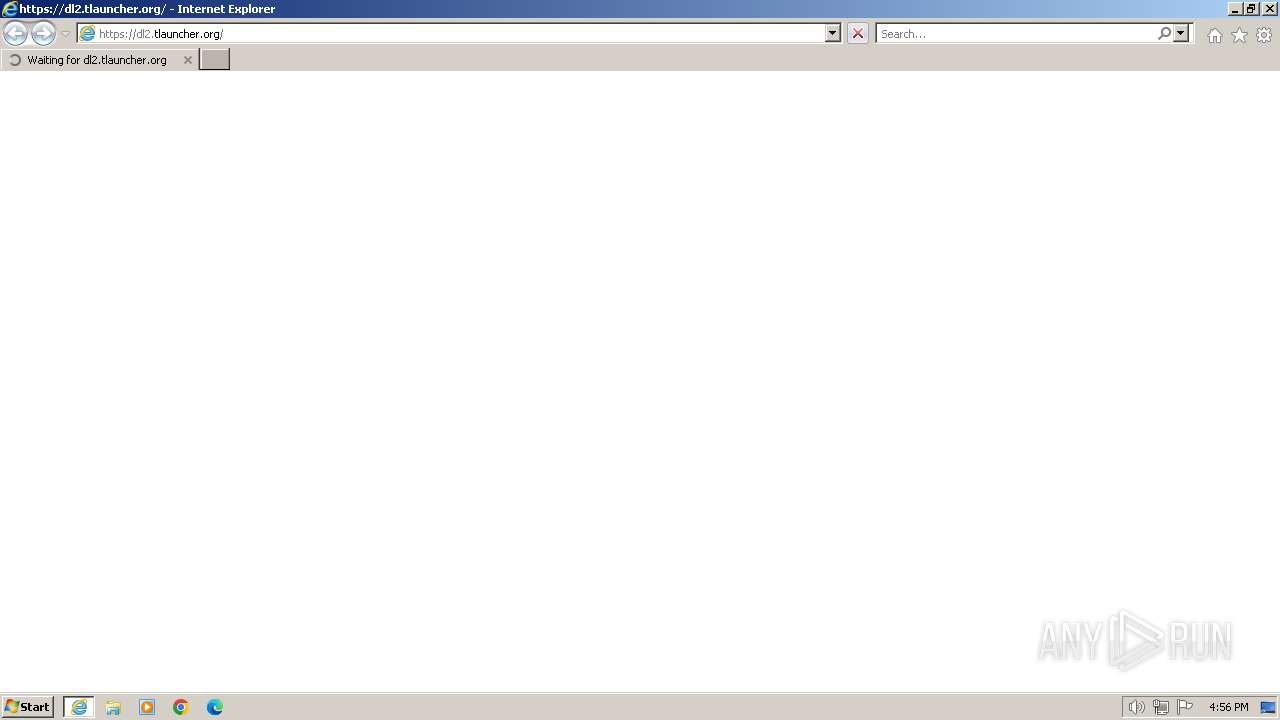
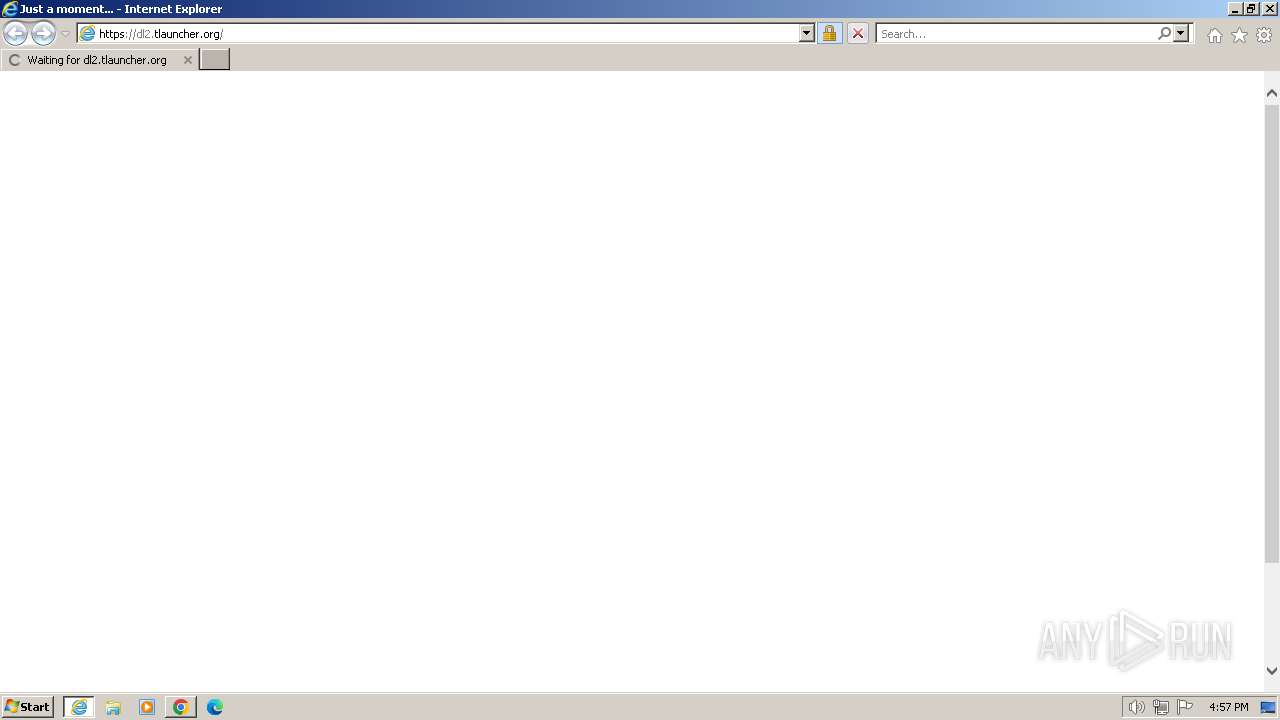
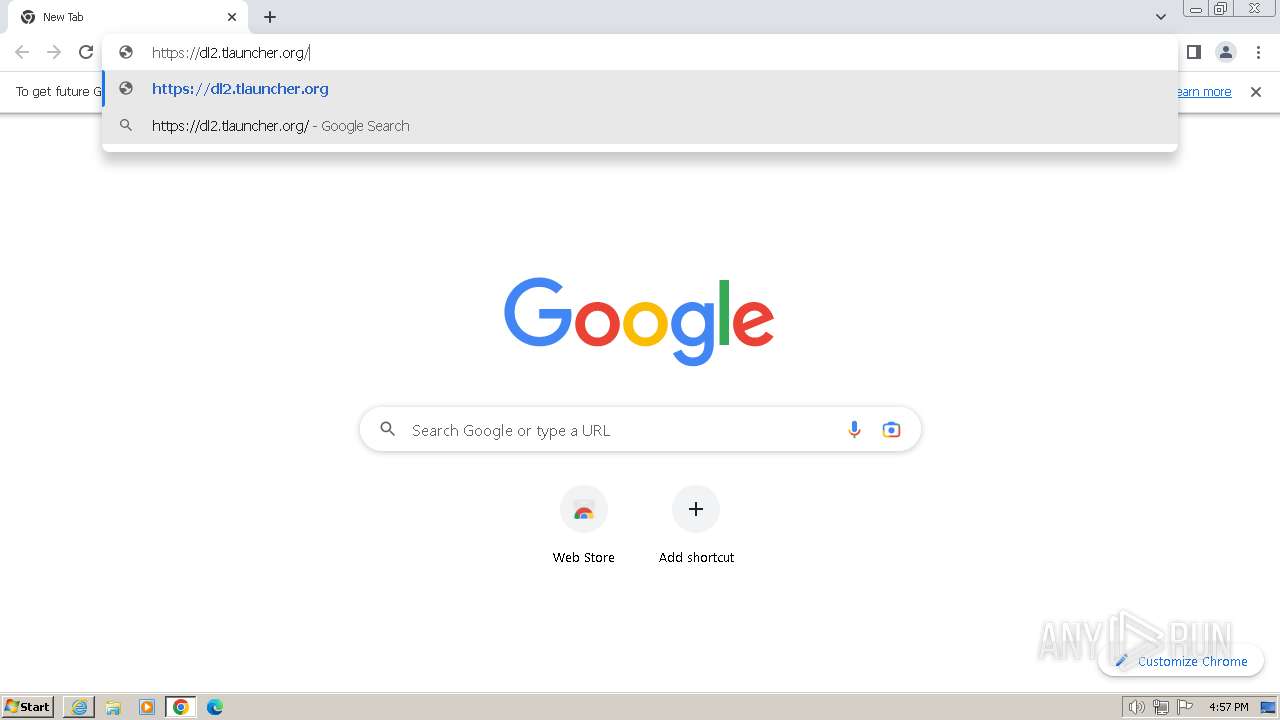
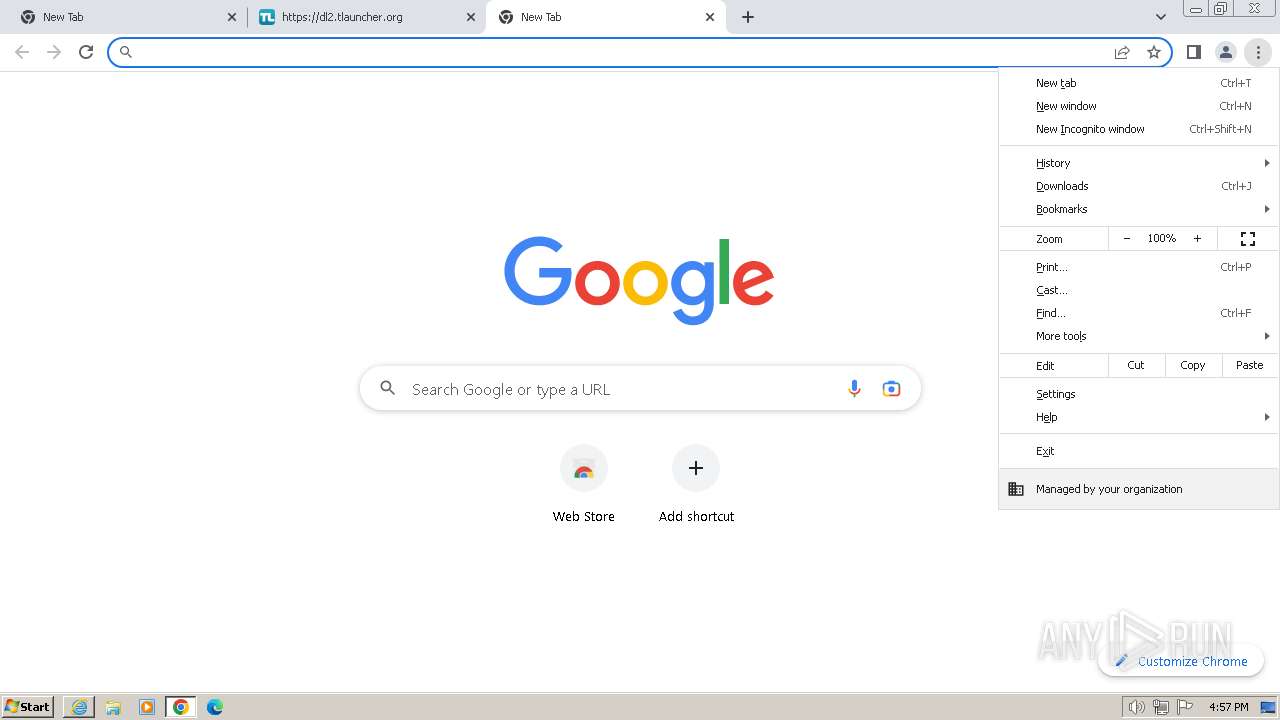
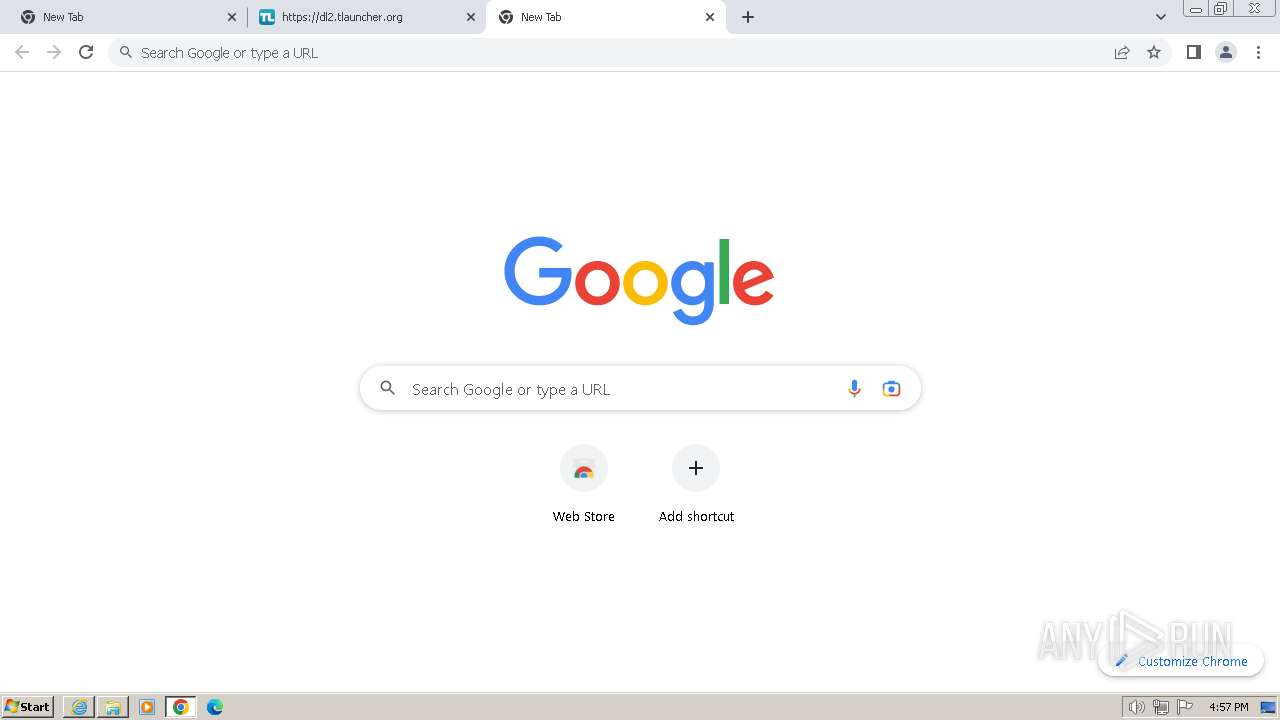
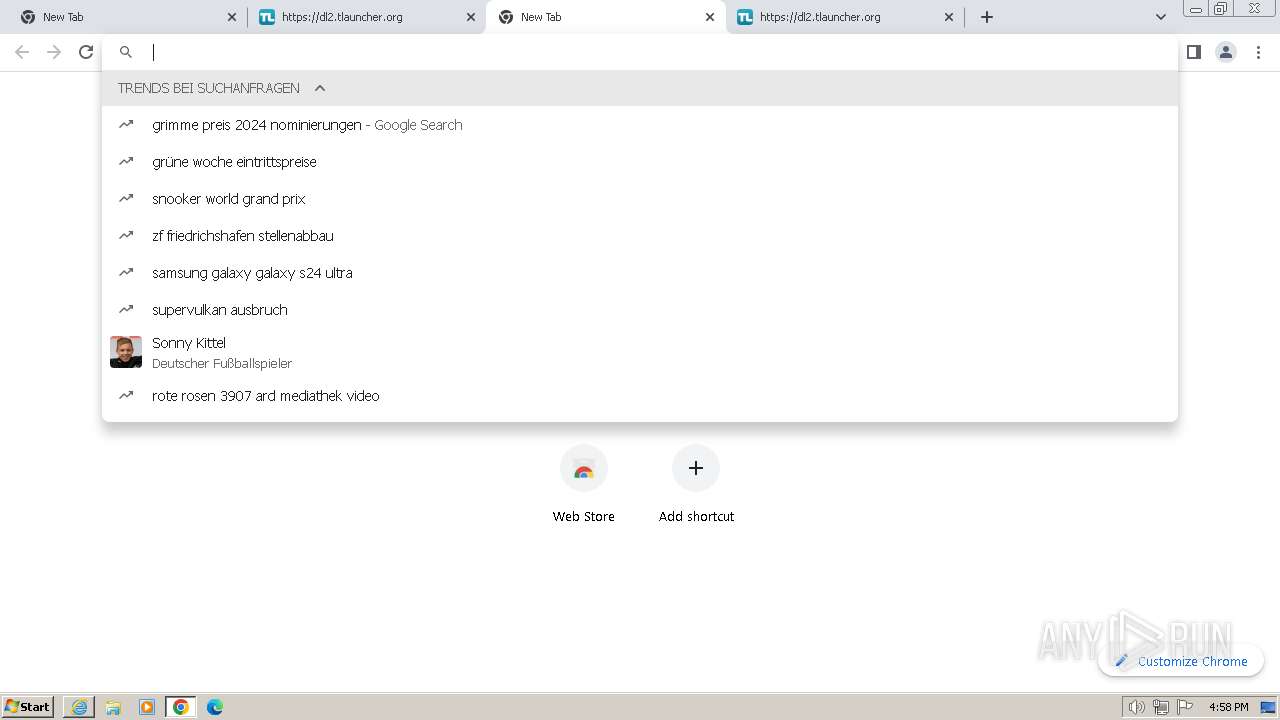
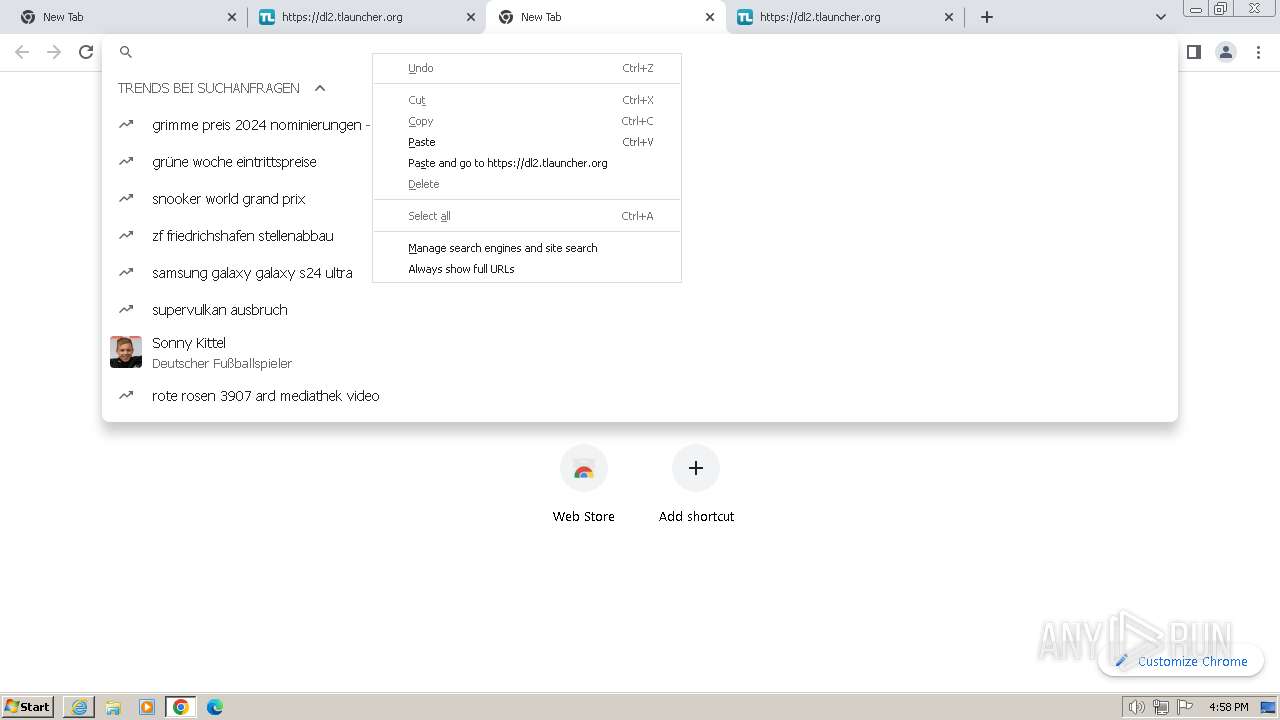
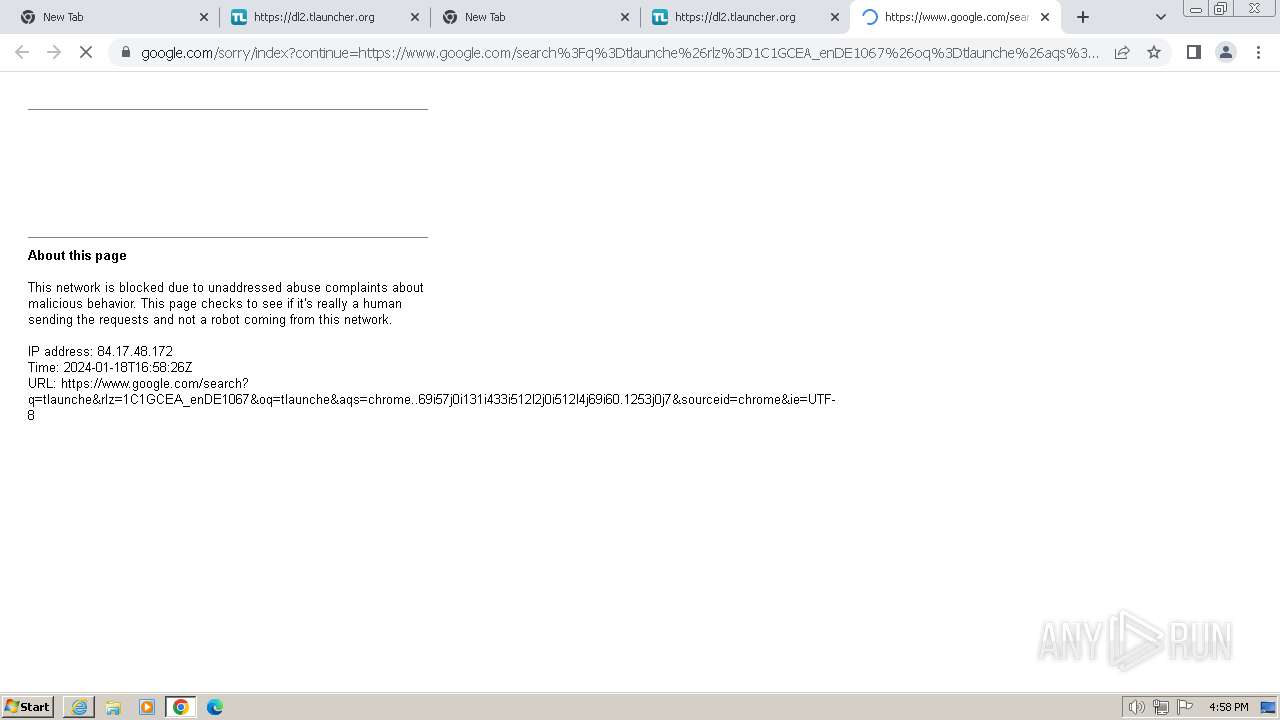
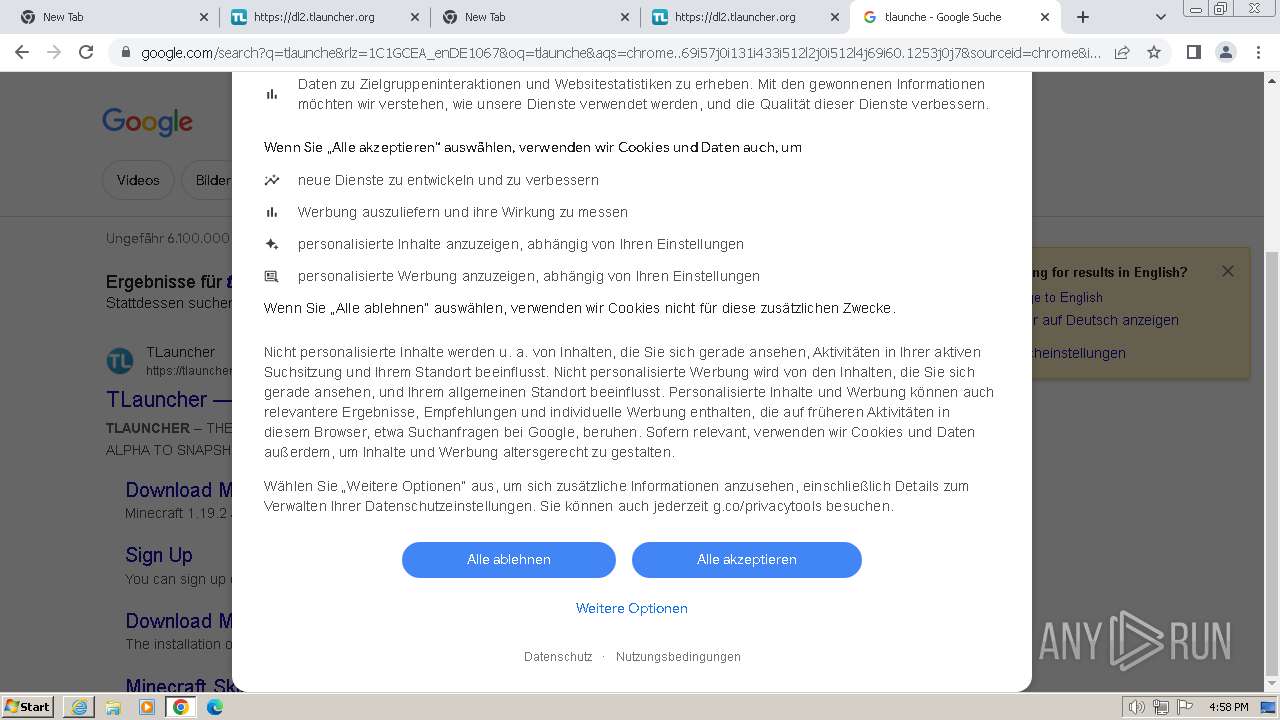
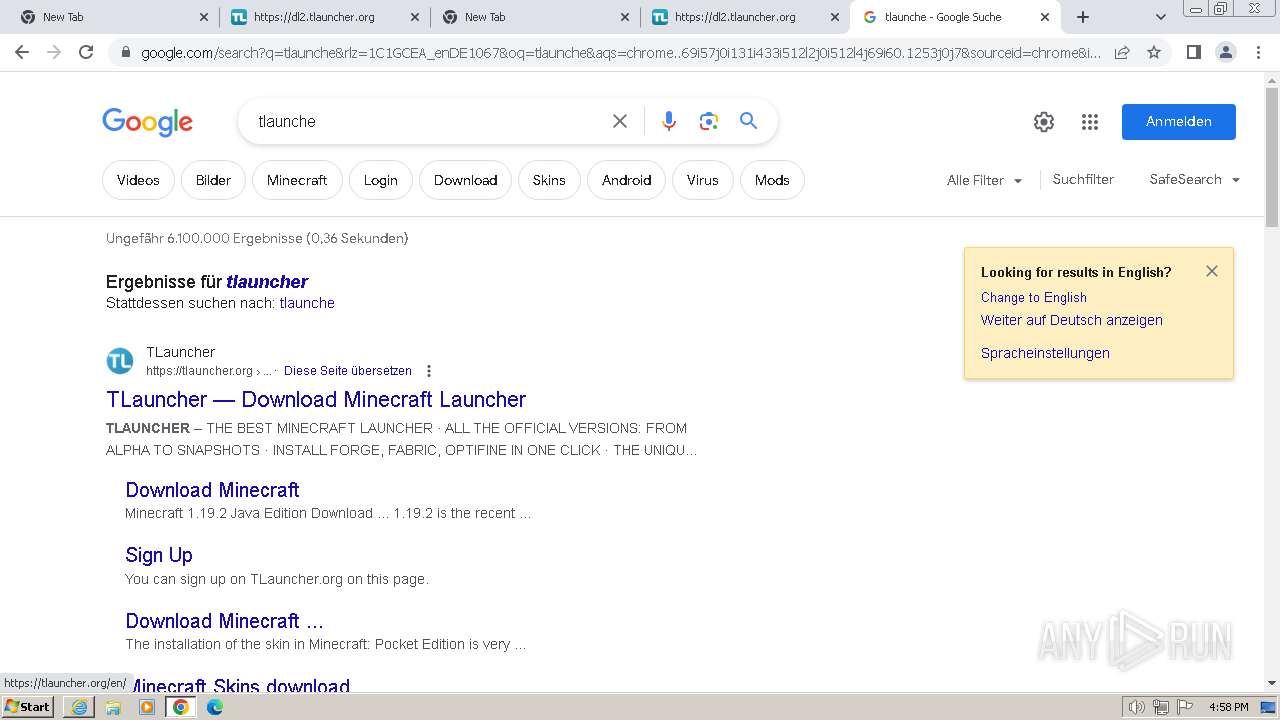
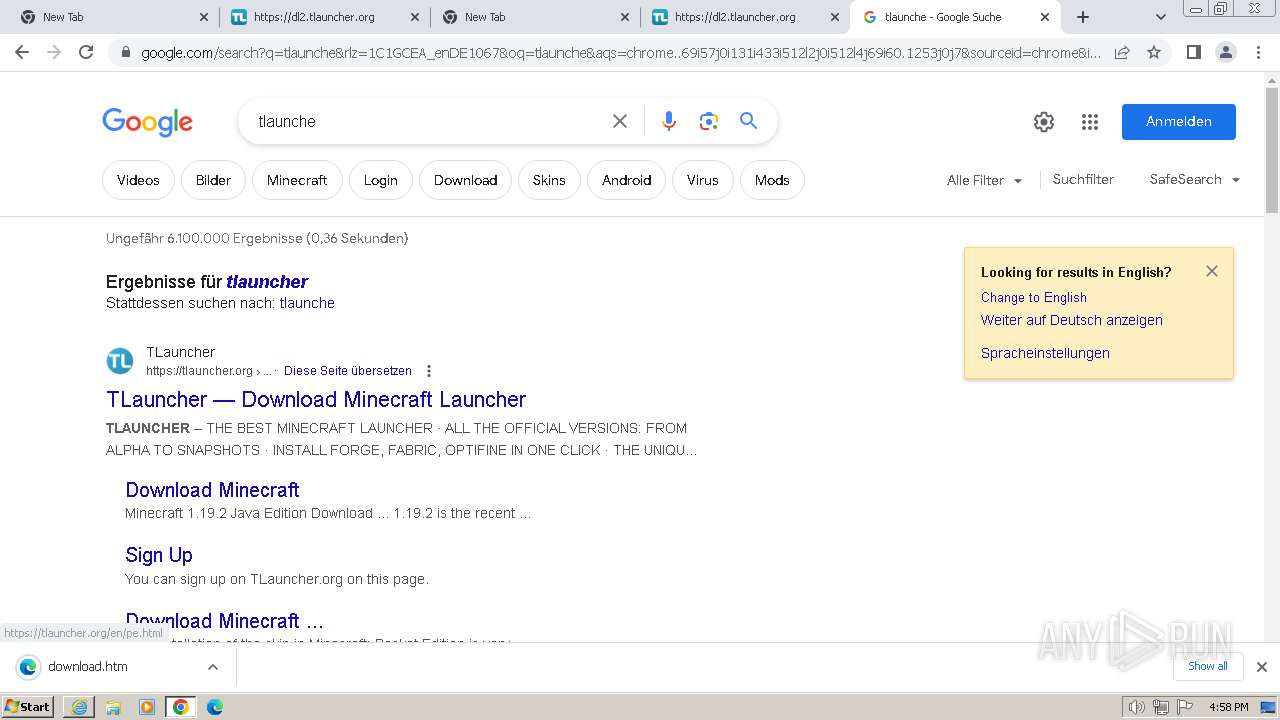
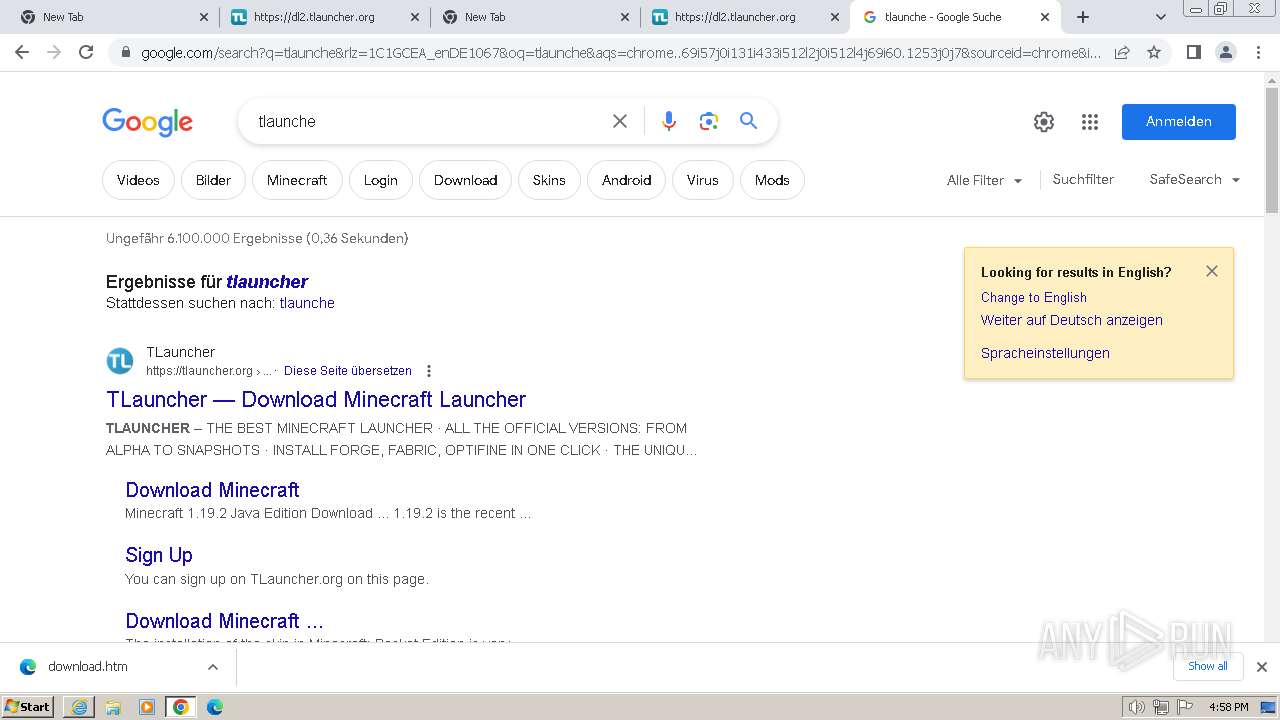
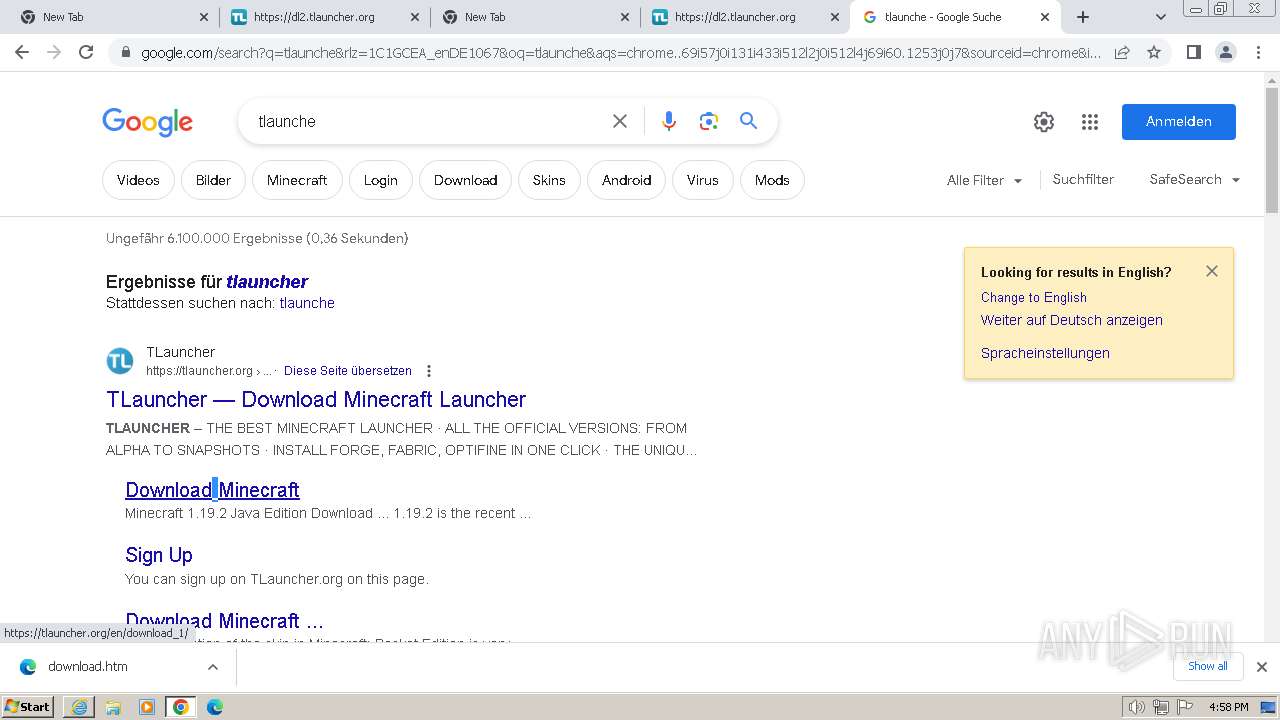
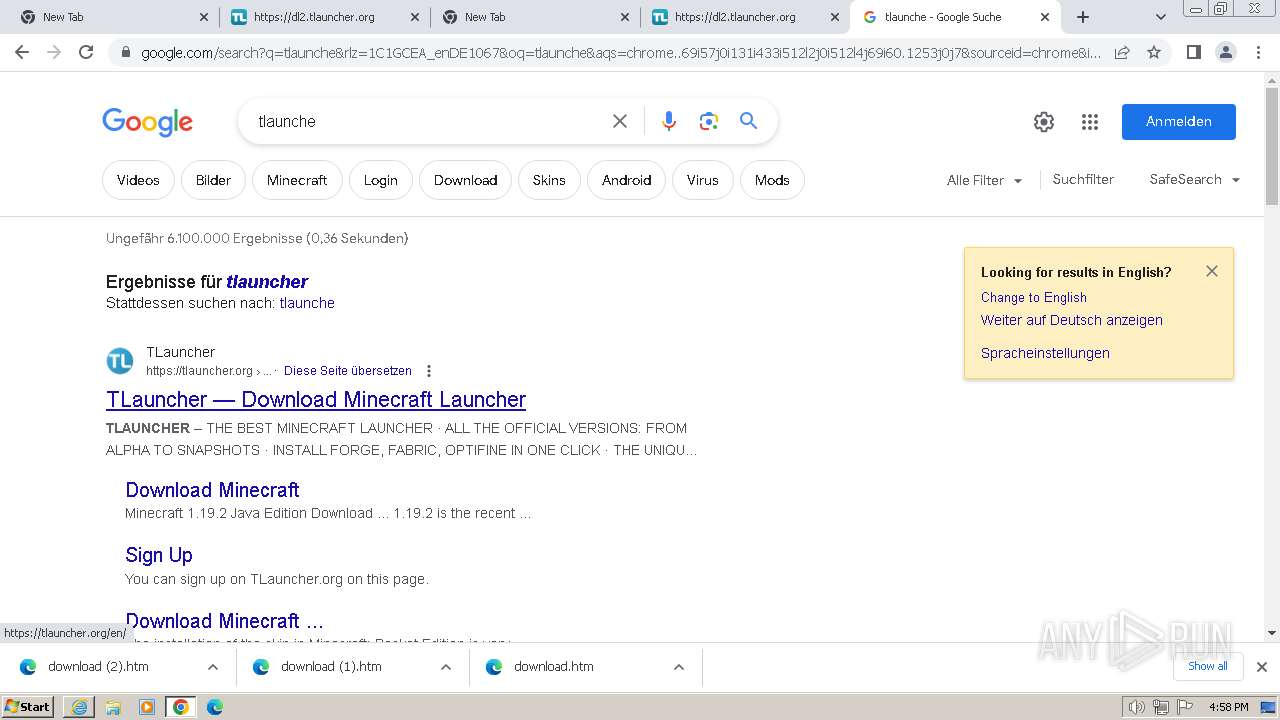
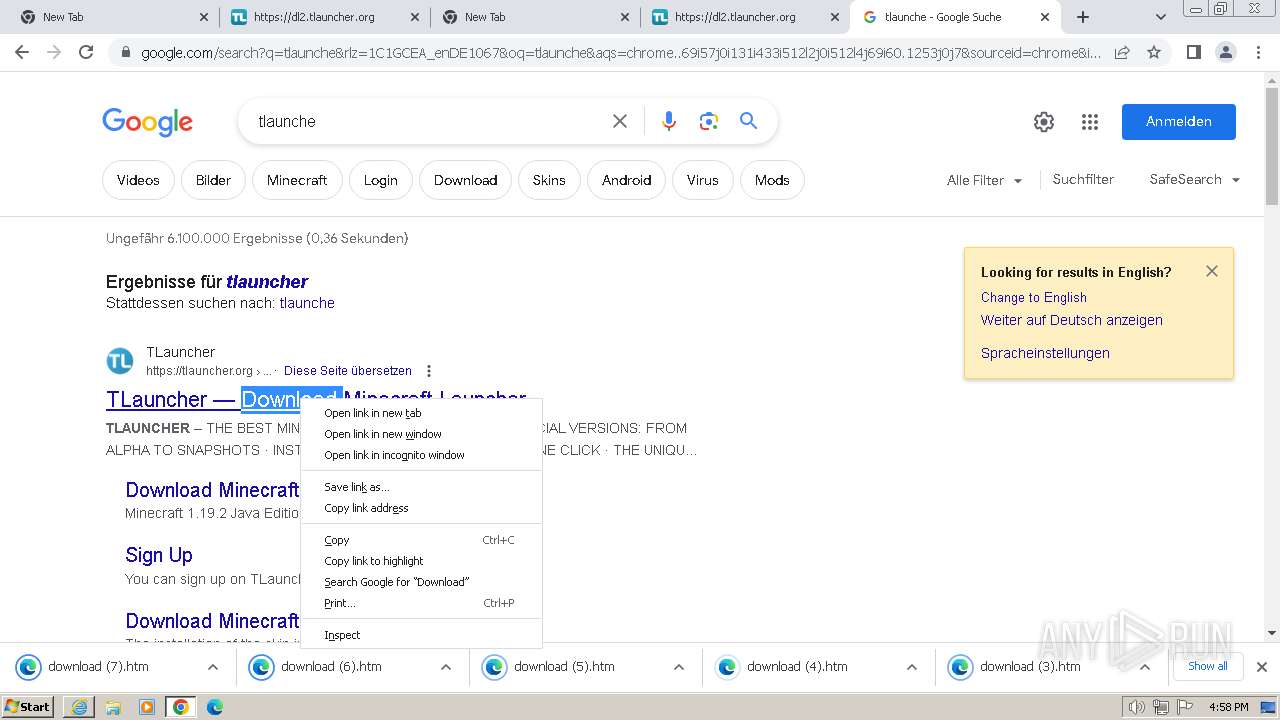
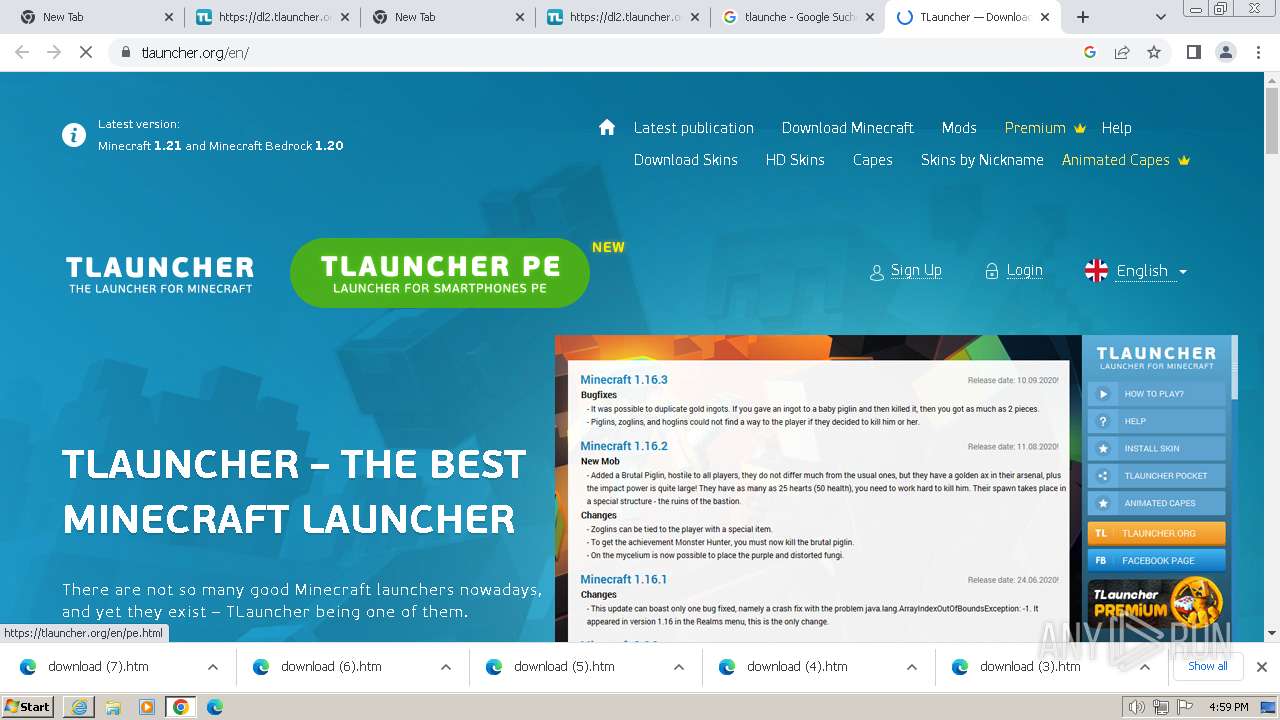
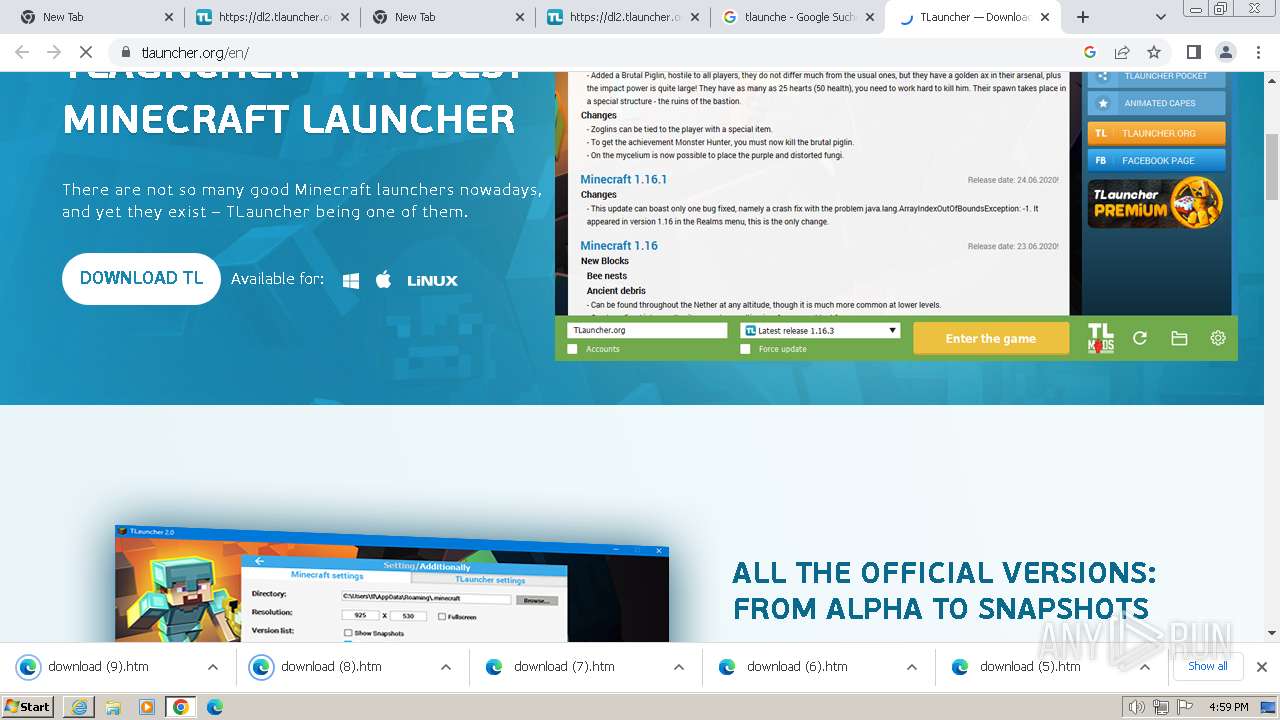
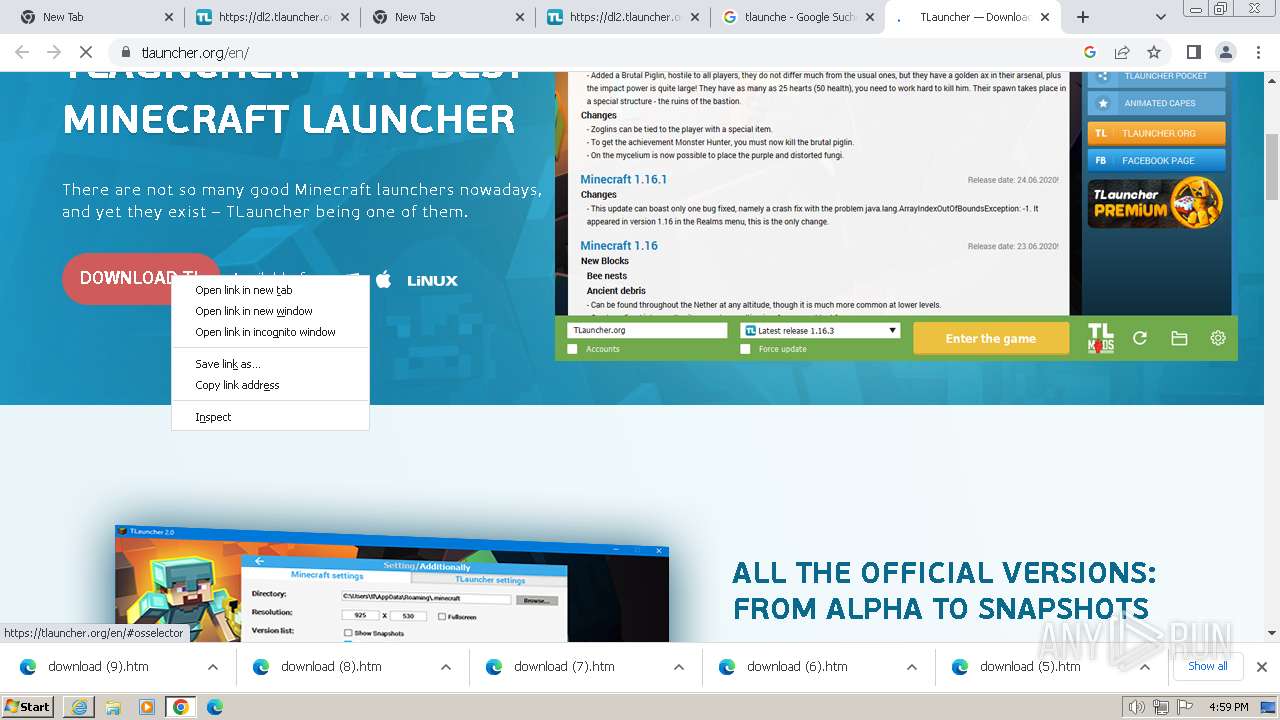
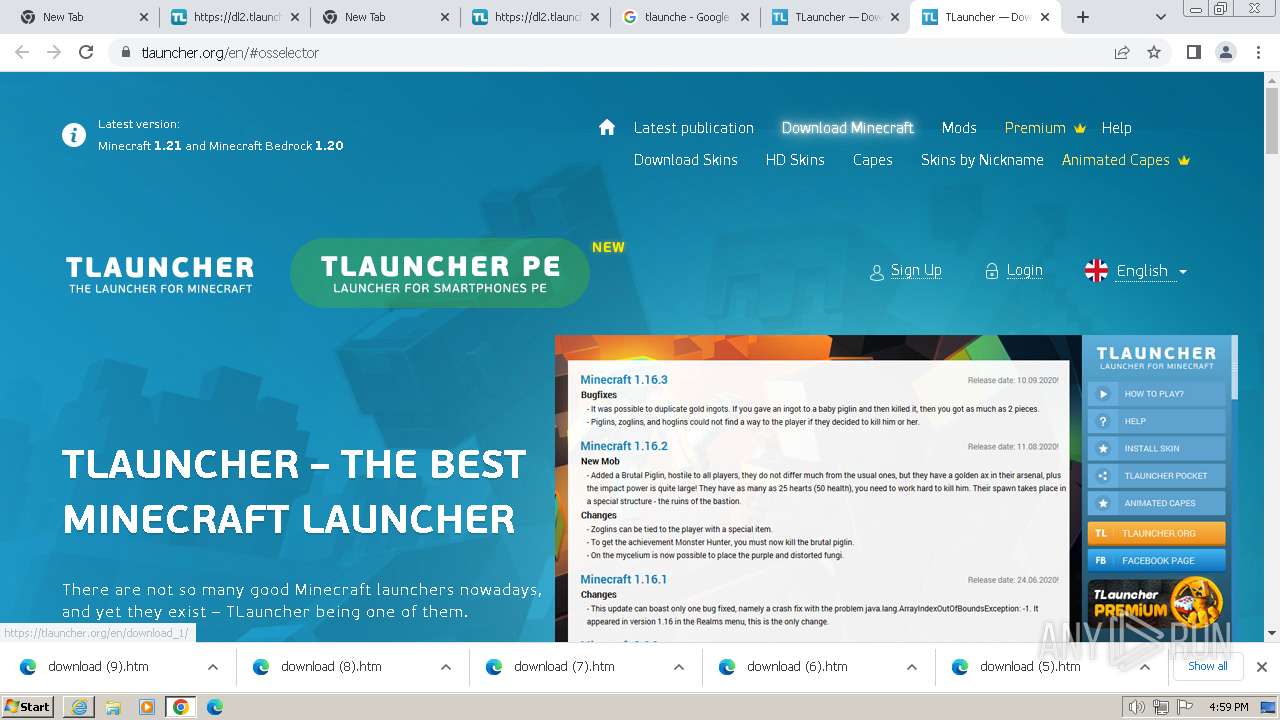
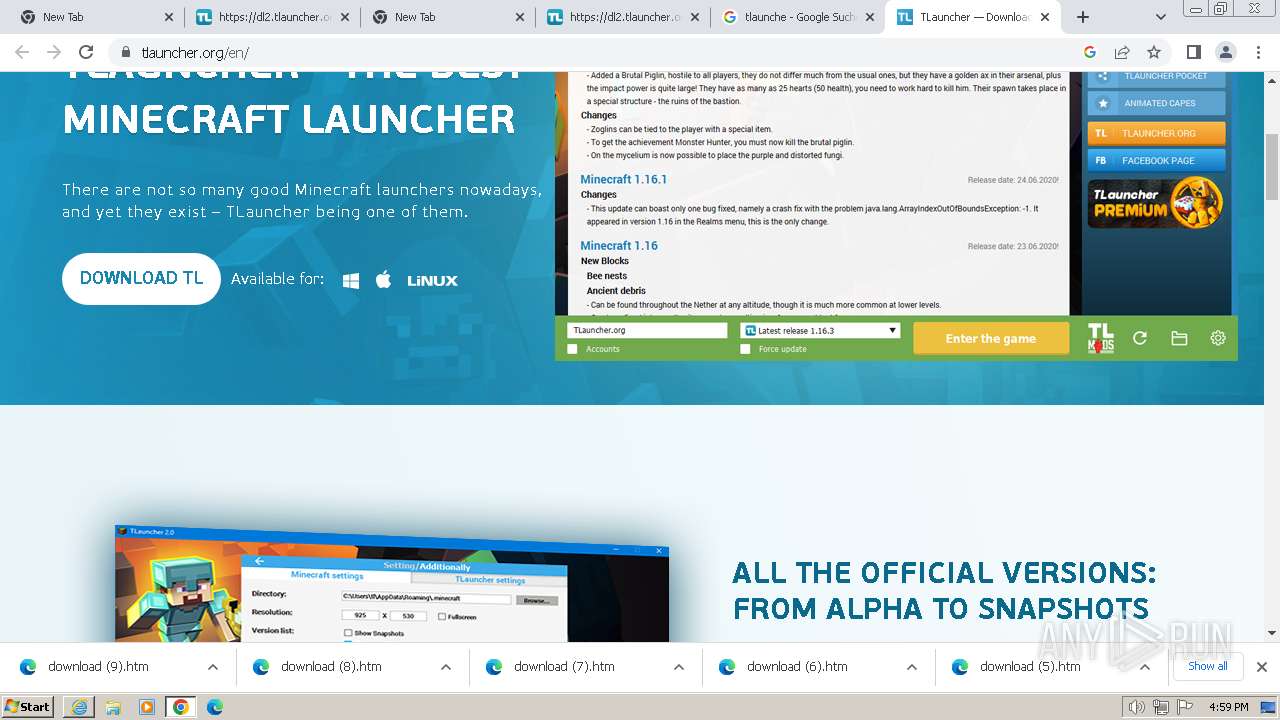
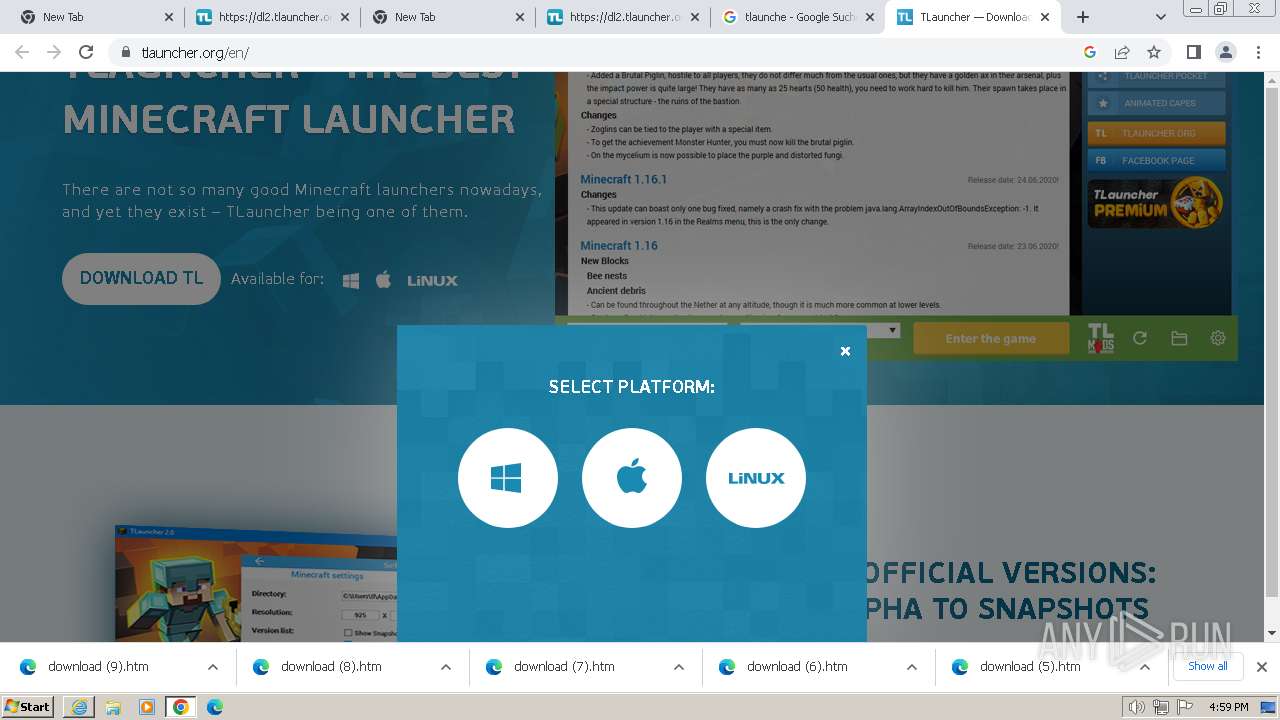
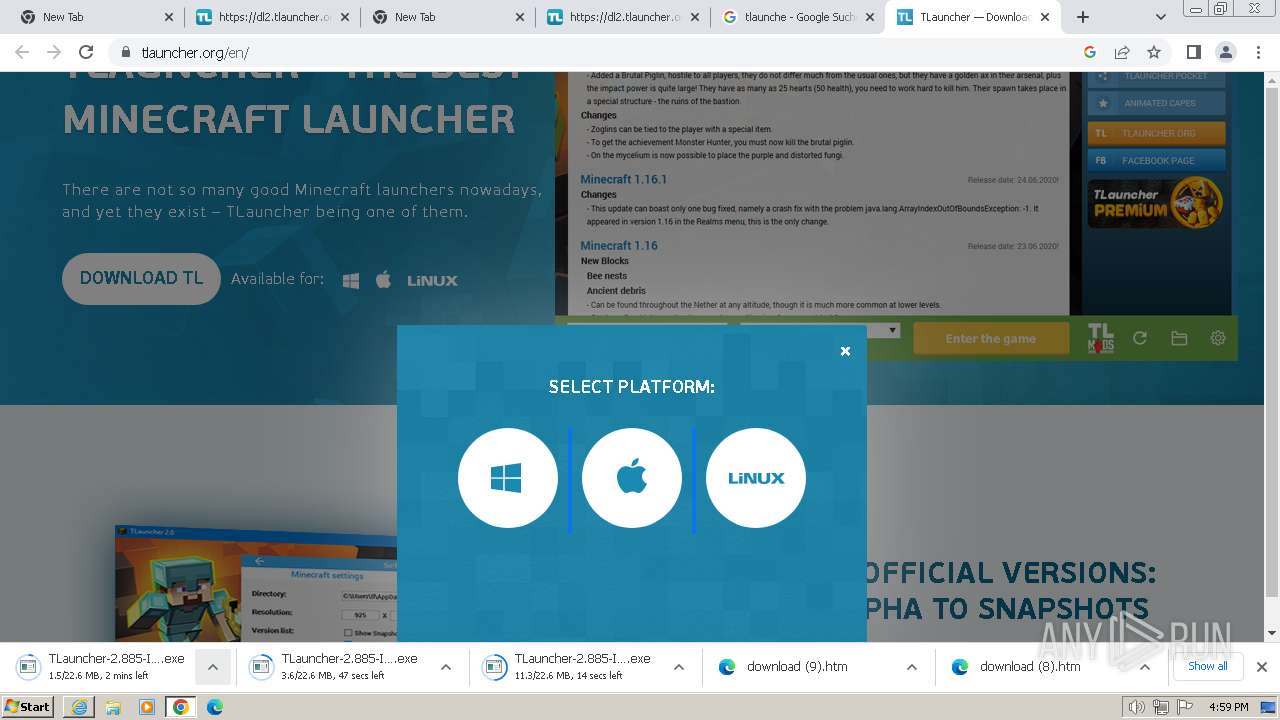
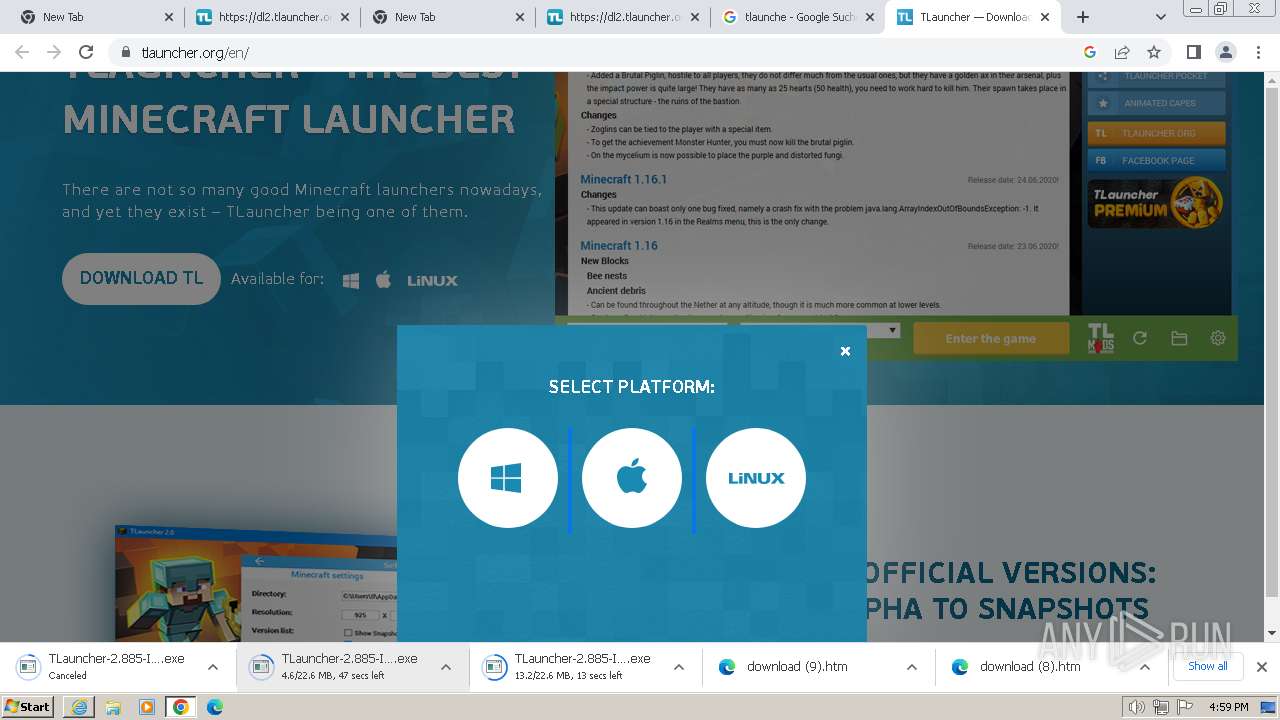
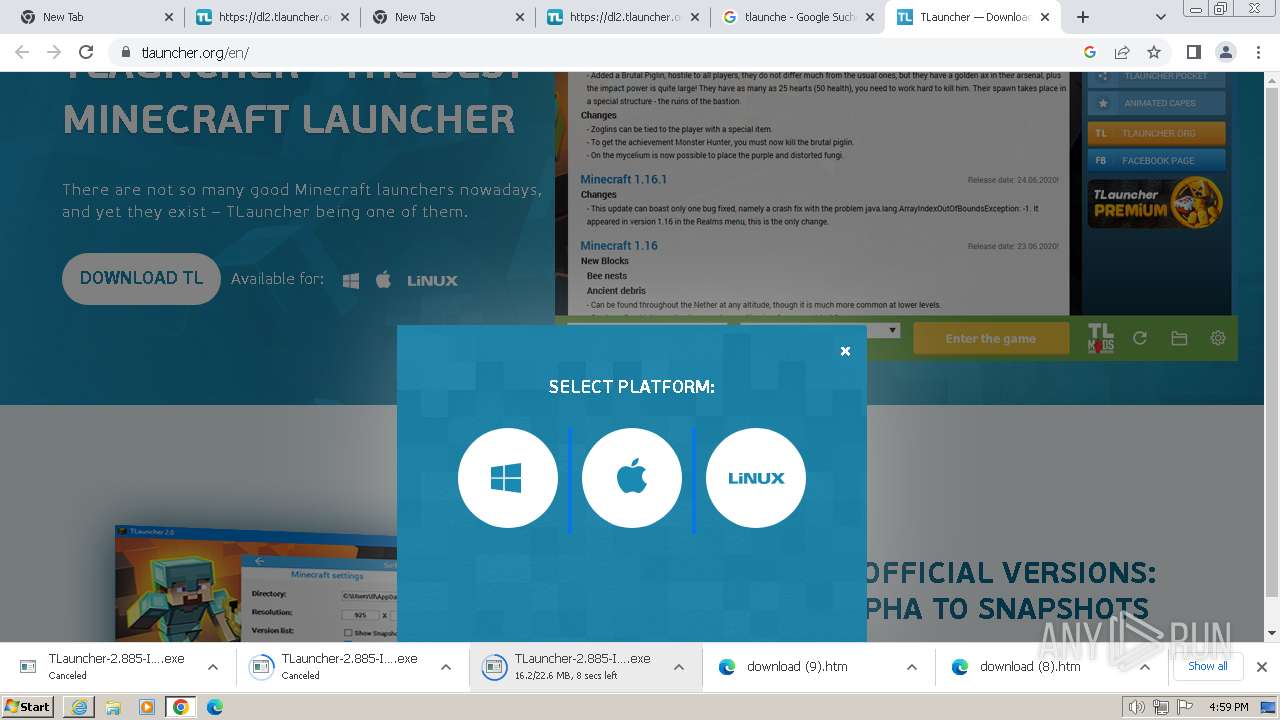
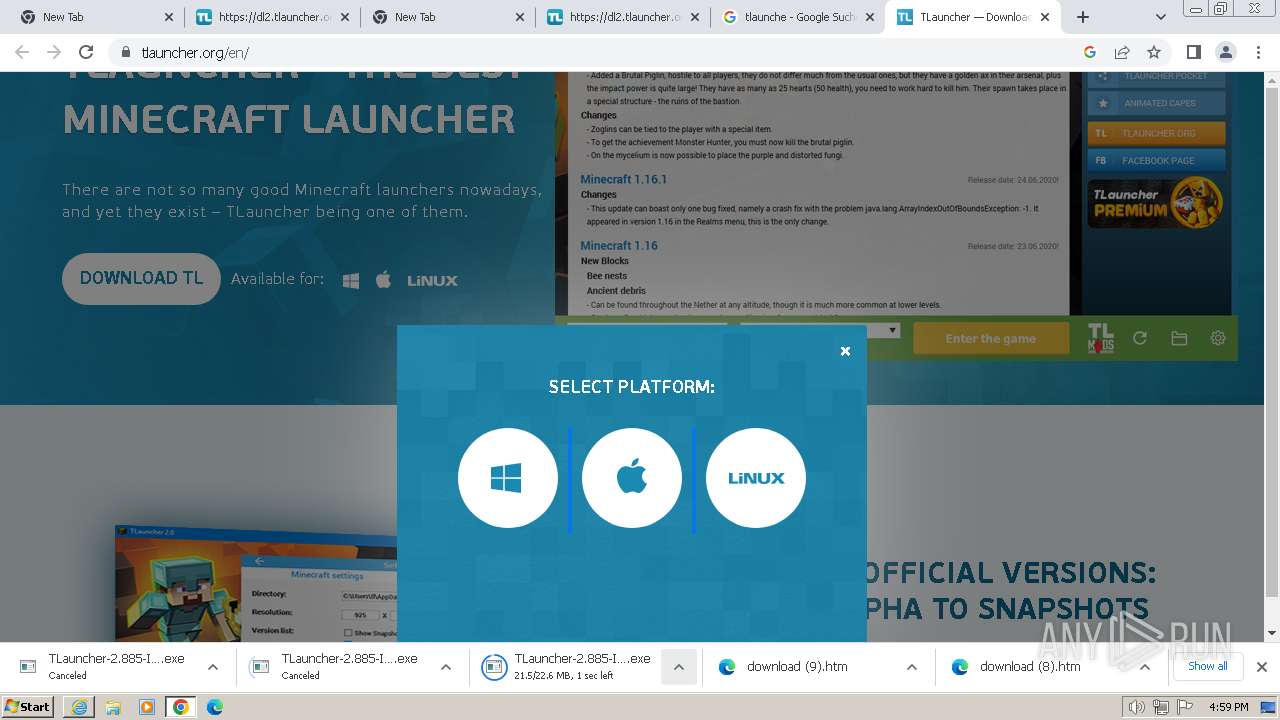
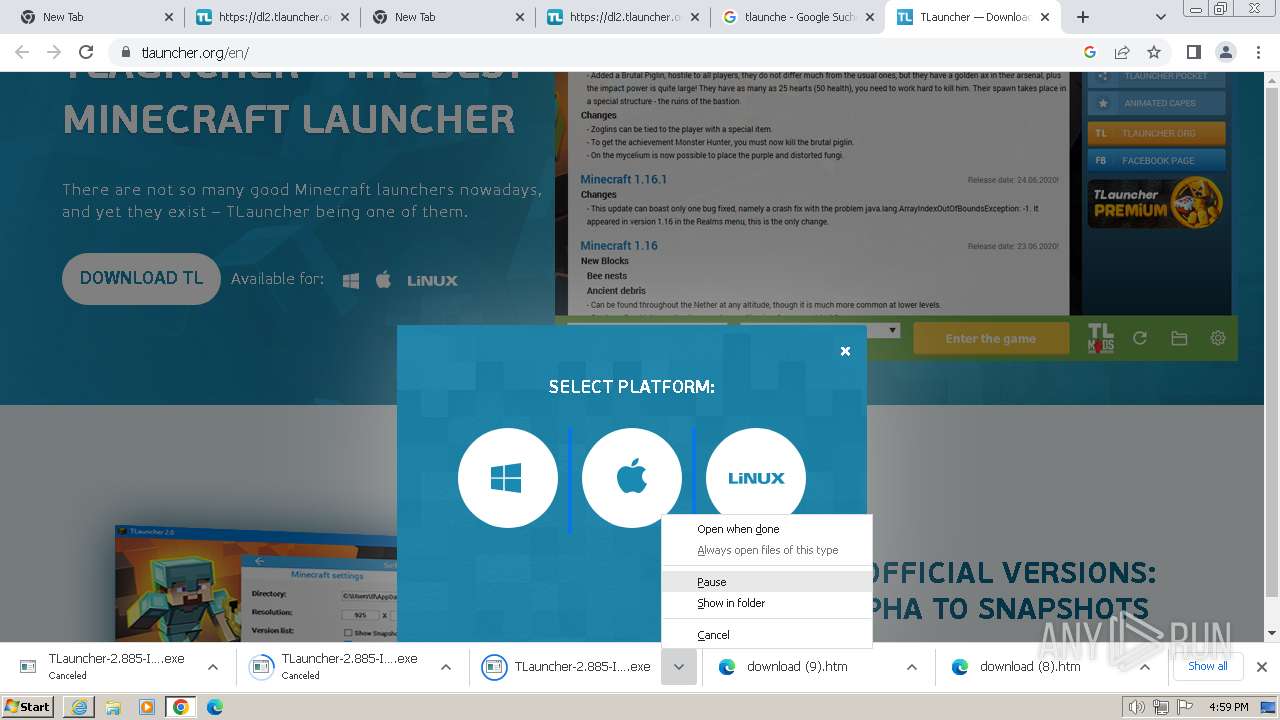
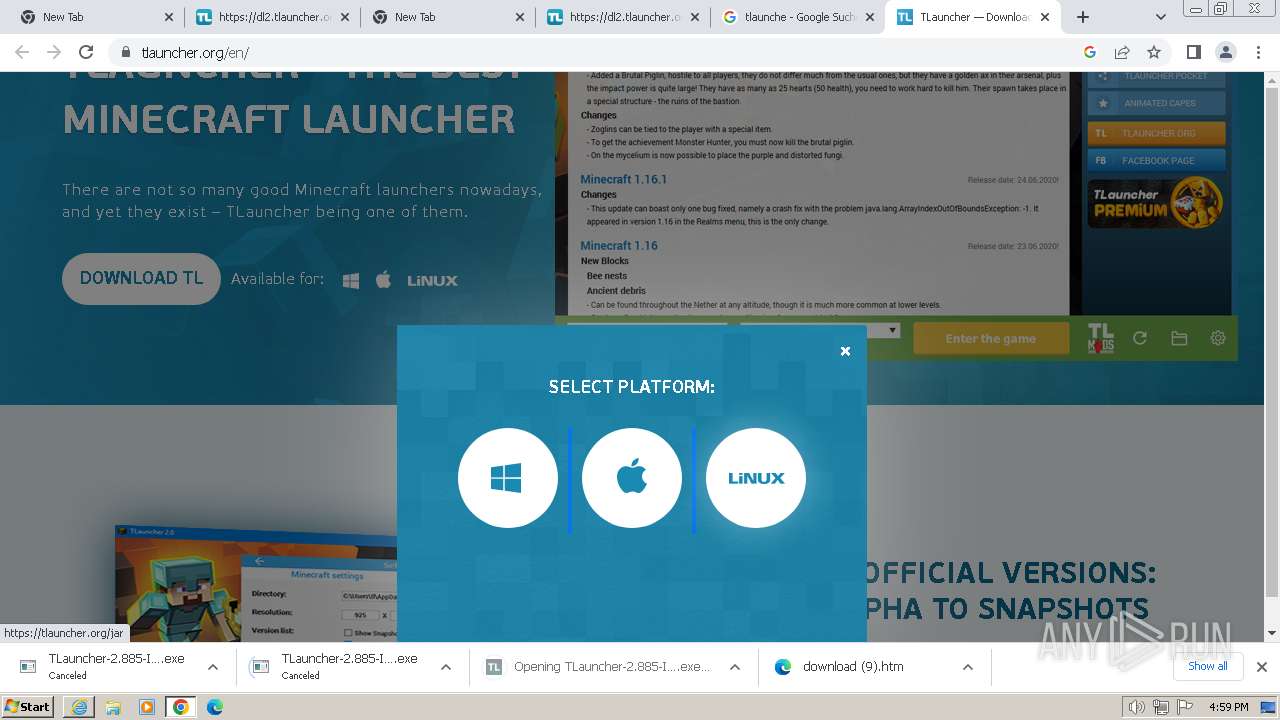
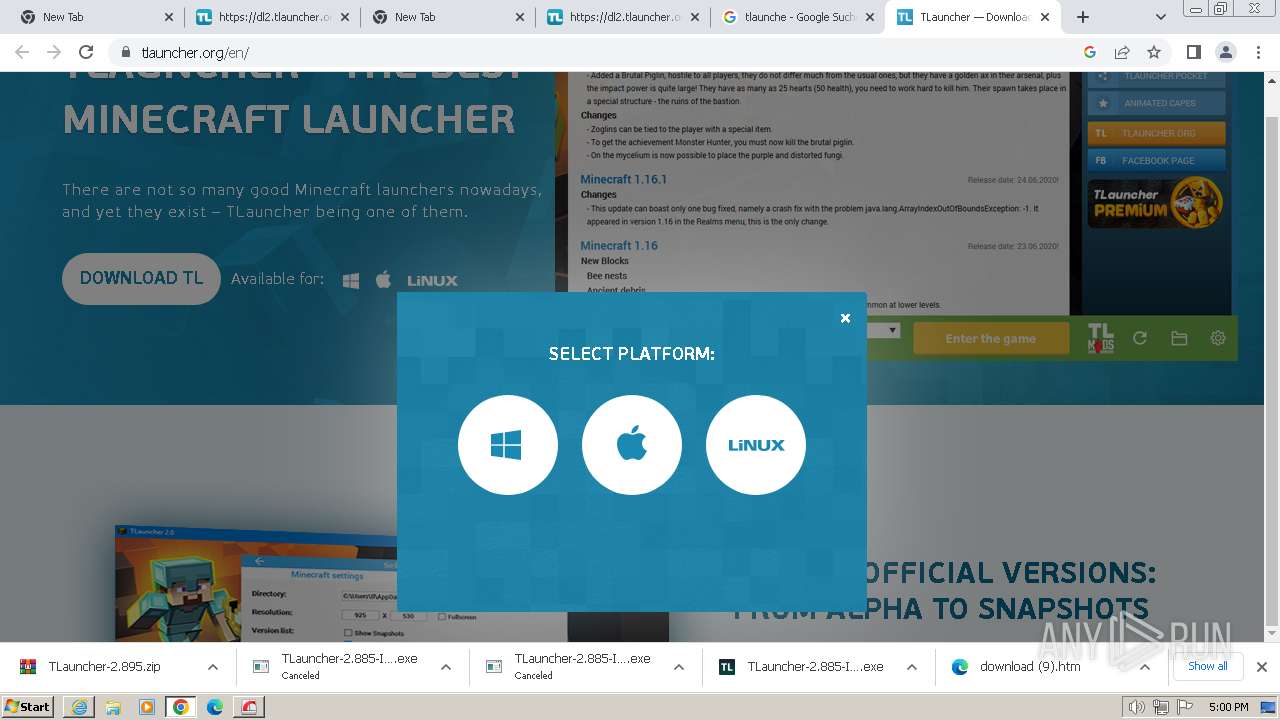
| URL: | https://dl2.tlauncher.org |
| Full analysis: | https://app.any.run/tasks/be08259b-cc95-48ce-b1b3-1b32a9ad8c78 |
| Verdict: | Malicious activity |
| Analysis date: | January 18, 2024, 16:56:37 |
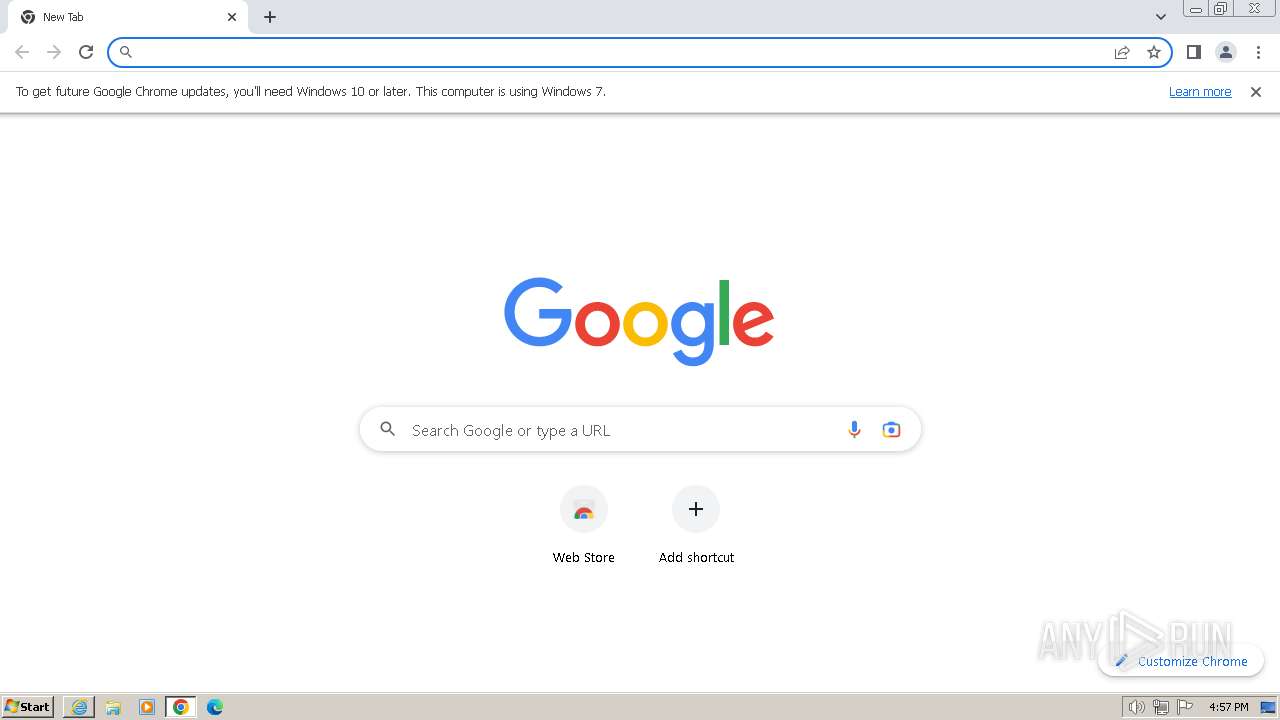
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 29420D3BD7E152A9A9C4225AB733796C |
| SHA1: | 005F34641BDBC334BB6AA777FEA620798D1C2F98 |
| SHA256: | ACCC23EE21EA836325F2FCE0F97286BE11ADAA50C7DC03ACCF23EAB4E84EEEFC |
| SSDEEP: | 3:N8R1JVLuS:2D/6S |
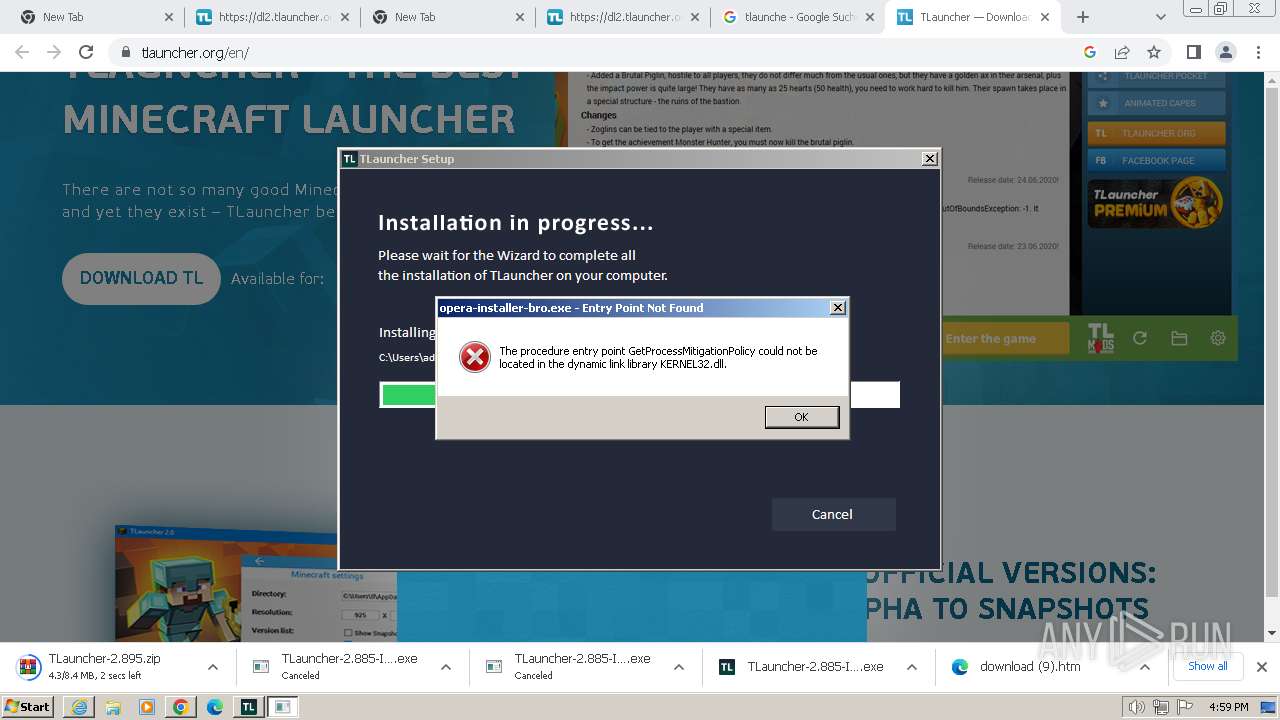
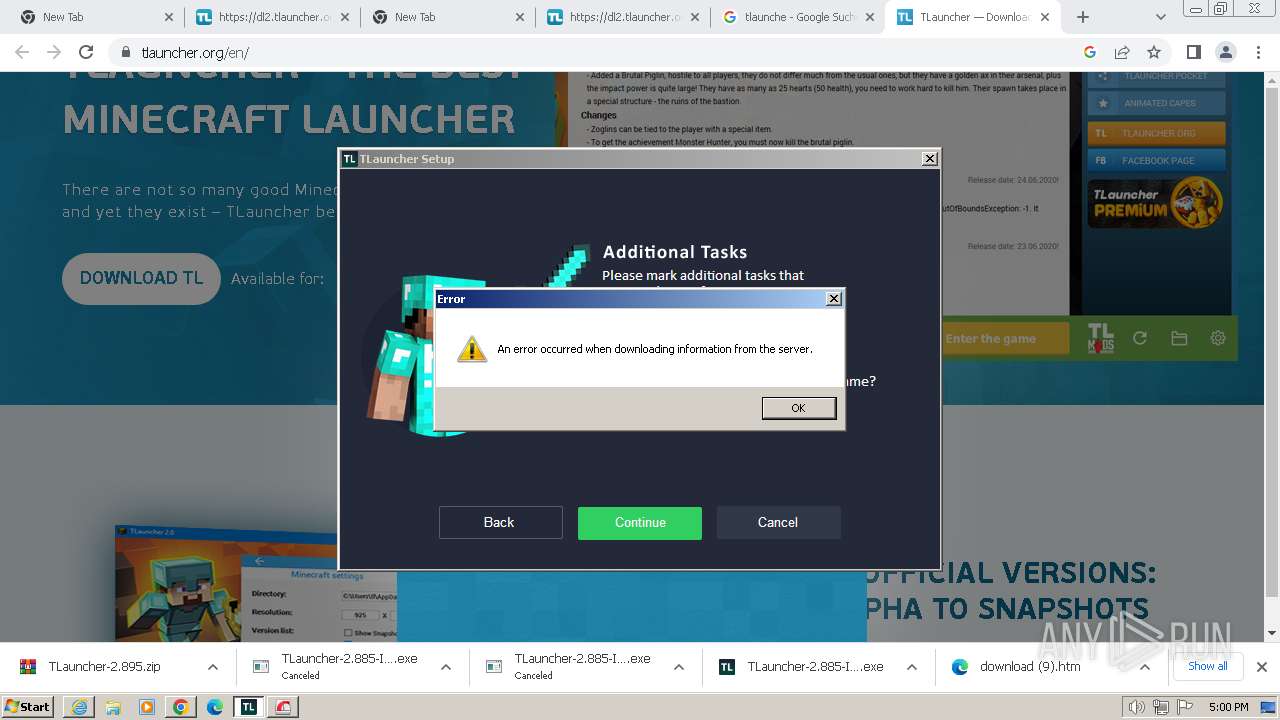
MALICIOUS
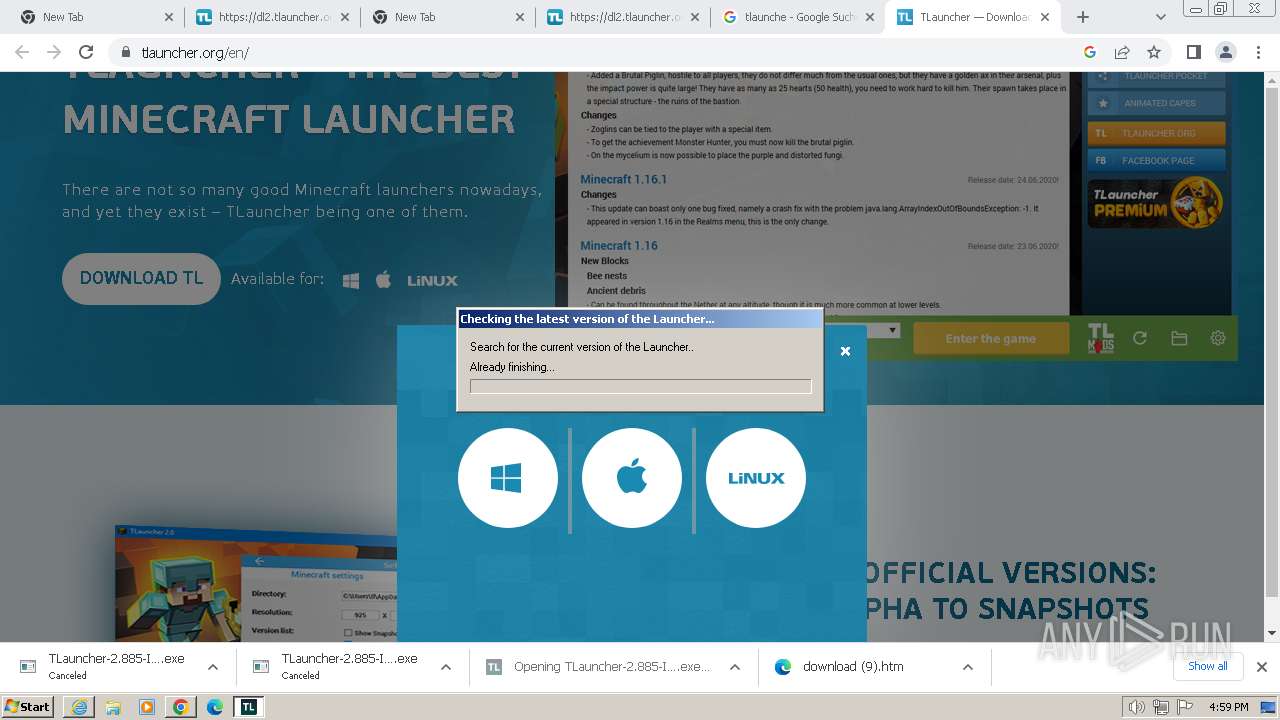
Drops the executable file immediately after the start
- irsetup.exe (PID: 3988)
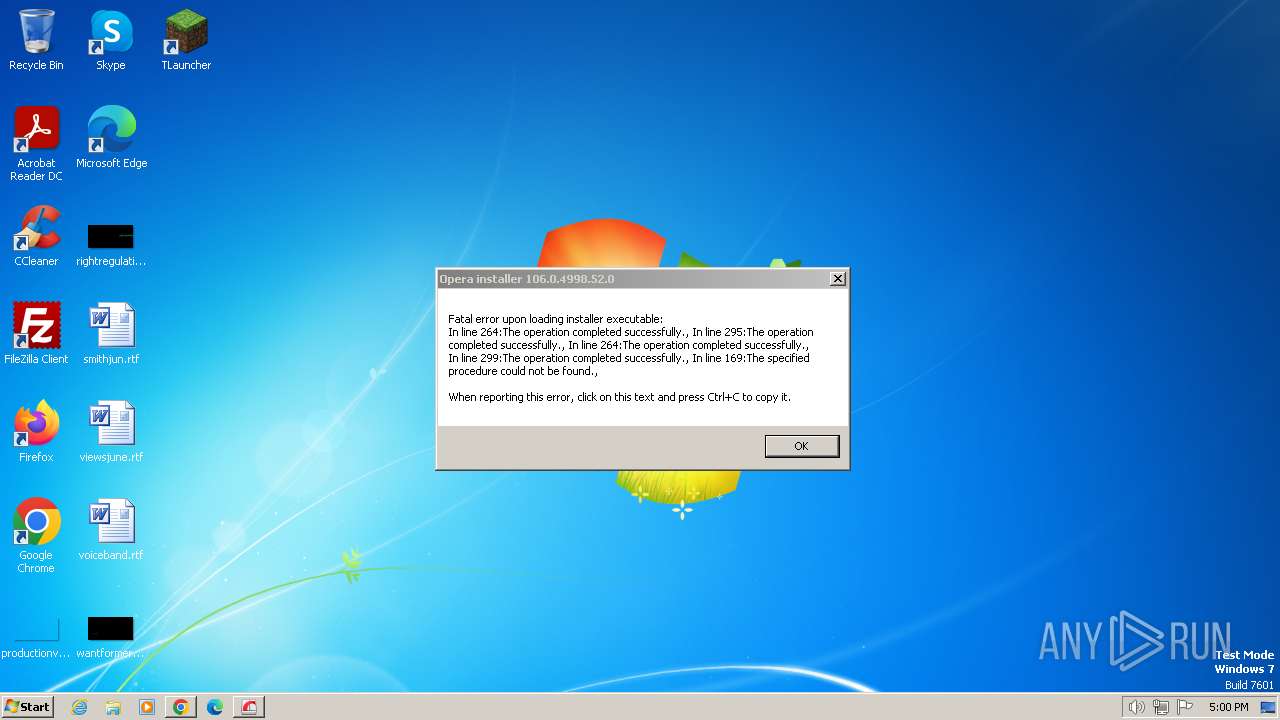
- BrowserInstaller.exe (PID: 1644)
- opera-installer-bro.exe (PID: 2088)
- irsetup.exe (PID: 3268)
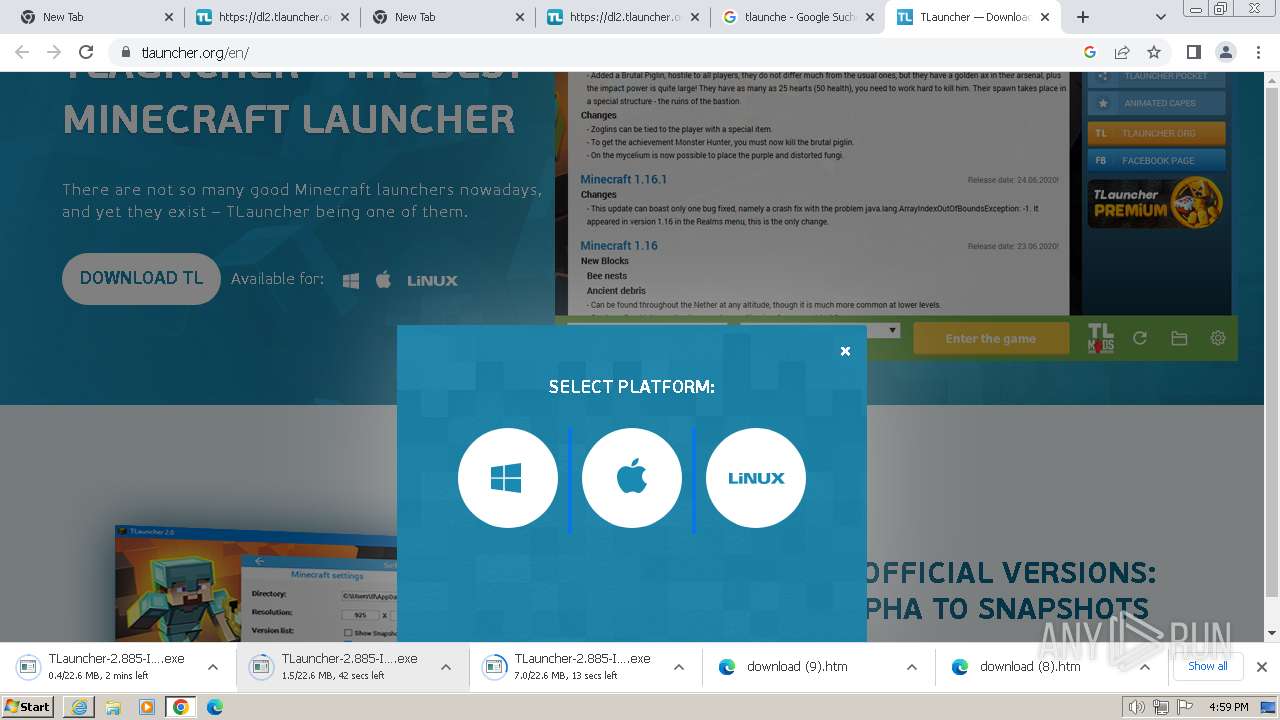
- TLauncher-2.885-Installer-1.1.3.exe (PID: 3924)
Actions looks like stealing of personal data
- irsetup.exe (PID: 3988)
SUSPICIOUS
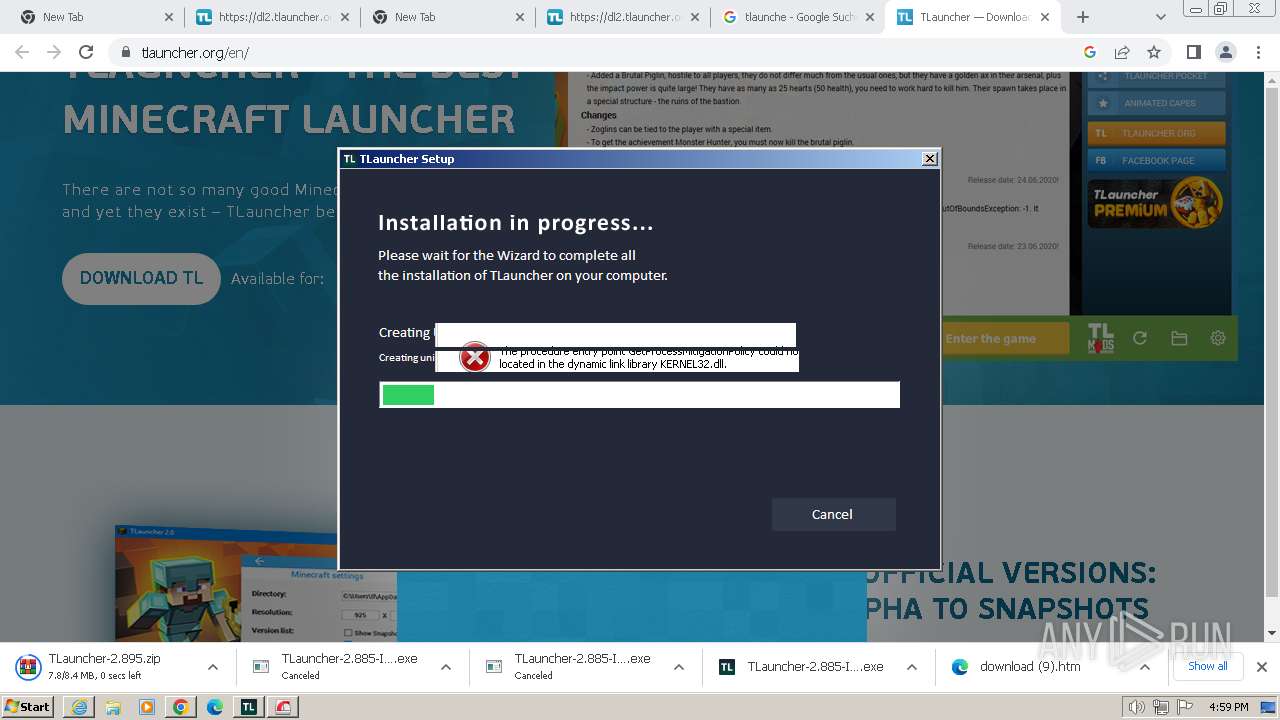
Executable content was dropped or overwritten
- TLauncher-2.885-Installer-1.1.3.exe (PID: 3924)
- irsetup.exe (PID: 3988)
- BrowserInstaller.exe (PID: 1644)
- irsetup.exe (PID: 3268)
- opera-installer-bro.exe (PID: 2088)
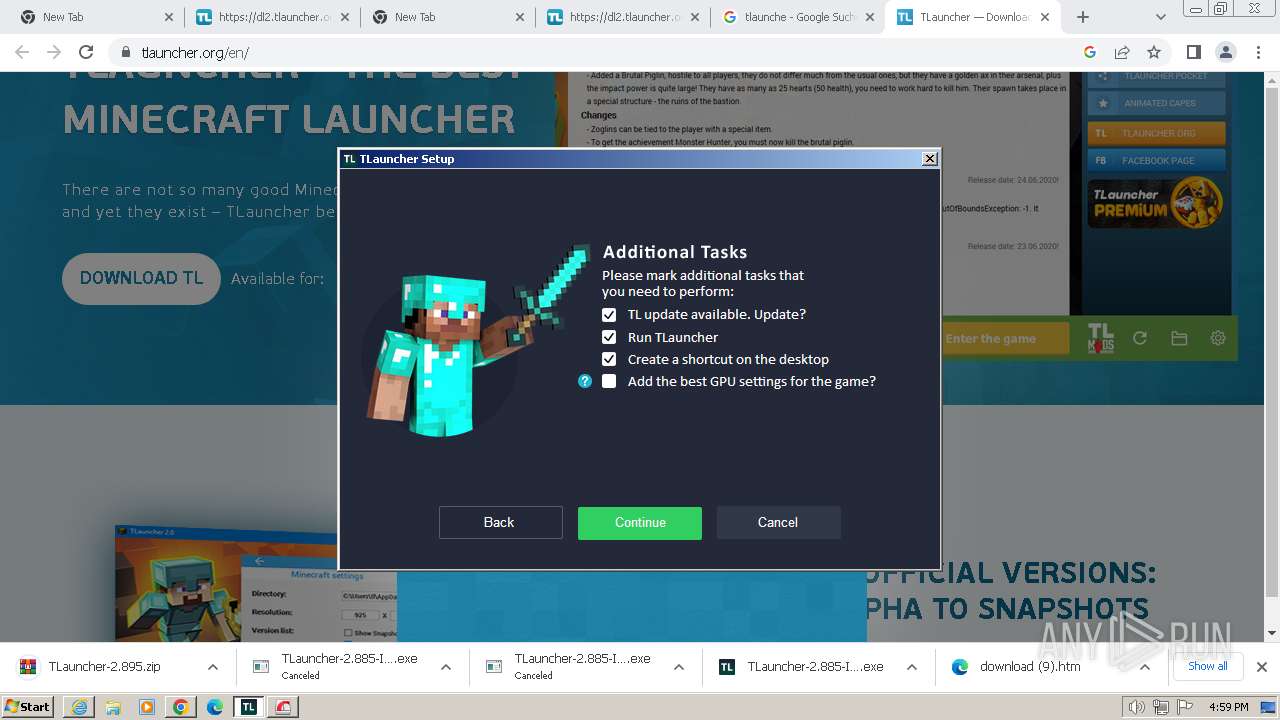
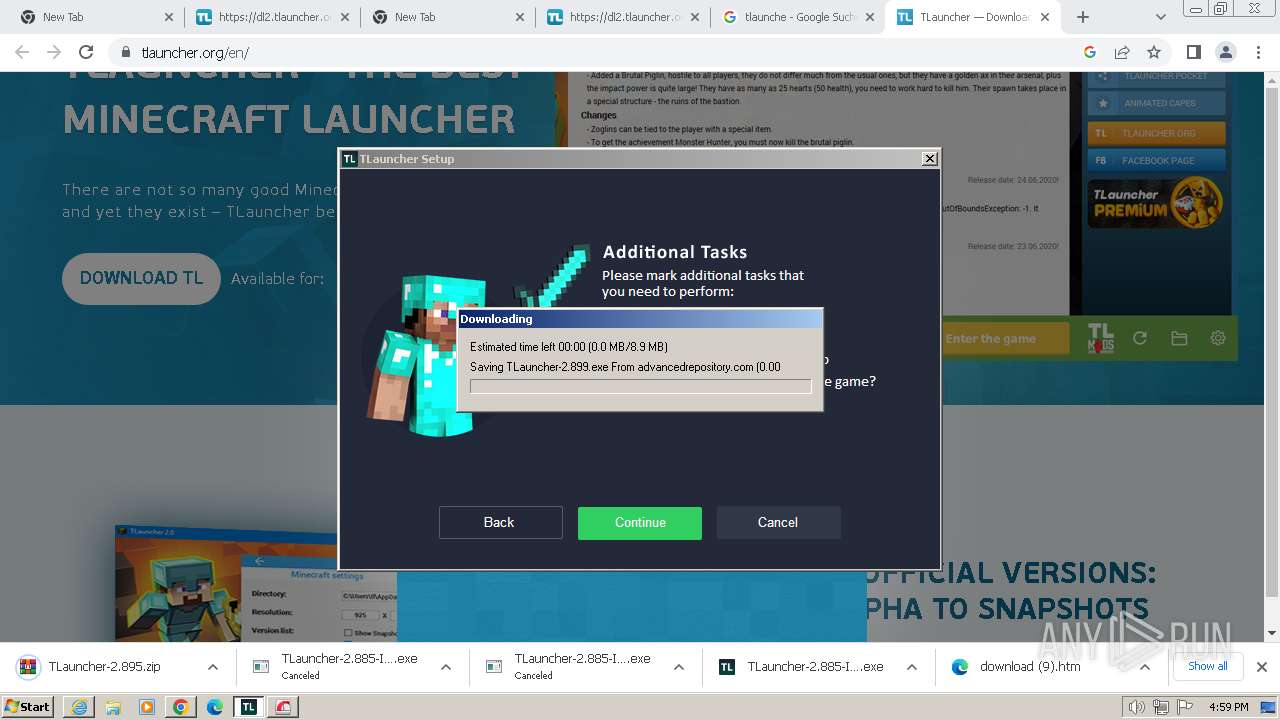
Reads the Internet Settings
- TLauncher-2.885-Installer-1.1.3.exe (PID: 3924)
- irsetup.exe (PID: 3988)
- BrowserInstaller.exe (PID: 1644)
- irsetup.exe (PID: 3268)
Reads the Windows owner or organization settings
- irsetup.exe (PID: 3988)
- irsetup.exe (PID: 3268)
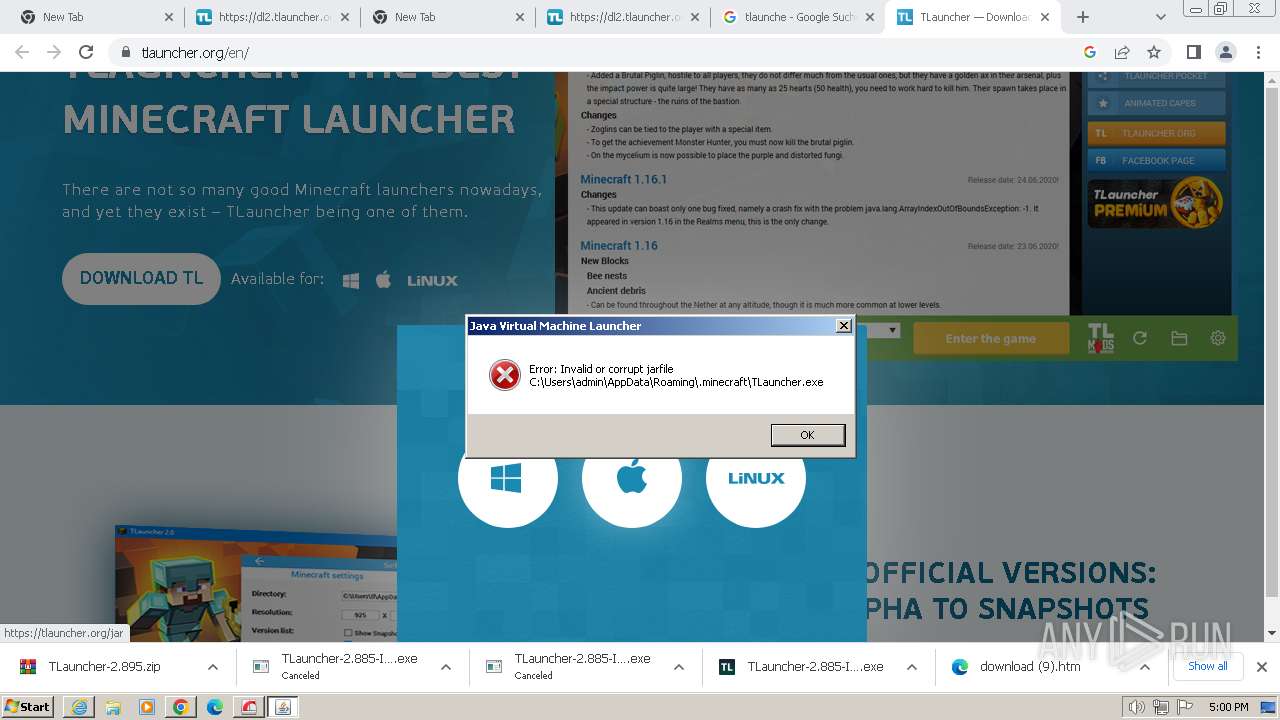
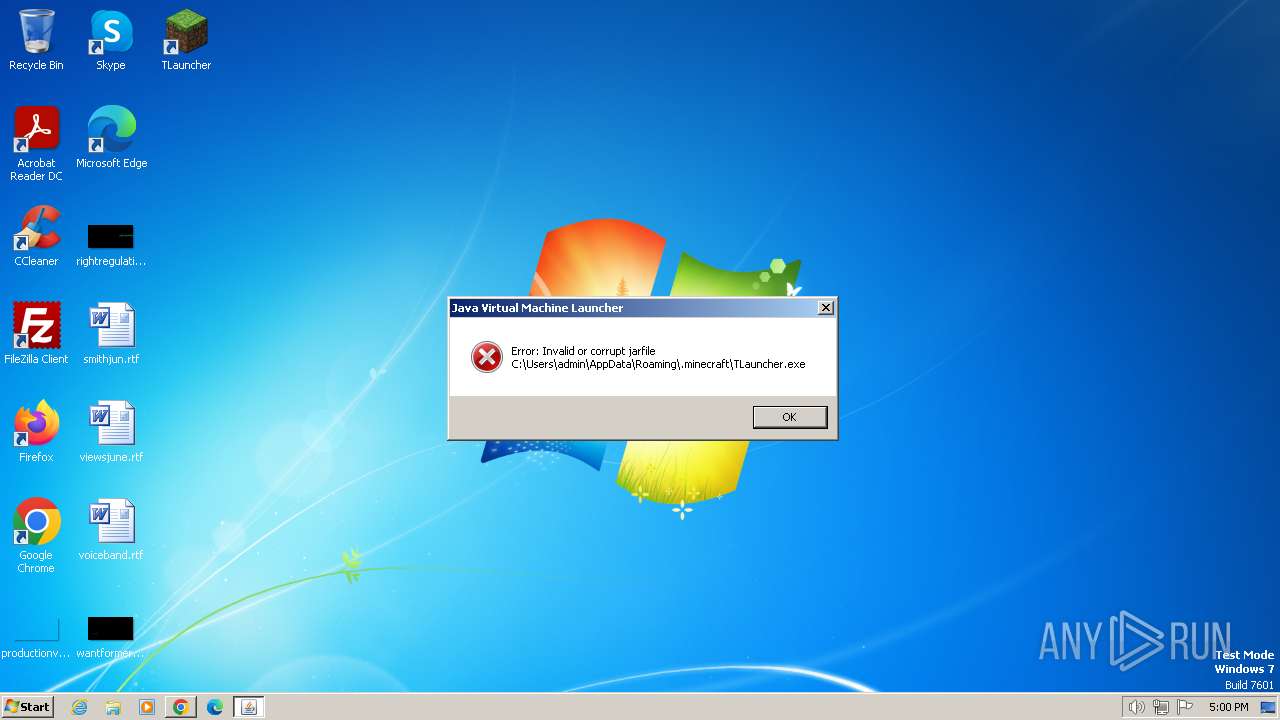
Checks for Java to be installed
- irsetup.exe (PID: 3988)
- TLauncher.exe (PID: 532)
- TLauncher.exe (PID: 4052)
Reads security settings of Internet Explorer
- irsetup.exe (PID: 3988)
- irsetup.exe (PID: 3268)
Reads settings of System Certificates
- irsetup.exe (PID: 3988)
- irsetup.exe (PID: 3268)
Reads Microsoft Outlook installation path
- irsetup.exe (PID: 3988)
Checks Windows Trust Settings
- irsetup.exe (PID: 3988)
- irsetup.exe (PID: 3268)
Reads Internet Explorer settings
- irsetup.exe (PID: 3988)
Adds/modifies Windows certificates
- irsetup.exe (PID: 3988)
INFO
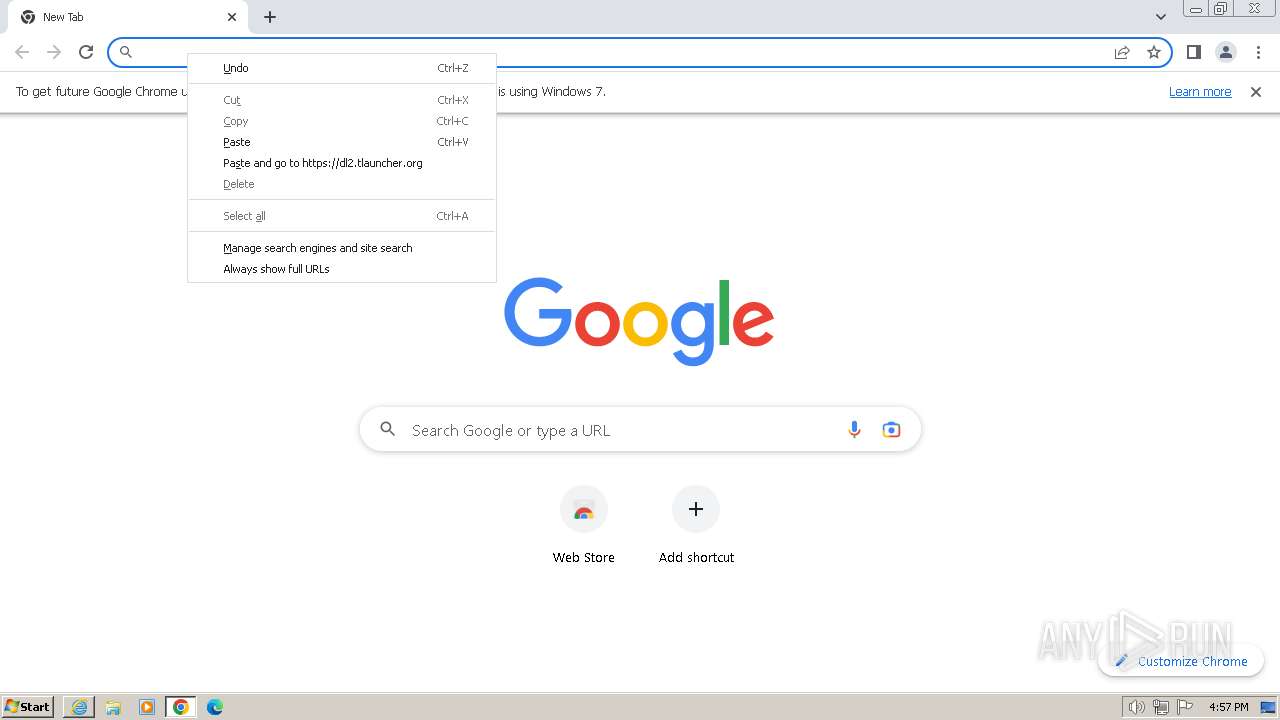
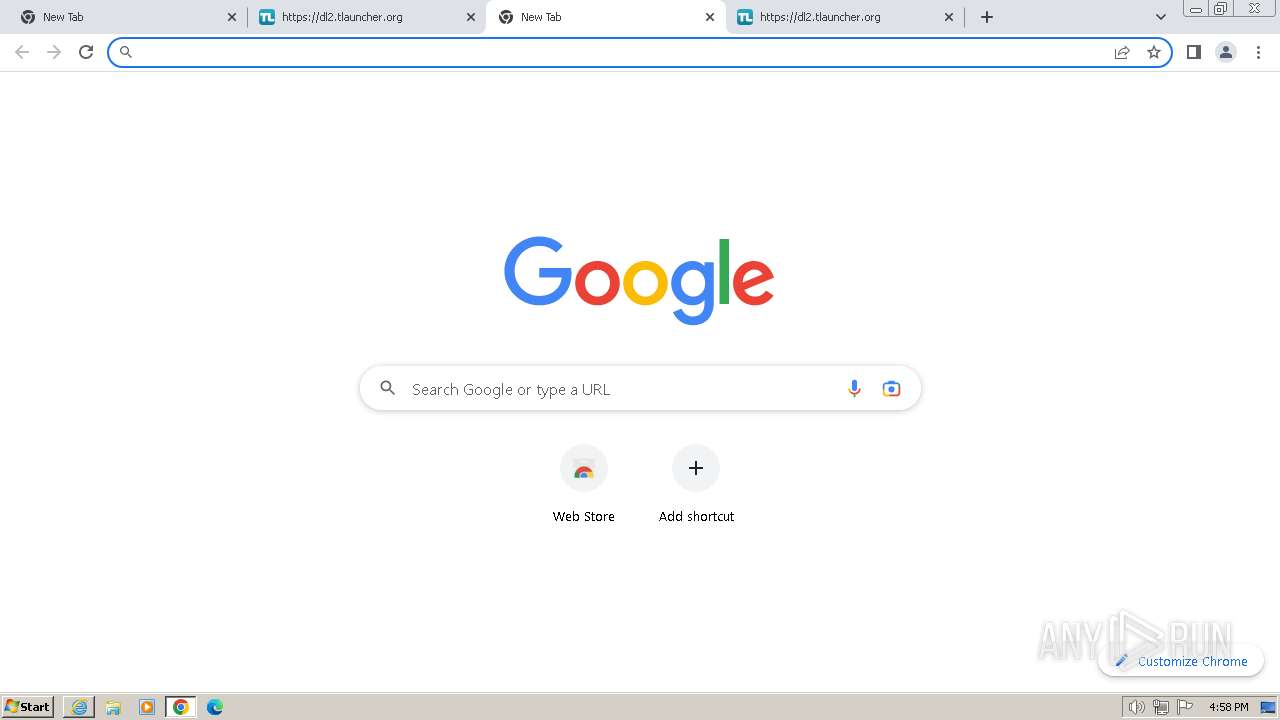
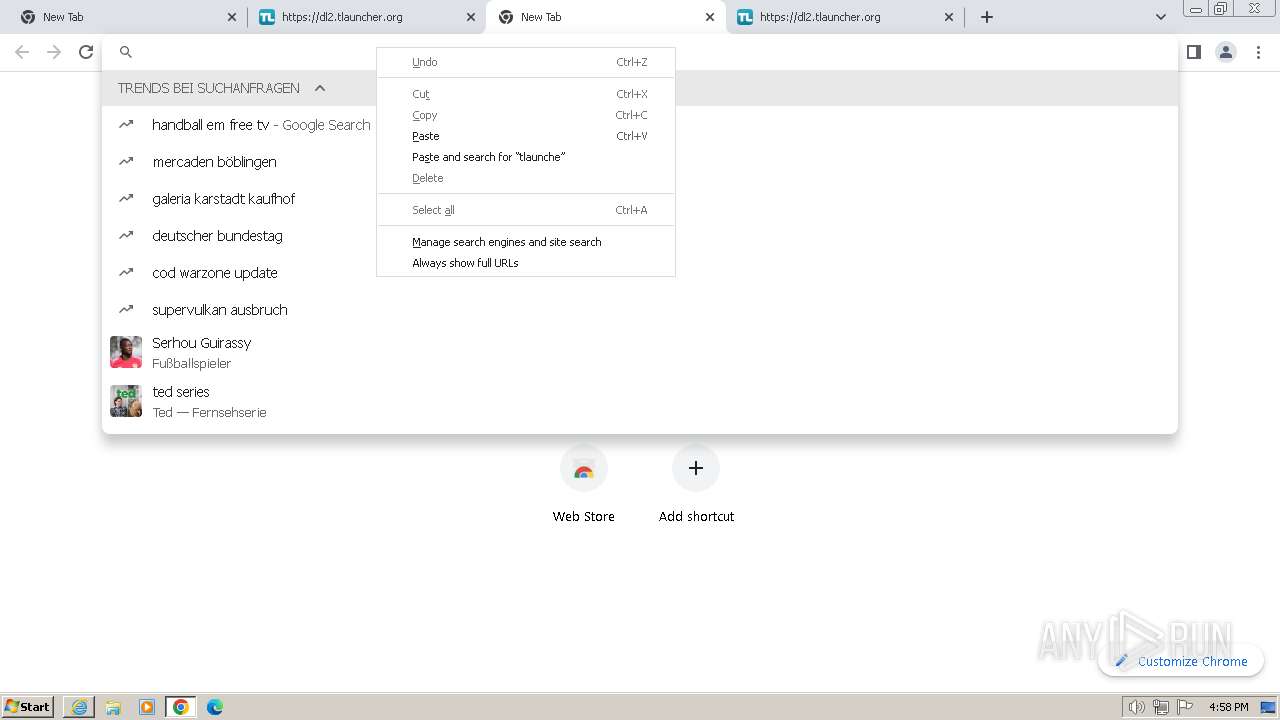
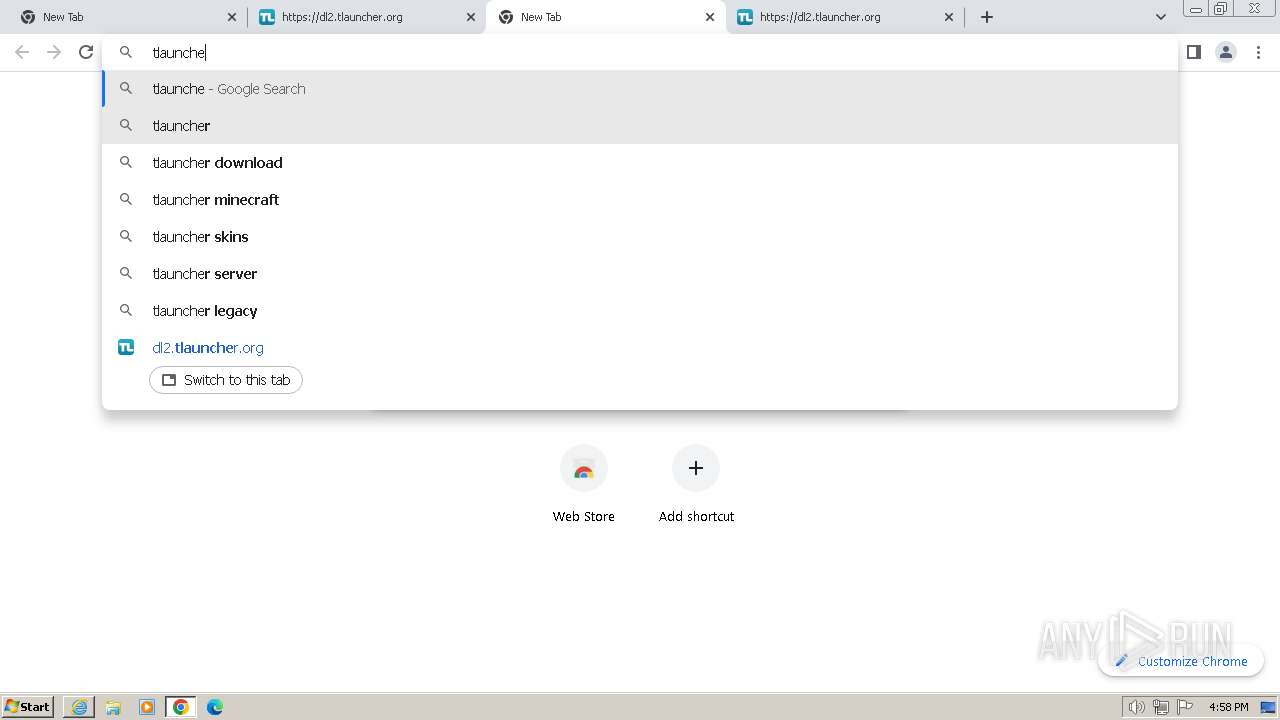
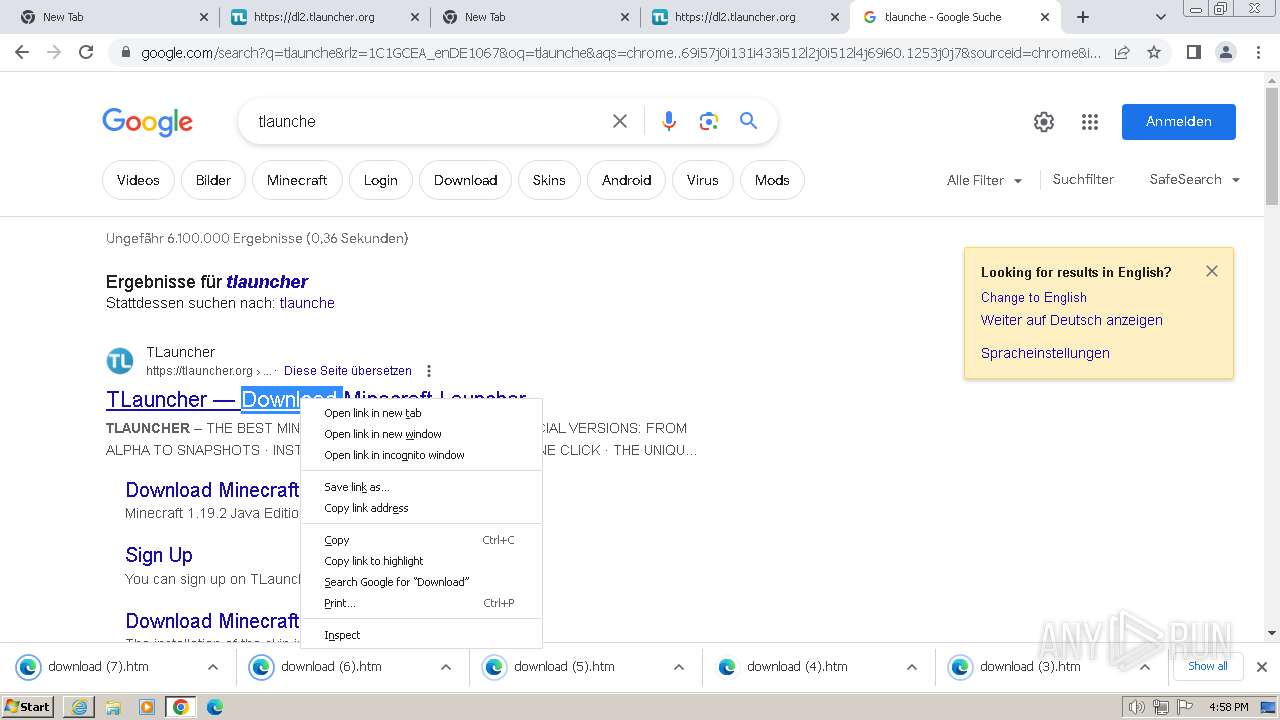
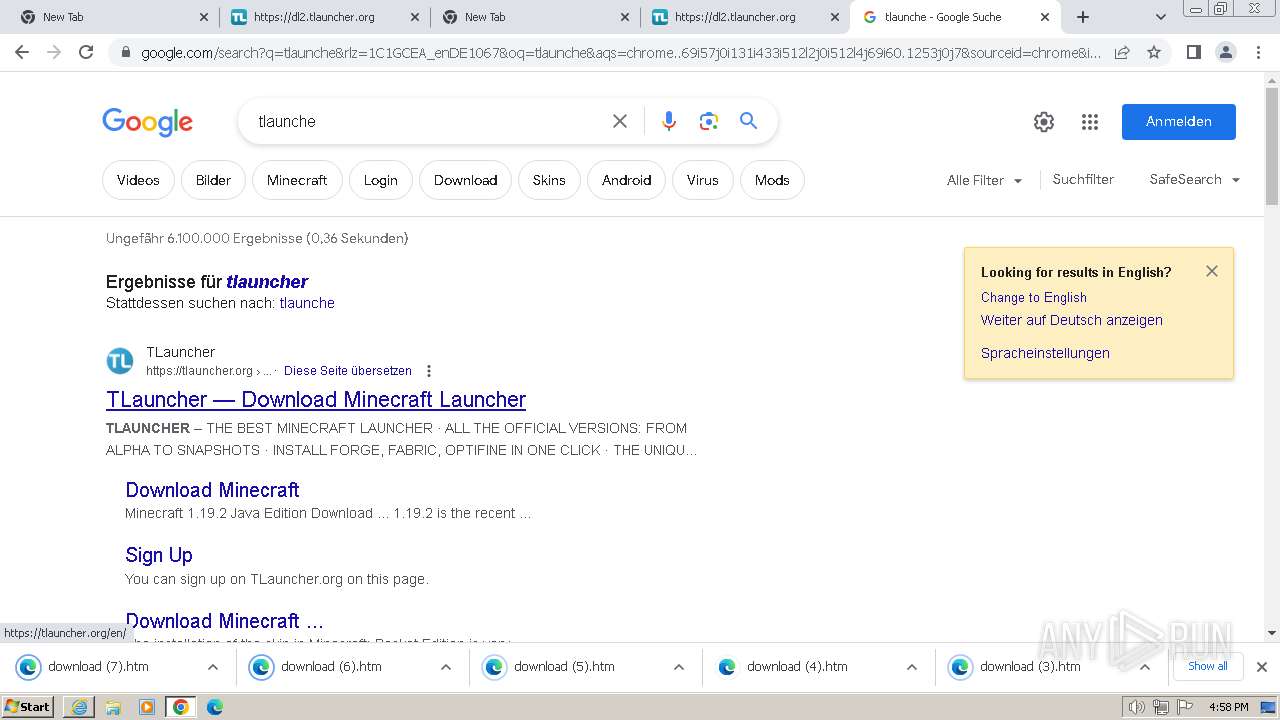
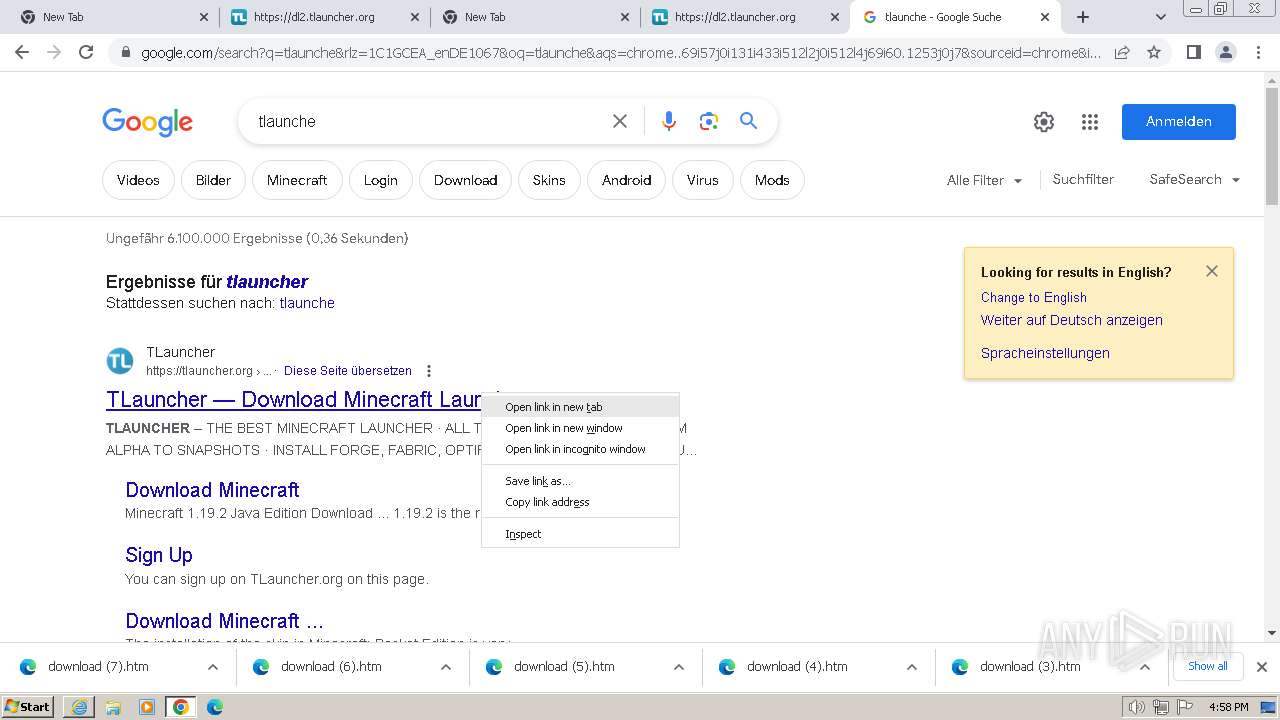
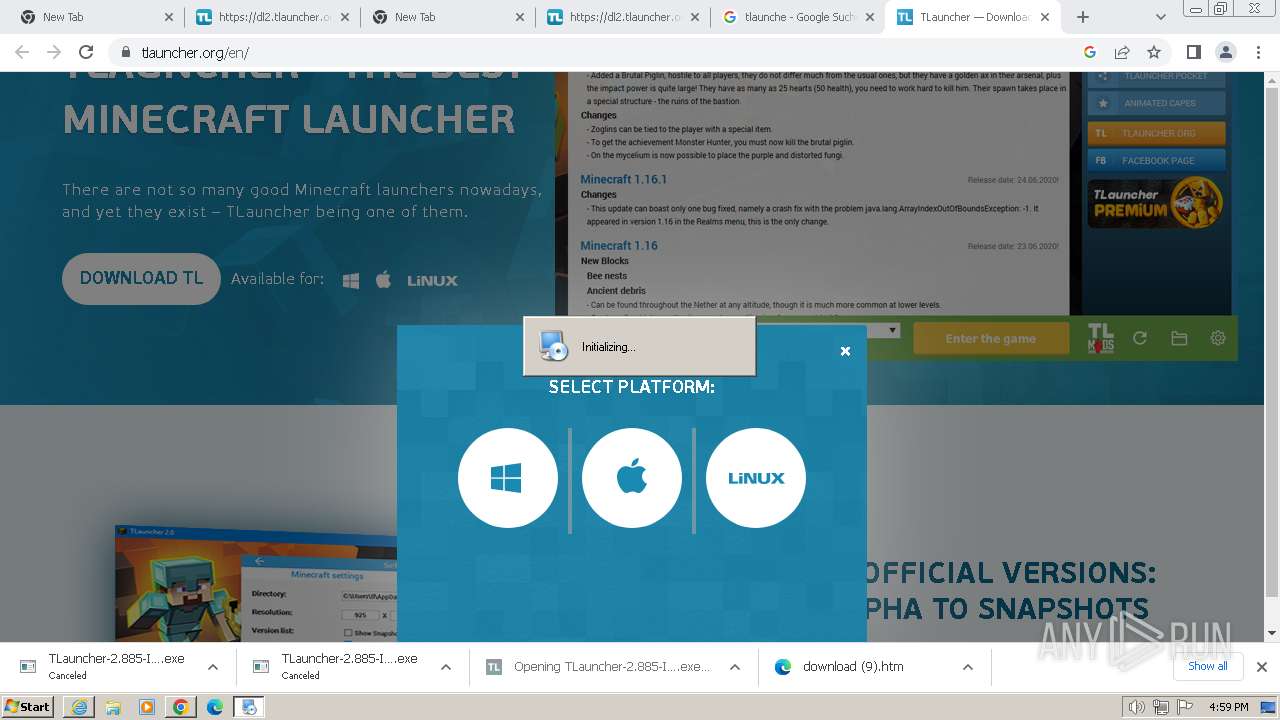
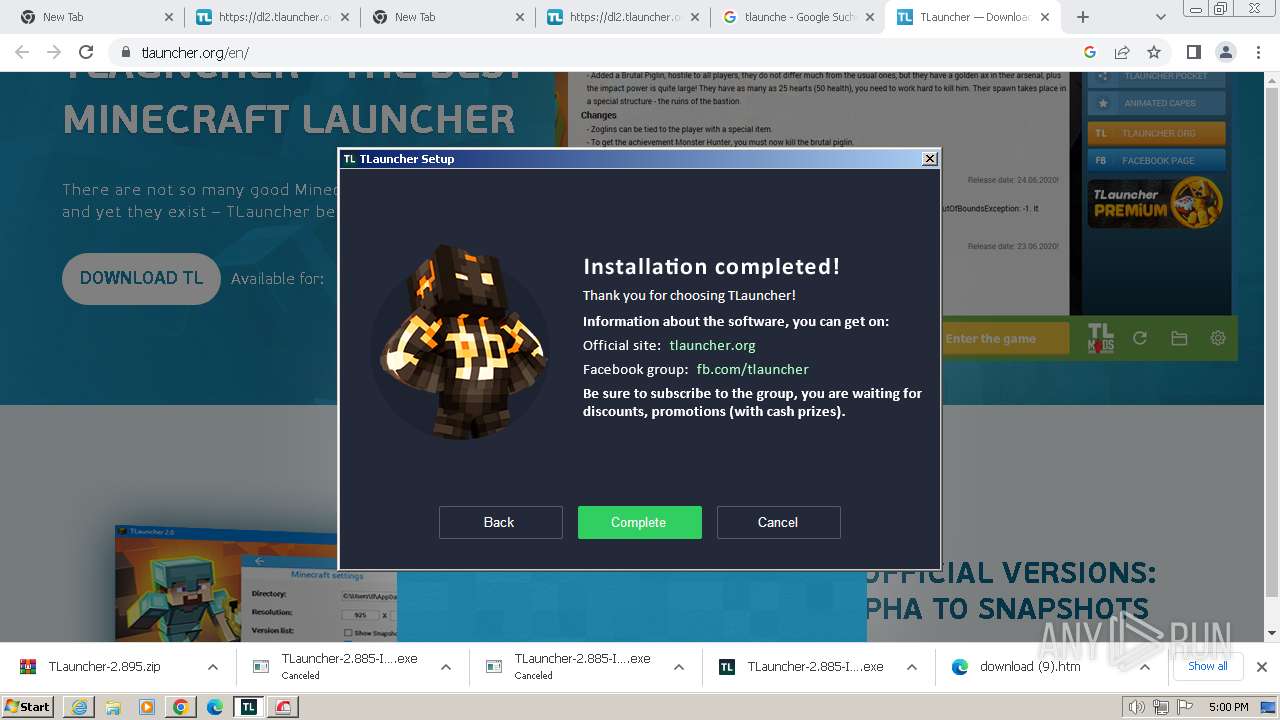
Manual execution by a user
- chrome.exe (PID: 1820)
- TLauncher.exe (PID: 532)
Application launched itself
- chrome.exe (PID: 1820)
- iexplore.exe (PID: 128)
Create files in a temporary directory
- TLauncher-2.885-Installer-1.1.3.exe (PID: 3924)
- irsetup.exe (PID: 3988)
- BrowserInstaller.exe (PID: 1644)
- irsetup.exe (PID: 3268)
- opera-installer-bro.exe (PID: 2088)
The process uses the downloaded file
- chrome.exe (PID: 3900)
- chrome.exe (PID: 492)
- chrome.exe (PID: 2960)
- chrome.exe (PID: 2748)
- chrome.exe (PID: 532)
- chrome.exe (PID: 2908)
- chrome.exe (PID: 1836)
- chrome.exe (PID: 2256)
- chrome.exe (PID: 1644)
- chrome.exe (PID: 4048)
- chrome.exe (PID: 3244)
- chrome.exe (PID: 1984)
- chrome.exe (PID: 1820)
Drops the executable file immediately after the start
- chrome.exe (PID: 1820)
Reads the computer name
- TLauncher-2.885-Installer-1.1.3.exe (PID: 3924)
- irsetup.exe (PID: 3988)
- BrowserInstaller.exe (PID: 1644)
- irsetup.exe (PID: 3268)
Checks supported languages
- irsetup.exe (PID: 3988)
- BrowserInstaller.exe (PID: 1644)
- irsetup.exe (PID: 3268)
- opera-installer-bro.exe (PID: 2088)
- TLauncher.exe (PID: 4052)
- javaw.exe (PID: 2152)
- TLauncher.exe (PID: 532)
- javaw.exe (PID: 1808)
- TLauncher-2.885-Installer-1.1.3.exe (PID: 3924)
Checks proxy server information
- irsetup.exe (PID: 3988)
- irsetup.exe (PID: 3268)
Reads the machine GUID from the registry
- irsetup.exe (PID: 3268)
- irsetup.exe (PID: 3988)
Creates files or folders in the user directory
- irsetup.exe (PID: 3268)
- irsetup.exe (PID: 3988)
Creates files in the program directory
- irsetup.exe (PID: 3988)
Executable content was dropped or overwritten
- chrome.exe (PID: 1820)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
100
Monitored processes
58
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://dl2.tlauncher.org" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=1948 --field-trial-handle=1140,i,16522388356940060081,945932374441459757,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 324 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:128 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 452 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=5220 --field-trial-handle=1140,i,16522388356940060081,945932374441459757,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=4448 --field-trial-handle=1140,i,16522388356940060081,945932374441459757,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=4400 --field-trial-handle=1140,i,16522388356940060081,945932374441459757,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
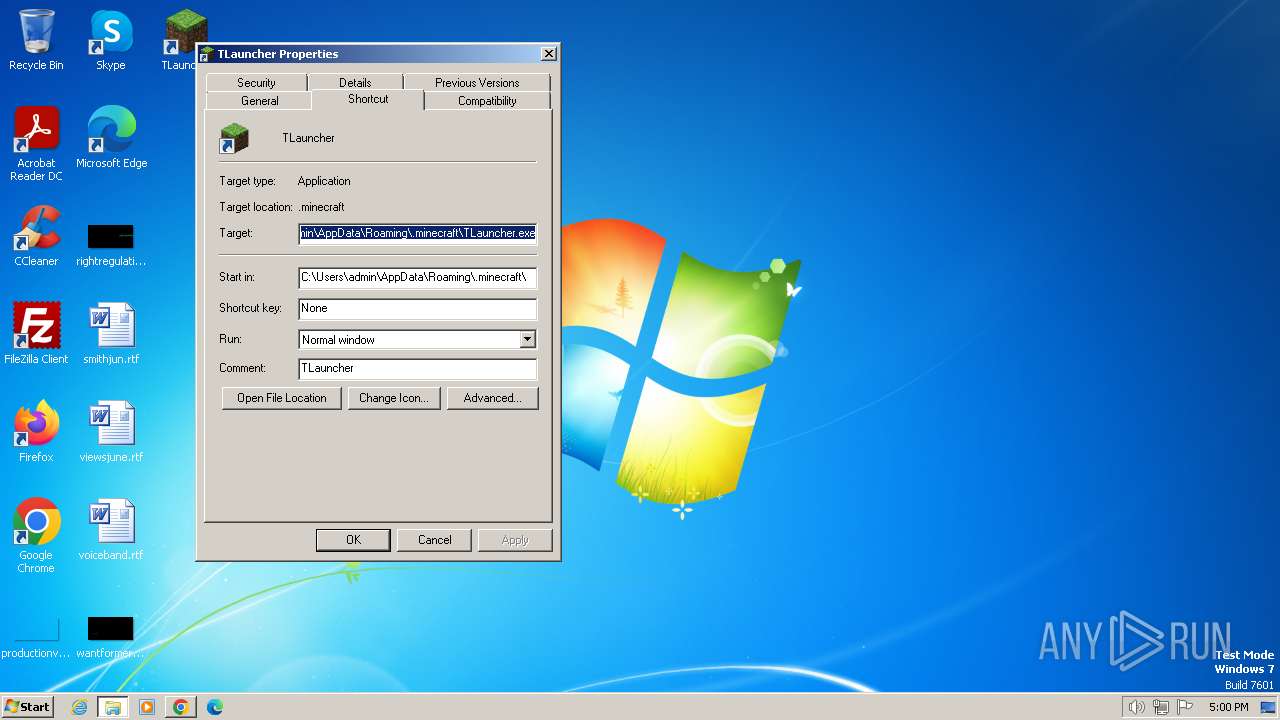
| 532 | "C:\Users\admin\AppData\Roaming\.minecraft\TLauncher.exe" | C:\Users\admin\AppData\Roaming\.minecraft\TLauncher.exe | — | explorer.exe | |||||||||||
User: admin Company: TLauncher Inc. Integrity Level: MEDIUM Description: TLauncher Exit code: 0 Version: 2.899 Modules
| |||||||||||||||
| 632 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1364 --field-trial-handle=1140,i,16522388356940060081,945932374441459757,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1968 --field-trial-handle=1140,i,16522388356940060081,945932374441459757,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2192 --field-trial-handle=1140,i,16522388356940060081,945932374441459757,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
35 805
Read events
35 367
Write events
434
Delete events
4
Modification events
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (128) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
32
Suspicious files
321
Text files
547
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RFe64b1.TMP | — | |
MD5:— | SHA256:— | |||
| 324 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:90365B20AD9005C2443E17D35DBBAF96 | SHA256:B0A056A609C18444DE9A45E1A1EA07CC8D9BD76FF7B7CDD31E094CFAE47C8B9E | |||
| 1820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 324 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 324 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\v84a3a4012de94ce1a686ba8c167c359c1696973893317[1].js | text | |
MD5:DD1D068FDB5FE90B6C05A5B3940E088C | SHA256:6153D13804862B0FC1C016CF1129F34CB7C6185F2CF4BF1A3A862EECDAB50101 | |||
| 128 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\favicon[2].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 128 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EAF8AA29A62AB29E614331747385D816_F9E4DC0B9D5C777357D7DB8DEF51118A | binary | |
MD5:66588665848D4927818655116CDD2131 | SHA256:2802CB0F57F6E494F5ED2D32F18785CBC80492A175E2E97A029DB5E331684451 | |||
| 324 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\0DA515F703BB9B49479E8697ADB0B955_96EEC010953ED454BBCDFA69FC071E7C | binary | |
MD5:2D76F6C22ACBFDD91BAB7309BE01C02D | SHA256:51E6EDF1E48694DC278478B5F4E1332C5EA29E9FE5944479A24D5B7DC78EB65D | |||
| 1820 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 128 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
73
DNS requests
75
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
324 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?6b21170b0e7a1648 | unknown | compressed | 4.66 Kb | unknown |
324 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?53bfb7cf8a6cf97e | unknown | compressed | 4.66 Kb | unknown |
128 | iexplore.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?1a6e676fbb64f2cc | unknown | — | — | unknown |
128 | iexplore.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?56a48ccbaf965781 | unknown | — | — | unknown |
324 | iexplore.exe | GET | 200 | 104.18.21.226:80 | http://ocsp.globalsign.com/rootr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEH1NQqkrQx1%2BZFPnwZqNWHc%3D | unknown | binary | 1.41 Kb | unknown |
128 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | unknown | binary | 313 b | unknown |
324 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | unknown | binary | 1.47 Kb | unknown |
128 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | binary | 471 b | unknown |
128 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAqvpsXKY8RRQeo74ffHUxc%3D | unknown | binary | 471 b | unknown |
128 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | unknown | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
324 | iexplore.exe | 104.20.235.70:443 | dl2.tlauncher.org | CLOUDFLARENET | — | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
128 | iexplore.exe | 2.23.209.133:443 | www.bing.com | Akamai International B.V. | GB | unknown |
324 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
324 | iexplore.exe | 104.18.21.226:80 | ocsp.globalsign.com | CLOUDFLARENET | — | shared |
128 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
128 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
324 | iexplore.exe | 104.16.56.101:443 | static.cloudflareinsights.com | CLOUDFLARENET | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dl2.tlauncher.org |
| unknown |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
static.cloudflareinsights.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
632 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] A free CDN for open source projects (jsdelivr .net) |