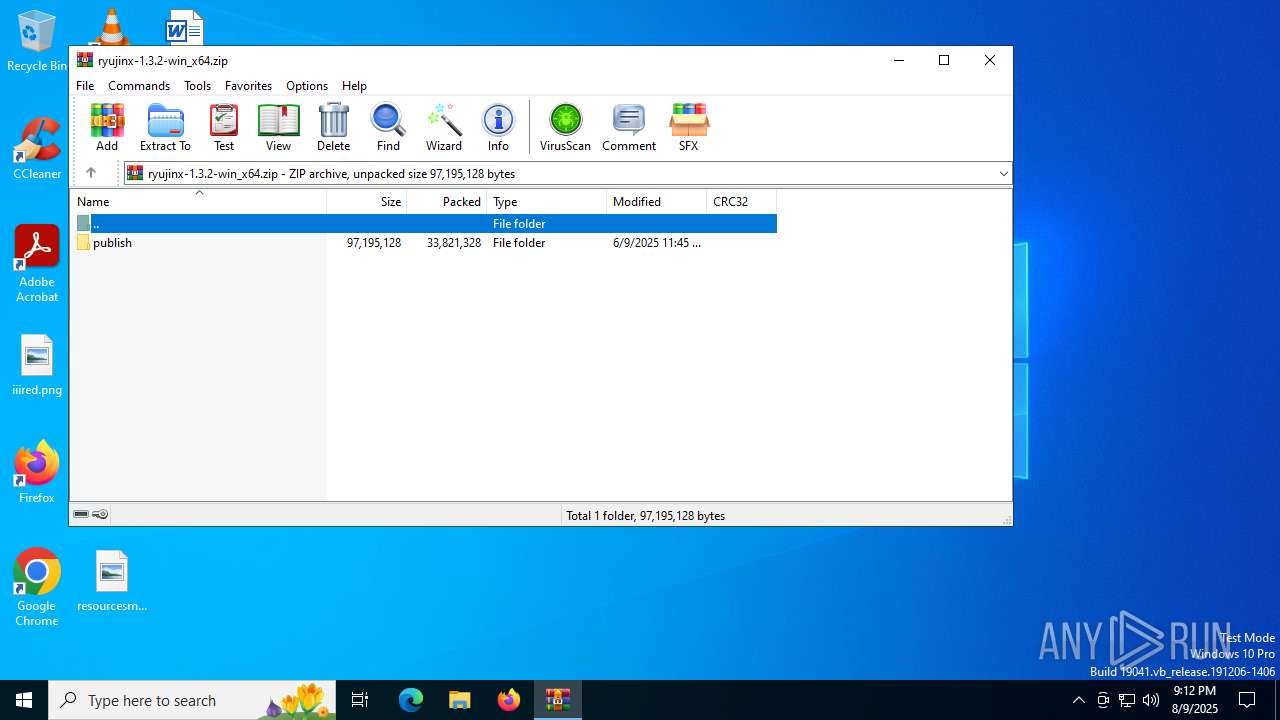
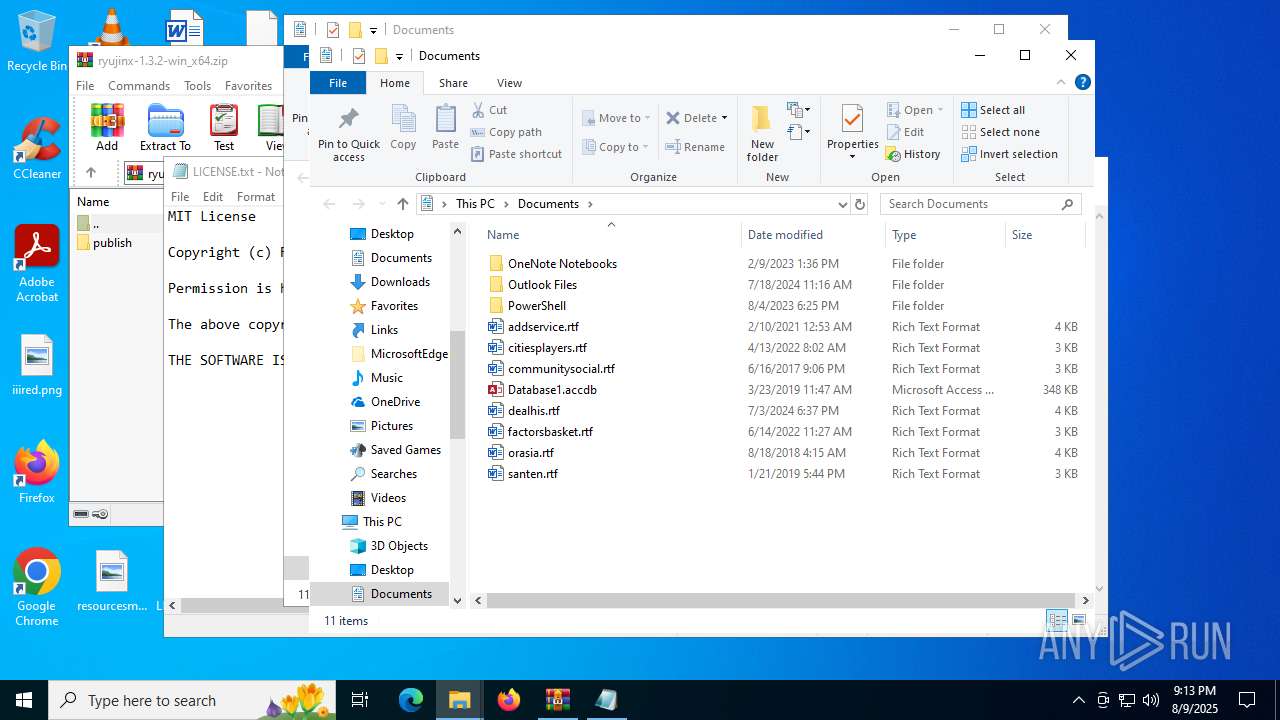
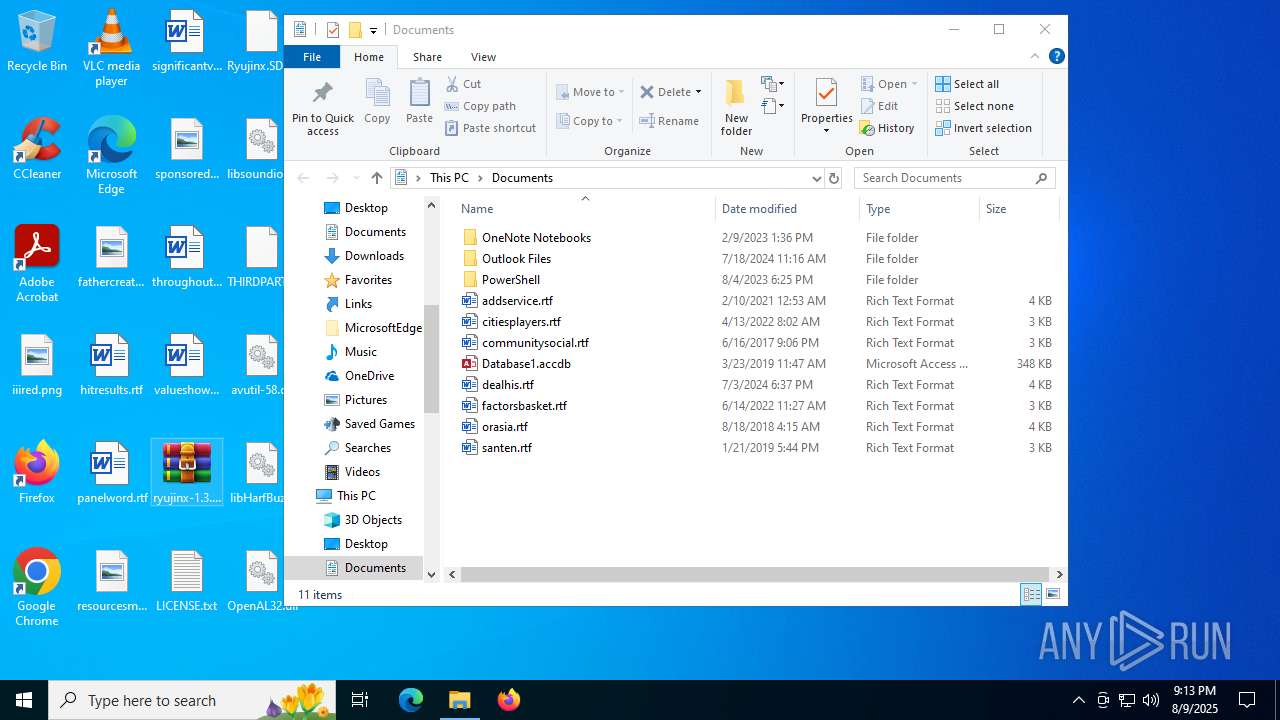
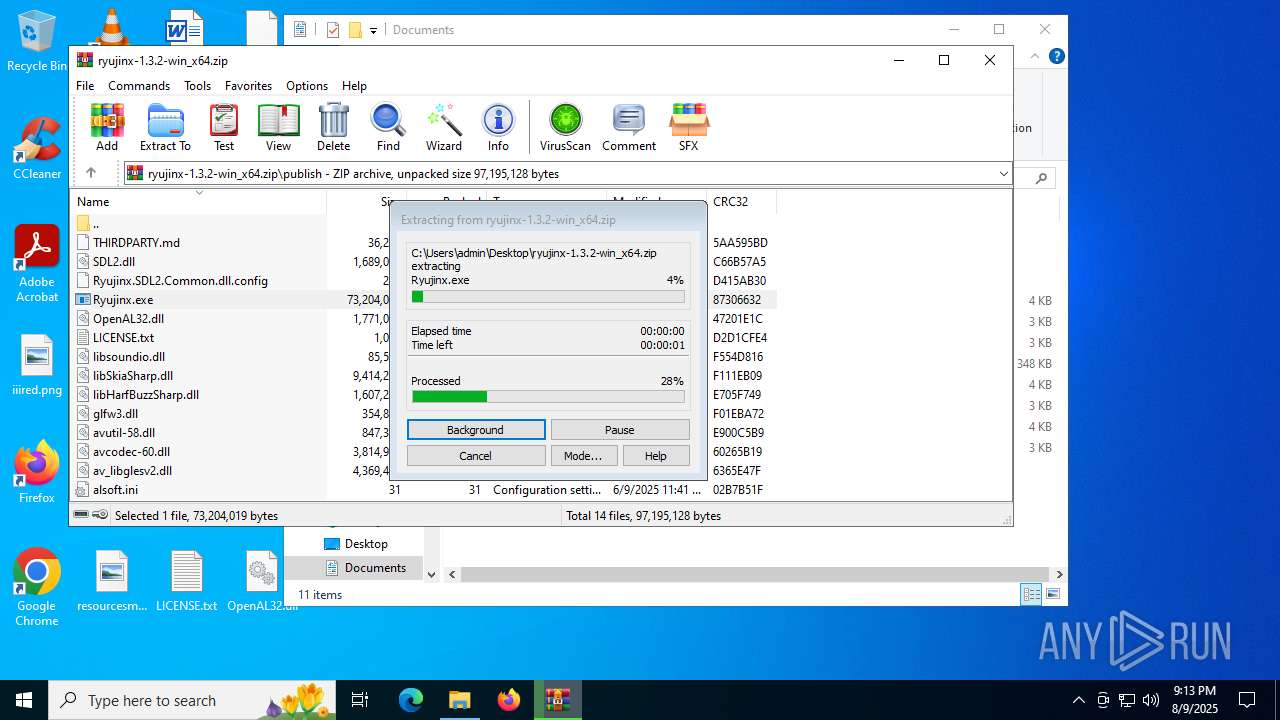
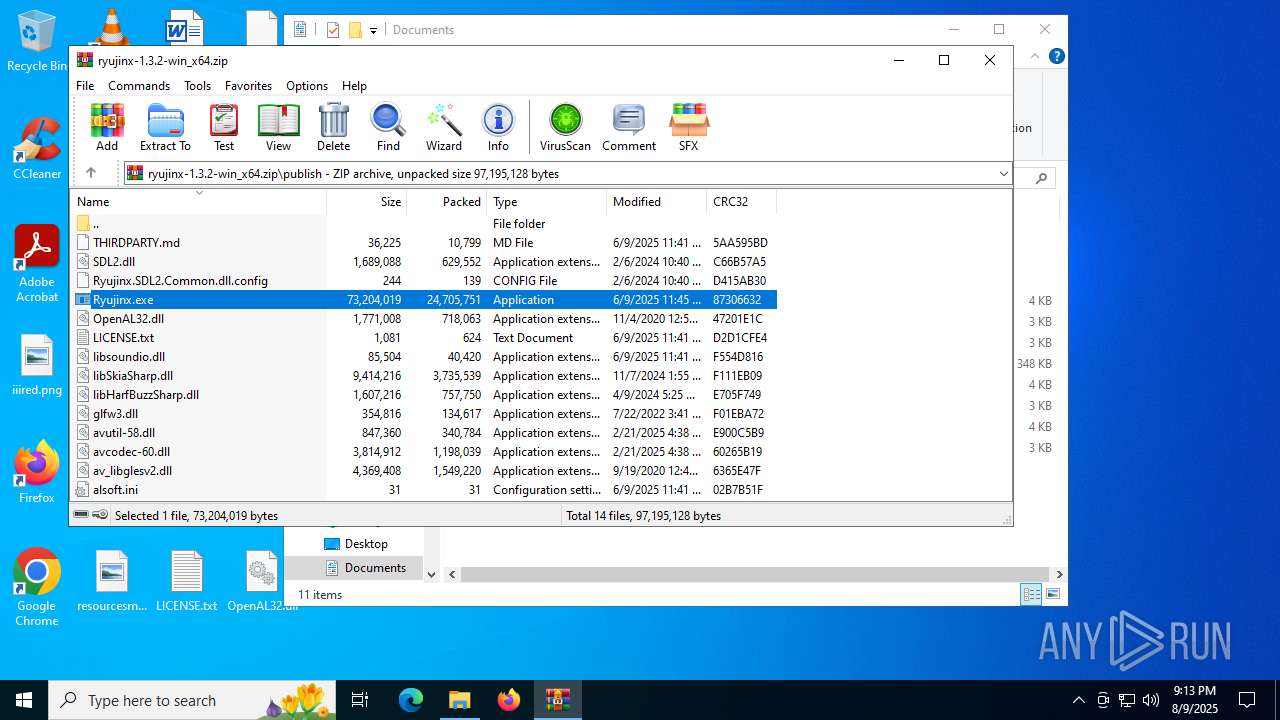
| File name: | ryujinx-1.3.2-win_x64.zip |
| Full analysis: | https://app.any.run/tasks/6676c405-670b-4db6-a50d-761efc48b74c |
| Verdict: | Malicious activity |
| Analysis date: | August 09, 2025, 21:12:33 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | 0912F130874EA795C33B2D5BDA7A3168 |
| SHA1: | CAD5C734BB1076259529AFF3B51CD787A7FF2337 |
| SHA256: | ACB7A4252C538D6B537F917E09C20996D141DC2E41E5177B8D8A78FB61278F06 |
| SSDEEP: | 393216:/SaiY/SeQdmLfMhRdcLYb5zxPRodd0DX5h5kKTdqO:KtY/CwLfMiLi5zsdd0DpFd |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 4684)
INFO
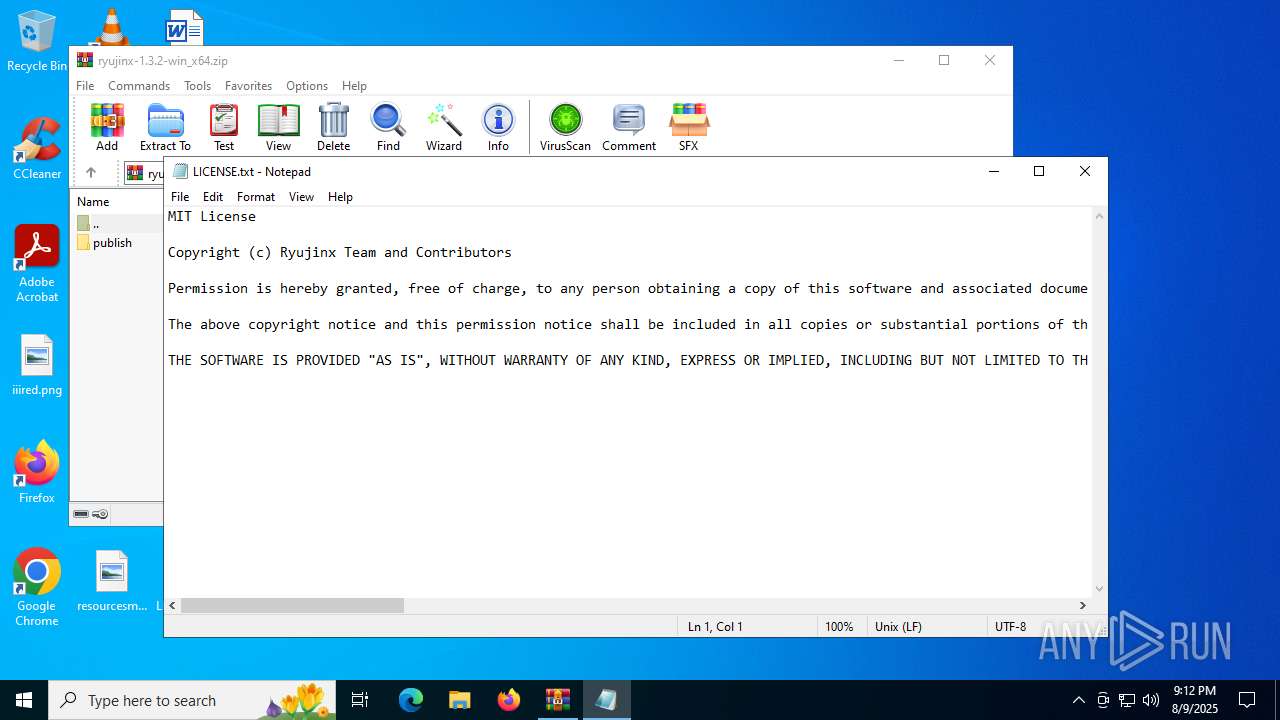
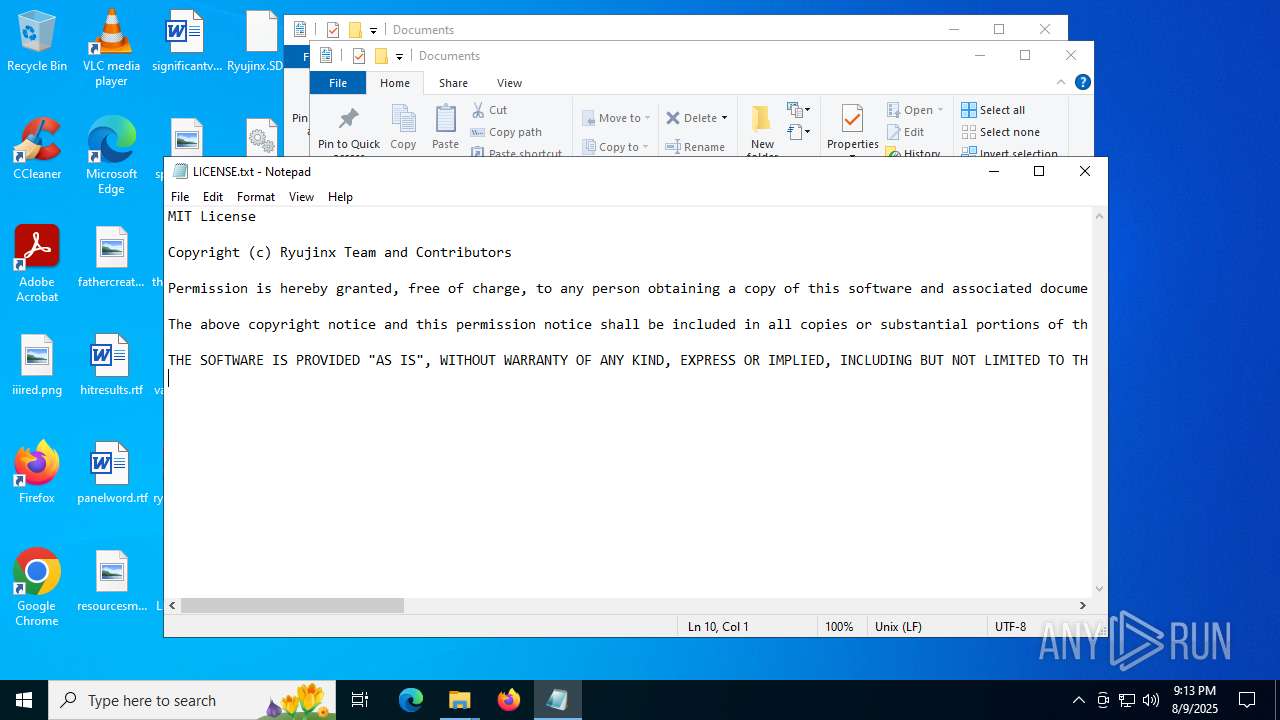
Manual execution by a user
- notepad.exe (PID: 2400)
- WinRAR.exe (PID: 4684)
The sample compiled with english language support
- WinRAR.exe (PID: 3288)
- WinRAR.exe (PID: 4684)
Reads security settings of Internet Explorer
- notepad.exe (PID: 2400)
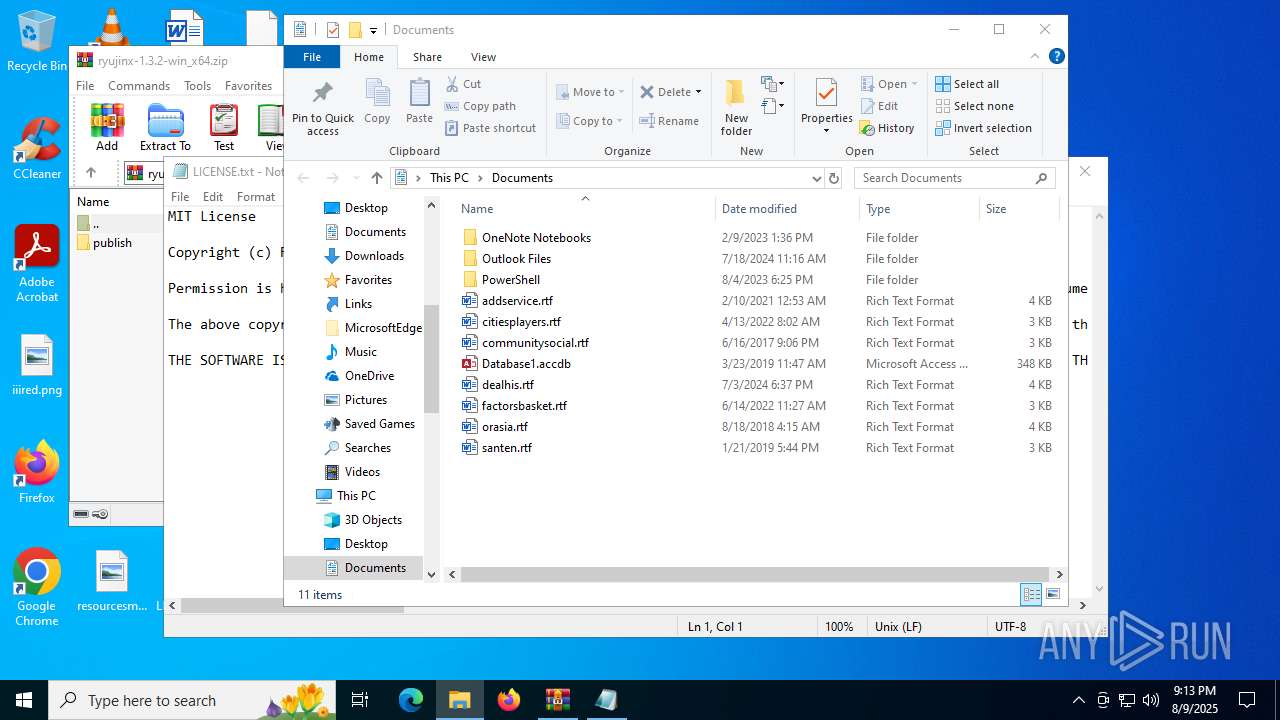
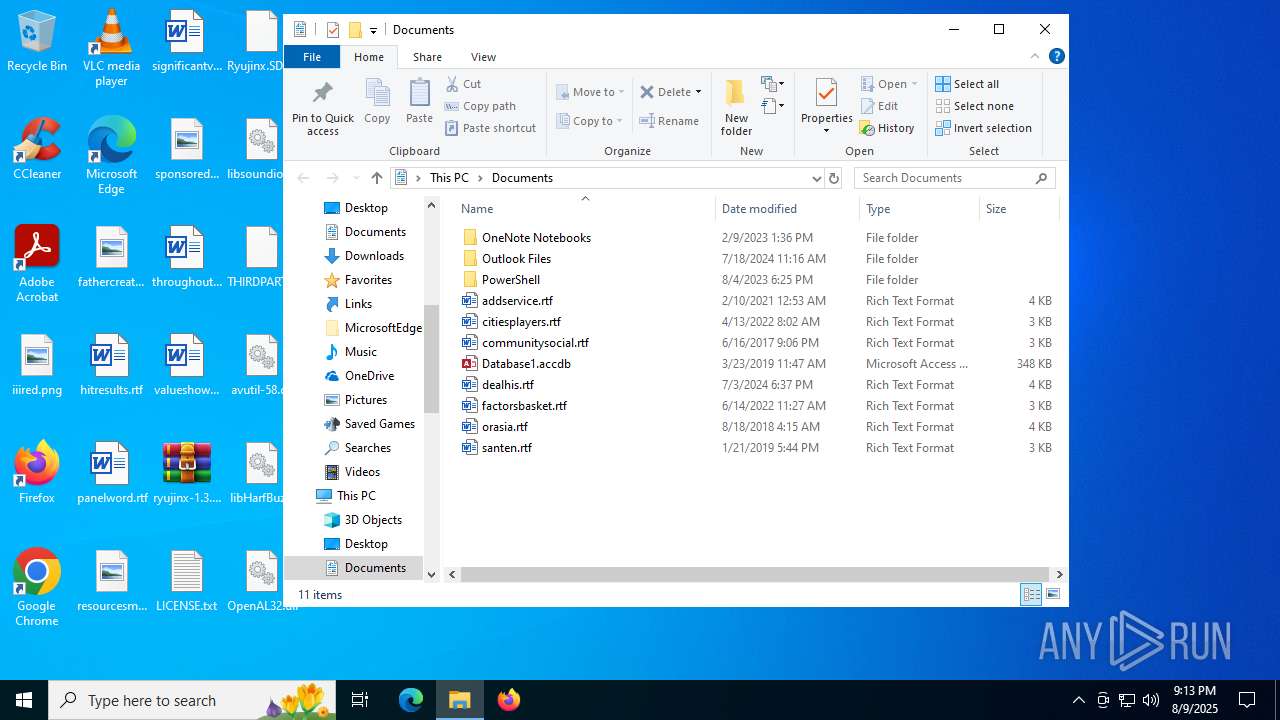
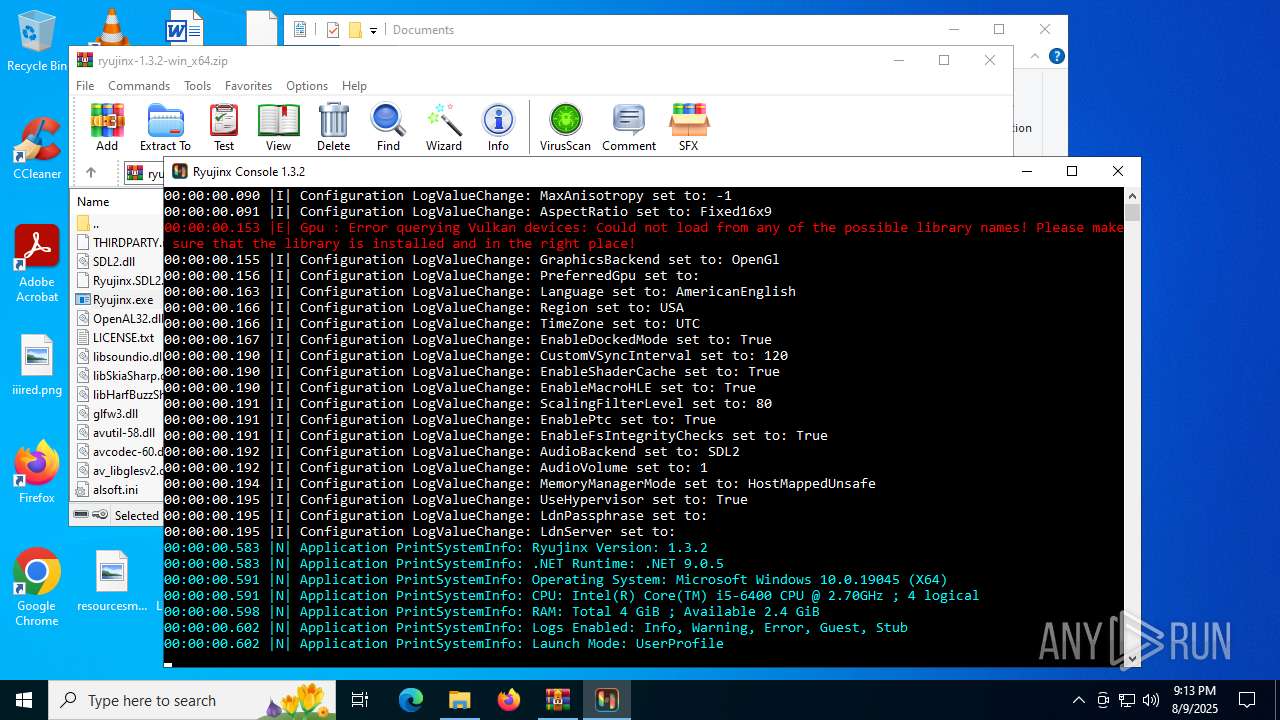
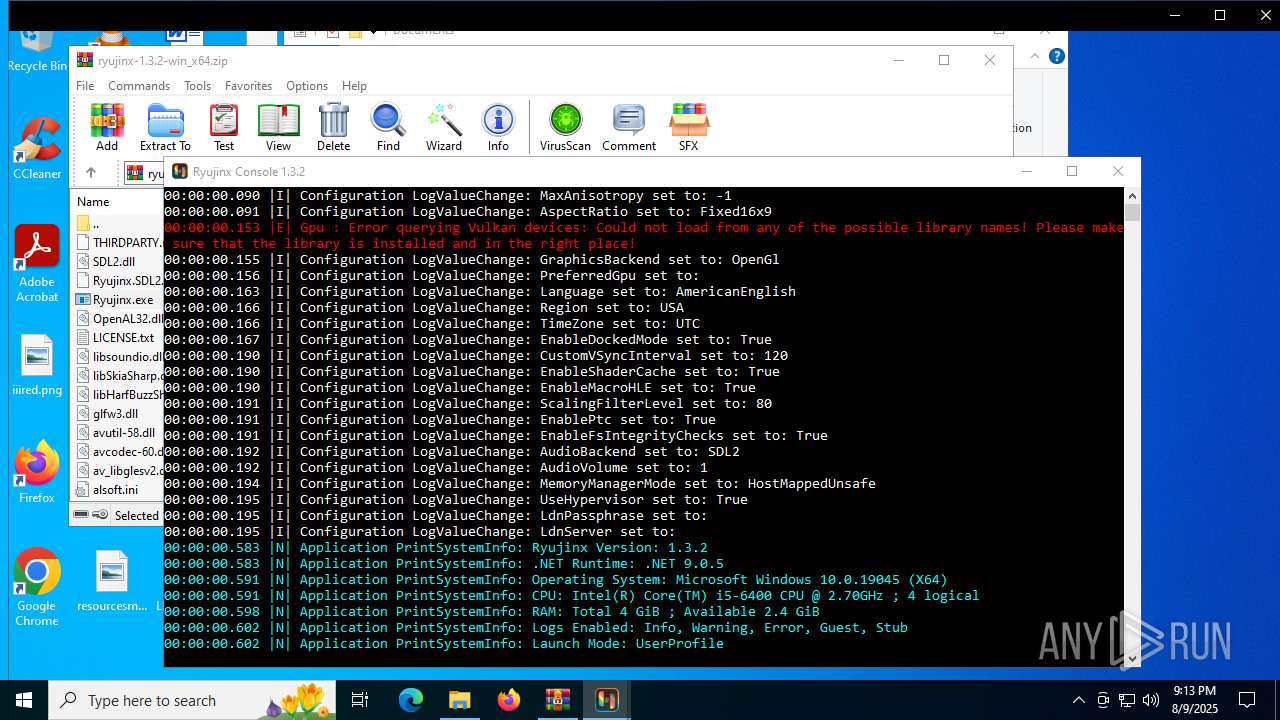
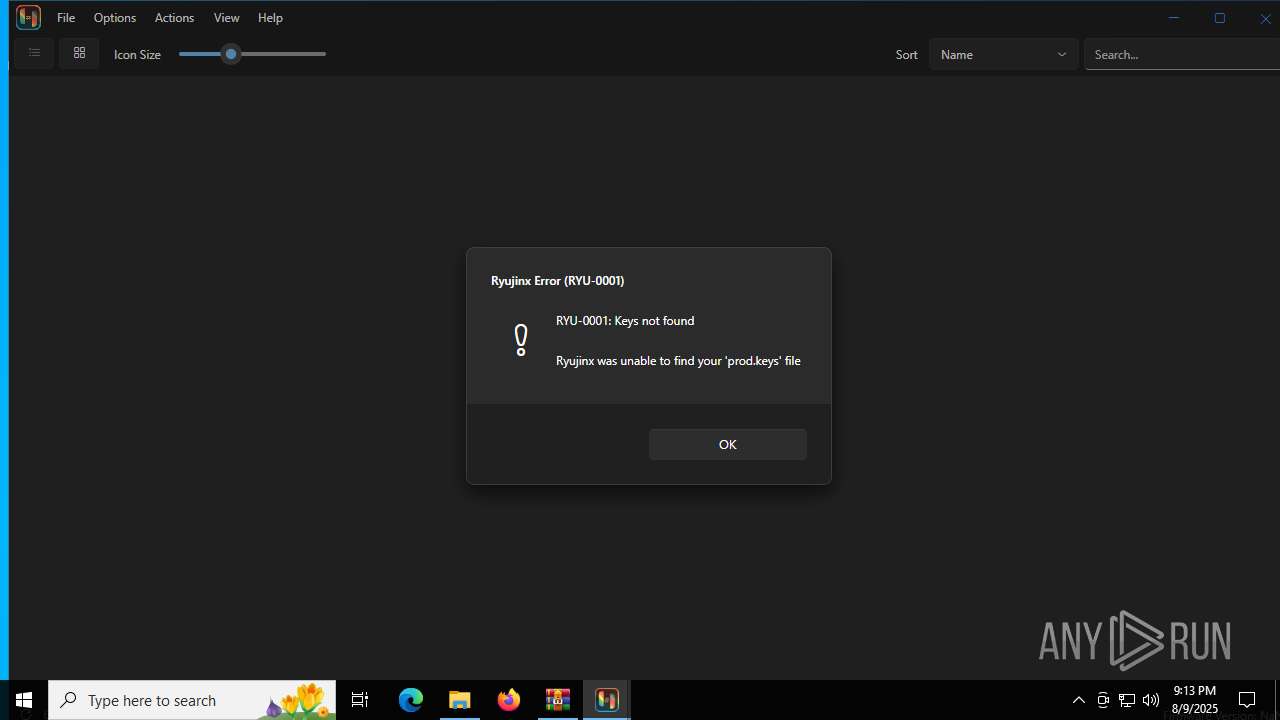
Creates files in the program directory
- Ryujinx.exe (PID: 3160)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 5436)
Checks supported languages
- Ryujinx.exe (PID: 3160)
Process checks computer location settings
- Ryujinx.exe (PID: 3160)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4684)
Reads the computer name
- Ryujinx.exe (PID: 3160)
Create files in a temporary directory
- Ryujinx.exe (PID: 3160)
Creates files or folders in the user directory
- Ryujinx.exe (PID: 3160)
Reads mouse settings
- Ryujinx.exe (PID: 3160)
Checks proxy server information
- Ryujinx.exe (PID: 3160)
- slui.exe (PID: 7084)
Reads the software policy settings
- Ryujinx.exe (PID: 3160)
- slui.exe (PID: 7084)
Reads the machine GUID from the registry
- Ryujinx.exe (PID: 3160)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
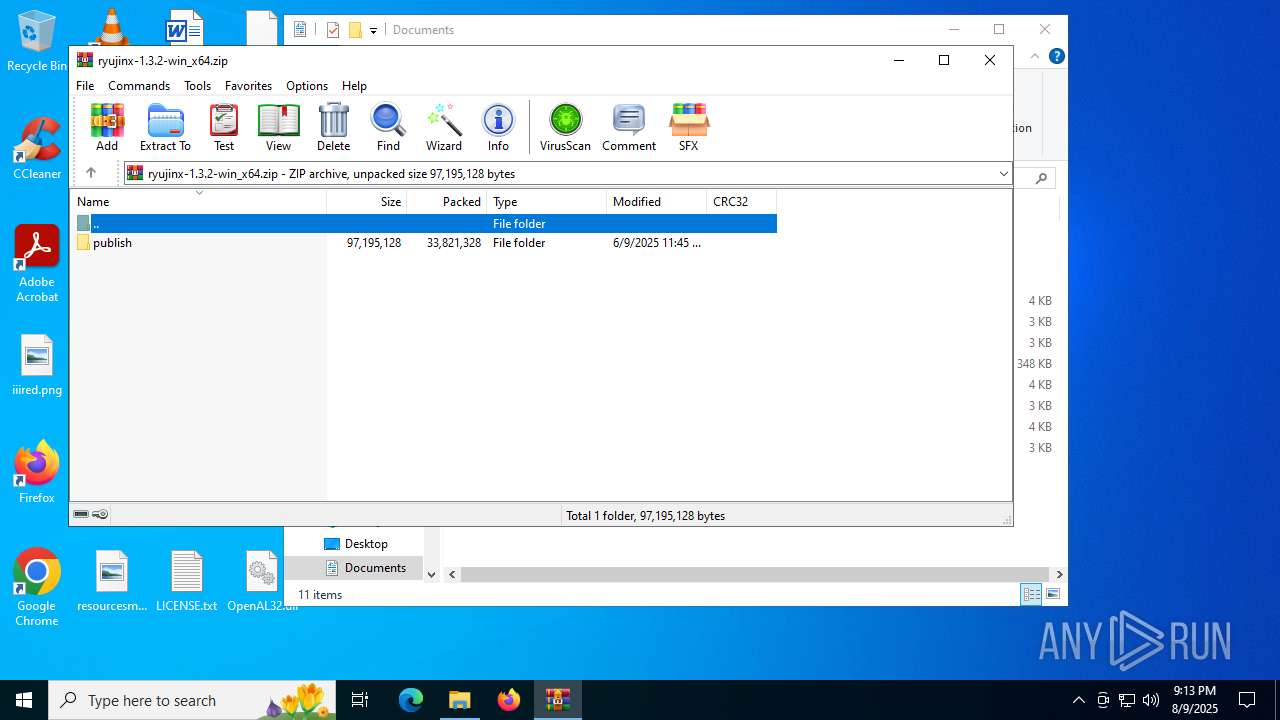
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2025:06:09 23:45:10 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | publish/ |
Total processes
130
Monitored processes
8
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2400 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\LICENSE.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2632 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Ryujinx.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
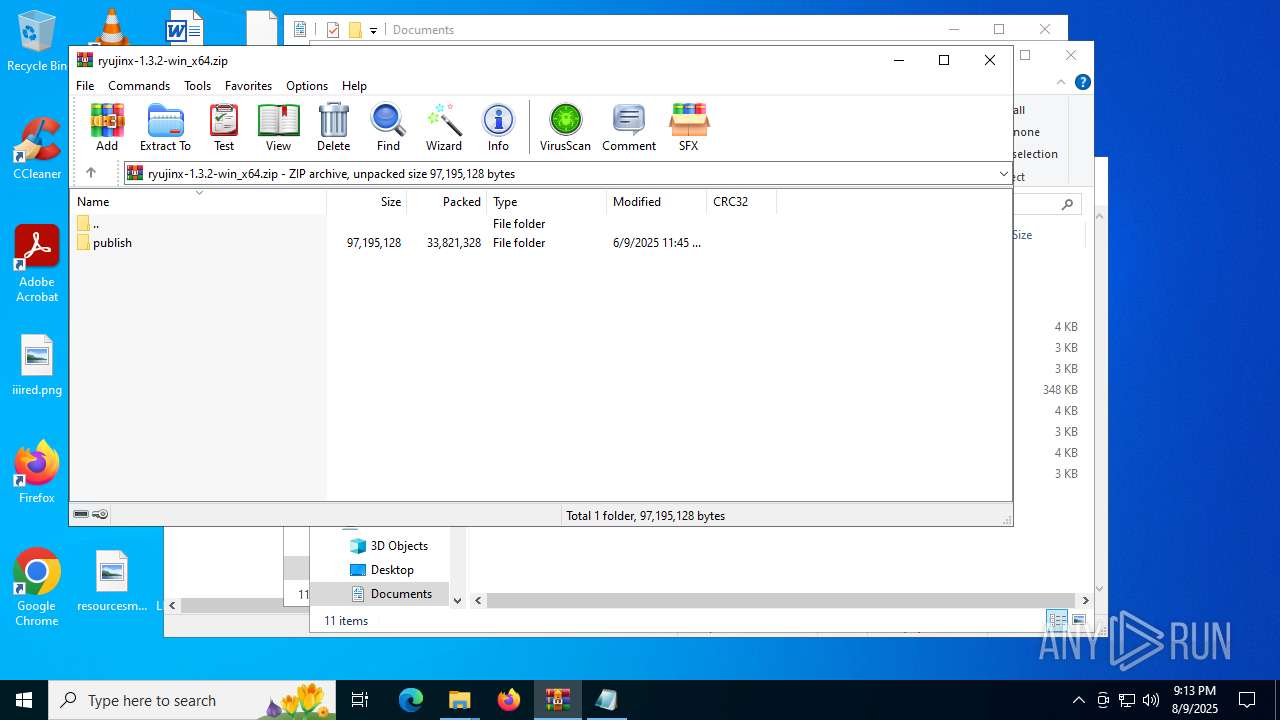
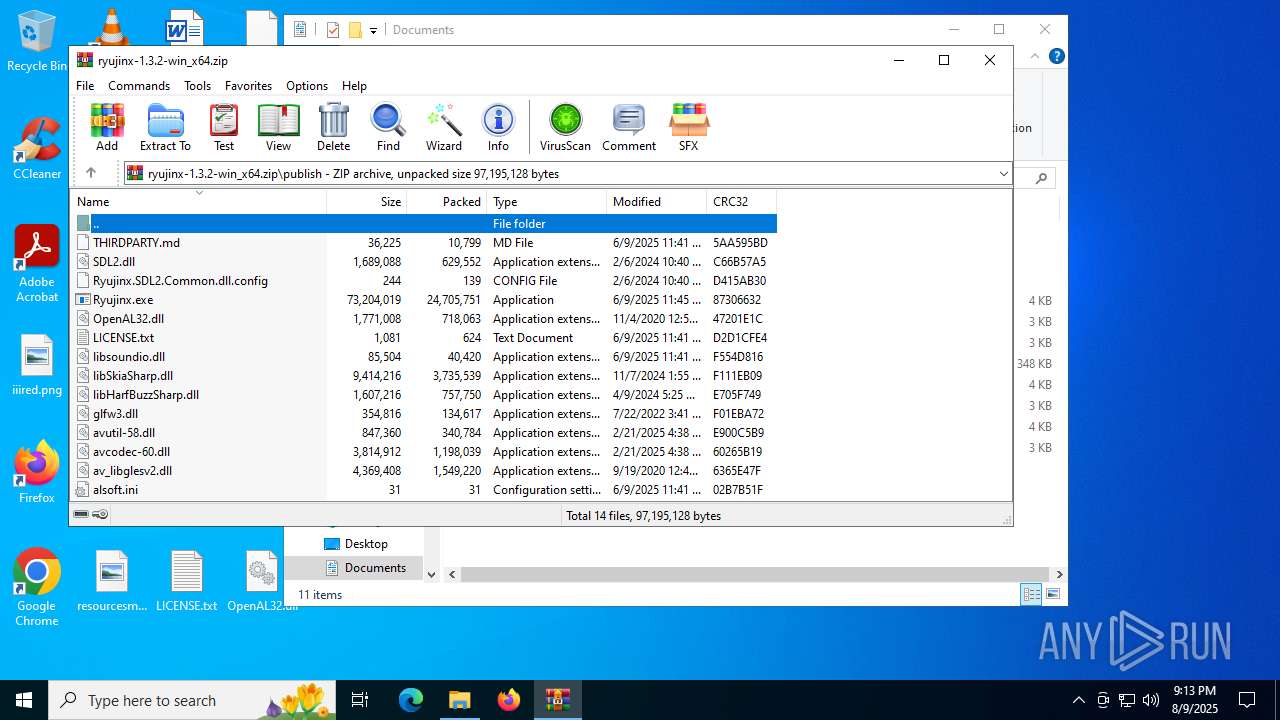
| 3160 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa4684.32226\publish\Ryujinx.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa4684.32226\publish\Ryujinx.exe | WinRAR.exe | ||||||||||||
User: admin Company: Ryujinx Integrity Level: MEDIUM Description: Ryujinx Version: 1.3.2.0 Modules
| |||||||||||||||
| 3288 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\ryujinx-1.3.2-win_x64.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 4400 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4684 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\ryujinx-1.3.2-win_x64.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 5436 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7084 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
12 578
Read events
12 553
Write events
25
Delete events
0
Modification events
| (PID) Process: | (3288) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (3288) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (3288) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (3288) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\ryujinx-1.3.2-win_x64.zip | |||
| (PID) Process: | (3288) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3288) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3288) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3288) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3288) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList |
| Operation: | write | Name: | ArcSort |
Value: 32 | |||
| (PID) Process: | (3288) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
Executable files
9
Suspicious files
18
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4684 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa4684.32226\publish\Ryujinx.exe | — | |
MD5:— | SHA256:— | |||
| 3160 | Ryujinx.exe | C:\Users\admin\AppData\Roaming\Ryujinx\bis\system\save\8000000000000000\.lock | — | |
MD5:— | SHA256:— | |||
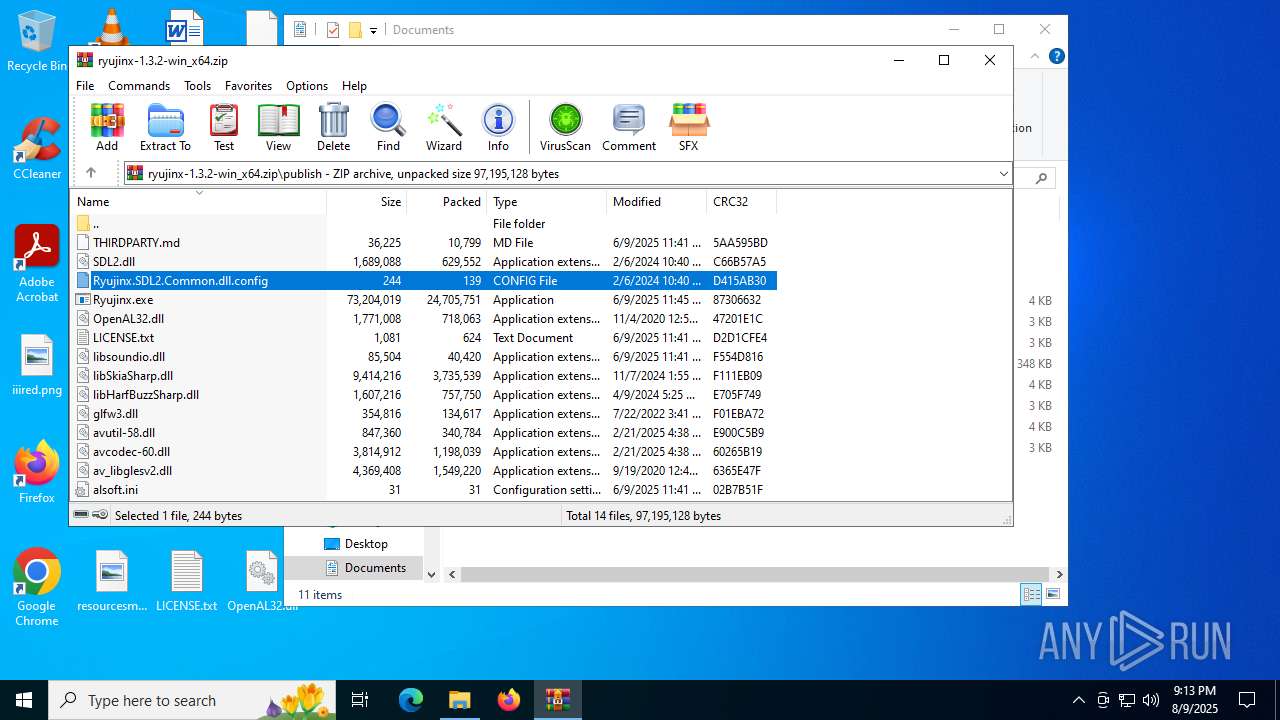
| 4684 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa4684.32153\Ryujinx.SDL2.Common.dll.config | xml | |
MD5:2D175F1DAD5AFD5FF46691DB53D9459A | SHA256:CCB8D75668D09DA1D56153FEF48E62DE2EF3C6248CFB1B98169C4D94EAC77CEB | |||
| 3160 | Ryujinx.exe | C:\Users\admin\AppData\Roaming\Ryujinx\bis\system\save\8000000000000000\_\lastPublishedId | binary | |
MD5:7DEA362B3FAC8E00956A4952A3D4F474 | SHA256:AF5570F5A1810B7AF78CAF4BC70A660F0DF51E42BAF91D4DE5B2328DE0E83DFC | |||
| 4684 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa4684.32226\publish\glfw3.dll | executable | |
MD5:529BF9FB63A41E5CC66CB1FC0B4303D7 | SHA256:E15C2DCA331D4C15B7F60FBAD81F7774EC4CF23C94484D4DC1912C016EAA93EA | |||
| 4684 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa4684.32226\publish\Ryujinx.SDL2.Common.dll.config | xml | |
MD5:2D175F1DAD5AFD5FF46691DB53D9459A | SHA256:CCB8D75668D09DA1D56153FEF48E62DE2EF3C6248CFB1B98169C4D94EAC77CEB | |||
| 4684 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa4684.32226\publish\SDL2.dll | executable | |
MD5:26D8AF4C3B7E8AA2BDBEE75BE3506728 | SHA256:C48431A47D57D99D7A056D634427B2B9DD7D640D3E8D9AC14551EE39A9906ECC | |||
| 3160 | Ryujinx.exe | C:\Users\admin\AppData\Roaming\Ryujinx\Config.json | binary | |
MD5:E1F3FD3010ADD4B249DE318195AEE138 | SHA256:566CCE2DA98C4F38A9C4681D0710369AC40232478F6E25813E4A94B51C56BF20 | |||
| 3160 | Ryujinx.exe | C:\Users\admin\AppData\Roaming\Ryujinx\bis\system\save\8000000000000000\ExtraData1 | binary | |
MD5:BF619EAC0CDF3F68D496EA9344137E8B | SHA256:076A27C79E5ACE2A3D47F9DD2E83E4FF6EA8872B3C2218F66C92B89B55F36560 | |||
| 3160 | Ryujinx.exe | C:\Users\admin\AppData\Roaming\Ryujinx\bis\system\save\8000000000000000\1\lastPublishedId | binary | |
MD5:7DEA362B3FAC8E00956A4952A3D4F474 | SHA256:AF5570F5A1810B7AF78CAF4BC70A660F0DF51E42BAF91D4DE5B2328DE0E83DFC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
39
TCP/UDP connections
54
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
— | — | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 814 b | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
1268 | svchost.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 814 b | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 814 b | whitelisted |
— | — | POST | 400 | 20.190.159.129:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 203 b | whitelisted |
— | — | POST | 400 | 20.190.159.73:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 203 b | whitelisted |
— | — | POST | 400 | 40.126.31.1:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 203 b | whitelisted |
— | — | POST | 200 | 20.190.159.129:443 | https://login.live.com/RST2.srf | US | xml | 1.24 Kb | whitelisted |
— | — | POST | 400 | 20.190.159.64:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | US | text | 203 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 69.192.161.161:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 69.192.161.161:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1268 | svchost.exe | 69.192.161.161:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.126.32.72:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |