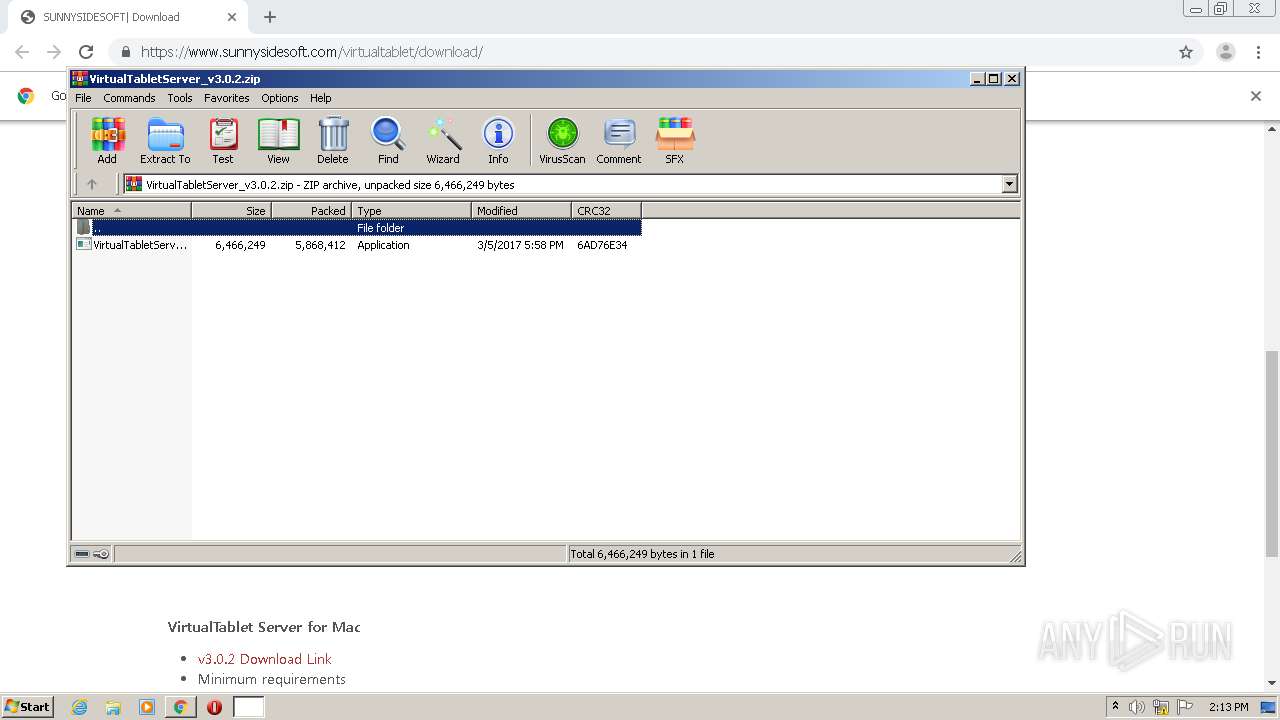
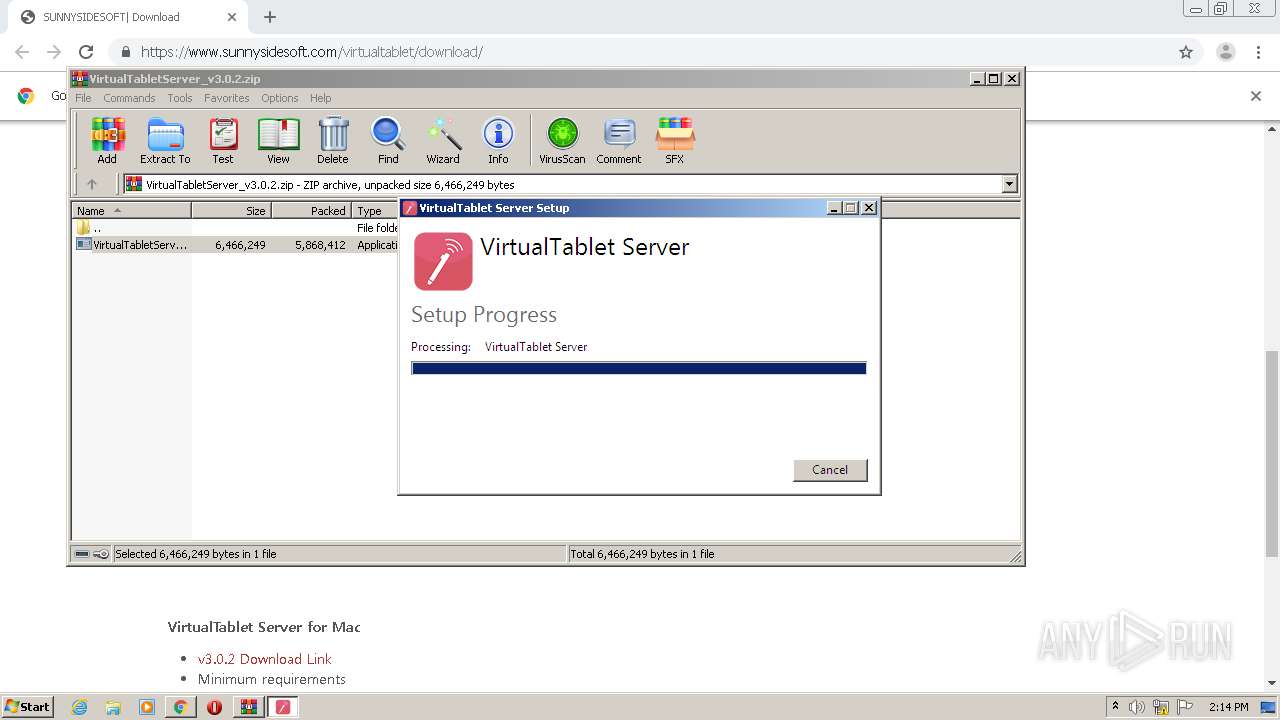
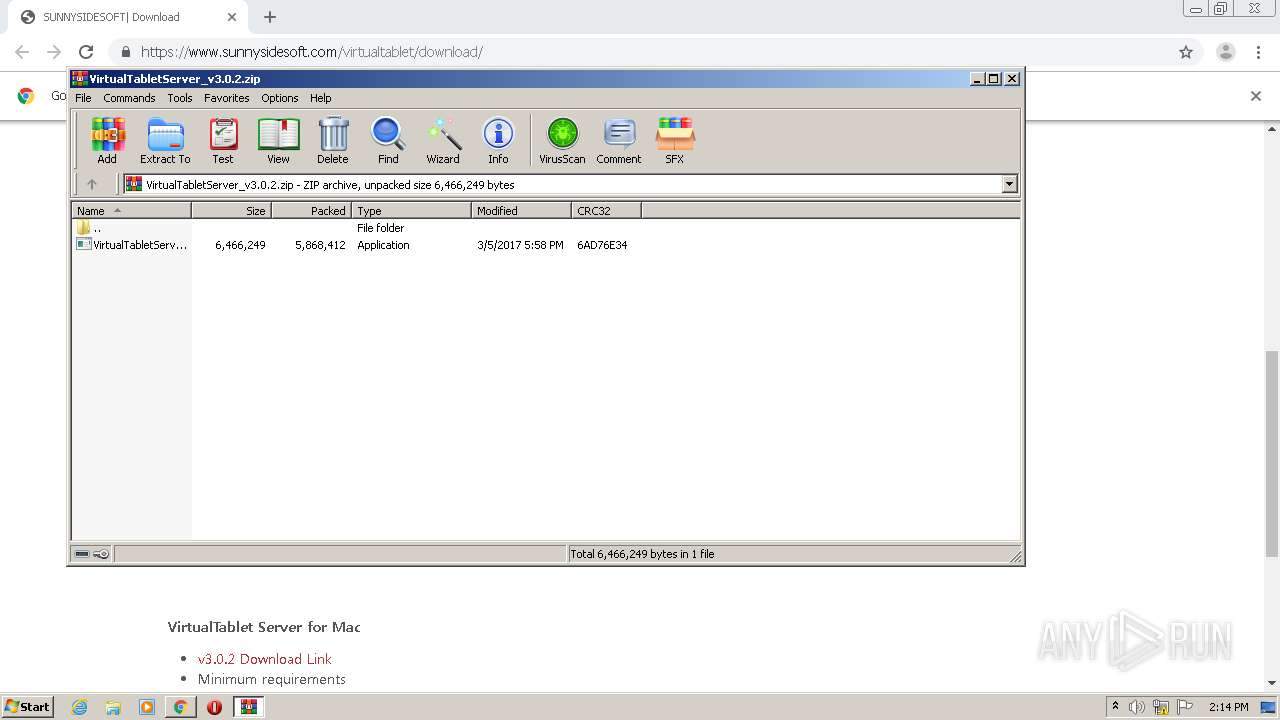
| URL: | https://www.sunnysidesoft.com/virtualtablet/download/ |
| Full analysis: | https://app.any.run/tasks/ef678745-7968-4bfb-9304-66ebbd5710d3 |
| Verdict: | Malicious activity |
| Analysis date: | January 15, 2021, 14:12:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 08208A8F0F09F8526CBE6156F79950B4 |
| SHA1: | 342E089A98FF723272863598BF4C6C08E1507FF8 |
| SHA256: | AC5F59500DBFE3CCB51F9299FCB291B588F227E235E8C75519EAF5794459D60F |
| SSDEEP: | 3:N8DSLvcYDRtoGz8Ln:2OLTDRtoG4L |
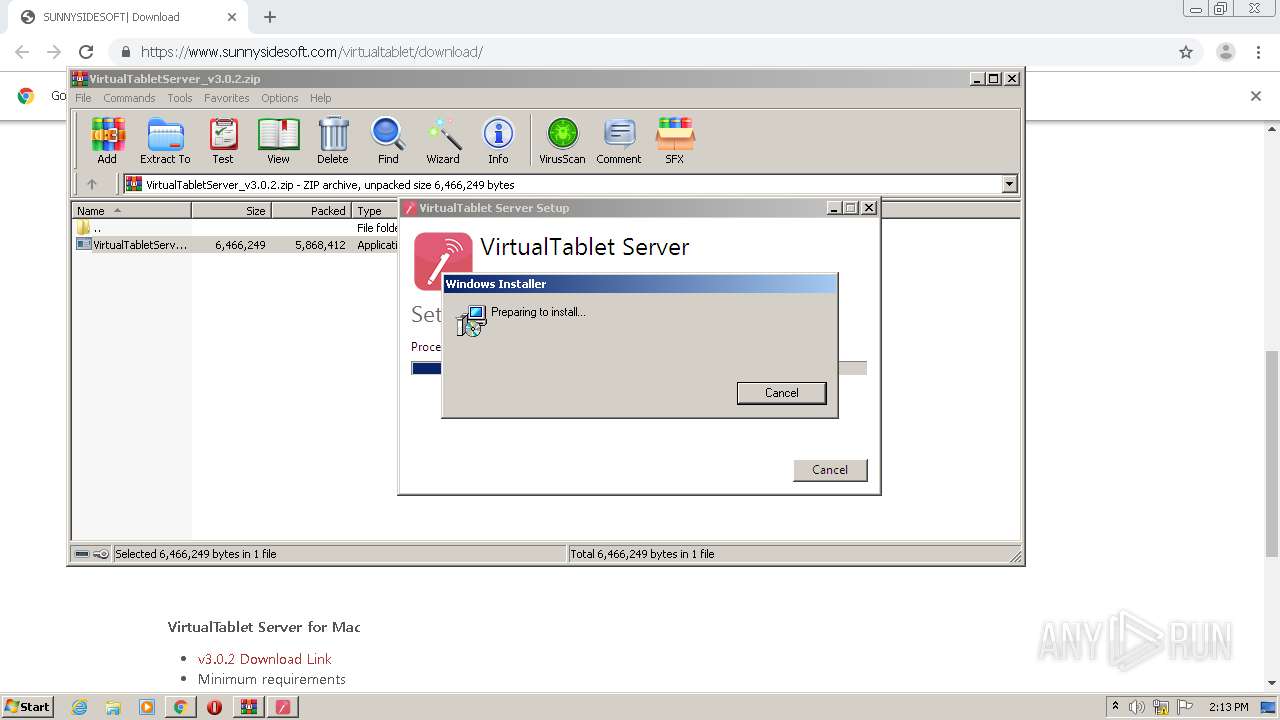
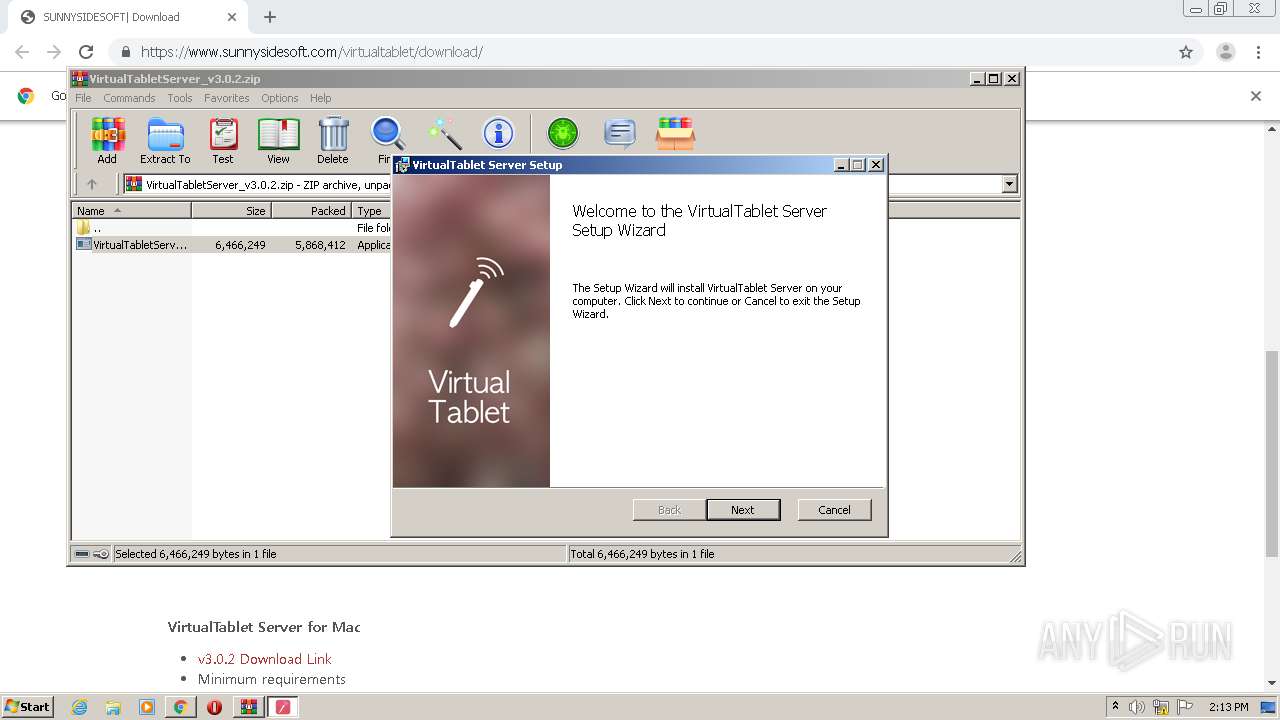
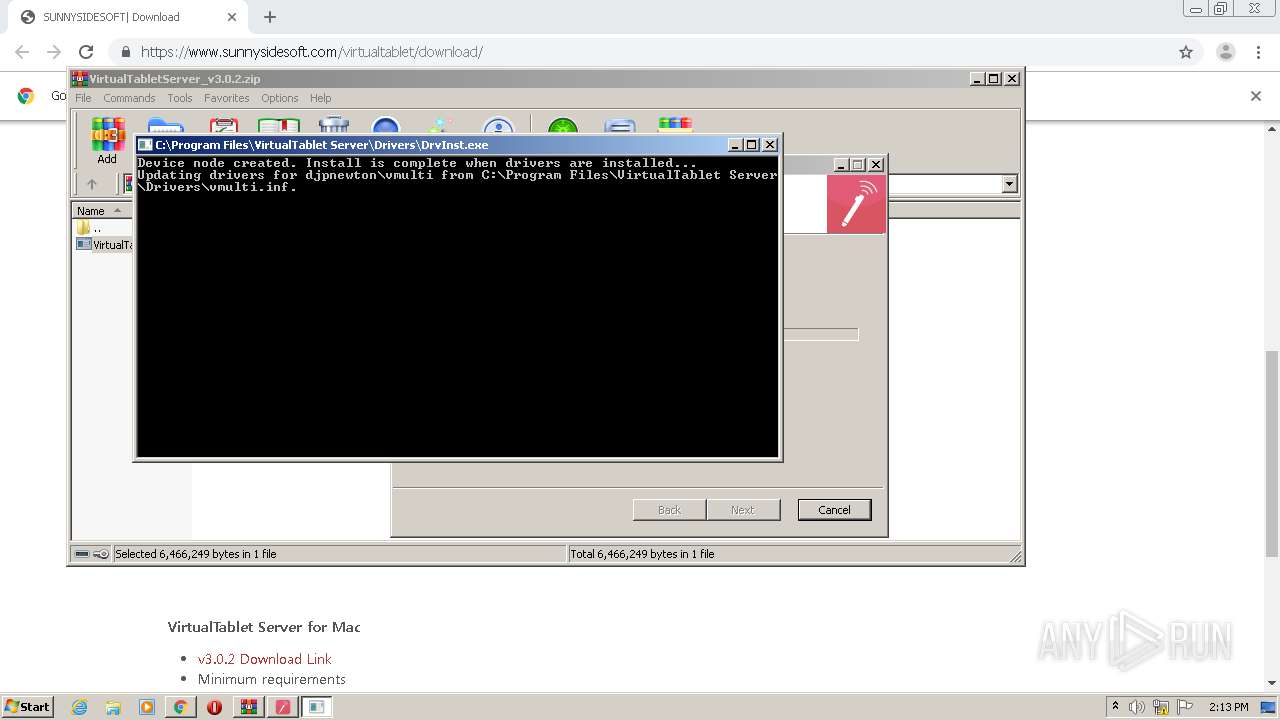
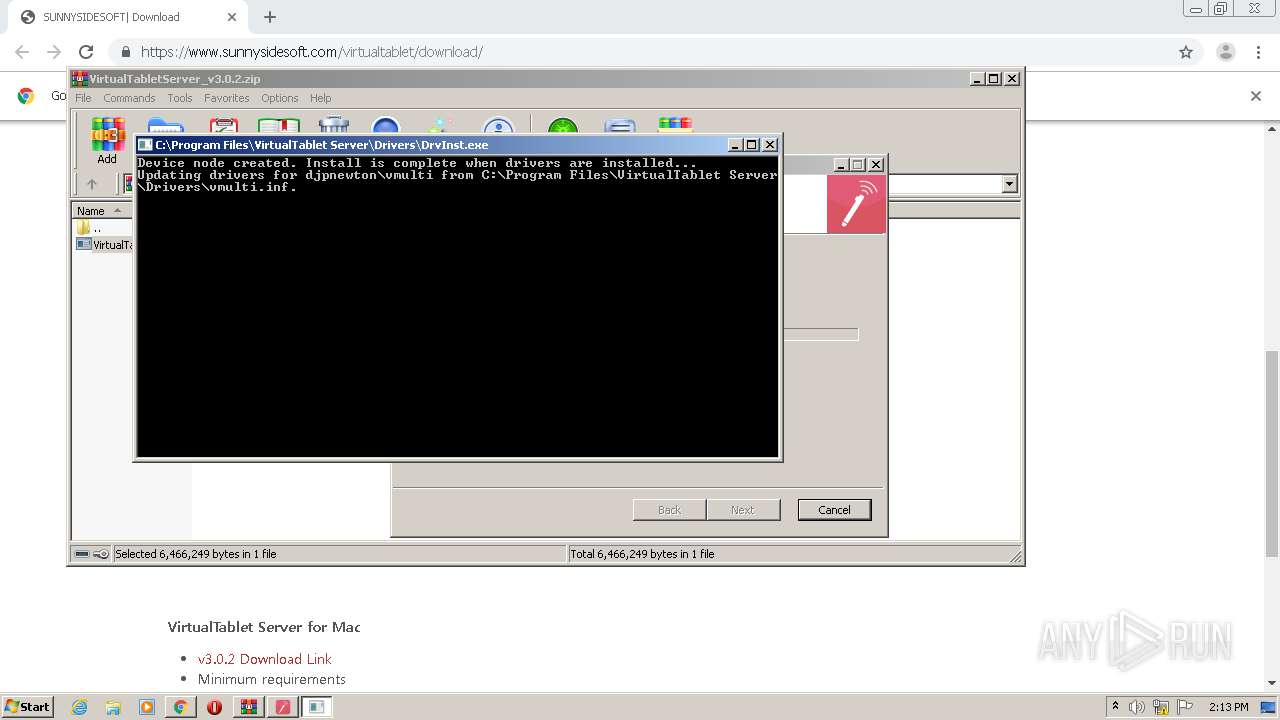
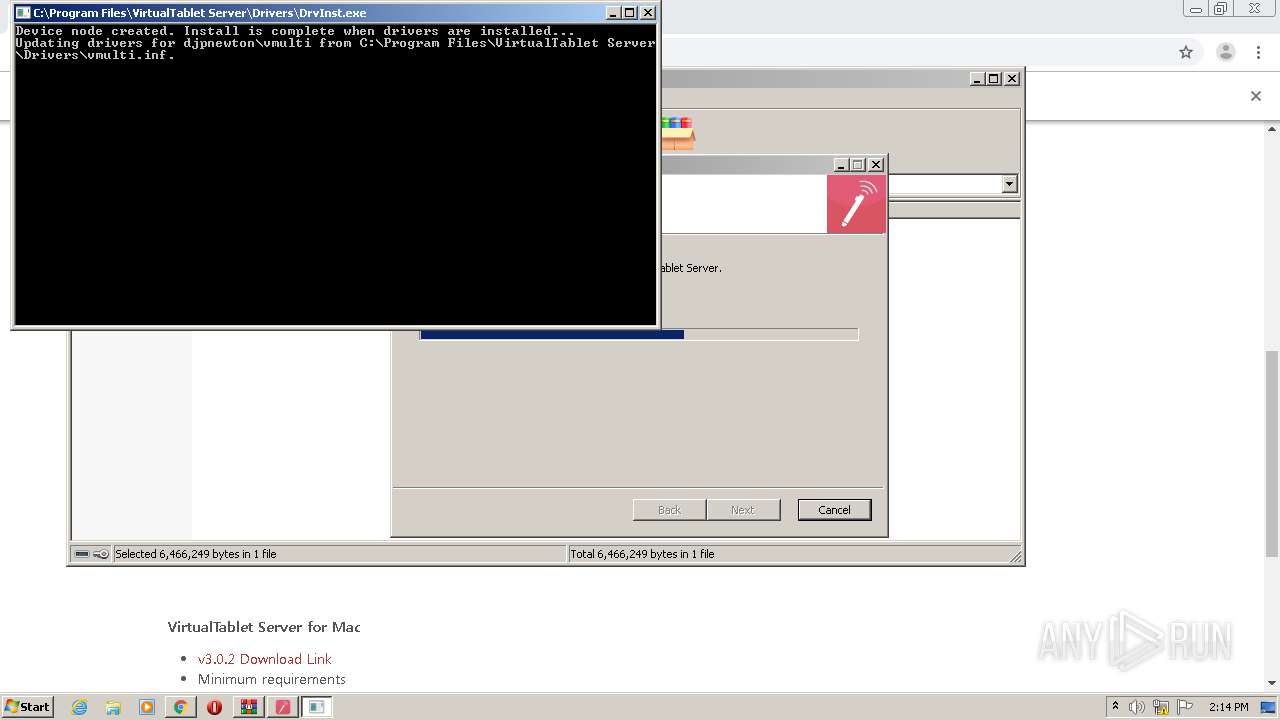
MALICIOUS
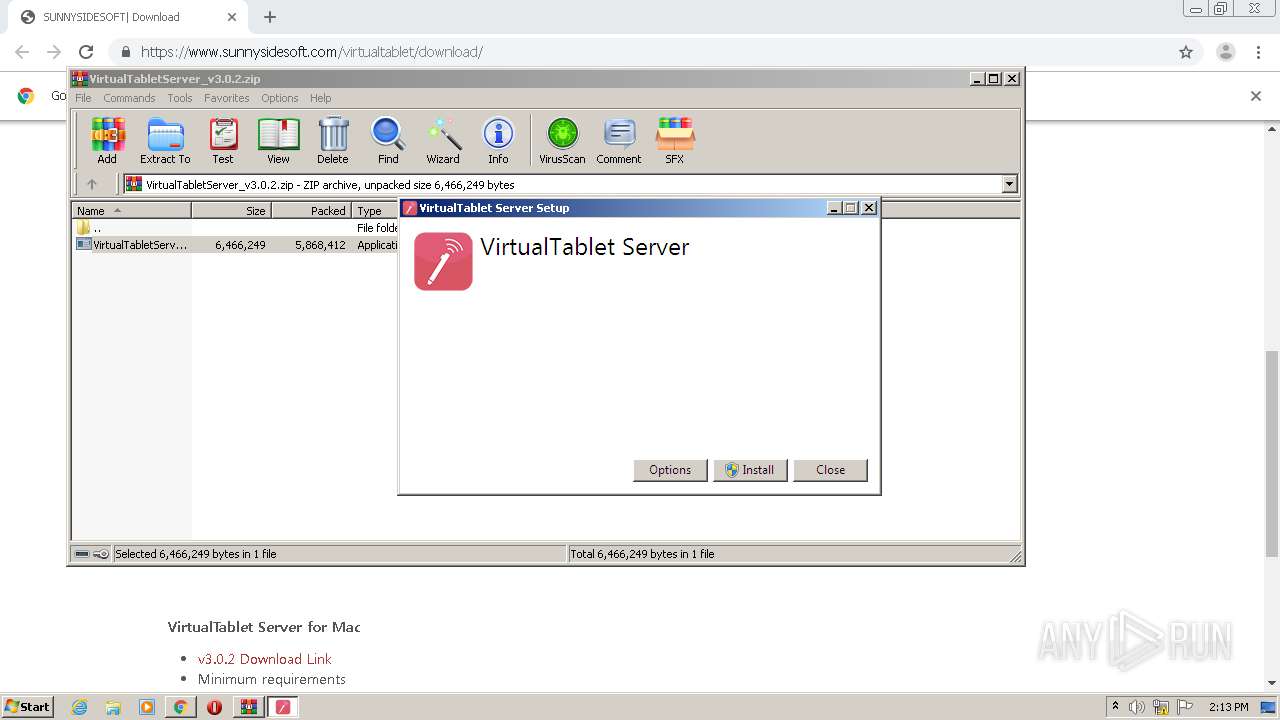
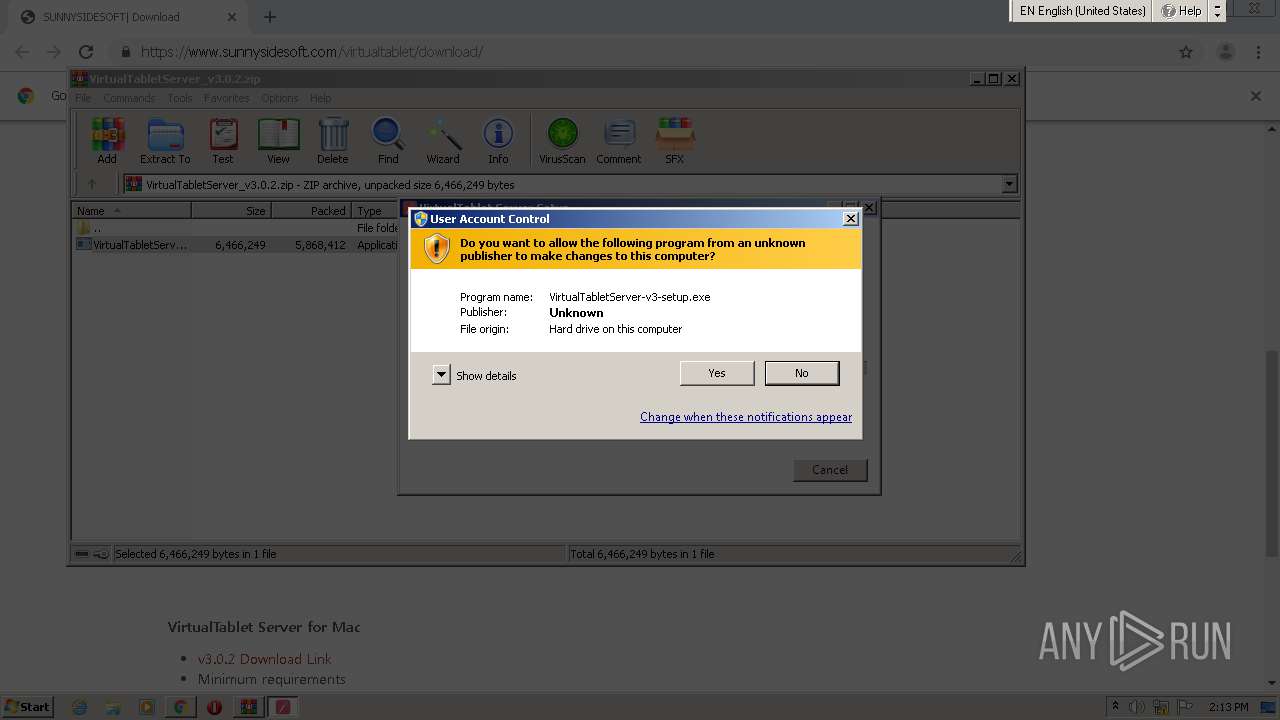
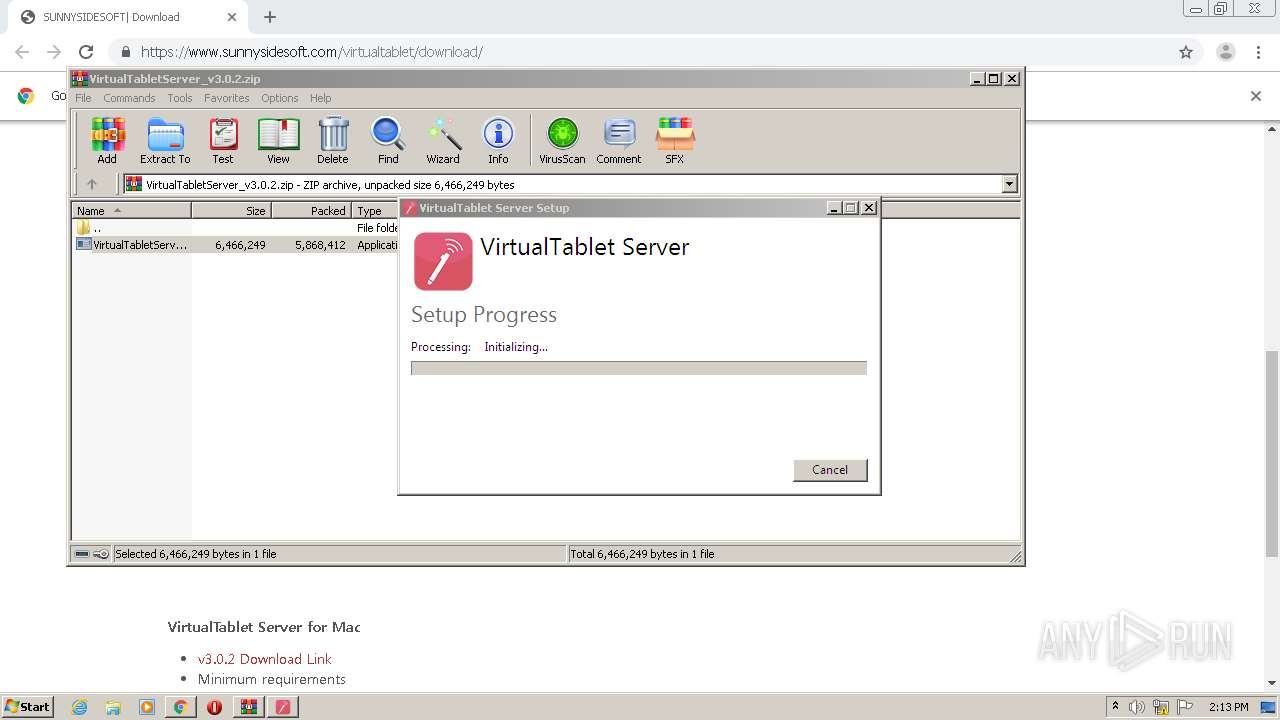
Drops executable file immediately after starts
- VirtualTabletServer-v3-setup.exe (PID: 2728)
- VirtualTabletServer-v3-setup.exe (PID: 1936)
- DrvInst.exe (PID: 2900)
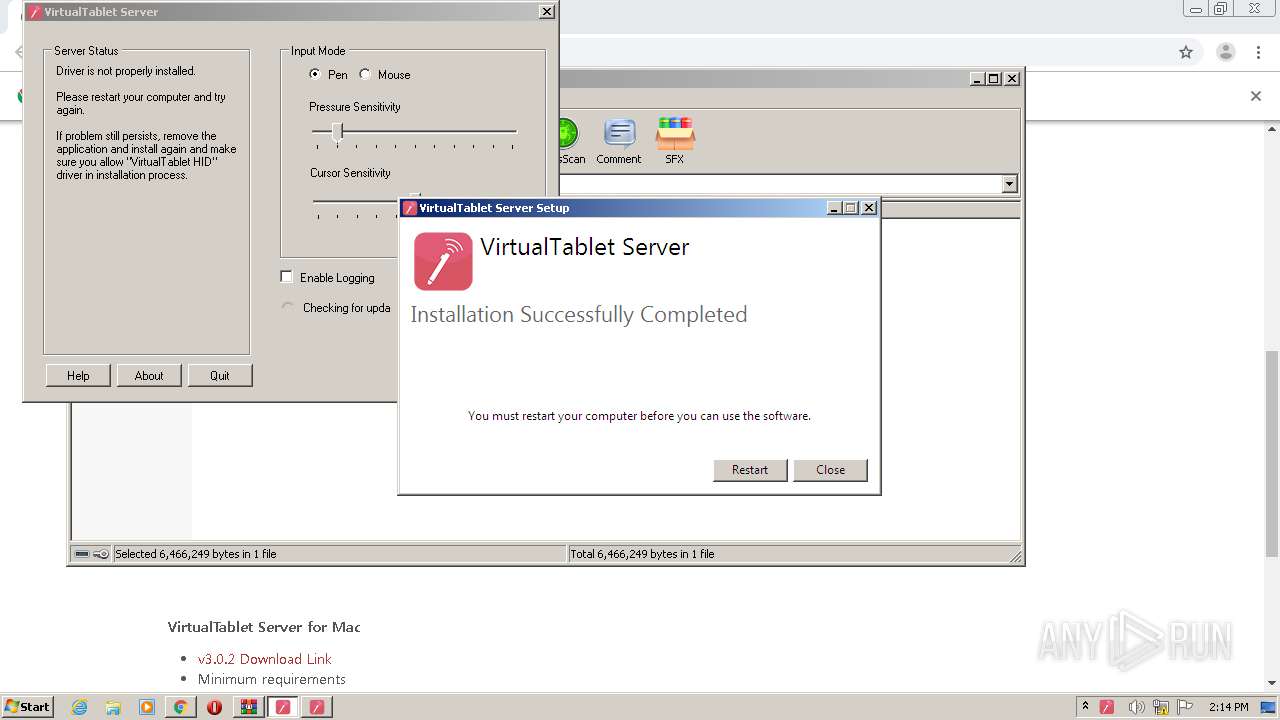
Loads dropped or rewritten executable
- VirtualTabletServer-v3-setup.exe (PID: 2728)
- DrvInst.exe (PID: 3792)
- adb.exe (PID: 760)
- VirtualTabletServer.exe (PID: 4000)
Application was dropped or rewritten from another process
- VirtualTabletServer-v3-setup.exe (PID: 2588)
- VirtualTabletServer-v3-setup.exe (PID: 1936)
- VirtualTabletServer-v3-setup.exe (PID: 2728)
- DrvInst.exe (PID: 1028)
- VirtualTabletServer.exe (PID: 4000)
- adb.exe (PID: 760)
- wyUpdate.exe (PID: 4004)
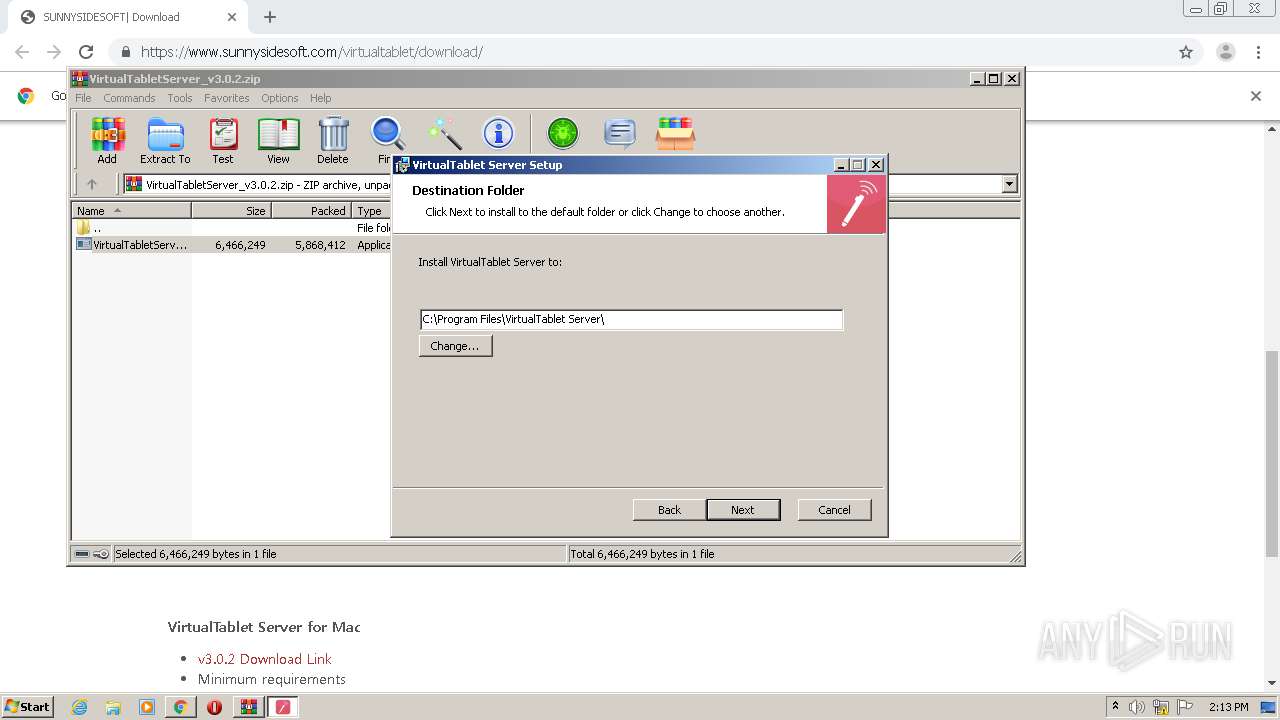
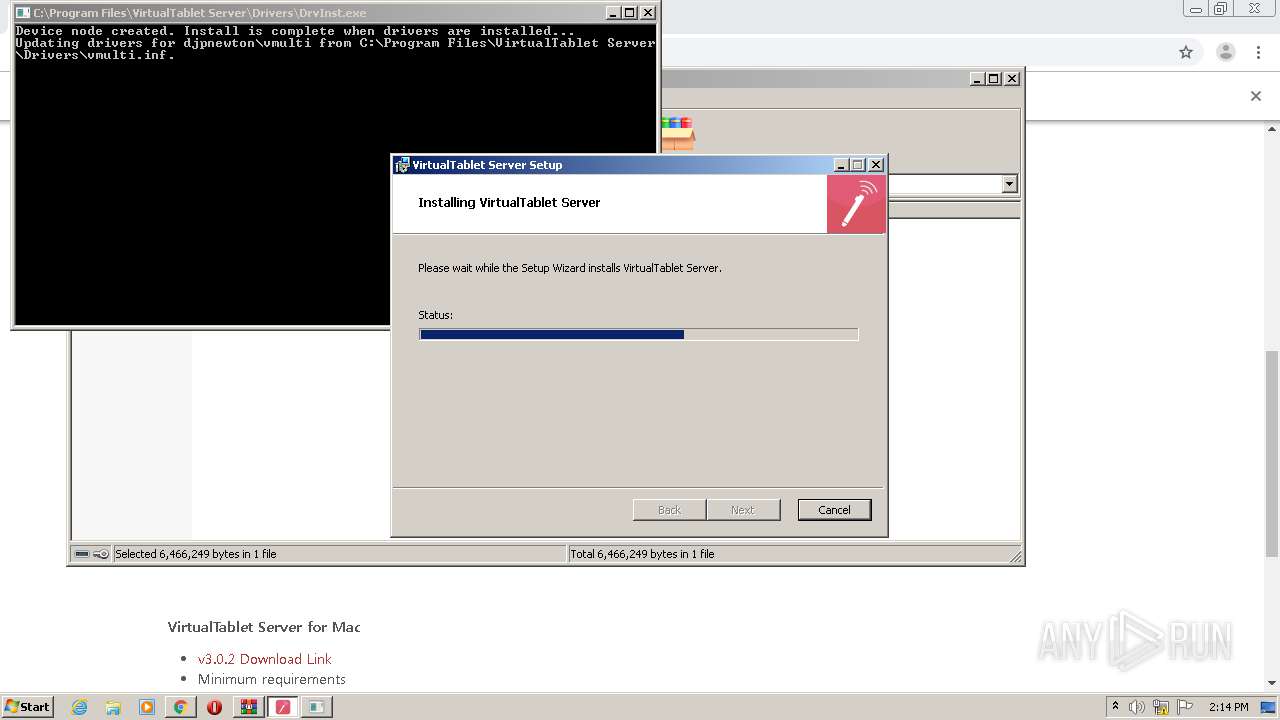
Changes the autorun value in the registry
- VirtualTabletServer-v3-setup.exe (PID: 2588)
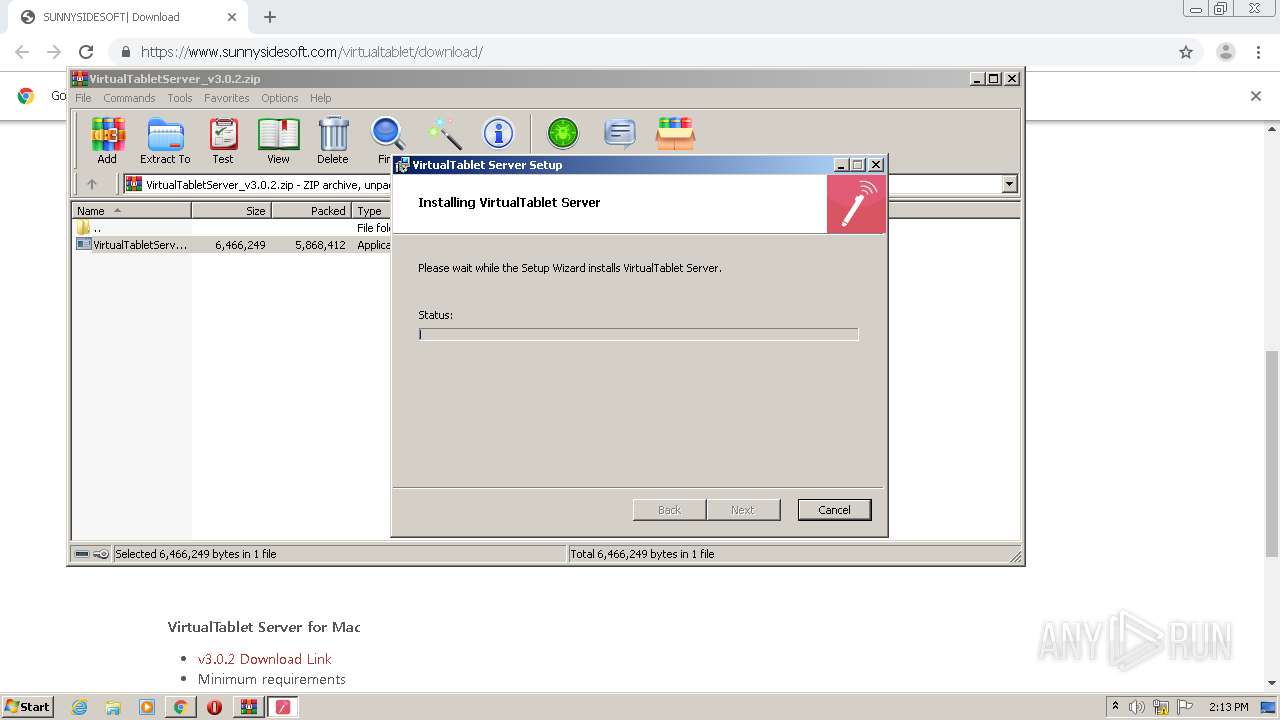
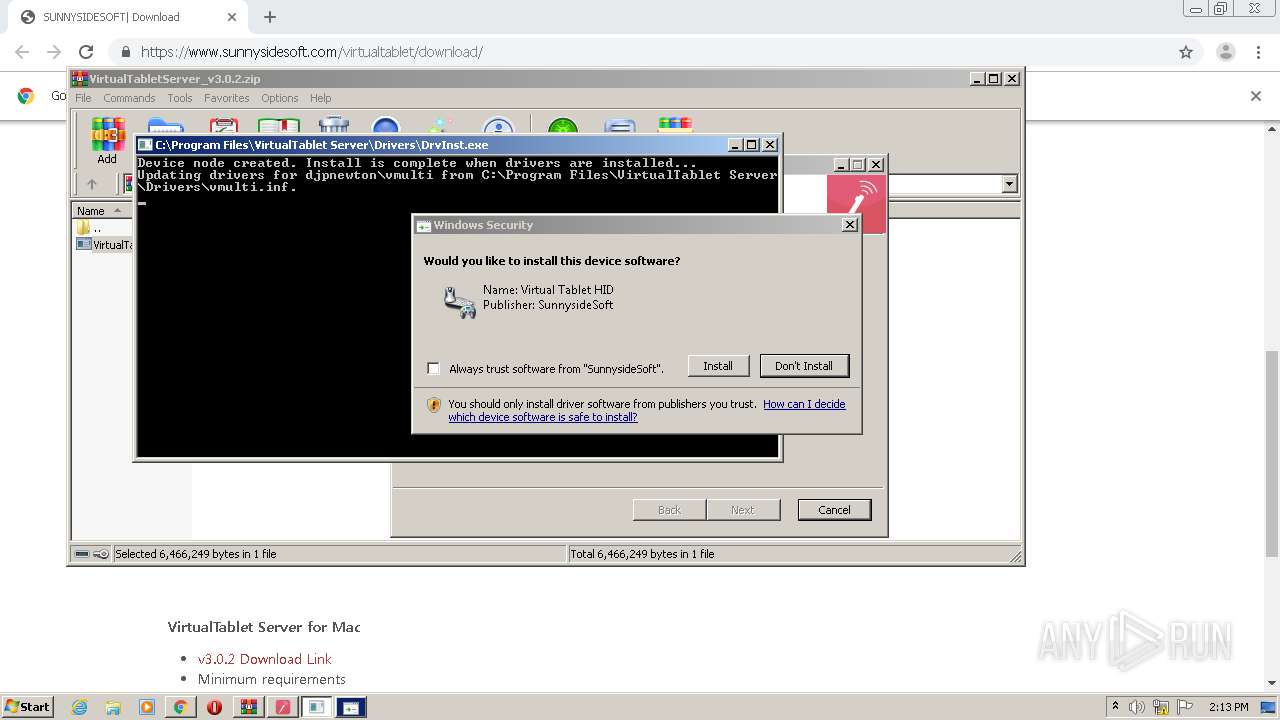
Changes settings of System certificates
- DrvInst.exe (PID: 1028)
- wyUpdate.exe (PID: 4004)
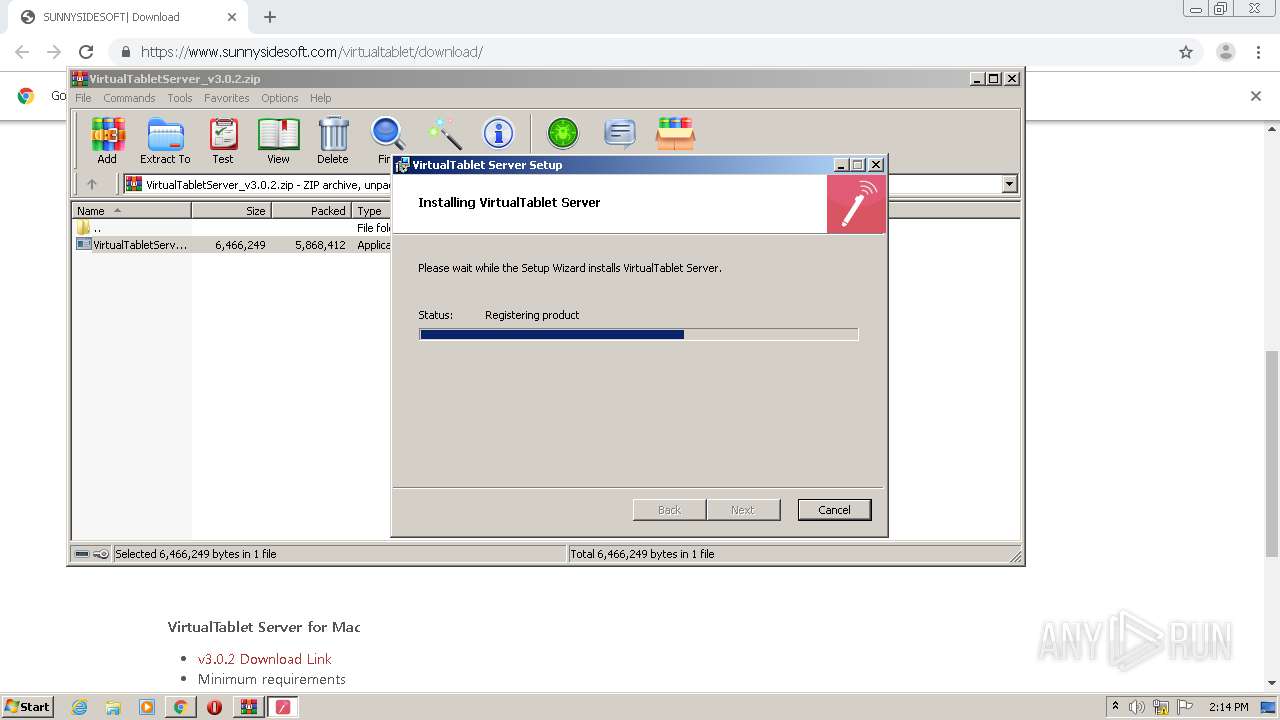
SUSPICIOUS
Executable content was dropped or overwritten
- VirtualTabletServer-v3-setup.exe (PID: 1936)
- WinRAR.exe (PID: 2504)
- VirtualTabletServer-v3-setup.exe (PID: 2728)
- VirtualTabletServer-v3-setup.exe (PID: 2588)
- DrvInst.exe (PID: 1028)
- DrvInst.exe (PID: 2900)
- msiexec.exe (PID: 3108)
- DrvInst.exe (PID: 3792)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 2504)
- VirtualTabletServer-v3-setup.exe (PID: 2588)
- VirtualTabletServer-v3-setup.exe (PID: 1936)
- VirtualTabletServer-v3-setup.exe (PID: 2728)
- DrvInst.exe (PID: 1028)
- DrvInst.exe (PID: 2900)
- msiexec.exe (PID: 3108)
- DrvInst.exe (PID: 3792)
Starts itself from another location
- VirtualTabletServer-v3-setup.exe (PID: 2728)
- VirtualTabletServer-v3-setup.exe (PID: 1936)
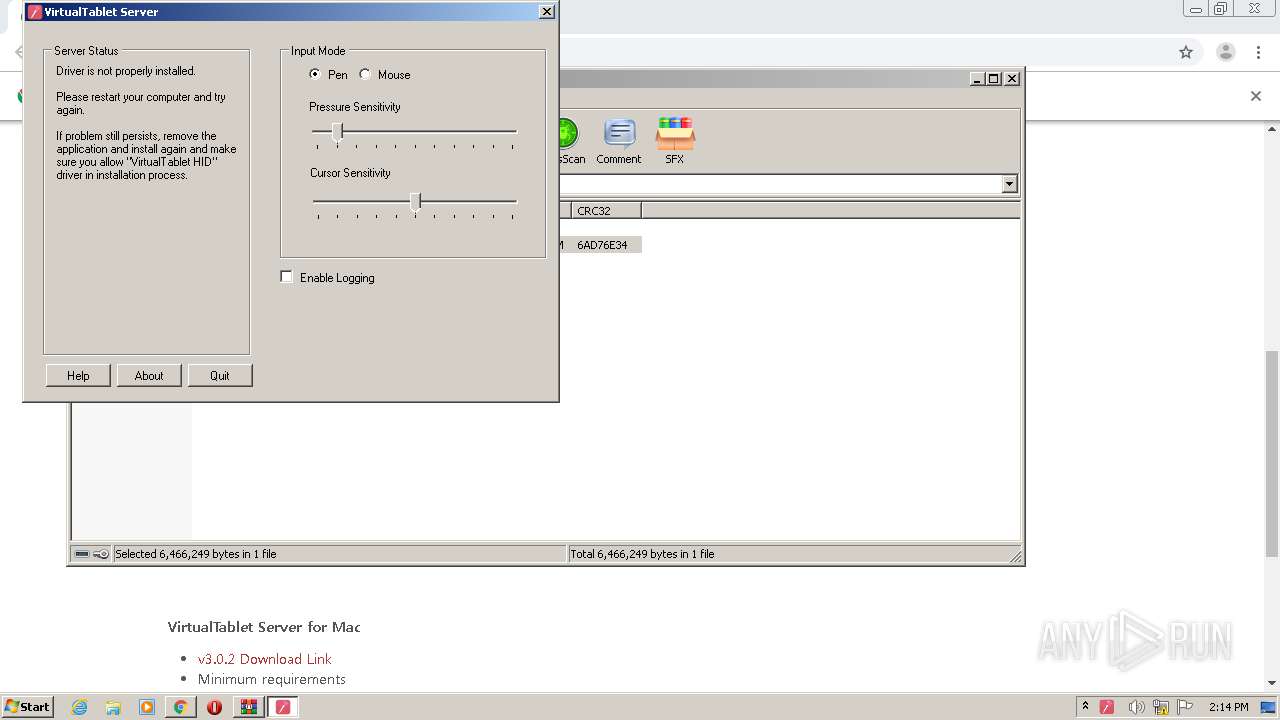
Searches for installed software
- VirtualTabletServer-v3-setup.exe (PID: 2588)
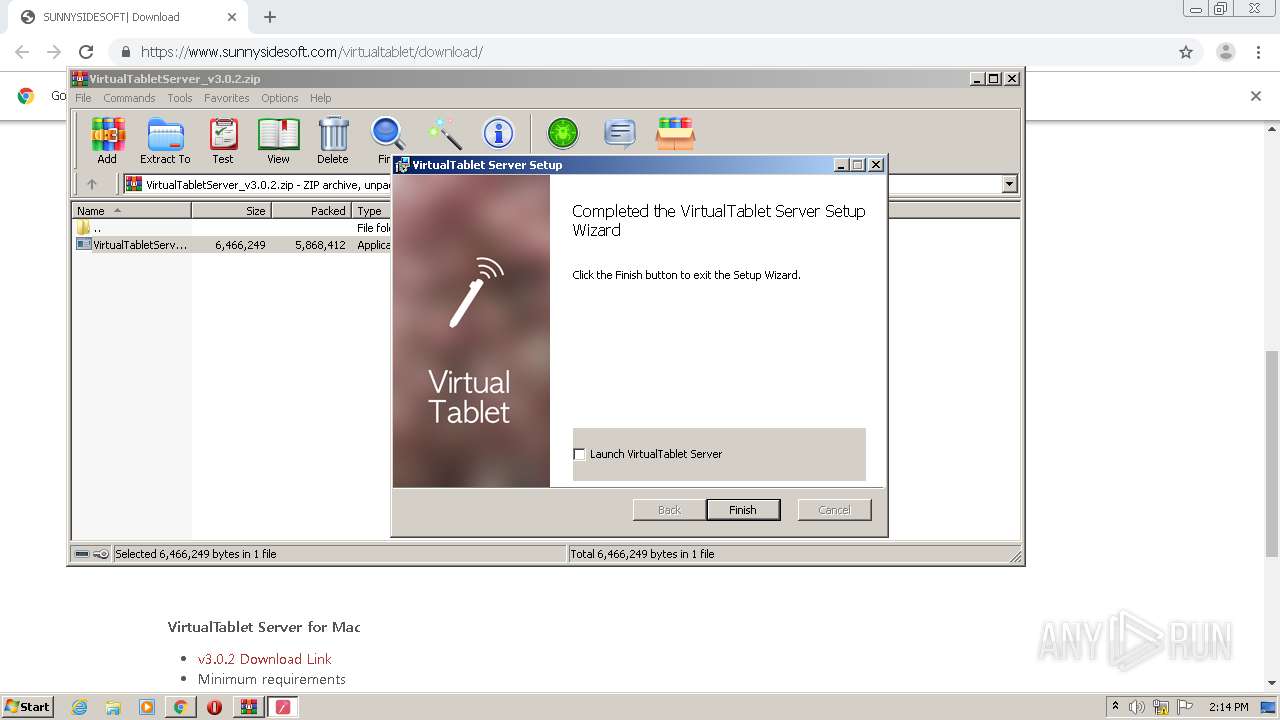
Creates a software uninstall entry
- VirtualTabletServer-v3-setup.exe (PID: 2588)
Creates files in the program directory
- VirtualTabletServer-v3-setup.exe (PID: 2588)
- VirtualTabletServer.exe (PID: 4000)
Executed as Windows Service
- vssvc.exe (PID: 2328)
Creates a directory in Program Files
- msiexec.exe (PID: 3108)
Adds / modifies Windows certificates
- DrvInst.exe (PID: 1028)
- wyUpdate.exe (PID: 4004)
Executed via COM
- DrvInst.exe (PID: 2900)
- DrvInst.exe (PID: 3792)
Creates files in the driver directory
- DrvInst.exe (PID: 2900)
- DrvInst.exe (PID: 3792)
Creates files in the Windows directory
- DrvInst.exe (PID: 2900)
- rundll32.exe (PID: 4016)
- DrvInst.exe (PID: 3792)
- wusa.exe (PID: 3908)
Removes files from Windows directory
- DrvInst.exe (PID: 2900)
- rundll32.exe (PID: 4016)
- DrvInst.exe (PID: 3792)
Uses RUNDLL32.EXE to load library
- DrvInst.exe (PID: 2900)
Drops a file with too old compile date
- msiexec.exe (PID: 3108)
Drops a file with a compile date too recent
- DrvInst.exe (PID: 2900)
- DrvInst.exe (PID: 1028)
- DrvInst.exe (PID: 3792)
Creates files in the user directory
- VirtualTabletServer.exe (PID: 4000)
Reads Environment values
- VirtualTabletServer.exe (PID: 4000)
INFO
Application launched itself
- chrome.exe (PID: 2540)
- msiexec.exe (PID: 3108)
Reads the hosts file
- chrome.exe (PID: 2540)
- chrome.exe (PID: 2336)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2328)
Creates files in the program directory
- msiexec.exe (PID: 3108)
Changes settings of System certificates
- DrvInst.exe (PID: 2900)
Searches for installed software
- DrvInst.exe (PID: 2900)
Creates a software uninstall entry
- msiexec.exe (PID: 3108)
Reads settings of System Certificates
- wyUpdate.exe (PID: 4004)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
72
Monitored processes
26
Malicious processes
12
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 468 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,12327114893495186691,16967171145161084627,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4484089304539266419 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2136 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 760 | "adb.exe" kill-server | C:\Program Files\VirtualTablet Server\adb.exe | VirtualTabletServer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=996,12327114893495186691,16967171145161084627,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=15386617675388108947 --mojo-platform-channel-handle=1016 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1028 | "C:\Program Files\VirtualTablet Server\Drivers\DrvInst.exe" install vmulti.inf djpnewton\vmulti | C:\Program Files\VirtualTablet Server\Drivers\DrvInst.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Setup API Exit code: 1 Version: 6.2.9200.16384 (win8_rtm.120725-1247) Modules
| |||||||||||||||
| 1936 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2504.31676\VirtualTabletServer-v3-setup.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2504.31676\VirtualTabletServer-v3-setup.exe | WinRAR.exe | ||||||||||||
User: admin Company: SunnysideSoft Integrity Level: MEDIUM Description: VirtualTablet Server Exit code: 3010 Version: 3.0.2 Modules
| |||||||||||||||
| 2184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2792 --on-initialized-event-handle=316 --parent-handle=320 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2328 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,12327114893495186691,16967171145161084627,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=8318637405384287912 --mojo-platform-channel-handle=1476 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2444 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,12327114893495186691,16967171145161084627,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2455725504420893567 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2352 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,12327114893495186691,16967171145161084627,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1064865129938013257 --mojo-platform-channel-handle=3464 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 177
Read events
2 556
Write events
603
Delete events
18
Modification events
| (PID) Process: | (2540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2184) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2540-13255193559215250 |
Value: 259 | |||
| (PID) Process: | (2540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2540) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2540) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
39
Suspicious files
50
Text files
221
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6001A2D7-9EC.pma | — | |
MD5:— | SHA256:— | |||
| 2540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\9e50375c-cefe-4c63-bd33-a53a6e4d12cc.tmp | — | |
MD5:— | SHA256:— | |||
| 2540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RF1545ec.TMP | text | |
MD5:— | SHA256:— | |||
| 2540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
| 2540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2540 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF1546c7.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
25
DNS requests
27
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4000 | VirtualTabletServer.exe | POST | 200 | 74.125.69.113:80 | http://www.google-analytics.com/collect | US | image | 35 b | whitelisted |
4004 | wyUpdate.exe | GET | 200 | 172.67.207.54:80 | http://static.sunnysidesoft.com/appUpdates/VTServerWin/wyserver.wys | US | compressed | 599 b | malicious |
4000 | VirtualTabletServer.exe | POST | 200 | 74.125.69.100:80 | http://www.google-analytics.com/collect | US | image | 35 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2336 | chrome.exe | 13.124.168.202:443 | www.sunnysidesoft.com | Amazon.com, Inc. | KR | unknown |
2336 | chrome.exe | 172.67.207.54:443 | static.sunnysidesoft.com | — | US | unknown |
2336 | chrome.exe | 216.58.212.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2336 | chrome.exe | 185.60.216.19:443 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
2336 | chrome.exe | 192.0.76.3:443 | stats.wp.com | Automattic, Inc | US | suspicious |
2336 | chrome.exe | 74.125.69.113:443 | www.google-analytics.com | Google Inc. | US | unknown |
2336 | chrome.exe | 172.217.16.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2336 | chrome.exe | 216.58.210.14:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2336 | chrome.exe | 74.125.69.100:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2336 | chrome.exe | 172.217.18.174:443 | clients1.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.sunnysidesoft.com |
| unknown |
accounts.google.com |
| shared |
fonts.googleapis.com |
| whitelisted |
static.sunnysidesoft.com |
| malicious |
0.gravatar.com |
| whitelisted |
1.gravatar.com |
| whitelisted |
2.gravatar.com |
| whitelisted |
jetpack.wordpress.com |
| whitelisted |
public-api.wordpress.com |
| whitelisted |
s.w.org |
| whitelisted |
Threats
Process | Message |
|---|---|
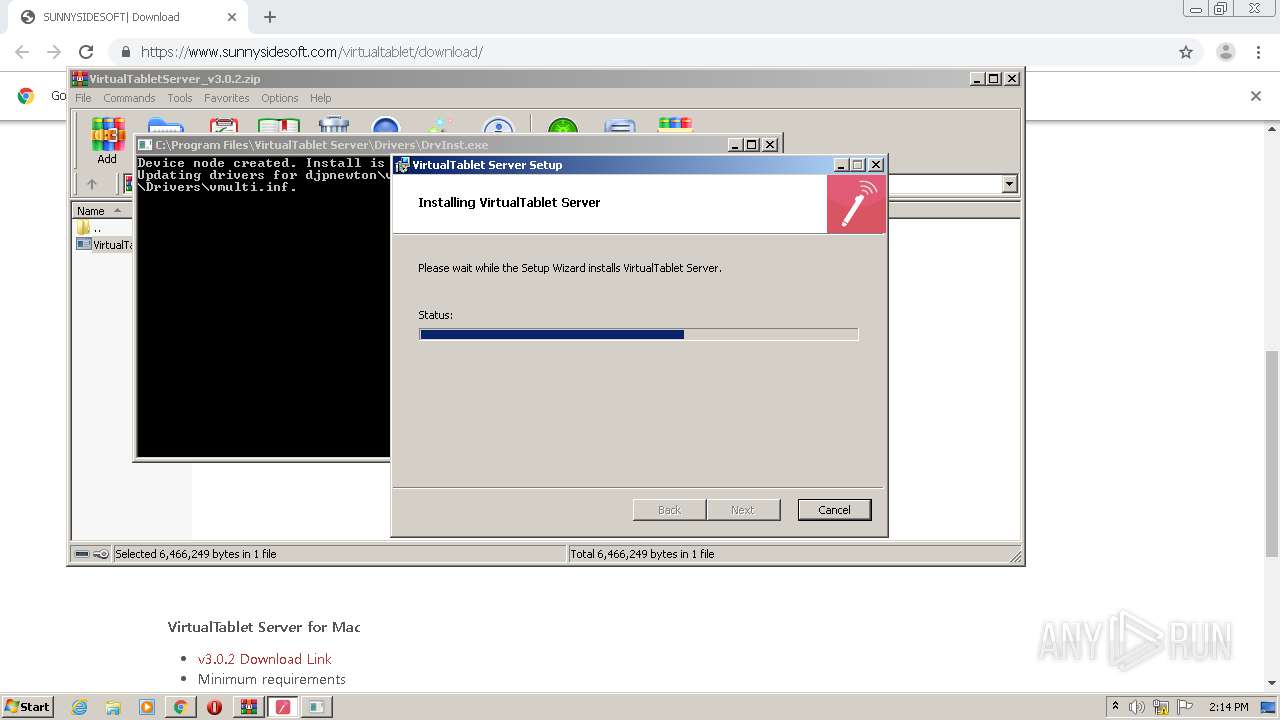
DrvInst.exe | WdfCoInstaller: [01/15/2021 14:14.11.579] DIF_INSTALLDEVICE: Pre-Processing
|
DrvInst.exe | WdfCoInstaller: [01/15/2021 14:14.11.579] ReadComponents: WdfSection for Driver Service vmulti using KMDF lib version Major 1, minor 11
|
DrvInst.exe | WdfCoInstaller: [01/15/2021 14:14.11.579] DIF_INSTALLDEVICE: Coinstaller version: 1.11.0
|
DrvInst.exe | WdfCoInstaller: [01/15/2021 14:14.11.579] DIF_INSTALLDEVICE: KMDF in-memory version: 1.9.7600
|
DrvInst.exe | WdfCoInstaller: [01/15/2021 14:14.11.595] DIF_INSTALLDEVICE: KMDF on-disk version: 1.9.7600
|
DrvInst.exe | WdfCoInstaller: [01/15/2021 14:14.11.595] Service Wdf01000 is running
|
DrvInst.exe | WdfCoInstaller: [01/15/2021 14:14.11.595] DIF_INSTALLDEVICE: Reboot is required, because the in-memory KMDF version is older than KmdfLibraryVersion for service vmulti.
|
DrvInst.exe | WdfCoInstaller: [01/15/2021 14:14.11.595] DIF_INSTALLDEVICE: Update is required, because the on-disk KMDF version is older than the coinstaller
|
DrvInst.exe | WdfCoInstaller: [01/15/2021 14:14.11.626] Invoking "C:\Windows\system32\wusa.exe "C:\Windows\Temp\WdfTemp\Kmdf-1.11-Win-6.1.msu" /quiet /norestart".
|
DrvInst.exe | WdfCoInstaller: [01/15/2021 14:14.23.642] The package was installed successfully: error(3010) The requested operation is successful. Changes will not be effective until the system is rebooted.
.
|