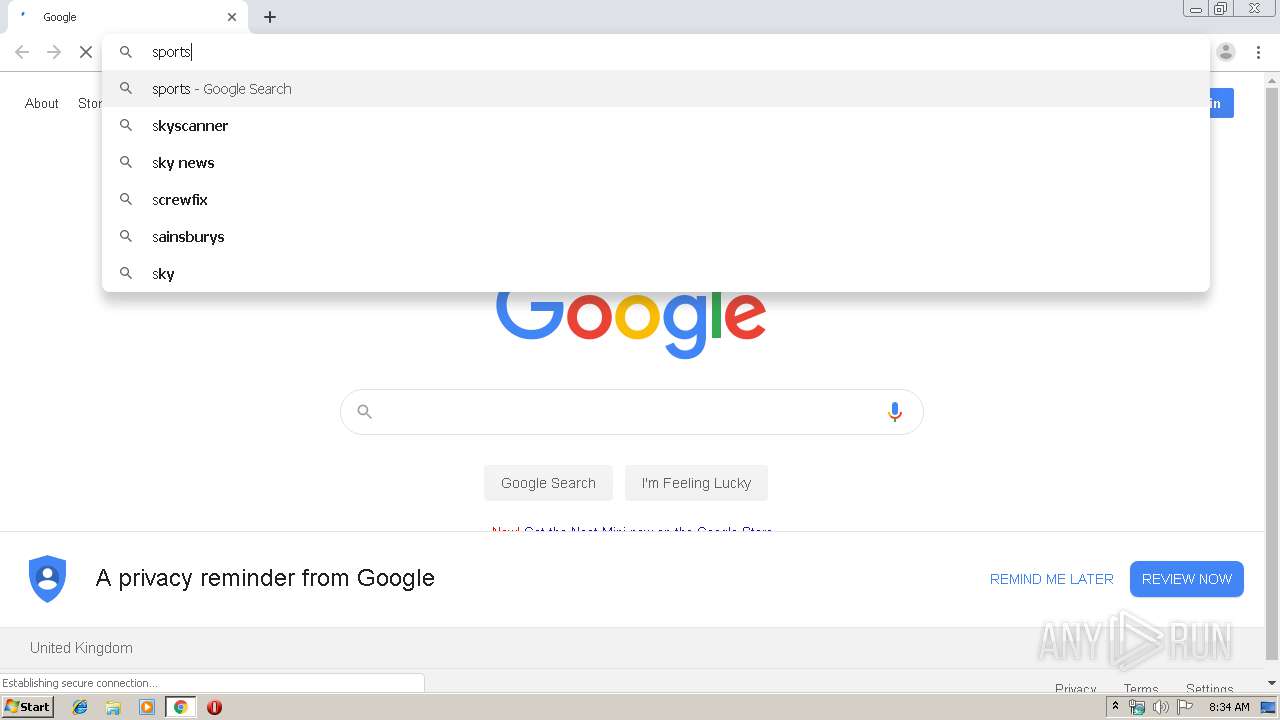
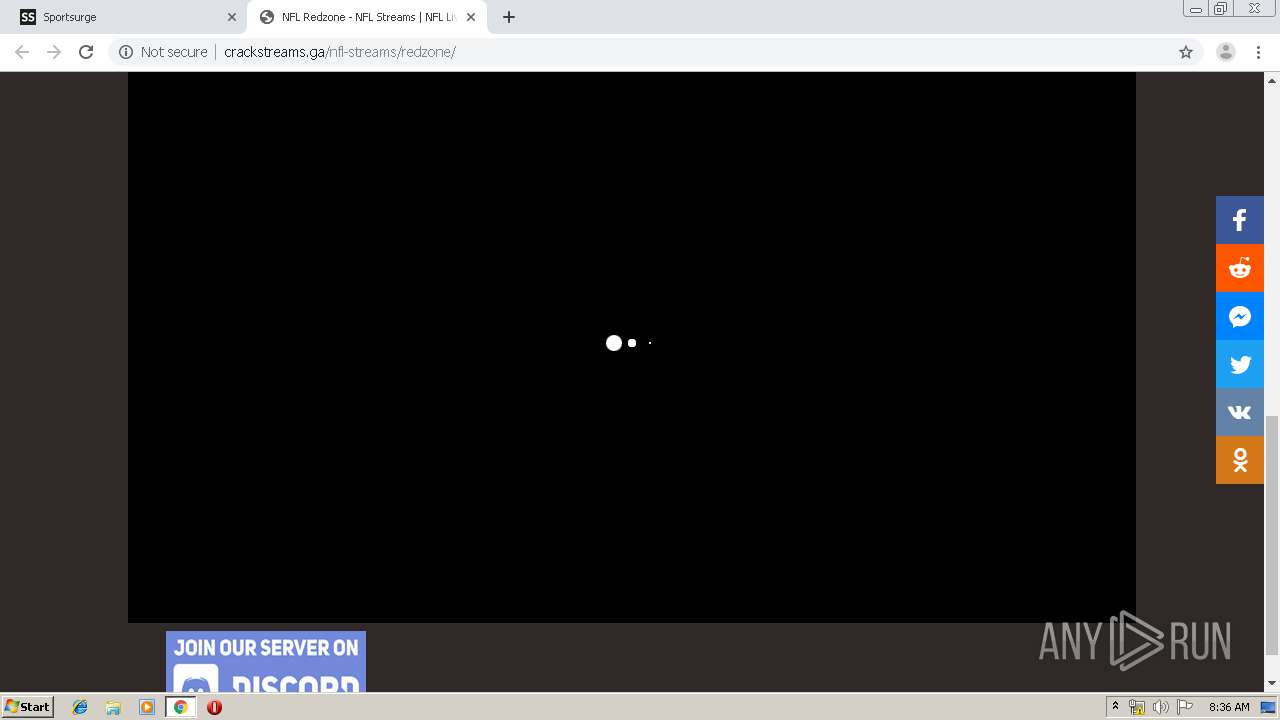
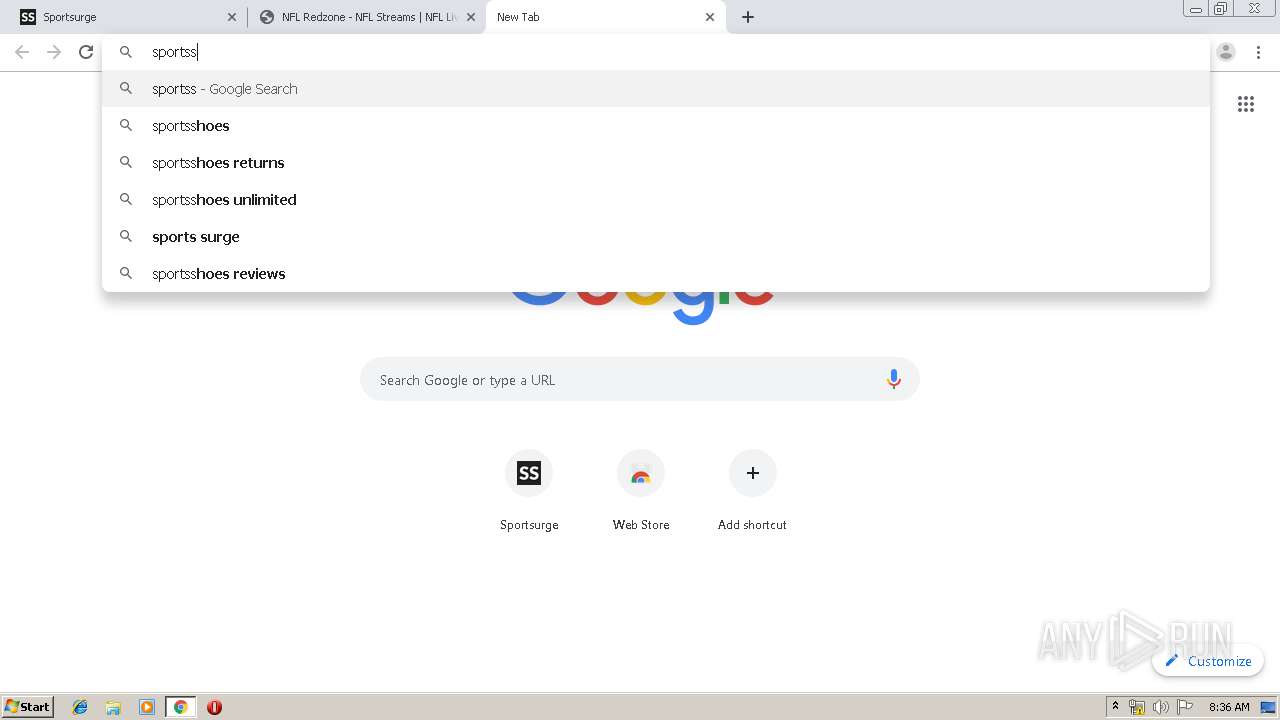
| URL: | https://www.google.com |
| Full analysis: | https://app.any.run/tasks/84dc5bbe-e545-4d58-882f-597f11ad2b14 |
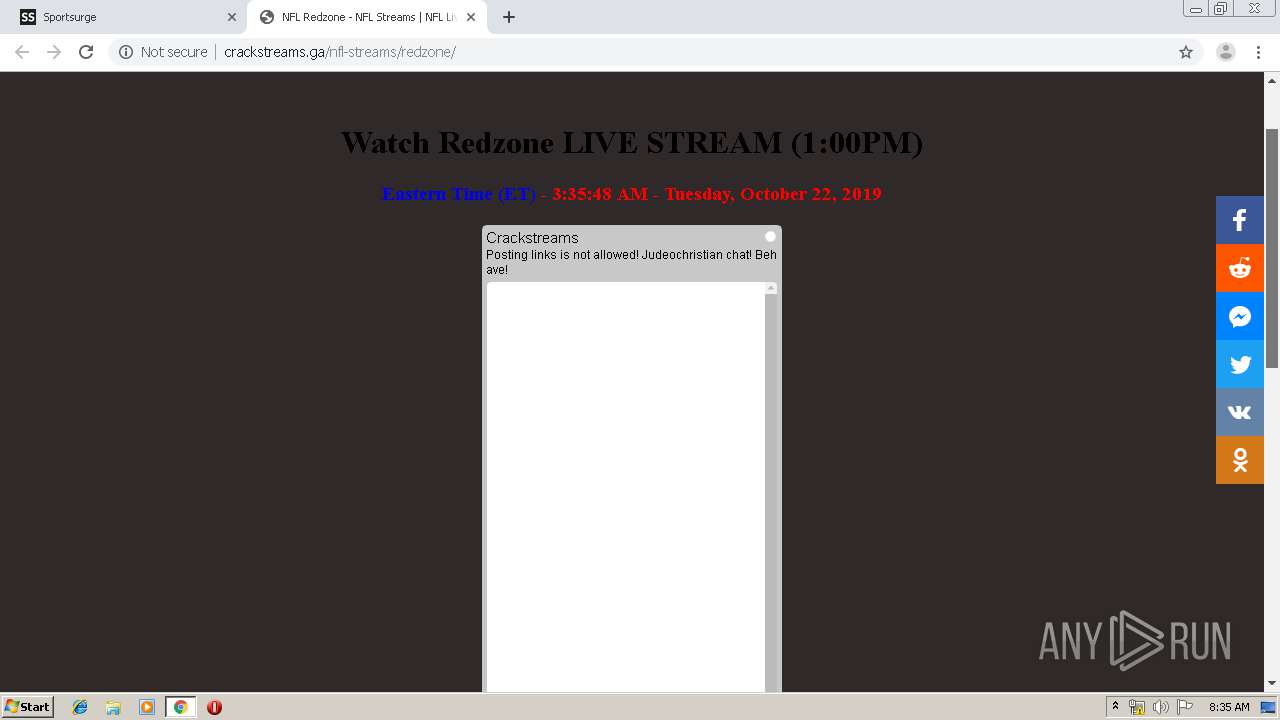
| Verdict: | Suspicious activity |
| Analysis date: | October 22, 2019, 07:34:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 8FFDEFBDEC956B595D257F0AAEEFD623 |
| SHA1: | EF7EFC9839C3EE036F023E9635BC3B056D6EE2DB |
| SHA256: | AC6BB669E40E44A8D9F8F0C94DFC63734049DCF6219AAC77F02EDF94B9162C09 |
| SSDEEP: | 3:N8DSLIK:2OLIK |
MALICIOUS
Connects to CnC server
- chrome.exe (PID: 1600)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2344)
INFO
Reads the hosts file
- chrome.exe (PID: 1600)
- chrome.exe (PID: 2344)
Application launched itself
- chrome.exe (PID: 2344)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
75
Monitored processes
40
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 564 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=980,13522906091185382535,15076140749420656543,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7476660160146758226 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2296 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 716 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,13522906091185382535,15076140749420656543,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=14026098655257332338 --mojo-platform-channel-handle=4728 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 912 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,13522906091185382535,15076140749420656543,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15764084657924297217 --mojo-platform-channel-handle=3780 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,13522906091185382535,15076140749420656543,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5640521495584703010 --mojo-platform-channel-handle=4664 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1216 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=980,13522906091185382535,15076140749420656543,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3191587044753164613 --renderer-client-id=31 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4640 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,13522906091185382535,15076140749420656543,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7077472946477048059 --mojo-platform-channel-handle=4224 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=980,13522906091185382535,15076140749420656543,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14842063399676930334 --renderer-client-id=33 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3968 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,13522906091185382535,15076140749420656543,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=10234732292235973505 --mojo-platform-channel-handle=1576 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=980,13522906091185382535,15076140749420656543,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1735909402127489398 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2588 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1648 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,13522906091185382535,15076140749420656543,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9896716352222477528 --mojo-platform-channel-handle=4188 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
635
Read events
525
Write events
105
Delete events
5
Modification events
| (PID) Process: | (2344) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2344) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2344) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2344) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2344) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2132) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2344-13216203260048375 |
Value: 259 | |||
| (PID) Process: | (2344) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2344) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2344) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2344) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
98
Text files
260
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF39a9f6.TMP | — | |
MD5:— | SHA256:— | |||
| 2344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\1c6cbe62-d234-4f08-aa8b-ad30d3e61707.tmp | — | |
MD5:— | SHA256:— | |||
| 2344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF39aa06.TMP | text | |
MD5:— | SHA256:— | |||
| 2344 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
38
TCP/UDP connections
94
DNS requests
66
Threats
5
HTTP requests
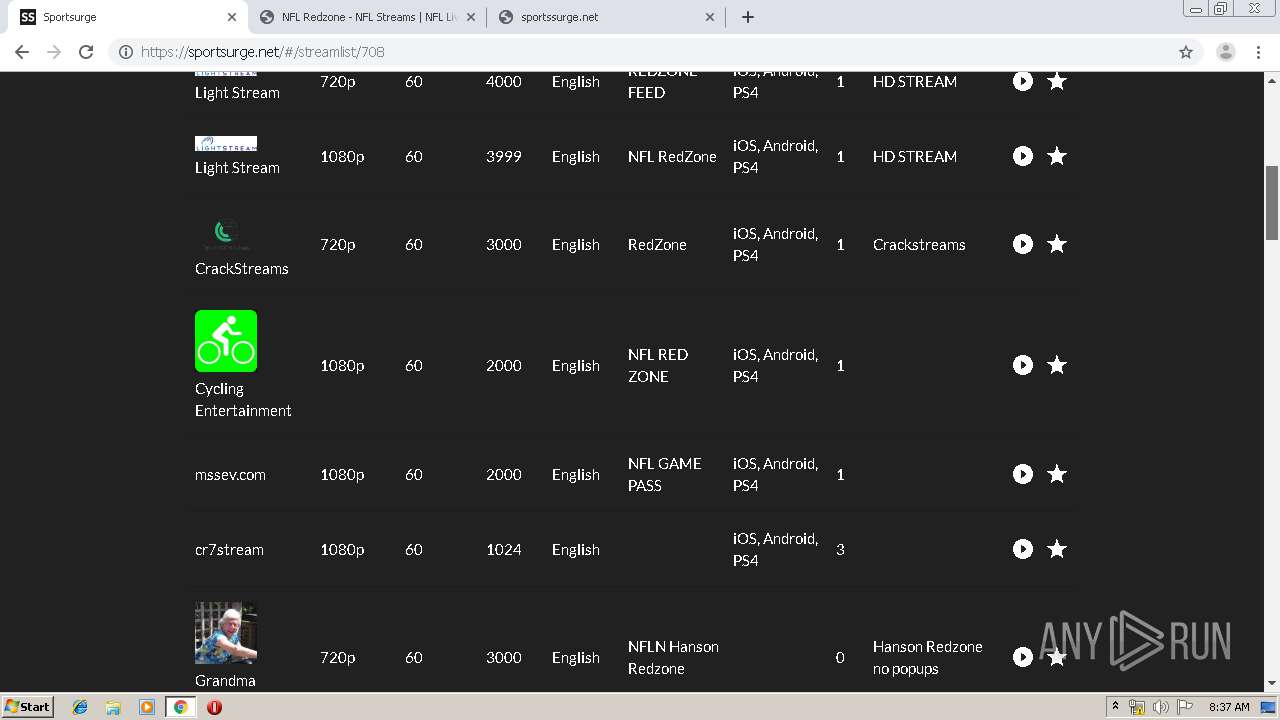
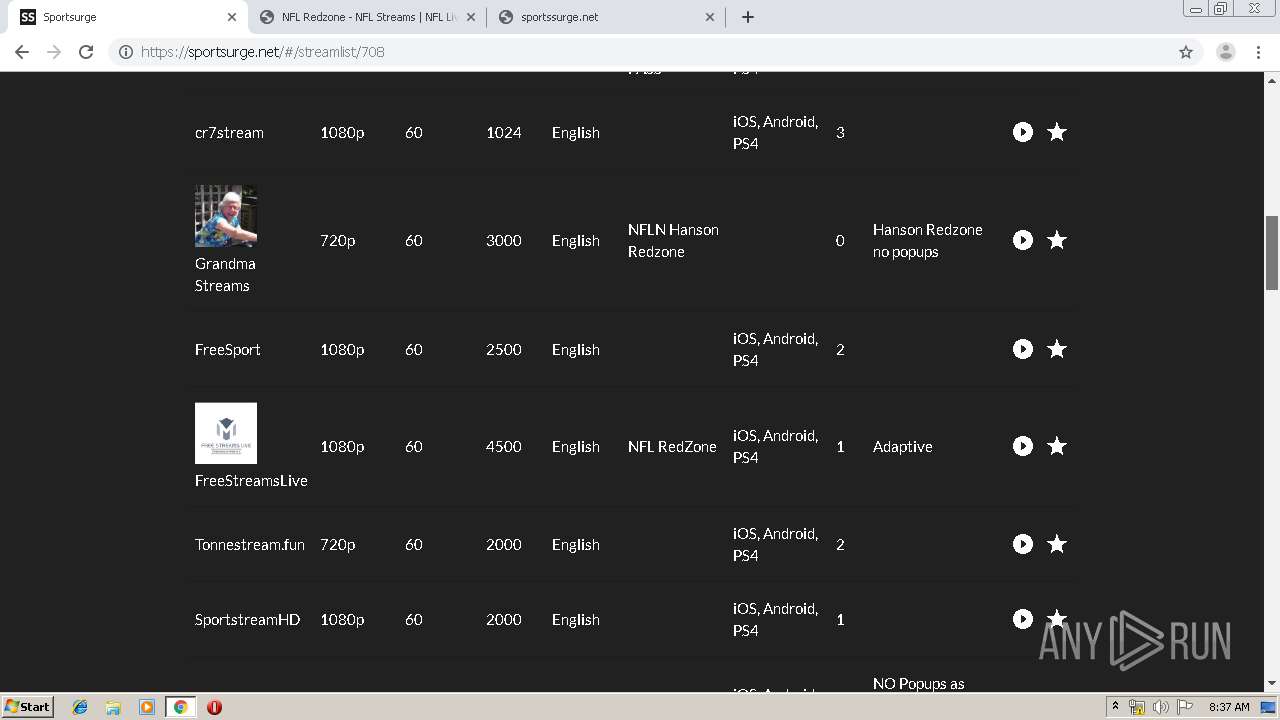
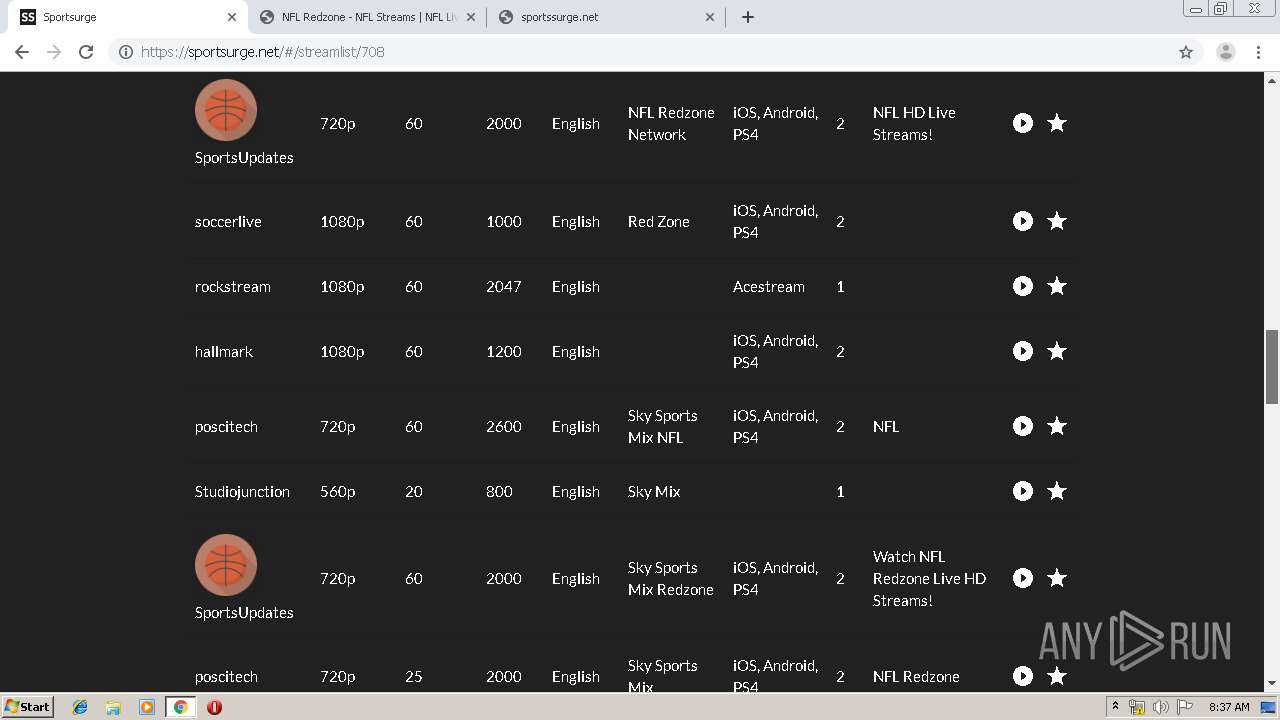
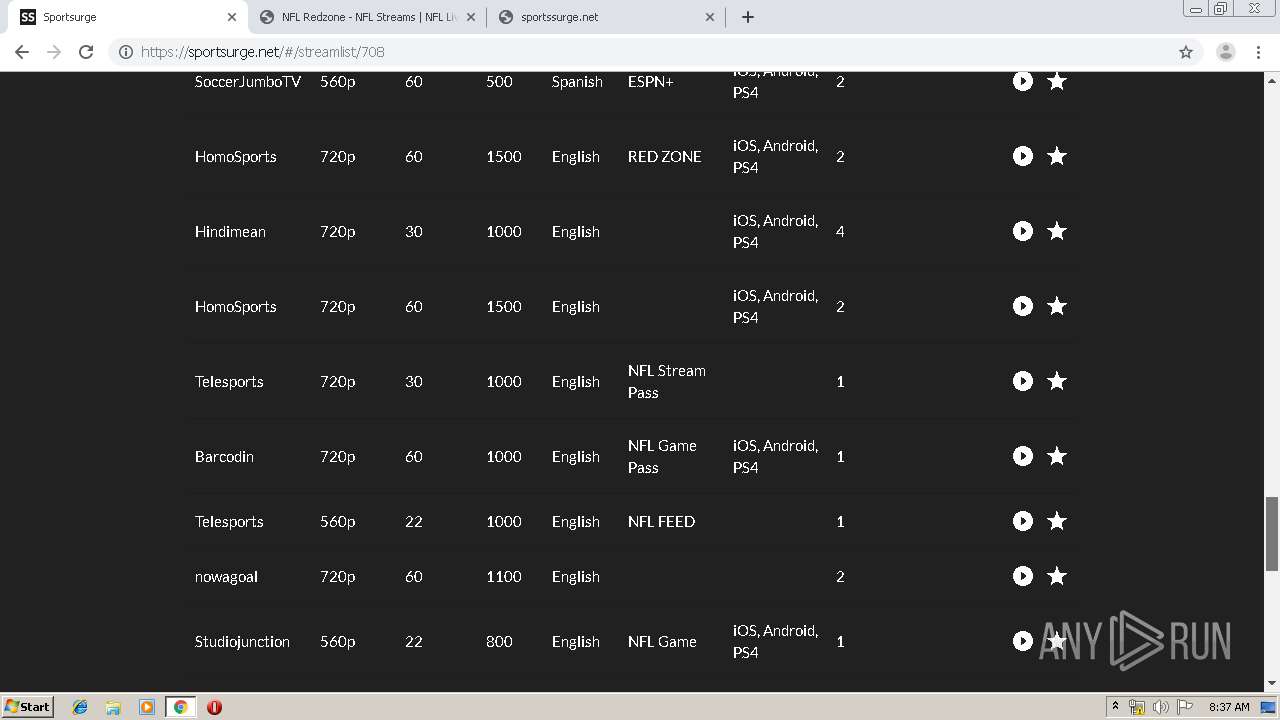
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
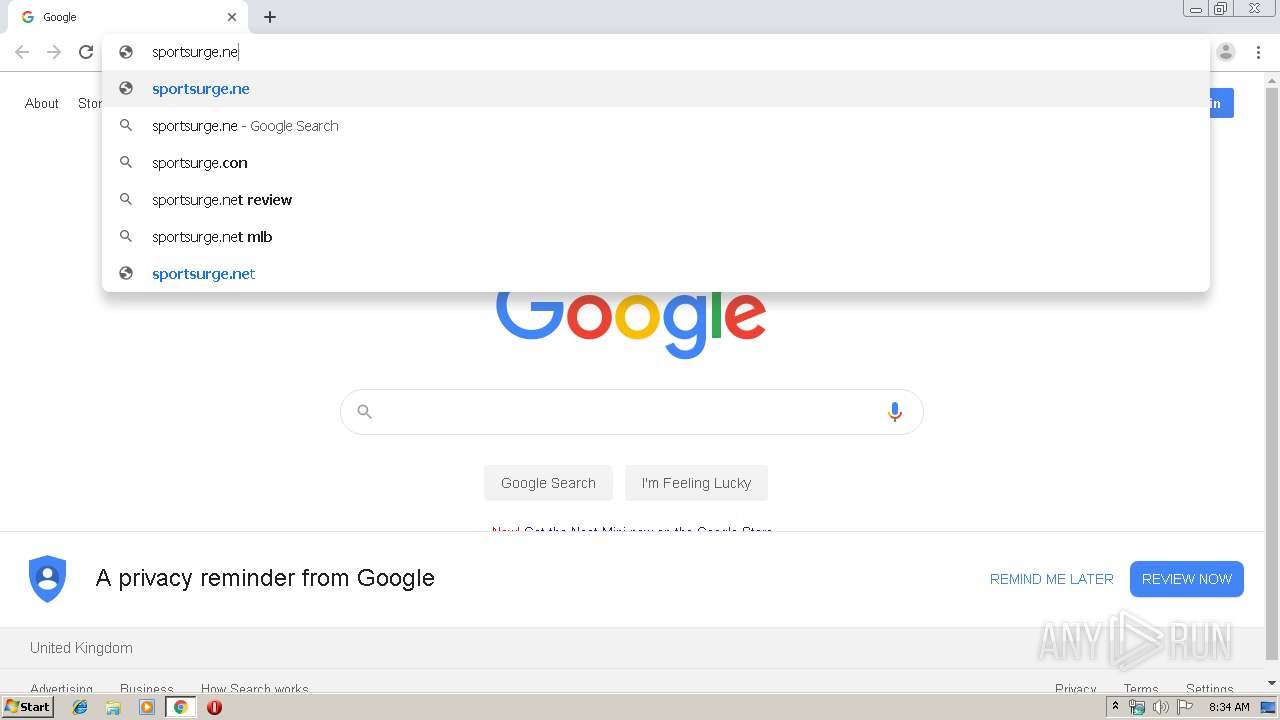
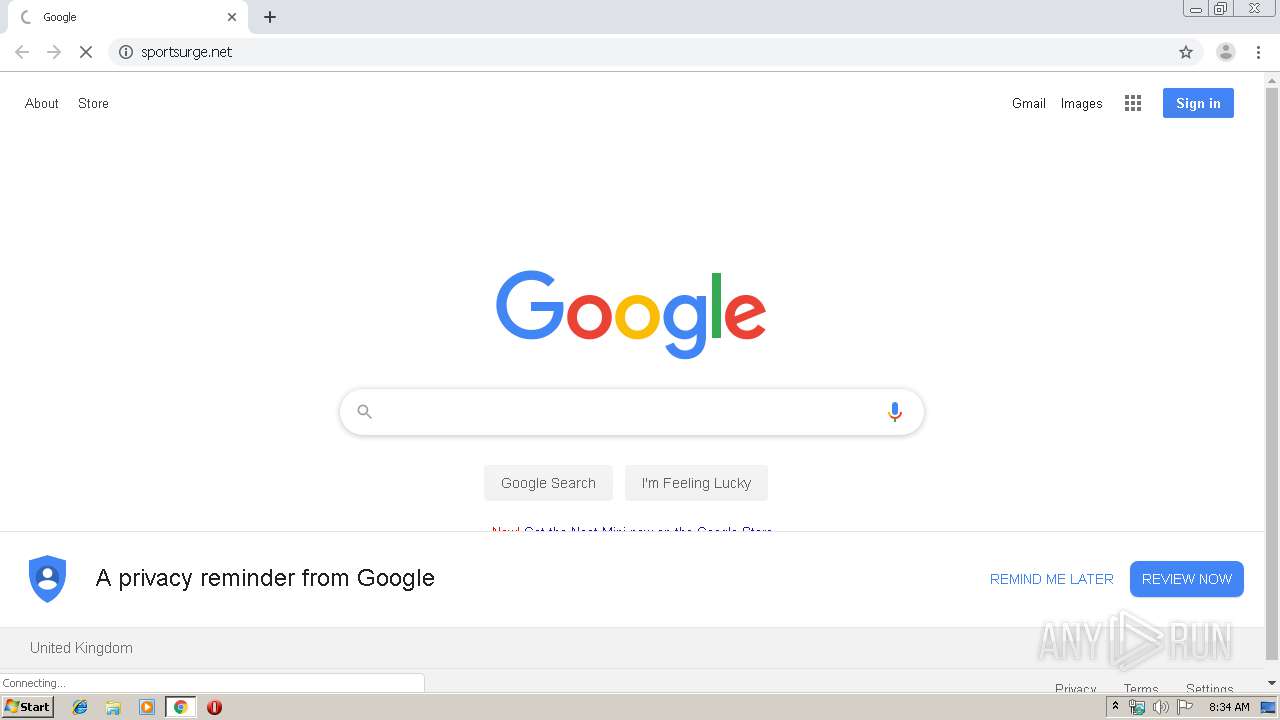
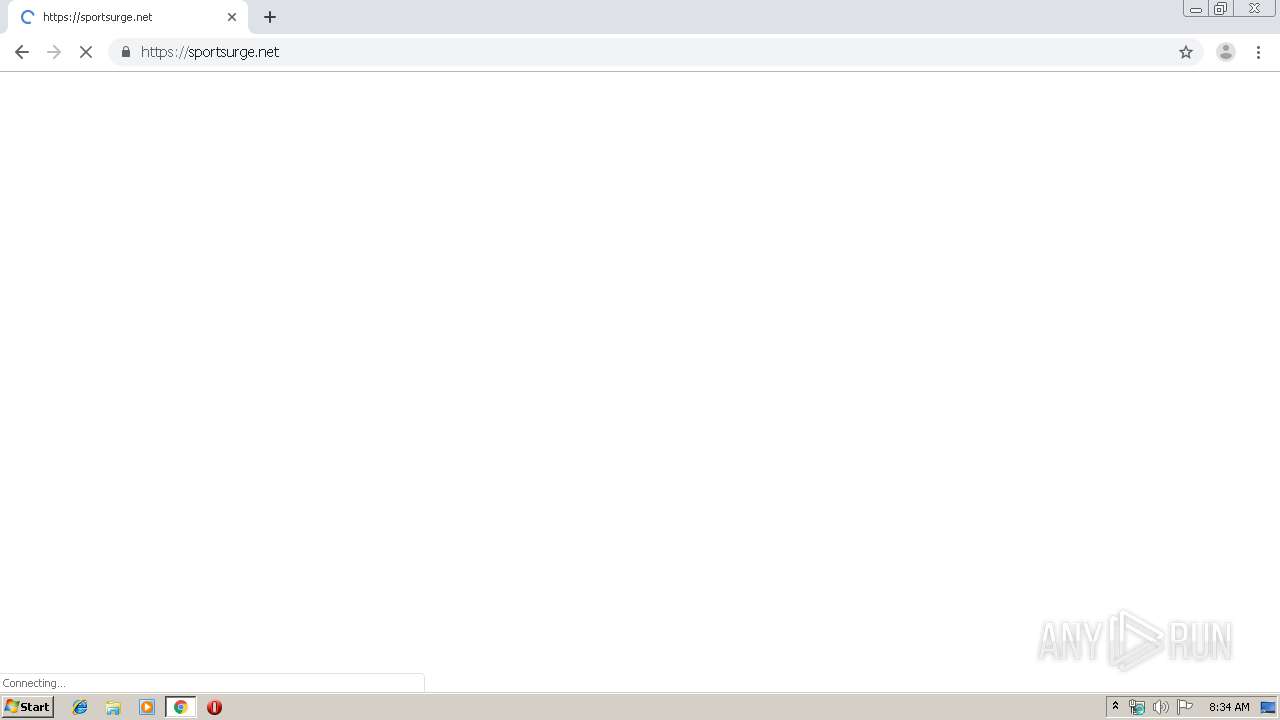
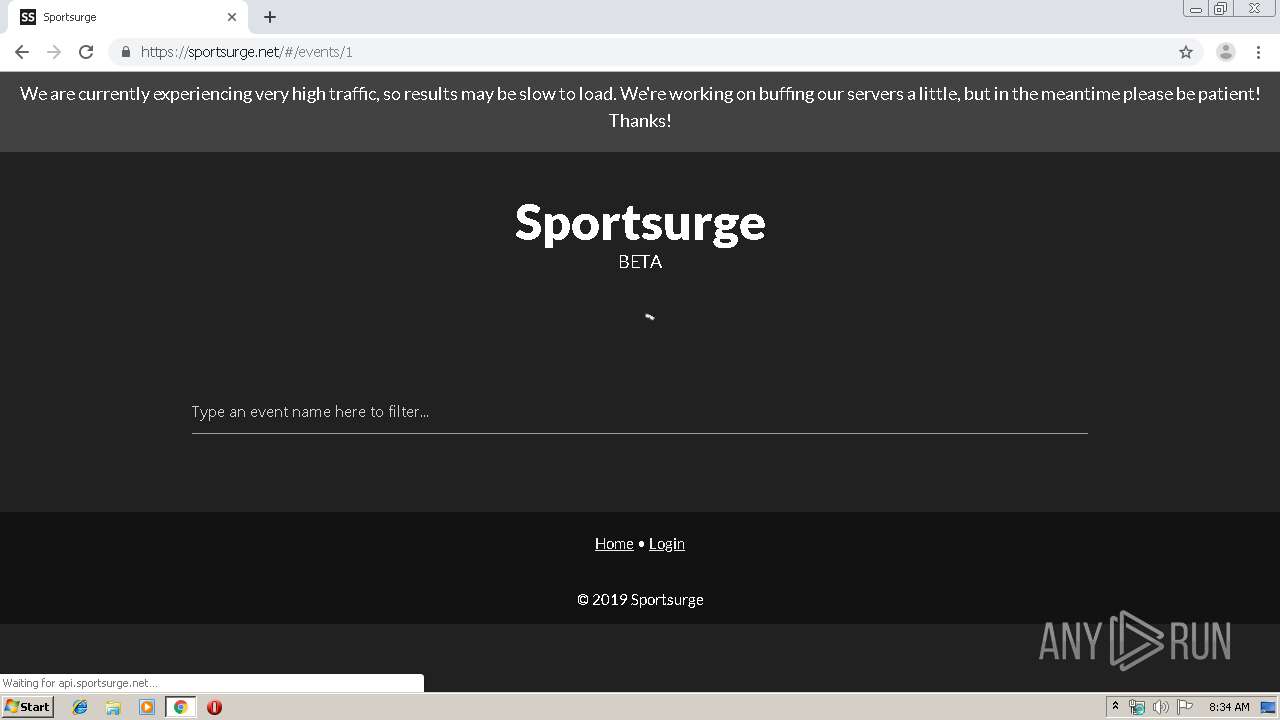
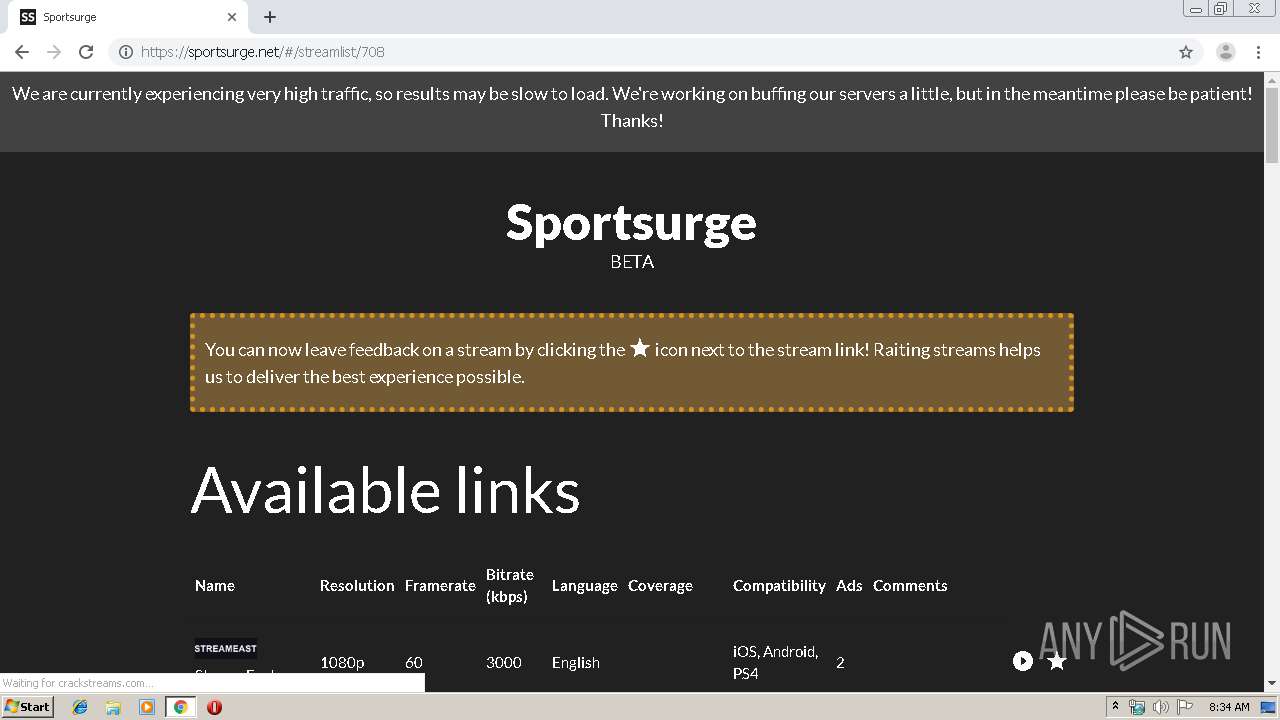
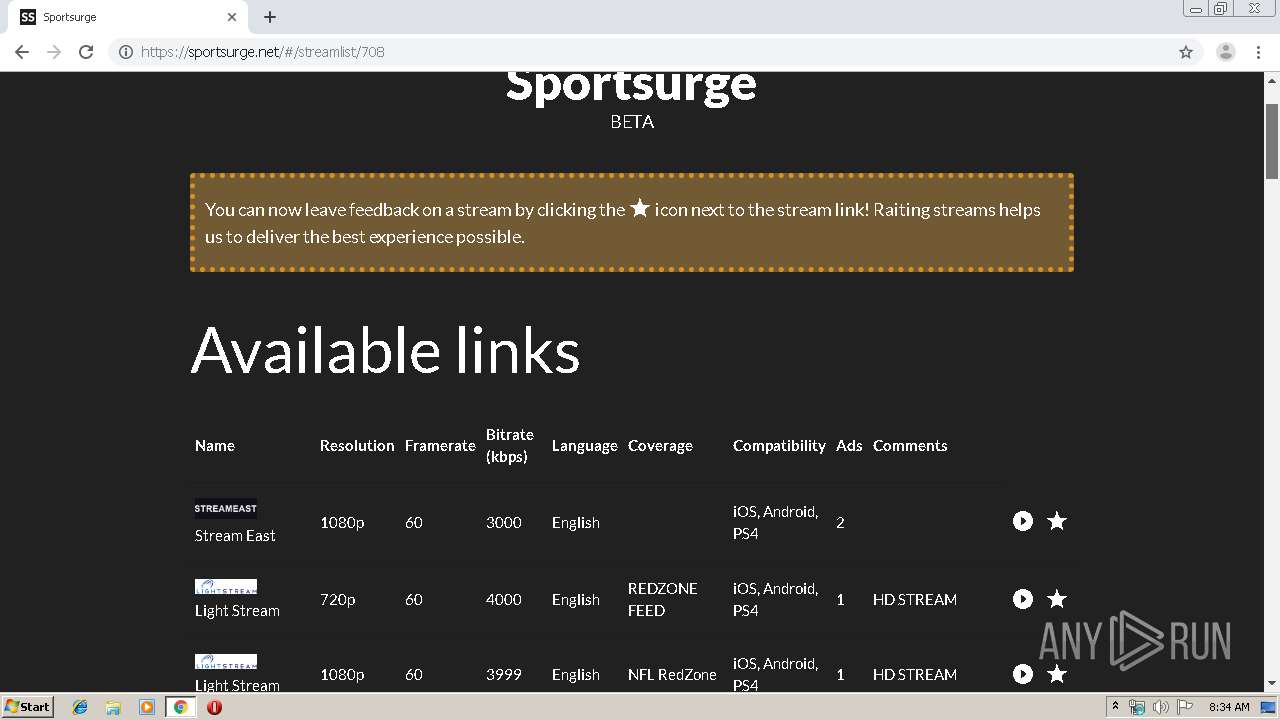
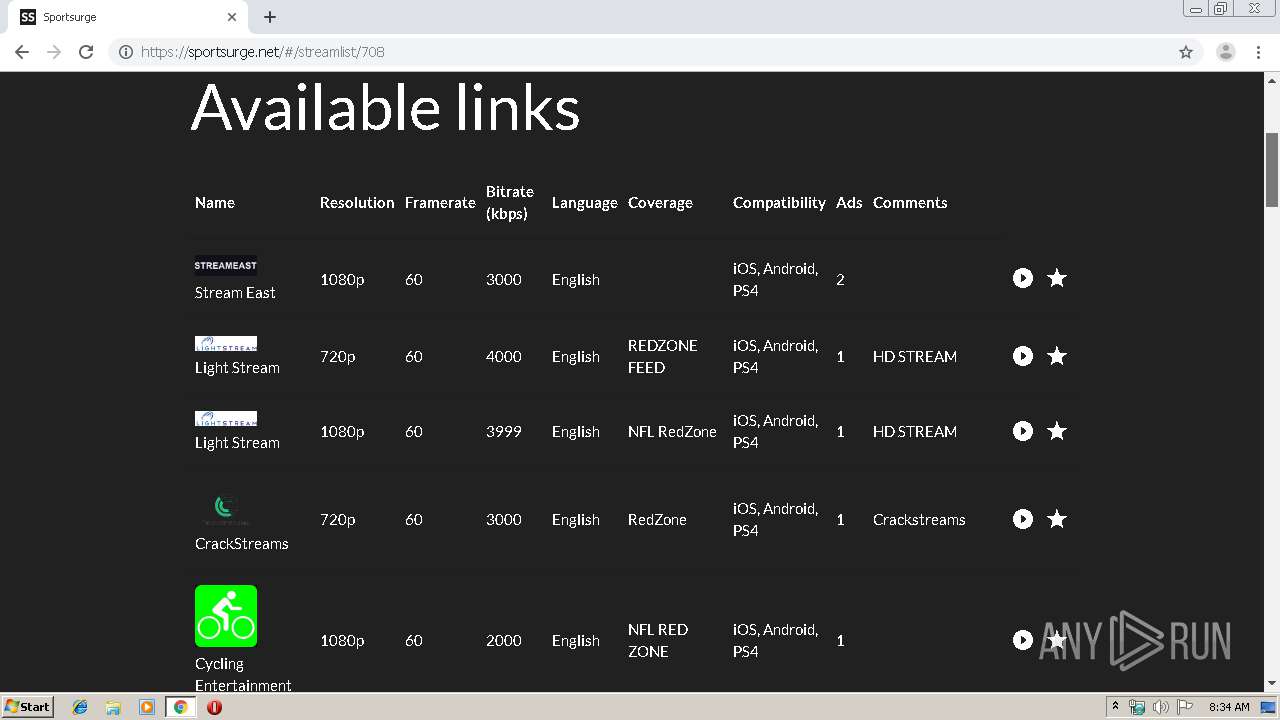
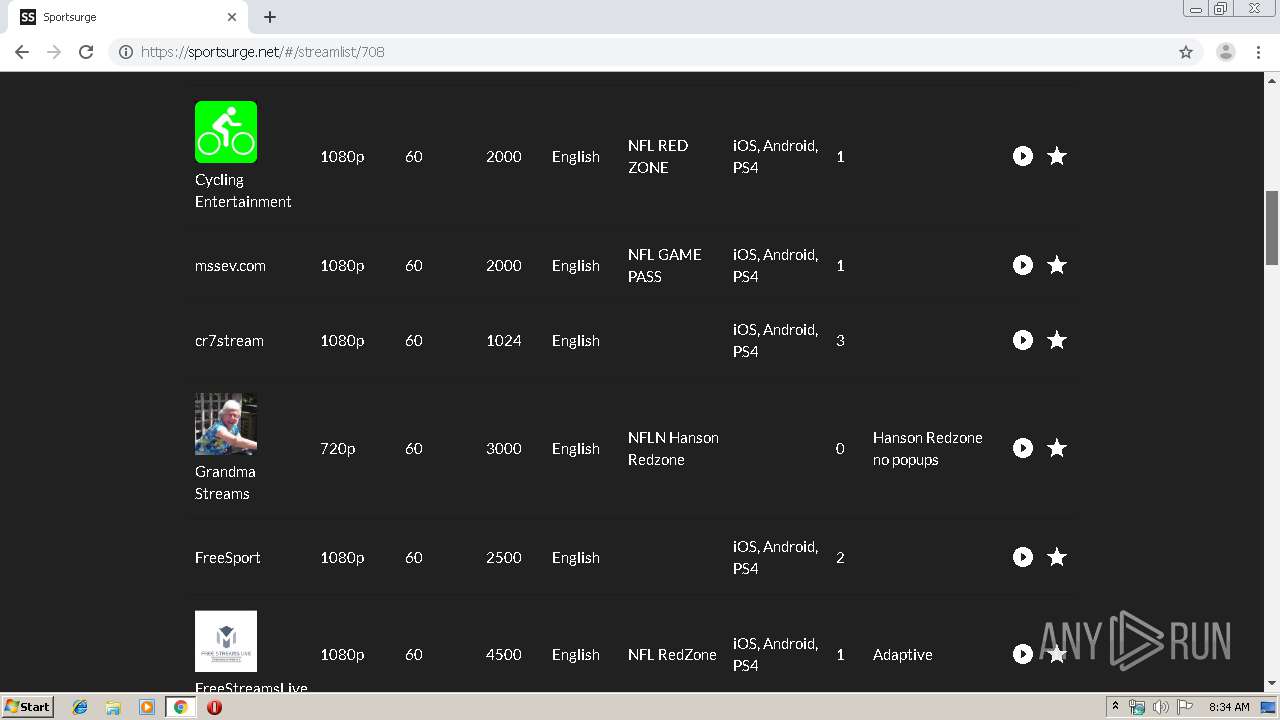
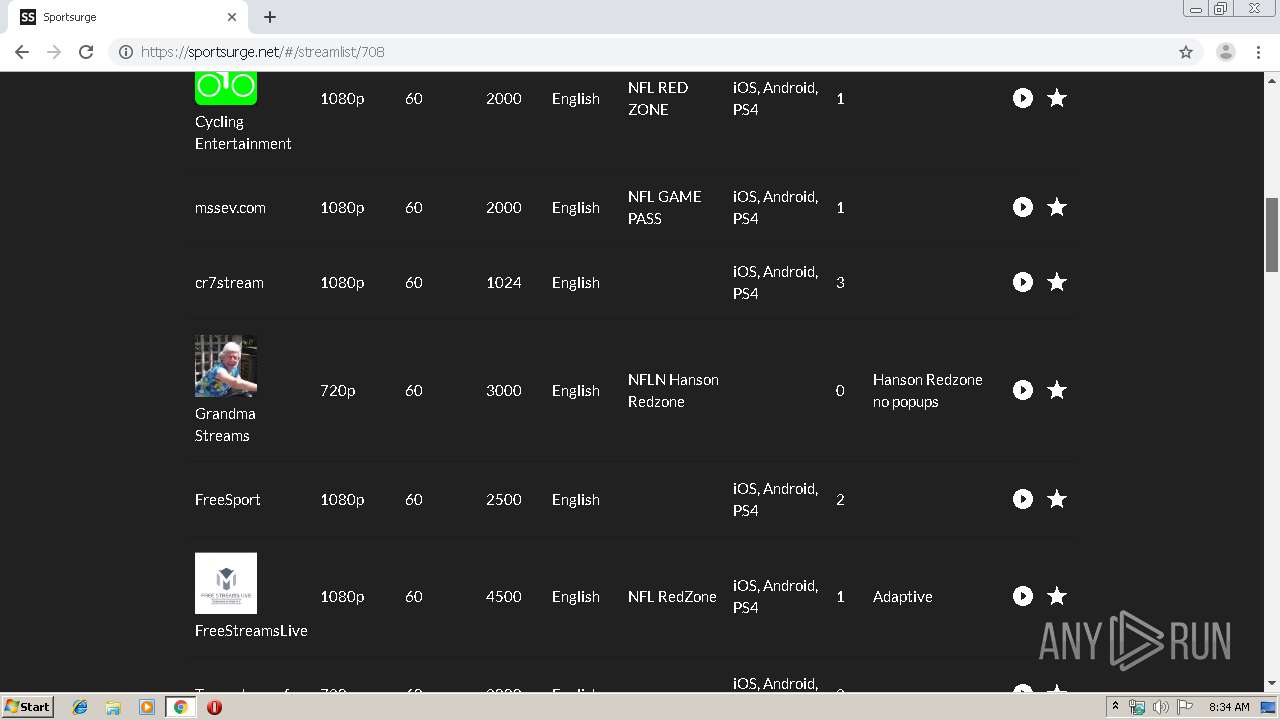
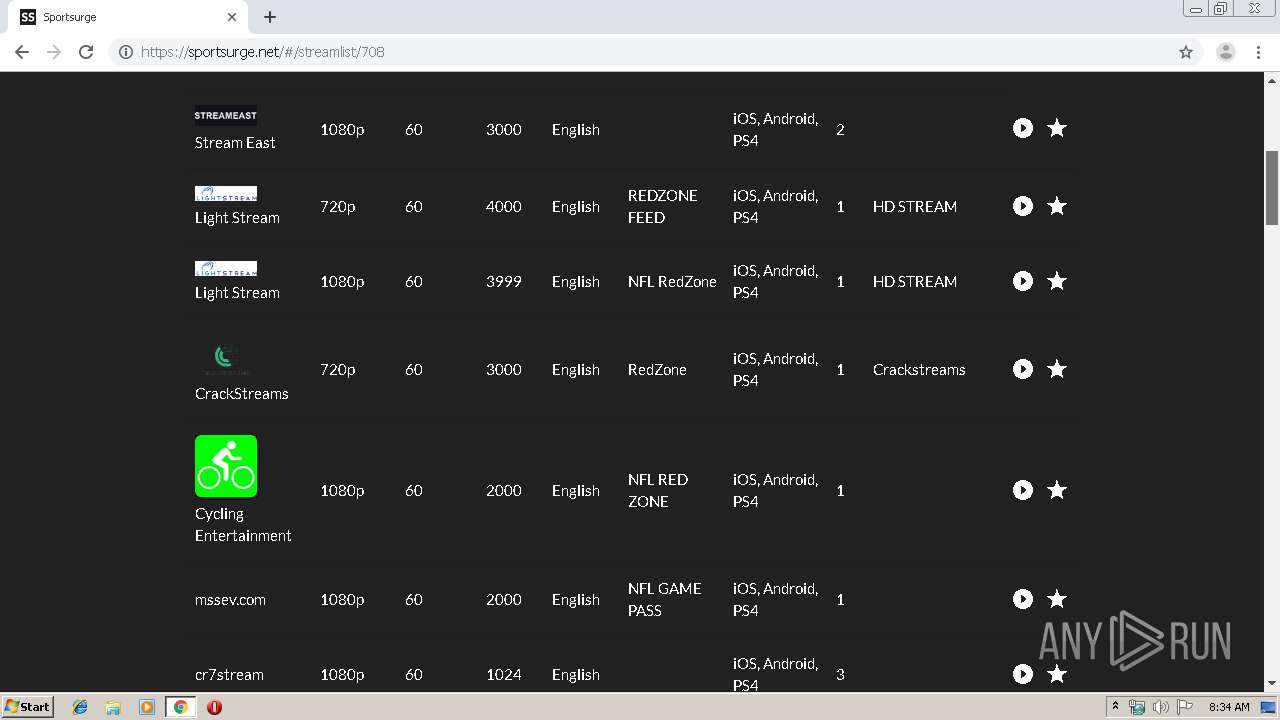
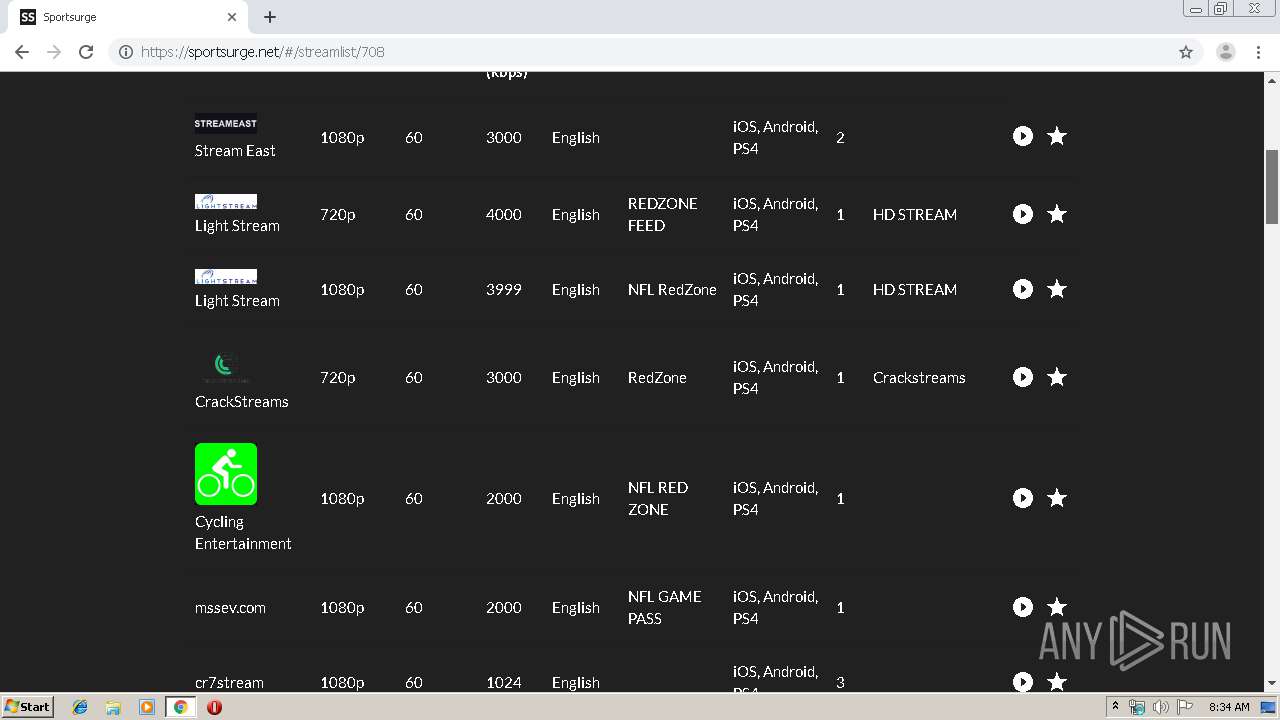
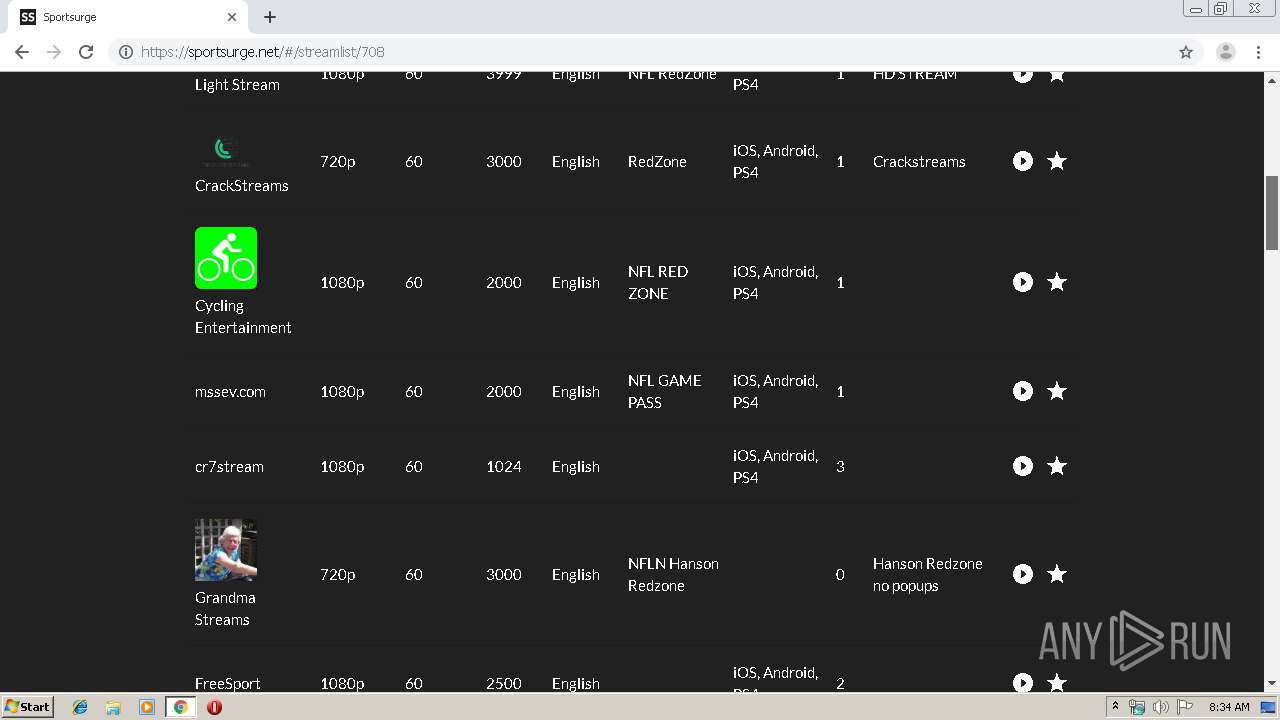
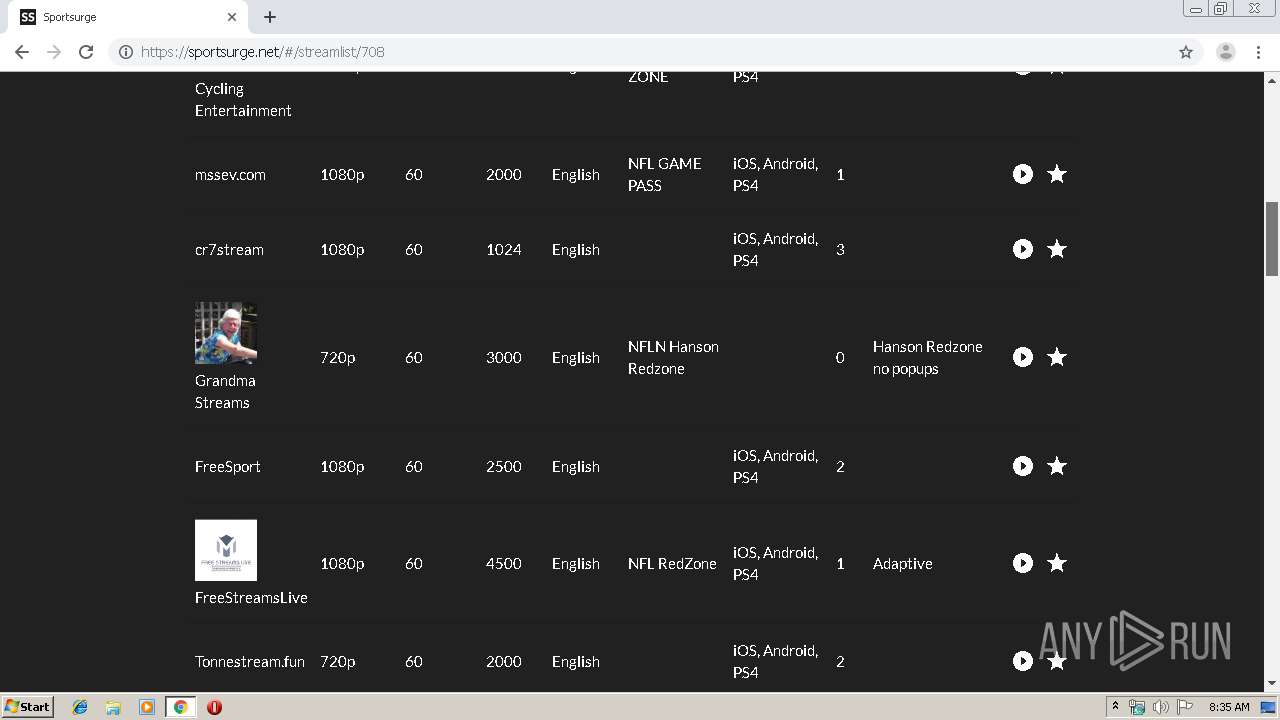
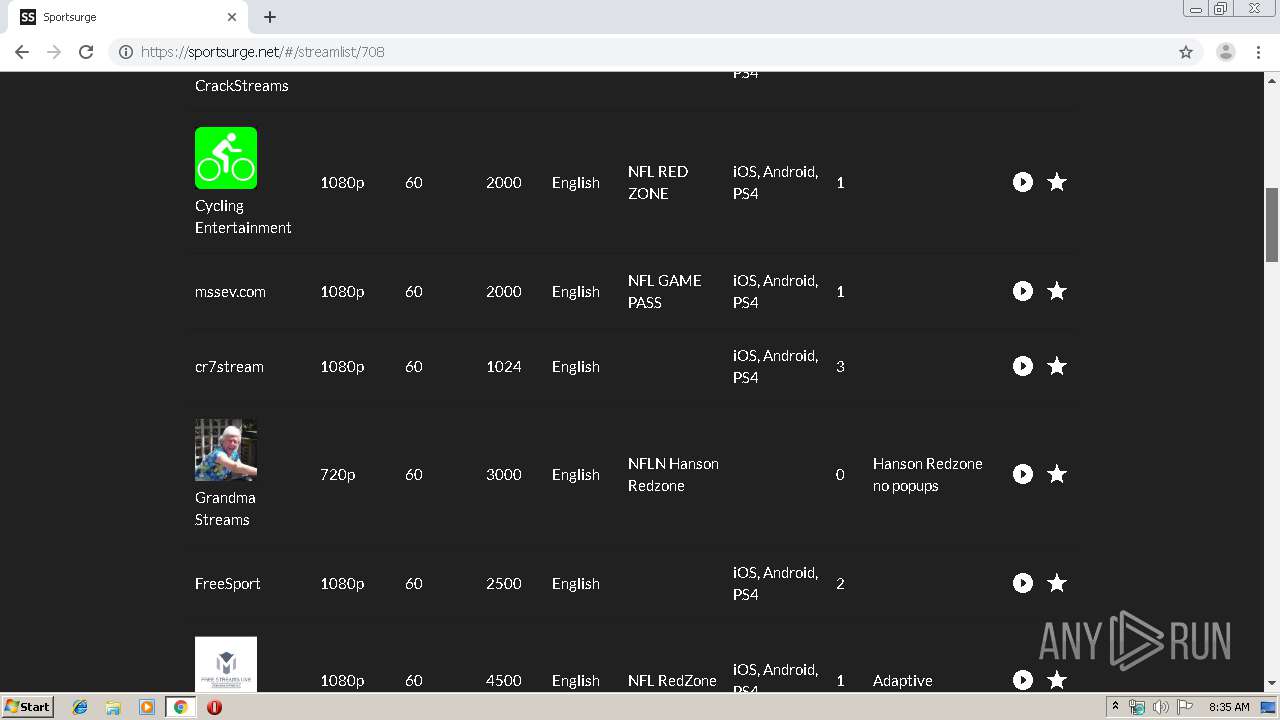
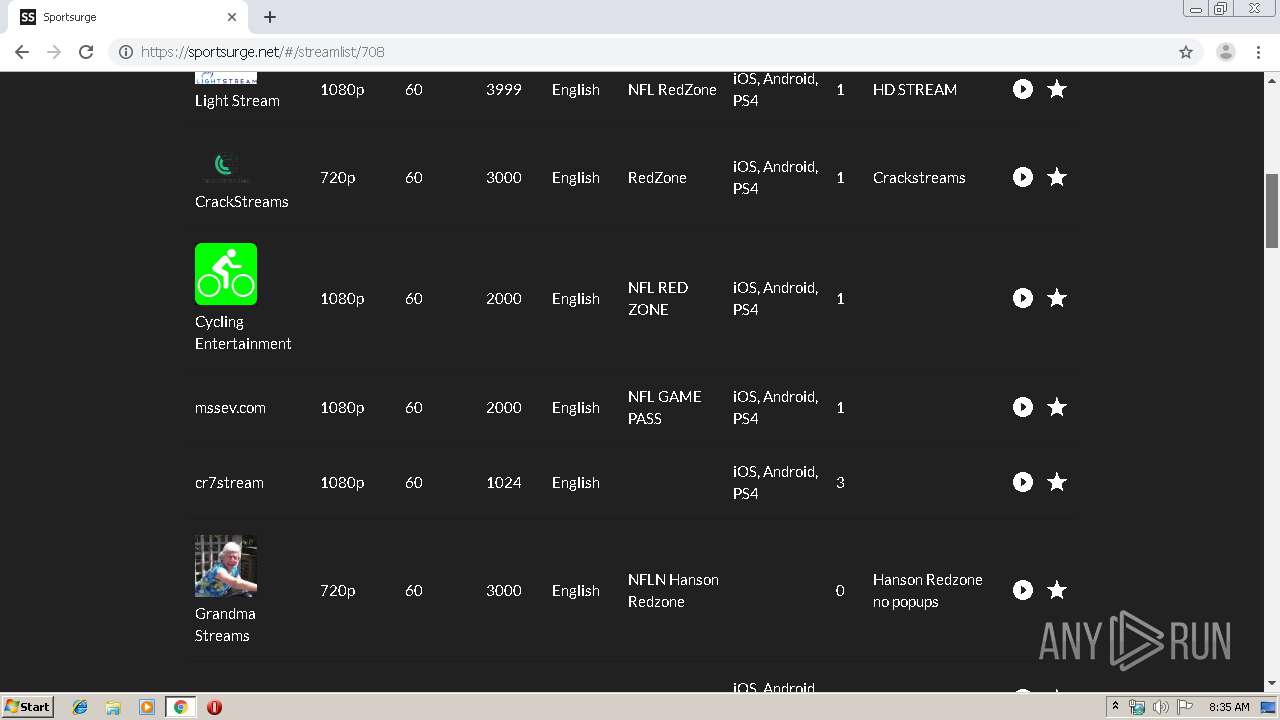
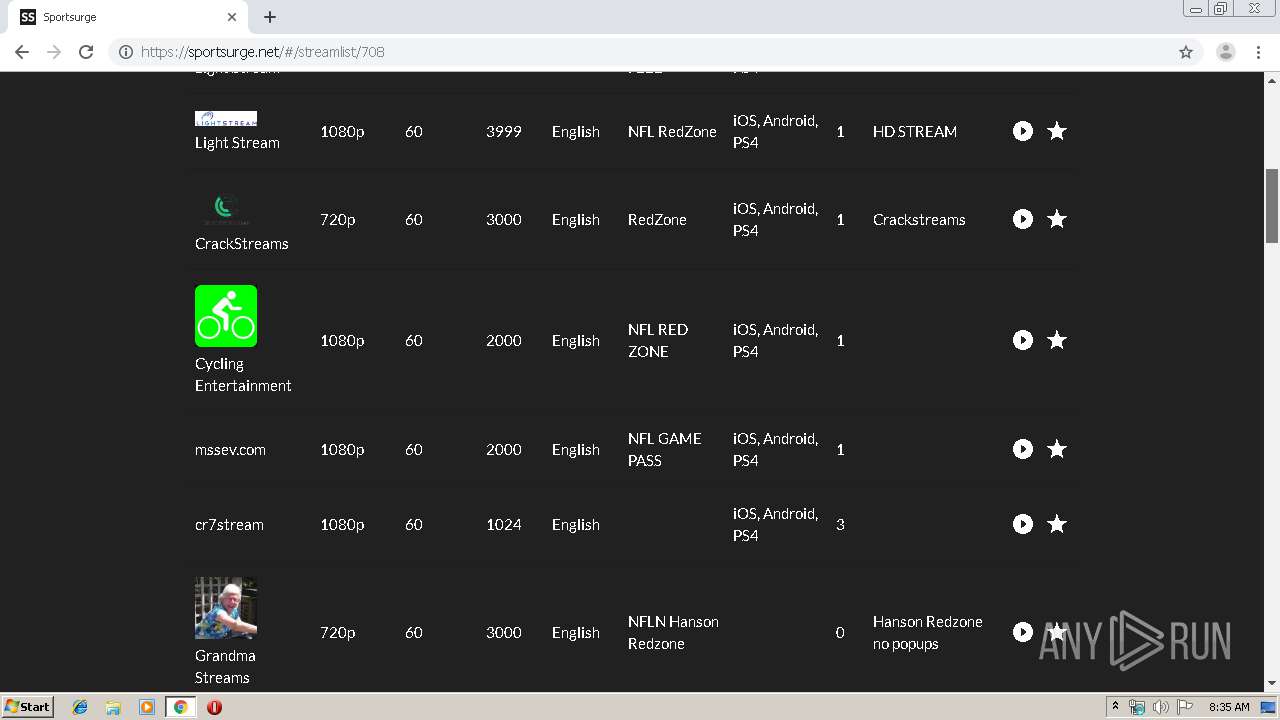
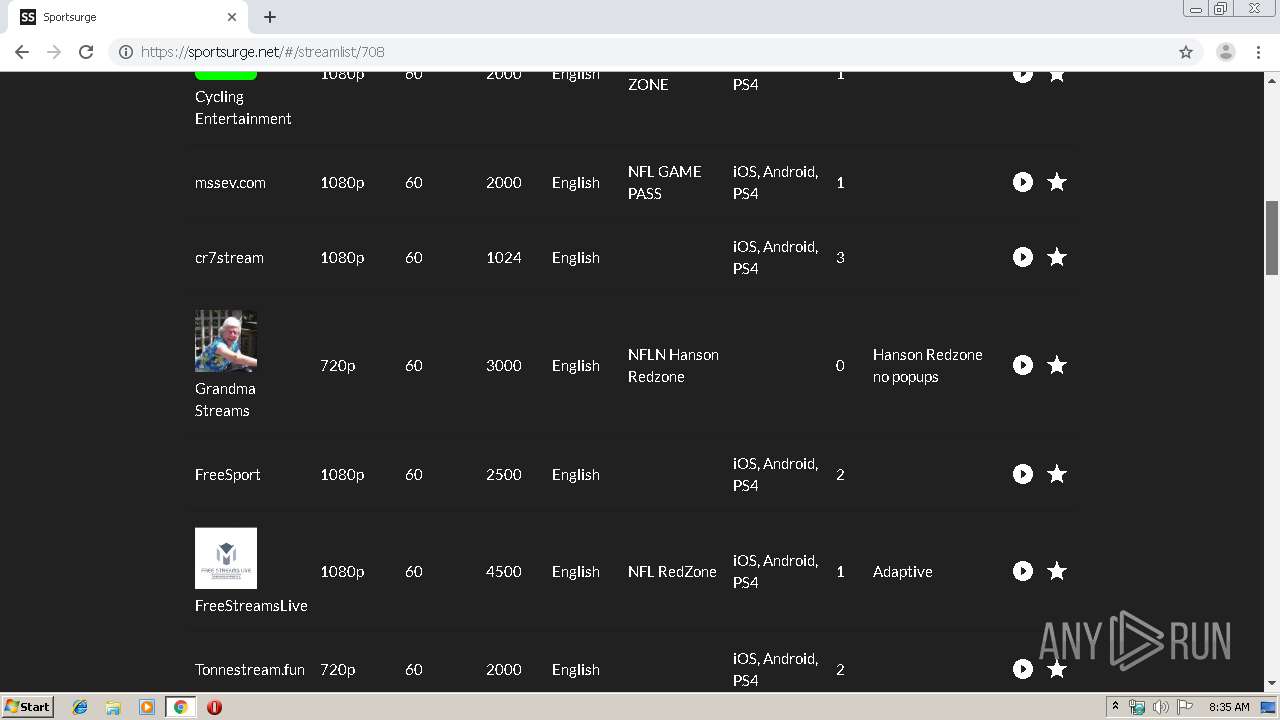
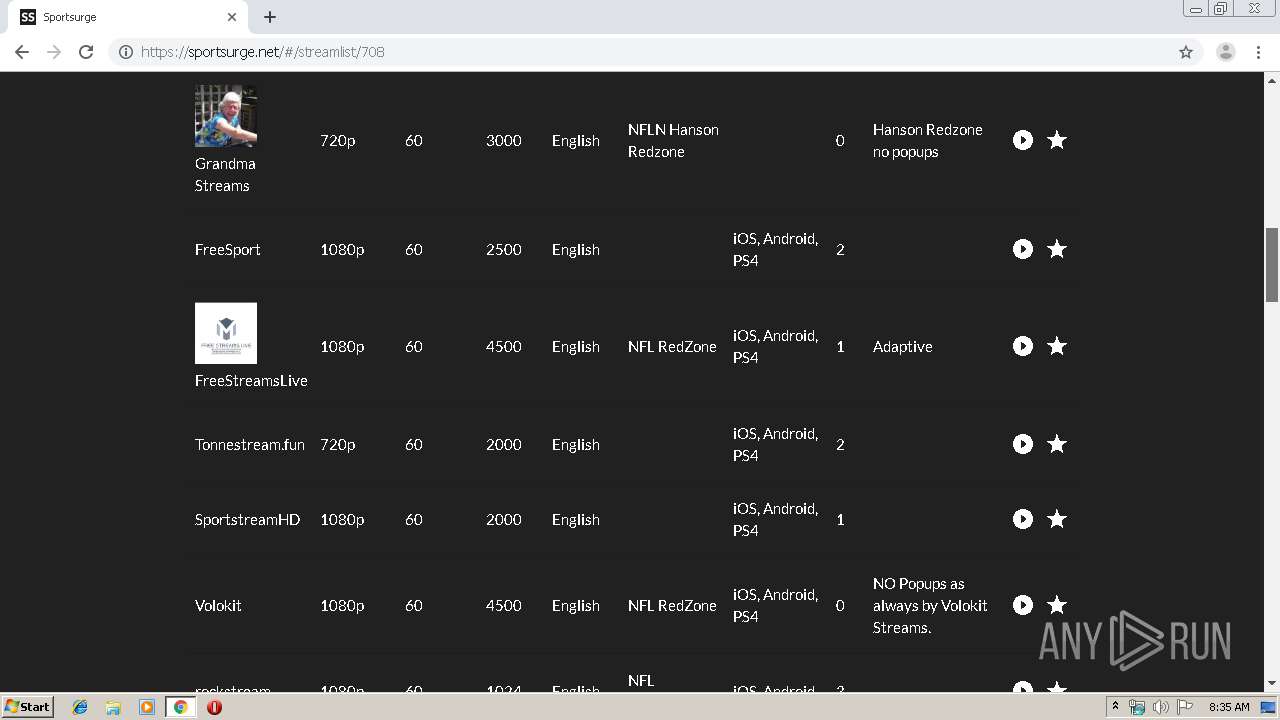
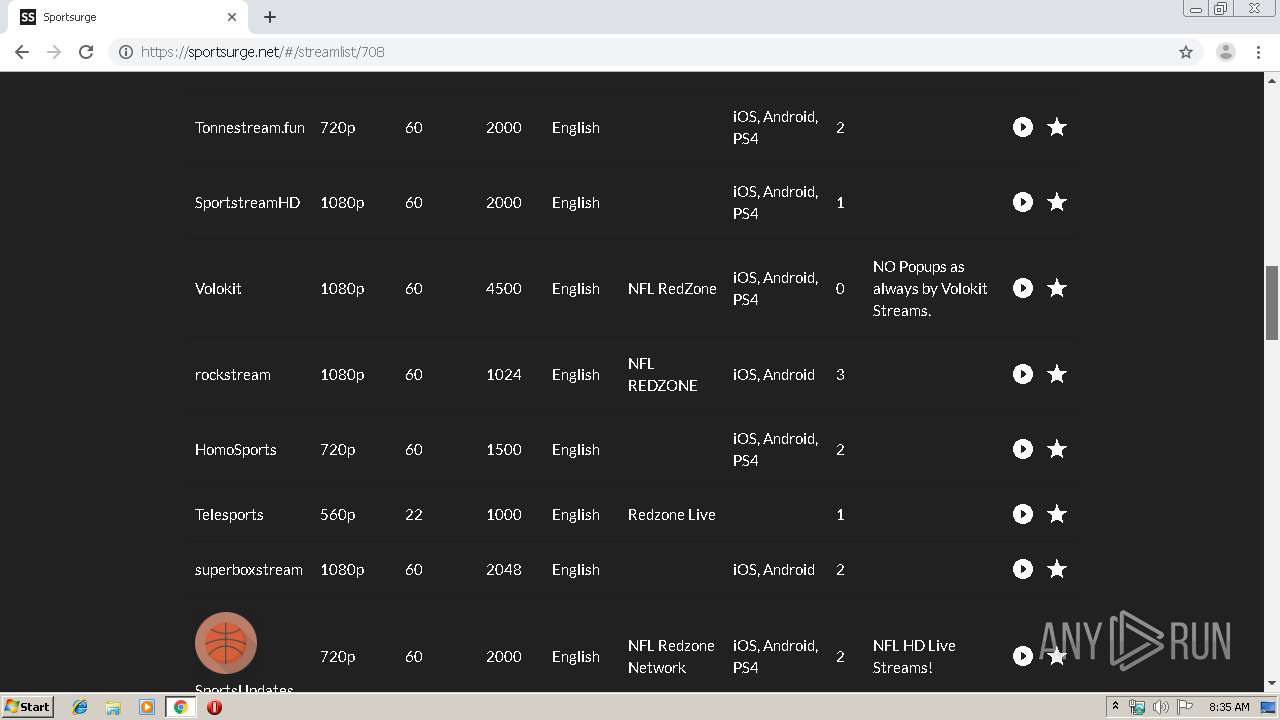
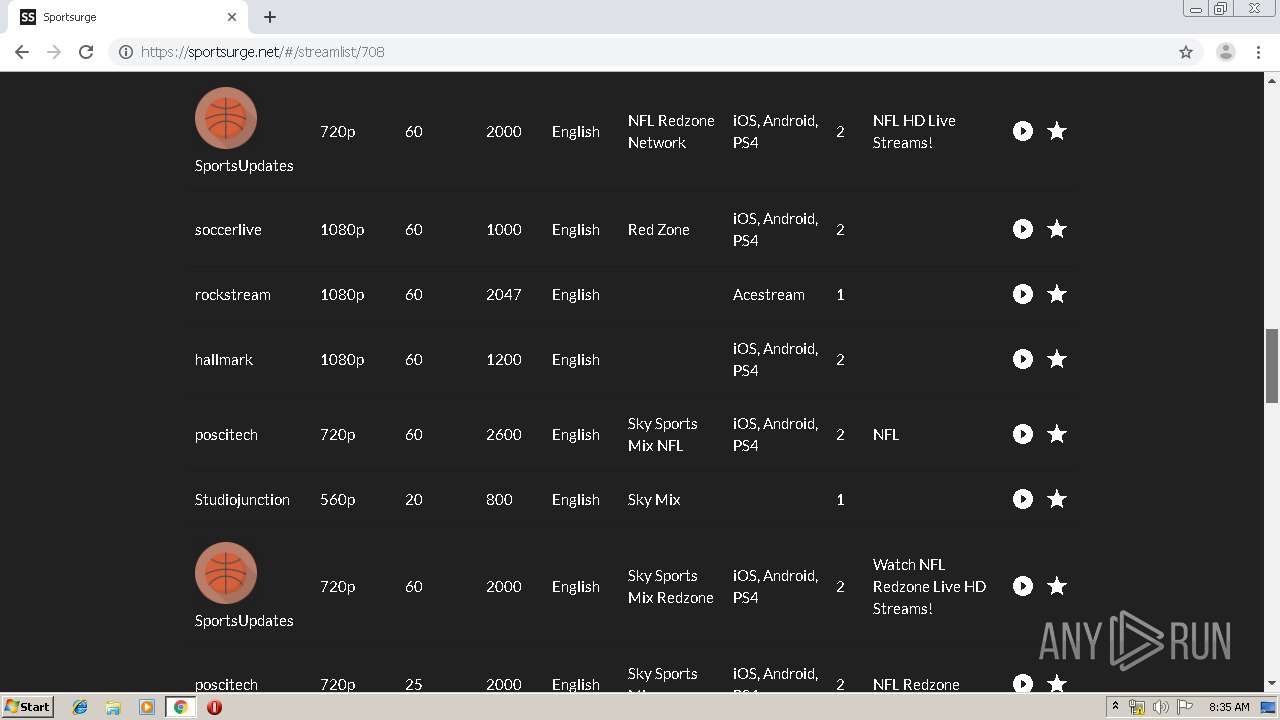
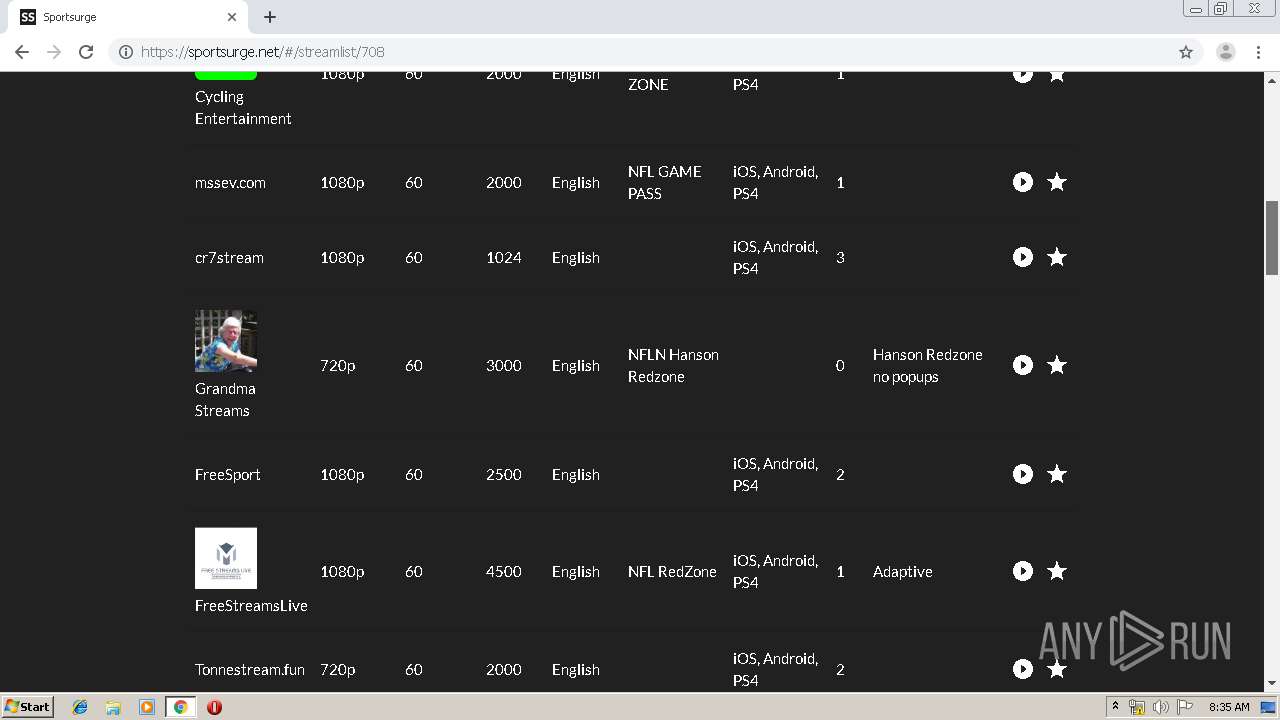
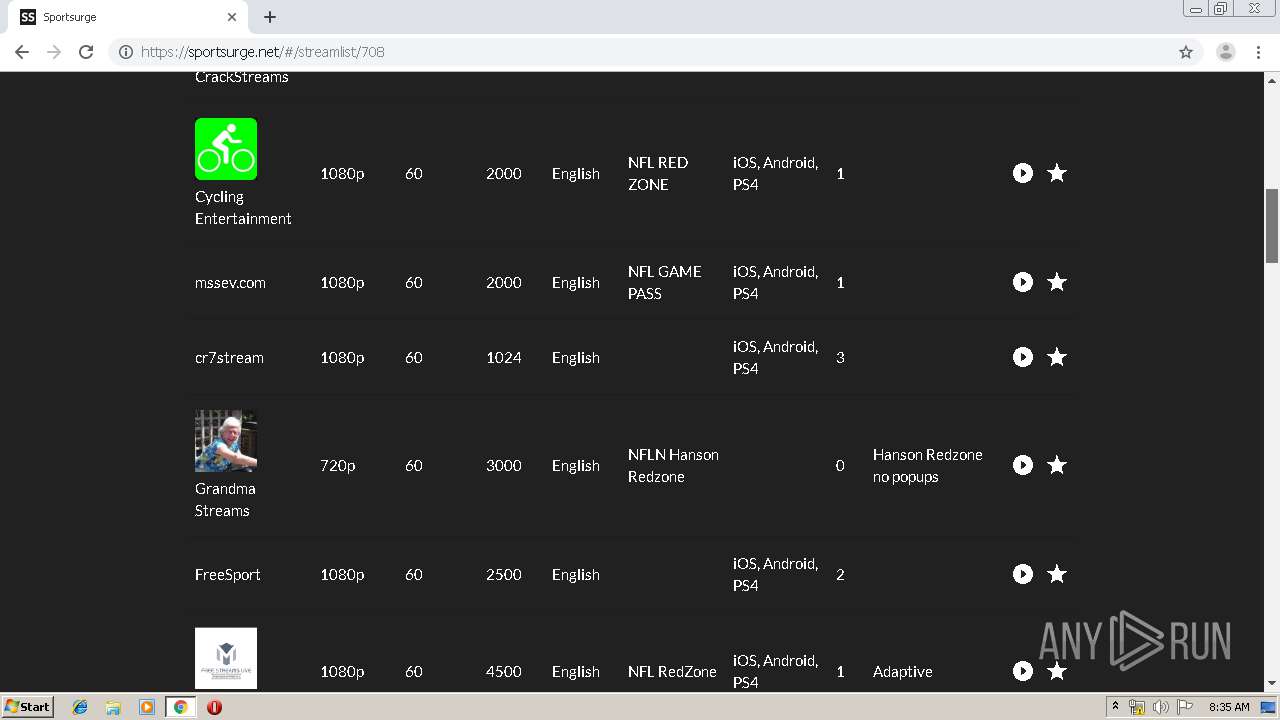
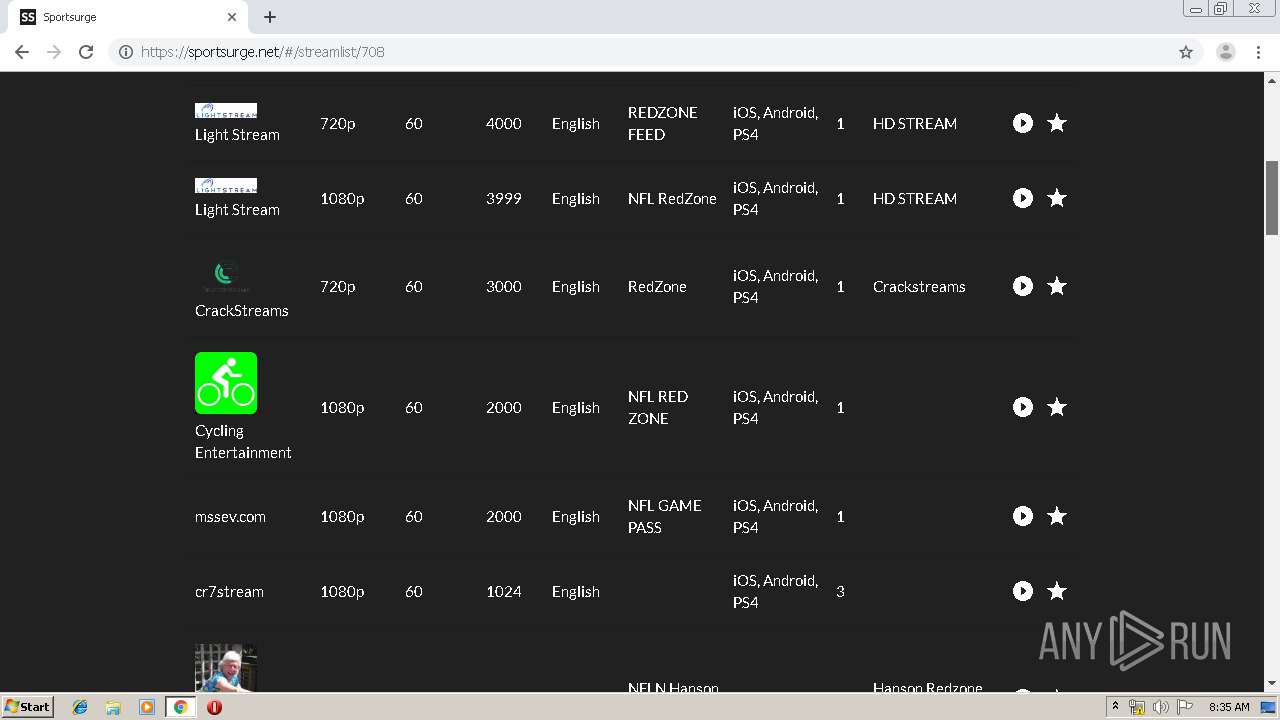
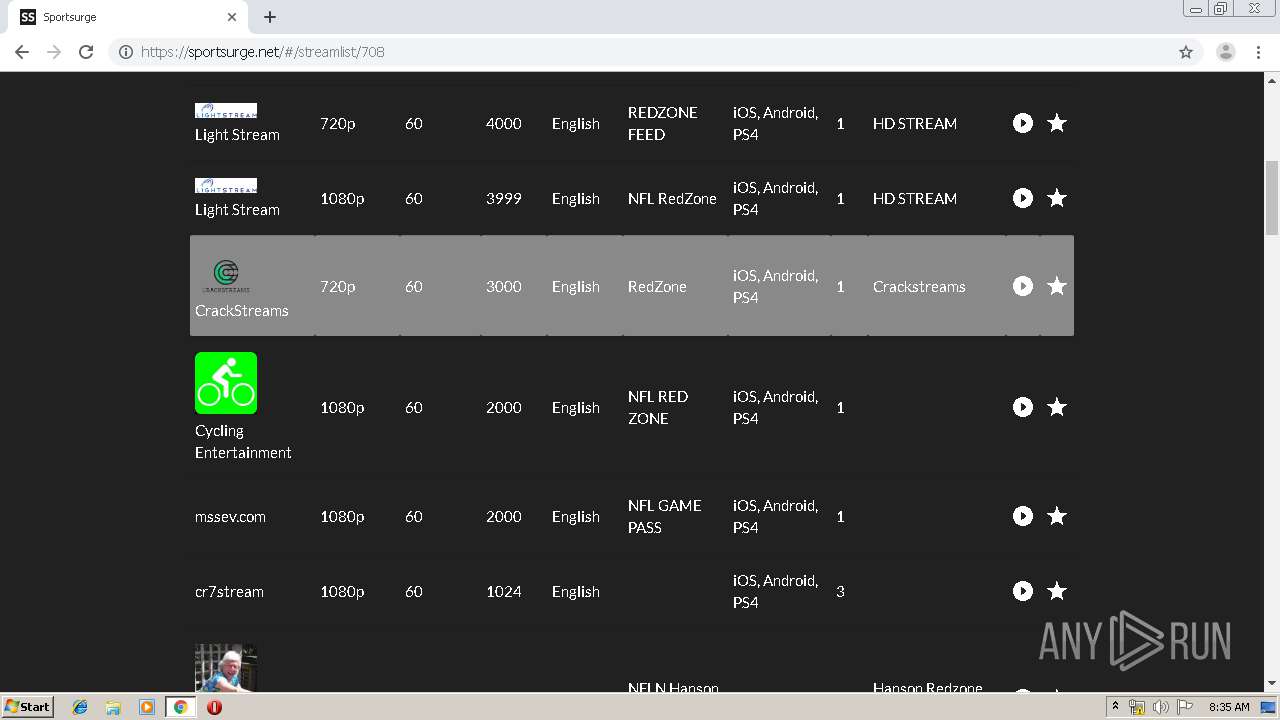
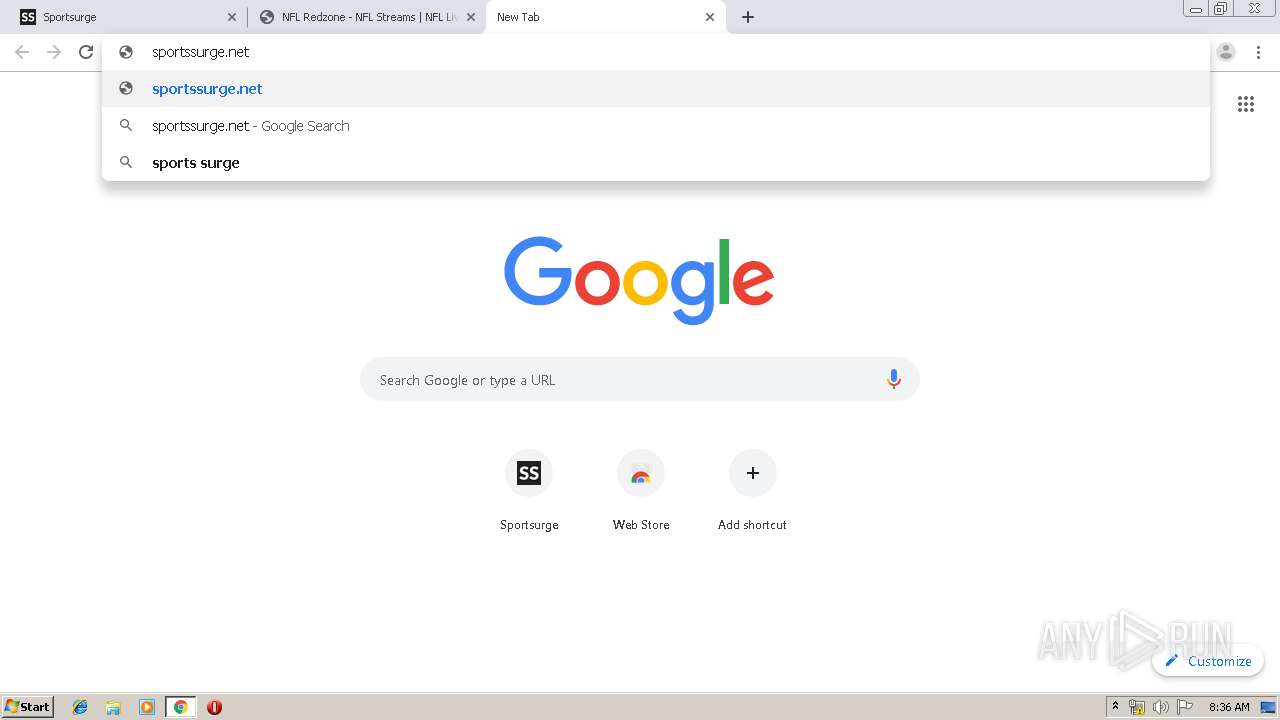
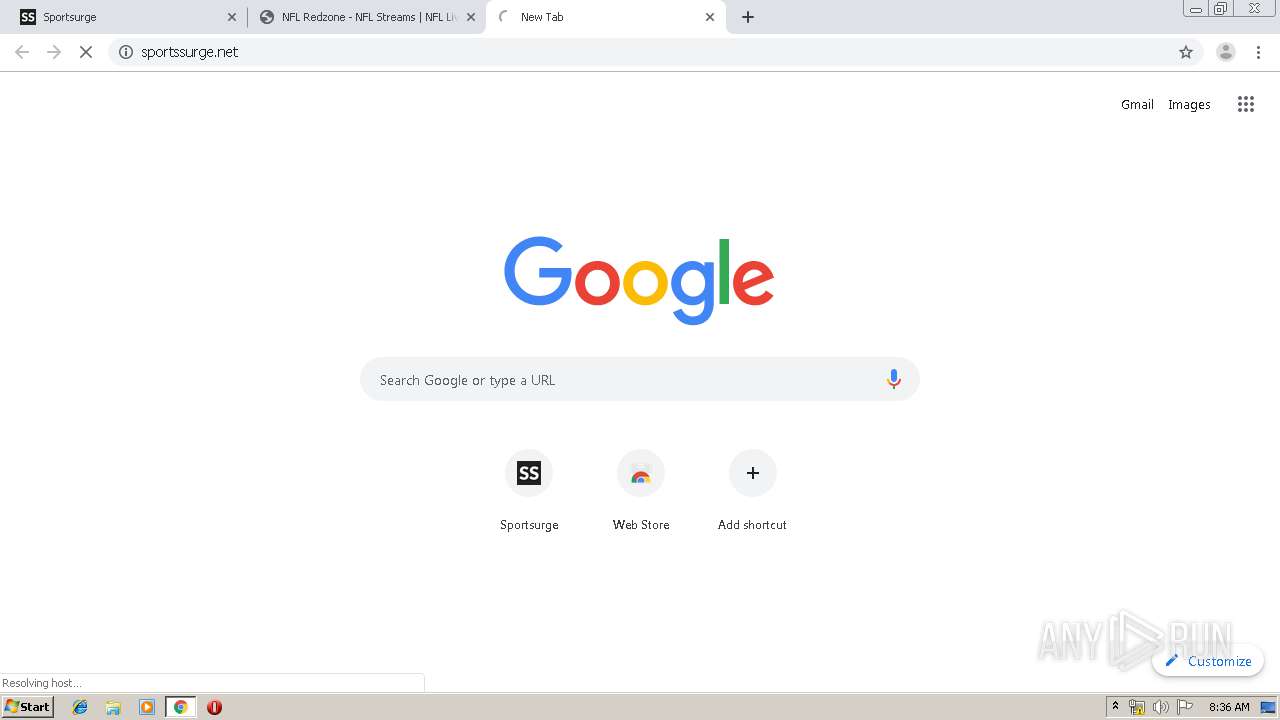
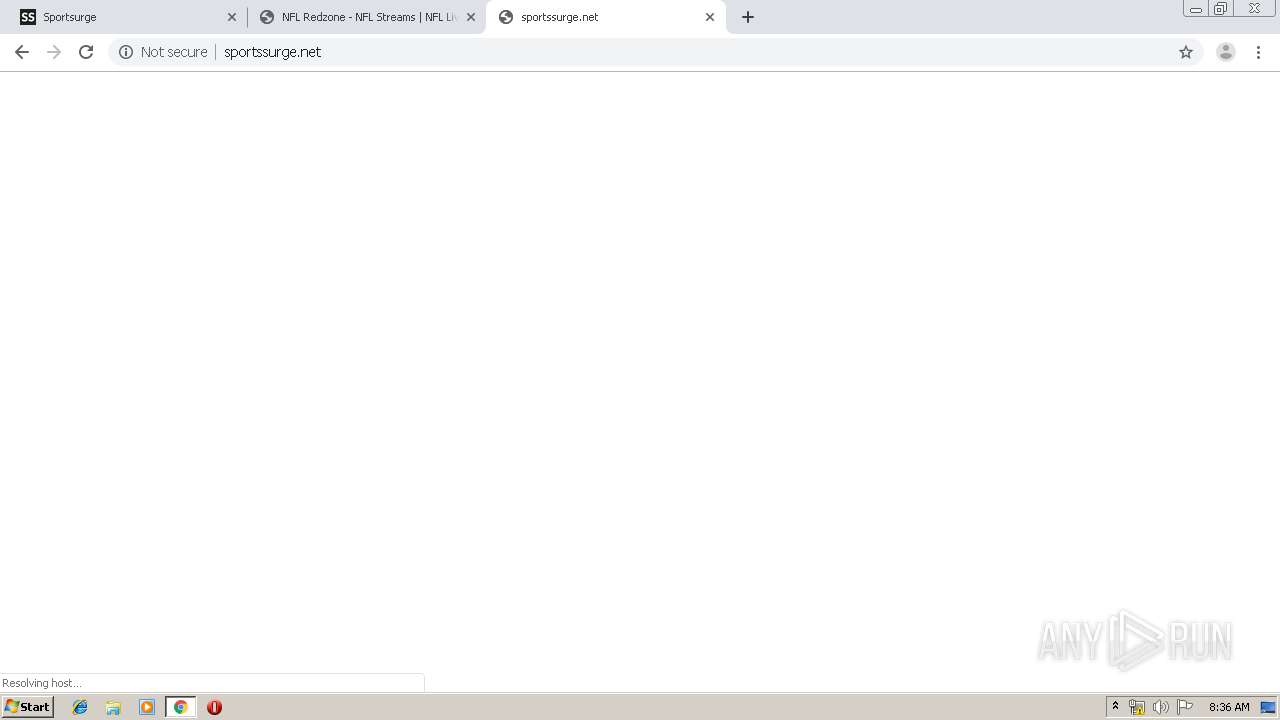
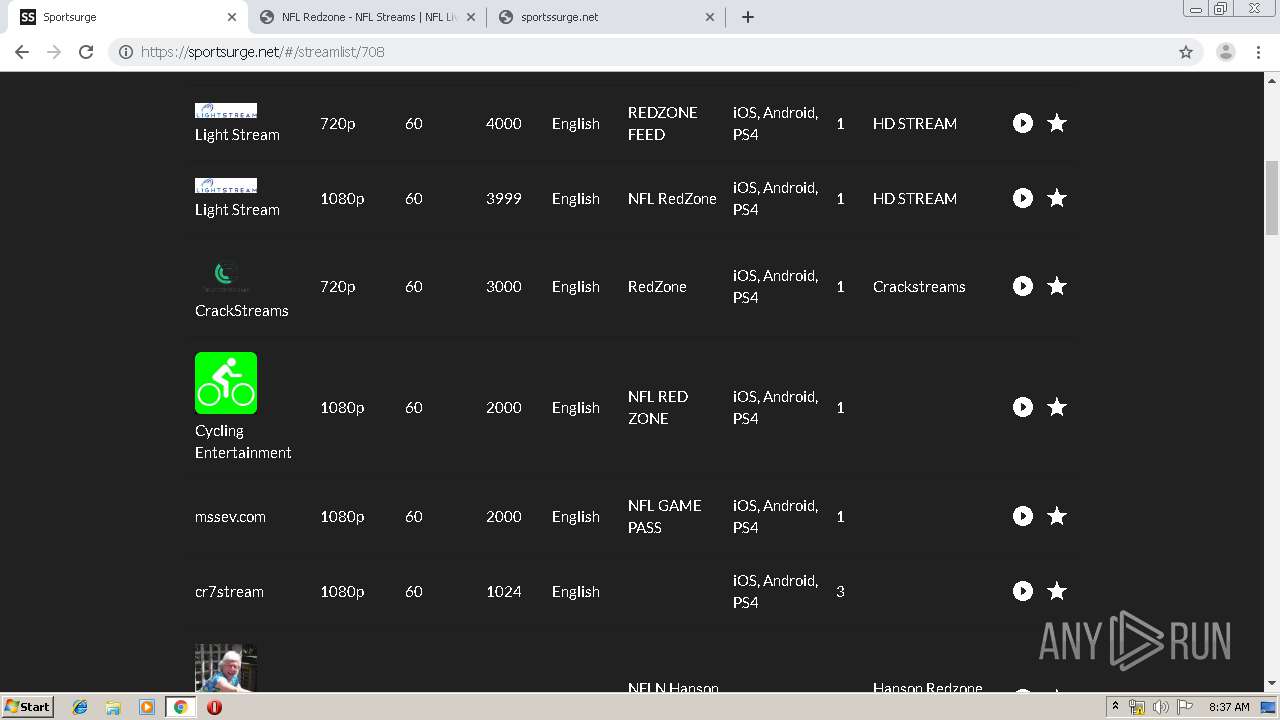
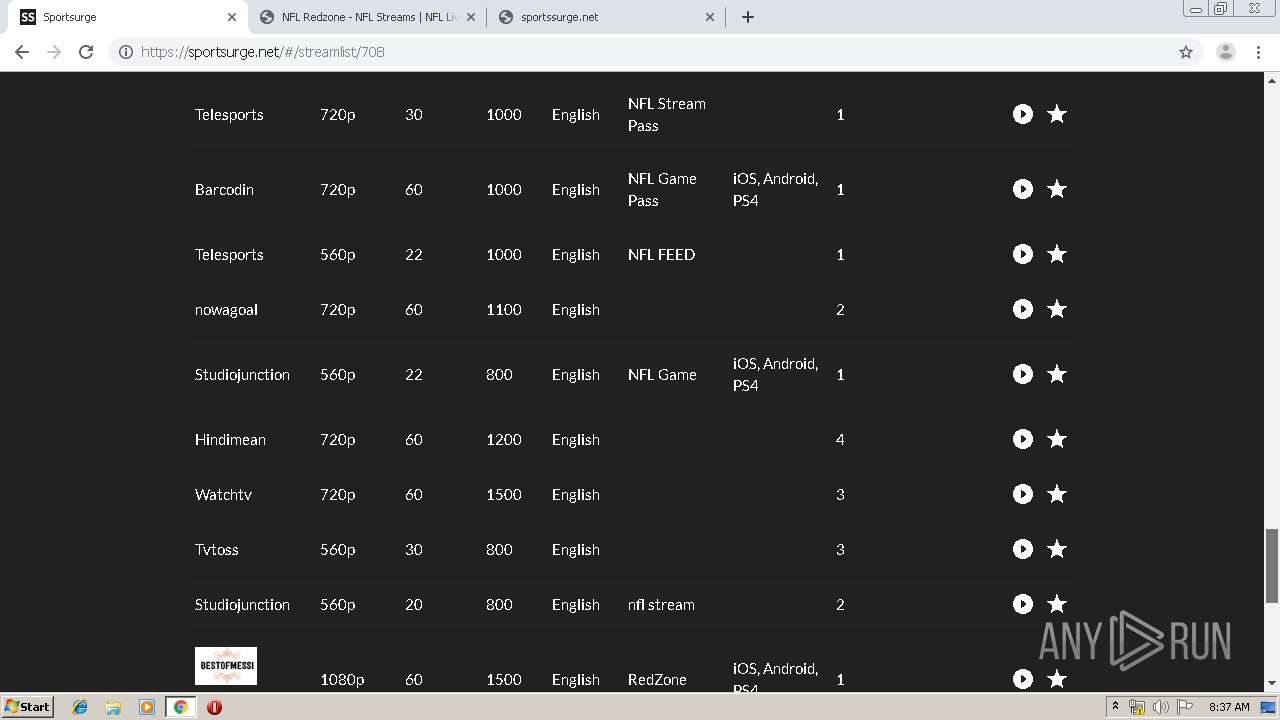
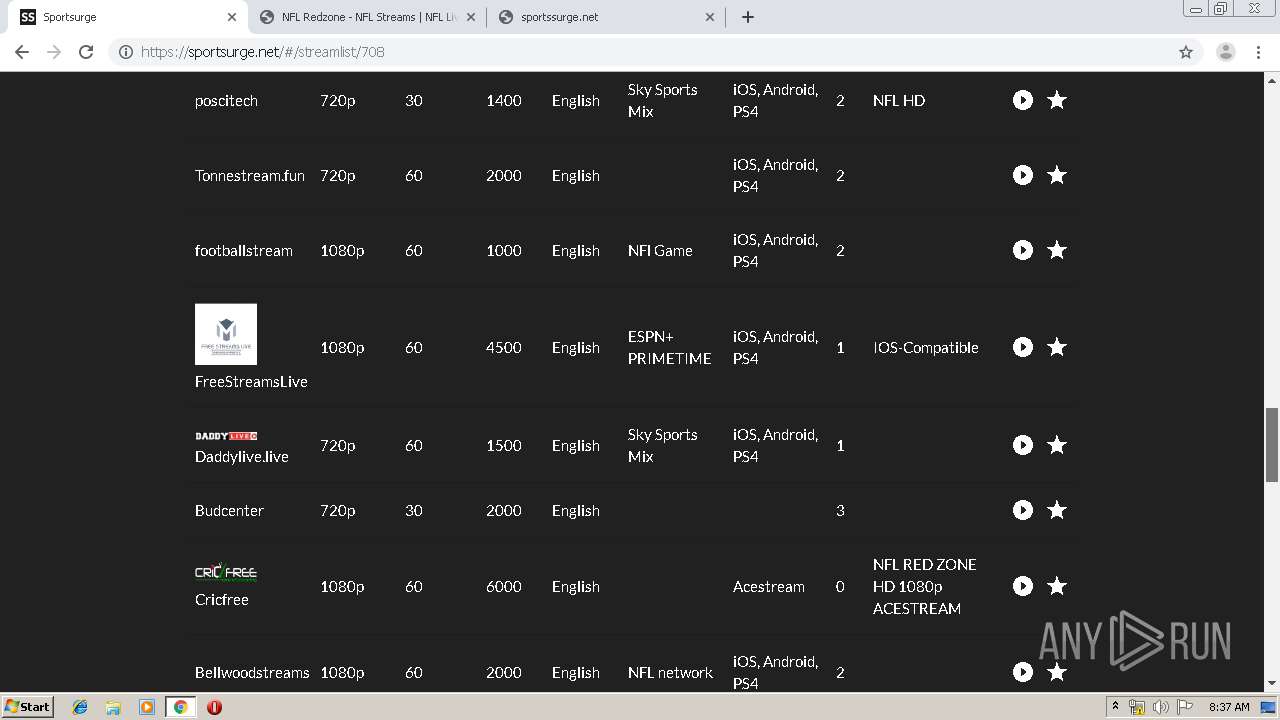
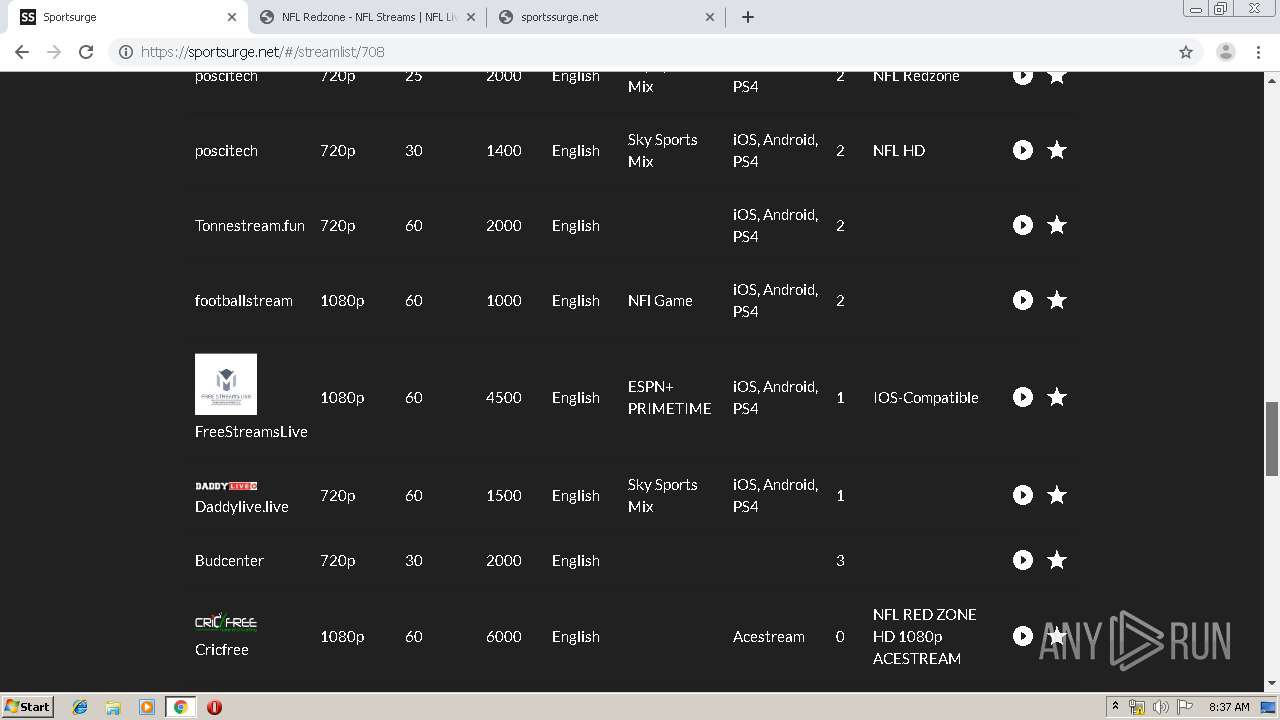
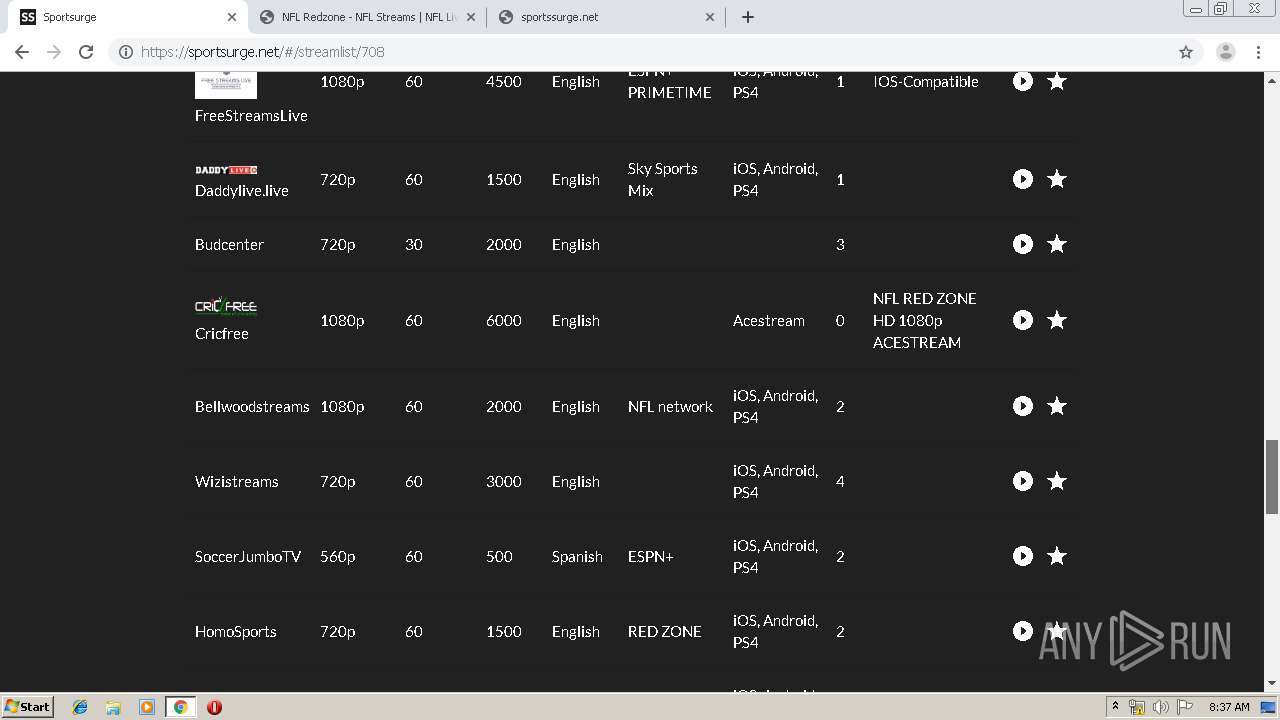
1600 | chrome.exe | GET | 301 | 104.27.165.249:80 | http://sportsurge.net/ | US | — | — | malicious |
1600 | chrome.exe | GET | 204 | 35.190.64.167:80 | http://onclickmega.com/script/suurl.php?r=2524319&cbrandom=0.8615546694459708&cbiframe=0&cbWidth=1280&cbHeight=620&cbtitle=NFL%20Redzone%20-%20NFL%20Streams%20%7C%20NFL%20Live%20%7C%20Football%20Streams&cbref=&cbdescription=nflstreams%20reddit%20-%20Watch%20NFL%20Redzone%20streams%20live.%20NFL%20Redzone%20live%20streams&cbkeywords=live%20NFL%20streams%2C%20chiefs%2C%20jaguars%2C%20watch%20superbowl%2C%20kansas%20city%20chiefs%2C%20jacksoville%20jaguars%2C%20NFL%20stream%2C%20nflstreams%2C%20preseason%20live%2C%20nfl%20preseason%20streams%2C%20watch%20preseason%20free%2C%20NFL%20score%2C%20NFL%20video&cbcdn=moneymakercdn.com&ufp=211064630412532036121477449636 | US | — | — | whitelisted |
1600 | chrome.exe | GET | 302 | 172.217.18.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 515 b | whitelisted |
1600 | chrome.exe | GET | 302 | 172.217.18.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 510 b | whitelisted |
1600 | chrome.exe | GET | 200 | 216.58.210.1:80 | http://3.bp.blogspot.com/-WZeK7dUOuZk/XXQOLN-U3fI/AAAAAAAAAKw/RQIIkPfq9JQPtM9G1swTjwkWLGyUIEinwCK4BGAYYCw/s1600/light.png | US | image | 3.65 Kb | whitelisted |
1600 | chrome.exe | GET | 200 | 104.27.172.208:80 | http://www.streameast.live/ssseast.png | US | image | 1.64 Kb | malicious |
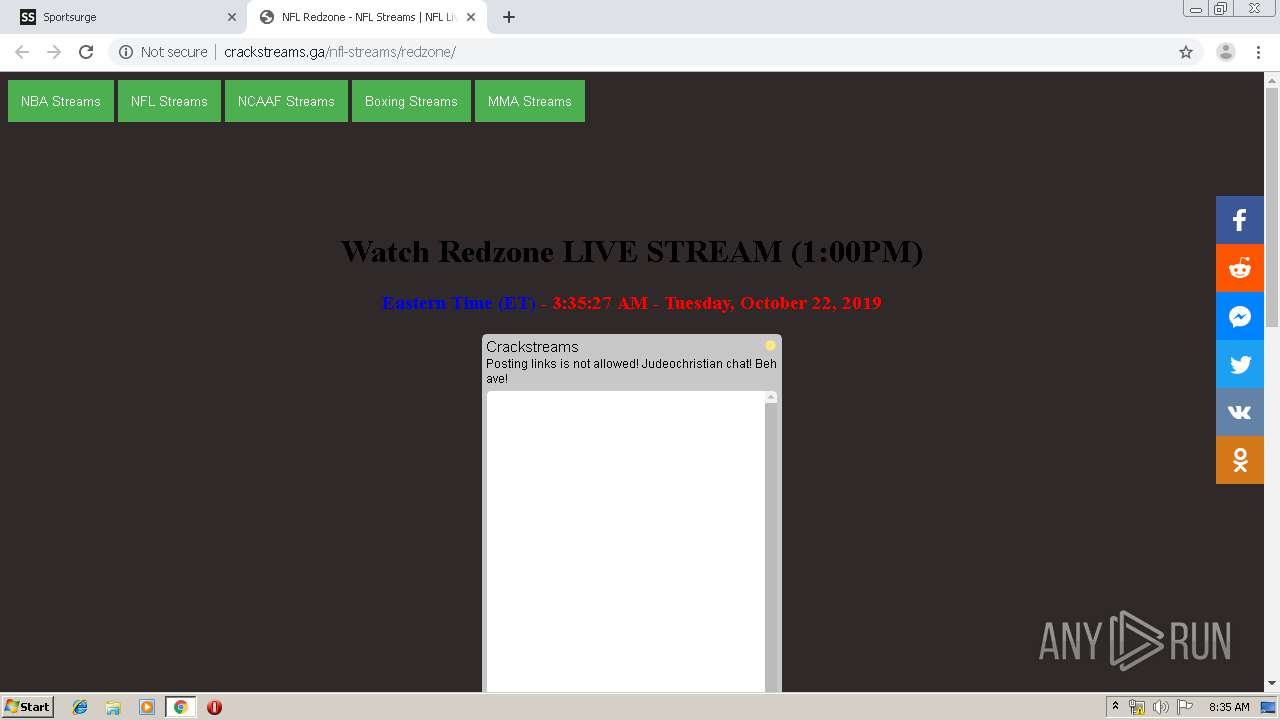
1600 | chrome.exe | GET | 200 | 104.18.59.243:80 | http://crackstreams.com/crack.png | US | image | 33.1 Kb | malicious |
1600 | chrome.exe | GET | 200 | 104.24.127.84:80 | http://zunoxhd.stream/zunoxide.png | US | image | 25.6 Kb | suspicious |
1600 | chrome.exe | GET | 200 | 104.28.31.227:80 | http://crackstreams.ga/discord.jpg | US | image | 9.75 Kb | suspicious |
1600 | chrome.exe | GET | 200 | 104.18.41.85:80 | http://w.24timezones.com/l.js | US | text | 7.49 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1600 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1600 | chrome.exe | 172.217.18.164:443 | www.google.com | Google Inc. | US | whitelisted |
— | — | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1600 | chrome.exe | 216.58.206.2:443 | adservice.google.co.uk | Google Inc. | US | whitelisted |
1600 | chrome.exe | 172.217.16.162:443 | googleads.g.doubleclick.net | Google Inc. | US | whitelisted |
1600 | chrome.exe | 104.27.165.249:80 | sportsurge.net | Cloudflare Inc | US | unknown |
1600 | chrome.exe | 104.27.165.249:443 | sportsurge.net | Cloudflare Inc | US | unknown |
1600 | chrome.exe | 216.58.205.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1600 | chrome.exe | 209.197.3.24:443 | code.jquery.com | Highwinds Network Group, Inc. | US | malicious |
1600 | chrome.exe | 172.217.16.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
consent.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
www.google.co.uk |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .ga Domain |
1600 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
1600 | chrome.exe | A Network Trojan was detected | ET CNC Ransomware Tracker Reported CnC Server group 59 |
1 ETPRO signatures available at the full report