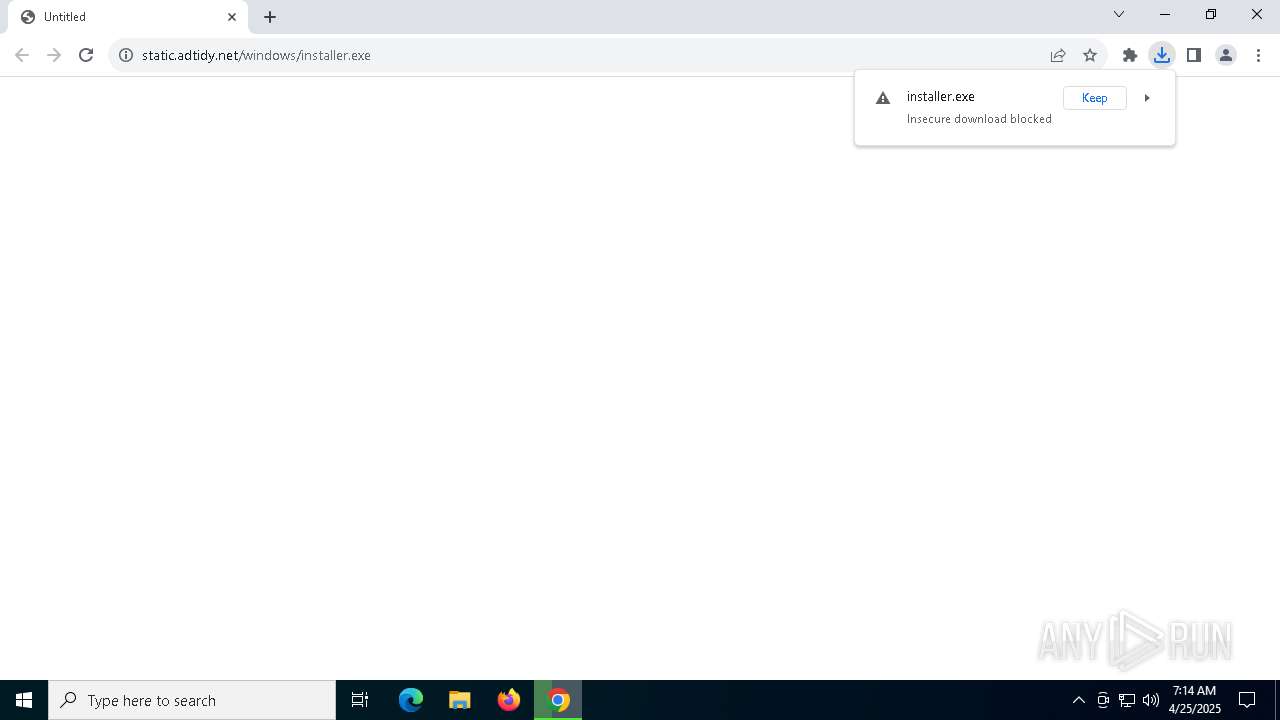
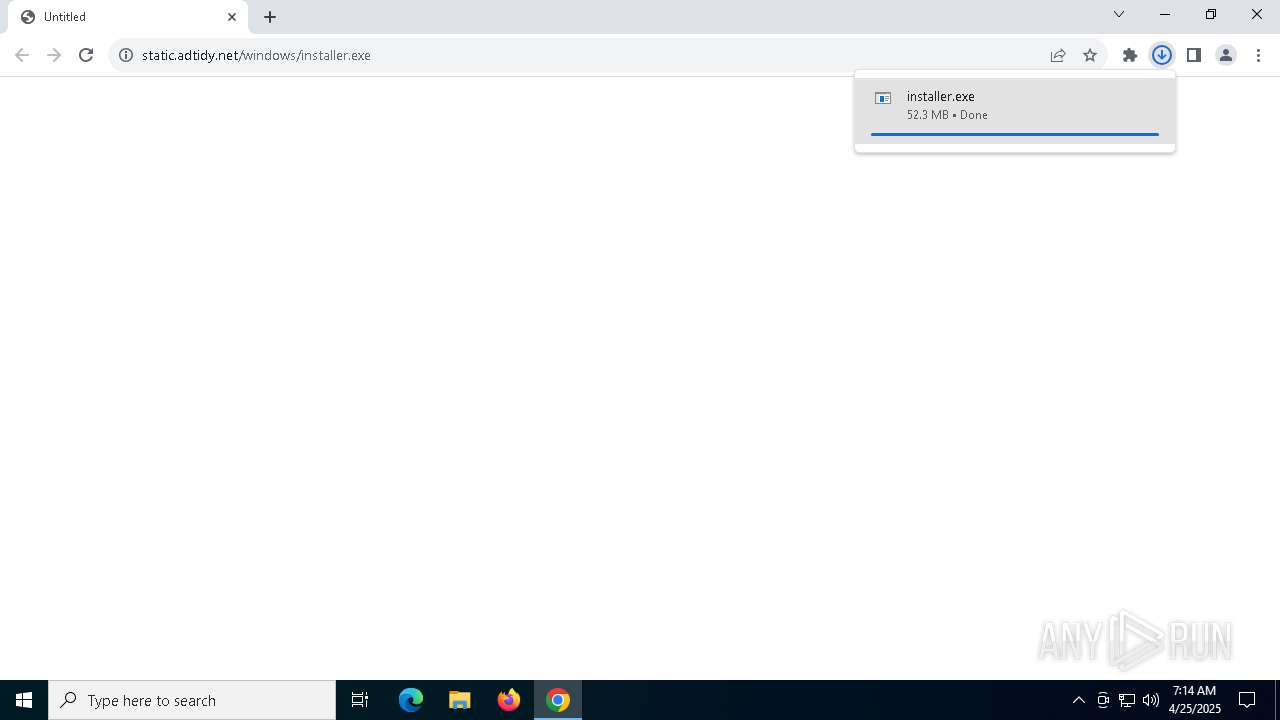
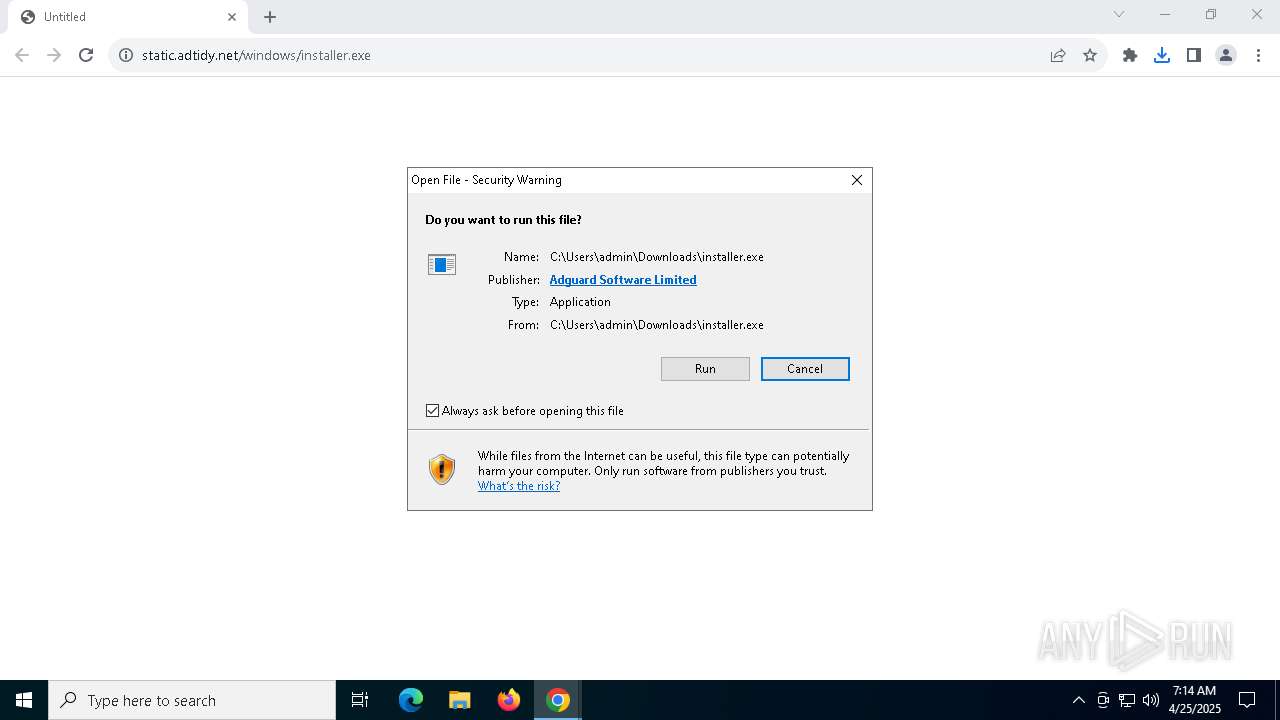
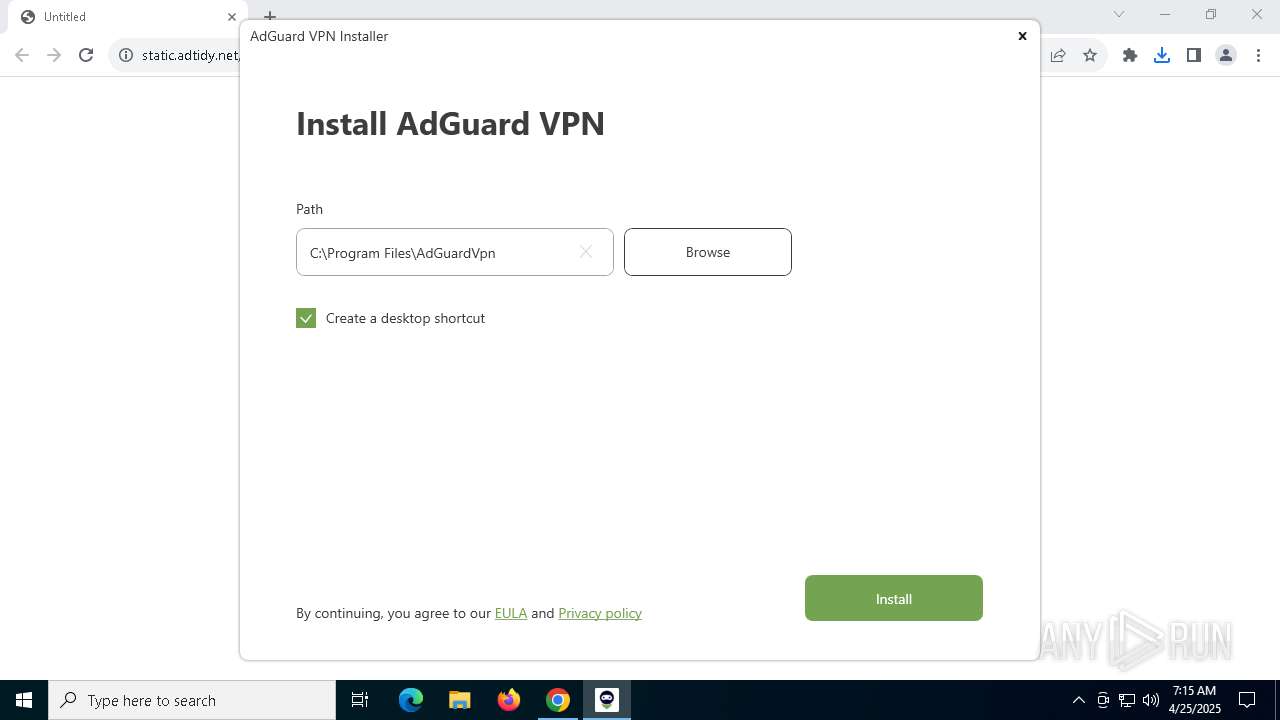
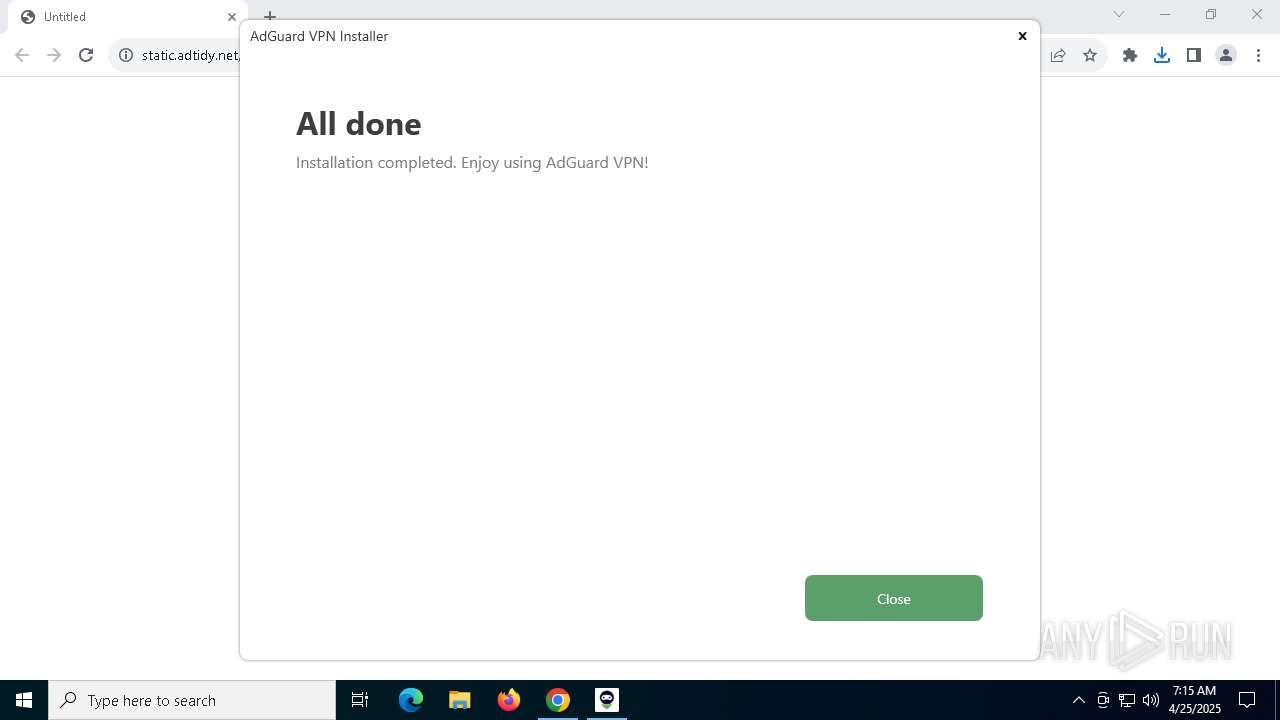
| URL: | static.adtidy.net/windows/installer.exe |
| Full analysis: | https://app.any.run/tasks/65ba53cb-ede4-4165-a1d2-5af8d4b1f17c |
| Verdict: | Malicious activity |
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | April 25, 2025, 07:14:24 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 75F73A711795CC330BF66FF16AE4C62F |
| SHA1: | 61D050BD74DB9E0CB1FE83C8AE39B56BB8D54FA6 |
| SHA256: | ACCA33BA2061714EB480468737C29339772572B1C847B99DA9806AB7F5C28B18 |
| SSDEEP: | 3:NrMhzuiqOXLNn:1MAiqOXLN |
MALICIOUS
Executing a file with an untrusted certificate
- installer.exe (PID: 7668)
- installer.exe (PID: 8104)
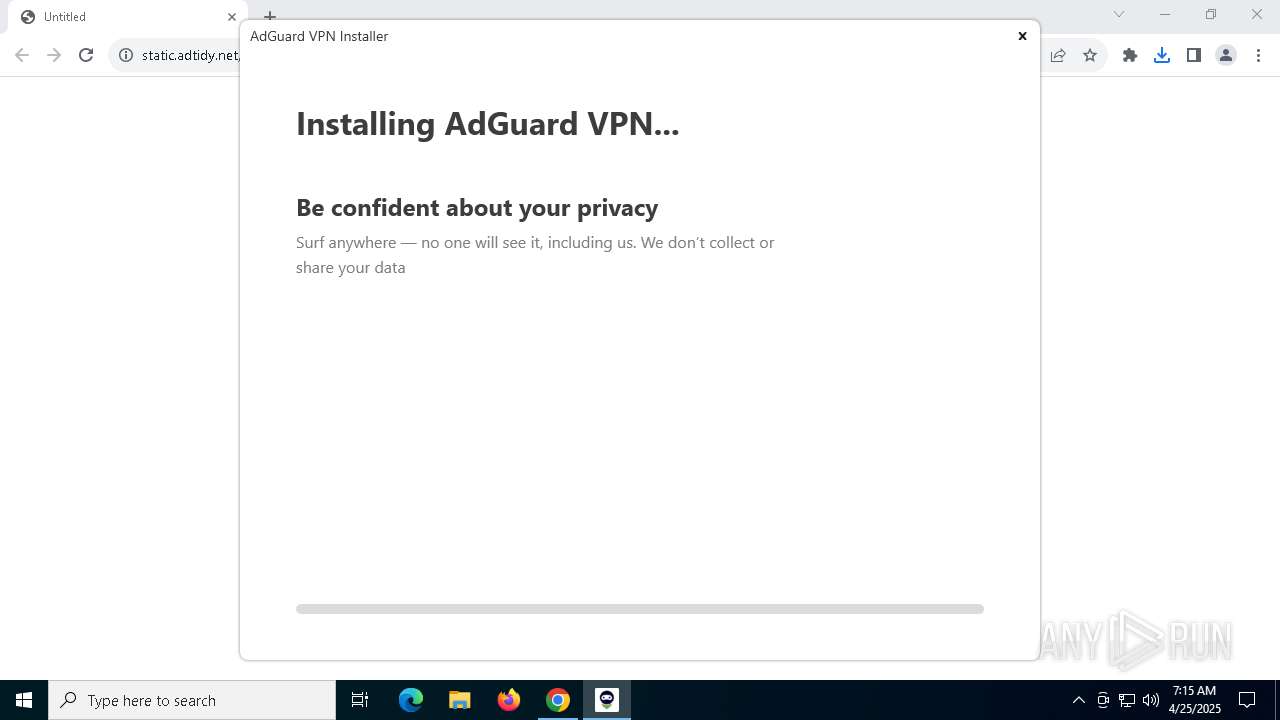
Changes the autorun value in the registry
- installer.exe (PID: 8104)
- ie4uinit.exe (PID: 6540)
Starts NET.EXE for service management
- net.exe (PID: 7740)
- cmd.exe (PID: 7584)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 3896)
SUSPICIOUS
Executable content was dropped or overwritten
- installer.exe (PID: 7664)
- installer.exe (PID: 7668)
- installer.exe (PID: 8104)
- rundll32.exe (PID: 6388)
- rundll32.exe (PID: 3268)
- rundll32.exe (PID: 1512)
- rundll32.exe (PID: 4688)
- rundll32.exe (PID: 6136)
- rundll32.exe (PID: 4200)
- AdGuardVpnSvc.exe (PID: 7084)
The process creates files with name similar to system file names
- installer.exe (PID: 7668)
Process drops legitimate windows executable
- installer.exe (PID: 7668)
- msiexec.exe (PID: 8148)
Searches for installed software
- installer.exe (PID: 7668)
Process requests binary or script from the Internet
- installer.exe (PID: 7668)
Reads security settings of Internet Explorer
- installer.exe (PID: 7668)
There is functionality for taking screenshot (YARA)
- installer.exe (PID: 7664)
Starts itself from another location
- installer.exe (PID: 7668)
Creates a software uninstall entry
- installer.exe (PID: 8104)
Application launched itself
- msiexec.exe (PID: 8148)
Uses RUNDLL32.EXE to load library
- msiexec.exe (PID: 6268)
Executes as Windows Service
- WmiApSrv.exe (PID: 2692)
- AdGuardVpnSvc.exe (PID: 7084)
The process checks if it is being run in the virtual environment
- rundll32.exe (PID: 3268)
Adds/modifies Windows certificates
- msiexec.exe (PID: 8148)
- rundll32.exe (PID: 6136)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 8148)
Starts CMD.EXE for commands execution
- rundll32.exe (PID: 6136)
- AdGuardVpnSvc.exe (PID: 7084)
Drops a system driver (possible attempt to evade defenses)
- AdGuardVpnSvc.exe (PID: 7084)
Starts SC.EXE for service management
- AdGuardVpnSvc.exe (PID: 7084)
Windows service management via SC.EXE
- sc.exe (PID: 6416)
- sc.exe (PID: 1020)
- sc.exe (PID: 4188)
The process executes via Task Scheduler
- AdGuardVpn.exe (PID: 7768)
Deletes scheduled task without confirmation
- schtasks.exe (PID: 6252)
INFO
Application launched itself
- chrome.exe (PID: 5936)
- msedge.exe (PID: 1184)
The sample compiled with english language support
- installer.exe (PID: 7664)
- installer.exe (PID: 7668)
- installer.exe (PID: 8104)
- rundll32.exe (PID: 3268)
- rundll32.exe (PID: 6388)
- rundll32.exe (PID: 1512)
- rundll32.exe (PID: 4688)
- rundll32.exe (PID: 6136)
- msiexec.exe (PID: 8148)
- rundll32.exe (PID: 4200)
- chrome.exe (PID: 7708)
Checks supported languages
- installer.exe (PID: 7664)
- installer.exe (PID: 7668)
- installer.exe (PID: 8104)
- msiexec.exe (PID: 8148)
- msiexec.exe (PID: 6268)
- msiexec.exe (PID: 8084)
- msiexec.exe (PID: 4436)
- AdGuardVpnSvc.exe (PID: 7084)
Create files in a temporary directory
- installer.exe (PID: 7664)
- installer.exe (PID: 7668)
- installer.exe (PID: 8104)
Executable content was dropped or overwritten
- chrome.exe (PID: 5936)
- msiexec.exe (PID: 8148)
- chrome.exe (PID: 7708)
Reads the computer name
- installer.exe (PID: 7668)
- installer.exe (PID: 8104)
- msiexec.exe (PID: 8148)
- msiexec.exe (PID: 6268)
- msiexec.exe (PID: 8084)
- msiexec.exe (PID: 4436)
- AdGuardVpnSvc.exe (PID: 7084)
Reads the machine GUID from the registry
- installer.exe (PID: 7668)
- installer.exe (PID: 8104)
- msiexec.exe (PID: 8148)
- AdGuardVpnSvc.exe (PID: 7084)
Disables trace logs
- installer.exe (PID: 7668)
Checks proxy server information
- installer.exe (PID: 7668)
Reads the software policy settings
- installer.exe (PID: 7668)
- msiexec.exe (PID: 8148)
- rundll32.exe (PID: 6136)
- AdGuardVpnSvc.exe (PID: 7084)
- slui.exe (PID: 7836)
ADGUARDVPN mutex has been found
- installer.exe (PID: 7668)
Process checks computer location settings
- installer.exe (PID: 7668)
Creates files in the program directory
- installer.exe (PID: 8104)
- installer.exe (PID: 7668)
- rundll32.exe (PID: 6136)
- AdGuardVpnSvc.exe (PID: 7084)
Reads the time zone
- rundll32.exe (PID: 3268)
SQLite executable
- msiexec.exe (PID: 8148)
Creates a software uninstall entry
- msiexec.exe (PID: 8148)
Reads security settings of Internet Explorer
- ie4uinit.exe (PID: 6540)
Creates files or folders in the user directory
- ie4uinit.exe (PID: 6540)
Reads Environment values
- AdGuardVpnSvc.exe (PID: 7084)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
220
Monitored processes
85
Malicious processes
10
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5616 --field-trial-handle=2616,i,11562350491434086239,577377774623544683,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1020 | "sc" sdshow "Adguard VPN Service" | C:\Windows\System32\sc.exe | — | AdGuardVpnSvc.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
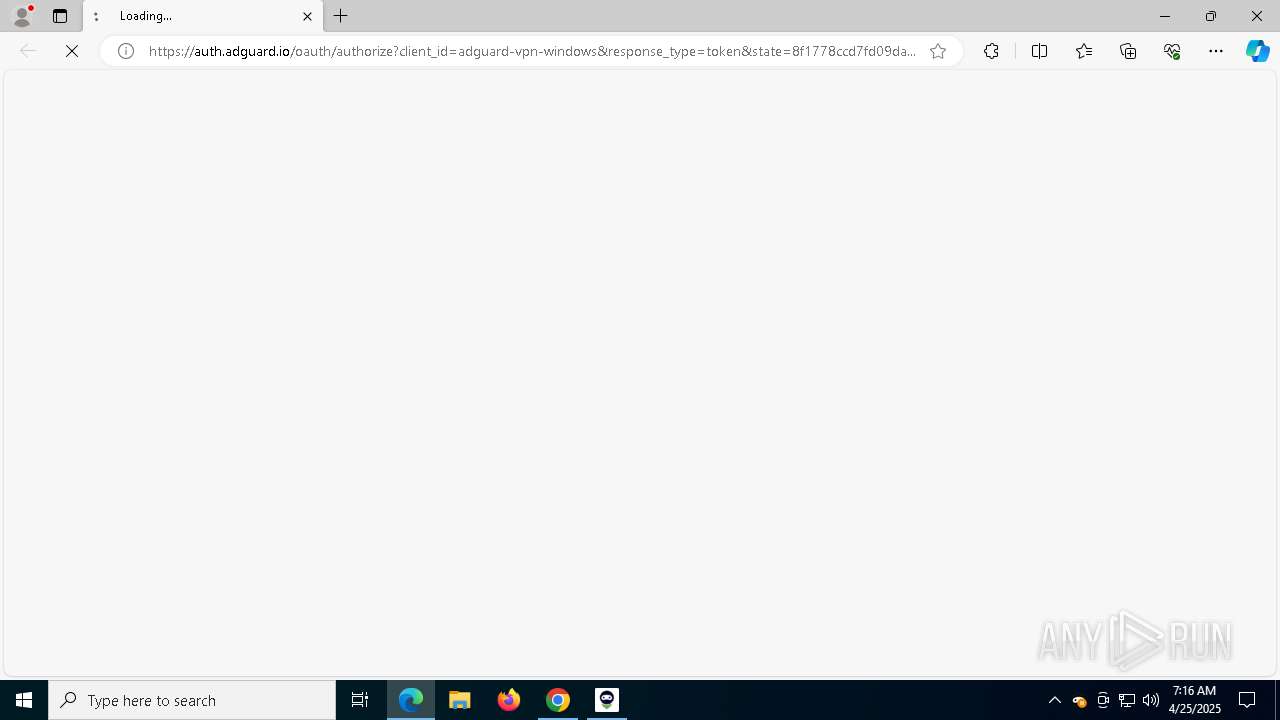
| 1184 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --single-argument https://auth.adguard.io/oauth/authorize?client_id=adguard-vpn-windows&response_type=token&state=8f1778ccd7fd09da02be99034ab9f1a0&scope=trust&redirect_uri=adguardvpn:oauth_authorize&marketing_consent=false®_mode=ALWAYS&social_provider=unknown&app_id=160a60ef0d0644ec996019a577c20f6a | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | AdGuardVpn.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1388 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1512 | rundll32.exe "C:\WINDOWS\Installer\MSI707B.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1143937 14 AdGuardVpn.CustomActions!AdGuardVpn.CustomActions.CustomActions.PermanentActions | C:\Windows\System32\rundll32.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1616 | C:\WINDOWS\system32\net1 start "AdGuard VPN Service" | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1672 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3688 --field-trial-handle=2616,i,11562350491434086239,577377774623544683,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2192 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5744 --field-trial-handle=2616,i,11562350491434086239,577377774623544683,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2384 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=122.0.6261.70 --initial-client-data=0x220,0x224,0x228,0x1fc,0x22c,0x7ffc898edc40,0x7ffc898edc4c,0x7ffc898edc58 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 2664 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5904 --field-trial-handle=2616,i,11562350491434086239,577377774623544683,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
38 155
Read events
37 865
Write events
263
Delete events
27
Modification events
| (PID) Process: | (5936) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5936) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5936) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5936) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5936) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (4008) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000330C4FBAB1B5DB01 | |||
| (PID) Process: | (7668) installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\installer_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (7668) installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\installer_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (7668) installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\installer_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (7668) installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\installer_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
Executable files
334
Suspicious files
611
Text files
110
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10bf5a.TMP | — | |
MD5:— | SHA256:— | |||
| 5936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF10bf6a.TMP | — | |
MD5:— | SHA256:— | |||
| 5936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF10bf6a.TMP | — | |
MD5:— | SHA256:— | |||
| 5936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF10bf6a.TMP | — | |
MD5:— | SHA256:— | |||
| 5936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10bf6a.TMP | — | |
MD5:— | SHA256:— | |||
| 5936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
79
DNS requests
75
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1328 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
1328 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
1328 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5936 | chrome.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEEj8k7RgVZSNNqfJionWlBY%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5936 | chrome.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSdE3gf41WAic8Uh9lF92%2BIJqh5qwQUMuuSmv81lkgvKEBCcCA2kVwXheYCEGIdbQxSAZ47kHkVIIkhHAo%3D | unknown | — | — | whitelisted |
5936 | chrome.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBQVD%2BnGf79Hpedv3mhy6uKMVZkPCQQUDyrLIIcouOxvSK4rVKYpqhekzQwCEQCxOOZmDcp8w3fLL29gJ%2FYW | unknown | — | — | whitelisted |
7684 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5936 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7248 | chrome.exe | 185.102.217.56:443 | static.adtidy.net | Datacamp Limited | RO | unknown |
7248 | chrome.exe | 185.102.217.56:80 | static.adtidy.net | Datacamp Limited | RO | unknown |
7248 | chrome.exe | 64.233.167.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
static.adtidy.net |
| malicious |
accounts.google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
www.google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6136 | rundll32.exe | Misc activity | ET INFO Observed DNS Over HTTPS Domain (dns .alidns .com in TLS SNI) |
6136 | rundll32.exe | Misc activity | ET INFO Observed DNS Over HTTPS Domain (dns .alidns .com in TLS SNI) |
6136 | rundll32.exe | Misc activity | ET INFO Observed Google DNS over HTTPS Domain (dns .google in TLS SNI) |
7084 | AdGuardVpnSvc.exe | Misc activity | ET INFO Observed DNS Over HTTPS Domain (dns .alidns .com in TLS SNI) |
7084 | AdGuardVpnSvc.exe | Misc activity | ET INFO Observed DNS Over HTTPS Domain (dns .alidns .com in TLS SNI) |
7776 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
7776 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
Process | Message |
|---|---|
AdGuardVpnSvc.exe | Native library pre-loader is trying to load native SQLite library "C:\Program Files\AdGuardVpn\x64\SQLite.Interop.dll"...
|
AdGuardVpnSvc.exe | SQLite error (261): database is locked
|
AdGuardVpnSvc.exe | SQLite error (261): database is locked
|
AdGuardVpnSvc.exe | SQLite error (261): database is locked
|
AdGuardVpnSvc.exe | SQLite error (261): database is locked
|
AdGuardVpnSvc.exe | SQLite error (261): database is locked
|
AdGuardVpnSvc.exe | SQLite error (261): database is locked
|
AdGuardVpnSvc.exe | SQLite error (261): database is locked
|
AdGuardVpnSvc.exe | SQLite error (261): database is locked
|
AdGuardVpnSvc.exe | SQLite error (5): database is locked
|