| File name: | iSetups.exe |
| Full analysis: | https://app.any.run/tasks/f36d5dce-36c0-4a47-8ab9-cd71a74eda53 |
| Verdict: | Malicious activity |
| Analysis date: | December 10, 2025, 15:00:41 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 11 sections |
| MD5: | A0EA5FD95765AAA8BD1E230161950AE7 |
| SHA1: | 01E57777C80571302F73A0D40CED66D6DC2E1C8D |
| SHA256: | ACAA6D40C3ADBD7079E1411DE4E33782EBD5C118BACA2AB01562E7F2220E8EAB |
| SSDEEP: | 98304:APXS+DPCqpT/nobF7L79C1bDCuXDfyGSIycUN8NNwF/SLjHezsJ/t1PJKlX69/eq:MDuP6d0Wd8FBds |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- iSetups.tmp (PID: 7404)
Executable content was dropped or overwritten
- iSetups.exe (PID: 7384)
- iSetups.exe (PID: 7584)
- iSetups.tmp (PID: 7608)
Reads the Windows owner or organization settings
- iSetups.tmp (PID: 7608)
Possible usage of Discord/Telegram API has been detected (YARA)
- iSetups.exe (PID: 7384)
- iSetups.tmp (PID: 7404)
- iSetups.exe (PID: 7584)
- iSetups.tmp (PID: 7608)
INFO
Checks supported languages
- iSetups.exe (PID: 7384)
- iSetups.tmp (PID: 7404)
- iSetups.exe (PID: 7584)
- iSetups.tmp (PID: 7608)
Create files in a temporary directory
- iSetups.exe (PID: 7384)
- iSetups.exe (PID: 7584)
- iSetups.tmp (PID: 7608)
Reads the computer name
- iSetups.tmp (PID: 7404)
- iSetups.exe (PID: 7584)
- iSetups.tmp (PID: 7608)
Process checks computer location settings
- iSetups.tmp (PID: 7404)
Detects InnoSetup installer (YARA)
- iSetups.exe (PID: 7384)
- iSetups.tmp (PID: 7404)
- iSetups.exe (PID: 7584)
- iSetups.tmp (PID: 7608)
Compiled with Borland Delphi (YARA)
- iSetups.exe (PID: 7384)
- iSetups.exe (PID: 7584)
- iSetups.tmp (PID: 7608)
- iSetups.tmp (PID: 7404)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (53.5) |
|---|---|---|
| .exe | | | InstallShield setup (21) |
| .exe | | | Win32 EXE PECompact compressed (generic) (20.2) |
| .exe | | | Win32 Executable (generic) (2.1) |
| .exe | | | Win16/32 Executable Delphi generic (1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:09:11 13:05:07+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 716800 |
| InitializedDataSize: | 164352 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb0028 |
| OSVersion: | 6.1 |
| ImageVersion: | - |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | nordlayer |
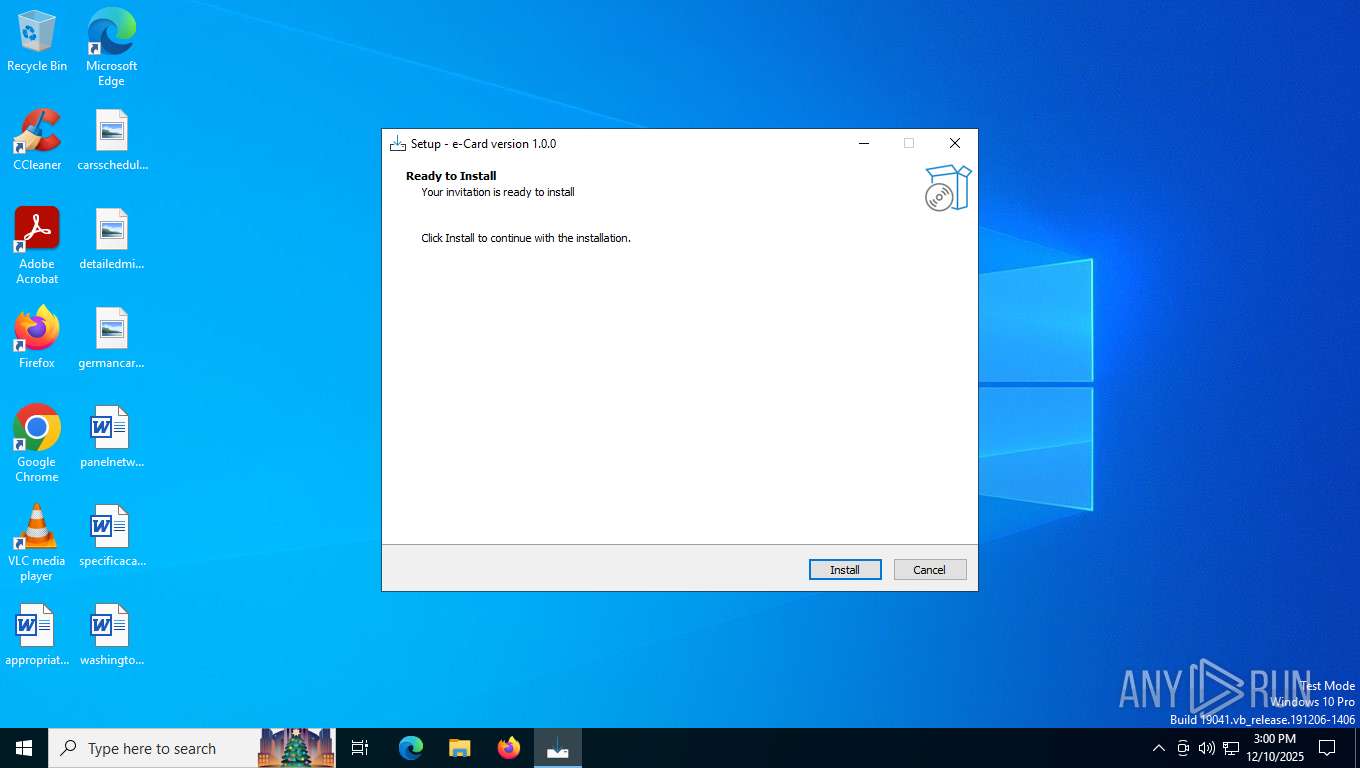
| FileDescription: | e-Card Setup |
| FileVersion: | |
| LegalCopyright: | |
| OriginalFileName: | |
| ProductName: | e-Card |
| ProductVersion: | 1.0.0 |
Total processes
142
Monitored processes
5
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 7300 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7384 | "C:\Users\admin\AppData\Local\Temp\iSetups.exe" | C:\Users\admin\AppData\Local\Temp\iSetups.exe | explorer.exe | ||||||||||||
User: admin Company: nordlayer Integrity Level: MEDIUM Description: e-Card Setup Version: Modules
| |||||||||||||||
| 7404 | "C:\Users\admin\AppData\Local\Temp\is-O2D6P.tmp\iSetups.tmp" /SL5="$6002E,3780661,882176,C:\Users\admin\AppData\Local\Temp\iSetups.exe" | C:\Users\admin\AppData\Local\Temp\is-O2D6P.tmp\iSetups.tmp | — | iSetups.exe | |||||||||||
User: admin Company: nordlayer Integrity Level: MEDIUM Description: Setup/Uninstall Version: 51.1052.0.0 Modules
| |||||||||||||||
| 7584 | "C:\Users\admin\AppData\Local\Temp\iSetups.exe" /SPAWNWND=$402EC /NOTIFYWND=$6002E | C:\Users\admin\AppData\Local\Temp\iSetups.exe | iSetups.tmp | ||||||||||||
User: admin Company: nordlayer Integrity Level: HIGH Description: e-Card Setup Version: Modules
| |||||||||||||||
| 7608 | "C:\Users\admin\AppData\Local\Temp\is-M7IAU.tmp\iSetups.tmp" /SL5="$60254,3780661,882176,C:\Users\admin\AppData\Local\Temp\iSetups.exe" /SPAWNWND=$402EC /NOTIFYWND=$6002E | C:\Users\admin\AppData\Local\Temp\is-M7IAU.tmp\iSetups.tmp | iSetups.exe | ||||||||||||
User: admin Company: nordlayer Integrity Level: HIGH Description: Setup/Uninstall Version: 51.1052.0.0 Modules
| |||||||||||||||
Total events
546
Read events
546
Write events
0
Delete events
0
Modification events
Executable files
3
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7608 | iSetups.tmp | C:\Users\admin\AppData\Local\Temp\is-S6DQE.tmp\_isetup\_setup64.tmp | executable | |
MD5:E4211D6D009757C078A9FAC7FF4F03D4 | SHA256:388A796580234EFC95F3B1C70AD4CB44BFDDC7BA0F9203BF4902B9929B136F95 | |||
| 7584 | iSetups.exe | C:\Users\admin\AppData\Local\Temp\is-M7IAU.tmp\iSetups.tmp | executable | |
MD5:991F83F24C3E0F71BA96FAEA7FBA9214 | SHA256:41BFD6ECB5102811311D45BECD94EEDF3D0227795FE06F9493D73D4799368797 | |||
| 7384 | iSetups.exe | C:\Users\admin\AppData\Local\Temp\is-O2D6P.tmp\iSetups.tmp | executable | |
MD5:991F83F24C3E0F71BA96FAEA7FBA9214 | SHA256:41BFD6ECB5102811311D45BECD94EEDF3D0227795FE06F9493D73D4799368797 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
23
DNS requests
17
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8040 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.3.crl | unknown | — | — | whitelisted |
8040 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
8040 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
144 | svchost.exe | GET | 200 | 23.216.77.15:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
144 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1780 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8040 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8040 | SIHClient.exe | GET | 200 | 23.216.77.42:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
8040 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8040 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
144 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1176 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
144 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
144 | svchost.exe | 23.216.77.15:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
144 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
1780 | svchost.exe | 40.126.32.136:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1780 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |