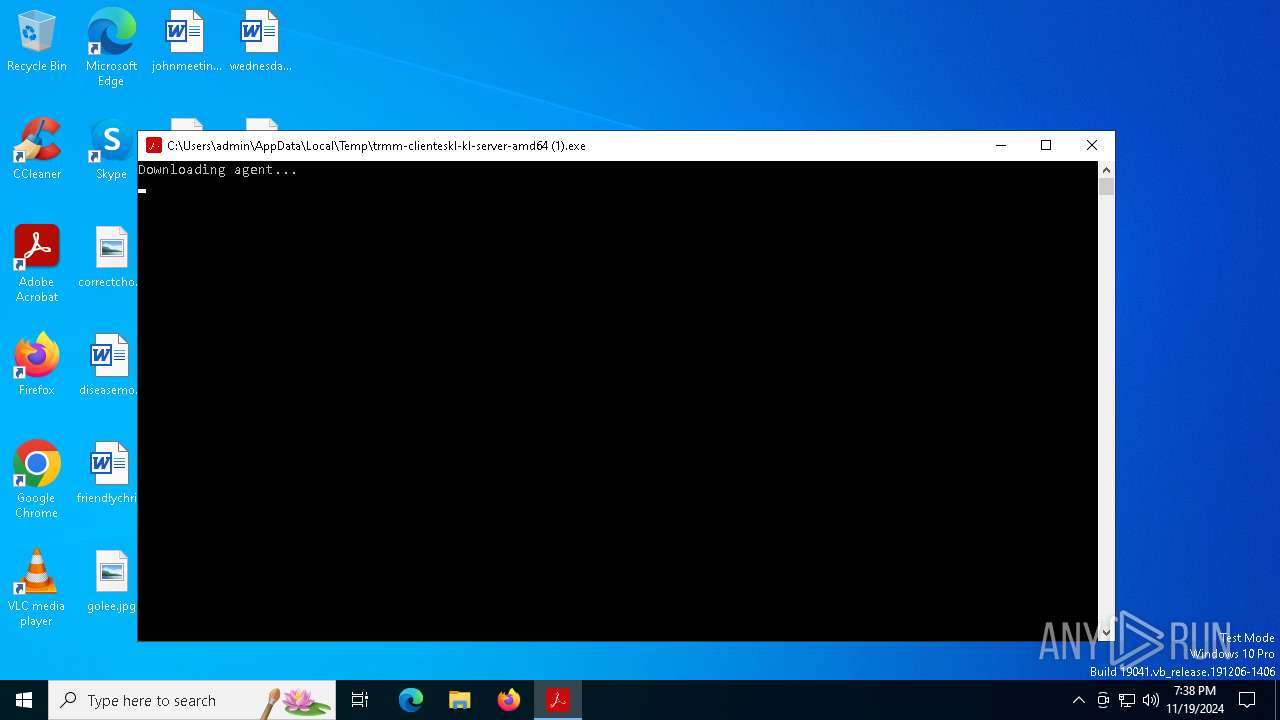
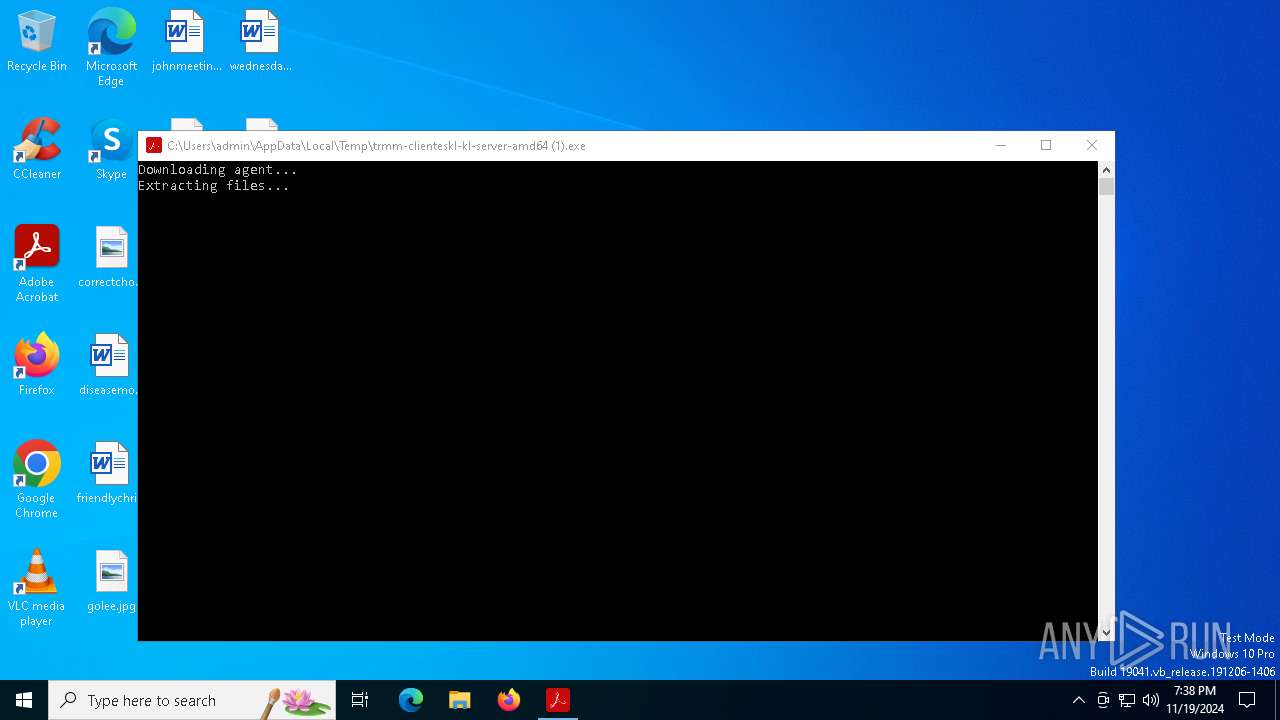
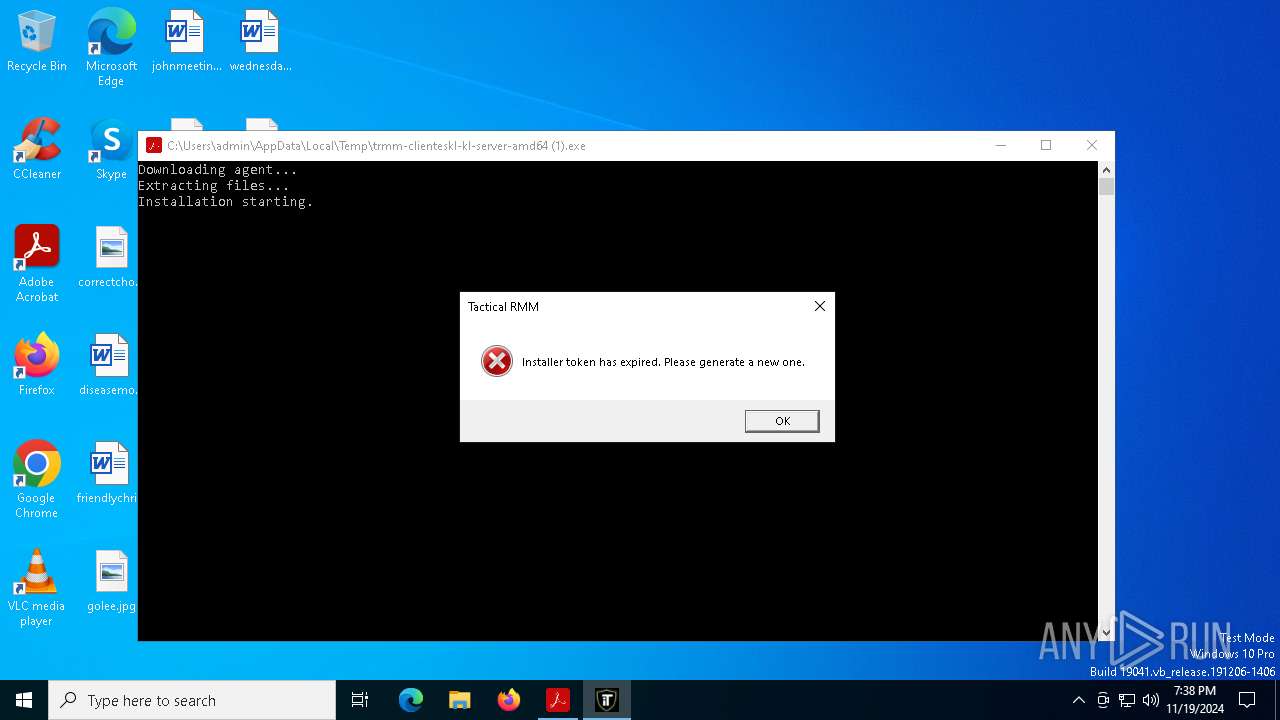
| File name: | trmm-clienteskl-kl-server-amd64 (1).exe |
| Full analysis: | https://app.any.run/tasks/1b28b34c-29c0-4207-84fc-f42d043535fb |
| Verdict: | Malicious activity |
| Analysis date: | November 19, 2024, 19:37:55 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64 (stripped to external PDB), for MS Windows, 7 sections |
| MD5: | 06ED29BCDE04DB56ECA31401693D8832 |
| SHA1: | 8299D1CE614E455ACFF7921A5CC13C3F2FA6357C |
| SHA256: | ACB4F7538DB2025DE794D0676890CC0F4BEE1E3EC6BD5A14FEFE4B8761CC5360 |
| SSDEEP: | 49152:i3fzJ1SuAah+Y8Zf5ilmLHH+LLDXAMLri68caOhYoqZUSKNK+9oBxfPKPjbj2jjB:WTSWF8eXAMZaOhh0w5yM4ZSC/O1w |
MALICIOUS
Starts NET.EXE for service management
- cmd.exe (PID: 5696)
- cmd.exe (PID: 720)
- net.exe (PID: 5872)
- net.exe (PID: 5544)
- net.exe (PID: 5920)
- cmd.exe (PID: 5096)
- cmd.exe (PID: 3648)
- net.exe (PID: 5920)
SUSPICIOUS
Executable content was dropped or overwritten
- trmm-clienteskl-kl-server-amd64 (1).exe (PID: 5092)
- tacticalagent-v2.8.0-windows-amd64.exe (PID: 376)
- tacticalagent-v2.8.0-windows-amd64.tmp (PID: 396)
Adds/modifies Windows certificates
- trmm-clienteskl-kl-server-amd64 (1).exe (PID: 5092)
Reads the Windows owner or organization settings
- tacticalagent-v2.8.0-windows-amd64.tmp (PID: 396)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 5696)
- cmd.exe (PID: 5096)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 720)
Starts CMD.EXE for commands execution
- tacticalagent-v2.8.0-windows-amd64.tmp (PID: 396)
INFO
Creates files in the program directory
- trmm-clienteskl-kl-server-amd64 (1).exe (PID: 5092)
Reads the computer name
- trmm-clienteskl-kl-server-amd64 (1).exe (PID: 5092)
- tacticalagent-v2.8.0-windows-amd64.tmp (PID: 396)
Checks supported languages
- trmm-clienteskl-kl-server-amd64 (1).exe (PID: 5092)
- tacticalagent-v2.8.0-windows-amd64.exe (PID: 376)
- tacticalagent-v2.8.0-windows-amd64.tmp (PID: 396)
Reads the machine GUID from the registry
- trmm-clienteskl-kl-server-amd64 (1).exe (PID: 5092)
Reads the software policy settings
- trmm-clienteskl-kl-server-amd64 (1).exe (PID: 5092)
Create files in a temporary directory
- tacticalagent-v2.8.0-windows-amd64.exe (PID: 376)
- tacticalagent-v2.8.0-windows-amd64.tmp (PID: 396)
Application based on Golang
- trmm-clienteskl-kl-server-amd64 (1).exe (PID: 5092)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 0000:00:00 00:00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, No debug |
| PEType: | PE32+ |
| LinkerVersion: | 3 |
| CodeSize: | 2520576 |
| InitializedDataSize: | 265216 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x66fe0 |
| OSVersion: | 6.1 |
| ImageVersion: | 1 |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 2.0.4.0 |
| ProductVersionNumber: | 2.0.4.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Abode LLC |
| FileDescription: | Abode LLC |
| FileVersion: | v2.0.4.0 |
| InternalName: | Abode LLC |
| LegalCopyright: | Copyright (c) 2022 AmidaWare LLC |
| OriginalFileName: | installer.go |
| ProductName: | Abode LLC |
| ProductVersion: | v2.0.4.0 |
Total processes
160
Monitored processes
36
Malicious processes
2
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 376 | C:\ProgramData\TacticalRMM\tacticalagent-v2.8.0-windows-amd64.exe /VERYSILENT /SUPPRESSMSGBOXES | C:\ProgramData\TacticalRMM\tacticalagent-v2.8.0-windows-amd64.exe | trmm-clienteskl-kl-server-amd64 (1).exe | ||||||||||||
User: admin Company: AmidaWare Inc Integrity Level: HIGH Description: Tactical RMM Agent Setup Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 396 | "C:\Users\admin\AppData\Local\Temp\is-SS1JI.tmp\tacticalagent-v2.8.0-windows-amd64.tmp" /SL5="$201E0,3660179,825344,C:\ProgramData\TacticalRMM\tacticalagent-v2.8.0-windows-amd64.exe" /VERYSILENT /SUPPRESSMSGBOXES | C:\Users\admin\AppData\Local\Temp\is-SS1JI.tmp\tacticalagent-v2.8.0-windows-amd64.tmp | tacticalagent-v2.8.0-windows-amd64.exe | ||||||||||||
User: admin Company: AmidaWare Inc Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 720 | "cmd.exe" /c net stop tacticalagent | C:\Windows\SysWOW64\cmd.exe | — | tacticalagent-v2.8.0-windows-amd64.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 720 | "cmd.exe" /c taskkill /F /IM tacticalrmm.exe | C:\Windows\SysWOW64\cmd.exe | — | tacticalagent-v2.8.0-windows-amd64.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 128 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 720 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 772 | "cmd.exe" /c sc delete tacticalagent | C:\Windows\SysWOW64\cmd.exe | — | tacticalagent-v2.8.0-windows-amd64.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1060 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1616 | sc delete tacticalrpc | C:\Windows\SysWOW64\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2768 | "cmd.exe" /c sc delete tacticalrpc | C:\Windows\SysWOW64\cmd.exe | — | tacticalagent-v2.8.0-windows-amd64.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1060 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3556 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3648 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
9 520
Read events
9 491
Write events
27
Delete events
2
Modification events
| (PID) Process: | (5092) trmm-clienteskl-kl-server-amd64 (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates |
| Operation: | delete value | Name: | 2A1D6027D94AB10A1C4D915CCD33A0CB3E2D54CB |
Value: | |||
| (PID) Process: | (5092) trmm-clienteskl-kl-server-amd64 (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\2A1D6027D94AB10A1C4D915CCD33A0CB3E2D54CB |
| Operation: | write | Name: | Blob |
Value: 0400000001000000100000005DB66AC46017246A1A99A84BEE5EB426140000000100000014000000804CD6EB74FF4936A3D5D8FCB53EC56AF0941D8C62000000010000002000000071CCA5391F9E794B04802530B363E121DA8A3043BB26662FEA4DCA7FC951A4BD19000000010000001000000086665B2DECDDA69376F98E02CD5FA29A0300000001000000140000002A1D6027D94AB10A1C4D915CCD33A0CB3E2D54CB0F0000000100000030000000DF03EE17776FAE07203AE956F6094206455C833A06297419E38793A34C4E010E8E0DD06107E0CD574F970FB35FB7C04E09000000010000002A000000302806082B0601050507030206082B0601050507030406082B0601050507030106082B060105050703080B0000000100000018000000470054005300200052006F006F00740020005200340000001D00000001000000100000006D81CF5A57E7A81939F2FA048E7CB95020000000010000000E0200003082020A30820191A00302010202106E47A9C88B94B6E8BB3B2AD8A2B2C199300A06082A8648CE3D0403033047310B300906035504061302555331223020060355040A1319476F6F676C65205472757374205365727669636573204C4C43311430120603550403130B47545320526F6F74205234301E170D3136303632323030303030305A170D3336303632323030303030305A3047310B300906035504061302555331223020060355040A1319476F6F676C65205472757374205365727669636573204C4C43311430120603550403130B47545320526F6F742052343076301006072A8648CE3D020106052B8104002203620004F37473A7688B60AE43B835C581307B4B499DFBC161CEE6DE46BD6BD5611835AE40DD73F78991305AEB3CEE857CA240763BA9C6B847D82AE792916A73E9B172399F299FA298D35F5E5886650FA1846506D1DC8BC9C773C88C6A2FE5C4ABD11D8AA3423040300E0603551D0F0101FF040403020106300F0603551D130101FF040530030101FF301D0603551D0E04160414804CD6EB74FF4936A3D5D8FCB53EC56AF0941D8C300A06082A8648CE3D040303036700306402306A50527408C470DC9E507421E88D7A21C34F966E15D12235612DFA0837EE196DADDBB2CC7D0734F560192CB534D96F2002300371B1BAA3600B86ED9A086A95689FE2B3E193647C5E93A6DF792D8D85E394CF235D71CCF2B04DD6FE99C894A975A2E3 | |||
| (PID) Process: | (5092) trmm-clienteskl-kl-server-amd64 (1).exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\2A1D6027D94AB10A1C4D915CCD33A0CB3E2D54CB |
| Operation: | write | Name: | Blob |
Value: 5C0000000100000004000000800100001D00000001000000100000006D81CF5A57E7A81939F2FA048E7CB9500B0000000100000018000000470054005300200052006F006F007400200052003400000009000000010000002A000000302806082B0601050507030206082B0601050507030406082B0601050507030106082B060105050703080F0000000100000030000000DF03EE17776FAE07203AE956F6094206455C833A06297419E38793A34C4E010E8E0DD06107E0CD574F970FB35FB7C04E0300000001000000140000002A1D6027D94AB10A1C4D915CCD33A0CB3E2D54CB19000000010000001000000086665B2DECDDA69376F98E02CD5FA29A62000000010000002000000071CCA5391F9E794B04802530B363E121DA8A3043BB26662FEA4DCA7FC951A4BD140000000100000014000000804CD6EB74FF4936A3D5D8FCB53EC56AF0941D8C0400000001000000100000005DB66AC46017246A1A99A84BEE5EB42620000000010000000E0200003082020A30820191A00302010202106E47A9C88B94B6E8BB3B2AD8A2B2C199300A06082A8648CE3D0403033047310B300906035504061302555331223020060355040A1319476F6F676C65205472757374205365727669636573204C4C43311430120603550403130B47545320526F6F74205234301E170D3136303632323030303030305A170D3336303632323030303030305A3047310B300906035504061302555331223020060355040A1319476F6F676C65205472757374205365727669636573204C4C43311430120603550403130B47545320526F6F742052343076301006072A8648CE3D020106052B8104002203620004F37473A7688B60AE43B835C581307B4B499DFBC161CEE6DE46BD6BD5611835AE40DD73F78991305AEB3CEE857CA240763BA9C6B847D82AE792916A73E9B172399F299FA298D35F5E5886650FA1846506D1DC8BC9C773C88C6A2FE5C4ABD11D8AA3423040300E0603551D0F0101FF040403020106300F0603551D130101FF040530030101FF301D0603551D0E04160414804CD6EB74FF4936A3D5D8FCB53EC56AF0941D8C300A06082A8648CE3D040303036700306402306A50527408C470DC9E507421E88D7A21C34F966E15D12235612DFA0837EE196DADDBB2CC7D0734F560192CB534D96F2002300371B1BAA3600B86ED9A086A95689FE2B3E193647C5E93A6DF792D8D85E394CF235D71CCF2B04DD6FE99C894A975A2E3 | |||
| (PID) Process: | (396) tacticalagent-v2.8.0-windows-amd64.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{0D34D278-5FAF-4159-A4A0-4E2D2C08139D}_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 6.2.2 | |||
| (PID) Process: | (396) tacticalagent-v2.8.0-windows-amd64.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{0D34D278-5FAF-4159-A4A0-4E2D2C08139D}_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\TacticalAgent | |||
| (PID) Process: | (396) tacticalagent-v2.8.0-windows-amd64.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{0D34D278-5FAF-4159-A4A0-4E2D2C08139D}_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\TacticalAgent\ | |||
| (PID) Process: | (396) tacticalagent-v2.8.0-windows-amd64.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{0D34D278-5FAF-4159-A4A0-4E2D2C08139D}_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: (Default) | |||
| (PID) Process: | (396) tacticalagent-v2.8.0-windows-amd64.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{0D34D278-5FAF-4159-A4A0-4E2D2C08139D}_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (396) tacticalagent-v2.8.0-windows-amd64.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{0D34D278-5FAF-4159-A4A0-4E2D2C08139D}_is1 |
| Operation: | write | Name: | Inno Setup: Language |
Value: english | |||
| (PID) Process: | (396) tacticalagent-v2.8.0-windows-amd64.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\{0D34D278-5FAF-4159-A4A0-4E2D2C08139D}_is1 |
| Operation: | write | Name: | DisplayName |
Value: Tactical RMM Agent | |||
Executable files
7
Suspicious files
1
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 396 | tacticalagent-v2.8.0-windows-amd64.tmp | C:\Program Files\TacticalAgent\is-0IBTL.tmp | executable | |
MD5:BB383B7C3D5E4ACB1001AB099B5B0F3C | SHA256:A6D3159C858AA3704F35D69B27829618AD0D1BAE894C848A5233100C17464F95 | |||
| 5092 | trmm-clienteskl-kl-server-amd64 (1).exe | C:\ProgramData\TacticalRMM\tacticalagent-v2.8.0-windows-amd64.exe | executable | |
MD5:2F046950E65922336CD83BF0DBC9DE33 | SHA256:412E1F600251B21911C582E69381F677E663231F5E1D10786D88A026E00EA811 | |||
| 396 | tacticalagent-v2.8.0-windows-amd64.tmp | C:\Program Files\TacticalAgent\is-KHRTJ.tmp | executable | |
MD5:5E81857286E2795352225BE245FBD62B | SHA256:2624C22DA19E89717DCD522D22B21849A1C3F0EB781333DF85BE5FCD57597278 | |||
| 396 | tacticalagent-v2.8.0-windows-amd64.tmp | C:\Users\admin\AppData\Local\Temp\is-NKKER.tmp\_isetup\_setup64.tmp | executable | |
MD5:E4211D6D009757C078A9FAC7FF4F03D4 | SHA256:388A796580234EFC95F3B1C70AD4CB44BFDDC7BA0F9203BF4902B9929B136F95 | |||
| 396 | tacticalagent-v2.8.0-windows-amd64.tmp | C:\Program Files\TacticalAgent\unins000.exe | executable | |
MD5:5E81857286E2795352225BE245FBD62B | SHA256:2624C22DA19E89717DCD522D22B21849A1C3F0EB781333DF85BE5FCD57597278 | |||
| 396 | tacticalagent-v2.8.0-windows-amd64.tmp | C:\Users\admin\AppData\Local\Temp\Setup Log 2024-11-19 #001.txt | text | |
MD5:0E5EBD13455AA62CD1651AA7BFF48B79 | SHA256:8A80437558804C9A70FD6CC6E936BBA8E6310BA0A7195AD20512E5D1810AD4E0 | |||
| 396 | tacticalagent-v2.8.0-windows-amd64.tmp | C:\Program Files\TacticalAgent\tacticalrmm.exe | executable | |
MD5:BB383B7C3D5E4ACB1001AB099B5B0F3C | SHA256:A6D3159C858AA3704F35D69B27829618AD0D1BAE894C848A5233100C17464F95 | |||
| 396 | tacticalagent-v2.8.0-windows-amd64.tmp | C:\Program Files\TacticalAgent\unins000.dat | binary | |
MD5:6D4A8C87373F55298D866030E1EF7B76 | SHA256:EB74134FD58F402A5162A4B119712F2CA3FDE195C181DEEFDFEDD0092D0A5703 | |||
| 376 | tacticalagent-v2.8.0-windows-amd64.exe | C:\Users\admin\AppData\Local\Temp\is-SS1JI.tmp\tacticalagent-v2.8.0-windows-amd64.tmp | executable | |
MD5:A639312111D278FEE4F70299C134D620 | SHA256:4B0BE5167A31A77E28E3F0A7C83C9D289845075B51E70691236603B1083649DF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
34
DNS requests
22
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4932 | svchost.exe | GET | 200 | 2.16.164.97:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4932 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6576 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6576 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5696 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4932 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5896 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5064 | SearchApp.exe | 2.23.209.149:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5092 | trmm-clienteskl-kl-server-amd64 (1).exe | 172.67.151.233:443 | agents.tacticalrmm.com | CLOUDFLARENET | US | unknown |
4932 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4932 | svchost.exe | 2.16.164.97:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
agents.tacticalrmm.com |
| unknown |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
api.computadoratualizacao.com |
| unknown |
go.microsoft.com |
| whitelisted |