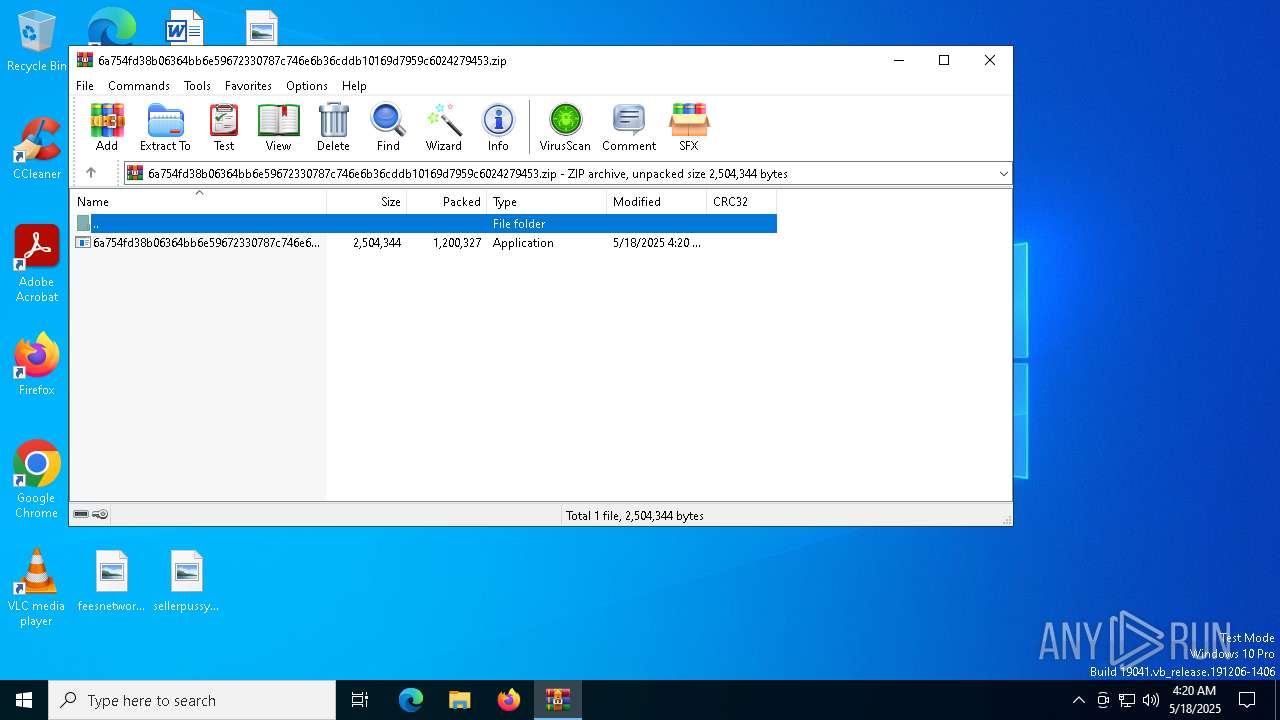
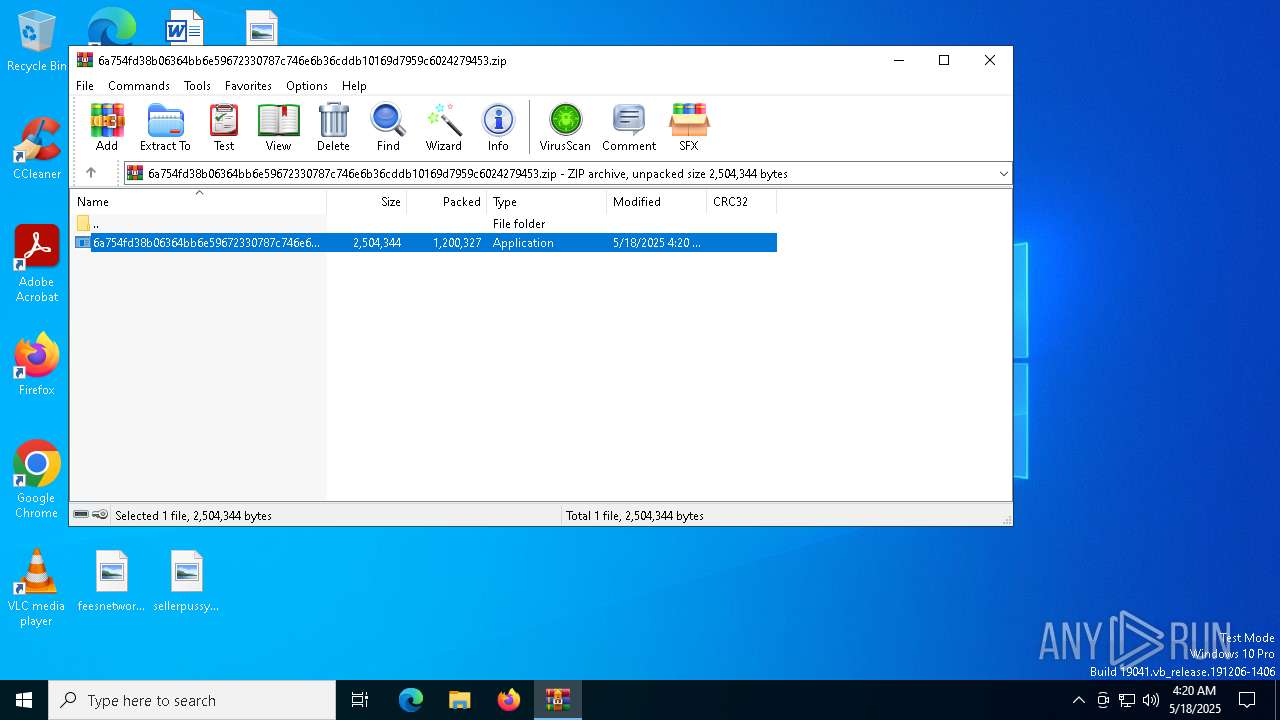
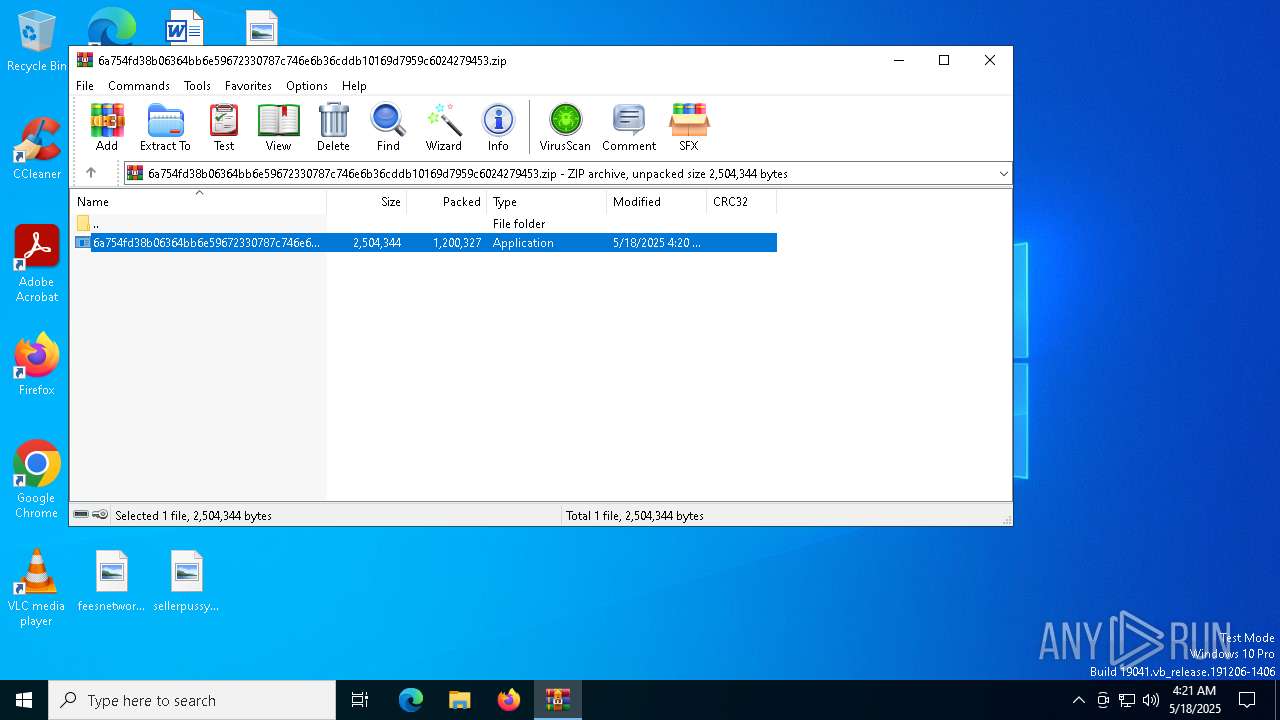
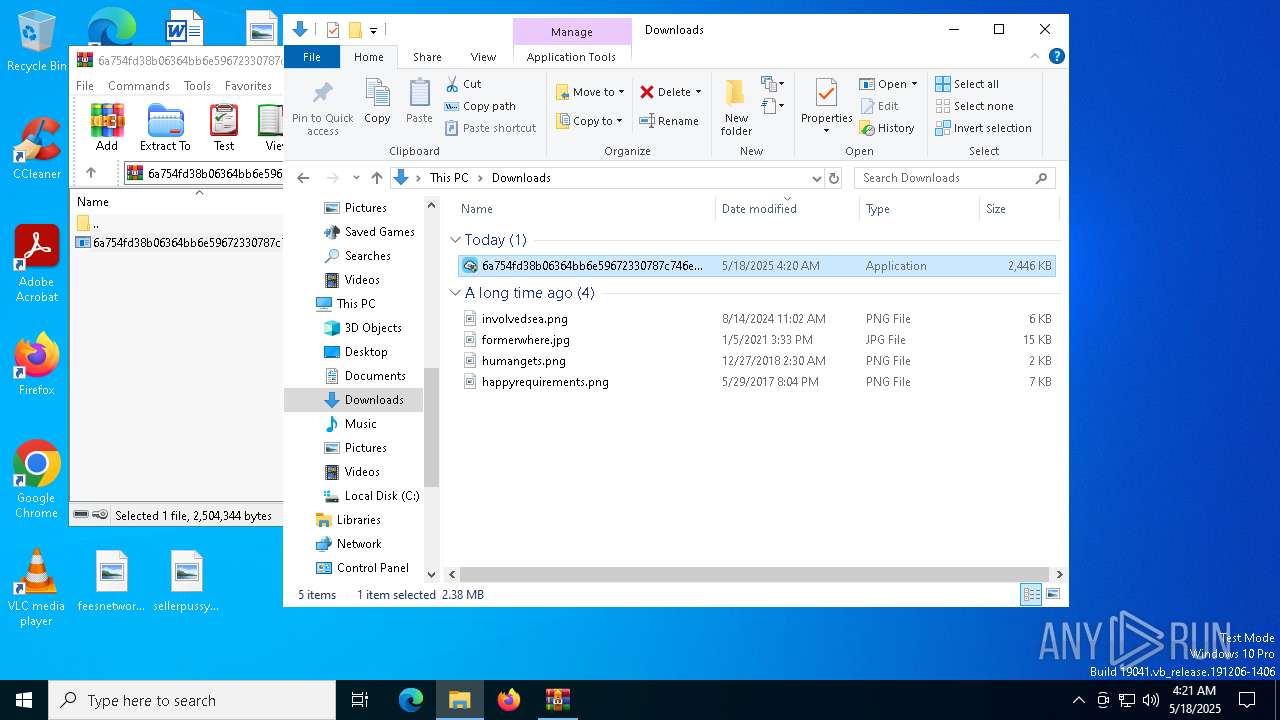
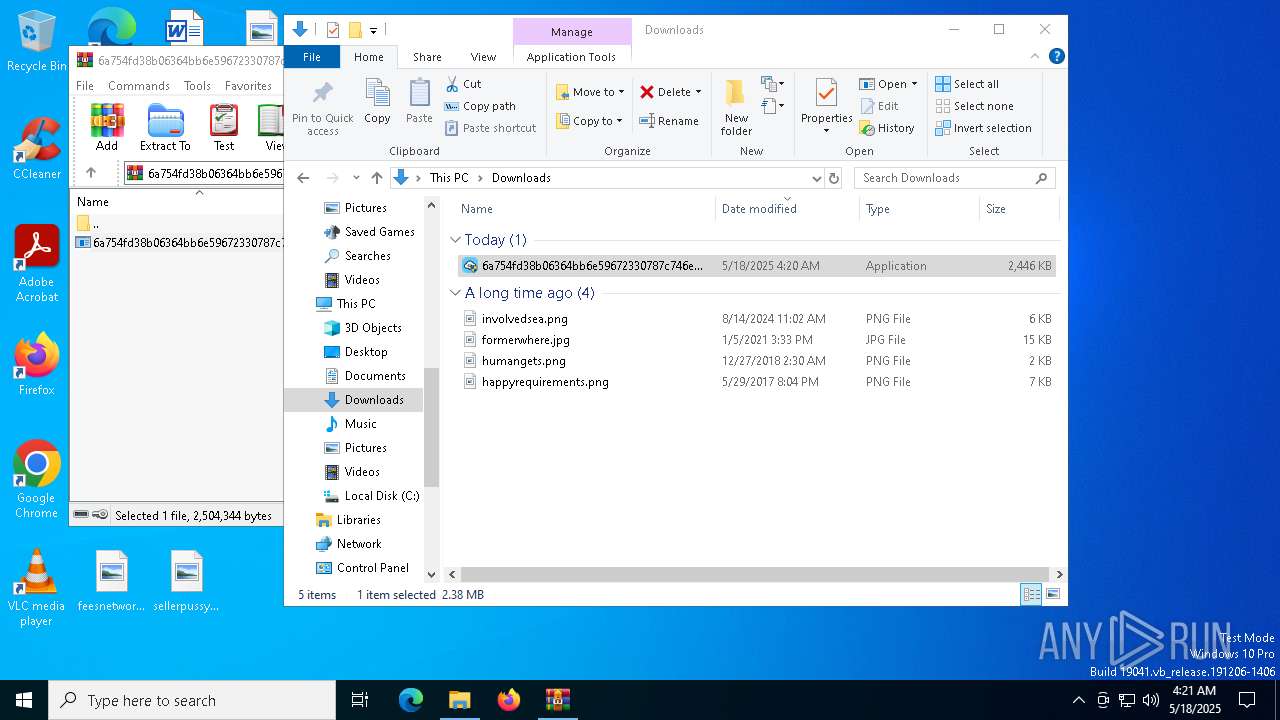
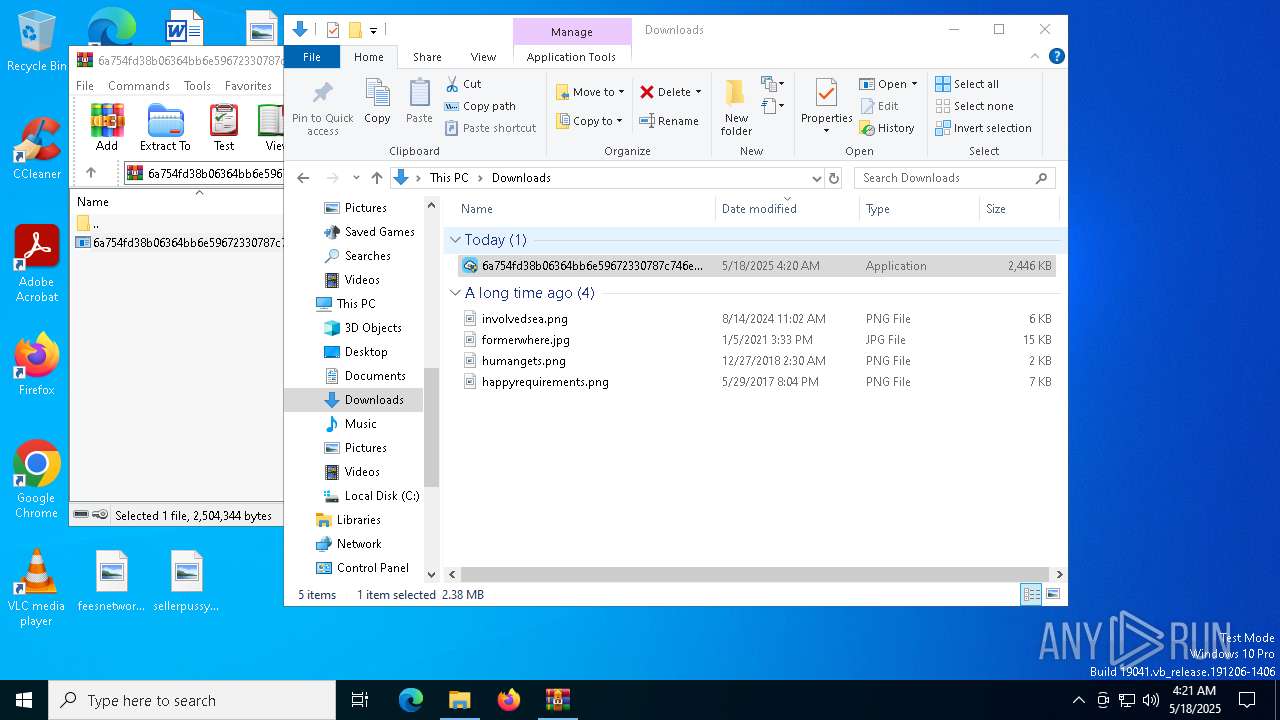
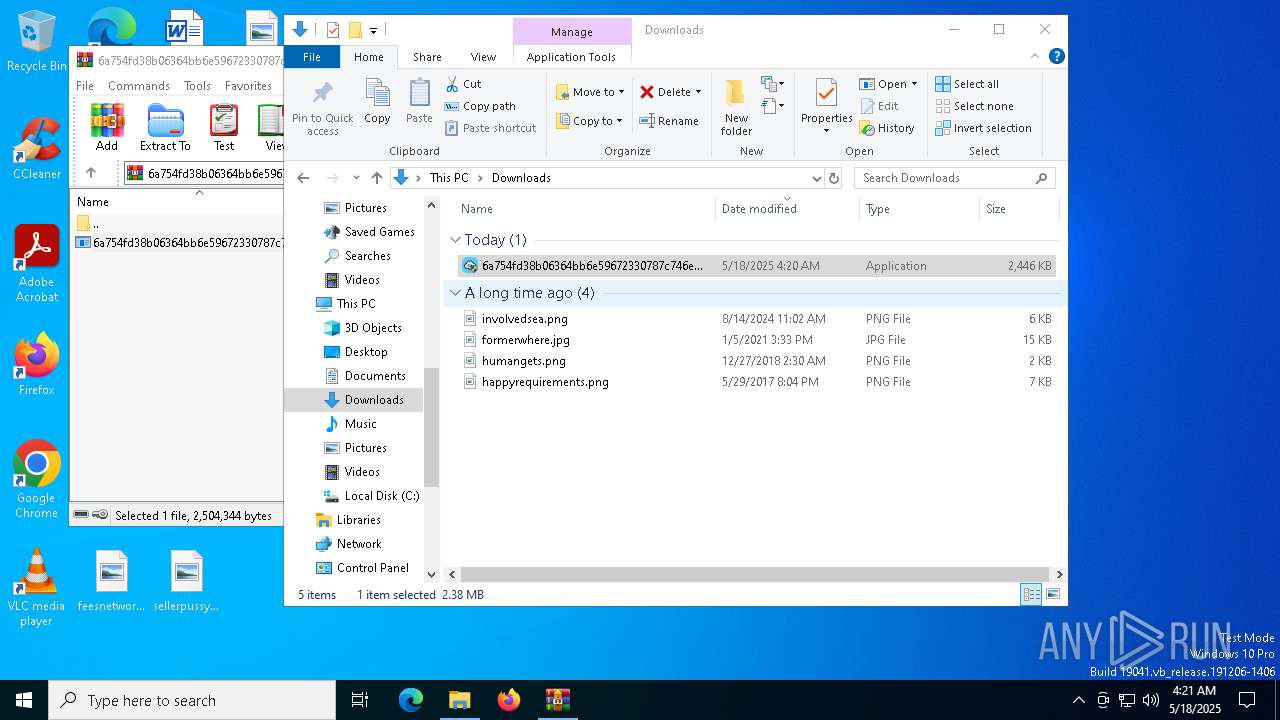
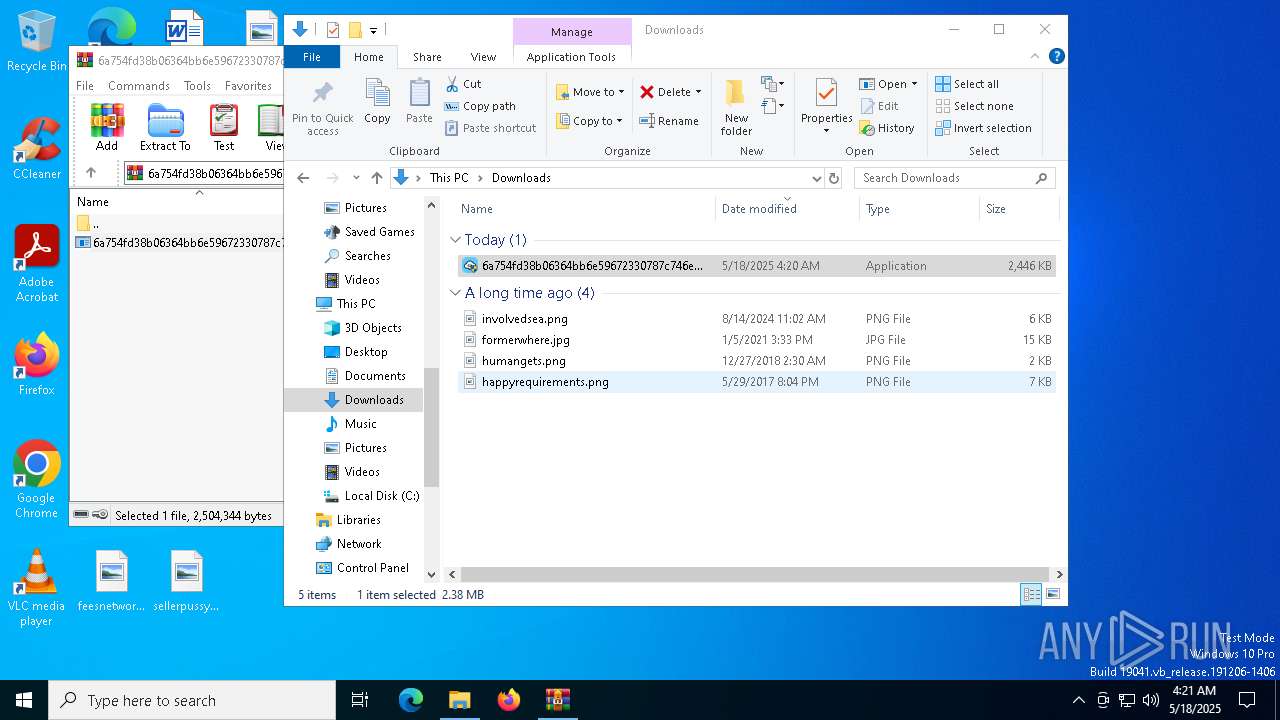
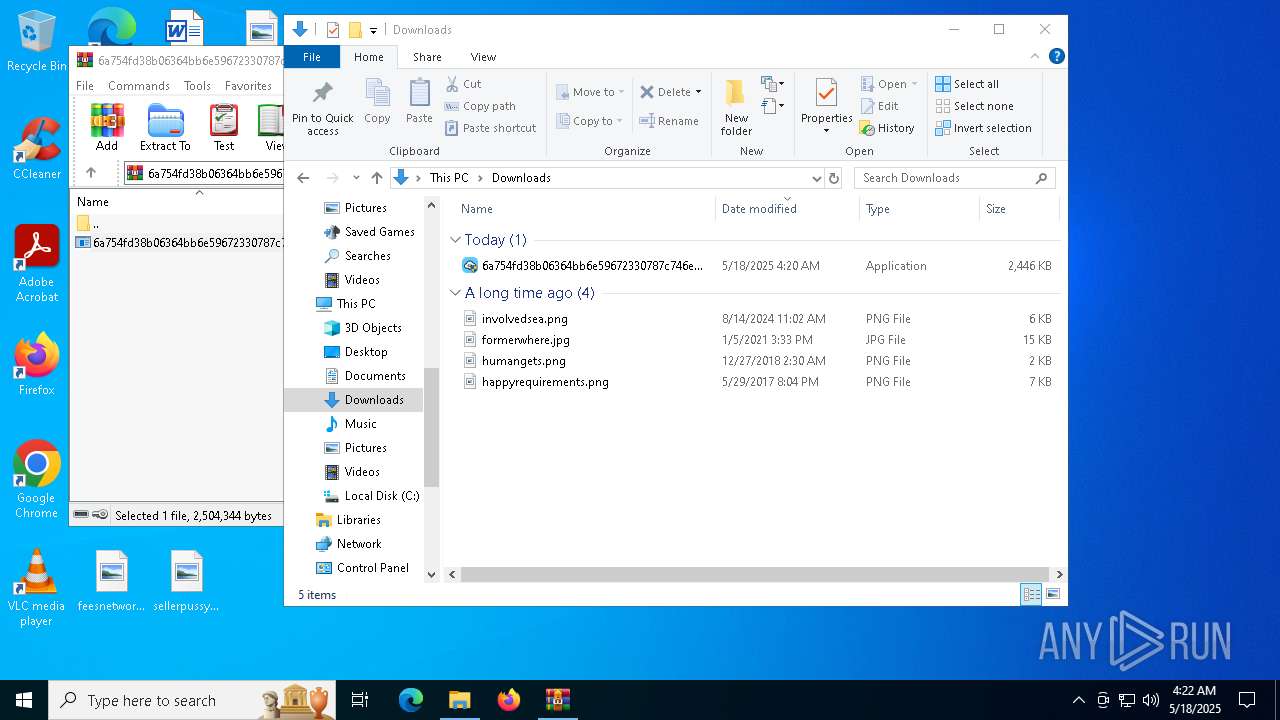
| File name: | 6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.zip |
| Full analysis: | https://app.any.run/tasks/cbdaf4ec-2e85-4e9e-8219-3c8f96edb751 |
| Verdict: | Malicious activity |
| Analysis date: | May 18, 2025, 04:20:47 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
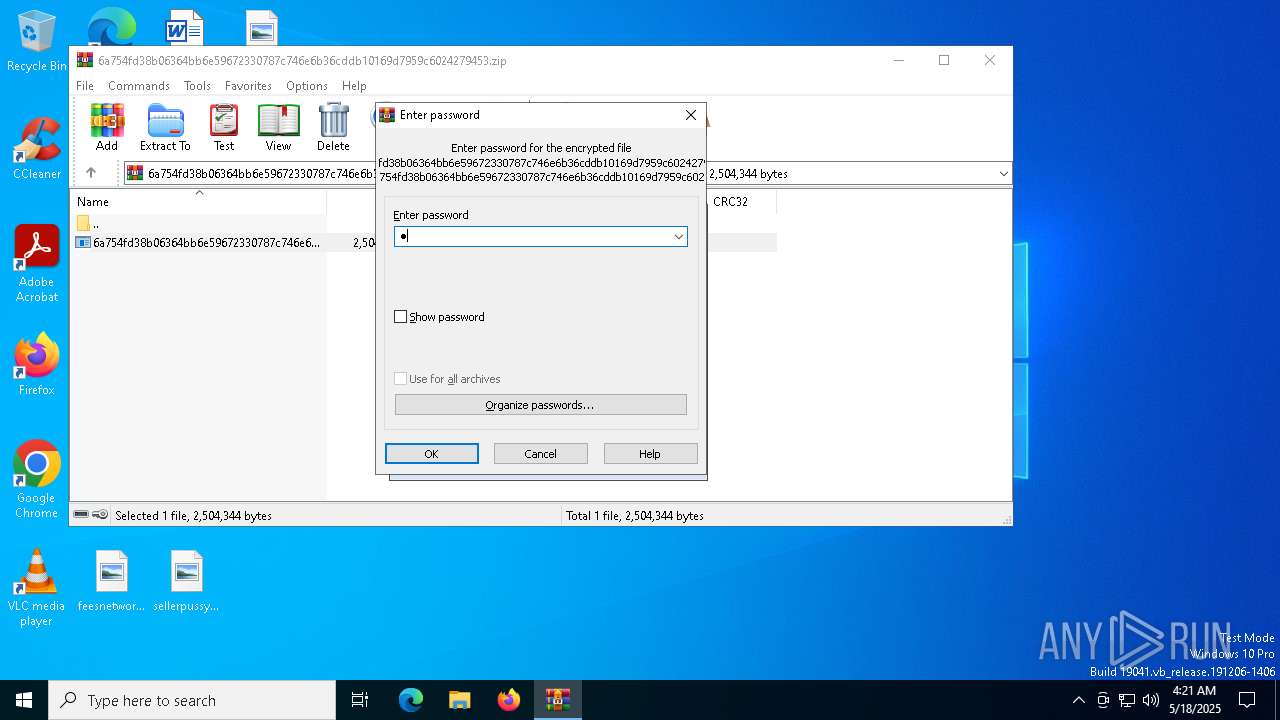
| File info: | Zip archive data, at least v5.1 to extract, compression method=AES Encrypted |
| MD5: | 2D561A1E8C0619135BB91EA40CCCB307 |
| SHA1: | 1D2725C747D32FAB122F6E59EE06C6817674319E |
| SHA256: | AC5DCF2A40820915A39E9C1F775A27EE0814B1F90BF2B0AC43C5BC2F0A86A47D |
| SSDEEP: | 49152:q3TXsI+AjdWUgCw6KWvnmsoIRj7m1seXibYgoZUZUOFMvMOpFYs88po9WFao0May:q3TsAjdWUgCRKen2i+WeXiEhzOkM888x |
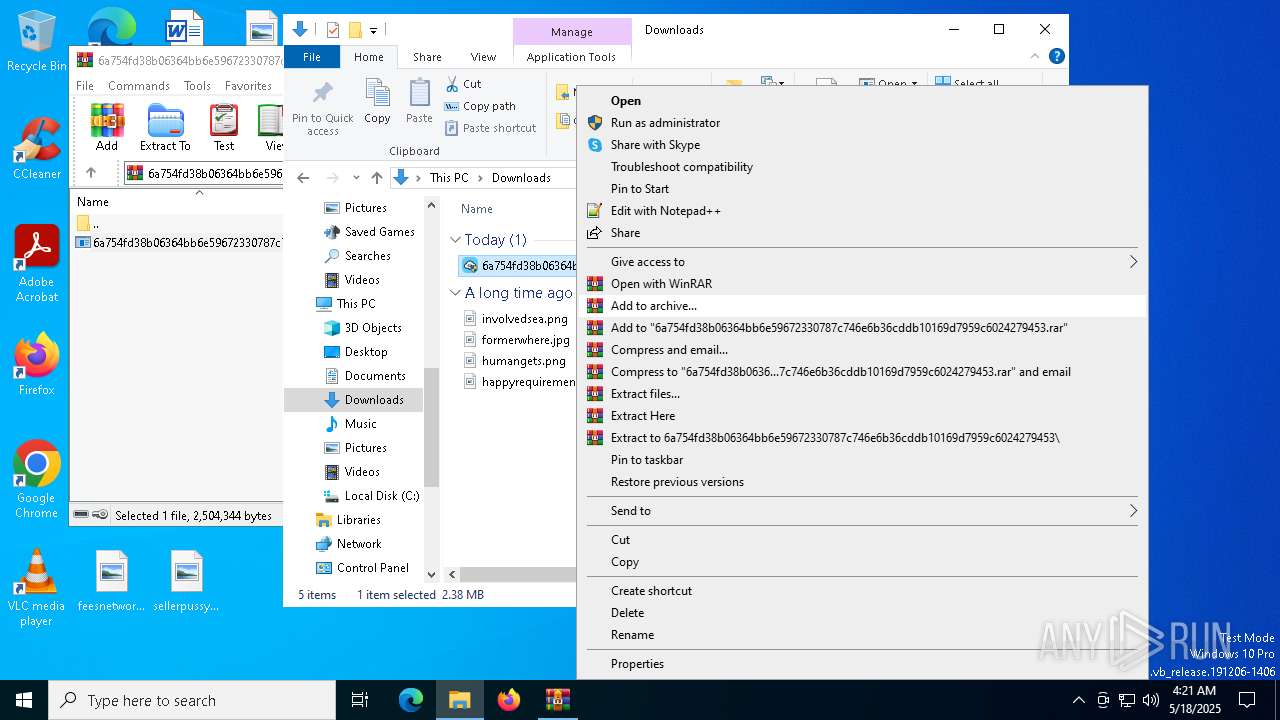
MALICIOUS
Changes the autorun value in the registry
- 6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.exe (PID: 8108)
Adds path to the Windows Defender exclusion list
- 6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.exe (PID: 8108)
Changes Windows Defender settings
- 6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.exe (PID: 8108)
Changes powershell execution policy (Bypass)
- 6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.exe (PID: 8108)
Bypass execution policy to execute commands
- powershell.exe (PID: 4208)
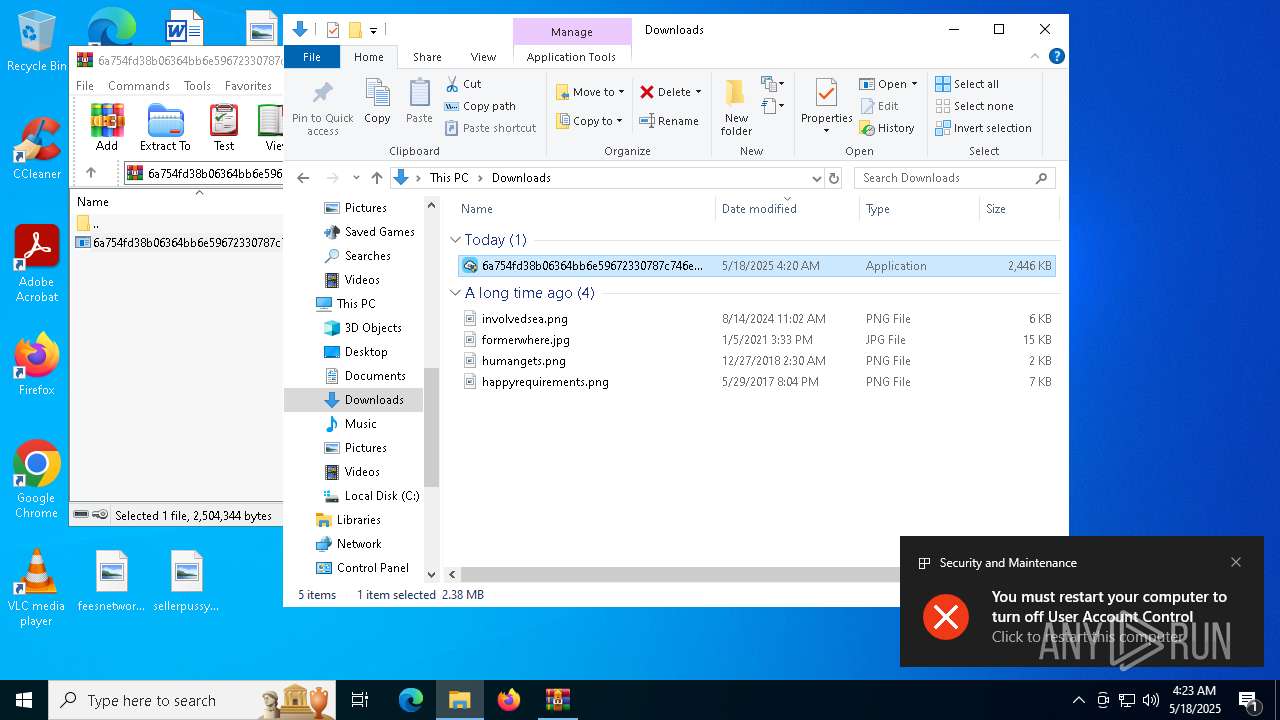
UAC/LUA settings modification
- 6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.exe (PID: 8108)
Executing a file with an untrusted certificate
- c2W0ED4.exe (PID: 7620)
SUSPICIOUS
There is functionality for taking screenshot (YARA)
- 6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.exe (PID: 8108)
- c2W0ED4.exe (PID: 7620)
Reads security settings of Internet Explorer
- 6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.exe (PID: 8108)
- ShellExperienceHost.exe (PID: 7704)
Contacting a server suspected of hosting an CnC
- 6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.exe (PID: 8108)
Executable content was dropped or overwritten
- 6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.exe (PID: 8108)
Script adds exclusion path to Windows Defender
- 6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.exe (PID: 8108)
Starts POWERSHELL.EXE for commands execution
- 6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.exe (PID: 8108)
Connects to unusual port
- c2W0ED4.exe (PID: 7620)
INFO
The sample compiled with chinese language support
- WinRAR.exe (PID: 4880)
Executable content was dropped or overwritten
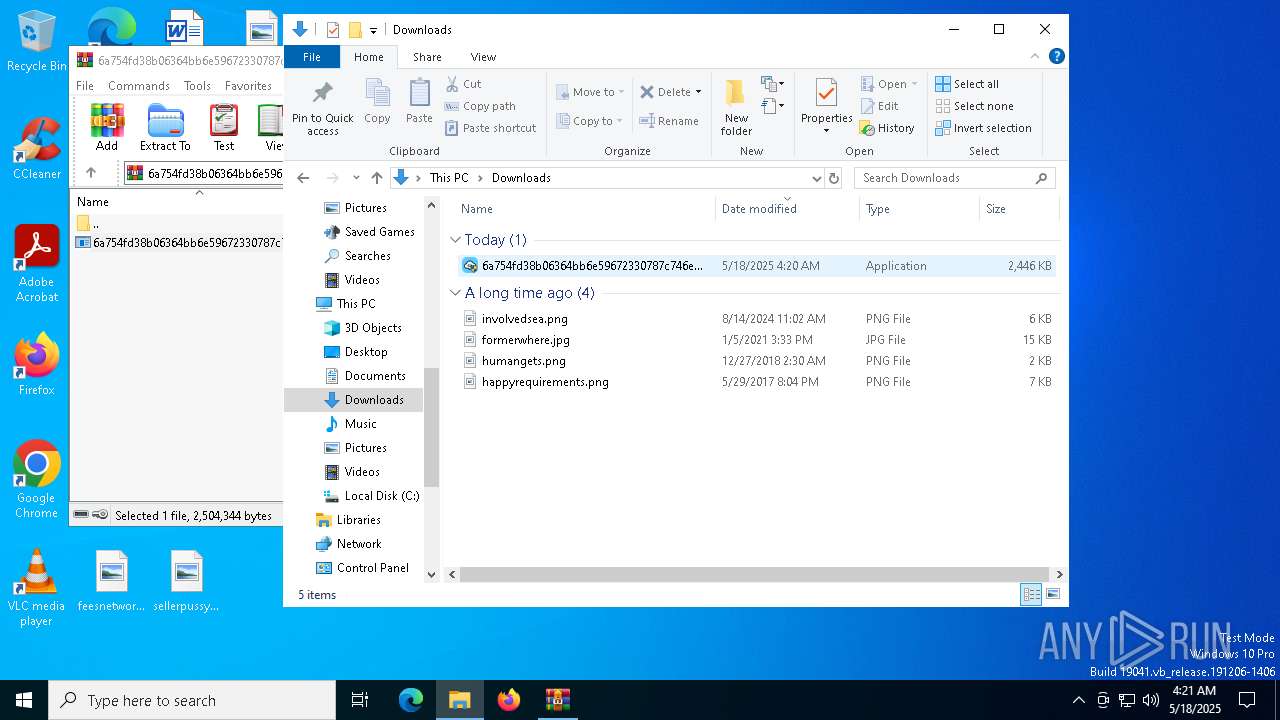
- WinRAR.exe (PID: 4880)
Checks supported languages
- 6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.exe (PID: 8108)
- 6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.exe (PID: 7448)
- ShellExperienceHost.exe (PID: 7704)
- c2W0ED4.exe (PID: 7620)
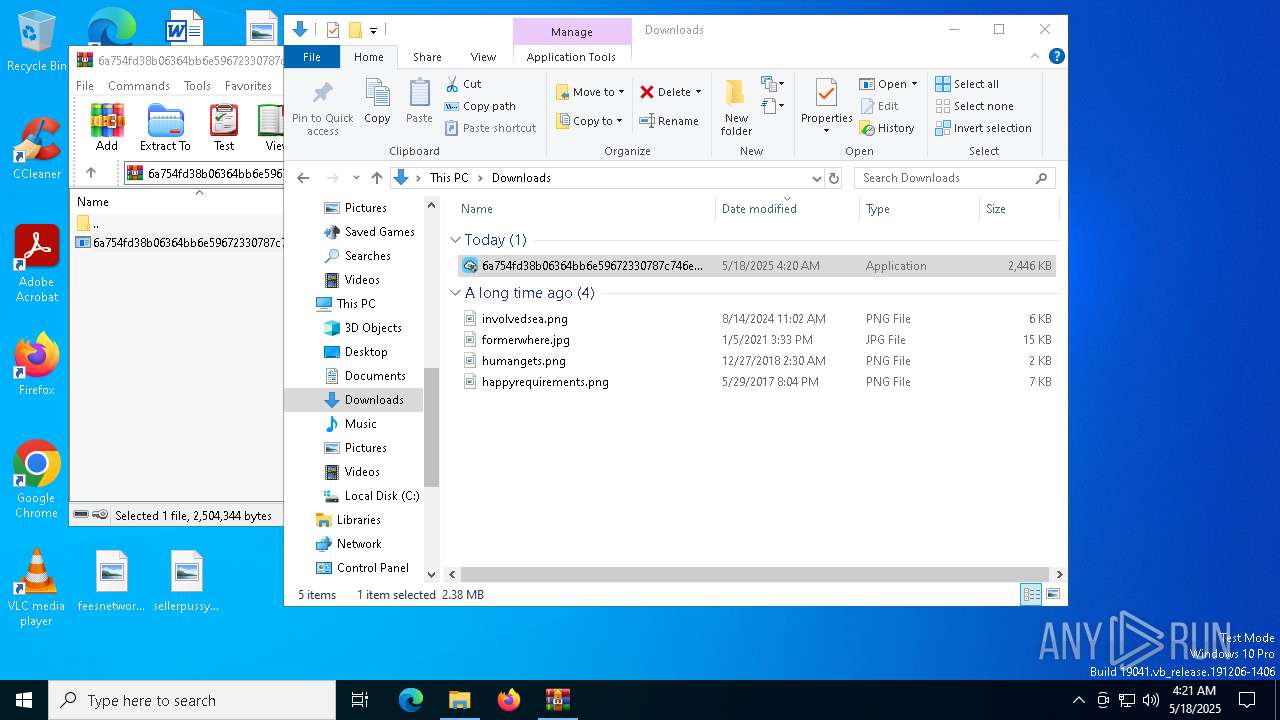
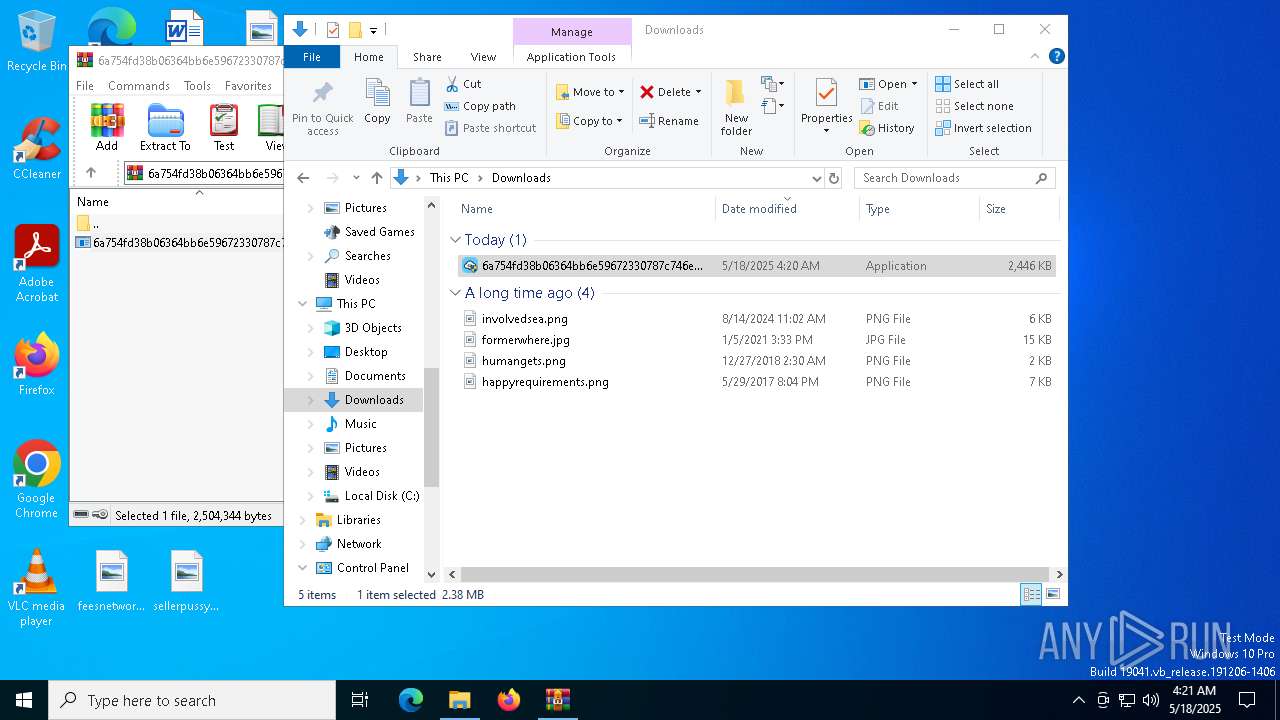
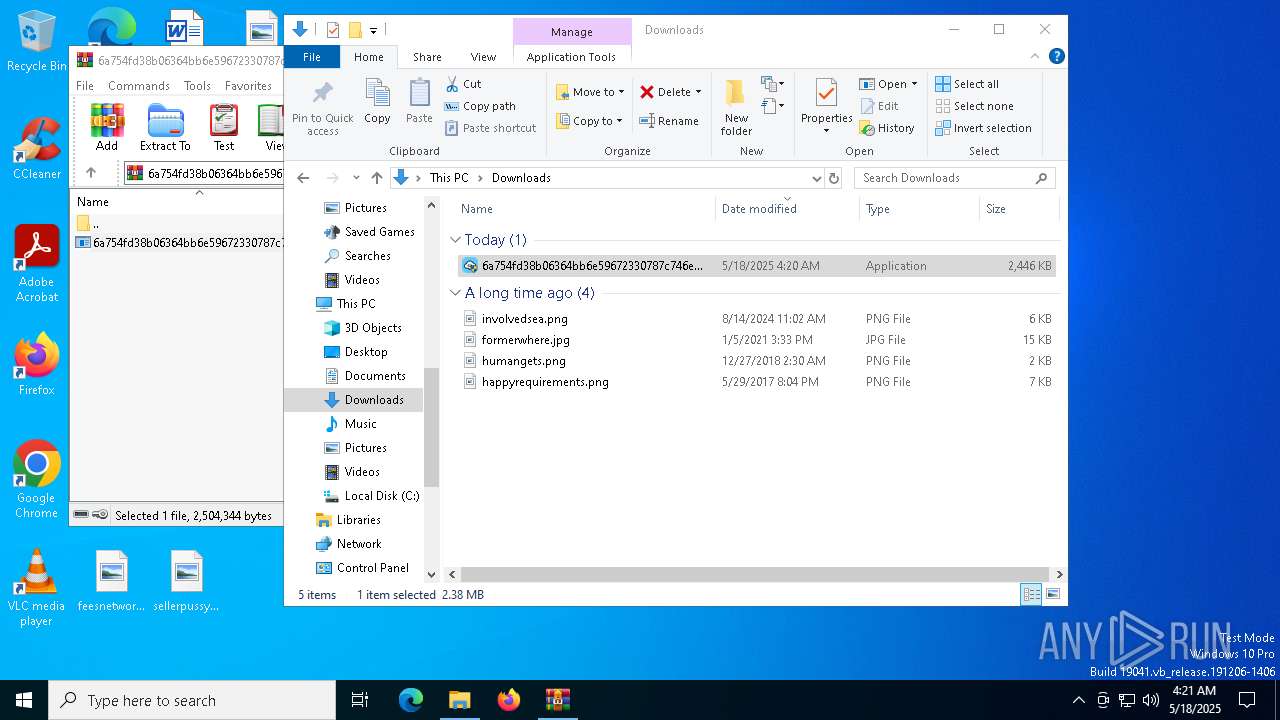
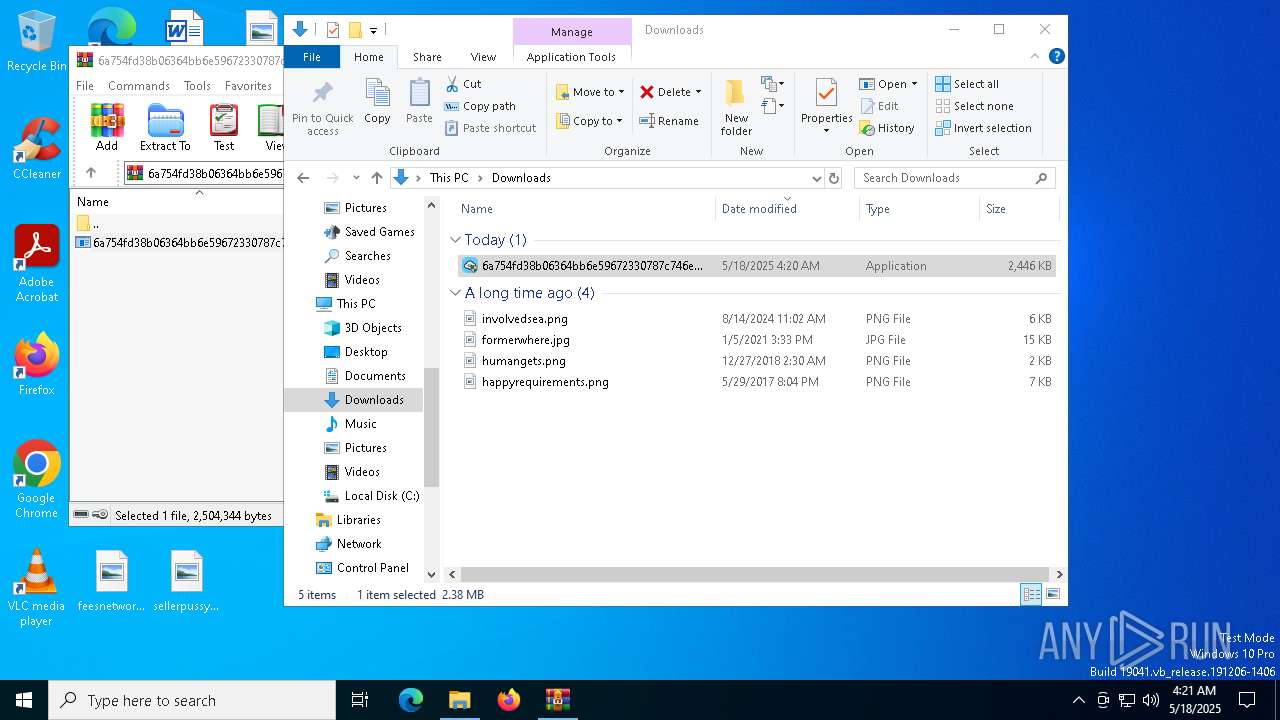
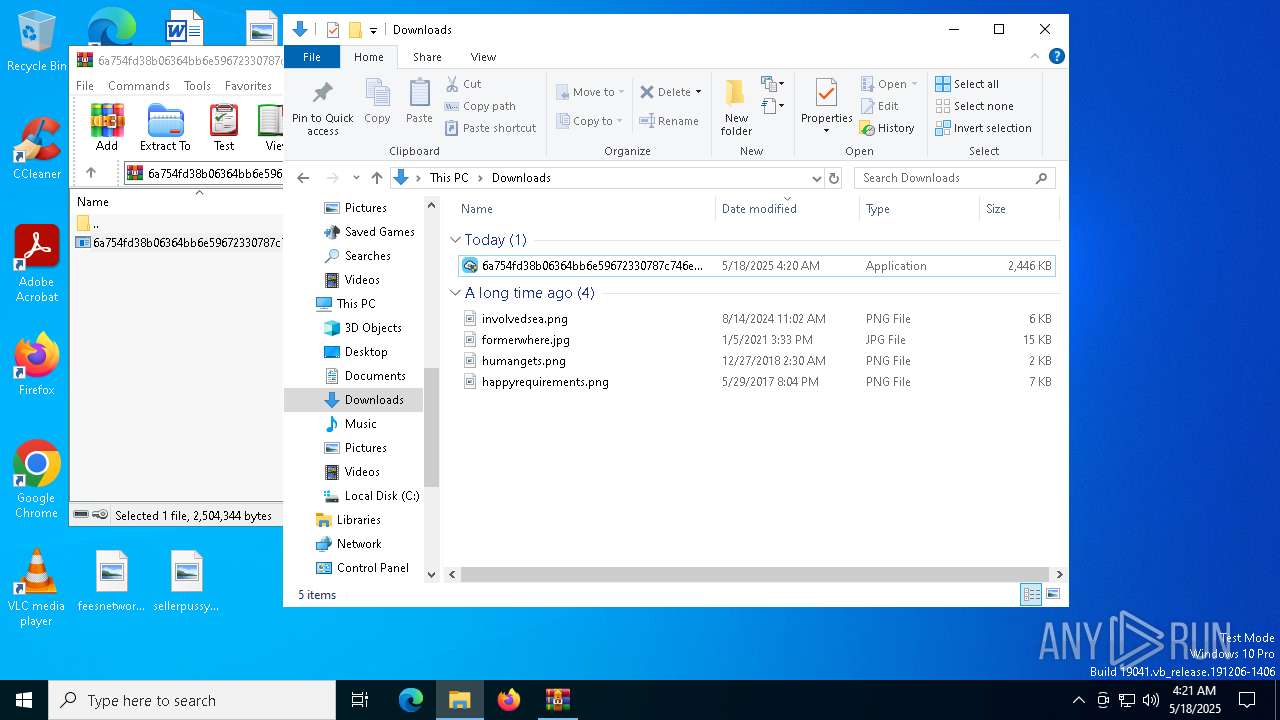
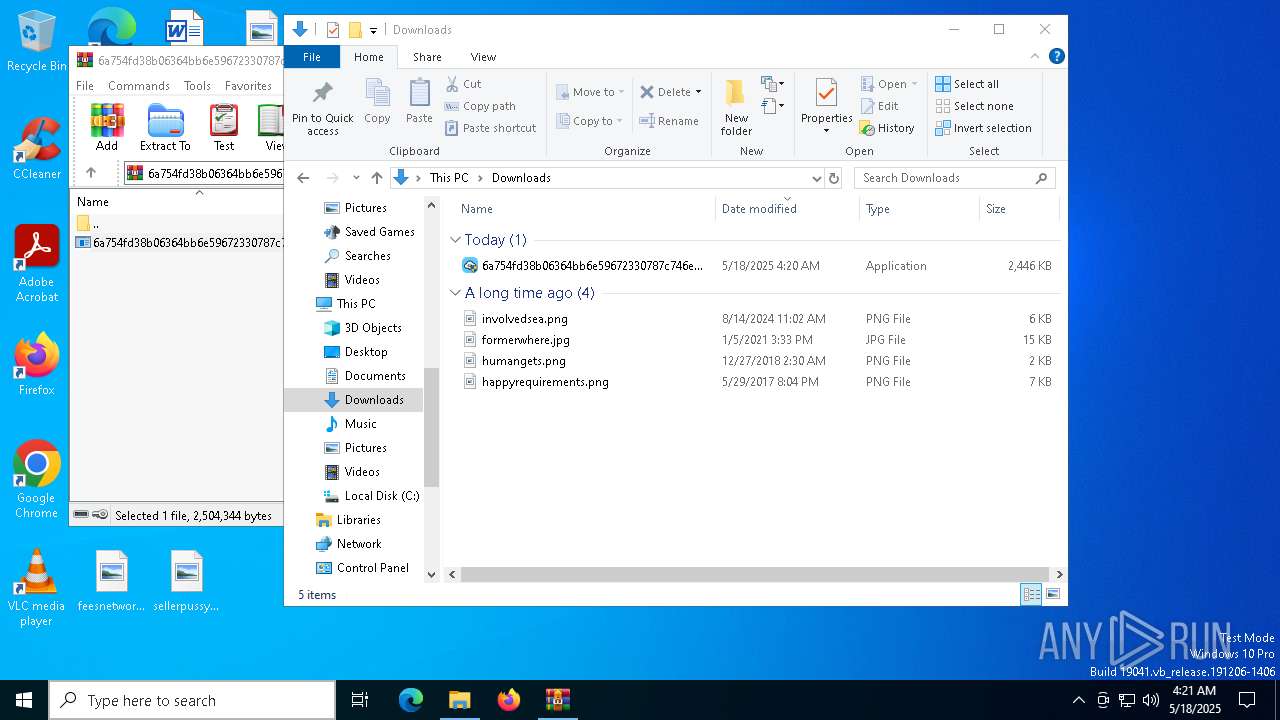
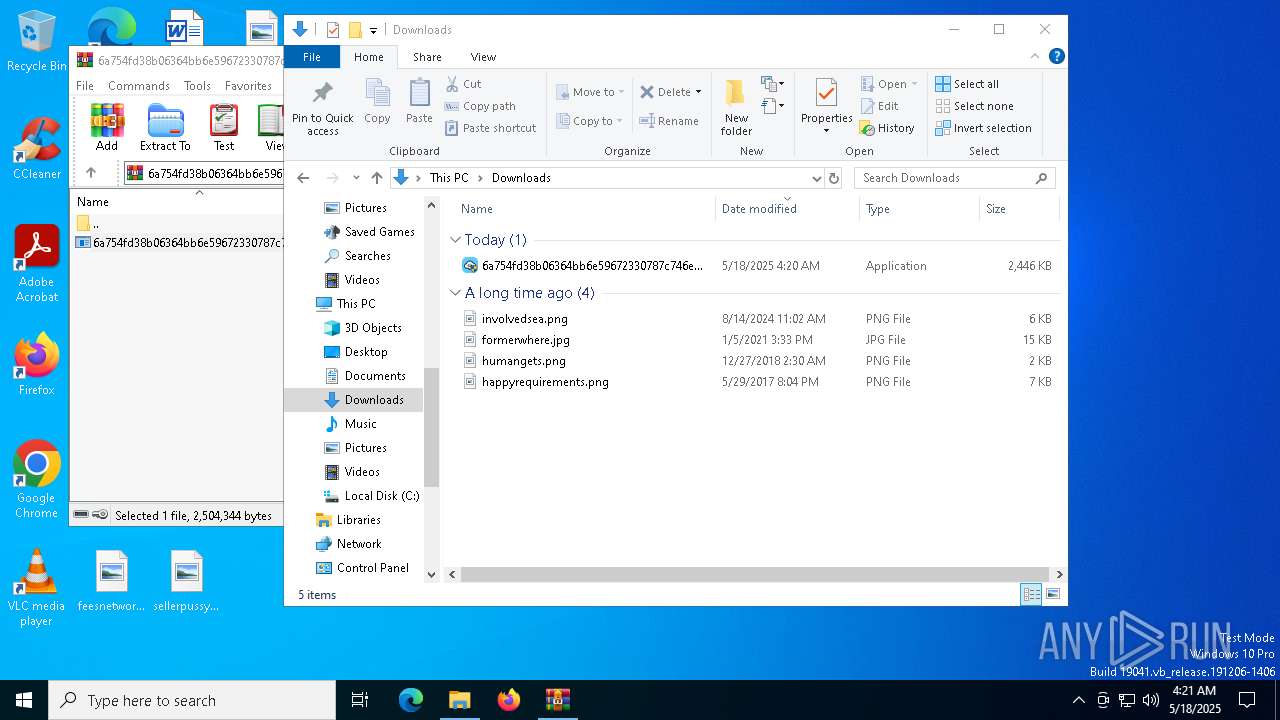
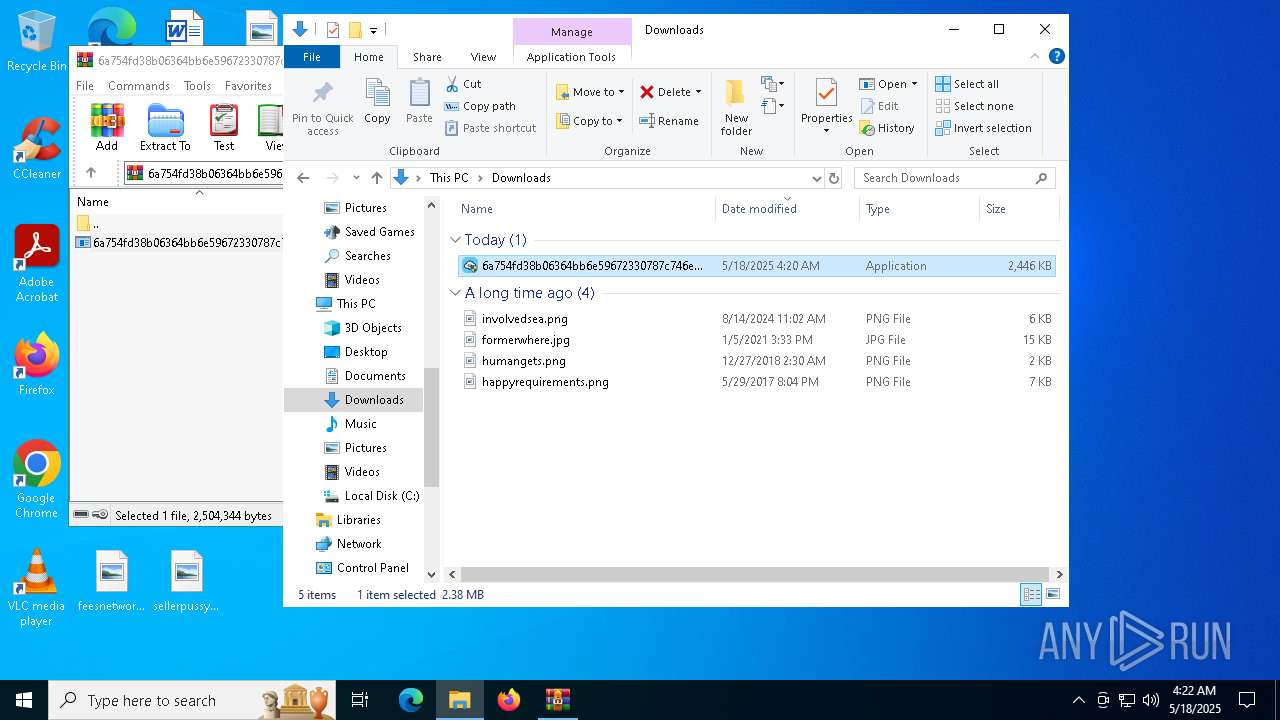
Manual execution by a user
- 6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.exe (PID: 8108)
- 6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.exe (PID: 7372)
- 6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.exe (PID: 7448)
Reads the software policy settings
- slui.exe (PID: 7288)
- slui.exe (PID: 7236)
Reads the computer name
- 6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.exe (PID: 8108)
- ShellExperienceHost.exe (PID: 7704)
Checks proxy server information
- 6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.exe (PID: 8108)
- slui.exe (PID: 7236)
Creates files or folders in the user directory
- 6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.exe (PID: 8108)
Creates files in the program directory
- 6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.exe (PID: 8108)
Process checks computer location settings
- 6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.exe (PID: 8108)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 4208)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4208)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2025:05:18 04:20:42 |
| ZipCRC: | 0x6c0420d0 |
| ZipCompressedSize: | 1200327 |
| ZipUncompressedSize: | 2504344 |
| ZipFileName: | 6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.exe |
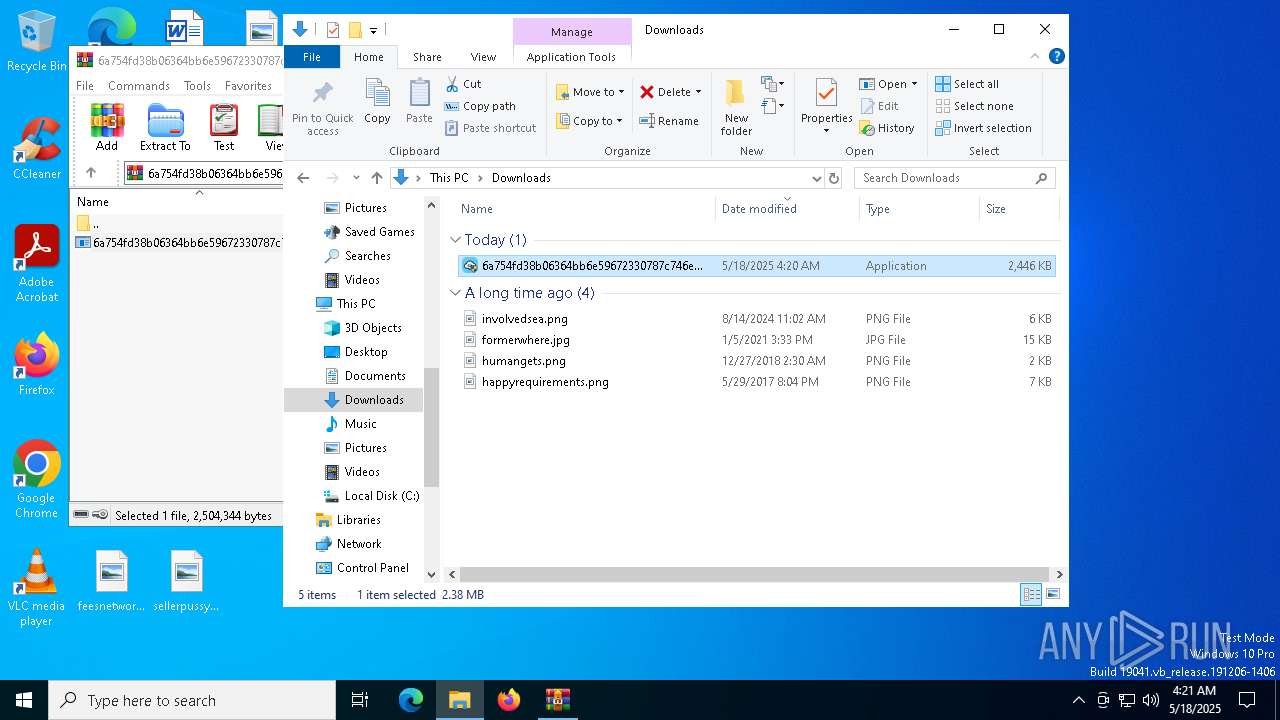
Total processes
152
Monitored processes
12
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1280 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4208 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy Bypass Add-MpPreference -ExclusionPath 'C:\Program Files (x86)\h2Ar3z' -Force | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | — | 6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4880 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 7236 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7252 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7288 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7372 | "C:\Users\admin\Downloads\6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.exe" | C:\Users\admin\Downloads\6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.exe | — | explorer.exe | |||||||||||
User: admin Company: 云吞 Integrity Level: MEDIUM Description: 云吞 Exit code: 3221226540 Version: 1.0.116.0 Modules
| |||||||||||||||
| 7448 | "C:\Users\admin\Downloads\6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.exe" | C:\Users\admin\Downloads\6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.exe | explorer.exe | ||||||||||||
User: admin Company: 云吞 Integrity Level: HIGH Description: 云吞 Exit code: 4294967295 Version: 1.0.116.0 Modules
| |||||||||||||||
| 7620 | "C:\Program Files (x86)\h2Ar3z\c2W0ED4.exe" | C:\Program Files (x86)\h2Ar3z\c2W0ED4.exe | 6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 7704 | "C:\WINDOWS\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe" -ServerName:App.AppXtk181tbxbce2qsex02s8tw7hfxa9xb3t.mca | C:\Windows\SystemApps\ShellExperienceHost_cw5n1h2txyewy\ShellExperienceHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shell Experience Host Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
10 507
Read events
10 475
Write events
19
Delete events
13
Modification events
| (PID) Process: | (4880) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (4880) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4880) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4880) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.zip | |||
| (PID) Process: | (4880) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4880) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4880) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4880) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4880) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 3 |
Value: | |||
| (PID) Process: | (4880) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Preferences | |||
Executable files
2
Suspicious files
4
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8108 | 6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.exe | C:\Program Files (x86)\h2Ar3z\libcef.dll | — | |
MD5:— | SHA256:— | |||
| 8108 | 6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.exe | C:\Program Files (x86)\h2Ar3z\t3d.tmp | compressed | |
MD5:32DEC240057078BC4EB5F13A6B69E6F4 | SHA256:699E5521EF4B5258C777E9B0AF41304F71E4A0CA6B31620D4E8009DE4091F836 | |||
| 4880 | WinRAR.exe | C:\Users\admin\Downloads\6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.exe | executable | |
MD5:A574F73378CFF4B73AEC42CF71671C12 | SHA256:6A754FD38B06364BB6E59672330787C746E6B36CDDB10169D7959C6024279453 | |||
| 4208 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_wvwykgz4.4fd.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4208 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_tfajh2tj.hom.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 8108 | 6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\RR3E01RZ\tan2[1].bmp | binary | |
MD5:E7576A7EF62A578C4A0F75AA6A2E72B5 | SHA256:2161A60C51C3989C3B55E5B887AC1D6B4E7FD0258FCA25596102B647B5AE5C3B | |||
| 4208 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:6D358E2E4DD5AB4F41330C35FE5D8A7F | SHA256:FC657DBFF339DC77BAC522F85DCCBDFDC8F4FE93F129A8199AA11794D9F66568 | |||
| 8108 | 6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.exe | C:\Program Files (x86)\h2Ar3z\t5d.tmp | image | |
MD5:5752242C89D5F5888CC76E50E5379498 | SHA256:55FEAD8B55F17FD73CF3AFDD5DFFB0F0535F3D4AF3A57371B91422941A541024 | |||
| 8108 | 6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.exe | C:\Program Files (x86)\h2Ar3z\t4d.tmp | binary | |
MD5:A180B827058D03159925C5A3629990A6 | SHA256:966953FBD039D449C95B2D12C389B1C407D200FBE35D25535B91F0A23B6E1A4F | |||
| 4208 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_foxjg3ab.gf3.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
136
DNS requests
21
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.42:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7880 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
8108 | 6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.exe | GET | 200 | 188.114.96.3:80 | http://td49t44g.com/1/tan2.bmp | unknown | — | — | unknown |
7880 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8108 | 6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.exe | HEAD | 200 | 188.114.96.3:80 | http://td49t44g.com/1/text.bmp | unknown | — | — | unknown |
8108 | 6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.exe | GET | 200 | 188.114.96.3:80 | http://td49t44g.com/1/text.bmp | unknown | — | — | unknown |
8108 | 6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.exe | HEAD | 200 | 188.114.96.3:80 | http://td49t44g.com/1/o.bmp | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
7000 | RUXIMICS.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.42:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
8108 | 6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.exe | Malware Command and Control Activity Detected | ET MALWARE Winos4.0 Framework Fake BMP Download Containing XOR encoded .dll |
8108 | 6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.exe | Malware Command and Control Activity Detected | ET MALWARE Winos4.0 Framework Fake BMP Download Containing XOR encoded .dll |
8108 | 6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.exe | Malware Command and Control Activity Detected | ET MALWARE Winos4.0 Framework Fake BMP Download Containing XOR encoded .dll |
8108 | 6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.exe | Malware Command and Control Activity Detected | ET MALWARE Winos4.0 Framework Fake BMP Download Containing XOR encoded .dll |
8108 | 6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.exe | Malware Command and Control Activity Detected | ET MALWARE Winos4.0 Framework Fake BMP Download Containing XOR encoded .dll |
8108 | 6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.exe | Malware Command and Control Activity Detected | ET MALWARE Winos4.0 Framework Fake BMP Download Containing XOR encoded .dll |
8108 | 6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.exe | Malware Command and Control Activity Detected | ET MALWARE Winos4.0 Framework Fake BMP Download Containing XOR encoded .dll |
8108 | 6a754fd38b06364bb6e59672330787c746e6b36cddb10169d7959c6024279453.exe | Malware Command and Control Activity Detected | ET MALWARE Winos4.0 Framework Fake BMP Download Containing XOR encoded .dll |