| URL: | https://www.google.com |
| Full analysis: | https://app.any.run/tasks/88a45ae6-b81e-48fd-902a-485dffd7cee5 |
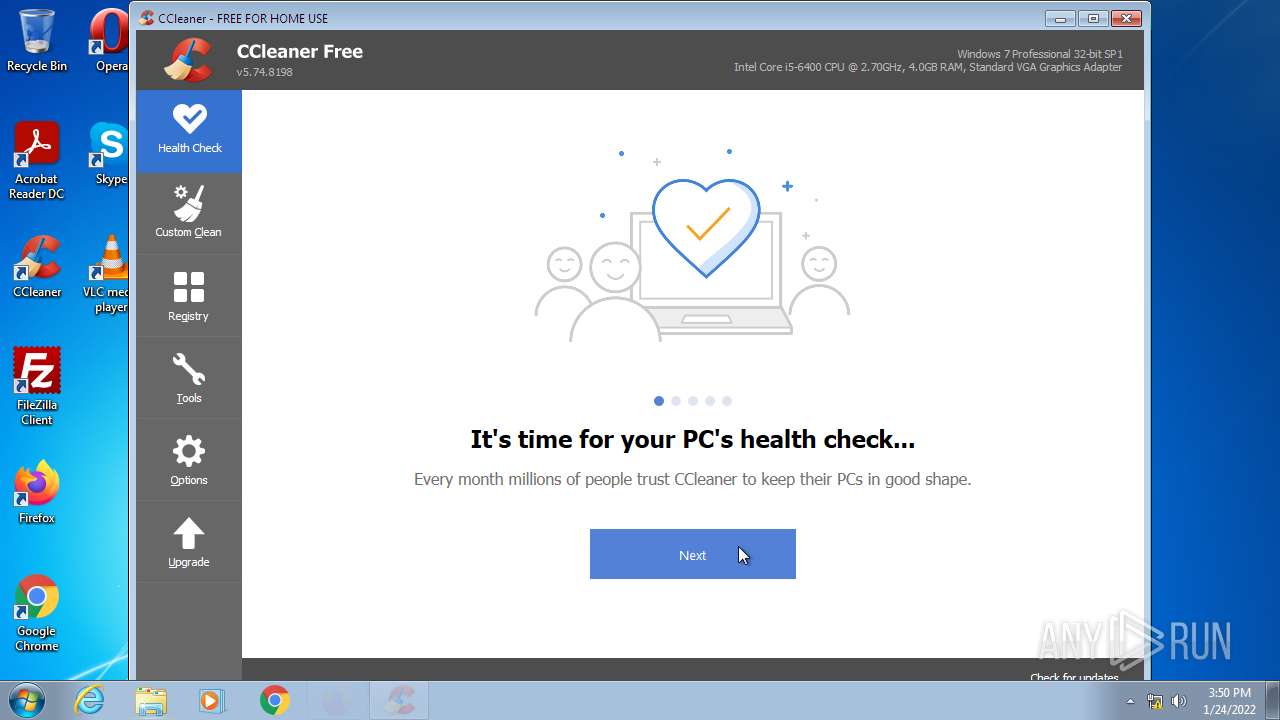
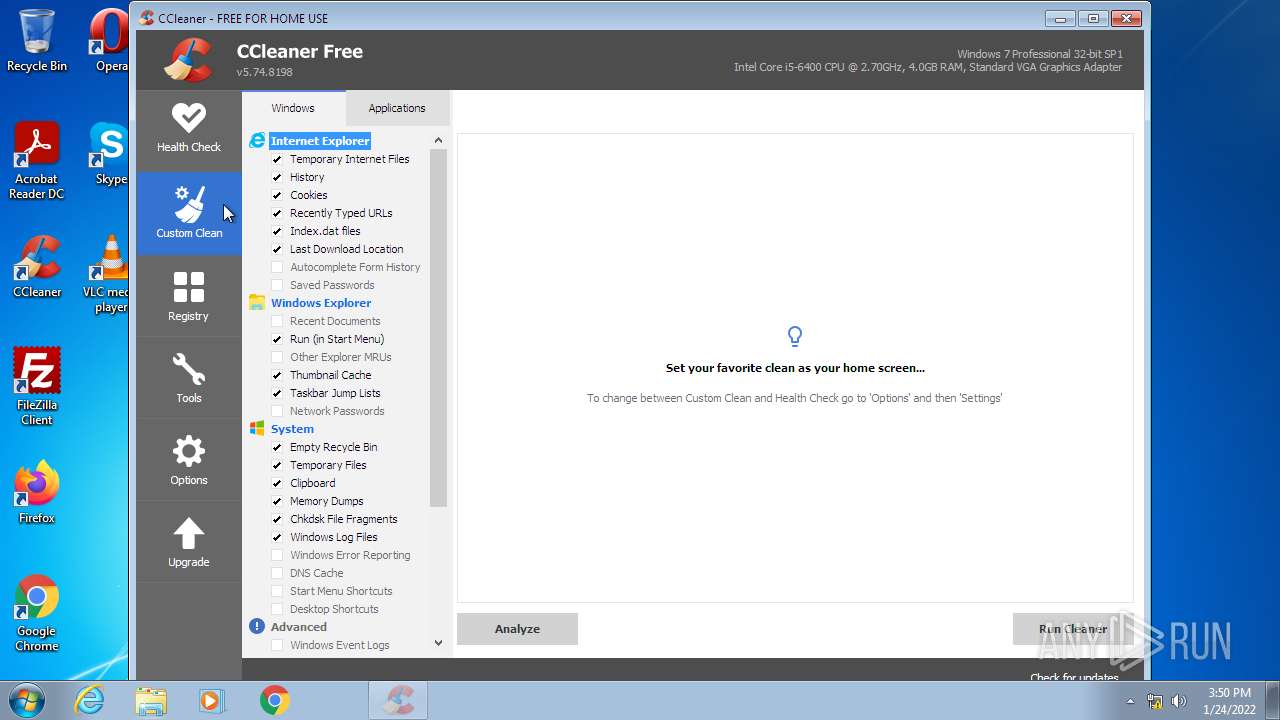
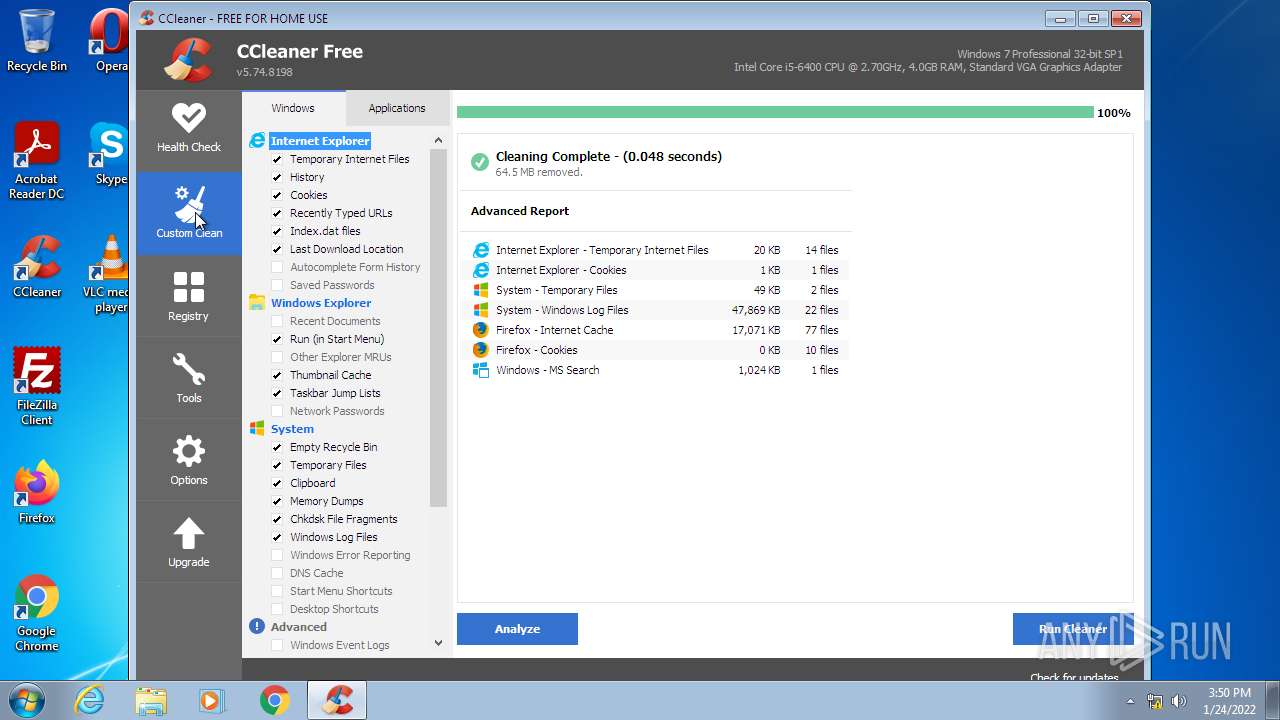
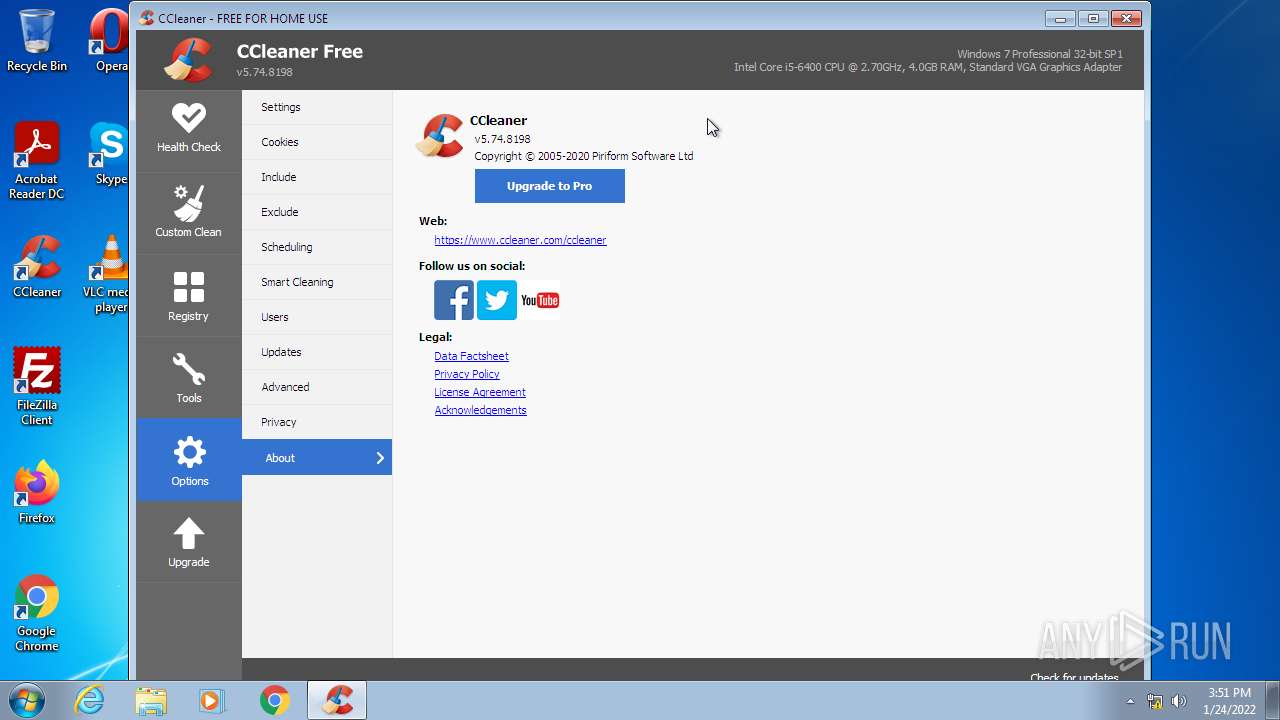
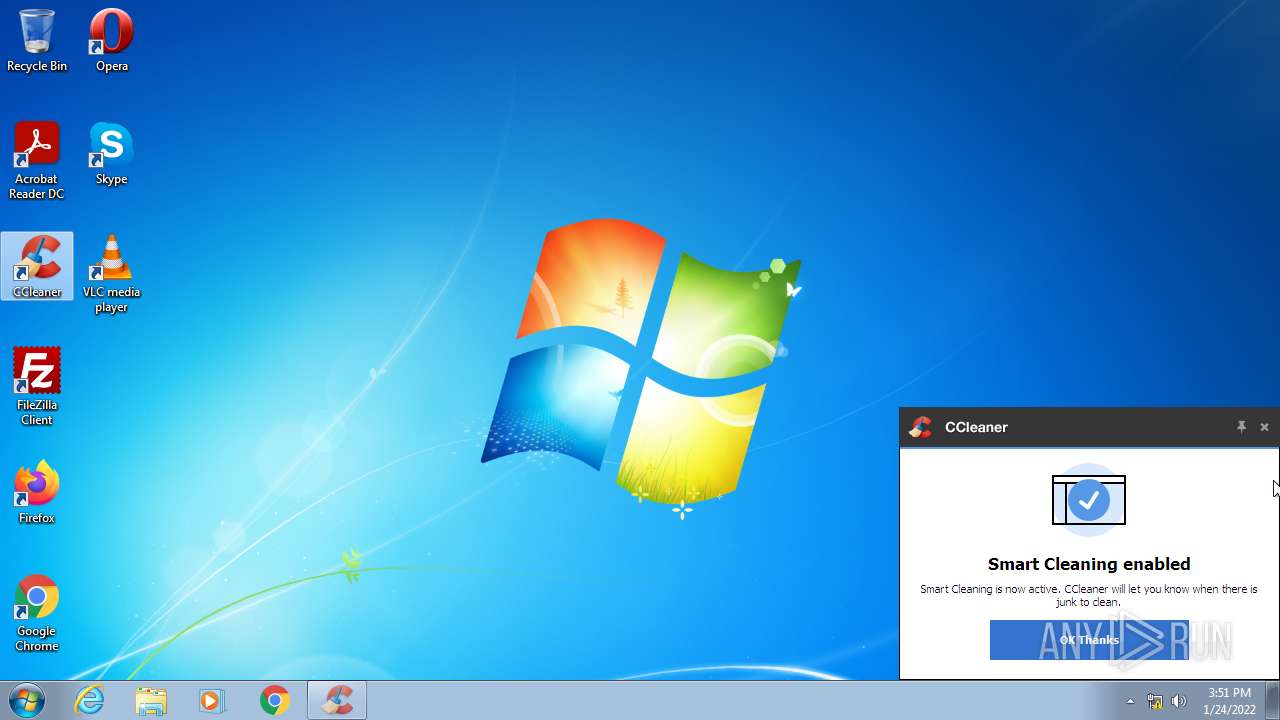
| Verdict: | Malicious activity |
| Analysis date: | January 24, 2022, 15:46:42 |
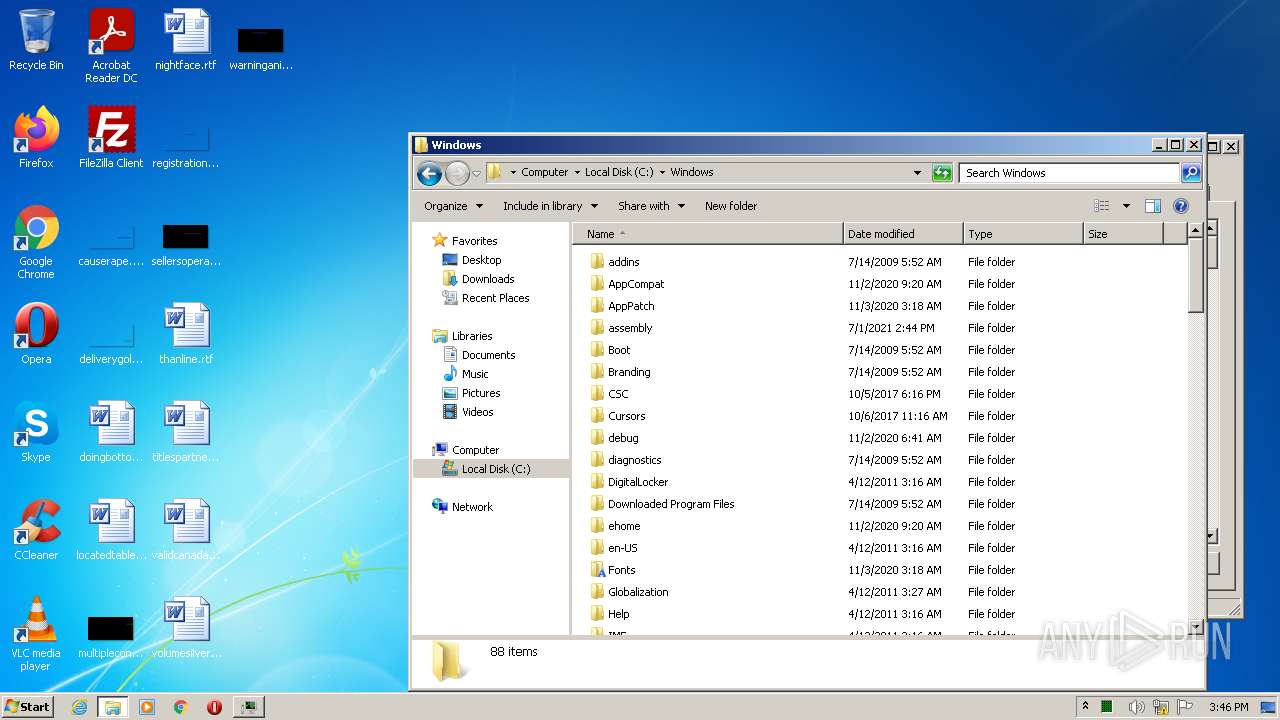
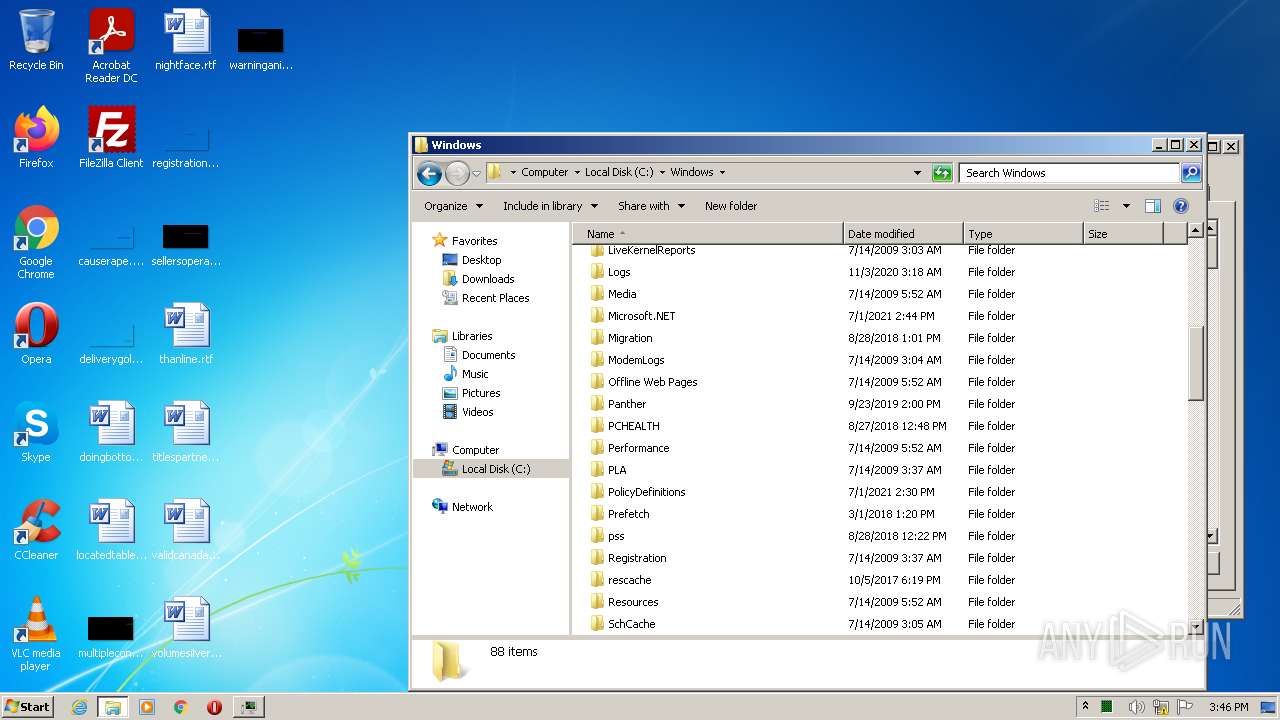
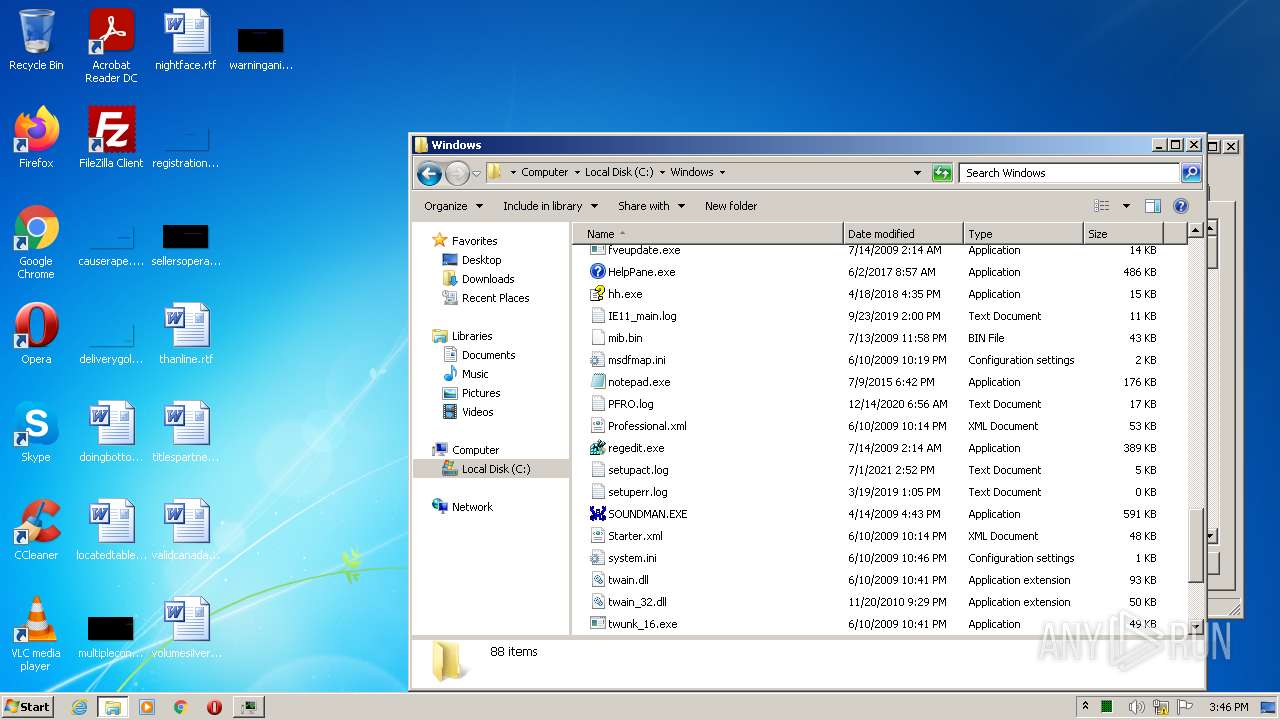
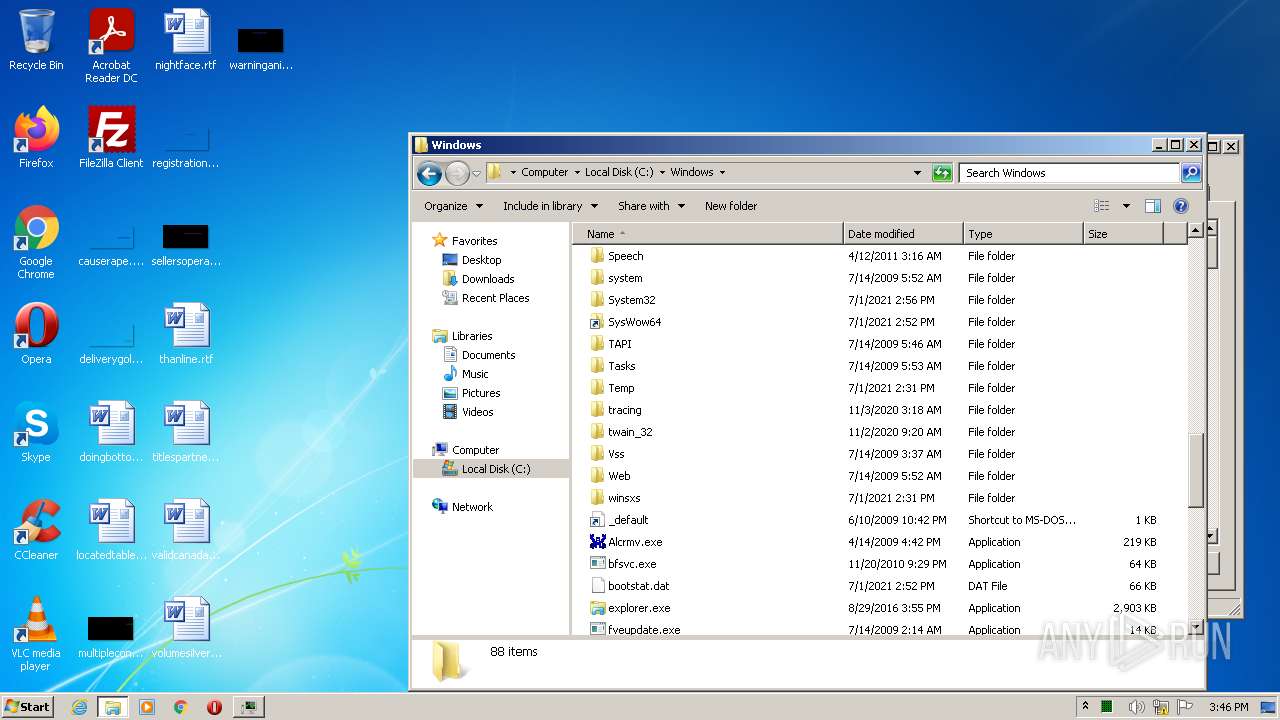
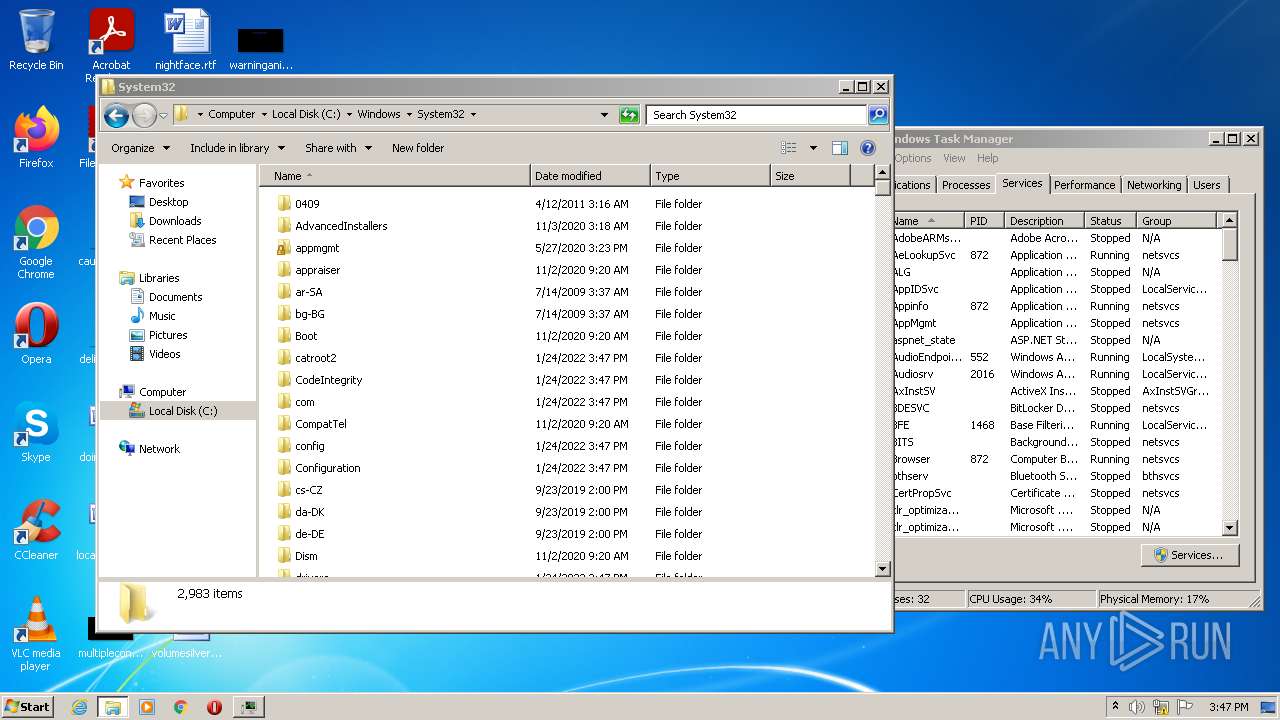
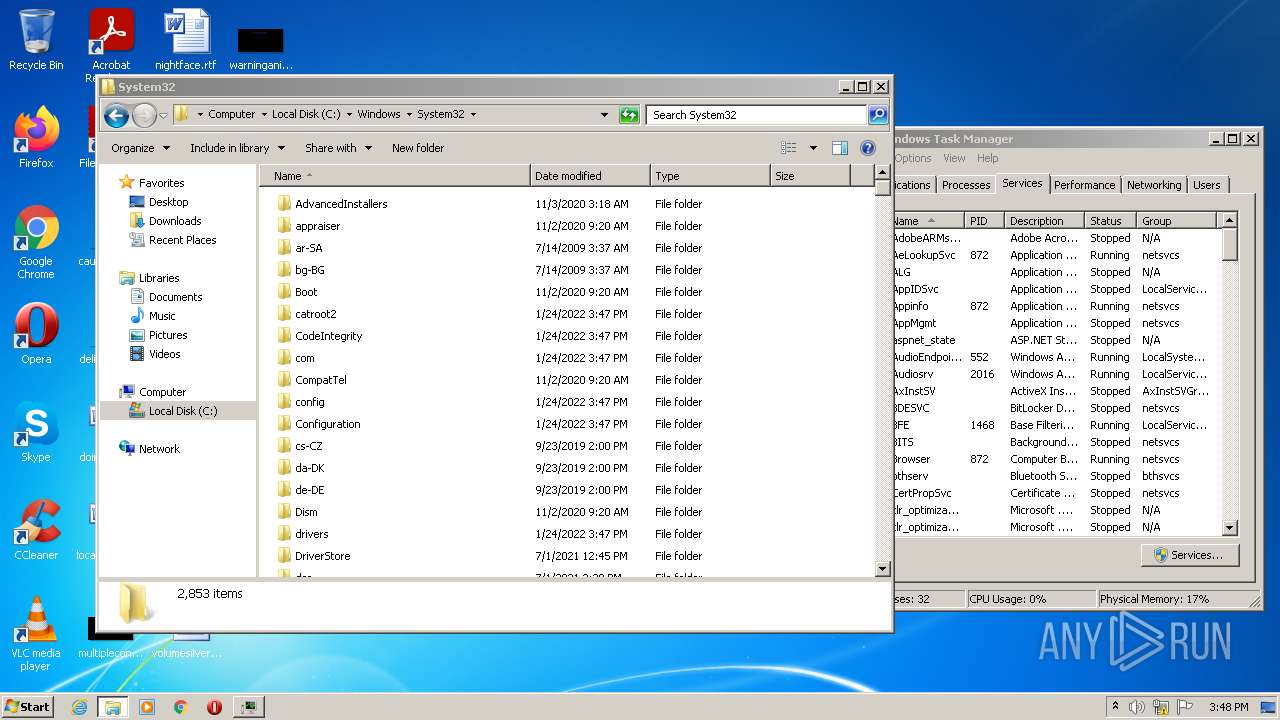
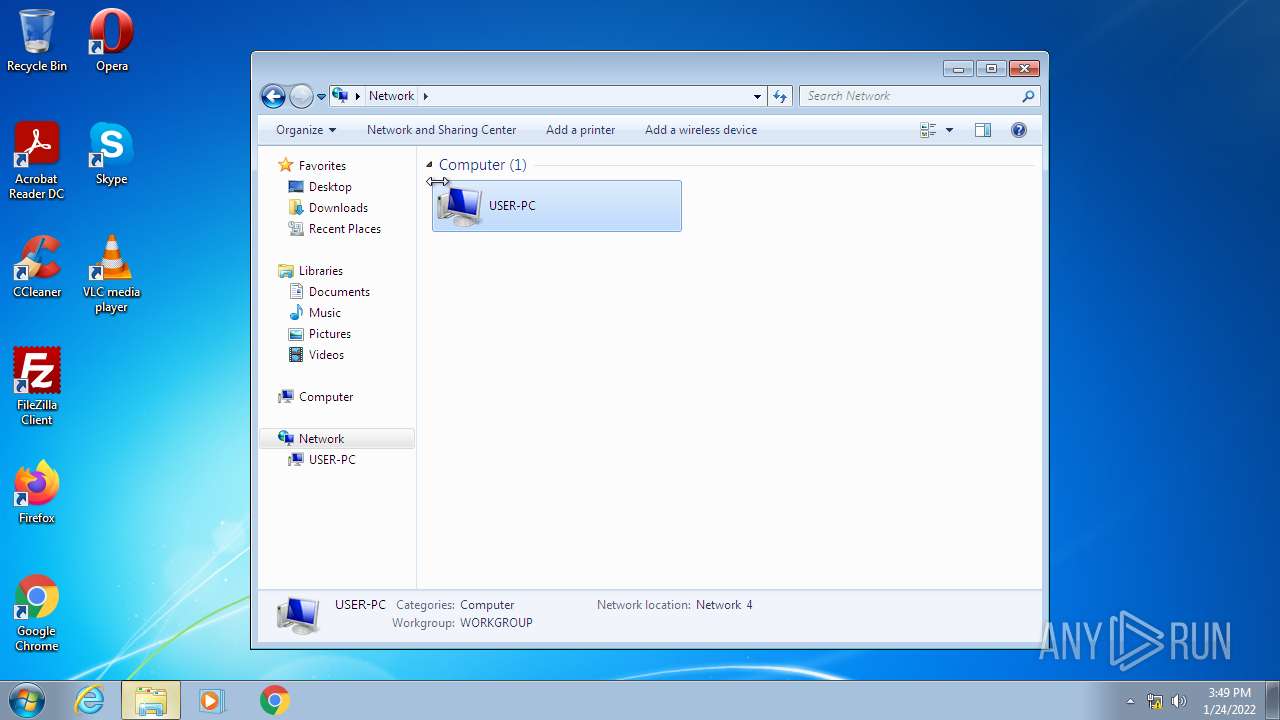
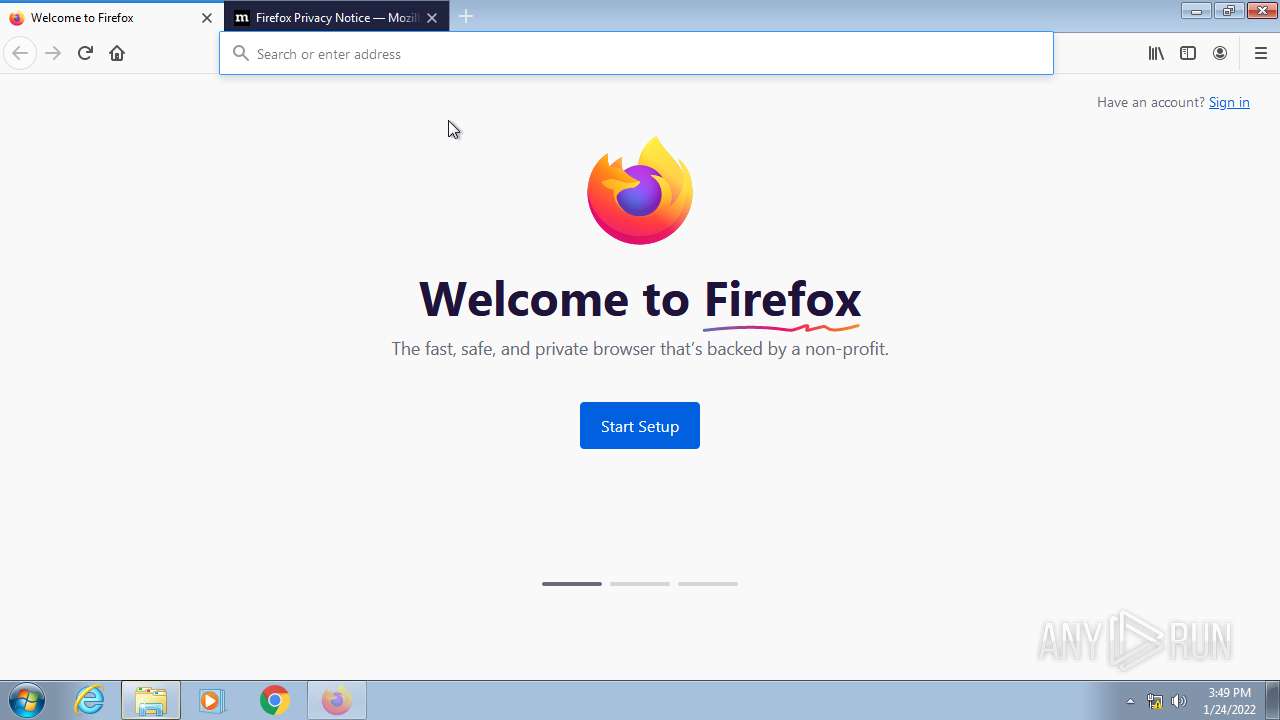
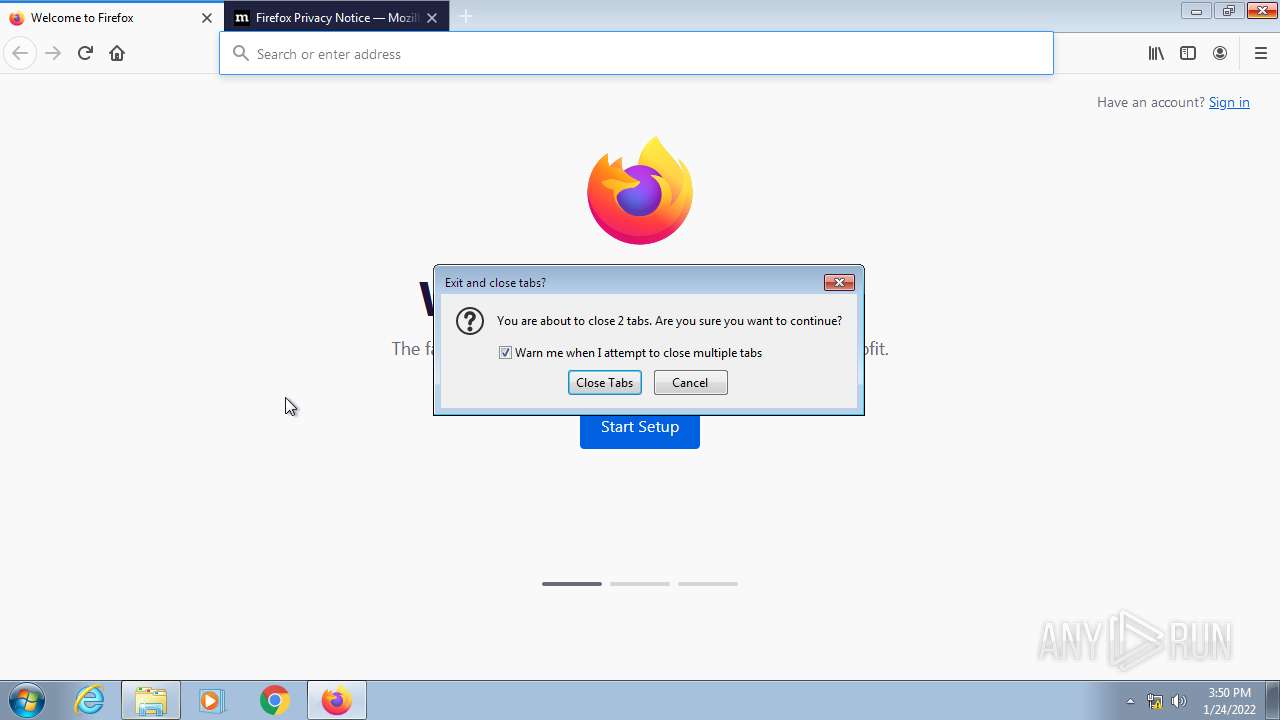
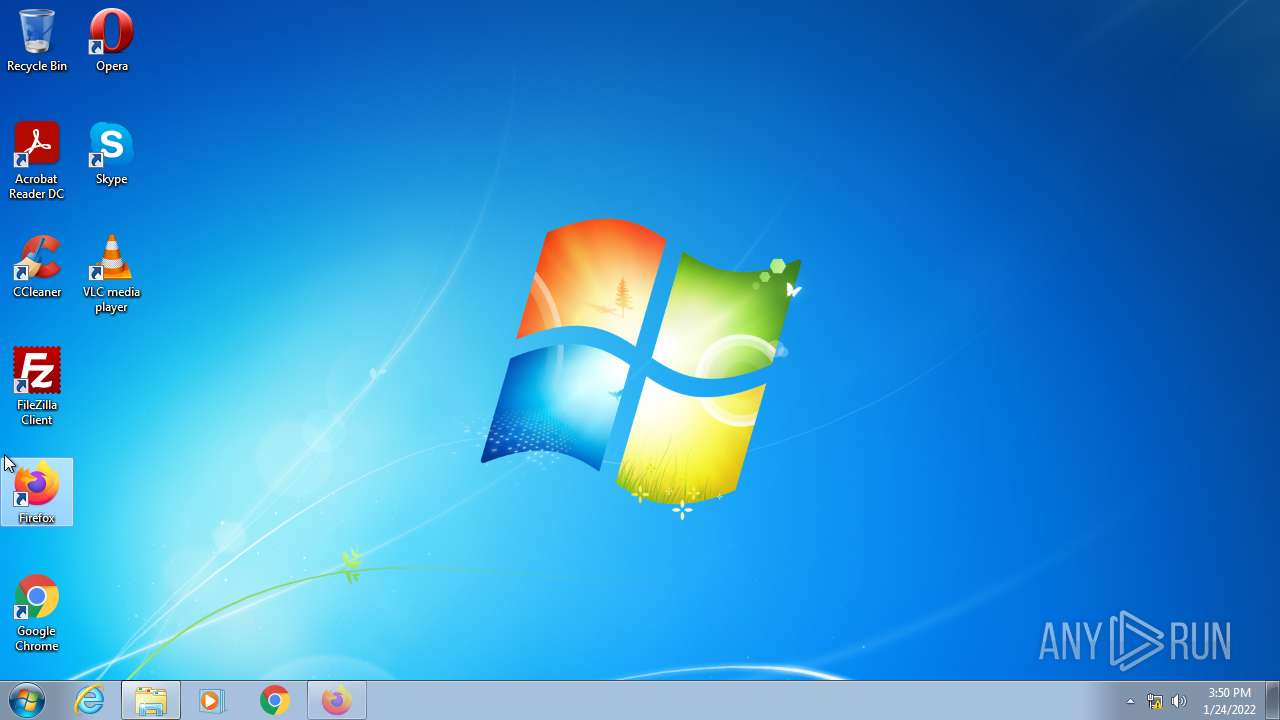
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 8FFDEFBDEC956B595D257F0AAEEFD623 |
| SHA1: | EF7EFC9839C3EE036F023E9635BC3B056D6EE2DB |
| SHA256: | AC6BB669E40E44A8D9F8F0C94DFC63734049DCF6219AAC77F02EDF94B9162C09 |
| SSDEEP: | 3:N8DSLIK:2OLIK |
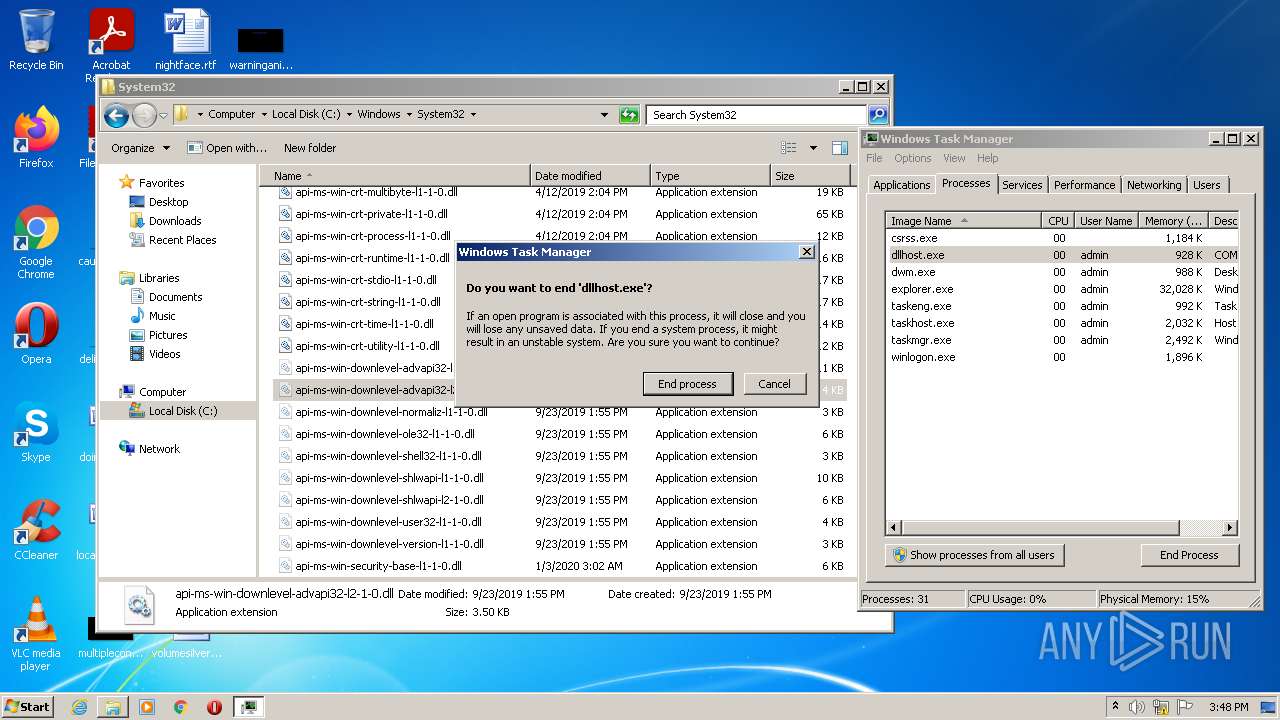
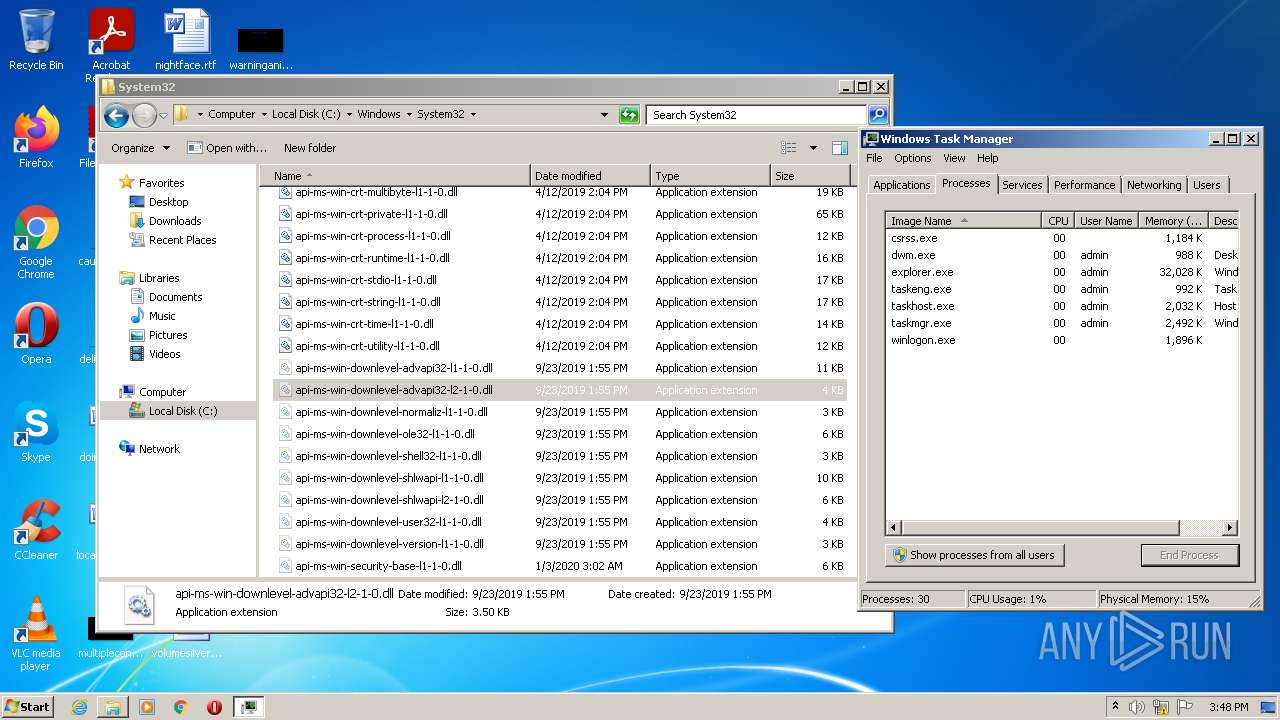
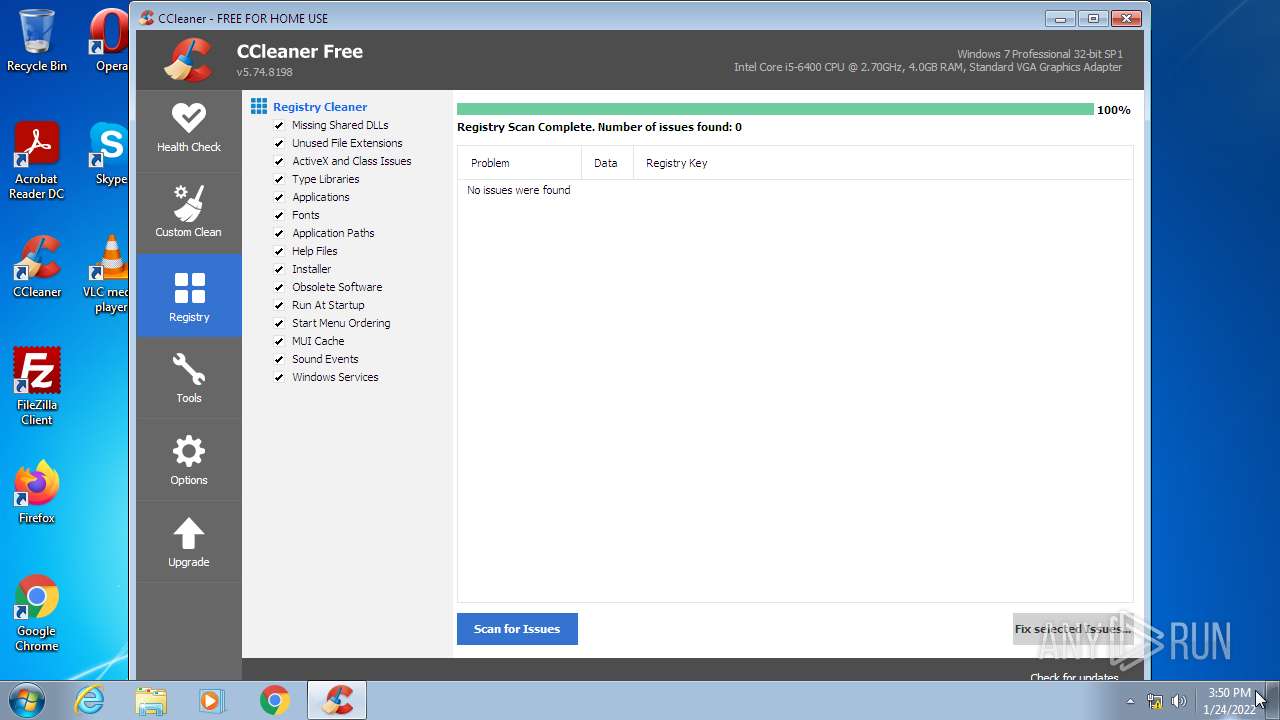
MALICIOUS
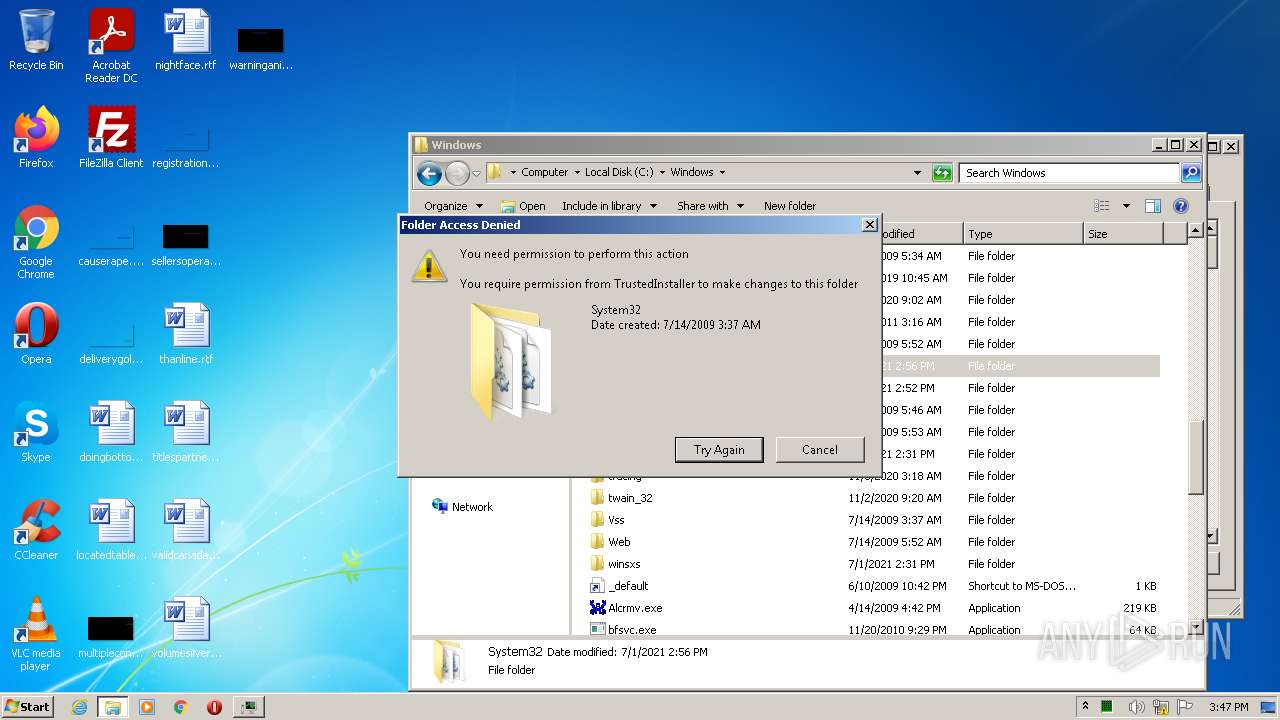
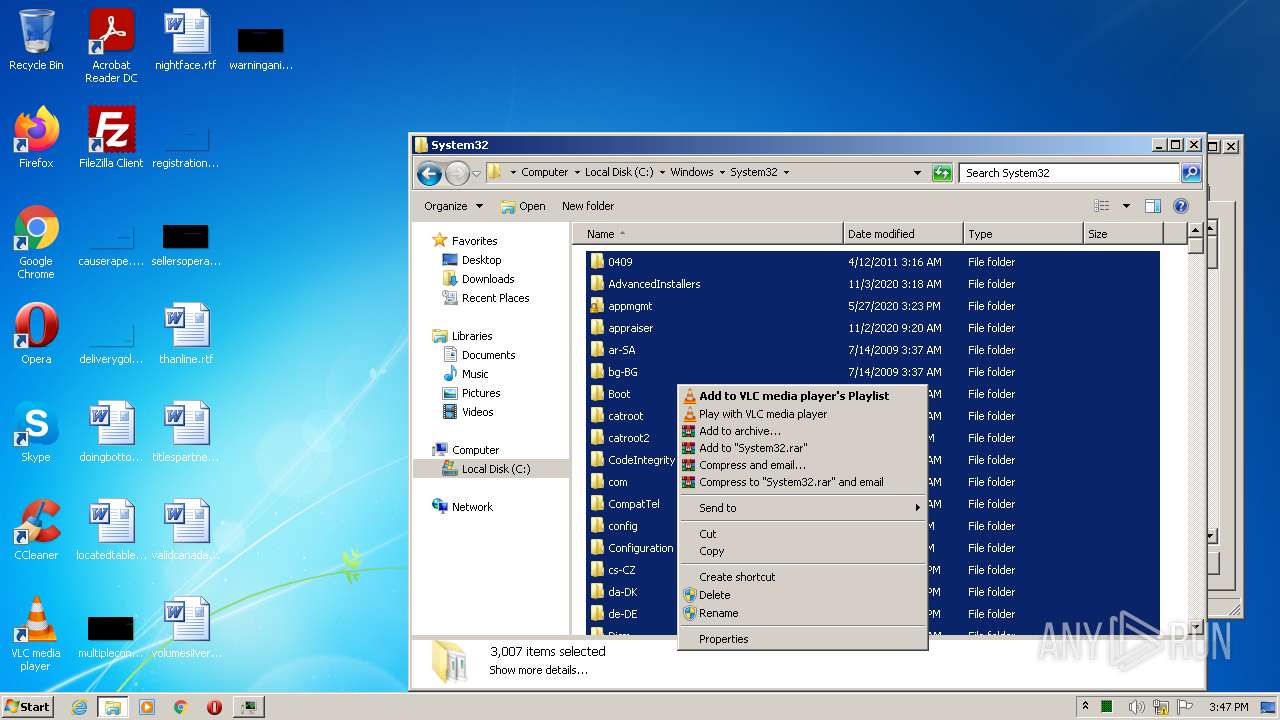
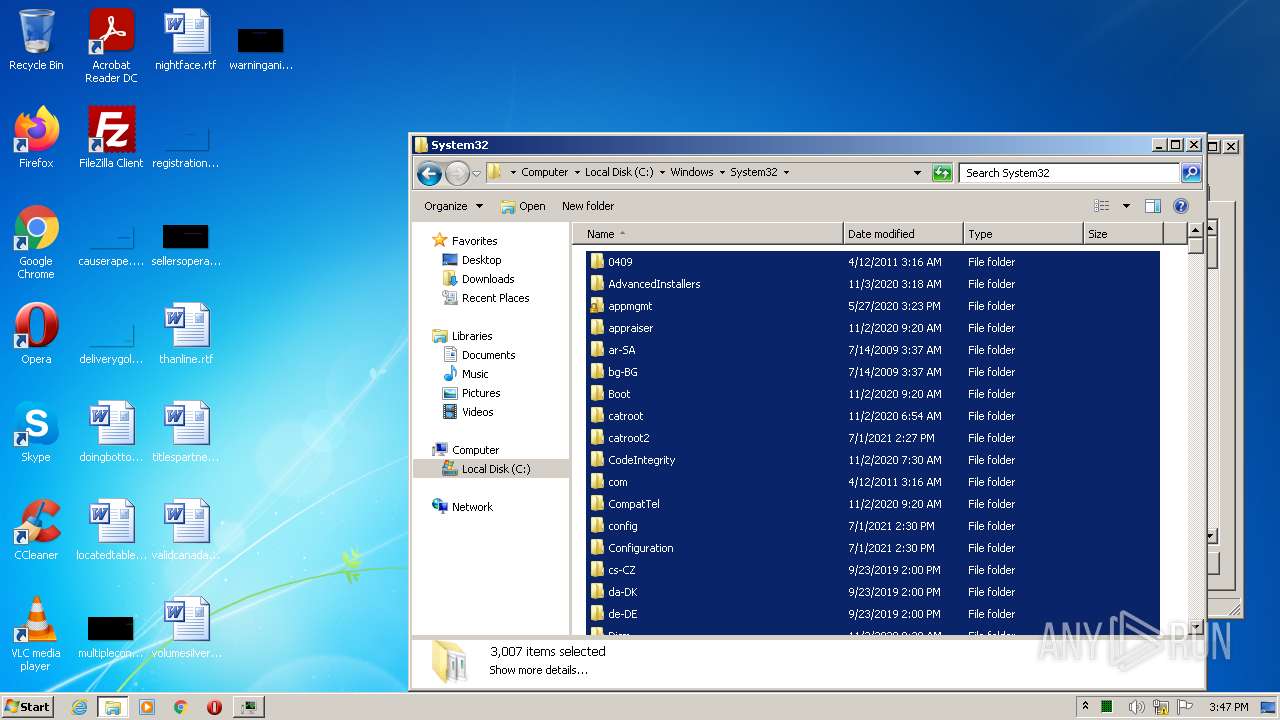
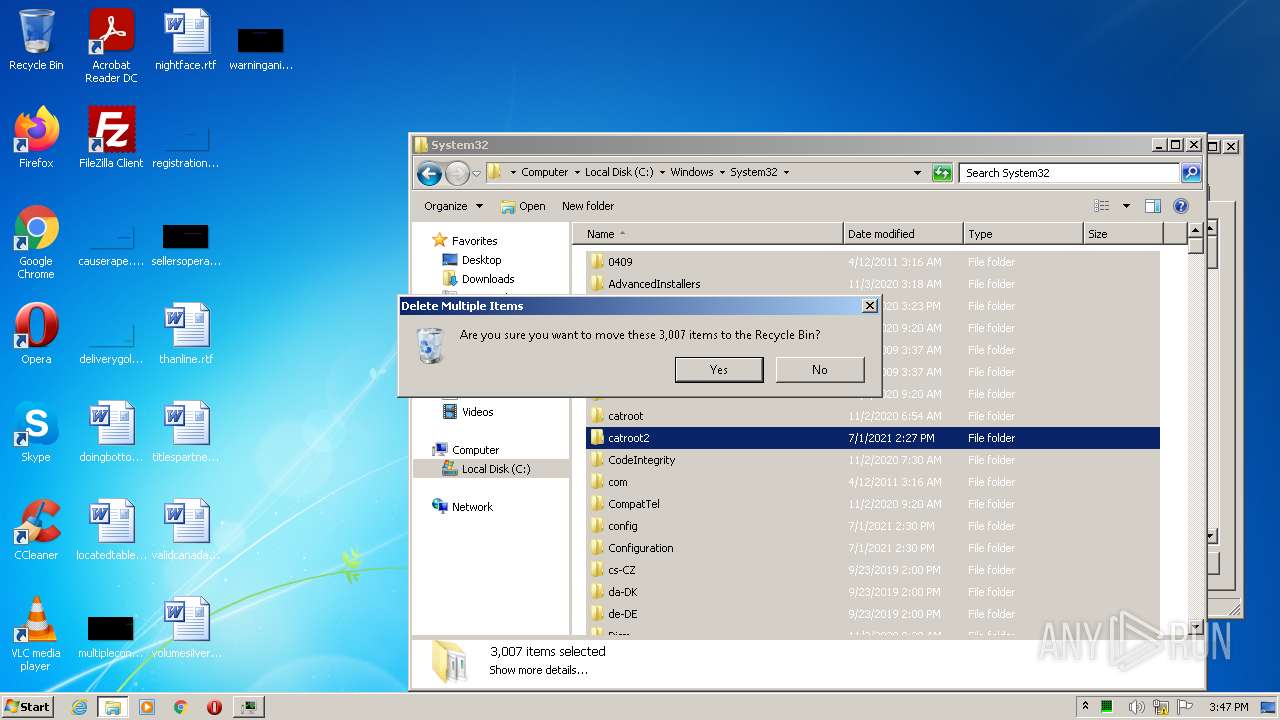
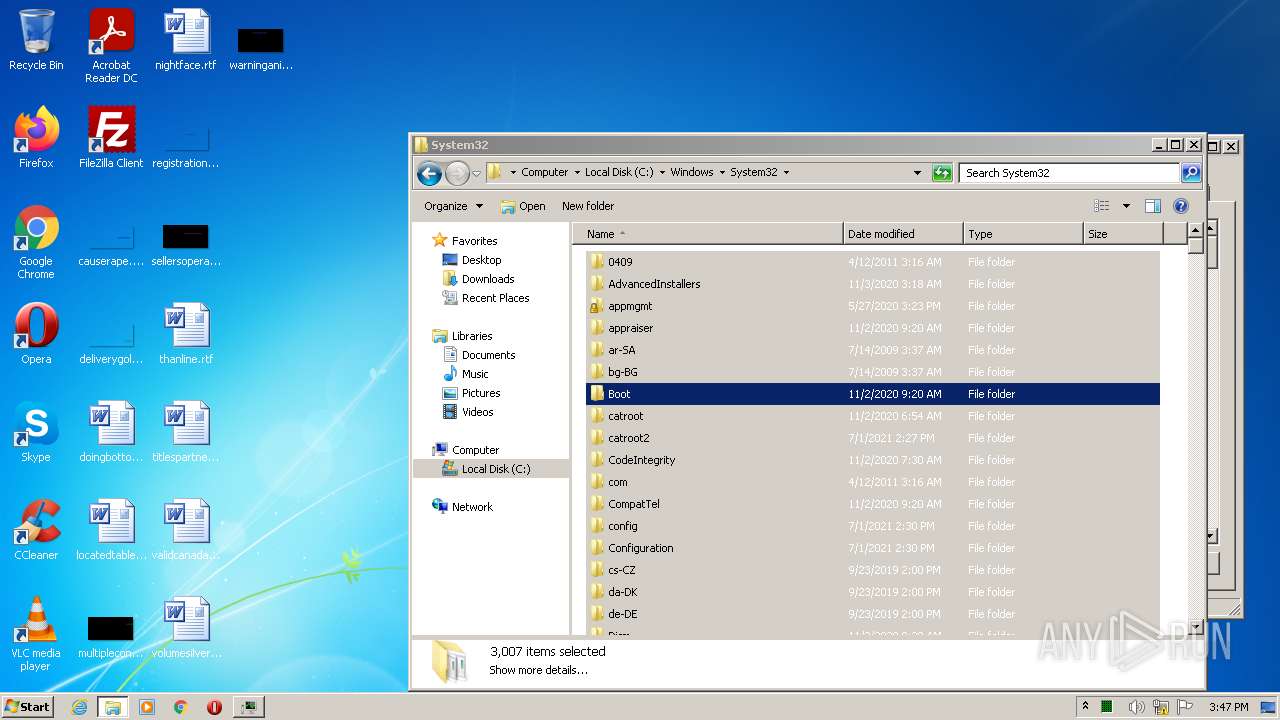
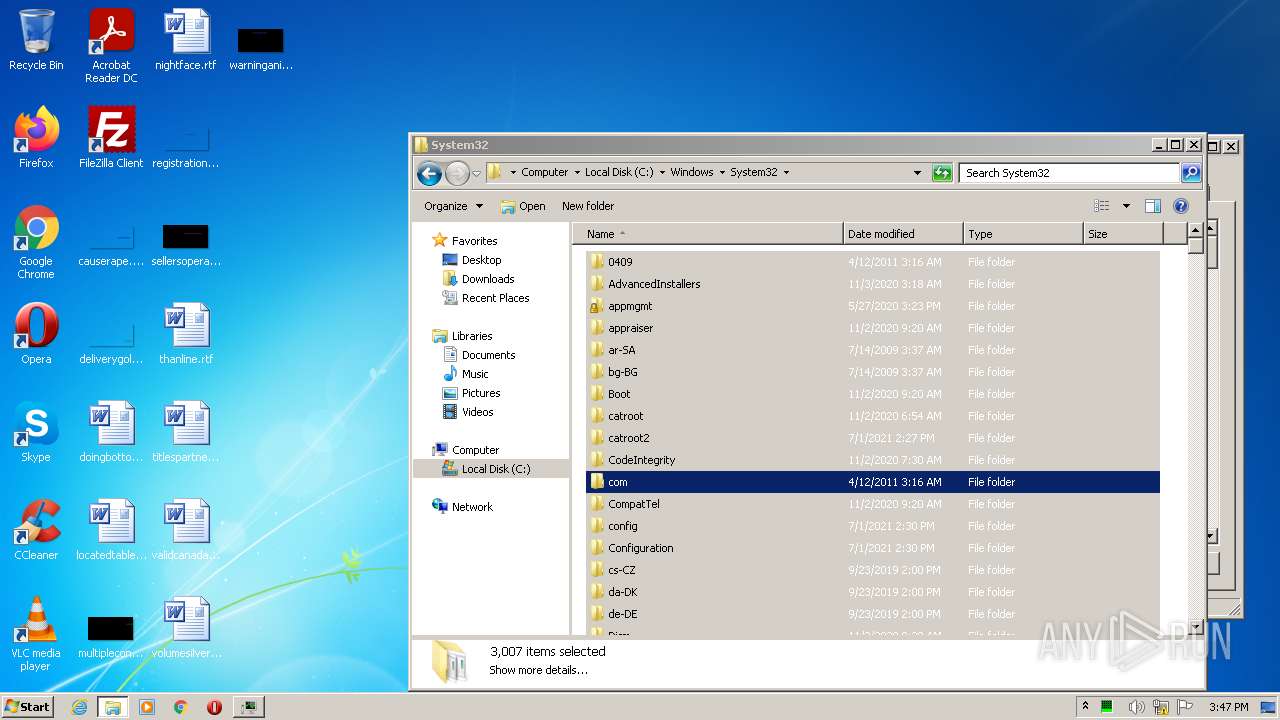
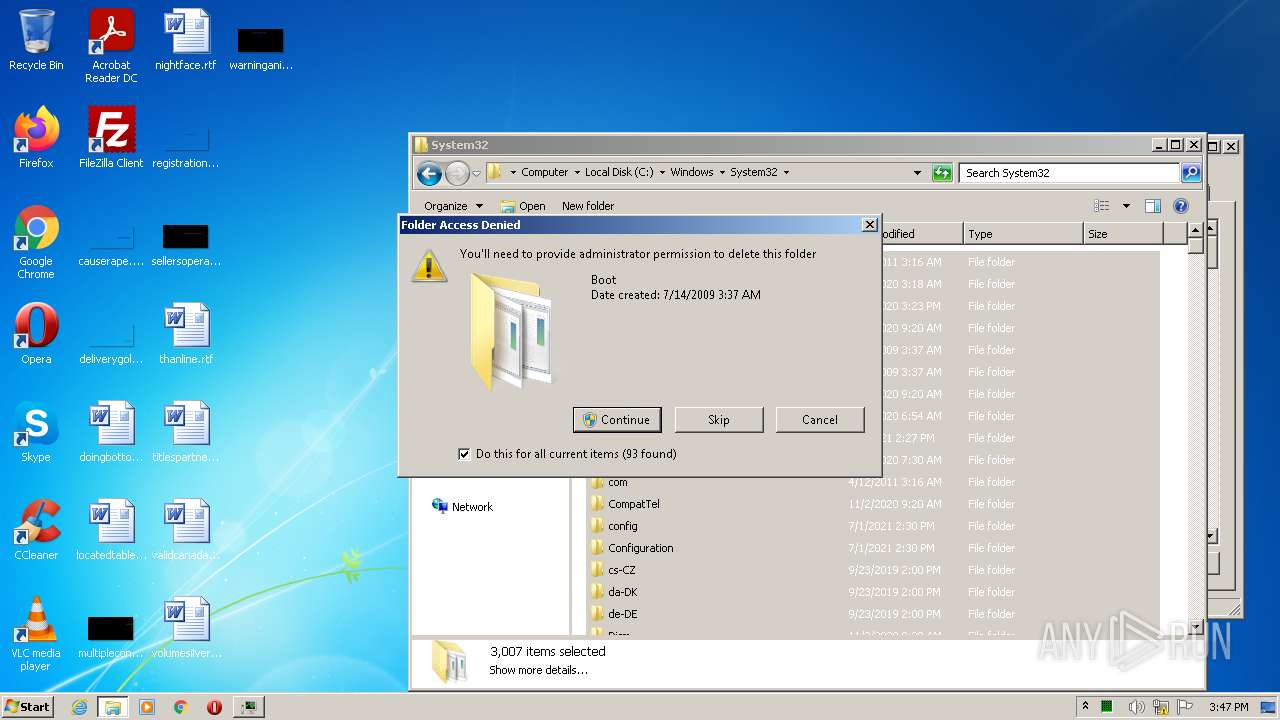
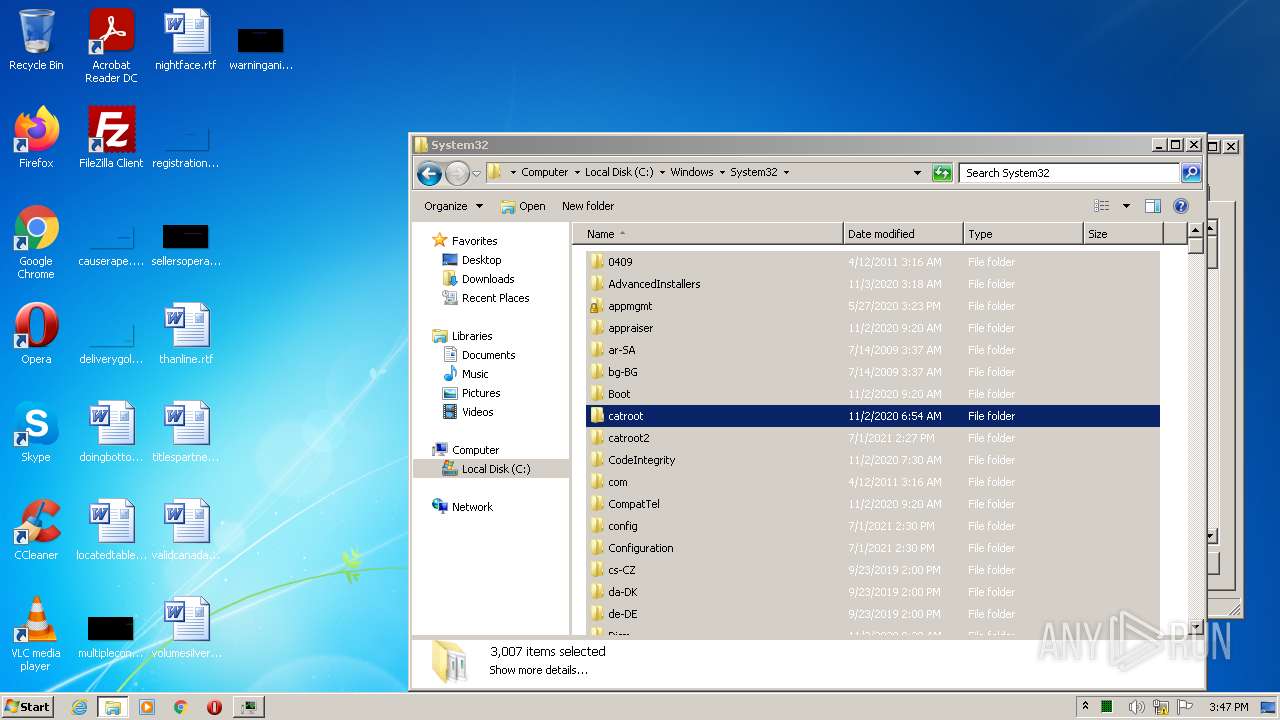
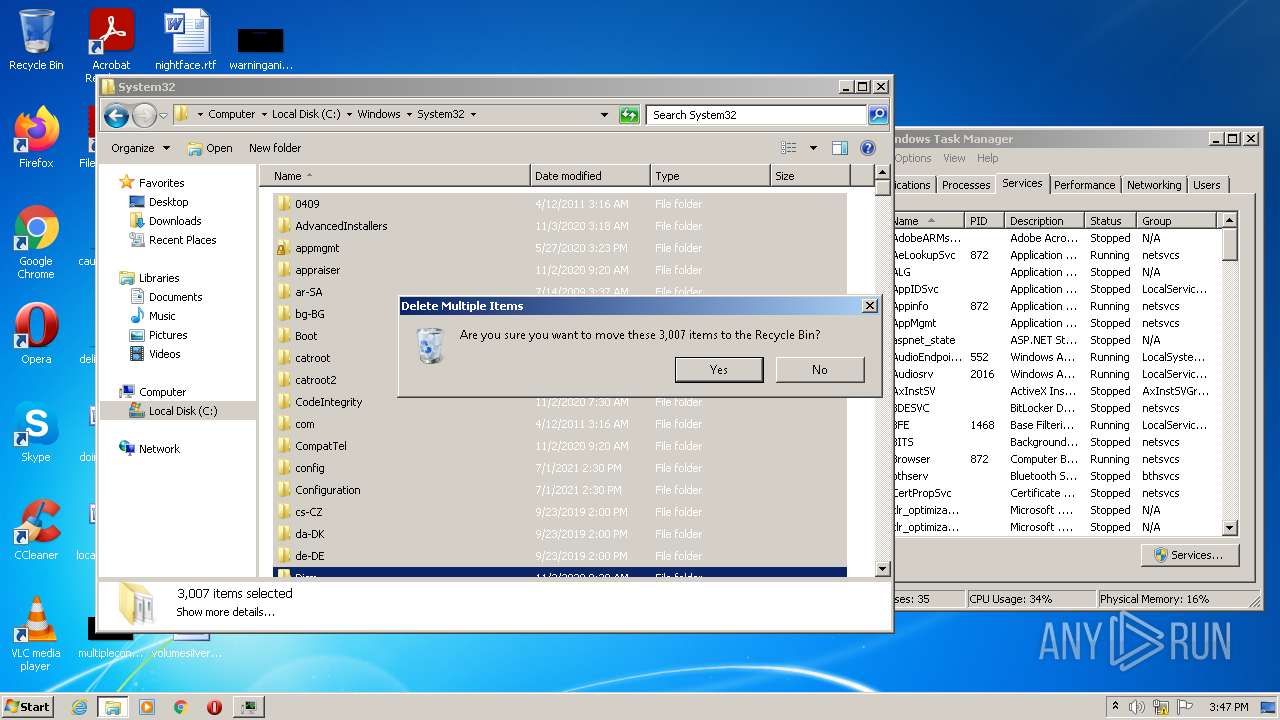
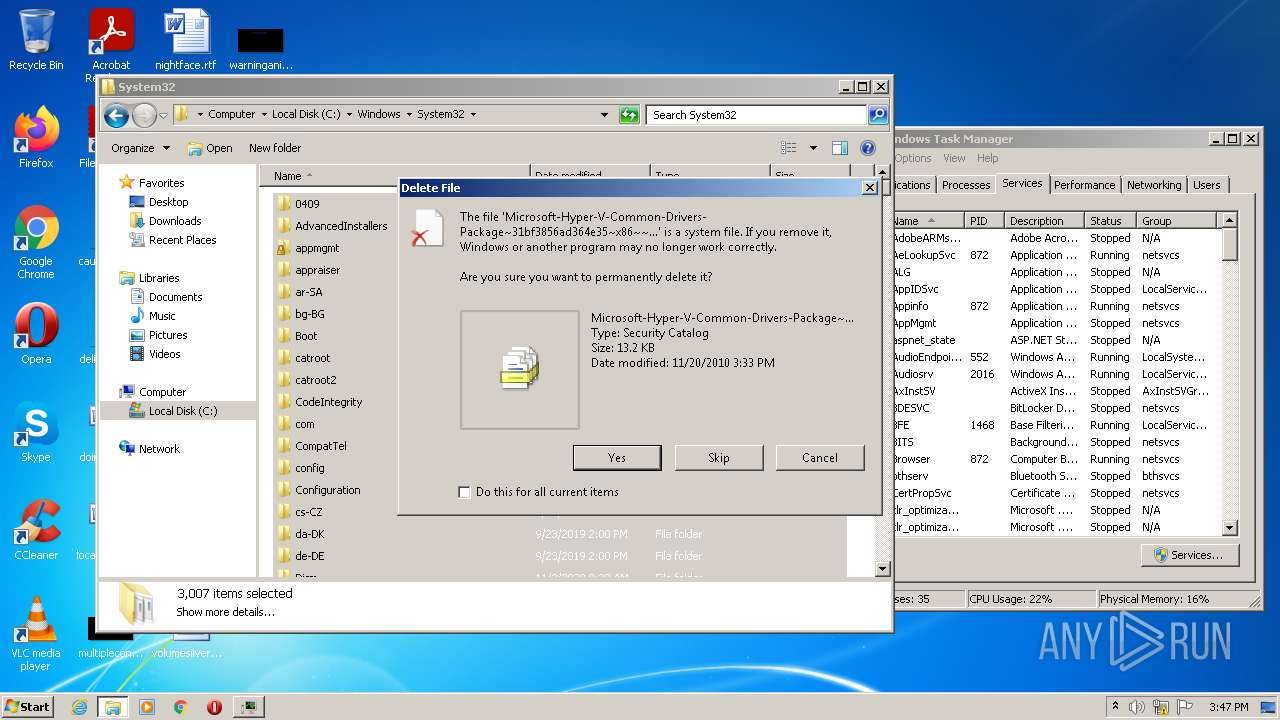
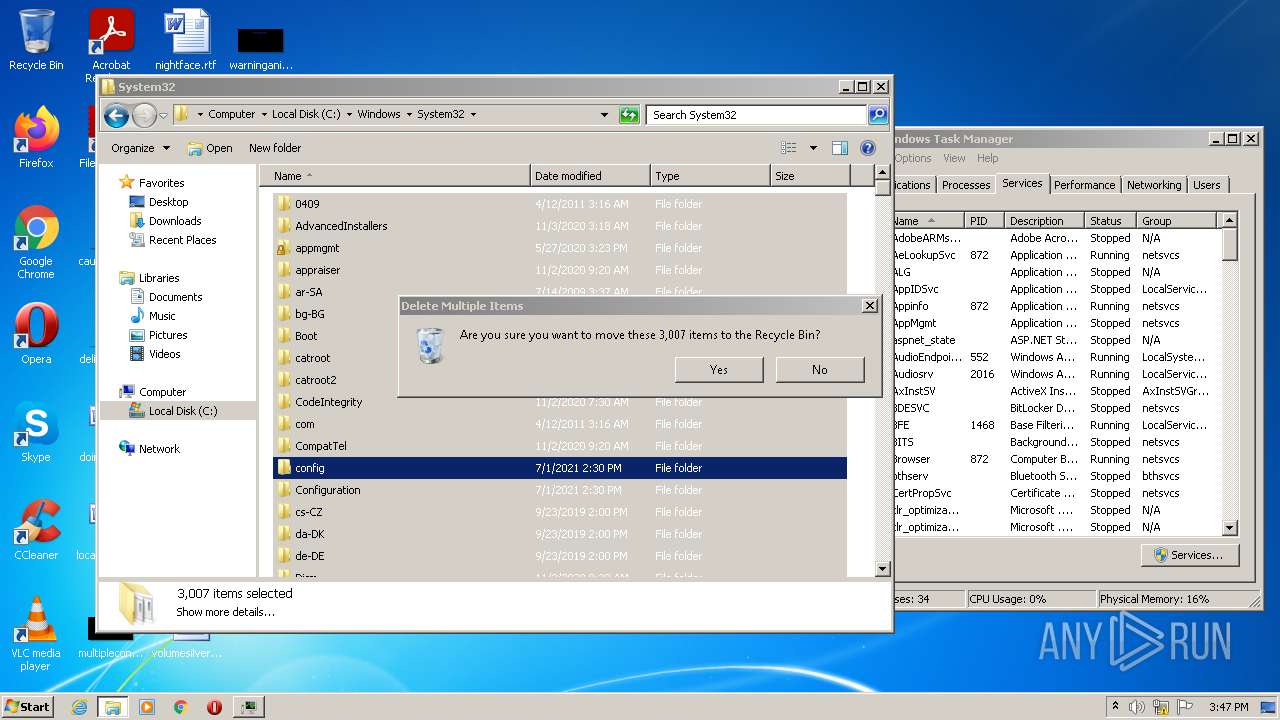
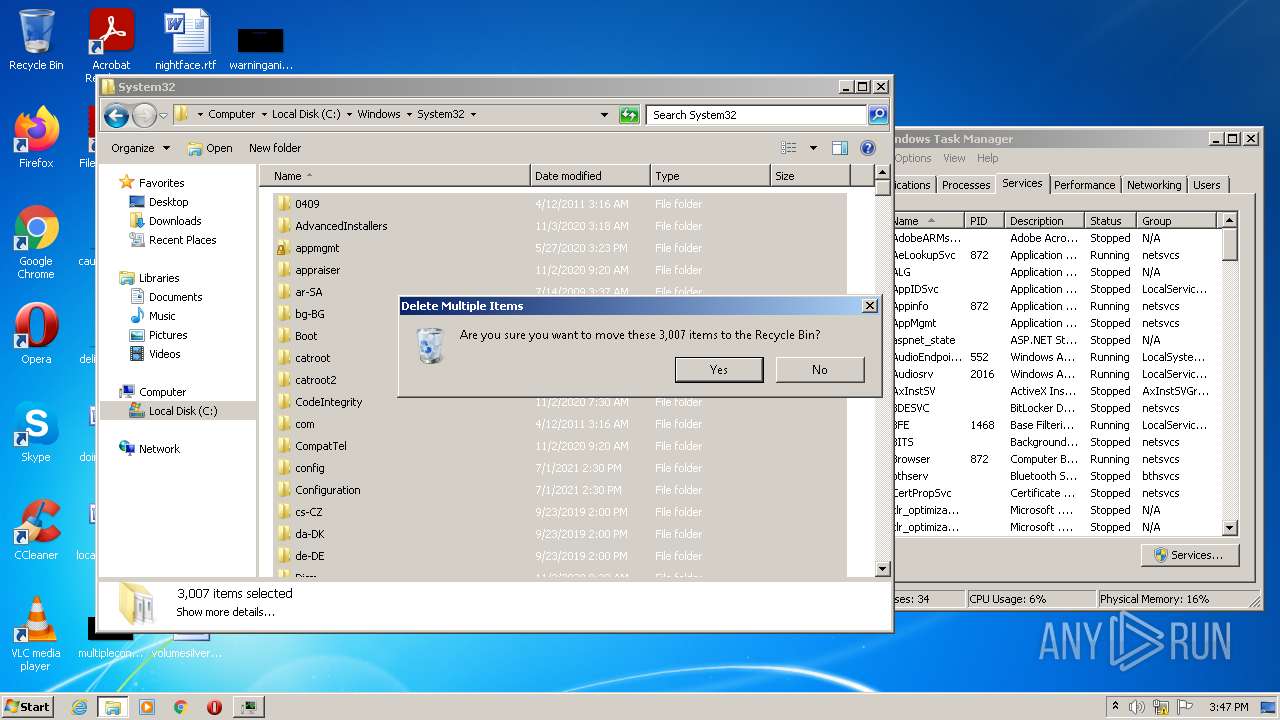
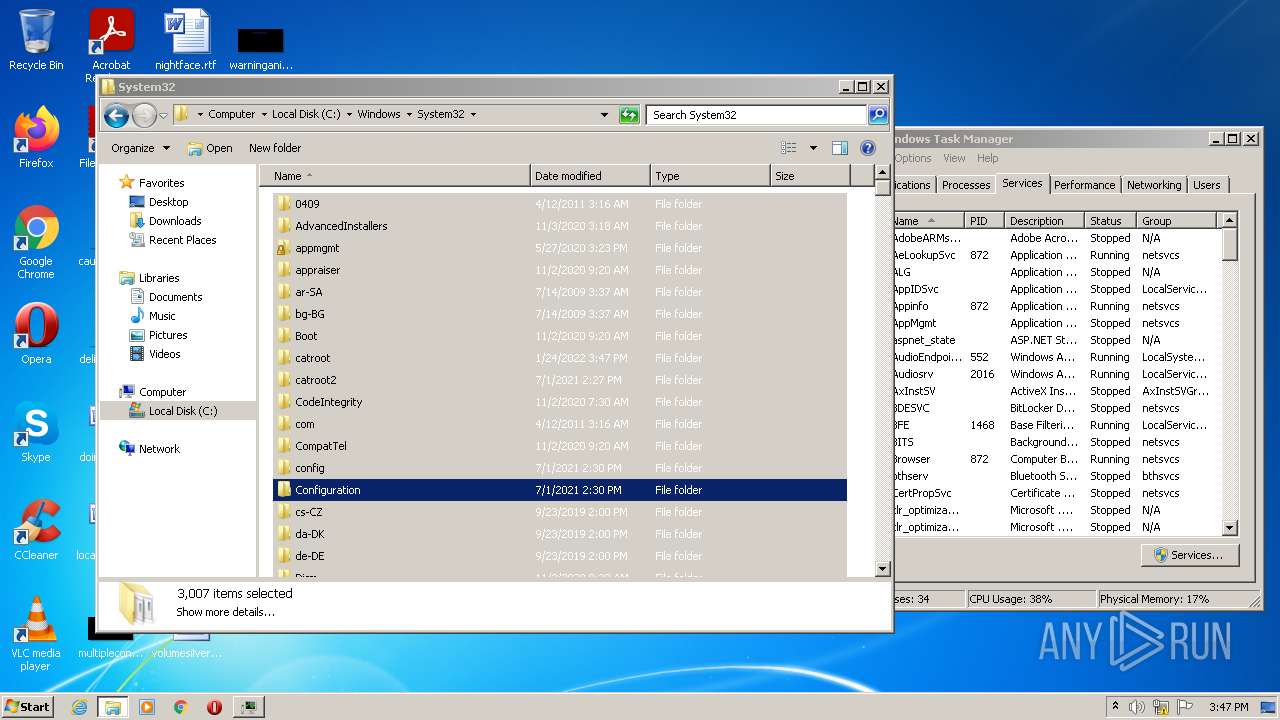
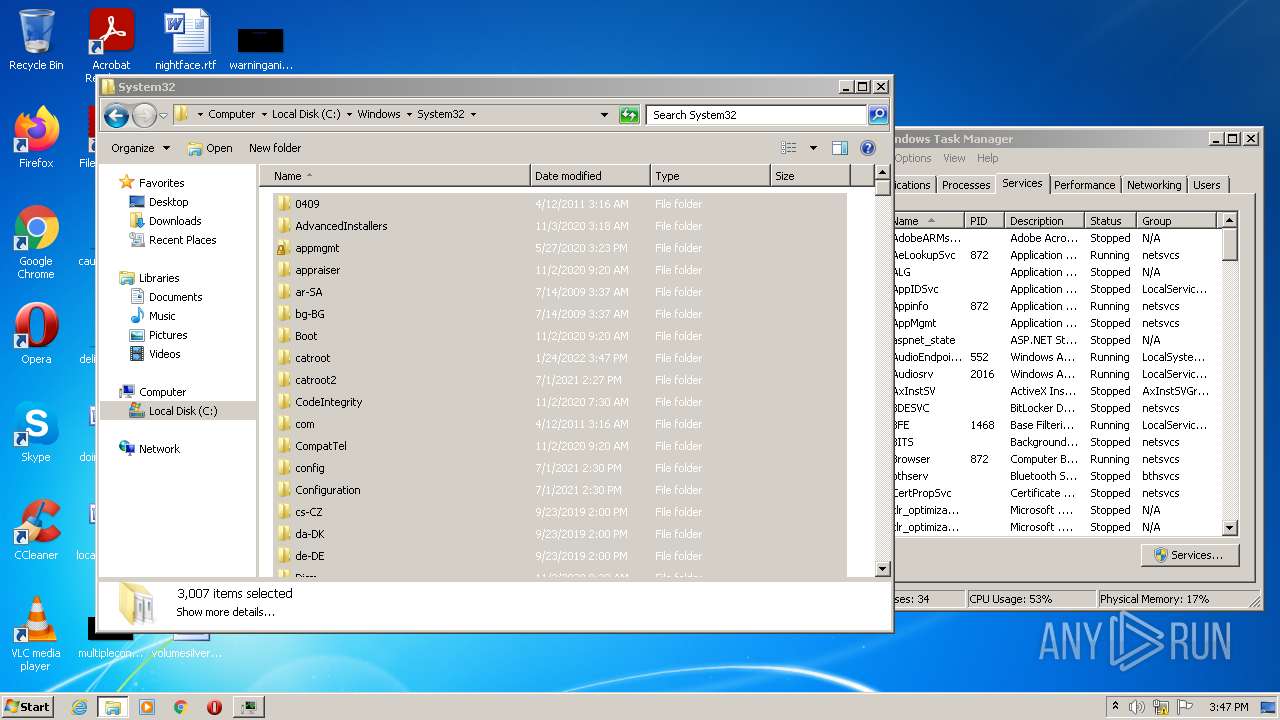
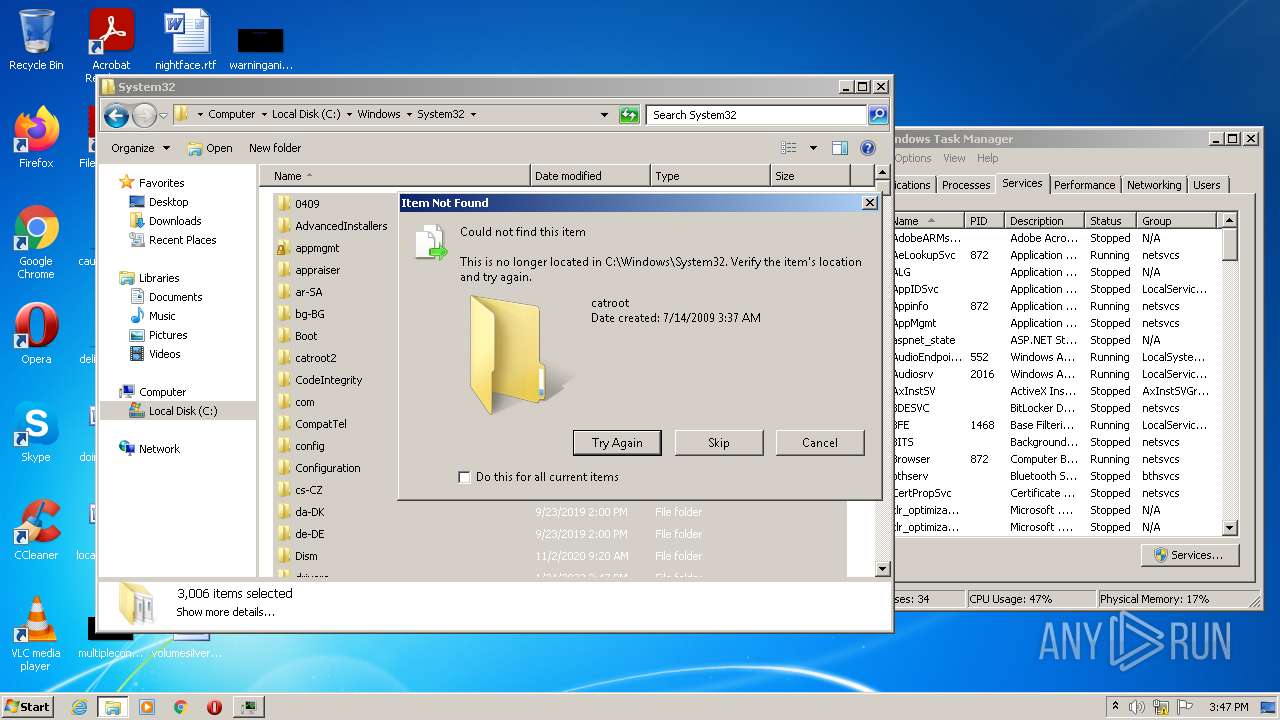
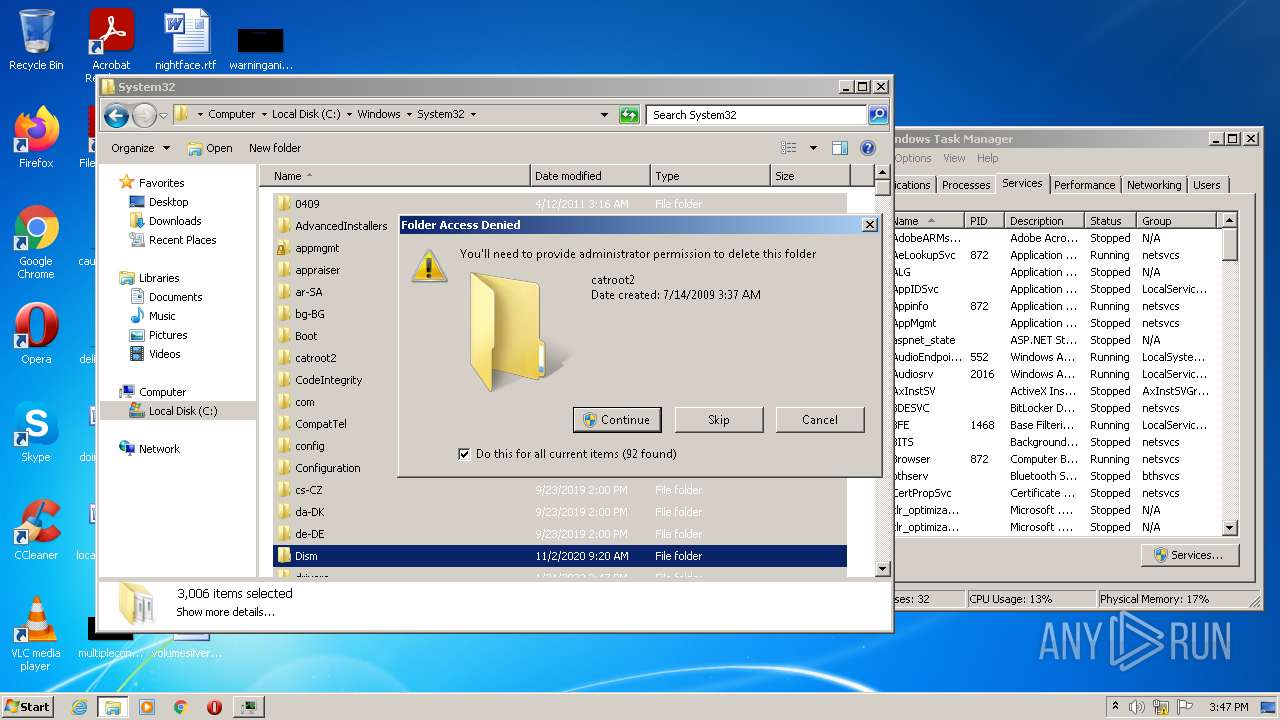
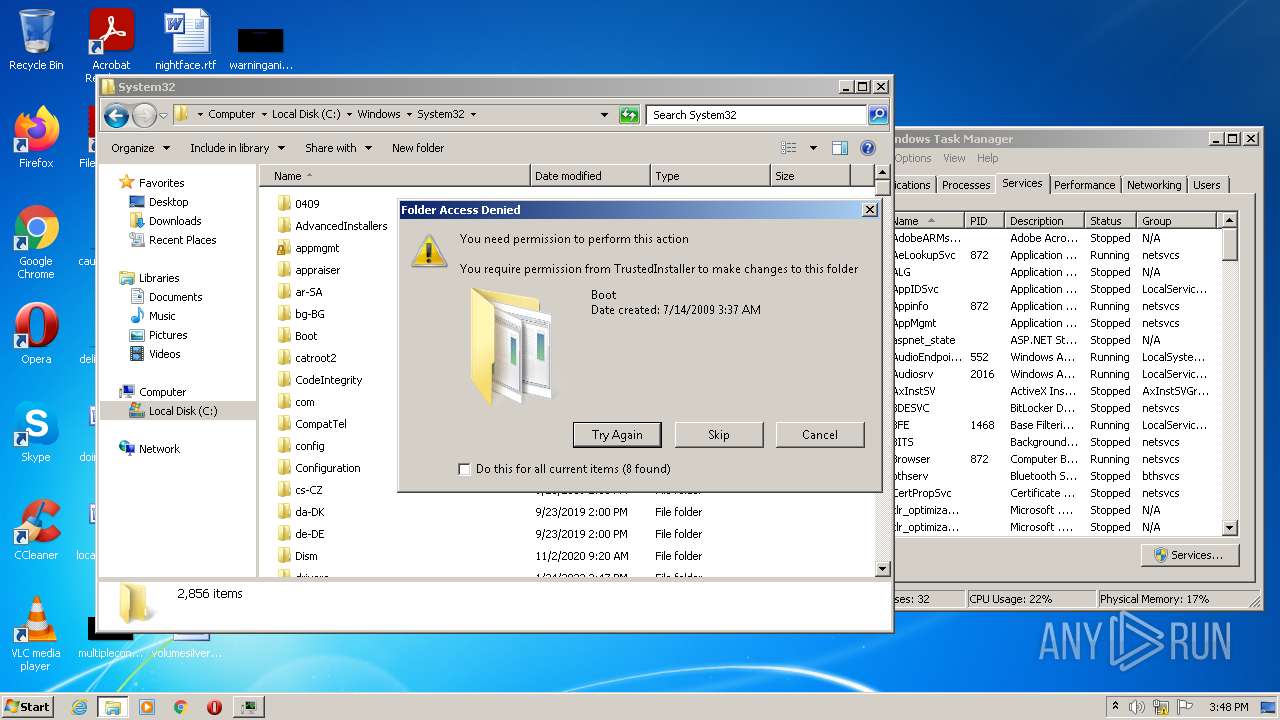
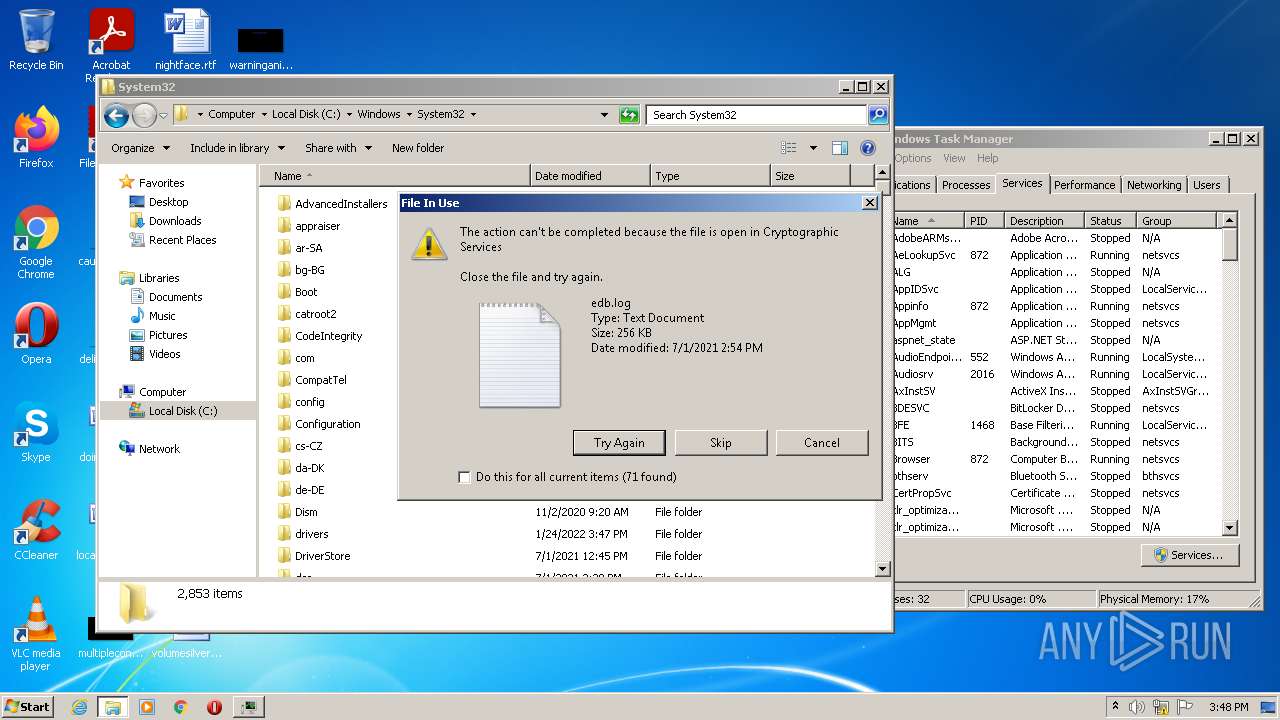
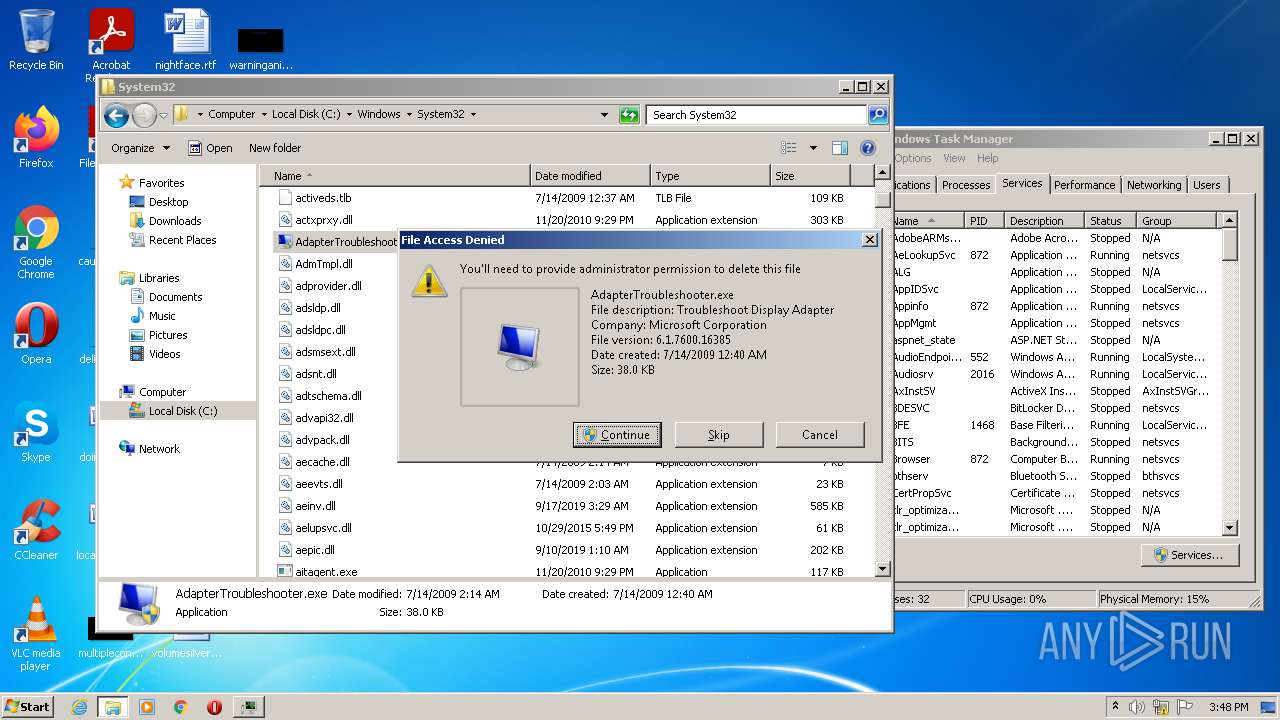
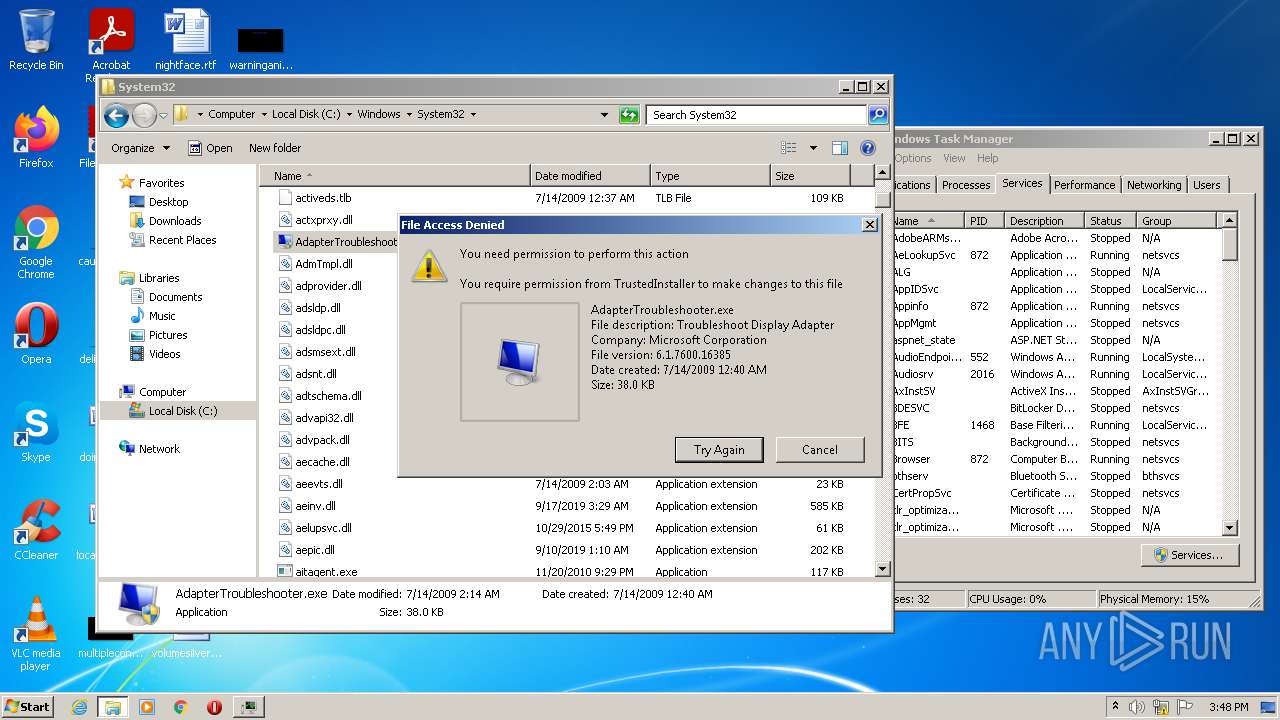
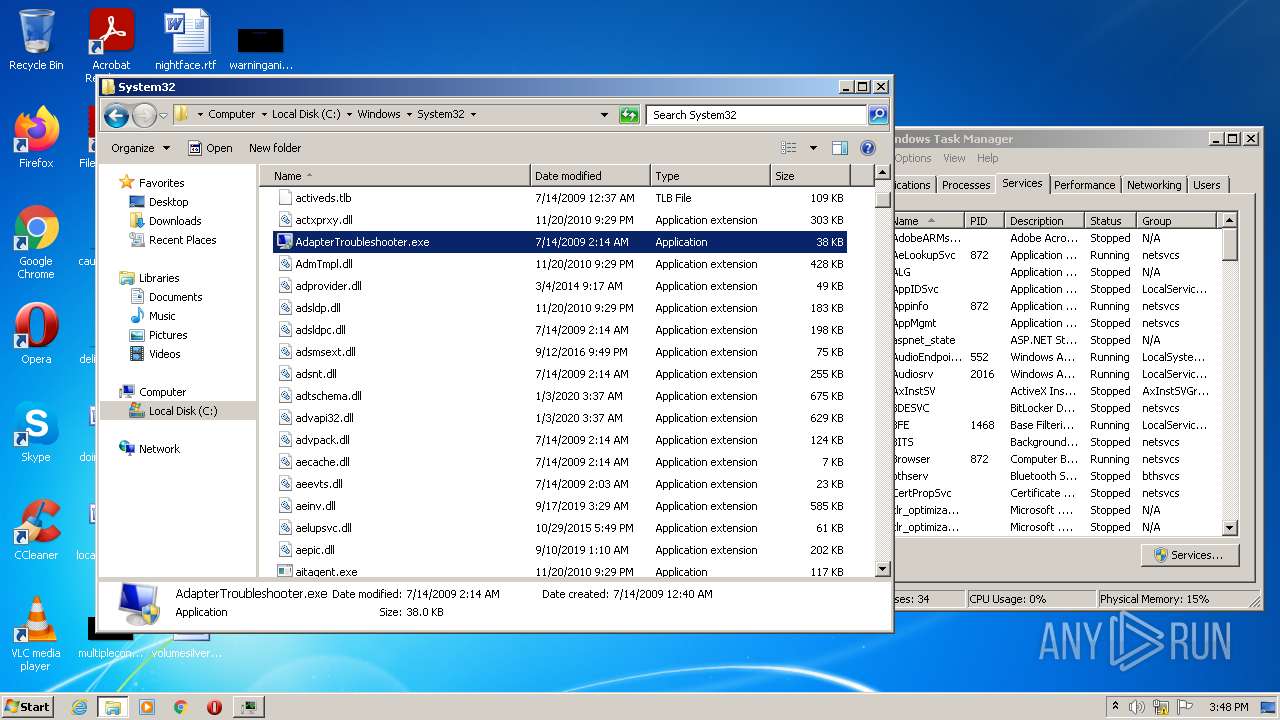
Tries to delete the host file
- DllHost.exe (PID: 3472)
- DllHost.exe (PID: 3808)
Changes internet zones settings
- ie4uinit.exe (PID: 2816)
Loads the Task Scheduler COM API
- rundll32.exe (PID: 2516)
- CCleaner.exe (PID: 3428)
- CCleaner.exe (PID: 284)
Changes the autorun value in the registry
- unregmp2.exe (PID: 2080)
- CCleaner.exe (PID: 284)
Writes to a start menu file
- regsvr32.exe (PID: 2636)
Changes the Startup folder
- regsvr32.exe (PID: 2636)
Actions looks like stealing of personal data
- pingsender.exe (PID: 3748)
- pingsender.exe (PID: 304)
- pingsender.exe (PID: 1172)
- CCleaner.exe (PID: 284)
- CCleaner.exe (PID: 3428)
Steals credentials from Web Browsers
- pingsender.exe (PID: 3748)
- pingsender.exe (PID: 1172)
- pingsender.exe (PID: 304)
- CCleaner.exe (PID: 284)
- CCleaner.exe (PID: 3428)
Drops executable file immediately after starts
- CCleaner.exe (PID: 3428)
- CCleaner.exe (PID: 284)
Changes settings of System certificates
- CCleaner.exe (PID: 3428)
Loads dropped or rewritten executable
- CCleaner.exe (PID: 3428)
- CCleaner.exe (PID: 284)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2068)
- ie4uinit.exe (PID: 2816)
- CCleaner.exe (PID: 3428)
Executed via COM
- DllHost.exe (PID: 3472)
- DllHost.exe (PID: 3808)
- DllHost.exe (PID: 2896)
- DllHost.exe (PID: 4020)
- DllHost.exe (PID: 2460)
Reads default file associations for system extensions
- DllHost.exe (PID: 2896)
- DllHost.exe (PID: 3808)
Application launched itself
- ie4uinit.exe (PID: 2816)
- rundll32.exe (PID: 2516)
- chrmstp.exe (PID: 3468)
- CCleaner.exe (PID: 3428)
Uses RUNDLL32.EXE to load library
- ie4uinit.exe (PID: 2816)
- rundll32.exe (PID: 2516)
Reads internet explorer settings
- ie4uinit.exe (PID: 2816)
- CCleaner.exe (PID: 3428)
- CCleaner.exe (PID: 284)
Creates files in the program directory
- ie4uinit.exe (PID: 2816)
- chrmstp.exe (PID: 3468)
- CCleaner.exe (PID: 3428)
- CCleaner.exe (PID: 284)
Writes to a desktop.ini file (may be used to cloak folders)
- ie4uinit.exe (PID: 2816)
- unregmp2.exe (PID: 2080)
- regsvr32.exe (PID: 2636)
Changes default file association
- unregmp2.exe (PID: 2080)
Checks supported languages
- chrmstp.exe (PID: 3468)
- chrmstp.exe (PID: 468)
- IMEKLMG.EXE (PID: 1996)
- IMEKLMG.EXE (PID: 2428)
- jusched.exe (PID: 1292)
- imkrmig.exe (PID: 3044)
- pingsender.exe (PID: 304)
- pingsender.exe (PID: 3748)
- pingsender.exe (PID: 1172)
- CCleaner.exe (PID: 284)
- CCleaner.exe (PID: 3428)
Reads the date of Windows installation
- chrmstp.exe (PID: 3468)
- CCleaner.exe (PID: 3428)
Reads the computer name
- chrmstp.exe (PID: 3468)
- IMEKLMG.EXE (PID: 2428)
- IMEKLMG.EXE (PID: 1996)
- pingsender.exe (PID: 3748)
- pingsender.exe (PID: 1172)
- pingsender.exe (PID: 304)
- CCleaner.exe (PID: 3428)
- CCleaner.exe (PID: 284)
Creates files in the Windows directory
- chrmstp.exe (PID: 468)
Reads Environment values
- unregmp2.exe (PID: 2080)
- CCleaner.exe (PID: 284)
- CCleaner.exe (PID: 3428)
Check for Java to be installed
- jusched.exe (PID: 1292)
Loads DLL from Mozilla Firefox
- pingsender.exe (PID: 3748)
- pingsender.exe (PID: 304)
- pingsender.exe (PID: 1172)
Executable content was dropped or overwritten
- CCleaner.exe (PID: 3428)
- CCleaner.exe (PID: 284)
Drops a file that was compiled in debug mode
- CCleaner.exe (PID: 3428)
- CCleaner.exe (PID: 284)
Reads CPU info
- CCleaner.exe (PID: 3428)
- CCleaner.exe (PID: 284)
Adds / modifies Windows certificates
- CCleaner.exe (PID: 3428)
Creates a directory in Program Files
- CCleaner.exe (PID: 3428)
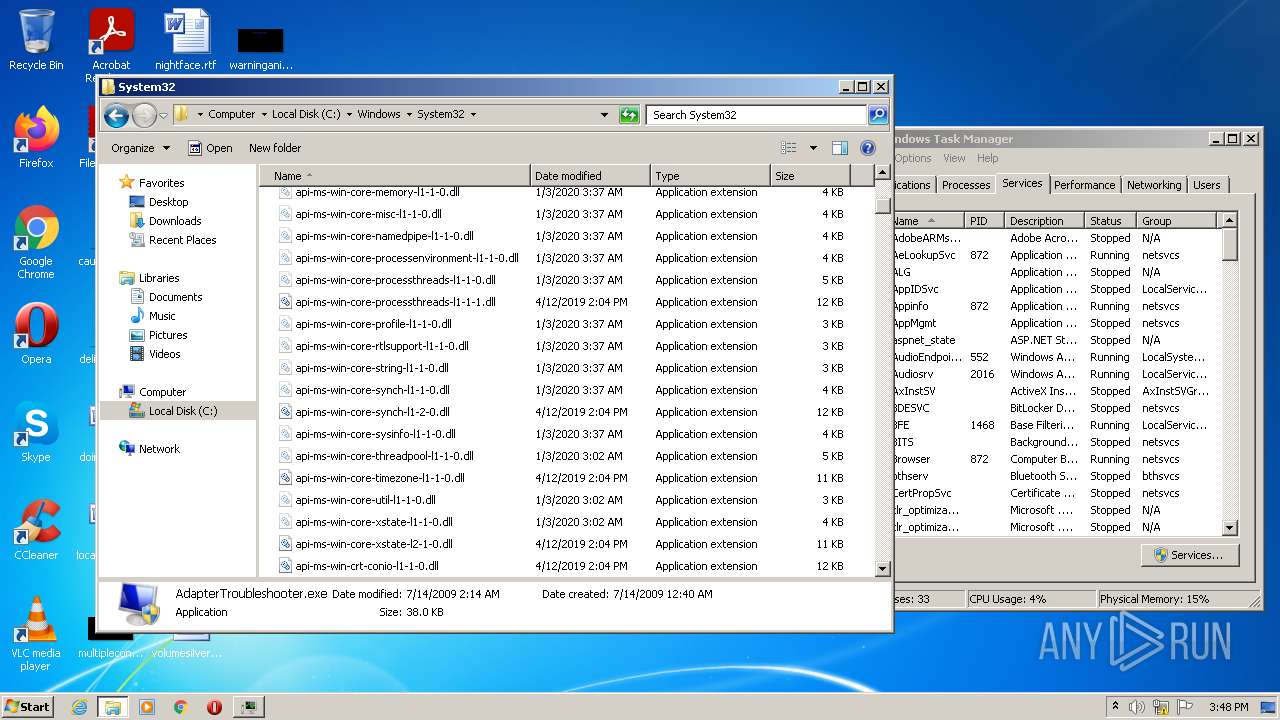
Removes files from Windows directory
- CCleaner.exe (PID: 3428)
- DllHost.exe (PID: 3808)
- DllHost.exe (PID: 3472)
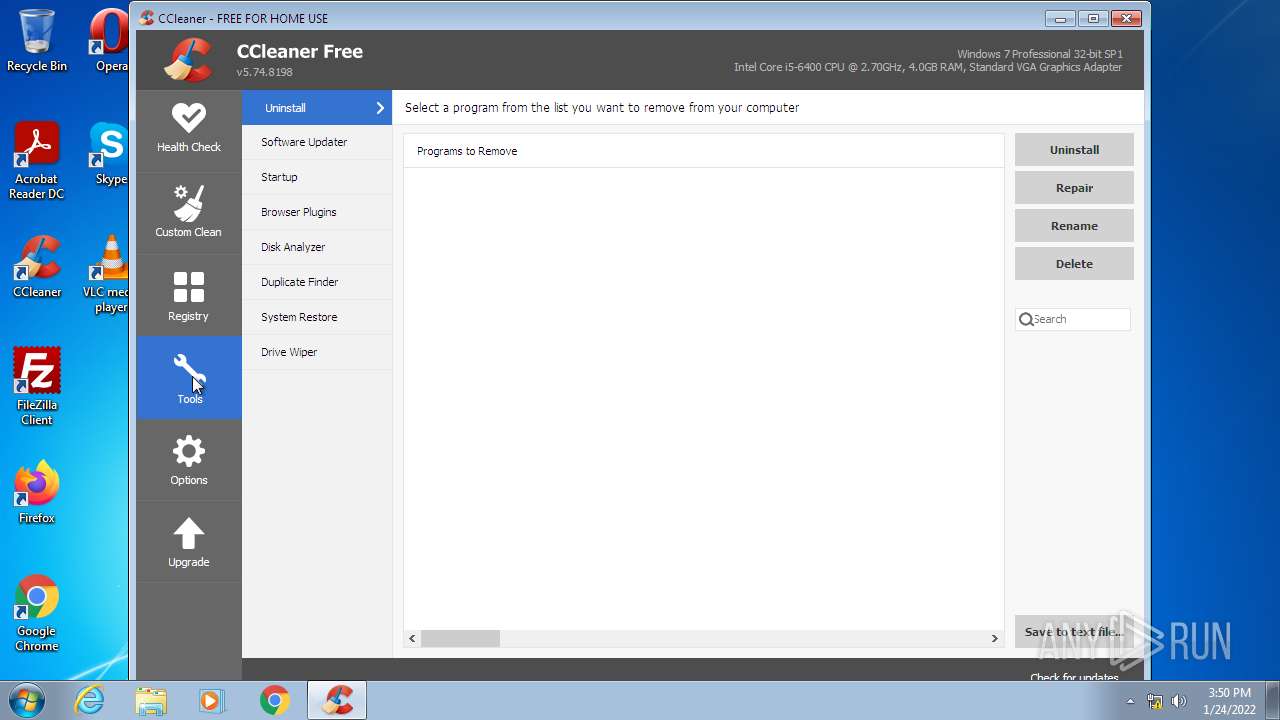
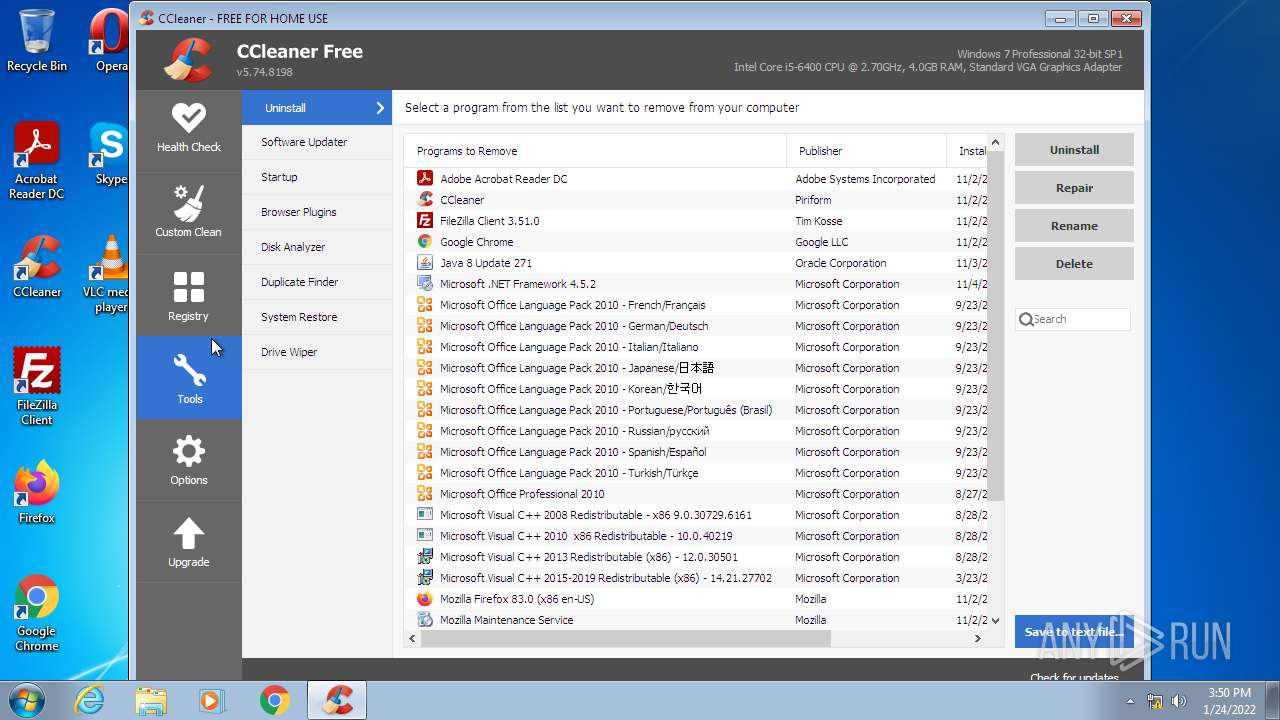
Searches for installed software
- CCleaner.exe (PID: 284)
- CCleaner.exe (PID: 3428)
INFO
Checks supported languages
- iexplore.exe (PID: 2068)
- iexplore.exe (PID: 3432)
- explorer.exe (PID: 1068)
- DllHost.exe (PID: 3472)
- ie4uinit.exe (PID: 2924)
- DllHost.exe (PID: 2896)
- DllHost.exe (PID: 3808)
- ie4uinit.exe (PID: 2816)
- rundll32.exe (PID: 2440)
- RunDll32.exe (PID: 572)
- rundll32.exe (PID: 2516)
- RunDll32.exe (PID: 496)
- taskmgr.exe (PID: 904)
- ie4uinit.exe (PID: 2548)
- regsvr32.exe (PID: 2636)
- ie4uinit.exe (PID: 516)
- unregmp2.exe (PID: 2080)
- explorer.exe (PID: 968)
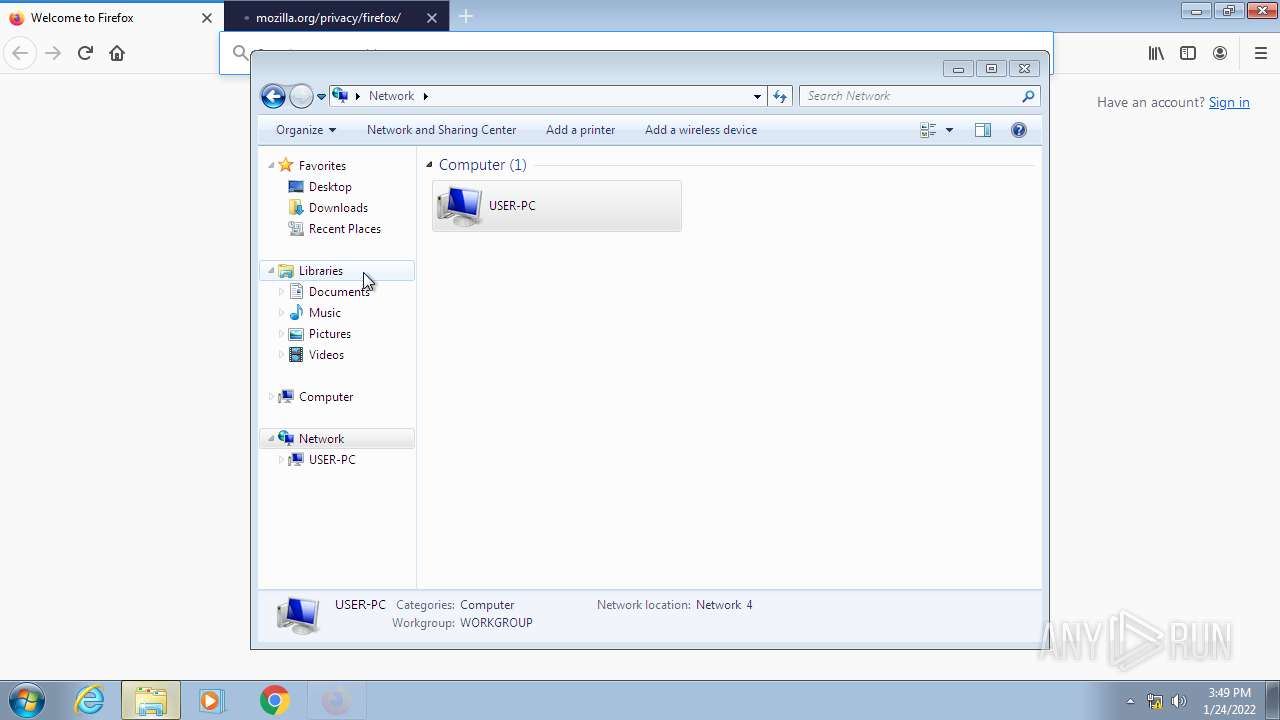
- firefox.exe (PID: 1176)
- firefox.exe (PID: 2464)
- firefox.exe (PID: 3736)
- firefox.exe (PID: 1608)
- firefox.exe (PID: 2520)
- firefox.exe (PID: 2628)
- firefox.exe (PID: 3708)
- firefox.exe (PID: 2308)
- DllHost.exe (PID: 4020)
- DllHost.exe (PID: 2460)
Reads the computer name
- iexplore.exe (PID: 3432)
- taskmgr.exe (PID: 904)
- iexplore.exe (PID: 2068)
- DllHost.exe (PID: 3472)
- explorer.exe (PID: 1068)
- DllHost.exe (PID: 2896)
- DllHost.exe (PID: 3808)
- ie4uinit.exe (PID: 2816)
- rundll32.exe (PID: 2516)
- RunDll32.exe (PID: 496)
- rundll32.exe (PID: 2440)
- RunDll32.exe (PID: 572)
- unregmp2.exe (PID: 2080)
- regsvr32.exe (PID: 2636)
- ie4uinit.exe (PID: 2924)
- explorer.exe (PID: 968)
- firefox.exe (PID: 2464)
- firefox.exe (PID: 1608)
- firefox.exe (PID: 3736)
- firefox.exe (PID: 2628)
- firefox.exe (PID: 3708)
- firefox.exe (PID: 2520)
- firefox.exe (PID: 2308)
- DllHost.exe (PID: 4020)
- DllHost.exe (PID: 2460)
Application launched itself
- iexplore.exe (PID: 3432)
- firefox.exe (PID: 1176)
- firefox.exe (PID: 2464)
Changes internet zones settings
- iexplore.exe (PID: 3432)
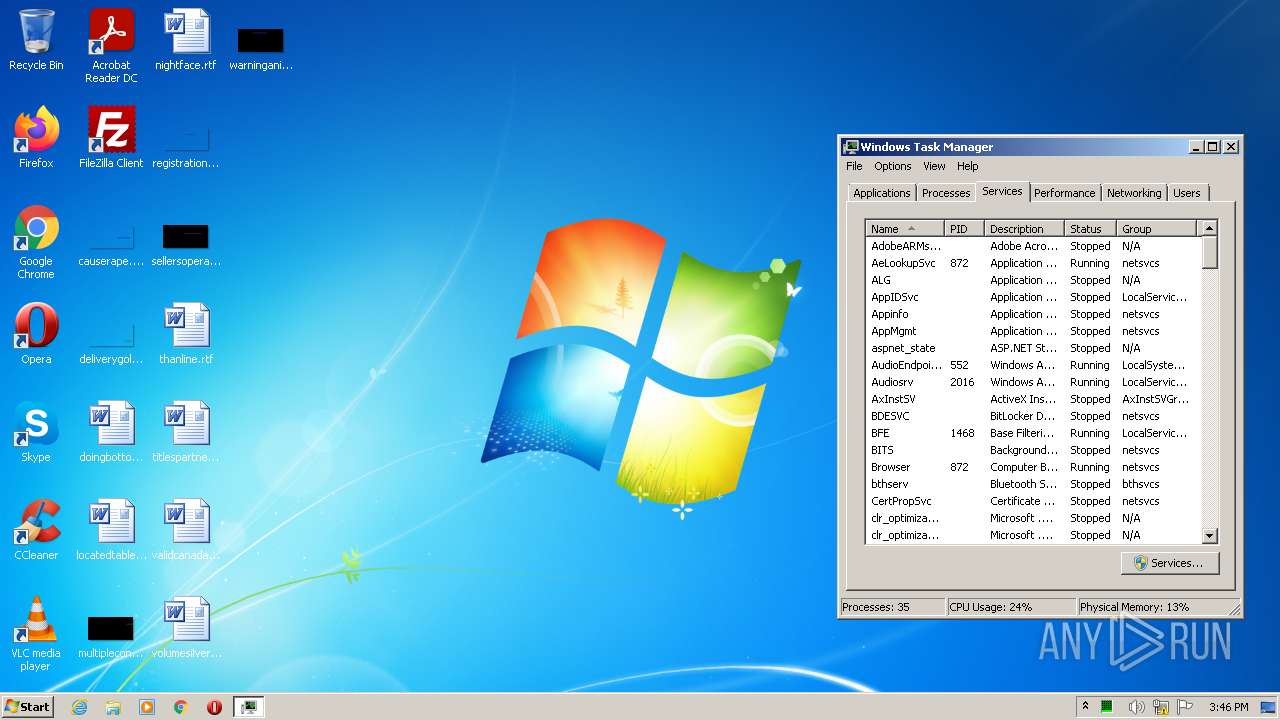
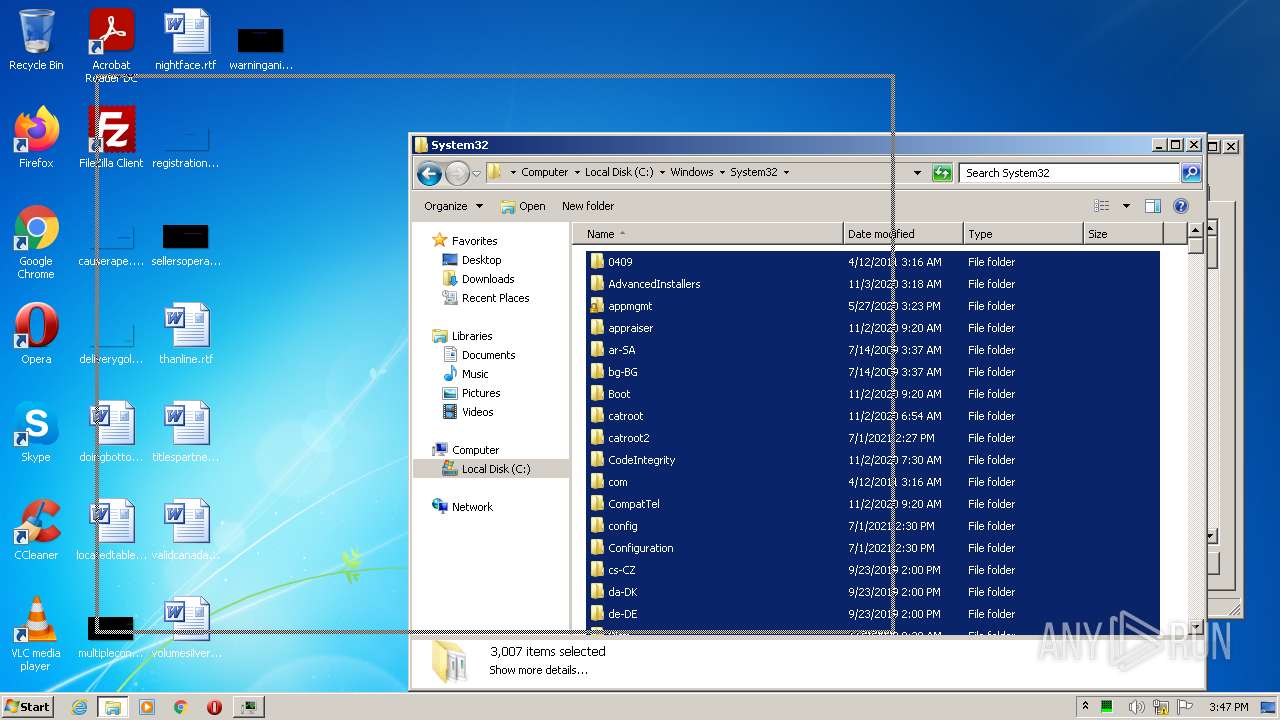
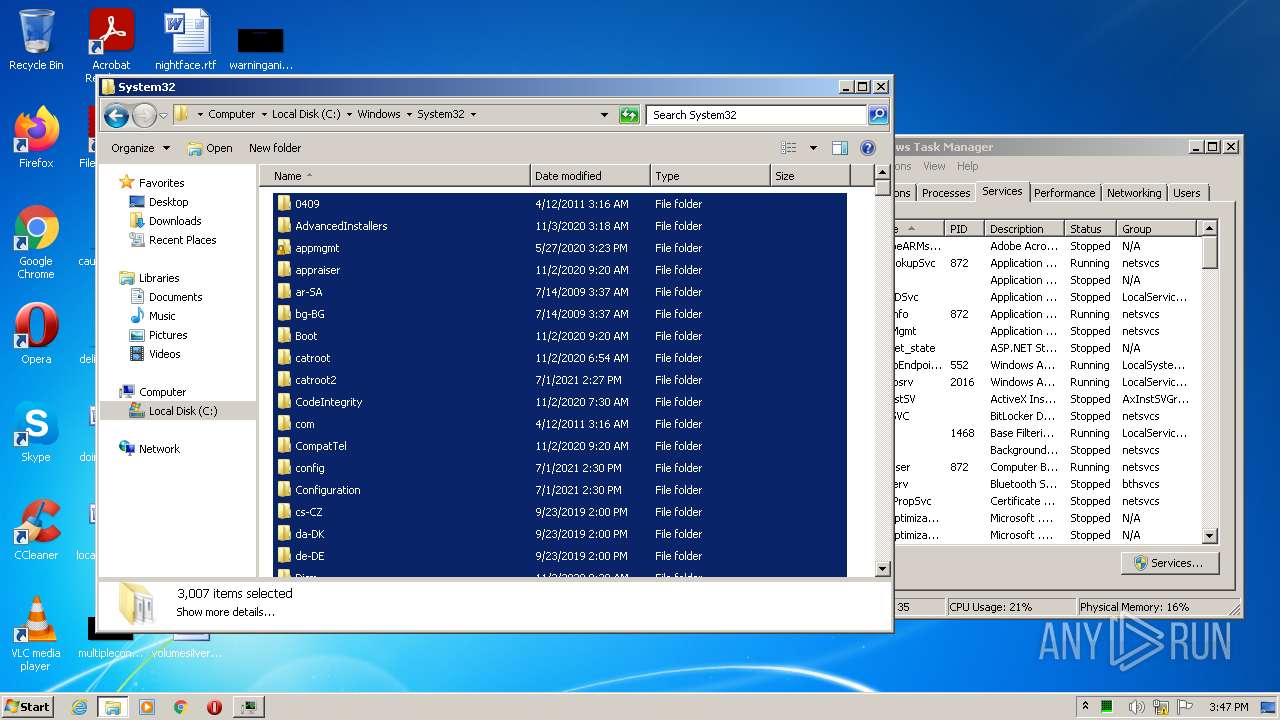
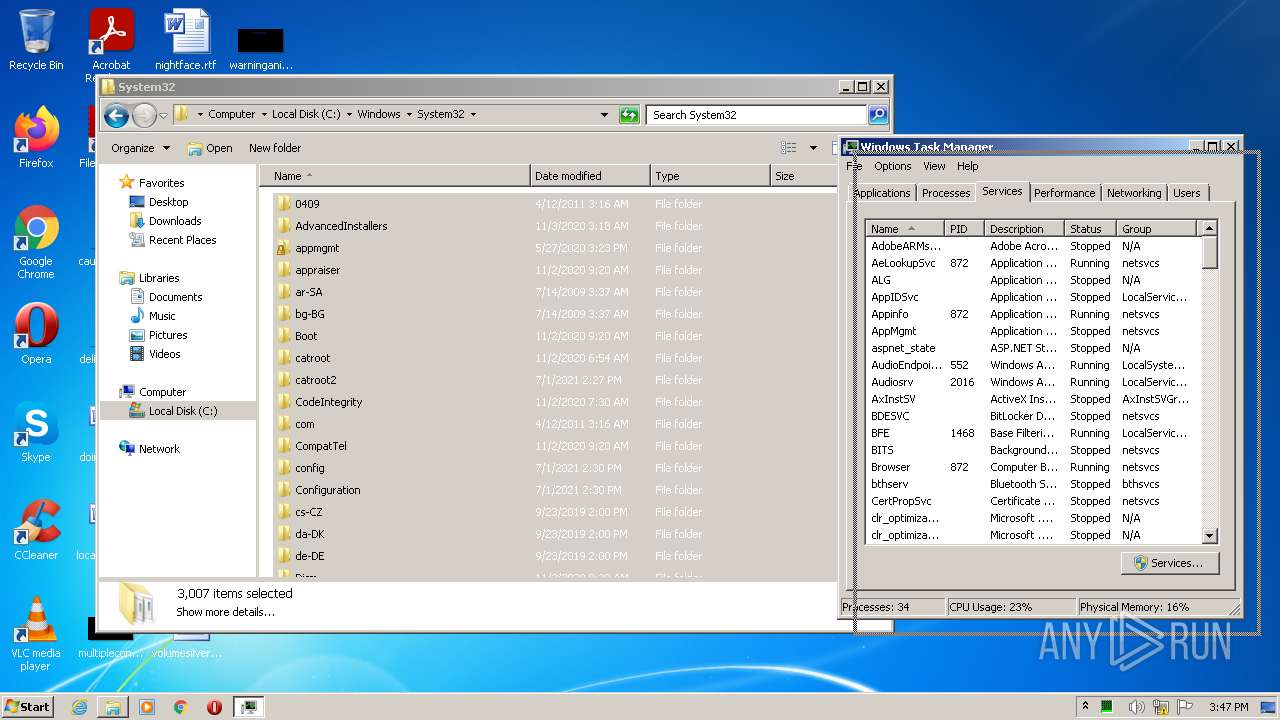
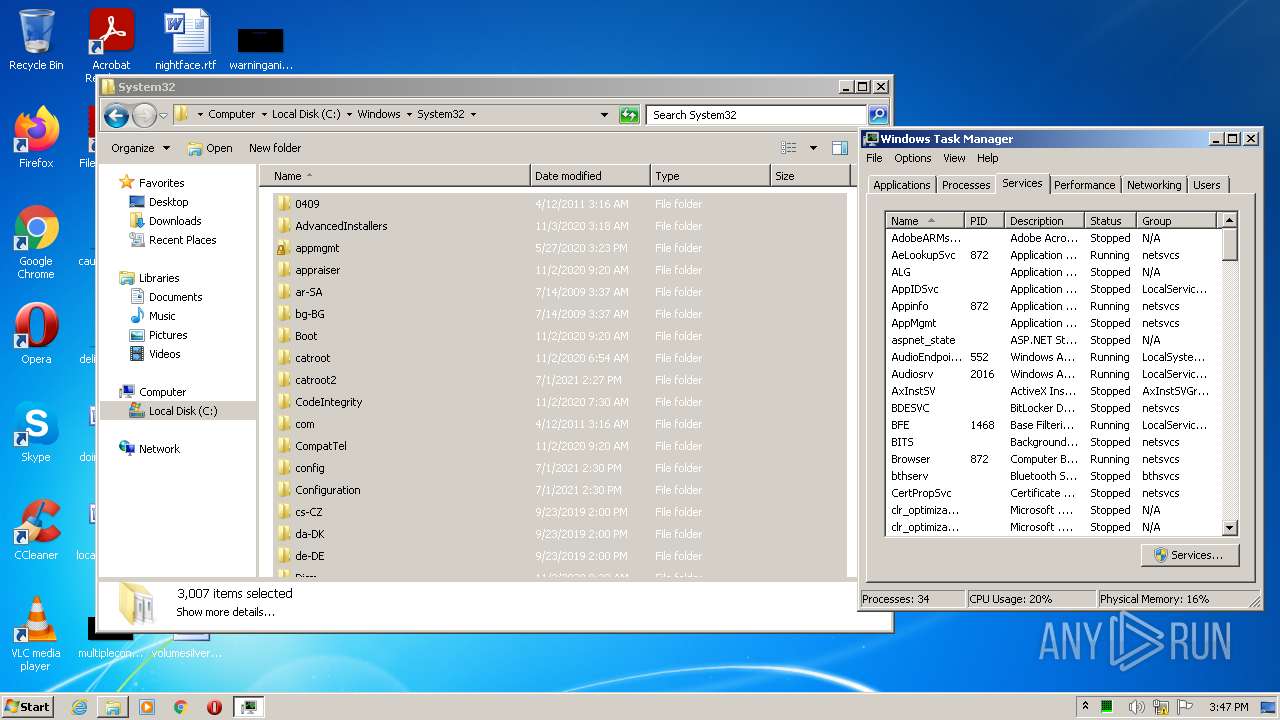
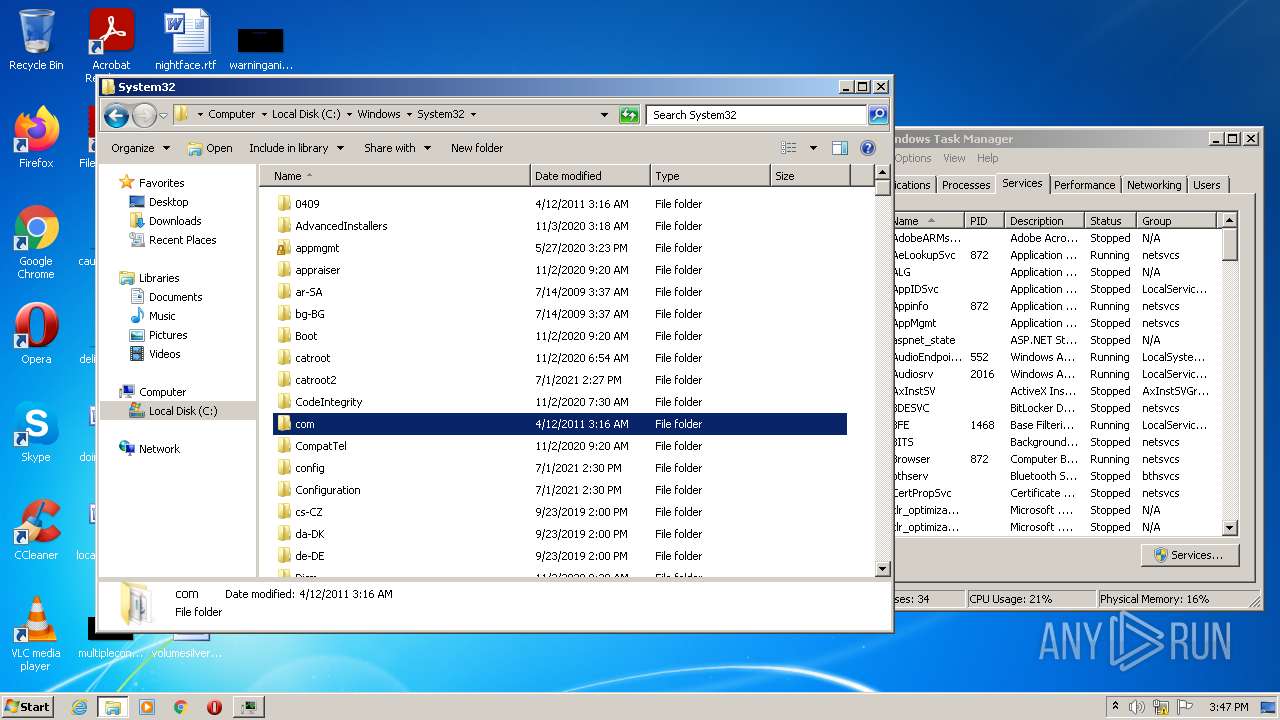
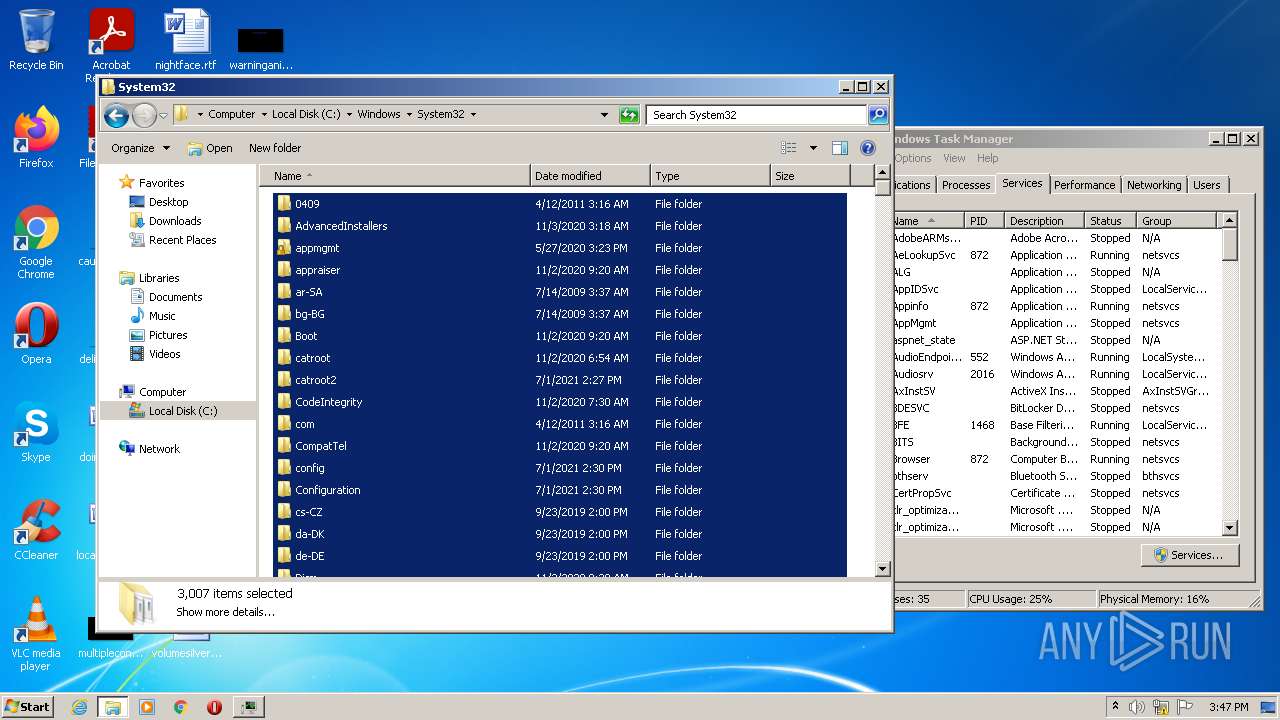
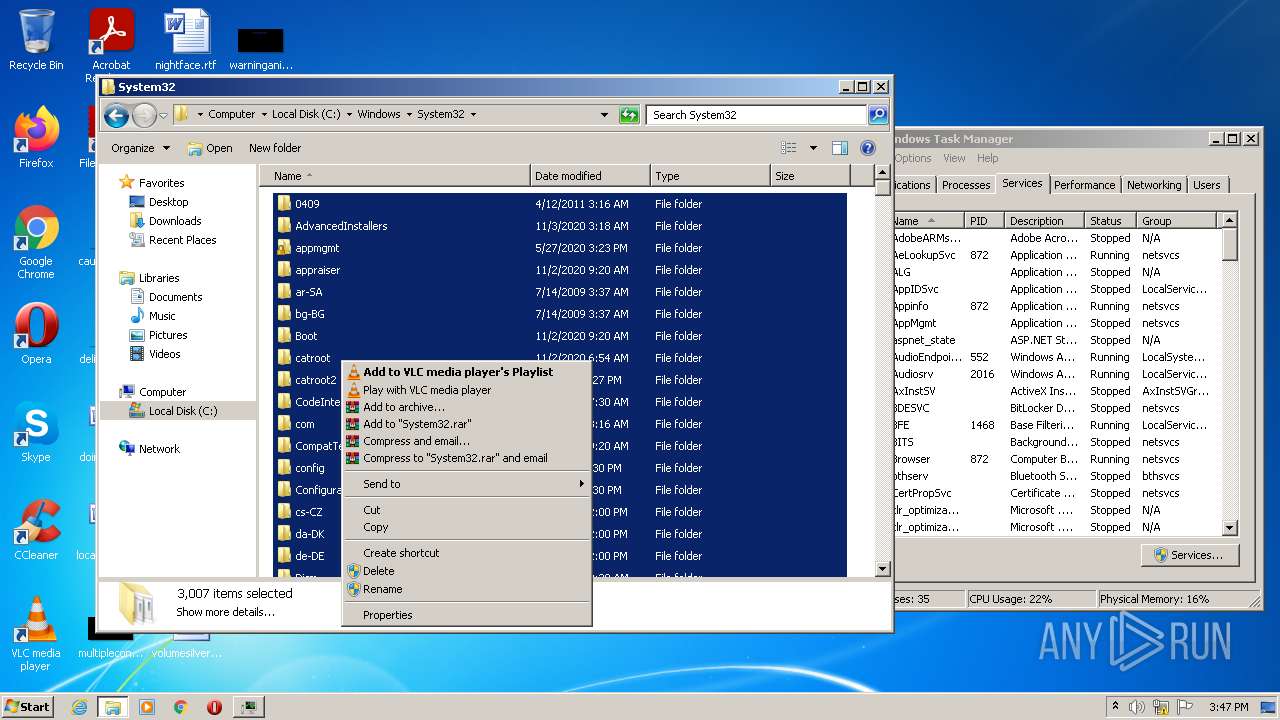
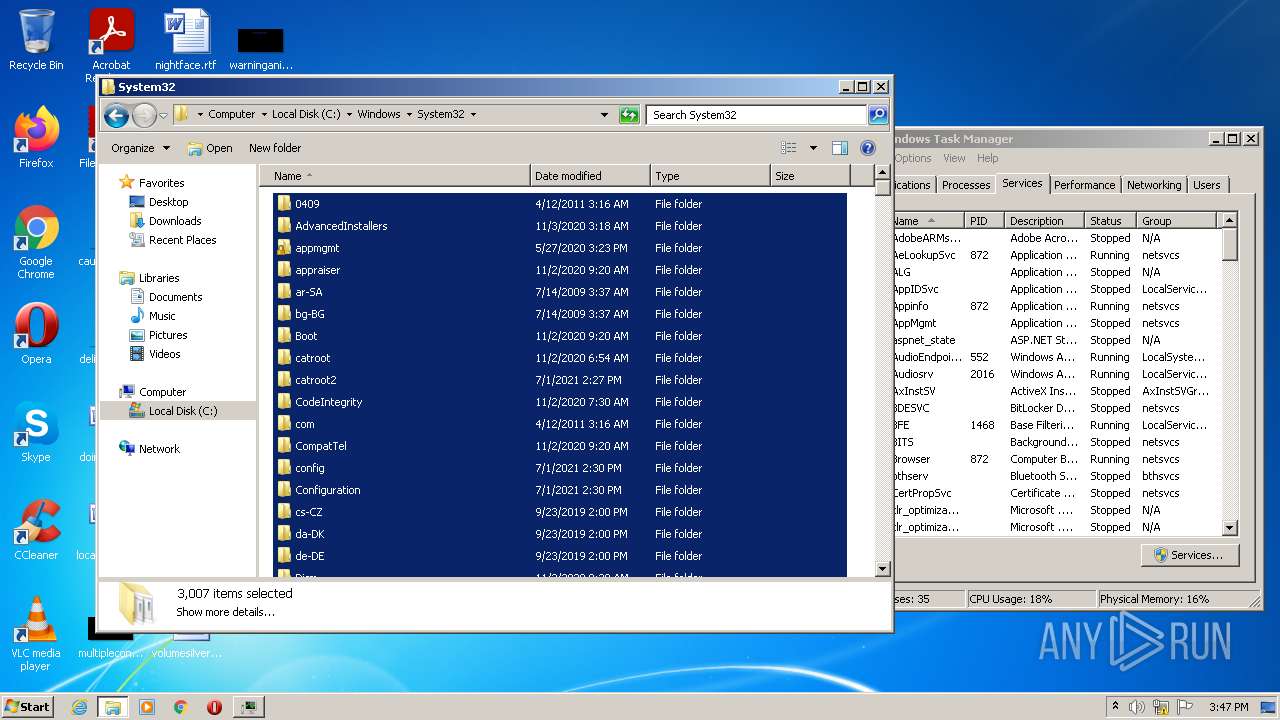
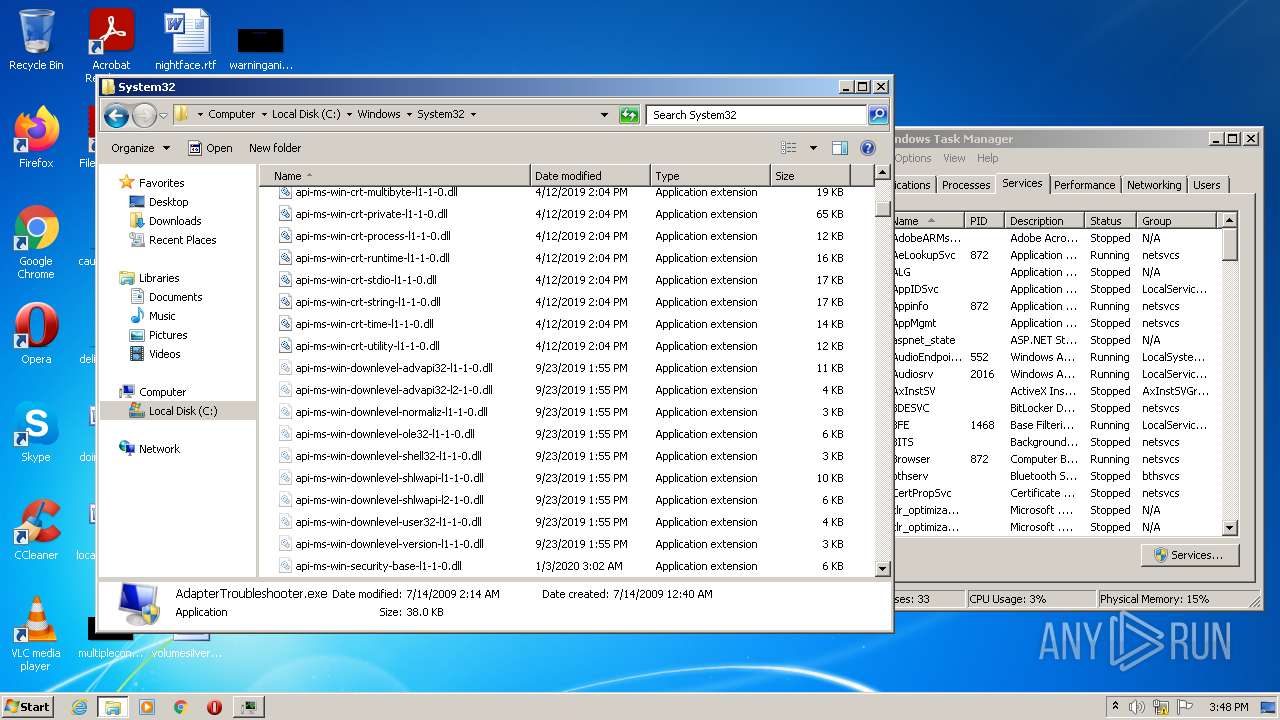
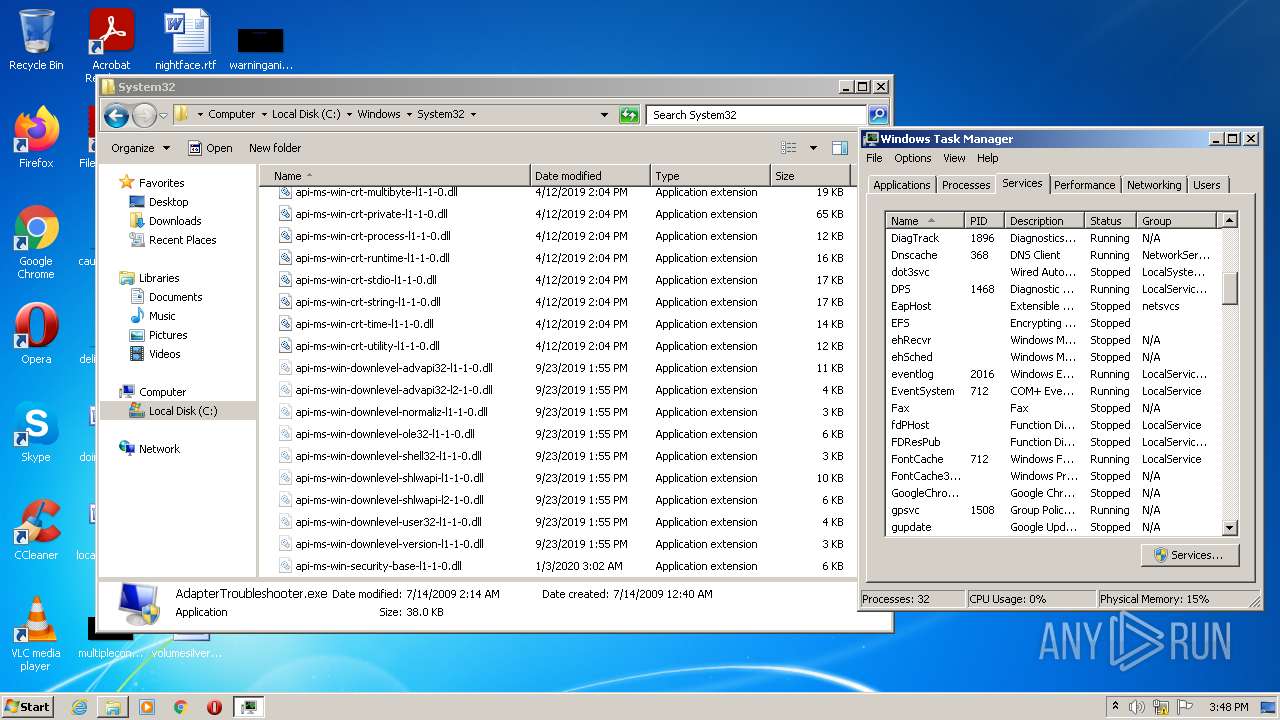
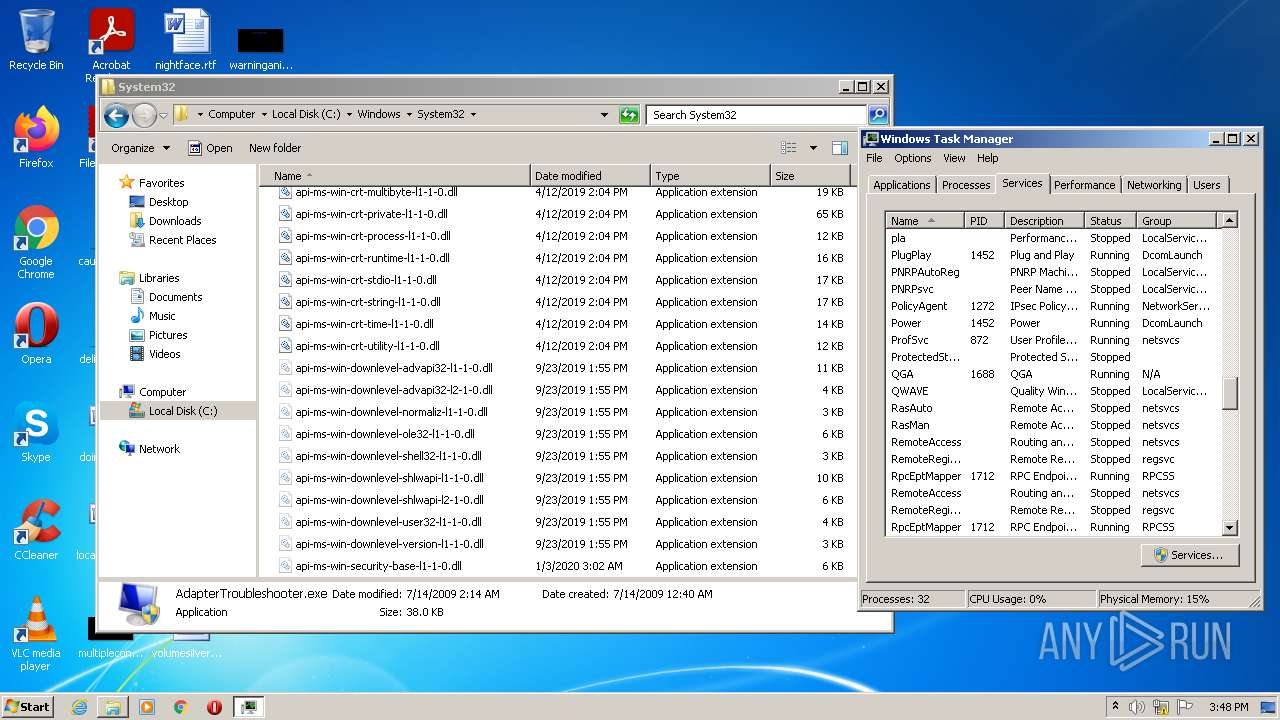
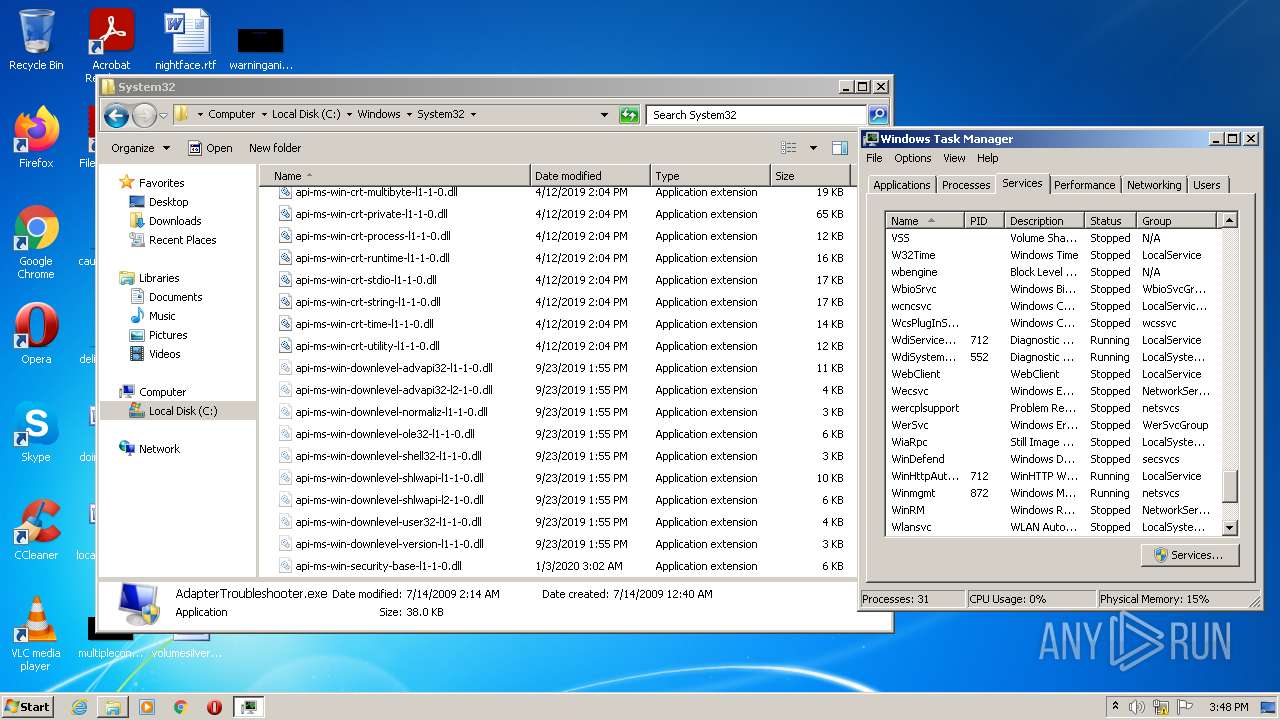
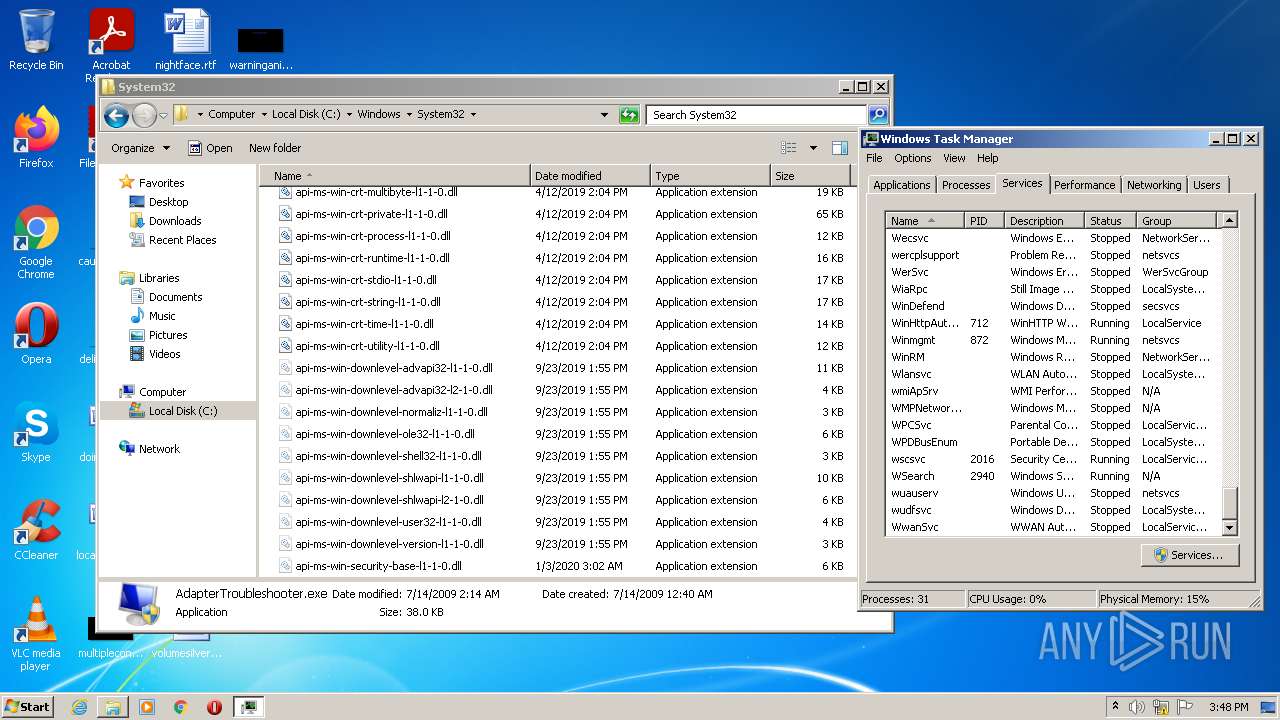
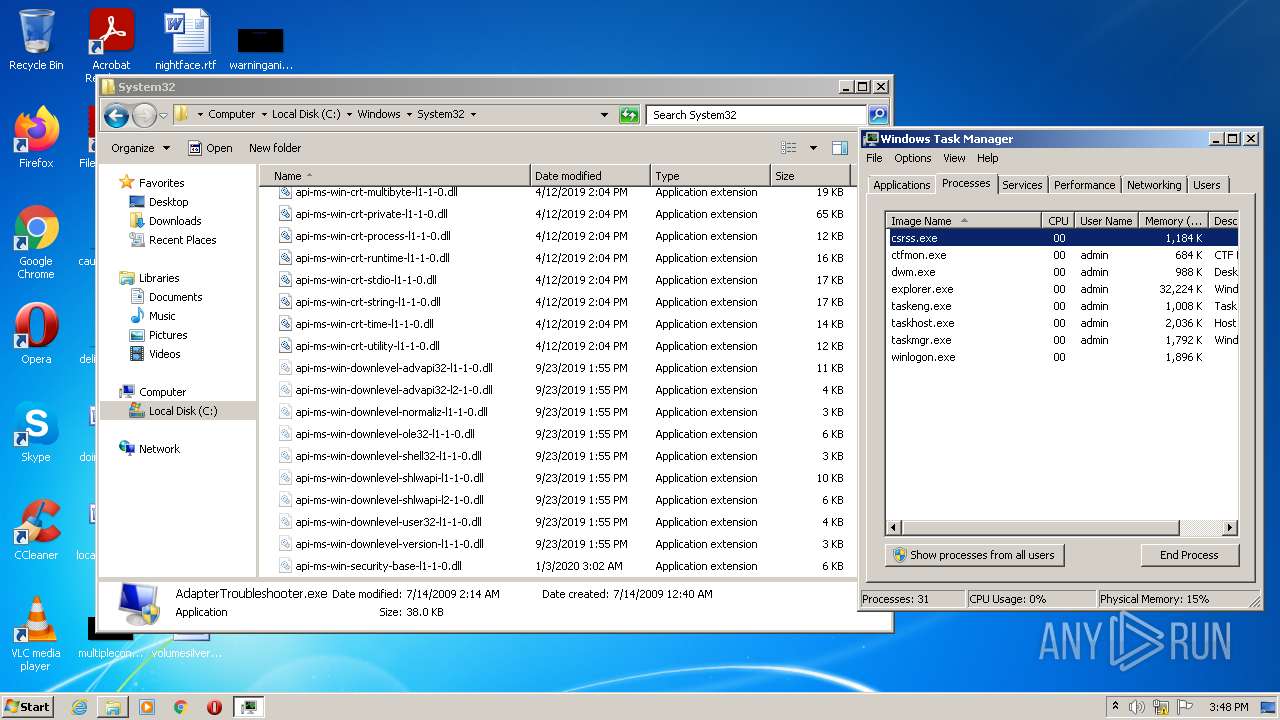
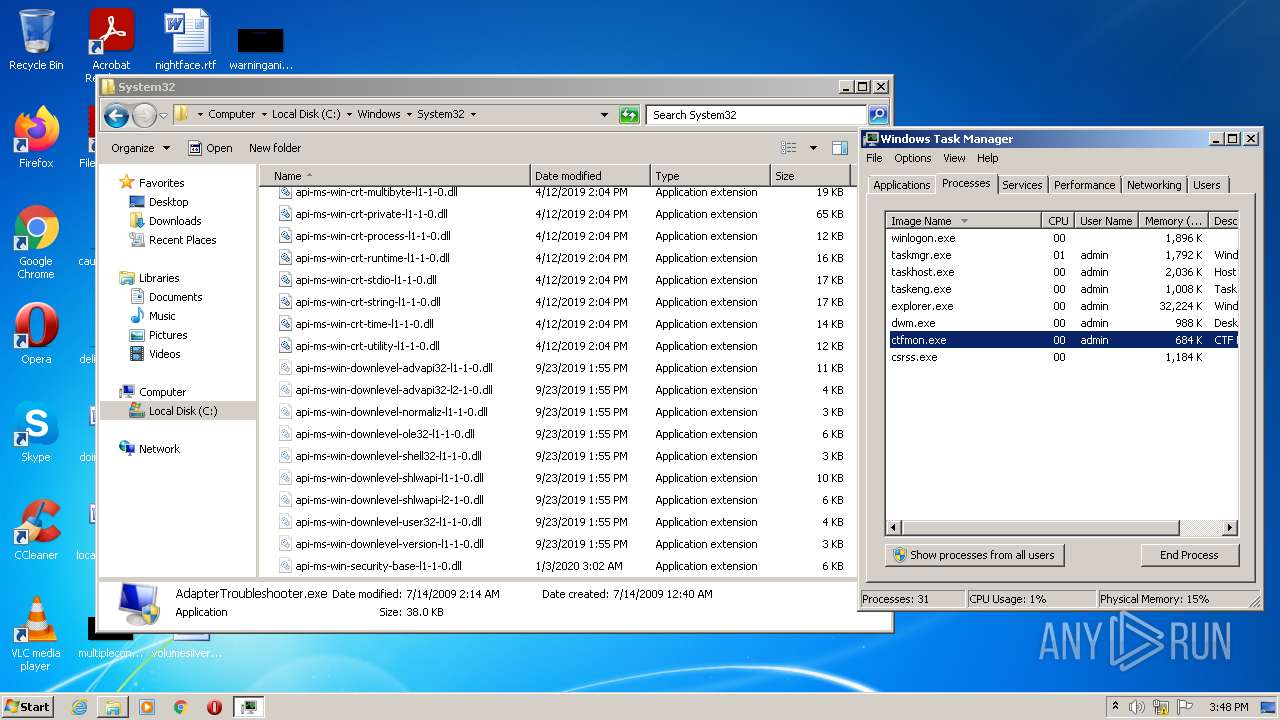
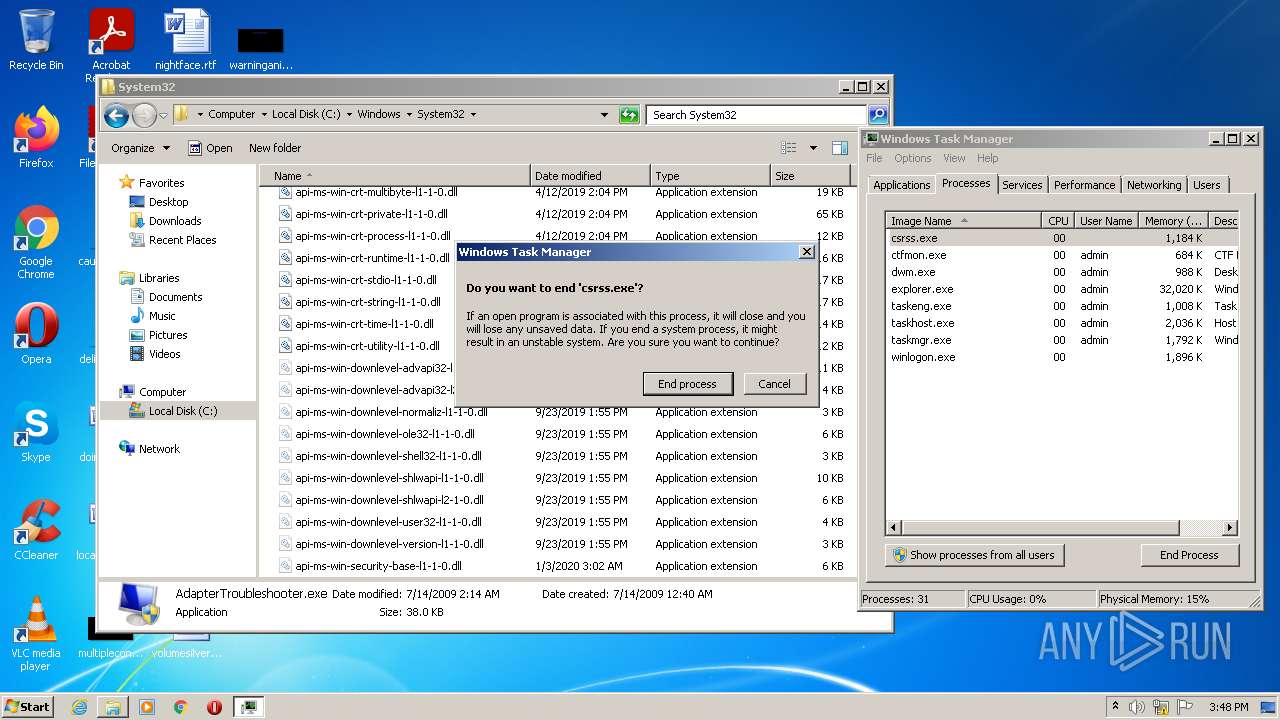
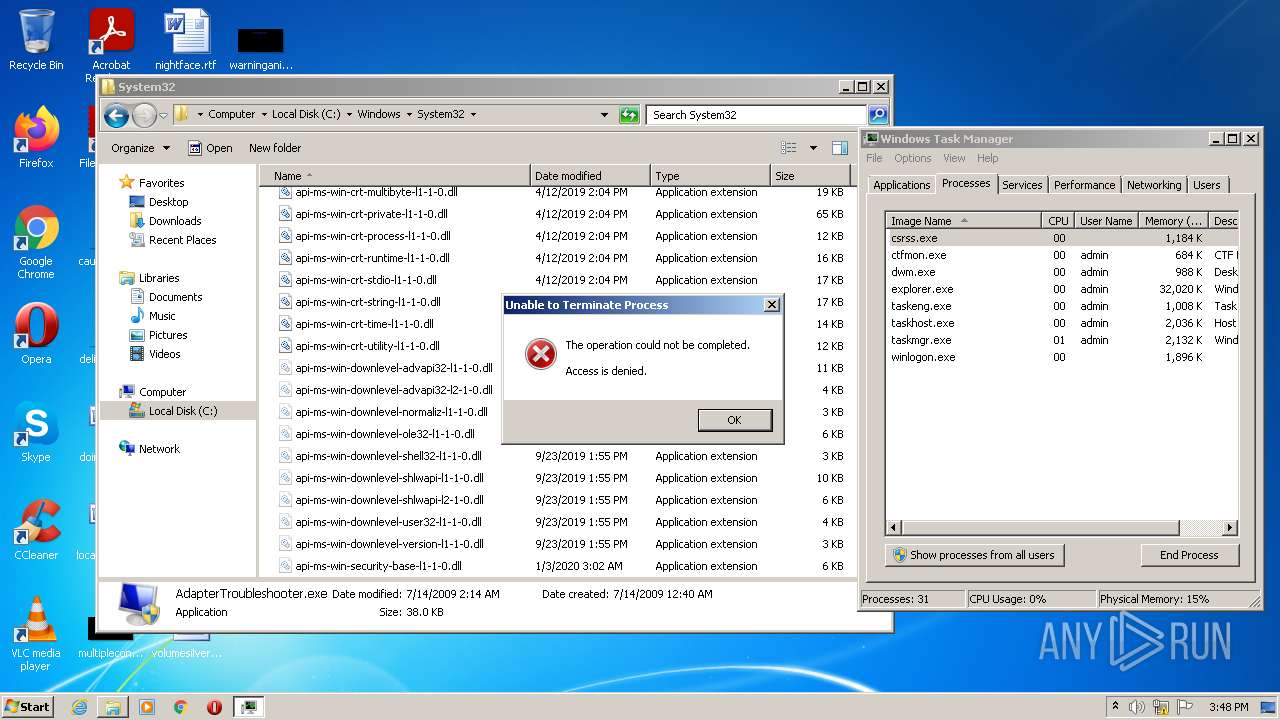
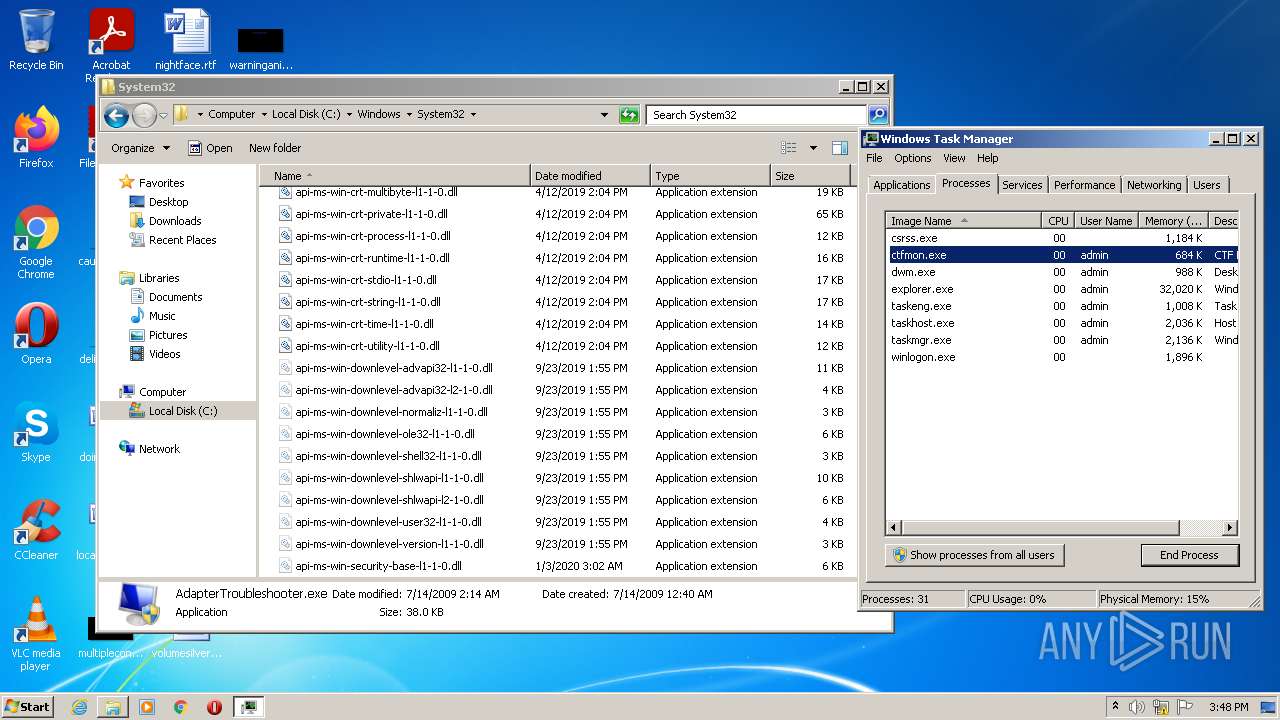
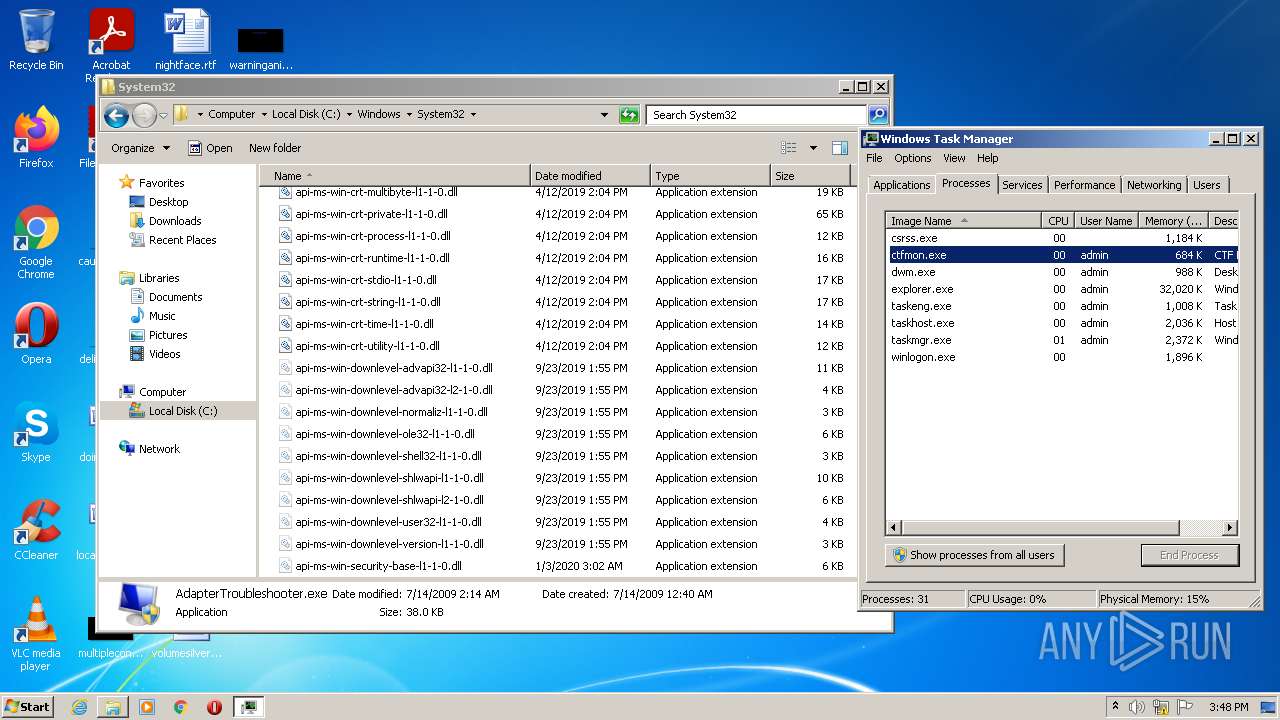
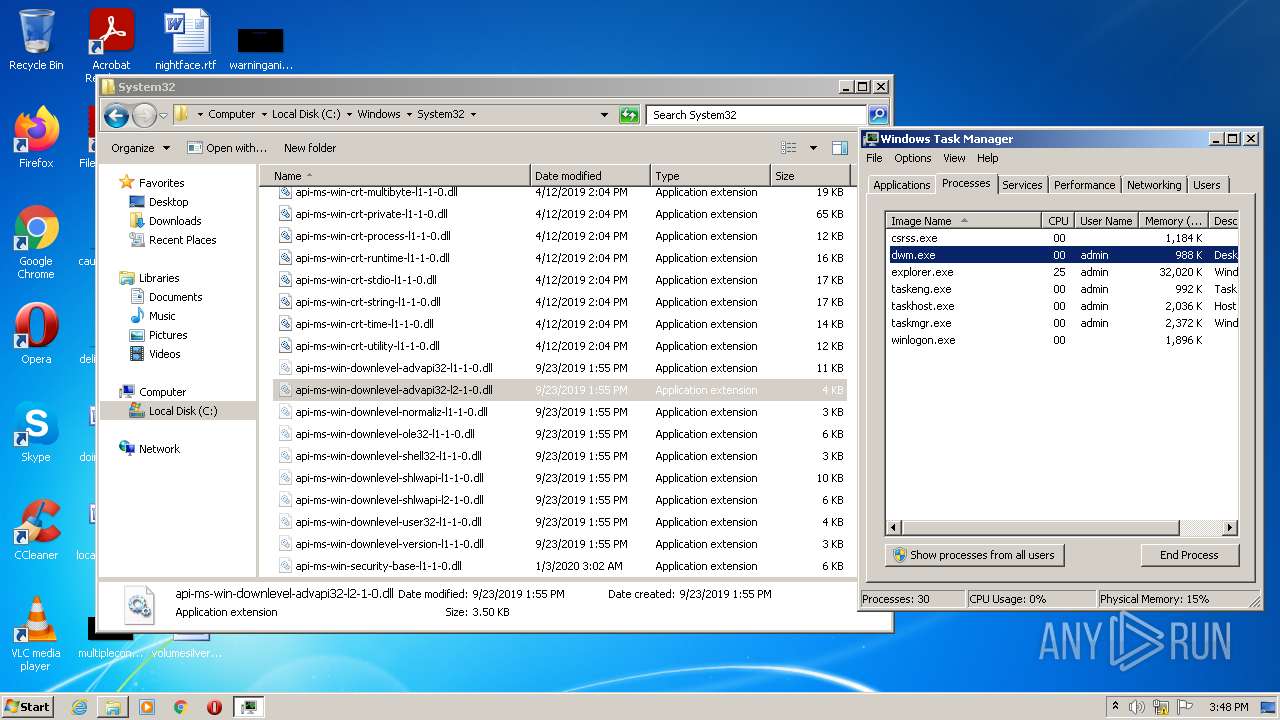
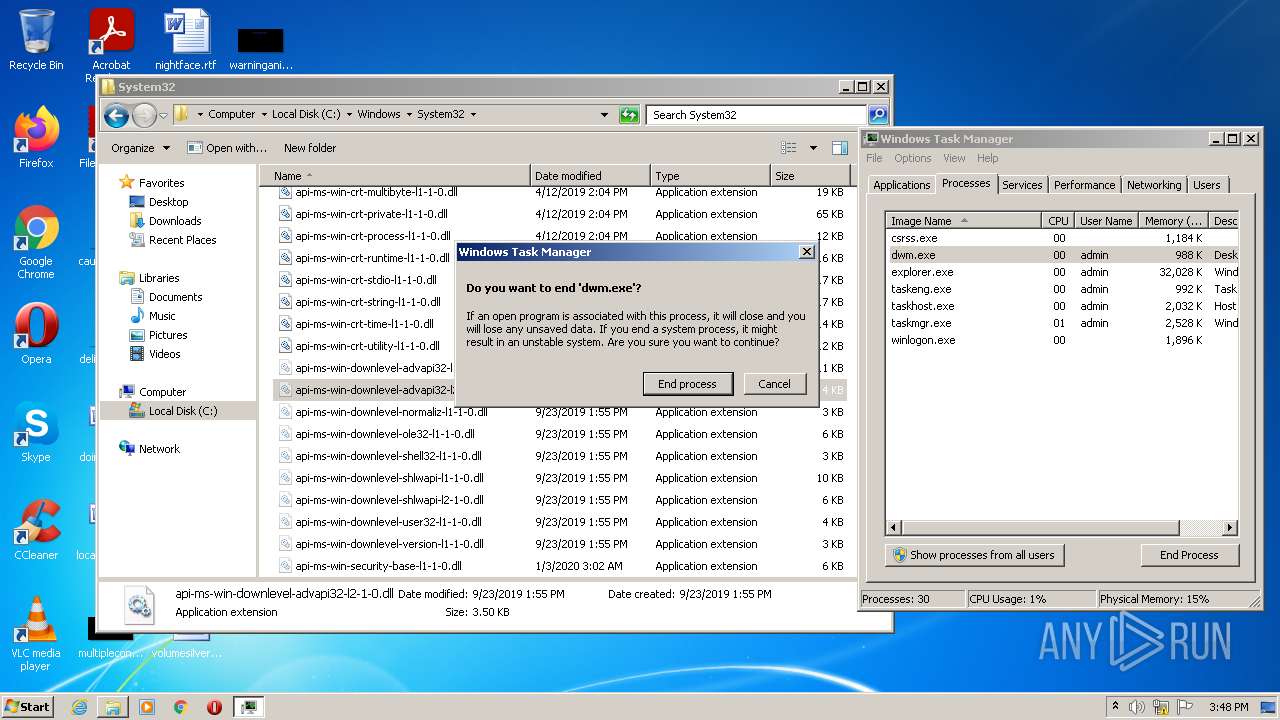
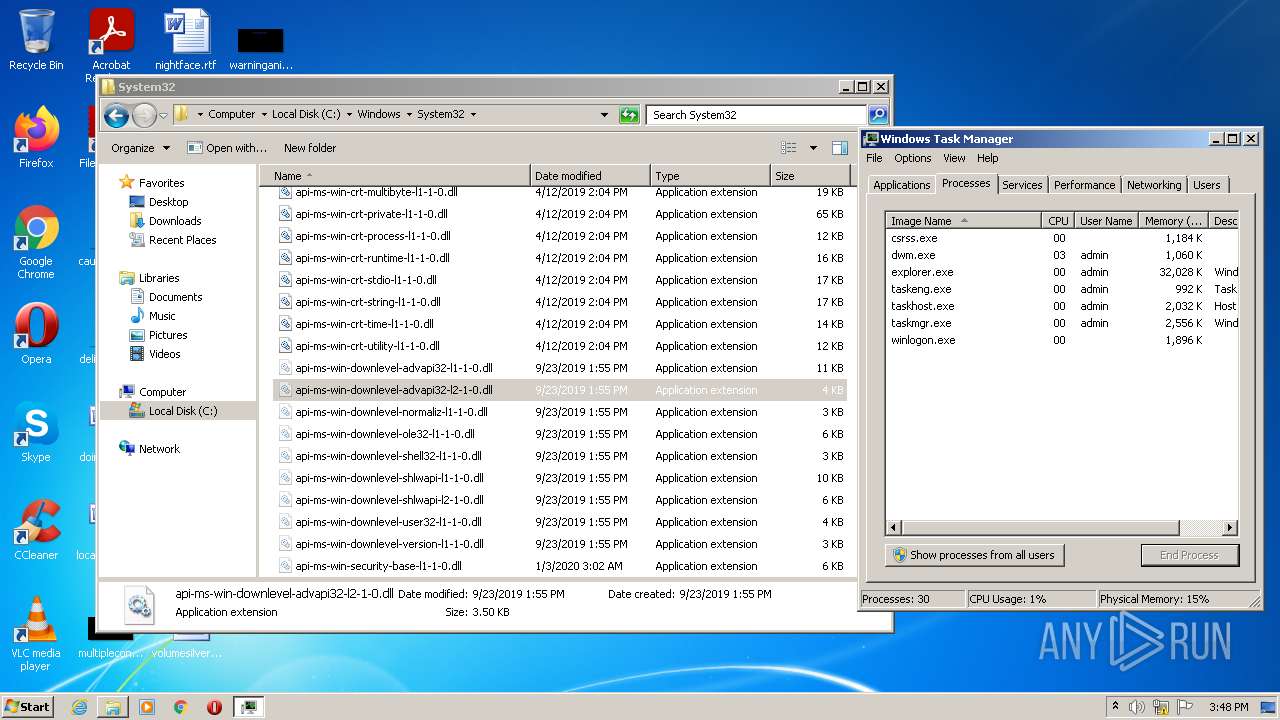
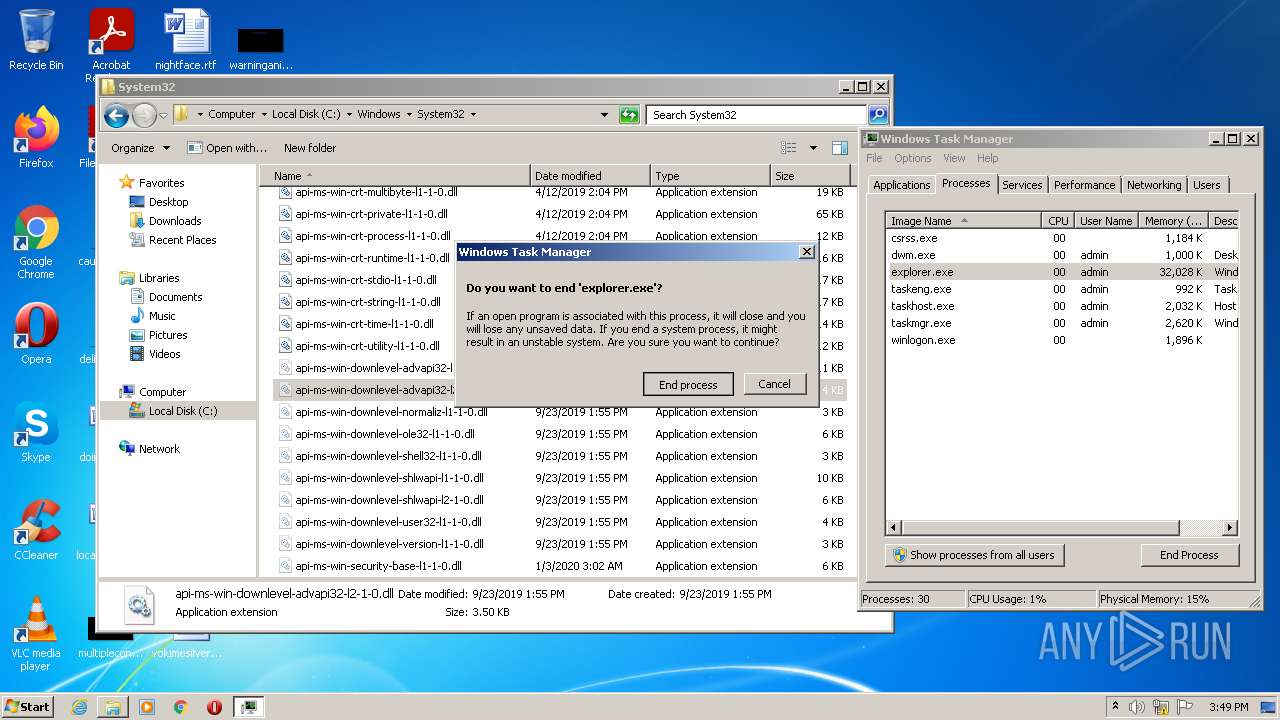
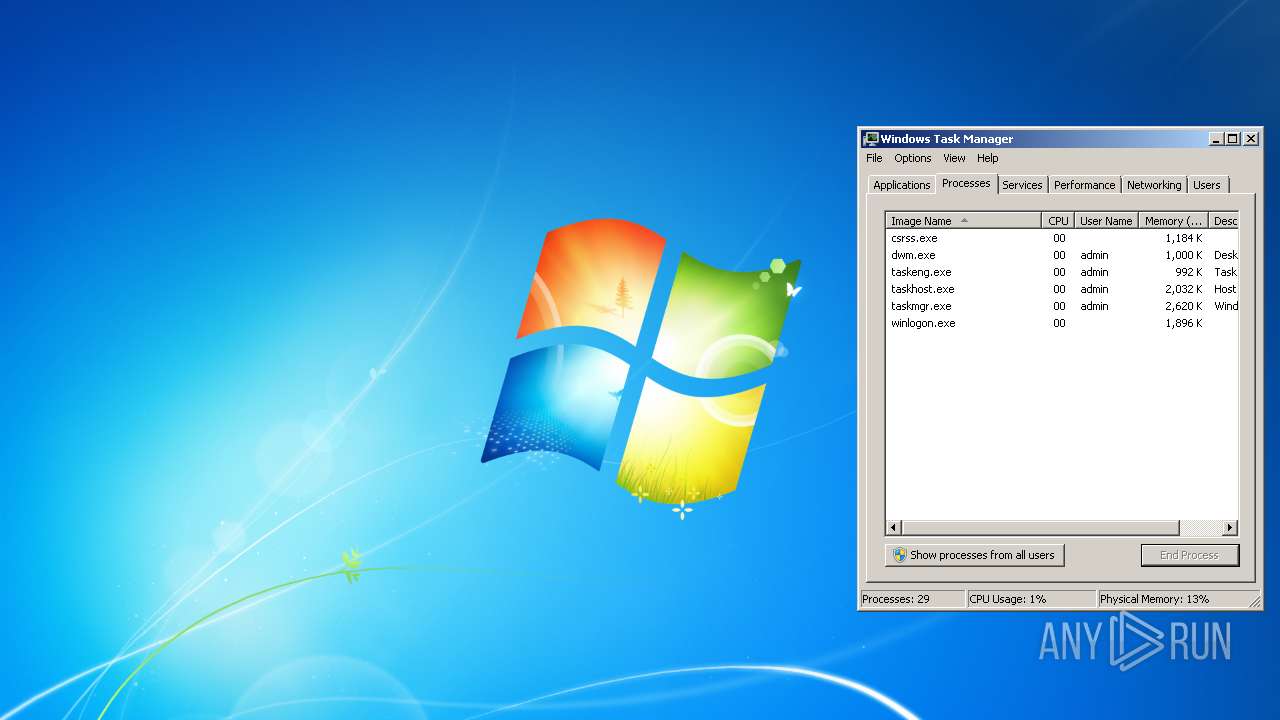
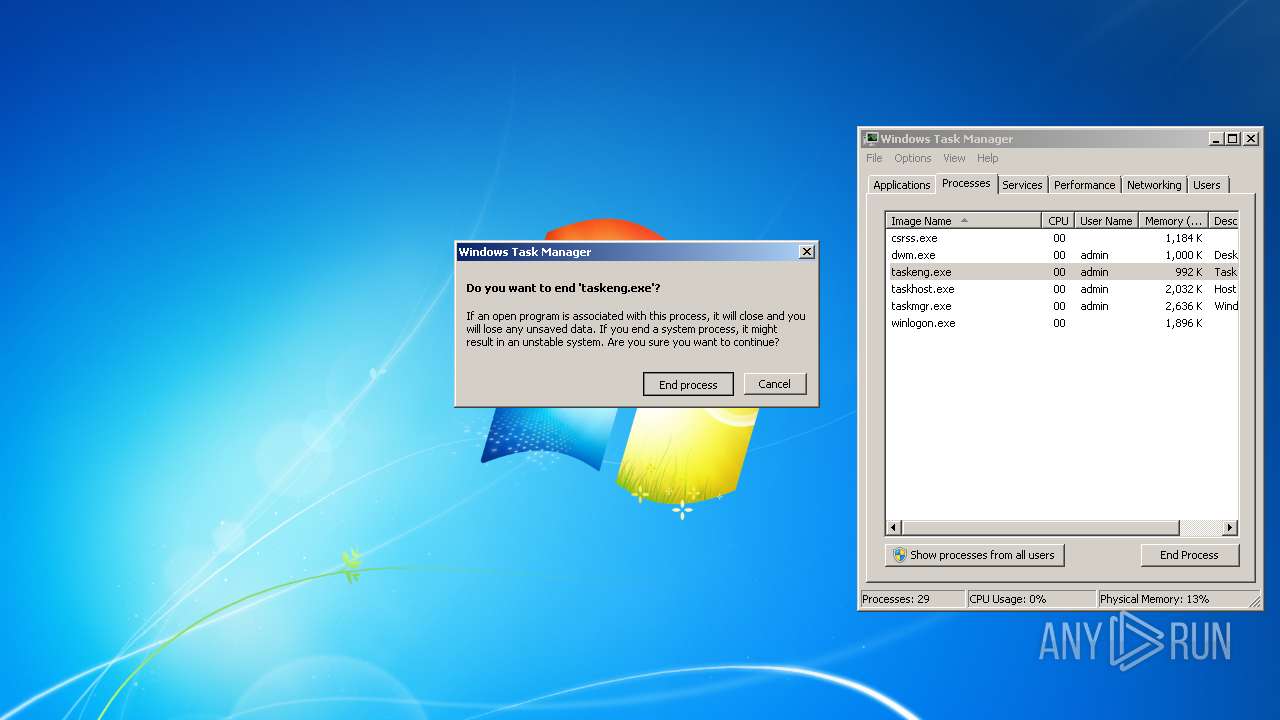
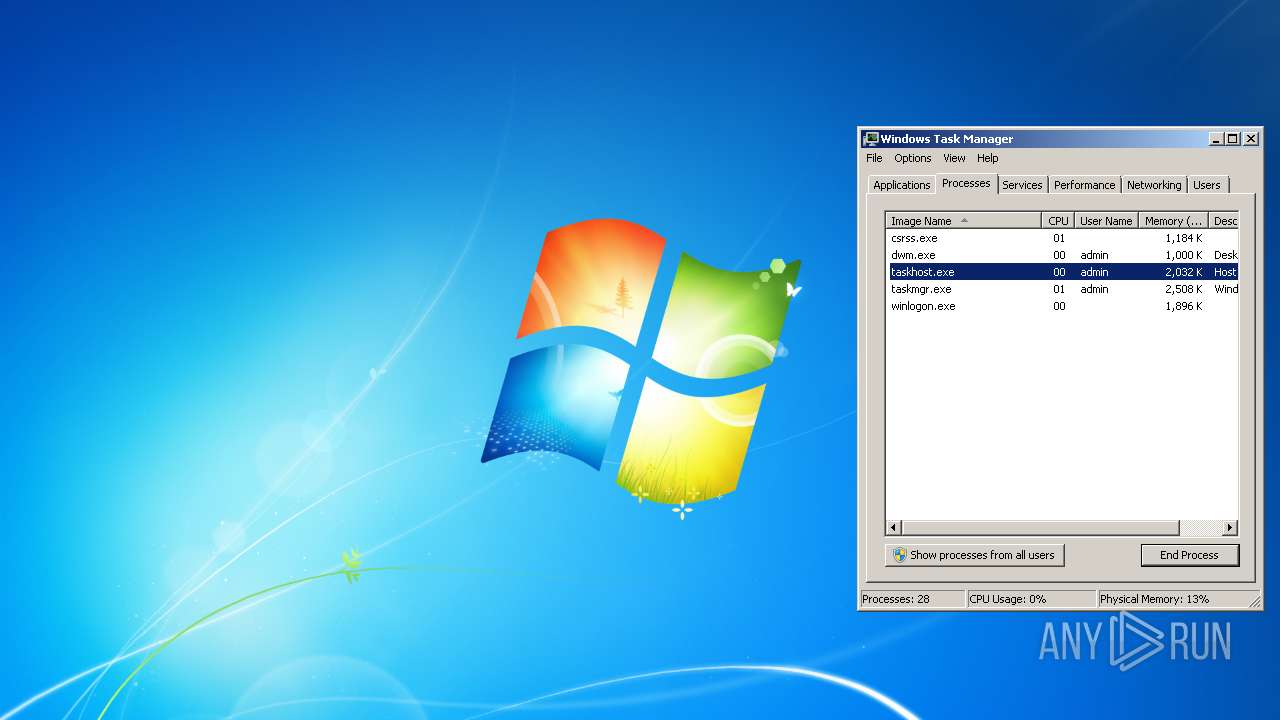
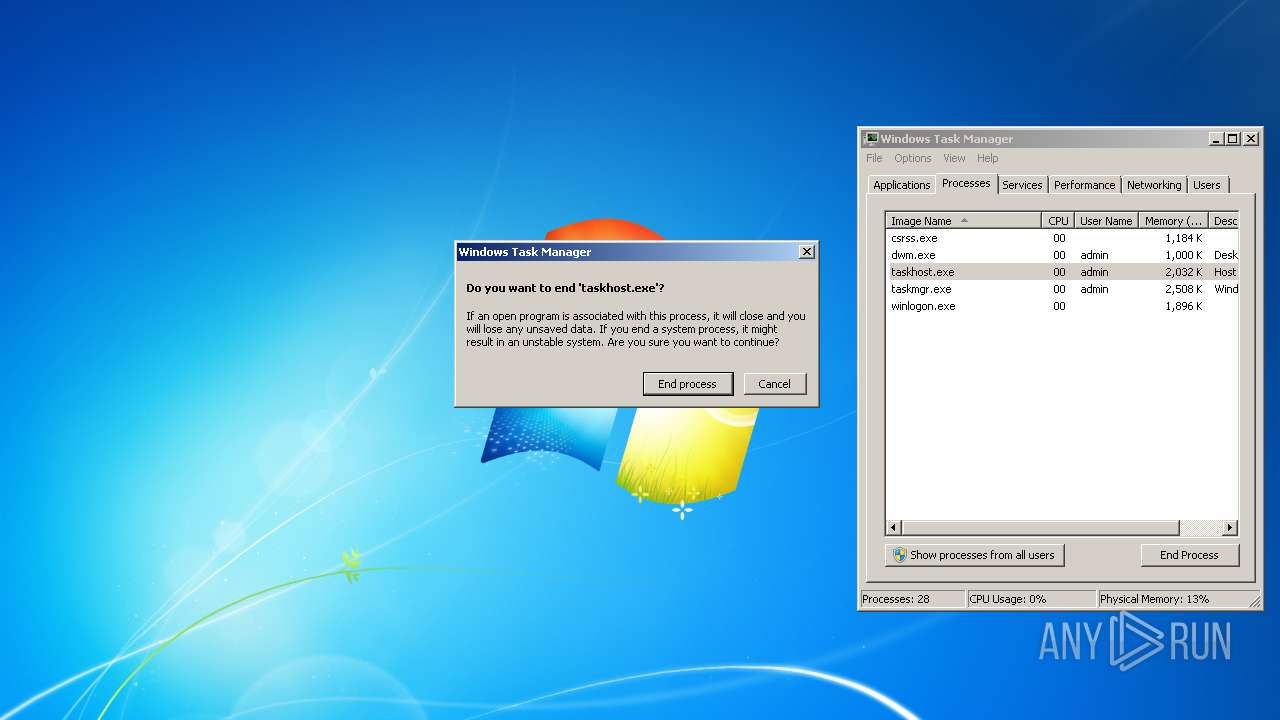
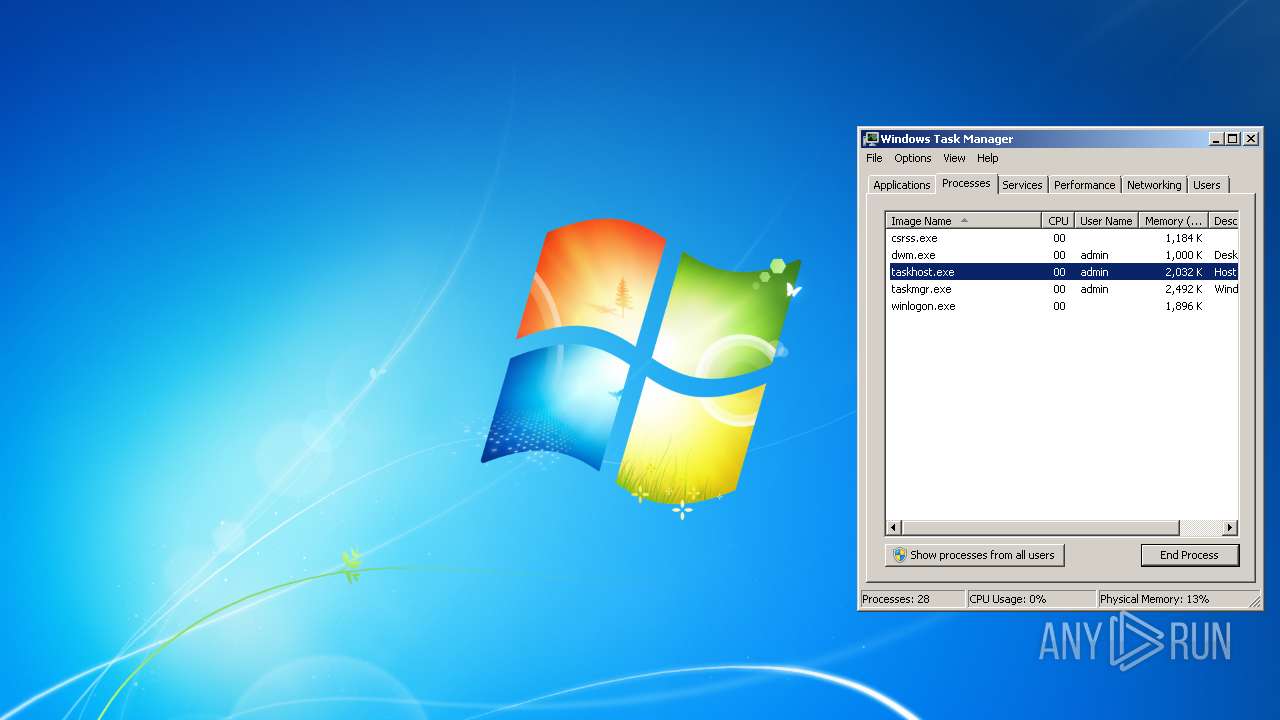
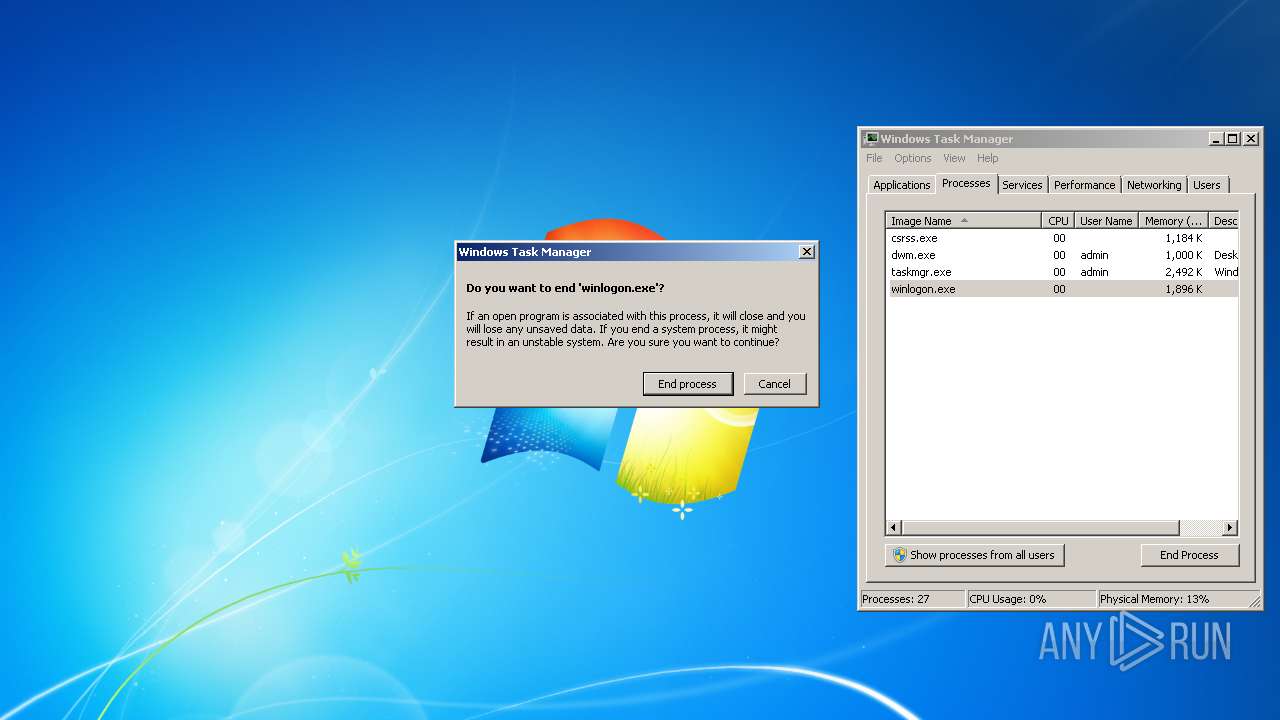
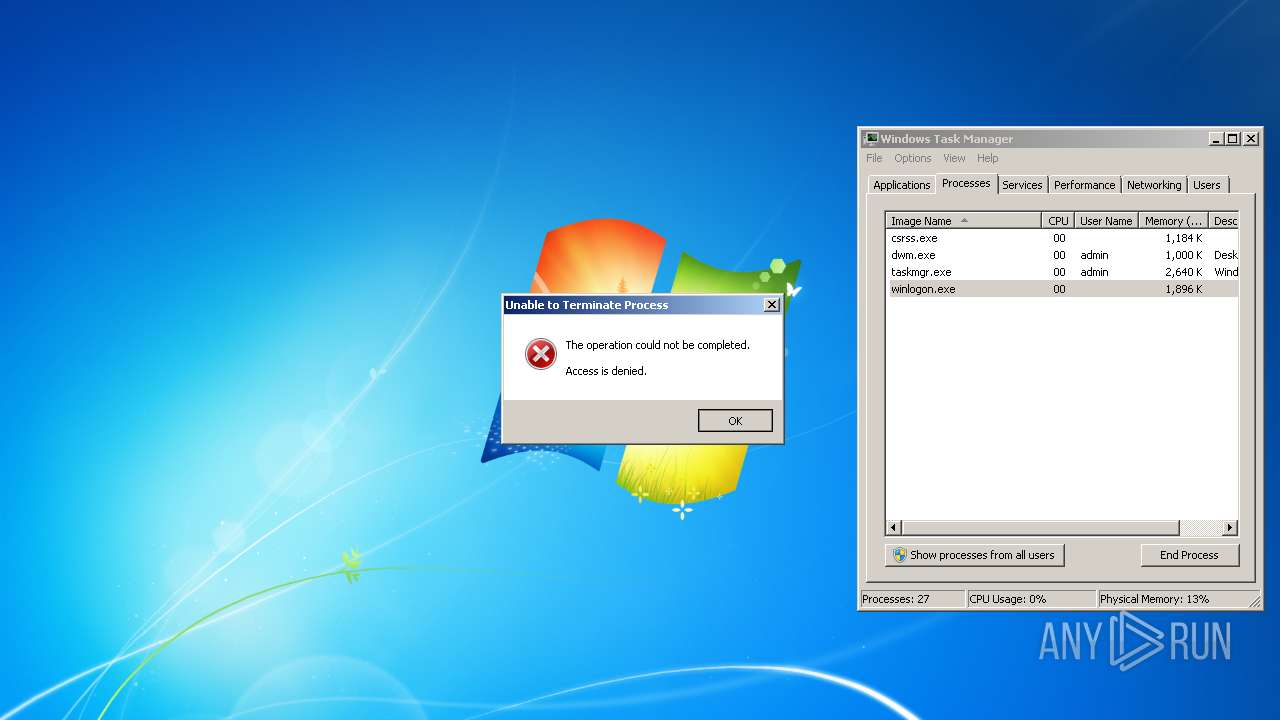
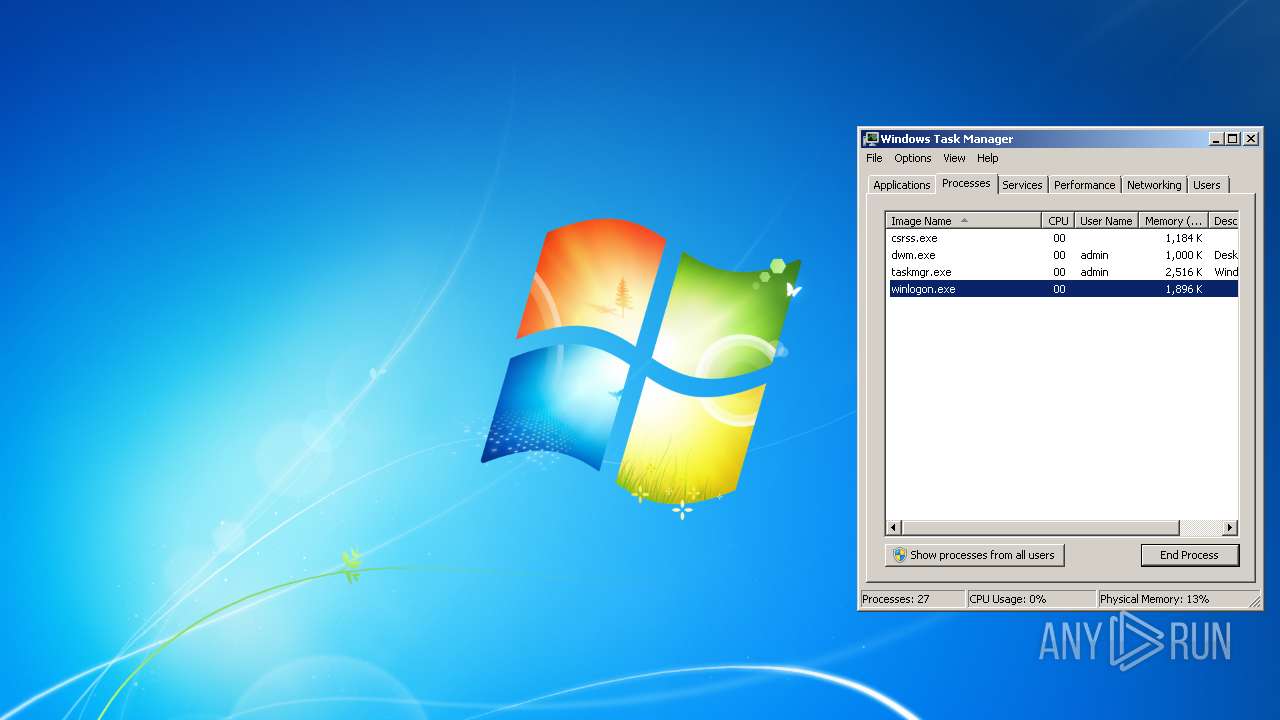
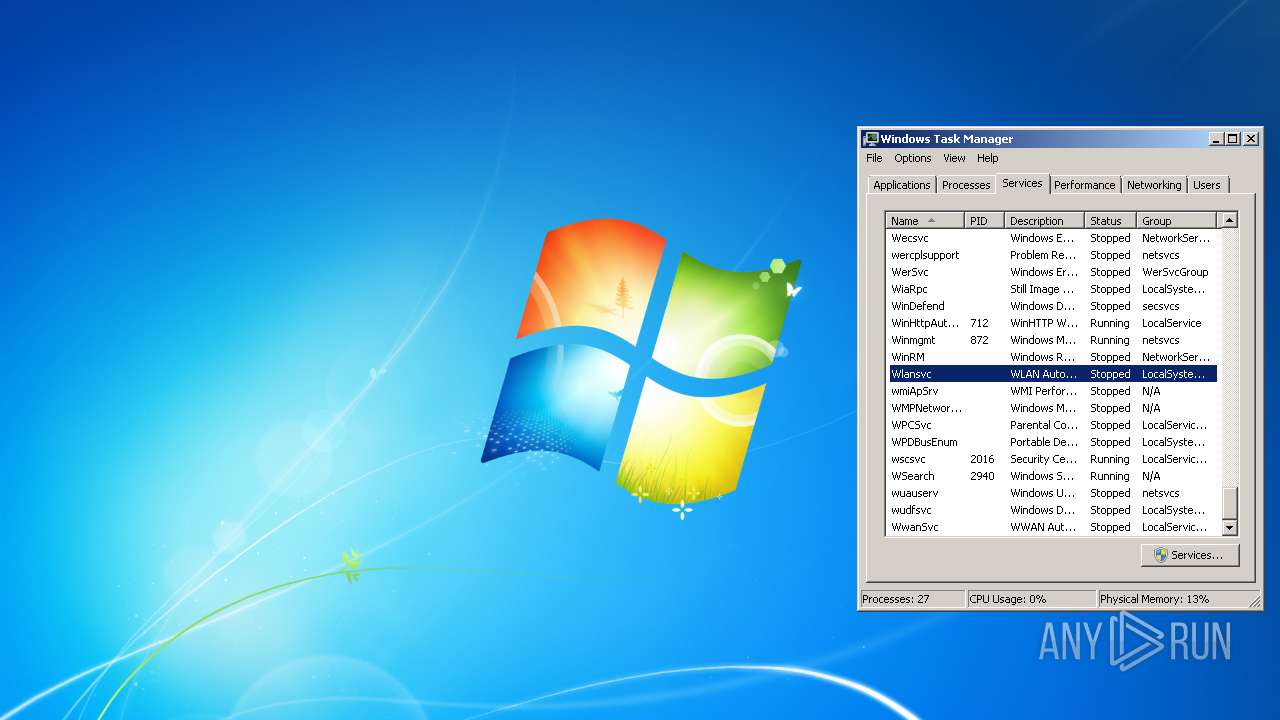
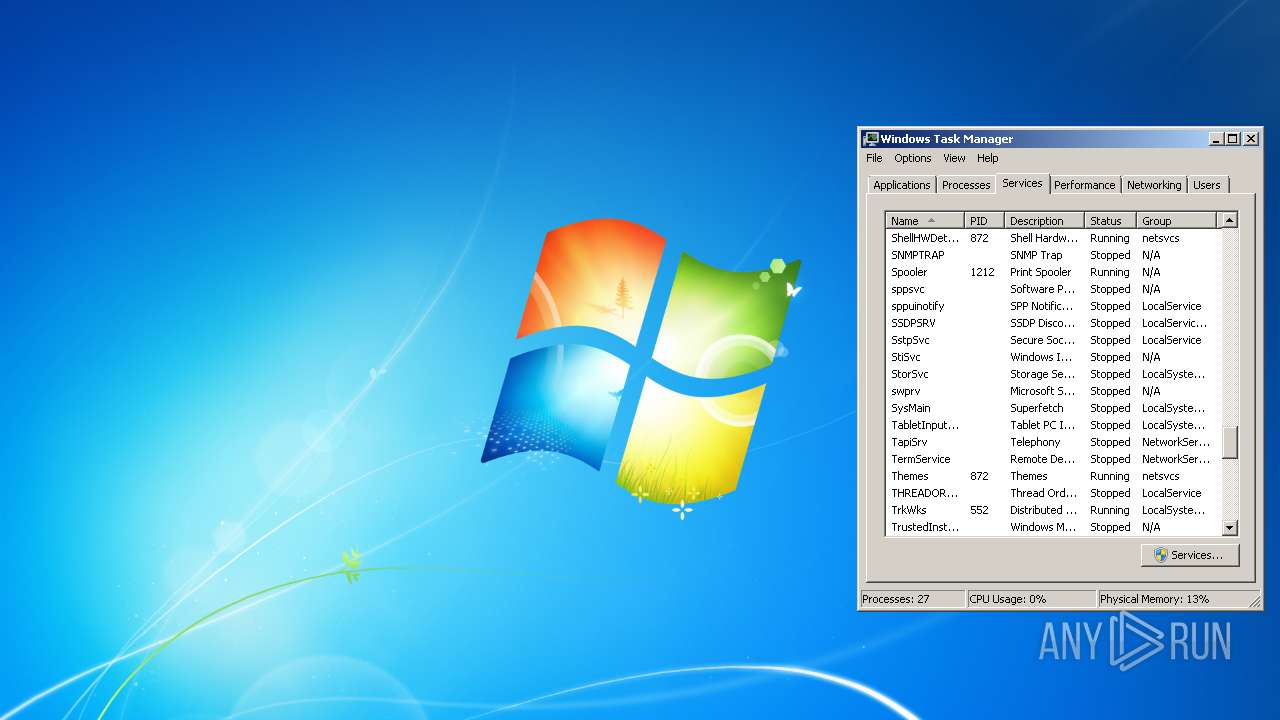
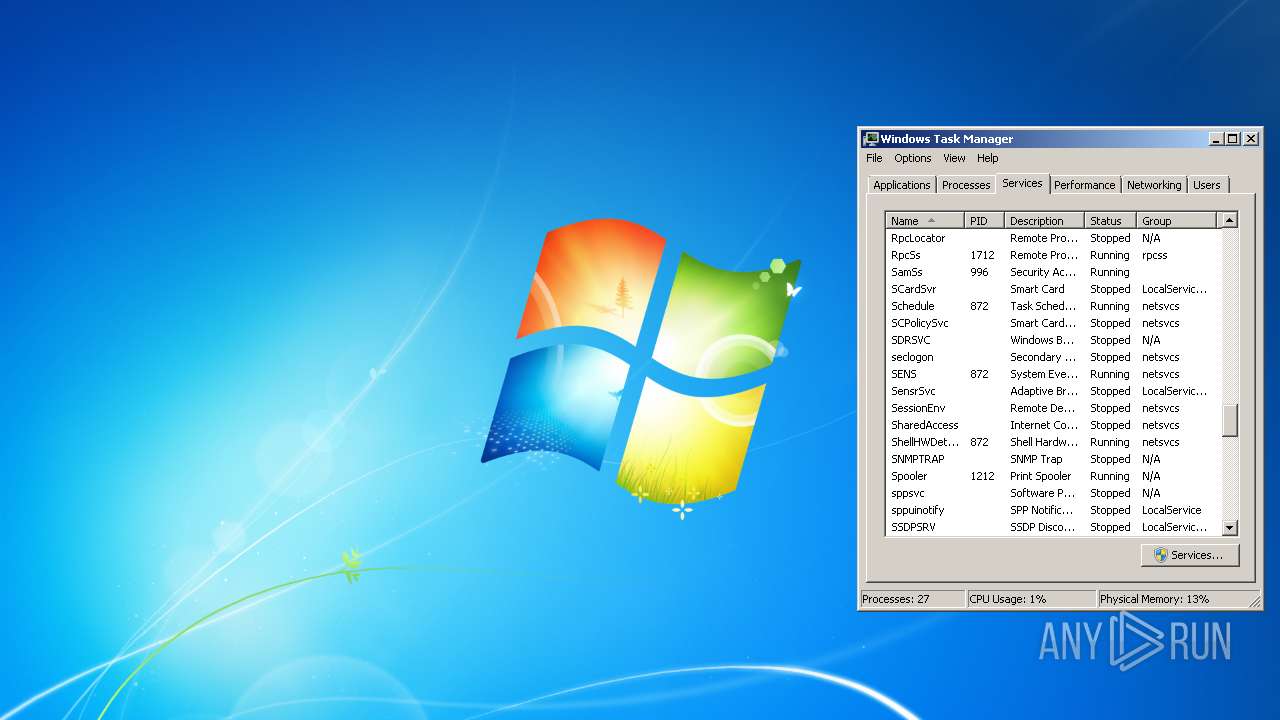
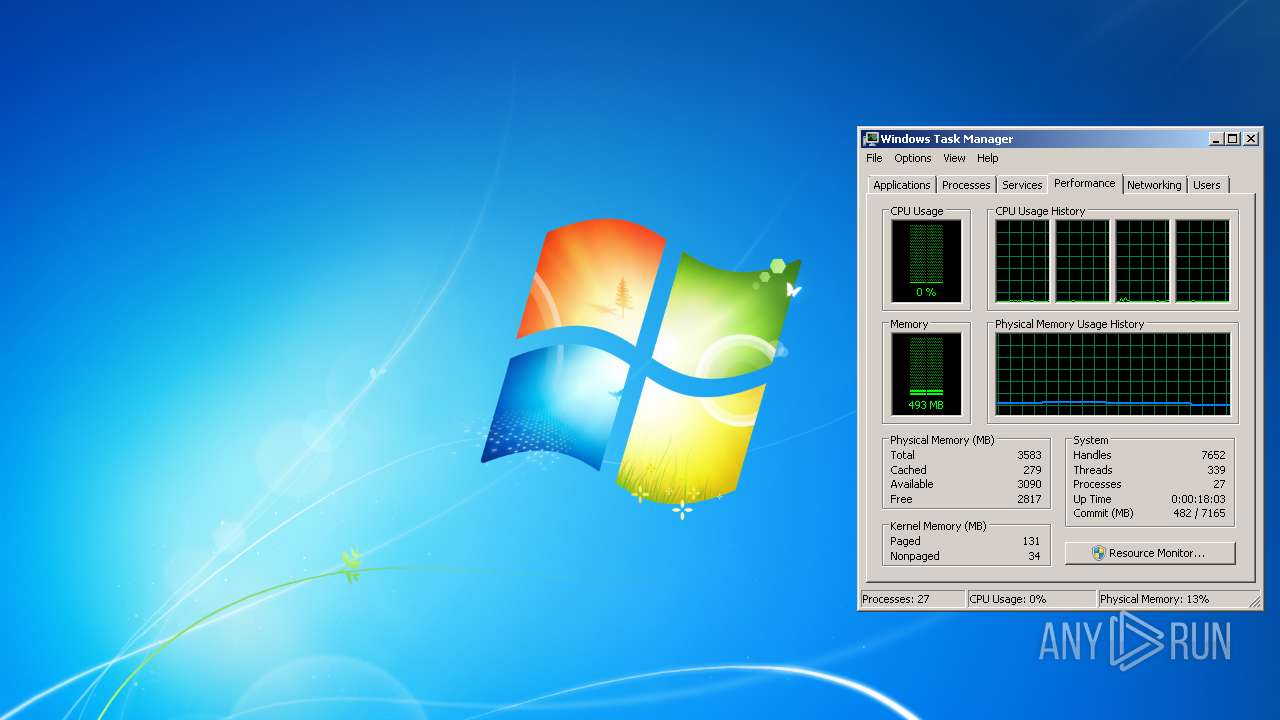
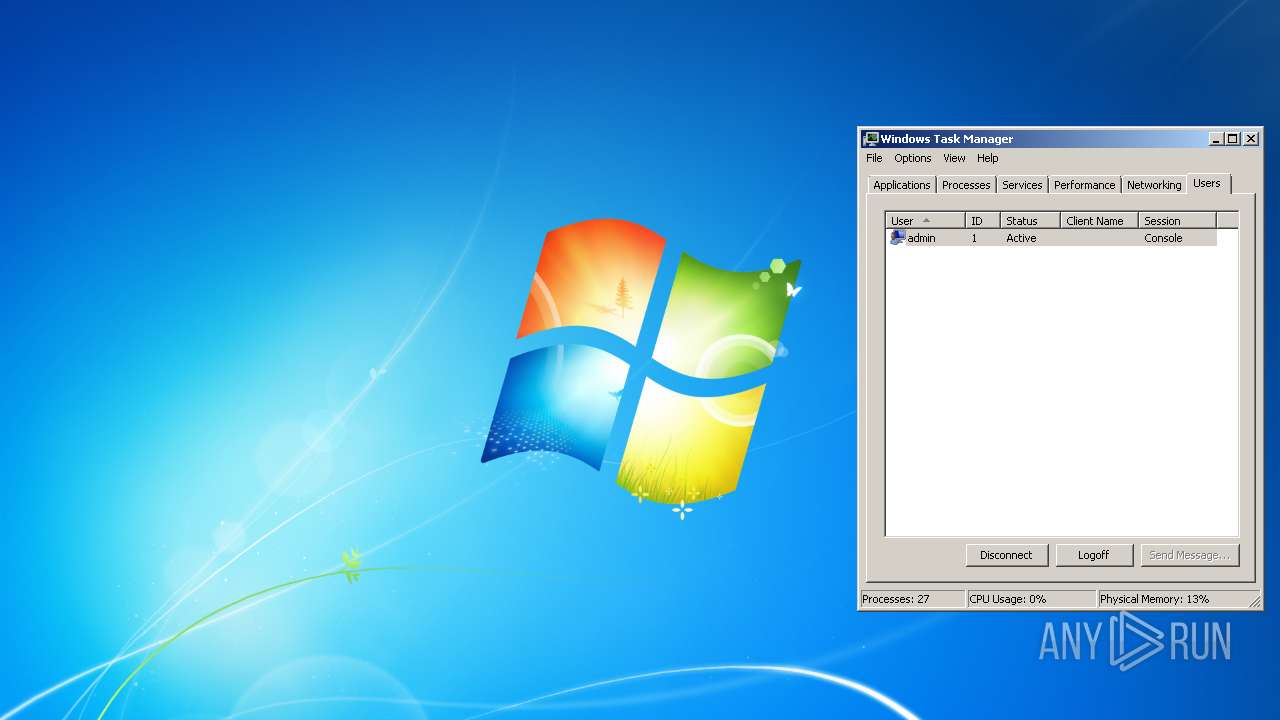
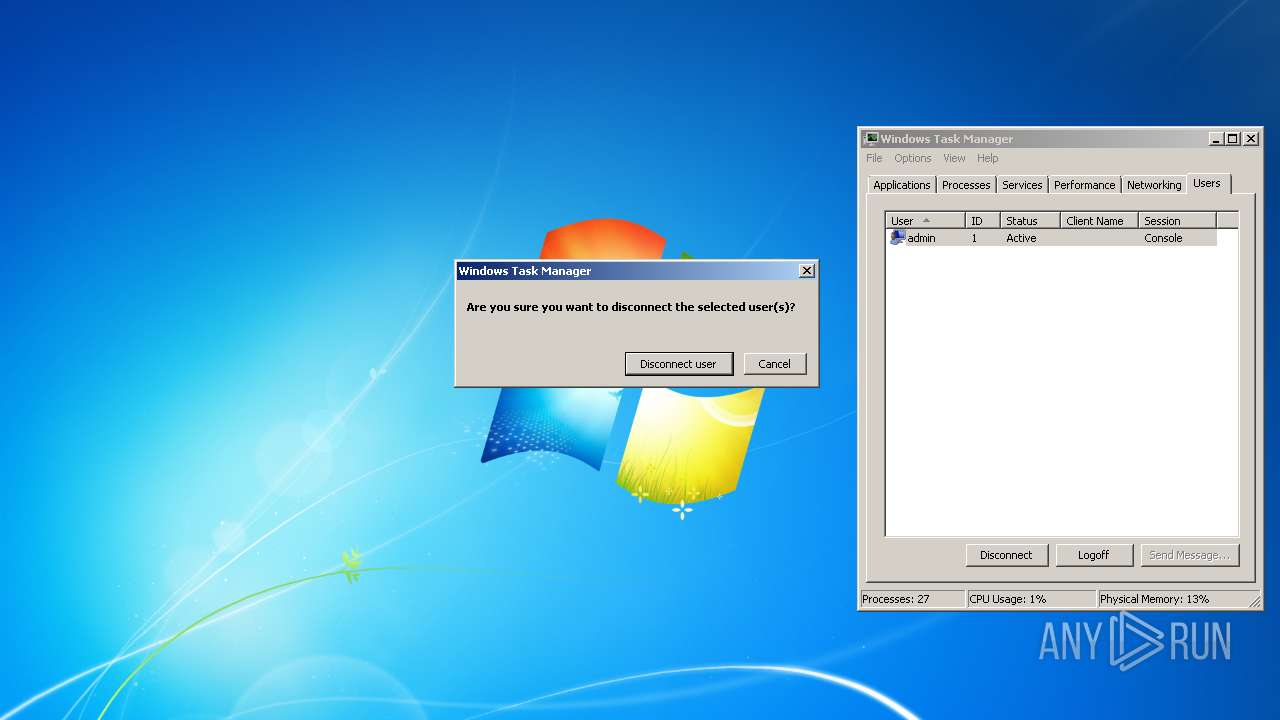
Manual execution by user
- taskmgr.exe (PID: 904)
- explorer.exe (PID: 1068)
- ie4uinit.exe (PID: 2816)
- unregmp2.exe (PID: 2080)
- ie4uinit.exe (PID: 2548)
- chrmstp.exe (PID: 3468)
- ie4uinit.exe (PID: 516)
- regsvr32.exe (PID: 2636)
- jusched.exe (PID: 1292)
- IMEKLMG.EXE (PID: 2428)
- explorer.exe (PID: 968)
- firefox.exe (PID: 1176)
- IMEKLMG.EXE (PID: 1996)
- CCleaner.exe (PID: 3428)
Reads the date of Windows installation
- iexplore.exe (PID: 3432)
- firefox.exe (PID: 2464)
Reads CPU info
- firefox.exe (PID: 2464)
Creates files in the program directory
- firefox.exe (PID: 2464)
Checks Windows Trust Settings
- pingsender.exe (PID: 1172)
- pingsender.exe (PID: 304)
- pingsender.exe (PID: 3748)
- CCleaner.exe (PID: 3428)
- CCleaner.exe (PID: 284)
Reads settings of System Certificates
- pingsender.exe (PID: 3748)
- pingsender.exe (PID: 1172)
- pingsender.exe (PID: 304)
- CCleaner.exe (PID: 3428)
- CCleaner.exe (PID: 284)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
110
Monitored processes
39
Malicious processes
7
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | "C:\Program Files\CCleaner\CCleaner.exe" /monitor | C:\Program Files\CCleaner\CCleaner.exe | CCleaner.exe | ||||||||||||
User: Administrator Company: Piriform Software Ltd Integrity Level: HIGH Description: CCleaner Exit code: 0 Version: 5.74.0.8198 Modules
| |||||||||||||||
| 304 | "C:\Program Files\Mozilla Firefox\pingsender.exe" https://incoming.telemetry.mozilla.org/submit/telemetry/72e952e3-24cc-4ba0-9fb8-b58d37f15abc/event/Firefox/83.0/release/20201112153044?v=4 C:\Users\Administrator\AppData\Roaming\Mozilla\Firefox\Profiles\9co9si08.default-release\saved-telemetry-pings\72e952e3-24cc-4ba0-9fb8-b58d37f15abc | C:\Program Files\Mozilla Firefox\pingsender.exe | firefox.exe | ||||||||||||
User: Administrator Company: Mozilla Foundation Integrity Level: MEDIUM Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 468 | "C:\Program Files\Google\Chrome\Application\86.0.4240.198\Installer\chrmstp.exe" --type=crashpad-handler /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler --database=C:\Windows\TEMP\Crashpad --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0x148,0x14c,0x150,0x11c,0x154,0x200fe8,0x200ff8,0x201004 | C:\Program Files\Google\Chrome\Application\86.0.4240.198\Installer\chrmstp.exe | — | chrmstp.exe | |||||||||||
User: Administrator Company: Google LLC Integrity Level: HIGH Description: Google Chrome Installer Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 496 | C:\Windows\system32\RunDll32.exe C:\Windows\system32\migration\WininetPlugin.dll,MigrateCacheForUser /m /0 | C:\Windows\system32\RunDll32.exe | — | rundll32.exe | |||||||||||
User: Administrator Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 516 | "C:\Windows\System32\ie4uinit.exe" -DisableSSL3 | C:\Windows\System32\ie4uinit.exe | — | Explorer.EXE | |||||||||||
User: Administrator Company: Microsoft Corporation Integrity Level: HIGH Description: IE Per-User Initialization Utility Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 572 | C:\Windows\system32\RunDll32.exe C:\Windows\system32\migration\WininetPlugin.dll,MigrateCacheForUser /m /0 | C:\Windows\system32\RunDll32.exe | — | rundll32.exe | |||||||||||
User: Administrator Company: Microsoft Corporation Integrity Level: LOW Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 904 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 968 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: Administrator Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1068 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1172 | "C:\Program Files\Mozilla Firefox\pingsender.exe" https://incoming.telemetry.mozilla.org/submit/telemetry/1fb35033-5f9a-4f9a-85cb-a4c34898253f/first-shutdown/Firefox/83.0/release/20201112153044?v=4 C:\Users\Administrator\AppData\Roaming\Mozilla\Firefox\Profiles\9co9si08.default-release\saved-telemetry-pings\1fb35033-5f9a-4f9a-85cb-a4c34898253f | C:\Program Files\Mozilla Firefox\pingsender.exe | firefox.exe | ||||||||||||
User: Administrator Company: Mozilla Foundation Integrity Level: MEDIUM Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
Total events
58 685
Read events
55 700
Write events
1 698
Delete events
1 287
Modification events
| (PID) Process: | (3432) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3432) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3432) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30937401 | |||
| (PID) Process: | (3432) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3432) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30937401 | |||
| (PID) Process: | (3432) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3432) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3432) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3432) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3432) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
10
Suspicious files
275
Text files
178
Unknown types
87
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 496 | RunDll32.exe | C:\Users\Administrator\AppData\Local\Microsoft\Feeds Cache\U4H6UN70\fwlink[1] | — | |
MD5:— | SHA256:— | |||
| 496 | RunDll32.exe | C:\Users\Administrator\AppData\Local\Microsoft\Feeds Cache\17SH7JUP\fwlink[1] | — | |
MD5:— | SHA256:— | |||
| 496 | RunDll32.exe | C:\Users\Administrator\AppData\Local\Microsoft\Feeds Cache\DYV61OEO\fwlink[1] | — | |
MD5:— | SHA256:— | |||
| 496 | RunDll32.exe | C:\Users\Administrator\AppData\Local\Microsoft\Feeds Cache\UHGTR186\fwlink[1] | — | |
MD5:— | SHA256:— | |||
| 496 | RunDll32.exe | C:\Users\Administrator\AppData\Local\Microsoft\Feeds Cache\U4H6UN70\fwlink[2] | — | |
MD5:— | SHA256:— | |||
| 496 | RunDll32.exe | C:\Users\Administrator\AppData\Local\Microsoft\Feeds Cache\17SH7JUP\fwlink[2] | — | |
MD5:— | SHA256:— | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{D4EA05E7-7D2C-11EC-BB61-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 3432 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\{D4EA05E8-7D2C-11EC-BB61-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 2816 | ie4uinit.exe | C:\Users\Administrator\AppData\Local\Microsoft\Internet Explorer\Tiles\pin9728060290\msapplication.xml | xml | |
MD5:— | SHA256:— | |||
| 2816 | ie4uinit.exe | C:\Windows\INF\setupapi.app.log | ini | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
31
TCP/UDP connections
64
DNS requests
102
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2464 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2464 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2464 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2464 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2464 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2464 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2464 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2464 | firefox.exe | POST | 200 | 2.16.186.27:80 | http://r3.o.lencr.org/ | unknown | der | 503 b | shared |
2464 | firefox.exe | POST | 200 | 2.16.186.27:80 | http://r3.o.lencr.org/ | unknown | der | 503 b | shared |
2464 | firefox.exe | POST | 200 | 2.16.186.27:80 | http://r3.o.lencr.org/ | unknown | der | 503 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2068 | iexplore.exe | 142.250.181.228:443 | www.google.com | Google Inc. | US | whitelisted |
2464 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | — | US | whitelisted |
2464 | firefox.exe | 18.66.139.17:443 | content-signature-2.cdn.mozilla.net | Massachusetts Institute of Technology | US | suspicious |
2464 | firefox.exe | 13.32.119.185:443 | www.mozilla.org | Amazon.com, Inc. | US | suspicious |
2464 | firefox.exe | 44.229.226.207:443 | accounts.firefox.com | University of California, San Diego | US | unknown |
2464 | firefox.exe | 34.120.208.123:443 | incoming.telemetry.mozilla.org | — | US | malicious |
2464 | firefox.exe | 18.66.139.84:443 | firefox.settings.services.mozilla.com | Massachusetts Institute of Technology | US | unknown |
2464 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2464 | firefox.exe | 34.213.76.57:443 | shavar.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2464 | firefox.exe | 35.163.112.241:443 | location.services.mozilla.com | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| malicious |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
www.mozilla.org |
| whitelisted |
www.mozorg.moz.works |
| suspicious |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
firefox.settings.services.mozilla.com |
| whitelisted |
accounts.firefox.com |
| whitelisted |
incoming.telemetry.mozilla.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2464 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
2464 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
3428 | CCleaner.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
284 | CCleaner.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |