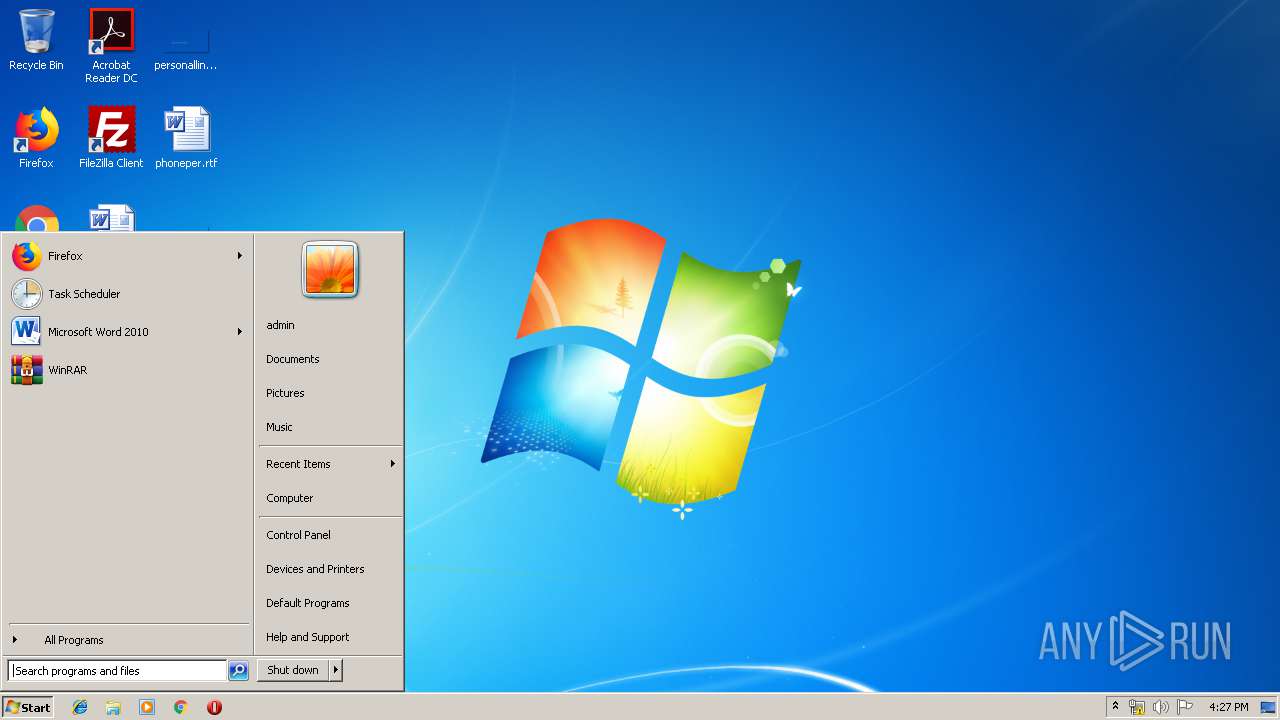
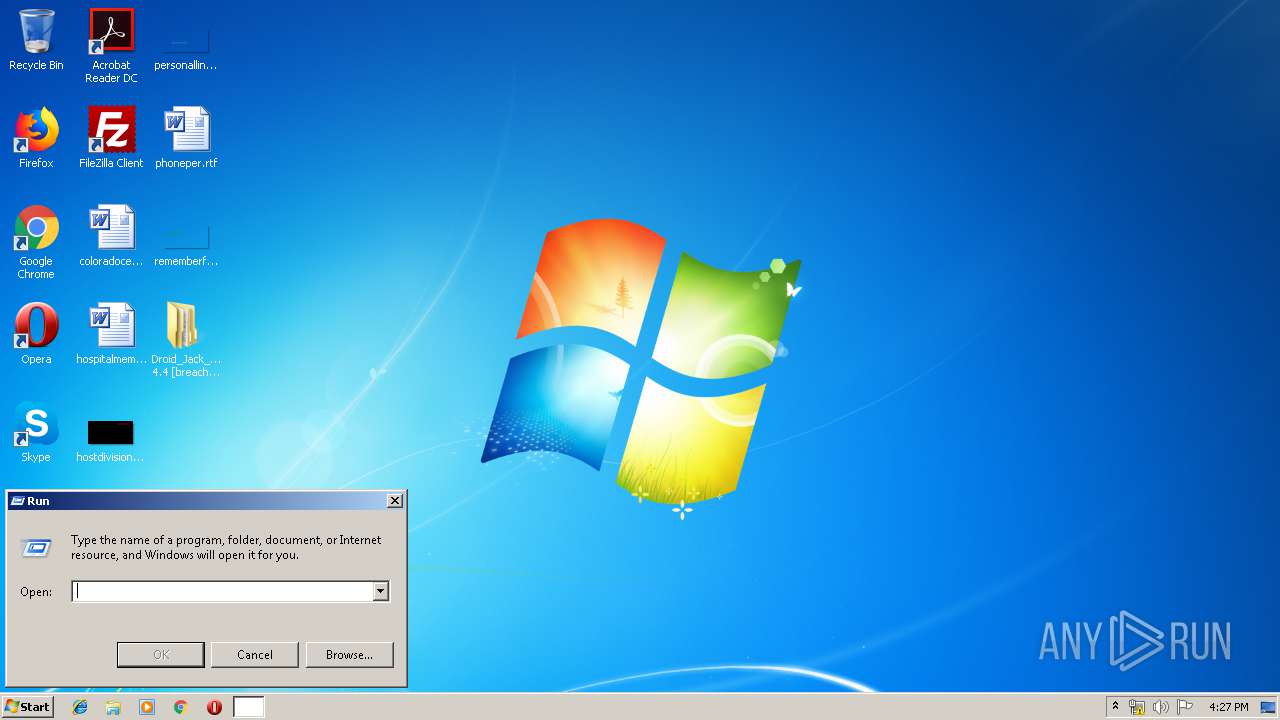
Manual execution by user
- javaw.exe (PID: 3700)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0808 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:12:10 00:25:05 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | 2 |
| ZipUncompressedSize: | - |
| ZipFileName: | Droid_Jack_Rat 4.4 [breachthesecurity.com]/ |
Total processes
40
Monitored processes
3
Malicious processes
0
Suspicious processes
0
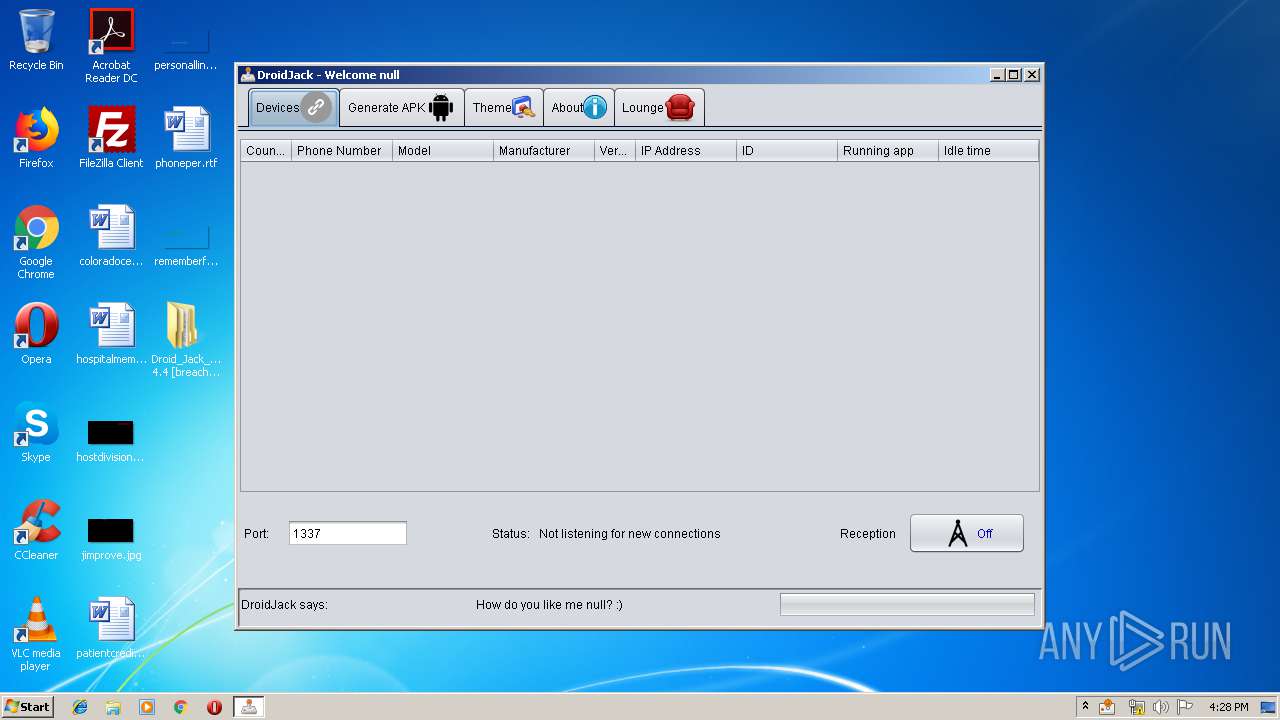
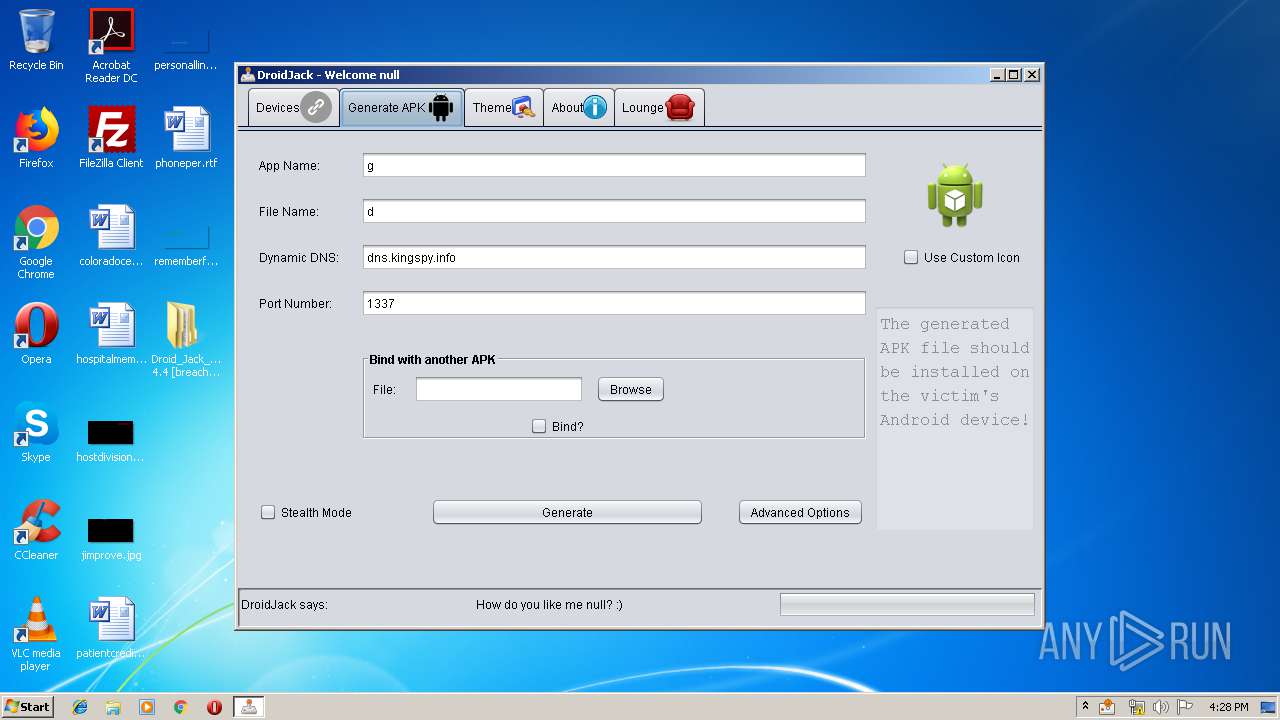
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
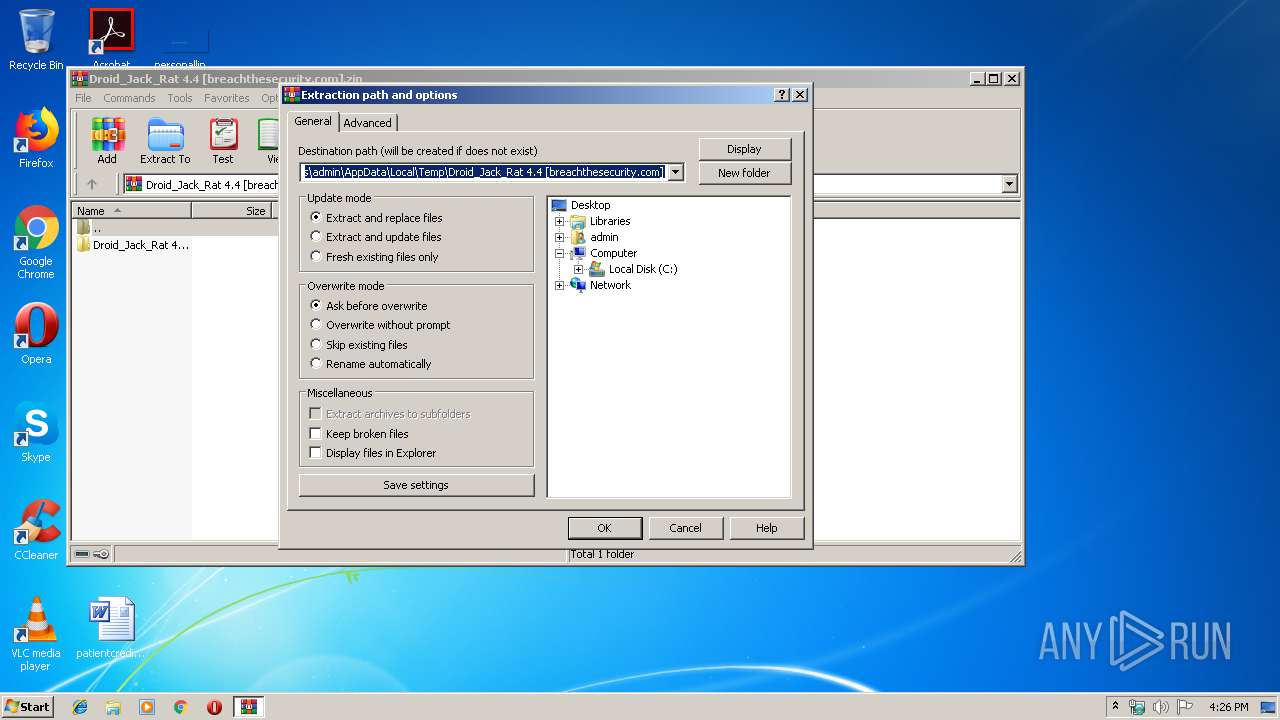
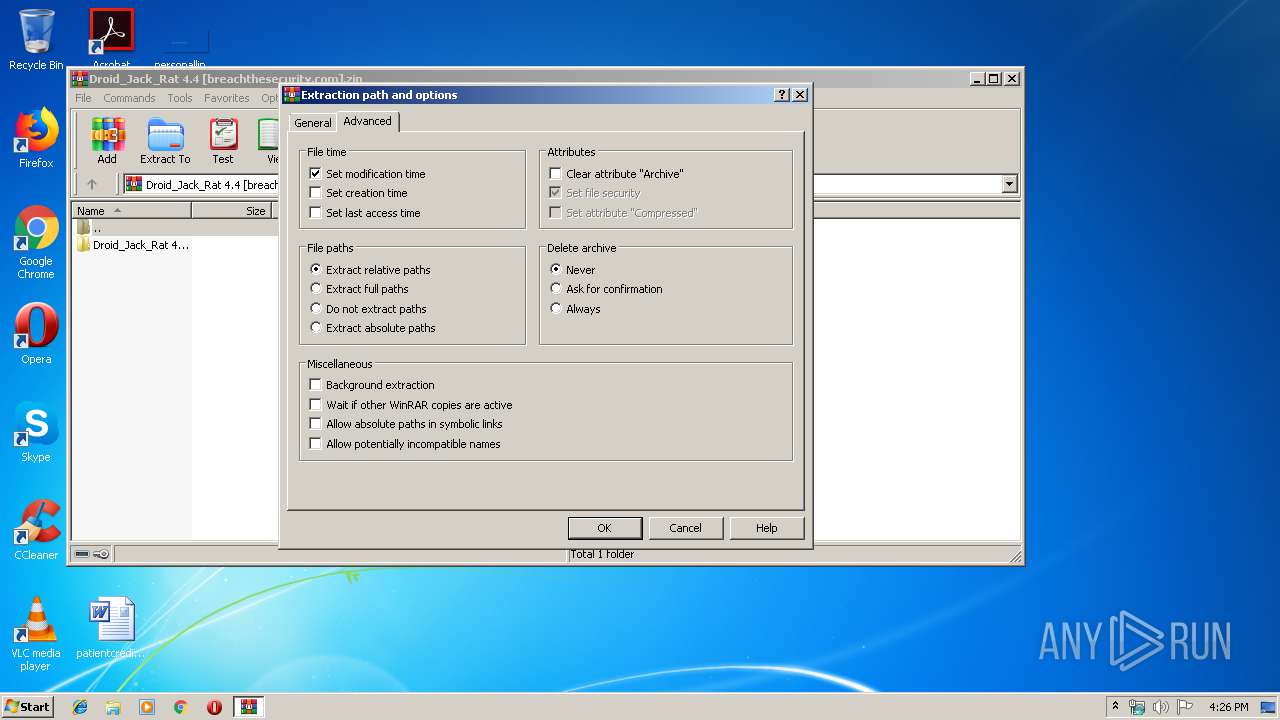
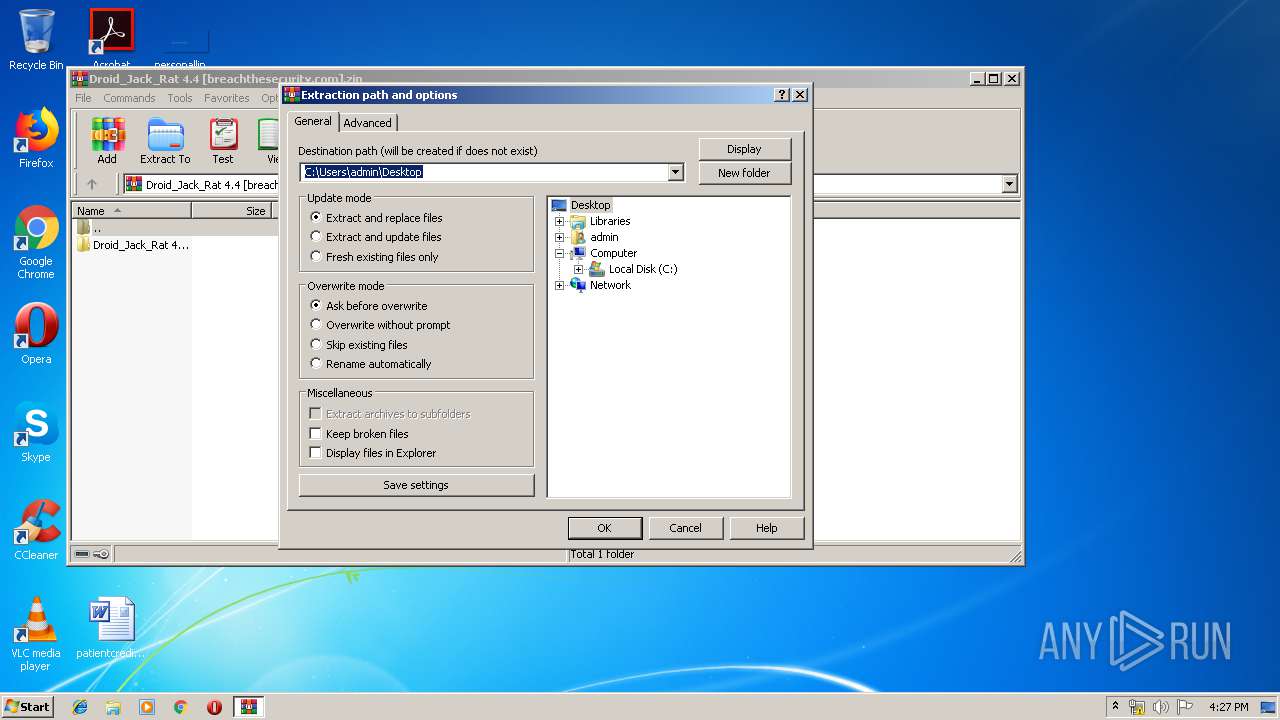
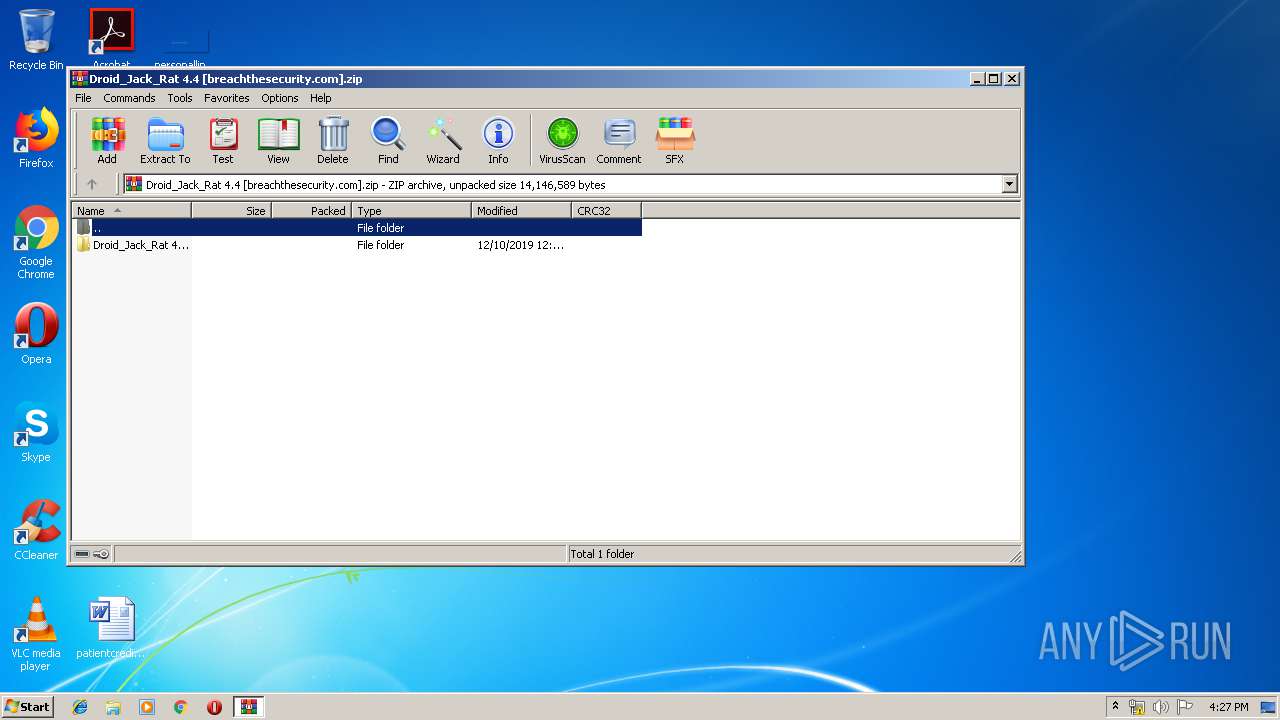
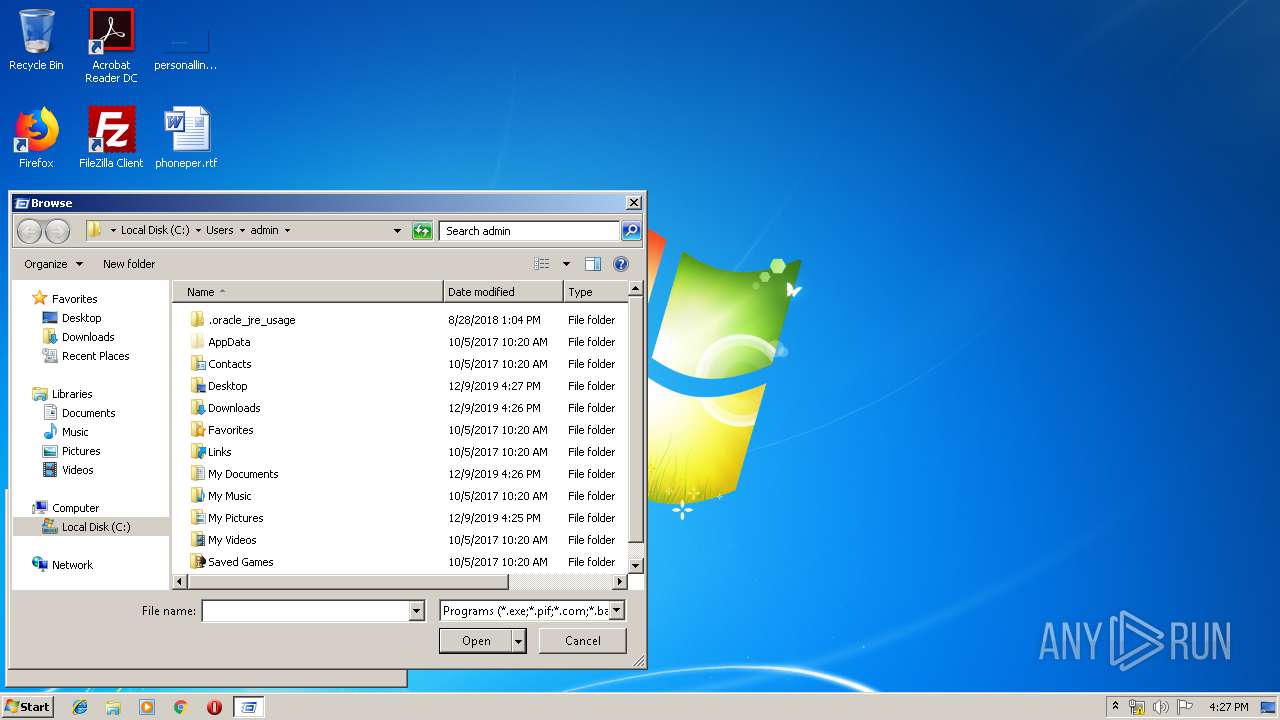
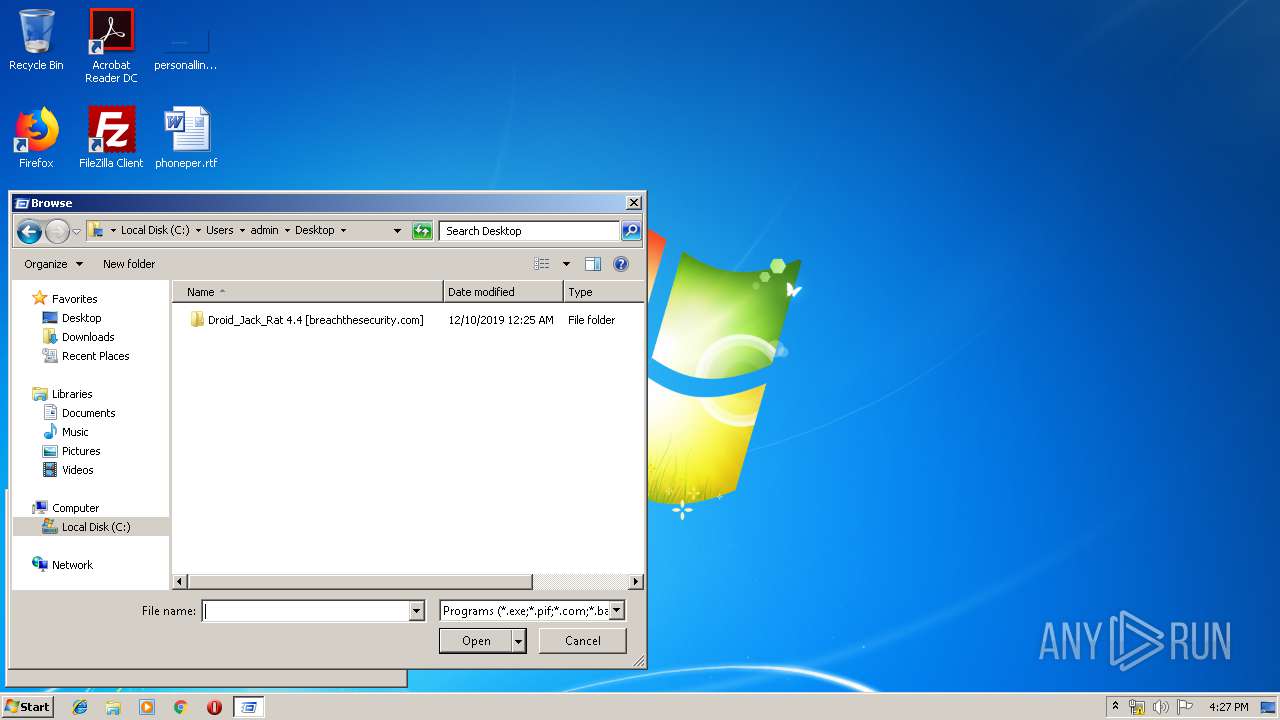
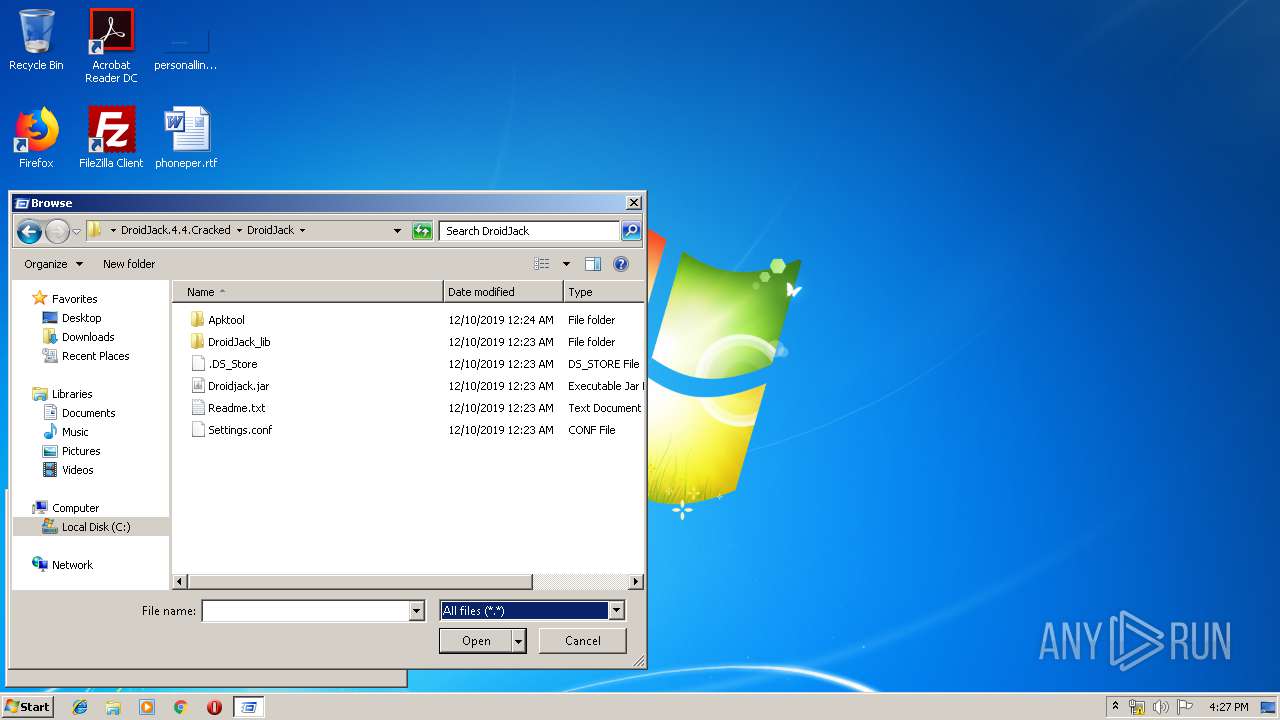
| 956 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Droid_Jack_Rat 4.4 [breachthesecurity.com].zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3320 | java -jar Apktool/apktool.jar d Apktool/SandroRat.apk -o Apktool/SandroRat | C:\Program Files\Java\jre1.8.0_92\bin\java.exe | — | javaw.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 1 Version: 8.0.920.14 Modules
| |||||||||||||||
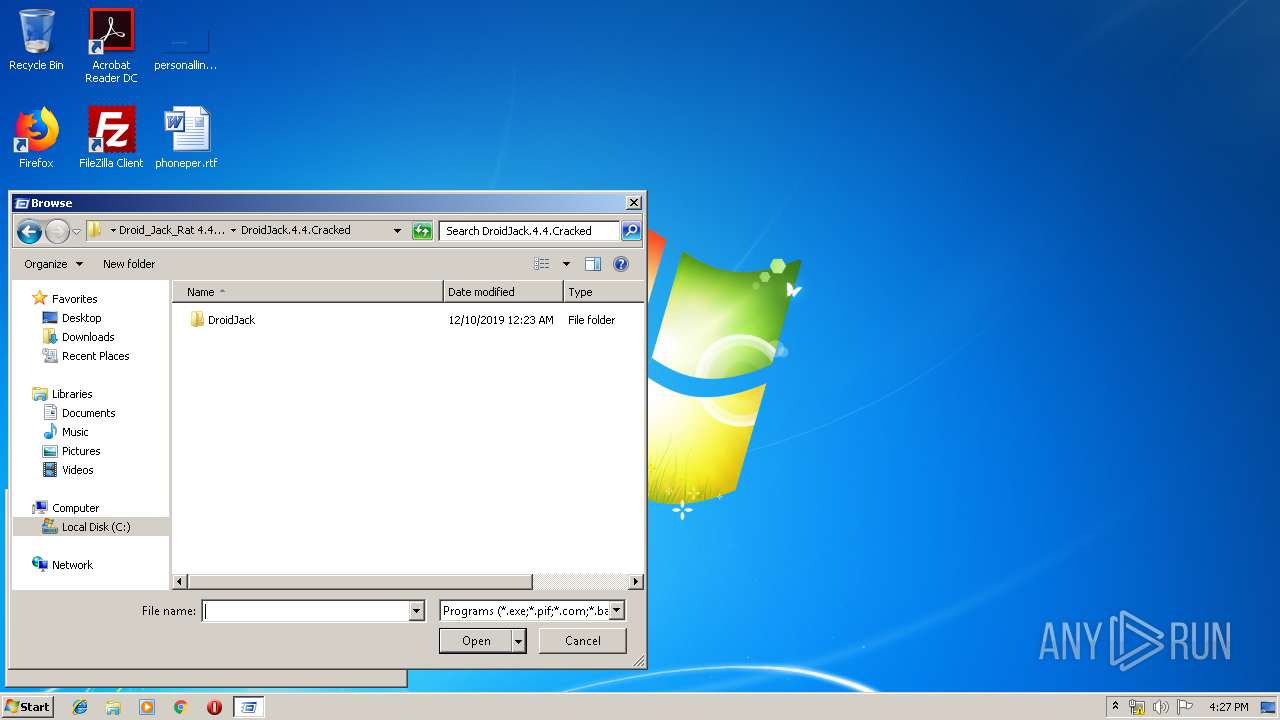
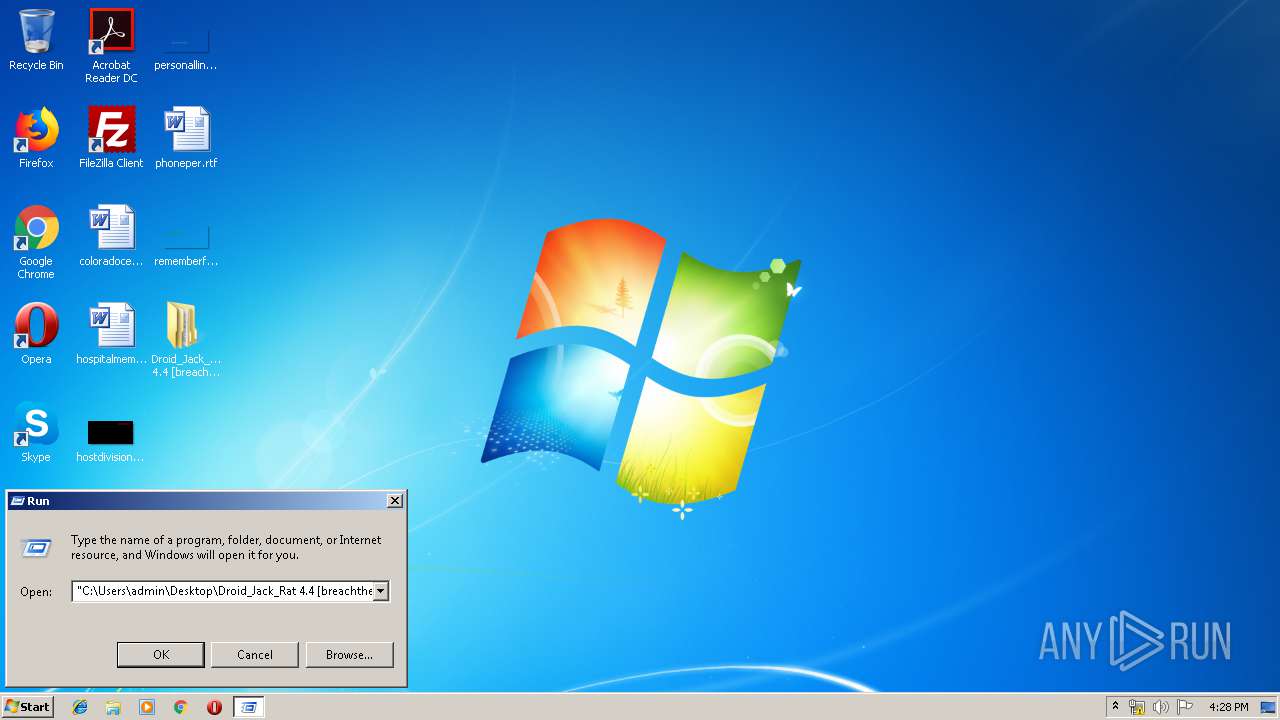
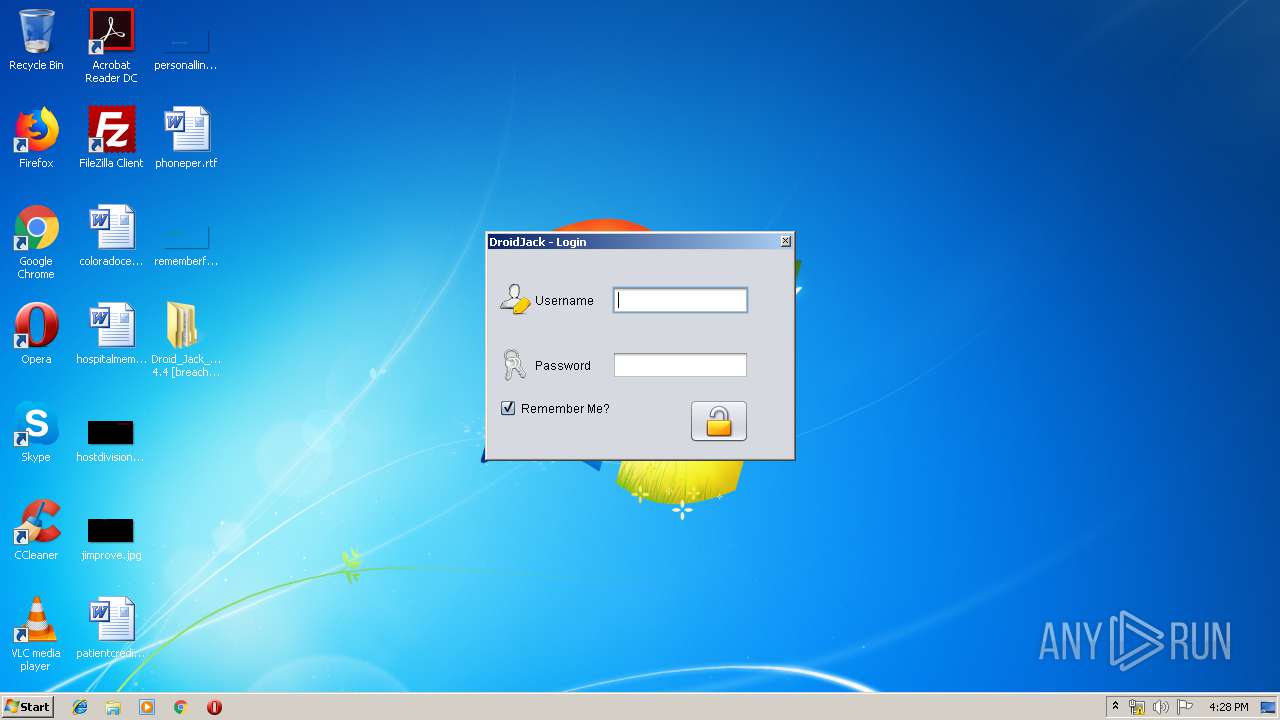
| 3700 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -jar "C:\Users\admin\Desktop\Droid_Jack_Rat 4.4 [breachthesecurity.com]\DroidJack.4.4.Cracked\DroidJack\Droidjack.jar" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | explorer.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
Total events
477
Read events
455
Write events
22
Delete events
0
Modification events
| (PID) Process: | (956) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (956) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (956) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (956) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Droid_Jack_Rat 4.4 [breachthesecurity.com].zip | |||
| (PID) Process: | (956) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (956) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (956) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (956) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (956) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (956) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
6
Suspicious files
15
Text files
4
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 956 | WinRAR.exe | C:\Users\admin\Desktop\Droid_Jack_Rat 4.4 [breachthesecurity.com]\DroidJack.4.4.Cracked\DroidJack\Apktool\certificate.pem | text | |
MD5:483A7FBA0FA4025A87FF40730926CC54 | SHA256:B2E32152E7972032FD64AD351323F50008602C60FEB19522B1AADD414BF1F7B4 | |||
| 956 | WinRAR.exe | C:\Users\admin\Desktop\Droid_Jack_Rat 4.4 [breachthesecurity.com]\DroidJack.4.4.Cracked\DroidJack\Apktool\SandroRat.apk | compressed | |
MD5:15F7199148DD83CC0F76FBD7EDCD6EE5 | SHA256:30AA2EEEB8401E4A312A7E99462432769A7C569114180AAEDBFCBEF18B6DB268 | |||
| 956 | WinRAR.exe | C:\Users\admin\Desktop\Droid_Jack_Rat 4.4 [breachthesecurity.com]\DroidJack.4.4.Cracked\DroidJack\Apktool\.DS_Store | ds_store | |
MD5:010C44C7918725F07BC33DDA1FE1938B | SHA256:8C7D7C53AF7189A9235E4A43ED2694F874C20CE061CE23B1F271436E8404A64D | |||
| 956 | WinRAR.exe | C:\Users\admin\Desktop\Droid_Jack_Rat 4.4 [breachthesecurity.com]\DroidJack.4.4.Cracked\DroidJack\Apktool\aapts.zip | compressed | |
MD5:4D936C19E227412689D07A172CF7C073 | SHA256:9BA477194B6BEE993D26D1051A4E02143540F6B12CF93D498F380EA0E40E1A1A | |||
| 956 | WinRAR.exe | C:\Users\admin\Desktop\Droid_Jack_Rat 4.4 [breachthesecurity.com]\DroidJack.4.4.Cracked\DroidJack\Apktool\efm.jar | text | |
MD5:A91F7CBBD06F657BD7608B70CF7FB864 | SHA256:91D79633B19D62B0EA71341B1692F49B2B59F9535E30A181D66FC4E83B0A2660 | |||
| 956 | WinRAR.exe | C:\Users\admin\Desktop\Droid_Jack_Rat 4.4 [breachthesecurity.com]\DroidJack.4.4.Cracked\DroidJack\Apktool\key.pk8 | der | |
MD5:D4E79235C7AABFDA87C59B6FA81CAE63 | SHA256:A07CE769D17334F803A499C520D4A7D88478CEB1A9CF740FAF296F8F54616E82 | |||
| 956 | WinRAR.exe | C:\Users\admin\Desktop\Droid_Jack_Rat 4.4 [breachthesecurity.com]\DroidJack.4.4.Cracked\DroidJack\Apktool\signapk.jar | java | |
MD5:AEC6985FE2314E4D032BA6D192AC4163 | SHA256:B17534E89A5B58D5E343BA54A49DA579CF9213988F4BEEAE24FE4582A0C226BB | |||
| 956 | WinRAR.exe | C:\Users\admin\Desktop\Droid_Jack_Rat 4.4 [breachthesecurity.com]\DroidJack.4.4.Cracked\DroidJack\Droidjack.jar | java | |
MD5:6A572A2D8B9A7D037EFE7DD32B270AA6 | SHA256:EB2E735C63BF6B17C349E4089F2C8C0D2463BC552D0DC8383A06E917F799EEFF | |||
| 956 | WinRAR.exe | C:\Users\admin\Desktop\Droid_Jack_Rat 4.4 [breachthesecurity.com]\DroidJack.4.4.Cracked\DroidJack\DroidJack_lib\commons-io-2.4.jar | compressed | |
MD5:7F97854DC04C119D461FED14F5D8BB96 | SHA256:CC6A41DC3EAACC9E440A6BD0D2890B20D36B4EE408FE2D67122F328BB6E01581 | |||
| 956 | WinRAR.exe | C:\Users\admin\Desktop\Droid_Jack_Rat 4.4 [breachthesecurity.com]\DroidJack.4.4.Cracked\DroidJack\.DS_Store | ds_store | |
MD5:5EFC66C86F9EE056C23448A95D827D1C | SHA256:923211913F3C80FB88E966BE6301E7965C28785E911372ABA7CB4ADFFAC305A2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
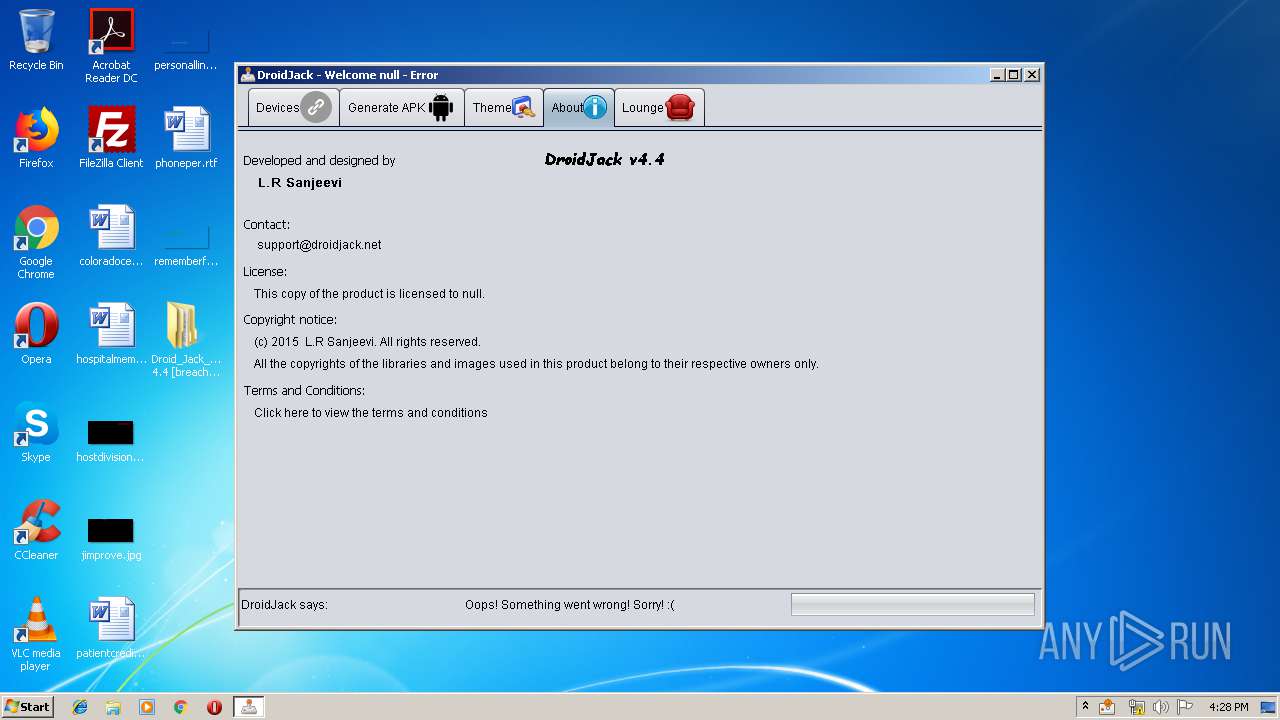
3700 | javaw.exe | GET | 200 | 162.251.80.24:80 | http://www.droidjack.net/Terms.html | US | html | 3.37 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3700 | javaw.exe | 162.251.80.24:80 | www.droidjack.net | PDR | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.droidjack.net |
| malicious |