| URL: | vidcombo.com |
| Full analysis: | https://app.any.run/tasks/c86ee53c-1cc1-40de-85b0-fc54e4ccfbea |
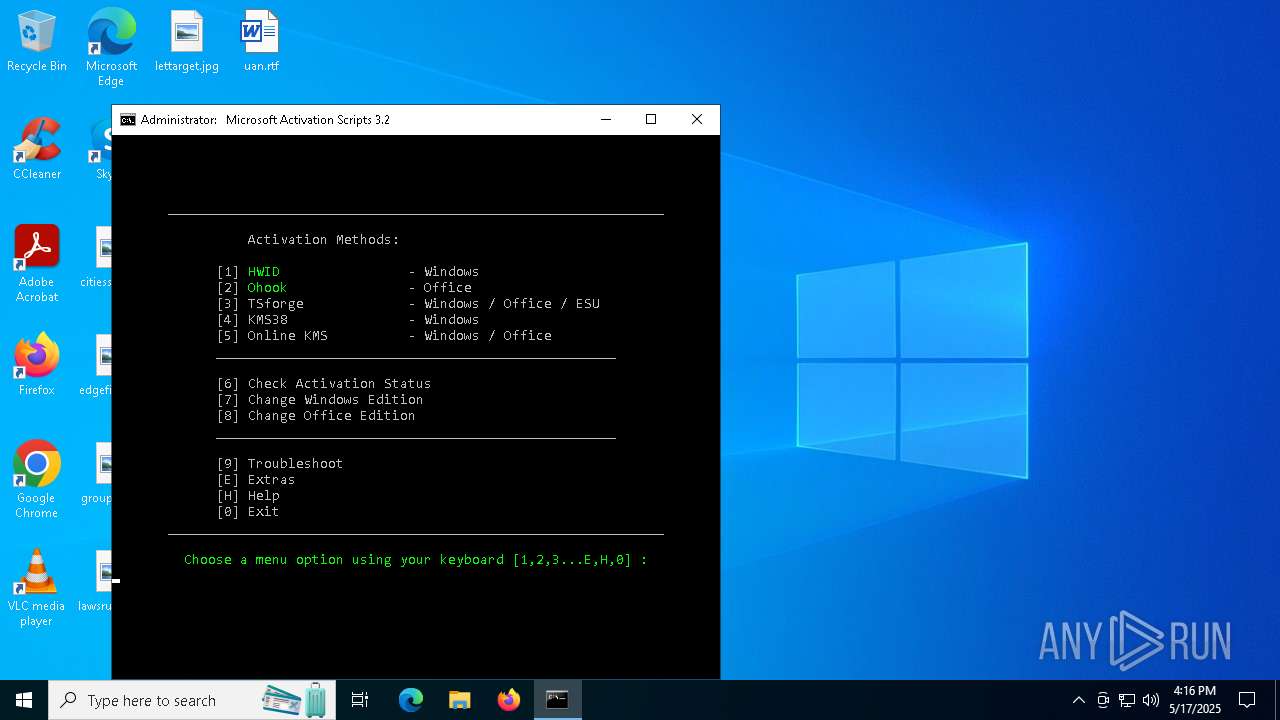
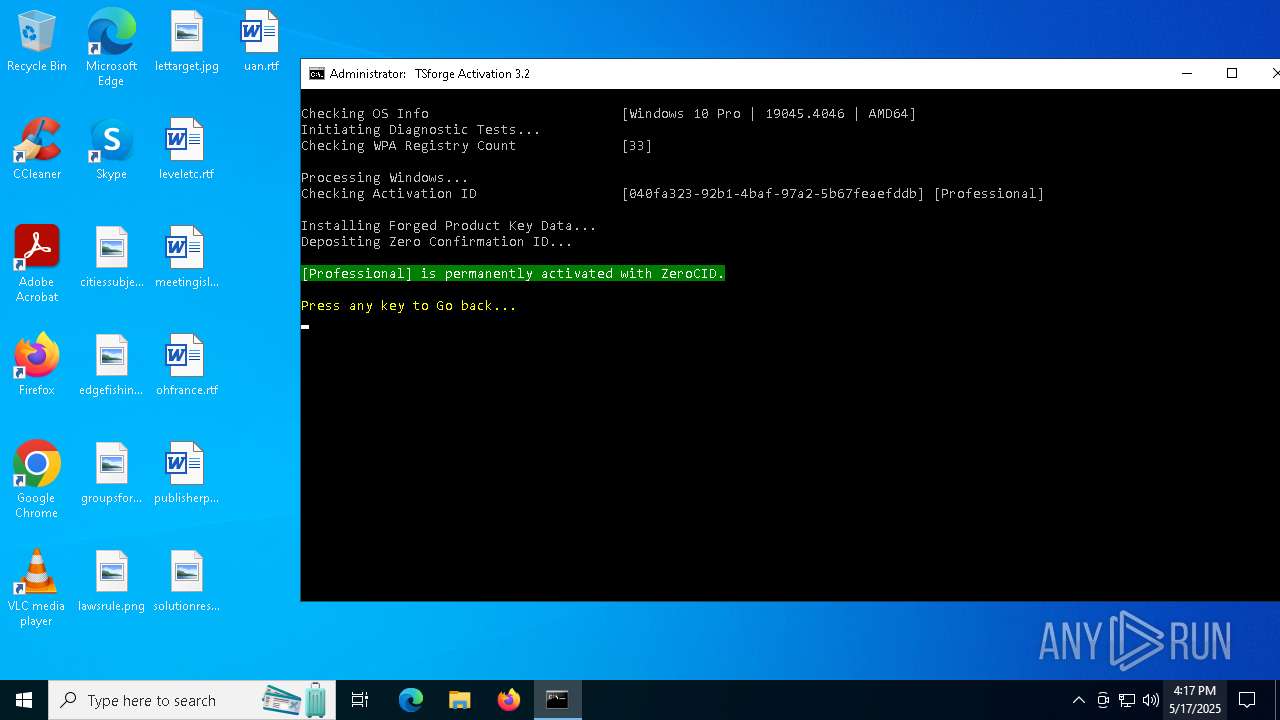
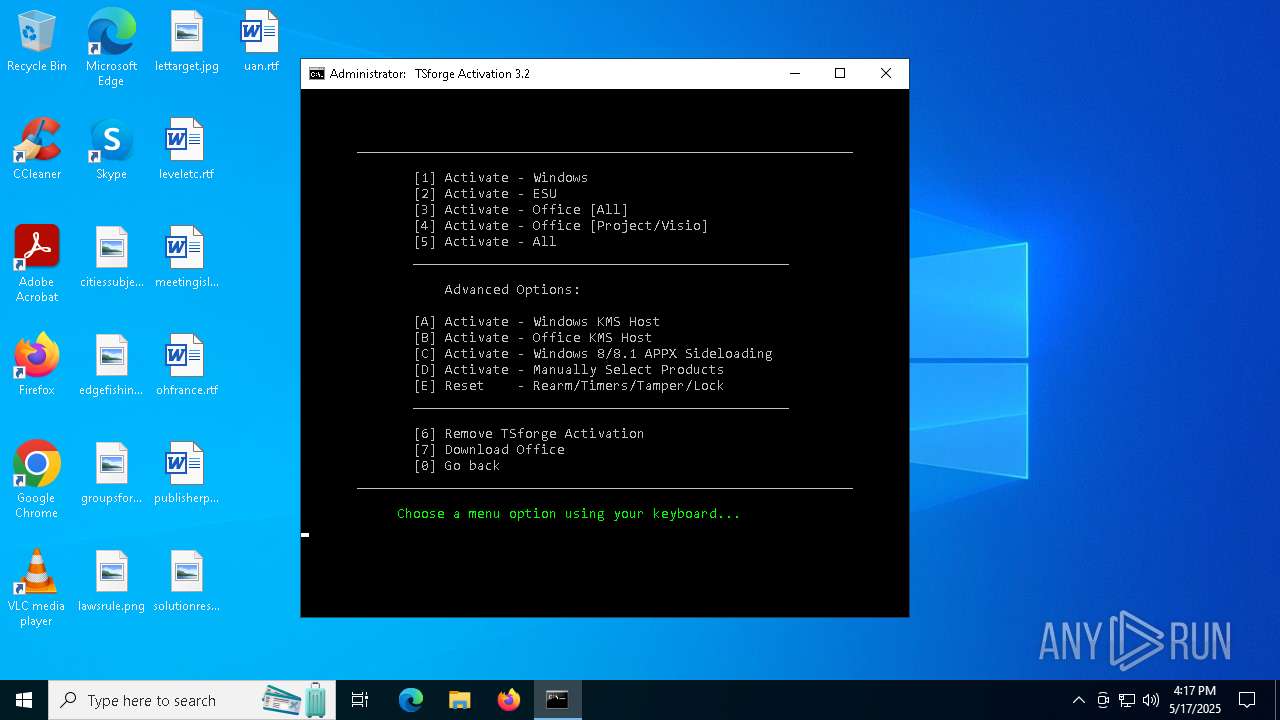
| Verdict: | Malicious activity |
| Analysis date: | May 17, 2025, 16:15:10 |
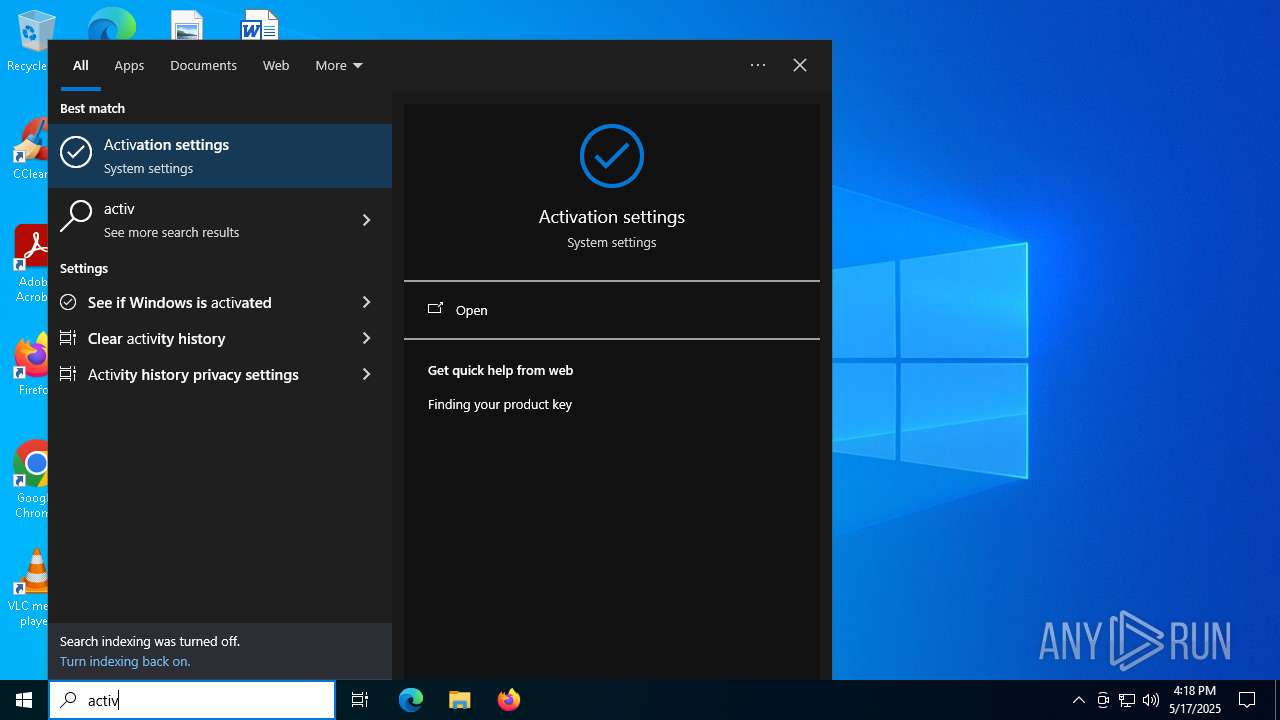
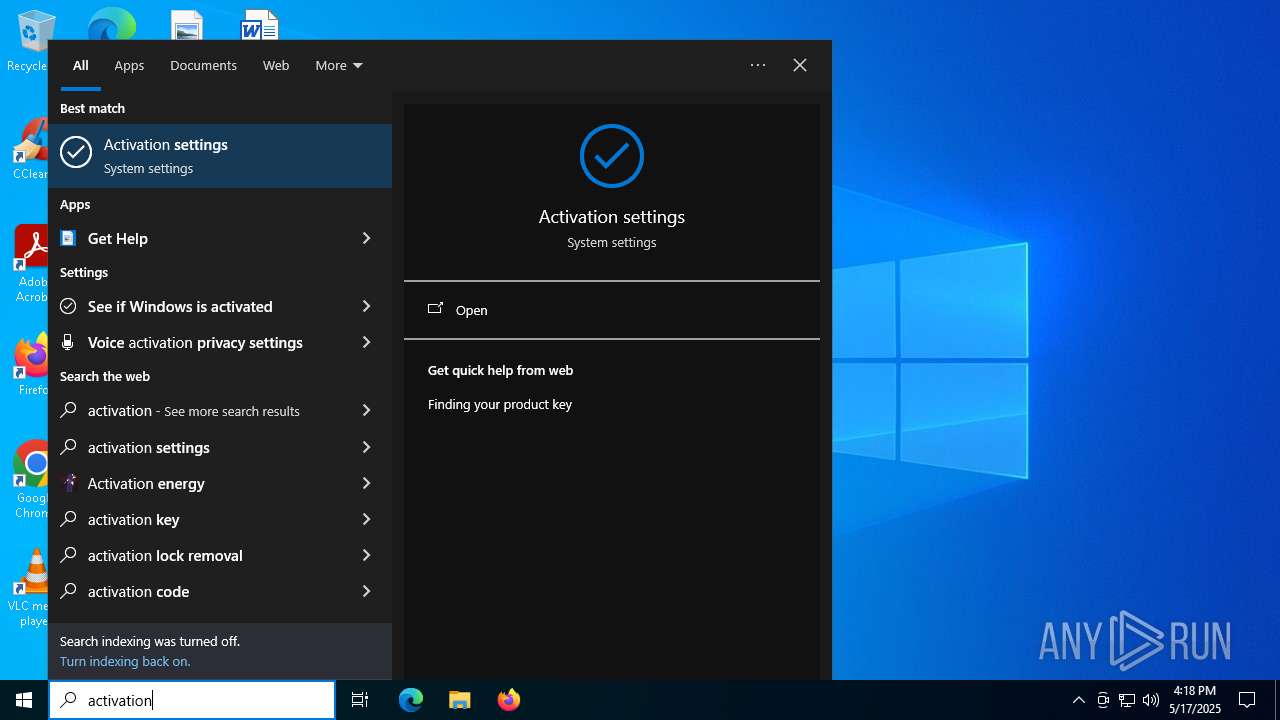
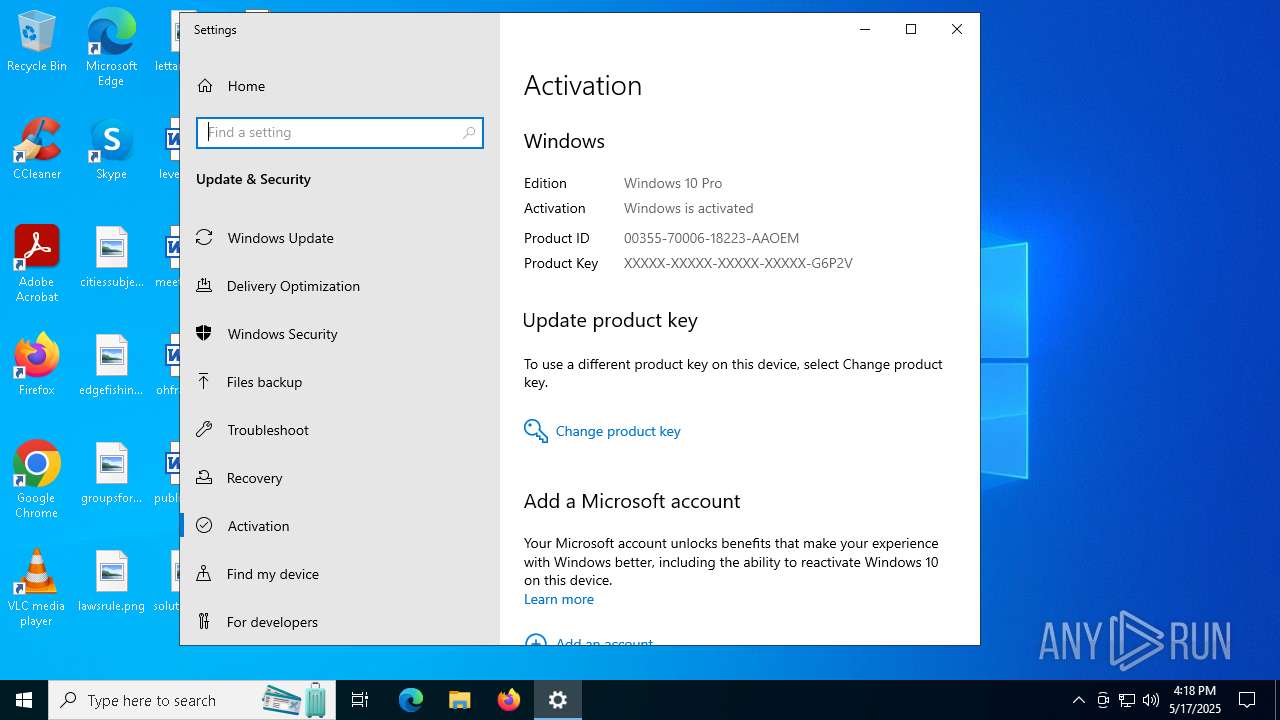
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | F5983A0BE71FD9F50D580073EB3FC0AC |
| SHA1: | B88FF2C8C0F282D52CAFCCD74EF0FEC2008B1750 |
| SHA256: | ACA804D7D38727F16EEBF05571D8D8DA3D6F89E5B5E0C8CDEE4C610E92DA23B2 |
| SSDEEP: | 3:kKwGT:kPK |
MALICIOUS
No malicious indicators.SUSPICIOUS
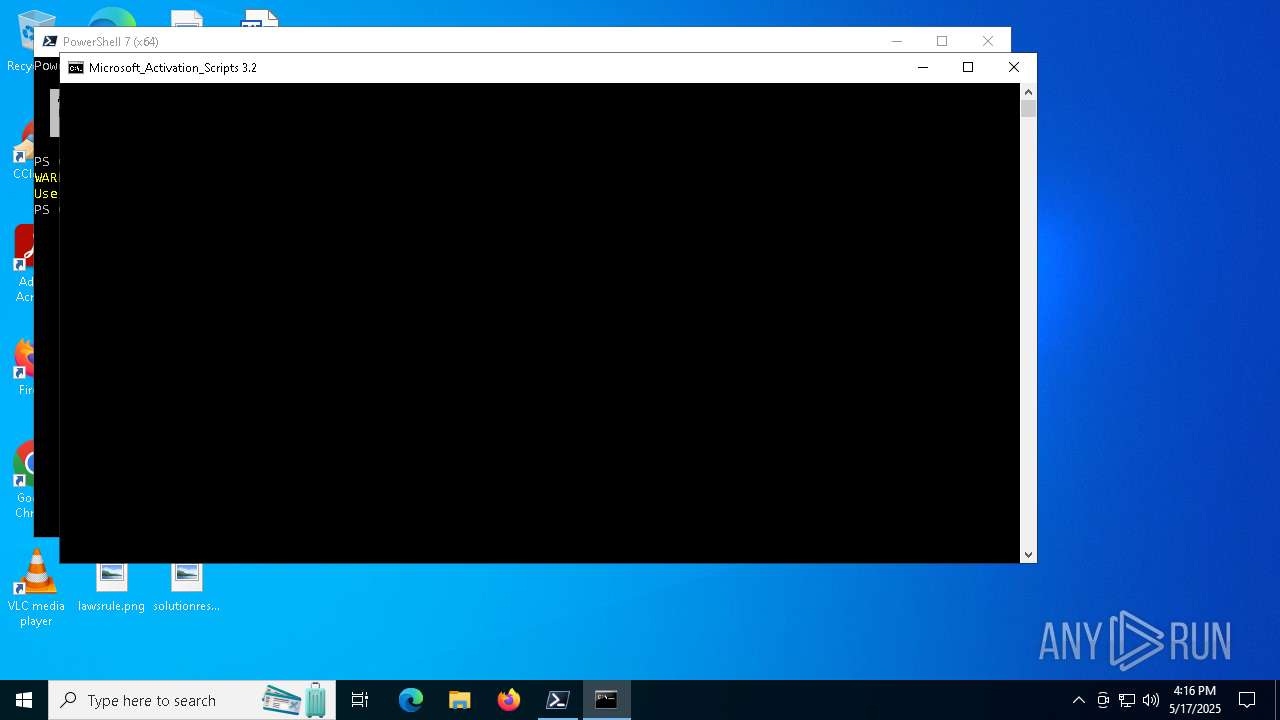
Reads the date of Windows installation
- pwsh.exe (PID: 7884)
Executing commands from ".cmd" file
- pwsh.exe (PID: 7884)
- cmd.exe (PID: 5072)
- powershell.exe (PID: 7596)
- cmd.exe (PID: 6576)
- cmd.exe (PID: 5936)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 5072)
- cmd.exe (PID: 6576)
- cmd.exe (PID: 5936)
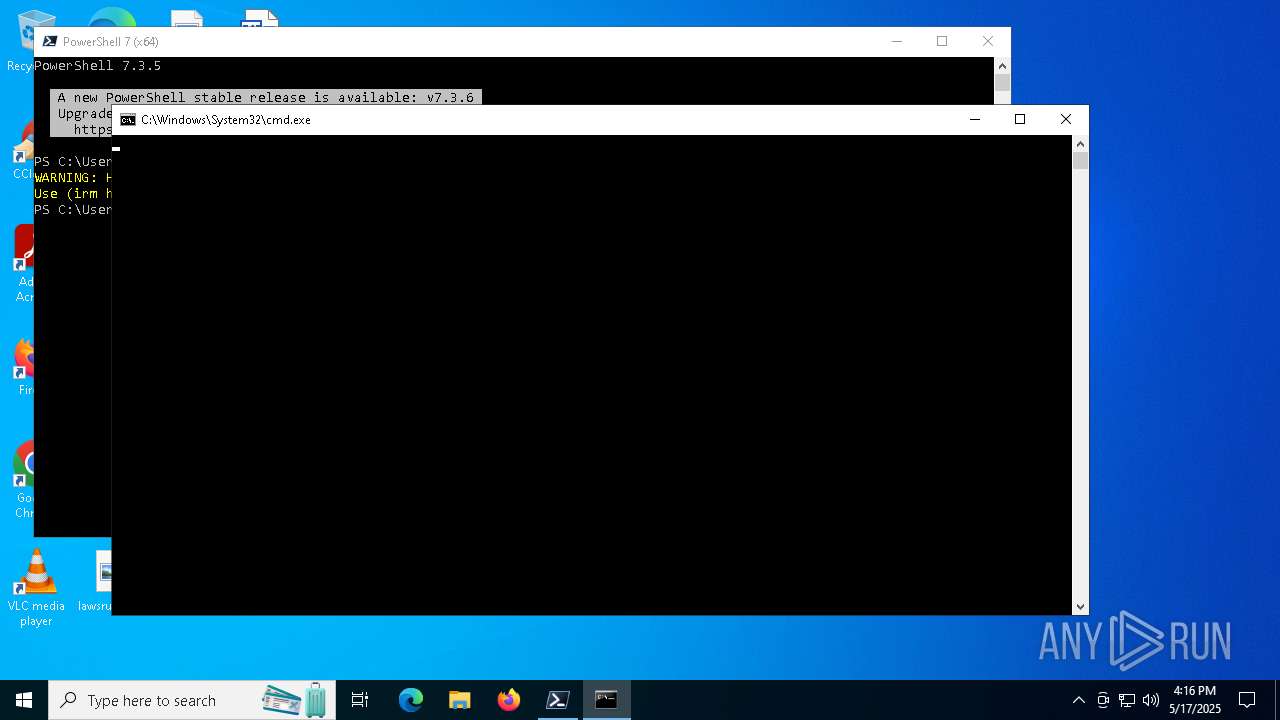
Starts CMD.EXE for commands execution
- cmd.exe (PID: 8012)
- cmd.exe (PID: 5072)
- pwsh.exe (PID: 7884)
- powershell.exe (PID: 7596)
- cmd.exe (PID: 6576)
- cmd.exe (PID: 6824)
- cmd.exe (PID: 5936)
- cmd.exe (PID: 6032)
Starts SC.EXE for service management
- cmd.exe (PID: 5072)
- cmd.exe (PID: 6576)
- cmd.exe (PID: 5936)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 5072)
- cmd.exe (PID: 7392)
- cmd.exe (PID: 3124)
- cmd.exe (PID: 5936)
- cmd.exe (PID: 7996)
- cmd.exe (PID: 7212)
- cmd.exe (PID: 6660)
- powershell.exe (PID: 4436)
- cmd.exe (PID: 7356)
- cmd.exe (PID: 5544)
- cmd.exe (PID: 2600)
- powershell.exe (PID: 8112)
Application launched itself
- cmd.exe (PID: 5072)
- cmd.exe (PID: 8012)
- cmd.exe (PID: 6576)
- cmd.exe (PID: 6824)
- cmd.exe (PID: 5936)
- cmd.exe (PID: 6032)
- powershell.exe (PID: 4436)
- powershell.exe (PID: 8112)
Windows service management via SC.EXE
- sc.exe (PID: 7196)
- sc.exe (PID: 7868)
- sc.exe (PID: 6940)
- sc.exe (PID: 7412)
- sc.exe (PID: 8164)
- sc.exe (PID: 6372)
- sc.exe (PID: 6192)
- sc.exe (PID: 4120)
- sc.exe (PID: 7240)
- sc.exe (PID: 7852)
- sc.exe (PID: 7792)
- sc.exe (PID: 5984)
- sc.exe (PID: 7184)
- sc.exe (PID: 5756)
- sc.exe (PID: 3008)
- sc.exe (PID: 8176)
- sc.exe (PID: 7964)
Executes script without checking the security policy
- powershell.exe (PID: 7596)
- powershell.exe (PID: 7316)
- powershell.exe (PID: 6960)
- powershell.exe (PID: 1388)
- powershell.exe (PID: 6028)
- powershell.exe (PID: 6728)
- powershell.exe (PID: 6940)
- powershell.exe (PID: 5228)
- powershell.exe (PID: 4436)
- powershell.exe (PID: 6576)
- powershell.exe (PID: 7376)
- powershell.exe (PID: 7940)
- powershell.exe (PID: 4736)
- powershell.exe (PID: 5256)
- powershell.exe (PID: 3796)
- powershell.exe (PID: 5400)
- powershell.exe (PID: 8112)
- powershell.exe (PID: 2236)
- powershell.exe (PID: 6208)
- powershell.exe (PID: 2288)
Hides command output
- cmd.exe (PID: 7392)
- cmd.exe (PID: 3124)
- cmd.exe (PID: 7996)
- cmd.exe (PID: 7504)
- cmd.exe (PID: 4172)
- cmd.exe (PID: 1600)
- cmd.exe (PID: 7992)
- cmd.exe (PID: 4740)
- cmd.exe (PID: 1568)
- cmd.exe (PID: 2600)
- cmd.exe (PID: 7356)
- cmd.exe (PID: 4920)
- cmd.exe (PID: 5544)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 7392)
- cmd.exe (PID: 3124)
- cmd.exe (PID: 5936)
- cmd.exe (PID: 6660)
- cmd.exe (PID: 7356)
- cmd.exe (PID: 5544)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 5072)
- cmd.exe (PID: 7392)
- cmd.exe (PID: 3124)
- cmd.exe (PID: 7996)
- cmd.exe (PID: 7212)
- cmd.exe (PID: 5936)
- cmd.exe (PID: 6660)
- powershell.exe (PID: 4436)
- cmd.exe (PID: 7356)
- cmd.exe (PID: 5544)
- cmd.exe (PID: 2600)
- powershell.exe (PID: 8112)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 7392)
- cmd.exe (PID: 3124)
- cmd.exe (PID: 5936)
- cmd.exe (PID: 7356)
- cmd.exe (PID: 5544)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7316)
- powershell.exe (PID: 6960)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 6576)
- cmd.exe (PID: 5936)
Uses sleep to delay execution (POWERSHELL)
- powershell.exe (PID: 7316)
- powershell.exe (PID: 6960)
Gets content of a file (POWERSHELL)
- powershell.exe (PID: 7316)
- powershell.exe (PID: 6960)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 7732)
- cmd.exe (PID: 5936)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 4172)
Probably file/command deobfuscation
- cmd.exe (PID: 6660)
The process hides Powershell's copyright startup banner
- powershell.exe (PID: 4436)
- powershell.exe (PID: 8112)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 1600)
- cmd.exe (PID: 1568)
- cmd.exe (PID: 4920)
Uses WMIC.EXE to obtain service application data
- cmd.exe (PID: 5936)
Executable content was dropped or overwritten
- csc.exe (PID: 6620)
CSC.EXE is used to compile C# code
- csc.exe (PID: 6620)
INFO
Application launched itself
- firefox.exe (PID: 1912)
- firefox.exe (PID: 5576)
Checks operating system version
- cmd.exe (PID: 5072)
- cmd.exe (PID: 6576)
- cmd.exe (PID: 5936)
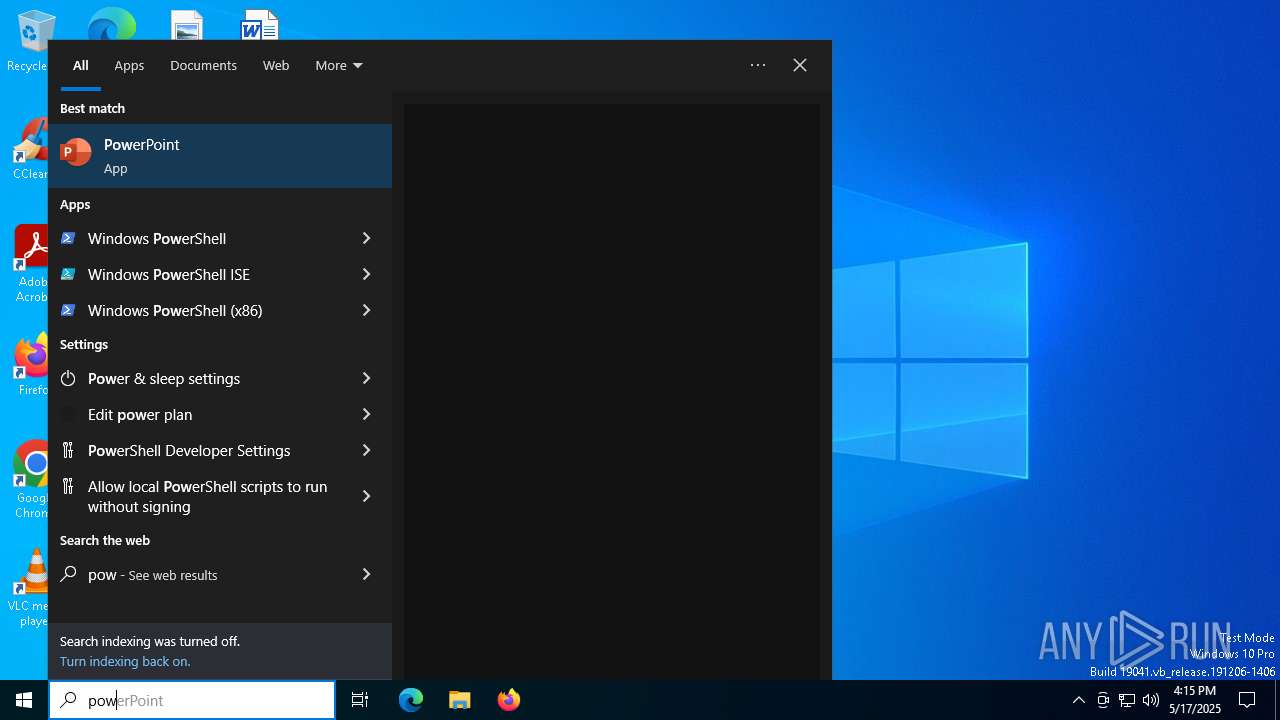
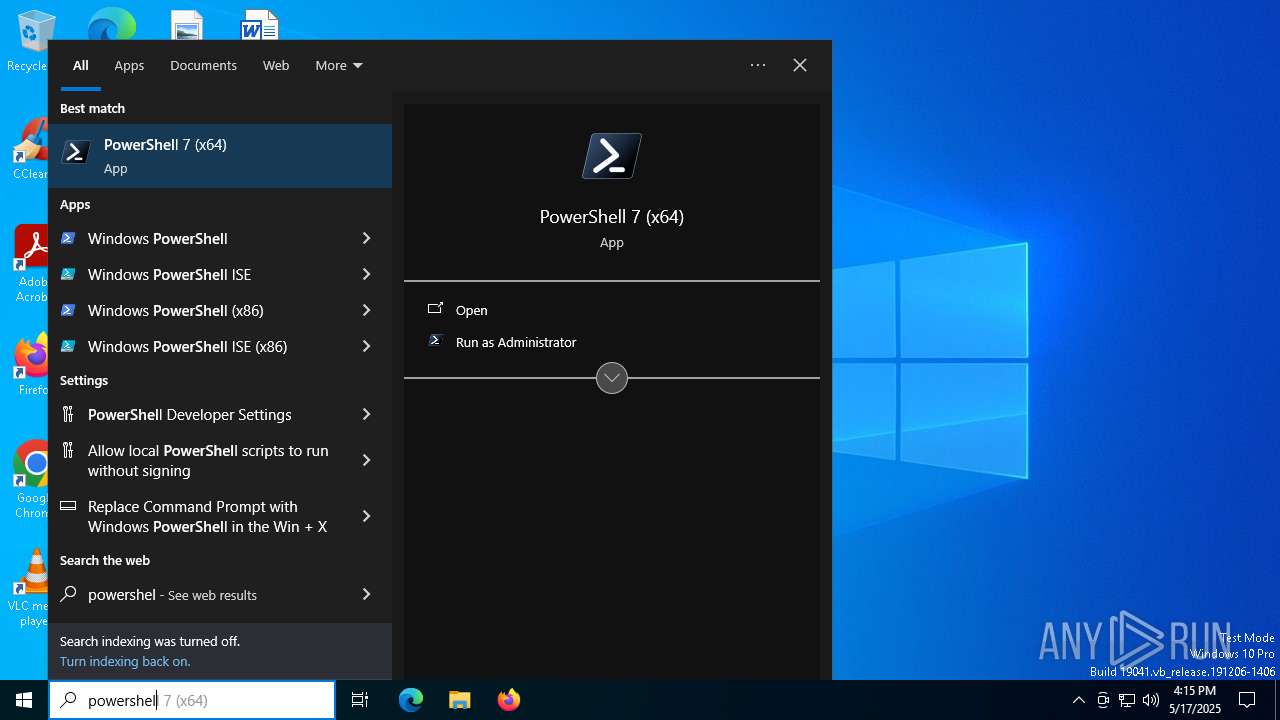
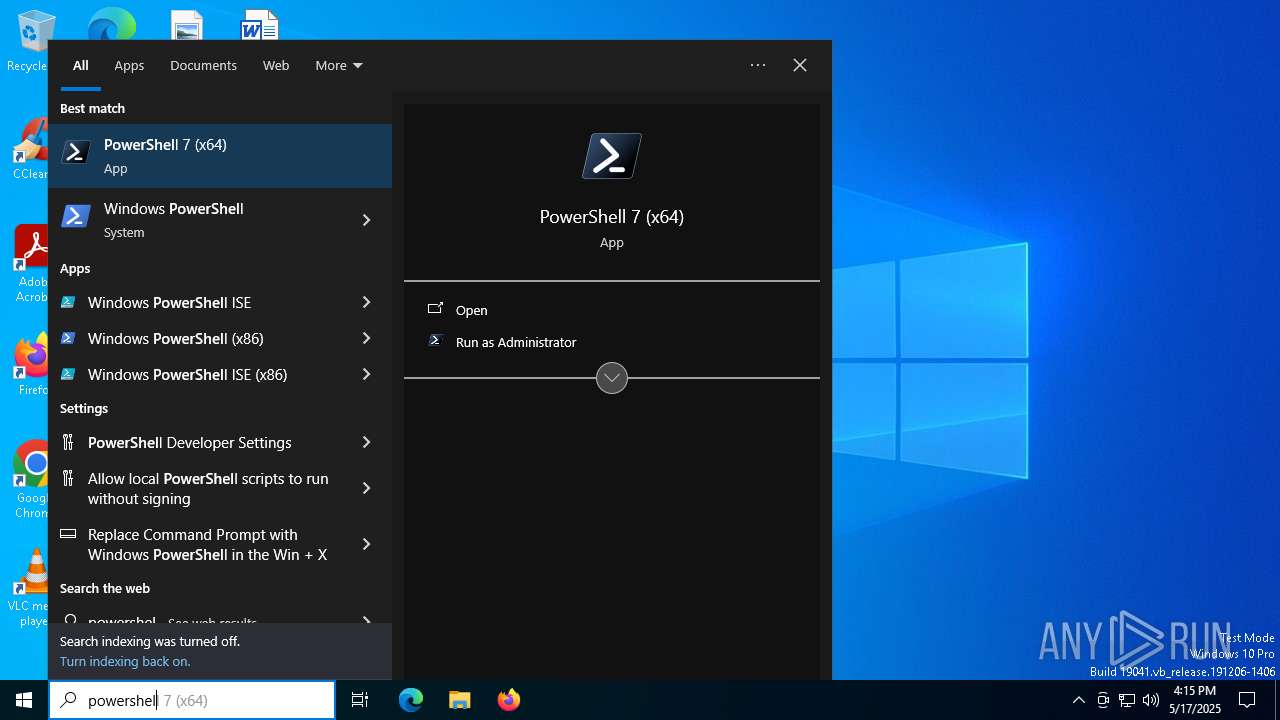
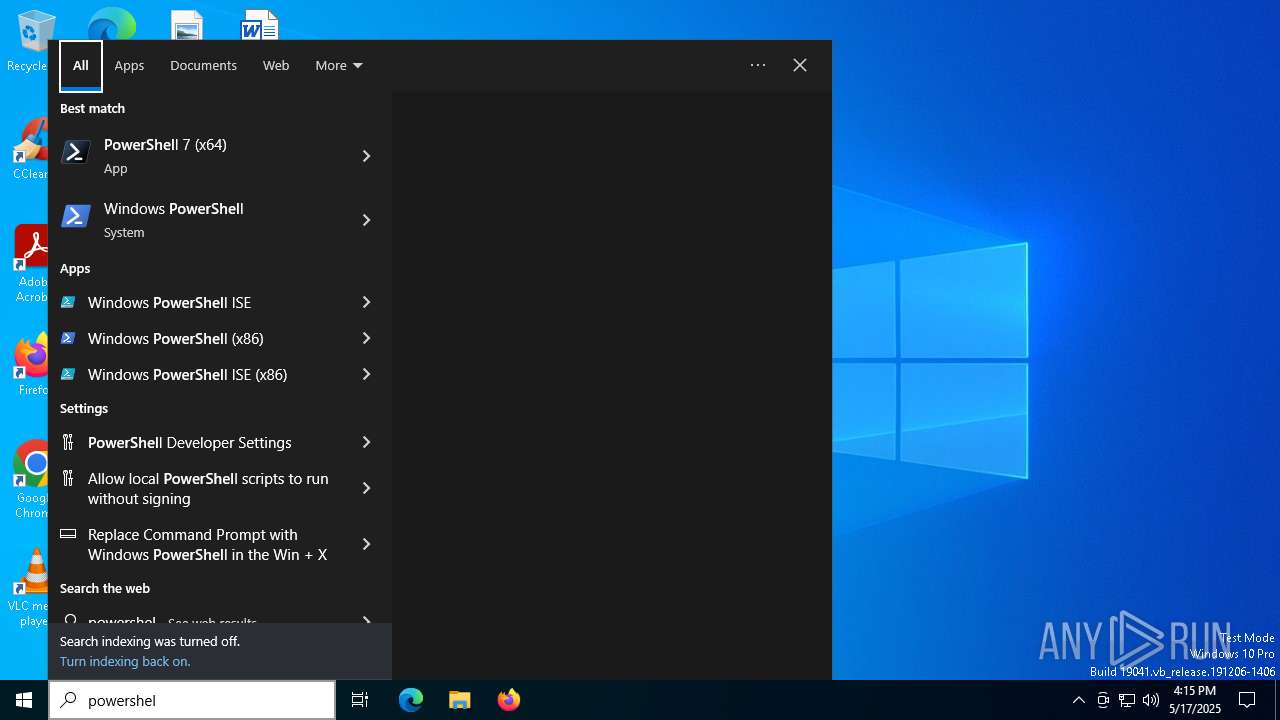
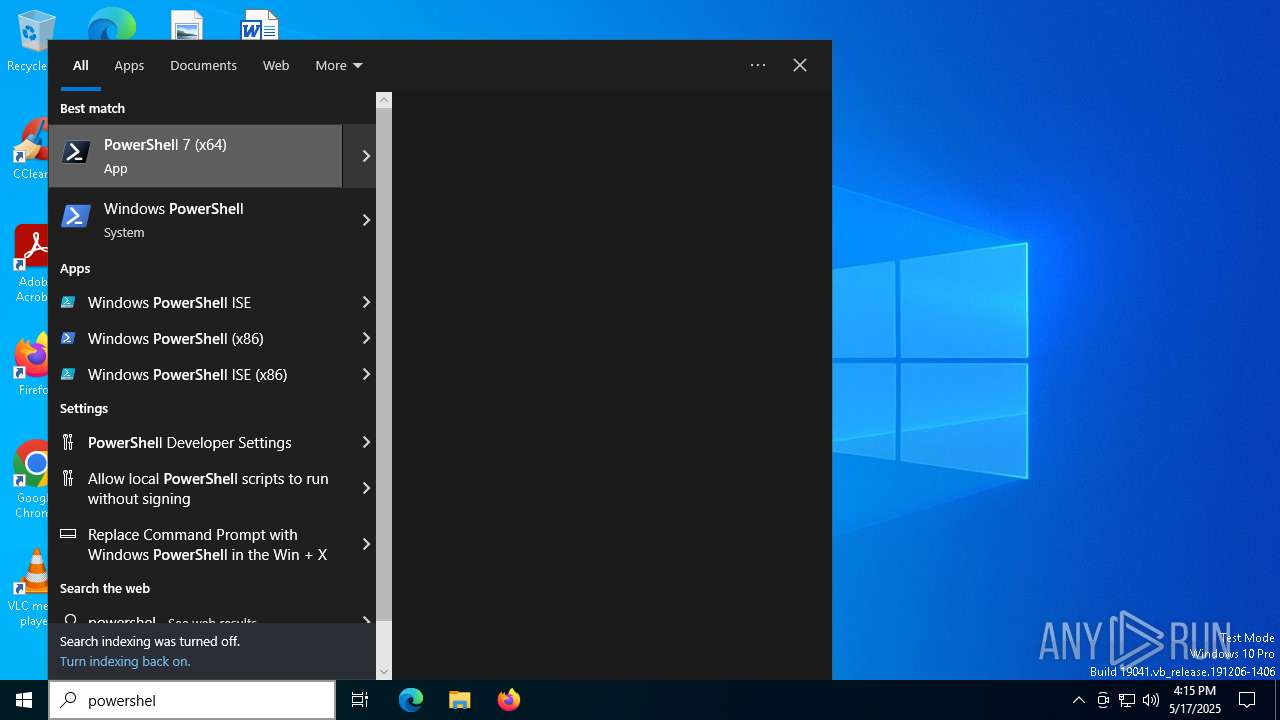
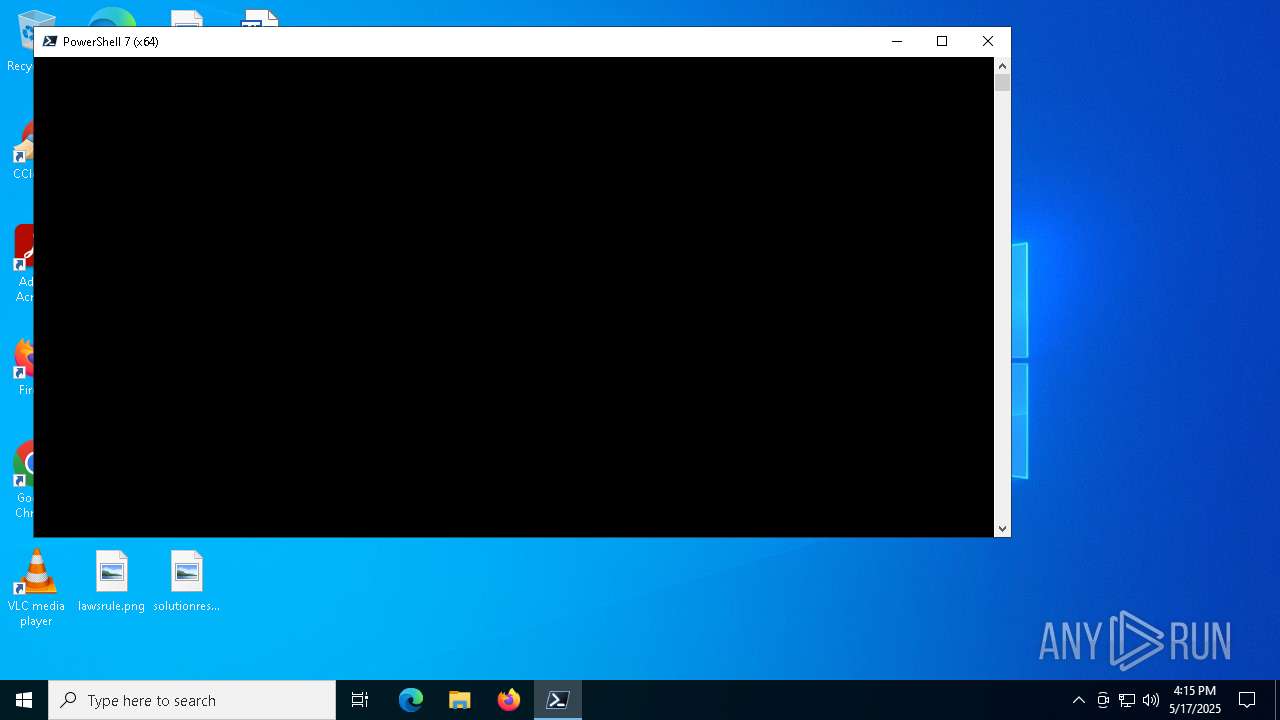
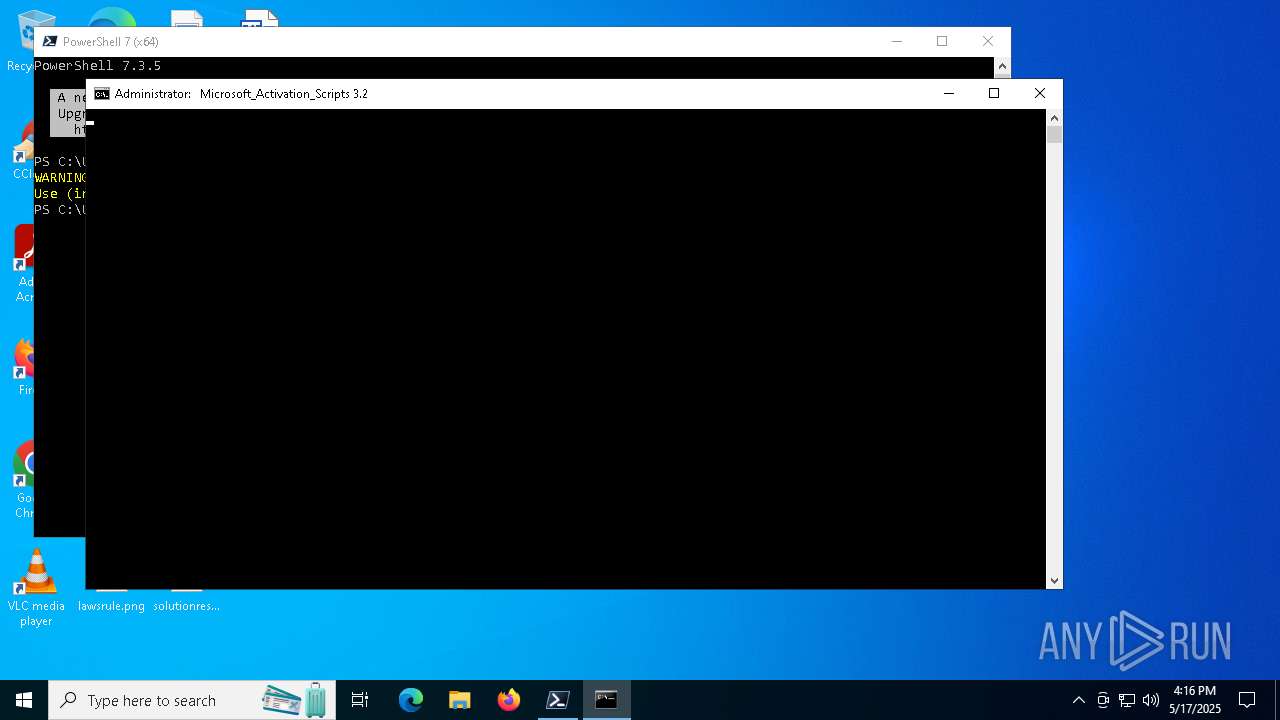
Manual execution by a user
- pwsh.exe (PID: 7884)
Checks supported languages
- pwsh.exe (PID: 7884)
- mode.com (PID: 8072)
- mode.com (PID: 5972)
- mode.com (PID: 7644)
- mode.com (PID: 1040)
- mode.com (PID: 7864)
Reads the computer name
- pwsh.exe (PID: 7884)
Process checks computer location settings
- pwsh.exe (PID: 7884)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 7316)
- powershell.exe (PID: 6960)
Starts MODE.COM to configure console settings
- mode.com (PID: 8072)
- mode.com (PID: 7644)
- mode.com (PID: 5972)
- mode.com (PID: 1040)
- mode.com (PID: 7864)
- mode.com (PID: 1348)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 7316)
- powershell.exe (PID: 6960)
Creates a byte array (POWERSHELL)
- powershell.exe (PID: 7316)
- powershell.exe (PID: 6960)
Reads the software policy settings
- slui.exe (PID: 7784)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
373
Monitored processes
237
Malicious processes
9
Suspicious processes
12
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | reg query "HKU\S-1-5-20\Software\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform\PersistedTSReArmed" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 536 | C:\WINDOWS\System32\cmd.exe /S /D /c" echo "Windows 10 Pro" " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 664 | C:\WINDOWS\System32\cmd.exe /c ping -n 1 updatecheck32.activated.win | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 728 | find /i " Professional " | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 960 | C:\WINDOWS\System32\cmd.exe /c ver | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1040 | mode 76, 33 | C:\Windows\System32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DOS Device MODE Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1072 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1088 | wmic path SoftwareLicensingProduct where (ApplicationID='55c92734-d682-4d71-983e-d6ec3f16059f' and PartialProductKey is not null) get ID /VALUE | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1096 | reg query HKLM\SYSTEM\CurrentControlSet\Services\Winmgmt /v ErrorControl | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1196 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
123 163
Read events
123 160
Write events
1
Delete events
2
Modification events
| (PID) Process: | (1912) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (7200) reg.exe | Key: | HKEY_USERS\S-1-5-20\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform\PersistedSystemState |
| Operation: | delete value | Name: | State |
Value: | |||
| (PID) Process: | (7520) reg.exe | Key: | HKEY_USERS\S-1-5-20\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform\PersistedSystemState |
| Operation: | delete value | Name: | SuppressRulesEngine |
Value: | |||
Executable files
1
Suspicious files
63
Text files
61
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1912 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 1912 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 1912 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 1912 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\datareporting\glean\db\data.safe.bin | binary | |
MD5:D30F5B10F3D4B3992E4D666F622163F4 | SHA256:2585819A7401A308DA879FA416278E473CEA5F6D0D24C59F514C5A698C61D03A | |||
| 1912 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 1912 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 1912 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 1912 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs.js | text | |
MD5:2C99A16AED3906D92FFE3EF1808E2753 | SHA256:08412578CC3BB4922388F8FF8C23962F616B69A1588DA720ADE429129C73C452 | |||
| 1912 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\datareporting\glean\db\data.safe.tmp | binary | |
MD5:D30F5B10F3D4B3992E4D666F622163F4 | SHA256:2585819A7401A308DA879FA416278E473CEA5F6D0D24C59F514C5A698C61D03A | |||
| 1912 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3561288849sdhlie.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
72
DNS requests
69
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.32:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1912 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
1912 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
1912 | firefox.exe | POST | 200 | 142.250.184.195:80 | http://o.pki.goog/s/wr3/FIY | unknown | — | — | whitelisted |
1912 | firefox.exe | POST | 200 | 184.24.77.65:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
1912 | firefox.exe | POST | 200 | 142.250.184.195:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
1912 | firefox.exe | POST | 200 | 184.24.77.65:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
1912 | firefox.exe | GET | 301 | 104.21.35.139:80 | http://vidcombo.com/ | unknown | — | — | unknown |
1912 | firefox.exe | POST | 200 | 184.24.77.54:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.32:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1912 | firefox.exe | 104.21.35.139:80 | vidcombo.com | CLOUDFLARENET | — | unknown |
1912 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
1912 | firefox.exe | 34.36.137.203:443 | contile.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
1912 | firefox.exe | 34.160.144.191:443 | content-signature-2.cdn.mozilla.net | GOOGLE | US | whitelisted |
1912 | firefox.exe | 184.24.77.65:80 | r11.o.lencr.org | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
vidcombo.com |
| unknown |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7884 | pwsh.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Front Door domain observed in TLS SNI ( .azurefd .net) |