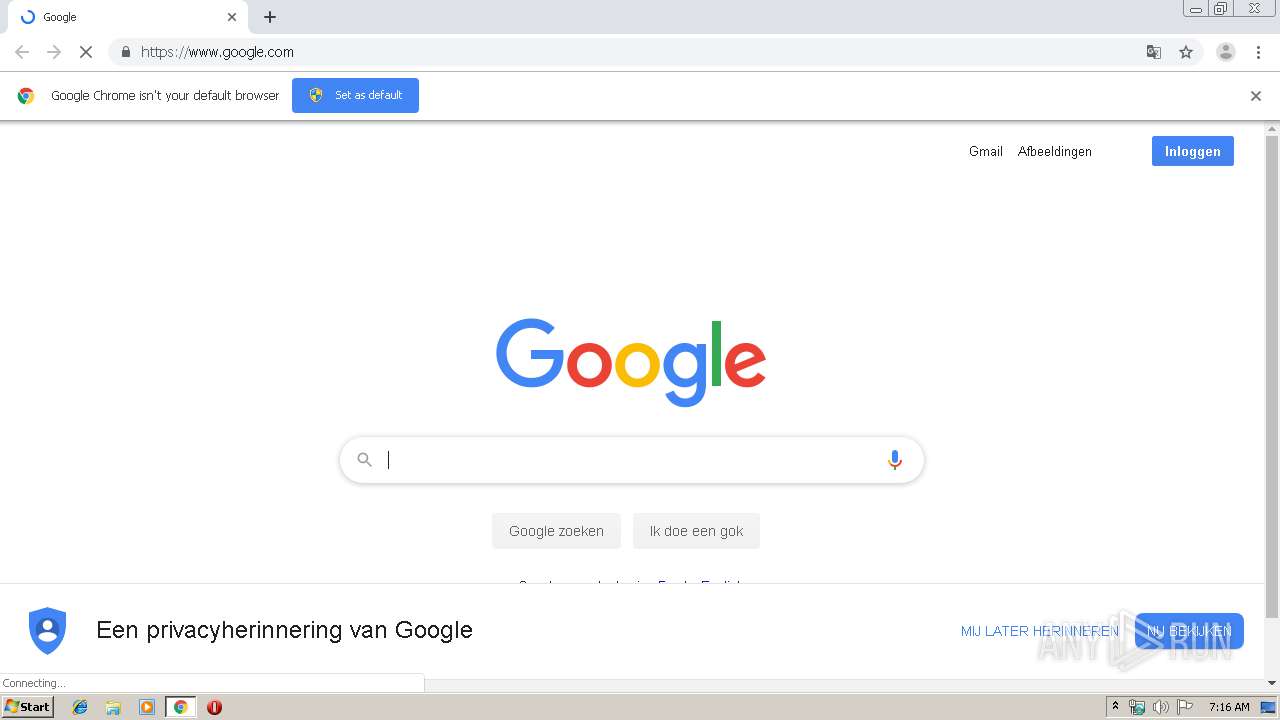
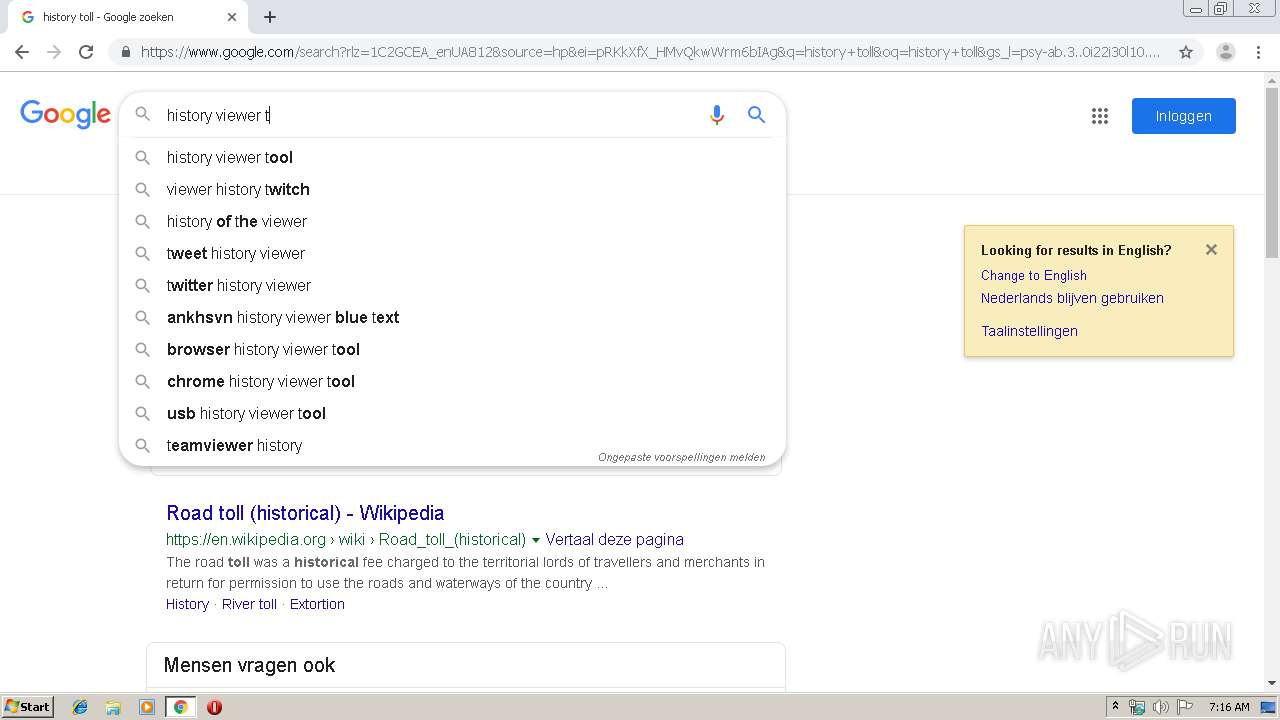
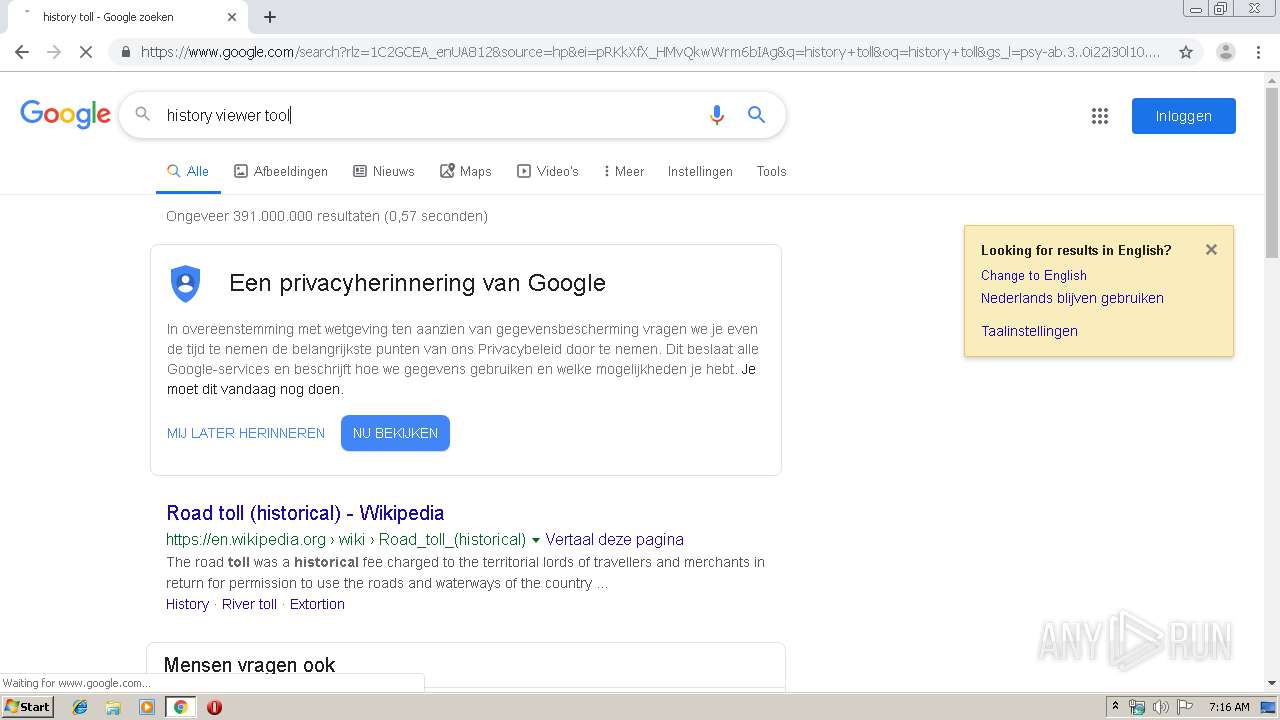
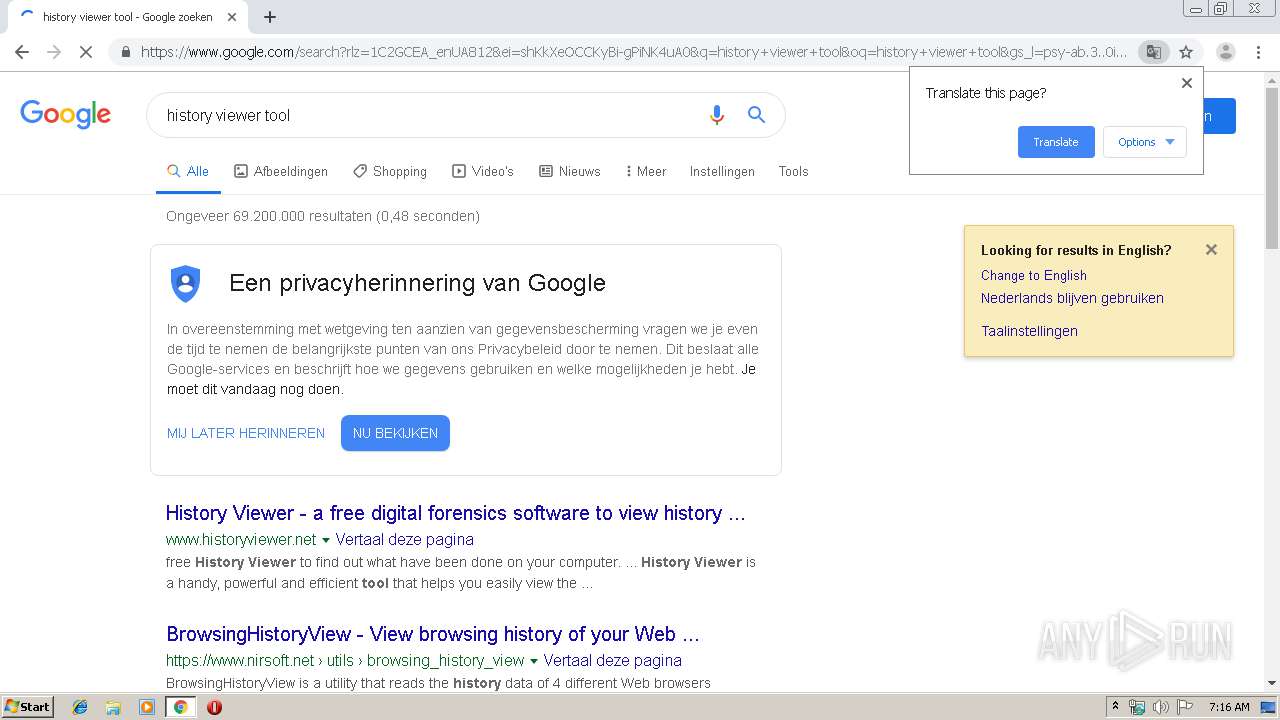
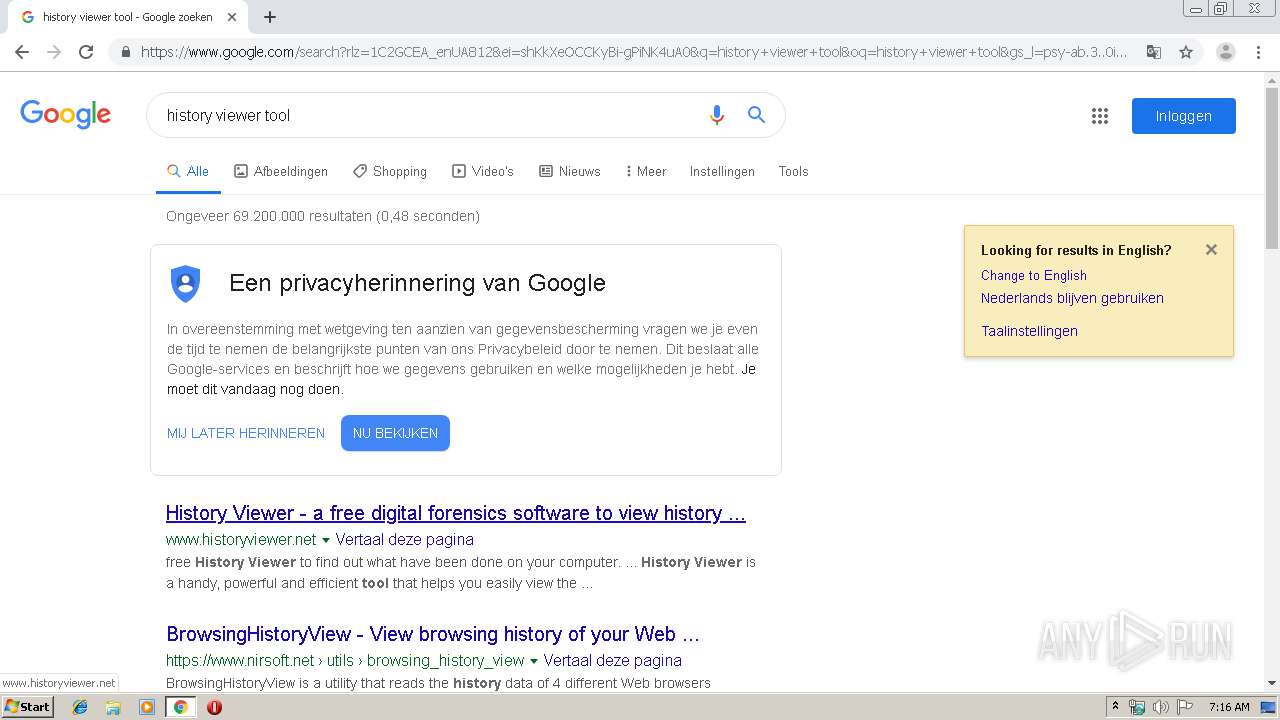
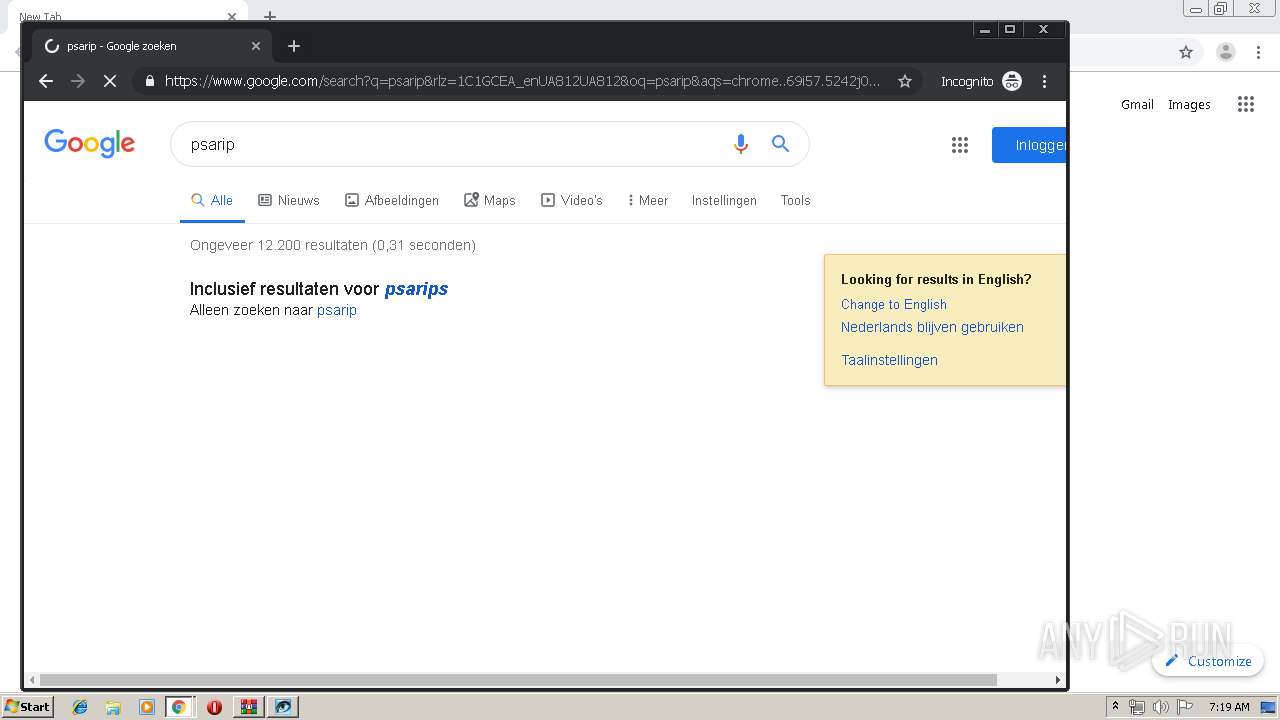
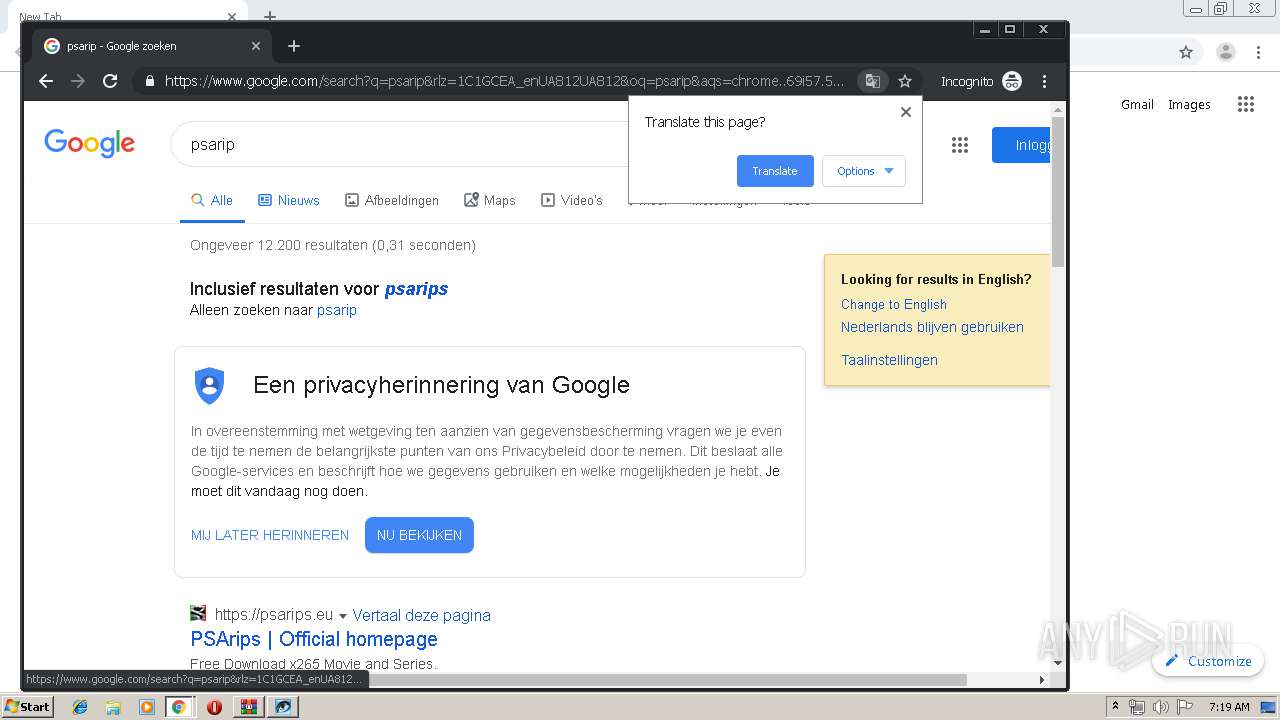
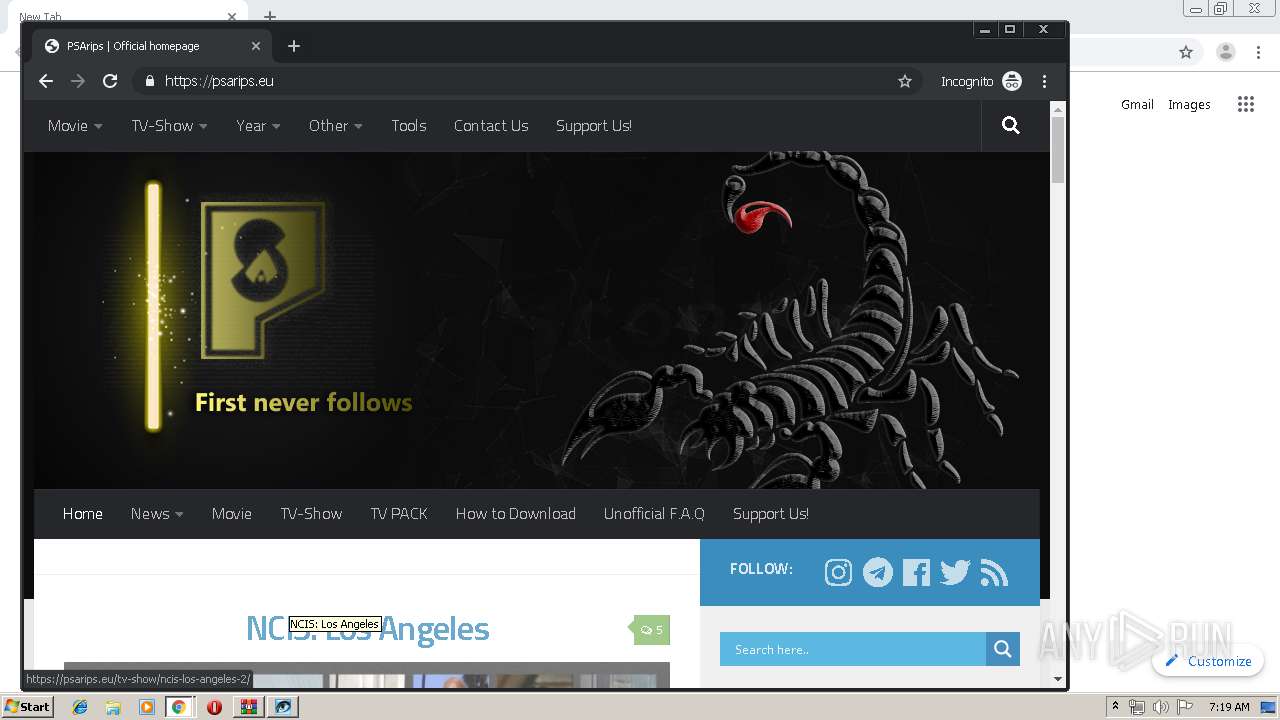
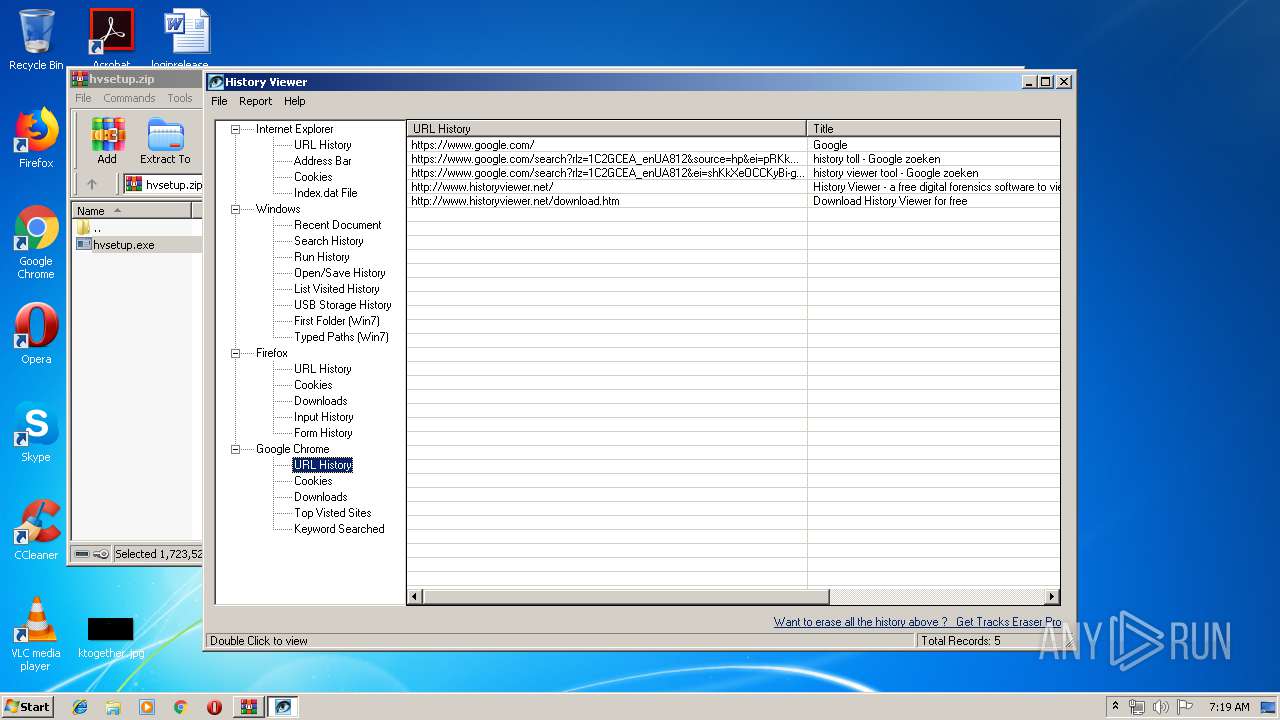
| URL: | https://www.google.com |
| Full analysis: | https://app.any.run/tasks/343bcbaf-f98f-48e6-9b04-fc155a00e783 |
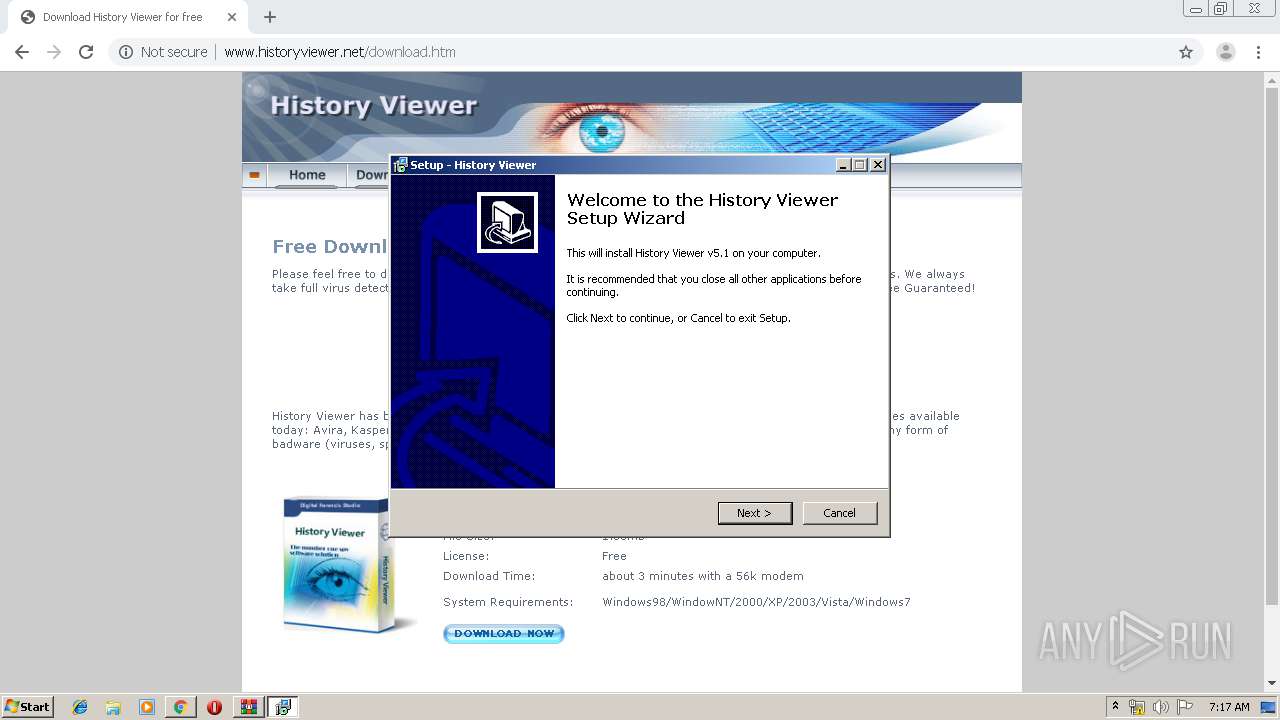
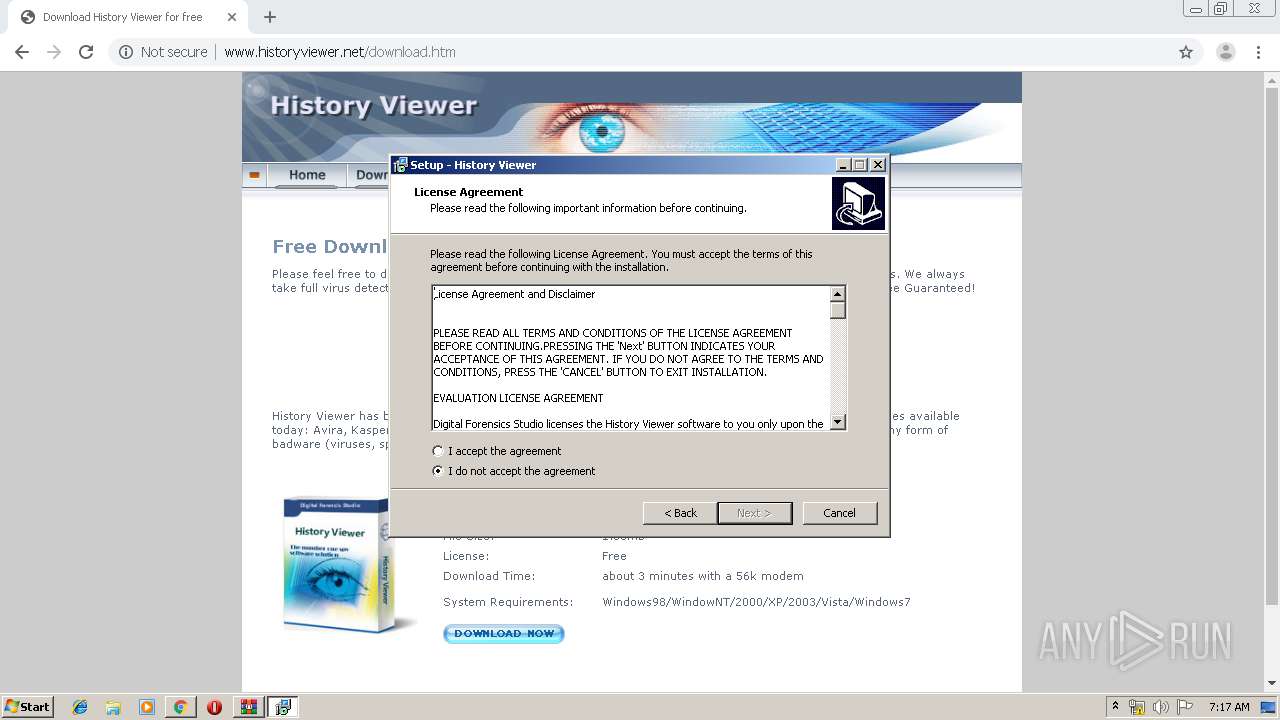
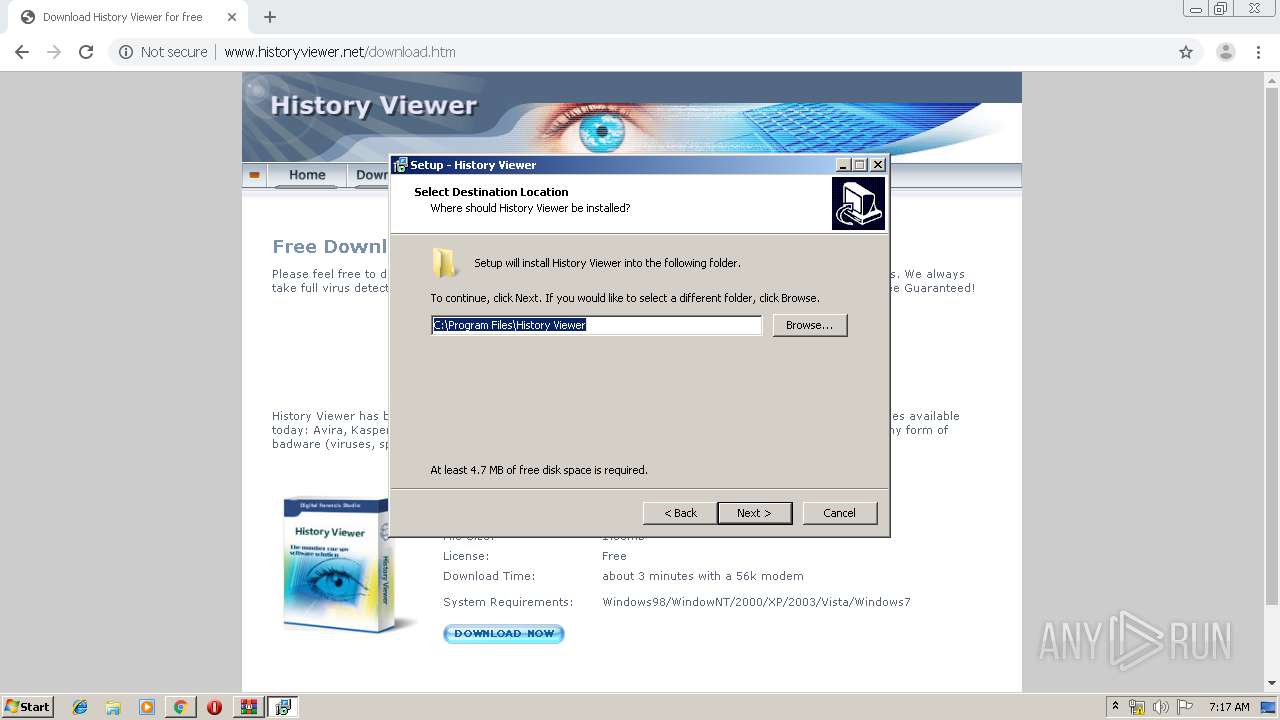
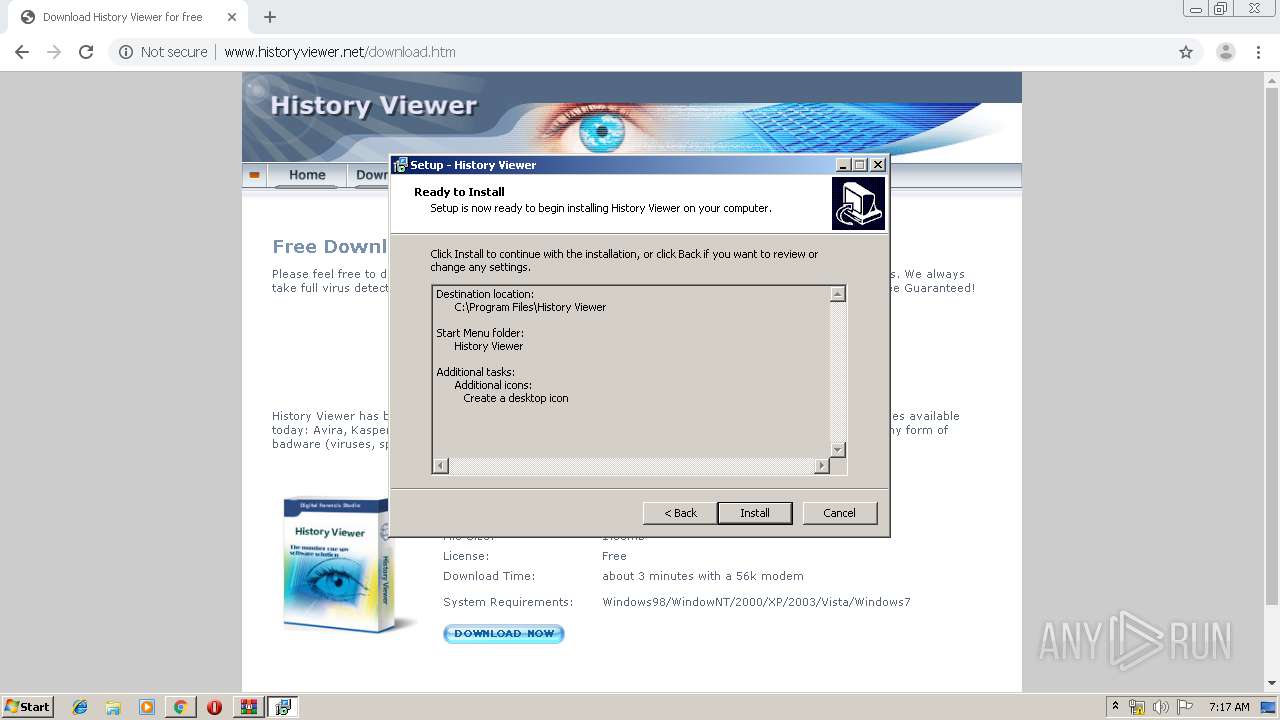
| Verdict: | Malicious activity |
| Analysis date: | October 14, 2019, 06:15:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 8FFDEFBDEC956B595D257F0AAEEFD623 |
| SHA1: | EF7EFC9839C3EE036F023E9635BC3B056D6EE2DB |
| SHA256: | AC6BB669E40E44A8D9F8F0C94DFC63734049DCF6219AAC77F02EDF94B9162C09 |
| SSDEEP: | 3:N8DSLIK:2OLIK |
MALICIOUS
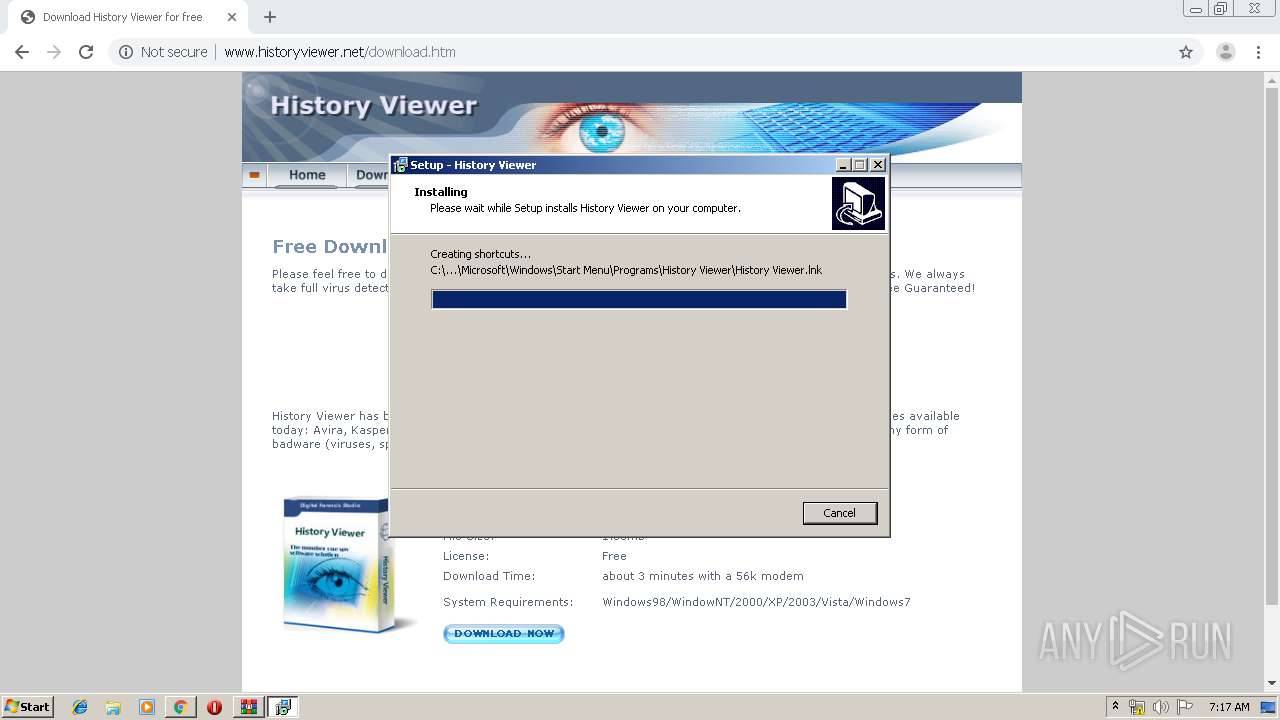
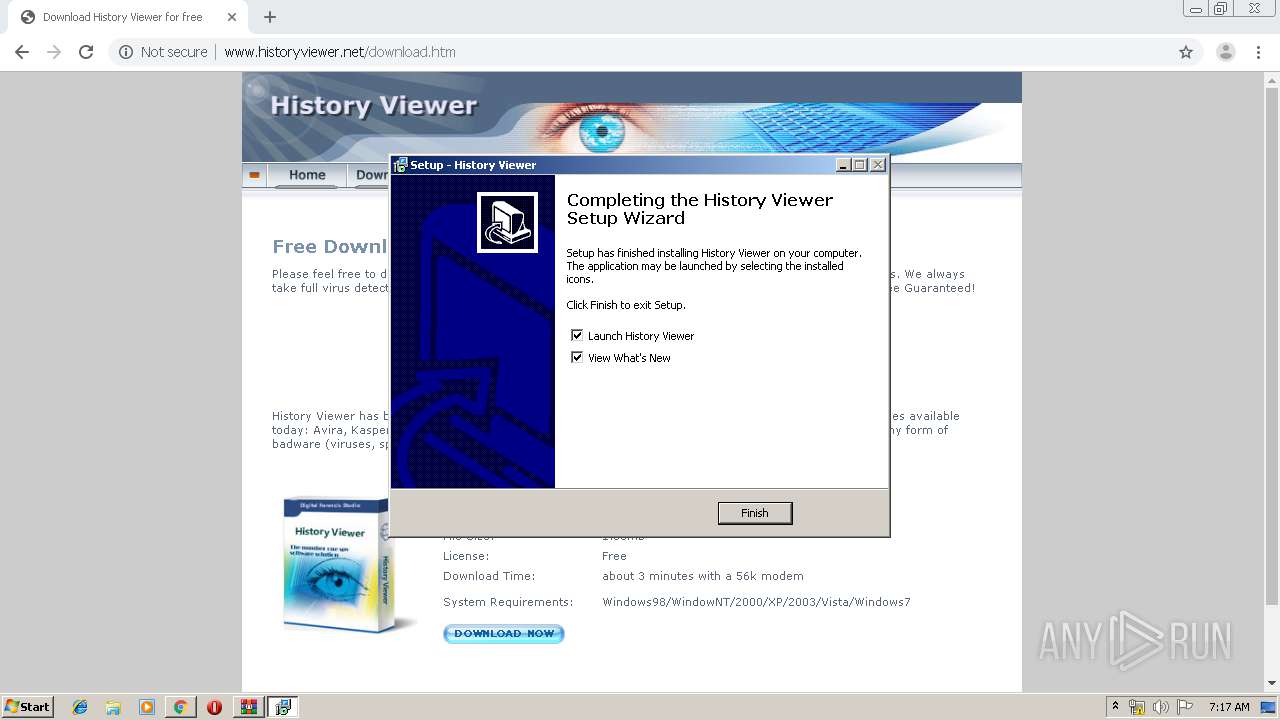
Application was dropped or rewritten from another process
- hvsetup.exe (PID: 2136)
- hvsetup.exe (PID: 1412)
- hviewer.exe (PID: 4016)
- hviewer.exe (PID: 2348)
Connects to CnC server
- hvsetup.tmp (PID: 3816)
Registers / Runs the DLL via REGSVR32.EXE
- hvsetup.tmp (PID: 3816)
Loads dropped or rewritten executable
- regsvr32.exe (PID: 3296)
- hviewer.exe (PID: 4016)
- hviewer.exe (PID: 2348)
SUSPICIOUS
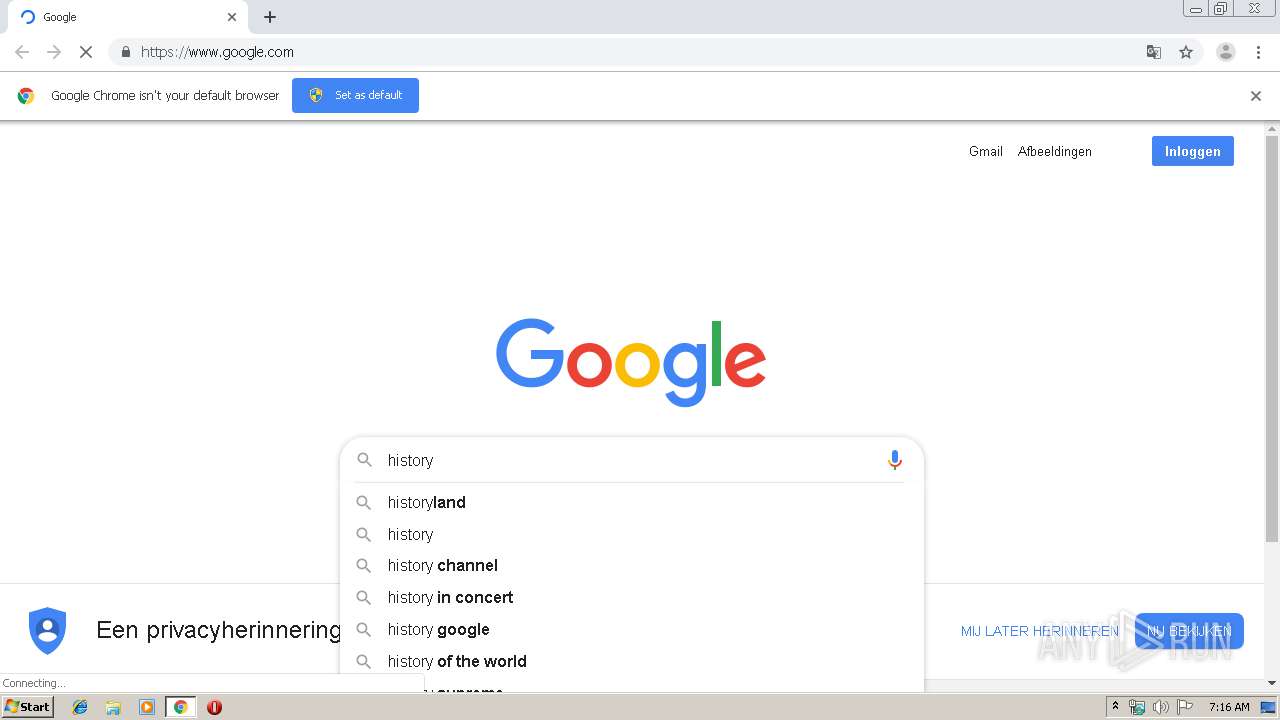
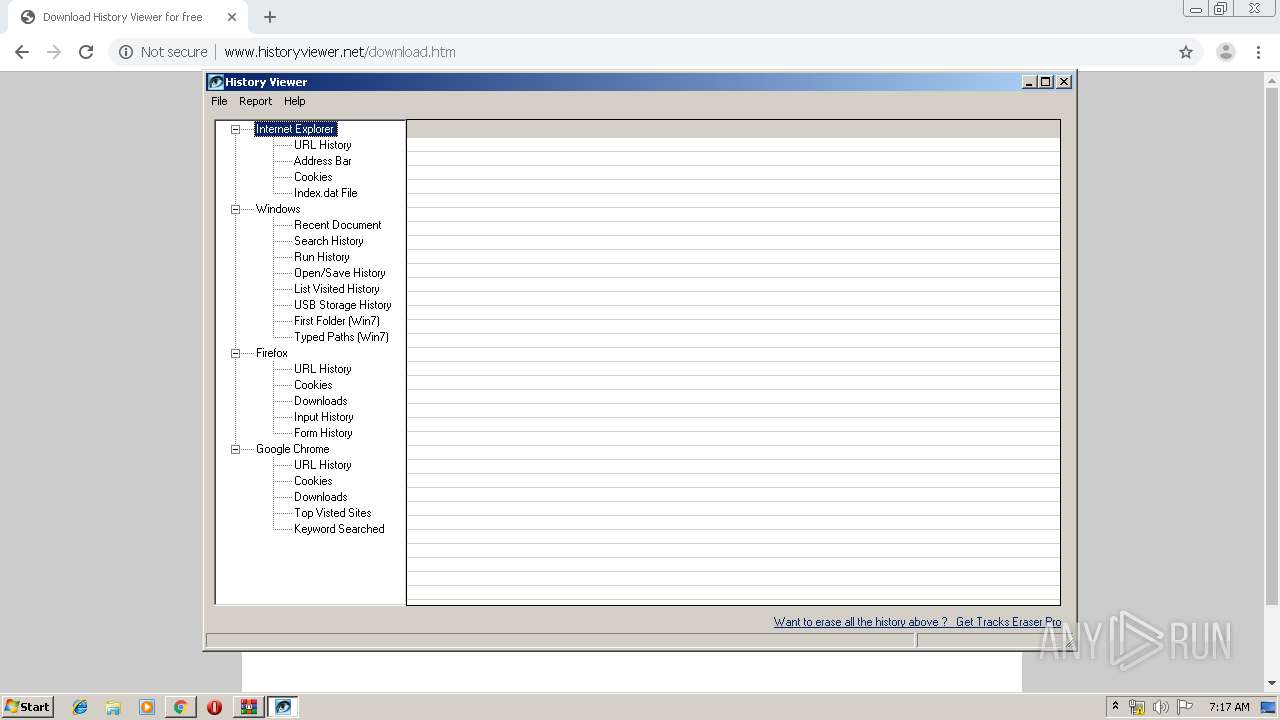
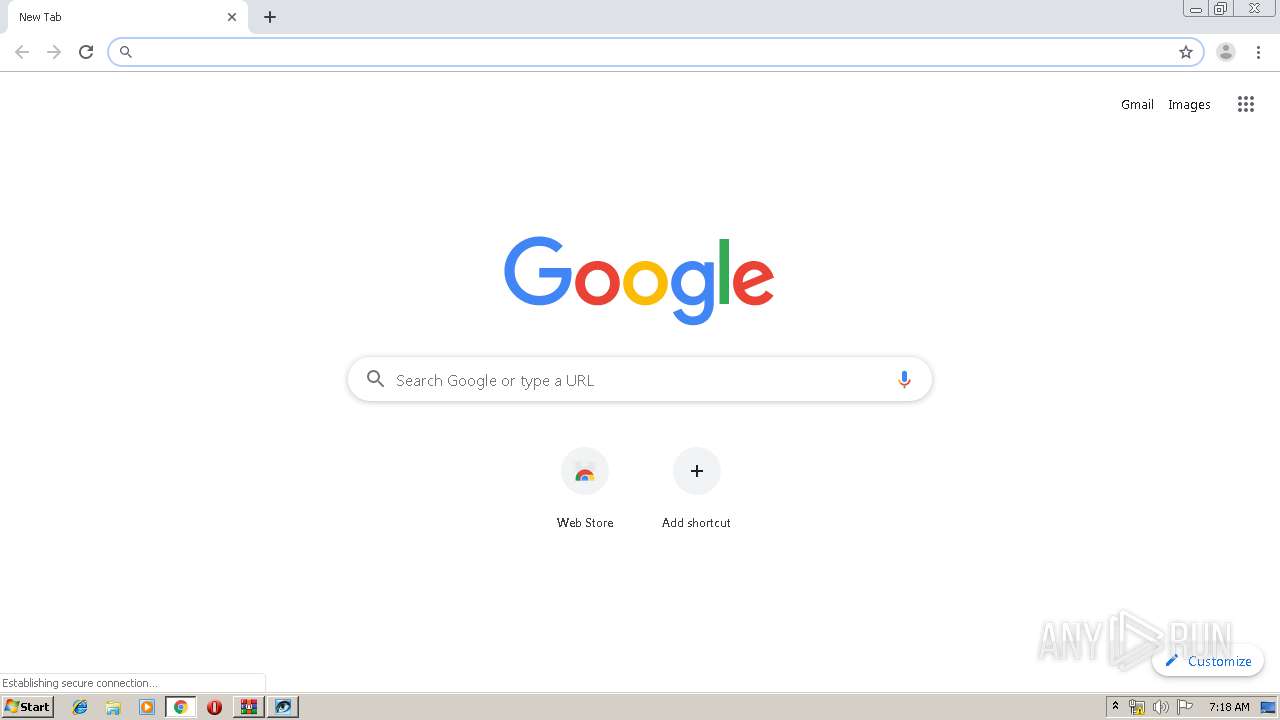
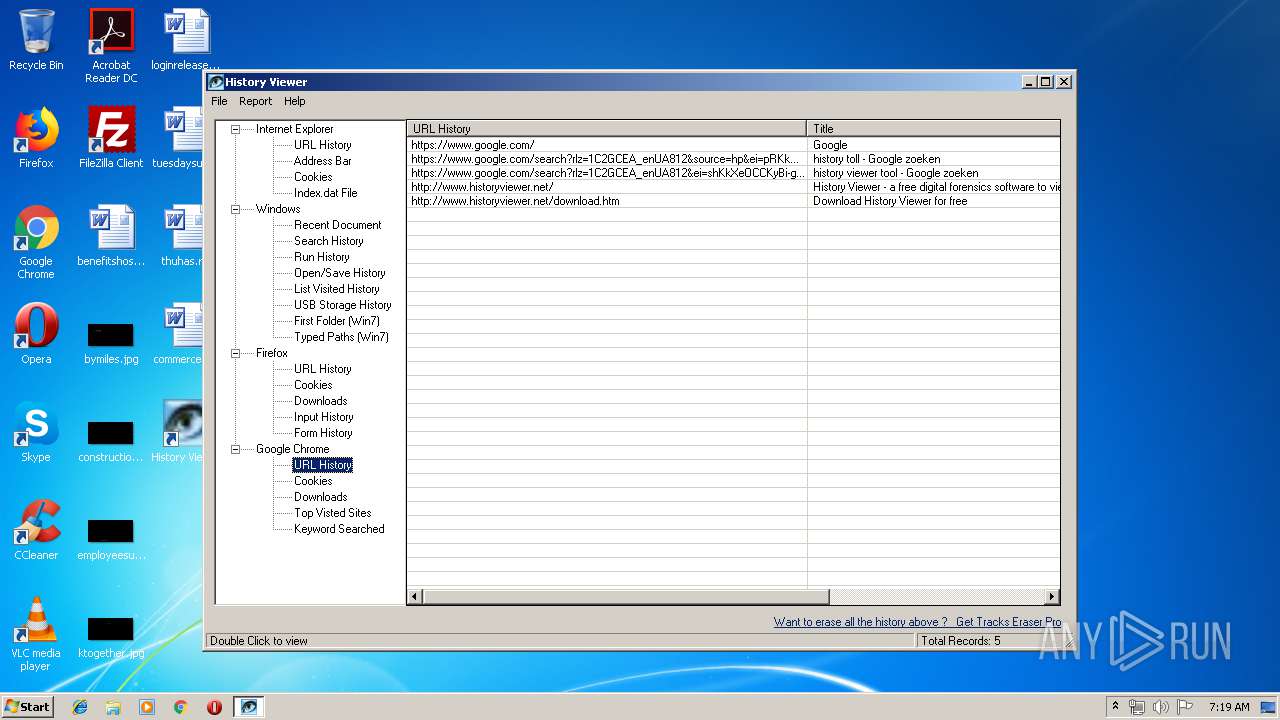
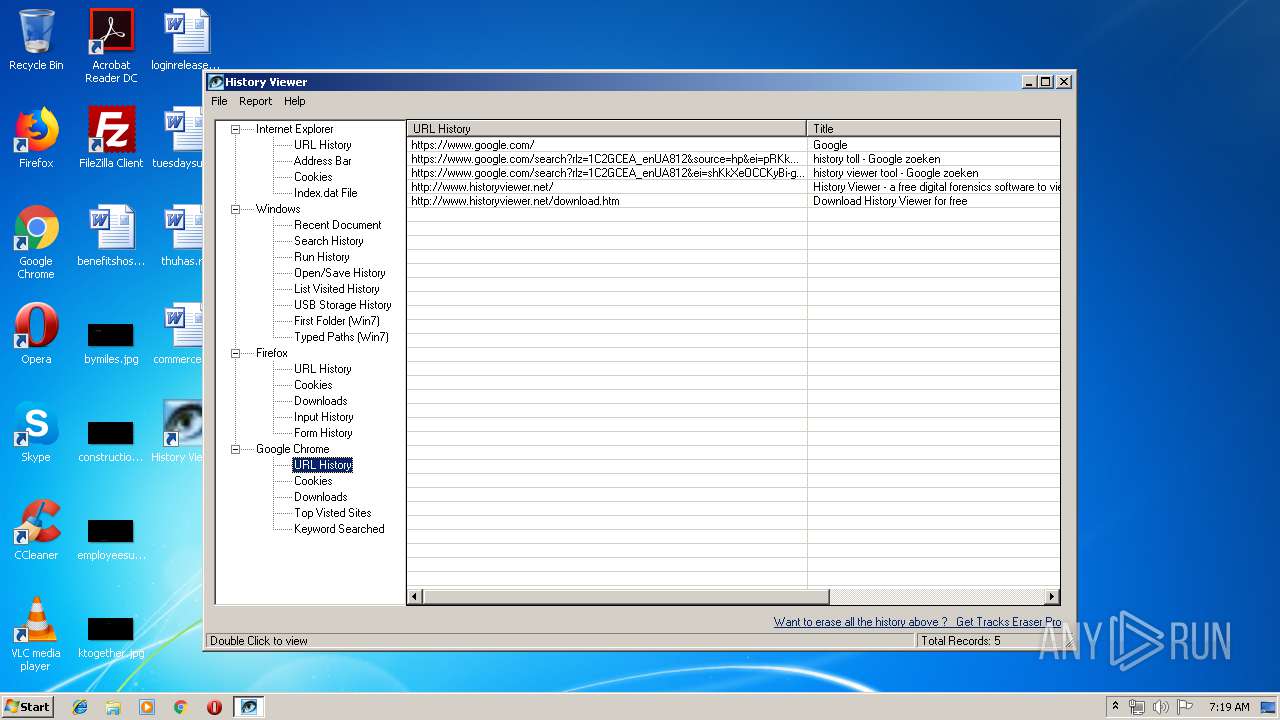
Modifies files in Chrome extension folder
- chrome.exe (PID: 2088)
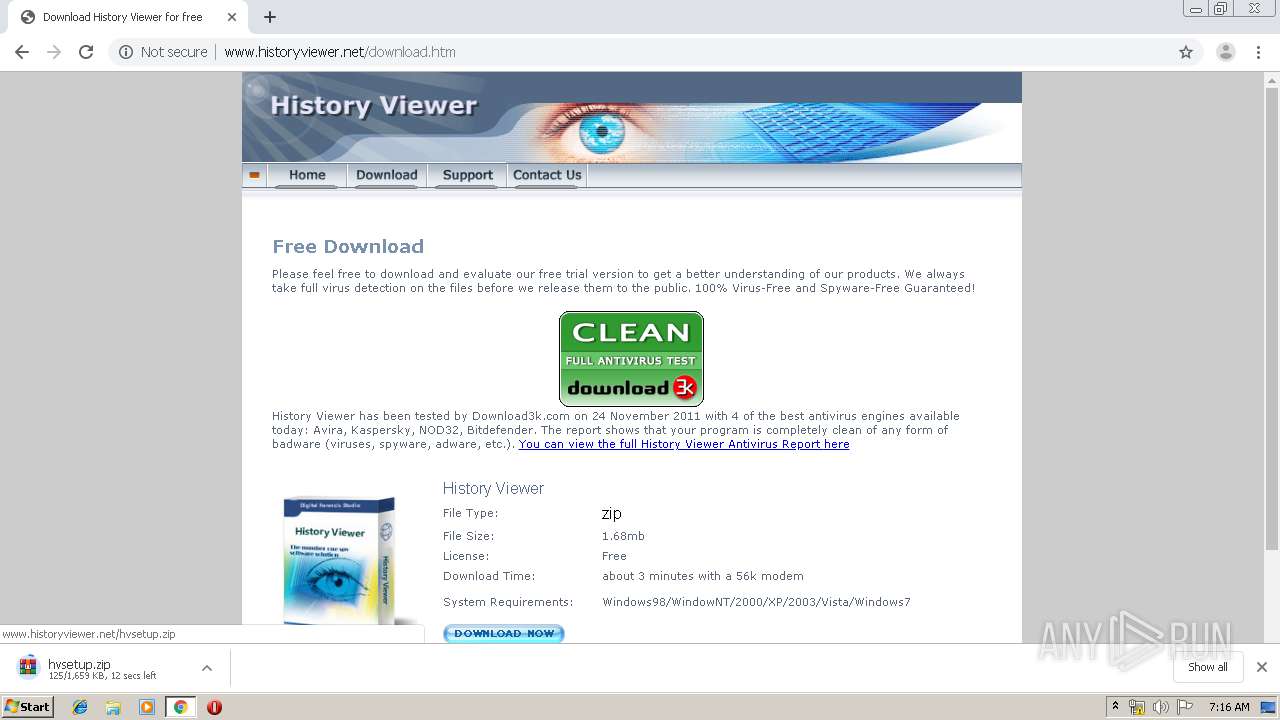
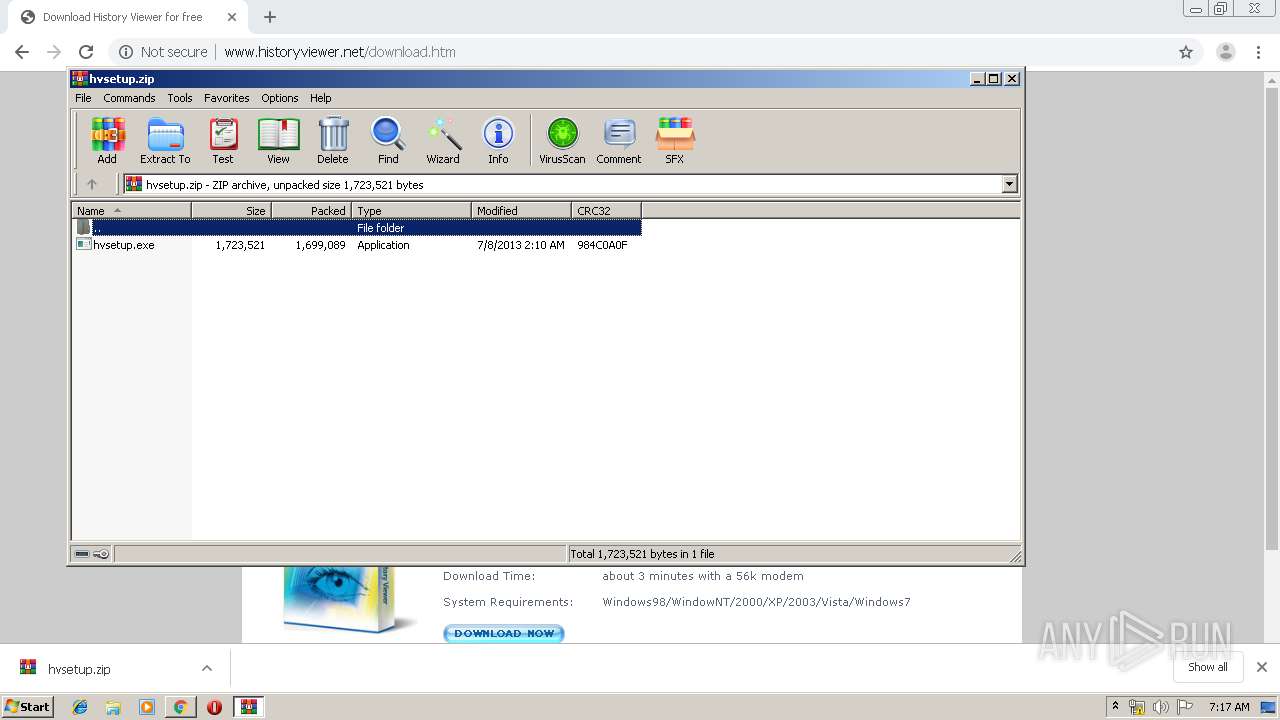
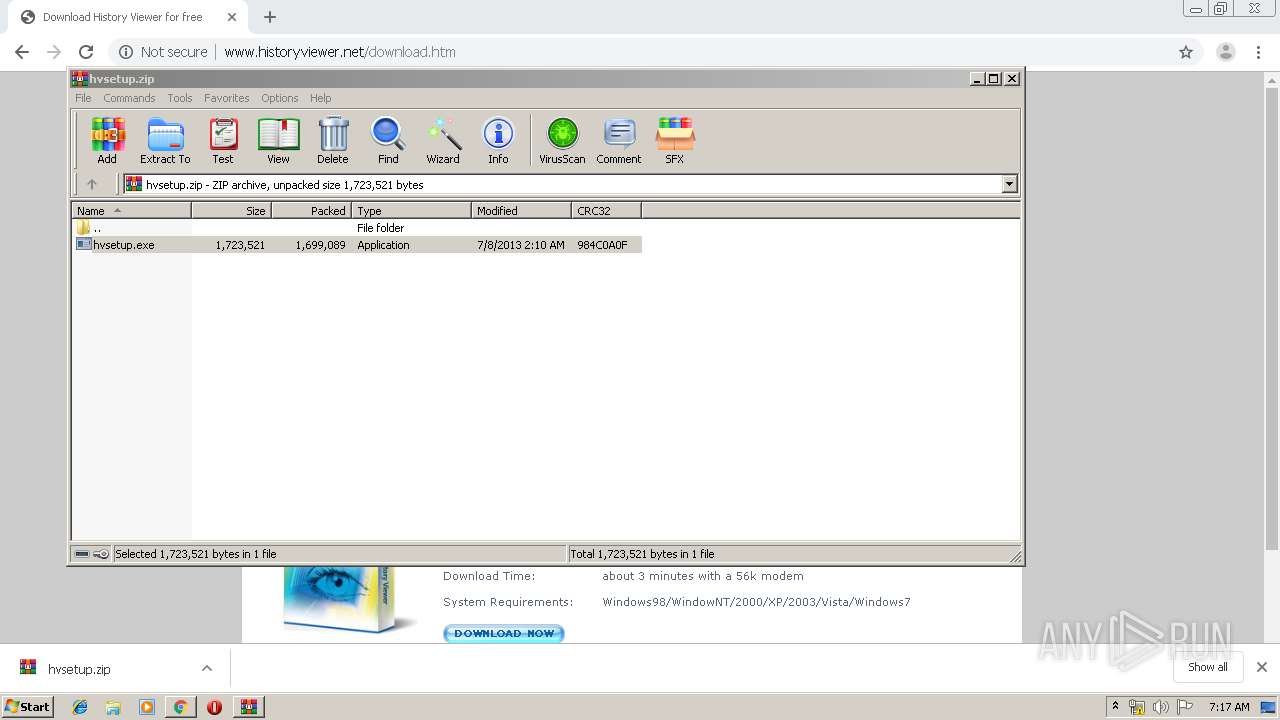
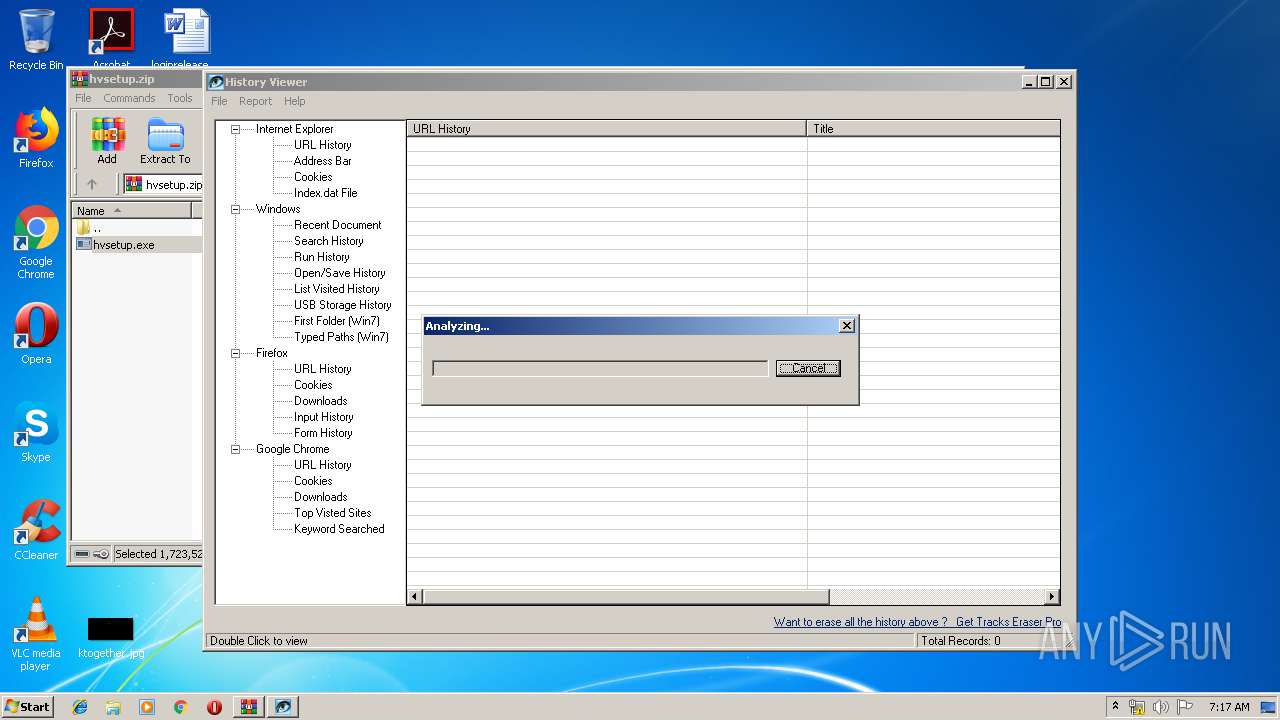
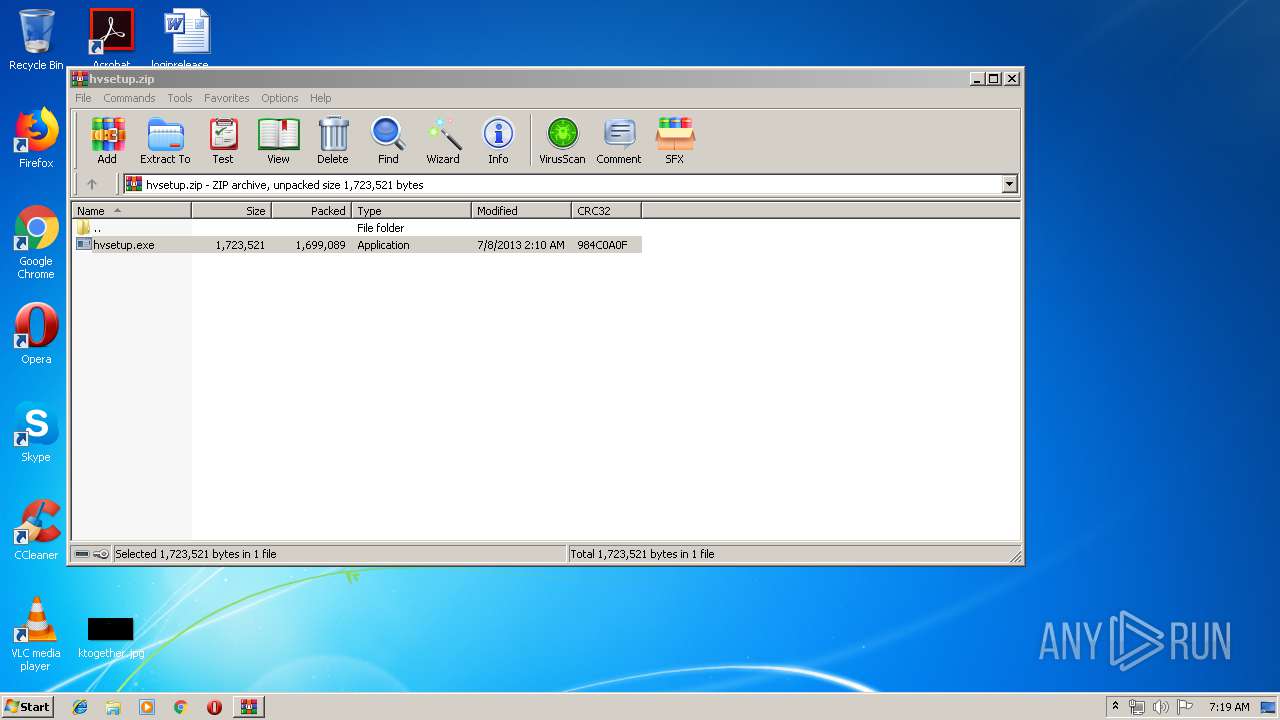
Executable content was dropped or overwritten
- hvsetup.exe (PID: 2136)
- WinRAR.exe (PID: 1936)
- hvsetup.exe (PID: 1412)
- hvsetup.tmp (PID: 3816)
Creates files in the Windows directory
- hvsetup.tmp (PID: 3816)
Creates COM task schedule object
- regsvr32.exe (PID: 2744)
Creates files in the program directory
- hviewer.exe (PID: 4016)
Creates files in the user directory
- hviewer.exe (PID: 4016)
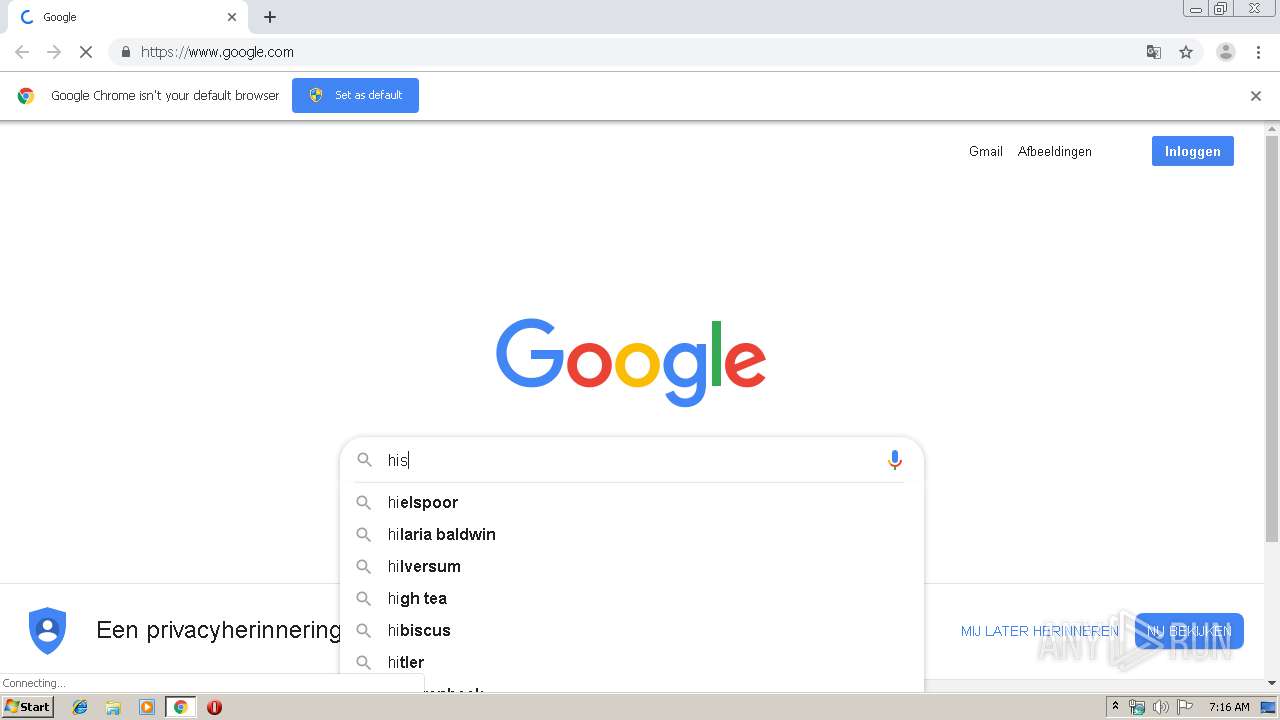
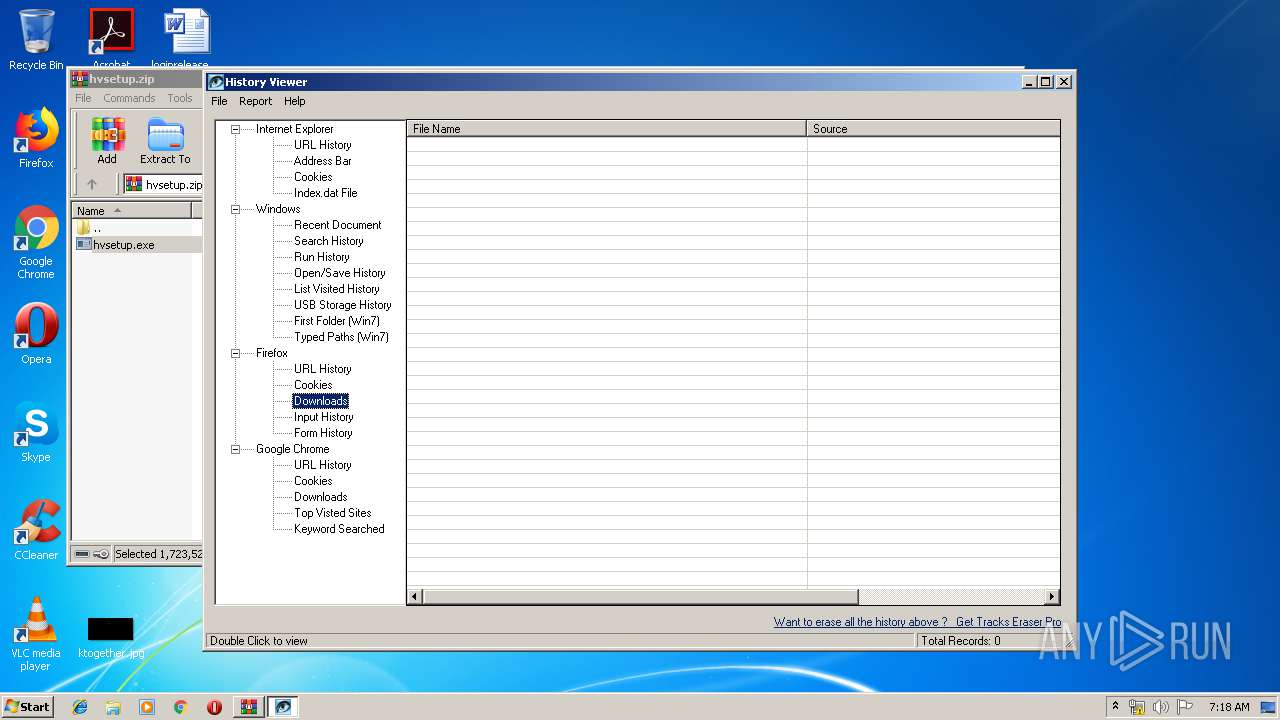
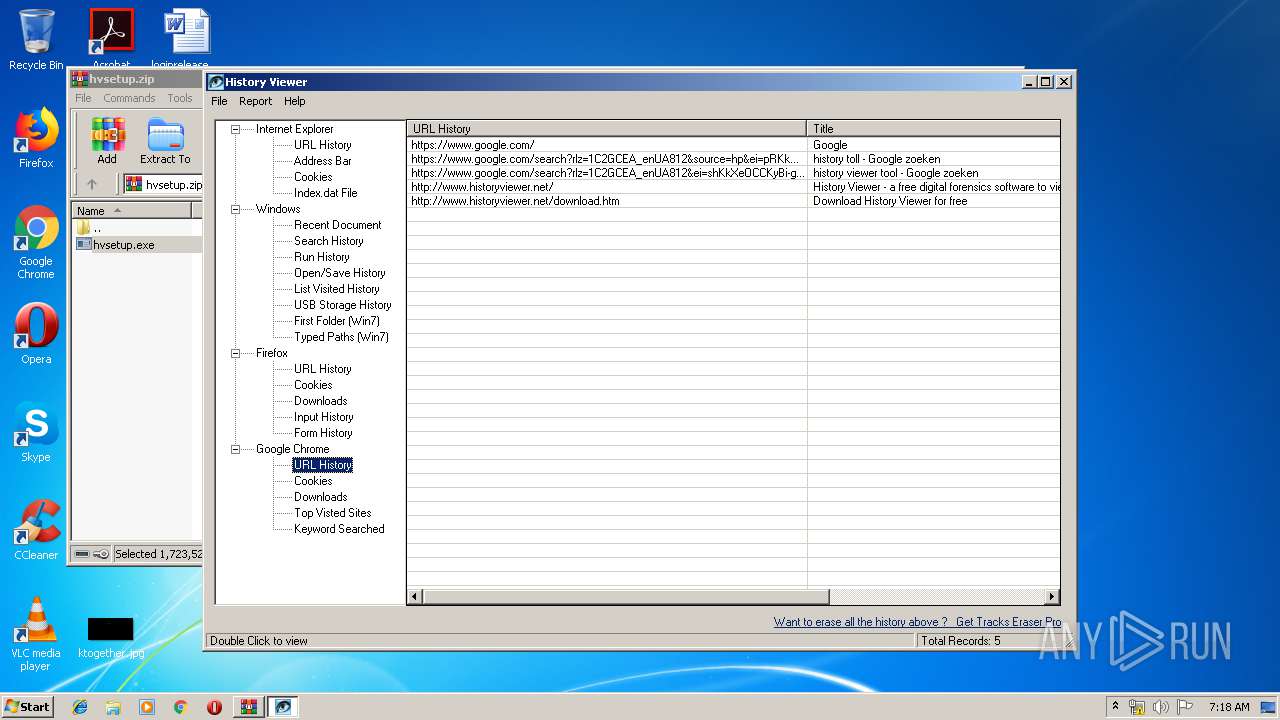
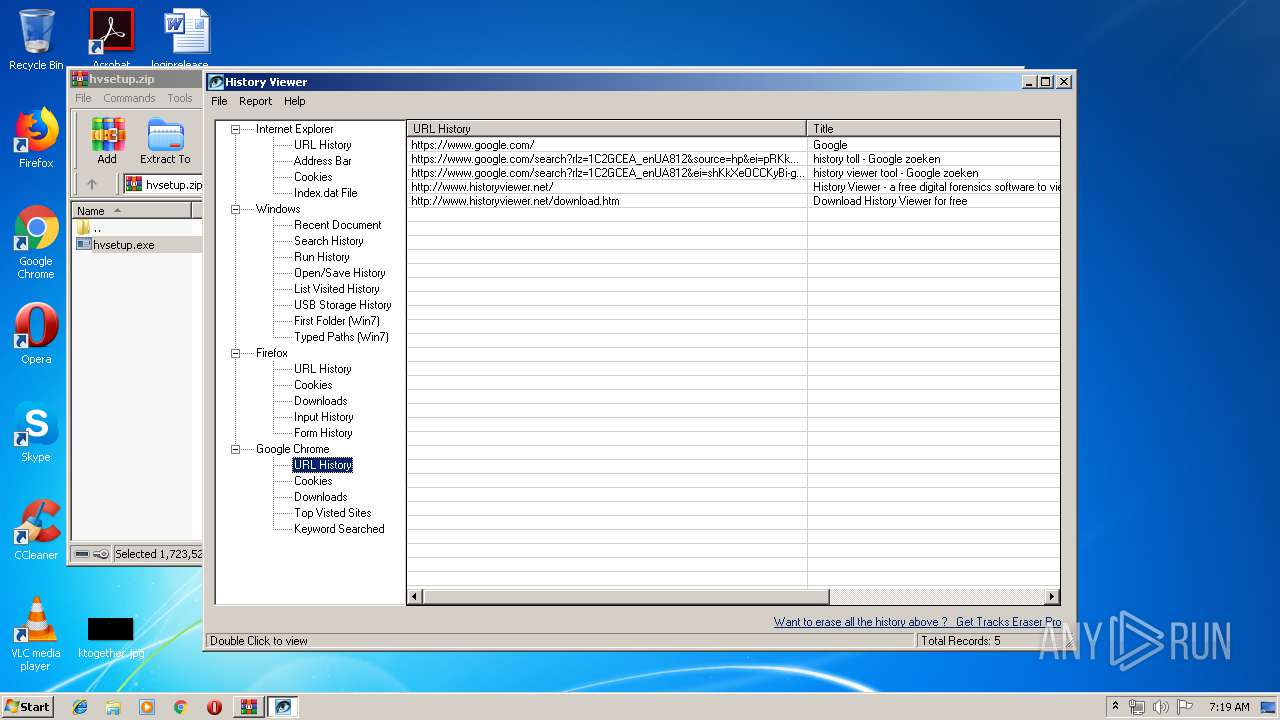
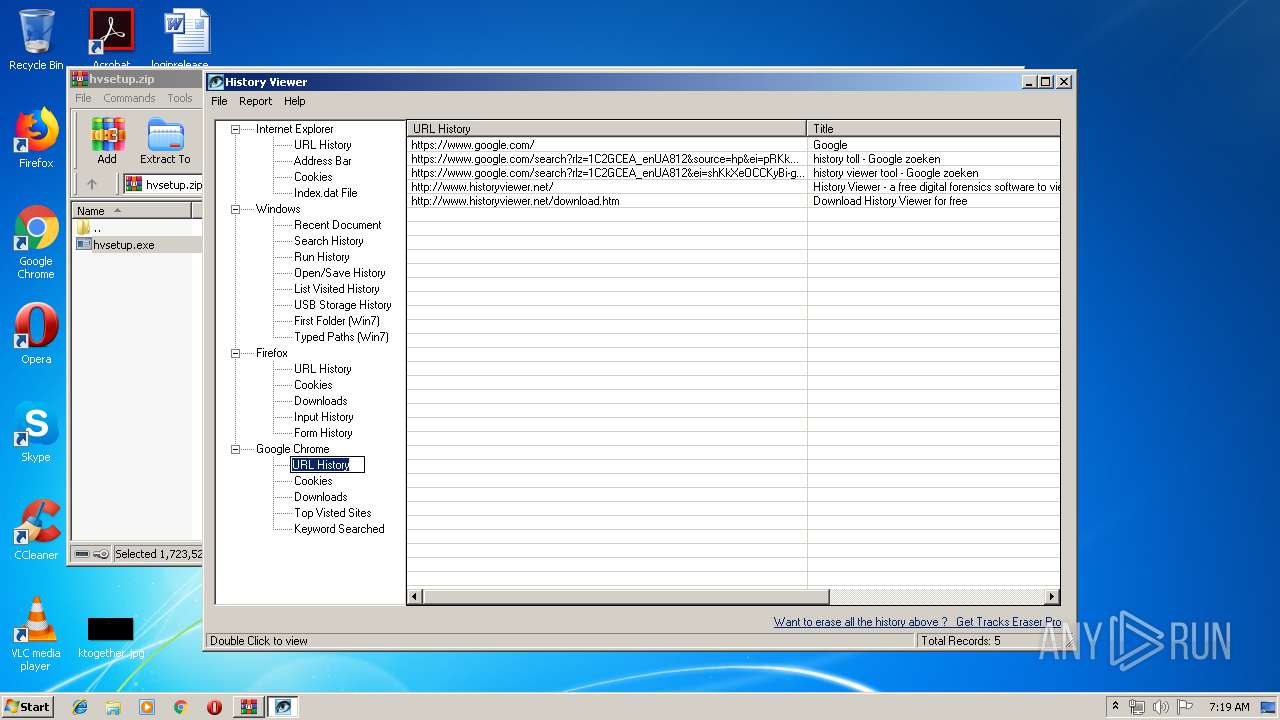
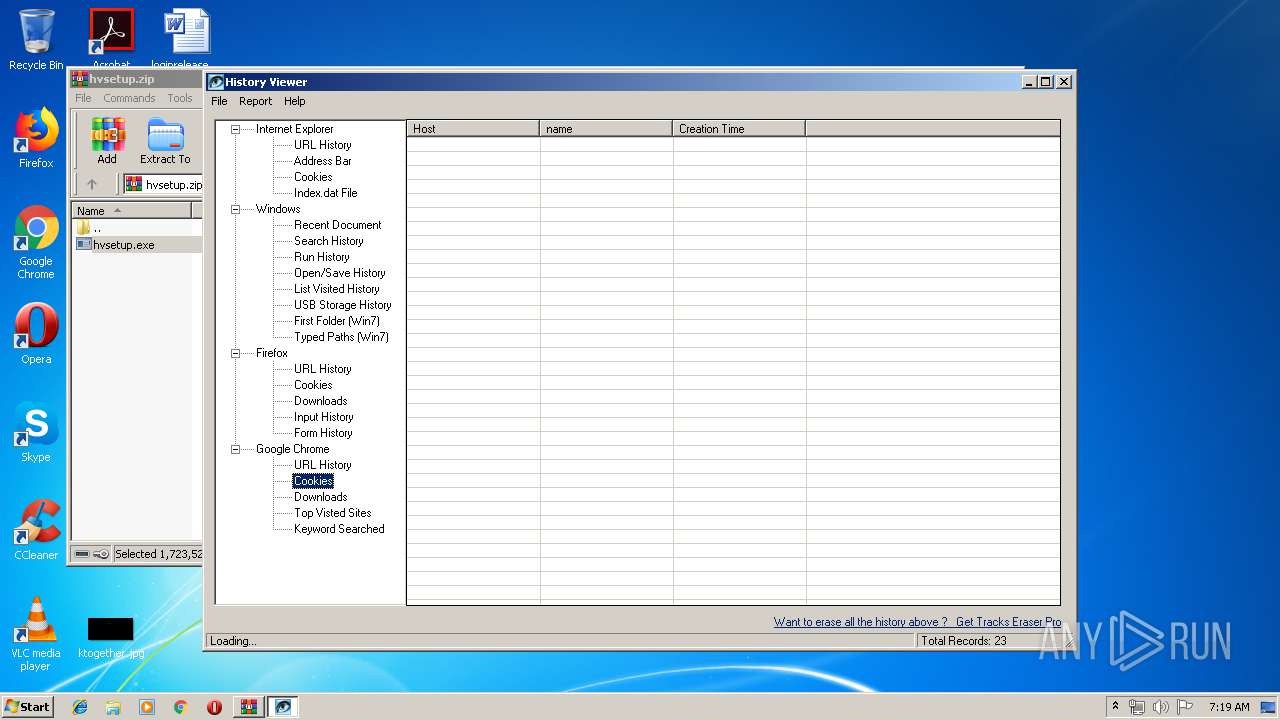
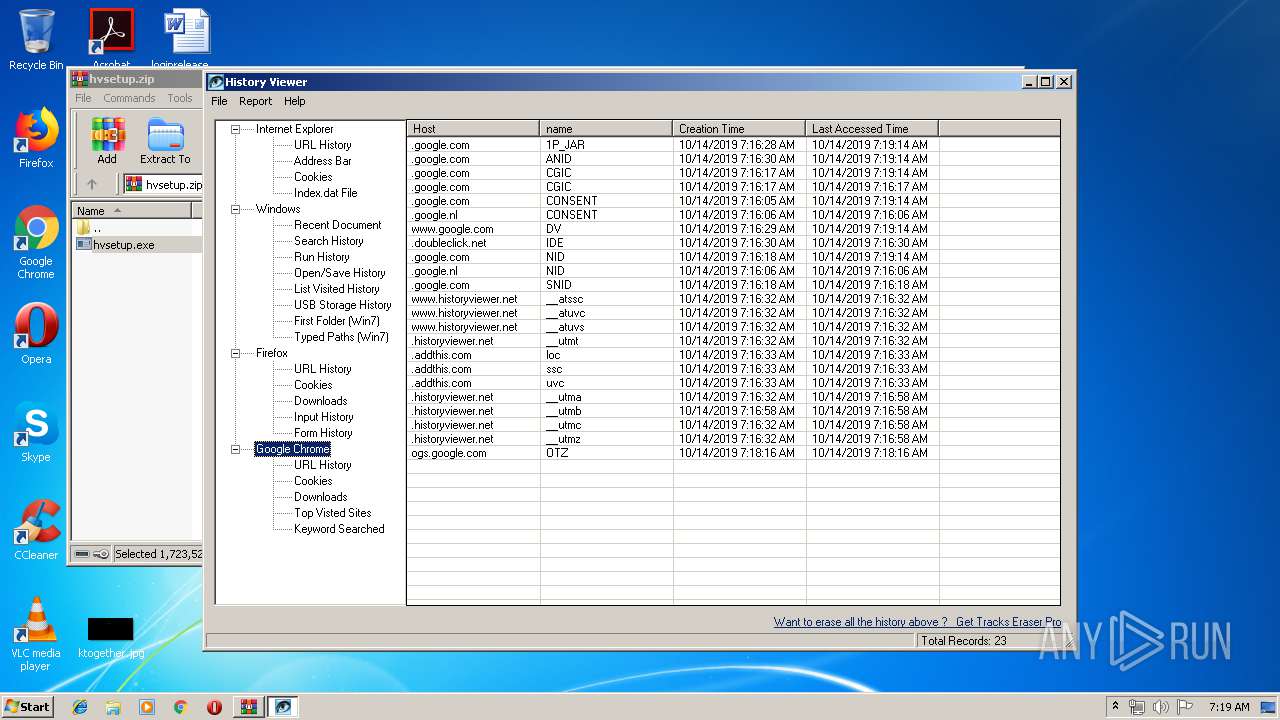
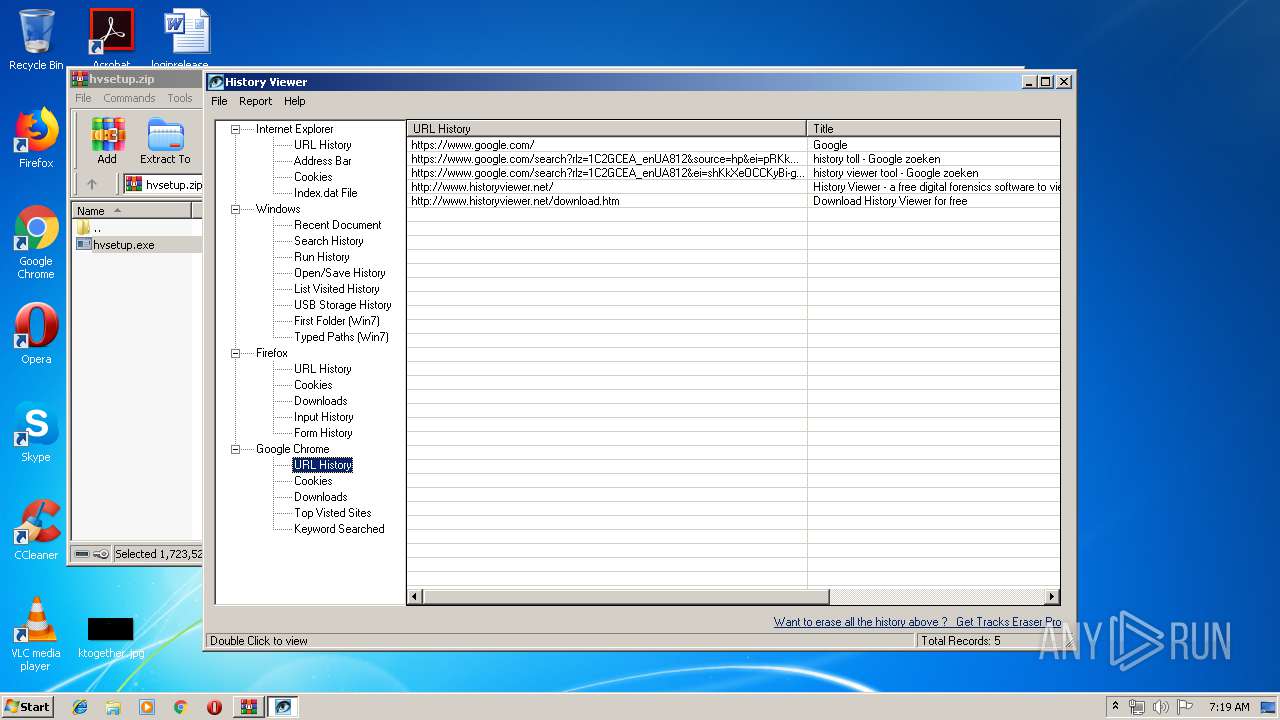
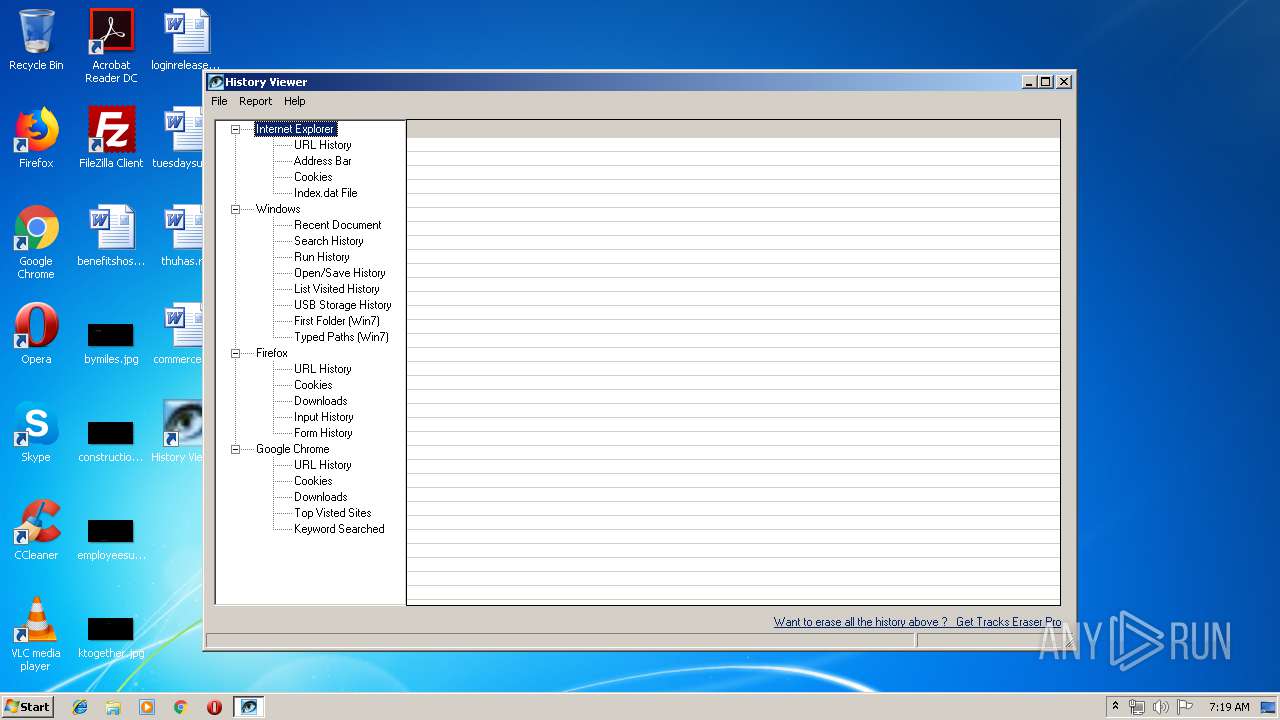
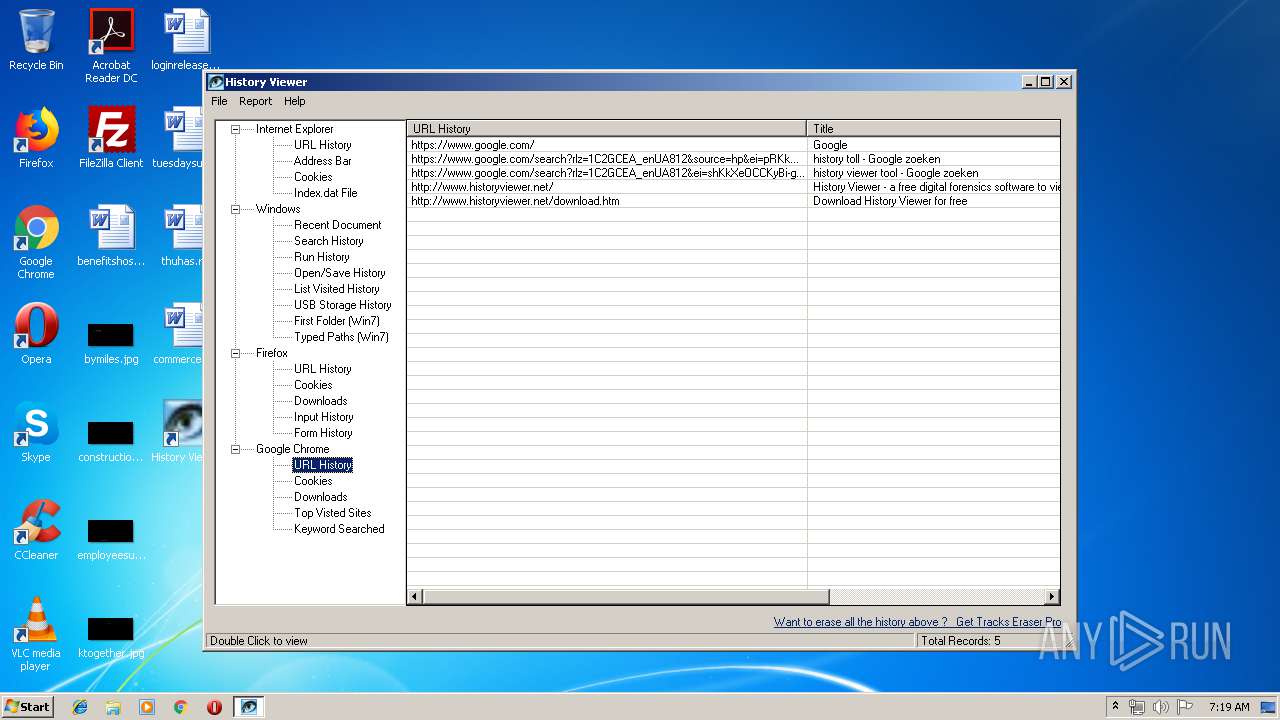
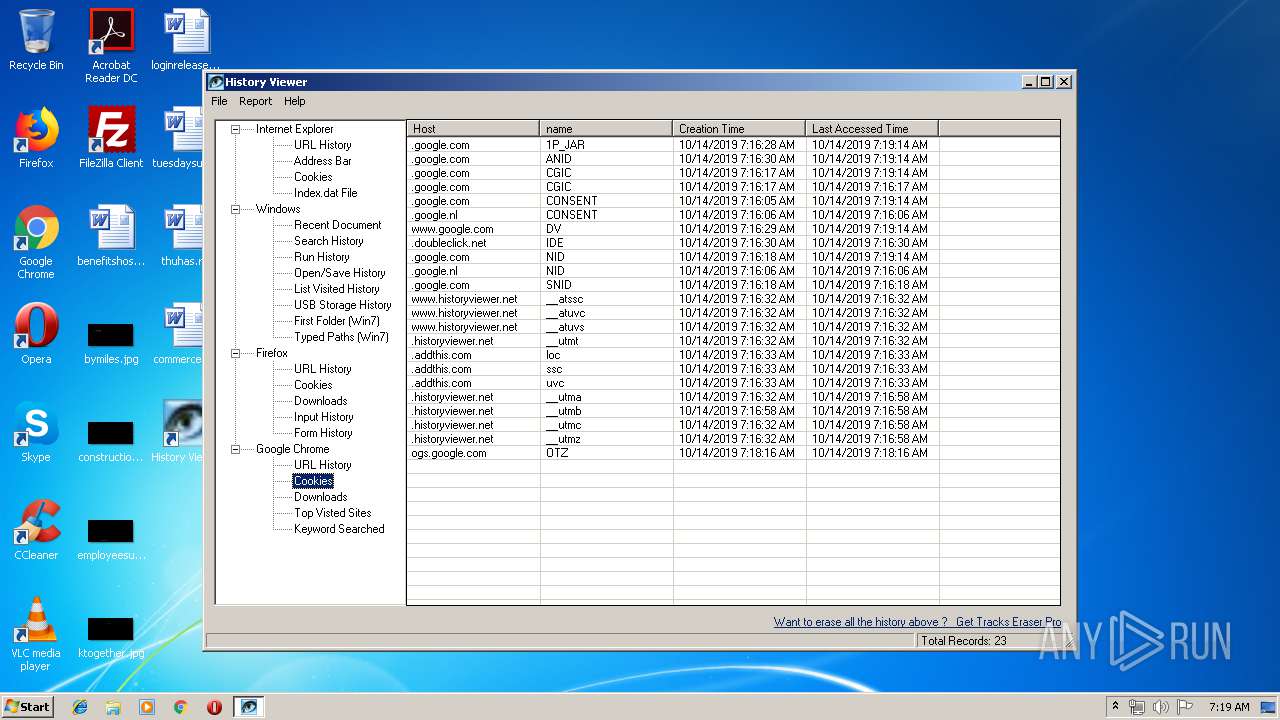
Reads the cookies of Google Chrome
- hviewer.exe (PID: 4016)
- hviewer.exe (PID: 2348)
INFO
Reads the hosts file
- chrome.exe (PID: 2088)
- chrome.exe (PID: 1880)
- chrome.exe (PID: 184)
- chrome.exe (PID: 3148)
Reads settings of System Certificates
- chrome.exe (PID: 1880)
- chrome.exe (PID: 3148)
Application launched itself
- chrome.exe (PID: 2088)
- chrome.exe (PID: 184)
Reads Internet Cache Settings
- chrome.exe (PID: 2088)
Application was dropped or rewritten from another process
- hvsetup.tmp (PID: 3816)
- hvsetup.tmp (PID: 3648)
Loads dropped or rewritten executable
- hvsetup.tmp (PID: 3816)
Creates files in the program directory
- hvsetup.tmp (PID: 3816)
Creates a software uninstall entry
- hvsetup.tmp (PID: 3816)
Manual execution by user
- chrome.exe (PID: 184)
- hviewer.exe (PID: 2348)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
103
Monitored processes
63
Malicious processes
6
Suspicious processes
2
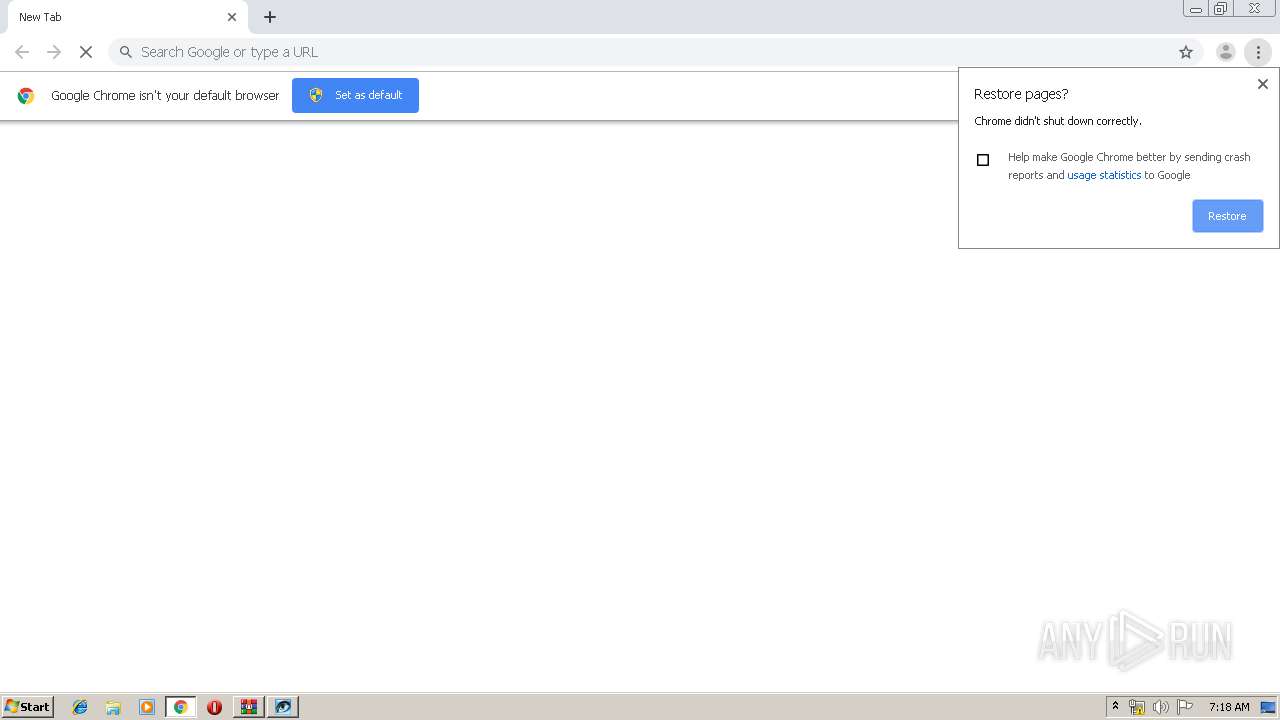
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,9044770843775295558,4135837686831159242,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4139315134929598141 --mojo-platform-channel-handle=3476 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,9044770843775295558,4135837686831159242,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10696669555338980010 --mojo-platform-channel-handle=3832 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 640 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1036,5320964399447521367,4965164294710510503,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=8318676427006255065 --mojo-platform-channel-handle=4040 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1036,5320964399447521367,4965164294710510503,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=17652703399258903148 --mojo-platform-channel-handle=1064 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,9044770843775295558,4135837686831159242,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11137165542094104753 --mojo-platform-channel-handle=2748 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1104 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,5320964399447521367,4965164294710510503,131072 --enable-features=PasswordImport --disable-databases --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7092883880173100030 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3716 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=980,9044770843775295558,4135837686831159242,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17340726217518977730 --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2828 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1412 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa1936.33498\hvsetup.exe" /SPAWNWND=$301B6 /NOTIFYWND=$40184 | C:\Users\admin\AppData\Local\Temp\Rar$EXa1936.33498\hvsetup.exe | hvsetup.tmp | ||||||||||||
User: admin Company: Digital Forensics Studio Integrity Level: HIGH Description: History Viewer Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 1504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,5320964399447521367,4965164294710510503,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14107435762386397755 --mojo-platform-channel-handle=3972 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
5 211
Read events
4 514
Write events
627
Delete events
70
Modification events
| (PID) Process: | (2088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2504) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2088-13215507362004875 |
Value: 259 | |||
| (PID) Process: | (2088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2088) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
11
Suspicious files
104
Text files
346
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\85b9877b-b05b-4de0-b322-58e5bf2c2236.tmp | — | |
MD5:— | SHA256:— | |||
| 2088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF39a708.TMP | text | |
MD5:— | SHA256:— | |||
| 2088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF39a7b4.TMP | text | |
MD5:— | SHA256:— | |||
| 2088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF39a708.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
68
TCP/UDP connections
97
DNS requests
43
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
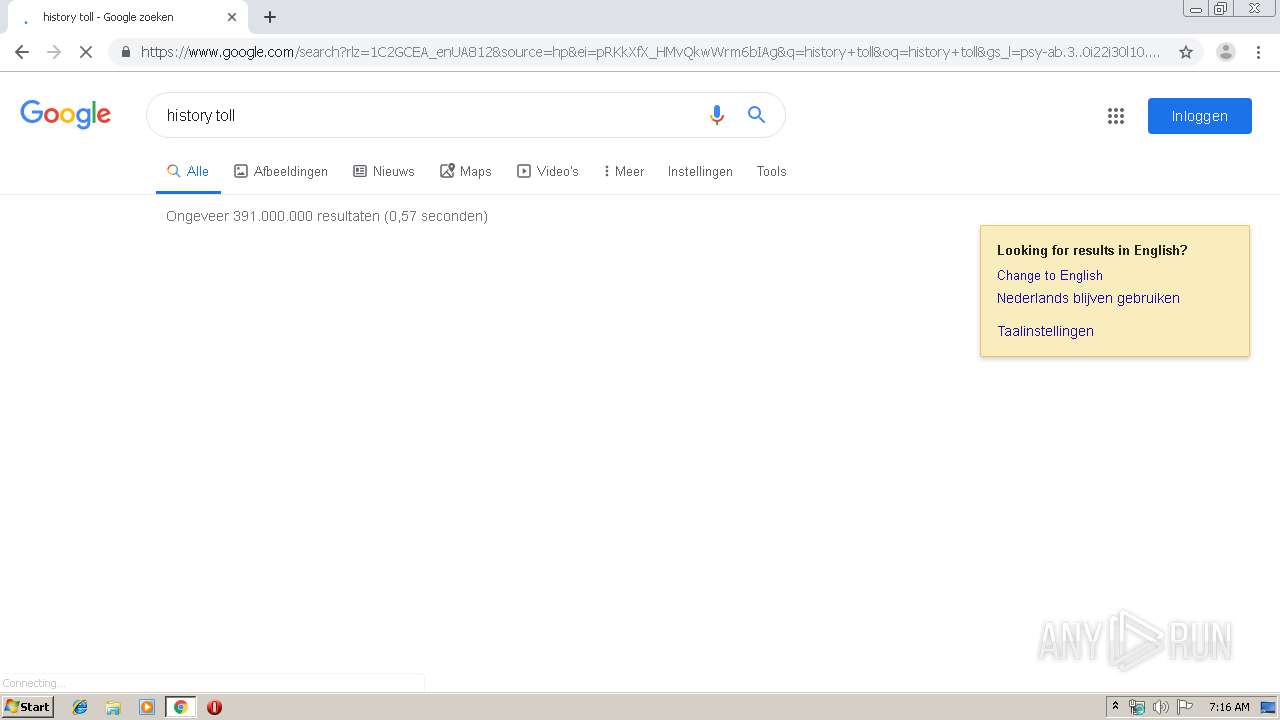
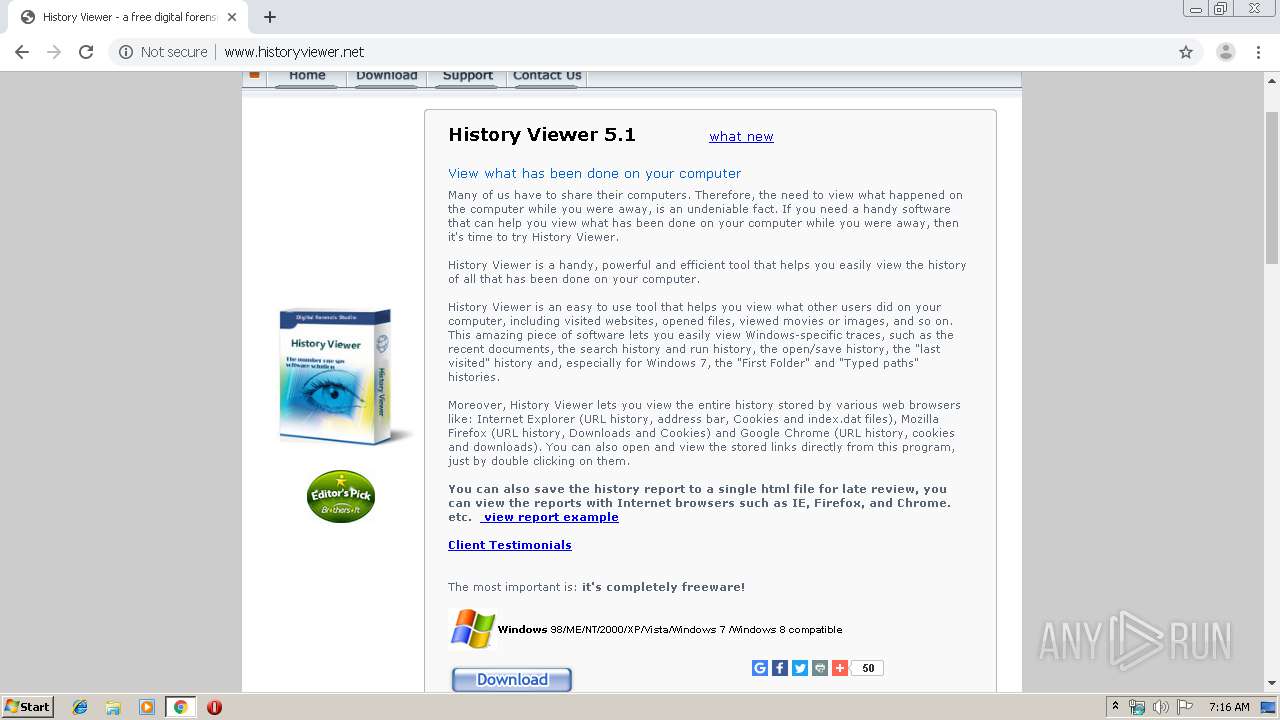
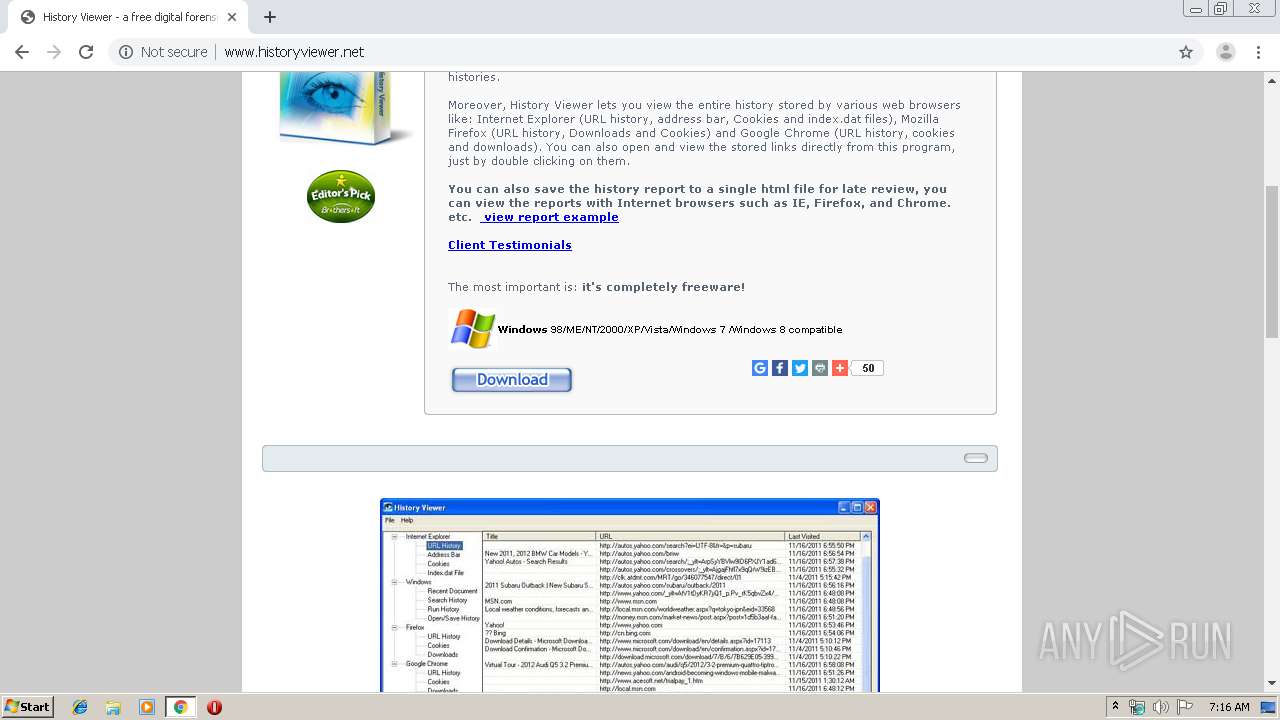
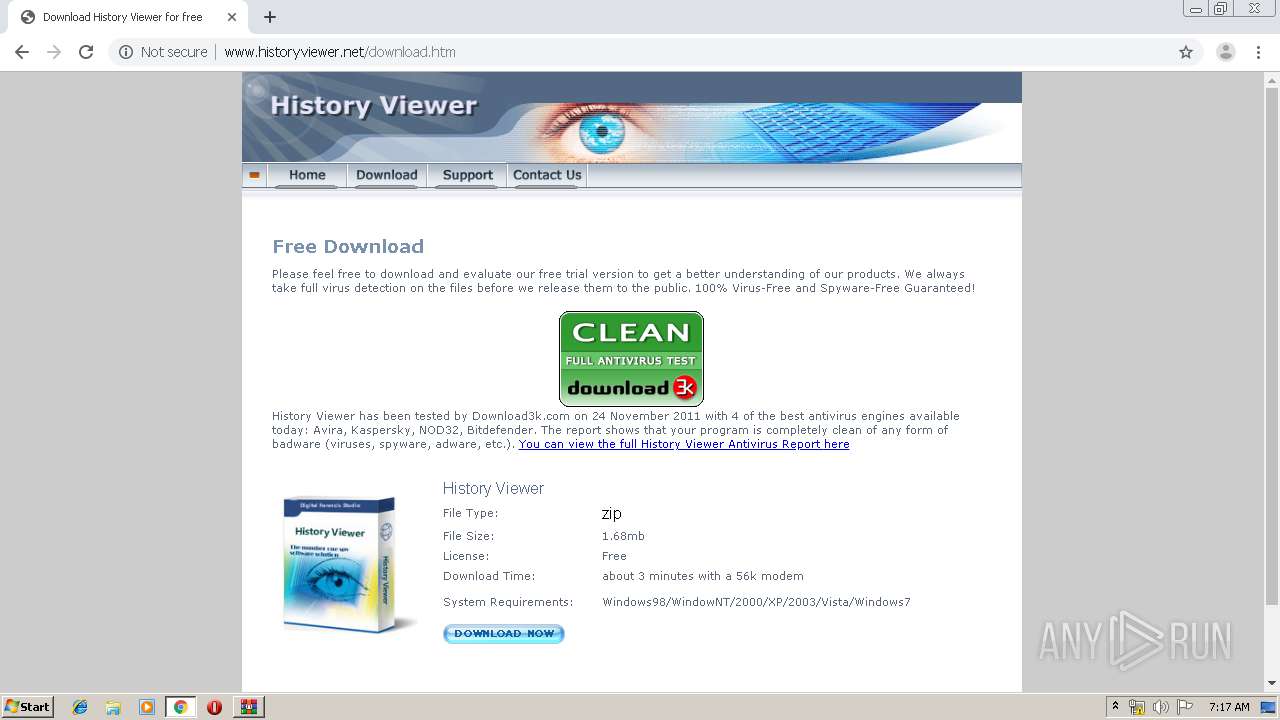
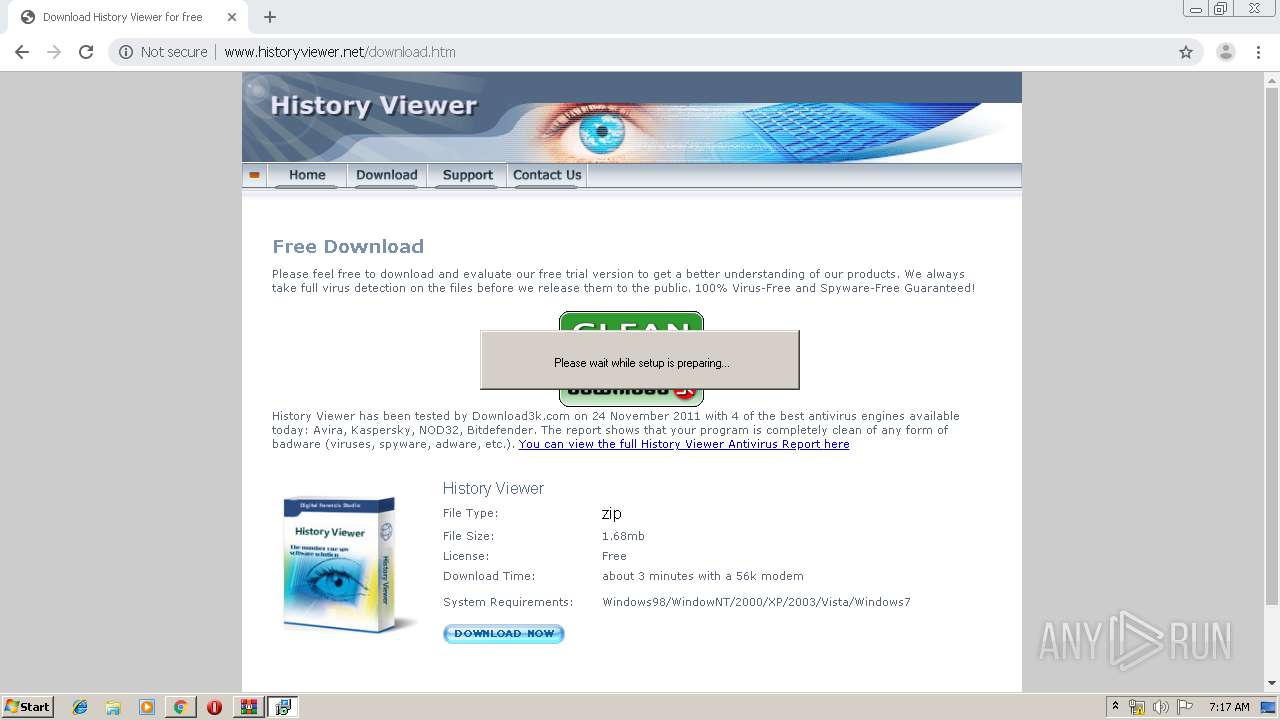
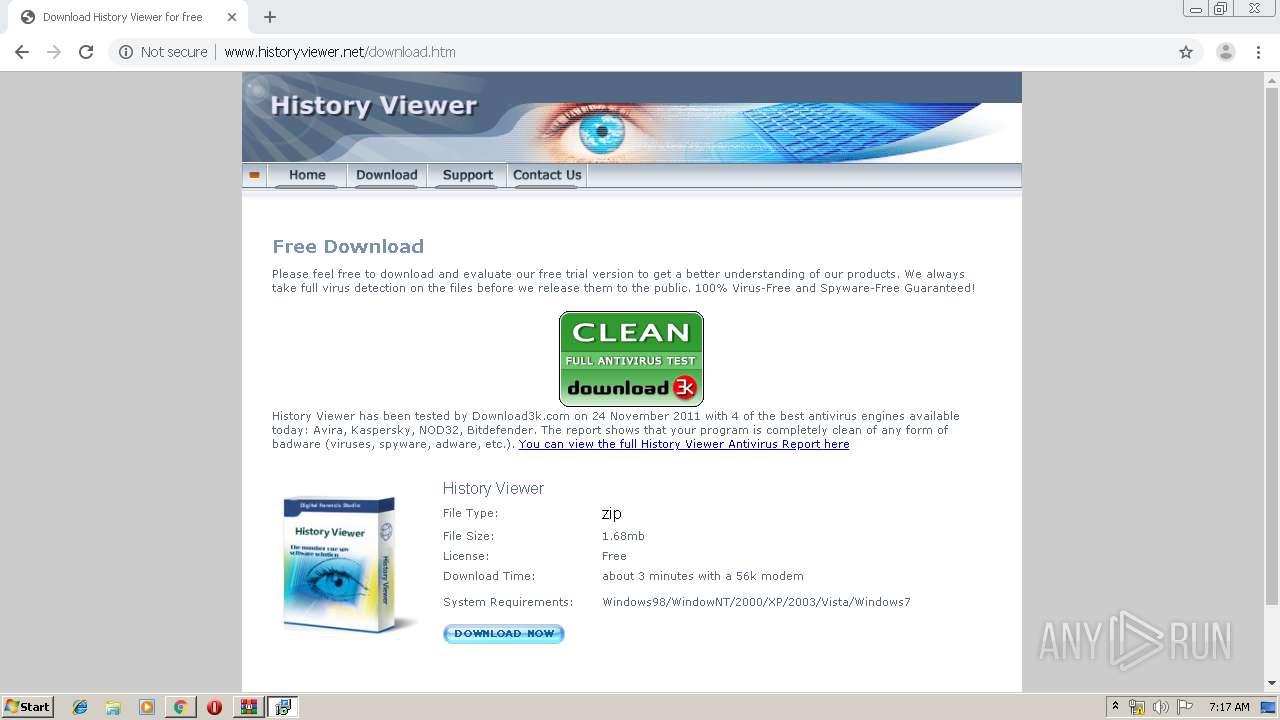
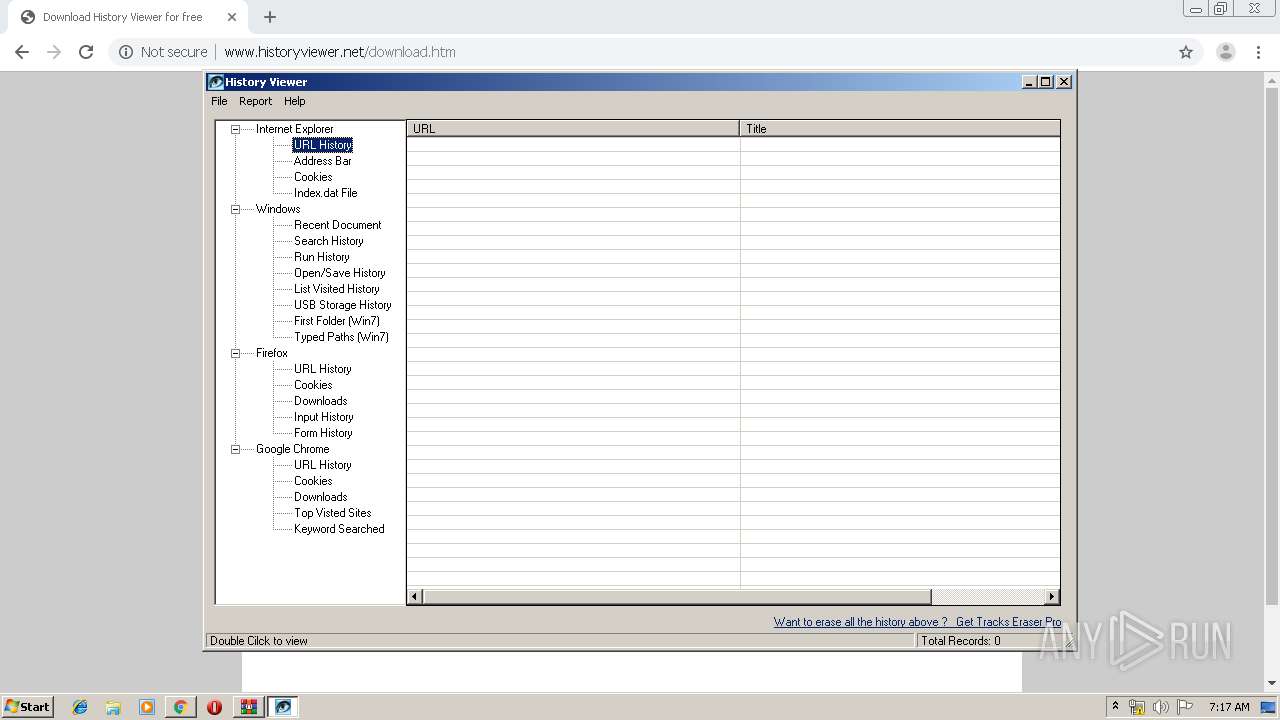
1880 | chrome.exe | GET | 200 | 198.199.93.38:80 | http://www.historyviewer.net/images/download.gif | US | image | 1.91 Kb | unknown |
1880 | chrome.exe | GET | 200 | 198.199.93.38:80 | http://www.historyviewer.net/ | US | html | 18.7 Kb | unknown |
1880 | chrome.exe | GET | 200 | 198.199.93.38:80 | http://www.historyviewer.net/css/txt.css | US | text | 1.26 Kb | unknown |
1880 | chrome.exe | GET | 200 | 198.199.93.38:80 | http://www.historyviewer.net/images/home.gif | US | image | 1.65 Kb | unknown |
1880 | chrome.exe | GET | 200 | 198.199.93.38:80 | http://www.historyviewer.net/images/index/di.gif | US | image | 351 b | unknown |
1880 | chrome.exe | GET | 200 | 198.199.93.38:80 | http://www.historyviewer.net/images/contact.gif | US | image | 1.98 Kb | unknown |
1880 | chrome.exe | GET | 200 | 198.199.93.38:80 | http://www.historyviewer.net/images/support.gif | US | image | 1.83 Kb | unknown |
1880 | chrome.exe | GET | 302 | 216.58.208.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 513 b | whitelisted |
1880 | chrome.exe | GET | 200 | 198.199.93.38:80 | http://www.historyviewer.net/images/index/kuang03.gif | US | image | 180 b | unknown |
1880 | chrome.exe | GET | 302 | 216.58.208.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 508 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1880 | chrome.exe | 172.217.16.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1880 | chrome.exe | 216.58.205.228:443 | www.google.com | Google Inc. | US | whitelisted |
1880 | chrome.exe | 172.217.23.99:443 | www.google.nl | Google Inc. | US | whitelisted |
1880 | chrome.exe | 172.217.16.206:443 | clients1.google.com | Google Inc. | US | whitelisted |
1880 | chrome.exe | 172.217.22.14:443 | apis.google.com | Google Inc. | US | whitelisted |
1880 | chrome.exe | 216.58.206.2:443 | adservice.google.com | Google Inc. | US | whitelisted |
1880 | chrome.exe | 216.58.208.46:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
1880 | chrome.exe | 74.125.8.185:80 | r3---sn-5hne6nlr.gvt1.com | Google Inc. | US | whitelisted |
1880 | chrome.exe | 172.217.18.1:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
1880 | chrome.exe | 198.199.93.38:80 | www.historyviewer.net | Digital Ocean, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.google.com |
| malicious |
accounts.google.com |
| shared |
consent.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
www.google.nl |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3816 | hvsetup.tmp | A Network Trojan was detected | MALWARE [PTsecurity] Win32/DownWare.L Check-in |
3816 | hvsetup.tmp | A Network Trojan was detected | MALWARE [PTsecurity] Win32/DownWare.L Check-in |
3816 | hvsetup.tmp | A Network Trojan was detected | MALWARE [PTsecurity] Carbanak VBS/GGLDR Checkin |
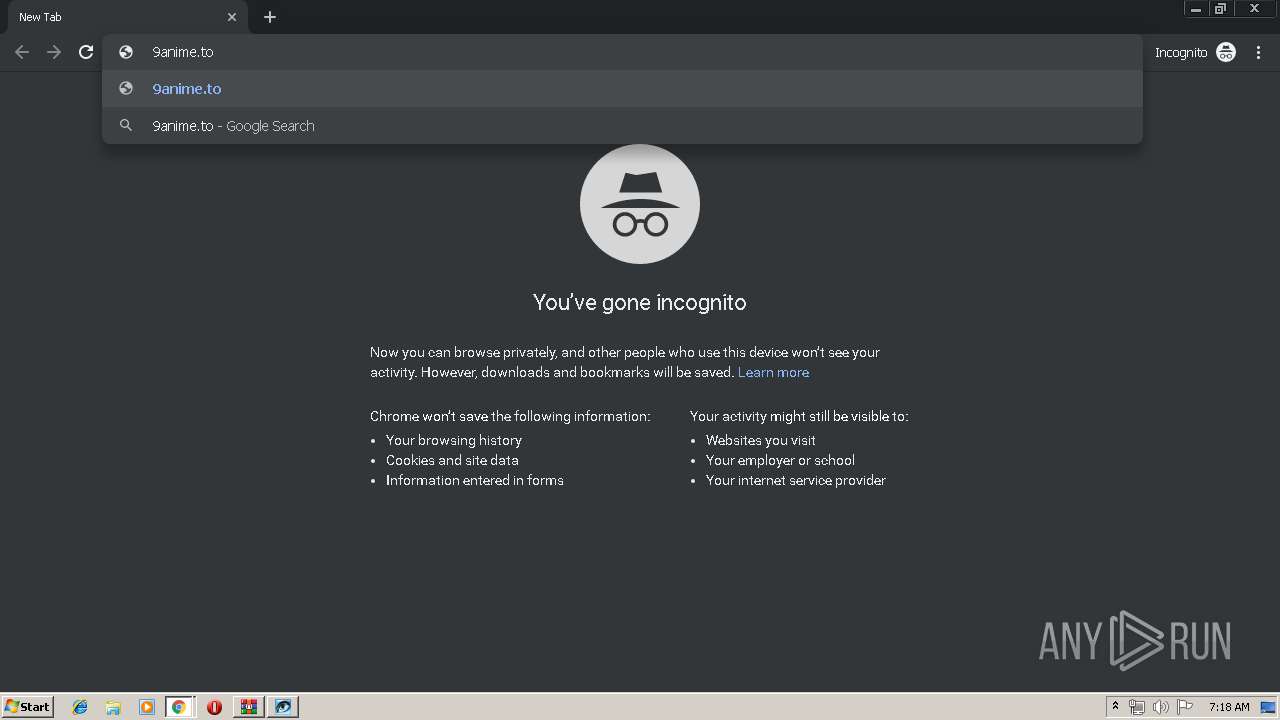
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .to TLD |
1 ETPRO signatures available at the full report